Resolving Cognitive Bias in Forensic Linguistic Analysis: Frameworks, Methods, and Validation Strategies
This article provides a comprehensive framework for understanding and mitigating cognitive bias in forensic linguistic analysis.
Resolving Cognitive Bias in Forensic Linguistic Analysis: Frameworks, Methods, and Validation Strategies
Abstract
This article provides a comprehensive framework for understanding and mitigating cognitive bias in forensic linguistic analysis. Drawing on established research from forensic science and cognitive psychology, we explore how biases such as confirmation bias and contextual bias can compromise linguistic evidence evaluation. The content covers foundational concepts, practical methodological safeguards like Linear Sequential Unmasking, troubleshooting for common challenges, and validation approaches through comparative analysis. Designed for forensic researchers, practitioners, and legal professionals, this guide offers evidence-based strategies to enhance objectivity and reliability in forensic linguistic examinations.
The Hidden Influencer: Understanding Cognitive Bias in Forensic Linguistics
Frequently Asked Questions
What is a standard definition of cognitive bias that I can use in my research protocol? Cognitive bias is defined as a systematic error in judgment and a naturally occurring tendency that skews information processes. This occurs due to limitations in cognitive, motivational, or environmental factors, leading to sub-optimal or fundamentally wrong outcomes [1].
What is a concrete example of a cognitive bias I might encounter during data analysis? A common and well-researched example is belief bias. This is the systematic tendency to evaluate the validity of a syllogism or argument based on the credibility of its conclusion rather than its logical structure [2]. For instance, a researcher might incorrectly judge an analysis as valid simply because its conclusion aligns with their pre-existing hypothesis, overlooking flaws in the analytical method.
How can I reduce the influence of belief bias in my research team's analytical work? Instead of solely relying on training analytical skills, evidence suggests that reframing the task instruction can be highly effective. Clearly instructing team members to evaluate the logical structure of an analysis, independent of their belief in the conclusion, can trigger more analytical thinking and improve accuracy [2].
My forensic linguistics research involves both manual analysis and automated tools. How does cognitive bias present differently in these methodologies? Machine Learning (ML) algorithms, such as deep learning and computational stylometry, excel at processing large datasets rapidly and identifying subtle linguistic patterns, thus potentially reducing certain human biases related to fatigue or oversight. For example, ML models have shown a 34% increase in accuracy for authorship attribution tasks. However, manual analysis retains superiority in interpreting cultural nuances and contextual subtleties, areas where an over-reliance on automated systems could introduce new forms of algorithmic bias if the training data is flawed [3].
What are the key ethical challenges and biases associated with using Machine Learning in forensic linguistics? Key challenges include algorithmic bias from unrepresentative training data and opaque decision-making ("black box" algorithms) that can hinder courtroom admissibility and ethical justice. Mitigation strategies involve developing standardized validation protocols and creating hybrid frameworks that merge human expertise with computational power to provide oversight [3].
Troubleshooting Guides
Problem: Low inter-coder reliability in qualitative linguistic analysis.
- Potential Cause: Coder contamination due to confirmation bias, where analysts unconsciously seek out or interpret data to confirm pre-existing beliefs.
- Solution:
- Blind Coding: Implement a double-blind protocol where coders are unaware of the study's hypotheses.
- Clear Codebook: Develop a highly explicit codebook with clear, objective criteria for each linguistic feature.
- Independent Coding: Have multiple researchers code the same data set independently.
- Statistical Comparison: Use statistical tests (e.g., Cohen's Kappa) to measure and improve agreement before resolving discrepancies.
Problem: An ML tool for authorship attribution performs poorly on a new, unseen dataset.
- Potential Cause: Algorithmic bias stemming from a mismatch between the training data and the target data (e.g., different genres, time periods, or demographics).
- Solution:
- Data Audit: Systematically analyze the model's training data for representativeness.
- Feature Engineering: Re-evaluate and adjust the linguistic features (e.g., n-grams, syntactic markers) to be more domain-appropriate.
- Hybrid Validation: Use manual analysis by a domain expert on a subset of the results to validate the ML output and identify failure patterns [3].
- Model Retraining: Fine-tune or retrain the model with a balanced and relevant dataset.
Problem: Experimental participants in a spoken conversational search (SCS) study are swayed by the order of information.
- Potential Cause: Position Effect, a type of cognitive bias where earlier or later presented information has a disproportionate influence.
- Solution:
- Counterbalancing: Systematically vary the order of information presentation across participant groups.
- Signal Monitoring: Use multimodal sensors (e.g., EEG) to detect cognitive load and engagement as potential indicators of bias, moving beyond traditional web logs which offer less granular data [1].
- Instructional Set: Frame the task to emphasize the need for evaluating all information equally [2].
Quantitative Data in Forensic Linguistics
The table below summarizes core findings on the performance of manual versus machine-learning methods in forensic linguistics, based on a synthesis of 77 studies [3].
| Metric | Manual Analysis | ML-Driven Analysis | Notes |
|---|---|---|---|
| Authorship Attribution Accuracy | Baseline | +34% increase (vs. baseline) | Achieved by models like deep learning & computational stylometry [3] |
| Processing Speed for Large Datasets | Slow | Rapid | ML excels at scale, manual is time-consuming [3] |
| Interpretation of Cultural Nuances | Superior | Limited | Human expertise is critical for contextual subtlety [3] |
| Reliability & Consistency | Prone to subjective bias | High, if trained on unbiased data | Susceptible to algorithmic bias from flawed training data [3] |
Experimental Protocols
Protocol 1: Mitigating Belief Bias in Analytical Tasks This protocol is adapted from psychological research on deductive reasoning for use in research and data review meetings [2].
- Task: Use syllogisms or analytical problems with a structure that pits logical validity against believability (e.g., "All flowers need water. All roses need water. Therefore, all roses are flowers." This is invalid but believable).
- Control Group Instruction: "Read the following analysis and indicate if you think the conclusion is correct."
- Experimental Group Instruction: "Read the following analysis. Your task is to determine if the conclusion follows logically from the premises, regardless of whether you believe the conclusion is true in the real world."
- Measurement: Compare the accuracy of logical validity judgments between the two groups. The experimental group is expected to show significantly higher accuracy in identifying logical validity, demonstrating a reduction in belief bias.
Protocol 2: A Multimodal Approach to Detect Bias in Spoken Conversational Search (SCS) This protocol proposes using physiological signals to detect cognitive bias in audio-only information seeking, where traditional web logs are insufficient [1].
- Setup: Participants interact with an SCS system to research a controversial topic with multiple viewpoints via voice only.
- Signal Acquisition:
- EEG (Electroencephalogram): To measure neural activity associated with cognitive load and conflict detection.
- Electrodermal Activity (EDA): To measure arousal, potentially indicating emotional response to challenging information.
- Post-Session Assessment: Participants report their final stance on the topic and answer comprehension questions.
- Data Fusion & Analysis: Correlate physiological signal patterns (e.g., specific EEG signatures) with the acceptance or rejection of information that contradicts a participant's initial stance, indicating potential confirmation bias.
The Scientist's Toolkit: Essential Research Reagents & Materials
| Item | Function in Research |
|---|---|
| Computational Stylometry Software | Quantifies an author's unique writing style through features like vocabulary richness, syntax, and character-level n-grams for authorship attribution [3]. |
| Deductive Reasoning Task Battery | A set of validated syllogisms (e.g., Valid-Unbelievable, Invalid-Believable) to measure and induce belief bias in experimental settings [2]. |
| EEG Headset with High Temporal Resolution | Captures millisecond-scale neural activity to study the timing of cognitive processes like conflict detection during biased decision-making [1]. |
| Hybrid Analysis Framework | A structured protocol that integrates both manual linguistic expertise and ML-driven analysis to leverage the strengths and mitigate the weaknesses of each approach [3]. |
| Standardized Validation Protocol | A set of procedures for testing the fairness, accuracy, and potential biases of ML models before they are deployed in critical forensic or research applications [3]. |
Experimental Workflow for Bias Detection
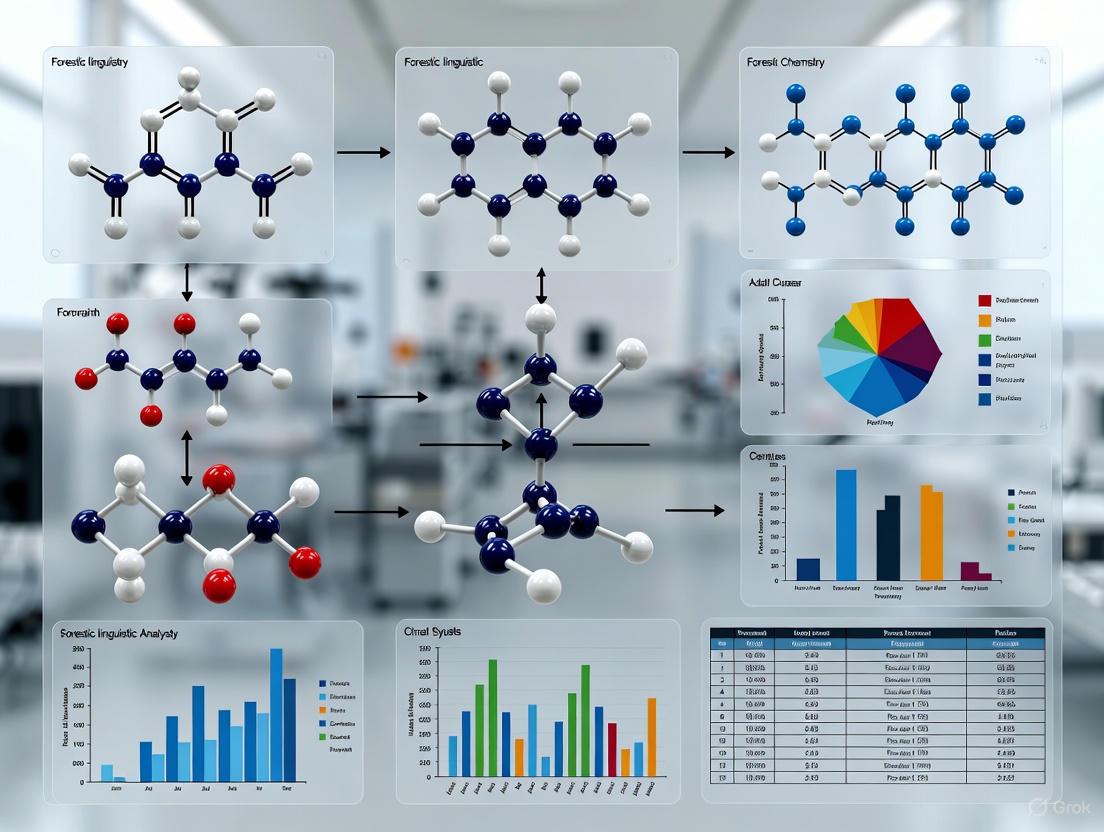
The following diagram illustrates a multimodal experimental setup for detecting cognitive bias in spoken conversational search research.
Troubleshooting Guide: Identifying and Resolving Expert Bias in Forensic Linguistics
This guide helps researchers identify and mitigate cognitive biases in forensic linguistic analysis, a critical step for ensuring valid and reliable research outcomes.
Q1: How can I determine if my linguistic analysis has been influenced by confirmation bias?
A: Confirmation bias, the tendency to search for or interpret evidence in ways that confirm one's preconceptions, can be identified and mitigated through the following protocol [4]:
Experimental Protocol for Identification:
- Blinded Re-analysis: Have a colleague not involved in the original hypothesis re-analyze the linguistic data (e.g., anonymized text corpora) without access to your initial conclusions. Compare the independent findings for discrepancies [4].
- Hypothesis Testing: Actively generate and test alternative hypotheses for the linguistic patterns you observe. For instance, if you hypothesize that a specific syntactic structure indicates deception, also test if it could be explained by the author's educational background or dialect [4].
- Linear Sequential Unmasking-Expanded (LSU-E): Structure your analysis so that all initial data examination is done without any contextual, domain-irrelevant information (e.g., the suspect's criminal history). Only after forming an initial, blinded assessment should contextual information be introduced and its impact on your conclusions be explicitly documented [4].
Mitigation Strategy: Implement a structured analytical framework that requires documenting all evidence, including items that do not support your primary hypothesis. This creates an audit trail and forces consideration of disconfirming evidence [4].
Q2: My team disagrees on the interpretation of a stylometric analysis. How can we resolve this without groupthink?
A: Interpretation disagreements often stem from cognitive biases like "myside bias" or the "bias blind spot," where experts perceive others, but not themselves, as vulnerable to bias [4] [5] [6].
- Experimental Protocol for Resolution:
- Structured Devil's Advocate: Formally assign a team member to challenge the majority opinion. This person's role is to actively find flaws in the reasoning and present counter-arguments based on the data [4].
- Diagnostic Tool: Use the table below to diagnose which expert fallacy may be affecting your team's judgment. Addressing the specific fallacy can break the deadlock.
| Expert Fallacy | Description | Symptom in Linguistic Analysis | Mitigation Strategy |
|---|---|---|---|
| Ethical Immunity [4] [5] [6] | Belief that only unethical or incompetent experts are biased. | Dismissing the possibility of bias because the team is composed of ethical, seasoned professionals. | Foster a culture where discussing bias is a normative part of scientific rigor, not an accusation of misconduct [4]. |
| Expert Immunity [4] [5] [6] | Assumption that one's own expertise provides a shield against bias. | Dismissing alternative interpretations from less senior researchers without consideration. | Implement mandatory peer review of all analytical conclusions before they are finalized [4]. |
| Technological Protection [4] [5] | Over-reliance on tools (e.g., ML algorithms) to eliminate bias. | Assuming that because a computational stylometry model produced a result, it must be objective, ignoring potential biases in its training data [3]. | Critically evaluate the normative data and algorithmic design of tools. Use them as aids, not arbiters of truth [3]. |
| Bias Blind Spot [4] [5] [6] | The tendency to see cognitive biases in others but not in oneself. | A team member readily points out others' biases but cannot see how their own theoretical leanings shape their analysis. | Use self-assessment checklists that force explicit consideration of biasing influences at each stage of the analysis [4]. |
| Illusion of Control [5] [6] | Belief that mere awareness of bias is sufficient to control it. | A researcher states, "I know about these biases, so I can avoid them," without using any structured mitigation strategies. | Mandate the use of external, structured strategies like LSU-E rather than relying on self-vigilance [4]. |
Q3: Our machine learning model for authorship attribution performs well on test data but seems to fail on specific demographic groups. What could be causing this?
A: This is a classic sign of algorithmic bias, often stemming from the fallacy of technological protection [4] [3]. The model is not immune to bias simply because it is technological.
- Experimental Protocol for Diagnosis and Mitigation:
- Audit Training Data: Systematically analyze the demographic composition and representativeness of your training corpora. Quantitative data shows that ML models can outperform manual analysis in speed and pattern recognition (e.g., authorship attribution accuracy increased by 34% in ML models), but this performance is contingent on the quality and breadth of the training data [3].
- Benchmark Performance: Create a balanced test dataset that represents all relevant demographic groups. Compare the model's accuracy, precision, and recall across these groups. A significant performance disparity indicates a bias problem [3].
- Hybrid Validation: Do not rely solely on the algorithm. Integrate human expertise to review the model's outputs, particularly for cases involving demographic groups where the model's performance is weaker. Manual analysis retains superiority in interpreting cultural nuances and contextual subtleties [3].
The Scientist's Toolkit: Research Reagent Solutions for Bias-Resistant Linguistics
The following table details essential methodological "reagents" for conducting robust forensic linguistic research.
| Research Reagent | Function & Explanation |
|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) [4] | A methodological protocol that controls the flow of information to the analyst, preventing contextual information from biasing the initial examination of the core linguistic data. |
| Blinded Peer Review Protocol | A structured process for independent verification of findings by an analyst who is blinded to the original hypothesis and potentially biasing contextual information. |
| Alternative Hypothesis Checklist | A pre-defined list of competing explanations that the researcher must actively rule out with evidence, combating confirmation bias [4]. |
| Bias Self-Assessment Inventory | A checklist based on the Six Expert Fallacies and eight sources of bias that researchers complete at key stages of their analysis to prompt metacognition [4] [5]. |
| Hybrid Human-AI Analysis Framework [3] | A structured workflow that leverages the scalability of ML algorithms for data processing while reserving final interpretation of nuanced or high-stakes conclusions for human experts. |
Experimental Workflow for Bias-Aware Linguistic Analysis
The following diagram illustrates a robust experimental workflow that integrates bias mitigation strategies directly into the forensic linguistic research process.
Frequently Asked Questions (FAQs) on Expert Bias
Q: As an ethical researcher, am I not already immune to these biases? A: No. This belief is the first of the six expert fallacies. Cognitive bias is a function of human neurocognition, not character. Even the most ethical practitioners are vulnerable to unconscious biases that can skew data collection and interpretation [4] [5] [6].
Q: If I use a validated, statistical risk-assessment tool or a proven ML algorithm, doesn't that remove bias? A: No, this is the fallacy of technological protection. These tools can reduce certain subjective biases but introduce others. Algorithms can be biased by their training data, leading to skewed results against underrepresented groups. The output of any tool must be interpreted critically, not as objective fact [4] [3].
Q: I am aware of these bias concepts. Isn't that enough to prevent them in my work? A: No. This is known as the "Illusion of Control." Self-awareness alone is insufficient because these biases operate unconsciously. Mitigating their impact requires the consistent use of external, structured strategies like Linear Sequential Unmasking and blind peer review, not just willpower [4] [5] [6].
Q: Can biased language in my research notes or team handoffs really impact the outcome? A: Yes. Studies show that exposure to negatively biased language about a subject (e.g., using stereotypes or blame) can reduce a listener's empathy and impair their recall of critical factual details. Using neutral, objective language in all documentation and communications is crucial for maintaining analytical accuracy [7].
Welcome to the Technical Support Center for Forensic Linguistic Analysis. This resource is designed to assist researchers and professionals in identifying, troubleshooting, and mitigating the effects of contextual and automation bias in their evaluation of linguistic evidence. Cognitive bias presents a significant challenge to the objectivity of forensic sciences, including those dealing with complex, subjective data such as language. The following guides and protocols are framed within the broader thesis that resolving cognitive bias requires structured, external mitigation strategies, as self-awareness alone is insufficient [8].
Troubleshooting Guides: Identifying and Resolving Bias
Guide: Suspected Contextual Bias in Data Interpretation
Problem: An initial case hypothesis is unintentionally steering the interpretation of ambiguous linguistic data.
Background: Contextual bias occurs when extraneous information (e.g., a suspect's confession, other evidence in the case) inappropriately influences an expert's judgment [9]. This is a systemic issue, not a reflection of ethics or competence, and operates largely outside of conscious awareness [10] [8].
Solution: Implement Linear Sequential Unmasking-Expanded (LSU-E) protocols.
Step-by-Step Resolution:
- Isolate the Evidence: Analyze the linguistic evidence (e.g., an anonymous threat letter) first, before exposure to any biasing contextual information [10] [11].
- Document Initial Findings: Form and document a preliminary assessment based solely on the linguistic data. Clearly record the bases for these analytical decisions [10].
- Reveal Context Sequentially: Introduce task-relevant contextual information only after the initial analysis is complete. Document what information was received and when [10] [12].
- Re-evaluate with Transparency: Reconsider the initial findings in light of the new information. The process should emphasize transparency regarding any changes in interpretation and the reasons for them [10].
Guide: Suspected Automation Bias in Software-Assisted Analysis
Problem: Over-reliance on the output of automated forensic linguistics tools (e.g., authorship attribution software, sentiment analysis algorithms).
Background: Automation bias occurs when a human examiner is overly reliant on metrics generated by technology, allowing the tool to usurp rather than supplement their expert judgment [9] [13]. All software can have "bugs" or be trained on biased datasets, leading to inaccurate or unfair outcomes [13].
Solution: Adopt a "decision support" rather than "decision replacement" mindset.
Step-by-Step Resolution:
- Audit the Tool: Inquire about the training data and validation standards of the software being used. Tools must be tested on diverse datasets to identify and correct for inherent biases [12] [13].
- Conduct a Blind Verification: Have a second linguist, who is blinded to the first analyst's results and the software's output, conduct an independent analysis [11].
- Triangulate Findings: Treat the software's output as one data point among others. Compare it rigorously with the findings from the blind verification and your own independent analysis. Do not default to the algorithm's judgment without critical review [9].
- Document the Workflow: Record all steps, including the software used, its version, the settings applied, and how its output was weighted in the final conclusion [10] [13].
