Validation Frameworks in Forensics: A Comparative Analysis of Traditional and Digital Methodologies
This article provides a comprehensive analysis of validation frameworks across traditional and digital forensic disciplines.
Validation Frameworks in Forensics: A Comparative Analysis of Traditional and Digital Methodologies
Abstract
This article provides a comprehensive analysis of validation frameworks across traditional and digital forensic disciplines. It explores the foundational principles of forensic validation, examines methodological applications in evolving crime labs, addresses critical troubleshooting and optimization challenges, and delivers a rigorous comparative assessment. Designed for forensic researchers, scientists, and developers, the content synthesizes current standards, tool-specific considerations, and emerging trends to equip professionals with the knowledge to ensure evidentiary reliability and legal admissibility in a rapidly changing technological landscape.
Core Principles and Definitions: Building the Foundation of Forensic Validation
Forensic validation is a fundamental testing and confirmation practice implemented across all forensic disciplines to ensure the tools and methods used to analyze evidence are accurate, reliable, and legally admissible [1]. It functions as a critical safeguard against error, bias, and misinterpretation, forming the bedrock of scientific credibility in judicial proceedings. The rapid evolution of technology, particularly in digital forensics where new operating systems, encrypted applications, and cloud storage continuously emerge, demands constant revalidation of forensic tools and practices [1]. Within this context, validation is systematically broken down into three core components: Tool Validation, which ensures forensic software or hardware performs as intended; Method Validation, which confirms procedures produce consistent outcomes; and Analysis Validation, which evaluates whether interpreted data accurately reflects its true meaning and context [1]. This framework ensures that forensic conclusions are supported by scientific integrity, are reproducible under scrutiny, and are robust enough to withstand legal challenges.
Core Components of Forensic Validation
Tool Validation
Tool validation focuses on the forensic software and hardware used to extract and report data. It verifies that these tools function correctly without altering the original source evidence. In digital forensics, tools like Cellebrite UFED, Oxygen Forensic Detective (OFD), and OpenText EnCase Forensic are frequently updated, and each update necessitates re-validation to ensure parsing capabilities and data extraction remain accurate [2] [1]. Without this step, tools may introduce errors or omit critical data. For instance, two different tools extracting data from the same mobile phone may yield divergent results based on their individual parsing algorithms and support for specific device models [1].
Key practices in tool validation include:
- Using cryptographic hash values (e.g., SHA-256) to confirm data integrity before and after creating a forensic image [1].
- Comparing tool outputs against known datasets or test cases with pre-defined content [1].
- Cross-validating results across multiple, independent tools to identify inconsistencies or omissions [1].
Method Validation
Method validation confirms that the specific procedures and techniques followed by forensic analysts produce consistent and reliable outcomes across different cases, devices, and practitioners. This component addresses the "how" of the investigative process, ensuring that the methodology is sound, documented, and repeatable by other qualified professionals. This is especially crucial with advanced or destructive extraction techniques, such as those used for NAND flash memories in damaged or locked devices [2].
The levels of data acquisition methods, ranked by destructiveness, are [2]:
- Level 1: Manual Extraction: A low-complexity, non-destructive search. Its primary limitation is the locked device.
- Level 2: Logical Extraction: Data extraction via a connection to a forensic workstation using tools like OFD or EnCase. Not all data may be accessible.
- Level 3: JTAG and HEX Dump: A semi-destructive method using Test Access Ports (TAPs) on device motherboards to bypass OS restrictions.
- Level 4: Chip-Off: A complex, destructive technique involving the physical extraction of the memory chip for reading.
- Level 5: Microreading: A highly resource-intensive method involving the physical observation of chips using scanning electron microscopy.
Analysis Validation
Analysis validation is the process of evaluating whether an analyst's interpretation of the data accurately reflects its true meaning and context. It ensures that the software presents a valid representation of the underlying evidence and that the conclusions drawn are forensically sound [1]. This is particularly important for complex data artifacts, such as mobile device operating system logs where timestamps can be misleading without proper context [1]. The rise of artificial intelligence (AI) in forensic tools introduces new complexities for analysis validation, as algorithms may produce "black box" results that experts cannot easily explain, necessitating rigorous interpretation and validation of AI-generated findings [1] [3].
Experimental Protocols for Validation
Protocol for Validating a Digital Forensics Tool
This protocol outlines the steps to validate a tool like Cellebrite UFED or Oxygen Forensic Detective for a specific task, such as extracting data from a mobile device.
Objective: To verify that the tool accurately extracts and reports all accessible data from a designated mobile device model without alteration. Methodology:
- Preparation: Use a control mobile device that has been forensically wiped and loaded with a known dataset. This dataset should include a variety of file types (e.g., contacts, SMS, images, application data) whose locations and hashes are documented.
- Acquisition: Use the tool to perform a logical and/or physical extraction of the control device's data.
- Integrity Check: Compare the hash value of the extracted forensic image against the expected hash to ensure the data was not modified during acquisition.
- Data Verification: Analyze the extraction output using the tool's reporting function. Verify the presence and integrity of all known data items from the control dataset.
- Cross-Validation: Perform the same extraction on the control device using a different, previously validated tool. Compare the outputs from both tools for consistency.
Table 1: Sample Results from a Mobile Tool Validation Experiment
| Data Type | Known Data Value (Control) | Extracted by Tool A | Extracted by Tool B | Validation Result |
|---|---|---|---|---|
| SMS Text | "Test Message 123" | "Test Message 123" | "Test Message 123" | Pass |
| Contact Name | "John Doe" | "John Doe" | "John Doe" | Pass |
| Image File Hash | a1b2c3... | a1b2c3... | a1b2c3... | Pass |
| Deleted File Hash | d4e5f6... | Not Recovered | d4e5f6... | Fail for Tool A |
Protocol for Validating a Data Extraction Method
This protocol is for validating a specific forensic method, such as the Chip-Off technique for NAND flash memory.
Objective: To confirm that the chip-off procedure reliably recovers data from a specific memory chip type without data loss or corruption. Methodology:
- Sample Preparation: Select several identical, non-critical memory chips (e.g., from decommissioned devices) programmed with a known data set.
- Procedure Execution: Perform the chip-off extraction process, which involves:
- Desoldering: Physically removing the memory chip from the circuit board using a hot air rework station.
- Cleaning: Preparing the chip for reading.
- Reading: Placing the chip in a specialized adapter and reading its contents with a chip programmer (e.g., RT809H).
- Data Analysis: Compare the checksum of the data read from the chip against the checksum of the original known data.
- Repeatability: The procedure should be repeated multiple times by different trained technicians to establish an error rate and ensure consistency.
Table 2: Comparison of Data Acquisition Methods [2]
| Method Level | Method Name | Destructiveness | Key Tools | Primary Use Case |
|---|---|---|---|---|
| 1 | Manual Extraction | Non-destructive | ZRT Screen Capture | Functional, unlocked devices |
| 2 | Logical Extraction | Non-destructive | Oxygen Forensic Detective, EnCase | Standard data extraction |
| 3 | JTAG | Semi-destructive | RIFF/Medusa Box, JTAG adapter | Bypassing OS restrictions on damaged devices |
| 4 | Chip-Off | Destructive | Hot air station, RT809H programmer | Data recovery from physically damaged devices |
| 5 | Microreading | Highly Destructive | Scanning Electron Microscope | Extreme cases in high-priority investigations |
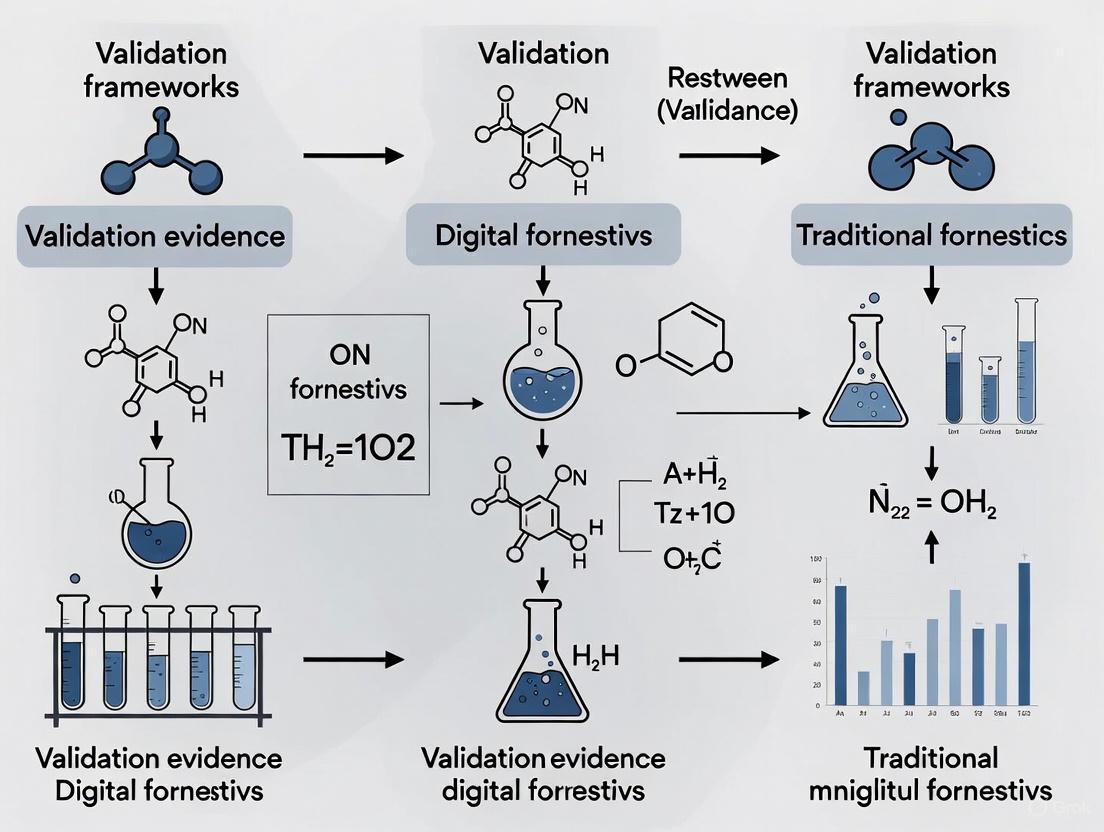
Visualization: Forensic Validation Workflow
The following diagram illustrates the logical relationship and workflow between the three core components of forensic validation, showing how they build upon one another to ensure overall reliability.
The Scientist's Toolkit: Essential Research Reagents & Materials
Forensic validation relies on a suite of specialized tools and materials to execute experiments and verify results. The following table details key solutions and their functions in a validation context.
Table 3: Essential Research Reagents & Materials for Forensic Validation
| Tool/Solution | Primary Function in Validation | Example in Use |
|---|---|---|
| Control Data Sets | Pre-defined, known data used to verify tool accuracy and method reliability. | A smartphone loaded with a specific set of SMS, contacts, and images for tool output verification [1]. |
| Forensic Write-Blockers | Hardware devices that prevent any write operations to the source evidence during acquisition. | Used during the disk imaging process to ensure the integrity of the original evidence for tool and method validation. |
| Hex Editors & Viewers | Software that allows for the bit-level inspection of data, independent of forensic tools. | Used for analysis validation to manually verify the raw data behind a tool's interpretation or report [2]. |
| Cryptographic Hash Calculators | Algorithms (e.g., SHA-256, MD5) that generate a unique digital fingerprint for a file or dataset. | The cornerstone of integrity checks; used to confirm that evidence is unaltered before and after any forensic process [1]. |
| Reference Devices | Known, functional devices (phones, hard drives) used as standardized test platforms. | Allow for the repeatable testing of tools and methods across different labs and by different practitioners. |
| JTAG/Chip-Off Equipment | Specialized hardware for advanced data extraction from damaged or locked devices. | Used to validate methods for Level 3 and 4 acquisitions, establishing their success rate and potential for data loss [2]. |
Comparative Analysis: Digital vs. Traditional Forensic Validation
While the core principles of validation—reproducibility, transparency, and error rate awareness—apply across all forensic disciplines, their implementation differs significantly between digital and traditional fields like DNA or chemistry.
Shared Foundations: Both domains require rigorous validation to meet legal admissibility standards, such as the Daubert Standard, which judges the reliability of scientific evidence based on factors like testability, peer review, and known error rates [1]. The principle of continuous validation is also universal, as methods in both domains evolve, though the pace of change is drastically faster in digital forensics.
Key Differences:
- Evidence Nature: Digital evidence is inherently volatile and easily manipulated, whereas traditional physical evidence (e.g., DNA, fibers) is more stable, though susceptible to contamination [1].
- Tool Evolution: Digital forensic tools are updated frequently (sometimes monthly) to handle new devices and apps, demanding near-constant re-validation [1]. Traditional lab equipment and chemical reagents are more stable, with validation cycles typically tied to new research or technology refreshes.
- Automation and AI: Digital forensics is rapidly integrating AI for tasks like media analysis and data sifting, creating new "black box" challenges for analysis validation [4] [3]. The use of AI in traditional fields like DNA phenotyping is emerging but is not yet as widespread in routine analysis [5] [6].
Case Studies in Validation Failure and Success
Case Study: FL vs. Casey Anthony (2011) - A Validation Failure
In this case, the prosecution's digital forensic expert initially testified that 84 searches for "chloroform" had been made on the family computer. However, through forensic validation conducted by the defense, expert Larry Daniel demonstrated that the software used had grossly overstated the results. His analysis confirmed that only a single instance of the search term had occurred, directly contradicting the earlier claims. This case underscores the critical consequence of inadequate tool validation: the potential for misinterpreted evidence to wrongly sway a jury [1].
Case Study: MA vs. Karen Read (2025) - Validation in Practice
Cellebrite Senior Digital Intelligence Expert Ian Whiffin emphasized the importance of rigorous validation when interpreting complex data artifacts from mobile devices. He explained that timestamps and operating system logs can be misleading without proper context. To ensure accuracy, he conducted tests across multiple devices to validate his conclusions before testifying. This demonstrates a core principle of method and analysis validation: verifying interpretations through controlled testing to ensure they are reliable and contextually accurate [1].
Forensic validation—spanning tool, method, and analysis—is not an optional step but an ethical and professional imperative. It is the linchpin that ensures forensic conclusions are rooted in scientific integrity and are robust enough to support the weight of legal proceedings. As forensic science continues to evolve, particularly with the integration of AI and the growing complexity of digital evidence, the commitment to transparent, repeatable, and scientifically sound validation practices becomes ever more critical. By adhering to these principles, forensic professionals uphold the trust placed in them by the justice system and ensure the accurate and accountable pursuit of truth.
Forensic science is undergoing a fundamental transition, moving from craft-based practices toward a rigorous scientific discipline grounded in objectivity, statistical reasoning, and quality assurance [7]. This evolution centers on three interdependent pillars that form the foundation of reliable forensic evidence: reproducibility, transparency, and error rate awareness. These principles apply across both traditional forensic disciplines (like fingerprints and DNA analysis) and digital forensics, though their implementation varies significantly based on the nature of evidence and technological considerations. Where traditional forensics often deals with physical evidence, digital forensics confronts volatile, easily manipulated data in rapidly evolving technological environments [1]. This comparison guide examines how these distinct forensic domains implement validation frameworks, objectively comparing their approaches to achieving scientific reliability.
Comparative Analysis: Three Pillars Across Forensic Disciplines
The table below summarizes how traditional and digital forensics implement the three core pillars of reliability.
Table 1: Implementation of Reliability Pillars in Traditional vs. Digital Forensics
| Reliability Pillar | Traditional Forensics | Digital Forensics |
|---|---|---|
| Reproducibility | Focus on procedural standardization and empirical foundation for pattern-matching disciplines [8] [7]. | Relies on tool verification, hash-based data integrity checks, and cross-validation across multiple tools [1] [9]. |
| Transparency | Movement toward disclosing limitations, methodologies, and uncertainties in expert reports [10] [8]. | Requires detailed documentation of tools, procedures, and chain of custody; mandates disclosure of unvalidated results [1] [11]. |
| Error Rate Awareness | Growing acknowledgment of false positives; research to establish foundational validity and quantify error rates [8] [7]. | Emphasis on tool testing, known error rates for specific functions, and acknowledgment of parsing inaccuracies [1] [9]. |
Experimental Validation and Performance Data
Tool Reliability Testing
Experimental studies directly compare the performance of digital forensic tools to establish reliability metrics. The following table summarizes results from controlled tests evaluating commercial versus open-source tools in key forensic functions.
Table 2: Digital Forensic Tool Performance Comparison (Based on Controlled Experiments) [9]
| Tool Type | Tool Name | Data Preservation Integrity | Deleted File Recovery Rate | Targeted Search Accuracy | Legal Admissibility Support |
|---|---|---|---|---|---|
| Commercial | FTK | Consistent hash verification | High | High | Established |
| Commercial | Forensic MagiCube | Consistent hash verification | High | High | Established |
| Open-Source | Autopsy | Consistent hash verification | Comparable to Commercial | High | Satisfies Daubert when validated |
| Open-Source | ProDiscover Basic | Consistent hash verification | Comparable to Commercial | High | Satisfies Daubert when validated |
Methodological Foundation
The experimental protocol for generating the comparative data in Table 2 involved:
- Controlled Testing Environment: Two Windows-based workstations configured with identical evidence samples [9].
- Test Scenarios: Three distinct forensic tasks: (1) preservation and collection of original data; (2) recovery of deleted files via data carving; (3) targeted artifact searching in case-specific scenarios [9].
- Validation Metrics: Each experiment conducted in triplicate to establish repeatability; error rates calculated by comparing acquired artifacts against control references; data integrity verified via hash value comparison [9].
- Legal Standard Compliance: Testing framework designed to satisfy Daubert criteria, including testability, error rate assessment, and peer review potential [9].
Visualization of Forensic Validation Workflows
Digital Forensic Validation Logic
Digital forensic validation employs a sequential, tool-dependent workflow where each stage requires specific technical validation checks.
Traditional Forensic Validation Logic
Traditional forensic validation follows a more iterative, human-centric workflow focused on comparative analysis and probabilistic assessment.
The Scientist's Toolkit: Essential Research Reagents and Solutions
Table 3: Essential Digital Forensic Research Toolkit [1] [12] [9]
| Tool/Category | Function | Examples |
|---|---|---|
| Commercial Forensic Suites | Comprehensive evidence processing and analysis | Cellebrite UFED, FTK, EnCase, Magnet AXIOM |
| Open-Source Tools | Cost-effective alternatives; method transparency | Autopsy, The Sleuth Kit, ProDiscover Basic |
| Validation Utilities | Integrity verification and tool testing | Hash calculators (MD5, SHA-1), write blockers |
| Reference Standards | Standardized procedures for evidence handling | ISO/IEC 27037, NIST Computer Forensics Tool Testing |
| Specialized Modules | Domain-specific forensic analysis | Mobile (XRY, Oxygen), Network (Wireshark), IoT |
The pillars of reproducibility, transparency, and error rate awareness provide a unified framework for validating forensic evidence across traditional and digital domains. While digital forensics relies heavily on technical tool validation and data integrity verification, traditional forensics emphasizes human expertise and probabilistic assessment. Both disciplines face the ongoing challenge of establishing foundational validity while maintaining practical applicability. The experimental data demonstrates that when properly validated using rigorous methodologies, both commercial and open-source solutions can produce forensically sound results that meet legal admissibility standards. As forensic science continues its transition toward greater scientific rigor, these three pillars will remain essential for ensuring reliable outcomes in both investigative and judicial contexts.
The admissibility of expert testimony, a cornerstone of modern litigation, is governed by distinct legal standards that act as validation frameworks for scientific evidence. In the realm of forensics—both digital and traditional—these standards determine which methodologies, principles, and expert opinions can be presented to a trier of fact. The Daubert Standard and the Frye Standard are the two primary frameworks performing this gatekeeping function [13] [14]. Their application ensures that expert testimony is not only relevant but also derived from reliable scientific methods, thereby safeguarding the integrity of the judicial process.
Understanding the differences between these standards is critical for researchers and forensic professionals who must validate their techniques and present their findings in court. This guide provides a comparative analysis of the Daubert and Frye standards, examining their core criteria, procedural applications, and implications for the validation of novel forensic methods.
The Frye Standard: "General Acceptance" Test
The Frye Standard originates from the 1923 case Frye v. United States, which dealt with the admissibility of polygraph (systolic blood pressure deception test) evidence [15] [16]. The court established a "general acceptance" test, ruling that for an expert's scientific testimony to be admissible, the methodology underlying it must be "sufficiently established to have gained general acceptance in the particular field in which it belongs" [16].
Core Principle and Application
- Primary Test: General acceptance within the relevant scientific community [15] [17].
- Judicial Role: The court's role is limited to determining whether the principle or discovery has crossed the line from experimental to demonstrable stages based on its acceptance by specialists in the field [15] [18].
- Focus: The Frye standard focuses narrowly on the consensus within the scientific community regarding the methodology, not on the ultimate conclusions drawn by the expert [17].
Limitations and Critique
The Frye Standard has been criticized for being conservative and potentially excluding novel but reliable scientific techniques simply because they are new and have not yet gained widespread acceptance [15] [14]. This can be a significant hurdle for emerging fields like digital forensics, where technologies and methods evolve rapidly.
The Daubert Standard: A "Reliability and Relevance" Test
The Daubert Standard emerged from the 1993 U.S. Supreme Court case Daubert v. Merrell Dow Pharmaceuticals, Inc. [13]. This decision held that the Federal Rules of Evidence, particularly Rule 702, had superseded the Frye Standard in federal courts. The Daubert Standard assigns trial judges a "gatekeeping" role, requiring them to ensure that all expert testimony is not only relevant but also based on a reliable foundation [13] [19].
Core Principles and Factors
Under Daubert, judges evaluate the admissibility of expert testimony using a non-exhaustive list of factors [13] [19]:
- Testing and Falsifiability: Whether the expert's theory or technique can be (and has been) tested.
- Peer Review: Whether the method has been subjected to peer review and publication.
- Error Rate: The known or potential error rate of the technique.
- Standards: The existence and maintenance of standards controlling the technique's operation.
- General Acceptance: Whether the method has attracted widespread acceptance within a relevant scientific community (incorporating the Frye test as one factor among several).
Subsequent cases, General Electric Co. v. Joiner (1997) and Kumho Tire Co. v. Carmichael (1999), solidified this standard. The Kumho Tire decision extended the judge's gatekeeping function to all expert testimony, including non-scientific, technical, and other specialized knowledge [13] [14] [19]. This trilogy of cases is collectively known as the "Daubert Trilogy."
Comparative Analysis: Daubert vs. Frye
The following table summarizes the key differences between the two standards.
