The Human Factor: Understanding and Mitigating Reasoning Challenges in Forensic Science Decisions
This article provides a comprehensive analysis of human reasoning challenges in forensic science decision-making.
The Human Factor: Understanding and Mitigating Reasoning Challenges in Forensic Science Decisions
Abstract
This article provides a comprehensive analysis of human reasoning challenges in forensic science decision-making. It explores the foundational cognitive limitations, from systemic biases to workplace stress, that can compromise forensic analysis. The content details proven methodological frameworks and procedural safeguards, such as Linear Sequential Unmasking, for mitigating error. It further examines troubleshooting via error typologies from wrongful conviction data and offers a comparative evaluation of human versus AI performance. Synthesizing key insights, the article concludes with strategic recommendations for embedding high-reliability principles to enhance accuracy and fairness in forensic practice and related biomedical fields.
The Inherent Flaws: How Human Cognition Shapes Forensic Judgment
The success of forensic science depends heavily on human reasoning abilities, yet decades of psychological science research reveal that human reasoning is not always rational [1]. Dual-process theory, a fundamental framework in cognitive psychology, provides a critical lens for understanding the cognitive mechanisms underlying forensic decision-making. This theory posits two distinct modes of thinking: System 1 (fast, automatic, intuitive) and System 2 (slow, deliberate, analytical) [2] [3]. In forensic science contexts, where decisions carry substantial consequences, the interplay between these systems significantly influences analytical outcomes. System 1 operates effortlessly and automatically, drawing on patterns and experiences to enable quick judgments, while System 2 requires intentional effort for complex problem-solving and analytical tasks [2].
Forensic science often demands that practitioners reason in "non-natural ways," countering the brain's inherent tendency to automatically integrate information from multiple sources to create coherent narratives [1]. This automatic integration, while typically advantageous for navigating daily life, introduces vulnerability to cognitive biases when forensic analysts must evaluate pieces of evidence independently of contextual information about a case. The tension between these natural cognitive processes and forensic science requirements creates critical challenges for analytical accuracy. This technical guide examines the manifestations of dual-process theory in forensic decision-making, explores specific cognitive challenges, and presents evidence-based protocols to mitigate bias through structured analytical procedures.
Theoretical Foundations of Dual-Process Theory
Defining System 1 and System 2 Characteristics
Dual-process theories in psychology describe how thought arises through two qualitatively distinct processes, often characterized as an implicit (automatic), unconscious process and an explicit (controlled), conscious process [3]. The table below summarizes the core characteristics of these two systems based on extensive psychological research:
Table 1: Core Characteristics of System 1 and System 2 Thinking
| Feature | System 1 (Intuitive) | System 2 (Deliberative) |
|---|---|---|
| Speed | Fast, immediate | Slow, sequential |
| Processing | Parallel, associative | Serial, analytical |
| Cognitive Demand | Low effort, automatic | High effort, controlled |
| Conscious Awareness | Unconscious, intuitive | Conscious, reflective |
| Evolutionary History | Older, shared with animals | Recent, predominantly human |
| Learning Mechanism | Associative conditioning | Logical inference, explicit instruction |
| Error Proneness | Vulnerable to cognitive biases | More reliable but not infallible |
| Dependency | Independent of working memory | Dependent on working memory capacity |
System 1 thinking is grounded in preconscious, automatic processing where information is processed rapidly and in parallel through associative networks [4]. This system operates effortlessly and opaquely, placing minimal demands on cognitive resources and acting upon schemas derived from concrete, emotionally significant, or repetitive experiences. In contrast, System 2 employs slow, deliberate information processing in a controlled and self-aware fashion, utilizing deductive reasoning that is effortful and cognitively demanding [4]. This system acquires knowledge through conscious learning from explicit sources rather than automatically established associations.
Neuropsychological Evidence and Theoretical Evolution
Neuropsychological research provides compelling evidence supporting the neural differentiation of intuitive and deliberate reasoning. Functional MRI studies reveal that deliberate reasoning activates the right inferior prefrontal cortex, while intuitive, belief-based responses associate with activation of the ventral medial prefrontal cortex [4]. These findings corroborate the behavioral distinction between the two systems and suggest System 2 processes can intervene in or inhibit System 1 processes.
The theoretical framework continues to evolve, with recent research challenging traditional classifications that associate intuitive processes solely with noncompensatory models and deliberate processes exclusively with compensatory ones [4]. Instead, a more nuanced framework suggests intuitive and deliberate characteristics coexist within both compensatory and noncompensatory processes, indicating greater complexity in the interaction between cognitive systems than previously theorized.
Cognitive Architecture of Forensic Decision-Making
Dual-Process Interactions in Analytical Contexts
In forensic decision-making environments, System 1 and System 2 do not operate in isolation but rather engage in dynamic interaction. The default-interventionist model suggests System 1 processes generate initial intuitive responses automatically, while System 2 monitors these outputs and may intervene when errors are detected or when cognitive conflict arises [5]. During forensic analysis, this interaction manifests when an examiner's initial impression of evidence similarity (System 1) is subsequently verified through deliberate point-by-point comparison (System 2).
The two systems operate in parallel, competing to determine final responses [4]. When forensic examiners face analytical tasks, System 1 processes the most accessible information and immediately proposes an intuitive answer, while System 2 simultaneously monitors the quality of this response, potentially approving, altering, or overriding it. The relative contribution of each system depends on situational factors (time pressure, complexity, contextual information) and decision-maker characteristics (expertise, cognitive capacity, training) [4].
Cognitive Flow in Forensic Analysis
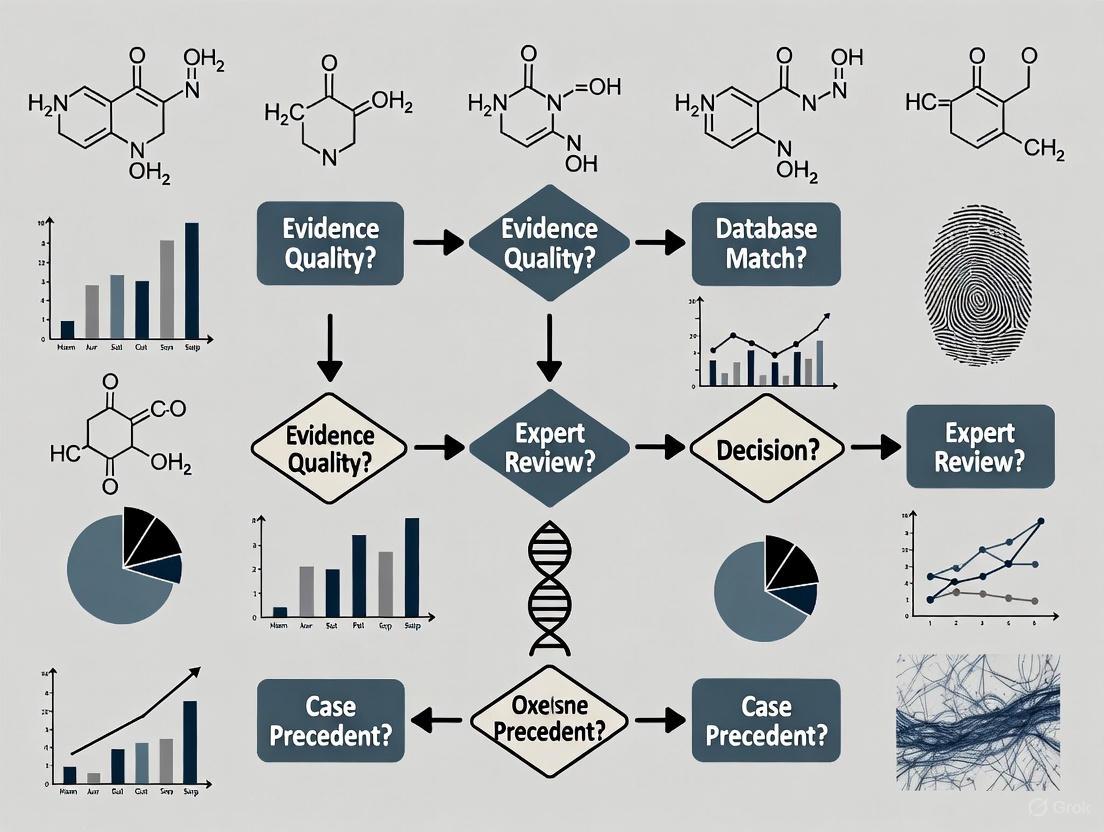
The following diagram illustrates the interaction between System 1 and System 2 during typical forensic evidence analysis:
This cognitive architecture creates inherent vulnerabilities when System 2 monitoring fails to engage adequately, potentially allowing automatic System 1 judgments to proceed without sufficient scrutiny—particularly under conditions of time pressure, fatigue, or high cognitive load [1] [6].
System 1 Heuristics and Cognitive Biases in Forensic Analysis
Mechanisms of Heuristic Thinking in Forensic Contexts
System 1 thinking relies on cognitive heuristics—mental shortcuts that enable efficient decision-making but introduce predictable errors in forensic contexts. These heuristics operate outside conscious awareness, making them particularly challenging to recognize and control [7]. The human brain develops numerous heuristics that support reasonably good decisions quickly, but this efficiency comes at the cost of occasional inaccurate conclusions based on insufficient analysis [8].
The automatic nature of System 1 processing creates specific vulnerabilities in forensic science, where practitioners must often resist natural cognitive tendencies toward coherence and pattern completion. Forensic examiners automatically combine information from multiple sources, create coherent narratives from potentially unrelated events, and construct interpretations through bottom-up (data-driven) and top-down (knowledge-driven) processing [1]. While this information integration generally serves us well, in forensic contexts it can lead to seeing "what we expect to see" and interpreting information in ways that confirm pre-existing beliefs [8].
Critical Biases in Forensic Decision-Making
Table 2: System 1 Heuristics and Corresponding Biases in Forensic Science
| Heuristic | Cognitive Mechanism | Forensic Manifestation | Impact on Analysis |
|---|---|---|---|
| Confirmation Bias | Seeking information that confirms existing beliefs | Selectively attending to features that match initial hypothesis | Premature closure on suspect identity; ignoring contradictory evidence |
| Anchoring Effect | Relying too heavily on initial information | Initial exposure to contextual information influences subsequent judgments | Initial suspect information "anchors" interpretation of ambiguous evidence |
| Representativeness | Judging probability by similarity to prototypes | Overemphasizing typical features while ignoring base rates | Assuming evidence matches suspect based on superficial similarity |
| Availability | Estimating likelihood based on ease of recall | Recent or memorable cases disproportionately influencing current analysis | Overestimating frequency of rare pattern matches based on memorable case |
| Affect Heuristic | Emotional responses influencing judgments | Emotional reaction to crime details affecting evidence interpretation | Gruesome crime scenes increasing perceived strength of ambiguous evidence |
These automatic System 1 processes demonstrate "cognitive impenetrability"—even when analysts know certain perceptions are false, they cannot always make themselves perceive the information differently [1]. This phenomenon explains why forensic examiners may continue to perceive a match between non-matching fingerprints even after learning they are from different sources, as System 1 processing continues to influence perception despite contradictory knowledge.
Experimental Studies and Empirical Evidence
Key Experimental Paradigms in Forensic Decision Research
Research examining dual-process theory in forensic contexts employs rigorous experimental designs to isolate the effects of System 1 and System 2 thinking on analytical accuracy. These studies typically utilize between-subjects designs where different groups of examiners receive varying levels of contextual information while analyzing identical evidence samples.
One foundational experimental protocol examined fingerprint analysis under different contextual conditions [6]. Participants were randomly assigned to either a biasing context group (exposed to emotional case details and suggestions of suspect guilt) or a blind group (no extraneous context). The biasing context group received a case narrative describing a violent crime with emotional victim impact statements, while the control group received only the prints without contextual information. All participants then analyzed ambiguous fingerprint pairs where ground truth had been established. Results demonstrated significantly higher match declarations in the biasing context group, particularly for ambiguous prints, revealing how System 1 processing integrates emotionally charged contextual information into analytical judgments.
Another experimental approach utilizes evidence "line-ups" to reduce comparative bias [6]. In this protocol, rather than comparing a single suspect sample to crime scene evidence, examiners evaluate multiple reference materials (including known innocent samples) presented simultaneously. This method counters the System 1 assumption that the provided suspect is the source, instead engaging System 2 to deliberately compare the evidence against multiple possibilities. Implementation of this protocol has demonstrated reduced false positive rates in firearms and toolmark identification.
Quantitative Findings on Cognitive Bias in Forensic Analysis
Table 3: Empirical Evidence of System 1 Vulnerabilities in Forensic Decisions
| Forensic Discipline | Experimental Manipulation | Effect on Decision Accuracy | Research Findings |
|---|---|---|---|
| Fingerprint Analysis | Contextual information about case | Increased false positives with biasing context | 52% of examiners changed conclusions when exposed to biasing context [6] |
| DNA Mixture | Base rate expectations | Altered threshold for declaring match | 23% variance in inclusion probabilities with different contextual cues [6] |
| Forensic Pathology | Order of information presentation | Premature closure on cause of death | 38% of pathologists ignored contradictory evidence after forming initial hypothesis [1] |
| Firearms Identification | Evidence line-ups vs. single suspect | Reduced confirmation bias | False positives decreased by 46% with multiple reference samples [6] |
| Handwriting Analysis | Emotional content of writing | Increased match declarations with disturbing content | Examiners 3.2x more likely to declare match when content was violent [6] |
These experimental findings consistently demonstrate that System 1 processing automatically incorporates task-irrelevant information into forensic judgments, even among highly trained and experienced examiners. The magnitude of these effects varies by discipline, with pattern recognition fields (fingerprints, firearms, handwriting) particularly vulnerable to contextual influences, while disciplines relying on instrumental analysis show somewhat less susceptibility.
Methodological Framework for System 2 Engagement
Procedural Safeguards Against Automatic Biases
Since cognitive biases operate largely outside conscious awareness, simply warning analysts about bias or encouraging them to "be objective" proves ineffective [6] [8]. Instead, structured procedural frameworks that systematically engage System 2 thinking provide the most reliable defense against automatic System 1 errors. These methodologies explicitly design analytical workflows to minimize exposure to potentially biasing information and create decision points that require deliberate, reflective thinking.
Linear Sequential Unmasking (LSU) and its expanded version LSU-E represent comprehensive approaches to managing the sequence of information exposure during forensic analysis [6]. This protocol emphasizes controlling the flow of task-relevant information to practitioners at times that minimize biasing influence while maintaining transparency about what information was received and when. The LSU-E framework utilizes three evaluation parameters—biasing power (information's perceived strength of influence), objectivity (variability of interpretation across individuals), and relevance (perceived relevance to analysis)—to determine optimal information sequencing.
Blind verification procedures constitute another essential methodological safeguard, providing true independence in technical review [6] [8]. In this protocol, a second examiner reviews the evidence with no knowledge of the first examiner's conclusions or any potentially biasing contextual information. This approach creates genuine System 2 engagement by preventing automatic alignment with the initial examiner's judgment and requiring independent analytical reasoning.
Experimental Workflow for Minimizing Cognitive Bias
The following diagram illustrates a structured experimental workflow designed to engage System 2 thinking and minimize System 1 biases in forensic analysis:
This methodological framework systematically engages System 2 at critical decision points throughout the analytical process, creating multiple opportunities for deliberate reasoning to override automatic intuitive judgments. The protocol emphasizes documentation at each stage to maintain transparency and create an audit trail of the decision-making process.
Research Reagents and Methodological Tools
Essential Materials for Dual-Process Research in Forensic Science
Research investigating dual-process theory in forensic contexts utilizes specific methodological tools and experimental materials designed to isolate cognitive mechanisms and measure their effects on decision quality. These "research reagents" enable standardized investigation across laboratories and facilitate direct comparison of findings.
Table 4: Essential Research Materials for Studying Dual-Process Theory in Forensic Contexts
| Research Tool | Composition/Configuration | Experimental Function | Application in Forensic Domains |
|---|---|---|---|
| Ambiguous Evidence Samples | Pre-validated evidence with known ground truth but ambiguous features | Measures susceptibility to contextual influences | Fingerprints, firearms, handwriting with borderline characteristics |
| Contextual Manipulation Stimuli | Case narratives with varying emotional content and suggestive elements | System 1 priming for confirmation bias studies | Emotional victim statements, suggestions of suspect guilt or innocence |
| Evidence Line-Up Sets | Multiple known samples including innocent sources alongside suspect | Counters presumption of guilt in single-suspect comparisons | Firearm cartridges, fingerprints, shoeprints with distractor items |
| Process-Tracing Software | Eye-tracking, mouselab, or verbal protocol analysis tools | Tracks information acquisition and processing strategies | Identifies heuristic versus systematic processing during evidence comparison |
| Cognitive Load Tasks | Simultaneous working memory tasks (e.g., digit retention) | Depletes cognitive resources available for System 2 monitoring | Measures expertise degradation under high cognitive demand |
| Blinded Verification Protocols | Standardized procedures for independent technical review | Tests effectiveness of System 2 engagement strategies | Validation of sequential unmasking in various forensic disciplines |
These research tools enable precise experimental manipulation of factors that influence the balance between System 1 and System 2 processing in forensic decision-making. By systematically employing these materials across studies, researchers can identify domain-specific vulnerabilities and develop targeted interventions to promote analytical reasoning.
Dual-process theory provides a powerful explanatory framework for understanding human reasoning challenges in forensic science decisions. The automatic, intuitive operations of System 1 thinking—while efficient for everyday decisions—create systematic vulnerabilities in forensic contexts where objectivity is paramount. Conversely, the deliberate, analytical processes of System 2 offer protection against these biases but require cognitive resources and structured implementation to function effectively.
The experimental evidence and methodological frameworks presented in this technical guide demonstrate that effective bias mitigation requires more than awareness or intention—it demands systematic procedural safeguards that explicitly manage information flow, engage analytical reasoning at critical decision points, and create accountability through documentation and verification. As forensic science continues to evolve its scientific foundations, integrating these cognitive principles into standard practice represents an essential step toward enhancing the reliability and validity of forensic evidence analysis.
Future research should continue to refine our understanding of the complex interactions between System 1 and System 2 across different forensic disciplines, develop more effective protocols for engaging analytical reasoning under operational constraints, and explore individual differences in cognitive style that might predict bias susceptibility. Through such efforts, the forensic science community can transform theoretical insights from dual-process research into practical advances that strengthen the foundation of justice systems worldwide.
The success of forensic science depends heavily on human reasoning abilities. Although we typically navigate our lives well using those abilities, decades of psychological science research shows that human reasoning is not always rational [9] [10]. Cognitive contamination refers to the process by which task-irrelevant information—such as investigative context, suspect background, or other extraneous knowledge—inappropriately influences the collection, perception, or interpretation of forensic evidence [11] [12]. This phenomenon represents a critical challenge to the validity and reliability of forensic science, particularly in disciplines that rely on human judgment for pattern matching and evidence interpretation.
The forensic community has undergone a significant transformation in recognizing these challenges since the 2009 National Academy of Sciences (NAS) report, which highlighted that pattern-matching disciplines are susceptible to cognitive bias effects due to their reliance on people to make judgments about evidence without sufficient scientific safeguards [11]. This technical guide examines the mechanisms of cognitive contamination, its impact on forensic decision-making, and evidence-based mitigation strategies, framed within the broader context of human reasoning challenges in forensic science decisions.
Theoretical Foundations: The Cognitive Science of Forensic Reasoning
Defining Cognitive Contamination in Forensic Contexts
Cognitive contamination occurs when forensic examiners are exposed to information that should not logically influence their analytical decisions, yet unconsciously affects their judgments [13] [12]. Unlike physical contamination of evidence, cognitive contamination operates through psychological mechanisms that can alter perception and interpretation without the examiner's awareness. Technical definition for cognitive biases is decision patterns that occur when people's "preexisting beliefs, expectations, motives, and the situational context may influence their collection, perception, or interpretation of information, or their resulting judgments, decisions, or confidence" [11].
Research has identified multiple sources of bias that can contribute to cognitive contamination in forensic practice. Dror (2020) summarized eight distinct sources of bias that have unique and compounding effects on expert decisions [11]:
- The Data: The evidence obtained in connection with the crime event can contain biasing elements and evoke emotions that can influence decisions.
- Reference Materials: The materials gathered to compare to the data and infer something about its source can affect forensic examiner's conclusions.
- Contextual Information: Extraneous details about the case, suspect, or investigation can unconsciously shape interpretation.
- Base-Rate Expectations: Prior expectations about the likelihood of certain events or matches can influence current judgments.
- Organizational Factors: Laboratory policies, productivity pressures, and hierarchical structures can introduce systematic biases.
- Motivational Factors: Career ambitions, desire to please investigators, or avoidance of cognitive dissonance can affect decision-making.
- Human Factors: General cognitive limitations in attention, memory, and perception underlie all forensic judgments.
- Educational and Training Factors: The way examiners are trained creates foundational assumptions and approaches to evidence.
The table below summarizes the key bias types, their mechanisms, and representative examples from forensic practice:
Table 1: Cognitive Bias Types in Forensic Evidence Interpretation
| Bias Type | Technical Definition | Mechanism of Influence | Forensic Examples |
|---|---|---|---|
| Contextual Bias | Extraneous case information inappropriately influencing perceptual judgment | Prior knowledge shapes expectation, which directs attention toward confirming information | Fingerprint examiners changing judgments when told suspect confessed or had verified alibi [12] |
| Confirmation Bias | Seeking or interpreting evidence in ways that confirm pre-existing beliefs | Selective attention to confirming features while discounting disconfirming evidence | Emphasizing similarities between evidence and reference materials while minimizing differences [11] |
| Automation Bias | Over-reliance on automated systems or algorithmic outputs | Technology usurps rather than supplements expert judgment | Examiners favoring candidate images presented at top of AFIS/FRT list regardless of actual match quality [12] |
| Memory Bias | Systematic errors in encoding, storage, or retrieval of forensic data | Prior experiences and cases influence perception of current evidence | Analysts overlooking critical details in current case due to similarity with previous case [13] |
Experimental Evidence: Quantifying Cognitive Contamination Effects
Foundational Studies in Pattern Evidence Disciplines
Seminal research by Dror and Charlton (2006) demonstrated that contextual information could cause fingerprint examiners to change 17% of their own prior judgments when presented with the same prints but different contextual information [12]. In this protocol, five experienced fingerprint examiners were presented with pairs of fingerprints they had previously evaluated and found to be matches. The experimental manipulation involved providing extraneous contextual information suggesting the prints should not match (verified alibi) or should match (suspect confession). The results demonstrated that even highly trained experts were vulnerable to cognitive contamination from task-irrelevant information.
A similar study with DNA analysts found they formed different opinions of the same DNA mixture when they knew that one of the suspects had accepted a plea bargain, demonstrating that cognitive contamination affects even disciplines considered more objective [12].
Recent Experimental Protocols: Facial Recognition Technology
A 2025 study examined cognitive bias in simulated facial recognition searches using a rigorous experimental protocol [12]. The methodology was designed to test both contextual and automation bias effects:
Participants: N = 149 participants acting as mock forensic facial examiners.
Materials: Two simulated FRT tasks, each containing a probe image of a perpetrator's face and three candidate faces that FRT allegedly identified as possible matches.
Experimental Conditions:
- Automation bias condition: Each candidate randomly paired with either a high, medium, or low numerical confidence score.
- Contextual bias condition: Each candidate randomly paired with extraneous biographical information (e.g., prior criminal record).
Dependent Variables: Perceived similarity ratings and identification decisions.
Results: Participants rated whichever candidate's face was paired with guilt-suggestive information or a high confidence score as looking most like the perpetrator's face, even though those details were assigned at random. Furthermore, candidates randomly paired with guilt-suggestive information were most often misidentified as the perpetrator [12].
This experimental protocol demonstrates that cognitive contamination can systematically distort face matching judgments, with significant implications for the use of FRT in criminal investigations.
Historical Case Studies: Dreyfus and Mayfield
The Dreyfus Affair (late 19th century) and Brandon Mayfield case (2004) provide historical examples of cognitive contamination with profound consequences [14]. In the Dreyfus case, handwriting analysis was distorted by antisemitic prejudice, while in the Mayfield case, multiple fingerprint examiners misidentified an innocent man in connection with the Madrid train bombing, partly due to knowledge that other examiners had already made the identification [14]. These cases highlight how cognitive contamination can occur even with experienced examiners and can propagate through verification processes.
Mitigation Strategies: Technical Protocols for Reducing Cognitive Contamination
Linear Sequential Unmasking-Expanded (LSU-E)
Linear Sequential Unmasking-Expanded is a procedural safeguard designed to manage the flow of information to forensic examiners [11]. The protocol involves:
- Documenting all relevant information available to the examiner before the analysis begins.
- Conducting the initial examination using only the essential information needed for the analysis.
- Recording conclusions from the initial examination before additional information is revealed.
- Systematically revealing additional information only when necessary, with documentation of how each new piece of information affects the conclusions.
The Costa Rican Department of Forensic Sciences implemented LSU-E in a pilot program within their Questioned Documents Section, demonstrating its practical feasibility and effectiveness in reducing cognitive contamination [11].
Blind Verification and Case Management
Blind verification prevents one examiner's conclusions from influencing another by ensuring that verifying examiners do not know the initial examiner's results or have access to potentially biasing contextual information [14]. This approach is particularly important for difficult or ambiguous evidence where cognitive contamination risk is highest.
The case manager model separates the forensic examiner from direct communication with investigators, controlling the information flow to ensure examiners receive only task-relevant information [11]. This system has been successfully implemented in the Costa Rican pilot program, providing a practical model for other laboratories.
Analytical Flowcharts for Cognitive Bias Mitigation
The following diagram illustrates a standardized workflow for implementing cognitive bias mitigation strategies in forensic analysis:
Diagram 1: Cognitive bias mitigation workflow
Laboratory Implementation Framework
Successful implementation of cognitive bias mitigation strategies requires addressing common misconceptions within the forensic community. The table below identifies six fallacies about cognitive bias and provides evidence-based corrections:
Table 2: Correcting Misconceptions About Cognitive Bias in Forensic Science
| Fallacy Name | Common Misconception | Evidence-Based Correction |
|---|---|---|
| Ethical Issues | "Only bad people are biased" | Cognitive bias is not an ethical issue but a normal decision-making process with limitations [11] |
| Bad Apples | "Only incompetent people are biased" | Bias does not result from lack of skill; even highly competent experts are vulnerable [11] |
| Expert Immunity | "Experience makes me immune to bias" | Expertise may increase reliance on automatic decision processes, potentially increasing bias [11] |
| Technological Protection | "Technology will eliminate subjectivity" | AI and algorithms are built, programmed, and interpreted by humans, so cannot eliminate bias [11] |
| Blind Spot | "I know bias exists, but I'm not vulnerable" | People consistently show a "bias blind spot," underestimating their own susceptibility [11] |
| Illusion of Control | "Awareness alone prevents bias" | Willpower cannot overcome automatic processes; systematic safeguards are necessary [11] |
Specialized Research Reagents and Materials for Cognitive Contamination Studies
The experimental study of cognitive contamination requires specific materials and methodological approaches. The following table details key resources for designing rigorous experiments in this domain:
Table 3: Research Reagent Solutions for Cognitive Contamination Experiments
| Reagent/Material | Technical Specification | Research Application | Example Use Case |
|---|---|---|---|
| Forensic Comparison Stimuli | Matched sets of pattern evidence (fingerprints, faces, handwriting) with ground truth established | Creating experimental tasks with known correct answers | Testing bias effects using fingerprints previously evaluated by same examiners [12] |
| Contextual Manipulation Protocols | Standardized textual case information (e.g., suspect confessions, prior records) | Experimental manipulation of contextual variables | Providing false contextual information to test confirmation bias [12] |
| Automation Bias Probes | Simulated algorithm confidence scores (high/medium/low) for pattern matches | Testing over-reliance on technological outputs | Assigning random confidence scores to facial recognition candidates [12] |
| Blind Analysis Software | Information management systems controlling revelation of case details | Implementing sequential unmasking in laboratory settings | Limiting examiner access to non-essential information during initial analysis [11] |
| Eye-Tracking Equipment | Gaze pattern and fixation duration measurement systems | Quantifying attentional allocation during evidence examination | Identifying how contextual information directs attention to confirming features [13] |
Emerging Challenges: Artificial Intelligence and Cognitive Contamination
The integration of artificial intelligence into forensic practice introduces new dimensions to cognitive contamination. Research indicates that AI systems can both reduce and amplify biases depending on their design and implementation [14]. Dror and Mnookin (2010) proposed a taxonomy of human-technology interaction that helps analyze these effects:
- Offloading: Experts delegate routine tasks to machines while retaining ultimate judgment.
- Collaborative Partnership: Humans and algorithms jointly negotiate interpretation.
- Subservient Use: Humans defer to machine outputs and suspend critical scrutiny.
Each interaction mode produces distinct epistemic vulnerabilities at the human-AI interface [14]. A 2025 study found that participants using facial recognition technology were biased by both extraneous biographical information and algorithmic confidence scores, demonstrating that automation bias represents a significant form of cognitive contamination in modern forensic systems [12].
The following diagram illustrates the bidirectional relationship between human cognition and AI systems in forensic contexts:
Diagram 2: Human-AI interaction in forensic decision-making
Cognitive contamination represents a fundamental challenge to the validity and reliability of forensic science. The research evidence demonstrates that contextual information and extraneous knowledge can systematically distort forensic decision-making across multiple disciplines, from traditional pattern evidence fields to emerging technologies like facial recognition. Mitigating these effects requires implementing evidence-based procedural safeguards such as Linear Sequential Unmasking-Expanded, blind verification, and case management systems.
