Navigating Budget Constraints in Forensic Technology: Strategic Implementation and TRL Scaling for Researchers
This article addresses the critical challenge of implementing advanced forensic technologies amid significant budget constraints, providing researchers and forensic professionals with strategic frameworks for Technology Readiness Level (TRL) scaling.
Navigating Budget Constraints in Forensic Technology: Strategic Implementation and TRL Scaling for Researchers
Abstract
This article addresses the critical challenge of implementing advanced forensic technologies amid significant budget constraints, providing researchers and forensic professionals with strategic frameworks for Technology Readiness Level (TRL) scaling. Drawing on current market analysis and sustainable forensic frameworks, we explore cost-effective implementation methodologies, troubleshooting common financial barriers, and validation approaches that maintain scientific rigor while optimizing resources. With the global forensic technology market projected to reach $18.025 billion by 2030 yet facing systemic funding crises in many jurisdictions, this comprehensive guide offers practical solutions for maximizing technological impact within limited budgets, particularly focusing on digital forensics, rapid DNA analysis, and AI integration.
Understanding the Forensic Technology Funding Landscape and Budgetary Pressures
Forensic science is navigating a critical juncture, caught between groundbreaking technological potential and a severe, systemic funding shortfall. This resource crisis directly impacts the capacity of research institutions and forensic laboratories to adopt new technologies, validate methods, and scale innovations from basic research to practical implementation. An analysis of data from UK Research and Innovation (UKRI), the United Kingdom's premier public funding body for science, quantifies this deficit with stark clarity. Between 2009 and 2018, forensic science research secured only £56.1 million from UKRI research councils, representing a mere 0.01% of the total UKRI budget allocated over that decade [1] [2] [3]. This technical support center addresses the specific, practical challenges that researchers and scientists face in this constrained environment, providing troubleshooting guides for experiments hampered by limited resources and offering strategies for navigating the "valley of death" between research and development (R&D) and operational deployment.
Quantitative Analysis of UKRI Forensic Science Funding
The following tables break down the UKRI funding data to reveal the strategic priorities and significant gaps in research investment.
Table 1: Overall UKRI Forensic Science Research Funding (2009-2018)
| Metric | Value |
|---|---|
| Total Number of Projects | 150 |
| Cumulative Project Value | £56.1 million |
| Percentage of Total UKRI Budget | 0.01% |
| Projects with Dedicated Forensic Science Aims | 69 (46.0% of projects) |
| Value of Dedicated Forensic Science Projects | £17.2 million |
Table 2: Funding Distribution by Research Type and Evidence Focus
| Category | Funding Amount | Percentage of Total Forensic Funding | Number of Projects |
|---|---|---|---|
| By Research Type | |||
| Technological Development | £37.2 million | 69.5% | 91 |
| Foundational Research | £10.7 million | 19.2% | 27 |
| By Evidence Type | |||
| Digital & Cyber | £14.4 million | 25.7% | 33 |
| DNA & Genetics | £2.9 million | 5.1% | 13 |
| Fingerprints | £0.7 million | 1.3% | 2 |
The data reveals a pronounced imbalance, with a heavy focus on short-term technological outputs over the foundational research required to ensure their robustness and long-term validity [1] [4]. Furthermore, traditional forensic evidence types like fingerprints and DNA have been significantly underfunded compared to emerging areas like digital forensics [2] [3].
Troubleshooting Guides and FAQs for Researchers
This section addresses common operational problems exacerbated by budget constraints and the lack of scalable funding pathways.
FAQ 1: Our research demonstrates a promising new DNA collection method, but we cannot secure funding for the large-scale validation studies required for market adoption. What options exist for bridging this "valley of death"?
Answer: The gap between successful research and commercially viable, court-ready technology is a well-documented consequence of systemic underfunding. Consider these approaches:
- Strategic Stakeholder Engagement: Proactively build a network of forensic practitioners, commercial suppliers, and legal representatives. As demonstrated by the SCAnDi project, hosting workshops and regular meetings ensures technical development remains aligned with end-user needs and can open pathways to alternative funding or pilot study opportunities [5].
- Targeted Funding Calls: Diligently monitor calls from innovation-focused bodies like Innovate UK, which may have specific programs for scaling near-market technologies, unlike pure research councils [6].
- Phased Validation: Design your research project with a clear, modular pathway. Initial proof-of-concept studies can be conducted with research grants, with subsequent phases explicitly designed to gather the data required for commercial and regulatory approval, making the project more attractive to later-stage funders.
FAQ 2: How can we improve the success rate of grant applications for foundational forensic science research, which seems to be chronically undervalued?
Answer: The data confirms that foundational research received less than a fifth of the dedicated forensic science budget [1]. To improve success rates:
- Articulate Systemic Value: Frame your proposal to demonstrate how the foundational science addresses a root cause of a known crisis in forensic science (e.g., the reproducibility of evidence), rather than just a symptomatic technological fix. Emphasize the long-term value and cost-saving potential for the entire criminal justice system [4].
- Interdisciplinary Alignment: While advocating for forensic science as a coherent discipline, leverage its interdisciplinary nature. Partner with established departments (e.g., chemistry, biology, computer science) to submit proposals through funding streams with larger budgets, while ensuring the core forensic science question remains central.
- Pilot Data is Key: Even for foundational work, use low-cost preliminary studies or computational modeling to generate pilot data that de-risks the proposal for reviewers.
FAQ 3: Budget cuts are preventing our lab from updating to the latest equipment. How can we maintain research productivity with outdated instrumentation?
Answer: This is a pervasive issue, with laboratories often unable to purchase new equipment due to funding cuts or pauses [7].
- Collaborative Resource Sharing: Establish formal or informal consortia with neighboring university departments or research institutes to access their core facilities and high-end equipment.
- Focus on Data Analysis: Invest in computational skills and infrastructure. Often, more value can be extracted from existing datasets through advanced bioinformatics or AI-driven re-analysis than from generating new data with old equipment [8].
- Open-Source and Modular Tools: Explore the use of open-source hardware and software solutions for specific tasks, which can be more affordable and customizable than commercial black-box systems.
Featured Experimental Protocol: Single-Cell DNA Analysis for Complex Mixtures
This protocol, inspired by the UKRI-funded SCAnDi project, details a methodology for deconvoluting complex DNA mixtures, a common challenge in forensic casework that can be hindered by backlogs and resource limitations [9] [5].
Objective: To isolate and generate DNA profiles from individual cells within a mixed biological sample to attribute DNA to specific donors.
Principle: Combining single-cell isolation techniques with established DNA profiling methods to overcome the limitations of bulk analysis, which loses cell-of-origin information.
Materials and Reagents:
- Laser Capture Microdissection (LCM) system or Imaging Cell Sorter: For precise isolation of individual cells based on morphological characteristics.
- Microfluidic platforms: For automated processing of single cells.
- Lysis Buffer: A specialized buffer to break open individual cells without degrading DNA.
- Whole Genome Amplification (WGA) Kit: For amplifying the minute quantity of DNA from a single cell to a workable amount for profiling.
- STR Profiling Kit or Next-Generation Sequencing (NGS) Library Prep Kit: Depending on the desired downstream analysis (traditional databases or advanced sequencing).
- Artificial Mixture Cells: Cultured cells from known donors to validate the protocol.
Procedure:
- Sample Preparation: Create an artificial mixture of epithelial cells from two or more donors. Suspend in an appropriate buffer.
- Single-Cell Isolation:
- Option A (LCM): Smear the cell mixture on a specialized membrane slide. Use the LCM system to visually identify and isolate single cells by cutting and capturing them into a microfuge tube cap.
- Option B (Imaging Cell Sorter): Use a cell sorter that incorporates imaging to select and deposit single cells into a multi-well plate based on size, shape, or fluorescent markers.
- Cell Lysis and DNA Release: Add a small volume of lysis buffer to each isolated cell. Incubate to release genomic DNA.
- Whole Genome Amplification: Transfer the lysate to a microfluidic device or tube for WGA. Perform amplification according to the kit protocol to generate sufficient DNA for analysis.
- DNA Profiling:
- STR Pathway: Use a portion of the WGA product for PCR with a standard STR multiplex kit. Analyze the fragments on a capillary electrophoresis instrument.
- NGS Pathway: Prepare a sequencing library from the WGA product. Sequence on a suitable NGS platform and analyze the data for STRs and single nucleotide polymorphisms (SNPs).
- Data Analysis: Compare the single-cell DNA profiles to reference samples from the donors. The successful deconvolution is indicated by obtaining single-source profiles from individual cells within the mixture.
Troubleshooting:
- Low DNA Yield after WGA: Optimize lysis conditions and ensure the WGA reaction is performed on a clean, concentrated single cell. Include positive and negative controls.
- Allelic Dropout (STRs): A common issue in single-cell analysis. Consider using a dedicated, validated single-cell STR assay or switch to an NGS approach, which can be more tolerant of imbalanced amplification.
- Contamination: Implement rigorous cleaning protocols and use UV irradiation in workstations to destroy ambient DNA. Include negative controls at the single-cell isolation step.
Workflow and Systemic Analysis Diagrams
The following diagrams visualize the experimental protocol and the broader systemic challenges.
Diagram 1: Single-Cell DNA Analysis Workflow
Diagram 2: Systemic Impact of Forensic Science Underfunding
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials for Advanced Forensic DNA Analysis
| Reagent / Solution | Function | Key Considerations for Budget Constraints |
|---|---|---|
| Magnetic Bead-Based DNA Extraction Kits | Selective binding and purification of DNA from complex samples. | Prefer automated systems to reduce hands-on time and improve throughput, mitigating staff shortages [8]. |
| Whole Genome Amplification (WGA) Kits | Amplifying genome-wide DNA from single or low-copy number templates. | Essential for single-cell and low-template DNA workflows. Critical for maximizing data from scarce evidence. |
| STR Multiplex PCR Kits | Simultaneous amplification of multiple Short Tandem Repeat loci for database-compatible profiling. | The standard for most labs. Ensure any novel method (e.g., single-cell) maintains compatibility with these core kits [5]. |
| Next-Generation Sequencing (NGS) Library Prep Kits | Preparing DNA for massively parallel sequencing to access SNP/STR data and more. | Offers more information from degraded mixtures but at a higher cost. Requires significant investment in bioinformatics. |
| Lysis Buffers for Single Cells | Breaking open individual cells while preserving DNA integrity. | Formulations are critical for success in single-cell genomics. In-house optimization can reduce costs. |
| Microfluidic Chips/Cartridges | Automating and miniaturizing reactions (e.g., DNA extraction, PCR) for portability and efficiency. | Represents a high initial investment but can reduce long-term reagent consumption and improve reproducibility [8]. |
Technical Support Center
This support center provides resources for researchers and scientists navigating the challenges of implementing and validating forensic technologies in an environment of significant budget constraints.
Frequently Asked Questions (FAQs)
Q1: Our laboratory faces budget cuts while the market for new forensic technologies grows. How can we justify investment in new instruments? Justification requires a focus on long-term operational efficiency and demonstrable return on investment. Emphasize how new technologies can reduce analysis time, automate manual processes, and improve throughput, thereby offsetting initial costs over time. Frame proposals around specific, high-priority needs, such as addressing backlogs in digital forensics or improving the sensitivity of DNA analysis to solve more cases with less sample. Highlight how modern equipment can reduce the risk of errors and subsequent costly legal challenges [10].
Q2: What are the key legal standards a new forensic method must meet before it can be used in casework? Before implementation, a new method must meet rigorous legal standards for admissibility as evidence. In the United States, this is governed by the Daubert Standard (or the Frye Standard in some states), which requires that the technique has been tested, peer-reviewed, has a known error rate, and is generally accepted in the scientific community. In Canada, the Mohan Criteria govern admissibility based on relevance, necessity, the absence of exclusionary rules, and a properly qualified expert [10]. Always consult with your legal department to ensure compliance with local jurisdiction requirements.