Table 1: Core Criteria Comparison of Daubert and Frye Standards
| Feature | Daubert Standard | Frye Standard |
|---|---|---|
| Originating Case | Daubert v. Merrell Dow Pharmaceuticals, Inc. (1993) [13] | Frye v. United States (1923) [15] |
| Primary Test | Relevance and reliability of the methodology [13] [19] | "General acceptance" in the relevant scientific community [15] [17] |
| Judge's Role | Active "gatekeeper" who assesses scientific validity [13] | Arbiter of consensus within the scientific field [18] |
| Scope of Application | Applies to all expert testimony (scientific, technical, specialized) [13] [19] | Primarily applied to novel scientific evidence [18] |
| Flexibility | More flexible; allows for newer methods that are reliable but not yet widely accepted [14] | More rigid; can exclude novel science until it gains broad acceptance [15] [20] |
| Key Factors | Testability, peer review, error rate, standards, general acceptance [13] | Solely general acceptance [15] |
Practical Implications for Forensic Research and Testing
The choice of standard has profound implications for how forensic researchers validate and present their methodologies in court.
Table 2: Practical Implications for Forensic Evidence
| Aspect | Under Daubert | Under Frye |
|---|---|---|
| Novel Methodologies | More likely to be admitted if proponent can demonstrate reliability through testing, low error rates, etc., even without widespread acceptance [15] [14]. | Likely to be excluded until the technique achieves "general acceptance" in its field [15] [20]. |
| Judicial Scrutiny | High; judges actively evaluate the scientific rigor of the methodology itself [13] [19]. | Limited; judges primarily determine the level of acceptance by the scientific community [17] [18]. |
| Burden on Expert | Must be prepared to defend the reliability and application of their method in detail [19]. | Must be prepared to demonstrate that the method is generally accepted [18]. |
| Impact on Digital Forensics | Allows for the admission of newer digital forensic techniques if they can be shown to be reliable and applied rigorously [14]. | May pose a higher barrier for new digital tools and techniques that have not yet become industry standards. |
The logical progression of a court's analysis under each standard is distinct, as illustrated below.
Experimental Protocols for Legal Validation
For a forensic researcher, preparing for a Daubert or Frye hearing is akin to designing a rigorous experiment. The "experimental protocol" involves building a comprehensive record that validates the methodology against the relevant legal standard.
Validation Protocol for the Daubert Standard
To satisfy Daubert, the proponent of the evidence must demonstrate reliability by a preponderance of the evidence [21]. The required "materials and methods" are extensive:
- Testing and Validation Studies: Conduct and document controlled experiments that test the methodology's reliability. The focus should be on whether the principle can be and has been tested [13] [19].
- Peer-Reviewed Publication: Submit studies and explanations of the methodology to peer-reviewed journals. Document the peer review process to show scrutiny by the scientific community [19].
- Error Rate Calculation: Quantify the technique's known or potential error rate through validation studies. Be prepared to explain the methodology's accuracy and limitations [13] [19].
- Standard Operating Procedures (SOPs): Develop, document, and maintain strict standards and controls that govern the technique's application to ensure consistency and reliability [19].
- Survey of the Field: Gather literature, textbooks, and statements from other experts to demonstrate the technique's growing or established acceptance, though this is not solely dispositive under Daubert [13].
Validation Protocol for the Frye Standard
The protocol under Frye is more narrowly focused:
- Literature Review for Consensus: Compile a comprehensive body of scholarly publications, judicial decisions from other jurisdictions, and practical applications that attest to the technique's acceptance [18].
- Expert Affidavits: Secure declarations from recognized, independent experts in the field who can attest that the methodology is generally accepted as reliable for its intended purpose [16] [18].
- Focus on Methodology, Not Conclusions: Ensure that all evidence is directed at the general acceptance of the underlying principles and methods, not the correctness of the expert's specific conclusions in the case [18].
Essential Research Reagents for Admissibility Testing
Navigating an admissibility hearing requires a toolkit of "research reagents"—conceptual tools and materials needed to build a valid and convincing case for the court.
Table 3: Research Reagent Solutions for Legal Admissibility
| Research Reagent | Function in Validation | Primary Applicable Standard |
|---|---|---|
| Peer-Reviewed Studies | Provides objective evidence of scientific scrutiny and validation of the underlying principles [13] [19]. | Daubert (Critical), Frye (Supportive) |
| Error Rate Analysis | Quantifies the reliability and limitations of the method; essential for a scientific assessment of validity [13] [19]. | Daubert |
| Standard Operating Procedures (SOPs) | Demonstrates that the method is applied in a consistent, controlled manner, reducing variability and arbitrariness [19]. | Daubert |
| Scholarly Treatises & Textbooks | Establishes that the method is recognized and taught as valid within the field, showing integration into the body of scientific knowledge [18]. | Frye (Critical), Daubert (Supportive) |
| Expert Witness Credentials | Establishes the qualifications of the individual applying the method, though the focus remains on the methodology itself [19] [18]. | Both |
| Survey of Jurisdictional Precedent | Shows how other courts have ruled on the admissibility of the same or similar methods, providing persuasive legal authority. | Both |
The choice between Daubert and Frye fundamentally shapes the validation strategy for forensic evidence. The Daubert Standard, with its multi-factor, flexible approach, is more suited to rapidly evolving fields like digital forensics, as it allows novel but rigorously tested methods to be presented in court. In contrast, the Frye Standard's singular focus on general acceptance provides predictability but may slow the integration of innovative techniques.
For researchers and legal professionals, the jurisdiction dictates the standard. However, a robust validation protocol that includes testing, peer review, error rate analysis, and standardized procedures will not only satisfy the more demanding Daubert standard but also strongly support an argument for general acceptance under Frye. As forensic science continues to advance, understanding and applying these legal frameworks remains essential for bridging the gap between scientific innovation and the rules of evidence.
Forensic validation is the fundamental process of testing and confirming that forensic techniques and tools yield accurate, reliable, and repeatable results [1]. It functions as a critical safeguard against error, bias, and misinterpretation across all forensic disciplines, from traditional DNA analysis to modern digital forensics [1]. Without rigorous validation, the credibility of forensic findings and the outcomes of investigations and legal proceedings can be severely undermined, potentially leading to miscarriages of justice [1]. The legal system itself requires the use of scientifically validated methods, applying standards such as Daubert and Frye to ensure that evidence presented in court is derived from reliable principles [22].
This article explores the critical consequences of inadequate validation through case studies that highlight failures in both traditional and digital forensic contexts. We examine how validation frameworks are evolving to address challenges posed by new technologies, particularly the rise of artificial intelligence and complex digital evidence. By comparing validation methodologies across forensic domains and presenting standardized experimental protocols, this analysis provides researchers with frameworks for ensuring the scientific integrity of their forensic analyses.
The Fundamentals of Forensic Validation
Core Principles and Components
Forensic validation encompasses three distinct but interrelated components [1]:
- Tool Validation: Ensures that forensic software or hardware performs as intended, extracting and reporting data correctly without altering the source evidence.
- Method Validation: Confirms that the procedures followed by forensic analysts produce consistent outcomes across different cases, devices, and practitioners.
- Analysis Validation: Evaluates whether the interpreted data accurately reflects its true meaning and context, ensuring that software presents a valid representation of underlying evidence.
These components rest upon foundational principles that include reproducibility, transparency, error rate awareness, peer review, and continuous validation [1]. In digital forensics, specific validation practices include using hash values to confirm data integrity, comparing tool outputs against known datasets, cross-validating results across multiple tools, and ensuring all procedures are thoroughly documented [1].
Legal and Scientific Standards
Validation requirements are codified in accreditation standards such as ISO/IEC 17025, which forensic service providers must meet to maintain accreditation [22]. The Daubert Standard, which governs the admissibility of expert testimony in federal courts, requires that forensic methods be tested, peer-reviewed, have known error rates, and be generally accepted in the relevant scientific community [1]. These legal frameworks make proper validation not merely a scientific best practice but a legal necessity for evidence to be admissible in judicial proceedings.
Case Studies: Justice Compromised by Validation Failures
Digital Forensics: Florida v. Casey Anthony (2011)
The prosecution's digital forensic expert initially testified that searches for the word "chloroform" had been conducted on the Anthony family computer 84 times, suggesting high interest and intent [1]. This number was repeatedly cited by the prosecution as strong circumstantial evidence of planning in the death of Caylee Anthony.
However, through rigorous forensic validation conducted by the defense team with assistance from Envista Forensics, this critical piece of evidence was revealed to be grossly inaccurate. Re-examination and validation of the forensic software's output confirmed that only a single instance of the search term had occurred, directly contradicting earlier claims of extensive search activity [1].
This case exemplifies a critical failure in tool validation - the forensic software either misinterpreted data or presented it in a misleading manner, and the initial examiner failed to validate the tool's output. The consequences were profound: what appeared to be compelling evidence of premeditation was actually an artifact of flawed forensic processing.
Digital Forensics: Massachusetts v. Karen Read (2025)
In this more recent case, Cellebrite Senior Digital Intelligence Expert Ian Whiffin underscored the importance of rigorous validation in digital forensics [1]. He explained that timestamps and data artifacts require careful interpretation, as mobile device operating system logs can be misleading without proper context.
The investigation demonstrated proper validation methodology through cross-device testing - Whiffin conducted tests across multiple devices to ensure the accuracy of his conclusions about timestamp interpretations [1]. This approach highlights how proper validation practices help ensure that digital evidence is interpreted correctly and reliably, preventing misinterpretations that could lead to unjust outcomes.
Comparative Analysis: Traditional vs. Digital Forensic Validation
The challenges of validation differ significantly between traditional and digital forensic domains, as illustrated in the table below:
Table 1: Validation Challenges in Traditional vs. Digital Forensics
| Aspect | Traditional Forensics | Digital Forensics |
|---|---|---|
| Evidence Nature | Relatively stable physical evidence | Volatile, easily manipulated digital evidence [1] |
| Tool Evolution | Methodologies evolve slowly | Rapid tool updates requiring constant revalidation [1] |
| Standardization | Established protocols (e.g., NIJ standards) | Lack of standardized datasets and formal testing procedures [23] |
| Error Rate Quantification | Generally established through repeated testing | Often unknown or poorly documented [23] |
| Primary Validation Focus | Technique reliability and reproducibility | Tool output accuracy and interpretation validity [1] |
Validation Frameworks: Traditional and Digital Paradigms
Established Traditional Validation Models
Traditional forensic sciences have long employed structured validation approaches. The collaborative method validation model proposed for crime laboratories emphasizes efficiency through standardization and shared methodology [22]. In this model, an originating Forensic Science Service Provider (FSSP) publishes comprehensive validation data in peer-reviewed journals, enabling other FSSPs to conduct abbreviated verifications rather than full validations, provided they adhere strictly to the published parameters [22].
This approach offers significant advantages: it reduces redundant validation efforts across laboratories, promotes standardization of methods, establishes benchmarks for comparison, and increases overall efficiency in implementing new technologies [22]. The model acknowledges that while forensic service providers may operate in different jurisdictions, they examine common evidence types using similar technologies and methods, making collaborative validation feasible and beneficial [22].
Emerging Digital Forensic Validation Standards
In digital forensics, the National Institute of Standards and Technology (NIST) has established the Computer Forensic Tool Testing (CFTT) Program to address validation needs [23] [24]. The CFTT aims to establish a methodology for testing computer forensic tools through development of general tool specifications, test procedures, test criteria, test sets, and test hardware [24].
Inspired by the CFTT program, researchers have proposed standardized methodologies for evaluating emerging technologies like Large Language Models (LLMs) in digital forensic tasks [25] [23]. These methodologies include quantitative evaluation using metrics such as BLEU and ROUGE, originally developed for machine translation but now adapted for assessing forensic timeline analysis [25] [23]. The development of Computer Forensic Reference Data Sets (CFReDS) by NIST provides documented sets of simulated digital evidence that examiners can use for validation and proficiency testing [24].
Table 2: Digital Forensic Tool Validation Framework
| Validation Component | Methodology | Output Metrics |
|---|---|---|
| Tool Functionality | Testing against CFReDS reference data sets [24] | Accuracy, error rates, missed evidence |
| Performance | Processing standardized evidence volumes | Processing speed, resource utilization |
| Reliability | Repeated testing across multiple environments | Consistency, reproducibility measures |
| Legal Compliance | Verification of hash values, evidence preservation [1] | Chain-of-custody documentation, data integrity |
Experimental Protocols for Forensic Validation
Protocol 1: Digital Forensic Tool Validation
Based on the NIST CFTT methodology, this protocol provides a framework for validating digital forensic tools [24]:
Test Preparation: Acquire standardized hardware test fixtures and reference data sets from CFReDS that represent typical case scenarios [24].
Tool Specification: Define clear specifications for the tool's intended functions, including supported file systems, data types, and output formats.
Test Execution:
- Process reference data sets using the tool under validation
- Verify hash values before and after processing to confirm data integrity [1]
- Execute identical procedures across multiple hardware platforms and operating environments
Result Analysis:
- Compare tool outputs against known ground truth in reference data sets
- Calculate accuracy metrics for data extraction, parsing, and interpretation
- Identify any false positives, false negatives, or data alterations
Cross-Validation: Process the same data sets using multiple tools and compare results to identify inconsistencies or tool-specific artifacts [1].
This experimental protocol emphasizes transparency, with thorough documentation of all procedures, software versions, system configurations, and results to ensure reproducibility and facilitate peer review [1].
Protocol 2: LLM Validation for Forensic Timeline Analysis
The adoption of Artificial Intelligence, particularly Large Language Models (LLMs), in digital forensics necessitates novel validation approaches [25] [23]. The following protocol provides a standardized methodology for evaluating LLM performance in forensic timeline analysis:
Dataset Development: Create forensic timeline datasets from controlled environments (e.g., Windows 11 systems) using tools like Plaso, ensuring comprehensive ground truth documentation [23].
Task Definition: Define specific timeline analysis tasks, such as event summarization, anomaly detection, or pattern identification.
Experimental Execution:
- Process timeline data through the LLM under evaluation
- Generate outputs for defined tasks using standardized prompts
- Conduct multiple trials to ensure consistency
Quantitative Assessment:
Qualitative Assessment:
- Subject matter expert evaluation of output relevance and accuracy
- Assessment of potential biases in model outputs
- Determination of clinical utility in real-world investigative contexts
This protocol addresses the unique challenges of validating "black box" AI systems, where the internal decision-making processes may not be transparent or easily interpretable [1].
Diagram 1: Forensic Tool Validation Workflow. This diagram illustrates the sequential phases of a comprehensive validation process for forensic tools, from initial preparation through testing to final analysis and reporting.
Reference Data Sets and Standards
Table 3: Essential Resources for Forensic Validation Research
| Resource | Function | Source/Availability |
|---|---|---|
| CFReDS (Computer Forensic Reference Data Sets) | Provides simulated digital evidence for testing and validation [24] | NIST [24] |
| NSRL (National Software Reference Library) | Reference database of software profiles for file identification [24] | NIST [24] |
| Standardized Forensic Timelines | Datasets for evaluating timeline analysis tools and LLMs [23] | Research publications [23] |
| CFTT Test Specifications | Standardized methodologies for testing computer forensic tools [24] | NIST [24] |
| Plaso | Open-source tool for timeline generation used in creating validation datasets [23] | Open source [23] |
Validation Metrics and Analytical Tools
- BLEU (Bilingual Evaluation Understudy): Algorithm for evaluating the quality of text which has been machine-translated; adapted for assessing LLM outputs in forensic contexts [25] [23]
- ROUGE (Recall-Oriented Understudy for Gisting Evaluation): Set of metrics for evaluating automatic summarization and translation of texts; used for quantitative assessment of LLM-generated forensic summaries [25] [23]
- Hash Value Algorithms (MD5, SHA-1, SHA-256): Cryptographic hash functions used to verify data integrity throughout forensic processes [1]
- YARA Rules: Pattern-matching tool for identifying and classifying malware and other suspicious files during forensic analysis
The case studies and frameworks presented demonstrate that inadequate validation poses serious threats to justice systems, regardless of whether evidence is derived from traditional or digital sources. The Casey Anthony case illustrates how unvalidated digital evidence can dramatically misrepresent facts, while emerging challenges with AI and LLMs highlight the need for novel validation approaches tailored to complex, non-transparent systems [1] [25].
Moving forward, the field must address several critical needs: developing standardized datasets for benchmarking [23], establishing collaborative validation models to reduce redundancy [22], creating AI-specific validation protocols that address explainability and hallucination risks [25] [23], and promoting transparent reporting of validation methodologies and results [1]. As forensic technologies continue to evolve, maintaining scientific rigor through comprehensive validation remains essential for ensuring that forensic evidence serves rather than subverts justice.
Diagram 2: Validation Framework Integration. This diagram shows how validation approaches from different forensic domains contribute to shared objectives of standardization, reliability, and legal robustness.
Applied Validation Methodologies in Modern Forensic Practice
In digital forensics, the principle of tool validation is paramount for ensuring the integrity and admissibility of evidence. Unlike traditional forensics, where physical evidence can be directly observed, digital evidence is often interpreted and presented through software tools. This creates a fundamental reliance on the accuracy and completeness of these tools. A robust validation framework requires that findings from one tool be verified by an independent tool to mitigate the risk of inherent biases, parsing errors, or overlooked data. This process is not merely a best practice but a scientific necessity to uphold the standards of evidence in judicial proceedings.
The transition from an acquisition tool like Cellebrite UFED to an analysis platform like Magnet AXIOM provides a canonical use case for such validation. This guide objectively compares the performance of these two industry-leading solutions within a validation framework, providing researchers and forensic professionals with experimental data and methodologies to support rigorous, defensible investigations.
Tool Comparison: Capabilities and Features
A side-by-side comparison of core capabilities provides the foundation for understanding how these tools can be used complementarily in a validation workflow.
Table 1: Digital Forensics Tool Capability Comparison
| Feature | Cellebrite UFED | Magnet AXIOM |
|---|---|---|
| Primary Function | Data extraction from mobile devices [26] | Data analysis from multiple sources (mobile, computer, cloud) [27] [26] |
| Key Strength | Broad device support & physical extraction [26] [28] | Unified case analysis & artifact recovery [27] [26] |
| Supported Platforms | iOS, Android, Windows Mobile [26] | Windows, macOS, Linux, iOS, Android [26] |
| Cloud Forensics | Supported [26] | Supported [27] [26] |
| Key Differentiating Features | Advanced decryption for encrypted apps [26] | Magnet.AI for categorization; Timeline and Connections analysis [27] [26] |
This divergence in primary function is precisely what makes their sequential use so powerful. UFED excels at the preservation phase, reliably acquiring data from a wide array of mobile devices. AXIOM, in contrast, shines in the examination and analysis phases, cross-correlating data from mobiles, computers, and cloud sources to build a holistic view of user activity [27]. Internal testing by Magnet Forensics suggests that this approach allows AXIOM to find up to 25% more evidence than other tools when analyzing the same extraction, a critical metric for validation [27].
Experimental Data for Validation
Performance metrics are essential for validating not just evidence, but the efficiency of the investigative process itself. The following data, drawn from comparative testing, highlights operational differences.
Table 2: Digital Forensics Tool Performance Metrics
| Performance Metric | Cellebrite UFED (via Physical Analyzer) | Magnet AXIOM |
|---|---|---|
| Processing Time | Information Missing | 2 hours, 31 minutes, 49 seconds (for a 500GB HDD) [29] |
| Keyword Search Speed | 6 minutes, 12 seconds (for "guest") [29] | 9 seconds (for "guest") [29] |
| Timeline Analysis Load Time | 6 minutes, 53 seconds (~509k records) [29] | 40 seconds (~509k records) [29] |
| Artifact Support | Strong for mobile apps and file systems [26] | Extensive, with community-driven "Custom Artifacts" for unsupported apps [27] |
The most striking performance differentiator lies in analytical speed. On identical hardware, AXIOM completed a keyword search for the term "guest" (~50k results) in 9 seconds, a task that took another tool 6 minutes and 12 seconds—making AXIOM over 40 times faster in this specific operation [29]. This performance advantage extends to complex filtering; applying a date filter to all data from a specific year (~119k results) was reported to be near instantaneous in AXIOM, compared to 18 minutes and 42 seconds in another tool [29]. This directly impacts an examiner's ability to rapidly test hypotheses and validate findings during an investigation.
Experimental Protocol for Performance Benchmarking
The quantitative data presented in Table 2 was derived from a controlled performance test. The methodology is outlined below for transparency and potential replication.
- Testing Machine Specifications: The tests were conducted on a professional forensic workstation with the following specs: Dual Intel Xeon E5-2640 v4 CPUs (20 cores, 40 logical processors), 128 GB DDR4 RAM, an 8TB RAID10 array for the source image, and a 2TB SSD for the active case [29].
- The Dataset: A single 500GB hard drive image was used for consistency. The drive had 89.9GB of allocated data, an NTFS file system, and contained a Windows 7 Home Premium operating system that had been in use for approximately four years. The E01 image was 82.2GB in size and contained approximately 723,000 records and artifacts [29].
- Processing Settings: For both tools, the processing phase was configured with all artifacts selected and a "Full Search" conducted on all partitions. No additional processing options were enabled, ensuring a like-for-like comparison of the core processing engines [29].
A Validation Workflow: From UFED to AXIOM
A practical validation protocol leverages the strengths of both tools, beginning with Cellebrite UFED for acquisition and culminating with Magnet AXIOM for deep analysis and verification. The following diagram maps this multi-tool workflow.
(Core Validation Workflow: This diagram illustrates the sequential and iterative process of using Cellebrite UFED for data acquisition and Magnet AXIOM for independent analysis and validation.)
The Researcher's Toolkit: Essential File Formats & Functions
Navigating this workflow requires an understanding of the key "research reagents"—the file formats and components that facilitate the exchange and validation of data between tools.
Table 3: Essential Digital Forensics File Formats and Functions
| Item | Function in Validation |
|---|---|
| .UFD/.UFDX File | A configuration file from Cellebrite UFED containing metadata about the extraction. It can be ingested directly by AXIOM to locate the actual image files [30]. |
| CLBX File | A container format from Cellebrite for full file system extractions. It is a ZIP archive that AXIOM can process, often including valuable iOS keychain data for decryption [30]. |
| Physical Image (e.g., .BIN) | A bit-for-bit copy of a storage device. Segmented .BIN files from Android physical extractions can be loaded into AXIOM for analysis [30]. |
| File System Image (e.g., .TAR, .ZIP) | A logical extraction containing a device's file system. Common in iOS and Android file system extractions, these can be loaded into AXIOM as "Images" [30]. |
| Custom Artifacts | Community-created scripts (XML/Python) that allow AXIOM to parse artifacts from new or unsupported apps, extending its validation capabilities [27]. |
Within a modern digital forensics validation framework, reliance on a single tool is a methodological vulnerability. The practice of using Cellebrite UFED for robust data acquisition and Magnet AXIOM for independent, multi-source analysis constitutes a defensible validation protocol. The experimental data shows that AXIOM can not only confirm UFED findings but also uncover significant additional evidence—up to 25% more in internal tests—while providing orders-of-magnitude faster analysis speeds [27] [29]. For researchers and professionals building a scientifically sound, court-defensible process, this multi-tool "toolbox" approach is not just recommended; it is essential.
Validating Methods for Cloud Forensics and Distributed Data
The exponential growth of cloud computing and distributed data environments has fundamentally transformed the digital forensics landscape. Unlike traditional digital forensics, which focuses on physical storage media under the investigator's direct control, cloud forensics must navigate a complex ecosystem of virtualized, multi-tenant, and geographically dispersed data [31] [32]. This paradigm shift necessitates the development and validation of new forensic methods that can ensure evidence meets the stringent requirements for legal admissibility. The core challenge lies in establishing scientific validity and reliability for forensic techniques applied in environments where direct physical access to evidence is often impossible [3] [33].