The future of forensic science depends on building a culture that acknowledges the inherent limitations of human cognition while implementing systematic protections against cognitive contamination. This approach requires moving beyond the fallacy of expert immunity and recognizing that bias mitigation is not an ethical failing but a scientific necessity. As forensic science continues to evolve with new technologies, maintaining focus on the human factors underlying evidence interpretation will be essential for ensuring both the accuracy and integrity of forensic practice.
The integrity of forensic science and forensic mental health assessment is foundational to the administration of justice. Despite advanced training and professional credentials, forensic experts remain vulnerable to systematic cognitive errors that can compromise objectivity and accuracy. Groundbreaking work by cognitive neuroscientist Itiel Dror has demonstrated that even highly competent professionals are susceptible to biases influenced by cognitive processes and external pressures [15]. This technical analysis examines the core expert fallacies that perpetuate what is termed the "bias blind spot" - the pervasive tendency to recognize biases in others while denying their influence on one's own judgments [16]. Within the context of human reasoning challenges in forensic science decisions research, we explore the psychological mechanisms underlying these fallacies, present empirical evidence of their effects across forensic disciplines, and propose structured mitigation protocols grounded in cognitive science.
The challenge is particularly acute in forensic mental health assessments, where evaluators often operate in feedback vacuums, cutoff from corrective feedback, peer review, and consultation [15]. This isolation allows fallacies and biasing influences to threaten objectivity and fairness in evaluations, ultimately undermining the validity of findings and potentially compromising justice [15]. Understanding these cognitive vulnerabilities is essential for developing effective countermeasures and advancing toward more aspirational forensic practice [17].
Theoretical Framework: Dual-Process Theory and Expert Cognition
Systems of Reasoning in Forensic Decision-Making
Human reasoning operates through two distinct cognitive systems, as theorized by Daniel Kahneman, who integrated these insights into psychological research on judgment and decision-making under uncertainty [18]. The application of this framework to forensic science reveals fundamental tensions between natural reasoning patterns and the demands of rigorous forensic analysis.
Table 1: Cognitive Systems in Forensic Decision-Making
| Attribute | System 1 Thinking | System 2 Thinking |
|---|---|---|
| Process | Fast, intuitive, reflexive | Slow, analytical, deliberate |
| Cognitive Effort | Low effort, automatic | High effort, controlled |
| Awareness | Subconscious | Conscious and intentional |
| Basis | Innate predispositions, learned patterns | Logic, rule application, deliberate memory search |
| Vulnerability | Highly susceptible to cognitive biases | Less susceptible but requires cognitive resources |
| Role in Expertise | Enables pattern recognition through experience | Facilitates careful evidence weighing and hypothesis testing |
The interplay between these systems explains how experienced experts can simultaneously demonstrate remarkable pattern recognition abilities while remaining vulnerable to elementary cognitive errors. System 1 thinking enables efficient processing of complex information through learned patterns but introduces vulnerabilities through what Kahneman terms "fast thinking" or snap judgments based on minimal data [15]. Forensic practice demands System 2 thinking - slow, effortful, and intentional reasoning executed through logic and conscious rule application - yet the cognitive economy of System 1 creates persistent vulnerabilities [15] [18].
Dror's Pyramidal Model of Biasing Elements
Itiel Dror's cognitive framework conceptualizes how biases infiltrate expert decisions through a pyramidal structure demonstrating how cognitive processes interact with case-specific and baseline biases to influence outcomes [15]. This model provides a systematic architecture for understanding how ostensibly objective forensic analyses can be compromised through multiple pathways.
Figure 1: Dror's Pyramidal Model of Biasing Elements in Forensic Decision-Making
The pyramidal model illustrates how baseline biases rooted in professional socialization, education, training, worldview, and experience create foundational vulnerabilities [15]. These baseline influences shape how case-specific biases - including contextual information, motivational factors, and organizational pressures - are processed [15]. These biasing elements ultimately affect cognitive processes through data selection (what information is collected), data weighting (what importance is assigned), and data interpretation (how information is understood), ultimately influencing the final forensic decision [15].
The Six Expert Fallacies: Manifestations and Mechanisms
Dror identified six expert fallacies that increase risk for bias by creating false security about vulnerability to cognitive contamination [15]. These fallacies represent fundamental misunderstandings about the nature and operation of bias in expert judgment.
Fallacy 1: Only Unethical Practitioners Are Biased
The belief that cognitive bias primarily affects unscrupulous peers driven by greed or ideology represents a fundamental misunderstanding of cognitive science [15]. In reality, vulnerability to cognitive bias is a human attribute unrelated to character or ethical commitment [15]. Forensic psychiatrists and psychologists may correctly view themselves as ethical practitioners who adhere to ethics mandates, yet as humans in a complex world, even the most ethical practitioners experience cognitive biases [15]. This fallacy stems from confusion between cognitive biases (unconscious processing errors) and intentional discriminatory biases.
Fallacy 2: Bias Stems from Incompetence
This fallacy presumes that only incompetent evaluators fall prey to biasing influences, and that technical competence provides immunity [15]. In reality, an evaluation can be well-written, logical, and employ widely accepted assessment instruments yet conceal biased data gathering through selective attention to certain data types or failure to consider contextual factors [15]. For example, an evaluator might overrely on criminal history while omitting discussion of how risk instruments may be racially biased or inapplicable to specific populations [15]. Technical competence does not obviate the crucial need for bias-mitigating actions.
Fallacy 3: Expert Immunity Through Experience
Paradoxically, the mantle of "expert" may itself enhance bias risk through the development of cognitive efficiencies or shortcuts [15]. Experience may lead experts to selectively attend to data that comports with preconceived notions while neglecting novel, potentially salient data points [15]. The cognitive mechanisms that enable pattern recognition and predictive expectations can simultaneously create blind spots. For example, a forensic evaluator specializing in malingering assessments might automatically dismiss certain symptom presentations based on past experience, failing to consider alternative explanations [15].
Fallacy 4: Technological Protection
Forensic experts may believe that technological methods - including instrumentation, machine learning, artificial intelligence, or actuarial risk tools - eliminate bias [15]. This technological protection fallacy overlooks how algorithms and statistical values can foster false empiricism [15]. Risk assessment tools may incorporate inadequate normative representation of racial groups, potentially overestimating risk in minority populations [15] [14]. The assumption that statistical data represents "good psychological science" ignores how risk factors reflect researcher values and dominant cultural norms about maladaptive behavior [15] [16].
Fallacy 5: The Bias Blind Spot
The bias blind spot represents the well-documented phenomenon where experts perceive others as vulnerable to bias but not themselves [15] [16]. Because cognitive biases operate beyond awareness, experts frequently fail to recognize their own susceptibility [15]. Survey research with forensic mental health professionals demonstrates this blind spot clearly: while 86% acknowledge bias impacts forensic sciences generally and 79% recognize its influence on forensic evaluation specifically, only 52% acknowledge its effect on their own evaluations [16]. This self-other asymmetry creates significant barriers to effective bias mitigation.
Fallacy 6: Willpower and Introspection Are Sufficient
Most evaluators express concern about cognitive bias but hold the incorrect view that mere willpower or conscious effort can reduce bias [16]. Survey data indicates that 87% of forensic evaluators believe that consciously trying to set aside preexisting beliefs reduces their influence [16]. This perspective misunderstands the automatic, unconscious nature of cognitive biases, which cannot be eliminated through introspection alone [16]. Decades of research overwhelmingly indicate that cognitive bias operates automatically and cannot be eliminated through willpower [16].
Experimental Evidence: Quantifying Bias Effects
Contextual Bias in Forensic Pattern Matching
Empirical studies across multiple forensic disciplines demonstrate how extraneous contextual information systematically distorts expert judgment. In a seminal study, Dror and Charlton found that fingerprint examiners changed 17% of their own prior judgments of the same prints when presented with contextual information suggesting the suspect had confessed or provided a verified alibi [19] [12]. Similar effects have been documented in DNA analysis, where analysts formed different opinions of the same DNA mixture when aware a suspect had accepted a plea bargain [19] [12]. Contextual bias effects are particularly pronounced in ambiguous or difficult judgments, where cognitive uncertainty creates greater reliance on contextual cues [19] [12].
Automation Bias in Technological Systems
Automation bias occurs when examiners become overly reliant on metrics generated by technology, allowing the technology to usurp rather than supplement their judgment [19] [12]. In fingerprint analysis, when examiners were presented with AFIS search results in randomized order, they spent more time analyzing whichever print appeared at the top of the list and more frequently identified that print as a match - regardless of its actual validity [19] [12]. This automation bias demonstrates how human experts may defer to algorithmic outputs rather than maintaining independent critical assessment.
Experimental Protocol: Facial Recognition Technology Study
Objective: To test whether contextual and automation biases distort judgments in facial recognition technology (FRT) searches [19] [12].
Participants: 149 participants acting as mock forensic facial examiners [19] [12].
Design: Participants completed two simulated FRT tasks, each comparing a probe image of a perpetrator against three candidate faces that FRT allegedly identified as potential matches [19] [12].
- Automation Bias Condition: Candidates were randomly paired with high, medium, or low numerical confidence scores [19] [12].
- Contextual Bias Condition: Candidates were randomly paired with extraneous biographical information (prior similar crimes, already incarcerated, or military service) [19] [12].
Measures: Participants rated each candidate's similarity to the probe and indicated which candidate they believed was the perpetrator [19] [12].
Results: Participants consistently rated candidates paired with guilt-suggestive information or high confidence scores as looking most similar to the perpetrator, despite random assignment [19] [12]. Those randomly paired with guilt-suggestive information were most frequently misidentified as the perpetrator [19] [12].
Table 2: Quantitative Findings from FRT Bias Study
| Bias Type | Experimental Manipulation | Effect on Similarity Ratings | Misidentification Rate |
|---|---|---|---|
| Contextual Bias | Biographical information (prior crimes, incarceration, military service) | Significant increase for guilt-suggestive candidates | Highest for candidates with criminal history |
| Automation Bias | Confidence scores (high, medium, low) | Significant increase for high-confidence candidates | Elevated for high-confidence candidates |
| Combined Effects | Interaction of contextual and automation cues | Potentially additive biasing effects | Requires further investigation |
This experimental protocol demonstrates that even when using technologically advanced identification systems, human cognitive biases significantly influence outcomes, supporting the need for structured safeguards in forensic procedures [19] [12].
Bias Mitigation: Structured Approaches
Linear Sequential Unmasking-Expanded (LSU-E)
Linear Sequential Unmasking-Expanded represents a procedural approach to minimizing cognitive contamination by controlling the sequence and exposure of information during forensic analysis [15] [20]. This method extends basic linear sequential unmasking by incorporating additional safeguards against contextual influences.
The core principles of LSU-E include:
- Information Sequencing: Ensuring that base analysis of evidence is conducted before exposure to potentially biasing contextual information [15] [20].
- Documentation of Initial Impressions: Recording preliminary conclusions before accessing domain-irrelevant information [15] [20].
- Transparent Reporting: Clearly documenting all information considered at each decision point in the analytical process [15] [20].
Implementation of LSU-E and related procedural safeguards in forensic laboratories has demonstrated feasibility and effectiveness in reducing subjectivity and enhancing reliability [20]. The Department of Forensic Sciences in Costa Rica successfully piloted a program incorporating LSU-E, blind verification, and case managers to mitigate bias in questioned document analysis [20].
The Scientist's Toolkit: Research Reagents for Bias Mitigation
Table 3: Essential Methodological Components for Bias Research and Mitigation
| Tool/Component | Function | Application Context |
|---|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | Controls information flow to prevent contextual bias | Forensic pattern comparison, document analysis |
| Blind Verification | Prevents one examiner's conclusions from influencing another | All forensic disciplines requiring verification |
| Context Management Protocols | Limit exposure to irrelevant potentially biasing information | Crime scene analysis, forensic evaluations |
| Alternative Hypothesis Testing | Requires explicit consideration of competing explanations | Forensic mental health, autopsy decisions |
| Cognitive Bias Training | Increases awareness of inherent vulnerabilities | Foundational for all forensic practitioners |
| Decision Documentation Tools | Creates record of analytical process and timing | Quality assurance, procedural transparency |
Bayesian Frameworks for Evaluative Reporting
The European Network of Forensic Science Institutes and other standards bodies have developed protocols requiring reporting of evidence probability under multiple hypotheses using likelihood ratios [18]. This approach requires forensic scientists to consider the probability of evidence under both prosecution and defense hypotheses, providing a more balanced and transparent framework [18].
The likelihood ratio is expressed as:
LR = p(E|Hp) / p(E|Hd)
Where:
- p(E|Hp) = probability of evidence given prosecution hypothesis
- p(E|Hd) = probability of evidence given defense hypothesis
This methodological approach directly addresses cognitive vulnerabilities in human reasoning, particularly the tendency to neglect alternative explanations and baseline probabilities [18]. Proper application requires training in elementary probability theory to avoid common reasoning errors such as transposing conditional probabilities (the prosecutor's fallacy) [18].
The research evidence unequivocally demonstrates that expertise and ethical commitment provide insufficient protection against cognitive biases that systematically influence forensic decision-making. The six expert fallacies identified in Dror's framework create dangerous misconceptions about vulnerability to these influences, while the bias blind spot prevents professionals from recognizing their own susceptibility [15] [16].
Advancing beyond competent to exceptional forensic practice requires acknowledging these inherent vulnerabilities and implementing structured safeguards rather than relying on introspection or willpower [16] [17]. Procedural approaches like Linear Sequential Unmasking-Expanded, blind verification, Bayesian frameworks, and cognitive bias training represent evidence-based strategies for mitigating these universal human reasoning challenges [15] [20] [18].
Future directions should emphasize cross-domain research integrating insights from cognitive psychology, forensic science, and decision theory. Additionally, forensic training programs must incorporate comprehensive education about cognitive vulnerabilities alongside technical skill development. By embracing these approaches, forensic professionals can progressively narrow the gap between actual practice and aspirational standards, enhancing both the accuracy and fairness of forensic science within the justice system.
Within the rigorous domain of forensic science, the accuracy of expert decision-making is a cornerstone of justice. Traditional research has rightly focused on methodological precision and technological advancements. However, a critical human factor often remains overlooked: the pervasive impact of workplace stress and well-being on forensic experts' decision quality and error rates. A growing body of evidence suggests that stress is not merely an individual comfort issue but a significant variable that can systematically influence forensic judgments [21]. This whitepaper synthesizes current research to argue that workplace stress acts as a pivotal, yet frequently unaccounted for, factor in forensic decision-making. By exploring its mechanisms, impacts, and potential mitigations within the context of human reasoning challenges, this document aims to provide forensic researchers, scientists, and drug development professionals with a scientific framework for understanding and integrating this variable into their quality control and research paradigms.
Theoretical Framework: Stress as a Human Factor in Forensic Decisions
The Challenge-Hindrance Stressor Framework in Forensic Science
The impact of stress on professional performance is not monolithic. The Challenge-Hindrance Stressor Framework provides a useful lens for understanding its dual nature in forensic contexts. Within this model, stressors can be categorized as either challenge stressors or hindrance stressors [21].
- Challenge Stressors: These are work demands perceived as potential opportunities for growth and mastery, such as a complex, novel case that stretches an expert's analytical skills. When managed effectively, these stressors can potentially contribute to improved performance and engagement.
- Hindrance Stressors: These are work demands perceived as impediments to personal growth and goal achievement, such as unrealistic administrative demands, lack of organizational support, or unfair treatment. These stressors are consistently associated with negative outcomes, including reduced job satisfaction and increased error rates [21] [22].
The net effect of stress on a forensic expert's decision-making is posited to depend on the type, level, and context of the stress experienced, creating a complex relationship that requires context-specific understanding [21].
Decision Fatigue in High-Stakes Environments
A specific manifestation of cognitive resource depletion highly relevant to forensic work is decision fatigue. This psychological phenomenon refers to the deterioration in decision quality after a long sequence of choice-making [23]. Rooted in the concept of "ego depletion," it suggests that the mental energy required for self-control and deliberate decision-making is a finite resource that can be exhausted [23]. In fields like emergency medicine—a useful analogue for the high-stakes, rapid-turnaround environment of some forensic labs—physicians face a relentless stream of complex decisions. Evidence indicates that as cognitive resources diminish, professionals are more likely to resort to impulsive, less-considered decisions or even avoid making decisions altogether [23]. For a forensic expert examining fingerprint after fingerprint or complex DNA mixtures, decision fatigue could manifest as a tendency toward default "inconclusive" judgments or an increased likelihood of overlooking critical details as a shift progresses.
Quantitative Evidence: Linking Stress to Decision-Making Outcomes
Empirical studies across various high-stakes professions provide quantitative data on the correlation between workplace stress, decision-making processes, and outcomes. The table below summarizes key findings from relevant fields.
Table 1: Quantitative Evidence of Stress and Fatigue Impacts on Professional Decision-Making
| Profession / Context | Key Stressor | Impact on Decision-Making | Measured Outcome | Citation |
|---|---|---|---|---|
| Forensic Fingerprint Experts | Induced stress (experimental) | - Performance: Improved accuracy for same-source evidence.- Risk-Aversion: Increased reports of "inconclusive" on difficult same-source prints.- Confidence: Minimal impact on expert confidence. | - Performance metrics- Conclusion rates- Confidence ratings | [24] |
| Forensic Fingerprint Novices | Induced stress (experimental) | - Performance: Mixed impacts.- Response Time: Significant impact.- Confidence: Significant impact on overall confidence levels. | - Performance metrics- Response time- Confidence ratings | [24] |
| General Workforce | Adverse working conditions & management practices | - Causes of Stress: Unrealistic demands, lack of support, unfair treatment, low decision latitude, effort-reward imbalance.- Reported Prevalence: Working conditions cited as a main stress source by 42 of 51 interviewees. | - Qualitative interview data- Frequency analysis | [22] |
| Emergency Medicine Physicians | Decision fatigue from prolonged, high-stakes shifts | - Error Rates: Correlated with increased diagnostic errors and medication errors.- Decision Quality: Decline in appropriateness and effectiveness of clinical judgments. | - Observed error rates- Quality assessment of decisions | [23] |
The data reveals a nuanced picture. In controlled studies, stress can sometimes coincide with improved performance on specific tasks, as seen with fingerprint experts [24]. However, it also alters decision-making patterns, promoting risk-aversion. In real-world settings, stressors like poor management and high workloads are consistently linked to negative perceptual and health outcomes, which are known precursors to performance degradation [22]. The correlation between fatigue and error rates in emergency medicine further solidifies the link between resource depletion and diminished decision quality [23].
Experimental Protocols for Investigating Stress in Forensic Decision-Making
To rigorously study this variable, controlled experimental protocols are essential. The following methodology, adapted from a seminal study on forensic decision-making, provides a template for investigating the impact of stress on expert judgment.
Protocol: Fingerprint Decision-Making Under Induced Stress
1. Objective: To examine the effect of acute psychosocial stress on the accuracy, conclusion types, and confidence of fingerprint experts and novices.
2. Participants:
- Expert Group: Practicing fingerprint experts with significant casework experience (e.g., N=34).
- Novice Group: Individuals with no professional fingerprint identification experience (e.g., N=115).
- Design: Randomized controlled trial, typically with a between-subjects design (Stress Group vs. Control Group).
3. Stress Induction Manipulation:
- Stress Group: Participants are subjected to a standardized psychosocial stress protocol, such as the Trier Social Stress Test (TSST), which involves public speaking and mental arithmetic tasks in front of an evaluative panel. Salivary cortisol or subjective stress scales (e.g., State-Trait Anxiety Inventory) are collected to physiologically and psychologically validate the stress induction.
- Control Group: Participants complete a non-stressful control task of similar duration.
4. Decision-Making Task:
- Following the stress/control manipulation, participants complete a computerized fingerprint matching task.
- Stimuli: The task contains a series of fingerprint pairs. The set should include:
- Same-Source Pairs (SS): Prints from the same finger, varying in quality and clarity.
- Different-Source Pairs (DS): Prints from different fingers that may share some similar features.
- The difficulty level (easy vs. difficult) should be controlled and pre-tested.
5. Data Collection Measures:
- Primary Outcome 1 - Decision Accuracy: The proportion of correct identifications and exclusions across SS and DS pairs.
- Primary Outcome 2 - Decision Type: The rate of each possible conclusion ("Identification," "Exclusion," "Inconclusive").
- Primary Outcome 3 - Response Time: The time taken to reach each decision.
- Primary Outcome 4 - Confidence: Self-reported confidence in each decision on a Likert scale (e.g., 1-7).
6. Data Analysis:
- Employ statistical tests (e.g., ANOVA, t-tests) to compare the Stress and Control groups on all outcome measures.
- Analyze interactions between Group (Expert/Novice), Condition (Stress/Control), and Print Difficulty.
- Mediation analyses can explore whether the effect of stress on accuracy is mediated by changes in risk-taking (e.g., inconclusive rates) or confidence [24].
Pathways and Workflows: Visualizing the Stress-Decision Relationship
The following diagrams, generated using Graphviz, illustrate the conceptual and experimental relationships between workplace stress and forensic decision quality.
Conceptual Model of Stress Impact on Forensic Decisions
Experimental Workflow for Stress Testing
The Scientist's Toolkit: Research Reagents and Key Materials
To conduct rigorous research into workplace stress and decision-making, specific tools and methodologies are required. The following table details essential "research reagents" for this field.
Table 2: Key Research Reagents and Tools for Studying Stress and Decision-Making
| Tool or Material | Function/Description | Application in Research |
|---|---|---|
| Trier Social Stress Test (TSST) | A standardized protocol for reliably inducing moderate psychosocial stress in laboratory settings, involving public speaking and mental arithmetic. | Used as the primary independent variable (stress manipulation) to study its causal effect on subsequent decision-making tasks [24]. |
| Salivary Cortisol Assay Kits | Biochemical kits for measuring cortisol levels in saliva. Cortisol is a key hormonal biomarker of the body's physiological stress response. | Objective verification of the effectiveness of the stress induction manipulation (e.g., TSST). Samples are typically taken pre- and post-manipulation. |
| Standardized Decision Tasks | Curated sets of forensic stimuli (e.g., fingerprint pairs, DNA profiles) with ground truth established. These include both "same-source" and "different-source" samples of varying difficulty. | Serves as the dependent variable task to measure decision outcomes—accuracy, conclusion type, and response time—in a controlled and ecologically valid manner [24]. |
| Psychometric Scales | Validated self-report questionnaires. Key examples include: - Decisional Regret Scale (DRS): Measures distress after a decision.- CollaboRATE: Measures shared decision-making.- PHQ-2/9: Measures depressive symptoms.- Subjective Well-being Scales (e.g., ICECAP-A). | Quantifies psychological states such as regret, perceived collaboration, mental health, and well-being, which may mediate or moderate the stress-decision relationship [25]. |
| Statistical Analysis Software (R, Python, SPSS) | Software platforms capable of running advanced statistical analyses, including Analysis of Variance (ANOVA), mediation analysis, and structural equation modeling (SEM). | Used to analyze complex datasets, test for significant group differences, and model the direct and indirect pathways through which stress impacts decision outcomes [25]. |
The evidence is compelling: workplace stress and well-being are not peripheral concerns but central variables that can fundamentally shape the quality and nature of forensic decision-making. The relationship is complex, with stress sometimes sharpening focus on specific tasks but at the potential cost of increased risk-aversion and, under conditions of fatigue or hindrance, a clear pathway to heightened error rates. For a field built on the pillars of objectivity and reliability, integrating the science of human factors is no longer optional but essential. Future research must move beyond correlation to causation, employing the rigorous experimental protocols and tools outlined herein. Furthermore, the development and validation of evidence-based interventions—from structured decision breaks and cognitive debiasing techniques to organizational reforms that reduce hindrance stressors—are critical next steps. By acknowledging and systematically studying the overlooked variable of workplace well-being, the forensic science community can safeguard not only the health of its professionals but also the integrity of the justice system it serves.
This whitepaper examines the automatic integration of information through top-down processing and preexisting schemas, a fundamental characteristic of human reasoning that enables efficiency at the cost of potential systematic error. Framed within forensic science decision-making research, we explore how these cognitive processes contribute to the formation of coherent yet potentially flawed narratives. The mechanisms underlying these reasoning challenges are detailed through quantitative data synthesis, experimental protocols from cognitive neuroscience, and visualizations of signaling pathways. Finally, we present a scientist's toolkit of research reagents and methodologies for investigating and mitigating these biases in forensic practice, providing researchers with practical resources for advancing the field's accuracy and reliability.
Human reasoning demonstrates a paradoxical duality: it is both remarkably efficient and systematically fallible. This dichotomy stems from core cognitive architectures that automatically integrate information from multiple sources to construct coherent interpretations of the world. Top-down processing leverages preexisting knowledge, expectations, and experience to interpret incoming sensory information, while bottom-up processing builds perceptions purely from external stimuli [1]. In most daily functions, the integration of these processes serves us well; however, in specialized domains like forensic science, this automatic integration can introduce significant vulnerabilities into decision-making [1] [26].
The success of forensic science depends heavily on human reasoning abilities, yet the field often demands that practitioners reason in "non-natural ways" – evaluating pieces of evidence independently of contextual information that their brains automatically strive to incorporate [1]. This conflict between natural cognitive tendencies and forensic ideals creates a critical challenge: preexisting schemas (organized knowledge structures about events, situations, or concepts) automatically influence the interpretation of new information, potentially leading to coherent but forensically inaccurate narratives [1]. Understanding these mechanisms is essential for developing procedures that decrease errors and improve analytical accuracy in forensic contexts ranging from feature comparison to causal attribution.
Quantitative Synthesis: Key Experimental Findings on Top-Down Influences
Research across cognitive psychology and neuroscience has quantified how top-down processes influence perception and judgment. The table below synthesizes key experimental findings relevant to forensic decision-making.
Table 1: Quantitative Data on Top-Down Processing Effects in Perception and Judgment
| Experimental Paradigm | Key Finding | Effect Size/Magnitude | Implication for Forensic Science |
|---|---|---|---|
| Müller-Lyer Illusion [1] | Participants perceive equal lines as different lengths due to contextual cues | Illusion strength varies by environment; stronger in industrialized urban areas | Context can distort basic visual perception, potentially affecting evidence measurement |
| Bank Robbery Schema Memory Test [1] | Participants falsely recalled schema-consistent elements not present in original stimulus | Not specified; significant injection of non-present elements | Preexisting event schemas can corrupt memory of case details over time |
| Dot Perspective Task (dPT) with Forensic Cases [27] | Borderline personality disorder patients with court-ordered measures (BDL-COM) showed altered neural activation during perspective-taking | Significantly lower beta oscillation power (400-1300ms post-stimulus) in Avatar-Other condition | Population-specific neural processing differences may affect perspective-taking in legal contexts |
| Visual Processing Pathways [28] | Magnocellular (M) pathway processes information faster (80-120ms) than parvocellular (P) pathway (~150-200ms) | M pathway: 5-15% contrast sensitivity; P pathway: color-sensitive, <8% contrast ineffective | Fast, coarse processing may initiate top-down predictions before detailed analysis completes |
These quantitative findings demonstrate that top-down influences are not merely theoretical concepts but measurable phenomena with significant effects on perception, memory, and judgment. The neural evidence indicates that these processes occur rapidly and automatically, often outside conscious awareness, making them particularly challenging to mitigate in forensic contexts where objective analysis is paramount.
Neurocognitive Mechanisms: The Signaling Pathways of Top-Down Processing
The neural basis of top-down processing involves complex interactions between brain regions responsible for prior knowledge, sensory processing, and prediction. The following diagram illustrates the primary signaling pathways involved in top-down visual processing, which serves as a model system for understanding these mechanisms more broadly.
Visual Pathways of Top-Down Processing
This neural architecture demonstrates how higher-order cognitive regions (prefrontal cortex, temporoparietal junction) generate predictions that influence sensory processing regions (visual cortex, ventral and dorsal streams) through top-down signaling pathways [28]. The magnocellular pathway provides rapid, coarse information that initiates preliminary interpretations, while the slower parvocellular pathway provides detailed information that refines these interpretations [28]. In forensic contexts, this means initial impressions based on limited evidence can persistently influence subsequent analysis, creating a coherence that may not align with ground truth.
Experimental Protocols: Investigating Top-Down Influences in Forensic Reasoning
Dot Perspective Task (dPT) with EEG Recording
The dPT has emerged as a key experimental paradigm for investigating neural correlates of perspective-taking, with particular relevance to forensic populations [27].
Objective: To dissect differences in neural generator activation between forensic cases with court-ordered measures and healthy controls during visual perspective taking, specifically examining the distinction between mentalizing (Avatar) and non-mentalizing (Arrow) stimuli.
Participants:
- 15 borderline personality disorder patients with court-ordered measures (BDL-COM)
- 54 age-matched healthy controls without history of convictions
- All participants male gender to control for gender effects
Stimuli and Task Design:
- Participants view displays containing an Avatar or Arrow positioned in a room with dots on the walls
- Two conditions: Self-perspective ("How many dots do you see?") and Other-perspective ("How many dots does the Avatar/Arrow see?")
- Trials are classified as consistent (Self and Other see same number) or inconsistent (conflict between Self and Other perspective)
- Analysis focuses on inconsistent trials to maximize cognitive conflict
EEG Recording and Analysis:
- High-density EEG recording with 128 electrodes
- Analysis of event-related potentials (ERPs) at multiple time windows: <80ms, 80-400ms, and 400-1300ms post-stimulus
- Time-frequency decomposition to examine beta oscillation power (13-30Hz)
- Source localization to identify neural generators of electrical activity
Key Outcome Measures:
- Activation patterns in mentalizing network (temporoparietal junction, inferior frontal gyrus)
- Beta oscillation power differences between groups and conditions
- Timing differences in neural processing between forensic cases and controls
This protocol revealed that BDL-COM patients showed altered topography of EEG activation patterns and reduced abilities to mobilize beta oscillations during treatment of mentalistic stimuli, indicating neural correlates of their perspective-taking deficits [27].