Q3: We are considering implementing a new technique like Comprehensive Two-Dimensional Gas Chromatography (GC×GC). What is its current readiness level for routine casework? GC×GC is a powerful research tool with high peak capacity for complex mixtures like illicit drugs, toxicological evidence, and ignitable liquid residues. However, its Technology Readiness Level (TRL) for routine forensic casework is still developing. Key barriers to routine implementation include the need for extensive intra- and inter-laboratory validation studies, the establishment of standardized methods, and the determination of known error rates to meet legal admissibility standards like the Daubert Standard [10]. It is currently more suited to advanced research applications rather than routine evidence processing.
Q4: How can we manage the increasing volume of digital evidence with limited resources and staff? The surge in digital evidence is a major market driver [11]. To manage this, prioritize investments in forensic software solutions that incorporate automation, artificial intelligence (AI), and machine learning. These tools can help process large datasets more quickly and accurately, reducing the manual burden on limited staff. Furthermore, leveraging cloud-based solutions and exploring partnerships with private forensic service providers can help manage workflow peaks without the need for immediate capital expenditure on new hardware and additional full-time staff [11] [12].
Q5: A key piece of our instrumentation has failed, and we lack the budget for a like-for-like replacement. What are our options? First, explore service contracts and manufacturer support for repair. If replacement is unavoidable, consider:
- Refurbished Instruments: Purchasing certified refurbished equipment from reputable vendors can offer significant cost savings.
- Collaborative Partnerships: Partner with nearby university laboratories or other government agencies to share access to essential equipment.
- Reagent & Consumable Management: Audit current reagent and consumable usage to identify potential cost savings, which can be reallocated [13].
- Grants and Funding Opportunities: Actively monitor for new grant announcements from federal and state agencies, as funding priorities can shift [14].
Troubleshooting Guides
Guide: Troubleshooting Instrument Validation Under Budget Constraints
Problem: Difficulty conducting full validation studies for new methods or instruments due to limited funding for overtime, reference materials, and dedicated instrument time.
Background: Method validation is a non-negotiable requirement for forensics, but budget cuts can make this process challenging [7].
Solution:
- Phased Validation Approach: Break the validation into smaller, manageable phases funded across multiple budget cycles. Begin with critical parameters like specificity and precision.
- Leverage Vendor Data: Request comprehensive validation data from instrument and reagent manufacturers. While not a substitute for in-house verification, this can reduce the scope of testing required.
- Collaborative Inter-Laboratory Studies: Partner with other laboratories to share the workload and cost of validation studies. This also strengthens the data by incorporating multiple data points.
- Utilize Free Proficiency Tests: Use proficiency testing samples from quality assurance programs, like those offered by the Center for Forensic Sciences at RTI International, for additional method performance data at low cost [15].
Guide: Troubleshooting Staff Shortages in a Specialized Field
Problem: Inability to hire or retain skilled forensic professionals, leading to backlogs and increased pressure on existing staff [11] [13].
Background: A conspicuous shortage of skilled forensic experts is a major market challenge, exacerbated by budget limitations that restrict competitive salaries [11].
Solution:
- Cross-Training: Implement cross-training programs to create a more versatile workforce where staff can support multiple disciplines during shortages.
- Automation Investment: Prioritize investments in laboratory automation for repetitive, high-volume tasks (e.g., liquid handling, sample preparation) to free up expert time for complex analysis and interpretation [11].
- University Partnerships: Establish internship and fellowship programs with local universities to build a pipeline of new talent and access specialized academic expertise for complex casework [15].
The following tables summarize the key quantitative data highlighting the conflict between projected market growth and the reality of budget reductions.
Table 1: Forensic Technology Market Growth Projections
| Metric | Value | Source & Time Period |
|---|---|---|
| Market Size (2024) | USD 10,017 Million | MarkSpeak Solutions (2025-2030) [11] |
| Projected Market Size (2030) | USD 18,025 Million | MarkSpeak Solutions (2025-2030) [11] |
| Compound Annual Growth Rate (CAGR) | 8.6% | MarkSpeak Solutions (2025-2030) [11] |
| Alternative CAGR | 13.3% | Technavio (2024-2029) [12] |
| North America Market Share (2024) | 45.33% | MarkSpeak Solutions [11] |
Table 2: Documented Budget Reductions and Constraints
| Metric | Value | Context & Source |
|---|---|---|
| DOJ Grant Terminations (Apr 2025) | 373 grants | Terminated for not effectuating new departmental priorities [14] |
| Rescinded Funding Value | ~ USD 500 Million | Estimated remaining balances of terminated grants [14] |
| Community Violence Intervention Cuts | ~ USD 145 Million | Cuts to the Community Violence Intervention and Prevention Initiative [14] |
| Key Challenge | Funding constraints | Limiting acquisition of new equipment per AAFS 2025 report [7] |
Experimental Protocols
Detailed Methodology: Drug Analysis via Gas Chromatography-Mass Spectrometry (GC-MS)
This protocol details the definitive confirmatory test for controlled substances, considered the "gold standard" in forensic laboratories [16].
1. Principle: A sample is vaporized and separated by a gas chromatograph (GC) based on the volatility and affinity of its components for the column's stationary phase. The separated components are then ionized and identified by a mass spectrometer (MS) based on their mass-to-charge ratio, providing a unique molecular fingerprint.
2. Materials and Reagents:
- Suspected controlled substance sample
- Appropriate organic solvent (e.g., methanol)
- Internal standard solution
- GC-MS system with autosampler
- Helium or nitrogen carrier gas
- GC column (e.g., 5% phenyl polysiloxane)
- Reference standards of suspected drugs
3. Procedure:
- Sample Preparation: Accurately weigh a small amount of the sample (~1-2 mg) and dissolve it in 1 mL of solvent. Add a known amount of internal standard. Mix thoroughly and centrifuge if necessary to separate particulates.
- Instrument Calibration: Calibrate the MS using a manufacturer-recommended calibration standard. System suitability should be verified by running a known reference standard and ensuring it produces the correct retention time and mass spectrum.
- GC Parameters:
- Injection Port Temperature: 250-280°C
- Carrier Gas Flow Rate: ~1.0 mL/min (optimize for column)
- Oven Temperature Program: Ramp from an initial low temperature (e.g., 80°C) to a high temperature (e.g., 300°C) at a defined rate to achieve optimal separation.
- Injection Volume: 1 µL (split or splitless mode)
- MS Parameters:
- Ionization Mode: Electron Impact (EI)
- Ion Source Temperature: 230°C
- Scan Range: e.g., 40-550 m/z
- Data Analysis:
- Compare the retention time and the full mass spectrum of the analyte in the sample to that of a certified reference standard analyzed under identical conditions.
- A positive identification is confirmed when the sample's mass spectrum and retention time match the reference standard within accepted tolerances.
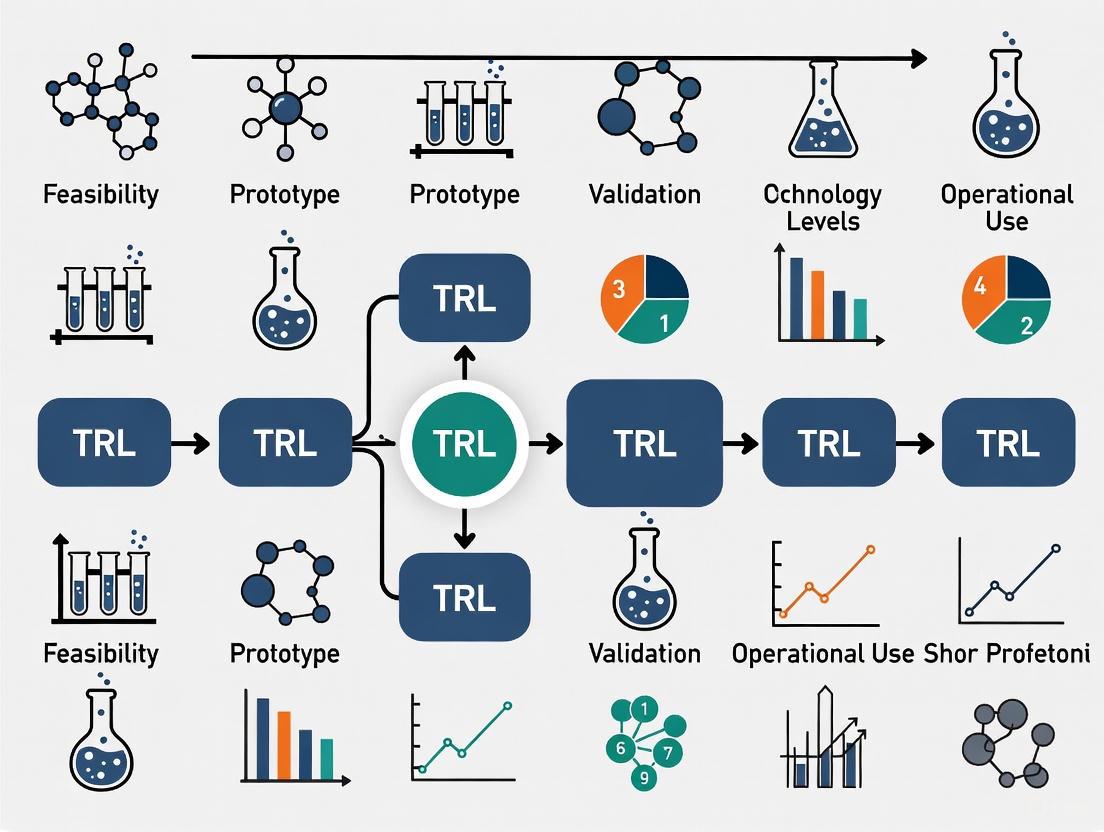
Workflow: Scaling a Technology from Research to Courtroom
This diagram illustrates the pathway and challenges, including budget constraints, for implementing a new forensic technology like GC×GC in a forensics laboratory.
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials for Forensic Drug Chemistry Analysis
| Item | Function | Example / Note |
|---|---|---|
| Presumptive Test Kits | Provides initial, non-definitive indication of a drug's class (e.g., Marquis test for opioids/amphetamines). Prone to false positives. [16] | Commercial kits from suppliers like Sirchie. |
| GC-MS Reference Standards | Certified pure compounds used to calibrate instruments and confirm the identity of an unknown sample by matching retention time and mass spectrum. [16] | Available from chemical suppliers; essential for court-admissible results. |
| Internal Standards (IS) | A known compound added to a sample at a known concentration; used in quantitative GC-MS to correct for losses during sample preparation and instrument variability. | Often a deuterated analog of the target analyte. |
| LC-MS/MS Solvents & Buffers | High-purity solvents and mobile phase additives are critical for reliable results in Liquid Chromatography-Tandem Mass Spectrometry, used for difficult-to-vaporize or thermally labile compounds. [17] | Acetonitrile, methanol, ammonium formate. |
| Solid Phase Extraction (SPE) Cartridges | Used for sample clean-up and concentration of target analytes from complex biological matrices like urine or blood, reducing ion suppression in MS. [17] | C18, mixed-mode cation exchange phases. |
| Proficiency Test Samples | Blind samples provided by external quality assurance programs to objectively assess a laboratory's analytical performance and ensure continued competency. [15] | Sourced from providers like RTI's Center for Forensic Sciences. |
Technical Support Center
Troubleshooting Guides
Guide 1: Troubleshooting Technology Validation Stalls
Problem: My technology prototype works perfectly in the lab but fails during field testing in realistic environments. The performance metrics have dropped significantly, and I can't progress beyond TRL 5.
Diagnosis: This indicates a classic "relevant environment gap" where controlled laboratory conditions don't adequately simulate real-world operational stresses [18].
Solution: Implement an Environmental Stress Testing Protocol:
- Deconstruct Environment Variables: Break down the target operational environment into specific, testable parameters (temperature ranges, vibration profiles, humidity cycles, user interaction patterns)
- Create Stepped Validation: Develop a testing protocol that gradually introduces environmental stresses rather than immediate full exposure
- Instrumentation for Diagnostics: Add additional sensors and data collection specifically for understanding failure modes during testing
- Iterative Redesign Cycles: Plan for multiple rapid redesign iterations based on field test findings
Guide 2: Troubleshooting Budget Exhaustion Before Validation
Problem: My project funding is running out before we can complete the critical transition from laboratory demonstration to operational environment testing.