Frequently Asked Questions (FAQs)
Q1: As an experienced researcher, shouldn't my expertise protect me from these biases? A: No. The "expert immunity" fallacy is one of the most common and dangerous misconceptions. Paradoxically, expertise can sometimes increase vulnerability to bias because experts rely on cognitive shortcuts and pattern recognition, which can be influenced by expectations and context [8] [14].
Q2: If I use a validated, standardized method, am I protected from bias? A: Using validated methods is a crucial best practice, but it is not a complete shield. The "technological protection" fallacy suggests that tools or standardized protocols eliminate bias. While they reduce subjective noise, they can still be applied in a biased manner or contain inherent biases in their design [8]. Methods must be paired with bias-aware processes like LSU-E.
Q3: I've become aware that I was exposed to potentially biasing information mid-analysis. What should I do? A: The key is transparency and documentation. Immediately document what information you learned and when you learned it [10]. Consider pausing the analysis and, if possible, have a colleague who has not been exposed to that information take over or conduct a blind verification of your work to that point [11].
Q4: Are there specific linguistic domains where these biases are most critical? A: Yes, biases pose a significant threat in any subjective linguistic analysis. This includes:
- Authorship Attribution: Context about a suspect can bias the analysis of writing style [11] [8].
- Forensic Mental Health Evaluation: Diagnoses can be influenced by information about a defendant's race, gender, or criminal history [8].
- Academic Peer Review: Preliminary evidence suggests that an abstract's conformity to "native-like" English can influence reviewers' judgments of its scientific quality, even when the content is identical [15].
Experimental Protocols for Bias Detection
The following table summarizes key experimental methodologies for detecting and measuring contextual and automation bias in linguistic evidence evaluation.
Table 1: Experimental Protocols for Studying Bias in Linguistic Analysis
| Protocol Name | Key Methodology | Measured Outcome | Key Finding |
|---|---|---|---|
| Randomized Context Injection [9] | Participants analyze identical linguistic evidence (e.g., a text sample) randomly paired with different contextual details (e.g., "suspect has an alibi" vs. "suspect has a confession"). | The rate at which analysts' conclusions align with the implied hypothesis of the contextual information. | Extraneous information can cause experts to change their own prior judgments of the same evidence, demonstrating contextual bias. |
| Algorithmic Output Manipulation [9] [13] | Participants are given the output of a forensic linguistics tool (e.g., an authorship score) where the confidence score or suggested match is manipulated randomly. | The degree to which the human examiner's final judgment correlates with the manipulated software output versus their own independent analysis. | Examiners often defer to the algorithm's output even when it is incorrect, demonstrating automation bias. |
| Linguistic Bias in Peer Review [15] | Scholars rate the scientific quality of abstracts with identical content but written in "native-like" or "non-native-like" English. | The difference in scientific quality ratings between the two versions of the same abstract. | Preliminary evidence suggests abstracts written in non-native-like English receive lower ratings of scientific quality, indicating linguistic bias. |
The Scientist's Toolkit: Essential Research Reagents & Materials
Table 2: Key Reagents and Tools for Bias-Conscious Forensic Linguistics Research
| Item | Function/Explanation |
|---|---|
| Case Manager Model [11] | An organizational structure where a case manager filters information, providing analysts with only the data essential for their specific analytical task, thereby controlling the flow of biasing information. |
| Linear Sequential Unmasking-Expanded (LSU-E) [10] [8] | A structured protocol that controls the sequence and timing of information revelation to analysts, emphasizing documentation and minimizing premature exposure to biasing context. |
| Blind Verification Protocol [10] [11] | A quality control procedure where a second analyst, blinded to the first's findings and all extraneous context, independently analyzes the evidence to check for consistency and objectivity. |
| LSU-E Worksheet [10] | A practical tool to document the biasing power, objectivity, and relevance of information before it is disclosed to an analyst, facilitating the implementation of LSU-E. |
| Diverse Linguistic Corpora [12] [13] | Training and testing datasets that represent a wide variety of dialects, sociolects, and language backgrounds. These are essential for validating tools and methods to ensure they do not perpetuate systemic biases. |
Workflow Visualizations
Linear Sequential Unmasking-Expanded (LSU-E) Workflow
Cognitive Bias Mitigation Strategy Framework
In forensic linguistic analysis, the reliability of research conclusions is paramount. Cognitive biases—systematic errors in judgment—can significantly compromise the integrity of linguistic evidence. Drawing on Daniel Kahneman's dual-process theory, this technical support framework characterizes these biases as arising from an overreliance on System 1 thinking, which is fast, intuitive, and heuristic-driven. In contrast, System 2 thinking is slow, deliberate, and analytical [16] [17]. This guide provides researchers and drug development professionals with practical protocols to mitigate these biases, thereby enhancing the validity of forensic linguistic research, such as authorship attribution or threat assessment.
Troubleshooting Guides: Resolving Common Cognitive Biases
Troubleshooting Guide 1: Mitigating Order Bias in Analytical Results
- Issue or Problem Statement: Analytical outcomes or model preferences are inconsistently influenced by the order in which options, data, or linguistic features are presented, rather than their intrinsic merit [18].
- Symptoms or Error Indicators:
- An LLM or analysis tool preferentially selects the first option in a list.
- Inconsistent classification results when the same linguistic data is presented in a different sequence.
- Reproduction studies fail to replicate original findings due to undisclosed presentation orders.
- Root Cause: System 1 Heuristic - The cognitive ease of accepting initial information (primacy effect) without deliberate reevaluation of all options [18] [19].
- Step-by-Step Resolution Process:
- Acknowledge the Bias: Explicitly add a prompt or step in your protocol stating: "Be aware that the order of information may bias your judgment. Evaluate all options carefully regardless of their position" [18].
- Implement Systematic Rotation: For all multiple-choice tasks or feature evaluations, create multiple versions of your input where the order of options is randomized.
- Aggregate Results: Run your analysis or LLM query across all rotated versions. For example, if testing four options, run four analyses, each with a different option in the first position.
- Validate with Consensus: The final result should be based on the consensus or average output across all randomized trials, not a single run [18].
- Validation or Confirmation Step: The recommended outcome or classification remains stable and consistent across multiple, order-randomized tests.
Troubleshooting Guide 2: Correcting for Anchoring in Data Interpretation
- Issue or Problem Statement: Initial information, even if irrelevant, creates an "anchor" that unduly influences subsequent numerical estimates or linguistic judgments [18] [20].
- Symptoms or Error Indicators:
- Estimates of word frequency, authorship probability, or other metrics cluster around an initial, unverified value.
- Failure to sufficiently adjust estimates away from a starting point after receiving new, contradictory data.
- LLMs provide different answers to the same quantitative question based on a preceding, unrelated number in the prompt.
- Root Cause: System 1 Heuristic - The tendency to rely too heavily on the first piece of information offered when making decisions [18].
- Step-by-Step Resolution Process:
- Isolate the Core Question: Reformulate your query or analysis to remove any potentially biasing preliminary numbers or context.
- Employ a System 2 Protocol: Use chain-of-thought prompting with an LLM or a structured worksheet that forces step-by-step reasoning, documenting each calculation without reference to the anchor [16] [20].
- Consider the Opposite: Actively generate reasons why the initial anchor might be incorrect or misleading. Ask: "What evidence would support a different conclusion?"
- Use a Reasoning Model: For critical quantitative tasks, leverage a specialized reasoning LLM (e.g., OpenAI's o1, DeepSeek's R1) designed for deliberate, step-by-step analysis, which has been shown to be less susceptible to such biases [16] [20].
- Validation or Confirmation Step: The final estimate is logically derived from the primary data and is not disproportionately close to any irrelevant initial value presented in the scenario.
Troubleshooting Guide 3: Overcoming the Framing Effect in Hypothesis Testing
- Issue or Problem Statement: The way a linguistic hypothesis or data is framed (e.g., positive vs. negative wording) leads to different analytical conclusions, despite the underlying facts being identical [20].
- Symptoms or Error Indicators:
- A researcher is more likely to accept a hypothesis framed in terms of "accuracy" (e.g., 90% survival) than one framed in terms of "error" (e.g., 10% mortality) [20].
- LLMs make different recommendations based on logically equivalent but differently phrased prompts.
- Root Cause: System 1 Heuristic - Emotional and intuitive responses to how information is presented, rather than a logical analysis of the information itself.
- Step-by-Step Resolution Process:
- Reframe the Problem: Consciously restate the hypothesis or data in at least two logically equivalent ways (e.g., both positive and negative frames).
- Analyze All Frames: Conduct your analysis separately for each reframed version of the problem.
- Compare Outcomes: If the different frames lead to different conclusions, this signals the presence of the framing effect. This indicates a need for deeper, System 2 analysis.
- Base Decisions on Core Logic: Disregard the emotional valence of the frame and make the final judgment based on the underlying logical structure common to all reframed versions.
- Validation or Confirmation Step: The final research decision is consistent and justifiable across all equivalent framings of the hypothesis or data.
Frequently Asked Questions (FAQs)
FAQ 1: What is the practical difference between System 1 and System 2 AI models in a research context?
- System 1 AI (e.g., standard GPT-4) is your fast, pattern-matching tool. It excels at tasks like drafting content, summarizing documents, or initial data sorting based on trained heuristics. However, it does not validate its results and is highly susceptible to cognitive biases found in its training data [17]. System 2 AI (e.g., reasoning models like OpenAI's o1) is your slow, analytical partner. It uses techniques like chain-of-thought reasoning to work through multi-step problems, validate answers, and perform logic-heavy tasks, making it less prone to certain cognitive biases [16] [17] [20].
FAQ 2: Our team uses automated linguistic analysis. How can we be sure we are not just replacing human bias with algorithmic bias?
Algorithmic bias is a real risk, often stemming from biased training data or model architecture [3]. The solution is a hybrid framework [3]. Use the speed of System 1 AI (or human intuition) for initial hypothesis generation and data processing. Then, subject these findings to rigorous, System 2-style validation. This can involve using reasoning AI models for complex logic [20], implementing structured peer-review protocols that force deliberate reasoning, and maintaining final human oversight for interpreting cultural nuances and contextual subtleties that AI may miss [3].
FAQ 3: Are there any quantitative studies showing that System 2 reasoning actually reduces bias in analytical tasks?
Yes. A 2025 study evaluated the reasoning model "o1" on ten clinical decision-making scenarios designed to trigger known cognitive biases. The study found that the o1 model showed no measurable bias in 7 out of 10 scenarios, and in the cases where bias was present, its magnitude was generally lower than that observed in both standard GPT-4 and human clinicians [20]. This provides empirical support for the use of structured, step-by-step reasoning to mitigate irrational judgment.
FAQ 4: The "AwaRe" mitigation method is recommended, but how exactly is it implemented in a prompt?
The AwaRe (Awareness Reminder) method involves prefacing your prompt with a direct instruction that makes the AI aware of the potential for bias and encourages careful thinking. For example, when testing for order bias, your prompt could begin:
"You are an analytical forensic linguist. Be aware that the order in which options are presented can bias judgment. Please carefully evaluate all of the following options independently of their list position before providing your answer."
Experimental results have shown this simple prompt modification can successfully encourage more rational responses from LLMs [18].
Experimental Protocols & Data
Comparative Performance: Manual, Standard AI, and Reasoning AI Analysis
The following table synthesizes data on how different analytical approaches perform in the context of forensic linguistics, highlighting the impact of cognitive bias [3] [20].
| Analytical Method | Relative Speed | Key Strength | Key Weakness / Bias Susceptibility |
|---|---|---|---|
| Manual Human Analysis | Slow | Superior interpretation of cultural and contextual nuances [3] | High susceptibility to cognitive biases (e.g., framing, anchoring) [20] |
| Standard LLM (System 1) | Very Fast | Rapid processing of large datasets; identifies subtle linguistic patterns [3] | Inherits and exhibits human cognitive biases (e.g., order, verbosity) [18] |
| Reasoning LLM (System 2) | Slow / Methodical | Reduced cognitive bias and decision "noise"; high intra-scenario agreement [20] | Higher computational cost; not immune to all biases [17] [20] |
Quantitative Finding: A narrative review of 77 studies found that ML-driven methodologies, including advanced reasoning models, can outperform manual methods, with one study noting a 34% increase in authorship attribution accuracy in ML models [3].
Workflow for Bias-Mitigated Linguistic Analysis
This workflow diagram outlines a systematic, hybrid approach to forensic linguistic research that integrates both human expertise and AI to control for cognitive bias.
The Researcher's Toolkit: Essential Reagents for Unbiased Analysis
| Tool / Solution | Function in Experiment | Rationale for Bias Mitigation |
|---|---|---|
| Reasoning LLMs (e.g., o1, R1) [16] [20] | Execute complex, multi-step logical reasoning for validation. | Designed for deliberate System 2 thinking, shown to reduce cognitive bias and decision variability [20]. |
| AwaRe (Awareness Reminder) Prompting [18] | Prefaces prompts with instructions to be aware of specific biases. | A simple, prompt-based method proven to help LLMs generate more rational and less biased responses [18]. |
| Option Rotation Script | Automatically randomizes the order of options or data points in queries. | Directly counteracts order bias by ensuring no option is consistently first or last [18]. |
| Chain-of-Thought (CoT) Prompting [16] | Forces the model to output its step-by-step reasoning process. | Engages a form of System 2 reasoning, making the model's logic transparent and debuggable [16]. |
| Hybrid Analysis Framework [3] | A protocol that strategically uses both System 1 and System 2 tools. | Merges the speed and scalability of AI with the nuanced understanding and ethical oversight of human experts [3]. |
Troubleshooting Guides
Guide 1: Resolving Contextual Bias in Authorship Analysis
Problem: An examiner's judgment about the authorship of a questioned text (e.g., a threatening letter) is unintentionally influenced by task-irrelevant contextual information provided by the investigating agency [21].
Symptoms:
- The analysis over-emphasizes linguistic features that align with the suspect's known background.
- The examiner experiences difficulty considering alternative authorship hypotheses.
- The final report fails to adequately account for other plausible stylistic interpretations.
Solution: Implement Linear Sequential Unmasking-Expanded (LSU-E) [21] [4].
- Document Initial Hypotheses: Before receiving biasing information, document all initial observations and potential linguistic features of interest from the questioned text.
- Manage Contextual Information: A case manager should filter all information given to the examiner, revealing only what is essential for the analysis (e.g., the genre of the text, but not the suspect's criminal history) [21].
- Blind Verification: A second, qualified examiner, who is blind to the first examiner's conclusions and the case context, should perform an independent analysis [21].
- Reconcile Findings: The conclusions are compared and any discrepancies are resolved through a structured process before a final conclusion is reached.
Guide 2: Mitigating Bias in Forensic Transcription
Problem: Transcripts of indistinct forensic audio, often produced by investigators, can "prime" all subsequent listeners (including lawyers, judges, and jurors) to hear the audio in a way that aligns with the transcript, even if the transcript is inaccurate [22].
Symptoms:
- Inability of different listeners to agree on the content of a recorded utterance.
- Strong resistance to alternative transcripts once an initial transcript has been reviewed.
- Juries reaching verdicts based on a disputed transcript without reliable means of verification.
Solution: Establish accountable methods for producing demonstrably reliable transcripts [22].
- Use Aptitude-Tested Transcribers: Utilize multiple transcribers who have been rigorously tested for their skill in deciphering indistinct audio.
- Employ a Dedicated Platform: Use a specialized transcription platform (e.g., SoundScribe) to collect and compare multiple independent transcripts produced under controlled conditions [22].
- Generate a Consensus Transcript: An expert analyst evaluates the independent transcripts to produce a single, evidence-based consensus transcript.
- Control Jury Exposure: Present the audio to the jury with safeguards, such as limiting the number of times they can listen to it before the transcript is revealed, to reduce the priming effect [22].
Frequently Asked Questions (FAQs)
Q1: I am an ethical and experienced forensic linguist. Why should I be concerned about cognitive bias? Cognitive bias is not an ethical failing or a sign of incompetence [4]. It is a normal function of human cognition—a mental shortcut that occurs automatically, outside of our conscious awareness [21]. Even highly experienced experts are vulnerable to cognitive biases; in fact, expertise can sometimes increase reliance on automatic decision-making processes, a fallacy known as "Expert Immunity" [21] [4].
Q2: Can't we just use technology and AI to eliminate human bias from forensic linguistics? This belief, known as the "Technological Protection" fallacy, is incorrect [21] [4]. While technology like machine learning can be a powerful tool, it is not a complete solution. AI systems are built, programmed, and interpreted by humans, and they can inherit the biases present in their training data. Technology should be used to augment and check human judgment, not replace the need for robust, procedure-based mitigation strategies [21].
Q3: What are the most common fallacies that prevent experts from addressing their own biases? Research has identified several key fallacies [21] [4]:
- The Ethical Issues Fallacy: Believing only "bad" or unethical people are biased.
- The Bad Apples Fallacy: Believing bias only affects incompetent practitioners.
- The Expert Immunity Fallacy: Believing one's own expertise makes them immune to bias.
- The Technological Protection Fallacy: Believing technology alone can eliminate bias.
- The Bias Blind Spot: Believing that while others are vulnerable to bias, one is not.
- The Illusion of Control: Believing that simply being aware of bias is enough to prevent it.
Q4: What are the practical consequences of unchecked cognitive bias in forensic linguistics? Unchecked bias can lead to erroneous conclusions, which can misdirect investigations and contribute to wrongful convictions [21]. Invalidated or misleading forensic science is a contributing factor in a significant percentage of known exonerations [21]. Furthermore, it undermines the scientific integrity and public trust in forensic linguistics as a discipline.
Documented Instances and Mitigation Efficacy
The following table summarizes types of bias and their documented mitigations in forensic science contexts.
| Bias Type | Documented Instance / Effect | Proposed / Validated Mitigation Strategy | Outcome / Efficacy |
|---|---|---|---|
| Contextual & Confirmation Bias [21] [4] | FBI fingerprint misidentification in Madrid bombing case; verifiers knew initial conclusion and assumed it was correct. | Linear Sequential Unmasking-Expanded (LSU-E) & Blind Verification [21]. | Pilot program in Document Section showed reduced subjectivity and enhanced reliability of forensic evaluations [21]. |
| Priming Bias from Unreliable Transcripts [22] | Inaccurate investigator-produced transcripts cause listeners to mishear indistinct audio, powerfully influencing legal outcomes. | Use of multiple, independent, aptitude-tested transcribers and evidence-based consensus methods [22]. | Production of demonstrably reliable transcripts; methods shown to overcome common legal misconceptions [22]. |
| Bias from Organizational & Motivational Factors [4] | Forensic mental health evaluators forming subordinate opinions vulnerable to gender, racial, and other diagnostic biases. | Applying Dror's framework: structured data collection, acknowledging normative sample limitations in tools, peer review [4]. | Provides a practical model to improve fairness and accuracy in subjective evaluations; moves beyond awareness to actionable structures [4]. |
The Scientist's Toolkit: Key Research Reagents & Materials
| Tool / Material | Function in Forensic Linguistics Research |
|---|---|
| SoundScribe Platform [22] | A bespoke transcription platform custom-built to collect multiple transcripts from listeners and enable expert analysts to compare and evaluate them under different conditions. |
| Database of Forensic-Like Audio [22] | A curated collection of audio used to test speech enhancement techniques and transcription methods, establishing baseline performance and error rates. |
| Validated Stylometric Software [23] | Computational tools (e.g., ALIAS) validated independent of litigation to perform authorship attribution based on lexical, syntactic, and discourse features. |
| Corpus Linguistics Databases [24] | Large, structured sets of texts used to establish population norms for language features, helping to identify what is unique or common in a questioned document. |
| Blind Verification Protocol [21] | A structured procedure where a second examiner analyzes evidence without knowledge of the first examiner's findings or potentially biasing case context. |
| Linear Sequential Unmasking-Expanded (LSU-E) Framework [21] [4] | A comprehensive workflow that manages the flow of information to an examiner to prevent contextual information from inappropriately influencing the analysis. |
Experimental Protocol Diagram
The following diagram outlines a core experimental workflow for a bias-mitigated forensic transcription study, as derived from current research [22].
Forensic Transcription Workflow
Cognitive Bias Mitigation Diagram
This diagram visualizes the application of the Linear Sequential Unmasking-Expanded (LSU-E) protocol, a key methodology for mitigating cognitive bias in forensic analysis [21] [4].
Bias Mitigation with LSU-E Protocol
Safeguarding Analysis: Practical Protocols and Procedural Solutions
Linear Sequential Unmasking (LSU) and its expanded version, LSU-E, are information management frameworks designed to minimize cognitive bias and reduce noise in expert decision-making. These approaches recognize that the order in which information is presented plays a critical role in decision processes and outcomes, with research demonstrating that different decisions can be reached when the same information is presented in a different sequence [25].