Schema Intrusion Memory Paradigm
This behavioral protocol examines how preexisting schemas influence memory reconstruction in forensically relevant contexts.
Objective: To quantify how preexisting event schemas distort memory for case-relevant details.
Stimuli and Procedure:
- Participants listen to audio recording of a bank robbery trial testimony
- Testimony contains some schema-consistent and some schema-inconsistent details
- Control condition contains neutral testimony without strong schema associations
- After distraction task, participants complete free recall and recognition tests
Measurement:
- Number of schema-consistent intrusions (details not in original but consistent with bank robbery schema)
- Accuracy for schema-consistent versus schema-inconsistent details
- Confidence ratings for correct and incorrect memories
This paradigm demonstrates cognitive impenetrability – even when participants know about the potential for bias, they cannot completely prevent schema-based intrusions into their memories [1].
The Scientist's Toolkit: Research Reagents for Studying Forensic Reasoning
Table 2: Essential Methodologies and Assessment Tools for Forensic Reasoning Research
| Research Tool | Primary Function | Application in Forensic Reasoning Research | Key Metrics |
|---|---|---|---|
| High-Density EEG | Records electrical brain activity with high temporal resolution | Measures neural correlates of perspective-taking and decision-making in real-time | Event-related potentials (ERPs), beta oscillation power, neural source localization |
| fMRI | Measures brain activity through blood oxygen level-dependent (BOLD) signal | Identifies brain networks involved in top-down control and schema activation | Activation in mentalizing network (TPJ, medial PFC), attentional control regions |
| Psychopathy Checklist-Revised (PCL-R) [27] | Assesss psychopathic traits in clinical and forensic populations | Evaluates relationship between personality traits and perspective-taking abilities | Two-factor structure: interpersonal-affective traits and social deviance traits |
| HCR-20 [27] | Assesss historical, clinical, and risk management factors for violence | Examines how risk assessment correlates with cognitive processing patterns | 20 items across historical, clinical, and risk management domains |
| Mini-Social cognition and Emotional Assessment (SEA) [27] | Brief clinical assessment of Theory of Mind and emotion recognition | Quantifies social cognitive deficits in forensic populations | Theory of Mind score, emotion recognition score, composite social cognition score |
| Wechsler Adult Intelligence Scale (WAIS) [27] | Measures cognitive abilities and intelligence quotient (IQ) | Controls for general cognitive ability in forensic cognition studies | Verbal Comprehension, Perceptual Reasoning, Working Memory, Processing Speed indices |
| Dot Perspective Task (dPT) [27] | Assesss implicit and explicit perspective-taking abilities | Differentiates mentalizing from attention-orienting processes in forensic groups | Response times, accuracy rates, self-other consistency effects |
Discussion: Implications for Forensic Science Practice
The automatic integration of information through top-down processing presents fundamental challenges for forensic science. In feature comparison judgments (e.g., fingerprints, firearms, bitemarks), the primary challenge is avoiding biases from extraneous knowledge or from the comparison method itself [1] [26]. The cognitive tendency to create coherent narratives can lead analysts to prematurely converge on matches despite ambiguous evidence. In causal and process judgments (e.g., fire scenes, pathology), the main challenge is maintaining multiple potential hypotheses as investigations continue, resisting the brain's natural inclination to settle on a single coherent story [1].
The experimental protocols and tools detailed in this whitepaper provide pathways for both researching these phenomena and developing evidence-based mitigations. For instance, the temporal dynamics revealed by EEG studies suggest specific time windows during which cognitive interventions might be most effective. The individual differences observed in dPT performance indicate that certain forensic populations may require tailored approaches to minimize reasoning biases.
Future research should focus on translating these experimental findings into practical procedural safeguards that acknowledge the cognitive realities of forensic analysis while maximizing accuracy. This might include structured decision-making protocols that explicitly counter top-down biases, specialized training to develop metacognitive awareness of automatic integration tendencies, and technological solutions that leverage objective measurement while recognizing the indispensable role of human expertise in forensic science.
Building a Bulwark Against Bias: Procedural Safeguards and Mitigation Frameworks
Implementing Linear Sequential Unmasking-Expanded (LSU-E) to Control Contextual Information
Linear Sequential Unmasking–Expanded (LSU-E) represents a paradigm shift in forensic science decision-making, offering a structured framework to mitigate cognitive bias through systematic information management. This technical whitepaper examines the implementation of LSU-E within the broader context of human reasoning challenges in forensic science, addressing the critical need for standardized protocols that enhance analytical reproducibility and minimize contextual influences. We present comprehensive experimental methodologies, quantitative bias assessment data, and practical implementation tools designed for research scientists and forensic professionals seeking to optimize decision-making processes in evidentiary analysis.
Forensic science success depends heavily on human reasoning abilities, yet decades of psychological science research demonstrate that human reasoning is not always rational [9]. The inherent challenge lies in the fact that forensic science often demands that practitioners reason in non-natural ways, creating vulnerability to cognitive biases—systematic patterns of deviation from norm or rationality in judgment [9]. These biases emerge when preexisting beliefs, expectations, motives, or situational context influence how forensic professionals collect, perceive, or interpret evidence [29]. In high-stakes environments such as forensic analysis, where decisions can significantly impact judicial outcomes, even highly skilled, ethical individuals are not immune to these cognitive influences that typically operate outside conscious awareness [6].
The 2009 NAS report and subsequent research have empirically demonstrated across multiple forensic domains (including DNA, fingerprinting, forensic pathology, and toxicology) that cognitive bias can affect analyst decision-making, particularly in cases involving complex, difficult, or high-stress situations [6]. A striking example emerged from the notorious 2004 Madrid train bombing case, where senior FBI latent print examiners erroneously identified Brandon Mayfield, with the Office of the Inspector General concluding that confirmation bias played a significant role in this misidentification [29]. This case underscores the critical need for structured frameworks that manage contextual information flow to protect the integrity of forensic conclusions.
Theoretical Foundations of LSU-E
From LSU to LSU-E: Evolution of a Framework
Linear Sequential Unmasking (LSU) emerged as an initial research-based procedural framework designed to guide forensic laboratories' and analysts' consideration and evaluation of case information, primarily focusing on minimization of cognitive bias in disciplines related to pattern recognition [30] [6]. The core principle emphasized controlling the sequence of task-relevant information flow to practitioners, ensuring they receive necessary information at a time that minimizes its biasing influence [6].
LSU-Expanded (LSU-E) represents an enhanced framework that broadens LSU to make it more generally applicable to all forensic disciplines while simultaneously reducing "noise" from additional human factors [31] [6]. The strength of LSU-E derives from its systematic use of three evaluation parameters for information assessment: biasing power (the information's perceived strength of influence on analytical outcomes), objectivity (the information's perceived extent of variability of meaning to different individuals), and relevance (the information's perceived relevance to the analysis) [6]. This tripartite evaluation system enables laboratories to prioritize and optimally sequence information for forensic analyses, thereby improving decision quality through increased repeatability, reproducibility, and transparency [30].
The Cognitive Science Underpinnings
LSU-E operates on the empirical understanding that the order in which task-relevant information is received significantly impacts human cognition and decision-making processes [30] [29]. Contextual information can influence how forensic analysts perceive, interpret, and evaluate evidence through multiple mechanisms [29]:
- Confirmation bias: The tendency to search for, interpret, favor, and recall information in a way that confirms one's preexisting beliefs or hypotheses
- Contextual bias: The effect of case-specific contextual information on decision-making
- Sequential dependence: Where later information disproportionately influences interpretation of earlier data
These cognitive effects highlight why proper information sequencing serves as a critical mechanism for reducing bias and improving the repeatability and reproducibility of forensic decisions [29].
LSU-E Implementation Methodology
Core Implementation Framework
Figure 1: LSU-E Implementation Workflow - A systematic approach to implementing Linear Sequential Unmasking-Expanded in forensic practice
The LSU-E implementation framework comprises seven methodical stages designed to optimize information sequencing while maintaining analytical integrity:
Comprehensive Information Inventory: Identify all potential information sources available for a case, including evidence, reference materials, contextual details, and preliminary findings [30].
Three-Parameter Assessment: Evaluate each information element using the LSU-E parameters (biasing power, objectivity, and relevance) on standardized rating scales [6].
Information Sequencing Plan: Develop a structured sequence for information revelation, prioritizing objective, relevant, and minimally biasing information for initial analysis phases [29].
Initial Blind Analysis: Conduct preliminary evidence examination without exposure to potentially biasing contextual information, particularly when analyzing unknown samples [29] [6].
Sequential Information Revelation: Introduce additional information in controlled stages, with documentation of analytical conclusions at each stage before proceeding to subsequent information tiers [30].
Transparent Documentation: Maintain comprehensive records of all information received, when it was received, and its potential impact on analytical decisions throughout the process [6].
Independent Review: Implement blind verification procedures where reviewers examine evidence without exposure to initial analysts' conclusions to ensure independent assessment [6].
Practical Implementation Tool: The LSU-E Worksheet
Concrete implementation of LSU-E in forensic casework is facilitated through a practical worksheet designed to bridge the gap between research and practice [30] [29]. This structured tool guides practitioners through the systematic evaluation and sequencing of case information, providing:
- Standardized rating scales for biasing power, objectivity, and relevance
- A structured framework for developing information revelation sequences
- Documentation protocols for maintaining analytical transparency
- Quality assurance checkpoints throughout the analytical process
The worksheet serves as both a procedural guide and documentation mechanism, ensuring consistent application of LSU-E principles across cases and examiners [29].
Quantitative Analysis of Contextual Influences
Empirical Bias Ratings for Common Contextual Information
Table 1: LSU-E Parameter Ratings for Common Contextual Information Types in Forensic Analysis
| Contextual Information Type | Biasing Power (1-5) | Objectivity (1-5) | Relevance (1-5) | Key Research Findings |
|---|---|---|---|---|
| Another examiner's decision | 4 | 3 | 5 | Influences novice and expert analysts across fingerprints, DNA, questioned documents, and ballistics [29] |
| Suspect confession | 5 | 3 | 5 | Strongest biasing power; affects novice document analysts and polygraph experts [29] |
| Demographic/suspect background | 4 | 4 | 5 | Impacts fingerprint analysts, document examiners, toxicology trainees, and forensic anthropologists [29] |
| Type of crime/crime scene details | 4 | 4 | 4 | Affects novice and expert fingerprint analysts; relevance varies by discipline [29] |
| Verified suspect alibi | 4 | 3 | 5 | Demonstrated influence on expert fingerprint analysts [29] |
| Exposure to other forensic evidence | 5 | 3 | 5 | Impacts analysts across fingerprints, anthropology, bloodstain patterns, and digital forensics [29] |
Bias Source Categorization and Mitigation Approaches
Table 2: Eight Sources of Cognitive Bias in Forensic Decisions and Practitioner-Implementable Countermeasures
| Bias Source Category | Specific Source | Practitioner-Implementable Mitigation Actions | Case Example |
|---|---|---|---|
| Case-Specific Factors | Data (evidence itself) | Educate submitters on masking non-essential features; isolate features of interest [6] | Underwear characteristics revealing wearer information in sexual assault cases [6] |
| Reference materials | Analyze unknown evidence before known references; use multiple reference "line-ups" [6] | Mayfield case: side-by-side comparison encouraged circular reasoning [29] | |
| Task-irrelevant context | Avoid reading unnecessary submission documentation; document accidental exposures [6] | FBI examiners aware Mayfield was on watch list [29] | |
| Task-relevant context | Document what was learned, when, and potential impact; distinguish relevant vs. irrelevant [6] | Case-specific analytical requirements | |
| Practitioner & Organizational Factors | Base rate expectations | Consider alternative outcomes; reorder notes for pseudo-blinding [6] | Organizational expectations about certain case types |
| Organizational factors | Examine lab protocols for undue influence; revise policies as needed [6] | Laboratory culture and communication practices | |
| Education & training | Review for consistency with best practices; request ongoing cognitive bias training [6] | Initial training and continuing education | |
| Human Cognitive Architecture | Personal factors | Document justification for analytical decisions; recognize stress/fatigue symptoms [6] | Individual mental and physical well-being |
| Human brain mechanisms | Practice self-care; maintain mental and physical well-being [6] | Fundamental cognitive processes |
Experimental Protocols for LSU-E Validation
Controlled Studies of Contextual Information Influence
Research validating LSU-E methodologies typically employs rigorous experimental designs that systematically manipulate contextual variables while measuring their impact on analytical outcomes:
Protocol 1: Sequential Information Presentation
- Objective: Quantify the effect of information sequencing on analytical conclusions
- Methodology: Participants are randomly assigned to receive case information in different sequences (e.g., objective evidence first vs. contextual information first)
- Controls: Blind scoring of outcomes, counterbalanced design, control groups receiving minimal context
- Measures: Decision accuracy, confidence levels, consistency between examiners, susceptibility to contextual influences
- Applications: Validated across fingerprint, DNA, bloodstain pattern, and digital forensic disciplines [29]
Protocol 2: Multiple Reference Sample "Line-up"
- Objective: Assess the biasing effect of single-suspect comparisons versus multiple candidate comparisons
- Methodology: Analysts receive either single suspect samples or multiple samples including known-innocent distractors
- Controls: Ground truth known samples, blinding to ground truth during analysis
- Measures: False positive rates, analytical thoroughness, comparative reasoning documentation
- Findings: Multiple reference presentations reduce bias from inherent assumptions when only single samples are provided [6]
LSU-E Parameter Rating Validation
Establishing reliable parameter ratings (biasing power, objectivity, relevance) for different information types requires systematic methodology:
Expert Consensus Protocol:
- Convene panels of subject matter experts across relevant forensic disciplines
- Present detailed descriptions of information types and case scenarios
- Employ modified Delphi techniques to reach consensus on parameter ratings
- Validate ratings through controlled experimental studies
- Document rationale for ratings to guide application across case types [29]
Table 3: Essential Methodological Components for Effective LSU-E Implementation
| Toolkit Component | Function | Implementation Example |
|---|---|---|
| Structured Worksheet | Guides information assessment and sequencing; documents decision process | Practical tool bridging research and practice with standardized rating scales [30] |
| Information Rating Matrix | Standardizes evaluation of biasing power, objectivity, and relevance | Reference table with pre-rated common information types [29] |
| Blind Verification Protocol | Ensures independent assessment without exposure to previous conclusions | Secondary analyst examines evidence blinded to initial conclusions [6] |
| Sequential Revelation Template | Provides structure for controlled information disclosure | Tiered information release schedule with documentation checkpoints |
| Alternative Hypothesis Framework | Forces consideration of competing explanations | Mandatory generation and evaluation of alternative interpretations [6] |
| Transparency Documentation Standards | Creates audit trail for information exposure and its potential influence | Chronological accounting of communications and case information exposure [6] |
Discussion and Future Directions
The implementation of Linear Sequential Unmasking–Expanded represents a significant advancement in addressing fundamental human reasoning challenges within forensic science decisions. By providing a structured framework for managing contextual information, LSU-E directly confronts the cognitive realities that undermine forensic decision-making: even highly skilled experts remain vulnerable to influences that operate outside conscious awareness [6]. The empirical demonstrations of LSU-E's effectiveness across multiple forensic disciplines highlight its value as a standardized approach to minimizing cognitive bias while maintaining analytical thoroughness [30] [29].
Future development of LSU-E methodologies should focus on several critical areas. First, discipline-specific guidelines must be established to refine parameter ratings for information types unique to specialized forensic domains. Second, technological solutions that facilitate the implementation of LSU-E workflows—including case management systems with built-in sequencing protocols—would enhance consistent application. Third, expanded training programs incorporating realistic scenario-based exercises would strengthen practitioner competence in identifying and managing potentially biasing information. Finally, continued research should explore the interaction between individual differences in cognitive style and susceptibility to specific bias types, potentially enabling personalized implementation approaches.
The adoption of LSU-E represents more than procedural compliance; it embodies a fundamental commitment to scientific rigor in forensic practice. By systematically addressing the challenges of human reasoning through structured information management, the forensic science community demonstrates its dedication to objective, reproducible, and transparent analysis—cornerstones of both scientific integrity and justice system reliability.
Operationalizing Blind Verification and Case Management for Independent Review
The integrity of forensic science decisions is fundamentally threatened by cognitive biases—unconscious mental shortcuts that can systematically distort the collection, perception, and interpretation of evidence [9] [11]. These biases are not a reflection of incompetence or ethical failure but are inherent aspects of human reasoning that operate automatically, particularly under conditions of uncertainty or ambiguity [32] [11]. In forensic contexts, where decisions can profoundly impact lives and justice, cognitive biases such as confirmation bias (the tendency to seek information confirming pre-existing beliefs) and anchoring bias (over-reliance on initial information) present significant risks [32].
Blind verification and structured case management have emerged as foundational strategies for mitigating these biases by controlling the flow of potentially biasing information to examiners [11]. Operationalizing these processes involves implementing specific technical protocols and workflow modifications that protect examiners from irrelevant contextual information while maintaining analytical rigor. This guide provides a comprehensive framework for forensic laboratories seeking to implement these critical safeguards, with particular emphasis on practical implementation within pattern-matching disciplines and forensic drug analysis.
Theoretical Foundation: Cognitive Bias in Forensic Decision-Making
Key Cognitive Biases and Their Forensic Impacts
Table 1: Common Cognitive Biases in Forensic Analysis and Their Operational Impacts
| Cognitive Bias | Definition | Potential Impact on Forensic Analysis | Primary Mitigation Strategy |
|---|---|---|---|
| Confirmation Bias | Tendency to seek, interpret, and recall information that confirms pre-existing beliefs or hypotheses [32]. | May lead to "tunnel vision" where examiners emphasize confirming evidence while discounting contradictory information; contributed to misidentification in Brandon Mayfield fingerprint case [32] [11]. | Linear Sequential Unmasking; Blind verification; Case managers [11]. |
| Anchoring Bias | Relying too heavily on initial information (the "anchor") when making subsequent judgments [32]. | Initial suspect information or preliminary findings may inappropriately influence subsequent analytical decisions and evidence interpretation. | Information sequencing; Blind administration of evidence [11]. |
| Dunning-Kruger Effect | Individuals with limited knowledge overestimate their competence, while experts may underestimate theirs [32]. | Novice examiners may proceed with overconfidence in complex analyses without recognizing their limitations; experienced examiners may undervalue their judgment. | Structured mentoring; Clear competency standards; Regular proficiency testing [32]. |
| Sunk Cost Fallacy | Continuing an endeavor due to prior investment of time/resources rather than current rationale [32]. | Investigators may persist with an initial theory despite emerging contradictory evidence to justify previous investigative efforts. | Hypothesis diversity; Regular case review; Explicit exit criteria [32]. |
The Fallacy of "Expert Immunity"
A significant barrier to implementing bias mitigation strategies is the persistent misconception that experienced examiners are immune to cognitive biases [11]. Research consistently demonstrates that expertise does not confer immunity; in fact, experienced professionals may be more susceptible to certain biases due to increased reliance on automatic processing [11]. The "bias blind spot" phenomenon further complicates this issue, as professionals often acknowledge bias as a general problem while denying personal susceptibility [11].
Operational Framework for Blind Verification
Core Principles and Definitions
Blind verification refers to a verification process where the second examiner conducts their analysis without knowledge of the initial examiner's findings or any potentially biasing contextual information about the case [11]. This contrasts with traditional "open" verification, where the verifying examiner knows the initial results, creating potential for confirmation bias.
Linear Sequential Unmasking-Expanded (LSU-E) represents an advanced framework that incorporates blind verification principles while systematically controlling the sequence and timing of information disclosure to examiners [11]. This approach ensures examiners have access to necessary analytical information while being shielded from potentially biasing contextual details until after their initial examinations are complete.
Implementation Methodology: A Structured Approach
Phase 1: Pre-Analysis Information Triage
- The case manager (a role distinct from the examining analysts) reviews all case materials and identifies potentially biasing information [11].
- Task-relevant information (specific evidence for analysis) is separated from task-irrelevant information (investigative context, suspect statements, other forensic results).
- A formal case information protocol documents which information is essential for analysis versus potentially biasing.
Phase 2: Sequential Information Disclosure
- Primary examiners receive only the minimal information necessary to conduct their analysis.
- All documentary controls (request forms, laboratory worksheets) are stripped of biasing context.
- Verifying examiners conduct independent analyses using the same controlled information set, without knowledge of the initial findings.
- Only after all examiners have documented their independent conclusions is full case context revealed for final interpretation and reporting.
Phase 3: Documentation and Review
- All procedures, including information control measures and verification results, are thoroughly documented.
- Regular audits ensure adherence to blind verification protocols.
- Statistical monitoring tracks verification concordance rates and identifies potential process improvements.
Laboratory Implementation Protocol
Table 2: Step-by-Step Protocol for Implementing Blind Verification
| Implementation Phase | Key Activities | Quality Control Measures | Expected Outcomes |
|---|---|---|---|
| Pilot Program Design | Select specific discipline for initial implementation; Develop detailed SOPs; Train staff on cognitive bias concepts [11]. | Pre-implementation baseline error rate assessment; Staff feedback mechanisms; Protocol validation studies. | Refined protocols; Staff buy-in; Demonstrated feasibility. |
| Case Manager Implementation | Designate qualified staff as case managers; Define clear responsibilities for information management; Establish case manager training program [11]. | Documentation audits; Cross-training to prevent bottlenecks; Clear authority delineation. | Controlled information flow; Consistent application of blinding protocols. |
| Full Implementation | Phase blind verification across selected discipline; Monitor resource impacts; Adjust workflows as needed [11]. | Regular compliance audits; Concordance rate monitoring; Resource utilization tracking. | Reduced contextual bias; Maintained analytical accuracy; Sustainable processes. |
| Program Maintenance | Ongoing staff training; Regular protocol review; Continuous improvement based on performance data [11]. | Annual review of blinding effectiveness; Proficiency testing integration; External validation. | Sustained bias mitigation; Adaptive to new challenges; Culture of scientific rigor. |
Case Management for Independent Review
The Case Manager Role: Functions and Qualifications
The case manager serves as a critical safeguard in blind verification systems by controlling the flow of information between case investigators and forensic examiners [11]. This role requires:
- Technical expertise in the relevant forensic discipline to distinguish task-relevant from task-irrelevant information.
- Understanding of cognitive bias mechanisms and how different information types may influence analytical decisions.
- Administrative authority to enforce information protocols and resist pressure to disclose potentially biasing information.
- Communication skills to explain the rationale for information controls to investigators and legal stakeholders.
Operational Workflow for Case Management
The following diagram illustrates the integrated relationship between case management and blind verification processes:
Diagram 1: Blind Verification and Case Management Workflow
Measuring Effectiveness: Key Performance Indicators
Successful implementation of blind verification and case management requires robust metrics to assess both operational efficiency and scientific validity:
- Concordance rates between primary and verifying examiners
- Case turnaround times compared to pre-implementation baselines
- Discrepancy resolution patterns and their outcomes
- Proficiency testing performance under blind versus declared conditions
- Staff feedback on protocol feasibility and perceived value
Advanced Applications: Blind Proficiency Testing
Implementing Blind Proficiency Testing
Blind proficiency testing represents a more rigorous approach to quality assurance compared to traditional declared testing [33]. In blind proficiency tests, samples are introduced through normal casework channels without examiners' knowledge that they are being tested [33]. This approach provides several critical advantages:
- Ecological validity: Tests reflect real-world conditions and decision pressures [33]
- Comprehensive pipeline assessment: Evaluates the entire analytical process from evidence receipt to reporting
- Behavioral naturalism: Avoids altered performance that may occur when examiners know they are being tested [33]
- Misconduct detection: Can reveal intentional deviations from protocol that might otherwise go undetected [33]
Implementation Challenges and Solutions
Table 3: Challenges in Implementing Blind Proficiency Testing and Strategic Solutions
| Implementation Challenge | Impact on Forensic Laboratories | Demonstrated Solutions |
|---|---|---|
| Logistical Complexity | Creating realistic blind test materials that mimic casework without detection; Resource-intensive administration [33]. | Partnership with external providers; Phased implementation starting with straightforward disciplines; Use of actual case materials with known outcomes. |
| Cultural Resistance | Staff skepticism about "deception"; Concerns about performance evaluation under blind conditions [33]. | Transparent educational programs on cognitive science basis; Non-punitive assessment framework; Leadership endorsement and participation. |
| Resource Constraints | Financial and personnel requirements for developing, administering, and evaluating blind tests [33]. | Strategic prioritization of high-impact disciplines; Grant funding specifically for quality improvement; Collaboration between laboratories for resource sharing. |
| Legal and Accreditation Considerations | Potential discoverability of test results; Accreditation standard interpretations [33]. | Clear policies on result handling; Early engagement with accrediting bodies; Legal review of protocols before implementation. |
Table 4: Research and Implementation Resources for Blind Verification Systems
| Resource Category | Specific Tools/Methods | Function in Implementation | Example Applications |
|---|---|---|---|
| Cognitive Bias Mitigation Frameworks | Linear Sequential Unmasking-Expanded (LSU-E) [11] | Provides structured approach to information sequencing and disclosure controls. | Pattern evidence examination; Forensic document analysis. |
| Quality Assurance Tools | Blind Proficiency Testing [33] | Assesses laboratory performance under realistic operational conditions. | All forensic disciplines; Particularly valuable for subjective pattern interpretations. |
| Case Management Systems | Laboratory Information Management Systems (LIMS) with blinding capabilities | Enforces information control protocols through technical means. | Evidence tracking with information partitioning; Automated workflow management. |
| Statistical Monitoring Tools | Concordance rate tracking; Error rate statistical analysis | Provides quantitative measures of implementation effectiveness and areas for improvement. | Performance benchmarking; Protocol refinement decision support. |
Operationalizing blind verification and case management represents a critical evolution in forensic science practice—one that acknowledges the inherent limitations of human cognition while implementing robust safeguards to ensure analytical objectivity. The frameworks and protocols outlined in this guide provide a roadmap for laboratories committed to enhancing the scientific validity of their outputs and protecting against the insidious effects of cognitive bias.
Successful implementation requires more than procedural changes; it demands a cultural shift toward recognizing that bias mitigation is not about questioning examiner competence but about creating systems that support optimal decision-making. As forensic science continues to evolve in response to scientific scrutiny and legal expectations, blind verification and structured case management will increasingly become hallmarks of truly scientifically rigorous forensic practice.
The success of forensic science depends heavily on human reasoning abilities, yet decades of psychological science research reveals that human reasoning is not always rational [9] [10]. Forensic science often demands that practitioners reason in ways that contradict natural cognitive patterns, creating significant challenges for accuracy and objectivity. The inherent tension between human cognition and forensic requirements manifests differently across forensic disciplines, creating two distinct categories with specialized procedural needs: feature comparison judgments (such as fingerprints or firearms analysis) and causal and process judgments (such as fire scene investigation or pathology) [9] [10].
This technical guide examines the structured protocols necessary for these distinct forensic tasks within the broader context of human reasoning limitations. Despite the weight given to forensic evidence in legal contexts, research indicates that many forensic feature-comparison methods have limited scientific foundations for claims of individualization, with most lacking rigorous empirical validation [34]. Compounding these validity concerns, cognitive biases represent a fundamental challenge across all forensic disciplines, as they are normal decision-making processes that occur automatically outside conscious awareness, potentially leading to erroneous conclusions even among competent experts [11].
Theoretical Framework: Reasoning Challenges in Forensic Decision-Making
Cognitive Architecture and Its Forensic Implications
Human cognition in forensic science operates under predictable constraints that necessitate structured mitigation approaches. Cognitive biases are decision-making shortcuts that activate automatically in situations of uncertainty or ambiguity, where examiners lack sufficient data, time, or both to make fully informed decisions [11]. These biases are not indicators of ethical failure or incompetence; rather, they represent efficient mental strategies that function outside conscious awareness, making them particularly problematic in forensic contexts where absolute accuracy is paramount [11].
The forensic context presents special challenges as practitioners must often reason in "non-natural ways," resisting cognitive patterns that typically serve well in everyday life [9] [10]. This tension between natural cognitive tendencies and forensic requirements creates specific vulnerability points:
- Confirmation bias: The tendency to seek information confirming initial positions or pre-existing beliefs while ignoring contradictory evidence [11]
- Contextual influence: Task-irrelevant information inappropriately influencing forensic judgments [11]
- Source confusion: Multiple potential influences compounding to affect expert decisions [11]
Six Fallacies of Cognitive Bias in Forensic Practice
Research identifies several persistent misconceptions within the forensic community regarding cognitive bias [11]:
Table 1: Common Fallacies About Cognitive Bias in Forensic Science
| Fallacy | Description | Reality |
|---|---|---|
| Ethical Issues Fallacy | Belief that only unethical people experience bias | Bias is a normal cognitive process, unrelated to ethics |
| Bad Apples Fallacy | Assumption that only incompetent examiners are biased | Bias affects all decision-makers regardless of skill level |
| Expert Immunity Fallacy | Belief that expertise protects against bias | Expertise may increase reliance on automatic processes |
| Technological Protection Fallacy | Expectation that technology eliminates bias | Technology is still built and operated by humans |
| Blind Spot Fallacy | Recognition of general bias but denial of personal susceptibility | Nearly everyone exhibits the "bias blind spot" |
| Illusion of Control Fallacy | Belief that awareness alone prevents bias | Bias occurs automatically; willpower is insufficient |
Structured Protocols for Feature Comparison Disciplines
Core Challenges and Methodological Requirements
Feature comparison disciplines (including fingerprints, firearms, toolmarks, and DNA mixture interpretation) involve comparing evidentiary items to known samples to determine source attribution [34]. The primary challenge in these disciplines is avoiding biases from extraneous knowledge or those arising from the comparison method itself [9]. These fields require specialized protocols to manage the interaction between human pattern recognition capabilities and the cognitive vulnerabilities inherent in comparison tasks.