Diagnosis: This represents the budget manifestation of the "Valley of Death" where costs increase dramatically at higher TRLs [18].
Solution: Implement a Strategic Funding Bridge Strategy:
- Phased Budget Allocation: Reserve 60-70% of total budget specifically for TRL 5-7 transition activities
- Parallel Funding Pursuit: Simultaneously pursue multiple funding sources (grants, partnerships, internal funds) during early TRL stages
- Minimum Viable Demonstration: Identify the absolute minimum scope required to prove operational viability
- Incremental Milestone Funding: Structure funding releases against specific, measurable TRL advancement milestones
Frequently Asked Questions (FAQs)
We're struggling with legal admissibility standards for our new forensic analysis method. What validation is required?
Answer: Legal systems require rigorous validation before admitting new forensic technologies as evidence. In the United States, methods must meet either Frye ("general acceptance") or Daubert standards (testing, peer review, error rates, acceptance) [10]. For admissibility:
- Documented Error Rates: Establish known error rates through controlled validation studies
- Peer Review: Publish method details and validation results in peer-reviewed literature
- Standardization: Develop standard operating procedures and quality controls
- Inter-laboratory Validation: Conduct validation across multiple independent laboratories
Our technology demonstrates excellent analytical performance, but forensic laboratories won't adopt it. What are we missing?
Answer: You're likely facing implementation readiness gaps beyond pure technical performance. Focus on:
- Workflow Integration: Ensure compatibility with existing laboratory workflows and staffing patterns
- Cost-Benefit Justification: Document clear operational efficiencies or improved outcomes
- Training Requirements: Develop comprehensive training programs for laboratory personnel
- Regulatory Compliance: Address data integrity, chain of custody, and reporting requirements
- Support Infrastructure: Establish technical support and maintenance capabilities
How do we quantify our technology's current maturity level to secure additional funding?
Answer: Use the standardized Technology Readiness Level (TRL) scale with specific, evidence-based assessments [18]:
| TRL Level | Description | Key Evidence Required |
|---|---|---|
| TRL 3 | Proof of Concept | Laboratory experiments validating core principles [18] |
| TRL 4 | Component Validation | Integrated breadboard testing in laboratory environment [18] |
| TRL 5 | Relevant Environment Validation | Prototype testing in simulated relevant environment [18] |
| TRL 6 | Prototype Demonstration | System/subsystem model demonstration in relevant environment [18] |
| TRL 7 | Operational Prototype | Prototype demonstration in operational environment [18] |
What specific evidence do we need to advance from TRL 6 to TRL 7 for a forensic technology?
Answer: The TRL 6 to 7 transition requires moving from simulated to actual operational environments [18]:
- Operational Context Testing: Demonstration in real forensic casework or equivalent operational setting
- End-User Validation: Testing by intended users (forensic examiners, not developers)
- Real-World Performance Metrics: Documented performance under casework conditions (throughput, reliability, error rates)
- Robustness Documentation: Evidence of performance across expected operational variations
- Comparative Effectiveness: Data showing advantages over existing methods or complementary capabilities
The Researcher's Toolkit: Forensic Technology Implementation
Research Reagent Solutions
| Item | Function in TRL Scaling | Implementation Purpose |
|---|---|---|
| Standard Reference Materials | Validation benchmarking across TRL levels | Provides consistent baseline for performance comparison during technology maturation [10] |
| Proficiency Test Panels | Inter-laboratory validation and error rate determination | Establishes reproducibility and reliability metrics required for legal admissibility [10] |
| Quality Control Materials | Daily performance monitoring and standardization | Ensures consistent operation across technology transition from lab to field deployment |
| Sample Processing Kits | Workflow integration and compatibility testing | Validates practical implementation in existing forensic laboratory workflows |
| Data Standards Framework | Result interpretation and reporting consistency | Enables cross-platform compatibility and expert testimony reliability [10] |
Budget Planning Framework for TRL Scaling
| TRL Range | Primary Cost Drivers | Mitigation Strategies |
|---|---|---|
| TRL 1-3 | Research personnel, basic laboratory supplies | Grant funding, internal R&D investment, proof-of-concept awards [18] |
| TRL 4-5 | Prototype development, component integration, initial validation | Strategic partnerships, shared resources, phased development approach [18] |
| TRL 6-7 ("Valley of Death") | Environmental testing, operational demonstration, certification | Dedicated technology demonstration programs, public-private partnerships, strategic funding reserves [18] |
| TRL 8-9 | Manufacturing scale-up, quality systems, deployment support | Implementation grants, commercial partnerships, operational budgets [18] |
The forensic science landscape is defined by a significant divergence in resource allocation and funding priorities, creating a palpable tension between the established field of traditional crime scene investigation (CSI) and the emerging domain of digital forensics. This disparity is driven by distinct growth projections, market forces, and societal technological shifts. Traditional forensic labs, often operating within governmental structures, face chronic funding constraints and backlogs, struggling to keep pace with caseloads with outdated equipment [7] [19]. Conversely, the digital forensics sector is experiencing a rapid market expansion, fueled by the escalating volume of cybercrime and technological adoption across society [20] [21]. This article analyzes these disparities through quantitative data, provides methodologies for researching their impact, and offers guidance for professionals navigating this fragmented resource environment.
Quantitative Analysis of Disparities
The divergence between the two fields can be quantitatively measured through growth projections, salary data, and market size.
Table 1: Career Growth and Financial Allocation Comparison
| Aspect | Digital Forensics | Traditional CSI |
|---|---|---|
| Projected Job Growth (2024-2034) | 35% [22] | 13% [22] |
| Entry-Level Salary Range | $55,000 - $80,000 [22] | $40,000 - $50,000 [22] |
| Global Market Value | Projected to reach $18.2 billion by 2030 [20] | Not specified in search results, but indicated as constrained [7] [19] |
| Key Growth Driver | Market forces and private sector investment [21] | Primarily governmental budgets [23] |
Table 2: Funding Environment and Resource Challenges
| Aspect | Digital Forensics | Traditional CSI |
|---|---|---|
| Primary Funding Source | Corporate cybersecurity budgets, private investment, federal grants [21] | Governmental budgets (state, local), fixed tax revenues [23] |
| Key Resource Constraints | Shortage of court-certified examiners; encryption complicating data acquisition [21] | Inability to purchase new equipment; backlog of cases awaiting analysis [7] [23] |
| Defining Operational Issue | Adapting to rapid technological change (Cloud, AI, IoT) [20] | Managing case backlogs and processing physical evidence with limited capacity [23] |
Experimental Protocols for Impact Assessment
Researchers and lab directors can employ the following methodologies to empirically evaluate the impact of resource constraints and build cases for funding.
Protocol 1: Cost-Benefit Analysis of Backlog Reduction
This protocol uses a model based on "Project Resolution," a successful initiative by the Acadiana Criminalistics Laboratory [23].
- Objective: To quantify the net benefit of allocating additional resources to reduce a specific backlog (e.g., DNA evidence from no-suspect sexual assaults).
- Materials: Historical case files, cost data for analysis (internal & outsourcing), access to CODIS/NDIS, recidivism data.
- Methodology:
- Case Selection and Costing: Identify a cohort of backlogged cases (e.g., 605 no-suspect sexual assaults). Calculate the total cost to analyze the entire cohort, including personnel, reagents, and/or vendor costs [23].
- Evidence Analysis and Database Entry: Process the evidence to generate DNA profiles. Enter all eligible profiles into the national DNA database (CODIS/NDIS) [23].
- Outcome Tracking: Track the number of CODIS hits (matches to offenders or other cases) over a defined period (e.g., 10 years) [23].
- Benefit Calculation: Calculate the benefit by factoring in:
- Clearance Rate: Percentage of cases with a CODIS hit (Project Resolution achieved a 58% hit rate) [23].
- Recidivism Prevention: Assign a cost-avoidance value based on statistical data for crimes prevented by incarcerating a serial offender.
- Investigative Efficiency: Quantify savings from closing cold cases and reallocating investigative resources.
- Output: A net benefit figure (Total Benefits - Total Costs) that objectively supports requests for resource allocation to reduce backlogs.
Protocol 2: Technology Readiness Level (TRL) Scaling for Forensic Tools
This protocol assesses the maturity and scalability of new tools within a resource-constrained environment.
- Objective: To evaluate the implementation feasibility of a new forensic technology (e.g., an AI-based evidence triage tool) from prototype to integrated lab system.
- Materials: The new technology, a defined set of test cases, existing laboratory instrumentation/software, performance metrics.
- Methodology:
- Baseline TRL Assessment: Define the starting TRL (1-9) for the new tool. Most novel forensic tools start at TRL 3-4 (analytical and experimental proof of concept) [24].
- Pilot Validation (TRL 5-6): Run the tool in a lab environment with a small, controlled set of case data. Compare its accuracy, speed, and cost against the current "gold standard" method.
- System Integration (TRL 7): Integrate the tool into a single, representative operational workflow. This tests data transfer, chain-of-custody logging, and analyst usability.
- Operational Deployment & ROI Calculation (TRL 8-9): Deploy the tool for full operational use. Calculate the Return on Investment (ROI) by measuring the change in throughput (cases per analyst), reduction in processing time, and change in operational costs.
- Output: A TRL progression report with validated performance and cost data, providing a clear roadmap and justification for full-scale funding.
The Scientist's Toolkit: Research Reagent Solutions
This table details key materials and tools essential for research and experimentation in the modern forensic science landscape.
Table 3: Essential Research and Operational Tools
| Tool / Solution | Function | Field of Application |
|---|---|---|
| Cellebrite UFED / XRY | Extracts and analyzes data from mobile devices, bypassing security where possible. | Digital Forensics (Mobile) [22] [21] |
| EnCase / FTK (Forensic Toolkit) | Creates forensic images of computer hard drives and facilitates analysis of recovered data. | Digital Forensics (Computer) [22] |
| KinTest Software | Uses STR frequency data to calculate Likelihood Ratios (LR) for potential familial relationships from DNA. | Traditional CSI (DNA Analysis) [23] |
| Automated Fingerprint ID System (AFIS) | Database system for storing and comparing fingerprint patterns, enabling rapid suspect identification. | Traditional CSI (Fingerprint Analysis) [22] |
| Cloud-Native Acquisition APIs | Programmatic interfaces that allow for the forensic acquisition of data from cloud platforms like AWS, Azure, and GCP. | Digital Forensics (Cloud) [21] |
| AI-Powered Triage Suites | Use machine learning to automatically analyze large datasets (e.g., logs, files) to identify patterns and prioritize evidence. | Digital Forensics (Cross-Domain) [20] [25] |
Technical Support Center: FAQs and Troubleshooting Guides
FAQ 1: How can we justify increased funding for traditional forensic lab equipment when digital forensics is receiving more market investment?
- Issue: Securing capital for new traditional lab equipment (e.g., updated DNA sequencers, GC-MS) is challenging.
- Solution:
- Conduct a Cost-Benefit Analysis: Use Protocol 1 to demonstrate the long-term cost savings and public safety benefits of modern equipment. Highlight how faster processing reduces backlog, prevents recidivism, and saves investigative resources [23].
- Frame it as Foundational: Argue that traditional forensic evidence (DNA, fingerprints) remains the bedrock of many prosecutions and that reliable, timely analysis is a core government function that cannot be allowed to degrade [19].
- Pilot a Shared Service Model: Propose a regional equipment-sharing initiative with neighboring jurisdictions to maximize utilization and dilute costs.
FAQ 2: Our digital forensics unit is struggling with encrypted devices and a shortage of certified examiners. What are the practical steps to overcome this?
- Issue: Encryption and talent shortages are crippling digital evidence processing.
- Solution:
- For Encryption: Acknowledge that hardware-based encryption reduces success rates. Develop a multi-pronged strategy: 1) Invest in premium decryption utilities; 2) Shift focus to cloud-based evidence and backups that can be legally acquired; 3) Ensure legal teams are prepared to leverage court orders for device access [21].
- For Talent Shortages: 1) Advocate for funding for examiner certification (e.g., CDFE, GCFE). 2) Explore partnerships with local universities to create a talent pipeline. 3) Consider leveraging "Forensics-as-a-Service" providers for specific, high-volume tasks to free up internal experts for complex cases [22] [21].