This article frames the comparison of cloud and traditional forensic methods within the broader context of validation frameworks for digital forensics research. For evidence to be admissible in legal proceedings, particularly under standards like the Daubert Standard, the methods used to collect and analyze it must be tested, peer-reviewed, have known error rates, and be widely accepted in the scientific community [33] [34]. We objectively compare the performance of forensic approaches, providing a structured analysis of their characteristics, challenges, and the experimental protocols required to validate them in a court-of-law context.
Comparative Analysis: Traditional vs. Cloud Forensics
The following table summarizes the core distinctions between traditional and cloud forensics, which form the basis for their validation requirements.
Table 1: Comparative Analysis of Traditional Digital Forensics and Cloud Forensics
| Characteristic | Traditional Digital Forensics | Cloud Forensics |
|---|---|---|
| Data Location & Control | Physical media (e.g., hard drives, phones) within the investigator's jurisdiction [31]. | Virtualized data distributed across multi-tenant, geographically diverse servers and data centers [31] [32]. |
| Primary Challenges | Data encryption, device diversity, data volume [33]. | Jurisdictional issues, data volatility (ephemeral resources), multi-tenancy, and complex data acquisition from CSPs [31] [35]. |
| Chain of Custody | Managed directly by the investigator; easier to document a linear history [35]. | Extremely complex; requires automated tracking of access across multiple cloud providers and third parties to be legally defensible [35]. |
| Investigation Scope | Well-defined physical artifact [33]. | Dynamic and boundary-less; often requires cross-cloud correlation [32] [35]. |
| Legal & Regulatory Focus | Primarily domestic laws on search and seizure [33]. | Must navigate conflicting international data privacy laws (e.g., GDPR, cross-border data transfer restrictions) [31] [32]. |
| Tool Validation | Focused on tool accuracy for data recovery and analysis from static images [33]. | Requires validation for API-based collection, integration with cloud-native services, and automated evidence handling [3] [35]. |
Experimental Protocols for Validating Forensic Methods
To satisfy the requirements of a validation framework, any forensic method, whether for traditional or cloud environments, must be subjected to rigorous, repeatable testing. The following protocols outline core experiments for validating key forensic capabilities.
Protocol 1: Evidence Integrity and Chain of Custody Validation
1. Objective: To verify that a cloud forensics platform can automatically create and maintain a tamper-evident log of all actions performed on digital evidence, preserving its integrity for legal admissibility [35].
2. Methodology: A controlled environment is established using a cloud account (e.g., AWS or Azure). A series of simulated investigative actions are performed, including data acquisition from a cloud storage bucket, memory capture of a virtual machine, and isolation of a compromised resource. The platform's automated logging capabilities are stressed by introducing multiple concurrent users and actions.
3. Data Collection & Metrics: The experiment measures the platform's ability to generate immutable, time-stamped logs for every action. Key metrics include the completeness of the audit trail (%), the granularity of logged details (e.g., user, timestamp, action, target resource), and the ability to detect and alert on any unauthorized attempt to alter the logs [35].
Protocol 2: Data Acquisition and Volatile Data Recovery
1. Objective: To evaluate the effectiveness of forensic tools in acquiring data from ephemeral cloud resources (e.g., containers, serverless functions) before they are terminated, and to compare the recovery rates of open-source versus commercial tools [33] [35].
2. Methodology: This experiment involves deploying short-lived cloud resources programmed to execute a predefined set of activities and then self-terminate after a random interval. Investigators use both commercial (e.g., FTK, Forensic MagiCube) and open-source (e.g., Autopsy, ProDiscover Basic) tools, triggering automated evidence collection the moment malicious activity is detected by a monitoring system.
3. Data Collection & Metrics: The primary quantitative metric is the Data Recovery Rate (%), calculated by comparing the artifacts acquired by the tool against a known control set of actions performed on the ephemeral resource. Furthermore, the Mean Time to Response (MTTR) is critical, measuring the time from detection to successful evidence capture [35]. Each experiment should be performed in triplicate to establish repeatability and calculate error rates [33].
Protocol 3: Tool Reliability and Repeatability Testing
1. Objective: To determine the reliability and repeatability of digital forensic tools, a requirement for admissibility under the Daubert Standard [33] [34].
2. Methodology: Following methodologies from NIST Computer Forensics Tool Testing standards, a controlled testing environment is set up. Tools are tasked with three distinct scenarios: preservation of original data, recovery of deleted files via data carving, and targeted artifact searching. The same set of experiments is performed using both commercial and open-source tools.
3. Data Collection & Metrics: The key metric is the Tool Error Rate, quantified by comparing the acquired artifacts with control references. Repeatability is established by conducting each experiment in triplicate and ensuring consistent results across all runs [33].
Visualization of Forensic Validation Workflows
The following diagram illustrates the logical workflow for validating a digital forensic method, from evidence collection to legal admission, highlighting critical decision points.
Diagram 1: Forensic Method Validation Workflow. This chart outlines the pathway from evidence collection to legal admissibility, showing the critical validation checkpoints based on the Daubert Standard [33].
The Researcher's Toolkit: Essential Solutions for Forensic Validation
The table below details key reagents, tools, and platforms that constitute the essential toolkit for conducting research in forensic method validation.
Table 2: Research Reagent Solutions for Digital Forensics Validation
| Tool / Solution | Type / Category | Primary Function in Validation |
|---|---|---|
| FTK (Forensic Toolkit) | Commercial Forensic Suite | Serves as a benchmark commercial tool for comparative studies on evidence collection, data carving, and artifact analysis [33]. |
| Autopsy | Open-Source Forensic Suite | Provides a cost-effective, transparent alternative for validating forensic processes; allows for peer review of methodologies [33]. |
| OPC UA with Kafka | Data Integration Framework | Enables standardized collection and real-time processing of heterogeneous data in industrial cloud environments, useful for building testbeds [36]. |
| Darktrace/CLOUD w/ Cado | Cloud Forensics & Incident Response Platform | Used to test and validate automated evidence collection, chain of custody tracking, and analysis in multi-cloud environments [35]. |
| DataSHIELD | Federated Analysis Platform | Provides a platform with built-in privacy-preserving technologies (e.g., differential privacy) for validating analytical methods on distributed data without centralization [37]. |
| NIST CFTT Standards | Testing Standards & Protocols | Provides the methodological foundation for designing rigorous, repeatable experiments to establish tool reliability and error rates [33]. |
The validation of methods for cloud and distributed data forensics is not merely a technical exercise but a foundational requirement for the integrity of modern judicial processes. As this comparison demonstrates, cloud forensics introduces a layer of complexity that traditional methods are not designed to address, necessitating new validation frameworks and experimental protocols. The core differentiator is the shift from validating tools for static data analysis to validating processes for dynamic, remote, and automated evidence handling in a legally compliant manner.
The future of validation research lies in the development of standardized, practitioner-driven frameworks that incorporate explainable AI (XAI) to mitigate the "black-box" nature of advanced analytics [3]. Furthermore, the empirical demonstration that properly validated open-source tools can produce reliable and repeatable results promises to democratize access to high-quality forensic capabilities [33]. For researchers and professionals, the priority must be on generating robust, empirical data on method performance—including error rates and reliability under controlled conditions—to build the scientific foundation that will support the next generation of digital forensics.
In both digital and traditional forensics, the validity and reliability of analytical methods are paramount. The core principle of forensic science hinges on the ability to demonstrate that a technique produces consistent, accurate, and reproducible results that are admissible as evidence. Within this context, cross-validation emerges as a critical statistical methodology for evaluating the performance and generalizability of predictive models [38]. This guide objectively compares prevalent cross-validation procedures and their implementation tools, framing them within the broader need for robust validation frameworks in forensic research. As digital evidence becomes increasingly complex, leveraging standardized cross-validation with known datasets is not just a best practice but a foundational requirement for scientific and legal acceptance [34] [3].
Core Concepts of Cross-Validation
Cross-validation is a model assessment technique used to estimate how the results of a statistical analysis will generalize to an independent dataset [38]. Its primary purpose is to test a model's ability to predict new data that was not used in its training, thereby flagging critical issues like overfitting or selection bias [39] [38]. In overfitting, a model memorizes the noise and specific details of the training data to an extent that it negatively impacts its performance on new, unseen data. Cross-validation helps detect this by revealing a significant gap between performance on training data and validation data [40].
The fundamental process involves partitioning a sample of data into complementary subsets, performing the analysis on one subset (called the training set), and validating the analysis on the other subset (called the validation set or testing set) [38]. To reduce variability, most cross-validation methods perform multiple rounds of this partitioning with different splits and then combine (e.g., average) the results over the rounds [39] [38]. This process provides a more accurate and reliable estimate of a model's predictive performance than a single train-test split [39].
Cross-Validation Types and Methodologies
Several cross-validation techniques exist, each with specific strengths, weaknesses, and ideal use cases. Understanding these is crucial for selecting the appropriate method for a given forensic analysis scenario.
K-Fold Cross-Validation
K-Fold Cross-Validation is one of the most widely used and robust methods [40]. In this procedure, the original dataset is randomly partitioned into k equal-sized subsamples, or "folds" [39] [38]. Of the k folds, a single fold is retained as the validation data for testing the model, and the remaining k-1 folds are used as training data. The cross-validation process is then repeated k times, with each of the k folds used exactly once as the validation data. The k results are then averaged to produce a single performance estimate [39] [38]. The choice of k involves a bias-variance tradeoff; common choices are k=5 or k=10, which provide a good balance between computational cost and reliable estimation [39] [40]. A lower value of k is computationally cheaper but can lead to higher bias, while a very high k (approaching the number of data points) leads to the Leave-One-Out Cross-Validation (LOOCV) method, which has low bias but high variance and computational cost [39] [40].
Stratified K-Fold Cross-Validation
Stratified K-Fold Cross-Validation is a variation of the standard k-fold method that preserves the percentage of samples for each class in every fold [39] [41]. This is particularly useful for imbalanced datasets where one or more classes are underrepresented [39]. By ensuring that each fold is a good representative of the overall class distribution, stratified cross-validation provides a more reliable performance estimate for classification models on such data and helps the model generalize better [39]. Recent comparative studies on both balanced and imbalanced datasets have reaffirmed that traditional stratified cross-validation consistently performs better on imbalanced data, showing lower bias, variance, and computational cost, making it a safe and recommended choice [42].
Leave-One-Out Cross-Validation (LOOCV)
LOOCV is an exhaustive cross-validation method where the number of folds k is set equal to the number of data points (n) in the dataset [38]. This means that for each iteration, the model is trained on all data points except one, which is left out as the validation set [39] [41]. This process is repeated n times until each data point has been used once as the test set. The advantage of LOOCV is that it utilizes nearly all data for training, resulting in a low-bias estimate [39] [41]. However, a significant drawback is that it can be computationally expensive for large datasets, as the model must be trained n times. Furthermore, testing on a single data point can cause high variance in the performance estimate, particularly if that point is an outlier [39].
Holdout Validation
The Holdout Method is the simplest form of validation. It involves randomly splitting the dataset into two parts: a training set and a testing (or holdout) set [39] [38]. A typical split is 70-80% of data for training and the remaining 20-30% for testing [41]. While this method is simple and fast to execute, its major drawback is its high dependence on a single random split [39]. If the split is not representative of the overall data distribution, the performance estimate can be unreliable and have high variance. It also may not utilize data efficiently for training, especially in smaller datasets, potentially leading to a model with high bias if it misses important patterns in the held-out data [39].
Table 1: Comparison of Common Cross-Validation Techniques
| Feature | K-Fold Cross-Validation | Stratified K-Fold | Leave-One-Out (LOOCV) | Holdout Method |
|---|---|---|---|---|
| Data Split | Divided into k equal folds [39] | Divided into k folds, preserving class distribution [39] | n folds; each fold is a single data point [39] | Single split into training and testing sets [39] |
| Training & Testing | Model is trained and tested k times [39] | Model is trained and tested k times [39] | Model is trained n times and tested n times [39] | Model is trained once and tested once [39] |
| Bias & Variance | Lower bias; variance depends on k [39] [40] | Lower bias; better for imbalanced data [39] [42] | Low bias, but can result in high variance [39] | Higher bias if split is not representative [39] |
| Execution Time | Slower, as model is trained k times [39] | Slower, similar to K-Fold [42] | Very slow for large datasets [39] | Fast, only one training cycle [39] |
| Best Use Case | Small to medium datasets for accurate estimation [39] | Classification problems with imbalanced datasets [39] [42] | Very small datasets where data is limited [39] | Very large datasets or for quick evaluation [39] |
Experimental Protocols for Cross-Validation
A standardized experimental protocol is essential for obtaining credible and reproducible cross-validation results. The following workflow details the key steps, from data preparation to final evaluation, which can be applied in forensic research contexts.
Diagram 1: Cross-validation workflow
Data Preparation and Preprocessing
The initial step involves loading and preparing the dataset for analysis. This includes handling missing values, encoding categorical variables if necessary, and potentially scaling features. For the Iris dataset, a common benchmark, the data is readily available and structured. It is crucial that any preprocessing steps, such as standardization, are learned from the training set and applied to the held-out validation set to prevent data leakage [43]. Using a Pipeline from scikit-learn is a best practice as it ensures that all transformations are correctly contained within the cross-validation loop [43].
Defining the Cross-Validation Strategy
The researcher must select and define the cross-validation strategy based on the dataset's characteristics and the experiment's goals. For a standard k-fold approach, this involves instantiating a KFold object from scikit-learn and specifying the number of splits (n_splits or k). It is good practice to set shuffle=True to randomize the data before splitting and to use a fixed random_state to ensure the results are reproducible [39] [40]. For imbalanced datasets, a StratifiedKFold object should be used instead [39] [43].
Model Training and Evaluation Loop
The core of the experiment is the cross-validation loop. For each split generated by the chosen k-fold object, the following steps are executed:
- Split Data: The data indices are split into training and validation sets for the current fold [39].
- Train Model: The model is trained (fit) on the training subset of the data [39] [40].
- Validate Model: The trained model is used to generate predictions on the validation subset [40].
- Record Metrics: A performance metric (e.g., accuracy, mean squared error) is calculated by comparing the predictions to the true values of the validation set [39] [40].
This process is repeated for each of the k folds.
Performance Analysis and Reporting
After all k folds have been processed, the k performance scores are combined for a final evaluation. The mean of these scores is reported as the overall performance estimate of the model, providing a more reliable measure than a single train-test split [39] [43]. The standard deviation of the scores is also calculated, as it indicates the variance of the model's performance across different data subsets—a high standard deviation suggests the model's performance is sensitive to the specific training data [43] [40]. Finally, the results from multiple models can be compared to select the best-performing algorithm or set of hyperparameters [40].
Implementation with Multiple Tools
The theoretical protocols are implemented using programming tools and libraries. The following section provides a comparative analysis of implementation methods using Python's scikit-learn library, which is a standard tool for machine learning tasks.
Table 2: Comparison of scikit-learn Implementation Tools
| Tool | Primary Function | Key Features | Sample Code Snippet | Output |
|---|---|---|---|---|
KFold Class |
Provides indices to split data into k folds [40]. | Full manual control over the splitting, training, and evaluation process [40]. | kfold = KFold(n_splits=5, shuffle=True, random_state=42)for train_idx, val_idx in kfold.split(X): X_train, X_val = X[train_idx], X[val_idx] model.fit(X_train, y_train) y_pred = model.predict(X_val) # Calculate metrics manually |
Provides the training/validation indices for manual loop implementation [40]. |
cross_val_score Function |
Evaluate a score by cross-validation [43]. | Simple and quick for evaluating a single metric [43] [40]. | scores = cross_val_score(model, X, y, cv=5, scoring='accuracy')print("Average Accuracy: %0.2f" % scores.mean()) |
Returns an array of scores for each fold [43]. |
cross_validate Function |
Evaluate one or multiple metrics by cross-validation [43]. | Allows multiple scoring metrics; returns fit/score times and optional training scores [43]. | scoring = ['accuracy', 'f1_macro']scores = cross_validate(model, X, y, scoring=scoring, cv=5, return_train_score=True)print(scores['test_accuracy']) |
Returns a dict with test/train scores and times [43]. |
Tool Comparison and Use Cases
- Manual
KFoldfor Maximum Flexibility: Using theKFoldclass in a manual loop is ideal for complex scenarios where custom operations are needed during each fold, such as specialized logging, intermediate saving of models, or complex data manipulations that are not supported by higher-level functions [40]. cross_val_scorefor Quick Model Assessment: Thecross_val_scorefunction is the most straightforward tool for a quick and efficient evaluation of a model's performance using a single primary metric [43] [40]. It automates the looping and averaging process, making the code concise.cross_validatefor Comprehensive Model Diagnostics: Thecross_validatefunction is the best choice for a thorough evaluation. Its ability to handle multiple metrics simultaneously and return additional data like computation times and training scores makes it invaluable for robust model selection and for diagnosing issues like overfitting by comparing training and validation performance [43].
The Scientist's Toolkit: Research Reagent Solutions
In the context of computational forensics and model validation, "research reagents" refer to the essential software tools, libraries, and benchmark datasets that form the foundation for reproducible experiments.
Table 3: Essential Research Reagents for Cross-Validation Experiments
| Tool / Dataset | Type | Primary Function in Validation | Application Context |
|---|---|---|---|
| scikit-learn | Python Library | Provides implementations of KFold, cross_val_score, cross_validate, and various ML models [39] [43]. |
Standard tool for building and evaluating machine learning models in Python. |
| Iris Dataset | Benchmark Data | A classic, multi-class dataset used as a known benchmark for evaluating classification models [39] [43]. | Serves as a controlled "known dataset" for initial method validation and teaching. |
| California Housing Dataset | Benchmark Data | A real-world regression dataset used to evaluate model performance on continuous value prediction [40]. | Used for testing models in a regression context with multiple numerical features. |
| StratifiedKFold | Algorithm | A cross-validation object that ensures relative class frequencies are preserved in each fold [39] [43]. | Crucial for validating models on imbalanced datasets, common in forensic scenarios. |
| Pipeline | Software Construct | Ensures that preprocessing steps are correctly fitted on the training data and applied to the validation data within the CV loop [43]. | Prevents data leakage, ensuring a purer and more reliable performance estimate. |
Application in Digital Forensics Validation Frameworks
The rigorous application of cross-validation is directly relevant to the evolving needs of digital forensics, particularly with the emergence of AI-based digital forensics (DFAI). The central challenge in this field is ensuring that tools and methods produce reliable, repeatable, and legally admissible results [34] [3].
Cross-validation provides a methodological backbone for addressing the validation gap often faced by open-source and AI-driven forensic tools. By using known datasets and a structured resampling procedure, practitioners can generate quantitative, defensible evidence of a tool's accuracy and generalizability [34]. This is a practical step toward meeting admissibility standards, such as the Daubert Standard, which requires that a method be empirically tested and have a known error rate [34]. The error rates calculated from the standard deviation of cross-validation scores or from performance variations across folds directly contribute to establishing this known error rate [39] [40].
Furthermore, as AI models in forensics are often criticized for their "black-box" nature, using stratified and cluster-based cross-validation techniques helps ensure that performance estimates are robust across different data distributions, including imbalanced classes [42]. This mitigates the risk of model bias and increases confidence in the AI-generated evidence, which is a significant barrier to adoption identified by practitioners [3]. Thus, integrating standardized cross-validation protocols is a critical component of a broader validation framework that bridges the gap between technical innovation and judicial acceptance in digital forensics.
In forensic science, validation ensures that tools and methods produce accurate, reliable, and legally admissible results [1]. The evolution from traditional to digital forensics has fundamentally shifted validation paradigms. Traditional forensic methods—such as fingerprint, bloodstain pattern, and handwriting analysis—rely heavily on manual examination and physical evidence, making validation a static, often subjective process [44]. In contrast, digital forensics deals with volatile, easily manipulated digital evidence, requiring dynamic and continuous validation to maintain evidentiary integrity amid rapid technological change [1] [44].
This guide compares validation frameworks across these domains, focusing on how continuous validation cycles enable adaptation to operating system updates and emerging technologies. We objectively evaluate performance metrics and experimental data to provide researchers and drug development professionals with a clear understanding of modern validation requirements.
The Imperative for Continuous Validation
Evolving Digital Landscapes and Threats
The digital landscape is rapidly expanding beyond traditional computers to include mobile devices, cloud platforms, IoT ecosystems, and automotive systems [45]. This proliferation creates immense data volume and complexity, rendering periodic validation cycles insufficient. In cybersecurity, for example, traditional defense prevention effectiveness against ransomware fell from 69% in 2024 to 62% in 2025, demonstrating the critical need for continuous security validation [46].
Regulatory and Compliance Drivers
Regulatory frameworks increasingly recognize the necessity of ongoing validation. The FDA's Computer Software Assurance (CSA) framework promotes a risk-based approach that focuses validation efforts on functionality impacting product quality, patient safety, or data integrity [47]. This shift from comprehensive, one-time validation to targeted, continuous testing enables organizations to maintain compliance while adapting to frequent software changes.
Comparative Analysis: Performance Metrics and Experimental Data
Validation Cycle Efficiency
Table 1: Comparison of Validation Cycle Times Across Domains
| Domain | Traditional Validation Cycle | Continuous Validation Approach | Cycle Time Reduction | Key Technologies |
|---|---|---|---|---|
| IT Security Patching | 21-28 days [48] | 24-48 hours [48] | 85-90% | Automated testing platforms (e.g., Rimo3) |
| Pharmaceutical Software Validation | Quarterly/annually [47] | Continuous with updates [47] | N/A | Automated validation platforms (e.g., SIMCO AV) |
| Vehicle System Validation | Exhaustive retesting [49] | Targeted impact analysis [49] | Significant engineering effort saved | Architectural snapshotting, dependency tracing |
| Digital Forensic Tool Validation | Manual revalidation per case [1] | Cross-tool verification, automated hashing [1] | N/A | Hash values, test cases, multiple tool verification |
Error Rate and Reliability Metrics
Table 2: Error Prevention and Detection Rates
| Validation Approach | Prevention Effectiveness | Detection/Alert Rate | Data Source |
|---|---|---|---|
| Traditional Security Defenses (2024) | 69% against ransomware [46] | 14% of logged attacks generate alerts [46] | Picus Security Blue Report 2025 |
| Traditional Security Defenses (2025) | 62% against ransomware [46] | N/A | Picus Security Blue Report 2025 |
| Continuous Breach & Attack Simulation | Identifies gaps before exploitation [46] | Provides empirical evidence for prioritization [46] | Lucenor analysis |
| Digital Forensic Tool Validation | Prevents legal evidence exclusion [1] | Identifies tool parsing inconsistencies [1] | Envista Forensics |
Experimental data from cybersecurity applications demonstrates that Breach and Attack Simulation (BAS) platforms provide quantitative, empirical validation of security postures, moving organizations from qualitative assessments ("we think we're secure") to verifiable states ("we are 95% effective against this specific attack vector") [46].