The scientific validity of feature comparison methods depends on four key guidelines adapted from epidemiological frameworks [34]:
- Plausibility: The theoretical foundation justifying predicted actions or results
- Soundness of research design and methods: Construct and external validity
- Intersubjective testability: Replication and reproducibility of findings
- Valid methodology: Reasoning from group data to statements about individual cases
Quantitative Frameworks for Evidence Evaluation
Probabilistic genotyping represents a structured quantitative approach for interpreting complex forensic mixture samples, implementing mathematical models to compute likelihood ratios (LR) that compare probabilities of observations under alternative hypotheses [35]. Different software solutions employ varying approaches:
Table 2: Comparison of Probabilistic Genotyping Software Approaches
| Software | Model Type | Data Utilized | Key Characteristics | Typical LR Output |
|---|---|---|---|---|
| LRmix Studio | Qualitative | Detected alleles (qualitative information) | Lower computational complexity | Generally lower LRs |
| STRmix | Quantitative | Alleles plus peak height (quantitative information) | Higher discriminatory power | Generally higher LRs |
| EuroForMix | Quantitative | Alleles plus peak height (quantitative information) | Open-source alternative | Generally lower than STRmix |
These quantitative approaches demonstrate how structured mathematical frameworks can enhance objectivity in feature comparison disciplines, with studies showing 156 sample pairs producing systematically different probative values depending on the software approach utilized [35].
Cognitive Bias Mitigation Protocol for Feature Comparison
The Department of Forensic Sciences in Costa Rica implemented a comprehensive bias mitigation protocol for questioned document examination that provides a model for feature comparison disciplines [11]. This protocol incorporates:
- Linear Sequential Unmasking-Expanded (LSU-E): Controlling information flow to examiners
- Blind Verifications: Independent analysis without contextual influence
- Case Managers: Filtering task-irrelevant information before examiner exposure
- Structured Documentation: Recording conclusions before additional context exposure
Structured Protocols for Causal and Process Judgment Disciplines
Core Challenges and Methodological Requirements
Causal and process judgment disciplines (including fire investigation, pathology, and crime scene reconstruction) focus on determining the sequence of events, causal mechanisms, or origin points that created evidentiary patterns [9]. The main challenge in these disciplines is maintaining multiple potential hypotheses as investigations proceed, resisting premature closure on a single explanatory narrative [9].
Unlike feature comparison disciplines that match patterns to sources, causal analysis requires constructing explanatory frameworks from disparate pieces of evidence. This demands specialized protocols to manage the complex reasoning processes involved in moving from observations to causal explanations while maintaining scientific rigor.
Hypothesis Management Framework
The fundamental requirement for causal judgment disciplines is maintaining multiple competing hypotheses throughout the investigative process. This approach counters confirmation bias and "tunnel vision" by systematically considering alternative explanations [11]. The framework includes:
- Explicit alternative hypothesis generation: Documenting multiple plausible explanations early in the investigation
- Deductive consequence elaboration: Specifying what each hypothesis predicts should be present in the evidence
- Systematic evidence evaluation: Assessing how each piece of evidence supports or refutes each hypothesis
- Dynamic hypothesis updating: Revising hypothesis probabilities as new evidence emerges
Causal Inference Protocol for Process Reconstruction
Adapted from epidemiological frameworks, causal inference in forensic contexts follows a structured methodology to establish valid conclusions about mechanisms and origins [34]:
Implementation Framework: Standards and Validation
Forensic Science Standards Implementation
The Organization of Scientific Area Committees (OSAC) for Forensic Science maintains a registry of standards to strengthen the nation's use of forensic science, with 178 standards posted across 22 disciplines as of January 2024 [36]. Implementation data reveals variable adoption across the forensic community:
Table 3: Most Frequently Implemented OSAC Registry Standards
| Standard | Number of FSSPs Implementing | Forensic Discipline |
|---|---|---|
| ANSI/ASTM E2329-17 Standard Practice for Identification of Seized Drugs | 98 | Seized Drugs |
| ISO/IEC 17025:2017 General Requirements for the Competence of Testing and Calibration Laboratories | 93 | Interdisciplinary |
| ANSI/ASTM E2548-16 Standard Guide for Sampling Seized Drugs | 91 | Seized Drugs |
| ANSI/ASTM E2917-19a Standard Practice for Forensic Science Practitioner Training | 87 | Interdisciplinary |
| ANSI/ASB Best Practice Recommendation 068, Safe Handling of Firearms and Ammunition | 64 | Firearms/Toolmarks |
Among 150 reporting forensic science service providers (FSSPs), the average number of standards implemented was 15.06 per agency, totaling 2,259 implementation events across all reporting agencies [36].
Validation Requirements for Forensic Methods
Courts applying the Daubert standard require empirical validation of forensic methods, with specific factors for evaluating scientific evidence [34]:
- Empirical testing: Has the method been adequately tested?
- Error rates: What is the known or potential error rate?
- Standards: Do standards exist and were they maintained?
- Peer review: Has the method been published and peer-reviewed?
- Acceptance: Is the method generally accepted in the relevant community?
Despite these requirements, most forensic feature-comparison methods outside of DNA analysis have not been rigorously shown to consistently demonstrate connections between evidence and specific sources with a high degree of certainty [34].
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 4: Essential Materials for Forensic Science Research and Practice
| Item | Function | Application Context |
|---|---|---|
| Probabilistic Genotyping Software (e.g., STRmix, EuroForMix) | Quantifies genetic evidence through likelihood ratio computation | DNA mixture interpretation [35] |
| Linear Sequential Unmasking-Expanded (LSU-E) Framework | Controls contextual information flow to examiners | Cognitive bias mitigation [11] |
| Blind Verification Protocol | Provides independent analysis without contextual influence | Quality assurance across disciplines [11] |
| Hypothesis Management System | Maintains multiple competing explanations during investigation | Causal analysis disciplines [9] |
| Standard Reference Materials | Provides known samples for comparison | Feature comparison disciplines [34] |
| Color Contrast Analyzer | Ensures visual accessibility of documentation | Report preparation and presentation [37] |
| ASTM/EISO Standard Protocols | Provides standardized procedures for specific analyses | Quality assurance across disciplines [36] |
Structured protocols for forensic science must be discipline-specific, addressing the distinct cognitive challenges of feature comparison versus causal judgment tasks. While feature comparison disciplines require robust safeguards against contextual bias and mathematical frameworks for objective evaluation, causal judgment disciplines demand systematic hypothesis management to resist premature closure. Implementation of these protocols requires organizational commitment to standardized procedures, cognitive bias mitigation, and ongoing validation—all supported by the developing infrastructure of forensic science standards. As research continues to illuminate human reasoning challenges in forensic decisions, the evolution of these structured protocols represents the field's commitment to scientific rigor amidst the inherent limitations of human cognition.
Leveraging Mindfulness and Resilience Training to Counteract Cognitive Depletion and Stress
Forensic science decision-making requires an exceptional degree of cognitive precision, yet it occurs within a context of high-stakes pressure that can deplete mental resources and introduce cognitive biases. The challenging nature of forensic work—often involving traumatic material, heavy caseloads, and consequential determinations—makes practitioners particularly vulnerable to stress and cognitive fatigue, which can subsequently impact judgment quality [38]. This technical whitepaper explores the targeted application of mindfulness and resilience training as evidence-based interventions to mitigate these challenges.
Emerging research demonstrates that mindfulness-based interventions (MBIs) induce measurable neuroplastic changes that enhance emotional regulation and cognitive control [39]. Simultaneously, resilience training builds capacity to maintain adaptive functioning under adversity. For forensic scientists and researchers, these practices offer promising approaches to safeguard decision-making integrity against the erosive effects of chronic stress and cognitive depletion.
Theoretical Framework and Neurobiological Mechanisms
Defining the Core Constructs
Mindfulness represents a process of cultivating intentional, non-judgmental awareness of present-moment experiences. This practice is associated with demonstrable improvements in attentional control, emotional regulation, and stress tolerance [39]. In forensic contexts, this translates to enhanced capacity to maintain objective focus on evidence without premature cognitive closure.
Resilience refers to the adaptive capacity to recover from adversity, maintain stable functioning, and engage effective coping strategies when facing stressors [39]. For forensic professionals, resilience enables consistent performance despite exposure to disturbing evidence and high-consequence decisions.
Neuroplastic Changes Induced by Training
Neuroimaging research reveals that structured mindfulness practice induces significant structural and functional changes in brain regions central to cognitive control and emotional regulation:
- Prefrontal Cortex (PFC): Increased cortical thickness enhances executive functions including emotion regulation, planning, and goal-directed behavior [39].
- Anterior Cingulate Cortex (ACC): Enhanced volume and connectivity improves self-regulation and error detection capacity [39].
- Hippocampus: Growth in gray matter density supports memory consolidation and buffers against stress-related neurodegeneration [39].
Functional Neural Network Alterations
Mindfulness and resilience training fundamentally reshape interaction patterns between large-scale brain networks:
- Default Mode Network (DMN): Reduced hyperactivity correlates with decreased rumination and self-referential processing, minimizing intrusive thoughts during forensic analysis [39].
- Salience Network (SN): Improved functionality enables more accurate emotional salience detection and rapid attentional reorientation to relevant stimuli [39].
- Executive Control Network (ECN): Strengthened connectivity supports increased cognitive flexibility and working memory capacity [39].
The diagram below illustrates the impact of mindfulness training on these core brain networks:
Quantitative Evidence Base
Empirical Support for Efficacy
Recent controlled studies provide compelling quantitative evidence for the benefits of mindfulness and resilience training across diverse populations, including professionals in high-stakes fields.
Table 1: Quantitative Outcomes of Mindfulness and Resilience Interventions
| Study Population | Intervention Type | Duration | Key Metric | Results | Effect Size |
|---|---|---|---|---|---|
| University Students [40] | Mindfulness Training | 4 weeks | Academic Resilience | Significant increase in intervention group | PLS-SEM path coefficients significant |
| Corporate Employees [41] | Mindfulness & Positive Psychology | 3 months | Perceived Stress | Significant reduction in stress | Strong evidence (p < 0.05) |
| Corporate Employees [41] | Mindfulness & Positive Psychology | 3 months | Cognitive Flexibility | Significant increase | Strong evidence (p < 0.05) |
| Forensic Inpatients [42] | Mindfulness & Yoga | 8 weeks | Perceived Stress | Significant decrease | ηp² = 0.39 (large) |
| Forensic Inpatients [42] | Mindfulness & Yoga | 8 weeks | Describe Facet of Mindfulness | Significant increase | ηp² = 0.26 (large) |
| Healthy Young Adults [43] | Digital Meditation (MediTrain) | 6 weeks | Sustained Attention | Significant gains | fMRI neural signatures |
| Healthy Young Adults [43] | Digital Meditation (MediTrain) | 6 weeks | Working Memory | Significant improvements | fMRI neural signatures |
Stress-Specific Findings in Forensic Contexts
Research specifically examining forensic populations demonstrates the pronounced impact of mindfulness interventions on stress reduction. A study of forensic inpatients showed that an 8-week mindfulness and yoga training program produced statistically significant decreases in perceived stress with a large effect size (ηp² = 0.39) [42]. Notably, pairwise comparisons revealed a substantial reduction between baseline and post-intervention scores (Hedge's g = 0.70) [42].
The diagram below illustrates the mediating psychological mechanisms identified in experimental research:
Experimental Protocols and Methodologies
Standardized Mindfulness Training Protocol
The following detailed methodology is adapted from evidence-based protocols with demonstrated efficacy in high-stakes environments:
Program Structure:
- Duration: 8 weeks minimum
- Session Frequency: Weekly group sessions (2-2.5 hours)
- Home Practice: Daily guided exercises (45 minutes)
- Retreat: One full-day intensive session (week 6)
Core Curriculum Components:
- Session 1: Psychoeducation on mindfulness concepts and stress management; introduction to seated and walking meditation.
- Session 2: Development of breath and body awareness through guided meditation; exploration of mind-body connections in stress response.
- Session 3: Building consciousness of interconnectedness; recognizing shared human experiences in professional challenges.
- Session 4: Sensory awareness training across five modalities; developing non-reactive observation skills.
- Session 5: Emotional awareness and suffering management; understanding how perception creates distress.
- Session 6: Anger and frustration management skills; maintaining equilibrium in provoking situations.
- Session 7: Thought awareness and cognitive defusion; recognizing that "thoughts are not facts."
- Session 8: Integration of skills; development of maintenance practice plan [42].
Resilience Training Adjunct Protocol
Cognitive-Behavioral Resilience Components:
- Cognitive restructuring of adversarial interpretations
- Values clarification and committed action planning
- Stress inoculation through gradual exposure
- Social support network mapping and utilization
Measurement Protocol:
- Baseline Assessment: Pre-intervention psychological testing
- Process Measures: Weekly practice logs and adherence monitoring
- Post-Intervention: Immediate follow-up assessment
- Long-Term Follow-Up: 3-month and 6-month assessments to evaluate retention
Forensic Context Adaptations
For forensic professionals, specific adaptations enhance relevance and efficacy:
- Case Integration: Use of professionally relevant scenarios in exercises
- Ethical Framework: Explicit connection to forensic ethics and responsibilities
- Bias Mitigation: Direct application to cognitive bias recognition and management
- Organizational Support: Institutional endorsement and participation frameworks
Research Reagent Solutions and Methodological Tools
Table 2: Essential Methodological Tools for Mindfulness and Resilience Research
| Tool Category | Specific Instrument | Primary Function | Validation Evidence |
|---|---|---|---|
| Self-Report Measures | Five Facet Mindfulness Questionnaire (FFMQ) | Assesses observational, descriptive, acting-with-awareness, non-judgmental, non-reactive facets | Validated across clinical and non-clinical populations [42] |
| Self-Report Measures | Perceived Stress Scale (PSS) | Measures subjective appraisals of stressfulness of life situations | Well-validated with established norms [42] |
| Self-Report Measures | Self-Compassion Scale (SCS) | Assesses kindness toward self versus self-judgment | Demonstrates reliability in intervention research [40] |
| Self-Report Measures | Acceptance and Action Questionnaire (AAQ-II) | Measures psychological flexibility and experiential avoidance | Correlates with behavioral measures of flexibility [40] |
| Performance Measures | Computerized Cognitive Battery | Assesses attention, working memory, and cognitive control | Objective performance metrics less susceptible to bias [41] |
| Performance Measures | Incentivized Behavioral Tasks | Measures real decision-making with consequences | Provides ecologically valid assessment [41] |
| Physiological Measures | Heart Rate Variability (HRV) | Indexes parasympathetic nervous system activity | Objective biomarker of stress response [39] |
| Neuroimaging | Structural and Functional MRI | Quantifies gray matter density and functional connectivity | Direct assessment of neuroplastic changes [39] |
| Digital Platforms | MediTrain and Related Apps | Provides standardized intervention delivery with personalization | Demonstrated efficacy in controlled trials [43] |
Technological Innovations and Implementation Frameworks
Emerging Delivery Modalities
Contemporary research explores innovative delivery systems to enhance accessibility and efficacy of mindfulness and resilience training:
Digital Meditation Platforms:
- Adaptive Algorithms: Technology that personalizes difficulty based on performance, as demonstrated in the MediTrain application which adjusts sessions in response to user proficiency [43].
- Real-Time Biofeedback: Integration of wearable sensors measuring heart rate variability (HRV) and electrodermal activity to provide immediate feedback on physiological stress states [39].
Virtual Reality Applications:
- Immersive Environments: VR creates controlled settings for mindfulness practice, with studies showing significant reductions in acute anxiety through nature-based simulations [39].
- Neuroadaptive Feedback: Closed-loop systems where the virtual environment modifies in real-time based on physiological stress indicators [39].
Organizational Implementation Strategy
Successful integration into forensic science environments requires a systematic implementation approach:
Phased Rollout Protocol:
- Leadership Engagement: Secure administrative support and resource allocation
- Pilot Testing: Small-scale implementation with voluntary participants
- Program Evaluation: Rigorous assessment of efficacy and acceptability
- Scaled Implementation: Organization-wide deployment with ongoing support
Fidelity Maintenance:
- Certified instructor training and supervision
- Standardized protocol manuals with local adaptation guidelines
- Regular adherence monitoring and quality assurance
The comprehensive workflow for implementing these interventions in forensic settings is illustrated below:
Mindfulness and resilience training represent empirically-supported approaches to address the critical challenges of cognitive depletion and stress in forensic science decision-making. The neurobiological evidence demonstrates that these practices induce structural and functional brain changes that enhance precisely the cognitive and emotional capabilities most essential to forensic work: sustained attention, cognitive flexibility, emotional regulation, and bias recognition.
The experimental protocols and implementation frameworks outlined in this whitepaper provide a roadmap for integrating these evidence-based practices into forensic science contexts. As research continues to refine our understanding of optimal delivery methods, dosage, and individual differences in response, these interventions offer promising pathways to safeguard both the well-being of forensic professionals and the integrity of forensic decision-making processes.
Applying Dror's Cognitive Framework to Structure Data Collection and Hypothesis Testing
The success of forensic science depends heavily on human reasoning abilities. Decades of psychological science research, however, confirm that human reasoning is not always rational [44] [26]. Forensic science often demands that its practitioners reason in non-natural ways, creating a significant vulnerability to cognitive biases and systematic errors [26]. These biases can infiltrate decisions before, during, and after forensic analyses, potentially undermining the validity of scientific conclusions.
In 2020, cognitive neuroscientist Itiel Dror developed a cognitive framework to address biases influenced by cognitive processes and external pressures in decisions made by forensic experts [45]. This framework highlights how ostensibly objective data can be affected by bias driven by contextual, motivational, and organizational factors [45]. For researchers and scientists, particularly in fields like drug development where decision-making has significant consequences, understanding and applying Dror's framework provides a systematic approach to mitigating these inherent cognitive challenges.
This technical guide adapts Dror's model to structured data collection and hypothesis testing, offering forensic researchers and scientists a practical methodology for improving the fairness and accuracy of scientific assessments. The core thesis is that mitigating cognitive biases requires structured, external strategies, as self-awareness alone is insufficient to guarantee objective outcomes [45].
Dror's Cognitive Framework: Core Concepts
The Six Expert Fallacies
Dror identified six expert fallacies that increase risk for bias, representing cognitive traps even seasoned evaluators believe do not apply to them [45]. The table below summarizes these fallacies and their implications for scientific research.
Table 1: Dror's Six Expert Fallacies and Research Implications
| Fallacy | Core Misconception | Research Implication |
|---|---|---|
| The Unethical Practitioner Fallacy | Only unscrupulous peers driven by greed or ideology are biased [45]. | Vulnerability to cognitive bias is a human attribute, not a character flaw, and affects all researchers regardless of ethics [45]. |
| The Incompetence Fallacy | Biases result only from incompetence or deviations from best practices [45]. | Technically competent studies using validated methods can still conceal biased data gathering or interpretation [45]. |
| The Expert Immunity Fallacy | Experts are shielded from bias merely by being experts [45]. | Expert status may enhance bias risk by promoting cognitive shortcuts and overreliance on preconceived notions [45]. |
| The Technological Protection Fallacy | Technological methods (AI, algorithms, actuarial tools) eliminate bias [45]. | Algorithms and statistical tools are not immune to biasing effects, such as inadequate normative representation skewing data [45]. |
| The Bias Blind Spot | Experts perceive others, but not themselves, as vulnerable to bias [45]. | Because cognitive biases are beyond awareness, experts often fail to recognize their own susceptibility [45]. |
The Pyramidal Structure of Biasing Elements
Dror proposed a pyramidal model demonstrating how biases infiltrate expert decisions through multiple pathways [45]. This structure illustrates how base-level cognitive processes interact with case-specific information and organizational pressures to ultimately influence final evaluations.
Structured Protocols for Data Collection and Analysis
Linear Sequential Unmasking-Expanded (LSU-E)
Linear Sequential Unmasking-Expanded (LSU-E) is a cognitive bias mitigation strategy that controls the flow of information to the expert [45] [20]. This method ensures that domain-irrelevant information is excluded during critical evaluation phases, forcing reliance on System 2 thinking.
Table 2: LSU-E Protocol for Forensic Data Analysis
| Protocol Phase | Procedure | Cognitive Benefit |
|---|---|---|
| Phase 1: Evidence Examination | Examiner analyzes core evidence without contextual case information (e.g., suspect history, witness statements) [20]. | Promotes objective feature detection without contextual priming, reducing confirmation bias [45]. |
| Phase 2: Documentation of Initial Findings | Examiner documents all initial observations, interpretations, and conclusions before proceeding [45]. | Creates an audit trail of unbiased first impressions, anchoring the analysis in actual data rather than expectations. |
| Phase 3: Controlled Contextual Disclosure | Only after documentation are relevant but non-biasing contextual details revealed sequentially [45]. | Allows for integration of necessary context while maintaining primary reliance on objective evidence. |
| Phase 4: Hypothesis Re-evaluation | Examiner reassesses initial conclusions in light of new information, documenting any changes [45]. | Provides transparency regarding which information actually changed the interpretation, identifying potential bias sources. |
Blind Verification Procedures
The Department of Forensic Sciences in Costa Rica successfully implemented a blind verification protocol within its laboratory system [20]. This approach involves a second examiner conducting an independent analysis without knowledge of the first examiner's findings or the case context, effectively creating a controlled experimental condition within the casework process.
Implementing Structured Hypothesis Testing
The Forensic Hypothesis Testing Framework
Hypothesis testing provides a formal procedure for investigating ideas using statistics, ensuring conclusions are based on calculated likelihood rather than intuitive judgment [46]. The standard 5-step procedure, adapted for forensic science applications, creates a rigorous framework for evidential interpretation.
Multiple Hypothesis Maintenance
For causal and process judgments, a main challenge is keeping multiple potential hypotheses open as the investigation continues [26]. Researchers should formally document at least two competing explanations for observed phenomena early in the analytical process and systematically collect evidence for and against each.
The Scientist's Toolkit: Essential Research Reagents
Implementing Dror's framework requires specific methodological "reagents" that serve as essential materials for bias-resistant research.
Table 3: Essential Research Reagents for Cognitive Bias Mitigation
| Research Reagent | Function in Experimental Protocol | Application Context |
|---|---|---|
| Case Manager Protocol | Controls information flow to analysts, acting as an information filter between case investigators and laboratory examiners [20]. | All experimental designs where contextual information could potentially bias outcome measurements. |
| Blind Verification Checklists | Standardizes independent re-analysis procedures to ensure consistency in blinded evaluation protocols [20]. | Quality assurance phases of experimental replication and validation studies. |
| Linear Sequential Unmasking Templates | Provides structured documentation for recording findings at each stage of the unmasking process [45] [20]. | Complex data interpretation tasks where contextual information must eventually be integrated. |
| Hypothesis Testing Framework | Formal procedure for statistically testing predictions while minimizing the role of chance as an explanation [46]. | Data analysis phases where conclusions about relationships between variables must be drawn. |
| Alternative Hypothesis Database | Repository of competing explanations maintained throughout the research process to counter confirmation bias [26]. | Long-term research projects where initial assumptions may prematurely narrow investigative focus. |
Applying Dror's cognitive framework to structure data collection and hypothesis testing represents a paradigm shift from relying on individual expertise to implementing systematic safeguards against inherent cognitive limitations. The protocols outlined—including Linear Sequential Unmasking-Expanded, blind verification procedures, and formal hypothesis testing—provide researchers with practical tools to enhance the scientific rigor of their conclusions.
As the successful pilot program in Costa Rica's Department of Forensic Sciences demonstrates, existing research-based tools can be effectively implemented within laboratory systems to reduce error and bias in practice [20]. For the scientific community, adopting these methodologies addresses fundamental challenges in human reasoning, ultimately leading to more reliable, valid, and defensible research outcomes.
Learning from Error: A Forensic Error Typology for Systemic Improvement
The integrity of the criminal justice system relies heavily on the perceived infallibility of forensic science. However, wrongful convictions persist as a grave travesty, with the National Registry of Exonerations recording over 3,000 cases in the United States as of 2023 [47]. Organizations like the Innocence Project have exonerated 375 people, including 21 who served on death row, often uncovering flawed forensic evidence as a contributing factor [47]. Dr. Jon Gould of the University of California at Irvine has identified faulty forensic science as a significant element in these miscarriages of justice, alongside flawed eyewitness identification, confessions, and testimony [47]. These issues are not confined to the United States; a 2025 parliamentary inquiry in England and Wales described a forensic science sector in a "graveyard spiral," with biased investigations and a rising risk of wrongful convictions due to systemic failures [48].
To address these concerns, forensic scientists at the National Institute of Justice (NIJ) enlisted Dr. John Morgan to analyze the specific causes of errors in forensic science, leading to the development of a forensic error typology [47]. This typology provides a systematic framework for categorizing and understanding the failures that can lead to wrongful convictions, offering a crucial tool for researchers and practitioners aiming to reinforce the scientific foundations of forensic practice and mitigate the impact of human reasoning challenges on forensic decisions.
The NIJ Forensic Error Typology: A Systematic Classification Framework
Dr. Morgan's analysis of 732 cases and 1,391 forensic examinations from the National Registry of Exonerations led to the development of a forensic error typology, a codebook that categorizes errors into five distinct types [47]. This typology is essential for moving beyond merely identifying problems to understanding their root causes and developing targeted, systems-based reforms.
The following table summarizes the five error types in the NIJ typology, which range from technical missteps to systemic failures within the broader justice system.
Table 1: The NIJ Forensic Error Typology
| Error Type | Description | Examples |
|---|---|---|
| Type 1: Forensic Science Reports | A misstatement of the scientific basis of a forensic science examination in a report [47]. | Lab error, poor communication leading to excluded information, resource constraints [47]. |
| Type 2: Individualization or Classification | An incorrect individualization, classification, or interpretation that implies an incorrect association [47]. | Interpretation error or fraudulent interpretation intended to create an association [47]. |
| Type 3: Testimony | Testimony at trial that reports forensic science results in an erroneous manner, whether intended or unintended [47]. | Mischaracterized statistical weight or probability of the evidence [47]. |
| Type 4: Officer of the Court | An error related to forensic evidence created by an officer of the court (e.g., judge, prosecutor) [47]. | Exclusion of evidence, or a judge accepting faulty testimony over objection [47]. |
| Type 5: Evidence Handling and Reporting | A failure to collect, examine, or report potentially probative forensic evidence during investigation or trial [47]. | Broken chain of custody, lost evidence, or police misconduct [47]. |
A key finding from Morgan's work is that most errors related to forensic evidence were not direct identification or classification errors (Type 2) made by forensic scientists [47]. Instead, errors are often distributed across the entire ecosystem, implicating laboratory management, judicial actors, and evidence collection protocols. When forensic scientists do make errors, they are frequently associated with incompetent or fraudulent examiners, disciplines with an inadequate scientific foundation ("junk science"), or organizational deficiencies in training, management, and resources [47].
Quantitative Analysis of Forensic Errors Across Disciplines
The application of the NIJ error typology to a large dataset of exonerations provides a quantitative lens through which to identify the disciplines and practices most prone to failure. Of the 1,391 forensic examinations analyzed, 891 had an error related to the case, while 500 were valid with no associated error [47]. The distribution of these errors is not even across forensic disciplines.
Analysis reveals that specific disciplines have contributed disproportionately to wrongful convictions. The table below summarizes key findings from disciplines with sample sizes greater than 30 examinations, highlighting the percentage of examinations containing any case error and the specific rate of individualization or classification (Type 2) errors.
Table 2: Forensic Error Rates by Discipline
| Discipline | Number of Examinations | Percentage of Examinations Containing At Least One Case Error | Percentage of Examinations Containing Individualization or Classification (Type 2) Errors |
|---|---|---|---|
| Seized drug analysis | 130 | 100% | 100% |
| Bitemark | 44 | 77% | 73% |
| Shoe/foot impression | 32 | 66% | 41% |
| Fire debris investigation | 45 | 78% | 38% |
| Forensic medicine (pediatric sexual abuse) | 64 | 72% | 34% |
| Blood spatter (crime scene) | 33 | 58% | 27% |
| Serology | 204 | 68% | 26% |
| Firearms identification | 66 | 39% | 26% |
| Forensic medicine (pediatric physical abuse) | 60 | 83% | 22% |
| Hair comparison | 143 | 59% | 20% |
| Latent fingerprint | 87 | 46% | 18% |
| Fiber/trace evidence | 35 | 46% | 14% |
| DNA | 64 | 64% | 14% |
| Forensic pathology (cause and manner) | 136 | 46% | 13% |
Several critical insights emerge from this data. Seized drug analysis shows a 100% error rate, but this is almost entirely due to errors in using drug testing kits in the field, not in laboratory analysis [47]. Disciplines like bitemark analysis show extremely high rates of Type 2 errors (73%), indicating a technique with a weak scientific foundation [47]. In contrast, while hair comparison was involved in many cases (143 examinations), its Type 2 error rate was lower (20%); most testimony errors here conformed to historical standards that would not meet current rigorous expectations [47].
The Human Factor: Cognitive Bias as a Core Challenge in Forensic Reasoning
The success of forensic science depends heavily on human reasoning abilities, which are not always rational [9]. Decades of psychological science research confirm that cognitive biases can significantly impact forensic decisions, making the understanding of these biases a central concern for research on wrongful convictions.
Contextual and Automation Bias
Contextual Bias: This occurs when extraneous information inappropriately influences an examiner's judgment. In a seminal study, fingerprint examiners changed 17% of their own prior judgments when they were later provided with contextual information like a suspect's confession or verified alibi [19]. Similar effects have been documented in DNA analysis, where analysts formed different opinions of the same DNA mixture if they knew a suspect had accepted a plea bargain [19]. This bias is particularly potent in difficult or ambiguous cases where the physical evidence is less definitive [19].