FAQ 3: We are a small lab with limited budget. How do we prioritize between investing in traditional vs. digital forensics capabilities?
- Issue: Strategic resource allocation with constrained funds.
- Solution:
- Perform a Workload Analysis: Audit your incoming caseload for the past 2-3 years to quantify the proportion of cases requiring digital vs. traditional analysis. Let data drive the decision.
- Start with Cross-Training: Invest in cross-training existing traditional forensic staff in fundamental digital evidence handling to create a hybrid workforce [22].
- Targeted Digital Investment: Instead of building a full digital lab, initially invest in a single capability with the highest demand, such as mobile device extraction, and outsource more complex digital needs [21].
- Seek Grant Funding: Actively apply for federal and state grants aimed at modernizing forensic capabilities, which often have streams for both traditional and digital forensics [26].
Workflow Visualization
The following diagram illustrates the logical relationship and resource flow between the key challenges and potential solutions discussed in this article.
Technical Support Center: Troubleshooting Guides and FAQs
Frequently Asked Questions (FAQs)
FAQ 1: What are the immediate signs that commoditization is affecting my R&D budget?
The most immediate signs are margin compression and a reduction in revenue growth, which directly pressure R&D budgets. Management often responds by allocating less capital to R&D initiatives, implying that opportunities for product differentiation are declining. You will also observe a shift in competition towards pricing rather than features, making it harder to justify R&D for innovation [27].
FAQ 2: Our core technology is becoming a commodity. Should we stop investing in it entirely?
Not necessarily. A "no-frills" core product can be part of a profitable strategy, but it requires a different operational model. For example, Dow Corning created a separate brand, Xiameter, to sell its commoditized silicone products online at competitive prices to volume customers. This allows the company to profit from its commodity line while freeing up resources to develop more differentiated, value-added offerings [28].
FAQ 3: How can we demonstrate the return on investment (ROI) for R&D when budgets are tight?
Focus your R&D on developing Relational Capital—the mutual trust, respect, and friendship in customer relationships. Research shows that relational capital positively moderates the link between R&D services and profitability. When customers trust you, they are more likely to value and pay for your complex R&D services. Frame your R&D proposals around solving specific, high-value customer problems, as SKF did by moving from selling bearings to offering guaranteed performance in reducing machinery downtime [29] [28].
FAQ 4: What is a viable R&D strategy in a highly commoditized market?
The optimal strategy depends on where value is shifting in your market. Use the following table to diagnose your situation [30]:
| Market Environment | Dominant Advantage | Optimal R&D Strategy | Real-World Example |
|---|---|---|---|
| Premium Player | Meaningful differentiation | Protect/enhance differentiation via innovation, brand, patents. | Specialty pharmaceuticals, luxury goods. |
| Producer | Low-cost structure | R&D focused on cost efficiency: product design, process innovation. | Oil production, mining industries. |
| Arbitrager | Exploiting market imperfections | R&D for agility, data analysis to spot supply/demand mismatches. | Fixed-income and foreign-exchange trading. |
| Exit | Neither structural nor dynamic advantage | Redeploy R&D resources to more attractive markets. | IBM exiting the PC business. |
FAQ 5: How can we speed up R&D to keep up with rapidly commoditizing technology markets?
In markets moving quickly toward feature parity, the features arms race is often a losing battle. Instead of exhaustive in-house development, adapt your procurement. For commoditized components, shift from lengthy evaluations to fast-tracked purchasing of standard solutions. This saves person-years of effort, allowing your R&D team to focus on higher-value, integrative innovation that creates unique systems for customers [31].
Troubleshooting Guide: R&D Under Budget Constraints
Problem: Inability to justify R&D budget for foundational forensic research due to its perceived low commercial return.
Solution:
- Action: Link foundational research to specific, funded national initiatives.
- Methodology: Align proposals with the strategic R&D and standards priorities outlined by bodies like the National Institute of Standards and Technology (NIST) [32]. For example, pursue research that addresses the "validity of forensic methods" or develops "measures of uncertainty," as these are stated needs [33]. This frames your R&D as low-risk and policy-supported, making it more likely to secure public or private grants.
Problem: High-cost technology (e.g., gunshot detection systems) fails to deliver expected operational value, leading to budget cuts.
Solution:
- Action: Conduct a pre-implementation "Total Cost of Ownership (TCO) and Efficacy" analysis.
- Methodology: Before procurement, model not just the purchase price but all infrastructure, storage, and specialized personnel costs. Crucially, pilot the technology in a controlled setting to measure its impact on key outcomes (e.g., response time, arrest rates) versus existing methods. Research shows that while gunshot detection works technically, its operational value is often limited, making it a poor investment without prior validation [34].
Problem: Need to achieve Technology Readiness Level (TRL) scaling with limited funding.
Solution:
- Action: Adopt a "Solution Innovation" strategy.
- Methodology: Instead of developing a standalone product, use R&D to bundle your technology with high-value services into a customized solution. BASF did this with its Integrated Paint Shop, where it gets paid per painted car body that passes inspection, not for the volume of paint used. This funds further R&D by creating a new, high-margin revenue stream and demonstrates tangible value to customers [28].
Experimental Protocols & Methodologies
Protocol: Quantifying the Impact of Relational Capital on R&D Profitability
This protocol outlines a methodology to empirically test the hypothesis that relational capital enhances the profitability of R&D services, based on causal modeling techniques [29].
1. Hypothesis: Relational capital (e.g., trust, respect) positively moderates the relationship between a supplier's R&D service intensity and its profit performance within a specific customer relationship.
2. Data Collection:
- Unit of Analysis: Individual supplier-customer relationships.
- Sample: A minimum of 91 relationships to ensure statistical power for causal modeling [29].
- Variables and Measurement:
- Dependent Variable: Supplier Profitability. Measured as the profit margin (percentage) attributed to the specific customer relationship.
- Independent Variable: R&D Service Intensity. A Likert-scale survey metric assessing the extent of R&D services (e.g., feasibility studies, prototype design, product tailoring) provided to the customer.
- Moderating Variable: Relational Capital. A composite index based on survey items measuring mutual trust, respect, and the quality of personal friendships between the supplier and customer organizations [29].
3. Analysis:
- Use structural equation modeling (SEM) or hierarchical regression analysis.
- Test the main effect of R&D services on profitability.
- Test the interaction effect between R&D services and relational capital. A statistically significant positive interaction term confirms the moderating role of relational capital.
Protocol: Evaluating Operational Value of Commoditized Hardware
This methodology assesses whether a commoditized technology (e.g., gunshot detection) delivers sufficient operational value to justify its cost and further R&D investment [34].
1. Hypothesis: Implementation of Technology X will significantly improve operational outcome Y (e.g., response time, case clearance) compared to existing methods, after controlling for cost.
2. Experimental Design:
- Design: A quasi-experimental design comparing pre- and post-implementation data, with a control group (similar jurisdictions without the technology).
- Participants: Law enforcement agencies or forensic labs implementing the technology.
3. Metrics and Data Collection:
- Primary Metric: Operational Effectiveness. e.g., Reduction in average response time to incidents, increase in successful evidence collection rates.
- Secondary Metric: Total Cost of Ownership (TCO). Include initial acquisition, installation, infrastructure, data storage, maintenance, and specialized training costs.
- Data Sources: Internal agency records, 911 call logs, and cost accounting data collected over a 12-month period.
4. Analysis:
- Conduct a cost-benefit analysis, comparing the quantified improvement in operational effectiveness against the TCO.
- Perform a t-test or ANOVA to determine if the differences in outcomes between the experimental and control groups are statistically significant.
The Scientist's Toolkit: Research Reagent Solutions
Table: Essential Strategic "Reagents" for R&D in Commoditized Markets
| Research Reagent | Function & Explanation | Application Example |
|---|---|---|
| Relational Capital | The "catalyst" for R&D profitability. Builds trust and respect, allowing customers to perceive higher value in your R&D services and making them willing to pay a premium [29]. | A supplier uses deep customer relationships to co-develop a custom R&D service, securing a long-term, profitable contract. |
| Value Space Matrix | A "diagnostic assay" to identify strategic pathways for R&D. It plots Segmentation/Customization against Bundling to reveal four strategic quadrants (Core, Targeted, System, Solution) [28]. | A company stuck in the "Core" quadrant uses the matrix to plot a path toward "Solution Innovation," guiding its R&D portfolio decisions. |
| Commoditization Navigator | A "classification tool" to identify the optimal R&D strategy based on market dynamics. It assesses structural (cost/differentiation) and dynamic (market imperfections) advantage [30]. | A firm in a cost-advantaged "Producer" market focuses R&D on process efficiency, while an "Arbitrager" invests in data analytics for market timing. |
| De-bundled Core Product | A "purified compound" that profitably serves the price-sensitive segment of a commoditized market. Allows R&D resources to be focused on more innovative, bundled offerings [28]. | Dow Corning's Xiameter brand sells basic silicones online at low cost, while the main brand focuses on high-value, service-backed solutions. |
| NIST OSAC Standards | The "buffer solution" providing stability and reliability. Using established standards ensures forensic R&D is valid, reliable, and admissible, preventing wasted investment on non-compliant methods [33]. | A lab developing a new DNA analysis technique aligns its validation protocol with OSAC standards to ensure widespread adoption and credibility. |
Strategic Pathways for R&D Investment
The following diagram illustrates the logical decision process for aligning R&D strategy with market commoditization, based on the Commoditization Navigator framework [30].
Cost-Effective Implementation Strategies and Frugal Forensic Frameworks
Frugal forensics is an emerging paradigm that advocates for the sustainable provision of transparent, high-quality forensic services tailored to meet specific jurisdictional needs and limitations [35]. This approach addresses the stark disadvantages faced by many Global South jurisdictions in resourcing and technological capabilities, despite forensic science's growing importance as a global practice supporting peace, prosperity, and justice [35] [36]. The concept aligns with the United Nations Sustainable Development Goals and aims to narrow inequalities between jurisdictions by developing frameworks that prioritize cost-efficiency, resource optimization, and simplicity without compromising quality [35] [37]. This technical support center provides practical guidance for implementing frugal forensic principles within budget-constrained environments.
Core Principles of Frugal Forensics
- Sustainable Resource Allocation: Focus on maximizing output from limited resources through careful prioritization and strategic investment in areas with the highest impact on justice outcomes [35] [23].
- Context-Appropriate Technology: Select and implement forensic technologies based on jurisdictional needs, infrastructure limitations, and life-cycle costs rather than simply adopting the most advanced available systems [35].
- Supply Chain Resilience: Develop robust local supply chains and reagent management systems to minimize dependencies on international suppliers and reduce costs associated with transportation and importation [35].
- Quality Assurance Frameworks: Implement scalable quality assurance measures that ensure reliable results while remaining feasible within existing operational constraints [35].
- Data-Driven Decision Making: Employ cost-benefit analysis to objectively compare competing options for resource deployment, focusing on timeliness and investigative value [23].
Frequently Asked Questions (FAQs)
Q1: How can forensic laboratories demonstrate the value of additional resources to budget officials?
A: Conduct a formal cost-benefit analysis using historical data to quantify the impact of forensic resources on case resolution. The Project Resolution case study demonstrated that an investment of $186,000 to process 605 cold cases resulted in 164 CODIS matches (a 58% hit rate) over time, identifying serial offenders and solving previously unsolvable crimes [23]. Presenting such quantitative data on outcomes, including recidivism prevention and serial crime identification, provides objective evidence for resource allocation decisions [23].
Q2: What is the most effective approach to reducing case backlogs with limited personnel?
A: Focus resources on eliminating the backlog of cases awaiting analysis rather than just managing cases in-analysis. Studies suggest that ideal response time is achieved when case analysis commences immediately upon submission [23]. Implement triage protocols that prioritize cases with the greatest potential for investigative leads, such as no-suspect sexual assaults that are highly dependent on forensic databases for resolution [23].
Q3: How can laboratories maintain quality while implementing cost-saving measures?
