Strategies for Mitigating Contextual Bias in Forensic Laboratory Workflows: From Theory to Practice
This article provides a comprehensive analysis of contextual bias in forensic science, detailing its pervasive effects across disciplines from toxicology to DNA analysis.
Strategies for Mitigating Contextual Bias in Forensic Laboratory Workflows: From Theory to Practice
Abstract
This article provides a comprehensive analysis of contextual bias in forensic science, detailing its pervasive effects across disciplines from toxicology to DNA analysis. It explores the psychological foundations of cognitive bias, including System 1 and System 2 thinking frameworks, and presents empirically-validated mitigation strategies such as Linear Sequential Unmasking-Expanded (LSU-E), blind verification, and case management protocols. Drawing on recent international surveys and case studies, the content addresses implementation barriers, expert fallacies, and validation frameworks through ISO/IEC 17025 accreditation. Designed for forensic researchers, scientists, and laboratory managers, this resource offers practical guidance for enhancing methodological rigor, reducing subjective error, and improving the reliability of forensic conclusions in both research and casework applications.
Understanding the Pervasiveness and Psychology of Forensic Contextual Bias
Defining Cognitive and Contextual Bias in Forensic Science
Troubleshooting Guides
Guide 1: Unexpected Influence of Contextual Information on Analytical Results
Problem: Forensic analysis conclusions appear to be swayed by knowledge of case background information (e.g., suspect confessions, eyewitness accounts, or evidence from other domains) rather than being based solely on the scientific evidence.
Diagnosis Steps:
- Audit Case Documentation: Review case notes and reports for mentions of task-irrelevant information such as a suspect's criminal history, an investigator's presumption of guilt, or results from other forensic analyses [1].
- Check Information Flow: Determine when contextual information was received. Analyses are more vulnerable to bias if examiners were exposed to potentially biasing information before reaching their own scientific conclusions [2] [3].
- Compare with Standards: Verify if the analysis deviated from standard operating procedures (SOPs), for example, by skipping certain tests or confirmatory steps based on expectations [1].
Solutions:
- Immediate Action: Document all information received, including when it was received and its potential influence. Re-analyze the evidence, if possible, using a "blinded" protocol where this contextual information is withheld [3].
- Long-Term Protocol Change: Advocate for the implementation of Linear Sequential Unmasking (LSU) or Linear Sequential Unmasking-Expanded (LSU-E). This protocol controls the sequence and timing of information release to examiners, ensuring they have the necessary data for analysis but are protected from irrelevant contextual information until after their initial assessment is complete [2] [4] [3].
Guide 2: Recurring "Bias Blind Spot" Among Laboratory Staff
Problem: Forensic examiners acknowledge that cognitive bias is a general issue but deny or are unaware of their own susceptibility to it, a phenomenon known as the "bias blind spot" [2] [5].
Diagnosis Steps:
- Conduct a Self-Assessment Survey: Use anonymized surveys to gauge staff understanding of cognitive bias concepts and their perceived personal susceptibility. Past surveys have shown that many examiners are not properly trained about cognitive bias and maintain a bias blind spot [2] [6].
- Review Error and Near-Miss Reports: Analyze casework where initial conclusions were later revised. Check if exposure to contextual information was a factor, indicating a potential bias effect that was not initially recognized [4].
Solutions:
- Immediate Action: Implement mandatory education and training that specifically addresses the six expert fallacies [4] [5]:
- The fallacy that only unethical people are biased.
- The fallacy that only incompetent people are biased.
- The "Expert Immunity" fallacy.
- The "Technological Protection" fallacy.
- The "Bias Blind Spot" fallacy.
- The "Illusion of Control" fallacy.
- Long-Term Protocol Change: Introduce blind verifications as a standard quality control procedure. A second examiner verifies the results without knowledge of the first examiner's findings or any contextual case information, ensuring an independent assessment [4] [3].
Frequently Asked Questions (FAQs)
Q1: What is the fundamental difference between cognitive bias and contextual bias in a forensic setting?
A1: Cognitive bias is an umbrella term describing the various natural, often unconscious, mental shortcuts that can lead to incorrect judgments. Contextual bias is a specific type of cognitive bias where task-irrelevant background information—such as a suspect's confession, evidence from other experts, or an investigator's beliefs—unduly influences the collection, perception, or interpretation of forensic evidence [2] [3] [1]. Essentially, contextual bias is a primary mechanism through which cognitive bias manifests in forensic science.
Q2: Aren't objective, instrument-based disciplines like toxicology or DNA analysis immune to these biases?
A2: No. While the use of instrumentation provides a layer of objectivity, human decision-making is still involved in operating the instrumentation, interpreting the results, and deciding which tests to perform. Empirical research has demonstrated that even experts in these "objective" disciplines are vulnerable to contextual bias [6] [1] [5]. For example, a toxicologist who knows a deceased individual had a history of heroin use might decide to forego a broad screening test, potentially missing relevant compounds [1].
Q3: If I am aware of cognitive bias, can't I just use willpower to avoid it in my analysis?
A3: This belief is known as the "Illusion of Control" fallacy. Cognitive biases operate subconsciously, so awareness alone is insufficient to prevent them [4] [3]. Relying on willpower is not a reliable mitigation strategy. Effective mitigation requires structural changes to the workflow, such as blinding protocols, sequential unmasking, and blind verification, which are designed to prevent exposure to biasing information in the first place [7] [3].
Q4: What is the single most effective step a laboratory can take to mitigate contextual bias?
A4: There is no single silver bullet, but a highly effective strategy is the adoption of case managers and Linear Sequential Unmasking-Expanded (LSU-E) protocols [2] [4] [3]. A case manager acts as a filter, reviewing all incoming information and providing the examiner with only that which is deemed analytically relevant at the appropriate time. LSU-E provides a structured framework for deciding what information is released and when, based on its biasing power, objectivity, and relevance [4] [3].
Quantitative Data on Contextual Bias
The table below summarizes key findings from an empirical survey of forensic toxicology practitioners in China, illustrating the very real impact of contextual information on decision-making.
Table 1: Survey Data on Contextual Bias in Forensic Toxicology (n=200) [6] [1]
| Survey Aspect | Key Finding | Implication |
|---|---|---|
| Deviation from Standard Process | Most participants made decisions deviating from standard procedures under a biasing context. | Contextual information can lead to faster, simpler, but non-standard analytical pathways. |
| Familiarity with Bias Concept | Participants showed a low level of familiarity with the concept and nature of contextual bias. | A lack of training and awareness is a significant vulnerability in laboratory practice. |
| Communication with Investigators | Close contact with police investigators was common; some had a dual role as investigator and examiner. | Organizational structure can directly facilitate the flow of potentially biasing information. |
| Perception of Task-Relevance | There was a general opinion that all available case information should be considered in analysis. | A cultural norm exists that conflates having more information with better analysis, rather than recognizing its potential to bias. |
Experimental Protocols for Bias Research
Protocol 1: Testing for Contextual Bias Using Paired Case Studies
Objective: To empirically measure the effect of task-irrelevant contextual information on forensic decision-making.
Methodology:
- Stimuli Development: Create two versions of a hypothetical forensic case (e.g., a toxicology or fingerprint case). The "context" version includes extraneous, potentially biasing information (e.g., "the suspect has confessed"). The "no-context" version is identical but omits this information [6] [1].
- Participant Recruitment: Recruit forensic practitioners from the target discipline. Participants should be randomly assigned to evaluate one version of the case.
- Task: Participants analyze the case evidence and report their conclusions and the steps they would take.
- Data Analysis: Compare the outcomes (e.g., conclusions, steps skipped, tests ordered) between the two groups. A statistically significant difference indicates the contextual information biased the results [1].
Protocol 2: Implementing and Validating a Linear Sequential Unmasking-Expanded (LSU-E) Workflow
Objective: To integrate a structured information management protocol into a laboratory workflow and assess its impact on reducing cognitive bias.
Methodology:
- Worksheet Development: Create an LSU-E worksheet to be used for each case. This worksheet should list all available information and require the examiner/case manager to rate each piece for its Relevance, Objectivity, and Biasing Power before the analysis begins [4] [3].
- Sequential Information Release: Based on the ratings, the protocol dictates the order in which information is released to the examiner. Essential, low-bias information is provided first to allow for an initial analysis. High-bias information is provided later or withheld entirely [4].
- Blind Verification: After the primary analysis, a second examiner performs a verification. This verification should be conducted blindly, without knowledge of the first examiner's results or the contextual information [3].
- Validation: Track key metrics pre- and post-implementation, such as the rate of conclusive versus inconclusive findings, inter-examiner agreement, and the frequency of contextual information being documented as influential [4].
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Materials and Protocols for Bias-Mitigated Forensic Research
| Tool / Protocol | Function | Application in Workflow |
|---|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | A structured framework to control the flow of information to examiners, minimizing premature exposure to biasing context. | Used at the case intake and assignment phase to plan the sequence of analysis [4] [3]. |
| Blind Verification | A quality control procedure where a second examiner independently verifies results without knowledge of the initial findings or contextual details. | Applied after the primary analysis is complete to ensure objectivity and independence [4] [3]. |
| Case Manager | A role or system dedicated to filtering incoming case information and acting as a liaison between investigators and examiners. | Serves as a "firewall" to prevent contextual contamination before the analytical phase begins [2] [3]. |
| Evidence Line-ups | Presenting several known-innocent samples alongside the suspect sample during comparative analyses to prevent confirmation bias. | Used in pattern-matching disciplines (e.g., fingerprints, firearms) to counteract inherent assumptions of a single-suspect comparison [3]. |
| Pre-Analytical Worksheet | A documented pre-analysis plan where examiners define their evaluation criteria and sequence of operations before exposure to reference materials. | Helps commit to an objective methodology and reduces the temptation to adjust criteria to fit a desired outcome [3]. |
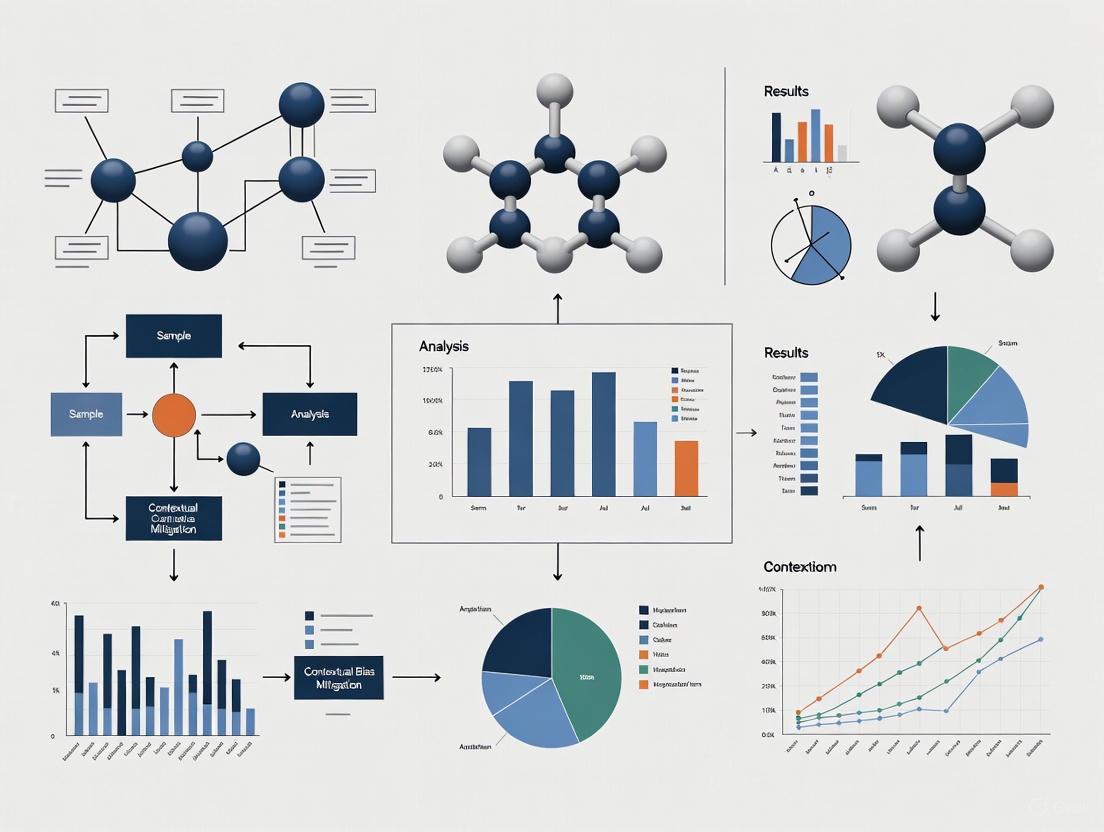
Workflow Diagrams
Cognitive Bias Mitigation Protocol
FAQ: Core Concepts and Definitions
What are System 1 and System 2 thinking? System 1 and System 2 are two distinct modes of cognitive processing introduced by Daniel Kahneman [8]. Their key characteristics are summarized below [5] [9] [8]:
| Feature | System 1 (Fast Thinking) | System 2 (Slow Thinking) |
|---|---|---|
| Speed | Fast, automatic, instantaneous | Slow, deliberate, effortful |
| Effort | Low or no effort, effortless | High effort, requires conscious attention |
| Control | Unconscious, intuitive, involuntary | Conscious, analytical, controlled |
| Process | Relies on heuristics (mental shortcuts) | Relies on logical rules and reasoning |
| Role | Gut feelings, snap judgements, pattern recognition | Complex problem-solving, critical evaluation |
Why is understanding these systems critical for forensic and drug development researchers? Expert decision-making is vulnerable to the cognitive shortcuts (heuristics) of System 1, which can introduce significant bias into analytical results [5] [10]. In forensic science, ostensibly objective data can be affected by bias driven by contextual, motivational, and organizational factors [5]. In drug development, machine learning models used to predict outcomes can be skewed by various forms of bias in historical data, affecting both financial value and patient safety [11]. Mitigating these biases requires structured, external strategies that engage the analytical power of System 2 [5].
What is the relationship between System 1 thinking and cognitive bias? System 1 thinking operates using heuristics to make efficient snap judgements [9]. While useful in daily life, these shortcuts can lead to systematic errors in scientific and clinical settings [5]. For example:
- Confirmation Bias: The tendency to seek, interpret, and favor information that confirms pre-existing beliefs [9] [10]. Once System 1 forms an initial belief, it becomes difficult to change, leading to "tunnel vision" [9].
- Representativeness Heuristic: Judging the probability that a person or item belongs to a group based only on how well it matches a stereotype, while ignoring base rate statistics [9].
FAQ: Bias Identification and Troubleshooting
What are common cognitive biases I might encounter in the laboratory? Researchers should be vigilant for the following common biases [10]:
| Bias | Description | Potential Impact in the Lab |
|---|---|---|
| Confirmation Bias | Selectively gathering or weighting evidence that supports an initial hypothesis while neglecting contradictory evidence. | Interpreting ambiguous data to support expected outcomes; dismissing anomalous results as "noise." |
| Base Rate Neglect | Ignoring or misusing the underlying prevalence of a condition or event in the population. | Over- or under-estimating the significance of a finding by failing to account for how common it truly is. |
| Hindsight Bias | Overestimating the predictability of an outcome after it is already known. | Influencing retrospective data analysis or audits, making it harder to learn from past unexpected results. |
| Allegiance Bias | A subtle form of confirmation bias where an expert's opinion is swayed by financial incentives or the side that retained them. | Compromising objectivity in settings where funding or partnership interests are present. |
I consider myself an ethical, competent expert. Am I still vulnerable to these biases? Yes. Vulnerability to cognitive bias is a human attribute and does not reflect a person's character or competence [5]. Experts often hold several "fallacies" that increase their risk, including [5]:
- The Ethical Immunity Fallacy: Believing only unethical practitioners are biased.
- The Competence Fallacy: Believing bias is only a result of incompetence.
- The Expert Immunity Fallacy: Belieiving expertise itself shields one from bias.
- The Bias Blind Spot: Perceiving others, but not oneself, as vulnerable to bias.
How can I tell if my data interpretation is being influenced by System 1 biases? Be alert to these warning signs in your workflow:
- Feeling Certainty Too Quickly: A strong, intuitive conclusion forms before all data is systematically analyzed [9].
- Discounting Discrepancies: Dismissing or explaining away results that don't fit the expected pattern without rigorous investigation [10].
- Seeking Only Confirmatory Evidence: Designing analyses or tests primarily to prove a hypothesis rather than to challenge it [9].
Experimental Protocols for Bias Mitigation
This section provides detailed methodologies for key experiments and procedures cited in bias mitigation research.
Protocol 1: Implementing Linear Sequential Unmasking-Expanded (LSU-E) LSU-E is a procedural method designed to minimize contextual bias by sequencing analytical tasks and controlling information flow [12] [13].
- Objective: To ensure key analytical judgments are made before exposure to potentially biasing contextual information (e.g., suspect history, other evidence).
- Materials: Case materials, standardized reporting forms, an independent case manager.
- Procedure:
- Step 1: Initial Analysis. The examiner performs all initial analyses using only the essential, non-biasing information required (e.g., a questioned sample and a set of reference samples).
- Step 2: Documentation. The examiner documents their initial findings, conclusions, and the confidence level in a preliminary report before proceeding.
- Step 3: Controlled Information Revelation. A case manager, who is fully informed of the case context, then reveals specific, pre-determined pieces of relevant information to the examiner in a structured sequence.
- Step 4: Integrated Analysis. After each piece of new information is revealed, the examiner re-evaluates their findings and notes any changes or reaffirmations.
- Validation: This protocol has been successfully piluted in forensic document and bloodstain pattern analysis, demonstrating reduced subjectivity and enhanced reliability [12] [13].
Protocol 2: The Case Manager Model This model separates informational functions within the laboratory to insulate examiners from unnecessary contextual information [13] [14].
- Objective: To create a barrier between investigators (who possess full case context) and forensic examiners (who perform analytical tasks).
- Materials: Modified case submission forms, a designated case manager role.
- Procedure:
- Step 1: Case Intake. The case manager receives all case information from investigators or attorneys.
- Step 2: Information Filtering. The case manager reviews the information and filters out all details not strictly necessary for the analytical examination (e.g., suspect confessions, prior criminal record).
- Step 3: Task Assignment. The case manager provides the "context-stripped" evidence and a specific analytical task to the examiner.
- Step 4: Result Reporting. The examiner returns their findings to the case manager, who then integrates them back into the full case context.
- Validation: Found and Ganas (as cited in [14]) successfully implemented this system using modified forms and email notices, effectively insulating document examiners from biasing information.
Protocol 3: Blind Verification This is a quality control procedure where a second examiner independently verifies the results of the first without exposure to the first examiner's conclusions or the biasing context [13].
- Objective: To independently replicate key judgments and ensure they are robust and not influenced by the initial examiner's potential biases.
- Materials: The same evidence samples used in the initial analysis.
- Procedure:
- Step 1: Initial Examination. The first examiner completes their analysis, which may or may not be blind to context.
- Step 2: Blind Re-examination. The original evidence is submitted to a second examiner for a completely independent analysis. This second examiner is blinded to the first examiner's findings and to any potentially biasing contextual information.
- Step 3: Comparison. The conclusions of both examiners are compared. Any discrepancies are resolved through a structured process, such as a conference or review by a third senior examiner.
The Scientist's Toolkit: Key Research Reagent Solutions
Essential materials and procedural "reagents" for conducting robust, bias-aware research.
| Tool / Solution | Function in Mitigating Bias |
|---|---|
| Linear Sequential Unmasking (LSU) | A procedural "reagent" that sequences information flow to protect core analytical judgments from contamination by contextual information [12] [13]. |
| Case Manager Protocol | An organizational "buffer solution" that filters out unnecessary and potentially biasing information before it reaches the analyst [13] [14]. |
| Blind Verification | A quality control "assay" that tests the robustness of an initial finding by having it independently replicated in a blinded manner [13]. |
| Pre-Documented Findings | A methodological "fixative" that locks in initial impressions and confidence levels before subsequent information or peer pressure can influence them [12]. |
| Cognitive Bias Awareness Training | A foundational "primer" that makes individuals and teams aware of the inherent vulnerabilities of System 1 thinking and common expert fallacies [5] [10]. |
| Standardized Reporting Forms | A "scaffolding" tool that structures the documentation of results, forcing consideration of alternative hypotheses and ensuring consistent evaluation criteria across cases [12]. |
Workflow and Relationship Visualizations
Diagram 1: Integrated Bias Mitigation Workflow. This diagram illustrates a combined protocol integrating the Case Manager Model and Linear Sequential Unmasking, with an optional Blind Verification step for critical findings.