Automation Bias: This is the tendency for humans to be overly reliant on metrics generated by technology. In fingerprint analysis, examiners using the Automated Fingerprint Identification System (AFIS) have been shown to spend more time analyzing and more frequently identify whichever print the algorithm randomly placed at the top of the candidate list, regardless of its true match status [19]. This bias undermines the examiner's role as an independent verifier and places undue weight on the algorithm's initial ranking.
An Experimental Protocol for Studying Bias in Facial Recognition
A 2025 study exemplifies rigorous experimental protocols for investigating cognitive bias, here applied to Facial Recognition Technology (FRT) [19].
- Objective: To test whether contextual bias and/or automation bias can distort judgments of FRT search results.
- Participants: 149 participants acting as mock forensic facial examiners.
- Task: Participants completed two simulated FRT tasks. Each task involved comparing a probe image of a "perpetrator" against three candidate faces that the FRT allegedly identified as potential matches.
- Independent Variables:
- Automation bias condition: Each candidate was randomly paired with a high, medium, or low numerical confidence score.
- Contextual bias condition: Each candidate was randomly assigned extraneous biographical information: that they had committed similar crimes, were already incarcerated, or had served in the military (control).
- Dependent Variables: Participants rated each candidate's similarity to the probe and indicated which, if any, was the same person as the perpetrator.
- Findings: Participants rated the candidate randomly paired with guilt-suggestive information or a high confidence score as looking most like the perpetrator. Furthermore, candidates with guilt-suggestive information were most often misidentified as the perpetrator, demonstrating both forms of bias [19].
This protocol provides a model for how to empirically test the influence of specific biasing factors on forensic decision-making.
Research Reagents and Materials: The Scientist's Toolkit
Research into forensic errors and cognitive bias relies on a specific set of "research reagents" and materials. The following table details key components essential for experimental work in this field.
Table 3: Essential Research Materials and Methodologies
| Tool/Material | Function in Research |
|---|---|
| Validated Forensic Datasets | Provides ground-truthed materials for "black box" studies to measure accuracy and reliability of forensic methods [49]. Includes known samples for pattern comparison (e.g., fingerprints, toolmarks) and reference collections for biological evidence. |
| Psychological Task Paradigms | Computer-based protocols for presenting evidence to participants under controlled conditions. Manipulates variables like contextual information and measures outcomes such as similarity ratings and source decisions [19]. |
| Statistical Software for Likelihood Ratios | Computational tools to quantitatively express the weight of evidence, moving away from subjective assertions to a more objective, probabilistic framework [49]. |
| Interlaboratory Study Materials | Identical sets of evidence samples distributed to multiple laboratories to assess the reproducibility and consistency of results across different organizations and practitioners [49]. |
| Simulated Case Files | Comprehensive dossiers containing crime scene details, witness statements, and suspect information. Used to study the effects of task-irrelevant contextual information on expert reasoning [19]. |
Visualizing the Error Ecosystem and Proposed Safeguards
The following diagram illustrates the ecosystem of forensic errors, from crime scene to courtroom, and integrates key procedural safeguards designed to mitigate these errors, such as sequential unmasking and improved standards.
Diagram 1: Forensic Error Ecosystem and Mitigation Framework
The NIJ forensic error typology provides an indispensable framework for systematically diagnosing the failures that lead to wrongful convictions. The quantitative data reveals that errors are not uniformly distributed but are concentrated in specific disciplines like bitemark analysis and field-based drug testing, and often stem from testimony and evidence handling issues rather than pure analytical errors. The pervasive influence of cognitive bias, including contextual and automation biases, represents a fundamental challenge rooted in human reasoning.
Addressing this crisis requires a multi-pronged approach grounded in the research priorities outlined by organizations like NIJ, including the advancement of applied and foundational research, workforce development, and community coordination [49]. Critical steps include the development and enforcement of clear standards through bodies like the Organization of Scientific Area Committees (OSAC) [50], treating wrongful convictions as "sentinel events" that trigger system-wide analysis [47], and implementing procedural safeguards like linear sequential unmasking to mitigate bias [19]. As the field grapples with its identity and mission—balanced between deep contextual understanding and the perils of bias—the continued application of a rigorous, scientific, and critical framework is paramount to restoring public trust and ensuring justice [51].
Forensic science is a critical pillar of the criminal justice system, yet its effectiveness is heavily dependent on human reasoning abilities. Decades of psychological science research confirm that human reasoning is not always rational, and forensic science often demands that practitioners reason in ways that do not come naturally [9]. This whitepaper examines three forensic disciplines—serology, bitemark analysis, and hair comparison—that have been disproportionately associated with wrongful convictions due to systemic vulnerabilities and human reasoning challenges.
Research on wrongful convictions has established that specific forensic disciplines exhibit higher error rates. A comprehensive analysis of 732 cases and 1,391 forensic examinations from the National Registry of Exonerations revealed that errors related to forensic evidence contributed significantly to miscarriages of justice [52]. The National Registry of Exonerations has recorded over 3,000 wrongful convictions in the United States as of 2023, with organizations like the Innocence Project contributing to 375 exonerations, including 21 individuals who served on death row [52].
The inherent challenges in forensic decision-making stem from multiple factors, including cognitive biases, inadequate scientific foundations in certain disciplines, organizational deficiencies, and the complex interaction between individual examiners and their working environments [53] [9]. In feature comparison judgments, such as those employed in hair and bitemark analysis, a primary challenge is avoiding biases from extraneous knowledge or from the comparison method itself [9]. This paper analyzes the specific error profiles, underlying causes, and potential reforms for these high-risk disciplines through the lens of human reasoning limitations.
Quantitative Analysis of Forensic Errors
Analysis of wrongful conviction data reveals distinct patterns across forensic disciplines. The following table summarizes error rates and primary issues identified in recent research:
Table 1: Forensic Discipline Error Analysis in Wrongful Convictions
| Discipline | % of Examinations with Errors | % with Individualization/Classification Errors (Type 2) | Primary Error Types and Contributing Factors |
|---|---|---|---|
| Serology | 68% [52] | 26% [52] | Testimony errors; blood typing misinterpretation; failure to collect reference samples; inadequate defense recognition of exculpatory evidence [52] |
| Bitemark Analysis | 77% [52] | 73% [52] | Invalid scientific foundation; incorrect identifications; examiners often independent consultants outside organizational oversight [52] |
| Hair Comparison | 59% [52] | 20% [52] | Testimony conforming to historical (now outdated) standards; subjective visual matching; FBI review found flawed testimony in >90% of cases [54] |
The data demonstrates concerning patterns across these disciplines. Bitemark analysis shows the highest rate of individualization errors at 73%, indicating fundamental issues with the discipline's foundational principles [52]. Serology errors predominantly involve testimony and interpretation rather than technical analytical errors, highlighting communication and reasoning challenges [52]. Hair comparison errors largely reflect evolving standards, with practices once considered acceptable now recognized as unreliable [52].
Table 2: Forensic Error Typology (Morgan, 2023)
| Error Type | Description | Examples in High-Risk Disciplines |
|---|---|---|
| Type 1: Forensic Science Reports | Misstatement of scientific basis in reports | Laboratory errors; poor communication; resource constraints [52] |
| Type 2: Individualization/Classification | Incorrect individualization/classification or interpretation | Bitemark misidentification; hair comparison false associations [52] |
| Type 3: Testimony | Erroneous presentation of forensic results at trial | Mischaracterized statistical weight or probability; unclear limitations [52] |
| Type 4: Officer of the Court | Legal professional errors related to forensic evidence | Excluded evidence; faulty testimony accepted over objection [52] |
| Type 5: Evidence Handling and Reporting | Failure to collect, examine, or report potentially probative evidence | Chain of custody issues; lost evidence; police misconduct [52] |
Discipline-Specific Analysis and Methodological Flaws
Serology: Blood Typing Limitations and Cognitive Pitfalls
Serology errors in wrongful convictions primarily involve the misinterpretation and miscommunication of blood typing results, known as serological typing [52]. The methodological process involves presumptive and confirmatory tests for biological fluids, followed by ABO blood group system typing and other genetic marker analyses. The limitations arise from the discriminatory power of these tests—while they can exclude individuals, they cannot uniquely identify a specific individual with high certainty due to relatively common blood types in the general population.
Characteristic errors in serology include:
- Inadequate Defense Recognition: Failure to recognize potentially exculpatory evidence that could prove innocence [52]
- Best Practice Failures: Operational shortcomings such as failure to collect appropriate reference samples or conduct confirmatory tests correctly [52]
- Testimony Errors: Exaggerating the evidential value of serological matches without proper statistical foundation or population frequency context [52]
The human reasoning challenge in serology primarily involves contextual bias, where examiners may overstate the significance of an association based on other case information rather than the serological evidence itself.
Bitemark Analysis: Fundamental Scientific Invalidity
Bitemark analysis rests on two unproven assumptions: that human dentition is unique and that human skin can reliably record and preserve this uniqueness [54]. The methodological process involves photographing suspected bitemarks, creating transparent overlays of suspects' dentition, and attempting to match patterns. Research from the National Institute of Standards and Technology (NIST) found no scientific data to support either fundamental assumption [54].
Critical flaws in bitemark analysis methodology include:
- Lack of Uniqueness Validation: No empirical evidence supports the claim of dental uniqueness in pattern transfer to skin [54]
- Unreliable Recording Medium: Skin distorts through healing, swelling, and curvature, making accurate pattern preservation impossible [54]
- Structural Oversight Issues: Bitemark examiners often work as independent consultants outside the structure of forensic science organizations, creating inadequate mechanisms for enforcement of standards [52]
The reasoning challenge involves confirmation bias, where examiners may seek to confirm a suspected match rather than objectively test the hypothesis. Bitemark analysis has been associated with a disproportionate share of incorrect identifications and wrongful convictions [52].
Hair Comparison: Subjective Pattern Recognition
Microscopic hair comparison involves visual matching of hair samples based on microscopic characteristics including color, texture, medullary structure, and pigment distribution [54]. The method is inherently subjective, with no validated standards for declaring a match. The FBI has acknowledged that in over 90% of cases reviewed, examiners provided flawed testimony regarding hair evidence [54].
Methodological limitations in hair comparison include:
- Subjectivity in Pattern Matching: Lack of objective, quantifiable criteria for determining matches [54]
- Testimony Conforming to Outdated Standards: Most testimony errors conformed to standards recognized at the time of trial but would not conform to current scientific standards [52]
- Inadequate Statistical Foundation: Failure to properly communicate the limited probative value of hair associations
The primary reasoning challenge involves overclaiming, where examiners may testify beyond the method's actual capabilities, often failing to adequately communicate the method's limitations and the potential for error.
Visualizing the Error Pathway in High-Risk Forensic Disciplines
The following diagram illustrates the systematic pathway through which human reasoning errors and methodological flaws contribute to wrongful convictions in high-risk forensic disciplines:
This systematic pathway demonstrates how initial methodological limitations interact with cognitive biases and organizational factors throughout the forensic process, ultimately leading to erroneous conclusions that the legal system may fail to correct.
Experimental Protocols for Validation Studies
Protocol for Bitemark Analysis Validity Testing
Objective: To empirically test the fundamental assumptions underlying bitemark analysis: (1) uniqueness of human dentition patterns, and (2) reliability of skin as a recording medium.
Materials:
- Dental casts from 500 diverse participants
- Synthetic skin substrate with biomechanical properties similar to human skin
- Pressure sensors to standardize application force
- Digital imaging system with standardized lighting
- Blinded examiner panel (n=20) with varying experience levels
Methodology:
- Create standardized bitemark impressions using a calibrated pressure application device
- Generate random pairings of bitemarks and dental casts (n=1000 pairings)
- Administer sequential examinations where examiners assess match/non-match for each pairing
- Counter-balance presentation order to control for context effects
- Collect confidence ratings for each judgment
- Analyze using signal detection theory to calculate discriminability (d') and response bias
- Conduct similarity analysis of dental patterns using computational geometry approaches
Validation Metrics:
- Sensitivity and specificity calculations
- Receiver Operating Characteristic (ROC) curves
- Inter-rater reliability using intraclass correlation coefficients
- False positive and false negative rates across confidence levels
This protocol addresses the NIST findings regarding the lack of scientific data supporting bitemark analysis fundamentals [54].
Protocol for Hair Comparison Reliability Testing
Objective: To establish error rates and sources of variability in microscopic hair comparison.
Materials:
- Reference hair samples from 200 donors (with DNA confirmation)
- Unknown hair samples from crime scene simulations
- Standardized microscopy equipment with digital imaging
- Blinded examiner cohort (n=30) representing different laboratories
- Statistical analysis software for pattern recognition algorithms
Methodology:
- Create a balanced design with matching and non-matching pairs
- Implement double-blind procedures to eliminate contextual information
- Incorporate proficiency testing throughout the study period
- Collect both categorical judgments (match/non-match/inconclusive) and continuous similarity ratings
- Analyze sources of variability using generalizability theory
- Compare microscopic findings with DNA analysis results as ground truth
Validation Metrics:
- False positive rate (primary outcome)
- False negative rate
- Inconclusive rate variability
- Between-examiner agreement statistics
- Within-examiner consistency over time
This protocol addresses the known issues with microscopic hair comparison, where the FBI found flawed testimony in over 90% of reviewed cases [54].
Reform Framework: The Scientist's Toolkit
Addressing the systemic issues in high-risk forensic disciplines requires a multifaceted approach targeting methodological, cognitive, and organizational vulnerabilities. The following table outlines essential components of a reform toolkit:
Table 3: Research and Reform Toolkit for High-Risk Forensic Disciplines
| Toolkit Component | Function | Application Example |
|---|---|---|
| Sentinel Event Review | Systematically analyzes errors to identify root causes rather than individual blame [52] | Treat wrongful convictions as learning cases to elucidate system deficiencies within specific laboratories [52] |
| Cognitive Bias Mitigation | Implements procedures to minimize contextual and confirmation biases during analysis [9] | Use linear sequential unmasking where case information is revealed gradually only as needed for analysis |
| Blinded Proficiency Testing | Assesses examiner competency without their knowledge to obtain authentic performance measures | Incorporate ongoing proficiency testing as part of quality assurance programs |
| Method Validation Studies | Empirically establishes the reliability and error rates of forensic techniques [54] | Conduct black-box studies to determine actual performance characteristics of methods like bitemark analysis |
| Standardized Terminology | Creates consistent language for reporting and testimony to prevent overstatement | Implement standardized statements that accurately convey the limitations of forensic evidence |
| Statistical Foundation | Provides quantitative frameworks for expressing the strength of forensic evidence | Develop population frequency data and likelihood ratios for evidence interpretation |
The persistence of wrongful convictions linked to serology, bitemark analysis, and hair comparison reveals fundamental challenges at the intersection of human cognition and forensic practice. In approximately half of wrongful convictions analyzed, improved technology, testimony standards, or practice standards might have prevented the erroneous outcome at the time of trial [52]. The reform imperative requires nothing less than a paradigm shift from experience-based claims to empirically validated forensic practices.
This transformation demands coordinated action across multiple domains: rigorous scientific validation of forensic methods, implementation of cognitive bias countermeasures, structural reforms within forensic organizations, and enhanced legal safeguards against unreliable evidence. As Dr. John Morgan's research indicates, the development and enforcement of clear standards within each forensic science discipline, along with governance structures to enforce such standards, will minimize wrongful convictions and strengthen public trust in the criminal justice system [52]. The scientific community has both the responsibility and capability to advance these reforms, ensuring forensic evidence serves justice rather than undermines it.
Within the high-stakes domain of criminal justice, forensic science is intended to be a pillar of objective truth. However, its effectiveness is entirely dependent on the integrity of its processes and the reasoning of its practitioners. Research indicates that human reasoning challenges are a critical, often unaddressed, vulnerability in forensic science, leading to errors that can result in grave miscarriages of justice [1]. The National Registry of Exonerations has recorded over 3,000 wrongful convictions in the United States, with a significant portion involving false or misleading forensic evidence [52] [55]. This whitepaper provides a technical guide for researchers and scientists, dissecting the core error types—individualization mistakes, testimony misstatements, and evidence handling failures—within the framework of human cognition and system design. By understanding these errors at a granular level, the scientific community can develop more robust, error-resistant protocols and reagents to safeguard the integrity of forensic science.
A Typology of Forensic Error
Systematic analysis of wrongful convictions has enabled the development of a forensic error typology, which categorizes factors contributing to erroneous outcomes [52]. This structure is essential for cataloging past problems and developing targeted, systems-based reforms. The following table summarizes the primary error types and their characteristics.
Table 1: Forensic Error Typology
| Error Type | Description | Common Examples |
|---|---|---|
| Type 1: Forensic Science Reports | A misstatement of the scientific basis of a forensic examination in a formal report [52]. | Lab error, poor communication (e.g., excluded information), resource constraints [52] [55]. |
| Type 2: Individualization or Classification | An incorrect individualization/classification of evidence or an incorrect interpretation of a result that implies a false association [52]. | Interpretation error, fraudulent interpretation of an association [52] [55]. |
| Type 3: Testimony | Testimony at trial that presents forensic science results in an erroneous manner [52]. | Mischaracterized statistical weight or probability; testimony that overstates the certainty of results [52] [56]. |
| Type 4: Officer of the Court | An error related to forensic evidence created by an officer of the court (e.g., judge, prosecutor) [52]. | Excluded exculpatory evidence, acceptance of faulty testimony over objection [52] [56]. |
| Type 5: Evidence Handling and Reporting | A failure to collect, examine, or report potentially probative forensic evidence during investigation or trial [52]. | Chain of custody breaks, lost evidence, police misconduct [52] [57] [55]. |
Individualization and Classification Errors (Type 2)
Core Concept and Experimental Data
Individualization or classification errors represent a fundamental failure in forensic analysis, where evidence is incorrectly tied to a specific person or source. A comprehensive study of 1,391 forensic examinations from wrongful conviction cases revealed that these errors are not uniformly distributed across disciplines [52]. The prevalence of these errors is often tied to disciplines with an inadequate scientific foundation, incompetent or fraudulent examiners, or organizational deficiencies in training and governance [52] [58].
The quantitative data from the study illustrates the disproportionate contribution of certain disciplines to individualization errors.
Table 2: Prevalence of Individualization/Classification Errors by Discipline [52]
| Forensic Discipline | Number of Examinations | Percentage with Individualization/Classification (Type 2) Errors |
|---|---|---|
| Seized drug analysis* | 130 | 100% |
| Bitemark comparison | 44 | 73% |
| Shoe/foot impression | 32 | 41% |
| Forensic medicine (pediatric sexual abuse) | 64 | 34% |
| Serology | 204 | 26% |
| Firearms identification | 66 | 26% |
| Hair comparison | 143 | 20% |
| Latent fingerprint | 87 | 18% |
| DNA | 64 | 14% |
| Forensic pathology (cause and manner) | 136 | 13% |
Note: The high error rate in seized drug analysis was primarily due to errors using drug testing kits in the field, not in laboratory settings [52].
Underlying Human Reasoning Challenges
The human mind excels at automatically integrating information from multiple sources to create coherent patterns and causal stories [1]. While this is a strength in many contexts, it is a critical weakness in forensic individualization, which demands objective, context-independent analysis.
- Similarity Judgments in Feature Comparison: Disciplines like fingerprints, bitemarks, and toolmarks rely on feature comparison. A primary challenge is avoiding biases from extraneous knowledge or from the comparison method itself [1]. For example, an analyst's judgment about whether a latent print matches a suspect's print can be unconsciously influenced by knowing the suspect has confessed, a phenomenon related to cognitive impenetrability, where prior knowledge biases perception even when the analyst knows it should not [1].
- Categorical Reasoning: Analysts use categories (e.g., "match," "inconclusive," "exclusion") based on learned features. Errors can occur when the training set is not representative of real-world variability, when features are weighted incorrectly, or when pre-existing beliefs about the case influence the categorization process [1].
Detailed Experimental Protocol: Bitemark Analysis
Bitemark analysis exemplifies a discipline with a high rate of individualization errors, as shown in Table 2. The following protocol outlines a typical, though flawed, methodology that has contributed to wrongful convictions [52] [59].
- Objective: To determine if a bitemark on a victim or object can be individually associated with the dentition of a specific suspect.
- Materials:
- Evidence: High-resolution photographs of the bitemark on skin or an object (scale included).
- Reference: Dental impressions and corresponding stone casts of the suspect's dentition.
- Reagents: Transparent acetates, digital calipers, imaging software (e.g., Adobe Photoshop).
- Methodology:
- Evidence Collection: The bitemark is photographed multiple times with and without scale under various lighting conditions. If on skin, the examination may be repeated over several days as the bruise evolves.
- Reference Creation: A dentist takes dental impressions of the suspect's teeth using polyvinyl siloxane. Stone casts are then poured and trimmed.
- Comparison: The analyst creates tracings or digital overlays of the suspect's dentition from the casts. These overlays are then compared to the life-sized photographs of the bitemark, looking for correspondences in tooth position, spacing, rotation, and unique features.
- Interpretation: The analyst renders an opinion on the degree of agreement, often using a subjective scale from "excluded" to "high degree of certainty."
- Inherent Vulnerabilities: This method is highly susceptible to cognitive bias because the analyst is typically not blind to the suspect's identity or other case context. Furthermore, the underlying premise—that human dentition is unique and can be accurately recorded and transferred to skin—lacks a solid scientific foundation and validation, making it a form of "junk science" [52] [60] [59].
Testimony Misstatements (Type 3)
Core Concept and Manifestations
Testimony errors occur when expert witnesses present forensic findings in an erroneous manner during trial proceedings. These misstatements, whether intentional or unintentional, distort the perception of scientific evidence presented to the trier of fact [52] [55]. Common manifestations include:
- Exaggerating Statistical Certainty: Presenting probabilistic evidence as definitive proof [52] [56].
- Misstating Scientific Principles: Making incorrect claims about foundational science, as seen in the Joe Bryan case where a blood-spatter analyst erroneously testified that "human blood has its own characteristic geometric patterns" [61].
- Failing to Clarify Limits: Not explaining the possibilities of secondary transfer (e.g., for gunshot residue) or uncertainties in interpretation [52].
- Using Unvalidated Methods: Providing opinions based on techniques that lack foundational and applied validity, as highlighted by the President’s Council of Advisors on Science and Technology (PCAST) report [62].
Experimental Protocol: Auditing Testimony for Misstatements
Researchers can systematically identify testimony errors by conducting a retrospective audit of trial transcripts. This methodology is crucial for understanding the scope of the problem and advocating for reformed testimony standards.
- Objective: To identify, categorize, and quantify misstatements in forensic expert testimony from past trials that resulted in exoneration.
- Materials:
- Primary Source: Complete trial transcripts and appellate court opinions for cases listed in the National Registry of Exonerations.
- Reference Materials: Current standards and guidelines from scientific bodies (e.g., OSAC, PCAST reports), relevant scientific literature, and laboratory standard operating procedures (SOPs) contemporary to the trial.
- Methodology:
- Blinded Review: A subject-matter expert reviews the forensic testimony sections of the transcript, initially blinded to the case outcome and the identity of the testifying expert.
- Coding: The reviewer codes each statement against the reference materials for:
- Factual Accuracy: Is the statement scientifically correct?
- Context & Limitations: Does the testimony properly contextualize the findings and explain the limitations of the method, including error rates?
- Exaggeration: Does the testimony use unscientific, absolute terms like "match," "identity," or "100% certain" when the discipline is inherently probabilistic?
- Analysis: Coded statements are analyzed to determine the frequency and type of misstatements per case and per discipline.
- Case Illustration: In the case of Joe Bryan, a re-investigation found the blood-spatter testimony was "egregiously wrong," "not accurate or scientifically supported," and involved a detective misstating scientific concepts and using flawed methodology [61].
Evidence Handling and Reporting Failures (Type 5)
Core Concept and Systemic Impact
This error category encompasses failures in the chain of evidence custody, the loss or destruction of physical evidence, and the failure to report or collect potentially probative forensic material [52] [55]. These are often systemic failures that occur outside the forensic laboratory but have a direct impact on the ability to achieve a just outcome. They undermine the very foundation upon which reliable forensic analysis is built.
- Chain of Custody Gaps: Meticulous documentation of everyone who handles evidence is required for admissibility. Gaps or inconsistencies in this record can be powerful tools for challenging evidence integrity [57] [56].
- Evidence Contamination: Improperly secured crime scenes or improper evidence handling by law enforcement or lab technicians can introduce foreign DNA or degrade original samples, rendering analysis unreliable [62] [57]. The Amanda Knox case is a prime example, where police did not wear proper protective gear, leading to cross-contamination of evidence [62].
- Preservation Failures: Biological samples require strict temperature control to prevent degradation. Failure to preserve evidence properly can destroy its value and admissibility [57].
- Suppression of Exculpatory Evidence: Investigators or prosecutors may discount or ignore forensic results that do not fit their theory of the case, a violation of due process [52] [60].
Visualizing the Forensic Evidence Lifecycle and Failure Points
The following diagram maps the pathway of forensic evidence through the criminal justice system, highlighting critical points where Type 5 (Evidence Handling) and other errors are most likely to occur.
The Scientist's Toolkit: Research Reagents for Error Mitigation
Addressing the human reasoning challenges in forensic science requires a toolkit of methodological "reagents"—procedural interventions and research tools designed to increase reliability and minimize error.
Table 3: Essential Research Reagents for Forensic Science Research
| Research Reagent / Tool | Primary Function | Application in Error Mitigation |
|---|---|---|
| Blinded Testing Protocols | To prevent contextual information from influencing an analyst's judgment [1]. | Mitigates cognitive bias in individualization and classification tasks (Type 2 errors). |
| Linear Sequential Unmasking | A structured procedure where evidence is examined without biasing context, which is only introduced sequentially after initial findings are recorded [1]. | Reduces the risk of confirmation bias in feature-comparison disciplines (Type 2 errors). |
| Error Rate Quantification Studies | To empirically establish the frequency of false positives/negatives for a given method or practitioner. | Provides critical data to contextualize testimony and prevent overstatement of certainty (Type 3 errors). |
| Standardized Statistical Reporting | To provide a framework for communicating the weight of evidence using validated statistical models (e.g., likelihood ratios). | Prevents testimony misstatements about probabilistic findings (Type 3 errors). |
| Chain of Custody Digital Platforms | To create an immutable, auditable record of every person who handles a piece of evidence. | Reduces evidence handling and reporting failures (Type 5 errors) by eliminating documentation gaps. |
| Sentinel Event Review | A high-reliability industry practice of conducting root-cause analysis after a grievous error [52]. | Allows forensic organizations to treat wrongful convictions as learning opportunities to address system-wide deficiencies. |
The distinction between individualization mistakes, testimony misstatements, and evidence handling failures is not merely academic; it is a critical first step in diagnosing and curing the systemic ailments that lead to wrongful convictions. As the research shows, these errors are frequently not the result of isolated incompetence but are born from a complex interaction between human reasoning flaws—such as the automatic, unconscious integration of biasing context—and systemic vulnerabilities in training, governance, and methodology [52] [1]. For researchers and scientists, the path forward is clear: the development and strict enforcement of validated scientific standards, the implementation of blinding and other procedural "reagents" to counter cognitive bias, and the cultivation of a culture that treats errors as sentinel events for continuous improvement. By framing forensic science as a high-reliability field on par with air traffic control or medicine, the community can strengthen the scientific foundation of justice and restore public trust.
Within the broader context of human reasoning challenges in forensic science, the concept of treating errors as invaluable learning opportunities is paramount. A "sentinel event" is a significant, unexpected occurrence involving death or serious physical or psychological injury, signaling a fundamental weakness in the system. This whitepaper proposes a formalized Sentinel Event Analysis framework for forensic science, adopting principles from High-Reliability Organizations (HROs) like aviation and nuclear power. These industries excel in high-risk environments by maintaining exceptionally low failure rates through specific cultural and operational principles. This guide details the integration of HRO principles with experimental protocols for error rate quantification and cognitive bias mitigation, providing researchers and practitioners with a structured pathway to enhance the reliability and validity of forensic decision-making.
Forensic science is at a pivotal juncture. Research indicates that faulty forensic science is a contributing factor in wrongful convictions, with over 3,000 documented cases in the United States alone [52]. The National Registry of Exonerations records numerous cases associated with "false or misleading forensic evidence," stemming from problems ranging from simple mistakes and invalid techniques to outright fraud [52]. These incidents are not merely isolated failures; they are symptomatic of systemic vulnerabilities that require a fundamental shift in how forensic laboratories and practitioners manage error and uncertainty.
The core thesis of this research is that the inherent challenges of human reasoning—including cognitive biases, subjective judgment in pattern-matching disciplines, and organizational pressures—represent a critical vulnerability in forensic science. To address this, the field must move beyond a culture that often perceives error as a personal failing and instead adopt the mindset of High-Reliability Organizations (HROs). HROs are entities that operate in complex, high-risk environments yet consistently achieve exceptional safety and performance records [63] [64]. The foundational HRO principles, as identified by researchers at Berkeley, are Preoccupation with Failure, Reluctance to Simplify, Sensitivity to Operations, Commitment to Resilience, and Deference to Expertise [63]. This paper provides a technical guide for translating these principles from theoretical concepts into actionable, measurable protocols within forensic science practice, thereby creating a robust defense against the frailties of human reasoning.
Quantitative Foundations: Error Analysis in Forensic Science
A data-driven approach is essential for targeting improvement efforts. Analysis of wrongful conviction cases reveals specific forensic disciplines and error types that are disproportionately associated with erroneous outcomes.
Table 1: Forensic Discipline Error Analysis from Exoneration Cases [52]
| Discipline | Number of Examinations | Percentage of Examinations Containing At Least One Case Error | Percentage of Examinations Containing Individualization/Classification Errors (Type 2) |
|---|---|---|---|
| Seized drug analysis | 130 | 100% | 100% |
| Bitemark | 44 | 77% | 73% |
| Forensic medicine (pediatric physical abuse) | 60 | 83% | 22% |
| Serology | 204 | 68% | 26% |
| Hair comparison | 143 | 59% | 20% |
| DNA | 64 | 64% | 14% |
| Latent fingerprint | 87 | 46% | 18% |
| Forensic pathology (cause and manner) | 136 | 46% | 13% |
A critical finding is that most errors related to forensic evidence are not pure identification or classification errors. A comprehensive typology categorizes the root causes of these failures, providing a framework for systematic analysis and intervention [52].