A: Develop context-appropriate quality assurance frameworks that focus on essential validation procedures and transparent documentation [35]. The frugal forensics approach emphasizes maintaining high-quality standards through method selection based on robust principles rather than expensive equipment, ensuring reliability without unnecessary complexity [35] [38].
Q4: What strategies can help overcome technological dependency in Global South jurisdictions?
A: Apply frugal principles that emphasize simplicity, local supply chain development, and appropriate technology levels [37] [38]. This includes building local technical capacity, adapting methods to use readily available reagents, and developing maintenance expertise within the region rather than relying on international vendors for all technical support [35].
Experimental Protocols & Methodologies
Cost-Benefit Analysis Protocol for Forensic Resource Allocation
Objective: To objectively evaluate the return on investment for forensic laboratory resources by analyzing historical case data [23].
Materials: Historical case records, laboratory information management system (LIMS) data, CODIS hit reports, cost accounting records.
Methodology:
- Case Selection: Identify a representative sample of cases, such as no-suspect sexual assaults that are highly dependent on forensic analysis for resolution [23].
- Cost Calculation: Document all direct costs associated with processing the selected cases, including personnel time, reagents, equipment usage, and external vendor costs if applicable [23].
- Outcome Measurement: Track CODIS hits, case resolutions, identifications of serial offenders, and linkages to other cases over an extended period to capture the full value [23].
- Benefit Quantification: Assign quantitative values to outcomes where possible, including saved investigative resources, prevention of future crimes through incapacitation of identified offenders, and justice provided to victims [23].
- Analysis: Calculate cost-benefit ratios and return on investment metrics to compare different resource allocation scenarios [23].
Latent Fingermark Detection Using Frugal Principles
Objective: To develop reliable latent fingermark detection methods appropriate for jurisdictions with limited resources and challenging environmental conditions [35].
Materials: Basic fingerprint powders, alternative light sources, digital imaging equipment, locally-sourced chemicals.
Methodology:
- Substrate Assessment: Categorize evidence by surface type (porous, non-porous, semi-porous) to determine appropriate processing sequences [35].
- Sequential Processing: Implement methodical progression from least to most destructive techniques to preserve evidence integrity [35].
- Local Reagent Development: Adapt formulations using locally available chemicals to reduce costs and supply chain dependencies [35].
- Quality Control: Implement standardized photography and documentation protocols to ensure reproducible results despite equipment limitations [35].
Workflow Diagrams
Frugal Forensics Implementation Workflow
Forensic Backlog Reduction Strategy
The Scientist's Toolkit: Research Reagent Solutions
Table: Essential Materials for Frugal Forensic Research
| Item | Function | Frugal Application |
|---|---|---|
| Alternative Light Sources | Enhances visibility of latent evidence including fingerprints, bodily fluids, and fibers [35] | Select energy-efficient models with minimal maintenance requirements; consider multi-wavelength LED systems for versatility [35] |
| Basic Fingerprint Powders | Develops latent fingerprints on non-porous surfaces [35] | Focus on core color types (black, white, magnetic); ensure proper storage to extend shelf life [35] |
| Local Chemical Substitutes | Replaces imported reagents for various chemical development techniques [35] | Develop formulations using locally available laboratory-grade chemicals; validate against standard methods [35] |
| Digital Documentation System | Captures and preserves evidence through imaging [24] | Implement standardized protocols using available digital cameras; ensure proper color calibration and scale placement [24] |
| Statistical Analysis Software | Provides quantitative assessment of evidence significance using likelihood ratio framework [24] | Utilize open-source platforms for statistical analysis and evidence interpretation to reduce licensing costs [24] |
Table: Project Resolution Cost-Benefit Analysis Outcomes [23]
| Metric | Result | Significance |
|---|---|---|
| Total Investment | $186,000 | Special legislative allocation for cold case sexual assault evidence testing |
| Cases Processed | 605 | Unsolved sexual assault cases with retained serological cuttings from 1985 onward |
| Semen-Positive Cases | 317 (52.4%) | Demonstrates value of retaining biological evidence long-term |
| Foreign Male Profiles Developed | 285 (90% of positive cases) | Successful DNA recovery from historical evidence |
| Initial CODIS Hits | 134 to 119 offenders (47% hit rate) | Immediate investigative leads generated |
| 10-Year Follow-up Hits | 164 total matches (58% hit rate) | Demonstrates increasing value as DNA database expands |
| Serial Offender Identification | Multiple serial rapists identified | Crime pattern recognition through DNA connectivity |
Table: Frugal Forensics Implementation Framework
| Principle | Traditional Approach | Frugal Approach |
|---|---|---|
| Technology Adoption | Latest available technology regardless of context | Appropriate technology matched to jurisdictional needs and limitations [35] |
| Supply Chain | Dependent on international suppliers | Local supply chain development and strategic reagent management [35] |
| Quality Assurance | Comprehensive systems potentially exceeding resources | Context-appropriate QA frameworks focused on essential validation [35] |
| Resource Allocation | Based on tradition or equipment availability | Data-driven using cost-benefit analysis and demonstrated impact [23] |
| Method Selection | Standardized protocols regardless of cost-benefit | Frugal principles emphasizing simplicity and robustness [37] [38] |
For researchers and drug development professionals, the integration of new forensic technologies presents a unique challenge: how to strategically allocate limited R&D resources between established traditional methods and emerging digital capabilities. The framework of Technology Readiness Levels (TRL) provides a critical methodology for assessing the maturity of these technologies, from basic principles (TRL 1) to full deployment (TRL 9) [39] [40]. This technical support center offers guides and protocols to navigate this complex landscape, helping your team make data-driven decisions on technology implementation amidst budget constraints.
► FAQs: Technology Prioritization and TRL Scaling
1. What is the TRL scale and why is it critical for forensic technology investment? The Technology Readiness Level (TRL) scale is a formal metric system used to assess the maturity of a specific technology. It ranges from TRL 1 (basic principles observed) to TRL 9 (actual system proven in operational environment) [39]. For forensic and drug development research, using the TRL scale helps identify immediate technical gaps, structure discussions on project status, and estimate the effort required to advance a technology toward deployment [39]. It is a vital tool for performing rough portfolio analysis based on technology maturity, ensuring that R&D budgets are allocated to projects with a viable path to implementation.
2. How does the volume and complexity of digital evidence impact research priorities? The sheer quantity of digital evidence—from smartphones, cloud storage, and Internet of Things (IoT) devices—can be overwhelming and risks overwhelming traditional analysis systems [41] [42]. Modern criminal investigations increasingly involve evidence that is both digital and volatile; features on mobile devices like auto-reboot and USB restricted mode can permanently erase data if not processed immediately [43]. This reality necessitates a strategic shift in research priorities towards developing automated, scalable digital forensics case management systems and tiered analytical approaches to manage this data deluge effectively [42] [43].
3. What are the key differences between traditional and modern digital forensics that affect resource allocation? Traditional digital forensics primarily focused on analyzing data from standalone computers and local hard drives, often involving a physical replica of the data source for offline analysis [41]. Modern digital forensics has evolved to encompass specialized domains like mobile forensics, cloud forensics, blockchain forensics, and analysis of data from drones, video surveillance, and vehicle systems [41]. This expansion requires a flexible and scalable approach, as data volume is now measured in terabytes rather than gigabytes, making traditional methods increasingly time-consuming and inefficient [41]. Budget allocation must therefore account for these new domains and the specialized tools and training they require.
4. How can a tiered approach to digital forensics optimize resource use in a research or operational setting? A tiered approach delineates roles to maximize efficiency. It involves employing Digital Evidence Technicians (DETs) to handle initial device intake, imaging, and triage to identify immediate leads. This frees up highly trained Digital Forensics Examiners (DFEs) to focus on deep-dive analysis, complex data reconstruction, and courtroom testimony [43]. This model prevents highly skilled personnel from being bogged down by routine tasks and allows an organization to build its digital forensics capacity in a staged, strategic way that aligns with budget realities and case complexity.
5. What is a common methodological pitfall when transitioning a technology from a low to a high TRL? A common pitfall is moving to testing in an operational environment before the technology's components have been properly validated in a laboratory setting. Per the TRL scale, a technology must first have its components validated in a laboratory environment (TRL 4) and its integrated components demonstrated in a laboratory environment (TRL 5) before a prototype can be tested in a relevant environment (TRL 6) [39]. Skipping these steps can lead to failures when the technology encounters real-world conditions because fundamental compatibility and performance issues were not resolved in a controlled setting.
► Troubleshooting Guides
Issue 1: Overwhelming Backlog of Digital Evidence
- Problem: A massive and ever-increasing backlog of devices and data is causing significant delays in investigations and research.
- Diagnosis: This is typically caused by the sheer volume of evidence, combined with inefficient, linear workflows and a lack of automated processes [42] [43].
- Solution:
- Implement a Digital Forensics Case Management System: Adopt a centralized platform to streamline workflows, track requests, and automate routine tasks [42].
- Adopt a Tiered Analytical Model: Utilize Digital Evidence Technicians for triage and initial data extraction to free up expert examiners for complex analysis [43].
- Explore Partnerships: Form consortia or regional partnerships with other institutions to share resources, tools, and reduce the financial burden on a single entity [43].
Issue 2: Inadmissible or Unreliable Digital Evidence
- Problem: Evidence collected is being challenged in legal proceedings or is found to be incomplete.
- Diagnosis: This can stem from a "button-pushing" approach where technicians use tools without a deep understanding of their function, improper evidence handling that breaks the chain of custody, or a failure to account for the volatile nature of modern data [43].
- Solution:
- Ensure Immediate Acquisition: Process mobile devices immediately to counter security features that can erase or lock data [43].
- Invest in Continuous Training: Move beyond basic tool proficiency to ensure personnel understand the underlying processes and legal standards [43].
- Maintain Chain of Custody: Use a case management system that automatically tracks the evidence chain of custody to ensure integrity [42].
Issue 3: Failure to Advance a Technology's TRL
- Problem: A research project remains at a low TRL and cannot progress to validation or operational testing.
- Diagnosis: The project may lack a clear integration plan, well-documented end-user requirements, or the component compatibility may not have been demonstrated in a laboratory environment (TRL 4) [39].
- Solution:
- Document End-User Requirements: Clearly define and document what the end-user needs from the technology [39].
- Develop a Plausible Integration Plan: Create a draft plan for integrating components and demonstrate their compatibility in a fully controlled lab environment [39].
- Validate Individual Components: Before full integration, successfully test individual components in a laboratory setting [39].
► Experimental Protocols & Methodologies
Protocol 1: Technology Maturity Assessment Using the TRL Scale
Objective: To systematically evaluate and determine the Technology Readiness Level of a specific forensic or pharmaceutical technology.
Workflow:
- Define the Technology: Precisely delineate the technology product or process to be assessed.
- Gather Documentation: Collect all available data on the technology, including research papers, test reports, and performance metrics.
- TRL Questionnaire: Assess the technology against the official TRL scale requirements [39]. Key questions include:
- Has basic scientific principle been observed and documented? (TRL 1)
- Has a proof-of-concept been validated through experiment or simulation? (TRL 3)
- Have integrated components been demonstrated in a laboratory environment? (TRL 5)
- Has a prototype been demonstrated in an operational environment? (TRL 7)
- Determine Maturity Level: The technology's TRL is the highest level for which it meets all requirements.
- Identify Gaps: Document the specific tests or developments required to advance to the next TRL.
Technology Readiness Level Assessment Workflow
Protocol 2: Spectroscopic Bloodstain Age Estimation
Objective: To estimate the age of a forensic bloodstain by analyzing age-related color changes in hemoglobin derivatives using spectroscopy.
Workflow:
- Sample Collection: Collect a controlled bloodstain sample from the crime scene or experimental setup.
- Spectroscopic Analysis: Subject the sample to spectroscopic analysis. This technique records the intensity distribution of light (spectra) as a function of wavelength [44].
- Spectral Band Identification: Identify key spectral bands, particularly the Soret band (~425 nm in young stains) and peaks for oxyhemoglobin (542 nm, 577 nm) and methemoglobin (510 nm, 631.8 nm) [44].