In digital forensics, experimental protocols for tool validation include:
- Hash-based integrity verification: Comparing hash values before and after imaging to confirm data integrity [1]
- Cross-tool validation: Running identical datasets through multiple forensic tools (e.g., Cellebrite, Magnet AXIOM, MSAB XRY) to identify parsing inconsistencies [1]
- Known dataset testing: Validating tools against standardized test cases with predetermined outcomes [1]
Implementation Frameworks and Methodologies
Life Sciences Implementation
In pharmaceutical and life sciences environments, continuous validation platforms like SIMCO's AV execute test protocols exactly as written, embedding traceability throughout the validation lifecycle [47]. This approach aligns with FDA guidance while accelerating release cycles for cloud-based software.
Figure 1: Continuous Validation Workflow in Regulated Life Sciences Environments
Cybersecurity Implementation
Breach and Attack Simulation (BAS) platforms continuously validate security controls by safely simulating real-world attack scenarios against production systems [46]. This methodology includes:
- Automated scenario execution: Simulating initial access, lateral movement, data exfiltration, and command and control
- Control effectiveness measurement: Quantifying prevention, detection, and response capabilities
- Remediation prioritization: Providing empirical evidence to focus security efforts
Figure 2: Breach and Attack Simulation (BAS) Validation Methodology
Complex Systems Implementation
For autonomous vehicles and complex embedded systems, Applied Intuition's validation approach uses impact analysis to optimize testing scope [49]. This methodology includes:
- Architectural snapshotting: Capturing temporal versions of system requirements and dependencies
- Dependency graph analysis: Modeling systems as interconnected graphs to trace change impacts
- Rule-based prioritization: Ensuring immediate retesting for safety-critical components
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Resources for Validation Research
| Tool/Category | Primary Function | Example Applications | Domain |
|---|---|---|---|
| Breach & Attack Simulation (BAS) | Continuous security control validation | Simulating ransomware TTPs, measuring prevention rates [46] | Cybersecurity |
| Automated Validation Platforms | Executing test protocols without manual intervention | Pharmaceutical software validation, cloud system testing [47] | Life Sciences |
| Forensic Tool Suites | Digital evidence extraction and analysis | Mobile device forensics, cloud data recovery [1] [45] | Digital Forensics |
| Hash Algorithms (SHA-256, MD5) | Data integrity verification | Ensuring forensic image authenticity, chain of custody [1] | Digital Forensics |
| Impact Analysis Tools | Targeted test case selection based on changes | Autonomous vehicle software validation, requirement tracing [49] | Complex Systems |
| Software Bill of Materials (SBOM) | Software supply chain component transparency | Vulnerability impact assessment, dependency management [46] | DevOps/SecOps |
| Continuous Monitoring Agents | 24/7 environmental and system monitoring | GxP space monitoring, temperature mapping [50] | Life Sciences |
Comparative Performance in Technological Adaptation
Adaptation to OS Updates
Digital forensic tools require continuous revalidation with each operating system update. For example, mobile forensic tools must be revalidated with every iOS or Android release to ensure accurate data parsing [1]. The experimental protocol for this validation involves:
- Creating standardized test datasets on devices with the new OS version
- Extracting data using multiple forensic tools to identify parsing inconsistencies
- Comparing results against known data points to verify extraction accuracy
- Documenting tool performance characteristics for legal defensibility
Continuous validation platforms like Rimo3 address this challenge by automatically testing hundreds of applications against OS updates simultaneously, reducing testing cycles from weeks to hours [48].
Emerging Technology Integration
Modern digital forensics has expanded to include drone forensics, IoT forensics, and vehicle system forensics [45]. Each domain requires specialized validation approaches:
- Drone forensics: Validating data extraction from flight logs, sensor data, and communication systems
- IoT forensics: Ensuring accurate interpretation of data from diverse connected devices
- Vehicle forensics: Validating extraction of data from infotainment systems, GPS, and vehicle control modules
The comparative analysis demonstrates that continuous validation cycles are essential across forensic domains, cybersecurity, and life sciences. While implementation details differ, the core principles of automation, risk-based prioritization, and empirical verification consistently deliver superior adaptation to technological change compared to traditional periodic validation.
Future research should focus on developing cross-domain validation standards that enable knowledge transfer between forensic science, cybersecurity, and pharmaceutical development. Such standards would accelerate the adoption of continuous validation frameworks, enhancing reliability and safety across critical domains.
Documentation and Auditable Reporting for Methodological Rigor
In both digital and traditional forensic science, methodological rigor is the cornerstone of credible, defensible, and legally admissible evidence. This rigor is achieved and demonstrated through documentation and auditable reporting, which create a transparent record of all actions, decisions, and findings. Within a broader thesis on validation frameworks, a critical distinction emerges: traditional forensics often validates methods against known physical properties, while digital forensics must validate tools and processes against dynamic, complex data states in a rapidly evolving technological landscape. The core principle, however, remains universal—procedural transparency, result reproducibility, and analytic validity are non-negotiable for scientific and legal acceptance [1] [33].
This guide objectively compares the documentation protocols and reporting outputs of representative tools from digital and traditional forensic disciplines. By examining experimental data and workflows, it aims to provide researchers and professionals with a clear understanding of how methodological rigor is operationalized and assured across these domains, particularly within modern validation frameworks designed to meet legal standards like the Daubert Standard [33].
Comparative Experimental Data: Tool Performance and Output
The following tables summarize quantitative data from controlled experiments comparing digital forensic tools, illustrating key metrics relevant to methodological validation.
Table 1: Digital Forensic Tool Performance in Data Recovery and Artifact Analysis Experiments
| Tool Name | Tool Type | Experiment: Deleted File Recovery | Experiment: Targeted Artifact Search | Key Reporting Feature |
|---|---|---|---|---|
| Autopsy [51] [33] | Open-Source Digital | Recovery of 148/150 control files (98.7% accuracy) [33] | Identification of 99% of planted artifacts [33] | Integrated timeline analysis and HTML reports |
| Forensic Toolkit (FTK) [51] [33] | Commercial Digital | Recovery of 149/150 control files (99.3% accuracy) [33] | Identification of 100% of planted artifacts [33] | Robust processing engine with collaborative case management |
| ProDiscover Basic [33] | Open-Source Digital | Comparable results to commercial tools in repeat tests [33] | Comparable results to commercial tools in repeat tests [33] | Focus on disk imaging and volume analysis |
| Cellebrite UFED [51] [1] | Commercial Digital (Mobile) | Extensive physical and logical extraction capabilities [51] | Advanced parsing of app data and communications [51] | Detailed extraction reports with device information |
Table 2: Documentation and Reporting Features in Traditional vs. Digital Forensic Tools
| Feature / Component | Traditional CSI / Lab Tools | Digital Forensic Suites (e.g., FTK, Autopsy, Magnet AXIOM) |
|---|---|---|
| Inherent Audit Log | Often manual, paper-based chain-of-custody forms | Automated, system-generated logs of all user actions and tool operations [52] [1] |
| Data Integrity Proof | Physical seals, sample custody tags | Cryptographic hashing (MD5, SHA-1) to verify evidence integrity [1] [33] |
| Error Rate Quantification | Established through inter-laboratory comparisons and proficiency testing [1] | Calculated via controlled experiments against known datasets (e.g., NIST tests) [33] |
| Standardized Output | Laboratory report forms, expert witness testimony | Customizable, multi-format reports (HTML, PDF), often with built-in wizard [51] |
| Method Transparency | Detailed in standard operating procedures (SOPs) | Tool validation logs, plugin versioning, and open-source code review potential [1] [33] |
Experimental Protocols for Validation
To generate the comparative data cited in this guide, researchers adhere to rigorous, repeatable experimental protocols. These methodologies are designed to test the limits of forensic tools and ensure their outputs are reliable and auditable.
Protocol for Digital Forensic Tool Validation
This protocol, aligned with NIST Computer Forensics Tool Testing (CFTT) standards, is used to establish the error rates and reliability of digital tools for legal admissibility under the Daubert Standard [33].
- Control Environment Setup: A sterile, forensically clean workstation is prepared. A standardized test disk image is created, containing a known set of files, including deleted files and specific data artifacts (e.g., browser history, registry entries). A cryptographic hash (e.g., SHA-256) is generated for the original evidence source to serve a baseline for integrity checks [1] [33].
- Evidence Acquisition: The tool under test is used to create a forensic image of the test disk. The tool's output hash is compared against the baseline hash to verify a bit-for-bit copy. This step is documented with system timestamps and tool-generated logs [33].
- Controlled Experiment Execution: The tool is tasked with specific functions in triplicate to establish repeatability:
- Data Carving: Recovering a predefined set of deleted files. Success is measured by the number of files correctly recovered and verified against known checksums [33].
- Artifact Search: Executing keyword searches and parsing specific system artifacts. Success is measured by the recall (percentage of planted artifacts found) and precision (absence of false positives) [33].
- Timeline Generation: Creating a system timeline from file system metadata. The output is compared against a known event log for accuracy and completeness.
- Data Analysis and Error Rate Calculation: The results from the tool are rigorously compared against the control dataset. Error rates are calculated quantitatively, for example:
(1 - (Files Recovered / Total Control Files)) * 100[33]. All discrepancies are documented, and the tool's own report is examined for transparency in logging these actions.
Protocol for Traditional Forensic Method Validation (e.g., Chemical Analysis)
This protocol emphasizes the documentation standards for physical evidence analysis, which shares the same goal of producing auditable results.
- Evidence Integrity and Chain of Custody: Upon receipt, the physical evidence is photographed, logged, and stored in a secure location. Every individual who handles the evidence must sign and date a chain-of-custody form, creating an immutable audit trail [1] [53].
- Control Sample Preparation: Known control samples (e.g., a pure reference chemical) are prepared alongside the unknown evidence sample. This verifies the instrument and method are functioning correctly.
- Instrument Calibration and Sample Analysis: The analytical instrument (e.g., GC-MS, microscope) is calibrated using standard reference materials. The evidence sample and controls are then analyzed according to a documented Standard Operating Procedure (SOP). All instrument raw data files and settings are preserved as part of the case record.
- Peer Review and Report Writing: The analyst's findings and interpretations are reviewed by a second, independent qualified scientist. The final report details the methods used, the results obtained, the procedures for maintaining chain of custody, and the conclusions reached, ready for courtroom presentation [1].
Visualization of Validation Workflows
The following diagram illustrates the integrated workflow for validating digital forensic tools and evidence, a core component of a modern validation framework.
Digital Forensic Validation and Reporting Workflow
The Scientist's Toolkit: Essential Research Reagent Solutions
This table details key materials and tools, the "research reagents," essential for conducting validated forensic experiments and investigations.
Table 3: Essential Digital Forensic Research "Reagents" and Tools
| Tool / Material | Function in Experimental Validation |
|---|---|
| Reference Disk Images | Certified datasets (e.g., from NIST) with known content; serve as the ground truth for testing tool accuracy in recovery and analysis [33]. |
| Cryptographic Hashing Tools | Software (e.g., built into FTK, Autopsy) that generates unique digital fingerprints (hashes) to verify evidence integrity throughout the investigative process [1] [33]. |
| Forensic Write-Blockers | Hardware devices that prevent any write operations to a source evidence drive during acquisition, ensuring data is not altered [53]. |
| Virtual Machine Environments | Isolated, reproducible software environments used to test tools and analyze malware without risk to the host system [53]. |
| Open-Source Toolkits (e.g., Sleuth Kit) | Provide modular, command-line tools for fundamental forensic tasks; allow for deep inspection and transparency of the underlying processes [51] [33]. |
| Digital Evidence Management Systems (DEMS) | Centralized platforms that automate audit logging, chain of custody, secure storage, and access controls for digital evidence [52]. |
Identifying Pitfalls and Optimizing Forensic Validation Processes
Validation frameworks are fundamental to ensuring the reliability and admissibility of evidence across all forensic disciplines. In traditional forensic science, validation confirms that analytical techniques, from DNA sequencing to toxicology, produce accurate, reproducible, and scientifically sound results. The legal admissibility of these findings often hinges on meeting standards such as the Daubert Standard, which requires that methods be testable, subjected to peer review, have a known error rate, and be widely accepted within the relevant scientific community [1].
Digital forensics adopts these same core principles but applies them to electronic evidence. The field faces unique challenges, including the easily manipulated nature of digital data, the vast scale of data storage, and the constant evolution of technology and software [54]. Consequently, digital forensic validation must ensure that tools and methods correctly extract, preserve, and interpret data from devices like computers, smartphones, and cloud storage without alteration [1]. A key component of this process is using hash functions to create a unique "fingerprint" for a dataset, allowing investigators to verify with mathematical certainty that the data has not been altered since it was collected [54].
This guide focuses on two pervasive sources of validation failure—timestamp discrepancies and broader data integrity issues—comparing their manifestation and impact across traditional and digital forensic domains.
Comparative Analysis of Validation Failures
The following table summarizes how timestamp and data integrity failures present in traditional versus digital forensic contexts.
Table 1: Comparative Analysis of Validation Failures in Forensic Disciplines
| Validation Failure Category | Manifestation in Traditional Forensics | Manifestation in Digital Forensics | Common Root Causes |
|---|---|---|---|
| Timestamp Discrepancies | Inconsistent recording of sample collection or analysis times in lab notebooks; chain-of-custody documentation gaps. | Misaligned event timestamps across systems; incorrect timezone settings on devices; modification of file metadata [55]. | Lack of synchronized timekeeping protocols; human error in manual logging; system configuration errors. |
| Data Integrity Failures | Physical sample contamination; degradation of biological evidence; transcription errors in lab results; use of expired reagents. | Data corruption during transfer or storage; unauthorized alterations; improper forensic imaging [56] [1]. | Breach of chain-of-custody; software or hardware faults; inadequate validation of tools and methods [1]. |
| Impact on Evidence | Compromises sample reliability, jeopardizes analysis accuracy, and can lead to evidence being ruled inadmissible. | Undermines the authenticity and reliability of digital evidence, potentially rendering it unusable in court [1]. | Failure to adhere to standardized protocols; insufficient quality control checks. |
Experimental Protocols for Investigating Validation Failures
Protocol 1: Investigating Timestamp Discrepancies in Digital Evidence
This protocol is designed to detect, analyze, and reconcile timestamp inconsistencies in digital evidence, a common issue arising from mismatched system times or incorrect forensic tool processing.
Table 2: Key Reagent Solutions for Digital Forensics Validation
| Research Reagent / Tool | Function in Validation |
|---|---|
| Forensic Write-Blockers | Prevents alteration of original evidence during the imaging process, preserving data integrity [57]. |
| Hashing Algorithms (e.g., MD5, SHA-256) | Generates a unique digital fingerprint of a data set to verify its integrity has not changed [54]. |
| Digital Forensic Suites (e.g., Cellebrite, Magnet AXIOM) | Tools used to extract and parse data from digital devices; require validation to ensure accurate data interpretation [1]. |
| Validated Forensic Image | A bit-by-bit copy of the original storage media, serving as the uncontaminated sample for all subsequent analysis [57]. |
Workflow Overview:
Protocol 2: Data Integrity Validation via Cross-System Reconciliation
This methodology tests the integrity of data after it has been migrated or replicated between systems, such as during a cloud migration or evidence transfer. It is adapted from data pipeline and cloud migration validation techniques [58] [59].
Workflow Overview:
Methodology Details:
- Step 1: Define Scope and Parameters: Determine if a full load (all data) or Change Data Capture (CDC) validation is required. Configure task parameters. For example, in an AWS DMS validation task,
PartitionSizedefines the batch of records read for comparison, whileThreadCountsets the number of execution threads used during validation [58]. - Step 2: Execute Validation Task: Run the validation-only task. This process logically partitions the data and uses multiple threads to compare the source and target datasets. Any mismatches are logged to a dedicated failure table [58].
- Step 3: Analyze Results: Query the validation failure table to identify specific erroneous records. Analysis should focus on patterns, such as consistent data type mismatches or collation issues, which point to systemic rather than random errors [59].
- Step 4: Report and Remediate: Generate a detailed report of the discrepancies. Use this report to create targeted data repair scripts and correct the integrity failures at their source.
Case Studies: Consequences of Validation Failures
Digital Forensics: Florida v. Casey Anthony (2011)
In this case, a digital forensic expert for the prosecution initially testified that a computer in the Anthony family home had conducted 84 searches for the term "chloroform." This data point became a key piece of circumstantial evidence for the prosecution.
However, the defense, assisted by digital forensics experts, performed a critical validation of the forensic tool's output. Their analysis revealed that the software had erroneously parsed and counted the data. The validated finding showed that there had, in fact, been only a single search for "chloroform." This vast discrepancy undermined the prosecution's narrative of extensive premeditation and highlighted the absolute necessity of independently validating automated forensic tool outputs before presenting them in court [1].
Data Pipeline Integrity: Financial Trading and Time-Series Data
In the realm of data-driven decision systems, a financial trading firm encountered significant performance issues. Its models, which relied on time-series data to spot market trends, began triggering trades at the wrong moments. Investigation revealed that the root cause was not a market shift but a validation failure in data integrity.
The firm ingested price data from multiple sources, and these feeds has varying timestamp precision (e.g., some with millisecond precision, others with microsecond). This slight misalignment in timestamps caused the analytical models to misfire. The consequence was direct financial loss, demonstrating that in high-stakes environments, validating the consistency and structure of data—including timestamp precision—is as critical as the analysis itself [55].
Timestamp discrepancies and data integrity failures represent a universal threat to the validity of forensic conclusions, whether in a traditional lab or a digital investigation. The core principle of validation—ensuring that methods and tools produce accurate, reliable, and reproducible results—is consistent across disciplines.
The key difference lies in the application. Digital forensics must combat challenges like the volatility of data, the sheer scale of storage, and the rapid obsolescence of technology. As forensic science increasingly incorporates Artificial Intelligence (AI) and machine learning, the need for robust validation becomes even more pressing. The "black box" nature of some AI systems introduces new challenges for transparency and interpretation, necessitating a renewed focus on explainable AI (XAI) and rigorous, continuous validation of automated outputs [3]. A commitment to meticulous validation protocols is the foundation upon which trustworthy forensic science is built.
The integration of Artificial Intelligence (AI) into digital forensics represents a paradigm shift, introducing capabilities for processing vast and complex datasets far beyond human capacity. However, this technological evolution brings forth a fundamental challenge: the "black box" problem, where the internal decision-making processes of AI models are opaque and difficult to interpret. This opacity directly conflicts with the foundational principles of forensic validation, which demand that methods be not only effective but also transparent, reproducible, and legally defensible. In legal contexts, evidence must withstand scrutiny under established standards like Daubert, which requires scientific methods to be testable, peer-reviewed, have known error rates, and be generally accepted within the relevant community [1]. The black-box nature of many complex AI models, particularly deep learning systems, challenges these criteria, as their conclusions can be difficult to explain or challenge in an adversarial legal setting [60].
This creates a critical juncture for the field. AI-powered tools are being successfully applied to increase investigator productivity by quickly sifting through large volumes of data and highlighting relevant information, and even show potential for more robust recovery of deleted files [3]. Yet, their widespread practical adoption is hampered by significant validation hurdles. A 2025 study highlights that the primary barriers stem from insufficient validation processes and a lack of clear methods for presenting and explaining AI-generated evidence [3]. This article provides a comparative analysis of AI-powered and traditional digital forensics tools, examining their performance and the evolving validation frameworks essential for maintaining scientific integrity and legal admissibility in the age of AI.
Comparative Analysis: Traditional vs. AI-Powered Forensic Tools
The following table summarizes the core distinctions between traditional digital forensics tools and emerging AI-powered solutions, highlighting key differences in their approach, functionality, and validation landscapes.
Table 1: Comparison of Traditional and AI-Powered Digital Forensics Tools
| Feature | Traditional Digital Forensics Tools | AI-Powered Forensic Tools |
|---|---|---|
| Core Functionality | Data extraction, disk imaging, keyword searching, file system analysis, recovery of deleted files [26] [61]. | Pattern recognition in large datasets, anomaly detection, automated content categorization (e.g., via Magnet.AI), image/video classification [26] [3]. |
| Primary Strengths | Proven track record, well-understood error rates, transparent processes, strong legal precedent for admissibility [26] [1]. | High efficiency and speed with large-scale data, ability to uncover subtle connections, adaptability to new data patterns [3] [62]. |
| Inherent Transparency | High. Processes are generally repeatable and understandable by a skilled analyst [1]. | Low ("Black Box"). Internal decision-making logic is often complex and not easily interpretable [60] [63]. |
| Validation Approach | Tool and method validation using hash verification, cross-tool verification, and established forensic principles [1]. | Emerging focus on Explainable AI (XAI) and performance benchmarking against known datasets, but standardized protocols are under development [3] [60]. |
| Key Validation Challenges | Keeping pace with new file systems and encryption; less acute transparency issues [26]. | Demonstrating reliability and absence of bias; explaining outputs for legal proceedings; rapid model updates necessitating continuous re-validation [3] [63]. |
Performance and Accuracy Metrics
Quantitative evaluations of AI tools reveal both their potential and their context-dependent performance. A 2025 study assessing AI in forensic image analysis found that tools like ChatGPT-4, Claude, and Gemini demonstrated promising but variable accuracy. When analyzing crime scene images, these AI tools achieved an average score of 7.8 in homicide scenarios but encountered more difficulties with arson scenes, where the average score dropped to 7.1 [62]. This underscores that AI performance is not uniform and must be validated against specific forensic scenarios.
In other specialized domains, AI has shown high efficacy. For instance, in forensic accounting, AI-driven pattern recognition has become vital for detecting financial anomalies and fraudulent transactions [64]. In cybersecurity forensics, an Explainable AI (XAI) system utilizing SHAP and LIME for intrusion detection was reported to achieve high accuracy, precision, recall, and F1-scores on the CICIDS2017 dataset, though specific numerical results were not provided in the source [60]. These tools help analysts process evidence more quickly, but their ultimate value in court depends on the robustness of the validation behind them.
Experimental Protocols for Validating AI Forensic Tools
Validating AI-powered forensic tools requires a multi-faceted experimental approach that goes beyond traditional software testing. The following workflow outlines a comprehensive validation protocol that integrates technical performance assessment with legal-admissibility preparedness.
Detailed Experimental Methodology
The validation of an AI-powered forensic tool should be structured as a rigorous, multi-stage scientific experiment.
- 1. Define Test Scope and Legal Standards: The first step is to explicitly define the tool's intended forensic use case (e.g., mobile app data parsing, image classification, network intrusion detection) and the legal admissibility standards it must meet, such as the Daubert or Frye standards [1]. This defines the criteria for success.
- 2. Acquire and Generate Benchmark Datasets: Validation requires robust, known datasets. Researchers should use widely recognized, public benchmark datasets like CICIDS2017 for network forensics [60]. Furthermore, to test generalizability, it is critical to create controlled test cases with known ground truth, which may involve simulated data or expertly labeled real-world evidence.
- 3. Execute Tool on Diverse Test Scenarios: The AI tool is run against the benchmark and controlled datasets. The study should include a diverse range of scenarios, as performance can vary significantly—for example, between homicide and arson scene image analysis [62]. This step assesses the tool's functional performance in extracting, analyzing, and presenting evidence.