Table 2: Forensic Evidence Error Typology [52]
| Error Type | Description | Examples |
|---|---|---|
| Type 1 – Forensic Science Reports | A misstatement of the scientific basis of an examination. | Lab error, poor communication, resource constraints. |
| Type 2 – Individualization or Classification | An incorrect individualization, classification, or interpretation. | Interpretation error, fraudulent interpretation. |
| Type 3 – Testimony | Testimony that reports results in an erroneous manner. | Mischaracterized statistical weight or probability. |
| Type 4 – Officer of the Court | An error created by an officer of the court. | Excluded evidence, faulty testimony accepted over objection. |
| Type 5 – Evidence Handling and Reporting | A failure to collect, examine, or report potentially probative evidence. | Chain of custody breaks, lost evidence, police misconduct. |
Understanding that "error is subjective" and "multidimensional" is the first step in managing it effectively [65]. Different stakeholders may define error differently, and a single case can involve multiple, overlapping error types.
The High-Reliability Organization (HRO) Framework
HROs achieve safety in complex environments through a disciplined culture focused on anticipating and containing unexpected events [64] [66]. The following five principles form the cornerstone of this approach and are directly applicable to forensic science.
The Five Principles of HROs
- Preoccupation with Failure: HROs treat any small failure or near-miss as a symptom of a larger system weakness and an opportunity for learning. They are proactively fixated on how processes could fail, even when no adverse outcome has occurred [63] [64]. In a forensic context, this means encouraging the reporting of minor deviations, near-misses in analysis, and procedural hiccups without fear of blame.
- Reluctance to Simplify: HROs reject simple, superficial explanations for problems. They embrace the complexity of their operations and insist on conducting thorough root cause analyses to understand the underlying, systemic factors contributing to an error [63] [64]. For forensic labs, this means looking beyond "human error" to investigate flawed protocols, inadequate training, resource constraints, or cognitive biases.
- Sensitivity to Operations: HROs maintain a constant, nuanced awareness of the state of frontline operations by those doing the work. Leaders stay connected to the real-time experiences of frontline personnel, who possess the most immediate understanding of potential risks and operational challenges [63] [66]. For forensic lab managers, this involves regular communication with examiners and technicians about workflow obstacles and potential sources of error.
- Commitment to Resilience: HROs assume that errors will occur and therefore invest in designing systems that can absorb, contain, and recover from them. Resilience is built through training, cross-functional teamwork, and the capacity to improvise solutions when faced with the unexpected [63] [64]. In forensics, this translates to robust quality control procedures, redundancy in critical analysis steps, and clear protocols for halting and reviewing work when a problem is suspected.
- Deference to Expertise: During a crisis or when facing an unexpected situation, HROs defer decision-making authority to the person with the most relevant expertise, regardless of their hierarchical rank. This requires leaders to know who possesses what specialized knowledge [63] [64]. In a forensic lab, a junior examiner with specific expertise in a novel analytical technique may be the best person to lead the response to a related technical problem.
HRO Implementation and Sentinel Event Analysis Workflow
Implementing HRO principles requires a structured approach. The following workflow visualizes the integrated process of responding to a sentinel event, from initial detection to the implementation of systemic reforms, all undergirded by the five HRO principles.
Experimental Protocols for Quantifying and Mitigating Error
To support the HRO framework, forensic science must adopt rigorous, empirical methods to quantify error rates and identify their sources. The following protocols provide a foundation for this research.
Protocol 1: Black-Box Study for Measuring Accuracy and Reliability
Objective: To measure the foundational accuracy and reliability of a forensic method by assessing the performance of examiners without exposing the internal decision-making process.
Methodology:
- Sample Selection: A set of ground-truth known evidence pairs is created. These include matching pairs (same source) and non-matching pairs (different sources), with the ground truth concealed from participants.
- Participant Recruitment: Certified forensic practitioners from the relevant discipline are recruited.
- Blinded Presentation: Participants are presented with the evidence pairs via a controlled software interface and are asked to make a determination (e.g., identification, exclusion, or inconclusive) for each pair.
- Data Collection: Responses are collected automatically. Key metrics include:
- False Positive Rate: Proportion of non-matching pairs incorrectly reported as an identification.
- False Negative Rate: Proportion of matching pairs incorrectly reported as an exclusion or inconclusive.
- True Positive and True Negative Rates.
- Inconclusive Rate.
Analysis: Results are analyzed to compute overall error rates and measures of inter-examiner reliability. This protocol is explicitly highlighted in the NIJ's Forensic Science Strategic Research Plan under "Decision Analysis" as a means to "measure the accuracy and reliability of forensic examinations" [49].
Objective: To identify the specific cognitive and procedural factors that contribute to errors, moving beyond mere rate calculation to understanding causation.
Methodology:
- Stimuli with Biasing Context: A set of challenging evidence pairs is selected. For a subset of these pairs, participants are exposed to task-irrelevant, potentially biasing information (e.g., "the suspect has confessed," or "another examiner has already made an identification").
- Think-Aloud Protocol: Participants are instructed to verbalize their thought process, observations, and reasoning as they conduct the analysis. These sessions are audio-recorded and transcribed.
- Eye-Tracking: An eye-tracker is used to record participants' gaze patterns, identifying which features of the evidence they attend to and for how long.
- Post-Task Interview: A structured interview is conducted to explore the examiner's confidence and the factors that most influenced their decision.
Analysis: Qualitative analysis of think-aloud transcripts is coded for themes such as hypothesis generation, confirmation seeking, and the influence of contextual information. Eye-tracking data is analyzed to see if attention is skewed by biasing information. Quantitative analysis compares error rates between biased and non-biased conditions. This protocol directly addresses the NIJ's priority to conduct research that "identif[ies] sources of error (e.g., white box studies)" and evaluates "human factors" [49].
The Scientist's Toolkit: Reagents and Materials for HRO Implementation
Transitioning to a high-reliability model requires specific "reagents" and tools. The following table details key solutions for building a more reliable and resilient forensic science system.
Table 3: Essential Research and Implementation Tools for HRO in Forensics
| Tool / Solution | Function / Purpose | Example in Practice |
|---|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | A procedural safeguard to mitigate cognitive bias by controlling the flow of information to the examiner. Irrelevant contextual information is withheld until after the initial evidential comparison is complete [11]. | A fingerprint examiner first compares a latent print to a reference print without knowing which suspect it came from or other investigative details. Their results are documented before any potentially biasing context is revealed. |
| Blind Verification | A quality control procedure where a second, verifying examiner conducts an independent analysis without knowledge of the first examiner's conclusion. | After Examiner A documents their conclusion, the case is assigned to Examiner B, who performs the analysis anew without access to A's notes or result, preventing "conformity bias." |
| Case Manager Role | An administrative role designed to act as an information filter between investigators and forensic examiners. The Case Manager receives all case information but provides examiners only with the data essential for their analysis [11]. | The Case Manager redacts investigative reports, providing examiners with only the specific items for comparison and no information about suspects, confessions, or other evidence. |
| Proficiency Testing & Sentinel Event Simulation | Tools for assessing individual and laboratory performance. This includes traditional proficiency tests and the creation of realistic "sentinel event" scenarios to test the laboratory's response and resilience protocols. | A laboratory intentionally introduces a challenging case with a known ground truth into its workflow to test if its quality control systems can detect and correct a potential error. |
| Standardized Likelihood Ratio Framework | A mathematical and logical framework for interpretation and reporting that aims to quantify the strength of evidence in a more transparent and logically valid manner. | Instead of testifying that two samples "match," an examiner reports: "The observed features are 10,000 times more likely if the samples originated from the same source than if they originated from different sources." [67] |
| Cognitive Bias Fallacy Training Materials | Educational resources to combat common misconceptions, such as the "Expert Immunity" and "Bias Blind Spot" fallacies, fostering a culture that acknowledges universal vulnerability to bias [11]. | Interactive training sessions that use real-world case studies (e.g., the Brandon Mayfield misidentification) to demonstrate how cognitive bias can impact even highly experienced experts. |
A Practical Implementation Model: Cognitive Bias Mitigation Protocol
The following diagram synthesizes several tools from the Scientist's Toolkit into a unified, practical workflow for handling a forensic case in a manner that embeds HRO principles and proactively mitigates cognitive bias.
This structured protocol, piloted successfully in the Questioned Documents Section of the Department of Forensic Sciences in Costa Rica, demonstrates that practical changes can systematically reduce subjectivity and enhance the reliability of forensic evaluations [11].
The integration of Sentinel Event Analysis with the principles of High-Reliability Organizations presents a transformative roadmap for forensic science. By adopting a preoccupation with failure, a reluctance to simplify root causes, and a structured approach to mitigating cognitive bias through protocols like Linear Sequential Unmasking and blind verification, the field can directly address the critical human reasoning challenges at the heart of its mission. The experimental protocols and practical tools outlined in this guide provide a scientific basis for this transformation, enabling researchers and laboratory managers to quantify error, build resilience, and ultimately foster greater trust in the criminal justice system. The journey toward high reliability is continuous, requiring sustained commitment, but the path forward is now clearly marked by the successes of other high-risk fields and the growing body of research within forensic science itself.
Within the high-stakes domain of forensic science, organizational deficiencies in training, management, and resource allocation present significant risks to decision-making quality and error prevention. Forensic scientists operate in dynamic environments characterized by common workplace pressures such as high workload volume, tight deadlines, and fluctuating priorities, compounded by industry-specific stressors including technique criticism, repeated exposure to traumatic case details, and a zero-tolerance culture for errors [53]. These human factors directly impact forensic decision-making, yet many organizations focus predominantly on technical proficiency while neglecting the systemic and cognitive dimensions of error prevention. This whitepaper examines how evidence-based management practices, strategic training methodologies that leverage errors, and optimized resource allocation can collectively address these organizational deficiencies. Framed within broader research on human reasoning challenges, we propose an integrated framework for building more resilient forensic science organizations capable of mitigating errors at their source.
Human Factors and Workplace Stress in Forensic Decision-Making
Organizational Stressors and Their Impact on Forensic Accuracy
Forensic science workplaces contain a unique constellation of stressors that directly impact decision-making quality. Research identifies two primary categories of pressures: general workplace stressors and industry-specific stressors. The combination creates an environment where cognitive resources are depleted, potentially compromising forensic accuracy [53].
Table 1: Organizational Stressors in Forensic Science Environments
| General Workplace Stressors | Industry-Specific Stressors | Impact on Decision-Making |
|---|---|---|
| Workload volume & tight deadlines | Technique criticism & validation challenges | Cognitive fatigue & reduced attention |
| Lack of advancement opportunities | Repeated exposure to traumatic case details | Emotional exhaustion & desensitization |
| Number of working hours & overtime | Adversarial legal system pressures | Premature closure & confirmation bias |
| Low salary structures | Zero tolerance for errors | Excessive risk aversion & defensive practices |
| Technology distractions & system limitations | Access to funding & resource constraints | Compromised evidence analysis & procedural shortcuts |
The impact of these stressors extends beyond individual well-being to directly affect organizational outcomes. Workplace stress functions as a critical human factor that must be mitigated for overall error management, productivity, and decision quality [53]. Without systematic interventions, these pressures create environments where cognitive biases thrive and analytical accuracy diminishes.
Cognitive Biases in Forensic Evidence Analysis
Human cognition inherently employs mental shortcuts (heuristics) that create vulnerability to biases in forensic analysis. Research indicates that humans naturally see what they expect to see and tend to seek out and interpret information in ways that confirm pre-existing beliefs [8]. For forensic examiners, this may manifest when analyzing fingerprints, shoeprints, or other comparative evidence where prior knowledge about a suspect or case details can unconsciously influence judgment. The "bias blind spot" phenomenon is particularly concerning—while most professionals recognize bias as a general problem, they consistently identify it in others rather than themselves [8]. This creates a fundamental challenge for organizational error prevention strategies, as simply making examiners aware of biases proves insufficient for mitigation. Instead, procedural and systematic changes are necessary to manage contextual information and implement structural safeguards.
Evidence-Based Management Framework for Forensic Organizations
Principles and Implementation Process
Evidence-based management (EBM) represents a paradigm shift from tradition-based decision-making to approaches grounded in scientific literature, internal data, professional expertise, and stakeholder values [68]. This methodology enables forensic managers to address organizational deficiencies through conscientious, explicit, and judicious use of best available evidence rather than convention or hierarchy of opinion [68]. The implementation follows a structured six-step process that transforms managerial decision-making.
Table 2: Six-Step Process for Implementing Evidence-Based Management
| Step | Process Description | Application in Forensic Context |
|---|---|---|
| 1. Asking | Translating practical problems into answerable questions | Formulate specific questions: "How can shift scheduling reduce cognitive fatigue in fingerprint analysis?" |
| 2. Acquiring | Systematically searching for and retrieving evidence | Access peer-reviewed journals, internal error rate data, and industry best practices |
| 3. Appraising | Critically judging trustworthiness and relevance of evidence | Evaluate research methodology, applicability to forensic context, and potential biases |
| 4. Aggregating | Weighing and pulling together evidence from multiple sources | Combine scientific literature, internal performance metrics, and examiner feedback |
| 5. Applying | Incorporating evidence into decision-making process | Implement new protocols with clear rationale based on aggregated evidence |
| 6. Assessing | Evaluating outcomes of the decision | Monitor key metrics post-implementation and adjust based on results |
The successful application of this framework requires organizational commitment to creating evidence-based cultures. Research indicates that leadership support and implementation of multiple concurrent management practices serve as key facilitators for building EBM capacity, while competing priorities and lack of political will represent significant barriers [69].
Management Practices for Organizational Change
Implementation of evidence-based management in public health chronic disease prevention programs provides an instructive case study for forensic organizations. Key management practices that successfully built EBDM capacity included restructuring organizational sections to foster collaboration, revising meeting agendas to incorporate EBDM information, establishing ongoing training series, ensuring access to scientific literature, implementing performance-based contracting, and adding EBDM expectations to staff performance plans [69]. Quantitative assessment demonstrated that these coordinated management practices significantly reduced skill gaps and increased use of research evidence to justify interventions. The commitment of leaders with authority to establish multiple management practices to help staff learn and apply evidence-based decision-making processes proved fundamental to improved outcomes [69].
Figure 1: Evidence-Based Management Process Cycle
Strategic Training Methodologies: The Instructional Value of Errors
Theoretical Foundation and Cognitive Benefits
A transformative approach to training forensic examiners involves reconceptualizing errors not as failures but as valuable learning opportunities. Robust literature from cognitive psychology demonstrates that errors made—and corrected—during training benefit the learning process and result in fewer errors during actual casework [70]. This research challenges the traditional American educational philosophy that emphasizes error avoidance, instead aligning with Asian educational approaches that view errors as "an index of what still needs to be learned" [70]. The cognitive benefits emerge from the deeper processing required when learners encounter and correct errors, which strengthens conceptual understanding and creates more resilient memory traces compared to error-free learning approaches.
The effectiveness of error-based learning is contingent upon several key principles. First, errors must occur in a protected training environment where consequences are minimized. Second, timely and specific feedback is essential following errors to guide correction. Third, training exercises should be challenging enough to push the boundaries of an examiner's abilities, as only difficult tasks that induce errors reveal the limits of the system [70]. Research on fingerprint comparison provides empirical support for this approach, showing that false-positive rates are highest among trainees (9.2%), drop to nearly zero in the first two years of independent casework, then rise again with experience to plateau at 2.9%—suggesting that continued challenging exercises throughout a career might prevent this stagnation or deterioration of accuracy [70].
Implementation Protocols for Error-Based Training
Experimental Protocol: Implementing Error-Based Learning in Forensic Training
Objective: To integrate beneficial errors into forensic science training programs to enhance long-term performance and reduce casework errors.
Materials:
- Challenging training specimens with known ground truth
- Structured feedback mechanisms
- Performance assessment rubrics
- Documentation system for tracking errors and corrections
Methodology:
- Baseline Assessment: Evaluate trainees using standard specimens to establish initial competency levels.
- Progressive Complexity Training: Introduce increasingly difficult specimens that approach the trainee's competency threshold.
- Guided Error Exploration: Allow trainees to encounter and commit to incorrect conclusions in controlled environments.
- Corrective Feedback: Provide immediate, specific feedback explaining why the error occurred and demonstrating correct analytical reasoning.
- Metacognitive Development: Guide trainees to reflect on their error patterns and develop self-monitoring strategies.
- Application Exercises: Assign additional challenging specimens to reinforce corrected reasoning.
- Longitudinal Assessment: Implement periodic challenging tests throughout careers to maintain analytical sharpness.
Quality Control: Document all training errors and corrections to demonstrate learning progression while protecting this information from inappropriate use in legal proceedings, consistent with National Commission on Forensic Science recommendations [70].
Resource Allocation Optimization and Bias Mitigation
Strategic Resource Allocation Frameworks
Effective resource allocation in forensic organizations requires moving beyond traditional incremental budgeting models toward evidence-based approaches that directly link resources to organizational priorities and assessed needs. The framework for optimizing resource allocation involves integrating assessment, strategic planning, and budgeting processes at all organizational levels [71]. This integration enables forensic laboratories to demonstrate institutional effectiveness by providing documented evidence that all activities using institutional resources support the organization's mission—a requirement of many accreditation standards.
Table 3: Resource Allocation Models for Forensic Organizations
| Model | Description | Pros & Cons in Forensic Context |
|---|---|---|
| Incremental Budgeting | Adjustments based on previously allocated budget with percent increase/decrease | Pros: Simple, predictableCons: Doesn't rely on assessment data, perpetuates historical inequities |
| Performance-Based Budgeting | Links funding to performance metrics and outcomes | Pros: Aligned with assessment data, promotes accountabilityCons: May encourage metric manipulation, complex to implement |
| Zero-Based Budgeting | Justifies all expenses for each new period | Pros: Eliminates unnecessary expenditures, efficient resource useCons: Time-consuming, requires extensive documentation |
| Formula-Based Budgeting | Uses quantitative measures to distribute resources based on program cost and demand | Pros: Objective, transparentCons: May not capture qualitative aspects, rigid |
Research indicates that hybrid models combining elements from multiple approaches often prove most effective for forensic organizations. The critical success factor is establishing clear linkages between assessment results, strategic priorities, and resource allocation decisions [71].
Experimental Protocols for Bias Mitigation
Experimental Protocol: Evaluating Blind Verification in Forensic Analysis
Objective: To assess the effectiveness of blind verification procedures in reducing cognitive bias in forensic evidence analysis.
Materials:
- Case sets with known ground truth
- Multiple qualified examiners
- Context management protocols
- Data collection forms
Methodology:
- Case Selection: Curate a set of challenging cases representing a spectrum of difficulty levels.
- Examiner Recruitment: Engage practicing forensic examiners with appropriate expertise.
- Experimental Conditions:
- Standard Protocol: Examiners receive complete case information including initial examiner's conclusions.
- Blind Verification: Second examiner reviews evidence with no information about first examiner's findings or potentially biasing contextual details.
- Performance Metrics: Measure accuracy rates, false positive/negative rates, and conclusion consistency across conditions.
- Data Analysis: Compare error rates between standard and blind verification conditions using appropriate statistical tests.
Expected Outcomes: Prior research indicates that blind verification procedures, where a second examiner reviews a case with no information about the first examiner's conclusions, increase confidence in analysis accuracy when the two examiners independently agree [8]. Context management, which involves limiting unnecessary contextual information irrelevant to the evidence analysis task, further enhances objectivity [8].
Figure 2: Bias Mitigation Through Blind Verification Workflow
The Scientist's Toolkit: Essential Methodological Solutions
Table 4: Research Reagent Solutions for Organizational Improvement
| Tool/Category | Specific Examples | Function in Addressing Organizational Deficiencies |
|---|---|---|
| Evidence-Based Management Tools | Academic journal subscriptions (JSTOR, ScienceDirect), Business intelligence software (Tableau), Industry association memberships | Provides access to scientific literature for decision-making, enables data visualization and analysis, facilitates professional networking and knowledge exchange |
| Bias Mitigation Protocols | Blind verification procedures, Context management protocols, Sequential unmasking techniques | Reduces cognitive bias in evidence analysis, limits exposure to potentially biasing information, ensures independent conclusions |
| Error-Based Training Materials | Challenging training specimens with known ground truth, Structured feedback mechanisms, Performance assessment rubrics | Creates controlled learning environments, facilitates corrective feedback, documents skill progression |
| Resource Optimization Frameworks | Program prioritization matrices, Performance-based budgeting templates, Assessment integration frameworks | Supports data-driven resource allocation, links funding to outcomes, connects planning with assessment |
| Stress Reduction Interventions | Mindfulness training programs, Resilience building workshops, Workload management systems | Mitigates workplace stress impacts, enhances cognitive capacity, promotes examiner well-being |
Addressing organizational deficiencies in forensic science requires a systematic approach that integrates evidence-based management, strategic training methodologies, and optimized resource allocation. By reconceptualizing errors as valuable learning opportunities rather than failures, implementing structural safeguards against cognitive biases, and creating decision-making processes grounded in scientific evidence, forensic organizations can significantly enhance their error prevention capabilities. The frameworks and protocols presented provide a roadmap for building more resilient forensic science organizations capable of navigating the complex interplay of human factors, cognitive limitations, and operational constraints that characterize modern forensic practice. As research on human reasoning challenges continues to evolve, forensic organizations must maintain commitment to ongoing organizational learning and evidence-based refinement of their practices, ultimately enhancing the reliability and validity of forensic science within the justice system.
Human vs. Machine: Validating Forensic Judgments in the Age of AI
The integration of artificial intelligence (AI) into domains traditionally reliant on human expertise represents a paradigm shift in forensic science and other high-stakes fields. This technical guide provides an in-depth analysis of benchmark studies comparing the performance of human experts, non-experts, and AI systems. Within forensic science decisions research, these comparative performance assessments are critical for establishing the validity and reliability of emerging technologies while addressing persistent challenges in human reasoning, such as cognitive bias and contextual influence. The rapid advancement of AI capabilities, particularly in complex reasoning tasks, necessitates rigorous benchmarking frameworks that move beyond theoretical exercises to evaluate real-world applicability [72]. This whitepaper synthesizes current research findings, methodological approaches, and practical implications for researchers and professionals navigating the evolving relationship between human and machine intelligence in forensic contexts.
Theoretical Framework: Human-Machine Interaction in Decision-Making
The interaction between human expertise and automated systems can be conceptualized through a practical taxonomy that identifies three distinct modes of operation within forensic practice. This framework is essential for understanding how different collaboration models produce distinct epistemic vulnerabilities and shape the formation of bias at the human-AI interface [14].
- Offloading: Experts delegate routine or memory-intensive tasks to machines while retaining ultimate judgment and oversight responsibility.
- Collaborative Partnership: Humans and algorithms jointly negotiate interpretation in a dynamic process that leverages the strengths of both entities.
- Subservient Use: Humans defer to machine outputs and thereby suspend critical scrutiny, potentially ceding judgment to automated systems.
Historical cases, such as the Dreyfus Affair and the Brandon Mayfield incident, illustrate how cognitive biases including confirmation bias and contextual bias can systematically distort human expert judgment [14]. These cases demonstrate that expert interpretation is not produced in a vacuum but is embedded within a network of institutional practices, informational flows, and social pressures that can systematically shape judgments. Similarly, AI systems can inherit and amplify biases present in their training data or through opaque algorithmic processes, creating new challenges for forensic validation [73]. Understanding these interaction modes provides a foundation for developing appropriate governance interventions, including technical validation, workflow redesign, and mandatory disclosure rules tailored to specific human-machine collaboration models.
Benchmarking Methodologies and Experimental Protocols
General AI Benchmarking Frameworks
Rigorous benchmarking of AI systems utilizes diverse methodologies to assess capabilities across different domains:
Humanity's Last Exam (HLE): This comprehensive benchmark consists of 2,500-3,000 questions across more than 100 academic disciplines, featuring graduate-level problems designed to evaluate genuine reasoning capabilities rather than simple pattern recognition [74]. Developed by the Center for AI Safety, HLE employs multiple-choice and exact-match short answer questions with clear-cut answers. The benchmark incorporates stringent quality control measures, including a bounty program for identifying ambiguities and a two-stage filtering process where questions correctly answered by top AI models are eliminated. This ensures the benchmark maintains difficulty and resists memorization. HLE also includes multi-modal elements with diagrams, charts, or images that require connecting visual information with textual reasoning [74].
GDPval Framework: OpenAI's GDPval evaluates AI performance on real-world business tasks curated by experts from 44 different professions across nine GDP-driving industries [75] [72]. Unlike traditional benchmarks that might test knowledge through multiple-choice questions, GDPval assesses capabilities through complete work products, such as crafting a 3,500-word legal memo assessing standards of review under Delaware law [72]. The framework evaluates models against deliverables designed by professionals with an average of 14 years of experience, ensuring the assessment reflects day-to-day responsibilities rather than theoretical exercises.
Specialized Forensic Benchmarking: Research on forensic applications often employs controlled experimental designs comparing AI systems, certified experts, and non-experts on specific tasks. These typically involve carefully curated datasets with ground truth measurements, standardized evaluation protocols, and statistical analysis of performance metrics [73].
Specific Experimental Protocol: Forensic Attribute Estimation
A 2023 study published in Scientific Reports provides a detailed protocol for comparing human and AI performance in estimating physical attributes from imagery, highly relevant to forensic identification [73]:
Dataset Creation:
- Participants: 58 participants (33 women, 25 men) recruited from a university campus
- Physical Measurements: Height and weight precisely measured and recorded alongside anonymized identifiers
- Imaging Conditions:
- Studio Setting: Fixed white background with artificial lighting using a tripod-mounted DSLR camera (4000 × 6000 pixels)
- In-the-Wild Setting: CCTV-like scene in a narrow corridor photographed by a ceiling-mounted GoPro camera (5184 × 3888 pixels)
- Pose Variations:
- Studio: 8 neutral poses, 6 dynamic poses, 1 neutral pose with reference object (standard stool)
- In-the-Wild: 2 static poses, 3 dynamic poses
- Total Images: 812 no-reference studio images, 58 reference studio images, 290 in-the-wild images
AI Methodology:
- Model Architecture: Augmented version of SMPLify-X system incorporating body shape parameter estimation alongside pose estimation [73]
- Metric Scaling: 3D models scaled using gender-specific average inter-pupillary distance (IPD: 6.17 cm women/6.40 cm men with SD 0.36/0.34 cm)
- Height Estimation: Scaled 3D model reposed into neutral, upright position with height measured from head top to foot bottom plane
- Weight Estimation: Model volume converted to kilograms using multiplier of 1023 kg/m³ (corresponding to gender-agnostic average body fat of 34%)
Human Evaluation Protocols:
- Expert Participants: 10 US-based certified photogrammetrists (4-6 years minimum experience)
- Expert Task: Provided random subset of 5 in-the-wild images (different persons) with schematic diagram of scene including two real-world measurements
- Non-Expert Participants: 325 participants recruited via Amazon Mechanical Turk
- Non-Expert Task: Estimated height/weight from assigned image sets (no-reference studio, reference studio, or in-the-wild images) with catch trials for quality control
- Validation: 65 participants excluded for failing catch trials, 24 for incomplete responses, yielding 236 valid responses
Comparative Performance Results
General AI vs. Human Performance Benchmarks
Table 1: AI vs. Human Performance Across Standardized Benchmarks
| Benchmark | Top AI Performance | Human Expert Performance | Performance Gap | Key Insights |
|---|---|---|---|---|
| Humanity's Last Exam (HLE) [74] | 79-87% (newest models) | ~90% | Narrowing | Early versions showed AI at ~30% vs. humans at ~90%; gap has narrowed significantly with model improvements |
| GDPval (Business Tasks) [75] [72] | 47.6% of tasks at/expert level (Claude Opus 4.1) | 100% (by definition) | Variable by domain | AI delivers 100x faster cycle times and 100x lower costs than human experts |
| MMMU [76] | 18.8 percentage point gain (2023-2024) | Not specified | Rapidly closing | AI masters new benchmarks faster than ever, showing remarkable year-over-year improvements |
| Coding (SWE-bench) [76] | 71.7% (2024, from 4.4% in 2023) | Not specified | AI advancing rapidly | AI systems now solve majority of coding problems they struggled with just one year prior |
Table 2: AI vs. Human Performance in Professional Domains (GDPval Framework)
| Professional Domain | Top AI Performance(% tasks at/expert level) | Strongest AI Model | Domains Where Humans Excel | Performance Notes |
|---|---|---|---|---|
| Counter & Rental Clerks | 81% | Claude Opus 4.1 | Film & Video Editing | AI performance varies significantly across professions |
| Shipping Clerks | 76% | Claude Opus 4.1 | Pharmacist Tasks | Variance reflects complexity of domain knowledge |
| Software Development | 70% | Claude Opus 4.1 | Audio & Video Technician Work | AI excels in structured cognitive tasks |
| Private Investigators | 70% | Claude Opus 4.1 | Production & Directing | Pattern recognition tasks show strong AI performance |
| Sales Management | 79% | GPT-5 Thinking | Healthcare Diagnostics | AI demonstrates strategic capability in some domains |
| Editing | 75% | GPT-5 Thinking | Complex Patient Care | Language and editing tasks show high AI proficiency |
Forensic-Specific Performance Comparisons
Table 3: Performance in Forensic Physical Attribute Estimation [73]
| Method | Mean Height Error | Mean Weight Error | Context | Limitations & Capabilities |
|---|---|---|---|---|
| AI System | ~5.3 cm | ~12.1 kg | In-the-wild images | Performance depends on image quality and pose variability |
| Expert Photogrammetrists | ~7.4 cm | ~12.9 kg | In-the-wild images with scene schematics | Experts provided with reference measurements and scene diagrams |
| Non-Expert Crowd | ~4.5 cm | ~10.8 kg | Studio images with reference object | "Wisdom of crowd" effect with multiple estimators |
| Individual Non-Experts | ~8.1 cm | ~17.2 kg | Various image conditions | High individual variability reduced through aggregation |
The forensic attribute estimation study revealed several critical findings. The AI system performed comparably to human experts in weight estimation but showed advantages in height estimation from challenging in-the-wild imagery [73]. Notably, the "wisdom of the crowd" approach with non-experts, particularly when provided with reference objects, achieved the most accurate height estimates, suggesting that aggregating multiple independent judgments can outperform both individual experts and AI systems for specific metric estimation tasks. However, AI systems demonstrated more consistent performance across varying image conditions compared to human estimators, who showed greater susceptibility to environmental factors and image quality.