Diagram 2: System 1 and System 2 Interaction in Analysis. This diagram shows the competition between the two cognitive systems when processing data. Unmitigated, System 1 often dominates, leading to potential bias. Structured protocols are designed to force the engagement of System 2 for more reliable outcomes.
FAQs: Understanding Bias Contamination
What is contextual bias in forensic science? Contextual bias occurs when a forensic examiner's judgment is unconsciously influenced by task-irrelevant information about the case. This is a form of "cognitive contamination" where extraneous details—such as a suspect's criminal record, eyewitness identifications, or other evidence—can affect how evidence is collected and evaluated. It is not a result of unethical behavior or incompetence, but rather a natural function of human cognition where the brain uses shortcuts in ambiguous situations [4] [2].
What empirical evidence demonstrates confirmation bias in forensic disciplines? A systematic review of 29 studies across 14 forensic disciplines found robust evidence of confirmation bias effects [15]. The research shows that forensic examiners' conclusions can be influenced by:
- Knowledge of case-specific information about the suspect or crime scenario (9 of 11 studies showed this effect)
- The way reference materials are presented (4 of 4 studies)
- Knowledge of a previous examiner's decision (4 of 4 studies) [15]
What are the real-world consequences of forensic confirmation bias? Forensic errors have led to wrongful convictions and lasting injustices:
- Brandon Mayfield: Wrongfully implicated in the 2004 Madrid train bombings due to a fingerprint misidentification, despite having no connection to Spain [16] [17]. Multiple FBI examiners confirmed the erroneous match, demonstrating how cognitive bias can affect even experienced professionals [4].
- Josiah Sutton: Served 4 years in prison for rape after Houston Crime Lab analysts misidentified his DNA. The lab was later found to have systemic issues including cross-contamination and human error [16].
- Toxicology Errors: In the District of Columbia, breath alcohol analyzers were miscalibrated 20-40% too high for 14 years before discovery, affecting thousands of cases [18].
Can technology eliminate cognitive bias in forensic analysis? No. The "technological protection fallacy" incorrectly assumes that technology, algorithms, or AI will completely resolve subjectivity. These systems are still built, programmed, and interpreted by humans, and can even amplify existing biases if not properly designed and monitored [4] [17]. Technological tools can help reduce bias but cannot eliminate it entirely.
Troubleshooting Guides: Mitigating Bias in Laboratory Workflows
Problem: Cross-Contamination and Error in DNA Analysis
Issue: DNA evidence has been misinterpreted due to laboratory error and cross-contamination, leading to wrongful convictions.
Empirical Case Study: The Josiah Sutton case demonstrated how laboratory errors and misinterpretation can have severe consequences. The Houston Crime Lab misidentified Sutton's DNA as matching evidence from a rape case, leading to his wrongful conviction. An independent review later revealed the DNA never actually matched, exposing systemic failures in the lab's procedures [16].
Solution Protocol: Linear Sequential Unmasking-Expanded (LSU-E) This methodology sequences analytical tasks to ensure key judgments are made before exposure to potentially biasing information:
- Document all initial observations from the evidence sample before any comparisons
- Record all relevant features and measurements objectively
- Make initial assessments without reference to suspect samples
- Only then compare with known reference samples
- Blind verification by a second examiner unaware of the first examiner's conclusions [4] [19]
Table: DNA Analysis Error Patterns and Detection
| Error Type | Case Example | Detection Method | Consequence |
|---|---|---|---|
| Sample Contamination | Houston Crime Lab | Independent audit | Wrongful conviction; lab shutdown |
| Misinterpretation of Results | Josiah Sutton case | Technical review | 4 years wrongful imprisonment |
| Systemic Quality Failures | Multiple cases | External oversight | Widespread case reviews required |
Problem: Cognitive Bias in Fingerprint Analysis
Issue: Even highly trained fingerprint examiners can erroneously match prints when exposed to contextual biasing information.
Empirical Case Study: The Brandon Mayfield case represents a classic example of contextual bias in fingerprint analysis. Despite Mayfield's fingerprint only partially resembling the one found in Madrid, multiple FBI examiners—including a highly respected supervisor—confirmed the erroneous match. Investigators, eager for a suspect, forced the evidence to fit their theory [16]. Verifiers who knew the initial conclusion made by their esteemed colleague unconsciously assumed "identification" was correct [4].
Solution Protocol: Case Manager Model with Blind Verification This approach separates case information management from analytical functions:
- Implement a case manager who receives all case information and evidence
- Case manager prepares materials for examiners, filtering out potentially biasing task-irrelevant information
- Examiners conduct analysis using only the information needed for their technical tasks
- Blind verification by independent examiner unaware of initial findings
- Resolution process for any discrepant results between examiners [13]
Enhanced Fingerprint Analysis Workflow with Bias Mitigation
Problem: Systemic Errors in Toxicology
Issue: Toxicology errors—including calibration problems, traceability issues, and discovery violations—have persisted for years or even decades before detection, typically being discovered by external sources rather than internal quality controls [18].
Empirical Case Studies:
- District of Columbia: Breath alcohol analyzers miscalibrated 20-40% too high for 14 years before discovery by a new employee [18]
- Washington State: Incorrect formula in spreadsheet used to calculate reference material concentration; fraud involving false certifications about who performed testing [18]
- Maryland: Laboratory used single-point calibration curves for blood alcohol analysis from 2011-2021, despite this method being scientifically inappropriate as it doesn't span the entire concentration range of interest [18]
Solution Protocol: Comprehensive Quality Assurance with Third-Party Oversight
- Multi-point calibration spanning entire concentration range of interest
- Regular independent audits of calibration protocols and reference materials
- Digital data retention with complete traceability of all adjustments and calculations
- Mandatory disclosure protocols for all exculpatory evidence
- Whistleblower protections for staff reporting quality issues [18]
Table: Toxicology Error Patterns and Reform Strategies
| Error Category | Example Cases | Duration Before Detection | Recommended Reform |
|---|---|---|---|
| Calibration Errors | DC, Maryland, Pennsylvania | 10-14 years | Multi-point calibration, independent audits |
| Traceability Issues | Alaska, Washington State | Years to decades | Digital data retention, full transparency |
| Discovery Violations | Multiple jurisdictions | Varies | Mandatory disclosure portals, whistleblower protections |
| Reference Material | Minnesota, New Jersey | 2+ years | Proper assignment protocols, validation |
Improved Toxicology Quality Assurance Pathway
Table: Key Research Reagent Solutions for Bias-Resistant Forensic Workflows
| Tool/Technique | Primary Function | Application Context | Evidential Support |
|---|---|---|---|
| Linear Sequential Unmasking (LSU/LSU-E) | Sequences information exposure to prevent premature conclusions | All comparative forensic disciplines | Empirical studies show reduced contextual bias effects [4] [13] |
| Case Manager Model | Separates contextual information management from analytical functions | Complex multi-evidence cases | Pilot programs demonstrate improved reliability [4] [13] |
| Blind Verification | Independent confirmation without exposure to previous conclusions | All subjective interpretation tasks | Research shows 4 of 4 studies found bias from knowledge of previous decisions [15] |
| Multiple Comparison Samples | Prevents narrow focus on single suspect | Pattern evidence disciplines | 4 of 4 studies show procedure affects examiner conclusions [15] |
| Context Management Protocols | Systematically limits exposure to task-irrelevant information | Laboratory settings | Supported by PCAST (2016) and NAS (2009) recommendations [4] [18] |
Frequently Asked Questions (FAQs) on Cognitive Bias
1. What are the six common fallacies about bias that experts believe? Many experts operate under six key fallacies about bias, which can increase their vulnerability to its effects [20] [21]:
- The Ethical Fallacy: The mistaken belief that bias is an ethical issue or a sign of dishonesty. In reality, cognitive bias impacts honest and dedicated professionals due to brain architecture, not a lack of character [20] [21].
- The "Bad Apples" Fallacy: The tendency to blame errors on individuals rather than recognizing that cognitive bias is a widespread, systemic issue not linked to incompetency [20] [21].
- The Expert Immunity Fallacy: The incorrect belief that experts are impartial and immune to biases. In fact, expertise can sometimes make professionals more susceptible due to their use of mental shortcuts and expectations from past experiences [20] [21].
- The Technological Protection Fallacy: The assumption that technology, automation, or machine learning eliminates bias. However, these systems are built, programmed, and interpreted by humans, so biases can still be introduced [20] [21].
- The Bias Blind Spot: The tendency for people to believe they are less affected by cognitive biases than others [20] [21].
- The Illusion of Control: The belief that one can overcome biases through mere willpower. This can be counterproductive, as increased effort to suppress a bias may sometimes amplify its effect due to "ironic processing" [20] [21].
2. How can bias affect the work of a forensic scientist or researcher? Bias can infiltrate multiple stages of an analysis [20] [21]:
- What the data are: Biases can influence how data is sampled, collected, or what is considered relevant and what is dismissed as noise.
- The actual results: Decisions on testing strategies, how an analysis is conducted, and when to stop testing can be biased.
- The conclusions: The final interpretation of results can be skewed to align with pre-existing expectations or contextual information.
3. What are some specific cognitive biases I should be aware of in my work? Several cognitive biases are particularly relevant in scientific and analytical work [22]:
- Confirmation Bias: The tendency to seek out or favor information that confirms one's pre-existing beliefs or hypotheses.
- Anchoring Bias: Relying too heavily on the first piece of information encountered (the "anchor") when making decisions.
- Overconfidence Bias: The tendency to have excessive confidence in one's own judgments or abilities.
- Selection Bias: Systematically including or excluding certain data or samples, leading to skewed conclusions.
- Base Rate Neglect: Ignoring general statistical information (base rates) in favor of specific, case-specific information [23].
Troubleshooting Guide: Mitigating Bias in Your Workflow
Problem: Suspected contextual bias influencing analytical decisions.
Solution: Implement a structured debiasing protocol.
The following workflow, based on practices successfully implemented in forensic laboratories, outlines a systematic approach to minimize cognitive bias [24] [25].
Diagram: A sequential workflow for mitigating cognitive bias, incorporating blinding and structured evaluation.
Detailed Experimental Protocols for Bias Mitigation
1. Protocol: Linear Sequential Unmasking-Expanded (LSU) This methodology controls the sequence and timing of information exposure to prevent biasing from reference materials [25].
- Objective: To ensure that the initial evidence is evaluated without being influenced by known reference samples or task-irrelevant contextual information.
- Procedure:
- Initial Analysis: The analyst performs an initial assessment of the evidence sample (e.g., a fingerprint, DNA profile, or document) in isolation.
- Record Findings: Document all initial observations, features, and potential conclusions before any comparison is made.
- Controlled Comparison: Only after the initial analysis is complete and documented is the evidence compared to a reference sample.
- Re-evaluation: Re-examine the evidence in the context of the reference sample and document any changes in interpretation, including the rationale.
2. Protocol: Blind Verification This protocol ensures an independent review of the evidence [25].
- Objective: To obtain a second opinion that is free from the influence of the primary analyst's conclusions or contextual information.
- Procedure:
- Case Manager Role: A case manager screens the case file and provides the evidence to the verifying analyst.
- Information Control: The verifying analyst is not informed of the primary analyst's results or any potentially biasing contextual details about the case.
- Independent Analysis: The verifier conducts their own analysis following the same LSU protocol.
- Comparison of Results: The results from the primary and verifying analyst are compared. Any discrepancies are resolved through a structured process before a final conclusion is reached.
Research Reagent Solutions: The Bias Mitigation Toolkit
The following table details key methodological "reagents" essential for designing robust experiments and analyses resistant to cognitive bias.
| Tool / Solution | Function & Explanation |
|---|---|
| Blinding & Masking | Prevents exposure to task-irrelevant information (e.g., suspect details, other analysts' opinions) that can skew perception and interpretation [21] [25]. |
| Linear Sequential Unmasking (LSU) | A structured protocol that controls the sequence of information exposure, ensuring evidence is evaluated before comparison to references to prevent backward reasoning [21] [25]. |
| Case Manager | An individual or system that screens and controls what information is provided to analysts and when, acting as a filter against biasing information [21] [25]. |
| Multiple Hypotheses | The practice of actively generating and considering alternative explanations or conclusions to counter confirmation bias and encourage exploratory analysis [21]. |
| Differential Diagnostic Approach | A framework where different possible conclusions are presented along with their associated probabilities, promoting transparent and balanced reasoning [21]. |
| Blind Proficiency Testing | A quality control measure where analysts are tested with samples without their knowledge, providing objective data on performance and error rates [24]. |
FAQs: Understanding Cognitive Bias in the Forensic Laboratory
This section addresses common questions about the nature, sources, and impact of cognitive bias in forensic science workflows.
Q1: What is cognitive bias, and why is it a problem in forensic science?
Cognitive bias refers to the unconscious and automatic mental shortcuts that can influence judgment, particularly in situations involving ambiguity or insufficient data [4]. In forensic science, this is problematic because disciplines that rely on human experts to make pattern-matching judgments (e.g., fingerprints, handwriting) are susceptible to these biases, which can introduce error into the criminal legal system [4]. These biases are not a result of incompetence or unethical behavior but are a normal part of human cognition that must be managed through systemic safeguards [4].
Q2: I am an experienced examiner. Aren't I immune to bias?
This belief is a common misconception known as the "Expert Immunity" fallacy [4]. Expertise does not cure bias; in fact, extensive experience may cause experts to rely more heavily on automatic decision-making processes. Another prevalent misconception is the "Bias Blind Spot," where individuals acknowledge bias as a general problem but believe they are personally less vulnerable to it [4]. Awareness of bias is crucial, but willpower alone is insufficient to prevent it, as these processes occur unconsciously [4].
Q3: What are the main sources of bias in a forensic examination?
A 2020 summary identifies eight key sources of bias that can uniquely and compoundingly affect expert decisions [4]:
- The Data: The evidence itself can contain biasing elements or evoke emotions.
- Reference Materials: The materials used for comparison can influence conclusions.
- Contextual Information: Task-irrelevant information about the case can inappropriately influence judgment.
- Base-Rate Expectations: Prior expectations about how common a finding might be.
- The Examiner's Own Background: Personal experiences and beliefs.
- Organizational Factors: The culture and pressures within the laboratory.
- The Presentation of Results: How findings are communicated and reported.
- The Human Factors of the Examiner: The individual's cognitive state (e.g., fatigue, stress).
Q4: Can't technology and AI completely eliminate bias from our workflows?
This belief is the "Technological Protection" fallacy [4]. While artificial intelligence, advanced instruments, and automation can significantly reduce bias, they will not eliminate it. These systems are built, programmed, operated, and interpreted by humans, meaning bias can still be introduced at various stages of their development and use [4].
Troubleshooting Guides: Mitigating Bias in Your Workflows
Guide 1: Troubleshooting Contextual Bias in Forensic Examination
Problem: Forensic conclusions are being inappropriately influenced by task-irrelevant contextual information (e.g., knowing about a suspect's confession or other evidence not related to the pattern-matching task).
Application Scope: This guide is designed for forensic examiners and laboratory managers in pattern-matching disciplines such as fingerprint analysis, questioned documents, and firearms examination.
Process:
- Identify the Problem: A conclusion in a case does not align with the expected scientific objectivity. The first step is to acknowledge the potential for bias without assigning blame [4].
- List All Possible Explanations/Sources: Use the list of eight sources of bias as a checklist to identify potential biasing influences in your specific case and laboratory environment [4].
- Collect Data: Review the case workflow to identify where task-irrelevant information could have been introduced. Was the case manager protocol followed? Was a blind verification performed? [4].
- Eliminate Some Explanations: Based on the data, rule out sources that were properly controlled. For example, if a blind verification was conducted and confirmed the original result, this reduces the likelihood that contextual bias was the sole cause.
- Check with Experimentation (Implement Mitigation Strategies): If contextual bias is a likely factor, design and implement procedural changes. Key research-based strategies include [4]:
- Linear Sequential Unmasking-Expanded (LSU-E): Revealing case information to the examiner in a structured sequence, only after their initial analysis of the evidence is complete.
- Blind Verification: Having a second examiner verify the results without knowledge of the first examiner's conclusion or any contextual information.
- Case Manager Model: Using a case manager to filter information and provide examiners with only the data essential for their specific analysis.
- Identify the Cause: After implementing mitigation strategies, re-evaluate the evidence. If conclusions become more robust and less variable, it indicates that contextual bias was a likely contributing factor. Document this outcome to support ongoing use of these procedures [4].
Guide 2: Troubleshooting Bias in Machine Learning Models for Forensic Data Classification
Problem: A machine learning model used for classifying forensic data (e.g., DNA samples, chemical spectra) is producing skewed or unfair outcomes, indicating potential algorithmic bias.
Application Scope: This guide is for data scientists and researchers developing or using ML models for classification tasks in forensic science laboratories.
Process:
- Identify the Problem: The model's predictions show statistically significant disparities across different sensitive or protected groups (e.g., demographic groups) when evaluated with fairness metrics [26].
- List All Possible Explanations/Sources: Bias can originate from the training data (e.g., unrepresentative samples), the model algorithm itself, or the interpretation of the outputs [26].
- Collect Data: Use fairness metrics like Demographic Parity, Equalized Odds, or Statistical Parity to quantify the bias in the model's predictions [26].
- Eliminate Some Explanations: Based on the metric results, hypothesize where in the ML pipeline the bias is most likely introduced.
- Check with Experimentation (Implement Mitigation Strategies): Apply bias mitigation techniques based on the stage of the ML pipeline [26]:
- Pre-processing: Adjust the training data before model training. Techniques include:
- Reweighing: Assigning different weights to training instances to balance the impact of protected groups.
- Sampling: Using methods like SMOTE (Synthetic Minority Over-sampling Technique) to balance dataset distribution [26].
- Feature-wise Mixing: A newer method that redistributes feature representations across datasets, which has been shown to reduce bias by 43.35% on average without needing explicit bias attribute identification [27].
- In-processing: Modify the learning algorithm during training.
- Regularization: Adding a fairness term to the algorithm's loss function to penalize discrimination.
- Adversarial Debiasing: Training a competing model to try to predict the protected attribute from the main model's predictions, thereby forcing the main model to learn features that are independent of the protected attribute [26].
- Post-processing: Adjust the model's outputs after training.
- Reject Option based Classification (ROC): Changing the predicted labels for instances where the model has low confidence, typically assigning favorable outcomes to unprivileged groups and unfavorable outcomes to privileged groups [26].
- Pre-processing: Adjust the training data before model training. Techniques include:
- Identify the Cause: After applying one or more mitigation techniques, re-run the fairness metrics. A significant reduction in disparity confirms the presence of algorithmic bias and the effectiveness of the chosen mitigation strategy.
Data Presentation: Quantitative Findings on Bias Mitigation
Table 1: Performance of Machine Learning Bias Mitigation Techniques
This table summarizes the effectiveness of different categories of bias mitigation methods used in classification tasks, based on a review of available strategies [26].
| Mitigation Category | Example Methods | Key Mechanism | Relative Effectiveness & Notes |
|---|---|---|---|
| Pre-processing | Reweighing, SMOTE, Feature-wise Mixing [27] [26] | Modifies the training dataset to remove bias before model training. | Feature-wise mixing reported 43.35% average bias reduction and significant decrease in Mean Squared Error [27]. |
| In-processing | Adversarial Debiasing, Prejudice Remover [26] | Alters the learning algorithm to incorporate fairness constraints during model training. | Directly penalizes bias in the objective function; can be highly effective but may require more specialized expertise to implement. |
| Post-processing | Reject Option Classification, Calibrated Equalized Odds [26] | Adjusts the model's predictions after they have been generated. | Useful when you cannot modify the model or training data; generally considered less frequent in literature than other methods [26]. |
Table 2: Checklist for Reporting Experimental Protocols to Enhance Reproducibility
A guideline for reporting experimental protocols proposes 17 key data elements to ensure reproducibility. The table below lists a subset of these fundamental elements [28].
| Data Element Category | Specific Item to Report | Importance for Reproducibility |
|---|---|---|
| Materials & Reagents | Unique identifiers (e.g., catalog numbers, RRIDs) [28] | Unambiguously identifies exact reagents used, as properties can vary between lots and suppliers. |
| Experimental Parameters | Precise values (e.g., temperature, time, concentration) [28] | Avoids ambiguities like "room temperature" or "store overnight," which can lead to procedural variations. |
| Sample Description | Relevant characteristics and preparation methods [28] | Provides necessary context for the experimental system and allows others to replicate the sample prep. |
| Workflow & Steps | A detailed, sequential description of the process [28] | Serves as the primary recipe for the experiment, enabling others to follow the same sequence of actions. |
Experimental Protocols
Protocol 1: Implementing a Linear Sequential Unmasking (LSU) Workflow
Objective: To minimize the influence of contextual and confirmation bias during the forensic examination of pattern evidence by controlling the sequence of information revelation [4].