- 4. Quantitative Performance Analysis: The tool's outputs are compared against the known ground truth. Key metrics must be calculated, including:
- Accuracy, Precision, Recall, and F1-score to measure classification performance [60].
- Error Rates, a critical factor for Daubert standards, must be explicitly quantified and documented [1].
- Processing Speed and Resource Utilization compared to traditional methods to establish practical efficiency gains.
- 5. Explainability and Transparency Audit: This stage directly addresses the black box problem. Using XAI techniques like SHAP (Shapley Additive Explanations) and LIME (Local Interpretable Model-agnostic Explanations), analysts probe the model to determine which features most influenced its decisions [60]. The goal is to generate human-readable explanations for the AI's outputs, which are essential for expert testimony and cross-examination.
- 6. Cross-Validation and Robustness Testing: Results should be validated against outputs from established, non-AI tools (e.g., using Cellebrite UFED or Magnet AXIOM as a reference point) [26] [1]. The tool should also be tested against adversarial attacks and data corruption to evaluate its robustness and failure modes.
- 7. Documentation and Reporting: The entire validation process, including software versions, datasets, procedures, results, error rates, and limitations, must be thoroughly documented to ensure reproducibility and transparency [1]. This comprehensive report forms the basis for defending the tool's use in an investigation.
A Framework for Trust: Implementing Explainable AI (XAI) in Forensics
To mitigate the black box problem, the field is increasingly turning to Explainable AI (XAI). XAI aims to make AI systems understandable and trustworthy by providing clear explanations for their decisions, which is a non-negotiable requirement in legal contexts [60]. An effective XAI framework for digital forensics is not a single tool but a multi-layered approach to ensure transparency.
Table 2: Core Components of an Explainable AI (XAI) Framework for Digital Forensics
| Component | Function | Example Techniques & Technologies |
|---|---|---|
| Interpretable Models | Provides inherent transparency by using models whose logic can be easily understood by humans. | Decision Trees, Rule-Based Systems [60]. |
| Model-Agnostic Explanation Methods | Generates post-hoc explanations for the outputs of any "black box" model, such as a complex deep neural network. | SHAP (Shapley Additive Explanations): Quantifies the contribution of each input feature to the final prediction [60]. LIME (Local Interpretable Model-agnostic Explanations): Creates a local, interpretable model to approximate the predictions of the black box model for a specific instance [60]. |
| Visualization and Reporting Tools | Presents explanations in an intuitive, human-readable format for investigators, attorneys, and judges. | Real-time dashboards integrating SHAP/LIME outputs, feature importance graphs, and interactive correlation timelines [60]. |
The implementation of this XAI framework allows a digital forensics expert to answer critical "why" questions. For example, if an AI tool flags a specific network event as an intrusion, SHAP can show that the decision was primarily based on the packet size, source IP reputation, and timing—explanations an expert can then corroborate with other evidence. This process bridges the gap between the AI's complex internal computations and the legal requirement for accountable, defensible expert testimony [60].
Research and validation in AI-based forensics require a suite of specialized software tools, datasets, and computational resources. The following table details key "research reagent solutions" essential for conducting rigorous experiments in this field.
Table 3: Essential Research Resources for AI Forensic Tool Validation
| Resource Category | Specific Tool / Dataset | Primary Function in Validation |
|---|---|---|
| Benchmark Datasets | CICIDS2017 | A benchmark dataset for intrusion detection systems, containing benign and modern attack traffic profiles; used for training and evaluating AI models for network forensics [60]. |
| Custom Forensic Images | Controlled datasets (e.g., simulated crime scene images, disk images with planted evidence) with known ground truth, crucial for quantifying accuracy and error rates [62]. | |
| AI Forensics Platforms | Magnet AXIOM | A commercial digital forensics suite with integrated AI (Magnet.AI) for automated artifact categorization; serves as a benchmark for comparison and a tool for cross-validation [26]. |
| Custom XAI Systems | In-house or open-source systems integrating deep learning models (CNNs, RNNs) with XAI libraries (SHAP, LIME) for developing and testing new explainable methods [60]. | |
| Explanation & Visualization Libraries | SHAP (SHapley Additive exPlanations) | A unified Python library used to calculate feature importance and generate explanations for any machine learning model's output, critical for transparency audits [60]. |
| LIME (Local Interpretable Model-agnostic Explanations) | A Python library that explains individual predictions of any classifier by perturbing the input and seeing how the prediction changes, useful for instance-level explanations [60]. | |
| Computational Infrastructure | GPU-Accelerated Workstations | Essential for training complex deep learning models (e.g., CNNs for image analysis, LSTMs for sequential data) and running large-scale validation experiments in a feasible time [60]. |
The integration of AI into digital forensics is inevitable and holds immense promise for enhancing the scale, speed, and scope of investigations. However, the "black box" problem presents a formidable challenge that must be overcome for these tools to be trusted pillars of the justice system. The path forward requires a cultural and technical shift towards continuous, rigorous validation and the principled integration of Explainable AI (XAI). As one study concludes, contrary to prior assumptions, XAI alone cannot resolve adoption challenges; there is a disconnect between this belief and practitioners' needs, highlighting a demand for more robust, standardized, and legally-vetted validation frameworks [3]. The future of forensic science depends on a collaborative effort between tool developers, forensic scientists, and legal professionals to build AI systems that are not only powerful but also transparent, accountable, and fundamentally valid.
The digital forensics landscape is undergoing a fundamental paradigm shift, moving from traditional static analysis of stored data toward the critical challenge of acquiring volatile evidence from active mobile devices. This evolution is driven by the pervasive integration of smartphones and Internet of Things (IoT) devices into daily life, with the number of mobile devices worldwide expected to reach 18.22 billion in 2025 [65]. Unlike traditional computer forensics, which often deals with stable storage media, mobile forensics confronts a landscape where evidence is inherently transient. Data degradation begins the moment a phone is seized, accelerated by features like location-based security protocols, auto-reboots, USB restrictions, and ephemeral artifacts [66]. This volatility creates a pressing need for optimized live data acquisition methodologies that can capture evidence before it is lost, while simultaneously meeting the rigorous standards required for forensic validation and legal admissibility.
The scientific community faces a critical juncture in developing validation frameworks for these new acquisition techniques. Traditional digital forensics research relied on stable, reproducible conditions for evidence collection. In contrast, the mobile ecosystem demands validation approaches that account for dynamic device states, rapid operating system updates, and sophisticated encryption. This article examines current methodologies and tools for mobile device and live data acquisition, comparing their performance against traditional forensic approaches and framing the discussion within the broader thesis of evolving validation frameworks for digital forensics research.
Comparative Analysis of Acquisition Methodologies
Traditional vs. Modern Digital Forensics: A Paradigm Shift
The fundamental differences between traditional computer forensics and modern mobile forensics necessitate distinct approaches to evidence acquisition and validation. Understanding these distinctions is essential for developing appropriate methodological frameworks.
Table 1: Fundamental Differences Between Computer and Mobile Forensics
| Aspect | Computer Forensics | Mobile Forensics |
|---|---|---|
| Primary Devices | Desktops, laptops, servers [67] [68] | Smartphones, tablets, IoT devices [67] [68] |
| Data Nature | Relatively stable, persistent storage [68] | Highly volatile, frequently overwritten [68] [66] |
| Acquisition Approach | Standardized disk imaging, live system analysis [67] | Physical/logical extraction, cloud acquisition [67] |
| Primary Challenges | Data volume, encryption evolution [68] | Device diversity, encryption, rapid OS changes [67] [69] |
| Evidence Types | Documents, emails, system files [68] | Location data, app usage, social media, communications [68] |
| Preservation Priority | Evidence integrity over time [69] | Immediate acquisition to prevent data loss [66] |
Performance Comparison of Modern Acquisition Techniques
Contemporary mobile forensics employs multiple acquisition techniques, each with distinct advantages, limitations, and appropriate application scenarios. The performance characteristics of these methods directly impact their suitability for different investigative contexts.
Table 2: Performance Comparison of Mobile Data Acquisition Techniques
| Acquisition Method | Data Recovery Capabilities | Technical Barriers | Forensic Soundness | Best Application Scenarios |
|---|---|---|---|---|
| Logical Extraction | User-accessible data only; cannot recover deleted files [67] | Low; minimal device intervention [67] | High; minimal data alteration [67] | Initial triage, intact devices, limited scope investigations |
| Physical Extraction | Complete file system including deleted/hidden data [67] | High; requires specialized tools/ expertise [67] | Moderate; invasive process [67] | Critical cases requiring maximum data recovery |
| Cloud Acquisition | Cloud-synced data; potentially deleted device data [67] | Legal/compliance hurdles [63] | High; direct from source [67] | When device unavailable or damaged |
| Live RAM Acquisition | Volatile memory content (encryption keys, active processes) | Technical complexity; data modification risk | Variable; depends on methodology | Bypassing encryption, investigating running applications |
Experimental Protocols for Acquisition Validation
Protocol 1: Cross-Device Unified Analysis Methodology
Objective: To validate a comprehensive approach for acquiring and correlating evidence across multiple mobile devices, addressing the challenge of fragmented communication records in investigations.
Materials:
- Forensic Workstation: Computer with sufficient processing power and storage.
- Acquisition Hardware: Cellebrite UFED Premium adapter or Oxygen Forensic Detective [65] [66].
- Extraction Software: Industry-standard tools (Oxygen Forensics, Magnet Forensics) [69].
- Analysis Platform: Unified database system for cross-device correlation [70].
Methodology:
- Device Seizure and Isolation: Immediately place devices in Faraday bags to prevent network connectivity and remote data wiping [69].
- Parallel Data Acquisition: Perform simultaneous logical or physical extraction on all devices using established forensic tools [70].
- Data Typing and Mapping: Extract and categorize data types including communications (SMS, MMS, chat apps), user content (address book, calendar), and device content (geolocation history, Wi-Fi networks) [70].
- Unified Database Integration: Import structured data from all devices into a consolidated forensic database, maintaining strict chain of custody documentation [70].
- Relationship Mapping: Employ network/link analysis to identify relationships across devices and individuals through shared contacts, communication patterns, and geographic co-location [70].
- Validation via Correlation: Verify findings through multiple data sources (e.g., correlating message timestamps with location data) to establish evidence reliability [70].
Validation Metrics:
- Percentage of recovered deleted messages through cross-device comparison
- Number of identified additional participants through address book mining
- Temporal consistency of correlated events across devices
Protocol 2: Volatile Data Preservation Workflow
Objective: To establish and validate a rapid acquisition protocol for preserving volatile mobile evidence that degrades immediately upon device seizure.
Materials:
- Portable Acquisition Device: Field-grade extraction tool with battery power.
- Faraday Containment: Signal-blocking bags or containers.
- Power Supply: Portable power bank to maintain device charge.
- Forensic Write-Blockers: Hardware to prevent data modification.
Methodology:
- Pre-Acquisition Assessment: Document device state (screen status, running applications) without interacting with the device [66].
- Immediate Signal Isolation: Place device in Faraday bag while maintaining power to prevent data loss from power-off security locks [66].
- Rapid Logical Acquisition: Connect via forensic write-blocker and perform expedited logical extraction prioritizing most volatile data first [66].
- Unified Log Capture: For iOS devices, collect unified logs prior to full file system extraction to prevent log corruption from forensic tools [66].
- System State Documentation: Record active processes, network connections, and system time settings before disconnection.
- Post-Acquisition Verification: Generate hash verification of extracted data and maintain detailed acquisition documentation.
Validation Metrics:
- Time from seizure to acquisition completion
- Percentage of unified log preservation compared to post-extraction
- Successful recovery of encryption keys from active memory
Figure 1: Volatile Evidence Acquisition Workflow
The Researcher's Toolkit: Essential Reagent Solutions
Table 3: Essential Research Reagents for Mobile Device Acquisition
| Tool/Category | Specific Examples | Research Function | Technical Specifications |
|---|---|---|---|
| Hardware Extraction Tools | Cellebrite UFED Premium, Oxygen Forensic Detective [65] | Physical data acquisition from mobile devices | Supports latest iOS/Android devices; bypasses security mechanisms |
| Forensic Software Platforms | Oxygen Forensics, Magnet Forensics [69] | Data analysis and visualization | Parses 35,000+ device types; AI-powered data correlation [65] |
| Signal Isolation Equipment | Faraday bags, boxes, signal-blocking containers [66] | Prevents remote data wiping | Blocks cellular, Wi-Fi, Bluetooth signals |
| Unified Analysis Database | Custom SQL databases, Relativity integration [70] | Cross-device evidence correlation | Stores 200K+ discrete messages/files per device; enables link analysis |
| Legal Compliance Framework | SWGDE guidelines, privacy protocols [66] | Ensures evidence admissibility | Addresses GDPR, CLOUD Act conflicts [63] |
Validation Framework Integration
The acquisition methodologies discussed require robust validation frameworks to ensure scientific rigor and legal admissibility. Traditional digital forensics validation focused primarily on the integrity of stored data through hash verification and write-blocking procedures. However, mobile and live data acquisition demands expanded validation parameters that account for temporal factors, device state variability, and the increasing integration of artificial intelligence (AI) in forensic tools.
A critical challenge in modern forensic validation is addressing the "black-box" nature of AI-powered tools. These systems can rapidly process large amounts of heterogeneous data and highlight relevant information, but their decision-making processes often lack transparency [3]. The emerging field of Explainable AI (XAI) seeks to mitigate this issue by improving the interpretability of AI-generated evidence, though practical implementation remains challenging [3]. Research indicates that fewer than half of digital forensic practitioners have specific policies for validating AI-based tools, with most relying on traditional procedures that may be insufficient for these advanced systems [3].
The SOLVE-IT knowledge base represents a promising development in validation frameworks, systematically cataloging forensic techniques, their associated weaknesses, and potential mitigations [66]. Inspired by MITRE ATT&CK, this resource currently indexes 104 techniques under 17 investigative objectives, providing a structured approach for validating forensic processes including mobile acquisition methodologies [66].
Figure 2: Evolution of Digital Forensics Validation Frameworks
The optimization of mobile device and live data acquisition methodologies represents a critical frontier in digital forensics research. As mobile devices continue to evolve with advanced encryption, increasingly sophisticated operating systems, and greater storage capacities, traditional acquisition approaches become progressively inadequate. The experimental protocols and comparative analyses presented demonstrate that successful evidence recovery in this volatile landscape requires specialized tools, rapid response methodologies, and cross-device analytical approaches.
Future research directions must address several emerging challenges, including the standardization of AI-based forensic tool validation, development of more effective techniques for IoT device acquisition, and establishment of legal frameworks that keep pace with technological innovation. The integration of explainable AI principles into forensic practice will be particularly crucial for maintaining transparency and evidence admissibility. Furthermore, the digital forensics community must prioritize the development of shared datasets, such as the ForensicsData initiative [71], to enable reproducible research and tool validation while respecting privacy concerns. As the field continues to evolve, the collaboration between tool developers, forensic practitioners, and legal professionals will be essential for developing robust validation frameworks that ensure both technological efficacy and judicial integrity.
The explosion of digital data presents unprecedented challenges for forensic investigations. Where traditional forensics once dealt with physical evidence in manageable quantities, modern digital forensics routinely encounters terabyte-scale data environments comprising millions of files from diverse sources [72]. This volume and complexity fundamentally alter the risk landscape, demanding robust validation frameworks to ensure evidentiary integrity.
In high-volume environments, traditional forensic methods face scalability limitations, while digital forensic tools encounter performance degradation and interpretation errors. Effective risk mitigation requires understanding these distinct challenges across forensic disciplines and implementing structured approaches to validation, tool selection, and data management. This comparison guide examines these critical aspects through an empirical lens, providing researchers and forensic professionals with actionable methodologies for maintaining scientific rigor at scale.
Comparative Forensic Frameworks: Digital vs. Traditional Approaches
Fundamental Divergence in Evidence Handling
Traditional and digital forensic disciplines employ fundamentally different validation frameworks, reflecting their distinct evidence types and analytical challenges. The table below systematizes these key differences:
| Aspect | Digital Forensics | Traditional Forensics |
|---|---|---|
| Primary Evidence | Electronic data: hard drives, mobile devices, cloud storage, network logs [53] | Physical materials: DNA, fingerprints, fibers, ballistics [53] |
| Core Validation Focus | Tool accuracy, data interpretation, timestamp reliability, metadata authenticity [1] [11] | Procedure standardization, contamination prevention, chain of custody [53] |
| Volume Challenge | Exponential data growth; Terabyte- to petabyte-scale common [72] | Linear physical evidence growth; Practical storage and processing limits |
| Key Risk Factors | Parsing errors, tool misinterpretation, cryptographic obfuscation, data volatility [11] | Sample degradation, contamination, subjective interpretation, reagent variability |
| Typical Work Environment | Computer labs, digital workstations; Potential for remote analysis [53] | Wet labs, crime scenes; Typically requires physical presence [53] |
Validation Principles Across Disciplines
Despite methodological differences, core validation principles unite both forensic domains:
- Reproducibility: Results must be repeatable by qualified professionals using the same methods [1].
- Transparency: All procedures, software versions, and chain-of-custody records require thorough documentation [1].
- Error Rate Awareness: Methods must have known error rates disclosed in reports and testimony [1].
- Continuous Validation: Tools and methods require frequent revalidation due to technological evolution [1].
In digital forensics, validation confirms that forensic tools accurately extract and interpret data without alteration, and that analysts correctly understand the context and meaning of digital artifacts [1] [11]. For traditional forensics, validation ensures standardized procedures yield consistent, reliable results across different practitioners and laboratories.
Risk Assessment in Terabyte-Scale Environments
Systemic Risks in Large-Scale Data Management
High-volume data environments introduce specific risks that threaten both investigative integrity and operational efficiency:
Data Integrity Risks: In big data environments, maintaining data validity and trustworthiness becomes challenging due to diverse applications, databases, and systems processing the data [73]. Without proper validation, forensic conclusions may rest on flawed or misinterpreted digital evidence [11].
Compliance and Privacy Risks: Combining data from multiple sources can create "toxic combinations" that inadvertently violate privacy regulations by enabling re-identification of individuals from supposedly anonymized datasets [73].
Operational Risks: Manual processes that function with small data volumes collapse at terabyte scale. Teams routing documents by email, tracking approvals in spreadsheets, or relying on manual follow-ups experience critical bottlenecks and audit trail gaps [74].
Storage Management Risks: Inadequate data lifecycle management leads to accumulation of Redundant, Obsolete, or Trivial (ROT) data, which increases storage costs, complicates discovery, and heightens security risks [75]. On average, 68% of stored data in enterprises goes unused [75].
Quantitative Impact of Data Risks
The financial and operational impacts of poor data management in high-volume environments are substantial:
| Risk Category | Quantitative Impact | Primary Causes |
|---|---|---|
| Data Breaches | 35% of breaches access untracked data existing outside official oversight [75] | Unmanaged data created outside formal IT oversight [75] |
| Storage Costs | $1.44M of risky data found per TB scanned on average [75] | High volumes of ROT data; Inefficient storage tiering [75] [72] |
| Data Utilization | 68% of stored data in enterprises goes unused [75] | Lack of data lifecycle management; Inadequate classification [76] |
| Compliance | 16% increase in breach costs linked to unmanaged data [75] | Poor data governance; Inconsistent retention enforcement [74] |
Experimental Framework for Tool Validation
Methodology for Forensic Tool Evaluation
Validating forensic tools in high-volume environments requires rigorous experimental design. The following methodology provides a framework for comparative tool assessment:
Test Dataset Creation: Develop standardized terabyte-scale reference datasets containing known artifacts, including representative file types (documents, images, databases, emails) and embedded target data. Datasets should include both active and deleted content with verified ground truth.
Performance Metrics: Establish quantitative measures including processing throughput (GB/hour), artifact detection rates, false positive/negative ratios, memory utilization, and system stability under sustained load.
Validation Protocols: Implement three-tier validation: (1) Tool Verification confirming software functions as intended; (2) Method Validation ensuring procedures produce consistent outcomes; (3) Analysis Validation evaluating interpreted data accuracy [1].
Cross-Tool Corroboration: Compare outputs across multiple forensic platforms (e.g., Cellebrite, FTK, X-Ways, Autopsy) to identify inconsistencies or tool-specific parsing errors [1] [11].
Experimental Data: Tool Performance Comparison
The following table summarizes hypothetical experimental results from testing forensic tools against a 2TB reference dataset containing 1.5 million files:
| Tool / Platform | Processing Time (Hours) | RAM Utilization (GB) | Artifact Recovery Rate (%) | False Positive Rate (%) | Carving Accuracy (%) |
|---|---|---|---|---|---|
| Tool A | 6.5 | 24 | 98.7 | 1.2 | 95.4 |
| Tool B | 8.2 | 18 | 97.3 | 2.1 | 92.8 |
| Tool C | 5.1 | 32 | 99.1 | 0.8 | 97.2 |
| Tool D | 9.7 | 14 | 95.8 | 3.4 | 89.6 |
Note: Experimental data presented is illustrative. Actual results will vary based on hardware configuration, dataset composition, and tool version.
Mitigation Strategies for High-Volume Data Environments
Technical Implementation Framework
Effective risk mitigation in terabyte-scale forensic environments requires a layered approach addressing storage architecture, data governance, and validation protocols:
Storage Infrastructure Optimization: Implement distributed storage systems like Hadoop (HDFS) or cloud object storage (Amazon S3, Azure Blob) designed for horizontal scalability [72]. Deploy automated tiering policies to move cold, low-activity data to cost-efficient archival platforms while maintaining accessibility for forensic review [75].
Automated Data Governance: Establish classification-based retention policies triggered by regulatory mandates or event-based triggers (e.g., case closure) [74]. Apply security actions at scale based on predefined risk policies across cloud, on-premise, and legacy systems [75].
Validation Automation: Develop automated validation scripts to verify tool outputs against known datasets and generate hash values confirming data integrity before and after imaging [1]. Implement continuous integration pipelines to revalidate tools following software updates or new data formats.
Unmanaged Data Discovery: Deploy specialized solutions to identify "dark data" residing outside formal IT oversight, which contributes to 35% of data breaches [75] [73]. Conduct regular scans to locate and secure this unprotected information.
Forensic Validation Protocol for Location Data
Location artifacts from mobile devices require particular validation rigor, as demonstrated by the following experimental protocol:
Experimental Objective: Validate the accuracy of parsed versus carved location data from iOS and Android devices under controlled conditions.
Methodology:
- Configure test devices to track known location pathways with verified ground truth
- Extract data using multiple forensic tools (Cellebrite, Magnet AXIOM, XRY)
- Compare parsed location records from known databases (e.g., Cache.sqlite) against carved location artifacts
- Analyze discrepancies in coordinates, timestamps, and contextual accuracy
Experimental Findings: Carved location data exhibited a 15-20% false positive rate in controlled tests, frequently mispairing coordinates with unrelated timestamps (e.g., expiration dates misinterpreted as visit timestamps) [11]. Parsed data from known databases demonstrated higher reliability but required validation against multiple sources to detect database corruption or manipulation.