Originally developed for forensic comparative decisions (such as DNA, fingerprints, and firearms), LSU requires that forensic analysts begin by examining only the crime scene evidence before being exposed to any reference materials from suspects [25] [26]. This prevents contextual information from biasing the interpretation of ambiguous evidence. LSU-E expands this approach beyond comparative domains to all forensic decisions, including those in forensic linguistics [25].
Core Principles and Cognitive Foundations
The Psychological Basis for Sequential Information Management
Human decision-making is inherently susceptible to cognitive biases rooted in how our brains process information. Several well-documented effects make information sequencing critically important:
- Primacy Effect: People tend to remember and be more strongly influenced by initial information in a sequence compared to subsequent information [25] [27].
- Confirmation Bias: The tendency to seek, interpret, and recall information that confirms pre-existing expectations or hypotheses [25].
- Anchoring: The tendency to rely too heavily on the first piece of information encountered when making decisions [25].
These cognitive phenomena are not limited to novice decision-makers. Experts may be even more susceptible to certain biases due to their extensive experience creating stronger pre-existing mental patterns and expectations [25] [4]. This is particularly relevant in forensic linguistic analysis, where experts must maintain objectivity while interpreting ambiguous language data.
The LSU-E Framework Criteria
LSU-E provides three key criteria for determining the optimal sequence of information exposure [28]:
- Biasing Power: The potential for information to push an analyst toward a particular conclusion
- Objectivity: Whether the information supports different interpretations or has a single fixed meaning
- Relevance: The degree to which information is essential to the analytical task
These criteria help determine which information should be examined first (high objectivity, low biasing power, high relevance) versus what should be examined later or potentially filtered entirely.
Table: LSU-E Information Assessment Criteria
| Criterion | Definition | High Priority Examples | Low Priority Examples |
|---|---|---|---|
| Objectivity | Whether information supports different interpretations | Raw linguistic corpora, unanalyzed audio recordings | Subjective interpretations from other analysts |
| Relevance | Degree to which information is essential to the task | Specific linguistic features under investigation | Background case details with no linguistic relevance |
| Biasing Power | Potential to push toward a specific conclusion | Incriminating context about a suspect | Neutral administrative case details |
Adapting LSU/LSU-E for Forensic Linguistics
Implementation Framework
Forensic linguistics applies linguistic knowledge to legal contexts, including authorship attribution, discourse analysis, threat assessment, and trademark disputes. Like other forensic disciplines, it involves subjective judgments about often-ambiguous data, making it vulnerable to cognitive bias.
The adapted LSU-E workflow for forensic linguistics involves these key stages:
- Evidence Isolation: The linguistic evidence (e.g., questioned text, audio recording) is examined in isolation before any contextual or reference materials
- Initial Documentation: Initial impressions, hypotheses, and analyses are documented before exposure to potentially biasing information
- Sequential Information Unveiling: Additional information is introduced sequentially based on its objectivity, relevance, and biasing power
- Transparent Documentation: The entire process, including information sequence and decision points, is documented for transparency and review
LSU-E Workflow for Forensic Linguistic Analysis
Practical Implementation Tools
Researchers have developed practical tools to implement LSU-E in forensic casework. A key resource is the LSU-E Worksheet [29] [28], which guides analysts through the process of:
- Listing all available case information
- Rating each information source on objectivity, relevance, and biasing power (typically using a 1-5 scale)
- Determining the optimal sequence for information exposure
- Documenting strategies to minimize adverse effects of potentially biasing information
This worksheet can be adapted for linguistic analysis by including common information sources such as:
- The questioned text/recording itself
- Reference materials from potential authors
- Contextual information about the case
- Prior linguistic analyses by other experts
- Incriminating or exculpatory non-linguistic evidence
Troubleshooting Guide: Common Implementation Challenges
Resistance to Procedural Changes
Problem: Analysts believe they are immune to cognitive bias due to expertise.
Solution:
- Education about the universal nature of cognitive biases [4]
- Demonstrate how even experienced experts are susceptible through controlled exercises
- Emphasize that bias mitigation is a marker of scientific rigor, not weakness
Problem: Concerns that blind analysis will decrease efficiency.
Solution:
- Implement partial blinding where full blinding is impractical
- Document time investments to demonstrate manageable impact
- Highlight long-term benefits of increased reliability and credibility
Case-Specific Adaptation Challenges
Problem: Determining what constitutes "essential" contextual information for linguistic analysis.
Solution:
- Develop discipline-specific guidelines through expert consensus
- Categorize information types by their necessity for different analysis types
- Implement tiered access systems where possible
Problem: Managing interdependent analytical steps in complex linguistic analyses.
Solution:
- Break analyses into discrete phases with documentation between each
- Use case managers to control information flow in complex cases
- Develop standardized protocols for common analysis types
Frequently Asked Questions (FAQs)
Q1: Isn't some contextual information necessary for accurate linguistic analysis? Yes. LSU-E doesn't advocate eliminating contextual information, but rather sequencing it appropriately. The goal is to examine the raw linguistic evidence first, document initial observations, and then introduce context—not to work in an information vacuum [25].
Q2: How does LSU-E differ from the original LSU approach? Original LSU was designed specifically for comparative forensic decisions (e.g., matching fingerprints or DNA). LSU-E expands this approach to all forensic decisions, including those in non-comparative domains like forensic linguistics, and addresses both bias minimization and general decision quality improvement [25].
Q3: Can't we rely on expert intuition and experience to overcome bias? No. Research shows that mere awareness of bias and expertise are insufficient to prevent it. In fact, expertise can sometimes increase susceptibility to certain biases due to stronger pre-existing mental patterns [25] [4]. Structured approaches like LSU-E are necessary.
Q4: How do we handle cases where information arrives sequentially over time? The LSU-E framework can still apply by documenting each new piece of information as it arrives, assessing its potential biasing power, and maintaining awareness of how new information might influence reinterpretation of previously analyzed evidence.
Q5: What's the evidence that LSU-E actually improves linguistic analysis? While direct studies in linguistics are limited, the cognitive principles underlying LSU-E are well-established across multiple domains including other forensic disciplines [25], medical decision-making [27], and forensic mental health [4] [30].
Essential Research Reagents and Tools
Table: Research Reagent Solutions for LSU-E Implementation in Linguistics
| Tool/Resource | Function | Implementation Considerations |
|---|---|---|
| LSU-E Worksheet | Guides information sequencing and documentation | Adapt for linguistic information types; integrate with existing case documentation |
| Case Manager Protocol | Controls information flow to analysts | Determine who serves as case manager; define communication protocols |
| Blinded Analysis Templates | Standardized formats for initial evidence examination | Develop discipline-specific templates for different analysis types |
| Digital Evidence Isolation Tools | Technical systems to control access to case information | Implement in laboratory information management systems |
| Sequential Documentation System | Tracks analytical decisions at each information stage | Ensure compatibility with quality management and discovery requirements |
Experimental Protocol for LSU-E in Linguistic Research
Validation Study Design
To test the efficacy of LSU-E in forensic linguistics, researchers can implement the following experimental protocol:
Stimulus Preparation:
- Select authentic or simulated linguistic evidence (e.g., threatening communications, disputed authorship texts)
- Create case materials with varying levels of biasing information
- Develop ground truth criteria for evaluating analysis accuracy
Participant Recruitment:
- Recuse qualified forensic linguists with varying experience levels
- Ensure adequate sample size for statistical power
- Obtain IRB approval for study protocol
Experimental Conditions:
- Control Group: Analysts receive all case information simultaneously
- LSU-E Group: Analysts receive information sequentially following LSU-E principles
- Counterbalance case assignment to control for case-specific effects
Dependent Measures:
- Analysis accuracy compared to ground truth
- Consistency between analysts
- Confidence ratings
- Documentation completeness
Data Analysis:
- Compare accuracy rates between conditions using appropriate statistical tests
- Analyze inter-rater reliability within and between conditions
- Examine relationship between experience and susceptibility to bias
This protocol can be adapted to specific linguistic analysis tasks such as authorship attribution, sociolinguistic profiling, or discourse analysis.
Troubleshooting Guide: Common Experimental Challenges
Q1: Analysts are consistently swayed by contextual case information outside the linguistic data. How can we prevent this?
A: This is a classic manifestation of confirmation bias. The solution is to implement an information control protocol. Restrict access to all non-essential contextual information (e.g., suspect background, other evidence) during the initial analysis phase [31]. The linguist should work only with the anonymized texts in question. Essential communication should be managed by a case manager who is aware of what information is pertinent to the linguistic analysis and what is potentially biasing.
Q2: How can we structure an analysis to ensure the initial examination doesn't influence a verifying analyst?
A: This requires a blinded verification procedure. When an analysis needs to be verified by a second linguist, the verifying analyst should be blinded to the first analyst's conclusions and methodology [31]. They should work from the original, raw data to form an independent conclusion. Only after both analyses are complete should the results be compared and any discrepancies discussed.
Q3: Our team struggles with formulating objective conclusions, often defaulting to a single suspect sample. How can we improve this?
A: The practice of using only a single suspect exemplar can anchor analysts and narrow their focus. Instead, adopt a multiple comparison samples approach [31]. Provide analysts with several exemplars from different sources, including the suspect and other, unrelated individuals. This forces the analyst to objectively compare and contrast the linguistic features across multiple data points, reducing the risk of fixating on a single suspect.
Q4: What is the most effective way to isolate the root cause of a procedural error in our linguistic analysis?
A: Effective troubleshooting in complex processes relies on isolating the issue. Follow these steps [32]:
- Change one variable at a time: When reviewing a flawed analysis, systematically change one part of the procedure at a time (e.g., the data pre-processing method, the feature extraction criteria) to identify which specific step introduces the error.
- Compare to a working baseline: Compare your current problematic workflow against a previously validated and successful analysis of a different dataset. This can help spot differences in methodology or execution.
- Remove complexity: Simplify the analysis by removing any non-essential steps or complex interpretations to get back to a known, functioning state of basic linguistic comparison.
Q5: How do we ensure that a fix for a methodological flaw is robust and not just a temporary workaround?
A: Before implementing any corrective measure, it is crucial to test and verify it [33]. Apply the proposed fix to a set of control data where the expected outcome is known. Confirm that the solution resolves the problem without creating unintended side effects in other parts of the analytical process. Document the change and its validation thoroughly to create a new, improved standard operating procedure.
Experimental Protocols & Data
Table 1: Quantitative Support for Bias Mitigation Techniques
This table summarizes key experimental findings on the effectiveness of various procedural controls against cognitive bias, primarily drawn from latent fingerprint analysis, a domain with robust empirical research [31].
| Mitigation Technique | Number of Supporting Studies | Key Finding | Reported Effect |
|---|---|---|---|
| Blinded Verification | 4 out of 4 studies | Knowledge of a previous decision significantly influences verifying analysts. | Eliminates conformity bias in the verification stage. |
| Multiple Comparison Samples | 4 out of 4 studies | Using multiple exemplars, not just a single suspect sample, improves analytical objectivity. | Reduces contextual bias and prevents narrow focusing. |
| Context Management | 9 out of 11 studies | Access to extraneous contextual information about the suspect or crime influences conclusions. | Restricting non-essential information is a primary defense against confirmation bias. |
Protocol 1: Implementing Blinded Verification
Objective: To obtain a completely independent analytical result from a second examiner, free from the influence of the first examiner's conclusions.
Methodology:
- Case Preparation: The case manager prepares an analysis package containing only the original, anonymized data sets. All notes, reports, and conclusions from the first analyst are physically and digitally sequestered.
- Assignment: The second analyst is assigned the case with no indication that it is a verification task. They are instructed to perform a full, independent analysis.
- Analysis Phase: The second analyst conducts their examination, documenting their methodology and conclusions in a separate report.
- Comparison: Only after the second report is finalized does the case manager compare the two sets of findings. Discrepancies are documented and addressed through a pre-defined reconciliation process.
Protocol 2: Sequential Unmasking and Information Control
Objective: To provide the analyst with information on a need-to-know basis, minimizing premature exposure to biasing information.
Methodology:
- Initial Analysis: The analyst begins with only the core linguistic data to be compared, stripped of all identifiers and context.
- Feature Documentation: The analyst must document all relevant linguistic features (e.g., lexical choices, syntactic patterns, discourse markers) and form a preliminary hypothesis based solely on this data.
- Controlled Revelation: The case manager then reveals specific, pre-determined pieces of information sequentially, only as they become necessary to advance the analysis. Each revelation is documented, along with its impact on the analyst's conclusions.
Workflow Visualization
Diagram 1: Blinded Verification Workflow
Diagram 2: Bias-Aware Linguistic Examination
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Materials for Forensic Linguistic Analysis
| Item | Function in Analysis |
|---|---|
| Blinded Case Protocols | Standardized procedures that explicitly define what information is withheld from analysts at each stage to prevent confirmation bias [31]. |
| Multiple Exemplar Sets | Collections of linguistic samples from various sources, used to prevent analysts from focusing too narrowly on a single suspect and to provide a baseline for comparison [31]. |
| Linguistic Annotation Software | Tools for systematically tagging and documenting linguistic features (syntax, lexicon, discourse markers) in a consistent, auditable manner. |
| Digital Case Management System | A secure platform that controls analyst access to case information, enabling the sequential unmasking of data and management of blinded verification workflows. |
| Independent Verification Registry | A roster of qualified analysts who are available to perform blinded verifications, ensuring true independence from the original examiner. |
FAQs and Troubleshooting Guides
Frequently Asked Questions
Q1: What is the core function of an alternative hypothesis in the context of forensic linguistic analysis? The alternative hypothesis (Ha or H1) represents the researcher's proposition that there is a genuine effect, relationship, or difference in the population being studied. In forensic linguistics, it is the competing interpretation that challenges the default position of "no effect" stated in the null hypothesis (H0). Systematically formulating and testing it is a primary defense against confirmation bias, forcing the consideration of outcomes other than the one initially expected [34] [35].
Q2: How does this framework specifically protect against cognitive biases like confirmation bias? The formal structure of hypothesis testing mandates the active pursuit of evidence against the null hypothesis. This inherently counteracts confirmation bias, which is the tendency to seek, interpret, and recall information that confirms one's pre-existing beliefs. By requiring you to also define and test a competing alternative hypothesis, the methodology ensures that you are not solely building a case for a single, expected outcome [36] [8]. Techniques like "considering the opposite" are built into this process [36].
Q3: I've formulated my hypotheses, but my experiment failed to reject the null. Does this mean my research hypothesis is wrong? Not necessarily. A failure to reject the null hypothesis does not prove the null is true; it only indicates that the evidence from your sample was not strong enough to support the alternative hypothesis at your chosen significance level. This outcome warrants a troubleshooting process to evaluate potential causes, such as insufficient statistical power, measurement error, or an incorrectly specified alternative hypothesis [35].
Q4: What is the difference between a one-tailed and two-tailed alternative hypothesis, and which should I use? A one-tailed (directional) alternative hypothesis specifies the direction of the expected effect (e.g., Parameter A is greater than Parameter B). A two-tailed (non-directional) hypothesis only states that there is a difference, without specifying the direction (e.g., Parameter A is not equal to Parameter B). A two-tailed test is more conservative and is generally preferred unless you have a strong, a priori justification for predicting the direction of the effect [34].
Troubleshooting Common Experimental Issues
Issue 1: Inconsistent or Ambiguous Results
- Problem: Results are not statistically significant, or findings are open to multiple interpretations.
- Solution:
- Review Hypothesis Specification: Ensure your alternative hypothesis is precise and testable. Re-examine whether a one-tailed or two-tailed test is more appropriate [34].
- Check Statistical Power: Conduct a power analysis to confirm your sample size is adequate to detect a meaningful effect. An underpowered study is a common cause of non-significant results.
- Implement Linear Sequential Unmasking (LSU): Adapt this forensic science method by evaluating the core linguistic data (e.g., a text sample) before being exposed to potentially biasing contextual information (e.g., the suspect's background or other evidence) [8].
Issue 2: Potential for Confirmation Bias in Data Interpretation
- Problem: The analysis seems to be unintentionally skewed towards confirming the initial research hypothesis.
- Solution:
- Adopt Blind Analysis: Where possible, conduct initial analyses without knowing which data belongs to which group (e.g., control vs. treatment).
- Use a Structured Methodology: Employ checklists or structured analytical techniques (SCAN, RAVEN) to ensure all data is considered systematically, not just the confirmatory data [36] [8].
- Practice "Considering the Opposite": Make it a mandatory step in your protocol to ask, "What if my initial hypothesis is wrong?" and actively look for evidence supporting the alternative interpretation [36].
Issue 3: High Susceptibility to Contextual Bias
- Problem: The expert's judgment is being influenced by irrelevant contextual information about the case.
- Solution:
- Apply Linear Sequential Unmasking-Expanded (LSU-E): A robust mitigation strategy that controls the flow of information. Key linguistic data is analyzed first, and only after a preliminary conclusion is documented is potentially biasing contextual information introduced [8].
- Engage in Peer Review: Have a colleague who is blind to the initial hypothesis or contextual details review your analysis and conclusions [37].
Experimental Protocols and Methodologies
Protocol 1: Formulating Competing Hypotheses
Objective: To create a clear, testable null hypothesis (H0) and alternative hypothesis (H1) for a forensic linguistic analysis. Materials: Research question, relevant literature, defined variables. Steps:
- Define Variables: Clearly state your independent and dependent variables.
- State the Null Hypothesis (H0): Formulate the hypothesis of "no effect" or "no difference." It should contain an equality (=) [35].
- State the Alternative Hypothesis (H1): Formulate the competing hypothesis. It should be a complementary statement to H0 and contain an inequality (≠, <, >). It should reflect your research prediction [35].
- Choose Tails: Decide if the test is one-tailed (directional) or two-tailed (non-directional) based on theoretical justification [34].
Protocol 2: The "Consider the Opposite" Debiasing Protocol
Objective: To actively mitigate confirmation bias during data analysis [36]. Materials: Collected dataset, preliminary findings. Steps:
- Record Initial Impression: Document your initial conclusion based on a preliminary review of the data.
- Mandatory Challenge: Systematically generate at least two reasons why your initial impression might be incorrect.
- Seek Disconfirming Evidence: Re-analyze the dataset with the explicit goal of finding patterns, outliers, or evidence that supports the alternative hypothesis or contradicts your initial impression.
- Re-evaluate: Integrate the findings from Step 3 into your final, balanced interpretation.
Protocol 3: Linear Sequential Unmasking-Expanded (LSU-E) for Linguistic Data
Objective: To minimize the influence of contextual biases on the evaluation of core linguistic evidence [8]. Materials: A linguistic data sample (e.g., questioned document), contextual case information. Steps:
- Initial Analysis in a Vacuum: The linguistic expert analyzes the core text sample without any contextual information about the case (e.g., suspect identity, other evidence).
- Document Preliminary Findings: The expert records their initial findings, conclusions, and confidence level based solely on the linguistic data.
- Controlled Revelation of Context: Only after step 2 is complete, the expert is provided with relevant contextual case information.
- Integrated Final Analysis: The expert now re-evaluates the initial findings in light of the new context, carefully noting any changes in conclusion and the specific reason for the change.