Key Research Reagent Solutions & Materials:
- Case File: Contains all evidence and contextual information.
- Laboratory Information Management System (LIMS): Used to manage and restrict access to case information.
- Standard Operating Procedure (SOP) Document: Details the LSU steps and rules.
Methodology:
- Initial Analysis: The examiner is provided only with the evidence item requiring analysis (e.g., a latent fingerprint). All contextual information (e.g., suspect statements, other forensic reports) is withheld.
- Documentation: The examiner performs their analysis and documents their findings, conclusions, and confidence level based solely on the evidence.
- Controlled Revelation: The case manager or system then reveals the first piece of additional information, typically the known reference sample(s) (e.g., a suspect's fingerprint card).
- Comparison: The examiner compares their documented analysis from Step 2 with the new information.
- Final Conclusion: The examiner integrates all information to form a final conclusion. This structured process helps isolate the examiner's objective analysis of the evidence from biasing contextual influences [4].
Protocol 2: Feature-Wise Mixing for Mitigating Contextual Bias in Predictive Models
Objective: To reduce contextual bias in supervised machine learning models by redistributing feature representations across multiple datasets, without requiring explicit identification of bias attributes [27].
Key Research Reagent Solutions & Materials:
- Source Datasets: Multiple datasets containing the predictive features and labels, presumed to contain different contextual biases.
- Computational Environment: Python/R environment with standard ML libraries (e.g., scikit-learn).
- Evaluation Metrics: Bias-sensitive loss functions (e.g., disparity metrics, Mean Squared Error).
Methodology:
- Dataset Preparation: Assemble your source datasets. The method is designed to work without pre-defined bias attributes.
- Feature-wise Mixing: Apply the feature-wise mixing framework. This involves systematically mixing or recombining feature columns from the different source datasets to create a new, blended training dataset. This process redistributes the feature representations that may be associated with contextual biases [27].
- Model Training: Train multiple ML classifiers (e.g., Logistic Regression, Decision Trees, Support Vector Machines) on the newly created mixed dataset using standard cross-validation techniques [27].
- Evaluation: Evaluate the trained models using the chosen bias-sensitive metrics and Mean Squared Error (MSE). Compare the results against models trained on the original, unmixed data or with other mitigation techniques like SMOTE [27].
- Validation: The protocol is considered successful if the models trained on the mixed dataset show a statistically significant reduction in bias metrics and MSE compared to baseline models [27].
Workflow Visualization
Forensic Bias Mitigation Strategy Map
Machine Learning Bias Mitigation Pathways
Implementing Practical Bias Mitigation Frameworks and Protocols
Troubleshooting Guides & FAQs
Common Implementation Challenges and Solutions
Q1: What is the most frequent error in applying LSU-E to non-comparative forensic domains, and how can it be resolved?
A: A common error is providing contextual information (e.g., presumed manner of death, investigative theories) to the expert before they have conducted an initial examination of the raw evidence. This violates the core LSU-E principle and introduces potential bias [29].
- Solution: Implement a strict protocol where all contextual information is withheld until after the analyst has performed and documented an initial assessment of the raw data or evidence. For example, crime scene investigators should not receive any case details until after they have initially seen the crime scene and documented their first impressions [29].
Q2: How can a laboratory manage the practical challenge of segregating information while still providing experts with the context needed to do their work?
A: This is a key implementation barrier. The solution is not to deprive experts of necessary information but to control the sequence in which it is presented [29].
- Solution: Adopt a phased information release system.
- Phase 1: Evidence-Centric Analysis. The analyst works solely with the raw data (e.g., the crime scene evidence, the digital hard drive, the biological sample).
- Phase 2: Contextual Integration. Only after documenting conclusions from Phase 1 is the analyst provided with relevant contextual information to aid in further interpretation, ensuring the initial judgment is driven by the evidence itself [29].
Q3: What is a major limitation of the original Linear Sequential Unmasking (LSU) framework that LSU-E aims to overcome?
A: The original LSU framework is limited in two significant ways [29]:
- Scope Limitation: It applies only to comparative decisions (e.g., comparing fingerprints or DNA profiles) and not to other forensic decisions like crime scene investigation or forensic pathology.
- Focus Limitation: Its function is limited to minimizing cognitive bias, rather than reducing noise and improving decision-making reliability more broadly.
LSU-E Procedural Troubleshooting
Q4: How can a laboratory objectively track the information an analyst received and when they received it?
A: Research recommends using a practical worksheet or checklist to document the information management process [30]. This tool bridges the gap between research and practice by providing a concrete mechanism to record:
- The pieces of information available in a case.
- The sequence in which they were disclosed to the analyst.
- The analyst's conclusions at each stage, thereby increasing the transparency and repeatability of the process [30].
Q5: Has LSU-E been successfully implemented in a working forensic laboratory?
A: Yes. The Department of Forensic Sciences in Costa Rica designed a pilot program that incorporated LSU-E, among other mitigation strategies. This program demonstrated that existing research recommendations can be used within laboratory systems to reduce error and bias in practice, providing a model for other laboratories [12].
Experimental Protocols & Methodologies
Core Protocol for Implementing LSU-E
The following methodology provides a step-by-step guide for integrating LSU-E into a forensic workflow, based on its foundational principles [29].
Objective: To minimize cognitive bias and reduce noise in forensic decision-making by optimizing the sequence of information processing.
Workflow:
- Information Audit: Identify all informational elements available in a case (e.g., evidence items, reference materials, witness statements, investigative hypotheses).
- Information Categorization: Classify each piece of information based on its objectivity, relevance to the specific forensic task, and potential biasing power [30].
- Sequencing: Establish a linear sequence for revealing information to the analyst, adhering to this rule: the most objective, task-relevant, and least biasing information must be presented first.
- Initial Analysis & Documentation: The analyst examines only the first piece of information (typically the raw, unknown evidence) and documents their findings and interpretations before proceeding.
- Sequential Unmasking: The next piece of information in the sequence is revealed. The analyst integrates this new information and documents any new or revised conclusions. This step repeats until all information has been considered.
- Blind Verification (Optional but Recommended): Where feasible, a second analyst should repeat the process without exposure to the first analyst's conclusions or any extraneous biasing information to verify results [12].
LSU-E Decision Workflow: This diagram visualizes the step-by-step process for implementing the LSU-E protocol, from information audit to final conclusion.
Key Experiment: Demonstrating Order Effects in Forensic Anthropology
Objective: To empirically demonstrate that the sequence of information processing can bias forensic conclusions, thereby validating the need for a framework like LSU-E.
Cited Methodology: [29]
- Independent Variable: The order in which skeletal material was analyzed (e.g., skull first vs. hip first).
- Dependent Variable: The resulting sex estimates for the skeletal remains.
- Procedure: Analysts were asked to estimate the sex of skeletal remains but were given different sequences of anatomical regions to analyze.
- Results: The study found that the order of analysis significantly biased the final sex estimates. For instance, starting with the skull led to different conclusions than starting with the hip bone, demonstrating a clear primacy effect where initial information disproportionately influences the final judgment.
Scope and Impact of Cognitive Bias in Forensic Science
The table below synthesizes evidence from the literature on the prevalence and impact of cognitive bias across forensic disciplines, underscoring the critical need for mitigation frameworks like LSU-E [29].
Table 1: Documented Reach of Cognitive Bias in Forensic Science
| Aspect of Bias | Documented Impact/Recognition | Key Sources / Domains |
|---|---|---|
| General Susceptibility | Recognized as a real and important issue impacting all domains of forensic decision-making. | National Academy of Sciences (2009); President's Council of Advisors on Science and Technology (PCAST); National Commission on Forensic Science [29]. |
| International Recognition | Guidance and concerns about bias have been issued by regulatory bodies worldwide. | United Kingdom's Forensic Science Regulator; Australian forensic authorities [29]. |
| Domain Prevalence | Effects observed and replicated across a wide range of forensic disciplines. | Fingerprinting, DNA, firearms, digital forensics, handwriting, pathology, anthropology, and crime scene investigation [29]. |
| Expert Susceptibility | Practicing forensic experts are susceptible to cognitive biases, which can operate without conscious awareness. | Documented among practicing forensic scientists; experts can be more susceptible than non-experts due to factors like escalation of commitment [29]. |
The Scientist's Toolkit: Essential Research Reagent Solutions
This table details the key components required for the implementation and study of bias mitigation strategies like LSU-E in a research or laboratory setting.
Table 2: Essential Components for Implementing LSU-E and Bias Research
| Tool / Component | Function in Research & Implementation |
|---|---|
| LSU-E Procedural Worksheet | A practical tool to guide labs and analysts in prioritizing and sequencing case information. It increases repeatability, reproducibility, and transparency [30]. |
| Blind Verification Protocol | A control procedure where a second examiner conducts an analysis without exposure to the first examiner's results or potentially biasing context, used to test and ensure reliability [12]. |
| Case Manager System | An administrative role or system responsible for controlling the flow of information to analysts, ensuring adherence to the LSU-E sequence and acting as a "case firewall" [12]. |
| Pilot Program Framework | A structured model for rolling out LSU-E in a single laboratory section first. This allows for barrier identification, protocol refinement, and demonstration of feasibility before lab-wide implementation [12]. |
Troubleshooting Guide: FAQs on Implementation and Workflow
This technical support guide addresses common challenges researchers and forensic professionals face when implementing bias mitigation protocols like Blind Verification and Case Manager systems into laboratory workflows.
Q1: What are the most common fallacies that hinder the adoption of cognitive bias mitigation procedures, and how can we counter them?
Researchers often hold misconceptions that impede implementation. The table below summarizes six common fallacies and evidence-based counterarguments [4].
| Fallacy | Reality Check |
|---|---|
| Ethical Issues: "Only bad people are biased." | Cognitive bias is not corruption or misconduct; it is a normal, automatic decision-making process with inherent limitations [4]. |
| Expert Immunity: "I am an expert, so I am not susceptible." | Expertise does not cure bias. Frequent decision-making may cause experts to rely more on automatic processes, increasing vulnerability [4]. |
| Technological Protection: "More AI and technology will solve subjectivity." | AI systems are built and interpreted by humans, so they reduce but do not eliminate bias effects [4]. |
| Blind Spot: "I know bias is an issue, but I am not vulnerable." | Most people exhibit a "bias blind spot," readily acknowledging general vulnerability but denying their own [4]. |
| Illusion of Control: "I'll just be mindful of bias during my analyses." | Willpower alone cannot overcome bias, as it occurs automatically and unconsciously. Systems must be built around examiners to catch bias [4]. |
| Bad Apples: "Only incompetent people are biased." | Bias is not a result of lack of skill or incompetence. It is a normal, efficient decision strategy [4]. |
Q2: Our laboratory is piloting a Case Manager system. What is the primary function of the Case Manager in controlling information flow?
The Case Manager acts as an information firewall. Their core function is to control the flow of task-irrelevant and potentially biasing contextual information to the examiner [4]. This includes segregating reference materials from the original evidence data during the initial examination phase to prevent confirmation bias, where an examiner might overemphasize similarities when comparing data and reference materials side-by-side [4].
Q3: During Blind Verification, the verifier reports difficulty reaching a conclusion without the original context. What is the proper procedure?
The verifier should never receive the original examiner's conclusion or the contextual details of the case. If the verifier cannot reach a conclusion based solely on the evidence presented, the result should be documented as "inconclusive" or "no conclusion." The verification must remain truly blind to be effective. Providing context or the initial result undermines the process, as seen in high-profile errors like the FBI's misidentification in the Madrid bombing case, where verifiers knew the initial conclusion from a respected colleague [4].
Q4: How can we validate that our Blind Verification and Case Manager protocols are effectively reducing cognitive bias?
Effectiveness should be measured through quantitative and qualitative metrics. Implement a pilot program and track key performance indicators over time. The table below outlines a framework for measuring protocol effectiveness [4].
| Metric Category | Specific Indicator | Goal |
|---|---|---|
| Workflow Integrity | Percentage of cases where Case Manager protocol was correctly followed. | >98% adherence to the established workflow. |
| Rate of contextual information leaks to examiners. | Zero leaks. | |
| Analytical Outcomes | Rate of inconclusive results from blind verifiers. | Stable or decreasing trend. |
| Discordance rate between initial examination and blind verification. | Maintain a low, stable rate consistent with known error rates. | |
| Operational Impact | Average time added to case completion. | Quantify and justify as a necessary cost for increased reliability. |
| Staff feedback and acceptance scores. | Gradual improvement in acceptance and understanding. |
Q5: What are the key sources of bias in forensic examinations that these systems are designed to address?
A 2020 summary identifies multiple compounding sources of bias. The Case Manager and Blind Verification systems directly target several of these, including the data itself, reference materials, and contextual information [4]. By controlling the flow of information, these systems help prevent contamination from pre-existing beliefs, expectations, and motives from inappropriately influencing the collection, perception, or interpretation of evidence [4].
Experimental Protocol: Implementing a Pilot Program for Bias Mitigation
The following protocol is adapted from a successful pilot program implemented in a questioned documents section, providing a model for systematic implementation [4].
Objective
To implement and evaluate a structured bias mitigation protocol within a forensic laboratory workflow, integrating Case Manager and Blind Verification procedures to enhance the reliability and objectivity of analytical results.
Materials and Reagent Solutions
| Item | Function in the Protocol |
|---|---|
| Laboratory Information Management System (LIMS) | An automated system for immutable record-keeping and tracking evidence movement, crucial for maintaining the chain-of-custody [31]. |
| Case Manager | A designated individual or role responsible for acting as an information firewall. They control the flow of all information to the examiner, ensuring only task-relevant data is provided [4]. |
| Blind Verifier | A second, independent examiner who performs the analysis without any knowledge of the initial examiner's findings, the case context, or any other potentially biasing information [4]. |
| Linear Sequential Unmasking-Expanded (LSU-E) Framework | A research-based tool that structures the examination process to reveal information to the examiner in a controlled, sequential manner, minimizing the risk of confirmation bias [4]. |
| Standardized Report Templates | Documentation that explains scientific conclusions using precise, defensible terminology and properly conveys statistical probabilities, avoiding overstatement [31]. |
Methodology
Pre-Implementation Phase
- Stakeholder Engagement: Conduct educational sessions to address common fallacies (see FAQ #1) and build consensus on the need for bias mitigation.
- Role Definition: Clearly define the responsibilities and authority of the Case Manager and Blind Verifiers.
- Workflow Mapping: Document the current evidence flow and identify all points where contextual information is introduced.
Case Manager Workflow Implementation
- Intake: All case materials and information are received by the Case Manager.
- Triage: The Case Manager assesses the case and segregates the evidence into two streams:
- Examiner Stream: Contains only the data necessary for the initial analysis (e.g., the latent print).
- Contextual Stream: Contains all other information (e.g., suspect information, reference materials, reports from other examiners).
- Assignment: The Case Manager assigns the decontextualized evidence from the Examiner Stream to an examiner for analysis.
Blind Verification Workflow Implementation
- Initial Examination: The first examiner completes their analysis and documents their conclusion in a report submitted to the Case Manager.
- Verification Assignment: The Case Manager prepares a new case file for the verifier, containing only the original evidence. The initial examiner's report is excluded.
- Independent Verification: The blind verifier conducts a full, independent analysis without access to the initial findings or contextual data.
- Conclusion Comparison: The Case Manager compares the two results. Any discordance is managed according to predefined laboratory policy (e.g., escalation to a third expert or panel).
Data Collection and Analysis
- Track the metrics outlined in FAQ #4 for a predetermined pilot period (e.g., 6-12 months).
- Use the data to refine the protocols, demonstrate the value to stakeholders, and justify permanent implementation.
Visualization of Workflow
The following diagram illustrates the controlled information flow, highlighting how the Case Manager acts as a critical firewall.
This technical support center provides practical guidance for researchers and forensic professionals implementing Linear Sequential Unmasking - Enhanced (LSU-E) worksheets to mitigate contextual bias in laboratory workflows.
Troubleshooting Guides and FAQs
Data Collection and Preparation Phase
Q: What is the most common source of bias in forensic data collection? A: Human biases represent the dominant origin of biases observed in analytical workflows. These include implicit bias (subconscious attitudes or stereotypes) and systemic bias (broader institutional norms, practices, or policies that can lead to societal harm or inequities). These rarely introduced deliberately, they reflect historic or prevalent human perceptions that can manifest across various stages of analytical development [32].
Q: How can we minimize exposure to irrelevant contextual information during evidence examination? A: Implement the case manager model, which separates functions in the laboratory between case managers and examiners. Case managers can be fully informed about context, while forensic examiners receive only the information needed for their specific analytical tasks. This prevents exposure to potentially biasing information that doesn't contribute to the scientific examination [13].
Q: What practical steps can individual practitioners take to reduce cognitive bias in their work? A: Practitioners can adopt several specific actions: ground work in evidence, create structures that encourage scrutiny, implement blind verification procedures, and maintain a questioning mindset that critically assesses evidence. These approaches allow practitioners to take ownership for minimizing cognitive bias [7].
Analysis and Interpretation Phase
Q: Our team often experiences confirmation bias. How can LSU-E worksheets help? A: LSU-E worksheets directly address confirmation bias (the tendency to seek, interpret, and remember information that confirms pre-existing beliefs) by structuring the analytical process. The worksheets enforce documentation of initial observations before exposure to reference materials, preventing "tunnel vision." Teams should also conduct blind re-examination, where key judgments are replicated by a second examiner not exposed to potentially biasing information [33] [13].
Q: What should we do when different analysts reach conflicting conclusions using the same worksheet? A: This may indicate anchoring bias (relying too heavily on first impressions) or the Dunning-Kruger effect (overestimating competence). Implement a structured consensus process where each analyst presents their documented observations from the worksheet. Focus discussion on the evidence rather than opinions, and consider bringing in a neutral third party with relevant expertise [33].
Q: How can we maintain worksheet consistency when dealing with complex, multi-part evidence? A: Break down complex evidence into discrete analytical units, with separate worksheet sections for each. Maintain a clear chain of documentation that shows how each piece was evaluated individually before integrated conclusions were drawn. This approach manages complexity while preserving analytical rigor [34] [13].
Implementation and Verification Phase
Q: What metrics should we track to evaluate the effectiveness of our LSU-E implementation? A: Monitor both process and outcome metrics. Process metrics include documentation completeness rates and adherence to sequencing protocols. Outcome metrics should track inter-rater reliability, reduction in contradictory findings, and quantitative bias assessments using established fairness metrics where applicable [32] [35].
Q: How can we adapt LSU-E worksheets for different types of forensic analysis? A: While maintaining core principles, customize worksheet templates to specific analytical domains. The key is preserving the sequential revelation of information, not standardizing every detail. Create domain-specific versions that address unique aspects of different evidence types while maintaining the unbiased examination sequence [34] [13].
Q: What is the most common implementation error when first adopting structured worksheets? A: The planning fallacy - underestimating the time, cost, and risks required to complete a task, despite experience suggesting otherwise. Teams often create overly optimistic timelines for worksheet completion. Mitigate this by tracking actual time requirements during the initial implementation phase and adjusting expectations accordingly [33].
Experimental Protocols and Methodologies
Protocol 1: Bias Assessment in Existing Workflows
Purpose: Establish baseline bias measurements before implementing LSU-E worksheets [35].