Current Limitations and Performance Gaps
Despite rapid advances, AI systems continue to demonstrate significant limitations in specific domains:
Complex Reasoning Challenges: Even with mechanisms like chain-of-thought reasoning, AI systems still cannot reliably solve problems for which provably correct solutions can be found using logical reasoning, such as complex arithmetic and planning, particularly on instances larger than those encountered in training [76]. This limitation impacts trustworthiness and suitability for high-risk applications where precision is critical.
Multi-Modal Reasoning Deficits: On the Humanity's Last Exam benchmark, AI performance drops several points when diagrams or data tables are involved, confirming that multi-modal reasoning still trails behind text processing capabilities [74].
Bias and Contextual Sensitivity: Studies of face-matching tasks have revealed suboptimal human-automation interaction, with AFRS-assisted individuals consistently failing to reach the level of performance the AFRS achieved alone [77]. This automation dependence creates new vulnerabilities in forensic decision-making.
Visualization of Methodologies and Relationships
Experimental Workflow for Forensic Attribute Estimation
Human-AI Collaboration Framework in Forensic Decisions
Research Reagent Solutions for Experimental Replication
Table 4: Essential Materials and Methods for Benchmarking Studies
| Research Component | Specific Solution/Product | Function in Experimental Protocol | Implementation Considerations |
|---|---|---|---|
| Imaging Systems | Tripod-mounted DSLR (4000×6000 pixels); Ceiling-mounted GoPro (5184×3888 pixels) [73] | Standardized image capture under controlled (studio) and realistic (CCTV-like) conditions | Resolution, lighting consistency, and camera positioning critical for comparability |
| 3D Body Modeling | Augmented SMPLify-X system with body shape parameter estimation [73] | Estimation of 3D body pose and shape from 2D images for physical attribute derivation | Requires gender-specific IPD averages (6.17/6.40 cm) for metric scaling |
| Participant Pool | Amazon Mechanical Turk with catch trial validation [73] | Recruitment of non-expert evaluators with quality control mechanisms | Exclusion of participants failing catch trials (20% failure rate in cited study) |
| Expert Recruitment | Certified photogrammetrists (4-6 years minimum experience) [73] | Provision of ground truth expert performance benchmarks | Certification requirements ensure minimum expertise level |
| Reference Objects | Standardized stool for scale reference [73] | Provision of metric scaling reference in visual estimation tasks | Consistent use of same reference object across all imaging sessions |
| Performance Metrics | Mean absolute error (height/weight); Percentage at/expert level | Quantification of performance differences between human and AI systems | Standardized metrics essential for cross-study comparability |
The benchmarking of human experts, non-experts, and AI systems reveals a complex landscape of complementary strengths and limitations. Current evidence demonstrates that AI systems have achieved human-expert level performance on specific, structured tasks, particularly in business environments where they can deliver dramatic efficiency improvements [75] [72]. However, in forensic applications, the relationship is more nuanced, with AI systems showing particular promise in reducing certain cognitive biases while potentially introducing new challenges related to automation dependence and algorithmic transparency [14] [77].
The most effective approaches appear to be those that leverage the respective strengths of human and artificial intelligence through thoughtful collaboration models rather than outright replacement. The "centaur" model of human-AI collaboration, where each component focuses on its comparative advantages, shows particular promise for forensic applications where the consequences of error are substantial [72]. As AI capabilities continue to evolve rapidly – with performance on demanding benchmarks sometimes improving by dozens of percentage points within a single year [76] – the need for robust, domain-specific benchmarking methodologies becomes increasingly critical for researchers and practitioners in forensic science and beyond.
Future research should focus on developing more sophisticated frameworks for evaluating the complex interaction between human expertise and artificial intelligence, particularly in high-stakes environments where cognitive biases and contextual factors can significantly impact decision-making outcomes. The integration of these evaluation methodologies into forensic practice will be essential for realizing the benefits of AI assistance while mitigating the risks associated with both human and algorithmic judgment.
Facial recognition technology represents a pivotal innovation in artificial intelligence, offering unprecedented capabilities for identity verification and physical attribute estimation. Within forensic science, where human reasoning is already susceptible to cognitive biases and contextual influences, the integration of such technologies introduces both transformative potential and significant ethical challenges. This whitepaper assesses the current state of facial recognition accuracy and bias through a forensic science lens, examining how these systems may either mitigate or compound existing human decision-making vulnerabilities. The evaluation of these technologies must consider not only their technical performance but also their interaction with human factors in forensic contexts, where decisions carry substantial legal and societal consequences.
Current State of Facial Recognition Accuracy
Facial recognition technology has achieved remarkable technical proficiency under controlled conditions, with performance metrics approaching near-perfect levels in laboratory environments. According to the National Institute of Standards and Technology (NIST) Face Recognition Technology Evaluation (FRTE), top-performing algorithms now demonstrate unprecedented precision, with some verification algorithms achieving accuracy rates as high as 99.97% [78]. In optimal conditions, these systems can achieve accuracy rates exceeding 99.5%, with 45 of the 105 identification algorithms tested performing at over 99% accuracy when comparing high-quality images [78]. This level of precision rivals other established biometric technologies, performing comparably to leading iris recognition (99-99.8% accuracy) and exceeding many fingerprint solutions [78].
Table 1: Facial Recognition Performance Metrics Under Controlled Conditions
| Performance Metric | Laboratory Performance | Comparative Biometric Technology |
|---|---|---|
| Verification Accuracy | 99.97% (top algorithms) | Iris Recognition: 99-99.8% |
| Identification Accuracy | >99.5% (optimal conditions) | Fingerprint Solutions: Lower than FRT |
| False Negative Identification Rate (FNIR) | <0.15% at FPIR=0.001 | N/A |
| Leading Algorithm Providers | NEC, SenseTime, Idemia | N/A |
The market growth reflects this technological maturation, with the facial recognition market reaching $6.94 billion in 2024 and projected to expand to $7.92 billion in 2025, representing a 14.2% annual growth rate [78]. Widespread adoption is evident across sectors, with over 176 million Americans using facial recognition technology, 131 million using it daily, and 68% of users employing facial verification to unlock personal devices [78].
The Bias Challenge: Disparate Performance Across Demographics
Despite impressive laboratory performance, facial recognition systems demonstrate significant disparities in accuracy across demographic groups, raising serious concerns about equitable deployment, particularly in forensic applications where biased outcomes can profoundly impact justice.
Documented Disparities in Algorithmic Performance
Substantial evidence indicates that facial recognition technologies perform differently across racial and gender groups. The foundational "Gender Shades" project by Joy Buolamwini and Timnit Gebru revealed alarming disparities, finding error rates of 0.8% for light-skinned males compared to 34.7% for darker-skinned females [79]. A 2019 federal government test concluded the technology works best on middle-age white men, with significantly reduced accuracy for people of color, women, children, and elderly individuals [79]. Subsequent testing by the federal government showed that African American and Asian faces were up to 100 times more likely to be misidentified than white faces, with the highest false-positive rate among Native Americans [80].
Table 2: Documented Performance Disparities in Facial Recognition Systems
| Demographic Group | Error Rate | Comparative Performance |
|---|---|---|
| Light-skinned men | 0.8% | Baseline |
| Darker-skinned women | 34.7% | 43x higher error rate |
| African American faces | Up to 100x more false IDs | Compared to white faces |
| Native Americans | Highest false-positive rate | Compared to other groups |
| Younger age groups (12-18) | Under-represented in testing | Performance data limited |
Real-World Consequences of Biased Systems
These performance disparities have manifested in tangible harms within legal and forensic contexts. Robert Williams, a Black man in Detroit, was wrongfully arrested in 2020 after being misidentified by facial recognition software, with police later admitting the mistake resulted from a poor-quality surveillance image [81]. Similarly, the ACLU-MN sued on behalf of Kylese Perryman, an innocent young man who was falsely arrested and detained based solely on incorrect facial identification [79]. An independent review of Live Facial Recognition trials by London's Metropolitan Police found that out of 42 matches, only eight could be confirmed as absolutely accurate [81].
These incidents highlight how technological bias can exacerbate existing disparities in forensic decision-making. The problem is compounded by datasets that disproportionately represent certain demographics - major systems have training datasets that are over 77% male and 83% white [82]. This underrepresentation in training data creates systems that effectively institutionalize and automate discrimination, particularly concerning when deployed in forensic contexts already struggling with cognitive biases.
The Real-World Performance Gap: Laboratory vs. Operational Environments
A critical consideration for forensic applications is the significant performance degradation observed when facial recognition systems transition from controlled laboratory environments to real-world operational settings.
Environmental and Technical Challenges
While laboratory testing demonstrates impressive results, real-world implementation presents substantial hurdles that reduce system reliability. The Center for Strategic and International Studies (CSIS) notes that accuracy drops significantly when facing suboptimal conditions [78]. An algorithm with a 0.1% error rate when matching high-quality mugshots can see this increase to 9.3% when processing images captured "in the wild" [78]. Several factors impact real-world performance:
- Lighting variations: Inconsistent illumination can significantly reduce recognition accuracy
- Facial positioning and angles: Non-frontal poses decrease matching precision
- Occlusions: Masks, glasses, and other face coverings present ongoing challenges
- Image quality: Low-resolution images from surveillance cameras yield less reliable results [78]
Scaling Effects and Database Limitations
Benchmark evaluations often fail to account for the scaling effects encountered in operational deployments. While NIST evaluations use datasets of up to 12 million individual faces, real-world applications may involve scanning hundreds of millions of faces [81]. As the pool of individuals to identify grows larger, the task becomes significantly harder for the algorithm, and accuracy tends to decline [81]. This scaling effect is particularly relevant for forensic databases that may encompass entire state or national populations.
The representativeness of evaluation datasets also limits their predictive value for real-world performance. Despite concerns about police stops of young people resulting from facial recognition misidentification, evaluation data often under-represents younger age ranges. In one UK National Physical Laboratory report, individuals between 12-18 are under-represented, and those under 12 entirely omitted [81].
Methodological Framework: Experimental Protocols for Bias Assessment
Robust evaluation of facial recognition systems requires standardized methodologies that account for real-world operational conditions and demographic diversity. The following experimental protocols provide a framework for assessing both accuracy and bias in forensic contexts.
NIST Facial Recognition Technology Evaluation (FRTE) Protocol
The NIST FRTE has emerged as the gold standard for evaluating facial recognition algorithms, employing a rigorous methodology that forensic researchers should understand [78] [81].
Experimental Design:
- Dataset Composition: Utilizes multiple image categories including mugshots, visa application photos, and webcam-captured images
- Algorithm Testing: Implements standardized testing protocols across submitted algorithms from various vendors
- Performance Metrics: Calculates false positive identification rate (FPIR), false negative identification rate (FNIR), and genuine acceptance rate across demographic cohorts
- Cross-Validation: Implements k-fold cross-validation to ensure statistical reliability
Key Measurements:
- Verification performance (1:1 matching)
- Identification performance (1:N matching)
- Demographic differentials in performance
- Processing speed and computational efficiency
Limitations for Forensic Application:
- Laboratory conditions may not reflect operational environments
- Limited representation of challenging acquisition conditions
- Potential demographic gaps in test datasets [81]
Real-World Performance Assessment Protocol
To address the limitations of laboratory testing, the following protocol adapts evaluation methodologies for operational forensic contexts:
Experimental Design:
- Field Testing: Deploy algorithms in simulated operational environments (e.g., variable lighting, angles, distances)
- Demographic Stratification: Ensure proportional representation across gender, race, age, and other demographic factors
- Scenario Testing: Evaluate performance across specific use cases (e.g., surveillance footage analysis, identity verification)
- Cross-Platform Comparison: Benchmark multiple algorithms against consistent datasets and conditions
Facial Recognition Evaluation Workflow
Key Measurements:
- Real-world false match rates across demographics
- Performance degradation under suboptimal conditions
- Failure mode analysis (common causes of misidentification)
- Confidence calibration across demographic groups
Human-Technology Interface in Forensic Decision-Making
The integration of facial recognition technology into forensic practice creates a complex human-technology ecosystem where both algorithmic and human biases can interact and amplify one another.
Cognitive Biases in Forensic Interpretation
Research on human factors in forensic decision-making reveals several vulnerabilities that may intersect with algorithmic limitations:
- Contextual bias: Forensic examiners may be influenced by extraneous contextual information when interpreting algorithmic outputs [83]
- Automation bias: Tendency to over-rely on automated systems, particularly when facing cognitive load or time pressure
- Ambiguity aversion: Decision-makers with low tolerance for uncertainty may inappropriately rely on algorithmic outputs to reduce cognitive dissonance [83]
- Confirmation bias: Selective attention to algorithmic outputs that confirm pre-existing beliefs or hypotheses
Recent experimental research has demonstrated that forensic experts are subject to these cognitive influences. A 2025 study examining human factors in triaging forensic items found that while explicit pressure manipulation didn't significantly alter decisions, foundational inconsistencies in triaging decisions persisted across practitioners [83]. This suggests that introducing algorithmic tools without addressing these inherent inconsistencies may simply automate unreliable processes.
Organizational and System Pressures
Forensic decision-making occurs within organizational contexts that introduce additional pressures potentially compromising reasoned evaluation:
- Casework pressures: Financial constraints, time pressure, stress, and high-profile cases can impact decision-making quality [83]
- Resource limitations: Backlogs and staffing constraints may create incentives to over-rely on automated solutions without sufficient validation
- Cultural factors: Organizational culture surrounding technology adoption can influence critical evaluation of algorithmic outputs
Research Reagents and Experimental Tools
The following reagents and tools represent essential components for rigorous facial recognition evaluation in forensic contexts:
Table 3: Essential Research Tools for Facial Recognition Evaluation
| Tool/Category | Function | Representative Examples |
|---|---|---|
| Benchmark Datasets | Algorithm training and validation | NIST FRVT datasets, Gender Shades evaluation set |
| Evaluation Frameworks | Standardized performance assessment | NIST FRTE protocol, UK NPL evaluation framework |
| Bias Assessment Tools | Demographic disparity measurement | Disparate impact analysis, error rate differentials |
| Image Quality Metrics | Quantification of input variability | ISO/IEC 29794-5:2010, NIST IQS |
| Statistical Analysis Packages | Performance data analysis | R, Python with scikit-learn, specialized biometric libraries |
Mitigation Strategies and Future Directions
Addressing the dual challenges of accuracy and bias in facial recognition requires multidisciplinary approaches spanning technical, regulatory, and human factors domains.
Technical Mitigations
- Multimodal biometric authentication: Integrating multiple biometric modalities (facial, fingerprint, voice recognition) provides backup options when one biometric factor is unavailable or performs poorly [78]
- Advanced neural architectures: Emerging approaches like capsule networks show promise for modeling facial features hierarchically to improve recognition across varied conditions [78]
- Representative data collection: Curating training datasets that reflect real-world demographic distributions to reduce performance disparities
- Uncertainty quantification: Developing systems that provide calibrated confidence estimates to support appropriate human interpretation
Human Factors Interventions
- Decision-support interfaces: Designing systems that present algorithmic outputs in ways that mitigate cognitive biases
- Structured validation protocols: Implementing standardized procedures for human verification of algorithmic matches
- Cross-disciplinary training: Educating forensic practitioners about both algorithmic limitations and human decision-making vulnerabilities
Bias Mitigation Framework
Regulatory and Oversight Frameworks
- Accuracy standards: Establishing legally-binding thresholds for sufficient accuracy in high-stakes applications [81]
- Bias auditing requirements: Mandating regular testing for demographic disparities in performance
- Transparency mandates: Requiring documentation of limitations and appropriate use cases
- Independent oversight: Facilitating independent research and evaluation through secure access to deployment data [81]
Facial recognition technology presents a dual-edged sword for forensic science—offering powerful new capabilities for identification while introducing significant risks related to accuracy limitations and biased performance. The integration of these systems into forensic practice must be guided by rigorous evaluation protocols that account for real-world operational conditions and demographic diversity. Crucially, the implementation of facial recognition must address the complex interaction between algorithmic limitations and human decision-making vulnerabilities that characterize forensic practice. A multidisciplinary approach incorporating technical improvements, human factors research, and thoughtful regulation offers the most promising path toward realizing the benefits of these technologies while minimizing their perils in sensitive forensic applications.
The integration of advanced technological systems into forensic science represents a paradigm shift in criminal investigations, yet introduces a critical vulnerability: automation bias. This cognitive phenomenon describes the human tendency to over-rely on automated aids, whereby users disproportionately trust algorithm-generated outputs while suspending their own critical judgment [14]. In forensic contexts, automation bias manifests when examiners permit technologies such as Automated Fingerprint Identification Systems (AFIS) and Facial Recognition Technology (FRT) to usurp rather than supplement their expert decision-making [19]. This whitepaper examines the empirical evidence for automation bias within these systems, frames the issue within the broader challenge of human reasoning in forensic science, and proposes structured methodological interventions to mitigate these risks without undermining technological utility.
The challenge is particularly acute because forensic science often demands that practitioners reason in "non-natural ways," counter to how human cognition typically functions [9] [10]. Characteristics of human reasoning, combined with situational pressures within criminal investigations, create a fertile environment for cognitive errors. When experts interact with complex technological systems, a form of distributed cognition occurs, where decision-making is offloaded across human and machine agents [14]. Without proper safeguards, this cooperation can deteriorate into a subservient relationship where human expertise is sidelined [14].
Theoretical Framework: Modes of Human-Technology Interaction
To analyze how automation bias emerges, it is helpful to adopt a taxonomy of human-technology interaction. Dror & Mnookin (2010) proposed a framework that distinguishes three primary modes of interaction, each with distinct epistemic vulnerabilities [14]:
- Offloading: Experts delegate routine or memory-intensive tasks to machines while retaining ultimate judgment.
- Collaborative Partnership: Humans and algorithms jointly negotiate interpretation in a dynamic process.
- Subservient Use: Humans defer to machine outputs and thereby suspend critical scrutiny.
The subservient use mode represents the greatest risk for automation bias. In this mode, the technology is not treated as a tool but as a final arbiter. This is particularly dangerous with "black box" algorithms whose decision-making processes are not transparent [84]. A 2023 report from the UK's Financial Reporting Council found that many professional firms "do not formally monitor how automated tools and artificial intelligence impact the quality of their audits," highlighting the pervasiveness of this uncritical acceptance [85].
Empirical Evidence: Documenting Automation Bias in Forensic Systems
Automation Bias in Automated Fingerprint Identification Systems (AFIS)
AFIS technology has revolutionized fingerprint analysis by enabling rapid searches through millions of fingerprint records. However, the very structure of its output creates a pathway for bias. The system generates a rank-ordered list of candidate matches based on algorithmic similarity scores [86]. In a seminal study, researchers provided 3,680 AFIS lists to 23 latent fingerprint examiners as part of their normal casework while manipulating the position of the matching print [87] [88]. The results demonstrated examiners were significantly influenced by the position of candidates in the list, with false identifications more likely to occur when prints appeared at the top, even when the correct match was present further down the list [87] [88].
Table 1: Documented Effects of Automation Bias in AFIS Environments
| Effect Type | Impact on Decision-Making | Empirical Support |
|---|---|---|
| Positional Bias | Examiners spend more time analyzing and more frequently identify whichever print appears at the top of the candidate list. | Dror et al. (2012) [87] [88] |
| Error Propagation | False identifications occur even when the correct match is present elsewhere in the list. | Dror et al. (2012) [87] [88] |
| Motivational Bias | Desire to reach a positive comparison to aid investigators or be recognized for solving a case. | Gibb & Riemen (2023) [86] |
Organizational factors exacerbate these cognitive risks. Operational hierarchies within police organizations can create pressure to reduce turnaround times (TATs), potentially sacrificing quality and accuracy for speed [86]. Furthermore, examiners may develop motivational bias—a desire to reach a positive comparison to help police informants or be recognized as the professional who solved the case [86].
Automation Bias in Facial Recognition Technology (FRT)
Facial Recognition Technology presents a similarly concerning profile for automation bias, compounded by the inherent difficulty of face-matching tasks. Even professional facial examiners show mean error rates of approximately 30% on simulated FRT tasks [19]. These challenges are amplified by the typical poor quality of probe images from surveillance footage, which are often blurry, poorly lit, or show only part of the face [19].
A 2025 experimental study tested for automation and contextual bias in simulated FRT tasks with 149 participants [19]. Researchers manipulated two variables:
- Biographical context: Candidates were randomly paired with guilt-suggestive information, an alibi, or neutral details.
- Confidence scores: Candidates were assigned high, medium, or low numerical confidence scores by the "system."
The findings revealed that participants consistently rated whichever candidate was paired with guilt-suggestive information or a high confidence score as looking most similar to the perpetrator, even though these details were assigned randomly [19]. This demonstrates a clear causal relationship between biasing information and perceptual judgment.
Table 2: Quantitative Results from Simulated FRT Bias Study (2025)
| Bias Condition | Effect on Similarity Ratings | Effect on Final Identification |
|---|---|---|
| High Confidence Score | Candidates with high scores were rated as looking most like the perpetrator. | Participants most often misidentified the high-score candidate as the perpetrator. |
| Guilt-Suggestive Context | Candidates with implied prior guilt were rated as more visually similar. | Candidates with guilt-suggestive information were most often misidentified as the perpetrator. |
| Combined Biases | Effects were compounded when multiple biasing factors were present. | Highest misidentification rates occurred with multiple biasing factors. |
Experimental Protocols for Studying Automation Bias
Protocol for Simulated FRT Bias Experiments
The following methodology, adapted from recent research, provides a template for investigating automation bias in facial recognition systems [19]:
- Participant Recruitment: Engage professional facial examiners or relevant law enforcement personnel where possible. For laboratory studies, use naive participants with appropriate sample sizes (N > 100) for statistical power.
- Stimulus Development: Create probe images of "perpetrators" and matching candidate images. Use a standardized database with controlled image quality, lighting, and angle.
- Bias Manipulation:
- Automation Bias Condition: Assign clearly visible confidence scores (e.g., "95% Match Confidence") to candidate images, randomized across participants.
- Contextual Bias Condition: Pair candidate images with brief biographical descriptions implying guilt (e.g., "has prior arrests for similar offenses"), innocence (e.g., "was incarcerated at time of offense"), or neutral information.
- Procedure: Present participants with a probe image and three candidate images simultaneously. Ask them to (1) rate each candidate's similarity to the probe on a Likert scale, and (2) make a binary decision about which candidate, if any, is the perpetrator.
- Data Analysis: Use analysis of variance (ANOVA) to test for main effects of bias conditions on similarity ratings and chi-square tests for identification decisions.
Protocol for AFIS Positional Bias Experiments
This protocol measures how candidate list positioning influences expert judgment [87] [88]:
- Stimulus Preparation: Use genuine casework marks with known matches. Create multiple versions of AFIS candidate lists where the position of the matching print is systematically manipulated (top, middle, bottom).
- Participant Pool: Certified latent print examiners conducting their normal casework, unaware they are participating in a study to ensure ecological validity.
- Procedure: Integrate manipulated lists into examiners' regular workflow. Examiners process lists as they normally would, documenting their comparison process and final decision for each candidate.
- Dependent Measures: Record (1) time spent examining each candidate, (2) decision accuracy, (3) frequency of false exclusions/inconclusives when match is present, and (4) frequency of false identifications when match is absent or lower on list.
- Analysis: Use multilevel modeling to account for nested data (candidates within lists within examiners), testing for main effects of position on all dependent measures.
Mitigation Strategies: Toward a Bias-Aware Forensic Workflow
Addressing automation bias requires both technical adjustments to systems and procedural reforms in human workflows. The National Police of the Netherlands (NPN) has implemented a benchmark system that incorporates several effective strategies [86]:
- Blind Verification: Implementing procedures where one examiner's conclusions are verified by another examiner who is blind to the initial findings and any potentially biasing contextual information [14].
- Context Management: Limiting examiner exposure to task-irrelevant information, particularly details about a suspect's prior legal involvement or other investigative details [86].
- List Randomization: "Removing the score and shuffling the candidate list for comparison" in AFIS to prevent algorithm-generated rankings from influencing human judgment [86].
- Linear Sequential Unmasking: Revealing information to examiners in a structured sequence, beginning with the evidence itself and only introducing contextual information after initial judgments are recorded [19].
The Scientist's Toolkit: Research Reagents for Bias Studies
Table 3: Essential Methodological Components for Forensic Bias Research
| Method Component | Function in Research | Implementation Example |
|---|---|---|
| Probe and Candidate Image Sets | Standardized facial stimuli for FRT studies with known ground truth. | High-quality portrait databases with controlled variables (lighting, angle, expression). |
| AFIS Candidate Lists | Testing positional effects in fingerprint identification. | Manipulated lists where known match position is systematically varied. |
| Confidence Score Manipulation | Isolating the effect of algorithmic confidence metrics. | Numeric or visual indicators of match confidence randomly assigned to candidates. |
| Contextual Information Priming | Measuring the effect of extraneous case information. | Biographical details implying guilt/innocence or investigative status. |
| Eye-Tracking Equipment | Objective measurement of visual attention during comparison tasks. | Tracking time spent examining each candidate and scan patterns between features. |
The integration of AI and automated systems into forensic science represents a dual-edged sword—offering unprecedented analytical power while introducing profound cognitive risks. As the historical lessons of the Dreyfus Affair and Brandon Mayfield case demonstrate, neither human expertise nor technological systems are immune to bias [14]. The solution lies not in rejecting technology, but in redesigning the human-technology interface to foster collaborative partnership rather than subservient use.
Future research must focus on developing explainable AI systems that make their reasoning processes transparent rather than operating as "black boxes" [84]. Furthermore, as expressed by Sebastiano Battiato of Italy's Catania University, "AI should always serve as an aid to human expertise, not as a substitute for it" [84]. This principle, embedded within rigorous procedural safeguards and continuous monitoring of system impacts on decision quality, offers the most promising path forward. By acknowledging and systematically addressing automation bias, the forensic science community can harness technological power while safeguarding the integrity of justice.
The integration of Artificial Intelligence (AI) into forensic science represents a paradigm shift, offering transformative potential to augment human expertise while simultaneously introducing complex ethical and operational challenges. This evolution occurs within a broader research context that recognizes persistent human reasoning challenges in forensic decision-making, including cognitive biases, the effects of casework pressure, and variability in examiner conclusions [83] [89]. The fundamental ethical boundary in forensic workflows lies not in choosing between human expertise or AI, but in designing collaborative systems that leverage their complementary strengths while mitigating their respective weaknesses. AI systems bring unparalleled processing speed, consistency, and the ability to detect patterns in complex datasets, potentially mitigating documented human factors such as contextual bias and fatigue [90] [91]. Conversely, human examiners provide crucial contextual understanding, ethical reasoning, and flexibility in novel situations—capabilities that remain beyond the scope of current AI systems. This technical guide examines the appropriate boundaries for AI implementation within forensic workflows, framed by research on human decision-making limitations and the necessary safeguards for responsible implementation.
Current State of AI Applications in Forensic Science
Categorization of AI Forensic Capabilities
AI technologies are being deployed across diverse forensic domains, with applications ranging from established operational tools to emerging research prototypes. The table below summarizes the key application areas, their capabilities, and implementation status based on current research and deployment.
Table 1: AI Applications in Forensic Science
| Forensic Domain | Key AI Applications | Implementation Stage | Reported Benefits |
|---|---|---|---|
| Biometric Analysis | Automated Fingerprint/Palmprint Identification, Facial Recognition, Iris Scanning | Established | Higher accuracy in pattern recognition, efficiency in processing large datasets [90] |
| Digital Forensics | Analysis of photos/videos, detection of AI-generated content, social media data analysis | Rapid Adoption | Processing vast volumes of digital data, detecting subtle patterns [90] [91] |
| DNA Analysis | Probabilistic genotyping for complex mixtures, predicting physical characteristics | Advanced | Interpretation of complex genetic mixtures, enhanced reproducibility [90] |
| Pattern Evidence | Firearm/toolmark analysis, footwear impression comparison, bloodstain pattern analysis | Emerging Research | Objectivity, reduced human bias, identifying subtle connections [90] [92] |
| Crime Scene Analysis | Automated image categorization, 3D scene reconstruction, evidence triaging support | Research & Early Adoption | Rapid initial screening, comprehensive evidence analysis [83] [91] |
| Drug Evidence | Classification of geographic origins, drug type identification | Specialized Deployment | Enhanced classification, tracing capabilities [90] |
Quantitative Performance of AI in Forensic Tasks
Recent empirical studies have begun quantifying AI performance across specific forensic tasks, providing crucial data for establishing appropriate implementation boundaries. These studies typically compare AI performance against human expert performance across different evidence types and conditions.