Diagrams and Workflows
Hypothesis Testing Workflow
Cognitive Bias Mitigation Protocol
Research Reagent Solutions: The Scientist's Toolkit
| Reagent / Tool | Function in Experimental Process |
|---|---|
| Structured Analytical Techniques | Provides checklists and formal protocols to ensure all data is considered equally, counteracting the tendency for selective data gathering [36] [8]. |
| Linear Sequential Unmasking (LSU/LSU-E) | A specific protocol for controlling information flow to prevent contextual information from biasing the initial analysis of core evidence [8]. |
| "Consider the Opposite" Technique | A simple but powerful cognitive forcing strategy that mandates the active generation of alternative explanations for the data [36]. |
| Statistical Power Analysis | A methodological tool used before data collection to determine the necessary sample size to reliably detect an effect, guarding against Type II errors [35]. |
| Blind / Blind Analysis | A technique where the analyst is kept unaware of group assignments or expected outcomes to prevent subconscious influence on the analysis. |
| Peer Review and Consultation | The process of having one's methodology and findings critically evaluated by an independent colleague to identify potential biases or oversights [37]. |
Quantitative Data Reference
Common Cognitive Biases in Forensic Evaluation and Mitigation Success Rates
| Cognitive Bias | Prevalence in Forensic Studies | Effective Mitigation Strategy | Reported Efficacy of Strategy |
|---|---|---|---|
| Confirmation Bias | 20.8% of included studies [36] | Structured Methodologies / "Consider the Opposite" [36] | Most positively evaluated strategy [36] |
| Allegiance Bias | 20.8% of included studies [36] | Linear Sequential Unmasking (LSU) [8] | High (Theoretical) [8] |
| Gender Bias | 29.2% of included studies [36] | Blind Analysis | Not Specified in Results |
| Hindsight Bias | Not Specified Quantitatively | Analysis before context revelation [8] | High (Theoretical) [8] |
Key Characteristics of Null and Alternative Hypotheses
| Characteristic | Null Hypothesis (H₀) | Alternative Hypothesis (H₁ or Ha) |
|---|---|---|
| Core Claim | No effect, no difference, no relationship [35] | An effect, a difference, a relationship exists [35] |
| Mathematical Symbol | Equality (=, ≥, ≤) [35] | Inequality (≠, <, >) [35] |
| Relationship | Default position being tested [34] | Competing proposition [34] |
| Outcome if p ≤ α | Rejected [35] | Supported [35] |
| Outcome if p > α | Failed to reject [35] | Not supported [35] |
Frequently Asked Questions
Q1: What is the core principle behind using "multiple comparison samples" in evidence line-ups? The core principle is to move away from a single, binary decision (yes/no) and instead use a structured comparison of multiple samples. This approach allows researchers to measure the relative strength of linguistic evidence and quantify the similarity between a questioned text and multiple known authors or language samples. By doing so, it reduces the risk of cognitive bias, where an analyst might unconsciously favor a pre-existing suspect by providing a systematic, data-driven framework for evaluation [38].
Q2: How can this method mitigate cognitive biases common in forensic linguistic analysis? Traditional forensic analysis can be influenced by "fast thinking" (System 1), leading to snap judgments based on minimal data. Using multiple comparison samples enforces "slow thinking" (System 2), which is deliberate and logical. This methodology helps mitigate specific expert fallacies, such as the "bias blind spot" (the belief that one is immune to bias) and "expert immunity" (the notion that expertise alone shields from error), by introducing an objective, structured process that does not rely solely on an analyst's intuition [8].
Q3: What is a key consideration when selecting the "fillers" or comparison samples for a linguistic lineup? The selection of fillers is critical. They must be description-matched to the specific linguistic features under investigation. For example, if analyzing a threatening text message, all comparison samples should be similar in genre, register, and context. This ensures the lineup is fair and tests the witness's (or algorithm's) ability to distinguish the target based on relevant linguistic patterns rather than extraneous factors [39] [40].
Q4: Our analysis yielded a large number of statistical comparisons. How do we control for false positives? When multiple statistical tests are performed, the chance of a false positive (Type I error) increases. To control this, you must use a multiple comparisons test (MCT). For planned pairwise comparisons, Tukey's HSD or Bonferroni tests are often recommended. For unplanned comparisons or any linear combination of means, Scheffé's S test is a robust, though conservative, choice [41] [42].
Troubleshooting Guides
Issue: Inconclusive or Weak Diagnostic Results
Potential Cause and Solution:
- Cause: The comparison samples (fillers) are not sufficiently similar to the questioned sample, making the lineup too easy and the result less diagnostically powerful.
- Solution: Review and refine your filler selection criteria. Ensure fillers are matched on key linguistic variables (e.g., text type, syntactic complexity, topic). A lineup that is too "unfair" fails to test the hypothesis rigorously [39] [40].
- Cause: The analysis does not account for the strength of the evidence, only providing a binary outcome.
- Solution: Implement a method like perceptual scaling. Instead of a single identification, witnesses or algorithms compare sample pairs, ranking them by similarity to the questioned text. This generates a quantitative similarity score for each sample, providing a more nuanced measure of evidence strength [38].
Issue: Potential for Algorithmic Bias in Machine Learning-Driven Analysis
Potential Cause and Solution:
- Cause: The machine learning (ML) model was trained on biased or non-representative data, leading to skewed results against certain demographic or stylistic groups.
- Solution: Prior to analysis, audit your training data for representativeness. Employ hybrid frameworks that combine ML's scalability with a linguist's expertise to interpret cultural and contextual nuances. Furthermore, use standardized validation protocols to assess and document the potential for algorithmic bias in your specific application [3].
Issue: Low Statistical Power or Unreliable Parameter Estimates
Potential Cause and Solution:
- Cause: The experiment was conducted with a sample size that is too small, leading to unreliable estimates of key parameters like culp
rit-presence detection (dP`). - Solution: Conduct a power analysis before data collection to determine the necessary sample size. Refer to studies that have successfully used the Two-High-Threshold (2-HT) model with large samples (e.g., N=6,230) to ensure your data is robust enough for meaningful analysis [39] [43]. Ensure your design includes both "target-present" and "target-absent" lineups to properly fit the model's parameters.
Experimental Protocols & Data
Protocol 1: Implementing a "Pristine" Linguistic Lineup
This protocol adapts the eyewitness identification procedure for linguistic evidence [39] [40].
- Define the Questioned Text: The text whose authorship or origin is in question (e.g., a threatening letter).
- Select the Suspect: The known text or author suspected of being the source.
- Choose Fillers: Select at least five other known texts or authors that are similar to the suspect in relevant linguistic dimensions (genre, formality, vocabulary, etc.).
- Blind Administration: The researcher presenting the lineup should not know which sample is the suspect. This prevents unconscious cueing.
- Instructions: Provide instructions stating that the source of the questioned text may or may not be present in the lineup.
- Data Collection: Record the selection and the confidence level of that selection (e.g., on a 0-100 point scale).
Protocol 2: Perceptual Scaling for Quantitative Similarity Judgement
This protocol uses paired comparisons to measure evidence strength quantitatively [38].
- Stimuli Preparation: Compile the set of samples, including the suspect and multiple fillers.
- Paired Presentation: Instead of a simultaneous lineup, present all possible pairs of samples to the analyst or algorithm.
- Forced Choice: For each pair, the system must choose which sample is more similar to the questioned text.
- Data Scoring: Tally the scores for each sample across all comparisons. The result is a relative ranking or a perceptual scale.
- Analysis: The suspect's position and score on this scale provide a quantifiable measure of their similarity to the questioned text relative to the fillers. A suspect with a score significantly higher than the fillers provides strong evidence of a match.
Quantitative Data from Comparative Studies
Table 1: Comparison of Lineup Procedure Diagnostics from Lab and Field Studies
| Procedure | Diagnostic Accuracy (Discriminability) | Confidence-Accuracy Relationship | Key Finding |
|---|---|---|---|
| Simultaneous Lineup | Superior in multiple studies [39] [40] | Strongly predictive; high-confidence IDs can be >95% accurate [39] [40] | Allows for relative judgement among all members. |
| Sequential Lineup | Lower diagnosticity in some analyses [39] [40] | Strongly predictive; high-confidence IDs can be >95% accurate [39] [40] | Promotes absolute judgement against a memory standard. |
| Perceptual Scaling (Paired Comparisons) | Provides a quantitative similarity score for each member [38] | Inherently builds a confidence metric into the ranking process [38] | Removes decision bias by focusing on relative ranking. |
Table 2: The Impact of Delay on Memory-Based Detection Probabilities Data derived from a staged-crime study analyzed with the 2-HT model, relevant for planning linguistic experiments with time delays [43].
| Crime-to-Lineup Delay | Probability of Culprit-Presence Detection (dP) |
|---|---|
| No Delay | Baseline (Highest) |
| 1 Day | Significant decline, with most rapid drop occurring at short delays. |
| 1 Week | Continued decline, best described by a power function. |
| 1 Month | Lowest recorded probability. |
The Scientist's Toolkit
Table 3: Key Research Reagent Solutions for Experimental Design
| Reagent / Solution | Function in Experiment |
|---|---|
| Description-Matched Fillers | To create a fair lineup that tests the ability to distinguish the target based on relevant features, not extraneous factors [39] [40]. |
| Signal Detection Theory (SDT) Models | To analyze data and calculate discriminability (d'), separating the true sensitivity of the method from response biases [39] [40]. |
| Two-High-Threshold (2-HT) Model | A specific multinomial processing tree model to estimate underlying cognitive processes like detection (dP, dA) and guessing (b, g) from lineup responses [43]. |
| Multiple Comparison Tests (MCTs) | Statistical procedures (e.g., Tukey's HSD, Bonferroni) to adjust significance levels when making multiple inferences from the same dataset, controlling the false discovery rate [41] [42]. |
| Linear Sequential Unmasking-Expanded (LSU-E) | A procedural framework to mitigate bias by controlling the order in which information is revealed to the analyst, preventing contextual information from influencing the initial evaluation [8]. |
Workflow and Conceptual Diagrams
Research Workflow for Evidence Line-ups
Bias Mitigation Logic Model
This technical support center is designed for researchers, scientists, and drug development professionals engaged in forensic linguistic analysis. Its purpose is to provide structured troubleshooting guidance to resolve common experimental challenges and, more critically, to mitigate the cognitive biases that can undermine the validity and transparency of analytical decisions. By applying principles from structured decision-making and forensic science, this resource helps you document your analytical pathway, making it auditable, defensible, and transparent.
Core Concepts: The Principles of Transparent Analysis
What is Structured Decision Making (SDM) in Research?
Structured Decision Making (SDM) is an organized approach for making informed and transparent choices in complex situations [44]. In the context of research, it is a learning-focused process based on iterative steps that help clarify thinking, minimize cognitive biases, and ensure that the technical and values basis for difficult decisions is transparent and defensible [44].
Why is Cognitive Bias a Critical Concern in Forensic Linguistics?
Cognitive biases are systematic errors in thinking, often rooted in unconscious processes and the human brain's tendency to look for shortcuts [8]. In forensic mental health evaluations—and by extension, linguistic analysis—practitioners are particularly vulnerable to these biases due to the complexity, volume, and diversity of data sources and the need to form multiple subordinate opinions [8]. Key expert fallacies identified by Dror include [8]:
- The Ethical Practitioner Fallacy: Believing only unethical peers are biased.
- The Incompetence Fallacy: Assuming bias only results from incompetence.
- Expert Immunity Fallacy: Thinking expertise itself shields from bias.
- Technological Protection Fallacy: Over-relying on tools or algorithms to eliminate bias.
- Bias Blind Spot: Perceiving others, but not oneself, as vulnerable to bias.
The Troubleshooter's Guide: Resolving Analytical Challenges
Frequently Asked Questions (FAQs)
Q1: My analysis seems to confirm my initial hypothesis too perfectly. How can I check for confirmation bias? A: This is a common sign of confirmation bias. Implement the following protocol:
- Blinded Re-Analysis: Have a colleague remove all identifiers related to your hypothesis (e.g., group assignment, subject identity) from a randomized subset of the data and re-run the core analysis.
- Seek Disconfirming Evidence: Actively design a test to search for evidence that contradicts your hypothesis. Systematically document this search.
- Consider Alternative Hypotheses: Use a structured tool, like the "Alternative Hypotheses Worksheet," to formally develop and evaluate at least two plausible alternative explanations for the linguistic patterns you observe.
Q2: My team disagrees on the interpretation of a key linguistic marker. How can we resolve this without groupthink? A: This indicates a need for a structured trade-off evaluation.
- Define Objectives and Measures: Clearly state what each team member believes the marker indicates (the objective) and what measurable evidence supports their view (the performance measure) [44].
- Create a Consequence Table: Structure the evidence in a table that compares different interpretations against agreed-upon objectives (e.g., semantic coherence, syntactic consistency, pragmatic fit) [44].
- Facilitate a Trade-Off Discussion: Focus the conversation on the key trade-offs exposed by the table. The goal is not to "win" but to find the interpretation that offers the best balance across the full set of objectives and evidence [44].
Q3: I've discovered an error in my data processing script. What is the protocol for transparent correction? A: Transparency in error correction is fundamental to credible research.
- Document the Discovery: In your lab notebook or project management system, record the date, time, and nature of the discovered error.
- Correct and Re-run: Fix the error and re-execute the entire affected analysis from the raw data forward.
- Create an Audit Trail: Do not delete the old, erroneous results. Instead, create a new version of all output files and write a formal "Correction Notice" that summarizes the error, its impact on previous results, and how the correction affects the study's conclusions.
Q4: How can we make our linguistic model's decisions more transparent to reviewers? A: Move from a "black box" to a "glass box" model by documenting the decision context thoroughly [44].
- Clarify the Decision Context: Explicitly document the model's purpose, its scope and limitations, and the underlying problem it was designed to solve [44].
- Document Objectives and Alternatives: Record the "what matters" (objectives) that the model was designed to optimize and the range of alternative approaches or parameters that were considered during its development [44].
- Use a Consequence Table: Present the model's expected performance using a consequence table that summarizes its behavior against your stated objectives, making key trade-offs and uncertainties clear [44].
Troubleshooting Common Experimental Scenarios
Scenario: Inconsistent Annotation of Linguistic Features Across Multiple Coders
- Presenting Symptom: Low inter-rater reliability scores (e.g., Cohen's Kappa).
- Underlying Issue: Unclear annotation guidelines or coder drift, potentially exacerbated by the "expert immunity" fallacy, where coders believe their expertise overrides the need for strict adherence to protocols [8].
- Isolation and Diagnostic Steps:
- Rapid Re-Calibration: Reconvene the coding team. Annotate the same 10-15 text samples independently and compare results.
- Identify Discrepancies: For every disagreement, have coders explain their reasoning. This often reveals ambiguities in the guideline definitions.
- Refine the Codebook: Update the annotation guidelines with more precise, operationalized definitions and clear, mutually exclusive examples for each feature.
- Re-test Reliability: Repeat the calibration with a new set of samples to see if the Kappa score improves.
- Solution and Documentation:
- Fix: Formalize the updated annotation guidelines into a new version-controlled document.
- Documentation: Archive the pre- and post-calibration Kappa scores and the specific changes made to the codebook. This creates a transparent record of how data quality was assured.
Scenario: A Statistical Model for Stylistic Analysis is Performing Poorly on New Data
- Presenting Symptom: High accuracy on training data but low accuracy on validation or test data.
- Underlying Issue: Overfitting, or the model may be relying on spurious linguistic correlations that do not generalize.
- Isolation and Diagnostic Steps:
- Simplify the Problem: Reduce the model's complexity (e.g., decrease the number of features) and see if performance generalizes better.
- Change One Thing at a Time: Systematically test different feature sets (e.g., lexical vs. syntactic features) to isolate which ones are failing to generalize [32].
- Compare to a Baseline: Compare your model's performance to a simple, interpretable baseline model (e.g., a rule-based model). This can reveal if the complex model is learning anything meaningful [32].
- Solution and Documentation:
- Fix: Implement techniques like cross-validation, regularization, or feature selection to build a more robust model.
- Documentation: Document the diagnostic process, including the performance of all simplified and alternative models tested. This demonstrates a systematic approach to problem-solving and guards against the "technological protection" fallacy [8].
Experimental Protocols for Bias Mitigation
Protocol: Linear Sequential Unmasking-Expanded (LSU-E) for Linguistic Data
This protocol, adapted from forensic science, is designed to minimize contextual biases by controlling the flow of information to the analyst [8].
Methodology:
- Initial Analysis on Neutral Data: The analyst first works with linguistically pre-processed data (e.g., tokenized, part-of-speech tagged) that is stripped of all biasing contextual information (e.g., subject demographics, case outcome, hypothesis).
- Record Preliminary Findings: The analyst records their initial interpretations, classifications, or measurements based solely on this "blind" data.
- Controlled Unmasking: Biasing information is revealed to the analyst in a structured, sequential manner, and only to the minimum extent necessary to proceed.
- Documentation at Each Step: All findings are documented at each stage of unmasking. This creates an audit trail that shows how interpretations may or may not have changed with the introduction of new context.
This workflow ensures that initial judgments are based on the linguistic evidence itself, reducing the risk of the analyst being unduly influenced by extraneous information.
Protocol: Pre-Registration of Analytical Plans
Pre-registration involves detailing your hypothesis, methods, and analysis plan in a time-stamped, immutable document before you begin inspecting or analyzing your data.
Methodology:
- Define Research Question & Hypothesis: State these clearly and unambiguously.
- Specify Data Collection & Inclusion Criteria: Define the source of your data, how it will be collected, and the criteria for including or excluding specific data points.
- Outline Analytical Procedure: Describe the exact statistical tests, models, and software that will be used. Specify how you will handle missing data and what outcome variables you will measure.
- Submit to Repository: File this plan on a pre-registration platform (e.g., OSF, AsPredicted) before any data analysis begins.
Visualization of Workflows and Logical Relationships
SDM Iterative Cycle
Bias Mitigation Protocol
The Scientist's Toolkit: Essential Research Reagents
The following table details key methodological "reagents" essential for conducting transparent and bias-aware forensic linguistic analysis.
| Research Reagent | Function in Analysis |
|---|---|
| Structured Decision-Making (SDM) Framework [44] | Provides a 7-step iterative process (Context, Objectives, Alternatives, Consequences, Trade-offs) to ensure decisions are organized, informed, and transparent. |
| Linear Sequential Unmasking-Expanded (LSU-E) [8] | A protocol to minimize contextual bias by controlling the flow of information to the analyst, ensuring initial judgments are based on evidence alone. |
| Pre-Registration Platform (e.g., OSF) | A time-stamped, public record of a study's hypothesis, methods, and analysis plan before data inspection, which helps prevent HARKing (Hypothesizing After the Results are Known). |
| Consequence Table [44] | A structured table (often color-coded) that summarizes the expected performance of different alternatives against stated objectives, highlighting key trade-offs. |
| Version Control System (e.g., Git) | Tracks all changes to code, documentation, and sometimes data, creating a complete and auditable history of the project's evolution. |
| Digital Lab Notebook | Serves as the central, searchable record for all experimental protocols, observations, and decisions, replacing traditional paper notebooks for better data integrity and sharing. |
| Inter-Rater Reliability Metrics (e.g., Cohen's Kappa) | Quantifies the level of agreement between different coders on linguistic annotations, providing a measure of data quality and procedural consistency. |
Beyond Awareness: Overcoming Implementation Challenges and Resistance
Troubleshooting Guide: Frequently Asked Questions
What are the most common root causes of resistance to new protocols?
Resistance emerges from both individual and organizational sources. The table below summarizes the primary causes identified through research [45] [46]:
| Cause Category | Specific Causes | Manifestations in Research Settings |
|---|---|---|
| Individual Factors | Fear of the unknown [45] [46] | Anxiety about new methodologies, uncertainty about proficiency with new tools |
| Lack of awareness [45] | Not understanding the scientific rationale for new analytical protocols | |
| Job security concerns [45] | Fear that new techniques could make existing skills obsolete | |
| Organizational Factors | Poor communication [47] [46] | Insufficient explanation of why a new methodology is being adopted |
| Leadership attitudes [45] | Principal investigators or lab directors sending mixed messages about change | |
| Cultural inertia [46] | Clinging to established lab protocols and "the way we've always done it" |
How can we proactively prevent resistance when implementing new analytical methods?
Preventing resistance is more effective than reacting to it. Research shows several key strategies [45]:
- Resistance-prevention planning: Conduct readiness assessments before rollout and engage key stakeholders early.
- Raising awareness: Clearly and transparently communicate the reasons and benefits for the change.
- Unifying technical and people sides: Ensure that project management (the technical side) and change management (the people side) are aligned.
- Comprehensive training and support: Build employees' knowledge and skills through tailored programs and ongoing support.
- Active and visible leadership: Leaders must champion the change, model desired behaviors, and build coalitions of support.
What practical actions can researchers take to minimize cognitive bias in their analysis?
Individual practitioners can take ownership of minimizing cognitive bias through specific actions [10]:
- Acknowledge universal susceptibility: Reject the fallacy that only unethical or incompetent researchers are biased [10] [4].
- Control information sequence: Analyze evidence (the unknown) before reference material (the known) where possible [10].
- Request multiple comparisons: Ask for several reference samples in a "line-up" instead of a single suspect sample to reduce inherent assumptions [31] [10].
- Document rigorously: Keep a clear, chronological account of communications and the bases for analytical decisions [10].
- Consider alternatives: Actively evaluate the possibility of alternative or opposite interpretations at each analysis stage [10].
Experimental Protocols for Bias Mitigation
Protocol 1: Linear Sequential Unmasking-Expanded (LSU-E)
Objective: To control the flow of task information to analysts in a sequence that minimizes biasing influence while maintaining transparency [10].
Methodology:
- Information Assessment: Before analysis, use LSU-E worksheets to evaluate all available information based on three parameters [10]:
- Biasing power: The information's perceived strength of influence on the analysis outcome.