Materials: Historical case data, assessment worksheets, statistical analysis software
Procedure:
- Select a representative sample of completed cases (minimum n=30 recommended)
- Document all available contextual information originally present during analysis
- Measure subgroup performance variations using appropriate fairness metrics
- Calculate Equal Opportunity Difference (EOD) values comparing false negative rates
- Identify specific bias patterns across different contextual factors
Table 1: Bias Assessment Metrics and Interpretation
| Metric | Calculation | Acceptance Threshold | Purpose |
|---|---|---|---|
| Equal Opportunity Difference (EOD) | Difference in false negative rates between subgroups | <5 percentage points [35] | Measures fairness across demographic groups |
| Inter-rater Reliability | Percentage agreement between independent examiners | >90% for major conclusions | Assesses analytical consistency |
| Contextual Influence Index | Rate of conclusion changes when context is modified | <5% variation | Quantifies susceptibility to contextual bias |
Protocol 2: LSU-E Worksheet Implementation
Purpose: Integrate sequential unmasking into daily laboratory practice [13].
Materials: LSU-E worksheets, case management system, blinding protocols
Procedure:
- Case Intake: Case manager receives all contextual information
- Evidence Preparation: Remove all identifying and contextual details not essential for analysis
- Initial Examination: Analyst completes sections 1-3 of worksheet documenting:
- Physical characteristics of evidence
- Class characteristics
- Initial observations and measurements
- Sequential Revelation: Case manager provides specific reference materials requested by analyst
- Comparative Analysis: Analyst completes sections 4-6 documenting comparison process
- Verification: Second analyst performs blind re-examination of key findings
- Contextual Integration: Case manager and analyst jointly review contextual information and document its influence (if any) on conclusions
LSU-E Worksheet Implementation Workflow
Protocol 3: Threshold Adjustment for Algorithmic Bias Mitigation
Purpose: Address performance disparities across subgroups in analytical algorithms [36] [35].
Materials: Classification algorithms, performance data across subgroups, threshold adjustment tools
Procedure:
- Establish baseline performance metrics for all relevant subgroups
- Identify subgroups with meaningful performance disparities (EOD >5 percentage points)
- Calculate optimal thresholds for each subgroup to minimize EOD
- Implement adjusted thresholds in analytical workflows
- Validate that accuracy reduction remains <10% and alert rate change <20%
- Document mitigation effectiveness for ongoing improvement
Table 2: Post-Processing Bias Mitigation Methods Comparison
| Method | Effectiveness | Accuracy Impact | Implementation Complexity | Best Use Cases |
|---|---|---|---|---|
| Threshold Adjustment | High (8/9 trials showed bias reduction) [36] | Low loss | Low | Binary classification models |
| Reject Option Classification | Moderate (5/8 trials showed bias reduction) [36] | Low loss | Medium | High-stakes decisions with uncertainty |
| Calibration | Moderate (4/8 trials showed bias reduction) [36] | No loss | Medium | Probabilistic predictions |
| Feature-Wise Mixing | High (43.35% average bias reduction) [27] | Statistically significant improvement | High | Complex predictive models |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials for Bias-Aware Forensic Research
| Item | Function | Implementation Example |
|---|---|---|
| LSU-E Worksheets | Structured documentation for sequential unmasking | Customizable templates for different evidence types [13] |
| Case Management System | Controls information flow to examiners | Implements case manager model [13] |
| Blinding Protocols | Prevents exposure to biasing information | Standard operating procedures for evidence preparation [34] |
| Bias Assessment Metrics | Quantifies fairness and performance disparities | Equal Opportunity Difference, demographic parity [32] [35] |
| Threshold Adjustment Tools | Implements post-processing bias mitigation | Aequitas, custom Python scripts [36] [35] |
| Adversarial Validation Sets | Tests system robustness to contextual bias | Artificially created datasets with controlled contextual variables [37] |
| Statistical Analysis Package | Measures inter-rater reliability and bias metrics | R, Python with fairness libraries [36] [35] |
Bias Mitigation Framework Overview
ISO/IEC 17025 Accreditation as a Foundation for Impartiality and Quality Management
Troubleshooting Guides & FAQs
This technical support center addresses common challenges forensic laboratories face when implementing and maintaining ISO/IEC 17025 accreditation to mitigate contextual bias and ensure quality management.
Troubleshooting Common Accreditation Challenges
Table: Frequent ISO/IEC 17025 Implementation Issues and Solutions
| Problem Area | Common Symptoms | Recommended Corrective Actions | Relevant ISO/IEC 17025 Clause |
|---|---|---|---|
| Document Control | • Uncontrolled document versions• Inconsistent procedure followings• Missing revision histories | • Implement centralized document management system• Establish automated version control• Define formal document approval workflows | Clause 8.3: Documented information control [38] |
| Management Review | • Reviews conducted irregularly• Incomplete review inputs• No improvement action tracking | • Schedule reviews at planned intervals (e.g., quarterly)• Use standardized checklist for inputs per 8.9.2• Implement action item tracking system | Clause 8.9: Management review [39] |
| Internal Audits | • Audits not conducted annually• No qualified internal auditors• Missing corrective action records | • Train and qualify internal auditors• Develop comprehensive audit schedule• Maintain complete nonconformity records | Clause 8.8: Internal audits [39] |
| Risk Management | • No systematic risk identification• Reactive rather than proactive approach• Missing risk-based thinking documentation | • Implement risk assessment framework• Document risk treatment plans• Integrate risk review into management meetings | Clause 8.5: Addressing risks and opportunities [40] [38] |
| Result Validity | • No systematic assurance program• Inadequate proficiency testing• Missing data trend analysis | • Implement regular proficiency testing• Conduct inter-laboratory comparisons• Use control charts for key parameters | Clause 7.7: Ensuring validity of results [38] |
Frequently Asked Questions (FAQs)
Q1: How does ISO/IEC 17025:2017 specifically help mitigate cognitive bias in forensic analysis?
ISO/IEC 17025:2017 promotes impartiality through several specific requirements. Clause 4.1 mandates laboratories to demonstrate impartiality and manage conflicts of interest structurally [38]. The standard's emphasis on method validation (Clause 7.2) and measurement uncertainty (Clause 7.6) introduces objective criteria that reduce reliance on subjective judgment [38]. Additionally, technical record requirements (Clause 7.5) ensure transparent decision trails, while nonconforming work controls (Clause 7.10) establish systematic correction processes that help identify and address potential bias sources [38].
Q2: What are the concrete differences between the 2005 and 2017 versions regarding bias mitigation?
The 2017 revision represents a fundamental shift from procedure-heavy requirements to a risk-based, outcome-focused approach [38]. Key differences include: the term "risk" appears over 30 times in the 2017 version compared to only four mentions in 2005; completely restructured format moving from two main clauses to five process-flow clauses; introduction of dedicated impartiality requirements in Clause 4.1; and explicit recognition of computer systems and electronic records, which supports automated bias controls like Linear Sequential Unmasking protocols [38].
Q3: Our laboratory is implementing Linear Sequential Unmasking (LSU). How can we document this within our ISO/IEC 17025 system?
Document LSU protocols within your process requirements (Clause 7) as part of method-specific procedures [12]. Define information control boundaries and sequencing in your examination procedures. Implement case manager roles (responsible for filtering extraneous information) within your structural requirements (Clause 5) [12]. Record maintenance (Clause 7.5) should demonstrate adherence to LSU sequencing, while personnel training records (Clause 6.2) must document competence in unbiased examination techniques [12] [2].
Q4: What specific evidence do assessors look for regarding impartiality and bias controls?
Assessors typically seek: documented impartiality commitments with examples of potential conflicts (Clause 4.1); personnel records showing bias mitigation training (Clause 6.2); procedure documents specifying context management protocols; case records demonstrating appropriate information sequencing; proficiency test results analyzed for potential bias patterns; and management review inputs (Clause 8.9.2) specifically addressing impartiality and bias incidents [38] [39].
Q5: How do we validate software tools used for bias mitigation like automated CAPA systems?
Software validation (including SaaS LIMS) must demonstrate fitness for purpose per Clause 6.4.13 [38]. For bias mitigation tools, this includes: verifying automated workflow routing functions correctly; testing escalation matrices for non-conforming work; validating audit trail completeness; ensuring data integrity through security testing; and confirming electronic signature reliability if used. For SaaS solutions, additionally verify vendor qualifications, data residency, tenant isolation, and update impact assessment protocols [38].
Experimental Protocols & Methodologies
Detailed Methodology: Measuring Contextual Bias Susceptibility
Purpose: Quantitatively assess the impact of contextual information on forensic examination conclusions.
Materials & Equipment:
- Case sets with matched pairs (known biased vs. blinded conditions)
- Digital case management system with information sequencing capability
- Standardized scoring rubrics with confidence scales
- Statistical analysis software (e.g., R, SPSS)
Procedure:
- Participant Selection: Recruit examiners representing different experience levels (novice to expert)
- Case Preparation: Create 20 case pairs with and without potentially biasing contextual information
- Randomized Presentation: Administer cases using counterbalanced design (Group A: blinded first, then contextual; Group B: reverse order)
- Data Collection: Record examination conclusions, confidence levels, and time-to-decision
- Blind Verification: Implement independent technical review without contextual information
- Data Analysis: Compare conclusion consistency between blinded and contextual conditions using appropriate statistical tests (e.g., Cohen's kappa for agreement, t-tests for confidence measures)
Validation Criteria:
- Significant difference (p<0.05) in conclusion rates between conditions indicates bias susceptibility
- Inter-rater reliability measures between examiners and blind verification
- Effect size calculation for contextual information impact
Protocol: Implementing Linear Sequential Unmasking-Expanded (LSU-E)
Purpose: Systematically control information flow to minimize contextual bias in forensic examinations [12].
Workflow Implementation:
Key Controls:
- Case Manager Role: Independent individual filters all extraneous information (suspect history, eyewitness statements, unrelated evidence) [12]
- Information Sequencing: Relevant technical context provided only after initial blinded examination documented
- Decision Documentation: Separate recording of conclusions at each phase enables bias detection
- Blind Verification: Independent technical review without potentially biasing information [12]
The Scientist's Toolkit: Research Reagent Solutions
Table: Essential Materials for Bias-Mitigated Forensic Research
| Tool/Reagent | Primary Function | Application in Bias Research | Quality Requirements |
|---|---|---|---|
| Proficiency Test Materials | Benchmark examiner performance | Create controlled case sets for bias measurement | ISO 17043 conformity for PT providers |
| Blinded Case Sets | Experimental stimulus delivery | Present matched pairs with/without context | Documented homogeneity and validation |
| Digital Case Management | Information sequencing control | Implement LSU-E protocols | 21 CFR Part 11 compliance for electronic records |
| Statistical Analysis Package | Data analysis and interpretation | Calculate effect sizes, significance testing | Validated algorithms, reproducibility features |
| Confidence Assessment Scales | Quantitative subjective measures | Measure certainty in conclusions under different conditions | Established psychometric validation |
| Audit Trail Software | Process documentation | Track information access and decision timing | Immutable records, timestamp verification |
| Training Materials | Examiner competency development | Bias recognition and mitigation techniques | Content validation by subject matter experts |
Standards & Compliance Framework
FBI Quality Assurance Standards Integration
The FBI has approved changes to the Quality Assurance Standards for Forensic DNA Testing Laboratories effective July 1, 2025 [41]. These revisions include specific provisions for implementing Rapid DNA testing on forensic samples and qualifying arrestees at booking stations [41]. Laboratories seeking NDIS approval must comply with both ISO/IEC 17025 and these specific QAS requirements, typically through accreditation bodies like ANAB that operate under MOUs with the FBI [42].
OSAC Registry Standards for Forensic Science
The Organization of Scientific Area Committees (OSAC) maintains a registry of approved standards for forensic science, with 225 standards currently listed (152 published and 73 OSAC Proposed) representing over 20 disciplines [43]. Recent additions relevant to bias mitigation include:
- OSAC 2023-N-0012: Best Practice Recommendations for Development of Criteria for Acceptance of Request for Friction Ridge Examinations
- OSAC 2023-S-0028: Best Practice Recommendations for Resolution of Conflicts in Toolmark Value Determinations and Source Conclusions
- OSAC 2024-S-0002: Standard Test Method for Examination and Comparison of Toolmarks for Source Attribution [43]
Cognitive Bias Mitigation Mechanisms
Understanding Bias Cascade Effects
Research demonstrates that cognitive biases don't operate in isolation but can create "bias cascade" and "bias snowball" effects throughout the justice system [44]. When multiple elements (crime scene investigation, forensic analysis, prosecution decisions) are coordinated rather than independent, biases can reinforce each other, creating compounded errors that become difficult to detect at later stages [44].
Table: Cognitive Bias Types and Mitigation Controls in Forensic Workflows
| Bias Type | Potential Impact | ISO/IEC 17025 Control Mechanism | Additional Mitigation Strategies |
|---|---|---|---|
| Confirmation Bias | Seeking evidence to confirm initial suspicions | Method validation requirements (7.2)Technical record keeping (7.5) | Linear Sequential Unmasking [12]Blind verification [2] |
| Contextual Bias | Extraneous information influencing decisions | Impartiality requirements (4.1)Process requirements (7) | Case management protocols [12]Information sequencing |
| Base Rate Bias | Overweighting prior probabilities | Decision rules requirements (7.8.4.1)Uncertainty measurement (7.6) | Statistical trainingLikelihood ratio frameworks |
| Expectation Bias | Seeing what you expect to see | Result validity assurance (7.7)Proficiency testing (6.6.2) | Independent technical reviewEvidence lineups |
Implementation Diagram: Bias-Aware Quality System
This technical support framework provides forensic researchers and laboratory professionals with practical tools for implementing ISO/IEC 17025 accreditation as a foundation for impartiality and quality management, with specific emphasis on mitigating contextual bias throughout forensic workflows.
DNA Analysis Troubleshooting Guide
This section addresses common challenges in forensic DNA analysis, providing mitigation strategies aligned with principles of scientific rigor and contextual bias mitigation [12].
Frequently Asked Questions
Q1: Our STR analysis results show elevated stutter peaks, complicating mixture interpretation. What are the primary causes and solutions?
A1: Elevated stutter peaks can arise from several technical issues. Review your amplification and electrophoresis parameters using this troubleshooting table:
| Potential Cause | Diagnostic Check | Corrective Action |
|---|---|---|
| Excessive DNA Input | Review quantitation values; target 0.5-1.0 ng for PowerPlex Fusion [45]. | Re-amplify with normalized DNA template. |
| Over-amplification | Check cycle number and extension time [45]. | Optimize amplification cycles per manufacturer's protocol. |
| Capillary Overload | Inspect raw data for peak heights exceeding linear range [45]. | Dilute amplified product and re-inject. |
| Degraded DNA | Check for increased stutter in higher molecular weight loci. | Use a degradation-sensitive quantification method [45]. |
Q2: How can we structure the analytical workflow to minimize contextual bias during STR interpretation?
A2: Implement a Linear Sequential Unmasking-Expanded (LSU-E) protocol [12]. This involves restricting task-irrelevant contextual information until after the initial analytical steps are complete and documented.
- Step 1: Blind Technical Review: Perform initial data quality assessment (peak morphology, signal strength, artifacts) without access to reference samples or suspect information.
- Step 2: Independent Interpretation: Interpret the DNA profile and record all possible genotypes before any comparisons.
- Step 3: Controlled Comparison: Only after the evidence profile is fully documented should comparisons to reference samples be conducted, preferably with a Blind Verification by a second analyst [12].
DNA Analysis Workflow for Mitigating Contextual Bias
The following diagram illustrates a core forensic biology workflow designed to minimize cognitive bias by separating technical analysis from comparative tasks.
Research Reagent Solutions for DNA Analysis
| Reagent / Kit | Primary Function | Key Consideration for Bias Mitigation |
|---|---|---|
| QIAcube / EZ1 Advanced XL [45] | Automated DNA extraction from various substrates. | Standardizes recovery, reducing analyst-specific variability. |
| Quantifiler Trio [45] | DNA quantification & quality assessment. | Detects inhibitors and degradation, informing valid interpretation limits. |
| PowerPlex Fusion / Y23 [45] | Co-amplification of STR loci. | Validated, multiplexed systems ensure consistent marker analysis. |
| STRmix [45] | Probabilistic genotyping software. | Provides objective, quantitative statistical weight to complex DNA evidence. |
Digital Evidence Management Troubleshooting Guide
This section addresses operational challenges in managing digital evidence, focusing on maintaining integrity, chain of custody, and admissibility in a high-volume environment [46].
Frequently Asked Questions
Q1: We are experiencing frequent breaks in our digital chain of custody, often when evidence is transferred between units. How can this be fixed?
A1: Breaks in the digital chain of custody often occur due to manual tracking methods. The solution is to implement a Digital Evidence Management System (DEMS) with automated auditing [46].
| Problem Scenario | Root Cause | Smart Solution |
|---|---|---|
| Untracked Copying | Evidence transferred via USB drive with no log. | Use a central DEMS with automated audit logging; every access is timestamped and user-identified [46]. |
| Unauthorized Access | Multiple personnel access a shared drive. | Implement role-based access controls (RBAC) to ensure only authorized personnel handle evidence [46]. |
| Unclear File Provenance | Uncertainty about which file copy is the evidence master. | Use cryptographic hash verification (e.g., SHA-256) upon ingestion; any alteration is instantly detected [46]. |
Q2: The volume and variety of digital evidence (CCTV, IoT, cloud data) is overwhelming our analysts. What tools can help triage and review this data efficiently?
A2: Leverage Artificial Intelligence (AI) and machine learning features within modern DEMS to automate the initial review of large datasets [46] [47].
- AI-Powered Video Analysis: Use automated object, face, and license plate detection to quickly locate relevant scenes in hours of footage, increasing review efficiency [46].
- Audio Transcription: Employ speech-to-text generation for audio and video evidence, enabling keyword searches instead of manual listening [46].
- Automated Redaction Tools: Utilize AI to identify and blur Personally Identifiable Information (PII) like faces and license plates, ensuring secure and compliant sharing [46].
- Caution: Be aware that AI is a double-edged sword; the same technology can be used to create sophisticated deepfakes, complicating digital forensics [47]. Always validate findings and use transparent tools.
Digital Evidence Management Workflow
This workflow outlines the secure lifecycle of digital evidence, from collection to disposition, emphasizing automated integrity checks.
Essential Tools for Digital Evidence Management
| System / Tool | Core Function | Role in Integrity & Efficiency |
|---|---|---|
| Digital Evidence Management System (DEMS) [46] | Centralized repository for all digital evidence. | Provides a unified platform for tracking, analysis, and sharing, breaking down evidence silos. |
| Cryptographic Hashing Algorithm (e.g., SHA-256) [46] | Creates a unique digital fingerprint for a file. | The cornerstone of evidence integrity; any change to the file alters the hash, detecting tampering. |
| Automated Audit Log [46] | Records every action taken on a piece of evidence. | Creates a tamper-evident record for the chain of custody, critical for legal admissibility. |
| AI-Based Analysis Tools [46] [47] | Automates review of large datasets (video, audio). | Reduces human analyst fatigue and potential for oversight, allowing focus on relevant data. |
Toxicology and Chemical Forensics Troubleshooting Guide
This section addresses challenges in toxicological analysis, focusing on sample integrity, the adoption of New Approach Methodologies (NAMs), and managing cognitive bias in interpretation.
Frequently Asked Questions
Q1: Our toxin samples (blood, urine) are showing signs of degradation upon analysis, risking inaccurate results. What are the critical handling protocols?
A1: Preserving the chemical integrity of toxin samples requires strict adherence to stabilization and storage protocols from the moment of collection [31].
| Degradation Sign | Likely Cause | Corrective Protocol |
|---|---|---|
| Decreased Analyte Concentration | Microbial or enzymatic activity post-collection. | Use preservation agents (e.g., sodium fluoride for blood) immediately upon collection [31]. |
| Unstable Analyte Levels | Improper or fluctuating storage temperature. | Implement mandatory, verifiable refrigeration or freezing with continuous monitoring and logging [31]. |
| Cross-Contamination | Improper segregation of samples and standards. | Enforce physical separation of samples, especially between high-concentration standards and casework [31]. |
Q2: How can in silico (computational) toxicology methods be integrated into a traditional workflow, and what are their limitations regarding validation and bias?
A2: In silico toxicology uses computational models to predict compound toxicity, offering a faster, cheaper, and more humane alternative to some animal testing [48]. Integration requires careful validation.
- Application: Use tools like the EPA's CompTox Chemicals Dashboard (CCD) to access curated data on chemical toxicity and bioactivity for early-stage risk prioritization [49].