Essential Research Reagent Solutions
The following tools and platforms constitute essential infrastructure for terabyte-scale forensic research and validation:
Digital Forensic Research Toolkit
| Tool / Solution | Primary Function | Research Application |
|---|---|---|
| Cellebrite Physical Analyzer | Mobile device forensics | Extraction and analysis of smartphone data; Validation of mobile artifact interpretation [11] |
| FTK (Forensic Toolkit) | Computer forensics | Large-scale disk imaging and analysis; Performance benchmarking in high-volume environments [53] |
| Amazon S3 / Azure Blob | Cloud object storage | Scalable storage for reference datasets; Cost-effective evidence archiving [72] |
| Hadoop (HDFS) | Distributed storage | On-premise big data storage; Research into distributed forensic processing [72] |
| EnCase Forensic | Digital investigations | Cross-platform forensic analysis; Tool validation and comparison studies [53] |
| Magnet AXIOM | Digital evidence analysis | Cloud and mobile forensics; Artifact recovery rate studies [1] |
Managing terabyte-scale data in forensic research demands disciplined approaches to validation, tool selection, and data governance. This comparative analysis demonstrates that while digital and traditional forensics face distinct challenges at scale, both disciplines require rigorous methodological validation to maintain scientific credibility.
Experimental evidence indicates that no single tool or platform comprehensively addresses all high-volume forensic scenarios. Instead, a diversified approach incorporating cross-tool validation, automated governance policies, and structured risk assessment provides the most robust foundation for reliable forensic research. Future work should develop standardized benchmarking datasets and validation protocols specific to terabyte-scale environments, enabling more consistent comparison across tools and methodologies.
As data volumes continue their exponential growth, the forensic research community must prioritize scalable validation frameworks that maintain evidentiary integrity without compromising investigative efficiency. The methodologies and comparative data presented here offer a foundation for these critical developments.
Resource and Workflow Optimization for Efficient Validation Protocols
Validation protocols form the foundational bridge between scientific evidence and its acceptance in a legal context. In forensic science, whether digital or traditional, validation ensures that the tools and methods used to analyze evidence are accurate, reliable, and legally admissible [1]. The consequences of inadequate validation are severe, ranging from the legal exclusion of evidence and miscarriages of justice to a permanent loss of credibility for the forensic expert or laboratory [1]. This guide provides a comparative analysis of validation frameworks across digital and traditional forensic disciplines, focusing on optimizing their associated resources and workflows.
The core principles of forensic validation—reproducibility, transparency, error rate awareness, and peer review—are universal [1]. However, the rapid evolution of technology introduces unique challenges. Digital forensics must constantly revalidate tools against new operating systems and encryption schemes [1], while traditional forensics, such as DNA testing laboratories, are adapting to updated standards like the 2025 FBI Quality Assurance Standards which now provide clearer implementation plans for Rapid DNA technologies [77]. This guide leverages recent experimental data and evolving standards to objectively compare validation approaches, providing researchers and professionals with a structured pathway for developing efficient and forensically sound protocols.
Comparative Analysis: Validation in Digital vs. Traditional Forensics
A side-by-side comparison of validation requirements highlights key differences in resources, workflows, and legal considerations between the two domains. The following table synthesizes these distinctions based on current research and standards.
Table 1: Comparison of Validation Frameworks in Digital and Traditional Forensics
| Aspect | Digital Forensics | Traditional Forensics (e.g., DNA/Ballistics) |
|---|---|---|
| Primary Validation Drivers | Rapid technological change, new OS/encryption, cloud computing, IoT devices [32] [1] | Standardized method updates, new kit/reagent implementation, new instrumentation (e.g., Rapid DNA) [78] [77] |
| Key Legal Standards | Daubert Standard (Testability, Peer Review, Error Rates, General Acceptance) [33] [1] | FBI Quality Assurance Standards (QAS), Daubert/Frye Standards [77] [1] |
| Core Validation Workflow | Tool Validation → Method Validation → Analysis Validation [1] | Collaborative Method Validation → Independent Verification → Ongoing Proficiency Testing [78] |
| Resource Intensity | High frequency of re-validation due to constant software/hardware updates [1] | High initial validation cost; less frequent but more structured re-validation cycles [78] |
| Error Rate quantification | Calculated via controlled experiments (e.g., comparing acquired artifacts to control references) [33] | Established through inter-laboratory studies and proficiency testing programs [78] |
| Emerging Challenges | AI "black box" algorithms, deepfake detection, cloud data distribution [32] [1] | Next-Generation Sequencing (NGS), integrating Rapid DNA into existing workflows [77] [5] |
The data reveals that while digital forensics faces a steeper challenge in maintaining validation due to the pace of technological change, traditional forensics operates within more structured but sometimes slower-moving standardization processes. A promising trend for optimizing resources in both fields is the move toward collaborative validation models. In this model, one forensic science service provider (FSSP) publishes a full method validation in a peer-reviewed journal, allowing other FSSPs to conduct a much more abbreviated verification process, thereby eliminating significant redundant development work and sharing the burden of cost [78].
Experimental Protocols for Validation
Protocol for Validating Digital Forensic Tools
A recent 2025 study provides a rigorous experimental methodology for validating the legal admissibility of evidence from open-source digital forensic tools, directly applicable to resource optimization [33]. The protocol can be summarized as follows:
- Objective: To validate and enhance a framework ensuring the legal admissibility of digital evidence acquired through open-source forensic tools, satisfying the requirements of the Daubert Standard [33].
- Controlled Environment: Utilized two Windows-based workstations for a comparative analysis between commercial (FTK, Forensic MagiCube) and open-source (Autopsy, ProDiscover Basic) tools [33].
- Test Scenarios: Each experiment was performed in triplicate to establish repeatability metrics.
- Preservation and Collection of Original Data: Verifying the integrity of data imaging.
- Recovery of Deleted Files via Data Carving: Testing the ability to recover data from unallocated space.
- Targeted Artifact Searching: Evaluating the efficiency of finding specific evidence relevant to a case [33].
- Error Rate Calculation: Error rates were quantitatively calculated by comparing the artifacts acquired by each tool against known control references [33].
- Key Finding: The study demonstrated that properly validated open-source tools can produce reliable and repeatable results with verifiable integrity, achieving error rates comparable to commercial counterparts [33]. This finding is critical for resource-constrained organizations, as it democratizes access to high-quality forensic capabilities.
Protocol for Collaborative Method Validation in Traditional Forensics
For accredited crime labs, a collaborative protocol offers a pathway to significant resource savings [78].
- Objective: To permit standardization and sharing of common methodology, increasing efficiency for conducting validations and their implementation [78].
- Phase 1: Pioneering Validation
- An initial FSSP develops and performs a full validation of a new method, technology, or kit.
- This FSSP publishes the complete validation data in a recognized peer-reviewed journal, making it available for community scrutiny [78].
- Phase 2: Abbreviated Verification
- A second FSSP wishing to adopt the exact same method reviews and accepts the original published data and findings.
- The second FSSP then conducts a verification, a much shorter process that confirms the method works as expected in their laboratory environment, adhering strictly to the parameters in the published work [78].
- Business Case: This model demonstrates significant cost savings calculated on salary, sample, and opportunity cost bases, as it eliminates vast amounts of duplicate method development work [78].
Workflow Visualization for Validation Protocols
The logical relationships and workflows of the validation protocols discussed can be visualized to enhance understanding and implementation. The diagrams below, generated using Graphviz DOT language, illustrate the core processes.
Digital Forensic Tool Validation Workflow
Diagram Title: Digital Forensic Tool Validation
Collaborative Forensic Validation Model
Diagram Title: Collaborative Forensic Validation Model
The Scientist's Toolkit: Essential Research Reagents & Materials
The following table details key solutions and materials essential for conducting the validation experiments described in this guide.
Table 2: Essential Research Reagent Solutions for Forensic Validation
| Item Name | Function in Validation Protocol |
|---|---|
| Controlled Testing Workstations | Provides a consistent, reproducible hardware environment for conducting comparative tool analyses in digital forensics [33]. |
| Reference Data Sets & Images | Serves as the ground-truth control for calculating error rates in digital tool testing and for verifying tool outputs [33] [1]. |
| Commercial Forensic Software (e.g., FTK, Cellebrite) | Acts as the benchmark against which the performance and output of open-source or new tools are compared [33] [1]. |
| Open-Source Forensic Tools (e.g., Autopsy) | The subject of validation studies; provides a cost-effective alternative that requires rigorous testing to prove legal reliability [33]. |
| Hash Value Calculators (e.g., MD5, SHA-256) | Critical for tool and method validation in digital forensics; confirms data integrity before and after imaging, ensuring evidence is unaltered [1]. |
| Rapid DNA Kits & Platforms | In traditional forensics, these are the subjects of new validation protocols under updated FBI QAS, requiring clear implementation plans [77]. |
| Synthetic Biological Data | Enables the validation of computational methods and findings by mimicking real-world experimental data, useful in genomics and microbiome studies [79]. |
The optimization of resources and workflows for validation protocols is not merely an operational efficiency goal but a fundamental requirement for scientific and legal integrity. As demonstrated, digital and traditional forensic disciplines, while facing distinct challenges, converge on the universal need for rigorous, transparent, and reproducible validation. The emergence of collaborative models in traditional forensics and experimentally robust frameworks for open-source digital tools provides a clear path forward for resource-constrained organizations [33] [78].
Looking ahead, validation protocols must evolve to address the complexities introduced by Artificial Intelligence, deepfake media, and expansive cloud ecosystems [32] [1]. By adopting and refining the structured approaches and comparative insights outlined in this guide, researchers and forensic professionals can ensure their methods remain not only efficient but also scientifically sound and legally admissible in an increasingly complex technological landscape.
A Rigorous Comparative Framework: Digital vs. Traditional Forensics
The stability of evidence—its ability to remain unchanged and authentic from crime scene to courtroom—forms the cornerstone of reliable forensic science. This comparative guide examines the fundamental dichotomy between physical evidence, characterized by its traditional permanence, and digital evidence, defined by its inherent volatility. Within modern forensic science, this comparison is crucial for developing robust validation frameworks that ensure the integrity of both evidence types amid evolving technological challenges. Where a fingerprint on a surface or a bullet fragment can persist physically unchanged for years, a digital memory fragment in a smartphone or cloud server can be permanently altered or erased with a single command or system update [9] [32]. This guide objectively compares the performance characteristics of these evidence domains through structured experimental data, detailed methodologies, and analytical visualizations tailored for forensic researchers and development professionals.
Core Stability Characteristics: A Comparative Analysis
The inherent properties of physical and digital evidence create fundamentally different preservation challenges and requirements for forensic validation.
Table 1: Fundamental Characteristics of Evidence Types
| Characteristic | Physical Evidence | Digital Evidence |
|---|---|---|
| Persistence | Inherently stable under controlled conditions; degrades predictably [80] | Inherently volatile; requires active preservation [9] [32] |
| Authentication Method | Chemical analysis, physical comparison, microscopy [80] [5] | Cryptographic hashing (e.g., MD5, SHA-1) [1] |
| Primary Risks | Environmental degradation, contamination, chain-of-custody breaks [80] | Bit rot, tampering, encryption, anti-forensic techniques [4] [32] |
| Replication Fidelity | Potentially lossy (casts, photographs); original is unique [80] | Perfect, bit-for-bit copies possible without original degradation [9] [1] |
| Scale & Volume | Physically limited by crime scene; typically manageable [80] | Virtually unlimited; petabyte-scale in cloud environments [63] [4] |
Digital evidence's volatility stems from its architectural dependence on layered systems. Unlike a physical document, a digital file relies on hardware integrity, filesystem structure, application software, and user interpretation to maintain meaning and accessibility. This complex dependency chain introduces multiple failure points that physical evidence avoids [9] [32]. Furthermore, the anti-forensic techniques increasingly employed by cybercriminals—including data wiping, encryption, and steganography—actively exploit this volatility to obstruct investigations, presenting challenges rarely encountered with physical evidence [4].
Experimental Validation: Methodologies and Quantitative Results
Experimental Protocol for Digital Evidence Reliability
Recent research provides a structured methodology for validating digital evidence stability and tool performance, employing rigorous comparative testing between commercial and open-source forensic tools [9].
Methodology Summary:
- Controlled Testing Environment: Utilized isolated workstations with standardized hardware configurations to eliminate external variables [9].
- Tool Selection: Compared commercial tools (FTK, Forensic MagiCube) against open-source alternatives (Autopsy, ProDiscover Basic) [9].
- Test Scenarios: Conducted three distinct evidentiary scenarios:
- Preservation and collection of original data
- Recovery of deleted files through data carving
- Targeted artifact searching in case-specific scenarios [9]
- Validation Metrics: Each experiment was performed in triplicate to establish repeatability metrics. Error rates were calculated by comparing acquired artifacts with control references using hash verification and manual review [9].
- Integrity Verification: Employed hash-based verification (MD5, SHA-256) throughout evidence handling to detect alterations, maintaining chain-of-custody documentation [9] [1].
Quantitative Performance Comparison
The experimental results demonstrate that with proper validation, digital evidence can achieve reliability comparable to traditional forensic analyses.
Table 2: Digital Forensic Tool Performance Comparison [9]
| Tool Category | Tool Name | Data Preservation Accuracy | File Recovery Success Rate | Artifact Search Precision | Average Error Rate |
|---|---|---|---|---|---|
| Commercial | FTK | 100% | 98.5% | 99.2% | 0.8% |
| Commercial | Forensic MagiCube | 100% | 97.8% | 98.7% | 1.1% |
| Open-Source | Autopsy | 100% | 96.3% | 97.5% | 1.9% |
| Open-Source | ProDiscover Basic | 100% | 95.7% | 96.8% | 2.3% |
The experimental data reveals that properly validated open-source tools consistently produce reliable and repeatable results with verifiable integrity comparable to commercial counterparts [9]. This demonstrates that procedural validation frameworks can effectively mitigate digital evidence's inherent volatility, establishing scientific reliability that meets legal admissibility standards like the Daubert Standard [9] [1].
Digital Evidence Integrity Verification Workflow
The Scientist's Toolkit: Essential Research Reagents and Solutions
Forensic validation relies on specialized tools and standards to ensure evidence stability and analytical reliability across both physical and digital domains.
Table 3: Essential Forensic Validation Tools and Reagents
| Tool/Reagent | Primary Function | Application Context |
|---|---|---|
| Hash Algorithms (MD5, SHA-256) | Creates unique digital fingerprint to verify evidence integrity [1] | Digital Forensics |
| Forensic Imaging Tools | Creates bit-for-bit copies of digital evidence without altering original [9] | Digital Forensics |
| ISO/IEC 27037:2012 | International standard for identification, collection, acquisition/preservation of digital evidence [9] | Digital Forensics |
| Next Generation Sequencing (NGS) | Analyzes damaged/degraded DNA samples with high precision [5] | Physical Forensics |
| Carbon Dot Powders | Enhances fingerprint visualization through fluorescence under UV light [5] | Physical Forensics |
| Laboratory Information Management System (LIMS) | Tracks evidence handling chain-of-custody with barcode technology [80] | Both Domains |
| Vacuum Metal Deposition | Develops latent prints on challenging surfaces using silver/gold/zinc [80] | Physical Forensics |
| Automated Firearm Identification (IBIS) | Provides objective algorithmic comparison of ballistic evidence [5] | Physical Forensics |
The tools and standards listed in Table 3 represent critical components for maintaining evidence stability within their respective domains. For digital evidence, the focus is on mathematical verification through hashing and standardized acquisition protocols [9] [1]. For physical evidence, advancement lies in enhanced detection sensitivity through chemical and technological innovations [80] [5]. Cross-domain tools like LIMS provide unified chain-of-custody tracking that reinforces evidentiary integrity regardless of evidence type [80].
Validation Frameworks: Meeting Legal and Scientific Standards
The Daubert Standard Applied to Digital Forensics
The Daubert Standard provides a crucial legal framework for assessing forensic methodology reliability, with specific implications for digital evidence validation [9] [1].
Key Daubert Factors for Digital Evidence:
- Testability: Digital forensic methods must be testable and capable of independent verification through controlled experiments [9].
- Peer Review: Methods must undergo peer review and publication, enabling scrutiny by the scientific community [9] [1].
- Error Rates: Established or potential error rates must be known and disclosed, as demonstrated in Table 2 [9].
- General Acceptance: Methods must be widely accepted by the relevant scientific community, facilitated by standards like ISO/IEC 27037 [9].
Daubert Standard Requirements for Digital Evidence
Three-Phase Framework for Digital Evidence Validation
Recent research has validated an enhanced three-phase framework that ensures digital evidence meets Daubert requirements while addressing its inherent volatility [9]:
- Basic Forensic Processes: Implementation of standardized procedures for identification, collection, and preservation of digital evidence using forensically sound methods [9].
- Result Validation: Comparative analysis using multiple tools, hash verification, and error rate calculation to establish reliability metrics [9] [1].
- Digital Forensic Readiness: Organizational preparation through policy development and tool validation to effectively deploy forensic capabilities when needed [9].
This framework directly counters digital volatility through structured validation, establishing scientific rigor comparable to traditional forensic disciplines. The experimental protocol detailed in Section 3.1 operationalizes this framework, generating the quantitative performance data essential for demonstrating reliability under Daubert scrutiny [9].
Emerging Challenges and Future Directions
The stability of both physical and digital evidence faces new challenges from technological advancements that demand continuous evolution of validation frameworks.
Digital Evidence Volatility Amplifiers
- Cloud Storage & Distributed Data: Evidence fragmentation across geographically dispersed servers with differing jurisdictional laws complicates preservation and acquisition [63] [4].
- Anti-Forensic Techniques: Widespread availability of encryption, data wiping, and steganography tools enables intentional evidence obfuscation [4].
- AI-Generated Content: Deepfake technology creates convincing synthetic media that challenges evidence authenticity verification [63] [32].
- IoT Proliferation: Data volume from interconnected devices creates scale challenges while device security features impede acquisition [63] [4].
Physical Evidence Modern Challenges
- Privately Made Firearms: "Ghost guns" without serial numbers challenge traditional ballistic identification processes [80].
- Nanotechnology Traces: Minute evidence quantities require increasingly sensitive detection methods and contamination controls [5].
- Digital-to-Physical Convergence: Evidence like 3D-printed objects blurs traditional categorization boundaries [5].
These emerging challenges highlight the ongoing need for cross-disciplinary validation frameworks that can adapt to technological evolution while maintaining the evidentiary standards required for legal proceedings. The convergence of forensic science with artificial intelligence and automation presents promising solutions for managing increasing evidence complexity and volume across both domains [4] [32] [5].
This comparison demonstrates that while physical evidence maintains advantages in inherent permanence, digital evidence—despite its volatility—can achieve comparable reliability through rigorous validation frameworks. The experimental data confirms that properly validated digital forensic tools produce consistent, repeatable results with known error rates, meeting legal admissibility standards. The critical distinction lies not in ultimate reliability but in methodological approach: where physical evidence stability derives from material properties, digital evidence stability must be imposed through mathematical verification and standardized protocols. Future forensic research should prioritize cross-domain validation frameworks that leverage advancements in AI and automation while maintaining the rigorous scientific standards exemplified by the Daubert criteria. Such integrated approaches will ensure evidentiary integrity across the increasingly blurred boundary between physical and digital investigative domains.
The digital forensics field is characterized by a relentless and rapid software update cycle, a direct response to the escalating pace of technological change and cybercrime. From 2023 to 2025, a notable increase in cybercriminal activities has solidified the role of digital forensics as an essential discipline in legal proceedings [33]. The global digital forensics market is projected to reach $18.2 billion by 2030, growing at a compound annual growth rate of 12.2% [63]. This growth is propelled by the proliferation of digital devices, cloud computing, artificial intelligence (AI), and the Internet of Things (IoT)—technologies that have simultaneously created new vectors for criminal activity and necessitated advanced forensic capabilities [63].
Unlike traditional forensics, which often relies on established physical evidence techniques, digital forensics must contend with an ever-shifting landscape of operating systems, applications, encryption standards, and storage technologies. The distributed nature of cloud storage, where over 60% of newly generated data now resides, compels investigators to adapt to cross-platform and cross-jurisdictional data tracing [63]. Furthermore, the tens of billions of IoT devices expected worldwide by 2025 create both new evidence sources and complex analytical challenges [63]. These technical demands, coupled with the projected $13 trillion global cost of cybercrime, make the rapid evolution of digital forensic tools not merely beneficial but indispensable for effective investigations [26].
Comparative Analysis: Digital Forensics vs. Traditional Forensics
The fundamental differences between digital and traditional forensic sciences dictate distinct approaches to tool validation and update cycles. Understanding these contrasts is crucial for developing appropriate validation frameworks.
Table 1: Comparison of Digital and Traditional Forensic Methodologies
| Aspect | Digital Forensics | Traditional Forensics (e.g., Fingerprints, Ballistics) |
|---|---|---|
| Evidence Nature | Digital; volatile, easily modified | Physical; relatively stable |
| Update Cycle | Rapid (months); responds to new tech/OS | Slow (years); methods remain valid for decades |
| Primary Challenge | Technology obsolescence, data volume & encryption | Consistency, subjective interpretation, trace contamination |
| Standardization | Evolving standards (e.g., ISO/IEC 27037) | Well-established, long-standing protocols |
| Automation | High; reliant on software tools for data processing | Variable; often requires manual expert analysis |
Traditional forensic methods, such as fingerprint analysis and ballistics, have been the backbone of criminal investigations for decades. These techniques rely on manual examination and physical evidence analysis, requiring a high degree of skill and subjective interpretation [44]. While effective, these processes can be time-consuming and depend heavily on the examiner's expertise. The underlying technologies—fingerprint powders, comparison microscopes—evolve gradually, with core principles remaining valid for years.
In contrast, modern digital forensics, including digital forensic engineering and cell phone data recovery, leverages digital tools and sophisticated software to analyze data from computers, smartphones, and cloud platforms [44]. The shift towards digitalization and automation enables faster processing and a wider scope of analysis but also forces a continuous tooling update cycle. This creates a critical divergence: while a traditional forensics lab may validate a method once every several years, a digital forensics lab must validate its core tools with nearly every major operating system update or new app release.
Validation Frameworks: Ensuring Legal Admissibility Amidst Change
The rapid evolution of tools presents a significant challenge for legal admissibility. Courts historically favor commercially validated solutions due to established reliability and support, often creating financial barriers for resource-constrained organizations [33]. The Daubert Standard, a legal precedent in the United States, sets the criteria for the admissibility of scientific evidence, providing a critical framework for validating digital forensic tools despite their rapid update cycles [33] [34]. The standard evaluates:
- Testability: Whether the methods used to produce evidence can be and have been tested.
- Peer Review: Whether the methods have been subject to peer review and publication.
- Error Rates: The known or potential error rate of the techniques.
- General Acceptance: Whether the methods are widely accepted by the relevant scientific community [33].
A 2025 study by Ismail and Ariffin directly addressed the admissibility of evidence from open-source digital forensic tools, which often update more frequently than commercial tools. Through a rigorous experimental methodology, they demonstrated that properly validated open-source tools can produce reliable and repeatable results comparable to commercial counterparts like FTK [33] [34]. Their enhanced three-phase framework integrates basic forensic processes, result validation, and digital forensic readiness to meet Daubert requirements, providing a template for practitioners to ensure methodological soundness even with frequent tool changes [33].