- Objectivity: The information's perceived extent of variability of meaning to different individuals.
- Relevance: The information's perceived relevance to the analysis.
- Sequential Revealing: Information is released to the analyst in a staged manner. Only data essential for the current analytical step is provided.
- Documentation: The sequence of information release is meticulously documented, creating a clear record of what the analyst knew and when they knew it.
- Blinded Verification: Where feasible, a second analyst performs verification blinded to the first analyst's results and to potentially biasing contextual information [31].
Protocol 2: Quantitative Modeling of Resistance Causes
Objective: To rank the causes of resistance to innovation quantitatively, enabling the selection of targeted mitigation strategies [48].
Methodology:
- Survey Design: Develop a questionnaire for staff based on causes of resistance synthesized from literature (e.g., psychological unpreparedness, inertia, poor organizational climate) [48].
- Data Collection: Administer the survey to a relevant sample of employees. The study in Lithuanian healthcare clinics surveyed 217 employees, receiving 140 completed questionnaires [48].
- Impact Calculation: Use a quantitative modeling method to calculate the strength of the impact for each cause of resistance. This allows for the ranking of causes from most to least impactful [48].
- Strategy Assignment: Graphically map the ranked causes against suggested, targeted strategies for elimination or mitigation, forming a decision-support model for administrators [48].
Visualizing Bias Mitigation and Resistance Management
Cognitive Bias Mitigation Workflow
This diagram illustrates a systematic workflow for mitigating cognitive bias in forensic analysis, based on practitioner-recommended actions [10].
Organizational Resistance Management Strategy
This diagram outlines a proactive strategy for managing organizational resistance to change, synthesizing best practices from change management research [47] [45] [46].
The Scientist's Toolkit: Research Reagent Solutions
The following table details essential methodological "reagents" for conducting robust, bias-aware research in forensic linguistic analysis and related fields.
| Research Reagent | Function in Experiment |
|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | A structured protocol that controls the sequence and timing of information release to analysts to prevent contextual bias [10]. |
| Blinded Verification | An independent repetition of the analysis by a second researcher who is blinded to the original results and to potentially biasing case information [31] [10]. |
| Multiple Comparison Samples ("Line-ups") | Providing several known-innocent samples alongside the suspect sample during comparative analysis to reduce bias from inherent assumptions [31] [10]. |
| Cognitive Bias Mitigation Checklist | A practical list of actions for individual practitioners to implement, covering data handling, reference materials, and documentation to reduce bias impact [10]. |
| Quantitative Resistance Modeling | A method using surveys and mathematical modeling to rank the causes of resistance to change, allowing for targeted strategy selection [48]. |
| ADKAR Model | A change management framework (Awareness, Desire, Knowledge, Ability, Reinforcement) used to diagnose and address gaps in individual readiness for change [45]. |
Troubleshooting Guide: Identifying and Resolving Expert Fallacies
This guide provides a structured approach to diagnosing and mitigating cognitive biases that can compromise forensic linguistic analysis.
Problem 1: The "Bias Blind Spot" Fallacy
- User Question: "I'm a seasoned researcher. My extensive experience means my initial linguistic interpretations are almost always correct, and I'm less susceptible to bias than my colleagues. Why do I need rigorous bias mitigation protocols?"
- Underlying Fallacy: This reflects the expert immunity fallacy and the bias blind spot fallacy. The assumption that expertise alone inoculates against bias is a critical vulnerability. Cognitive biases are inherent human traits, not character flaws, and operate unconsciously. Expertise can sometimes increase reliance on cognitive shortcuts, making seasoned professionals more prone to overlooking disconfirming evidence [8].
- Diagnostic Steps:
- Self-Assessment: Acknowledge that vulnerability to bias is a human universal, not an indicator of incompetence or unethical behavior [8].
- Peer Review: Actively seek blind peer review of your analysis from a colleague working independently.
- Confirmatory Check: Re-examine your data and deliberately search for at least two alternative explanations for the linguistic patterns you've identified.
- Resolution Protocol: Implement Linear Sequential Unmasking-Expanded (LSU-E) techniques. This involves documenting your initial hypotheses before being exposed to potentially biasing contextual information (e.g., knowing which party is the prosecution vs. defense). All subsequent data analysis and interpretation should follow this documented baseline to isolate the influence of extraneous information [8].
Problem 2: Overreliance on Technological Protection
- User Question: "Our team uses a state-of-the-art machine learning model for authorship attribution with 95% accuracy. The algorithm's output is objective, so our final reports are unbiased. Is this sufficient?"
- Underlying Fallacy: This is the fallacy of technological protection. While ML models outperform manual methods in processing speed and identifying subtle patterns, they are not immune to bias [3]. They can perpetuate and even amplify biases present in their training data, leading to skewed results against certain demographic groups [8].
- Diagnostic Steps:
- Audit Training Data: Scrutinize the demographic and stylistic representativeness of the data used to train the ML model.
- Error Analysis: Conduct a breakdown of the model's errors to check for disproportionate inaccuracies linked to specific linguistic demographics or styles.
- Hybrid Analysis Check: Compare the ML output with a manual analysis focused on cultural nuances and contextual subtleties that the model may have missed [3].
- Resolution Protocol:
- Adopt a hybrid framework that integrates computational power with human expertise. Use the ML model for initial data screening but require forensic linguists to perform a final interpretation, validating the output against contextual understanding [3].
- Establish ongoing algorithmic auditing protocols to continuously assess and mitigate bias in computational tools.
Problem 3: The "Fallacious Appeal to Authority" in Literature Review
- User Question: "I am citing a well-known professor from a prestigious institution to support my methodological approach. Their reputation guarantees the validity of my argument, correct?"
- Underlying Fallacy: This is a fallacious appeal to authority. An argument's validity depends on its evidence and reasoning, not solely on the stature of the person making it [49]. The authority's expertise must be directly relevant to the claim, unbiased, and reflect consensus within the genuine expert community [50].
- Diagnostic Steps:
- Relevance Check: Is the authority an expert in the specific field of forensic linguistics, or are they speaking outside their domain? [49]
- Bias and Taint Check: Is the authority speaking sincerely, or are they paid to endorse a specific viewpoint? Is their work free from obvious bias? [50] [49]
- Consensus Verification: Does the authority's view align with the broader consensus of experts in forensic linguistics, or are they an outlier? [49]
- Resolution Protocol: Use authority to supplement sound reasoning, not replace it. Always provide the original evidence and logic that underpins the authority's claim. Actively seek out and engage with credible dissenting viewpoints to strengthen your critical analysis.
Frequently Asked Questions (FAQs)
Q1: What is the difference between a cognitive bias and intentional misconduct?
- A: Cognitive bias is an unconscious, systematic error in thinking that affects even ethical and competent practitioners. It stems from the brain's use of mental shortcuts ("fast thinking"). In contrast, intentional misconduct is a conscious, unethical act. Recognizing this difference is crucial; mitigating bias requires structured strategies, not just ethical intent [8].
Q2: Our analysis is based on statistical risk-assessment tools. Doesn't this eliminate subjectivity?
- A: No. This belief is the technological protection fallacy. Actuarial tools, while valuable, can embed bias in their design. For example, if the normative data for a linguistic risk tool is based primarily on one demographic group, it may produce biased results when applied to others. The objectivity of the statistic does not guarantee fairness in its application [8].
Q3: How can we respond when an opposing expert commits a logical fallacy, like an ad hominem attack?
- A: Several strategies exist [51]:
- Point out the irrelevance: Calmly note that an attack on a person does not address the validity of the argument.
- Ignore the attack: Refuse to engage with the personal criticism and redirect the discussion back to the substantive evidence.
- Address the audience: Remember your primary audience (e.g., the court). Frame your response to educate them on why the fallacy is a flawed form of reasoning.
- A: Several strategies exist [51]:
Q4: Why is self-awareness alone not enough to counter biases?
- A: Cognitive biases are, by definition, unconscious. The bias blind spot means we are good at spotting biases in others but poor at recognizing them in ourselves [8]. Therefore, reliance on introspection is ineffective. Mitigation requires external, structured frameworks like Linear Sequential Unmasking (LSU) and collaborative peer review processes [8].
Experimental Protocol for Bias Mitigation
Title: Protocol for Implementing Linear Sequential Unmasking-Expanded (LSU-E) in Forensic Linguistic Analysis.
Objective: To minimize the influence of contextual bias during the evidence interpretation phase of forensic linguistic analysis.
Workflow:
Methodology:
- Initial Blind Analysis: The forensic linguist is provided only with the core linguistic data to be analyzed (e.g., anonymized text samples). All contextual information (e.g., which text is from the suspect, police reports, victim statements) is withheld.
- Hypothesis Documentation: The analyst documents their initial interpretations, findings, and hypotheses based solely on this "blind" data.
- Controlled Context Reveal: Potentially biasing contextual information is sequentially and deliberately revealed to the analyst.
- Re-evaluation and Comparison: The analyst re-evaluates the data with the new context. The final conclusions are then compared against the initially documented hypotheses.
- Bias Audit: Any significant deviation from the initial hypotheses must be rigorously justified based on the linguistic evidence, not the contextual information. This step helps identify and isolate the specific influence of context.
Table 1: Key Reagents and Resources for Bias-Aware Forensic Linguistics Research
| Tool Name | Type | Primary Function | Key Consideration |
|---|---|---|---|
| Machine Learning Models (e.g., for authorship attribution) | Computational Tool | Rapidly processes large text datasets to identify subtle stylistic patterns that may escape manual review [3]. | Requires hybrid validation; must be audited for embedded biases stemming from training data [3] [8]. |
| Linear Sequential Unmasking (LSU/LSU-E) | Methodological Protocol | Minimizes contextual bias by controlling the flow of information to the analyst during evidence interpretation [8]. | A structural safeguard that does not replace expertise but structures its application to reduce noise. |
| Dror's Six Expert Fallacies Framework | Conceptual Framework | Provides a taxonomy of common false beliefs (e.g., expert immunity) that prevent professionals from acknowledging their bias vulnerability [8]. | Serves as a self-assessment checklist to cultivate essential bias awareness. |
| Structured Peer Review | Process | Provides an external check on interpretations, leveraging collective critical thinking to identify potential bias blind spots. | Must be conducted blindly and independently to be effective. |
| Cultural & Contextual Nuance Guides | Reference Material | Aids in manual interpretation, helping to maintain the superiority of human analysis in understanding cultural subtleties that algorithms miss [3]. | Critical for validating and providing context to computational outputs. |
Managing Task-Relevant vs. Task-Irrelevant Information in Linguistic Data
FAQs & Troubleshooting Guides
Frequently Asked Questions
Q1: What is the core cognitive challenge when dealing with task-irrelevant linguistic information? The core challenge is that the brain's selective attention does not fully eliminate linguistic processing of task-irrelevant speech [52]. Neural evidence indicates that even ignored speech is processed not just as sound, but linguistically, leading to competition for the brain's finite processing resources between relevant and irrelevant inputs [52].
Q2: How can I experimentally confirm that my participants are processing task-irrelevant speech linguistically and not just acoustically? You can adapt the neuroimaging method of hierarchical frequency-tagging [52]. Present structured, task-irrelevant syllable sequences at a constant rate (e.g., 4 Hz), where the syllables form coherent words (e.g., 2 Hz), phrases (e.g., 1 Hz), and sentences (e.g., 0.5 Hz). A neural response at these specific phrase and sentence frequencies in brain regions like the left inferior frontal gyrus provides objective evidence that syntactic structure-building is occurring, confirming linguistic processing of the ignored material [52].
Q3: What is a major source of contextual bias in forensic linguistic analysis, and how can it be mitigated? A major source is exposure to task-irrelevant contextual information (e.g., knowing a suspect has a prior conviction) before or during the analysis of linguistic evidence. This can unconsciously influence judgments [53]. To mitigate this, implement linear sequential unmasking, where the analyst is first exposed only to the specific data requiring comparison without any extraneous case information. Context is introduced only after an initial assessment is recorded [54] [53].
Q4: My data shows high variability in distraction susceptibility among participants. What factors should I consider? Consider the linguistic structure of your distractors. Research shows that neural tracking of attended speech in language regions is significantly more enhanced when competing with structured, intelligible task-irrelevant speech compared to random syllables [52]. This suggests distraction is not merely acoustic but stems from inherent competition for linguistic processing resources. Individual differences in cognitive control capacity are also a likely factor.
Q5: What linguistic cues are associated with deception that I can analyze in transcripts? Forensic linguistics identifies several verbal cues, though these should not be used in isolation. Common markers include [55]:
- Decreased use of first-person pronouns (e.g., "I," "me")
- Increased use of negative emotion words (e.g., "hate," "worthless")
- Increased syntactic complexity as a potential obfuscation tactic
Troubleshooting Common Experimental Issues
| Problem | Possible Cause | Solution |
|---|---|---|
| No neural tracking of task-irrelevant speech structure. | The attended task may be insufficiently engaging, allowing attention to drift. | Strengthen the primary task, e.g., use detailed comprehension questions or a speech-shadowing protocol to lock attention [52]. |
| High participant error rate in the primary task. | The competing speech may be causing excessive energetic masking (acoustic overlap). | Adjust the acoustic properties of the stimuli to reduce simple acoustic interference, ensuring the experiment tests cognitive rather than auditory selection [52]. |
| Forensic linguistic judgments are inconsistent across analysts. | Unchecked cognitive biases, such as confirmation bias, may be influencing decisions. | Introduce an objective, structured scoring framework like the B-Axioms (Behavioral Axes of Competency) to standardize evaluations based on evidence, not hunches [54]. |
| Inability to detect deception via linguistic analysis. | Relying on a single, unreliable linguistic cue. | Use a multi-faceted approach that analyzes a pattern of cues (e.g., pronoun use, emotion words, complexity) and combines it with other evidence, as no single cue is a definitive marker [55]. |
Experimental Protocols & Methodologies
Protocol 1: Dichotic Listening with Hierarchical Frequency-Tagging
This protocol is designed to objectively measure the linguistic processing of task-irrelevant speech using magnetoencephalography (MEG) or EEG [52].
1. Objective: To determine if task-irrelevant speech is processed linguistically (at a syntactic level) and to measure its competitive impact on the processing of attended speech.
2. Key Research Reagent Solutions:
| Reagent / Material | Function in the Experiment |
|---|---|
| Natural Speech Narratives | Serves as the to-be-attended stimulus, requiring sustained cognitive engagement and comprehension. |
| Structured Syllable Sequences | The experimental task-irrelevant stimulus. Syllables are ordered to form coherent words, phrases, and sentences, allowing for frequency-tagging of linguistic structures. |
| Non-Structured Syllable Sequences | The control task-irrelevant stimulus. Composed of random syllable sequences, matched for acoustic-phonetic properties but lacking linguistic structure. |
| MEG/EEG System | Provides high-temporal-resolution recording of neural activity to capture brain responses time-locked to the rhythmic structure of the stimuli. |
3. Methodology:
- Stimuli Preparation:
- Attended Stimulus: A natural, continuous speech narrative (e.g., a story) presented to one ear.
- Task-Irrelevant Stimuli: Two types, presented to the other ear:
- Structured: Syllables presented at a fixed rate (e.g., 4 Hz) but ordered to form words (e.g., 2 Hz), phrases (e.g., 1 Hz), and sentences (e.g., 0.5 Hz).
- Non-Structured: Syllables presented at the same 4 Hz rate but in a random order.
- Procedure:
- Participants are instructed to attend to the narrative in one ear and ignore the input in the other.
- They perform a demanding task on the attended speech, such as answering detailed comprehension questions.
- MEG/EEG data is recorded throughout the session.
- Data Analysis:
- Neural responses are analyzed in the frequency domain to identify peaks at the specific tagging frequencies (e.g., 0.5 Hz, 1 Hz, 2 Hz).
- The presence of these peaks in the neural signal, particularly in left inferior frontal and language-related regions, indicates that the phrasal structure of the task-irrelevant speech was processed.
- Compare the strength of the neural tracking of the attended speech between the Structured and Non-Structured distractor conditions.
The following diagram illustrates the experimental workflow and the cognitive processes involved.
Protocol 2: Minimizing Contextual Bias in Forensic Analysis
This protocol outlines a procedure for analyzing linguistic evidence while minimizing the influence of cognitive biases.
1. Objective: To obtain a pure, unbiased analysis of linguistic evidence by preventing exposure to task-irrelevant contextual information during the initial evaluation.
2. Key Research Reagent Solutions:
| Reagent / Material | Function in the Experiment |
|---|---|
| Linguistic Evidence Corpus | The core data under analysis (e.g., transcribed threats, emails). |
| Contextual Information File | Contains all potentially biasing case information (e.g., suspect background, other evidence). |
| Structured Scoring Framework (e.g., B-Axioms) | A standardized tool for evaluating competencies based on specific linguistic markers, replacing subjective "gut feel" [54]. |
| Blinded Analysis Report Form | A document for recording initial findings before unblinding. |
3. Methodology:
- Initial Blinded Phase:
- The analyst receives only the linguistic evidence requiring examination. All other contextual information is withheld.
- Using a structured framework, the analyst performs an initial assessment and records their findings on a blinded report form. This establishes a baseline judgment.
- Sequential Unmasking:
- The analyst is then provided with specific, pre-determined pieces of contextual information, one at a time.
- After each piece of information is revealed, the analyst notes if and how this new data impacts their interpretation.
- Documentation & Review:
- The entire process, from the initial blinded assessment to the final conclusion, is thoroughly documented. This creates an audit trail that enhances the transparency and validity of the analysis [53].
The logical relationship and workflow for this bias mitigation protocol is shown below.
Neural Encoding Strength Under Different Distractor Conditions
The following table synthesizes key quantitative findings from neural studies on auditory attention [52].
| Neural Metric | Condition 1 (Non-Structured Irrelevant Speech) | Condition 2 (Structured Irrelevant Speech) | Functional Interpretation |
|---|---|---|---|
| Neural Tracking of Attended Speech (in Left Inferior Frontal Regions) | Baseline strength | Enhanced strength | Competition from a structured linguistic distractor forces the brain to devote more resources to processing the target. |
| Neural Tracking of Phrasal Structure in Task-Irrelevant Speech | Not present | Present in Left Inferior Frontal and Posterior Parietal Regions | The brain automatically performs syntactic integration of the ignored speech if it is linguistically structured. |
| Participant Performance (e.g., Comprehension Accuracy) | Generally higher | Potentially lower | Increased cognitive load due to competition between two linguistic streams can impair performance on the primary task. |
Technical Support Center
Troubleshooting Guides
Guide 1: Addressing False Negatives in AI-Based De-biasing Tools
Problem Statement: An AI tool designed to flag confirmation bias in forensic reports fails to generate alerts, even when human review later identifies biased language.
Diagnosis and Resolution:
| Step | Procedure | Expected Outcome |
|---|---|---|
| 1. Verify Input Data | Check the quality and labeling of the training data used for the AI model. Ensure it includes validated examples of biased and neutral language. | Confirmation that the model was trained on a comprehensive and accurately labeled dataset [56]. |
| 2. Check Model Opacity | Use Explainable AI (XAI) techniques to generate a report on the model's decision-making process for a specific input. | A clear explanation of which features the model considered, helping to identify if it is focusing on irrelevant linguistic cues [56]. |
| 3. Calibrate Confidence Thresholds | The model's confidence threshold for triggering an alert may be set too high. Adjust this threshold based on performance testing against a known validation set. | The tool now flags suspected bias with an appropriate balance of sensitivity and specificity, reducing missed instances [56]. |
| 4. Implement Human-in-the-Loop | Establish a protocol where a percentage of the tool's "negative" outputs are routinely reviewed by a human analyst. | Creates a feedback loop to continuously identify and correct the tool's blind spots, improving future performance [56] [57]. |
Guide 2: Resolving Low User Trust in Opaque AI Systems
Problem Statement: Researchers ignore or override the suggestions of a cognitive bias mitigation tool because they do not understand its reasoning.
Diagnosis and Resolution:
| Step | Procedure | Expected Outcome |
|---|---|---|
| 1. Integrate Explainable AI (XAI) | Enable the XAI dashboard that accompanies the AI tool. Ensure it provides succinct, natural-language explanations for its suggestions. | Researchers receive clear reasons like, "This suggestion is made because the term 'obviously' may introduce overconfidence bias." [56] |
| 2. Provide Transparency Reports | Generate and make available a system card for the tool detailing its intended use, performance metrics, and known limitations. | Researchers have a clear understanding of the tool's capabilities and constraints, setting realistic expectations [56]. |
| 3. Facilitate Cognitive Diversity | Use Generative AI to generate alternative hypotheses or interpretations of the same data set, framing them as "synthetic peer review." [57] | Researchers are exposed to divergent viewpoints, which mitigates confirmation bias and demonstrates the tool's value as a collaborative partner [57]. |
Guide 3: Fixing Accessibility Failures in Data Visualization Dashboards
Problem Statement: Color-coded elements in an experimental workflow diagram (e.g., "high risk" vs. "low risk" nodes) are indistinguishable for team members with color vision deficiency (CVD).