- Workflow Integration: These methods are best used as a triaging tool in the early phases of an investigation or research project to prioritize compounds for further, more resource-intensive testing [48].
- Limitations and Bias: A primary challenge is the "black box" nature of some complex AI models, which can undermine credibility in court [47]. Mitigation strategies include:
- Transparency: Using models that provide explainable predictions.
- Validation: Rigorously validating models against known, high-quality in vivo data (e.g., from ToxRefDB) to build scientific confidence [49].
- Awareness of Bias: Acknowledging that models can be biased by the limited chemical space of their training data [48].
Integrating Traditional and New Approach Methods (NAMs)
This diagram contrasts and connects traditional toxicology workflows with modern, computational New Approach Methodologies (NAMs).
| Resource / Technique | Function | Application Note |
|---|---|---|
| EPA CompTox Chemicals Dashboard [49] | Public access to chemistry, toxicity, and exposure data. | Used for initial chemical screening and gathering existing data for read-across. |
| ToxCast Database [49] | Repository of high-throughput screening bioactivity data. | Provides a broad basis for predicting potential molecular targets and mechanisms. |
| ToxValDB [49] | Database of summary-level in vivo toxicology data. | Critical for validating and building scientific confidence in NAM predictions. |
| Organ-on-a-Chip / 3D Models [48] | Advanced in vitro systems with improved physiological relevance. | Offers a more human-relevant data source than traditional 2D cell cultures, bridging in silico and in vivo gaps. |
Overcoming Implementation Barriers and Optimizing Laboratory Workflows
Technical Support Center: FAQs on Contextual Bias Mitigation
This technical support center provides troubleshooting guides for researchers and scientists implementing contextual bias mitigation strategies in forensic laboratory workflows. The following FAQs address common operational, technical, and cultural challenges encountered during this process.
Frequently Asked Questions
| Question | Common Challenge/Symptom | Evidence-Based Solution | Key References |
|---|---|---|---|
| How can we implement bias mitigation with limited staff and budget? | Inability to fund new positions or complex technical systems; staff feel overburdened. | Implement the Case Manager Model, which uses existing personnel efficiently by separating contextual and analytical roles [13]. Begin with a pilot program in a single laboratory section to demonstrate effectiveness before wider rollout [4]. | [4] [13] |
| Our examiners believe their expertise makes them immune to bias. How can we encourage buy-in? | Cultural resistance; staff dismiss training based on the "Expert Immunity" or "Bad Apples" fallacies [4]. | Training must explicitly address common myths, emphasizing that cognitive bias is a normal human function, not an ethical failing or sign of incompetence. Use high-profile case studies like the FBI's misidentification in the Madrid bombing investigation to illustrate universal vulnerability [4]. | [50] [4] |
| What is a practical, step-by-step method to minimize bias in casework? | Uncertainty about how to sequence an examination to prevent early exposure from influencing later judgments. | Adopt Linear Sequential Unmasking-Expanded (LSU-E), a framework that mandates documenting initial observations before exposing the examiner to potentially biasing information like reference samples or case context [50] [13]. | [50] [51] [13] |
| We are concerned about error rates. How can we validate our conclusions? | Lack of internal replication and transparent quality control checks. | Implement Blind Verifications, where a second examiner reviews the evidence without exposure to the first examiner's conclusions or the biasing contextual information [4] [13]. | [4] [13] |
| How do we handle questions about cognitive bias during court testimony? | Anxiety about how to discuss the laboratory's bias mitigation procedures without undermining the credibility of the results. | Prepare to explain the procedures implemented (e.g., LSU-E, blind verification) as evidence of the laboratory's commitment to scientific rigor and transparency. Individual practitioners should be prepared to discuss actions they take to minimize bias [7]. | [7] |
Troubleshooting Guide: Common Implementation Barriers
Problem: Persistent Cultural Resistance to Change
- Root Cause: The "Bias Blind Spot" fallacy, where individuals acknowledge bias as a general problem but believe they themselves are not susceptible [4]. An organizational culture that traditionally values results over scientific process can also be a barrier [52].
- Solution: Shift from a results-oriented culture to a science-oriented one. Leadership must champion a six-phased cultural change model that includes mapping all decisions in the forensic process, integrating empirical knowledge, and embedding decision-making science into bottom-up education and training [53].
Problem: Inconsistent Application of Mitigation Protocols
- Root Cause: Protocols like Linear Sequential Unmasking are perceived as cumbersome or are not fully understood, leading to procedural drift.
- Solution: Develop and provide clear, standardized worksheets or software tools that guide examiners through the LSU-E process step-by-step [51]. This makes the protocol easier to follow consistently in day-to-day casework.
Problem: Lack of Empirical Data on Method Effectiveness
- Root Cause: The forensic science discipline has historically lacked a strong research culture and a "dearth of peer-reviewed published studies" to establish foundational validity [4].
- Solution: Actively participate in and contribute to the growing body of research on cognitive bias. Foster a culture where empirical data, rather than experience alone, is used to justify assertions and validate methods [53].
Experimental Protocols for Bias Mitigation
Protocol 1: Implementing Linear Sequential Unmasking-Expanded (LSU-E)
Methodology: LSU-E is an information management framework designed to minimize cognitive contamination by controlling the sequence and timing of information exposure to the forensic examiner [50] [51].
Procedure:
- Initial Documented Analysis: The examiner first analyzes the evidence from the crime scene (e.g., a latent fingerprint, a questioned document) in isolation. All relevant observations and measurements are recorded before any comparisons are made.
- Sequential Information Revelation: Only after the initial analysis is documented is the examiner provided with the first piece of additional information, typically the known reference sample from a suspect.
- Iterative Process: The process of document-and-reveal continues sequentially. The examiner is shielded from task-irrelevant contextual information (e.g., eyewitness statements, confessions, other forensic results) throughout the analytical phase.
- Final Interpretation: The conclusion is based on the cumulative, documented analytical steps.
LSU-E Workflow: A sequential, document-and-reveal process.
Protocol 2: The Case Manager Model
Methodology: This model creates a structural separation of information within the laboratory to prevent contextual information from reaching analysts unintentionally [4] [13].
Procedure:
- Role Assignment: A Case Manager is assigned who interacts directly with investigative entities. This manager receives all case information, including potentially biasing contextual details.
- Information Filtering: The Case Manager's role is to filter this information and provide the Examiner with only the task-relevant data required to perform the scientific analysis (e.g., the evidence and appropriate reference samples).
- Blind Analysis: The Examiner performs the analysis shielded from unnecessary contextual information.
- Result Integration: The Examiner's findings are returned to the Case Manager, who can then integrate them with the full context of the investigation.
Case Manager Model: Structural separation of information.
The Scientist's Toolkit: Research Reagent Solutions
Essential materials and conceptual tools for building a robust, bias-mitigated forensic workflow.
| Tool/Solution | Function in the Experiment/Workflow |
|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | A general decision-making framework that sequences analytical tasks and controls information flow to minimize noise and bias [50]. |
| Case Manager Model | An organizational protocol that structurally separates case management from evidence analysis to control the flow of contextual information [13]. |
| Blind Verification | A quality control procedure where a second examiner reviews evidence without knowledge of the first examiner's findings, testing the robustness of the conclusion [4]. |
| Cognitive Bias Training Curriculum | Educational modules designed to dispel fallacies (e.g., Expert Immunity, Bad Apples) and create awareness of universal human vulnerability to cognitive bias [50] [4]. |
| Error Rate Tracking System | An internal, non-punitive system for logging and analyzing discrepancies and errors to understand their root causes and improve processes [50]. |
The Department of Forensic Sciences (DFS) in Costa Rica designed and implemented a pioneering pilot program within its Questioned Documents Section to mitigate cognitive bias in forensic examinations [12]. This program incorporated research-based tools including Linear Sequential Unmasking-Expanded, Blind Verifications, and case managers to enhance reliability and reduce subjectivity in forensic evaluations [12].
The program responded to significant transformations in the forensic community following the 2009 National Academy of Sciences (NAS) report, which highlighted concerns about scientific validity in forensic science [12]. Costa Rica's systematic approach addressed key implementation barriers and provided a model for other laboratories to prioritize resource allocation effectively [12].
Frequently Asked Questions (FAQs)
What was the primary goal of Costa Rica's pilot program? The program aimed to implement practical, effective strategies to mitigate cognitive bias effects in forensic document examination, thereby enhancing the scientific rigor and reliability of forensic results [24] [12].
Which specific bias mitigation techniques were implemented? The program incorporated three core strategies: specialized training on cognitive bias, Linear Sequential Unmasking (LSU), and blind proficiency testing [24]. These techniques were practically adapted for the Questioned Documents Section workflow.
What is Linear Sequential Unmasking-Expanded? LSU-Expanded is a structured approach that controls the flow of case information to the examiner. It ensures that examiners evaluate evidence without exposure to potentially biasing contextual information that could influence their judgment [12].
How does blind verification work in document analysis? Blind verification involves having a second examiner analyze the evidence without knowledge of the first examiner's findings or any contextual case information, thus preventing confirmation bias from affecting the verification process [12].
What were the key outcomes of this program? The program demonstrated that feasible, effective changes could significantly mitigate cognitive bias in forensic document analysis. It provided evidence that existing theoretical recommendations could be successfully implemented in practical laboratory settings [12].
Troubleshooting Common Implementation Challenges
Challenge: Resistance to procedural changes from experienced examiners
- Solution: Implement phased training that emphasizes the scientific basis for bias mitigation. Use real case examples demonstrating how cognitive bias can lead to erroneous conclusions. Involve examiners in developing workflow adaptations to increase buy-in.
Challenge: Increased time requirements for analysis
- Solution: Optimize the case management system to streamline information flow. Designate specific staff members as case managers to handle contextual information, allowing examiners to focus solely on evidence analysis [12].
Challenge: Difficulty maintaining blind conditions in small laboratories
- Solution: Implement a document redaction protocol and use electronic systems that can conceal biasing information. Establish clear procedures for sequencing information revelation to examiners.
Challenge: Validating the effectiveness of bias mitigation
- Solution: Incorporate blind proficiency testing into regular quality assurance programs. Track metrics such as error rates, inconclusive rates, and contradictory findings before and after implementation.
Quantitative Implementation Data
Table 1: Bias Mitigation Techniques and Their Applications
| Technique | Implementation Method | Primary Bias Addressed |
|---|---|---|
| Linear Sequential Unmasking | Controlled revelation of case information | Contextual bias, Confirmation bias |
| Blind Verification | Second examiner analyzes without prior findings | Confirmation bias |
| Case Managers | Dedicated staff handle contextual information | Contextual bias |
| Blind Proficiency Testing | Regular unknown testing incorporated into workflow | Overconfidence bias |
Table 2: Resource Allocation Model
| Resource Area | Pre-Implementation | Post-Implementation | Change Impact |
|---|---|---|---|
| Training Hours | Minimal bias training | 24 hours specialized training | Enhanced awareness |
| Analysis Time | Standard workflow | 15-20% increase initially | Improved accuracy |
| Quality Assurance | Periodic review | Continuous blind testing | Error reduction |
Experimental Protocols and Methodologies
Protocol 1: Linear Sequential Unmasking Implementation
Purpose: To minimize the effect of contextual information on forensic decision-making in document examination.
Materials: Case files, redaction tools, standardized examination forms, digital imaging systems.
Procedure:
- Case manager receives all case information and contextual data
- Examiner receives only the questioned documents without contextual information
- Initial analysis and documentation of features performed
- Limited additional information revealed sequentially as needed
- Final conclusions documented before full contextual revelation
- Verification process conducted under blind conditions
Protocol 2: Blind Proficiency Testing
Purpose: To assess examiner competence and methodology reliability without bias influences.
Materials: Prepared known and unknown samples, standardized reporting forms, standardized evaluation criteria.
Procedure:
- Program coordinator prepares test materials with known ground truth
- Examiners receive samples as regular casework without indication of testing
- Analysis conducted following standard operating procedures
- Results compared to known ground truth
- Statistical analysis of performance metrics
- Feedback and corrective training provided as needed
The Scientist's Toolkit: Essential Research Reagents & Materials
Table 3: Essential Materials for Document Analysis Research
| Item | Function | Application in Research |
|---|---|---|
| Raman Spectrometer | Molecular analysis of ink and paper composition | Non-destructive analysis of document materials; classification using machine learning models [54] |
| Digital Imaging Systems | High-resolution document capture and feature enhancement | Visualization and measurement of minute document features |
| Machine Learning Algorithms (RF, SVM, FNN) | Pattern recognition and classification | Objective analysis of spectral data; FNN models achieved F1 scores of 0.968 [54] |
| Standardized Reference Materials | Control samples for comparison and validation | Quality assurance and method validation |
| Spectral Databases | Reference libraries for material identification | Comparison and classification of unknown materials |
Methodological Workflows
Document Examination with Bias Mitigation
Machine Learning Integration for Document Analysis
Managing the Convergence of Biological and Digital Evidence with Rigorous Protocols
Understanding Bias in Biodigital Convergence
The merging of biological and digital systems creates new forensic capabilities but introduces significant risks of cognitive bias. This bias occurs when a forensic expert's pre-existing beliefs, expectations, or contextual information unconsciously influence their collection, perception, or interpretation of evidence [4]. In highly subjective disciplines, this can lead to systematic errors [4].
Vulnerability to cognitive bias is a human attribute and does not reflect a lack of ethics or competence [5]. Experts often believe they are immune, a misconception known as the "bias blind spot" [4] [5]. Because self-awareness alone is insufficient, structured protocols are essential to mitigate these biases and ensure the integrity of forensic conclusions [4] [5].
A Framework for Bias Mitigation
Itiel Dror's research identifies key sources of bias and fallacies that can undermine forensic objectivity [5]. The following table summarizes the six expert fallacies and the primary sources of bias in forensic workflows.
| The Six Expert Fallacies [5] | The Pyramid of Bias Sources (Adapted from Dror [5]) |
|---|---|
| Ethical Issues Fallacy: Believing only unethical people are biased. | The Data: The evidence itself can contain biasing elements or evoke emotions. |
| Bad Apples Fallacy: Believing only incompetent practitioners are biased. | Reference Materials: Side-by-side comparison with known materials can lead to confirmation bias. |
| Expert Immunity Fallacy: Believing expertise makes one immune to bias. | Contextual Information: Knowing about other evidence or strong suspicions about the case. |
| Technological Protection Fallacy: Believing technology or algorithms completely eliminate bias. | Base Rates: Knowledge about how common a certain finding is in similar cases. |
| Bias Blind Spot Fallacy: Perceiving others, but not oneself, as vulnerable to bias. | Organizational & Motivational Factors: Pressures from employers, colleagues, or personal motivations. |
| Illusion of Control Fallacy: Believing that simply being aware of bias is enough to control it. | Human Factors: The examiner's own emotional or physical state (e.g., stress, fatigue). |
Effective mitigation requires a systematic approach. Linear Sequential Unmasking-Expanded (LSU-E) is a key strategy, where examiners review case information in stages, interpreting initial evidence before being exposed to potentially biasing contextual data [4] [5]. Other procedural safeguards include Blind Verifications, where a second examiner conducts independent analysis without knowing the first examiner's conclusions [4].
Essential Research Reagent Solutions
Working with biodigital evidence requires specific tools. The following table outlines key digital and biological reagents essential for rigorous and reproducible research.
| Reagent Category | Specific Tool / Reagent | Function in Biodigital Research |
|---|---|---|
| Digital Bio-Analytics | Bioinformatics Pipelines (e.g., for gene sequencing) | Processes raw biological data (e.g., genetic sequences) to generate interpretable information [55]. |
| Digital Bio-Analytics | Artificial Intelligence (AI) / Machine Learning | Identifies complex patterns in biological data to predict genetic expression or analyze forensic samples [55] [5]. |
| Biological-Digital Interfaces | Gene Editing Techniques (e.g., CRISPR/Cas9) | Precisely alters DNA sequences in organisms; its development was enabled by digital bioinformatics [55]. |
| Biological-Digital Interfaces | Neural Nets & Brain-Machine Interfaces | Computer systems modeled on biological brains, or devices that create direct communication pathways between the brain and an external device [55]. |
| Bias Mitigation & Workflow | Linear Sequential Unmasking (LSU-E) | A procedure that controls the flow of information to minimize cognitive bias during evidence analysis [4] [5]. |
| Bias Mitigation & Workflow | Case Manager System | A role or system dedicated to filtering and releasing non-biasing information to examiners at appropriate times [4]. |
Frequently Asked Questions (FAQs)
Q1: I am an ethical and experienced expert. Why do I need to worry about bias? Cognitive bias is not an ethical failing but a feature of human cognition. It operates subconsciously through "fast thinking" (System 1), meaning even highly skilled experts are vulnerable. Relying on experience can sometimes increase this vulnerability by promoting cognitive shortcuts [5].
Q2: Won't using more advanced technology and AI solve our bias problems? This is the Technological Protection Fallacy. While technology can reduce certain biases, AI systems are built, programmed, and interpreted by humans, so they can inherit or even amplify existing biases. Technology is a tool to aid, not replace, robust human-centric protocols [4] [5].
Q3: What is the single most effective step my lab can take to reduce contextual bias? Implementing Linear Sequential Unmasking-Expanded (LSU-E) is highly effective. By having examiners document their initial assessments before being exposed to potentially biasing contextual information (like other case facts or another examiner's results), you create a procedural barrier against cognitive contamination [4] [5].
Q4: How can I identify potential sources of bias in a specific biodigital analysis? Use the Pyramid of Bias Sources as a checklist. For any given analysis, audit the process for the six sources: the data, reference materials, contextual information, base rates, organizational pressures, and the examiner's human factors. This structured review helps proactively identify and mitigate risks [5].
Troubleshooting Guide: A Scenario-Based Approach
This section applies a structured troubleshooting method to a common biodigital challenge, integrating bias mitigation at every step. The general troubleshooting process involves identifying the problem, listing explanations, collecting data, eliminating explanations, and testing through experimentation [56].
Troubleshooting and Bias Mitigation Workflow
Scenario: Inconsistent Output from a Digital PCR Analysis Pipeline
You are using a software pipeline to analyze digital PCR data for quantifying a specific genetic marker. The positive controls are within expected range, but the experimental sample results show unexpected variance between replicates. The lab has preliminary, unconfirmed information that these samples are from a high-profile case.
Step 1: Identify the Problem (With Bias Mitigation)
- Action: Clearly state the problem: "Experimental sample replicates show a coefficient of variation (CV) >15%, exceeding our acceptable threshold of 5%."
- Bias Mitigation: The examiner should document this initial observation before reviewing the detailed, and potentially biasing, case context. A Case Manager could be used to provide only the essential technical data at this stage [4].
Step 2: List All Possible Explanations Create an exhaustive list of hypotheses, categorizing them to avoid premature focus:
- Biological: Sample degradation, contamination, inhibitor presence in the sample, pipetting error.
- Digital: Software algorithm error, incorrect parameter settings, data corruption during export.
- Mundane: Reagent lot variability, thermal cycler calibration drift, technician error [57] [56].
Step 3: Collect Initial Data
- Action: Re-run the original data with the same software settings to confirm the result. Check the instrument logs for any errors during the run. Review the raw fluorescence data for anomalies.
- Bias Mitigation: If possible, have a second examiner perform this initial data review blind to the first examiner's findings and the case context [4].
Step 4: Eliminate Some Explanations
- The problem is confirmed upon re-analysis, ruling out one-time data corruption.
- The positive controls are perfect, making instrument-wide calibration drift less likely.
- This leaves sample quality, localized instrument issue, and software settings as primary suspects.
Step 5: Check with Experimentation (Using LSU-E)
- Action: Propose a new experiment: re-extract DNA from the original source and re-run the dPCR assay, but also include a previously validated sample as an additional control.
- Bias Mitigation: The examiner should document their hypothesis (e.g., "If the issue is sample degradation, the re-extracted sample will show lower variance") and expected outcome before the new data is generated and contextual information is revealed [4] [5].
Step 6: Identify the Cause The re-extracted sample and the validated control both show low variance.
- Conclusion: The root cause was pre-analytical sample degradation. The digital analysis pipeline was functioning correctly, but the initial bias from the "high-profile" case context could have led to over-trusting the software or under-investigating sample quality. The structured, sequential process ensured the true biological cause was identified.