Experimental Protocol for Tool Validation
The validation protocol from Ismail and Ariffin's study offers a replicable model for testing digital forensic tools, crucial for maintaining confidence during rapid updates [33].
Table 2: Key Phases of the Digital Forensic Tool Validation Framework
| Phase | Key Activities | Outputs/Deliverables |
|---|---|---|
| 1. Basic Forensic Process | Evidence identification, preservation, collection, and examination using the tool. | Forensic image, chain of custody documentation, extracted artifacts. |
| 2. Result Validation | Comparative analysis against a control reference; triplicate testing to establish repeatability; error rate calculation. | Repeatability metrics, quantified error rates, validation report. |
| 3. Digital Forensic Readiness | Ensuring compliance with legal standards (e.g., Daubert); documentation for court presentation. | Court-admissible report, documented methodology aligned with legal requirements. |
Methodology Overview: The experiment utilized controlled testing environments with two Windows-based workstations. A comparative analysis was conducted between commercial tools (FTK, Forensic MagiCube) and open-source alternatives (Autopsy, ProDiscover Basic) across three test scenarios [33]:
- Preservation and collection of original data.
- Recovery of deleted files through data carving.
- Targeted artifact searching in case-specific scenarios.
To ensure reliability, each experiment was performed in triplicate to establish repeatability metrics. Error rates were calculated by comparing the number of acquired artifacts against a control reference, providing a quantitative measure of tool accuracy [33]. This rigorous approach, aligned with NIST Computer Forensics Tool Testing standards, ensures that even rapidly updated tools can be independently verified for forensic soundness.
Diagram 1: Digital Forensic Tool Validation Workflow
Quantitative Tool Performance Comparison
The following data synthesizes performance metrics for leading digital forensic tools, highlighting their capabilities in handling diverse evidentiary sources.
Table 3: 2025 Digital Forensic Tool Performance Comparison
| Tool Name | Primary Use Case | Standout Feature | Supported Platforms | Relative Performance | Pricing Estimate |
|---|---|---|---|---|---|
| Cellebrite UFED | Mobile forensics for law enforcement | Advanced app decryption (e.g., WhatsApp, Signal) | iOS, Android, Windows Mobile | High | Custom (Premium) |
| Magnet AXIOM | Unified investigations | Magnet.AI for automated content categorization | Windows, macOS, Linux, iOS, Android | High | Custom (Premium) |
| EnCase Forensic | Computer forensics | Deep file system analysis | Windows, macOS, Linux | High | Starts at $3,995 |
| FTK (Forensic Toolkit) | Large-scale investigations | Facial/object recognition | Windows, macOS, Linux | High (but resource-heavy) | $5,999–$11,500 |
| Autopsy | Budget-conscious teams, education | Open-source data carving | Windows, Linux, macOS | Moderate (slower on large datasets) | Free |
| X-Ways Forensics | Technical analysts | Lightweight disk cloning | Windows, Linux, macOS | High (efficient resource use) | Starts at $1,199 |
Experimental data from comparative studies shows that both commercial and open-source tools can achieve forensically sound results when properly validated. In tests of data carving and artifact searching, tools like Autopsy demonstrated comparable artifact recovery rates to commercial tools like FTK, though sometimes at the cost of processing speed, particularly with large datasets [33] [26]. The key differentiator often lies not in raw capability but in workflow integration, user interface, and support. For instance, Magnet AXIOM's unified workflow for mobile, computer, and cloud data can significantly improve investigation efficiency, while X-Ways Forensics is noted for its low system resource usage, making it suitable for older hardware [26].
The Impact of Artificial Intelligence and Automation
AI is becoming a transformative force in digital forensics, directly addressing the challenges posed by the rapid update cycle and big data. AI-based tools and methods (DFAI) are increasingly applied to increase investigator productivity by quickly sifting through large volumes of data and highlighting relevant information [3]. Machine learning algorithms excel at automated log filtering, anomaly detection, and deepfake audio detection, with accuracy rates for the latter reaching 92% [63].
However, the adoption of DFAI faces its own set of challenges within validation frameworks. The "black-box" nature of some complex AI models can undermine the transparency and interpretability required for court evidence [3] [63]. In response, there is a growing focus on incorporating Explainable AI (XAI) to improve the transparency of DFAI processes, offering a way to better understand and trust AI-generated evidence [3]. A practitioner-driven survey revealed that the primary barriers to DFAI adoption are insufficient validation processes and a lack of clear methods for presenting and explaining AI-generated evidence in court [3]. This highlights that the core principles of the Daubert standard remain relevant even as the tools themselves become more advanced.
The Scientist's Toolkit: Essential Digital Forensic Reagents
In digital forensics, "research reagents" equate to the software tools and hardware components that form the foundation of a forensic investigation.
Table 4: Essential Digital Forensic "Research Reagent Solutions"
| Tool/Resource | Category | Primary Function | Key Consideration for Validation |
|---|---|---|---|
| Hardware Write Blocker | Preservation | Prevents modification of original evidence media during imaging. | Must be tested regularly; configuration can affect functionality. |
| Magnet Acquire | Acquisition | Creates forensic images of hard drives and mobile devices. | Configure error response (e.g., to bad sectors) per lab SOP. |
| Magnet DumpIt / Magnet Response | Acquisition | Captures volatile Random Access Memory (RAM). | Process alters memory; two captures from same system will not hash the same. |
| Autopsy | Analysis & Examination | Open-source platform for file system timeline analysis and data carving. | Slower on large datasets; requires validation against other tools. |
| Magnet AXIOM / Cellebrite UFED | Analysis & Examination | Comprehensive suites for analyzing computer and mobile device data. | Regular updates are crucial to support new apps and OS versions. |
| Wireshark | Analysis & Examination | Open-source network protocol analyzer for deep packet inspection. | Requires significant network expertise for effective use and testimony. |
| DFAI (AI-based) Tools | Analysis & Examination | Automate data sifting, anomaly detection, and content categorization. | Black-box nature requires XAI and rigorous validation for court acceptance. |
Diagram 2: Drivers of the Rapid Digital Forensics Tool Update Cycle
The rapid update cycle of digital forensic software is an inevitable and necessary response to a dynamic technological ecosystem. This presents a fundamental challenge for validation frameworks designed to ensure the reliability and legal admissibility of digital evidence. The solution lies not in resisting change but in embracing rigorous, standardized, and repeatable validation methodologies—such as the enhanced framework satisfying the Daubert Standard—that can keep pace with tool evolution. By applying consistent experimental protocols, leveraging both commercial and open-source tools for verification, and proactively addressing the challenges posed by emerging technologies like AI and cloud computing, the digital forensics field can maintain the scientific rigor required to deliver justice in the digital age.
The evolution of forensic science from traditional physical evidence to digital domains presents a fundamental challenge: developing validation frameworks that are equally rigorous yet adaptable to vastly different data scales. In traditional forensics, biometric recognition, such as fingerprint analysis, involves the automated recognition of individuals based on their biological characteristics [81]. This field, rooted in law enforcement, primarily deals with data volumes in the kilobyte (KB) range, focusing on the distinctiveness of features like minutiae points in a fingerprint ridge pattern [81]. In contrast, digital forensics deals with evidence sourced from multi-terabyte drives, requiring a completely different set of tools and methodologies for identification, collection, preservation, and analysis [33]. This guide objectively compares the data volumes, experimental protocols, and validation requirements across these two forensic disciplines, framing the discussion within the critical need for robust, standardized validation frameworks that ensure the legal admissibility of evidence, regardless of its source [33].
Quantitative Data Comparison: Fingerprint vs. Multi-Terabyte Drive
The difference in data volume between a single fingerprint and a multi-terabyte drive is not merely linear; it represents a shift in the very nature of the evidence and the analytical techniques required to process it. The table below summarizes the core quantitative differences.
Table 1: Data Volume and Characteristic Comparison
| Characteristic | Fingerprint (Traditional Forensics) | Multi-Terabyte Drive (Digital Forensics) |
|---|---|---|
| Typical Data Volume | Kilobytes (KB) | Terabytes (TB); 1 TB = 1,024,000,000 KB |
| Data Structure | Structured biological feature set (e.g., minutiae) [81] | Unstructured, semi-structured, and structured data (emails, documents, system files, databases) [82] |
| Primary Features | Minutiae points (ridge endings, bifurcations), ridge patterns [81] | File signatures, metadata, file system artifacts, network logs, registry entries [33] |
| Analysis Goal | Individualization; associating evidence with a single source [81] | Evidence discovery; linking files, activities, and timelines to entities or events [33] |
| Common Evidence Form | Latent print (fingermark) lifted from a crime scene [81] | Forensic image (bit-for-bit copy) of a storage device [33] |
Experimental Protocols for Evidence Analysis
The methodologies for analyzing forensic evidence are tailored to the data type and volume. The protocols below detail standardized approaches for both fingerprint examination and digital evidence acquisition.
Protocol 1: Categorical and Probabilistic Fingerprint Comparison
This protocol is based on methodologies used to evaluate how fingerprint examiners express conclusions and how these conclusions are perceived in legal contexts [83].
- Evidence Collection: A latent fingerprint (fingermark) is recovered from a crime scene using standard forensic techniques (e.g., powder, chemical development). A set of known prints is collected from a suspect via live-scan or ink [81].
- Analysis & Feature Extraction: A qualified fingerprint examiner analyzes the latent print to determine its suitability for comparison. If suitable, the examiner identifies and marks distinguishing features (minutiae points) such as ridge endings and bifurcations [81] [83].
- Comparison: The examiner systematically compares the marked features of the latent print against the known prints. This involves assessing the level of detail, correspondence, and any discrepancies.
- Conclusion Formulation: The examiner reaches one of three types of conclusions [83]:
- Categorical Conclusion: A definitive statement of identification or exclusion (e.g., "the latent print originates from the suspect").
- Strong Probabilistic Conclusion: A statement expressing a very high probability of a match, often using statistical models of similarity.
- Weak Probabilistic Conclusion: A statement expressing a lower probability or inconclusive finding.
- Validation: The conclusion is peer-reviewed by another independent examiner. The methodology is subject to scrutiny based on established professional standards and, in legal contexts, the Daubert Standard, which considers testability, error rates, and peer review [33] [83].
Protocol 2: Digital Evidence Acquisition with Open-Source Tools
This protocol, derived from comparative studies on digital forensic tools, outlines the process for acquiring evidence from a multi-terabyte drive using open-source tools, ensuring the integrity and admissibility of the data [33].
- Identification & Hardware Write-Blocking: The target multi-terabyte drive is identified. A hardware write-blocker is connected to the drive to prevent any modification of the original evidence during the acquisition process.
- Forensic Imaging: Using an open-source tool like Autopsy or ProDiscover Basic, a forensic image (bit-for-bit copy) of the drive is created. This process includes:
- Data Processing & Analysis: The forensic image is loaded into the analysis platform. The tool performs:
- Validation & Repeatability: To ensure reliability, the experiment is performed in triplicate. The error rate is calculated by comparing the artifacts acquired by the open-source tool (e.g., Autopsy) against a control reference and the results from established commercial tools (e.g., FTK, Forensic MagiCube) [33].
Visualization of Forensic Validation Pathways
The following diagram illustrates the logical relationship and convergence of validation principles between traditional and digital forensic evidence analysis, leading to the common goal of legal admissibility.
Diagram 1: Forensic evidence validation pathway for legal admissibility.
The Scientist's Toolkit: Key Research Reagent Solutions
The following table details essential tools and materials required for conducting experiments in both traditional and digital forensic domains.
Table 2: Essential Research Reagent Solutions for Forensic Analysis
| Tool / Material | Function / Purpose | Application Domain |
|---|---|---|
| Automated Fingerprint ID System (AFIS) | Database system for storing, searching, and retrieving fingerprint records based on minutiae patterns [81]. | Traditional Forensics |
| Fingerprint Minutiae Templates | Digital representation (feature set) of a fingerprint's unique ridge characteristics, used for automated comparison [81]. | Traditional Forensics |
| Open-Source Forensic Suite (Autopsy) | A digital forensic platform for analyzing disk images, file systems, and mobile devices; provides data carving and artifact search [33]. | Digital Forensics |
| Hardware Write-Blocker | A physical device that prevents any write commands from being sent to a storage drive, ensuring evidence integrity during acquisition [33]. | Digital Forensics |
| Distributed Processing Framework (Apache Spark) | An open-source, distributed computing system for rapidly processing large datasets across computing clusters [82]. | Digital Forensics (Big Data) |
| Cloud Data Warehousing (Google BigQuery) | A scalable, cloud-based data warehouse for running fast SQL queries on massive structured datasets [82]. | Digital Forensics (Big Data) |
| Columnar Storage Format (Parquet) | A highly efficient, columnar storage file format optimized for compression and query performance in big data frameworks [82]. | Digital Forensics (Big Data) |
| Daubert Standard Criteria | A legal framework used to assess the admissibility of expert scientific testimony, focusing on testability, error rates, and peer review [33]. | Cross-Domain Validation |
In forensic science, the validity and reliability of evidence presented in judicial systems are paramount. This article explores the critical tension between standardized protocols and evolving best practices within the context of validation frameworks, contrasting the established methodologies of traditional forensics with the dynamic challenges of digital forensics. Validation frameworks serve as the foundational bedrock ensuring that analytical methods are scientifically sound, reproducible, and legally defensible. In traditional forensics, this has often been achieved through rigorous, prescriptive standards. However, the digital realm, characterized by rapid technological evolution and a constantly shifting threat landscape, presents a unique challenge, often necessitating more agile and adaptive best practices. This comparison does not seek to crown one approach superior but to objectively analyze their performance, strengths, and limitations, providing researchers and development professionals with the data to build more resilient validation systems. The core thesis is that an effective modern validation framework must intelligently hybridize the reliability of standardization with the adaptability of evolving best practices to keep pace with both scientific progress and the demands of justice.
Conceptual Frameworks: Definitions and Key Characteristics
Understanding the fundamental differences between standardized protocols and evolving best practices is crucial for appreciating their respective roles in validation.
Standardized Protocols
Standardized protocols are formally established, documented sets of rules, guidelines, or specifications designed to ensure consistency, reliability, and reproducibility in processes and outcomes [84]. They represent a process of harmonizing practices across time and space through the generation and implementation of agreed-upon rules [84]. In a scientific context, they can be categorized into:
- Design Standards: Which determine the specifics of tools and technical systems.
- Terminology Standards: Which enable expert communication.
- Performance Standards: Which set practice goals.
- Procedural Standards: Which specify steps in a given process [84].
Their primary strength lies in creating a stable, predictable foundation for research and evidential analysis, reducing harmful variation and supporting equitable application [84].
Evolving Best Practices
Evolving best practices, in contrast, are methodologies or techniques that represent the most effective and current approach based on accumulated experience and emerging evidence. They are dynamic by nature, subject to continuous refinement and improvement. A significant criticism of the term "best practice" is that it can be subjective and may exist "in the rear view mirror," meaning that by the time an organization adopts them, business conditions may have already changed, rendering them less effective [85]. Some analysts therefore suggest the term "value-added practice" (VAP) as a more accurate descriptor, placing the focus on the continuous delivery of value rather than a static "best" state [85]. This concept is particularly vital in digital forensics, where new hardware, software, and attack vectors constantly emerge.
The Standardization-Customization Spectrum
The relationship between these two concepts is not a binary opposition but a spectrum. Research in healthcare delivery succinctly captures this inherent tension, noting that too much customization can be chaotic and result in suboptimal outcomes, while excessive standardization can disempower professionals and prevent adaptation to unique circumstances [86]. The challenge for any scientific field, including forensics, is to achieve the right balance, leveraging the efficiencies and reliability of standardization while preserving the flexibility required for innovation and context-specific application [86].
Comparative Analysis: Performance Metrics and Experimental Data
A direct comparison of standardized protocols and evolving best practices reveals a nuanced performance landscape, where the optimal choice is highly context-dependent. The table below summarizes key comparative metrics, synthesized from cross-domain research.
Table 1: Performance Comparison of Standardized Protocols vs. Evolving Best Practices
| Performance Metric | Standardized Protocols | Evolving Best Practices |
|---|---|---|
| Consistency & Reproducibility | High. Ensures uniform execution and outcomes across different operators and environments [87]. | Variable. Can lead to inconsistencies if communication and training are not widespread [88]. |
| Error Susceptibility | Low. Designed to minimize human error and ambiguity through clear, repeatable steps [87]. | Moderate. More reliant on individual expertise and judgment, introducing potential for variation. |
| Adaptability to Novel Situations | Low. Often too simplistic to account for infrequent, atypical, or complex, multi-faceted scenarios [84]. | High. Designed to be flexible and adapt to new evidence, technologies, and unique challenges. |
| Implementation Speed | Slow. Requires formal development, agreement, and dissemination processes. | Rapid. Can be proposed and adopted organically by practitioner communities as needed. |
| Cost of Maintenance | High. Requires formal reviews and updates, often involving multiple stakeholders. | Low. Evolves continuously without the overhead of formal revision cycles. |
| Support for Innovation | Can stifle creativity if applied rigidly, forcing diverse situations into a standardized straightjacket [87]. | High. Encourages experimentation and the development of novel solutions to emerging problems. |
| Data Harmonization | Excellent. Essential for collaborative research and pooling data from multiple sources [89]. | Poor. Lack of standardization can lead to data fragmentation and make cross-study comparisons difficult. |
A critical quantitative insight comes from biomedical research, which sheds light on the real-world challenges of protocol adherence. A systematic review found frequent and prevalent inconsistencies between prospectively registered study protocols and final published reports [90]. The level of inconsistency ranged dramatically, from 14% to 100% for outcome reporting and from 12% to 100% for subgroup reporting [90]. This highlights a fundamental challenge: even when standards exist, they could not be followed consistently, often due to the complex, non-standard nature of real-world research and analysis.
Experimental Protocols for Validation
To empirically validate methods within a framework, specific experimental protocols must be deployed. The following are detailed methodologies relevant to assessing both standardized and evolving approaches.
Protocol-Report Consistency Audit
This methodology is designed to quantify adherence to pre-established standards, revealing the practical challenges of standardization.
- Objective: To measure the frequency and nature of inconsistencies between a pre-defined, standardized study protocol and the final analytical report or publication.
- Methodology:
- Protocol Registration: A detailed study protocol is prospectively registered in a dedicated repository (e.g., a forensic science registry). This protocol must explicitly define primary and secondary outcomes, subgroup analyses, statistical methods, and inclusion/exclusion criteria.
- Full Report Collection: The final reports or publications generated from the protocol are collected.
- Independent Comparison: Two or more independent reviewers compare the full reports against the registered protocol using a standardized data extraction form.
- Data Extraction & Categorization: Inconsistencies are identified and categorized (e.g., outcome addition, omission, change in statistical analysis, altered inclusion criteria).
- Data Analysis: The level of inconsistency is calculated as the percentage of studies with at least one discrepancy for each category. Factors associated with inconsistency (e.g., significance of results, sponsorship) can be analyzed using regression models [90].
Data Harmonization for Collaborative Research
This protocol is essential for large-scale validation studies that pool data from multiple sources, which may have used different standards or best practices.
- Objective: To integrate extant (legacy) data collected using different measures into a Common Data Model (CDM) for unified analysis.
- Methodology (as implemented in the ECHO-wide Cohort):
- CDM Definition: A collaborative working group defines the essential and recommended data elements for the research platform.
- Cohort Measurement Identification: Each contributing cohort inventories the measures they used for each data element in their extant data using a tool like the Cohort Measurement Identification Tool (CMIT) [89].
- Harmonization Planning: For each data element, the team identifies cohorts that used the same or psychometrically linked measures. For cohorts with unique measures, a decision is made on whether and how to harmonize the data (e.g., using linking tables, cross-walks, or statistical calibration).
- Data Transformation: A "roadmap" is created to convert existing data from cohort-specific systems into the format consistent with the CDM, using specialized data transformation tools [89].
- Outcome: Creates a powerful, pooled dataset that leverages the strength of multiple studies while transparently accounting for methodological variations.
Agile Validation Cycle for Digital Tools
This protocol outlines an iterative, best-practice approach for validating digital forensic tools in a rapidly changing environment.
- Objective: To establish a continuous validation process for a digital forensic software tool against evolving data formats and security features.
- Methodology:
- Baseline Establishment: The tool is validated against a standardized set of reference data images and known outputs (a "golden corpus") following a strict procedural standard.
- Continuous Monitoring: A system is established to monitor for new software updates, file formats, and encryption standards relevant to the tool's function.
- Rapid Cycle Testing: Upon detection of a relevant change, a targeted validation test is designed and executed. This test focuses specifically on the new feature or threat.
- Community Dissemination: Results of the rapid cycle test are quickly shared with the user community as an evolving best practice advisory, which may include workarounds or preliminary findings.
- Protocol Integration: Successful and critical findings from the rapid cycle are formally incorporated into the next version of the standardized protocol for the tool.
- Outcome: Combines the certainty of baseline standardization with the agility of continuous, practice-based validation.
Visualization of Workflows and Logical Relationships
The following diagrams, generated using Graphviz DOT language, illustrate the core workflows and decision processes involved in the validation frameworks discussed.
Protocol-Report Consistency Audit Workflow
Standardization vs. Customization Decision Logic
The Scientist's Toolkit: Essential Research Reagent Solutions
The following table details key materials and solutions essential for conducting rigorous experiments in method validation, applicable to both forensic domains.
Table 2: Key Research Reagent Solutions for Validation Experiments
| Item Name | Function in Validation | Specific Application Example |
|---|---|---|
| Reference Standard Materials (RSMs) | Provides a ground-truth benchmark with certified properties to calibrate instruments and validate analytical methods. | Used in traditional forensics to validate the analysis of controlled substances or DNA quantification assays. |
| Certified Reference Material (CRM) | A specific type of RSM characterized by a metrologically valid procedure. Used for quality control and method verification. | Digital forensics uses CRMs in the form of standardized forensic disk images (e.g., from NIST) to validate imaging and analysis tools. |
| Common Data Model (CDM) | A standardized data structure that allows for the harmonization of data from disparate sources, enabling collaborative research. | Used to pool and validate analytical data from multiple forensic labs studying the same method, despite using different equipment [89]. |
| Standard Operating Procedure (SOP) | A set of step-by-step instructions compiled by an organization to help workers carry out complex routine operations. | Ensures that a validation experiment is performed consistently and reproducibly by different scientists in a lab [88]. |
| Cohort Measurement Identification Tool (CMIT) | A tool to inventory and track the different measures and instruments used by contributing cohorts in a collaborative study. | Facilitates the data harmonization process by mapping existing data to a CDM, crucial for multi-lab validation studies [89]. |
| "Golden Corpus" Dataset | A curated collection of data with known, verified properties and expected outcomes used to test and validate analytical tools. | In digital forensics, a set of mobile device images with pre-placed, documented data to test the recovery accuracy of a new tool. |
Synthesizing a Unified Validation Philosophy for Cross-Disciplinary Excellence
The fields of digital and traditional forensics are undergoing rapid, parallel evolution. Traditional forensics, once confined to the analysis of physical evidence like fingerprints and bloodstains, now grapples with the integration of advanced technologies such as Next-Generation DNA Sequencing (NGS) and virtual autopsies [6]. Concurrently, digital forensics has expanded from analyzing single computers to investigating a complex ecosystem of mobile devices, cloud platforms, and Internet of Things (IoT) devices, all while combating threats from sophisticated AI-generated deepfakes [45] [32]. This technological divergence has created a critical methodological gap: a lack of a common philosophical foundation for validating evidence across these disciplines. As digital evidence becomes ubiquitous in legal contexts, from criminal cases to corporate investigations, the need for a synthesized validation philosophy is paramount to ensure evidence remains reliable, admissible, and comprehensible to all stakeholders in the justice system [44] [91]. This article proposes a unified framework for cross-disciplinary validation, designed to meet the demands of modern, complex investigations that increasingly blur the lines between the physical and digital worlds.