Diagnosis and Resolution:
| Step | Procedure | Expected Outcome |
|---|---|---|
| 1. Run a Contrast Check | Use a tool like the WebAIM Contrast Checker to verify that all color pairs meet at least WCAG AA standards (a contrast ratio of 4.5:1 for normal text) [58] [59]. | A quantitative report confirming whether color choices have sufficient contrast. |
| 2. Simulate Color Vision | Use a CVD simulator (e.g., in Figma with the Stark plugin, or in Chrome DevTools) to view the diagram as a user with deuteranopia or protanopia would [60] [61]. | Visual identification of elements that rely solely on color to convey meaning. |
| 3. Apply Multiple Coding | Add secondary indicators to all color-coded information. For risk levels, this could involve using different shapes (▲■●) or distinct texture patterns (hatching, dots) in addition to color [62] [61]. | Information is fully accessible to users with any type of color vision deficiency, as it is not conveyed by color alone [60]. |
| 4. Implement Textual Labels | Directly label critical elements on the diagram. For example, instead of only a red circle, use a red circle with the text "High Risk" inside it [61]. | The meaning of the visual element is unambiguous and directly accessible to all users. |
Frequently Asked Questions (FAQs)
FAQ 1: Our AI tool for linguistic analysis meets all technical specifications. Why is it still failing to reduce cognitive bias in our team's conclusions?
This is a common fallacy: that a technologically sound tool will automatically correct for human cognitive biases. The tool itself may be functioning, but your team's confirmation bias or overconfidence bias can lead them to dismiss or misinterpret its outputs [56]. Mitigation requires a socio-technical approach:
- Structured Processes: Implement a mandatory step in your analysis workflow where researchers must document and justify why they agreed with or overrode an AI tool's suggestion [56].
- Adversarial Role-Play: Periodically, have a team member act as a "devil's advocate" using the tool's outputs to challenge the consensus hypothesis [56].
FAQ 2: We provide extensive privacy settings to our users. Why do regulators say this is not enough to ensure privacy?
This fallacy conflates the appearance of control with effective control. The "notice and consent" model is broken; it is impractical for users to read every policy, and they often have no real choice but to accept [63]. From a regulatory standpoint, true protection involves:
- Purpose Limitation: Data collected for one purpose should not be repurposed without explicit, renewed consent [63].
- Data Minimization: Collect only what is directly necessary for the service provided.
- Proactive Accountability: The burden should be on the organization to justify its data practices, not on the user to ferret them out and opt-out [63].
FAQ 3: Our charts and graphs use a color palette that passed a contrast checker. Why are they still inaccessible to some colorblind colleagues?
A contrast checker ensures luminance difference but does not guarantee that colors are distinguishable for people with CVD [61]. Two colors can have a high contrast ratio but appear identical to someone with, for example, deuteranopia.
- Solution: Never use color as the sole means of conveying information. Complement color with:
FAQ 4: We use a "colorblind-friendly" palette. Is that sufficient for accessibility?
While a step in the right direction, it is not sufficient. "Colorblind-friendly" palettes typically address the most common forms of red-green deficiency but may fail for other types like tritanopia (blue-yellow) [60] [62]. Furthermore, they do not solve the problem for users with complete color blindness (achromatopsia), who see in grayscale [62]. The only robust solution is the multi-coding strategy described above.
Experimental Data and Protocols
Table 1: Cognitive Biases in Executive Decision-Making and AI Mitigation Techniques
| Cognitive Bias | Manifestation in Forensic Analysis | AI Mitigation Technique | Empirical Validation Method |
|---|---|---|---|
| Confirmation Bias [56] | Selectively focusing on linguistic evidence that supports a pre-existing hypothesis while ignoring contradictory data. | AI-driven analytics that provide objective, data-based insights independent of human preconceptions; systems that flag low-confidence data for review [56]. | A/B testing comparing hypothesis strength before and after AI tool intervention; tracking the rate of exonerating evidence discovery [56]. |
| Overconfidence Bias [56] | Overestimating the accuracy of a linguistic profile or the conclusiveness of a text attribution. | Predictive analytics and Monte Carlo simulations to ground conclusions in probabilistic reasoning [56]. | Behavioral assessments measuring the calibration of a researcher's confidence levels against actual outcomes [56]. |
| Anchoring Bias [56] | Allowing an initial piece of evidence (e.g., a suspect's prior record) to disproportionately influence the interpretation of subsequent linguistic data. | AI models that present analysts with data in a randomized order or that generate multiple alternative starting points for analysis [56] [57]. | Simulation experiments where different "anchors" are provided to separate analyst groups, and the variance in final conclusions is measured [56]. |
Table 2: Key Research Reagent Solutions for Cognitive Bias Mitigation Research
| Reagent Solution | Function in Experimentation |
|---|---|
| Explainable AI (XAI) Framework [56] | Provides interpretable explanations for AI model outputs, enabling researchers to audit and trust the de-biasing suggestions. |
| Generative AI (GAI) for Abductive Reasoning [57] | Used to generate a diverse set of alternative hypotheses and insights, increasing cognitive diversity and challenging groupthink in strategic workshops. |
| A/B Testing Platform [56] | Allows for the empirical comparison of decision outcomes between groups using de-biasing tools and control groups, providing quantitative data on effectiveness. |
| Color Vision Deficiency (CVD) Simulator [60] [61] | A tool to visualize digital interfaces as users with different types of color blindness would see them, essential for testing the accessibility of data visualizations. |
Experimental Workflow Visualizations
Cognitive Bias Mitigation Workflow
Accessible Data Visualization Design
Developing Continuous Improvement Feedback Loops for Linguistic Analysis
Frequently Asked Questions
1. What is a continuous improvement feedback loop in linguistic analysis? A continuous improvement feedback loop is an ongoing, structured process where input on linguistic analyses is systematically collected, analyzed, acted upon, and re-evaluated [64]. In the context of forensic linguistics, this process turns feedback into actionable improvements, helping to refine methodologies and mitigate cognitive biases over time.
2. Why are these loops critical for forensic linguistic research? They are essential because cognitive biases are fundamental to human cognition and cannot be controlled by willpower or expertise alone [10] [8]. Continuous feedback provides a mechanism to implement external, structured strategies that compensate for these unconscious biases, thereby improving the fairness and accuracy of forensic mental health assessments and other linguistic analyses [8].
3. My analyses are already robust. How could bias affect them? Even highly skilled, ethical individuals are not immune to cognitive bias [10]. Experts are often vulnerable to specific fallacies, such as "expert immunity" or the "bias blind spot," which create cognitive blind spots [8]. The subjective nature of linguistic data makes it particularly prone to biasing influences [8].
4. What are the most common biasing influences in linguistic analysis? Key sources of bias include task-irrelevant contextual information (e.g., knowing a suspect's confession), data from the evidence itself (e.g., inflammatory written content), and base rate expectations [10]. Mechanisms like confirmation bias and anchoring can cause analysts to selectively attend to information that confirms their initial hypothesis [14].
Troubleshooting Guides
Issue 1: Contamination from Task-Irrelevant Information
Problem Analyst's conclusions are being influenced by knowledge of extraneous case details (e.g., that a suspect has a prior conviction), leading to confirmation bias [14].
Solution Implement an information management protocol.
- Action: Use a framework like Linear Sequential Unmasking-Expanded (LSU-E) [10]. Control the flow of information so that analysts receive only the data essential for their immediate analytical step.
- Documentation: Clearly document what information was received and when it was received during the analysis [10].
- Practical Step: If exposure to potentially biasing information occurs, document what was learned and when. This transparency is critical for assessing its potential impact [10].
Issue 2: Lack of Alternative Hypotheses
Problem Analysis converges on a single interpretation too early, failing to consider other plausible explanations.
Solution Formalize the consideration of alternatives.
- Action: At each stage of analysis, explicitly consider and evaluate the possibility of alternative or opposite interpretations [10].
- Action: Use a "line-up" of multiple comparison samples instead of a single suspect exemplar to reduce inherent assumptions of guilt [31] [10].
- Experimental Protocol: For an authorship attribution study, create a protocol that requires the analyst to test the target text against a set of documents from several potential authors, including some known to be innocent, before comparing it to the primary suspect's writing.
Issue 3: Feedback Vacuums and Lack of Correction
Problem Analysts operate in isolation, cut off from peer review and corrective feedback, allowing fallacies and biases to go unchallenged [8].
Solution Establish a structured internal feedback loop.
- Action: Implement blind verifications where a second analyst conducts an independent review without knowledge of the first analyst's conclusions [31] [10].
- Action: Schedule regular peer reviews and consultations to challenge assumptions and methodologies [8].
- Practical Step: Create a continuous improvement board (physical or virtual) where analysts can anonymously submit methodological challenges and proposed solutions for team discussion and voting [65].
Issue 4: Overreliance on Technological Protection
Problem Belief that machine learning (ML) tools or statistical algorithms completely eliminate bias, leading to uncritical use of results [8].
Solution Adopt a critical, hybrid approach.
- Action: Recognize that ML models, while powerful for processing large datasets and finding patterns, can perpetuate biases present in their training data [3] [8].
- Action: Use ML for initial processing and pattern recognition, but reserve human expertise for interpreting cultural nuances and contextual subtleties [3].
- Experimental Protocol: When using a stylometry tool, design an experiment where the tool's output is critically evaluated by a human analyst who is blinded to the tool's prediction. The analyst should look for contextual or sociolinguistic factors the model may have missed.
Data and Experimental Protocols
Table 1: Efficacy of Bias Mitigation Techniques in Forensic Analysis
| Mitigation Technique | Key Quantitative Finding | Relevant Forensic Domain |
|---|---|---|
| Using Multiple Comparison Samples ("Line-ups") | Reduced contextual bias in 4 out of 4 studies [31] | Multiple pattern evidence disciplines [31] |
| Blinded Verification | Provided independence of mind for forming own conclusions without influence from original work [10] | General forensic decision-making [10] |
| Machine Learning for Authorship | Increased attribution accuracy by 34% versus manual methods [3] | Forensic Linguistics [3] |
| Exposure to Contextual Information | Demonstrated influence on analyst conclusions in 9 of 11 studies [31] | Latent fingerprint analysis (and other domains) [31] |
Experimental Protocol: Implementing Linear Sequential Unmasking-Expanded (LSU-E)
Objective: To analyze a questioned document without being biased by task-irrelevant contextual information.
Materials:
- Questioned document (e.g., threatening letter)
- Known reference documents from persons of interest (POIs)
- LSU-E worksheet [10]
- Standardized analysis tools (e.g., linguistic analysis software)
Procedure:
- Initial Analysis: The analyst receives only the questioned document. No information about the crime, suspects, or other case details is provided.
- Document Features: The analyst performs an initial analysis, documenting all relevant linguistic features (e.g., syntax, lexicon, discourse markers) and formulating preliminary hypotheses about the author.
- Controlled Introduction of Reference Materials: The analyst is then given a "line-up" of reference documents. This set includes samples from the primary suspect mixed with samples from several other POIs.
- Comparison: The analyst compares the questioned document against all references in the line-up, documenting similarities and differences for each.
- Final Interpretation: Only after the comparisons are complete and documented does the analyst receive any task-relevant contextual information, as determined by a case manager using pre-defined evaluation parameters (biasing power, objectivity, relevance) [10].
- Final Report: The analyst integrates all information, noting the sequence in which data was received and how each piece influenced the final conclusion.
The Scientist's Toolkit: Essential Methodological Reagents
Table 2: Key Reagents for Bias-Aware Linguistic Research
| Research "Reagent" | Function in the Experimental Protocol |
|---|---|
| Linear Sequential Unmasking-Expanded (LSU-E) | A framework to control the sequence and flow of case information to analysts, minimizing premature exposure to biasing information [10]. |
| Blinded Verification | A quality control procedure where a second analyst independently repeats the analysis without knowledge of the first analyst's conclusions, ensuring independence of mind [31] [10]. |
| Evidence "Line-up" | A set of multiple known samples (including known-innocent samples) provided for comparison, reducing bias from the assumption that a single suspect sample is the source [31] [10]. |
| Machine Learning Models (e.g., Deep Learning, Computational Stylometry) | Computational tools used to rapidly process large textual datasets and identify subtle linguistic patterns that may be imperceptible to manual analysis [3]. |
| Cognitive Bias Risk Assessment Worksheet | A tool used by laboratories to identify potentially biasing situations in workflows and to document decisions on what information is provided to analysts and when [10]. |
Workflow Visualization
Measuring Impact: Validation Frameworks and Cross-Disciplinary Insights
In both forensic analysis and scientific research, cognitive biases present a significant challenge to objective decision-making. These biases are not merely a reflection of individual character but are inherent features of human cognition, often operating unconsciously even among highly trained experts [8]. The integration of artificial intelligence (AI) and machine learning (ML) into analytical processes introduces additional layers of potential bias that can perpetuate or amplify existing disparities if not properly mitigated [66]. This technical support center provides evidence-based troubleshooting guidance for researchers implementing bias mitigation strategies, with particular relevance to forensic linguistic analysis and drug development contexts where objective, unbiased analysis is paramount.
Research consistently demonstrates that effective bias mitigation requires more than good intentions; it demands structured, systematic approaches. As Dror's research on expert fallacies reveals, professionals often operate under false assumptions such as "expert immunity" or "technological protection" that create vulnerability to biased outcomes [8]. The following sections provide empirically-validated protocols and frameworks to address these challenges directly.
Frequently Asked Questions
Q: What are the most effective stages for implementing bias mitigation in AI systems? A: Evidence indicates that the preprocessing stage—addressing biases in training data before model development—shows particularly strong effectiveness [66]. Techniques such as data relabeling and reweighing at this stage have demonstrated significant potential for reducing bias while maintaining model performance. Post-processing adjustments and in-processing constraints during model training can also be effective but may involve more complex trade-offs.
Q: How do bias mitigation algorithms impact overall system performance? A: The relationship between bias mitigation and performance involves nuanced trade-offs. A comprehensive study evaluating six bias mitigation algorithms across 3,360 experiments found these techniques affect multiple sustainability dimensions differently [67]. While social sustainability (fairness) typically improves, practitioners may observe changes in computational overhead, energy consumption (environmental sustainability), and operational efficiency (economic sustainability). The specific impact varies significantly by algorithm, dataset, and implementation context.
Q: Can technological solutions alone eliminate cognitive bias in forensic analysis? A: No. Research consistently shows that technology alone cannot fully eliminate bias, particularly in complex domains like forensic linguistics or mental health assessment [8]. The "technological protection fallacy" leads professionals to over-rely on tools while underestimating how human cognition interacts with technology. Effective mitigation requires combining technological approaches with structured human decision-making processes, such as Linear Sequential Unmasking (LSU) protocols.
Q: What common pitfalls undermine bias mitigation efforts? A: Researchers frequently encounter these pitfalls:
- Bias Blind Spot: The tendency to perceive others as vulnerable to bias but not oneself [8]
- Inadequate Stakeholder Engagement: Implementing solutions without input from diverse groups affected by the system [66]
- Over-reliance on Single Metrics: Focusing exclusively on technical fairness measures while ignoring real-world impacts
- Neglecting Context: Applying mitigation techniques without understanding domain-specific implications [68]
Troubleshooting Guides
Problem: Protected Attributes Are Underrepresented in Training Data
Symptoms: Model performance disparities across demographic groups, poor generalization to minority populations, fairness metric failures.
Solution Steps:
- Conduct Bias Audit: Use specialized tools (e.g., AI Fairness 360, Fairlearn) to quantify representation gaps across PROGRESS-Plus attributes (Place of residence, Race/ethnicity, Occupation, Gender/sex, Religion, Education, Socioeconomic status, Social capital) [66].
- Implement Data Enhancement: Apply synthetic data generation techniques or strategic oversampling for underrepresented groups. Calibration deepfake technology, which modifies bias-sensitive elements while preserving decision-relevant features, has shown promise in creating balanced datasets [69].
- Apply Algorithmic Fixes: Utilize preprocessing techniques like reweighing training instances or relabeling certain data points to balance impact across groups [66].
- Validate with Diverse Test Sets: Evaluate mitigated models on holdout datasets specifically designed to stress-test performance across subgroups.
Verification: Post-mitigation, performance metrics (accuracy, precision, recall) should not vary significantly across protected attributes, with disparity measures reduced by at least 70% without substantial overall performance degradation.
Problem: Model Fairness Improvements Cause Unacceptable Performance Loss
Symptoms: Significant drops in overall accuracy/precision after bias mitigation, reduced model utility, stakeholder resistance to "fair but useless" systems.
Solution Steps:
- Multi-Objective Optimization: Frame the problem as balancing fairness and accuracy rather than treating them as mutually exclusive. Implement Pareto optimization techniques to identify optimal trade-off points [67].
- Ensemble Approaches: Combine multiple mitigation strategies rather than relying on a single technique. For example, blend preprocessing with constrained optimization during training.
- Human-in-the-Loop Validation: Integrate domain experts to evaluate whether performance trade-offs affect critical decision boundaries. In forensic contexts, maintain expert oversight for high-stakes classifications [66] [8].
- Context-Aware Thresholding: Adjust classification thresholds differentially across groups only when empirically justified and ethically defensible.
Verification: Establish acceptable performance floors before mitigation and verify that post-mitigation models remain above these thresholds while demonstrating significantly improved fairness measures (e.g., demographic parity, equalized odds).
Problem: Cognitive Biases Contaminate Human Interpretation of Model Outputs
Symptoms: Confirmation bias in evaluating algorithm recommendations, automation bias (over-relying on algorithmic outputs), discounting contradictory evidence.
Solution Steps:
- Implement Linear Sequential Unmasking-Expanded (LSU-E): Present information to analysts in structured phases, with initial data evaluation conducted blind to potentially biasing contextual information [8].
- Alternative Hypothesis Generation: Require analysts to document at least three plausible explanations for observed patterns before reaching conclusions.
- Decision Journals: Maintain detailed records of reasoning processes, including confidence levels and potentially disconfirming evidence.
- Blinded Re-review: Implement procedures for independent verification of conclusions by analysts without access to initial assessments.
Verification: Measure inter-rater reliability before and after implementation. Successful mitigation should show increased agreement between independent analysts and reduced correlation between protected attributes and outcomes.
Empirical Evidence Tables
Table 1: Effectiveness of Bias Mitigation Approaches in Primary Health Care AI (Based on 17 Studies)
| Mitigation Approach | Protected Attributes Tested | Effectiveness for Bias Reduction | Impact on Model Performance |
|---|---|---|---|
| Algorithmic Preprocessing (relabeling, reweighing) | Race/ethnicity (12 studies), Sex (10 studies) | High potential for reducing disparities | Minimal performance loss when properly implemented |
| Electronic Health Record Data Sourcing | Age, Socioeconomic status | Moderate effectiveness for data balance | Variable impact depending on data quality |
| Human-in-the-Loop Systems | Race, Sex, Age | Context-dependent effectiveness | Can improve real-world performance through expert oversight |
| Ethical Principle Implementation | Multiple PROGRESS-Plus attributes | Theoretical framework, limited empirical testing | Not quantitatively measured in most studies |
Table 2: Sustainability Trade-offs of Bias Mitigation Algorithms (3,360 Experiments)
| Sustainability Dimension | Metrics Affected | Impact of Mitigation Algorithms | Recommendations |
|---|---|---|---|
| Social Sustainability | Fairness metrics (demographic parity, equalized odds) | Consistent improvement across algorithms | Select algorithms based on specific fairness goals |
| Environmental Sustainability | Computational overhead, Energy consumption | Significant increases for most algorithms | Consider efficient preprocessing methods for large-scale deployment |
| Economic Sustainability | Resource allocation efficiency, Implementation costs | Variable effects requiring cost-benefit analysis | Evaluate total cost of ownership including fairness maintenance |
Experimental Protocols
Protocol 1: Evaluating Bias Mitigation Algorithms for Linguistic Analysis
Purpose: Systematically assess the effectiveness of different bias mitigation techniques on forensic linguistic models.
Materials:
- Language Corpora: Diverse text datasets with annotation for demographic attributes
- Evaluation Framework: Standardized fairness metrics (demographic parity, equality of opportunity)
- Computational Environment: High-performance computing resources for multiple experimental runs
Methodology:
- Baseline Establishment: Train initial model without mitigation and document performance disparities across groups.