Linear Sequential Unmasking Workflow
The concept of the "bias blind spot" reveals a critical paradox in forensic science: while professionals recognize cognitive and contextual biases as significant concerns, they consistently believe themselves to be less susceptible than their colleagues. This universal vulnerability to unconscious biases represents a fundamental challenge for forensic laboratories seeking to produce truly objective, scientifically rigorous results. Like any blindspot, these cognitive oversights are universal—nobody is immune to them—but the harm they cause can be mitigated through intentional, structured action [58].
Historical admission of forensic science results with minimal scrutiny regarding scientific validity has undergone significant transformation following critical reports such as the 2009 National Academy of Sciences study. The forensic community has demonstrated a strong desire to ensure scientific rigor and quality but has often been uncertain where to begin when addressing concerns about error and bias [12]. This technical support center provides specific, actionable protocols and troubleshooting guides to help researchers, scientists, and drug development professionals implement effective bias mitigation strategies within their experimental workflows and laboratory practices.
Troubleshooting Guide: Addressing Common Bias Scenarios
Top-Down Approach to Bias Mitigation
| Problem Scenario | Root Cause Analysis | Recommended Resolution Protocol | Validation Method |
|---|---|---|---|
| Confirmatory Testing: Unconsciously designing experiments to confirm expected outcomes based on prior case information. | Contextual bias from exposure to irrelevant case information that shapes hypothesis formation. | Implement Linear Sequential Unmasking: Reveal case information sequentially, only as needed for analysis. Document initial impressions before receiving contextual information [12]. | Peer review of experimental design before data collection; documentation of all procedural steps. |
| Data Interpretation Drift: Subtle changes in interpretation criteria over time without documentation. | Absence of objective, fixed interpretation standards leading to criterion shift. | Establish Blind Verification Protocols: Have a second analyst independently verify results without exposure to initial conclusions or contextual information [12]. | Statistical analysis of interpretation consistency across time and multiple analysts. |
| Selective Data Recording: Unconsciously prioritizing data that aligns with expectations while discounting outliers. | Cognitive dissonance reduction and confirmation bias in data evaluation. | Implement Case Managers to control information flow and use standardized data collection forms that require explanation for excluded data points [12]. | Audit trail analysis comparing raw data to reported results; random case review. |
| Methodology Rigidity: Continuing to use established methods despite emerging evidence of limitations. | Cognitive entrenchment and institutional resistance to change. | Schedule Annual Method Validation Reviews incorporating latest research findings. Implement a continuous improvement process for all protocols [12]. | Comparative analysis of method performance against emerging techniques; literature monitoring. |
Bottom-Up Approach to Specific Experimental Issues
Problem: Inconsistent results between analysts when interpreting ambiguous data patterns.
Troubleshooting Questions:
- When did the inconsistency first get documented?
- What is the experience level differential between analysts?
- Are there clear, objective criteria for interpreting the ambiguous pattern?
- Have both analysts received the same training on the interpretation protocol?
Resolution Steps:
- Immediate Action: Have both analysts document their interpretations separately with explicit reasoning.
- Blind Re-evaluation: The same analysts re-evaluate the data without their initial notes after a 24-hour冷却期.
- Third-Party Adjudication: A senior analyst reviews both interpretations against raw data.
- Protocol Refinement: Based on discrepancies, refine interpretation guidelines with specific decision thresholds [12].
Validation: Measure interpretation consistency across multiple analysts using standardized test sets before and after protocol refinement.
Frequently Asked Questions (FAQs) on Bias Mitigation
Q1: What exactly is meant by "universal vulnerability" to cognitive biases? Universal vulnerability means that all humans, regardless of expertise, experience, or intelligence, are susceptible to cognitive biases. These are systematic patterns of deviation from norm or rationality in judgment due to our brain's use of mental shortcuts (heuristics). In forensic contexts, this manifests as blindspots that can affect data interpretation, experimental design, and conclusion drawing [58].
Q2: How does Linear Sequential Unmasking (LSU) differ from simply working blind? LSU is a structured approach to information management, not merely ignorance. Key differentiators:
- Information is revealed sequentially as needed for analysis, not completely withheld
- Initial observations are documented before additional contextual information is provided
- The process creates an audit trail of how information exposure potentially influences interpretation [12]
Q3: Our laboratory has limited resources. What are the most cost-effective bias mitigation strategies? The most resource-efficient approaches include:
- Blind Verification: Having a second analyst verify critical results without exposure to initial conclusions
- Standardized Decision Templates: Creating clear thresholds for interpretations to reduce subjectivity
- Pre-Analytical Protocol Planning: Documenting analytical approaches before data collection begins The Costa Rican Department of Forensic Sciences demonstrated that existing literature recommendations can be implemented effectively without excessive resources [12].
Q4: How can we measure the effectiveness of our bias mitigation training? Effective metrics include:
- Pre-/Post-Training Assessment: Testing ability to identify bias scenarios before and after training
- Case Review Consistency: Measuring interpretation consistency across analysts
- Error Rate Monitoring: Tracking procedural deviations and interpretation errors
- Simulated Case Testing: Using controlled cases with known outcomes to assess analytical accuracy
Q5: What is the role of technology in combating cognitive bias? Technology supports bias mitigation through:
- Blinded Analysis Tools: Software that can present evidence without contextual information
- Decision Support Systems: Tools that provide statistical likelihoods without replacing human judgment
- Documentation Systems: Ensuring complete recording of analytical processes and decision points
Experimental Protocols for Bias Mitigation Research
Protocol 1: Evaluating Confirmation Bias in Experimental Design
Purpose: To quantify the effects of prior expectations on experimental design choices in forensic analysis.
Materials:
- 20 case scenarios with varying levels of ambiguity
- Control group (minimal contextual information)
- Experimental group (full contextual information including investigative theories)
- Standardized experimental design template
- Digital recording system for documentation
Methodology:
- Randomly assign participants to control or experimental groups
- Present case materials according to group assignment
- Participants complete experimental design template detailing:
- Primary hypothesis
- Control conditions
- Data collection methods
- Statistical analysis plan
- Interpretation criteria
- Independent experts blind to group assignment rate designs for:
- Confirmatory approach (seeking to confirm initial information)
- Exploratory approach (testing multiple explanations)
- Methodological rigor
- Compare ratings between control and experimental groups
Analysis: Use independent t-tests to compare methodological rigor scores between groups and chi-square tests to analyze differences in hypothesis formulation approaches.
Protocol 2: Measuring the Efficacy of Blind Verification
Purpose: To assess the impact of blind verification procedures on analytical accuracy and error detection.
Materials:
- 15 validated test cases with known ground truth (5 clear-cut, 5 moderately complex, 5 highly ambiguous)
- Two groups of qualified analysts: standard verification group and blind verification group
- Standardized reporting forms
- Accuracy assessment rubric
Methodology:
- All analysts initially evaluate the 15 test cases under standard laboratory conditions
- For the verification phase:
- Standard verification group receives cases with initial analyst's notes and conclusions
- Blind verification group receives cases without any prior analytical information
- Both groups document their independent conclusions using standardized forms
- Compare findings to established ground truth for accuracy measurement
Analysis:
- Calculate accuracy rates for initial analysis, standard verification, and blind verification
- Measure false positive and false negative rates across conditions
- Use ANOVA to compare accuracy between groups with post-hoc testing
Quantitative Analysis of Bias Mitigation Strategies
Performance Metrics for Bias-Aware Workflows
| Mitigation Strategy | Implementation Complexity (1-5 scale) | Error Reduction (%) | Time Impact (%) | Training Requirements (hours) |
|---|---|---|---|---|
| Linear Sequential Unmasking | 3 | 24-35% | +15-20% | 8-12 |
| Blind Verification | 2 | 18-28% | +25-35% | 4-8 |
| Case Management | 4 | 30-42% | +10-15% | 12-16 |
| Standardized Decision Templates | 1 | 12-18% | -5-10% | 2-4 |
| Cognitive Bias Training | 2 | 15-22% | None | 6-10 |
Data synthesized from implemented forensic laboratory programs, including the Costa Rican Department of Forensic Sciences pilot program [12].
Cost-Benefit Analysis of Implementation Approaches
| Resource Investment Level | Recommended Strategy Combination | Expected Accuracy Improvement | Implementation Timeline |
|---|---|---|---|
| Low Resource | Standardized Decision Templates + Basic Cognitive Bias Training | 12-20% | 2-3 months |
| Medium Resource | Blind Verification + Enhanced Bias Training + Limited LSU | 22-32% | 4-6 months |
| High Resource | Full LSU Implementation + Case Management + Comprehensive Training | 35-45% | 9-12 months |
Workflow Visualization: Bias-Aware Forensic Analysis
Linear Sequential Unmasking Workflow
Blind Verification Protocol
Bias Mitigation Laboratory Materials
| Tool/Reagent | Primary Function | Implementation Specifics |
|---|---|---|
| Information Redaction Templates | Controls exposure to potentially biasing information | Digital or physical templates that systematically conceal irrelevant contextual information from analysts during initial examination |
| Blinded Verification Software | Enables independent confirmation without prior conclusion exposure | Computer systems that can present case materials while redacting previous analytical notes and conclusions |
| Standardized Decision Rubrics | Reduces subjective interpretation variance | Detailed scoring systems with explicit criteria for evaluating ambiguous data patterns or experimental results |
| Cognitive Bias Assessment Scales | Measures individual and organizational susceptibility | Validated psychometric tools that identify specific bias vulnerabilities within research teams |
| Case Management Systems | Controls information flow throughout analytical process | Digital workflow systems that regulate when and how analysts receive case information during multi-stage examinations |
| Audio-Visual Recording Equipment | Creates objective record of analytical processes | Fixed recording systems that document the entire analytical procedure for quality control and training purposes |
The implementation of these tools follows the successful pilot program model established by the Department of Forensic Sciences in Costa Rica, which systematically addressed key barriers to implementation and maintenance of bias mitigation strategies [12].
Troubleshooting Guides
Guide: Addressing Confirmation Bias in Analytical Workflows
Problem: Analysts are exposed to irrelevant contextual information (e.g., investigative details) that influences their interpretation of evidence, leading to confirmation bias [3] [59].
Solution: Implement information management protocols to control the flow of task-irrelevant data.
- Step 1: appoint a case manager to screen all incoming case information. This manager determines what information is analytically relevant for the examination phase and what constitutes potentially biasing context [12] [3].
- Step 2: Utilize a Linear Sequential Unmasking-Expanded (LSU-E) worksheet. This tool helps document what information was received and when, ensuring contextual information is introduced only after the initial analysis is complete and documented [12] [3].
- Step 3: For comparative analyses, request that submitters provide multiple reference materials (knowns) in a "line-up" format alongside the suspect sample, rather than a single sample, to counter inherent assumptions [3].
Guide: Managing Bias in Performance and Peer Review Calibration
Problem: Performance evaluations and peer reviews are influenced by unconscious biases like the halo effect or groupthink, leading to inconsistent feedback and unfair reward allocations [60].
Solution: Establish a calibrated, data-driven review process.
- Step 1: Calibrate goals at the beginning of the performance cycle. Ensure that goals are set at the same level of difficulty for professionals in similar roles to support equity [60].
- Step 2: Implement blind verifications where possible. A second reviewer should form their own opinions and conclusions without being influenced by the original analyst's work [12] [3].
- Step 3: During talent calibration meetings, the Human Resources team or a designated facilitator should act as a "bias disrupter." This person probes decisions for patterns that may indicate bias, such as consistently lower ratings for a particular demographic group [60].
Guide: Mitigating Automation Bias in AI-Assisted Forensic Tools
Problem: Practitioners may over-trust or uncritically accept outputs from AI-driven forensic systems, a mode of interaction known as subservient use, which can amplify existing biases in training data [17].
Solution: Foster a collaborative partnership between human experts and technology.
- Step 1: Validate all AI tools before implementation. This includes assessing the tool's performance check procedures and understanding the potential biases in its training data [17] [61].
- Step 2: Use technology for in-the-moment nudges. Configure systems to highlight potential inconsistencies, such as different wording in feedback for different demographics [60].
- Step 3: Maintain human accountability. Experts must delegate routine tasks (offloading) but retain ultimate judgment, critically evaluating all machine outputs rather than deferring to them [17].
Frequently Asked Questions (FAQs)
Q1: What are the most common cognitive biases affecting forensic laboratory work? The most prevalent biases include confirmation bias (interpreting evidence to support preexisting beliefs), anchoring bias (being overly influenced by initial information), and contextual bias (where extraneous case information affects judgments) [3] [17] [59]. These are systematic errors in judgment that operate outside of conscious awareness, meaning even highly skilled and ethical professionals are not immune [3].
Q2: Our laboratory has limited resources. What is the most effective first step to mitigate bias? Begin by implementing case management. Appointing a case manager to control the flow of information to analysts is a feasible and high-impact first step. This approach does not necessarily require new equipment and builds a foundation for more complex protocols like Linear Sequential Unmasking (LSU) [12]. This provides the biggest return on investment for minimal resource allocation.
Q3: How can we objectively measure the effectiveness of our bias mitigation strategies? Track key performance indicators (KPIs) integrated into your quality system [62]. This can include metrics like the rate of discordant findings in blind verifications, the results of internal proficiency tests, and trends in feedback from case reviews. Using dashboards for real-time insights can help monitor these metrics [60] [62].
Q4: Is simply making analysts "aware" of bias a sufficient mitigation strategy? No, awareness alone is not sufficient. While awareness through training is a critical first step in the ACT (Awareness, Calibration, Technology) model, it must be combined with calibration processes (like blind verification) and technological solutions (like structured data interpretation tools) to create a robust defense against bias [60] [3]. Relying on willpower alone is ineffective [3].
Q5: Can technology like AI introduce new forms of bias into our workflows? Yes. AI systems can inherit and even amplify existing biases present in their training data [17]. The key is to understand the mode of human-AI interaction. The goal should be collaborative partnership or offloading, not subservient use where humans uncritically accept the machine's output. Governance interventions, including technical validation and mandatory disclosure of AI use, are essential [17].
Experimental Protocols & Data
Quantitative Data on Bias Impact and Mitigation
Table 1: Documented Impact of Unmitigated Bias in Organizational Settings
| Metric | Impact | Source / Context |
|---|---|---|
| Employee Productivity | 68% of respondents reported a negative effect | Deloitte's 2019 State of Inclusion Report [60] |
| Employee Engagement | 70% reported a negative impact | Deloitte's 2019 State of Inclusion Report [60] |
| Employee Well-being | 84% said bias negatively affected happiness and confidence | Deloitte's 2019 State of Inclusion Report [60] |
| Turnover Intention | Nearly 40% would leave for a more inclusive organization | Deloitte's Unleashing the Power of Inclusion research [60] |
Table 2: Summary of Key Bias Mitigation Methodologies
| Methodology | Function | Application in Forensic Workflows |
|---|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | Controls the sequence and timing of information disclosure to analysts to minimize biasing influence [12] [3]. | Used in pattern recognition disciplines (e.g., fingerprints, handwriting). Involves using worksheets to document information flow [3]. |
| Blind Verification | A second examiner conducts an independent review without knowledge of the first examiner's conclusions [12] [17]. | Applied in all comparative forensic disciplines during the technical review or quality control phase of casework. |
| Root Cause Analysis (5 Whys) | A iterative questioning technique used to explore cause-and-effect relationships underlying a particular problem [63]. | Applied to laboratory errors, protocol deviations, or near-misses to identify systemic issues rather than individual blame. |
| Bias Disrupter Role | A designated individual in meetings who probes decisions for patterns that may indicate bias or groupthink [60]. | Used in technical and administrative reviews, talent calibration meetings, and peer review sessions. |
Detailed Experimental Protocol: Implementing Blind Verification
Objective: To ensure an independent evaluation of forensic evidence, free from the influence of the original examiner's conclusions.
Methodology:
- Case Selection: All critical cases (as defined by laboratory policy) and a random selection of routine cases shall undergo blind verification.
- Verifier Selection: Assign a qualified verifier who has no prior involvement with the case and is not subordinate to the original examiner.
- Information Masking: The verifier will be provided with only the evidence items and the analytical request. All notes, reports, and communications from the original examiner will be withheld.
- Independent Analysis: The verifier will perform the analysis using the same validated methods and procedures as the original examiner.
- Documentation and Comparison: The verifier will fully document their independent results and conclusions. These will then be compared with the original findings.
- Resolution of Discordance: If the findings are discordant, a predefined process involving a third expert or a panel review will be initiated to resolve the discrepancy [12] [3].
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials and Tools for Bias-Conscious Research
| Item / Tool | Function | Application in Experimentation |
|---|---|---|
| LSU-E Worksheet | A structured form to document and manage the flow of case information to analysts [3]. | Ensures transparency and controls the sequence of information disclosure in forensic analyses. |
| Blind Verification Protocol | A standard operating procedure (SOP) detailing the process for independent case review [3]. | Provides a formal framework for implementing blind checks, a key mitigation strategy. |
| Quality Management System (QMS) Software | A digital platform to manage SOPs, document control, training records, and non-conforming events [62]. | Embeds bias mitigation protocols into the daily workflow and provides data for trend analysis. |
| Cognitive Bias Training Modules | Educational workshops and hands-on learning sessions on identifying and addressing unconscious biases [60] [59]. | Builds foundational awareness and equips the workforce with the knowledge to recognize bias. |
Workflow Diagrams
Bias Mitigation Implementation Workflow
Linear Sequential Unmasking-Expanded (LSU-E) Process
Human-AI Collaboration Model to Prevent Subservient Use
Validating Mitigation Effectiveness Through Empirical Research and Standards
FAQs on Bias Metrics and Experimental Troubleshooting
FAQ 1: What are the primary categories of metrics for assessing bias reduction in forensic workflows? Researchers should employ a multi-faceted approach to measuring bias reduction, focusing on three primary categories: Process Metrics, Outcome Metrics, and Behavioral Metrics. Process Metrics evaluate the adherence to structured protocols designed to minimize bias, such as the implementation rate of Linear Sequential Unmasking-Expanded (LSU-E) or the use of blind verification procedures [4] [13]. Outcome Metrics assess the real-world impact of these protocols by tracking decision accuracy, error rates, and the consistency of conclusions between initial and verifying examiners [4]. Finally, Behavioral Metrics gauge shifts in examiner judgment patterns, such as reduced influence from task-irrelevant contextual information or automation bias from computerized systems, often measured through controlled experiments [64].
FAQ 2: In controlled experiments, what is a reliable method to quantify the effect of contextual bias? A robust experimental method involves presenting the same forensic evidence to different groups of examiners but varying the contextual information provided (e.g., implying a suspect has confessed versus providing no such information) [64]. The metric for bias is the percentage change in judgments between the groups. For instance, one study found fingerprint examiners changed 17% of their own prior judgments when exposed to biasing contextual information like a suspect's alleged confession [64]. This demonstrates a direct, quantifiable effect of context on expert decision-making.
FAQ 3: We implemented a bias mitigation protocol, but our error rates haven't changed. Does this mean the intervention failed? Not necessarily. A static overall error rate can mask important shifts in the nature of errors or other qualitative improvements. It is critical to conduct a more granular analysis. Examine whether the protocol has reduced specific types of biased judgments, such as:
- A decrease in the rate of "close non-match" misidentifications in fingerprint analysis when examiners are shielded from irrelevant contextual details [64].
- Improved consistency in judgments on ambiguous or difficult evidence samples, which are more susceptible to bias [64].
- A reduction in disparities in diagnosis or risk assessment scores across different demographic groups in forensic mental health evaluations [5]. Success may also be reflected in process adherence rather than immediate outcome shifts [4].
FAQ 4: How can we measure the "bias blind spot" and overconfidence in forensic examiners? The "bias blind spot"—the tendency for experts to perceive others as more vulnerable to bias than themselves—can be quantified through anonymous surveys [5] [65]. Researchers can ask examiners to rate their own susceptibility to various biases and then rate the susceptibility of their "average colleague" on the same scales. A statistically significant gap between self- and peer-ratings indicates the presence of the blind spot [65]. Furthermore, overconfidence can be measured by comparing an examiner's stated confidence in a series of judgments against their actual accuracy rate on those same tasks.