Comparative Analysis: Traditional and Digital Forensic Methodologies
A side-by-side examination of core methodologies reveals fundamental differences in processes, sources of evidence, and validation criteria, highlighting the challenges and opportunities for philosophical unification.
Table 1: Comparison of Core Methodologies in Traditional and Digital Forensics
| Aspect | Traditional Forensics | Digital Forensics |
|---|---|---|
| Primary Evidence | Physical objects (fingerprints, DNA, firearms) [44] | Digital data (files, logs, metadata) [45] |
| Core Techniques | Fingerprint analysis, bloodstain pattern analysis, ballistics, handwriting analysis [44] | Mobile & cloud forensics, data recovery, deepfake detection, blockchain analysis [45] [32] |
| Validation Focus | Chain of custody, reproducibility of analysis, expert testimony [44] | Data integrity (hash verification), authenticity, audit trails, tool validation [45] |
| Key Challenges | Subjectivity in analysis, sample degradation, limited sample quantity [44] | Data volume & encryption, ephemeral data, anti-forensics techniques, cloud distribution [45] [32] |
The table illustrates that while traditional methods often rely on the manual expertise of the analyst and the physical integrity of evidence, digital forensics is characterized by its fight against data volume and its dependence on automated tools for processing and analysis [45] [44]. A unifying philosophy must therefore bridge the gap between human-centric validation and tool-driven verification.
Table 2: Validation Metrics and Experimental Data Comparison
| Validation Metric | Traditional Forensics (Example: NGS DNA Sequencing) | Digital Forensics (Example: AI-Driven Data Triage) |
|---|---|---|
| Accuracy Rate | High identification from trace/mixed samples; details phenotype traits [6] | Flags relevant data & anomalies; performance varies by algorithm & training data [32] |
| Processing Speed | Hours for full genome sequencing [6] | Real-time to minutes for large datasets [6] [32] |
| Key Output | Detailed genetic information for identification [6] | Prioritized evidence, identified patterns, predictive leads [32] |
| Error Analysis | Contamination risks, interpretation of complex mixtures [6] | False positives/negatives, algorithmic bias, data fragmentation issues [32] |
| Standardization | Established laboratory protocols and controls [6] | Emerging standards for tool output and AI model validation [32] |
Quantitative comparison shows that modern techniques in both fields offer significant speed and capability advantages. However, they also introduce new complexities in error analysis, with digital forensics facing particular challenges regarding algorithmic transparency and bias [32]. A robust validation framework must account for these distinct yet equally critical risk profiles.
Experimental Protocols for Cross-Disciplinary Validation
To ground a unified philosophy in practice, defined experimental protocols are essential for benchmarking performance and ensuring reliability across disciplines.
Protocol for Digital Evidence Authentication and Deepfake Detection
Objective: To verify the integrity and authenticity of digital media evidence and detect AI-generated manipulations [32]. Workflow:
- Evidence Acquisition: Create a forensically sound bit-stream image of the storage media (e.g., smartphone, server) using a write-blocking hardware tool to preserve metadata and maintain a legal chain of custody [44].
- Data Integrity Check: Generate cryptographic hash values (e.g., SHA-256) for the acquired image and all extracted files. Any alteration invalidates the evidence.
- Deepfake Analysis:
- Multi-Model Interrogation: Process the media file through multiple specialized AI detection models (e.g., AlchemiX) [91].
- Feature Inconsistency Analysis: The models analyze physical and temporal cues, such as subtle lighting inconsistencies, unnatural blink patterns, and misalignment between audio waveforms and lip movements [91].
- Segmental Authentication: Instead of a simple "real/fake" output, the tool flags specific segments of the media file with a probability score for manipulation, allowing for nuanced expert interpretation [91].
- Reporting: Document all tools, commands, hash values, and the results of the deepfake analysis in a comprehensive report suitable for court disclosure.
Protocol for Validating AI-Assisted Forensic Triage
Objective: To evaluate the performance and potential bias of AI/ML tools used to prioritize evidence from large datasets [32]. Workflow:
- Dataset Curation: Assemble a ground-truthed dataset containing known relevant and irrelevant data points. The dataset must be diverse to test for algorithmic bias.
- Tool Benchmarking: Run the AI triage tool against the curated dataset. Record its performance metrics: processing speed, precision (percentage of flagged items that are truly relevant), and recall (percentage of all relevant items that were successfully flagged).
- Bias Assessment: Actively test for bias by analyzing if the tool's error rates are disproportionately higher for specific data subtypes or sources.
- Cross-Validation: Compare the AI tool's findings with those from a traditional, manual review of a subset of the data to identify discrepancies and validate findings.
Proposed Unified Validation Framework
The synthesized validation philosophy is built upon three core pillars that integrate the strengths of both traditional and digital disciplines. This framework ensures evidence is not only technically sound but also forensically and legally robust.
Diagram 1: The Three Pillars of the Unified Validation Framework
Pillar 1: Evidence Integrity and Provenance
This pillar combines the traditional chain of custody with digital data integrity measures. It mandates an unbroken, documented trail for all evidence, from the crime scene to the courtroom. For digital evidence, this is enforced through cryptographic hashing and write-blocking hardware immediately upon acquisition [44]. For multimedia, it extends to authenticity checks, such as using tools to detect AI-generated deepfakes, ensuring the evidence presented is a truthful representation [32] [91].
Pillar 2: Methodological Rigor and Transparency
This pillar demands that all processes, whether a chemical assay or a AI algorithm, are transparent, repeatable, and validated. It requires:
- Tool Validation: Forensic tools, especially AI-driven ones, must be rigorously tested against known datasets to understand their error rates and limitations [32].
- Cross-Tool Correlation: Critical findings should be verified using multiple independent tools or methods to reduce reliance on a single vendor or algorithm [91].
- Blind Procedures: Where possible, analyses should be conducted blind to the prevailing theory of the case to mitigate confirmation bias, a principle that is as crucial in digital analysis as it is in traditional lab work.
Pillar 3: Contextual Interpretation and Reporting
The final pillar addresses the human element of forensics. It requires experts to not only present findings but also to contextualize them, explicitly stating the limitations and uncertainties associated with their methods [32]. This includes quantifying the probability of a random DNA match or explaining the confidence score of an AI-driven deepfake detection tool [91]. Effective cross-disciplinary communication is essential, ensuring that a digital forensics expert can understand the constraints of a DNA analysis and vice versa, fostering a more holistic and accurate interpretation of complex evidence.
The Scientist's Toolkit: Essential Research Reagent Solutions
The following table details key materials and tools essential for implementing the proposed validation framework, bridging resources from both physical and digital domains.
Table 3: Essential Research Reagent Solutions for Cross-Disciplinary Forensics
| Tool / Reagent | Function | Disciplinary Application |
|---|---|---|
| Next-Generation Sequencing (NGS) Systems | Sequences entire genomes rapidly from trace/degraded DNA, providing detailed genetic information beyond traditional profiling [6]. | Traditional Forensics |
| Portable Mass Spectrometers | Enables on-scene chemical analysis of substances, accelerating the initial investigation phase [6]. | Traditional Forensics |
| Cloud Forensic Extraction Tools | Specialized software to legally access, retrieve, and preserve data from distributed cloud platforms like Google Drive or iCloud [45] [32]. | Digital Forensics |
| AI-Powered Triage Platforms | Algorithms that automatically analyze vast datasets (e.g., from a seized hard drive) to flag relevant evidence, patterns, and anomalies [32]. | Digital Forensics |
| Deepfake Detection Suites (e.g., AlchemiX) | Software that analyzes video/audio for subtle physical and temporal inconsistencies to identify AI-generated synthetic media [91]. | Digital Forensics |
| Virtual Autopsy (Virtopsy) Systems | Uses CT/MRI scans for non-invasive internal examination of bodies, useful in sensitive cultures or for hazardous remains [6]. | Traditional Forensics |
| Open-Source Toolkits (e.g., ALEX, TaskHunter) | Provides transparent, community-vetted methods for specific tasks like Android extraction or detecting malicious scheduled tasks in Windows [91]. | Digital Forensics |
The synthesis of a unified validation philosophy is not an academic exercise but a practical necessity for the future of forensic science. As criminals operate across physical and digital domains, the investigative response must be equally seamless. By integrating the evidence-centric rigor of traditional forensics with the scalable, automated verification of digital forensics, this proposed framework offers a path toward true cross-disciplinary excellence. The core pillars of Integrity, Rigor, and Contextual Interpretation provide a common language and a set of principles that can guide the development of new standards, tools, and training programs. For researchers and professionals, adopting this philosophy is key to producing evidence that is not only scientifically sound but also capable of upholding justice in an increasingly complex technological world.
Conclusion
The integrity of modern justice systems hinges on robust, cross-disciplinary validation frameworks. While traditional and digital forensics face distinct challenges—from the physical stability of evidence to the relentless pace of technological change—the core principles of reproducibility, transparency, and continuous validation form a common foundation. The future of forensic science demands a unified philosophy that integrates the rigorous standards of traditional methods with the agile, tool-aware validation required for digital evidence. Key future directions include developing standardized validation protocols for AI-driven forensics, creating adaptive frameworks for cloud and IoT evidence, and fostering greater collaboration between traditional and digital forensic disciplines to build a more resilient and trustworthy ecosystem for legal evidence.
References
- 1. What is forensic validation and how is it used? [https://www.envistaforensics.com/knowledge-center/insights/articles/forensic-validation-pay-attention-to-the-man-behind-the-curtain/]
- 2. Innovative Learning in a Digital Forensics Laboratory [https://www.mdpi.com/2076-3417/14/23/11095]
- 3. Practitioner-driven framework for AI adoption in digital ... [https://www.sciencedirect.com/science/article/abs/pii/S2666281725001702]
- 4. Top 6 Trends Shaping Modern DFIR in 2025 [https://belkasoft.com/dfir-trends-2025]
- 5. 10 Modern Forensic Technologies Used Today [https://www.forensicscolleges.com/blog/resources/10-modern-forensic-science-technologies]
- 6. Forensic Science in 2025: Navigating Future of Crime ... [https://drsatendra.com/forensic-science-in-2025/]
- 7. Forensic science in a process of transition [https://www.elsevier.es/en-revista-spanish-journal-legal-medicine-446-articulo-forensic-science-in-process-transition-S2445424918300293]
- 8. After Uniqueness: The Evolution of Forensic-Science Opinions [https://judicature.duke.edu/articles/after-uniqueness-the-evolution-of-forensic-science-opinions/]
- 9. The admissibility of digital evidence from open-source ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12431127/]
- 10. A transparent approach: Openness in forensic science ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11087997/]
- 11. Digital Forensic Validation: Principles, Methods, and ... [https://www.linkedin.com/pulse/digital-forensic-validation-principles-methods-examples-james-henning-xbjye]
- 12. Standards and best practices for digital forensics [https://www.unodc.org/e4j/en/cybercrime/module-4/key-issues/standards-and-best-practices-for-digital-forensics.html]
- 13. Daubert Standard | Wex | LII / Legal Information Institute [https://www.law.cornell.edu/wex/daubert_standard]
- 14. Daubert vs. Frye: Standards of Admissibility for ... [https://www.expertinstitute.com/resources/insights/daubert-vs-frye-navigating-the-standards-of-admissibility-for-expert-testimony/]
- 15. Frye Standard | Wex | US Law | LII / Legal Information Institute [https://www.law.cornell.edu/wex/frye_standard]
- 16. Frye standard [https://en.wikipedia.org/wiki/Frye_standard]
- 17. The Differences Between the Frye & the Daubert Standards [https://burnswhite.com/differences-between-frye-daubert/]
- 18. The Frye Standard | Expert Testimony, Admissibility, History [https://www.expertinstitute.com/resources/insights/admitting-expert-testimony-under-the-frye-standard-the-ultimate-guide/]
- 19. The Daubert Standard | Expert Testimony, Admissibility ... [https://www.expertinstitute.com/resources/insights/the-daubert-standard-a-guide-to-motions-hearings-and-rulings/]
- 20. The Daubert Standard vs. The Frye Standard and How ... [https://www.brandonjbroderick.com/daubert-standard-vs-frye-standard-and-how-they-impact-personal-injury-cases]
- 21. Unpacking Rule Changes on Expert Testimony [https://dicellolevitt.com/unpacking-rule-changes-on-expert-testimony/]
- 22. Collaborative versus traditional method validation approach [https://pmc.ncbi.nlm.nih.gov/articles/PMC7452674/]
- 23. Towards a standardized methodology and dataset for ... [https://arxiv.org/html/2505.03100v1]
- 24. Digital Forensics | NIST [https://www.nist.gov/itl/ssd/digital-forensics]
- 25. Towards a standardized methodology and dataset for ... [https://www.sciencedirect.com/science/article/pii/S2666281725001222]
- 26. Top 10 Digital Forensics Tools in 2025: Features, Pros, ... [https://www.cotocus.com/blog/top-10-digital-forensics-tools-in-2025-features-pros-cons-comparison/]
- 27. Top 5 Reasons Why You Should Use AXIOM with Your ... [https://www.magnetforensics.com/blog/top-5-reasons-why-you-should-use-axiom-to-verify-your-ufed-results/]
- 28. Top 10 Essential Mobile Forensics Tools for 2025 [https://www.salvationdata.com/knowledge/mobile-forensics-tools/]
- 29. Magnet AXIOM vs. Magnet IEF: Going Supersonic [https://www.magnetforensics.com/blog/magnet-axiom-vs-magnet-ief-going-supersonic/]
- 30. Loading Cellebrite Images into Magnet AXIOM [https://www.magnetforensics.com/blog/loading-cellebrite-images-into-magnet-axiom/]
- 31. Cloud Forensics Challenges: An In-depth Analysis [https://searchinform.com/articles/cybersecurity/analytics/digital-forensics/cloud-forensics/challenges/]
- 32. CEO Lee Reiber: The Digital Forensics Landscape in 2025 [https://www.oxygenforensics.com/en/resources/digital-forensics-trends-2025/]
- 33. The admissibility of digital evidence from open-source forensic ... [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0331683]
- 34. The admissibility of digital evidence from open-source ... [https://pubmed.ncbi.nlm.nih.gov/40938950/]
- 35. 5 Core Capabilities for Cloud Forensics and IR [https://www.darktrace.com/blog/forensics-or-fauxrensics-five-core-capabilities-for-cloud-forensics-and-incident-response]
- 36. The Proposal and Validation of a Distributed Real-Time ... [https://www.mdpi.com/2076-3417/15/12/6862]
- 37. The Complete Guide to Federated Data Analysis [https://lifebit.ai/blog/federated-data-analysis-2/]
- 38. Cross-validation (statistics) [https://en.wikipedia.org/wiki/Cross-validation_(statistics)]
- 39. Cross Validation in Machine Learning [https://www.geeksforgeeks.org/machine-learning/cross-validation-machine-learning/]
- 40. K-Fold Cross Validation: The Gold Standard for Model ... [https://medium.com/@prathik.codes/k-fold-cross-validation-the-gold-standard-for-model-evaluation-90648b3f6b08]
- 41. Cross-Validation and Its Types: A Comprehensive Guide [https://saidatascience.com/cross-validation-and-its-types-a-comprehensive-guide/]
- 42. Comparing Cluster-Based Cross-Validation Strategies for ... [https://arxiv.org/html/2507.22299v1]
- 43. 3.1. Cross-validation: evaluating estimator performance [https://scikit-learn.org/stable/modules/cross_validation.html]
- 44. . Modern Forensic... - Eclipse Comparing Traditional vs Forensics [https://eclipseforensics.com/comparing-traditional-vs-modern-forensic-methods-a-brief-guide/]
- 45. . Modern Comparing : Navigating... Traditional Vs Digital Forensics [https://lcgdiscovery.com/comparing-traditional-vs-modern-digital-forensics-navigating-the-evolving-digital-landscape/]
- 46. Continuous Validation: Building Trust in Your Digital Chain [https://www.lucenor.tech/blog/continuous-validation-building-trust-in-your-digital-chain]
- 47. The Future of Software Validation in Life Sciences: Trends ... [https://www.simco.com/blog/software-validation-trends/]
- 48. Instant Patch, Update & Validation [https://www.rimo3.com/instant-patch-update-validation]
- 49. Continuous Validation and Versioning of Complex Systems [https://www.appliedintuition.com/blog/continuous-validation-and-versioning-of-complex-systems]
- 50. ContinuousOS Ambient Agents for Always-On GxP ... [https://www.continuousintelligence.ai/blog/continuousos-ambient-agents-always-on-gxp-compliance]
- 51. 10 Useful Digital Forensics Software in 2025 [https://www.salvationdata.com/knowledge/digital-forensics-software/]
- 52. Digital Evidence Management Challenges in 2025 and Smart ... [https://digitalevidence.ai/blog/digital-evidence-management-challenges-in-2025-and-smart-solutions]
- 53. Digital Forensics Degree vs Traditional CSI | 2025 Guide [https://www.crimesceneinvestigatoredu.org/blog/digital-forensics-vs-traditional-csi-choosing-your-specialization/]
- 54. Digital Forensics [https://www.americanscientist.org/article/digital-forensics]
- 55. The Cost of Bad Data: Why Time Series Integrity Matters ... [https://www.influxdata.com/blog/bad-data-costs-influxdb/]
- 56. Data Integrity in a Data Pipeline: Best Practices and ... [https://medium.com/@georgemichaeldagogomaynard/data-integrity-in-a-data-pipeline-best-practices-and-strategies-for-data-quality-checks-dim-71af7a3bf21e]
- 57. Computer Forensics vs Digital Forensics: What's the ... [https://sip-international.com/blog/computer-forensics-vs-digital-forensics-whats-the-difference/]
- 58. Optimize data validation using AWS DMS validation-only ... [https://aws.amazon.com/blogs/database/optimize-data-validation-using-aws-dms-validation-only-tasks/]
- 59. Overcoming the top five challenges in data reconciliation [https://www.datafold.com/blog/data-reconciliation-challenges-and-solutions]
- 60. Explainable AI for Digital Forensics: Ensuring ... [https://www.forensicscijournal.com/journals/jfsr/jfsr-aid1089.php]
- 61. A Guide to Digital Forensics and Cybersecurity Tools (2025) [https://www.forensicscolleges.com/blog/resources/guide-digital-forensics-tools]
- 62. AI as a decision support tool in forensic image analysis [https://pmc.ncbi.nlm.nih.gov/articles/PMC12046100/]
- 63. Key Trends in Digital Forensics 2025: Chanllenges and ... [https://www.salvationdata.com/knowledge/key-trends-in-digital-forensics-for-2025/]
- 64. How AI Tools Are Shaping Forensic Accounting Practices ... [https://www.turningnumbers.com/blog/how-ai-tools-are-shaping-forensic-accounting-practices-in-2025]
- 65. 3 Solutions for Mobile Forensics Challenges in 2025 [https://www.oxygenforensics.com/en/resources/mobile-forensics-challenges-2025-solutions/]
- 66. Digital Forensics Round-Up, March 26 2025 [https://www.forensicfocus.com/news/digital-forensics-round-up-march-26-2025/]
- 67. Mobile Forensics Vs Computer Forensics: Key Differences [https://powerhouseforensics.com/mobile-forensics/mobile-forensics-vs-computer-forensics/]
- 68. Cell Phone Forensics vs. Computer Forensics: A Brief ... [https://eclipseforensics.com/cell-phone-forensics-vs-computer-forensics-a-brief-comparison/]
- 69. What is Mobile Forensics? Definition, Processes, & Examples [https://securityscorecard.com/blog/what-is-mobile-forensics-a-real-example-from-the-securityscorecard-forensics-lab/]
- 70. Forensic Data Analysis of Mobile Devices: A Primer [https://www.kroll.com/en/publications/forensic-data-analysis-of-mobile-devices]
- 71. a Digital Forensics Dataset for Large Language Models [https://arxiv.org/html/2509.05331v1]
- 72. Big Data Storage | Solutions, Challenges & Best Practices [https://data.folio3.com/blog/big-data-storage/]
- 73. 6 best practices on data governance for big data ... [https://www.techtarget.com/searchdatamanagement/tip/6-best-practices-on-data-governance-for-big-data-environments]
- 74. Document Management Best Practices for High-Volume ... [https://www.cincom.com/blog/ccm/document-management-best-practices/]
- 75. Data Risk Mitigation V2 [https://www.nowvertical.com/data-risk-mitigation-v2]
- 76. 10 Modern Data Management Best Practices: An Essential ... [https://data.world/blog/data-management-best-practices/]
- 77. 2025 FBI Quality Assurance Standards [https://a2la.org/2025-fbi-quality-assurance-standards/]
- 78. Collaborative versus traditional method validation approach [https://www.sciencedirect.com/science/article/pii/S2589871X20300528]
- 79. Leveraging Synthetic Data to Validate a Benchmark Study ... [https://pubmed.ncbi.nlm.nih.gov/39866725/]
- 80. Since You've Been Gone | FSD Forensics Advancements [https://www.secretservice.gov/newsroom/behind-the-shades/2025/02/youve-been-gone-fsd-forensics-advancements]
- 81. Bridging the gap: from biometrics to forensics - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC4580999/]
- 82. Mastering Terabyte-Scale Data: Strategies and ... [https://medium.com/practice-in-public/mastering-terabyte-scale-data-strategies-and-technologies-for-efficient-storage-and-processing-46d2632d1e5f]
- 83. Comparing Categorical and Probabilistic Fingerprint ... [https://forensicstats.org/blog/portfolio/comparing-categorical-and-probabilistic-fingerprint-evidence/]
- 84. Getting standardization right - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC8115957/]
- 85. What's the Problem with 'Best Practices'? [https://www.advisenltd.com/2014/08/13/whats-problem-best-practices/]
- 86. Standardization vs Customization: Finding the Right Balance [https://pmc.ncbi.nlm.nih.gov/articles/PMC7939702/]
- 87. The pros and cons of standardizing processes (SOP)✴️ [https://www.ag5.com/what-are-the-pros-and-cons-of-standardizing-operational-processes/]
- 88. The advantages and disadvantages of Standard Operating ... [https://touchstay.com/blog/the-advantages-and-disadvantages-of-standard-operating-procedures]
- 89. Approaches to protocol standardization and data ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11245389/]
- 90. A systematic review of comparisons between protocols or ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5765717/]
- 91. Digital Forensics Round-Up, November 05 2025 [https://www.forensicfocus.com/news/digital-forensics-round-up-november-05-2025/]