- Monitor Spectral Shift: Note that as blood ages, the Soret peak shifts toward ~400 nm, and the oxyhemoglobin peaks diminish in favor of methemoglobin peaks [44].
- Mathematical Comparison: Compare the obtained spectral bands with established literature values to estimate the approximate age of the bloodstain [44].
Table 1: Technology Readiness Level (TRL) Definitions and Requirements
| TRL | Category | Description | Key Requirements |
|---|---|---|---|
| 1-3 | Basic Research | Basic principles observed and formulated; proof-of-concept established. | Basic principles documented; application formulated; feasibility validated via experiment/modeling [39]. |
| 4-5 | Applied Research | Components validated and integrated in a lab environment. | End-user requirements documented; components validated (TRL 4); integration demonstrated in lab (TRL 5) [39]. |
| 6-7 | Development | Prototype demonstrated in relevant and then operational environments. | Prototype tested in realistic environment (TRL 6); demonstrated in operational environment (TRL 7) [39]. |
| 8-9 | Implementation | Technology proven and deployed in its operational environment. | System proven in operational environment (TRL 8); technology deployed and operational (TRL 9) [39]. |
Table 2: Traditional vs. Modern Digital Forensics Domains
| Aspect | Traditional Digital Forensics | Modern Digital Forensics |
|---|---|---|
| Primary Focus | Standalone computers, local hard drives [41]. | Mobile devices, cloud platforms, blockchain, IoT, drones [41]. |
| Data Scale | Gigabytes (GB) [41]. | Terabytes (TB) [41]. |
| Key Challenges | Physical access to devices; creating data replicas [41]. | Data volatility; encryption; vast data volume; need for specialized domains (cloud, mobile) [41] [43]. |
| Investigation Scale | Single device, localized analysis [41]. | Distributed, multi-source, cross-platform analysis [41]. |
► The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials for Forensic Technology Research
| Item | Function |
|---|---|
| Spectrometer | A biophysical instrument used to record the interaction of electromagnetic radiation with matter, producing spectra for substance identification and analysis (e.g., bloodstain age estimation) [44]. |
| Mobile Forensics Tool | Advanced software and hardware used to extract and analyze data from smartphones, tablets, and wearables, often dealing with encrypted or locked devices [41]. |
| Cloud Forensics Platform | Specialized software for retrieving, analyzing, and preserving data from remote cloud environments, navigating complex, shared infrastructures [41]. |
| Digital Forensics Case Management System | A centralized software platform that streamlines workflows, tracks evidence chain-of-custody, automates tasks, and facilitates collaboration for managing complex digital evidence [42]. |
| TRL Scale | A formal assessment framework used as a guide to structure discussions and evaluate the maturity and readiness of a technology for deployment [39]. |
► Strategic Implementation Framework
Strategic Technology Implementation Framework
FAQs on TRLs and Budget-Led Implementation
1. What are Technology Readiness Levels (TRLs), and why are they important for managing budget constraints?
The Technology Readiness Level (TRL) is a systematic metric for assessing the maturity of a particular technology. It divides the product creation process into 9 distinct stages, providing a common language for researchers, funders, and stakeholders to evaluate progress and risk [45]. Originally developed by NASA, the scale is now widely used in other governmental departments and R&I programmes like the EU's Horizon Europe [46].
For projects operating under budget constraints, the TRL framework is indispensable for phasing investments according to risk. It helps prevent the common pitfall of over-investing in unproven concepts by ensuring that funding is released progressively as a technology delivers validated evidence of its feasibility and effectiveness. This methodical, stage-gated approach allows for rational allocation of often-limited public research funds, helping to bridge the "valley of death" between basic research and industrial application [46].
2. How can I map my drug development project to the TRL scale?
For medical product development, including drugs and biologics, more tailored TRL scales have been created. The following table aligns general TRL definitions with specific criteria for medical countermeasures, providing a concrete roadmap for your project [47].
| TRL | General Definition [45] [46] | Specific Milestones for Medical Products [47] | Typical Budget Focus |
|---|---|---|---|
| TRL 1-2 | Basic principles observed; practical applications formulated. | Review of scientific knowledge base; generation of hypotheses and experimental designs. | Minimal funding for foundational research. |
| TRL 3-4 | Active R&D; experimental proof-of-concept; first laboratory prototype. | Target identification; non-GLP in vivo proof-of-concept; candidate optimization. | Focused funding for de-risking core hypotheses. |
| TRL 5-6 | Validation in relevant environment; prototyping in a lab environment. | Initiation of GMP process development; GLP non-clinical studies; IND submission; Phase 1 clinical trial. | Major increase for process development & early regulatory steps. |
| TRL 7-8 | System prototype demonstration in operational environment; technology completed and qualified. | Scale-up and validation of GMP process; Phase 2 & 3 clinical trials; NDA/BLA submission and FDA approval. | Peak funding for pivotal trials and manufacturing. |
| TRL 9 | Actual system proven in operational environment. | Post-approval activities (Phase 4 studies, safety surveillance). | Budget for lifecycle management. |
3. What are the most common budget-related failures during the transition from mid to high TRLs?
The most common failure is underestimating the cost and complexity of scaling and validation, leading to a funding gap that halts promising technologies.
- Transition from TRL 4 to TRL 5-6: A proof-of-concept prototype (TRL 4) is often developed with research-grade materials and processes. The jump to TRL 5-6 requires initiating GMP process development and conducting GLP non-clinical studies to support an IND application [47]. This shift from research to regulated development entails a significant, non-linear increase in costs for specialized expertise, quality systems, and compliant documentation.
- Transition from TRL 6 to TRL 7-8: Success in early-phase clinical trials (TRL 6) must be followed by even more costly Phase 2/3 trials and GMP manufacturing scale-up (TRL 7-8) [47]. Budget forecasts often fail to account for the sheer expense of running large-scale, multi-center trials and validating commercial-scale manufacturing processes. A lack of proactive budget planning for these stages is a primary reason projects stall.
4. Beyond TRL, what other "readiness levels" should I consider for comprehensive planning?
While TRL assesses core technological maturity, a successful launch depends on other critical factors. Several complementary frameworks exist to provide a more holistic assessment [48].
- Manufacturing Readiness Level (MRL): Measures how close a technology is to being manufactured at scale. A high-TRL prototype may have a low MRL if it relies on non-scalable processes or materials [48].
- Commercial Readiness Level (CRL): Assesses market demand, competitive advantage, and business model viability. A "technically perfect" product will fail without a validated market [48].
- Integration Readiness Level (IRL): Evaluates the maturity of interfaces and compatibility between subsystems. This is crucial for complex technologies involving hardware, software, and data integration [48].
Troubleshooting Guide: Common Implementation Hurdles
| Problem | Underlying Cause | Solution & Action Plan |
|---|---|---|
| "Valley of Death": Promising basic research (TRL 3-4) fails to attract further development funding [46]. | Lack of a clear, de-risked path to commercial application; research outcomes not aligned with industry needs. | Action Plan: 1. Engage Early: Involve potential industry partners or technology transfer offices during TRL 2-3. 2. Draft a Target Product Profile (TPP): Early in development (by TRL 5), create a draft TPP detailing the desired safety, efficacy, and product characteristics. This aligns research with regulatory and market expectations [47]. 3. Public-Private Partnerships: Seek specialized R&D funding designed to foster collaboration between academia and industry [46]. |
| Runaway Cloud/IT Costs: Data storage and computational expenses for research (e.g., bioinformatics) spiral out of control. | Unmonitored usage-based pricing; over-provisioned resources; idle but active services [49] [50]. | Action Plan: 1. Adopt FinOps Principles: Implement financial governance for cloud spending. Track and attribute costs to specific projects [50]. 2. Right-Sizing: Regularly review and match resource allocations (e.g., VM sizes) to actual workload requirements [50]. 3. Automate Lifecycle Policies: Set rules to automatically archive data to cheaper storage tiers and shut down unused environments [50]. |
| Insufficient Non-Technical Budget: The project has funding for experimental work but lacks budget for critical ancillary activities. | Budgeting focused solely on direct research costs (reagents, salaries) while overlooking indirect needs. | Action Plan: 1. Conduct a Comprehensive Audit: Map all fixed and variable costs, including software licenses, equipment maintenance, and contract services [50]. 2. Create Budget Scenarios: Model financial requirements for different outcomes (e.g., success in a key experiment requiring immediate scale-up). 3. Prioritize with a Framework: Rank all initiatives based on impact and alignment with strategic objectives to guide reallocation [49]. |
| Poor Vendor & Contract Management: High costs for reagents, software, or equipment with poor service levels. | Lack of centralized oversight; auto-renewing contracts without performance review; fragmented purchasing across labs [50]. | Action Plan: 1. Consolidate and Negotiate: Consolidate purchases with key vendors to secure volume discounts. Renegotiate contracts based on usage data and market benchmarking [50]. 2. Implement Continuous Evaluation: Track vendor performance against agreed service-level agreements (SLAs). Run regular RFPs to maintain competitive pricing [50]. |
The Scientist's Toolkit: Essential Research Reagent Solutions
This table details key materials and their functions in the context of high-TRL biomedical research and development.
| Item / Solution | Function in Development | Budget & Scaling Consideration |
|---|---|---|
| GMP Pilot Lot | A product batch manufactured under Good Manufacturing Practice for use in non-clinical and early clinical trials (TRL 6) [47]. | Represents a major cost jump from research-grade material. Requires validated processes, quality control, and stringent documentation. |
| Validated Assay Kits | Qualified and validated analytical methods used for product characterization, release, and immunogenicity testing (from TRL 5 onward) [47]. | More expensive than research-use-only kits. Essential for generating data acceptable to regulatory authorities. |
| Relevant Animal Model | An appropriate and relevant in vivo model for efficacy and dose-ranging studies (developed from TRL 4 onward) [47]. | Development and maintenance are costly. Validation is required for regulatory acceptance under, for example, the FDA Animal Rule [47]. |
| Stable Cell Line | A consistent and reproducible biological system for producing biologics (therapeutics/vaccines). Critical for process development (TRL 5+). | Investing in a high-quality, stable cell line early prevents scalability and consistency issues later, saving significant costs. |
Phased Technology Adoption Workflow
The following diagram visualizes the staged process of implementing a technology, showing how activities at each TRL phase connect and which budget strategies to apply.
Diagnostic and Resolution Flowchart
This troubleshooting diagram outlines a systematic process for diagnosing and resolving common budget and project stagnation issues.
Forensic laboratories operate at a critical crossroads, balancing their scientific mission with complex financial realities. The modern forensic lab must sustain parallel infrastructures—from consumable-heavy DNA analysis to capital-intensive digital forensics—amid finite resources [51]. Effective forensic lab management now requires treating operations not only as scientific enterprises but also as financial systems that must optimize return on investment (ROI), manage risk, and ensure long-term sustainability [51].
The challenge is particularly acute for researchers and scientists seeking funding for new technology implementation. With traditional forensic science evidence types such as fingerprints receiving only 1.3% of total UK research council funding (2009-2018), and DNA analysis just 5.1%, the competition for resources is intense [1]. This resource constraint makes robust budget justification frameworks essential for securing funding for technological advancements.
This article provides a comprehensive framework for demonstrating ROI through quantifiable metrics, specifically case turnaround times and accuracy improvements, while addressing the Technology Readiness Level (TRL) scaling challenges unique to forensic research environments.
Core Budget Justification Concepts
Understanding Budget Justification in Forensic Contexts
A budget justification is a detailed, evidence-based explanation that outlines why specific resources are needed and how they will benefit the agency [52]. It translates scientific needs into financial terms that resonate with decision-makers. A well-crafted budget justification answers critical questions:
- What specific problem is being addressed (e.g., backlog issues, outdated equipment, understaffing)?
- What solution is proposed (e.g., new equipment, specialized training, additional personnel)?
- What data supports the request (e.g., caseload trends, turnaround times, industry standards)?
- What operational impact is expected (e.g., reduced case backlogs, improved forensic accuracy)? [52]
Without solid data to back up claims, budget requests can seem arbitrary. That's why tracking key performance metrics is essential for building compelling justifications [52].