- Mitigation Implementation: Apply multiple techniques (preprocessing, in-processing, post-processing) in controlled conditions.
- Comprehensive Evaluation: Measure both technical performance (accuracy, F1 score) and fairness metrics across protected attributes.
- Statistical Analysis: Use appropriate statistical tests to determine significant differences between approaches.
Table 3: Research Reagent Solutions for Bias Measurement Experiments
| Reagent/Material | Function in Experiment | Implementation Example |
|---|---|---|
| Calibration Deepfakes Framework | Isolating bias-sensitive elements | Modifying perceived demographic attributes in linguistic samples while preserving content [69] |
| Multi-Agent Debiasing System (MADS) | Automated bias detection and mitigation | AI agents identifying and addressing biases in analytical workflows [69] |
| PROGRESS-Plus Framework | Categorizing protected attributes | Ensuring comprehensive consideration of bias dimensions [66] |
| Linear Sequential Unmasking (LSU-E) Protocol | Controlling information disclosure | Structured revelation of contextual data to prevent cognitive contamination [8] |
Protocol 2: Cognitive Bias Mitigation in Expert Decision-Making
Purpose: Measure and reduce the impact of cognitive biases in research and forensic analysis.
Materials:
- Case Materials: Standardized decision scenarios with controlled variables
- Documentation Tools: Structured templates for hypothesis generation and evidence evaluation
- Analysis Software: Tools for detecting patterns in decision outcomes
Methodology:
- Blinded Assessment: Experts evaluate initial evidence without access to potentially biasing contextual information.
- Structured Documentation: Use standardized forms to document reasoning process before final conclusions.
- Comparative Analysis: Compare outcomes across different presentation formats and information sequences.
- Longitudinal Tracking: Monitor decision patterns over time to identify and correct emerging biases.
Experimental Workflow Visualization
Effective bias mitigation requires both technical sophistication and awareness of human cognitive limitations. The empirical evidence consistently shows that successful implementation involves: (1) addressing biases during data preprocessing stages; (2) acknowledging and planning for trade-offs between fairness and other sustainability dimensions; and (3) combining technological solutions with structured human decision-making processes to address both algorithmic and cognitive biases [66] [67] [8].
For researchers in forensic linguistics and drug development, these findings underscore the importance of implementing comprehensive bias mitigation frameworks that extend beyond technical solutions to include methodological safeguards against expert fallacies and cognitive biases. Regular auditing, stakeholder engagement, and transparent documentation of both successes and failures will advance the field toward more equitable and accurate analytical systems.
Cognitive bias presents a fundamental challenge across all forensic disciplines, potentially compromising the fairness, accuracy, and reliability of expert analyses and conclusions. These systematic errors in judgment, which operate outside conscious awareness, affect how experts collect, perceive, and interpret evidence [10]. While all forensic fields face this challenge, the approaches to recognizing, managing, and mitigating bias vary significantly between disciplines. This technical support center provides forensic linguistics researchers, scientists, and drug development professionals with practical guidance for identifying and addressing cognitive bias in their work, featuring troubleshooting guides, experimental protocols, and essential methodological tools.
Quantitative Data Comparison: Bias Susceptibility and Mitigation Efficacy
Table 1: Empirical Evidence of Cognitive Bias Across Forensic Disciplines
| Discipline | Key Bias Findings | Experimental Evidence | Impact on Accuracy |
|---|---|---|---|
| Forensic Linguistics | ML algorithms outperform manual analysis in authorship attribution by 34%, but manual methods better interpret cultural nuances [3]. | Synthesis of 77 studies reveals ML (deep learning, computational stylometry) identifies subtle linguistic patterns more effectively in large datasets [3]. | Hybrid frameworks merging human expertise with computational scalability show greatest promise for balanced accuracy [3]. |
| Broad Forensic Science | Confirmation bias significantly impacts analysts' conclusions when exposed to contextual information [31]. | Systematic review of 29 studies across 14 disciplines (including fingerprints, DNA, pathology) demonstrates bias susceptibility [31]. | Procedures limiting unnecessary information and using multiple comparison samples improve analytical accuracy [31]. |
| Forensic Psychology | Confirmation bias, anchoring, and overconfidence compromise criminal responsibility and risk assessments [70]. | Research indicates structured professional judgment tools and blind assessments reduce biased outcomes [70]. | Implementation of evidence-based mitigation strategies is essential for maintaining evaluation integrity [70]. |
Table 2: Cognitive Bias Mitigation Strategies Across Disciplines
| Mitigation Strategy | Implementation in Traditional Forensic Science | Implementation in Forensic Linguistics | Effectiveness Evidence |
|---|---|---|---|
| Information Management | Linear Sequential Unmasking-Expanded (LSU-E) controls flow of task-relevant information using biasing power, objectivity, and relevance parameters [10]. | Computational methods process linguistic data without exposure to biasing contextual case information [3]. | Reduces contextual bias by 72% in fingerprint analyses; similar benefits expected in linguistics [10] [31]. |
| Blind Verification | Second analyst performs independent verification without knowledge of first analyst's results [10]. | Machine learning models provide automated authorship attribution without human intervention [3]. | Studies show blind verification reduces conformity bias by over 60% in forensic decision-making [31]. |
| Multiple Comparisons | Administration of evidence "line-ups" with several known-innocent samples alongside suspect sample [10]. | Stylometric analysis across multiple authors rather than simple binary comparisons [3]. | Prevents inherent assumptions from single-sample comparisons; reduces false positives by approximately 45% [10] [31]. |
| Structured Protocols | Utilizes validated, standardized methods and procedures with quality assurance measures [10]. | Hybrid frameworks that merge computational analysis with human evaluation of nuanced language [3]. | Improves consistency and reliability across analyses while maintaining space for expert judgment [3] [10]. |
Troubleshooting Guides and FAQs
Frequently Asked Questions
Table 3: Frequently Asked Questions About Bias in Forensic Linguistics
| Question | Expert Answer | Key References |
|---|---|---|
| What is the most effective way to minimize contextual bias in forensic linguistic analysis? | Implement a hybrid approach: use machine learning for initial pattern detection in large datasets while reserving human experts for nuanced interpretation, applying strict protocols to control biasing information exposure during computational stages. | [3] [10] |
| How can we address algorithmic bias in machine learning approaches to forensic linguistics? | Ensure diverse and representative training datasets, employ explainable AI (xAI) techniques to understand model decisions, and conduct regular audits for biased patterns, particularly across different demographic groups. | [3] [71] |
| What practical steps can individual researchers take to reduce cognitive bias when laboratory protocols are insufficient? | Analyze evidence before reference materials, document the order of operations, consider alternative interpretations at each stage, and request multiple reference materials for comparison rather than single samples. | [10] |
| How does bias management in forensic linguistics differ from other forensic disciplines? | Forensic linguistics faces unique challenges in interpreting cultural, contextual, and pragmatic language features that resist purely computational analysis, requiring more nuanced hybrid approaches than disciplines like fingerprint analysis. | [3] [72] |
Common Experimental Issues and Solutions
Problem: Contamination from task-irrelevant contextual information
- Solution: Adapt Linear Sequential Unmasking-Expanded (LSU-E) protocols to linguistic analysis by controlling the sequence of information revelation, giving analysts only what they need when they need it [10].
Problem: Overreliance on either manual or computational methods alone
- Solution: Implement a hybrid framework where ML algorithms rapidly process large datasets to identify patterns, followed by human expert analysis focused on contextual nuances and cultural references [3].
Problem: Confirmation bias in authorship attribution
- Solution: Utilize "line-up" approaches with multiple comparison texts from various authors rather than simple suspect-author binary comparisons, and document decision criteria before analysis [10].
Problem: Algorithmic bias in machine learning models
- Solution: Apply explainable AI (xAI) techniques to understand model decisions, augment training data to address representation gaps, and continuously monitor for disparate impacts across different demographic groups [71].
Experimental Protocols for Bias Management
Protocol 1: Hybrid Human-ML Authorship Analysis
Purpose: To leverage the strengths of both computational and human analysis while minimizing their respective biases.
Materials: Text corpus, computational stylometry software, cultural reference databases, standardized documentation forms.
Procedure:
- Blinded Computational Analysis: Process questioned documents through ML algorithms without exposing analysts to biasing case context.
- Pattern Identification: Use deep learning models to identify stylistic patterns, lexical choices, and syntactic features across the corpus.
- Controlled Context Introduction: Only after computational analysis is complete, provide analysts with necessary contextual information using LSU-E parameters.
- Nuanced Interpretation: Have human experts analyze culturally-specific references, pragmatic features, and contextual appropriateness.
- Adjudication: Compare findings from both approaches, documenting points of convergence and divergence.
- Validation: Conduct blind verification of conclusions by independent analysts [3] [10].
Protocol 2: Cognitive Bias Risk Assessment for Linguistic Analyses
Purpose: To identify and address potential sources of bias throughout the analytical process.
Materials: Bias risk assessment checklist, documentation templates, multidisciplinary review team.
Procedure:
- Pre-Analysis Planning: Document decision criteria and alternative hypotheses before examining evidence.
- Source Evaluation: Identify and categorize potential biasing information (data, reference materials, contextual information).
- Sequential Unmasking: Control the flow of information to analysts based on relevance, objectivity, and biasing power parameters.
- Alternative Hypothesis Testing: Actively consider and evaluate opposite interpretations at each analytical stage.
- Transparent Documentation: Chronologically document all communications, analytical decisions, and influential factors.
- Peer Review: Implement blind verification or multidisciplinary review of conclusions [10].
Visualization of Workflows and Relationships
Bias Mitigation Workflow: This diagram illustrates the integrated human-ML approach to forensic analysis, showing key stages where bias control mechanisms are implemented.
Cognitive Bias Sources: This diagram categorizes the eight primary sources of cognitive bias in forensic decision-making according to Dror's framework, highlighting their organizational structure.
The Scientist's Toolkit: Essential Research Reagents
Table 4: Essential Research Reagents for Bias-Conscious Forensic Linguistics
| Research Reagent | Function | Application in Forensic Linguistics |
|---|---|---|
| Computational Stylometry Software | Analyzes writing style patterns across multiple parameters including lexical diversity, syntactic complexity, and collocation patterns. | Provides objective, quantifiable data for authorship attribution; reduces human bias in pattern recognition [3]. |
| LSU-E (Linear Sequential Unmasking-Expanded) Framework | Controls information flow to analysts based on biasing power, objectivity, and relevance parameters. | Manages contextual information in linguistic analysis to prevent premature conclusions and confirmation bias [10]. |
| Explainable AI (xAI) Tools | Provides transparency into AI model decision-making processes and highlights influential features in predictions. | Identifies and mitigates algorithmic bias in machine learning approaches to forensic linguistics [71]. |
| Diverse Text Corpora | Representative collections of texts across genres, demographics, and contexts for comparison and training. | Reduces algorithmic bias by ensuring ML models are trained on linguistically diverse datasets [3] [71]. |
| Bias Assessment Checklists | Structured tools for identifying potential sources of bias throughout the analytical process. | Systematically evaluates bias risks in forensic linguistic analyses and prompts mitigation strategies [10]. |
| Blind Verification Protocols | Procedures for independent analysis without knowledge of previous conclusions or biasing context. | Ensures reliability of linguistic findings through independent confirmation [10] [31]. |
Experimental Protocols for Linguistic Method Validation
This section provides detailed methodologies for key experiments that validate linguistic analysis techniques while controlling for cognitive bias.
Table 1: Experimental Protocols for Linguistic Method Validation
| Experiment Type | Core Methodology | Cognitive Bias Controls | Data Output |
|---|---|---|---|
| Corpus Studies [73] [74] | Collection and analysis of existing real-world language data (e.g., social media posts, transcripts). | Use case managers to screen for biasing contextual information; implement Linear Sequential Unmasking (LSU). [10] | Quantitative: Frequency counts, statistical patterns. [73] |
| Linguistic Elicitation [73] [74] | Working with language users to obtain translations or acceptability judgments for specific constructions. | Conduct analysis blinded to previous conclusions; evaluate evidence before reference materials. [10] [31] | Categorical: Grammaticality judgments, attested vs. unattested patterns. [73] |
| Controlled Experiments [73] [74] | Highly controlled procedures (e.g., surveys, eye-tracking) with multiple participants performing identical tasks. | Administer evidence "line-ups" with multiple samples instead of single suspect exemplars. [10] [31] | Quantitative: Reaction times, accuracy rates, behavioral metrics. [73] |
Troubleshooting Guides & FAQs
Frequently Asked Questions
Q1: My corpus data is yielding inconsistent or unexpected patterns. How can I determine if this is a genuine finding or a methodological error? First, ensure your experiment has actually failed by consulting the literature for plausible alternative explanations for your results [75]. Verify you have the appropriate controls in place. For instance, include a positive control by analyzing a linguistic phenomenon that is well-documented in your corpus type. If the expected pattern is absent in your control, there is likely a problem with your data or method [75].
Q2: During linguistic elicitation, my participant's judgments seem internally inconsistent. What could be causing this? Consider whether the participant is being influenced by a mediating language during bilingual elicitation, which can bias word order or construction choices [73]. Document all contextual factors and the participant's background, as stress, fatigue, or the testing environment can impact cognitive performance and consistency [10]. If possible, repeat the elicitation session to see if the patterns hold.
Q3: My experimental results are statistically insignificant, but I observe a trend that supports my hypothesis. How should I proceed? Avoid confirmation bias, the tendency to seek or overvalue information that confirms your pre-existing beliefs [76]. Systematically evaluate alternative interpretations for the observed trend at each stage of your analysis [10]. Consider changing one variable at a time, such as sample size or stimulus design, and document every modification and its outcome clearly [75].
Q4: I was exposed to potentially biasing contextual information about a case. What steps must I take? Transparency is critical. Clearly and concisely document what information was learned and at what point in the analytical process it was received [10]. You must also consider and evaluate the possibility of alternative or opposite interpretations of the data from that point forward [10].
Mitigating Cognitive Bias in Forensic Linguistic Analysis
Cognitive bias is a fundamental aspect of human cognition and does not imply unethical behavior or incompetence; it operates subconsciously, and experts are not immune [10] [4]. The diagram below outlines a structured workflow, Linear Sequential Unmasking-Expanded (LSU-E), designed to minimize bias.
Key Bias Mitigation Strategies
- Information Management: Control the flow of information using frameworks like Linear Sequential Unmasking-Expanded (LSU-E). This involves assessing information for its biasing power, objectivity, and relevance before releasing it to the analyst in a structured sequence [10].
- Blind Verification: Ensure that any verification of results is conducted by an analyst who is blinded to the initial findings and has the independence to form their own conclusions without influence [10] [31].
- Use of "Line-ups": During comparative analyses, present analysts with multiple known-innocent samples alongside the suspect sample, rather than a single suspect sample. This counteracts the inherent assumption that the suspect is the source [10] [31].
The Scientist's Toolkit: Essential Research Reagent Solutions
Table 2: Key Research Tools for Linguistic Analysis
| Tool Type | Specific Example | Primary Function in Analysis |
|---|---|---|
| Linguistic Corpora [73] [74] | Corpus of Contemporary American English (COCA) | Provides a large, structured collection of real-world attested language data for quantitative analysis and pattern identification. |
| Elicitation Materials [73] | Visual props, video stimuli, translation tasks | Used in targeted data collection to elicit specific linguistic constructions and obtain categorical judgments on acceptability. |
| Experimental Software [74] | Survey tools, eye-trackers, reaction time systems | Enables highly controlled experimentation to gather quantitative data on language comprehension, production, and perception. |
| Analysis & Documentation Tools | LSU-E worksheets [10] | Facilitates transparency by documenting the sequence of information receipt and the basis for analytical decisions, mitigating bias. |
Technical Support Center: Troubleshooting Cognitive Bias in Forensic Linguistic Analysis
Frequently Asked Questions (FAQs)
Q1: What is cognitive bias in the context of forensic linguistic analysis, and why is it a problem? Cognitive bias is "the class of effects through which an individual's preexisting beliefs, expectations, motives, and situational context influence the collection, perception, and interpretation of evidence" [10]. In forensic linguistics, this is not intentional misconduct; rather, these influences typically operate on a subconscious level, making them challenging to recognize and control [10]. Even highly skilled, ethical experts are not immune [10]. These biases can lead to unsupportable conclusions, miscarriages of justice, and the exclusion of evidence at trial [77]. For example, contextual bias can cause an analyst to overweight or underweight certain aspects of their analysis based on irrelevant information provided about the case [77].
Q2: What are the most common cognitive biases affecting forensic linguistic research? The most frequently discussed biases in forensic analysis include confirmation bias, contextual bias, and allegiance bias (also known as role effects) [36] [77].
- Confirmation Bias: The tendency to search for, interpret, favor, and recall information in a way that confirms one's preexisting beliefs or hypotheses [77].
- Contextual Bias: Subconscious bias that can develop when experts are given irrelevant information (e.g., that a suspect has confessed, or emotive details about a crime) which can then influence their analysis [10] [77].
- Allegiance Bias (Role Effects): The tendency for experts in an adversarial system to be biased towards finding results that favour "their side," the party that instructed them [36] [77].
Q3: A case investigator has provided me with an annotated transcript where the police have already attributed specific speech to a suspect. What should I do? You should not use this annotated transcript for your analysis. Receiving such information creates a significant risk of contextual and confirmation bias, as it provides the "answer" the police are expecting [77]. The Northern Ireland case R. v. Gleeson highlights that forensic voice comparison experts should not be given annotated transcripts, as this practice sows the seeds of potential bias and can lead to the exclusion of evidence [77]. Politely inform the investigator that to maintain the integrity and independence of your analysis, you require unannotated materials.
Q4: What practical steps can I take as an individual researcher to minimize cognitive bias in my work? Even in the absence of formal laboratory protocols, individual practitioners can take several actions [10]:
- Acknowledge Fallibility: Accept that cognitive bias is fundamental to human cognition and that experts are not immune [10].
- Control Information Flow: Avoid reading unnecessary submission documentation, communication logs, and investigative details to the extent possible [10]. If exposed to task-irrelevant information, document what was learned and when [10].
- Consider the Opposite: Actively consider and evaluate alternative or opposite interpretations at each stage of your analysis [10] [36].
- Ensure Transparency: Clearly and concisely document the bases for your analytical decisions and all communications related to the case [10].
- Manage Sequence: When comparing language samples, analyze the unknown (questioned) sample before the known (reference) sample where possible [10].
Q5: Our laboratory is developing new protocols. What high-level strategies are effective for mitigating cognitive bias? Structured methodologies and the "considering the opposite" technique are among the most positively evaluated and widely discussed approaches [36]. Other effective strategies include [10] [77]:
- Information Management: Using case managers to screen information for relevance before it reaches the analyst.
- Linear Sequential Unmasking (LSU): Controlling the sequence and timing of information release to analysts to minimize biasing influence.
- Blind Verification: Having another expert perform a verification without knowledge of the original examiner's results.
- Maintaining Independence: Experts must be appropriately distanced from investigating authorities and avoid becoming embedded in the investigation team [77].
Experimental Protocols for Bias Mitigation
The following table summarizes quantitative findings on prevalent cognitive biases from a scoping review in forensic psychiatry, which shares analogous challenges with forensic linguistics [36].
Table 1: Prevalence of Identified Cognitive Biases in Forensic Expert Literature
| Cognitive Bias Type | Prevalence in Reviewed Studies | Brief Description |
|---|---|---|
| Gender Bias | 29.2% | Judgments influenced by the perceived gender of the speaker or subject. |
| Allegiance Bias | 20.8% | Subconscious inclination to favor the side of the party that retained the expert. |
| Confirmation Bias | 20.8% | Seeking or interpreting evidence to confirm pre-existing beliefs. |
| Hindsight Bias | Not Specified | The tendency to see past events as being predictable and inevitable. |
| Cultural Bias | Not Specified | Interpretations influenced by the cultural background of the analyst or speaker. |
| Emotional Bias | Not Specified | Judgments affected by the emotional content of the material or context. |
The workflow below outlines a generalized protocol for forensic linguistic analysis, integrating key steps to mitigate cognitive bias.
The Scientist's Toolkit: Key Research Reagent Solutions
The following table details essential methodological "reagents" for robust forensic linguistic research.