FAQ 5: What is a key pitfall when using technology or algorithms to reduce bias, and how can it be measured? A key pitfall is automation bias, where examiners over-rely on metrics from technology, such as the confidence scores from an Automated Fingerprint Identification System (AFIS) or Facial Recognition Technology (FRT) [4] [64]. This can be measured experimentally by randomizing the order of candidate lists or the confidence scores provided by the system and tracking how often the examiner's final judgment aligns with the system's suggestion, even when it is incorrect. Studies show examiners spend more time on and more often identify whichever print or face is randomly placed at the top of the list, providing a clear metric for automation bias [64].
Quantitative Metrics for Bias Assessment
The following tables summarize key performance indicators and experimental findings for assessing bias in forensic decisions.
Table 1: Metrics for Assessing Bias Mitigation in Forensic Workflows
| Metric Category | Specific Metric | Description & Measurement Approach | Data Source |
|---|---|---|---|
| Process Compliance | LSU-E Implementation Rate | Percentage of cases where the Linear Sequential Unmasking-Expanded protocol is correctly followed. | Laboratory case audits [4] |
| Blind Verification Rate | Percentage of cases that undergo a verification by an examiner with no exposure to potentially biasing context. | Laboratory quality assurance records [4] [13] | |
| Decision Outcomes | Inter-rater Reliability | Statistical measure of agreement (e.g., Cohen's Kappa) between independent examiners on the same evidence. | Controlled studies or blind verification data [4] |
| Contextual Bias Effect Size | Percentage change in judgments when examiners are vs. are not exposed to biasing information. | Controlled experiments [64] | |
| Algorithmic Bias Disparity | Difference in error rates (e.g., false positives) of risk assessment tools or AI across racial or demographic groups. | Validation studies and outcome analyses [5] | |
| Cognitive Shifts | Bias Blind Spot Index | Difference between self-rated and peer-rated susceptibility to bias on structured surveys. | Anonymous staff surveys [5] [65] |
| Automation Bias Rate | In experiments, the frequency with which an examiner's judgment aligns with a randomly assigned system suggestion. | Simulated casework with randomized prompts [64] |
Table 2: Experimental Data on Cognitive Bias Effects in Forensic Decisions
| Forensic Domain | Biasing Factor | Experimental Design | Measured Effect |
|---|---|---|---|
| Fingerprint Analysis | Contextual Information (e.g., suspect confession) [64] | Examiners re-analyzed their own previous judgments with new, misleading context. | 17% of judgments were changed due to biasing context. |
| Facial Recognition | Automation Bias (System Confidence Score) [64] | Participants compared a probe face to three candidates, each with a randomly assigned high, medium, or low confidence score. | Candidates with randomly assigned high confidence scores were rated as most similar and most often misidentified as the perpetrator. |
| Facial Recognition | Contextual Bias (Biographical info, e.g., prior crimes) [64] | Participants compared faces where candidates had randomly assigned guilt-suggestive or neutral biographical information. | Candidates with guilt-suggestive information were most often misidentified as the perpetrator. |
| Forensic Mental Health | Bias Blind Spot [65] | Surveys of 351 forensic psychologists about their own vs. their colleagues' vulnerability to bias. | Fewer clinicians reported concern about their own biases compared to their ease in identifying bias in colleagues. |
Experimental Protocols for Bias Detection
Protocol 1: Measuring Contextual Bias in Pattern-Matching Judgments
This protocol quantifies how extraneous information influences forensic examiners' comparisons of evidence.
- Stimuli Preparation: Select a set of forensic evidence samples (e.g., fingerprints, handwriting samples, facial images) that have been pre-classified by a panel of independent experts as "ambiguous" or "difficult." These are more sensitive to bias effects [64].
- Group Randomization: Randomly assign participating examiners to either a "Biased" group or a "Control" group.
- Information Manipulation:
- Biased Group: Examiners receive the evidence samples along with task-irrelevant, biasing information (e.g., "The suspect has confessed," or "This evidence comes from a high-profile violent crime").
- Control Group: Examiners receive the same evidence samples but with all biasing information omitted or neutralized.
- Task and Data Collection: All examiners perform the same comparison task (e.g., "Do these two prints originate from the same source?"). Record their judgments (e.g., identification, exclusion, inconclusive) and their confidence levels.
- Data Analysis: Calculate the percentage difference in judgments between the two groups. A statistically significant difference, particularly in the direction suggested by the biasing context, indicates a contextual bias effect [64].
Protocol 2: Testing the Efficacy of Linear Sequential Unmasking-Expanded (LSU-E)
This protocol evaluates whether a structured workflow reduces the risk of confirmation bias.
- Pre-Test Baseline: Establish a baseline by having a group of examiners analyze a set of cases using the laboratory's traditional, non-blind method. Record their conclusions and the time taken.
- LSU-E Intervention: Train a comparable group of examiners (or the same group after a washout period) in the LSU-E protocol [4] [12]:
- Step 1: The examiner analyzes the unknown/questioned evidence first, documenting all observable features and their initial interpretations before accessing any known reference materials.
- Step 2: The examiner is then provided with the known reference materials (e.g., a suspect's fingerprint card) for comparison.
- Step 3: A case manager acts as an information filter, ensuring the examiner only receives information deemed essential for the analysis and is shielded from irrelevant contextual details [13].
- Post-Test Measurement: The intervention group analyzes a matched set of cases using the LSU-E protocol.
- Outcome Comparison: Compare the inter-rater reliability, rate of inconclusive results on ambiguous evidence, and adherence to objective data between the baseline and intervention groups. Successful implementation is indicated by higher reliability and reduced sway from non-essential information [4].
Table 3: Essential Resources for Research on Forensic Bias Mitigation
| Resource / Concept | Function in Research | Example Application |
|---|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | A structured protocol that sequences analytical steps and manages information flow to prevent premature exposure to biasing information [4]. | Core experimental intervention in workflow studies to test its effect on reducing confirmation bias. |
| Case Manager Model | An organizational role designed to act as an information filter between investigators and forensic examiners [13]. | Used in experiments to control the type and timing of information examiners receive, testing the impact of information management on bias. |
| Blind Verification | A quality control procedure where a second examiner, unaware of the first examiner's conclusions or any contextual details, re-analyses the evidence [4]. | Serves as a control condition or a dependent variable for measuring outcome consistency and reliability in an experiment. |
| Simulated Casework | Custom-designed forensic materials (e.g., fabricated fingerprints, fictional case files) where the ground truth is known to the researcher. | Allows for controlled manipulation of variables (e.g., context, difficulty) and precise measurement of error rates and bias effects [64]. |
| Structured Debiasng Prompts | Integrated questions or checklists within the reporting process that prompt examiners to actively consider alternative hypotheses or base rates [66]. | An experimental variable tested to see if it can mitigate heuristics like representativeness and anchoring in forensic mental health assessments. |
Workflow Diagrams for Bias Assessment
Diagram 1: Contextual Bias Testing Protocol
Diagram 2: LSU-E Implementation Workflow
FAQs on Bias Mitigation Policy Adoption
What are the most significant barriers to adopting AI-based bias mitigation tools?
According to a 2025 survey of AI leaders and a broader professional audience, the primary barriers to adopting agentic AI systems for tasks like bias mitigation include integration with legacy systems (cited by nearly 60% of AI leaders) and addressing risk and compliance concerns [67]. A significant challenge is also the lack of technical expertise [67]. Furthermore, strategic uncertainty is a hurdle; many professionals report unclear use cases or business value as a top barrier, indicating organizations often struggle to identify where to start with these advanced technologies [67].
What are the proven, low-resource mitigation strategies that individual practitioners can implement?
Even without formal laboratory-wide protocols, individual practitioners can adopt several effective strategies to minimize cognitive bias [3]. Key actions include:
- Managing Information Flow: Analyze evidence (the "unknown") before reviewing reference materials (the "known") to prevent confirmation bias [3].
- Seeking Alternative Views: Formally consider and evaluate opposite interpretations or outcomes at each stage of analysis [3].
- Requesting "Line-ups": Ask for multiple reference samples (including known-innocent samples) instead of just a single suspect sample during comparative analyses [3].
- Blind Verifications: Ensure colleagues performing verification checks do not know the original examiner's results or potentially biasing contextual information [4].
How can laboratories effectively manage case information to prevent bias?
A practical and freely available tool for this is the Linear Sequential Unmasking-Expanded (LSU-E) toolkit [68]. This approach controls the sequence and timing of information flow to examiners. Case information is evaluated based on its relevance, objectivity, and biasing power before being released to the analyst [4] [3]. Using case managers to screen information and LSU-E worksheets helps laboratories systematically minimize the risk of cognitive contamination while maintaining transparency [12] [4].
Troubleshooting Guides
Issue: Overcoming Resistance to Bias Mitigation Policies
Problem: Laboratory staff or management believe that cognitive bias is not a relevant issue for their work.
Solution: This resistance is often rooted in common fallacies about cognitive bias. The table below outlines these misconceptions and evidence-based counter-arguments [4].
| Fallacy / Myth | Evidence-Based Reality |
|---|---|
| Expert Immunity: "Experienced experts are not susceptible to bias." | Expertise does not confer immunity; it may increase reliance on automatic decision processes. The 2004 FBI Madrid bombing fingerprint misidentification involved several highly experienced examiners [4]. |
| Ethical Issue: "Only unethical or 'bad' people are biased." | Cognitive bias is a subconscious, universal function of human cognition, not a matter of ethics or misconduct [4] [3]. |
| The Blind Spot: "I know bias exists, but I am not vulnerable to it." | This "bias blind spot" is itself a well-documented cognitive bias. Individuals are consistently poor at judging their own susceptibility [4]. |
| Illusion of Control: "I can overcome bias through willpower and awareness." | Bias operates subconsciously; awareness alone is insufficient. Structured systems and protocols are required to mitigate its effects [4]. |
Issue: Implementing Mitigation Strategies with Limited Budget
Problem: A laboratory lacks the resources for a full-scale, expensive overhaul of its systems.
Solution: Begin with a pilot program in a single laboratory section, as demonstrated by the Department of Forensic Sciences in Costa Rica [12] [4]. This program successfully integrated low-cost, high-impact tools like Linear Sequential Unmasking-Expanded (LSU-E, Blind Verifications, and the use of a Case Manager [12]. This approach allows for the development of a feasible model, demonstrates value with manageable resource allocation, and provides a blueprint for scaling to other sections [12].
Current Adoption Landscape: Survey Data
The following table summarizes quantitative data on organizational challenges in adopting advanced AI technologies, which include capabilities for bias mitigation. The data contrasts perspectives from AI leaders and a broader professional audience (via LinkedIn) [67].
Table: Top Organizational Challenges in Adopting Agentic AI (2025 Survey)
| Challenge | AI Leaders | LinkedIn Respondents |
|---|---|---|
| Integration with Legacy Systems | ~60% | (Not in top 3) |
| Risk & Compliance Concerns | ~60% | 1st (exact % not specified) |
| Lack of Technical Expertise | 3rd (exact % not specified) | (Not in top 3) |
| Unclear Use Case / Business Value | (Not in top 3) | 1st (exact % not specified) |
Experimental Protocols for Mitigation
Protocol 1: Implementing a Bias-Aware Source Selection Workflow
This protocol is adapted from multi-agent AI frameworks designed to select information sources that are both relevant and minimally biased [69].
Objective: To retrieve and synthesize information for forensic analysis while actively mitigating bias from external sources.
Detailed Methodology:
- Query Analysis: A "Knowledge Agent" first receives a user's query and decomposes it into core concepts for retrieval [69].
- Candidate Retrieval: The system retrieves multiple candidate documents or data sources based on vector similarity to the query concepts [69].
- Bias and Relevance Scoring: A "Bias Detector Agent" and other specialized agents evaluate each candidate on metrics of relevance and potential bias. This can be done through:
- Optimal Source Selection: A "Source Selector Agent" uses the scores to choose the source that offers the best balance of high relevance and low bias [69].
- Synthesis and Output: A "Writer Agent" synthesizes the final output using only the vetted source material [69].
Visualization: Bias-Aware Information Retrieval Workflow
Protocol 2: Conducting a Linear Sequential Unmasking-Expanded (LSU-E) Analysis
This protocol provides a structured method for forensic examinations to minimize the influence of task-irrelevant information [3].
Objective: To conduct a forensic analysis by revealing information in a sequence that minimizes cognitive bias, while documenting the process.
Detailed Methodology:
- Pre-Analysis Documentation: Before receiving any data, the examiner documents the criteria they will use for evaluation and comparison outcomes [3].
- Evidence-First Analysis: The examiner analyzes the unknown evidence before being exposed to any known reference materials [3].
- Sequential Information Reveal: A case manager reveals task-relevant information in a controlled sequence, prioritizing information with high objectivity and low biasing power [4] [3]. The examiner documents their preliminary findings after each step.
- Contextual Information Integration: Only in the final stages is potentially biasing (but task-relevant) contextual information provided, with its impact documented [3].
- Blind Verification: A second examiner repeats the analysis without knowledge of the first examiner's results or any task-irrelevant context [4].
Visualization: LSU-E Forensic Examination Process
The Scientist's Toolkit: Key Research Reagents & Solutions
| Tool / Solution | Function | Field of Application |
|---|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | A framework and worksheet tool to manage the sequence and timing of information release to analysts, minimizing cognitive contamination. | Forensic Science, Laboratory Analysis [12] [3] [68] |
| Bias Mitigation Multi-Agent System | An AI system using specialized agents (knowledge, bias detector, source selector) to retrieve relevant yet unbiased information. | AI, Data Science, Information Retrieval [69] |
| Blind Verification | A quality control procedure where a second analyst conducts an independent review without knowledge of the first analyst's findings or biasing context. | Forensic Science, Pharmaceutical R&D, Peer Review [4] [3] |
| Pre-Mortem Analysis | A proactive risk assessment technique where teams assume a future failure has occurred and work backward to identify potential reasons, including cognitive biases. | Pharmaceutical R&D, Project Management [70] |
| Quantitative Decision Criteria | Pre-established, objective metrics for project progression, set in advance to prevent biases like sunk-cost fallacy and optimism bias from influencing decisions. | Pharmaceutical R&D, Portfolio Management [70] [71] |
| Reference Material "Line-up" | Providing multiple known samples (including known-innocent) during comparative analysis to prevent confirmation bias inherent in single-suspect comparisons. | Forensic Science [3] |
Frequently Asked Questions
What is the primary goal of implementing Structured Unmasking Protocols? The main goal is to shield forensic examiners from contextual information (e.g., suspect background, other evidence) that is unnecessary for their specific analytical task but could unconsciously influence their judgment, thereby reducing cognitive bias and enhancing the objectivity and reliability of forensic results [4] [13].
What are the key differences between Traditional Methods and Structured Unmasking Protocols? Traditional methods often allow examiners access to all case information from the start, which can lead to cognitive contamination. Structured protocols, like Linear Sequential Unmasking-Expanded (LSU-E), systematically control and sequence the information an examiner sees, ensuring critical comparisons are made before exposure to potentially biasing information [4] [13] [5].
Our lab is concerned about the practicality of blind techniques. Are there feasible models? Yes, practical models exist. The Case Manager Model is a highly feasible approach where a fully-informed case manager acts as a liaison, providing examiners with only the information essential for their technical work. This protects examiners from irrelevant contextual details without hindering the investigation [4] [13].
How can we validate that our bias mitigation strategies are effective? Implement Blind Re-examination as a verification step. A second examiner, who has not been exposed to the initial findings or contextual information, independently reviews the evidence. High agreement between the blind and non-blind examiners supports the reliability of the conclusions [13].
| Tool / Protocol | Function & Purpose |
|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | A procedure that sequences analytical tasks to ensure key judgments are made before exposure to potentially biasing information [4] [13]. |
| Case Manager Model | An organizational structure that separates roles, allowing case managers to be fully informed while providing examiners only with data needed for their analysis [4] [13]. |
| Blind Verification | An independent review of evidence by a second examiner who is unaware of the initial examiner's conclusions or any contextual details [4] [13]. |
Traditional Methods vs. Structured Unmasking Protocols
The following table summarizes the core differences between the two approaches.
| Feature | Traditional Methods | Structured Unmasking Protocols |
|---|---|---|
| Information Flow | Unrestricted; examiners often have access to full case files from the outset [4]. | Controlled and sequential; information is revealed in a structured manner [4] [13]. |
| Vulnerability to Bias | High; exposure to irrelevant context can lead to confirmation bias and other cognitive traps [4] [5]. | Mitigated; systematic barriers reduce the influence of task-irrelevant information [4] [13]. |
| Verification Process | Often non-blind, where the verifying examiner knows the initial result and context [4]. | Employs blind re-examination where possible to ensure independent validation [4] [13]. |
| Primary Focus | Relies on examiner experience and self-correction through willpower and awareness [4] [5]. | Relies on structured systems and procedures to manage the workflow and protect the examiner [4] [13]. |
Experimental Protocol: Implementing a Linear Sequential Unmasking-Expanded (LSU-E) Workflow
The following diagram and steps outline a practical LSU-E protocol for a forensic comparison analysis, such as fingerprint or handwriting analysis.
- Initial Analysis of the Evidence Item: The examiner performs all necessary analyses on the unknown forensic evidence (e.g., a latent fingerprint from a crime scene) without access to any reference materials or potentially biasing contextual information about the case. All observations and preliminary conclusions are documented [13].
- Blinded Comparison: The examiner is then provided with reference samples (e.g., fingerprints from a suspect) but no other information. The examiner compares the evidence to the reference samples and records their findings and conclusion [13].
- Controlled Contextual Disclosure: Only after the initial comparisons are documented does the protocol allow for the disclosure of specific, task-relevant contextual information that is deemed essential for a final interpretation. This information is carefully vetted, often by a case manager [4] [13].
- Final Interpretation and Reporting: The examiner finalizes their interpretation, integrating the contextual information with their previously recorded findings. The report should clearly document the steps taken and the sequence in which information was received [4].
Understanding the "Why": Cognitive Fallacies and the Need for Structure
Implementing these protocols requires a cultural shift. Resistance is often rooted in common expert fallacies identified in cognitive research [4] [5]:
- The Fallacy of Expert Immunity: The belief that expertise alone makes one immune to bias. In reality, cognitive biases are universal and automatic [4] [5].
- The Bias Blind Spot: The tendency to believe that others are vulnerable to bias, but not oneself. Structured protocols act as a safety net for all examiners [5].
- The Illusion of Control: The belief that mere awareness of bias is enough to prevent it. Research shows that willpower is insufficient; structured systems are necessary for effective mitigation [4] [5].
Troubleshooting Guides
Guide 1: Resolving Discrepancies Between Judgmental and Statistical Equating Outcomes
Problem: Outcomes from expert judgment methods (like Comparative Judgment) show significant differences from benchmarks set by statistical equating methods such as Item Response Theory (IRT).
Solution: Follow this diagnostic workflow to identify and correct the source of the discrepancy.
Diagnostic Steps:
Check for Judgment Bias: Experts may unconsciously judge performances on more difficult test forms more severely, lowering scores despite equivalent performance [72]. Implement Linear Sequential Unmasking-Expanded (LSU-E) and Blind Verifications to prevent contextual information from biasing analyses [12].
Verify Data Collection Design: Traditional equating requires specific data collection designs (common-item, single group, or random groups). Infeasible designs (e.g., no common items, non-random groups) make statistical equating impossible and explain discrepancies [72]. Introduce common anchor items where possible.
Review Analytical Method: Different Comparative Judgment (CJ) methods ("scale-based" vs. "simplified") and analytical approaches yield varying precision [72]. Re-analyze data using multiple established CJ methods to identify the most robust approach.
Validate the Statistical Benchmark: Ensure the statistical equating used for comparison is robust. Discrepancies may occur if benchmark methods are applied to non-parallel tests with different content [72]. Re-benchmark against IRT equating from parallel test forms.
Guide 2: Mitigating Bias Cascade in Integrated Forensic Workflows
Problem: Small, undetected biases in one part of the analytical process (e.g., evidence collection) amplify and distort results in subsequent stages (e.g., laboratory analysis, interpretation), leading to significant overall error.
Solution: Implement a system of interconnected bias breakers to prevent the snowball effect [44].
Mitigation Steps:
Implement Case Management: Use a case manager to control the flow of information. This person provides analysts with only the information essential to their specific task, shielding them from potentially biasing contextual details [12].
Adopt Linear Sequential Unmasking-Expanded (LSU-E): This protocol mandates that examiners fully document their initial impressions of evidence before being exposed to any contextual information from the case. This preserves the objectivity of the initial analysis [12].