Technology Readiness Levels (TRL) in Forensic Technology Scaling
Technology Readiness Levels (TRL) provide a systematic method for assessing the maturity of technologies during development and acquisition phases [53]. Originally developed by NASA, this nine-level scale has been widely adopted across research and innovation sectors, including by the European Union's Horizon programs [54].
Table: Technology Readiness Levels (TRL) Overview
| TRL | Description | Forensic Technology Example |
|---|---|---|
| 1-2 | Basic principles observed and formulated | Novel forensic concept development |
| 3-4 | Experimental proof of concept and lab validation | Experimental validation of new detection method |
| 5-6 | Validation in relevant environment and prototype demonstration | Prototype testing in simulated forensic workflow |
| 7-8 | System prototype demonstration in operational environment | Field testing of new forensic analysis system |
| 9 | Actual system proven in operational environment | Fully implemented technology in casework |
Understanding TRL is crucial for budget justification as it helps align funding requests with appropriate technology development stages. Research indicates that TRL models may require adaptation for collaborative innovation environments, suggesting forensic researchers should carefully map their technology's maturity when seeking funding [55].
Quantitative Framework for Demonstrating ROI
Establishing Baseline Metrics
Before implementing new technology or seeking additional resources, establishing comprehensive baseline metrics is essential. These pre-implementation measurements provide the reference point against which improvements can be quantified [56] [57].
Key baseline metrics for forensic laboratories include:
- Time spent per role on specific administrative or analytical tasks
- Average cost per forensic analysis or report
- Error rates in manual data processing and analysis
- Current case backlog numbers and growth trends
- Overtime costs linked to analysis or preparation activities [56]
Without establishing these baselines, it becomes impossible to definitively prove the improvement generated by new investments [56].
Core ROI Metrics for Forensic Laboratories
ROI demonstration in forensic science requires tracking both tangible and intangible returns [57]. The most compelling budget justifications connect operational improvements to financial value.
Table: Forensic Laboratory ROI Metrics Framework
| Metric Category | Specific Metrics | Calculation Method | Financial Translation |
|---|---|---|---|
| Time Savings & Productivity | Hours saved per analysis type; Percentage of activities automated; Reduction in report generation time | Pre- and post-implementation time tracking; Activity sampling | Labor cost savings = hours saved × fully burdened hourly rate [56] [57] |
| Operational Efficiency | Case throughput volume; Backlog reduction rate; Cost per case analysis | Caseload tracking; Backlog trend analysis; Cost accounting | Capacity value = additional cases processed × cost avoidance of outsourcing [51] |
| Quality & Accuracy | Error rate reduction; Reanalysis frequency; Protocol compliance improvements | Quality control data; Deviation tracking; Audit results | Risk mitigation = cost avoidance of rework, retesting, or challenged testimony [52] |
| Risk Mitigation | Compliance breach avoidance; Audit preparation time; Data security incidents | Incident reporting; Audit time tracking; Security monitoring | Compliance value = penalty avoidance + reduced audit costs [56] |
Implementing the Measurement Framework
A structured approach to ROI measurement ensures consistent, defensible results. The proven five-step framework below can be adapted for forensic technology implementation:
- Identify the specific workflow being enhanced - Determine whether the technology will impact evidence intake, analysis, reporting, or quality control [57].
- Set pre-implementation baseline metrics - Record current performance data for the targeted workflow [57].
- Forecast expected improvements - Use vendor data, peer-reviewed studies, or internal pilot tests to estimate potential gains [57].
- Track real performance post-implementation - Monitor the same metrics after technology deployment [57].
- Translate performance gains into financial ROI - Convert operational improvements into business value using appropriate calculations [57].
Budget Justification in Practice: Templates and Examples
Structured Justification Methodology
Building a compelling budget justification requires more than simply stating what is needed—it must be backed by data and framed in terms of agency-wide impact [52]. The following step-by-step methodology provides a template for forensic researchers:
Define the Need Clearly - Articulate the specific challenge and its impact on efficiency, case resolution, or accreditation compliance. Example: "The forensic unit is currently processing an average of 300 cases per examiner annually, exceeding the industry recommendation of 250 cases per examiner. Without additional staff, backlog and case turnaround times will continue to increase" [52].
Present Supporting Data - Use laboratory information management systems (LIMS) to collect and present metrics. Example: "Case submissions have increased by 15% over the past three years, while staffing levels have remained the same. This has resulted in a backlog of 500 cases, delaying investigative outcomes" [52].
Detail the Costs - Provide an itemized breakdown of all costs. Example: "Hiring one additional forensic analyst at $55,000/year will allow us to reduce backlog by 30% and maintain a 45-day turnaround time. Comparable agencies maintain a 45-day turnaround with one examiner per 250 cases annually" [52].
Explain the Operational Impact - Connect the funding to tangible operational improvements. Example: "Without additional personnel, the backlog is projected to reach 750 cases within the next fiscal year, negatively impacting investigations and court proceedings" [52].
Connect to Organizational Goals - Align the request with the agency's mission and priorities. Example: "This investment supports our agency's mission to provide timely and accurate investigative support, ensuring efficient case processing and maintaining accreditation standards" [52].
Budget Justification Workflow
The following diagram illustrates the systematic workflow for developing a comprehensive budget justification:
Technology Implementation ROI Timeline
Forensic technology implementation typically follows a predictable ROI timeline, with different metrics becoming measurable at various stages:
The Scientist's Toolkit: Essential Research Reagent Solutions
Table: Forensic Technology Budgeting Essential Tools
| Tool Category | Specific Examples | Function in Budget Justification |
|---|---|---|
| Data Collection Systems | Laboratory Information Management Systems (LIMS); Time-tracking software; Quality management systems | Tracks caseload trends, turnaround times, and error rates to support requests with empirical data [52] |
| Analysis Platforms | Statistical analysis software; Business intelligence tools; Process mining applications | Analyzes performance data to identify bottlenecks and forecast improvement impact [51] |
| Benchmarking Resources | Professional association databases; Accreditation body metrics; Peer laboratory comparisons | Provides industry standards context to justify requests based on established norms [52] |
| Financial Modeling Tools | ROI calculators; Total Cost of Ownership (TCO) models; Sensitivity analysis templates | Quantifies financial impact and demonstrates long-term value of investments [56] [51] |
Troubleshooting Guides and FAQs
FAQ 1: How can I justify technology investments when we're facing budget cuts?
Challenge: Budget committees often view technology investments as discretionary spending during financial constraints.
Solution: Reframe technology as a cost-saving, rather than cost-incurring, initiative. Present a clear before-and-after analysis showing how the technology reduces recurring operational expenses. For example, demonstrate how an automated DNA extraction system reduces per-sample labor costs by 20%, increasing throughput and lowering long-term operational expenditures [51]. Emphasize that strategic technology investment actually mitigates the impact of budget cuts by maintaining service levels with reduced resources.
FAQ 2: What specific metrics are most persuasive to budget committees?
Challenge: Uncertainty about which data points resonate most with financial decision-makers.
Solution: Focus on metrics that connect directly to financial and operational outcomes:
- Cost-per-case: Shows resource efficiency in tangible terms [51]
- Backlog reduction rate: Demonstrates impact on core service delivery [52]
- Turnaround time improvements: Connects to broader justice system efficiency [52]
- Error rate reduction: Quantifies quality improvements and risk mitigation [56]
Supplement these with peer benchmarks showing how your proposal aligns with or exceeds industry standards [52].
FAQ 3: How do we account for intangible benefits in ROI calculations?
Challenge: Some technology benefits, like improved morale or enhanced reputation, resist straightforward quantification.
Solution: Use proxy metrics to translate intangible benefits into tangible terms. For example:
- Risk reduction: Calculate the cost of a compliance breach and estimate how the technology reduces that exposure [56]
- Staff satisfaction: Track reductions in absenteeism or early turnover, which have direct cost implications [58]
- Quality improvements: Measure the reduction in rework or retesting requirements [56]
While not perfect, these proxies provide defensible estimates for benefits that would otherwise be overlooked.
FAQ 4: How should we approach TRL scaling for unproven forensic technologies?
Challenge: Budget committees may be skeptical of technologies at lower TRL levels (1-4).
Solution: Develop a phased funding approach that aligns with TRL progression:
- TRL 1-3: Seek research grants rather than operational funding
- TRL 4-6: Propose pilot implementations with clear success metrics and go/no-go decision points
- TRL 7-9: Position as operational investments with full ROI analysis [53] [55]
This approach matches funding type to technology maturity, reducing perceived risk for decision-makers.
FAQ 5: What's the most common mistake in budget justifications?
Challenge: Undermining credibility through common but avoidable errors.
Solution: Avoid these frequent missteps:
- Measuring activity rather than outcomes: Track cost reductions, not just processing volumes [56]
- Ignoring implementation costs: Include training, integration, and change management in ROI calculations [56]
- Overestimating time-to-value: Use conservative benchmarks (e.g., measurable returns within 90 days for well-implemented projects) [56]
- Undervaluing risk mitigation: Factor in the cost of compliance breaches or quality failures [56]
Successful justifications maintain credibility through realistic projections and comprehensive cost accounting.
Effective budget justification in forensic science requires a systematic approach that connects technological capabilities to operational and financial outcomes. By establishing clear baseline metrics, implementing structured measurement frameworks, and communicating results in terms that resonate with decision-makers, forensic researchers can build compelling cases for technology investments.
The frameworks presented here—centered on case turnaround times and accuracy metrics—provide a roadmap for demonstrating ROI in terms that bridge the scientific and financial domains. As forensic laboratories face increasing pressure to do more with less, these budget justification competencies become essential not just for securing resources, but for advancing the field through strategic technology adoption.
Remember that successful budget justification is not a one-time event but an ongoing practice of measurement, analysis, and communication. By embedding these principles into laboratory operations, forensic researchers can build a reputation for financial accountability that strengthens their case for future investments.
Technical Support Center
Troubleshooting Guides
Guide 1: Troubleshooting GC×GC-MS Analysis for Complex Forensic Mixtures
- Problem: Inadequate separation of analytes in a complex forensic sample (e.g., illicit drugs, fire debris) using 1D GC-MS, leading to co-elution and unreliable results.
- Context: This issue is common when scaling up forensic methods for evidence with a high number of chemical components. One-dimensional chromatography lacks the peak capacity for such complex mixtures [10].
- Root Cause: The primary cause is the limited separation power of the single-column chromatographic system, which cannot resolve all components in a complex sample [10].
Resolution Workflow:
- Quick Fix (Time: 2 hours)
- Action: Increase the modulation period by 1-2 seconds to improve the refocusing of analytes at the start of the second dimension.
- Verification: Re-run a standard mixture. Peak shapes in the 2D chromatogram should appear more symmetric.
- Standard Resolution (Time: 1 day)
- Action: Methodically optimize the temperature program. A slower ramp rate (e.g., 2°C/min instead of 5°C/min) can enhance separation in the first dimension.
- Verification: Process a quality control sample. The total number of detected peaks should increase, and co-elution should be visibly reduced in the 2D contour plot [10].
- Root Cause Fix (Time: 1 week)
- Action: Transition from a quadrupole MS to a time-of-flight (TOF) mass spectrometer if available. The higher acquisition rate of TOF-MS is better suited for capturing narrow peaks generated by GC×GC [10].
- Verification: Perform a validation study with spiked samples to demonstrate improved confidence in compound identification and a lower false-positive rate, a key requirement for courtroom admissibility [10].
Guide 2: Resolving High Error Rates in Novel Forensic Method Validation
- Problem: A new, cost-effective analytical method developed in-house shows unacceptably high error rates during validation, jeopardizing its admissibility under legal standards (e.g., Daubert Standard) [10].
- Context: This is a critical hurdle when scaling a method from Technology Readiness Level (TRL) 3 (research) to TRL 4 (validated for routine use). Courts require a known or potential error rate for scientific evidence [10] [24].
- Root Cause: Lack of robust empirical data and statistical modeling to define the method's performance boundaries and limitations.
Resolution Workflow:
- Quick Fix (Time: 1 day)
- Action: Re-calibrate all instruments with traceable standards and re-analyze a subset of samples. Document every step to identify procedural drift.