Table 2: Performance Metrics of AI in Experimental Forensic Studies
| Study Focus | AI System(s) Evaluated | Performance Metrics | Key Findings |
|---|---|---|---|
| Forensic Image Analysis [91] | ChatGPT-4, Claude, Gemini | Accuracy in crime scene observations (scale 1-10) | High accuracy in observations; Performance varied by crime scene type: Homicide scenes: 7.8, Arson scenes: 7.1 |
| Footwear Examiner Reliability [89] | N/A (Human baseline) | Accuracy, Reproducibility, Repeatability | When definitive conclusions were reported: 98.8% PPV for IDs, 91.2% for exclusions; false positive rate: 0.3% |
| AI Decision Support [91] | General-purpose AI models | Capability as rapid screening mechanism | Effective as assistive technology; Challenges in evidence identification; Complementary to human expertise |
Human Reasoning Challenges: The Research Foundation
Documented Cognitive Limitations in Forensic Decision-Making
A substantial body of research has established systematic human factors that affect forensic decision-making, creating a compelling case for AI augmentation while simultaneously highlighting the need for human oversight.
Cognitive Biases and Pressures: Forensic experts are susceptible to a range of cognitive biases and workplace pressures that can influence their decisions. Research on triaging forensic items has demonstrated that examiners operate under multiple pressures, including casework backlogs, time constraints, financial limitations, and high-profile case scrutiny [83]. While experimental studies found that explicitly manipulated pressure did not practically influence triaging decisions, the pervasive nature of these pressures in operational environments necessitates systemic solutions [83].
Ambiguity Aversion: Forensic decision-makers exhibit varying levels of ambiguity aversion—a dislike for uncertain probabilities—which can influence their decision-making processes. Those with higher ambiguity aversion may make different choices when faced with unreliable information, conflicting data, or generally uncertain situations [83]. This aversion to uncertainty represents a significant human factor that AI systems might help mitigate through quantitative confidence measures.
Between-Examiner Reliability: Multiple black-box studies have revealed concerning variability in conclusions between forensic examiners analyzing the same evidence. The largest study to date on forensic footwear examiners demonstrated that while accuracy was high when definitive conclusions were reported, there remains fundamental inconsistency in decision-making across practitioners [89]. This reproducibility challenge underscores the potential value of AI systems in promoting standardization.
Environmental and Systemic Factors
Human factors engineering research indicates that environmental conditions significantly impact forensic decision quality. Suboptimal working conditions, including distracting environments, inadequate lighting, temperature discomfort, and cognitive fatigue, can degrade performance [93]. Additionally, forensic analysts suffer from vicarious trauma due to repeated exposure to disturbing evidence, which may impact work quality and well-being [93]. Research-based recommendations include providing quiet workspaces, mandatory breaks, case rotation, and access to psychological support [93].
Experimental Protocols for Validating AI Forensic Systems
Protocol for AI-Human Collaborative Workflow Experiment
Objective: To quantitatively evaluate the performance characteristics of AI-human collaborative workflows compared to either alone in forensic evidence analysis.
Materials and Equipment:
- Test Dataset: Curated set of forensic evidence samples with ground truth established (200-500 samples)
- AI System: Validated forensic AI tool with API access or standalone application
- Participant Pool: Certified forensic examiners (minimum 15-20) with varying experience levels
- Control Condition: Traditional analysis without AI assistance
- Experimental Condition: Analysis with AI decision support
- Data Collection System: Electronic data capture of decisions, confidence levels, and time-to-completion
Methodology:
- Randomized Assignment: Participants are randomly assigned to control or experimental groups using block randomization
- Blinding Procedure: Double-blind design where neither participants nor outcome assessors know group assignment
- Task Administration: Participants analyze evidence samples using their standard protocol (control) or with AI-generated preliminary analysis (experimental)
- Outcome Measures: Primary: accuracy, false positive/negative rates; Secondary: time efficiency, confidence calibration, between-examiner reliability
- Statistical Analysis: Pre-specified analysis plan using mixed-effects models to account for both participant and sample variability
This protocol directly addresses human reasoning challenges by measuring how AI assistance affects documented problems such as cognitive bias, between-examiner reliability, and the effects of workload pressure [83] [89].
Protocol for Evaluating AI System Bias and Fairness
Objective: To assess potential performance disparities across demographic groups in AI-based forensic identification systems.
Materials and Equipment:
- Reference Dataset: Diverse dataset with balanced representation across demographic groups
- AI System: The forensic AI tool to be validated
- Testing Framework: Computational infrastructure for batch processing and metric calculation
- Statistical Analysis Software: R, Python with appropriate packages for fairness metrics
Methodology:
- Dataset Characterization: Document demographic composition of validation dataset using standardized categories
- Stratified Testing: Execute system evaluation across demographic subgroups with identical parameters
- Performance Metric Calculation: Compute accuracy, precision, recall, F1-score, and false match rates for each subgroup
- Disparity Assessment: Calculate comparative metrics between subgroups (e.g., min/max ratios, difference in error rates)
- Bias Mitigation: If disparities detected, implement and evaluate mitigation strategies (e.g., data augmentation, algorithmic adjustments)
This protocol addresses the ethical imperative to ensure AI systems do not exacerbate disparities in the criminal justice system, as highlighted in the DOJ report on AI in criminal justice [90].
Diagram 1: AI-Human Collaborative Forensic Workflow
The Scientist's Toolkit: Research Reagents for AI-Human Forensic Research
Table 3: Essential Materials for Experimental Research on AI in Forensics
| Research Tool | Specification Purpose | Experimental Function |
|---|---|---|
| Validated Reference Datasets | Curated forensic evidence with established ground truth | Gold standard for evaluating AI system performance and reliability [90] |
| Black-Box Testing Frameworks | Standardized protocols for evaluating examiner decisions | Measures accuracy, reproducibility, and repeatability of both human and AI systems [89] |
| Statistical Analysis Packages | R, Python with specialized forensic statistics libraries | Implements likelihood ratio calculations, error rate analysis, and validity testing [92] |
| Bias Assessment Toolkits | AI fairness libraries (e.g., IBM AIF360, Google What-If) | Detects performance disparities across demographic groups in AI systems [90] |
| Human Factors Metrics | Standardized scales for workload, pressure, ambiguity aversion | Quantifies human factors that may influence forensic decision-making [83] [93] |
| Commercial Forensic AI Tools | Specialized software (e.g., AFIS, probabilistic genotyping) | Provides benchmark for general-purpose AI tools; represents current best practices [91] |
Ethical Framework and Implementation Guidelines
Defining Boundaries Through Proportional Governance
Establishing ethical boundaries for AI in forensic workflows requires a proportional governance framework that matches oversight rigor with potential risk. The following diagram illustrates a structured approach to determining the appropriate level of human oversight based on multiple risk factors.
Diagram 2: AI Implementation Risk Assessment Framework
Core Ethical Principles for Implementation
Based on documented human reasoning challenges and AI capabilities, we propose five core principles for defining ethical boundaries in forensic AI implementation:
1. Primacy of Human Judgment for Consequential Decisions: AI systems should not make final determinations regarding source attribution or guilt/innocence in criminal proceedings. Human experts must retain ultimate authority for high-stakes conclusions, particularly given the limitations of AI in understanding contextual factors and the potential for unexplainable outputs from complex models [90] [91].
2. Rigorous Validation and Performance Transparency: AI systems must undergo extensive, domain-specific validation demonstrating reliability across diverse evidence types and demographic groups. Validation results should be publicly available for scrutiny, with continuous monitoring for performance degradation [90] [89].
3. Explainability and Interpretability Requirements: The operational logic of AI systems must be sufficiently transparent to allow meaningful explanation in court testimony. Forensic AI should prioritize interpretable models over "black box" systems when possible, particularly for pattern evidence disciplines [90] [92].
4. Bias Mitigation and Fairness Assurance: Proactive measures must identify and address potential performance disparities across demographic groups. This includes diverse training data, regular fairness auditing, and transparent reporting of differential performance [90].
5. Appropriate Scope Limitation: AI systems should be deployed only for their validated purposes with clear documentation of limitations. Transferring systems to new domains or evidence types requires revalidation [91].
The appropriate ethical boundaries for AI in forensic workflows emerge from a nuanced understanding of both human reasoning challenges and technological capabilities. The optimal framework positions AI as a powerful decision-support tool that augments human expertise while compensating for documented cognitive limitations, rather than as a replacement for human judgment. This balanced approach leverages AI's strengths in processing capacity, consistency, and quantitative analysis while preserving human strengths in contextual understanding, ethical reasoning, and adaptability. As AI technologies evolve, the forensic community must maintain rigorous standards for validation, transparency, and oversight to ensure these tools enhance rather than undermine the pursuit of justice. Future research should focus on developing standardized protocols for AI-human collaboration, more robust validation frameworks, and continuous monitoring systems that can adapt to rapidly advancing AI capabilities while maintaining appropriate ethical boundaries.
Forensic validation is the fundamental process of testing and confirming that forensic techniques and tools yield accurate, reliable, and repeatable results [94]. Within the context of human reasoning challenges, validation acts as a critical safeguard against cognitive biases and errors in judgment. It ensures the scientific integrity of forensic findings and their admissibility in legal proceedings under standards such as the Daubert Standards and US Federal Rules of Evidence, which require that expert evidence is derived from reliable principles and methods [65]. The rapid evolution of technology, including new operating systems, encrypted applications, and cloud storage, demands constant revalidation of forensic tools and practices to mitigate the risks of operational errors, wrongful convictions, and loss of credibility [94].
Core Principles of a Forensic Validation Framework
A robust validation framework is built upon core principles designed to counteract inherent human and systemic vulnerabilities.
- Reproducibility: Results must be repeatable by other qualified professionals using the same method. This principle challenges the subjective nature of human interpretation and provides a mechanism for detecting individual analyst error [94] [65].
- Transparency: All procedures, software versions, logs, and chain-of-custody records must be thoroughly documented. Transparency allows for the critical scrutiny of methods and conclusions, revealing potential cognitive biases or procedural missteps [94].
- Error Rate Awareness: Forensic methods should have known error rates that can be disclosed in reports and during testimony. Acknowledging that error is unavoidable in complex systems is the first step in managing its impact [94] [65].
- Peer Review: Validation processes should be reviewed by the broader forensic community. This collaborative examination helps identify unconscious biases and methodological flaws that may not be apparent to a single analyst or laboratory [94].
- Continuous Validation: Because technology and forensic tools evolve rapidly, tools and methods must be frequently revalidated. This ongoing process ensures that previously validated protocols remain reliable after software updates or in new contexts [94].
The Validation Protocol: A Tiered Methodology
A comprehensive validation protocol must address the tool, the method, and the analysis to ensure end-to-end reliability.
Tool Validation
Tool validation ensures that the forensic software or hardware performs as intended, extracting and reporting data correctly without altering the source. Key practices include [94]:
- Using cryptographic hash values (e.g., SHA-256) to confirm data integrity before and after creating a forensic image.
- Comparing tool outputs against known datasets or test cases with verified content.
- Cross-validating results across multiple tools (e.g., Cellebrite, Magnet AXIOM, MSAB XRY) to identify software-specific parsing inconsistencies.
Method Validation
Method validation confirms that the procedures followed by forensic analysts produce consistent outcomes across different cases, devices, and practitioners. This is vital because the same method applied by different humans can yield different results. Protocol steps include [94]:
- Establishing a detailed, step-by-step Standard Operating Procedure (SOP) for each analysis type.
- Conducting intra-lab and inter-lab proficiency testing to measure consistency between analysts and laboratories.
- Documenting all deviations from the SOP to assess their impact on the final result.
Analysis Validation
Analysis validation evaluates whether the interpreted data accurately reflects its true meaning and context, a stage highly susceptible to cognitive bias. This involves [94]:
- Implementing technical and administrative reviews where a second, independent analyst verifies the first analyst's conclusions.
- Ensuring that logs and reports are transparent and auditable, allowing for the reconstruction of the analytical process.
- Contextualizing digital artifacts within the broader framework of the case to avoid misinterpretation.
The following workflow diagram illustrates the interconnected nature of this tiered validation methodology and its critical feedback loops.
Quantitative Metrics and Error Management
A critical component of validation is the objective measurement of performance and the management of error. Research indicates that error is subjective and multidimensional, meaning there are different perspectives on what constitutes an error and different ways to compute it [65]. The following table summarizes key quantitative metrics used in validation studies.
Table 1: Key Quantitative Metrics for Forensic Validation
| Metric | Description | Calculation / Example | Context in Human Reasoning |
|---|---|---|---|
| Practitioner-Level Error Rate | Frequency of incorrect conclusions by an individual analyst. | Determined through proficiency testing [65]. | Measures individual competence and susceptibility to cognitive bias. |
| Case-Level Error Rate | Frequency of procedural mistakes that pass through technical review. | Metric for a laboratory's quality assurance system [65]. | Reveals weaknesses in systemic checks and balances against human error. |
| Discipline-Level Error Rate | Frequency with which a technique contributes to a wrongful conviction. | Estimated through longitudinal studies and case reviews [65]. | Informs the legal system about the inherent reliability of a scientific discipline. |
| False Positive Rate | Proportion of cases where evidence is incorrectly reported as a match. | Varies by discipline; e.g., documented in firearm and DNA analysis studies [65]. | Directly linked to confirmation bias, where examiners may be influenced by extraneous information. |
| Reproducibility Rate | Percentage of cases where independent analyses yield the same result. | Measured through intra-lab and inter-lab studies [94]. | Quantifies the objectivity and robustness of a method against subjective interpretation. |
The Scientist's Toolkit: Essential Research Reagents and Materials
Validation research requires specific tools and materials to design and execute effective experiments. The following table details essential components of a forensic validation toolkit.
Table 2: Essential Research Reagents and Materials for Validation Studies
| Item | Function in Validation | Application Example |
|---|---|---|
| Known Test Datasets | Provides ground truth data with verified content to test tool accuracy. | Used in tool validation to check if software correctly extracts and parses known artifacts [94]. |
| Proficiency Test Materials | Assesses the competence of individual analysts and the reliability of methods. | Administered regularly to measure practitioner-level error rates and identify training needs [65]. |
| Cryptographic Hashing Tool | Verifies the integrity of digital evidence, ensuring it has not been altered. | Used to generate a hash value (e.g., MD5, SHA-1) for a disk image before and after analysis [94]. |
| Forensic Software Suites | The primary tools under validation for data extraction, parsing, and reporting. | Examples include Cellebrite UFED, Magnet AXIOM, and X-Ways Forensics; validated against known datasets [94]. |
| Reference Standard Devices | Provides a controlled hardware environment for testing mobile and computer forensics tools. | A device with a known state (e.g., specific OS version, installed apps) used to test data extraction methods [94]. |
A Case Study in Validation: FL vs. Casey Anthony
The legal case of Florida vs. Casey Anthony (2011) provides a stark example of the consequences of inadequate validation and the critical role of human reasoning. The prosecution's digital forensic expert initially testified that a family computer had been used to search for the term "chloroform" 84 times, a figure presented as evidence of premeditation [94].
However, the defense, assisted by forensic experts, performed a validation of the forensic software's interpretation. This process revealed that the software had misrepresented the data; in reality, only a single instance of the search term existed. The initial, unvalidated conclusion was a result of the tool's flawed parsing algorithm, which was then compounded by the human expert's failure to critically validate the output [94]. This case underscores how unvalidated tool outputs can mislead human judgment and dramatically alter the perceived facts of a case, highlighting why transparent and reproducible validation is a non-negotiable component of forensic science.
Establishing robust protocols for testing and implementing new forensic technologies is not merely a technical exercise but an essential commitment to scientific integrity and justice. A effective validation framework must be holistic, addressing not only the tools and methods but also the human elements of analysis and interpretation. As forensic science continues to evolve with advancements in artificial intelligence and complex digital environments, the principles of reproducibility, transparency, and continuous validation become even more critical. By embracing a culture where error is educational and managed through rigorous, transdisciplinary frameworks, the forensic community can enhance the reliability of its findings, mitigate cognitive biases, and maintain public trust [65].
Conclusion
The challenges of human reasoning in forensic science are not insurmountable but demand a systematic, multi-faceted response. The key takeaways reveal that cognitive biases are inherent, not indicative of incompetence, and require structured procedural countermeasures like Linear Sequential Unmasking rather than relying on self-awareness alone. Learning from past errors through detailed typologies is crucial for targeted reform, while emerging technologies offer both new tools and novel biases that must be rigorously managed. The future of reliable forensic science lies in embracing a high-reliability organizational culture that integrates continuous training, robust mitigation protocols, and ethical technological augmentation. For biomedical and clinical research, these insights are profoundly transferable, emphasizing the need for similar safeguards in diagnostic interpretation, data analysis, and therapeutic development to prevent cognitive error and uphold the highest standards of scientific integrity.
References
- 1. Challenges to reasoning in forensic science decisions - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC9136362/]
- 2. System 1 and System 2 Thinking [https://thedecisionlab.com/reference-guide/philosophy/system-1-and-system-2-thinking]
- 3. Dual process theory [https://en.wikipedia.org/wiki/Dual_process_theory]
- 4. A New Perspective on Dual-System Theories in Decision ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11591345/]
- 5. Dual Process Theory - an overview [https://www.sciencedirect.com/topics/psychology/dual-process-theory]
- 6. Reducing the impact of cognitive bias in decision making [https://pmc.ncbi.nlm.nih.gov/articles/PMC10319185/]
- 7. Bias, cognitive heuristics, and forensic decision-making [https://dracklin.com/bias-cognitive-heuristics-and-forensic-decision-making/]
- 8. Human Factors in Forensic Science: CSAFE Researchers ... [https://forensicstats.org/blog/2018/01/30/human-factors-forensic-science-csafe-researchers-explain-cognitive-psychologys-role/]
- 9. Challenges to reasoning in forensic science decisions [https://www.sciencedirect.com/science/article/pii/S2589871X2100070X]
- 10. Challenges to reasoning in forensic science decisions [https://www.law.virginia.edu/scholarship/publication/barbara-spellman/1872641]
- 11. A practical approach to mitigating cognitive bias effects in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11720873/]
- 12. Cognitive Bias Affects Perception and Decision-Making in ... [https://www.mdpi.com/2076-328X/15/8/1094]
- 13. Cognitive Forensics: Battling Biases in Forensics Analysis [https://www.forensicscolleges.com/blog/guide-to-cognitive-forensics]
- 14. Evaluating bias in forensic evidence: From expert analysis to ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12639291/]
- 15. A Forensic Science-Based Model for Identifying and ... [https://jaapl.org/content/early/2025/05/05/JAAPL.250019-25]
- 16. Cognitive bias: A cause for concern [https://paloaltou.edu/resources/translating-research-into-practice-blog/cognitive-bias-a-cause-for-concern/]
- 17. Toward Aspirational Forensic Mental Health Practice [https://jaapl.org/content/early/2025/03/05/JAAPL.240123-24]
- 18. Should Medical Experts Giving Evidence in Criminal Trials ... [https://www.mdpi.com/2673-6756/5/1/13]
- 19. Cognitive Bias Affects Perception and Decision-Making in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12383771/]
- 20. A practical approach to mitigating cognitive bias effects in ... [https://www.sciencedirect.com/science/article/pii/S2589871X24001165]
- 21. Unpacking workplace stress and forensic expert decision- ... [https://www.sciencedirect.com/science/article/pii/S2589871X24000202]
- 22. Perceptions of work stress causes and effective ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5353523/]
- 23. Decision Fatigue in Emergency Medicine: An Exploration of Its ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10823191/]
- 24. The possible impact of stress on forensic decision-making [https://www.sciencedirect.com/science/article/pii/S2666353823000115]
- 25. The Relationship Between Decisional Regret and Well ... [https://www.frontiersin.org/journals/psychiatry/articles/10.3389/fpsyt.2021.657224/full]
- 26. Challenges to Reasoning in Forensic Science Decisions [https://nij.ojp.gov/library/publications/challenges-reasoning-forensic-science-decisions]
- 27. Visual perspective taking neural processing in forensic ... [https://www.nature.com/articles/s41598-024-66522-y]
- 28. Top-down predictions in the cognitive brain - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC2099308/]
- 29. A practical tool for information management in forensic decisions [https://pmc.ncbi.nlm.nih.gov/articles/PMC8866671/]
- 30. Using Linear Sequential Unmasking-Expanded (LSU-E) in ... [https://forensicstats.org/blog/portfolio/a-practical-tool-for-information-management-in-forensic-decisions-using-linear-sequential-unmasking-expanded-lsu-e-in-casework/]
- 31. Linear Sequential Unmasking–Expanded (LSU-E) [https://www.sciencedirect.com/science/article/pii/S2589871X21000310]
- 32. Fraud Tip Friday—Navigating Cognitive Bias in Forensic Accounting... [https://www.linkedin.com/pulse/fraud-tip-fridaynavigating-cognitive-bias-forensic-marks-cpa-mba-rr4xe]
- 33. Implementing blind proficiency testing in forensic laboratories [https://pmc.ncbi.nlm.nih.gov/articles/PMC7552087/]
- 34. Scientific guidelines for evaluating the validity of forensic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10576079/]
- 35. Quantification of forensic genetic evidence: Comparison ... [https://www.sciencedirect.com/science/article/pii/S1872497322000564]
- 36. Measuring the Impact of Implementation: 2023 [https://www.nist.gov/adlp/spo/organization-scientific-area-committees-forensic-science/measuring-impact-implementation]
- 37. Elements must meet minimum color contrast ratio thresholds [https://dequeuniversity.com/rules/axe/4.8/color-contrast]
- 38. Burnout and Stress in Forensic Science Jobs: A Systematic ... [https://www.mdpi.com/2227-9032/12/20/2032]
- 39. The Neuroscience of Mindfulness and Resilience Training [https://www.innsightful.com/the-neuroscience-of-mindfulness-and-resilience-training-mechanisms-clinical-evidence-and-future-directions/]
- 40. Enhancing academic resilience through mindfulness training [https://pmc.ncbi.nlm.nih.gov/articles/PMC12626827/]
- 41. Mindfulness training, cognitive performance and stress ... [https://www.sciencedirect.com/science/article/pii/S0167268123003888]
- 42. Evaluating the Use of Mindfulness and Yoga Training on ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7758348/]
- 43. Mindfulness and Meditation: Inward Attention as a Tool for ... [https://www.cogneurosociety.org/mindfulness-and-meditation-inward-attention-as-a-tool-for-mental-health/]
- 44. Challenges to reasoning in forensic science decisions [https://pubmed.ncbi.nlm.nih.gov/35647506/]
- 45. A Forensic Science-Based Model for Identifying and ... [https://jaapl.org/content/53/2/172]
- 46. Hypothesis Testing | A Step-by-Step Guide with Easy ... [https://www.scribbr.com/statistics/hypothesis-testing/]
- 47. Study Identifies Forensic Disciplines Most 'Prone' to Error [https://www.forensicmag.com/609152-Study-Identifies-Forensic-Disciplines-Most-Prone-to-Error/]
- 48. Miscarriages of justice more likely due to forensic science ... [https://www.theguardian.com/law/2025/jun/09/forensic-science-crisis-miscarriages-of-justice-england-and-wales-report]
- 49. Forensic Science Strategic Research Plan, 2022-2026 ... [https://nij.ojp.gov/topics/articles/forensic-sciences-strategic-research-plan-2022-2026]
- 50. OSAC Standards Bulletin - January 2025 | NIST [https://www.nist.gov/magazine/osac-standards-bulletin/january-2025]
- 51. Opinion: Forensic Science Faces an Identity Crisis [https://undark.org/2025/05/08/opinion-forensic-science-bias/]
- 52. The Impact of False or Misleading Forensic Evidence on ... [https://nij.ojp.gov/topics/articles/impact-false-or-misleading-forensic-evidence-wrongful-convictions]
- 53. Human Factors Effecting Forensic Decision Making [https://pubmed.ncbi.nlm.nih.gov/28464220/]
- 54. Flawed Forensics: The Dangerous Legacy of Junk Science ... [https://clutchjustice.com/2025/04/23/flawed-forensics-how-bite-marks-hair-bullet-analysis-and-soil-have-failed-justice-and-what-we-can-do-about-it/]
- 55. The Impact of False or Misleading Forensic Evidence on ... [https://simplyforensic.com/the-impact-of-false-or-misleading-forensic-evidence-on-wrongful-convictions/]
- 56. 5 ways forensic evidence errors can affect your defense [https://www.mooneyesq.com/blog/2025/08/5-ways-forensic-evidence-errors-can-affect-your-defense/]
- 57. Common Forensic Analysis Mistakes in Criminal ... [https://www.alariddefense.com/blog/common-forensic-analysis-mistakes-in-criminal-investigations]
- 58. Wrongful convictions and claims of false or misleading ... [https://pubmed.ncbi.nlm.nih.gov/36946413/]
- 59. Misapplication of Forensic Science [https://innocenceproject.org/misapplication-of-forensic-science/]
- 60. Forensic Science Failures - by Nathan Goetting - Discourse [https://www.discoursemagazine.com/p/forensic-science-failures]
- 61. Influential Texas Commission Says Blood-Spatter ... [https://www.propublica.org/article/texas-forensic-science-commission-blood-spatter-evidence-testimony-murder-case-joe-bryan]
- 62. Fraud in Forensics: Cases of Evidence Tampering and Abuse [https://www.forensicscolleges.com/blog/resources/real-cases-of-forensic-fraud-flawed-evidence]
- 63. 5 Principles of a High Reliability Organization (HRO) [https://blog.kainexus.com/improvement-disciplines/hro/5-principles]
- 64. High Reliability Organization (HRO) Principles and Patient ... [https://psnet.ahrq.gov/perspective/high-reliability-organization-hro-principles-and-patient-safety]
- 65. Understanding 'error' in the forensic sciences: A primer - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC11240290/]
- 66. High Reliability Organizations: Principles, Strategies & ... [https://www.cascade.app/blog/high-reliability-organizations-overview]
- 67. A guide to ISO 21043 Forensic Sciences from the ... [https://www.sciencedirect.com/science/article/pii/S1355030625000887]
- 68. What is Evidence-Based Management? [https://thoughtexchange.com/blog/what-is-evidence-based-management/]
- 69. Management Practices to Build Evidence-Based Decision ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC6053922/]
- 70. The benefits of errors during training - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC9136334/]
- 71. A Guide for Optimizing Resource Allocation [https://www.scup.org/resource/a-guide-for-optimizing-resource-allocation/]
- 72. AI models are already as good as experts at half of tasks ... [https://fortune.com/2025/09/30/ai-models-are-already-as-good-as-experts-at-half-of-tasks-a-new-openai-benchmark-gdpval-suggests/]
- 73. A comparative analysis of human and AI performance in ... [https://www.nature.com/articles/s41598-023-31821-3]
- 74. Humanity's Last Exam: AI vs Human Benchmark Results [https://galileo.ai/blog/humanitys-last-exam-ai-benchmark]
- 75. AI models now match human expert performance on ... [https://inkeep.com/blog/gdpval-ai-expert-performance]
- 76. Technical Performance | The 2025 AI Index Report [https://hai.stanford.edu/ai-index/2025-ai-index-report/technical-performance]
- 77. Benchmarking automation-aided performance in a forensic ... [https://pubmed.ncbi.nlm.nih.gov/39121521/]
- 78. Facial Recognition Technology Trends 2025 Insights - andopen [https://andopen.co.kr/the-state-of-facial-recognition-technology-in-2025-accuracy-performance-and-future-trends/]
- 79. Biased Technology: The Automated Discrimination of ... [https://www.aclu-mn.org/en/news/biased-technology-automated-discrimination-facial-recognition]
- 80. Racial bias in facial recognition algorithms [https://amnesty.ca/features/racial-bias-in-facial-recognition-algorithms/]
- 81. Why We Shouldn't Trust Facial Recognition's Glowing Test ... [https://techpolicy.press/why-we-shouldnt-trust-facial-recognitions-glowing-test-scores]
- 82. Facial Recognition Trends and Statistics [https://getsafeandsound.com/blog/facial-recognition-trends-and-statistics/]
- 83. Human factors in triaging forensic items: Casework ... [https://www.sciencedirect.com/science/article/abs/pii/S1355030625000164]
- 84. Beyond reasonable doubt? AI and the future of forensics [https://www.aa.com.tr/en/health/beyond-reasonable-doubt-ai-and-the-future-of-forensics/3700025]
- 85. Forensic Accounting in the Age of AI: Opportunities and Risks [https://www.cpapracticeadvisor.com/2025/10/09/forensic-accounting-in-the-age-of-ai-opportunities-and-risks/170680/]
- 86. Toward better AFIS practice and process in the forensic fingerprint environment - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC10338967/]
- 87. Impact of Human–Technology Cooperation and Distributed Cognition in Forensic Science: Biasing Effects of AFIS Contextual Information on Human Experts | National Institute of Justice [https://nij.ojp.gov/library/publications/impact-human-technology-cooperation-and-distributed-cognition-forensic-science]
- 88. The impact of human-technology cooperation and distributed cognition in forensic science: biasing effects of AFIS contextual information on human experts - PubMed [https://pubmed.ncbi.nlm.nih.gov/22212067/]
- 89. Accuracy, reproducibility, and repeatability of forensic ... [https://www.sciencedirect.com/science/article/abs/pii/S0379073822002481]
- 90. DOJ Report on AI in Criminal Justice: Key Takeaways [https://counciloncj.org/doj-report-on-ai-in-criminal-justice-key-takeaways/]
- 91. AI as a decision support tool in forensic image analysis [https://pmc.ncbi.nlm.nih.gov/articles/PMC12046100/]
- 92. Statistics [https://forensicstats.org/statistics/]
- 93. Research-Based Practices Can Help Forensic Scientists ... [https://www.nist.gov/blogs/taking-measure/research-based-practices-can-help-forensic-scientists-do-their-best-work]
- 94. What is forensic validation and how is it used? [https://www.envistaforensics.com/knowledge-center/insights/articles/forensic-validation-pay-attention-to-the-man-behind-the-curtain/]