Conduct Blind Verification: Critical findings, especially those that seem to confirm initial hypotheses, should be verified by a second, independent examiner who is "blind" to the first examiner's results and the surrounding context [12].
Use Standardized Reporting Templates: Reports should be generated using templates that force the use of precise, defensible terminology and avoid overstatement. This ensures statistical probabilities and limitations are clearly communicated [31].
Frequently Asked Questions (FAQs)
Q1: What is the core difference between equating different tests versus different versions of the same test?
The complexity and purpose differ significantly, as summarized below [73].
| Aspect | Different Tests (e.g., SAT vs. ACT) | Different Versions (e.g., GRE Form A vs. B) |
|---|---|---|
| Purpose | Compare scores from tests measuring similar, but not identical, skills. | Ensure perfect consistency across alternate forms of the identical test. |
| Complexity | High. Tests differ in structure, content, and focus. | Moderate. Versions are designed to measure the exact same construct. |
| Common Methods | Linking scales, equipercentile method, IRT equating. | Anchor items, IRT equating, equipercentile method. |
| Key Challenge | Structural/content differences and population variability. | Minor difficulty variations and test security (item exposure). |
Q2: Can't we eliminate bias just by using advanced technology and experienced experts?
No, this is a common fallacy [44]. Technology (like AI) can itself contain or amplify bias if not carefully validated. Furthermore, expertise does not protect against bias; it can sometimes increase it. Experienced experts develop strong top-down cognitive processes (expectations, "chunking" information) that can make them more susceptible to overlooking contradictory evidence. The solution is not just experience, but structured systems and protocols designed to mitigate bias [44].
Q3: Our lab is accredited to ISO/IEC 17025. Does this protect us from cognitive bias?
ISO/IEC 17025 provides a crucial framework for quality and technical competence, but it is not a complete shield against cognitive bias [31]. The standard mandates impartiality and addresses some systemic risks, but its primary focus is on procedural and technical accuracy. A truly robust system integrates specific, bias-aware practices—like Blind Verification and LSU-E—within the ISO/IEC 17025 quality management system to address the hidden influences of cognitive bias directly [12] [44].
Q4: What quantitative metrics should we use to validate the alignment between judgmental and statistical equating methods?
When benchmarking judgmental methods like CJ against statistical equating, monitor the following key metrics derived from validation studies [72] [74].
| Metric | What It Measures | Benchmark for Close Alignment |
|---|---|---|
| AUROC (Area Under ROC Curve) Difference | Discrimination accuracy between methods. | ≤ 0.02 - 0.03 difference [74]. |
| Calibration-in-the-Large Difference | Overall agreement in score scaling. | ≤ 0.08 error [74]. |
| Scaled Brier Score Difference | Overall predictive accuracy. | ≤ 0.07 error [74]. |
| Judgment Bias Effect Size | Tendency to underscore harder tests/forms. | Not statistically significant; minimal systematic drift [72]. |
The Scientist's Toolkit: Key Research Reagents & Materials
| Item | Function in Validation Research |
|---|---|
| IRT (Item Response Theory) Models | Provides a robust statistical benchmark for estimating test and item difficulty, against which judgmental methods can be evaluated for accuracy [72]. |
| Common Anchor Items | Sets of questions embedded across different test forms to provide a direct statistical link for equating and validating judgmental outcomes [72] [73]. |
| Linear Sequential Unmasking-Expanded (LSU-E) | A procedural "reagent" used to minimize cognitive bias by controlling the sequence and timing of information disclosure to analysts [12] [44]. |
| Electronic Lab Notebook (ELN) / LIMS | Software systems critical for maintaining an immutable audit trail, managing data, and ensuring the integrity of the evidence chain-of-custody throughout the research process [31] [75]. |
| Blind Verification Protocol | A mandatory control step where a second analyst, unaware of initial results or context, independently verifies findings to confirm objectivity [12]. |
Troubleshooting Guides and FAQs
Q1: The text in my automated workflow diagram has low contrast and is difficult to read. How can I fix this to ensure accessibility and clarity?
A: Ensure the contrast ratio between text and its background meets WCAG guidelines. For standard text, the ratio should be at least 4.5:1; for large-scale text (approximately 18pt or 14pt bold), it should be at least 3:1 [76]. For nodes in diagrams, explicitly set the fontcolor and fillcolor attributes to colors from a high-contrast palette. Avoid using the same or similar colors for foreground and background elements. Automated color calculation is possible but must account for perceived lightness (luma) to be accurate [77].
Q2: My experimental protocol diagram has nodes of different sizes, making the layout look unbalanced. How can I standardize the node sizes?
A: To ensure consistent node dimensions, use the width and height attributes, or set fixedsize=true in Graphviz. For text-containing nodes, the shape=plain option can be useful, as it sets the node's size to be entirely determined by the label, effectively setting width=0 height=0 margin=0 [78].
Q3: When I apply a fill color to a node in my diagram, the text disappears. What is causing this?
A: This occurs when the text color is not explicitly set and defaults to a color that matches the node's fill. Always explicitly define the fontcolor attribute for any node that has a fillcolor to ensure high contrast and visibility [79] [80].
The following table summarizes key quantitative thresholds for color contrast and text size as defined by WCAG 2.2 Level AA guidelines [76].
| Criterion | Minimum Threshold | Notes |
|---|---|---|
| Contrast Ratio (Standard Text) | 4.5:1 | Absolute minimum; 4.49:1 fails. |
| Contrast Ratio (Large Text) | 3:1 | Large text is approx. 18pt (24px) or 14pt (18.66px) bold. |
| Font Weight (Bold) | 700 | CSS value for 'bold'; no discretion for lower values. |
Experimental Protocol: Validating Color Contrast in Scientific Visualizations
Objective: To empirically verify that all elements in a scientific workflow diagram meet accessibility contrast standards, mitigating visual bias in data interpretation.
Materials:
- Workflow diagrams (e.g., in Graphviz DOT format)
- Color contrast analyzer tool (e.g., automated checker based on WCAG formulas)
- The specified color palette
Methodology:
- Diagram Generation: Create the workflow diagram using the DOT language, explicitly defining
fillcolorandfontcolorfor all nodes andcolorfor edges [78]. - Contrast Calculation: For each text-on-background pair (node labels, edge labels), calculate the contrast ratio using the sRGB Luma method: L = (red × 0.2126 + green × 0.7152 + blue × 0.0722) / 255 [77].
- Threshold Validation: Compare the calculated ratio against the required thresholds (see Quantitative Data Table). Any value below the threshold constitutes a failure.
- Iterative Correction: Adjust colors in the diagram source code and re-validate until all elements pass. Automated scripts can be implemented to perform this validation during the diagram generation process.
Diagram Specifications and Visualizations
The following diagrams were generated with strict adherence to the color contrast and style rules.
Automated Forensic Workflow

Bias Mitigation Protocol

The Scientist's Toolkit: Research Reagent Solutions
The following table details essential digital materials and their functions for creating robust, unbiased visual experimental protocols.
| Research Reagent | Function in Experimental Setup |
|---|---|
| Graphviz DOT Language | Defines the structure and layout of complex workflow diagrams programmatically, ensuring consistency and reproducibility. |
| WCAG 2.2 Contrast Guidelines | Provides the quantitative standard for verifying that visual information is accessible to all users, reducing interpretive bias. |
| sRGB Luma Formula | Calculates the perceived brightness of a color, which is critical for implementing automated contrast checks in scripts and tools. |
| High-Contrast Color Palette | A pre-defined set of colors (e.g., blues, reds, greens, yellows, grays, white) guaranteed to work together while maintaining legibility. |
Conclusion
Mitigating contextual bias in forensic science requires a fundamental shift from relying on individual expertise to implementing structured, systematic safeguards. The integration of frameworks like Linear Sequential Unmasking-Expanded (LSU-E) with robust quality management systems such as ISO/IEC 17025 provides laboratories with practical tools to enhance methodological rigor and decision transparency. Successful implementation depends on addressing both technical protocols and human factors—specifically overcoming the expert fallacies that prevent acknowledgment of bias vulnerability. As forensic evidence continues to evolve with technological advances, maintaining scientific integrity demands ongoing validation of bias mitigation strategies through empirical research, cross-disciplinary collaboration, and standardized performance metrics. The future of reliable forensic science lies in creating laboratory ecosystems where structured bias mitigation is embedded in every workflow, ultimately strengthening the credibility and scientific foundation of evidence presented in judicial systems worldwide.
References
- 1. Contextual bias on decision-making in forensic toxicology [https://www.sciencedirect.com/science/article/abs/pii/S0379073822000627]
- 2. Confirmation Forensic ( Bias Forensics) Cognitive Bias in [https://www.news-medical.net/life-sciences/Forensic-Confirmation-Bias-(Cognitive-Bias-in-Forensics).aspx]
- 3. Reducing the impact of cognitive decision making: Practical... bias in [https://pmc.ncbi.nlm.nih.gov/articles/PMC10319185/]
- 4. A practical approach to mitigating cognitive bias effects in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11720873/]
- 5. A Forensic Science-Based Model for Identifying and ... [https://jaapl.org/content/early/2025/05/05/JAAPL.250019-25]
- 6. Contextual bias on decision-making in forensic toxicology [https://pubmed.ncbi.nlm.nih.gov/35176676/]
- 7. Reducing the impact of cognitive bias in decision making [https://www.sciencedirect.com/science/article/pii/S2589871X23000281]
- 8. System 1 and System 2 Thinking [https://thedecisionlab.com/reference-guide/philosophy/system-1-and-system-2-thinking]
- 9. Reducing Bias with Cognitive Psychology [https://theforensicpractice.com/reducing-bias-with-cognitive-psychology/]
- 10. Recognizing and reducing cognitive bias in clinical and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5762024/]
- 11. Identifying and Mitigating Potential Biases in Predicting ... [https://pubmed.ncbi.nlm.nih.gov/35579815/]
- 12. A practical approach to mitigating cognitive bias effects in ... [https://www.sciencedirect.com/science/article/pii/S2589871X24001165]
- 13. Developing Effective Methods for Addressing Contextual Bias ... [https://nij.ojp.gov/library/publications/developing-effective-methods-addressing-contextual-bias-forensic-science]
- 14. Minimizing Cognitive Bias in Forensic Document ... [https://journal.asqde.org/articles/10.69525/jasqde.230]
- 15. Cognitive bias research in forensic science: A systematic ... [https://www.sciencedirect.com/science/article/pii/S0379073818304559]
- 16. When the Evidence Lies: Understanding Contamination ... [https://jenniferdornbush.com/when-the-evidence-lies-understanding-contamination-and-misinterpretation-in-forensics/]
- 17. Evaluating bias in forensic evidence: From expert analysis to ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12639291/]
- 18. Errors in toxicology testing and the need for full discovery - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC12284658/]
- 19. A Forensic Science-Based Model for Identifying and ... [https://jaapl.org/content/53/2/172]
- 20. Cognitive and Human Factors in Expert Decision Making [https://pubmed.ncbi.nlm.nih.gov/32508089/]
- 21. Cognitive and Human Factors in Expert Decision Making [https://safetyinsights.org/2023/10/09/cognitive-and-human-factors-in-expert-decision-making-six-fallacies-and-the-eight-sources-of-bias/]
- 22. Bias, Preconceptions, and Logical Fallacies - Finding Reliable ... [https://library.daytonastate.edu/reliable/logicalfallacies]
- 23. 15 Cognitive Errors Every Analyst Must Know [https://towardsdatascience.com/15-cognitive-errors-every-analyst-must-know-268540e34ade/]
- 24. Costa Rica: Department of Forensic Sciences Publishes ... [https://www.justice.gov/archives/criminal/criminal-icitap/blog/costa-rica-department-forensic-sciences-publishes-scientific-article-mitigating-bias]
- 25. A practical approach to mitigating cognitive bias effects in ... [https://pubmed.ncbi.nlm.nih.gov/39802316/]
- 26. Bias Mitigation Strategies and Techniques for ... [https://www.holisticai.com/blog/bias-mitigation-strategies-techniques-for-classification-tasks]
- 27. Feature-Wise Mixing for Mitigating Contextual Bias in ... [https://arxiv.org/abs/2506.23033]
- 28. A guideline for reporting experimental protocols in life sciences [https://pmc.ncbi.nlm.nih.gov/articles/PMC5978404/]
- 29. Linear Sequential Unmasking–Expanded (LSU-E) [https://pmc.ncbi.nlm.nih.gov/articles/PMC8385162/]
- 30. Using Linear Sequential Unmasking-Expanded (LSU-E) in ... [https://forensicstats.org/blog/portfolio/a-practical-tool-for-information-management-in-forensic-decisions-using-linear-sequential-unmasking-expanded-lsu-e-in-casework/]
- 31. Forensic Labs in the Age of Digital and Biological Evidence [https://www.labmanager.com/forensic-labs-in-the-age-of-digital-and-biological-evidence-34471]
- 32. Bias recognition and mitigation strategies in artificial ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11897215/]
- 33. Fraud Tip Friday—Navigating Cognitive Bias in Forensic ... [https://www.linkedin.com/pulse/fraud-tip-fridaynavigating-cognitive-bias-forensic-marks-cpa-mba-rr4xe]
- 34. The Most Common Types of Bias in a Human Bitemark ... [https://www.mdpi.com/2673-6373/4/1/10]
- 35. Identifying and mitigating algorithmic bias in the safety net [https://www.nature.com/articles/s41746-025-01732-w]
- 36. Post-processing methods for mitigating algorithmic bias in ... [https://bmcdigitalhealth.biomedcentral.com/articles/10.1186/s44247-025-00166-4]
- 37. Mitigating Bias in AI Models: A New Approach with TAB [https://ai.sony/blog/Mitigating-Bias-in-AI-Models-A-New-Approach-with-TAB/]
- 38. ISO 17025 Compliance Guide 2026: Requirements, ... [https://www.scispot.com/blog/iso-17025-compliance-guide-requirements-software-best-practices]
- 39. 10 Steps Toward Achieving ISO/IEC 17025 Accreditation [https://a2la.org/10-steps-toward-achieving-iso-iec-17025-accreditation/]
- 40. ISO/IEC 17025 - ANAB - American National Standards Institute [https://anab.ansi.org/standard/iso-iec-17025/?srsltid=AfmBOoqFa8UcybqOQl6XvNBnS4w1QQowwWRlMDB79ZaeWuf-fQ-6nyrV]
- 41. 2025 FBI Quality Assurance Standards [https://a2la.org/2025-fbi-quality-assurance-standards/]
- 42. ISO/IEC 17025 Forensic Testing Laboratory Accreditation [https://anab.ansi.org/accreditation/iso-iec-17025-forensic-testing-laboratory/?srsltid=AfmBOorjZA3ElorjLgHd7E-i3tLFAglHRJcxCnyAVC6aLLvDThnF8WWx]
- 43. OSAC Standards Bulletin - January 2025 | NIST [https://www.nist.gov/magazine/osac-standards-bulletin/january-2025]
- 44. The Hidden Bias Cascade and Bias Snowball Effects - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC12024198/]
- 45. Protocols for STR Analysis Manuals - OCME [https://www.nyc.gov/site/ocme/services/fbio-2025-protocols-for-str-analysis-manuals.page]
- 46. Digital Evidence Management Challenges in 2025 and Smart ... [https://digitalevidence.ai/blog/digital-evidence-management-challenges-in-2025-and-smart-solutions]
- 47. Key Trends in Digital Forensics 2025: Chanllenges and ... [https://www.salvationdata.com/knowledge/key-trends-in-digital-forensics-for-2025/]
- 48. Advancing predictive toxicology: overcoming hurdles and ... [https://pubs.rsc.org/en/content/articlehtml/2025/dd/d4dd00257a]
- 49. 2025 Society of Toxicology Satellite Meeting [https://www.epa.gov/chemical-research/new-approach-methods-training-2025-society-toxicology-satellite-meeting]
- 50. Forensic Bias Training and Expert Testimony [https://www.cci-hq.com/forensic-identification.html]
- 51. Cognitive Bias in Forensic Analyses - CSAFE Learning [https://learn.forensicstats.org/product?catalog=WB231024]
- 52. Cultural and Structural Impediments to Forensic Science ... [https://houstonlawreview.org/article/12193-roadblocks-cultural-and-structural-impediments-to-forensic-science-reform]
- 53. A cultural change to enable improved decision-making in ... [https://www.sciencedirect.com/science/article/abs/pii/S1355030619300218]
- 54. Raman spectroscopy and machine learning for forensic ... [https://pubs.rsc.org/en/content/articlelanding/2025/an/d4an01529k]
- 55. Exploring Biodigital Convergence: What happens when ... [https://horizons.service.canada.ca/en/2020/02/11/exploring-biodigital-convergence/index.shtml]
- 56. How to be a Better Troubleshooter in Your Laboratory [https://www.goldbio.com/blogs/articles/how-to-be-a-better-troubleshooter?srsltid=AfmBOorUiPizQ8GOurPqFvA18xRSAw3kQkgPfvZO7R1jAw_ll6MyAU_u]
- 57. Teaching troubleshooting skills to graduate students - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC11407763/]
- 58. AI Blindspot: A Discovery Process for preventing, detecting ... [https://aiblindspot.media.mit.edu/]
- 59. Fighting for objectivity: Cognitive bias in forensic ... [https://paloaltou.edu/resources/translating-research-into-practice-blog/fighting-objectivity-cognitive-bias-forensic-examinations/]
- 60. Mitigating bias in performance management [https://www.deloitte.com/us/en/insights/topics/talent/mitigating-bias-in-performance-management.html]
- 61. Assessing Cognitive Bias, Method Validation, and ... [https://www.ojp.gov/library/publications/assessing-cognitive-bias-method-validation-and-equipment-performance-forensic]
- 62. Best Practices for Continuous Improvement in Quality ... [https://oxford-management.com/articles/best-practices-for-continuous-improvement-in-quality-systems]
- 63. 9 Continuous Improvement Methodologies & Tools [https://www.viima.com/blog/continuous-improvement-tools]
- 64. Cognitive Bias Affects Perception and Decision-Making in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12383771/]
- 65. What Works and What Doesn't – Bias Awareness and ... [https://paloaltou.edu/resources/translating-research-into-practice-blog/works-doesnt-bias-awareness-correction-strategies-among-forensic-evaluators/]
- 66. Bias in Forensic Mental Health Evaluations [https://paloaltou.edu/resources/translating-research-into-practice-blog/bias-in-forensic-mental-health-evaluations/]
- 67. AI trends 2025: Adoption barriers and updated predictions [https://www.deloitte.com/us/en/services/consulting/blogs/ai-adoption-challenges-ai-trends.html]
- 68. An Ounce of Prevention: A Simple and Practical Tool ... [https://forensicstats.org/blog/portfolio/an-ounce-of-prevention-a-simple-and-practical-tool-for-mitigating-cognitive-bias-in-forensic-decisions/]
- 69. Bias Mitigation Agent: Optimizing Source Selection for Fair ... [https://arxiv.org/html/2508.18724v1]
- 70. How debunking biases in research and development ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11252826/]
- 71. The Hidden Pitfalls of Unconscious Bias in Drug Development [https://www.alacrita.com/blog/the-hidden-pitfalls-of-unconscious-bias-in-drug-development]
- 72. Evaluating accuracy and bias of different comparative ... [https://www.frontiersin.org/journals/education/articles/10.3389/feduc.2025.1538486/full]
- 73. Test Equating For Fair Score Comparisons (2025) [https://www.cogn-iq.org/blog/equating-different-tests-or-different-versions/]
- 74. Extensive benchmarking of a method that estimates ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11772677/]
- 75. Top 8 SciNote Functionalities for Forensic Science Labs [https://www.scinote.net/blog/forensic-science-labs/]
- 76. Contrast requirements for WCAG 2.2 Level AA [https://www.makethingsaccessible.com/guides/contrast-requirements-for-wcag-2-2-level-aa/]
- 77. Switch font color for different backgrounds with CSS [https://css-tricks.com/switch-font-color-for-different-backgrounds-with-css/]
- 78. Node Shapes [https://graphviz.org/doc/info/shapes.html]
- 79. tikzstyle default node text with fill color [https://tex.stackexchange.com/questions/48918/tikzstyle-default-node-text-with-fill-color]
- 80. Issue: Black text in colored task - Discussion & Questions [https://forum.camunda.io/t/issue-black-text-in-colored-task/4702]