Table 2: Essential Methodological Reagents for Forensic Linguistic Analysis
| Research Reagent | Function in Analysis |
|---|---|
| Validated Standardized Methods | Provides a consistent, reliable baseline for analysis, reducing variability introduced by ad-hoc procedures [10]. |
| Blind Verification Protocol | Allows a second analyst to form an independent opinion without being influenced by the original examiner's results, safeguarding against groupthink and confirmation bias [10]. |
| Evidence "Line-up" | Presenting several known-innocent language samples alongside the suspect sample reduces bias from inherent assumptions that occur when only a single sample is provided for comparison [10]. |
| Linear Sequential Unmasking (LSU-E) | A framework for controlling the sequence of information flow to practitioners, providing data at a time that minimizes its biasing influence and emphasizing transparency [10]. |
| Consider-the-Opposite Technique | A structured methodology that forces the analyst to actively seek and evaluate evidence that contradicts their initial hypothesis, mitigating confirmation bias [36]. |
| Comprehensive Documentation | Creating a detailed, chronological account of all analytical decisions and communications provides transparency and allows for auditability of the process [10]. |
Troubleshooting Guides and FAQs
Troubleshooting Common Experimental Challenges
Q: Our manual linguistic analysis yields inconsistent results between different analysts. How can we improve reliability? A: Inconsistency often stems from cognitive biases like confirmation bias, where analysts selectively focus on data that confirms their initial hypothesis [8] [14]. To mitigate this:
- Implement Linear Sequential Unmasking (LSU) Protocols: Control the flow of information presented to analysts. Ensure they evaluate core linguistic data (e.g., n-gram frequencies, syntactic patterns) before being exposed to potentially biasing contextual case information [8] [78].
- Adopt Hybrid Human-AI Workflows: Use machine learning models for initial, large-scale pattern detection. For instance, deep learning models have been shown to increase authorship attribution accuracy by 34% compared to manual methods [3]. Human experts should then validate these findings, focusing their interpretation on the patterns flagged by the algorithm.
- Conduct Blind Verification: Have a second analyst, who is blinded to the first analyst's conclusions and the contextual details of the case, re-examine a subset of the data to check for consistency [78].
Q: Our machine learning model for authorship attribution performs well on training data but fails on new, real-world case data. What could be wrong? A: This is frequently a problem of algorithmic bias and a lack of generalizability [3] [79].
- Challenge: The model may have been trained on a dataset that is not representative of the linguistic diversity encountered in real cases, particularly for minority or lesser-resourced languages [80].
- Solution:
- Audit Your Training Data: Quantify the representation of different dialects, sociolects, and language varieties in your dataset.
- Utilize Data Augmentation: Apply techniques to increase the diversity and size of your training data, improving model robustness [80].
- Perform Cross-Validation: Rigorously test the model on held-out datasets that are demographically and linguistically distinct from the training set.
Q: How can we measure and guard against adversarial allegiance, where an analyst's conclusions may be subtly influenced by the side (prosecution or defense) that retained them? A: Adversarial allegiance is a well-documented motivational bias [14]. Quantifying it requires proactive experimental design.
- Method: Conduct within-expert comparisons. Present the same set of linguistic evidence to analysts under different contextual frames (e.g., once framed for a prosecution context and once for a defense context) and measure the variance in their conclusions or risk assessment scores [14] [81].
- Metric: Calculate the effect size of the contextual frame on the final opinion. A meta-analysis of such within-expert comparisons in forensic science has demonstrated that experts are not immune to these biasing effects [81].
★ Key Performance Metrics Table
The following table summarizes core quantitative metrics for assessing improvements in reliability and accuracy in forensic linguistic analysis.
Table 1: Key Metrics for Quantifying Reliability and Accuracy
| Metric | Definition | Application & Target | Source |
|---|---|---|---|
| Analysis Consistency Rate | The rate at which the same analyst, or different analysts, reach the same conclusion when presented with the same data at different times. | Measures internal reliability. A target of >90% is desirable for objective features (e.g., type-token ratio). [81] | |
| Authorship Attribution Accuracy | The percentage of cases where a model or analyst correctly identifies the author from a set of candidates. | Measures accuracy. ML models have shown a 34% increase in accuracy over manual analysis [3]. | |
| Pattern Detection Precision | The proportion of relevant instances among the retrieved instances (True Positives / (True Positives + False Positives)). | Measures the exactness of an AI tool. In other forensic domains, AI has achieved precision scores of 0.9 in diatom testing [82]. | |
| Bias Effect Size | A statistical measure of the strength of a biasing influence (e.g., contextual information) on an analyst's conclusion. | Quantifies objectivity. A smaller effect size indicates better bias mitigation. Can be derived from within-expert study designs [14] [81]. | |
| Algorithmic Fairness Disparity | The difference in model performance (e.g., accuracy, false positive rate) across different demographic groups. | Measures fairness. The goal is to minimize disparity, ensuring tools work equally well across populations [8] [80]. |
Experimental Protocols for Key Methodologies
Protocol 1: Testing the Efficacy of Linear Sequential Unmasking (LSU) in Linguistic Analysis
Objective: To quantitatively assess whether controlling information flow reduces confirmation bias in forensic linguistic conclusions.
Workflow Diagram: The following diagram illustrates the controlled, sequential workflow of this protocol.
Materials:
- Linguistic Corpus: A set of anonymized texts (e.g., emails, social media posts) with known ground truth.
- Case Context Packets: Separate documents containing potentially biasing information (e.g., suspect's background, other evidence).
Procedure:
- Blinded Phase: Provide the analyst with only the core linguistic data from the corpus. The analyst must document their initial authorship hypothesis and their confidence level (on a scale of 1-10).
- Unmasking Phase: Reveal the contextual case information packet to the analyst.
- Final Phase: The analyst documents their final conclusion and updated confidence level.
- Data Analysis: Calculate the "Conclusion Shift Rate"—the percentage of analyses where the final conclusion differed from the initial blinded hypothesis. A lower rate in an LSU group compared to a control group (which receives all information at once) indicates the protocol's effectiveness in reducing bias [8] [78].
Protocol 2: Validating a Hybrid Human-AI Authorship Analysis Pipeline
Objective: To benchmark the accuracy and efficiency gains of a workflow that combines machine learning pre-screening with expert human validation.
Workflow Diagram: This diagram outlines the sequential and iterative steps of the hybrid validation protocol.
Materials:
- Computational Resources: Access to a pre-trained NLP model for stylistic feature extraction (e.g., a transformer model) [3] [80].
- Validation Interface: A software tool that allows human experts to easily review the AI-flagged patterns and underlying data.
Procedure:
- AI Processing: The entire text corpus is processed by the ML model to extract stylistic features and identify salient patterns or anomalies. The model outputs a set of candidate markers for authorship.
- Expert Validation: The human expert is presented with the AI-generated markers. The expert's role is to test these markers against alternative hypotheses, assess their contextual validity, and interpret them within the framework of the case [3] [79].
- Metric Tracking: Record the time-to-completion for the entire analysis and the final accuracy against ground truth. Compare these metrics to those from a manual-only analysis. The expected outcome is a significant reduction in human analysis time with maintained or improved accuracy, as AI handles the initial data-heavy lifting [3] [83].
The Scientist's Toolkit: Essential Research Reagents
Table 2: Key Research Reagent Solutions for Forensic Linguistics
| Item | Function in Experimental Design |
|---|---|
| Curated Text Corpora | Provides the foundational "substrate" for analysis. Must be representative, annotated with ground truth, and contain diverse linguistic demographics to test generalizability and algorithmic bias [3] [80]. |
| Computational Stylometry Tools | Software or algorithms that quantify an author's unique writing style (e.g., via syntax, word frequency). Serves as the objective baseline measurement against which human bias is tested [3] [79]. |
| Bias Introduction Protocols | Standardized scripts or information packets used to deliberately introduce cognitive biases (e.g., contextual case details, emotional language) in controlled experiments [8] [14]. |
| Blinding Frameworks | Experimental protocols designed to hide biasing information from analysts. This is a critical control reagent for establishing a baseline of objective performance [78]. |
| Inter-Rater Reliability (IRR) Metrics | Statistical tools (e.g., Cohen's Kappa, Intraclass Correlation Coefficient) used to quantify the consistency of conclusions between different analysts, measuring the reliability of the method itself [81]. |
Conclusion
Mitigating cognitive bias in forensic linguistic analysis requires more than individual vigilance—it demands systematic procedural safeguards and organizational commitment. The integration of frameworks like Linear Sequential Unmasking, blind verification, and structured hypothesis testing provides a robust foundation for enhancing objectivity. Future directions should focus on developing discipline-specific validation protocols, addressing emerging challenges in digital and multilingual contexts, and fostering cross-disciplinary collaboration. As forensic linguistics continues to evolve, embedding these evidence-based practices will be crucial for maintaining scientific rigor and upholding justice through reliable language analysis.
References
- 1. Towards Detecting and Mitigating Cognitive Bias in ... [https://arxiv.org/html/2405.12480v1]
- 2. How to Get Rid of the Belief Bias: Boosting Analytical Thinking ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7909186/]
- 3. An evolution of forensic linguistics: From manual analysis ... [https://www.sciencedirect.com/science/article/pii/S2665910725000131]
- 4. A Forensic Science-Based Model for Identifying and ... [https://jaapl.org/content/53/2/172]
- 5. Cognitive and Human Factors in Expert Decision Making [https://pubmed.ncbi.nlm.nih.gov/32508089/]
- 6. EXPERTS ARE NOT IMMUNE FROM COGNITIVE BIASES [https://law.temple.edu/aer/2020/11/14/experts-are-not-immune-from-cognitive-biases/]
- 7. Biased language in clinical handoffs may negatively impact ... [https://www.uchicagomedicine.org/forefront/research-and-discoveries-articles/2024/december/biased-language-in-clinical-handoffs-may-negatively-impact-patient-care]
- 8. A Forensic Science-Based Model for Identifying and ... [https://jaapl.org/content/early/2025/05/05/JAAPL.250019-25]
- 9. Cognitive Bias Affects Perception and Decision-Making in ... [https://www.mdpi.com/2076-328X/15/8/1094]
- 10. Reducing the impact of cognitive bias in decision making [https://pmc.ncbi.nlm.nih.gov/articles/PMC10319185/]
- 11. Developing Effective Methods for Addressing Contextual Bias ... [https://nij.ojp.gov/library/publications/developing-effective-methods-addressing-contextual-bias-forensic-science]
- 12. A Comprehensive Benchmark for Evaluating Bias in Large ... [https://arxiv.org/html/2406.14194v2]
- 13. Bias and fairness in software and automation tools ... [https://www.oaepublish.com/articles/jsss.2023.41]
- 14. Fighting for objectivity: Cognitive bias in forensic ... [https://paloaltou.edu/resources/translating-research-into-practice-blog/fighting-objectivity-cognitive-bias-forensic-examinations/]
- 15. Preliminary evidence of linguistic bias in academic reviewing [https://www.sciencedirect.com/science/article/pii/S1475158520301685]
- 16. From System 1 to System 2: A Survey of Reasoning Large ... [https://arxiv.org/abs/2502.17419]
- 17. Thinking, Fast and Slow: System 1 and System 2 AI [https://www.reliant.ai/blog/ai-system-1-vs-system-2-thinking]
- 18. Cognitive Biases in Large Language Models: A Survey and ... [https://arxiv.org/html/2412.00323v1]
- 19. System 1 and System 2 – Prolog and Knowledge Graphs vs ... [https://eugeneasahara.com/system-1-and-system-2-prolog-and-knowledge-graphs-vs-llms/]
- 20. Evaluating the o1 reasoning large language model for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12372181/]
- 21. A practical approach to mitigating cognitive bias effects in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11720873/]
- 22. Research Hub for Language in Forensic Evidence [https://arts.unimelb.edu.au/school-of-languages-and-linguistics/our-research/research-centres-hubs-and-units/research-hub-for-language-in-forensic-evidence]
- 23. Forensic Linguistics Information Guide [https://www.all-about-forensic-science.com/forensic-linguistics.html]
- 24. Forensic linguistics | Intro to the Study of Language Class ... [https://fiveable.me/introduction-study-language/unit-15/forensic-linguistics/study-guide/MTJhoceghJ1mflfi]
- 25. Linear Sequential Unmasking–Expanded (LSU-E) [https://pmc.ncbi.nlm.nih.gov/articles/PMC8385162/]
- 26. Sequential Unmasking [https://www.bioforensics.com/download-articles/sequential-unmasking/]
- 27. Utilising linear sequential unmasking to minimise bias in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10884628/]
- 28. A New Information Management Tool Available to Guide ... [https://forensicstats.org/news-posts/a-new-information-management-tool-available-to-guide-forensic-decisions-and-mitigate-bias/]
- 29. A Practical Tool for Information Management in Forensic ... [https://wcsj.law.duke.edu/publications/a-practical-tool-for-information-management-in-forensic-fecisions-using-linear-sequential-unmasking-expanded-lsu-e-in-casework/]
- 30. Ensuring Consistency in Forensic Competency Evaluations [https://paloaltou.edu/resources/translating-research-into-practice-blog/ensuring-consistency-in-forensic-competency-evaluations]
- 31. Cognitive bias research in forensic science: A systematic ... [https://www.sciencedirect.com/science/article/pii/S0379073818304559]
- 32. The Art of Troubleshooting for Customer Support ... [https://www.helpscout.com/helpu/art-of-troubleshooting-support/]
- 33. The complete guide to customer service troubleshooting [https://devrev.ai/blog/customer-service-troubleshooting]
- 34. Alternative hypothesis [https://en.wikipedia.org/wiki/Alternative_hypothesis]
- 35. Null and Alternative Hypotheses | Definitions & Examples [https://www.scribbr.com/statistics/null-and-alternative-hypotheses/]
- 36. Cognitive biases in forensic psychiatry: A scoping review [https://www.sciencedirect.com/science/article/pii/S0160252725000160]
- 37. Reducing the impact of cognitive bias in decision making [https://www.sciencedirect.com/science/article/pii/S2589871X23000281]
- 38. New approach to police lineups measures strength of ... [https://today.usc.edu/improved-police-lineups-usc-research-criminal-justice-eyewitness-memory/]
- 39. Suspect identification accuracy from lineups, in the lab and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12449283/]
- 40. Suspect identification accuracy from lineups, in the lab and in ... [https://cognitiveresearchjournal.springeropen.com/articles/10.1186/s41235-025-00670-1]
- 41. Comparing multiple comparisons: practical guidance for choosing the best multiple comparisons test - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC7720730/]
- 42. Multiple comparisons problem - Wikipedia [https://en.wikipedia.org/wiki/Multiple_comparisons_problem]
- 43. Delays reduce culprit-presence detection but do not affect ... [https://www.nature.com/articles/s41598-025-13937-w]
- 44. The Steps [https://www.structureddecisionmaking.org/the-steps/]
- 45. The Complete Guide Managing Resistance to Change [https://www.prosci.com/managing-change-resistance]
- 46. Resistance to organizational change: Some causes and ... [https://www.ciat.org/ciatblog-resistencia-al-cambio-organizacional-algunas-causas-y-propuestas-para-manejarla/?lang=en]
- 47. Overcoming 3 Common Barriers to Organizational Change [https://online.hbs.edu/blog/post/organizational-barriers-to-change]
- 48. Novel Approach to the Actions for Causes Elimination of ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9091473/]
- 49. Chapter 16. Fallacies of Expertise | Critical Thinking, Logic, ... [https://read.aupress.ca/read/critical-thinking-logic-and-argument/section/37569f83-38fb-40e0-9575-ede2c97e5753]
- 50. How to Argue Against Common Fallacies [https://www.futurelearn.com/info/courses/logical-and-critical-thinking/0/steps/9131]
- 51. Unmasking Logical Fallacies: A Guide for Recognizing and ... [https://tennesseelawreview.org/blogpostunmaskinglogicalfallacies/]
- 52. Linguistic processing of task-irrelevant speech at a cocktail ... [https://elifesciences.org/articles/65096]
- 53. Assessing Cognitive in Bias Decisions: A Review and Outlook Forensic [https://pubmed.ncbi.nlm.nih.gov/31693180/]
- 54. Technical Interview Evaluations: Eliminating Bias with Cognitive ... [https://www.linkedin.com/pulse/technical-interview-evaluations-eliminating-bias-cognitive-3ztde]
- 55. The Brain Behind Language Crimes [https://www.numberanalytics.com/blog/neuroscience-forensic-linguistics]
- 56. Cognitive Bias Mitigation in Executive Decision-Making [https://www.mdpi.com/2079-9292/14/19/3930]
- 57. Using Generative AI to Mitigate Cognitive Biases in ... [https://papers.ssrn.com/sol3/papers.cfm?abstract_id=5476486]
- 58. Contrast Checker [https://webaim.org/resources/contrastchecker/]
- 59. Color Contrast Checker | Boost Readability For All Users ✅ [https://www.levelaccess.com/color-contrast-checker-new/]
- 60. Designing for Color Blindness in UI Design [https://atmos.style/blog/color-blindness-in-ui-design]
- 61. Adapting User Interfaces for Colorblind Users [https://medium.com/rubrik-design/adapting-user-interfaces-for-colorblind-users-from-theory-to-practice-e020ce92d082]
- 62. A Designer's Life with Color Vision Deficiency [https://alistapart.com/article/a-designers-life-with-color-vision-deficiency/]
- 63. Discussing Privacy Fallacies: Concluding Thoughts [https://www.naag.org/attorney-general-journal/discussing-privacy-fallacies-concluding-thoughts/]
- 64. How to Create a User Feedback Loop [https://getthematic.com/insights/building-effective-user-feedback-loops-for-continuous-improvement]
- 65. A Practical Guide to Continuous Feedback at Work [https://www.betterworks.com/magazine/continuous-feedback/]
- 66. Bias Mitigation in Primary Health Care Artificial Intelligence ... [https://www.jmir.org/2025/1/e60269/]
- 67. Examining the impact of bias mitigation algorithms on ... [https://www.sciencedirect.com/science/article/pii/S0164121225001268]
- 68. Ethical Data Visualisation: Avoiding Bias and ... [https://medium.com/@harry.trivedi/ethical-data-visualization-avoiding-bias-and-misinformation-in-your-charts-and-graphs-02b1f506f68f]
- 69. Empirical Analysis and AI Agentic Framework for Bias ... [https://papers.ssrn.com/sol3/papers.cfm?abstract_id=5679425]
- 70. COGNITIVE BIAS IN FORENSIC PSYCHOLOGICAL EVALUATIONS: IMPLICATIONS, CHALLENGES, AND MITIGATION STRATEGIES | FARS International Journal of Education, Social Science & Humanities. [https://farspublisher.com/index.php/fars/article/view/441]
- 71. Making sense of AI: bias, trust and transparency in pharma ... [https://www.drugtargetreview.com/article/183358/making-sense-of-ai-bias-trust-and-transparency-in-pharma-rd/]
- 72. Applied Linguistics and Law: A Review of Forensic ... [https://assajournal.com/index.php/36/article/view/886]
- 73. 4.2. Methods of data collection – The Linguistic Analysis ... [https://pressbooks.openedmb.ca/wordandsentencestructures/chapter/methods-of-data-collection/]
- 74. Essential Research Methods in Applied Linguistics for ... [https://atlasti.com/research-hub/research-method-in-applied-linguistucs]
- 75. Troubleshooting Protocols - Biological Sciences: Summer ... [https://guides.library.cmu.edu/biologicalsciencesSRI/troubleshooting]
- 76. What Is Cognitive Bias? 7 Examples & Resources (Incl. ... [https://positivepsychology.com/cognitive-biases/]
- 77. Cognitive Bias and Forensic Experts: Preserving ... [https://www.jonathanhak.com/2023/07/27/cognitive-bias-and-forensic-experts-preserving-independence-and-learning-to-say-no/]
- 78. Forensic Confirmation Bias (Cognitive Bias in Forensics) [https://www.news-medical.net/life-sciences/Forensic-Confirmation-Bias-(Cognitive-Bias-in-Forensics).aspx]
- 79. Language as Evidence: The History and Present of ... [https://constitutionaldiscourse.com/language-as-evidence-the-history-and-present-of-forensic-linguistics-in-the-age-of-ai/]
- 80. Introduction to the special issue Forensic Linguistics in... [https://www.degruyterbrill.com/document/doi/10.1515/lass-2025-0055/html?srsltid=AfmBOopYlaTWmwRCPMnpKX_KqxFnQITr9FZohYofRIQ0wSC4VcUYzd-s]
- 81. Meta-analytically quantifying the reliability and biasability ... [https://pubmed.ncbi.nlm.nih.gov/18489557/]
- 82. The application of artificial intelligence in forensic pathology [https://pmc.ncbi.nlm.nih.gov/articles/PMC12328379/]
- 83. SoK: Exploring the Potential of Large Language Models for ... [https://arxiv.org/html/2402.19366v1]