- Verification: The relative standard deviation (RSD) of replicate measurements should decrease.
- Standard Resolution (Time: 2-4 weeks)
- Action: Design and execute an intra-laboratory validation study. Have multiple analysts test the method on different days using a designed set of blinded samples that include known negatives and positives.
- Verification: Generate a confusion matrix and calculate the method's false positive and negative rates. This provides an initial, quantifiable error rate [24].
- Root Cause Fix (Time: 6-12 months)
- Action: Lead a collaborative, inter-laboratory trial with other research institutions. Use a shared, open-source protocol and data analysis pipeline (e.g., in R or Python) to gather a large and robust dataset.
- Verification: Publish the collaborative study results, which provide a statistically sound error rate and demonstrate the method's reliability, directly addressing the "known error rate" criterion of the Daubert Standard [10] [24].
Frequently Asked Questions (FAQs)
Q: Our lab faces significant budget constraints. What are the most cost-effective open-source tools for data processing in novel forensic method development?
- A: For data processing and statistical analysis, R and Python with libraries like Pandas and Scikit-learn are indispensable. They offer powerful, reproducible alternatives to expensive proprietary software. For business intelligence and reporting on method performance, Metabase is an excellent open-source option [59].
Q: How can we address the "general acceptance" requirement (from the Frye Standard) when using a novel, open-source-based analytical method?
- A: "General acceptance" is built through peer-reviewed publication and adoption by other experts. You can foster this by:
- Publishing your validation data and open-source protocols in reputable scientific journals.
- Presenting your work at forensic science conferences.
- Engaging with the open-source community to encourage external use and citation of your methods [10].
- A: "General acceptance" is built through peer-reviewed publication and adoption by other experts. You can foster this by:
Q: We are developing a method for a forensic application where no commercial standards exist. How can we proceed without exorbitant costs?
- A: Leverage collaborative synthesis. Partner with university chemistry departments that may synthesize required reference materials as part of academic research. Alternatively, use open-source platforms to create and share digital mass spectral libraries with other labs working on similar compounds, reducing the need for every lab to physically possess every standard.
Q: What is the most efficient way to document our troubleshooting and method validation processes to satisfy legal criteria like the Daubert Standard?
- A: Maintain a detailed, version-controlled electronic lab notebook (ELN). Using an open-source platform like GitLab for your documentation allows you to track every change, the reason for the change (e.g., to resolve a specific troubleshooting issue), and who made it. This creates a transparent, auditable trail that demonstrates rigorous scientific practice [59] [60].
Experimental Protocols for Key Cited Experiments
Protocol 1: Intra-Laboratory Validation of a GC×GC-TOFMS Method for Illicit Drug Profiling
- Objective: To establish the repeatability, reproducibility, and preliminary error rate of a GC×GC-TOFMS method for quantifying cutting agents in street-level drug exhibits.
- Materials: See "Research Reagent Solutions" table below.
- Methodology:
- Sample Preparation: Spike a certified drug matrix (e.g., cocaine HCl) with a range of common adulterants (caffeine, levamisole, phenacetin) at 0.1%, 1%, and 5% (w/w). Prepare 6 replicates per concentration level.
- Data Acquisition: Analyze all samples in a randomized sequence over three separate days by two different analysts using the same GC×GC-TOFMS instrument method.
- Data Analysis: Use open-source data analysis pipelines (e.g., in Python) to perform peak picking, alignment, and integration. Calculate the following for each analyte:
- Repeatability (Relative Standard Deviation within-day)
- Reproducibility (Relative Standard Deviation between-days and between-analysts)
- Calibration curve linearity and limit of detection (LOD).
- Error Rate Calculation: From the blinded samples, calculate the false positive rate (incorrect identification of an adulterant) and false negative rate (failure to identify a present adulterant).
Protocol 2: Collaborative Inter-Laboratory Study for Error Rate Estimation
- Objective: To determine a robust, legally defensible error rate for a novel forensic method through multi-laboratory testing.
- Materials: A central lab prepares and distributes identical sets of 20 blinded samples to all participating laboratories. The set includes true positives, true negatives, and known cross-reactive substances.
- Methodology:
- Protocol Harmonization: All labs use the same open-source, version-controlled standard operating procedure (SOP) hosted on a platform like GitHub.
- Blinded Analysis: Participating labs analyze the samples according to the SOP and report raw data and conclusions to a central coordinator.
- Centralized Data Analysis: The coordinating lab analyzes all results using a standardized, scripted statistical analysis (e.g., using R) to ensure consistency.
- Reporting: The final report details the method's sensitivity, specificity, and likelihood ratios across all participating labs, providing a statistically powerful measure of its performance and error rate for courtroom purposes [24].
The Scientist's Toolkit: Research Reagent Solutions
Table 1: Essential materials for developing and validating cost-effective forensic methods.
| Item | Function/Benefit in Research | Cost-Saving Consideration |
|---|---|---|
| Certified Reference Materials (CRMs) | Provides the gold standard for instrument calibration and method validation, ensuring quantitative accuracy. | Purchase small quantities for critical validation steps only; use in-house prepared quality control materials for daily monitoring. |
| Open-Source Data Analysis Software (R, Python) | Offers powerful, flexible, and reproducible environments for statistical analysis and data visualization, replacing expensive licenses. | Eliminates per-seat licensing fees. The active developer community provides continuous updates and support [59]. |
| Open-Source Chromatography Data Systems (e.g., OpenChrom) | Provides a no-cost alternative for processing and interpreting data from GC×GC and other chromatographic instruments. | Can lead to substantial savings compared to proprietary instrument software licenses, though may require in-house technical expertise. |
| Collaborative Platforms (GitLab, GitHub) | Facilitates version control for protocols and documentation, enabling transparent and efficient collaboration between labs. | Free tiers are available. Improves efficiency and reduces errors in method development, saving personnel time [59]. |
| In-House Prepared Quality Control Materials | A stable, homogenous material used to monitor the daily performance of an analytical method. | Dramatically reduces costs compared to repeatedly purchasing commercial QC materials. Essential for long-term method monitoring. |
Table 2: Summary of cost and performance data for open-source versus proprietary tools.
| Tool Category | Example Open-Source Tool | Example Proprietary Tool | Estimated Cost Saving | Key Performance Consideration |
|---|---|---|---|---|
| Data Processing & Analytics | R, Python, Apache Spark | SAS, JMP, MATLAB | 100% on licensing | Comparable performance for most statistical applications; high customization [59]. |
| Business Intelligence & Reporting | Metabase, LightDash | Tableau, Microsoft Power BI | 100% on licensing | Sufficient for internal dashboards and reporting; may lack some advanced enterprise features [59]. |
| Database Management | PostgreSQL, MongoDB | Oracle Database, Microsoft SQL Server | 80-100% on licensing | Robust and scalable for most laboratory data management needs [59]. |
| Collaboration & Project Management | GitLab, Redmine | Jira, Asana | 100% on licensing (self-hosted) | Excellent for tracking method development sprints, issues, and version control [59]. |
Overcoming Implementation Barriers and Optimizing Limited Resources
Forensic laboratories stand at a scientific crossroads, tasked with maintaining excellence in traditional biological evidence processing while simultaneously integrating complex new digital forensic technologies [51]. This dual mandate creates a significant skills gap, as the technical expertise required for DNA analysis differs substantially from that needed for digital evidence extraction, data storage management, and cybersecurity protocols [51]. Within this challenging environment, forensic professionals face the additional pressure of implementing these evolving technologies amid stringent budget constraints and the need to demonstrate courtroom admissibility under standards such as Daubert and Frye [10].
The consequences of this skills gap are not merely theoretical; they directly impact operational effectiveness. Recent industry findings reveal that 48% of IT professionals and 58% of business professionals have had to abandon projects due to technical skill shortages, with cybersecurity, cloud infrastructure, and AI among the most affected domains [61]. This article explores cost-effective training models specifically designed to bridge this gap, enabling forensic researchers and drug development professionals to advance technologies along the Technology Readiness Level (TRL) scale while maintaining fiscal responsibility and scientific rigor.
Quantitative Landscape: The Cost of Expertise
Understanding the financial dimensions of the skills gap is crucial for developing effective training strategies. The table below summarizes key quantitative data that illustrates both the problem and the economic rationale for strategic investment in training.
Table 1: Skills Gap and Training Impact Metrics
| Metric Area | Specific Statistic | Value | Implication for Forensic Labs |
|---|---|---|---|
| Project Impact | Professionals abandoning projects due to skill shortages [61] | 48% of IT professionals, 58% of business professionals | Directly impacts case backlogs and research timelines |
| Training Support | Professionals lacking adequate learning support [61] | 95% | Highlights a critical gap in current organizational support systems |
| Cost Efficiency | Organizations reporting upskilling is more cost-effective than hiring [61] | 89% | Justifies strategic reallocation of funds from recruitment to development |
| Cost Comparison | Average U.S. cost to upskill an employee vs. hiring a new tech employee [61] | $5,770 (upskilling) vs. $14,170 (hiring) | Represents a 145% cost saving, making a clear financial case for upskilling |
| Digital Forensics | Price range for digital forensic tools and training [62] | $2,000 to over $100,000 | Underscores the need for strategic investment in high-return tools and training |
The data reveals a clear economic imperative: investing in internal skill development is significantly more cost-effective than external hiring [61]. For forensic laboratories operating under fixed budgets, this means that reallocating resources from recruitment efforts to comprehensive upskilling programs can simultaneously address capability gaps and improve financial efficiency.
Strategic Budget Allocation for Maximum Impact
Effective management of forensic technology budgets requires understanding the distinct financial profiles of different forensic disciplines. DNA forensics operates primarily through operational expenditures (OpEx), with recurring costs for reagents, test kits, and consumables, while digital forensics demands significant capital expenditures (CapEx) for hardware, software, and storage infrastructure [51].
Table 2: DNA vs. Digital Forensics Cost Profile Comparison
| Category | DNA Forensics | Digital Forensics |
|---|---|---|
| Primary Cost Type | Operational (reagents, consumables) [51] | Capital (hardware, software, storage) [51] |
| Recurring Expenses | Kits, QA/QC, service contracts [51] | Software updates, cybersecurity, data backups [51] |
| ROI Horizon | Short-term (backlog reduction, compliance) [51] | Long-term (infrastructure, case capacity) [51] |
| Major Risk Factor | Contamination, supply chain volatility [51] | Data breaches, technological obsolescence [51] |
| Training Focus | Molecular biology, accreditation standards [51] | Cybersecurity, cloud forensics, data integrity [51] |
Adopting a mission-weighted budgeting approach ensures funds are distributed according to evidence type prevalence, turnaround expectations, and public safety impact rather than historical precedent [51]. This strategic alignment is particularly important as digital evidence accounts for increasingly large portions of caseloads while often receiving disproportionately small budget allocations [51].
TRL Framework for Systematic Technology Implementation
For forensic researchers and drug development professionals, the Technology Readiness Level (TRL) framework provides a structured methodology for scaling technologies from basic research to court-admissible evidence or approved medical products [47] [63]. This framework is particularly valuable for planning stage-appropriate training interventions.
Diagram: TRL Workflow for Forensic and Drug Development Technologies
The following table details key activities and training focus areas at critical TRL stages, adapted for forensic and medical product development contexts [47] [63]:
Table 3: TRL Stages, Activities, and Corresponding Training Needs
| TRL Stage | Key Activities | Technical Skills Required | Cost-Effective Training Approach |
|---|---|---|---|
| TRL 1-3(Basic Research to Proof of Concept) | Scientific review, hypothesis development, preliminary efficacy testing [63] | Literature analysis, experimental design, laboratory techniques | Academic collaborations, journal clubs, method-specific workshops |
| TRL 4-5(Lab Validation to Advanced Characterization) | Non-GLP in vivo studies, assay development, preliminary manufacturing [63] | Animal models, assay validation, analytical method development | Vendor-based instrument training, cross-functional team projects |
| TRL 6-7(Pilot Scale to Scale-Up) | GMP manufacturing, regulatory submissions, Phase 1/2 clinical trials [63] | GMP compliance, regulatory writing, clinical trial management | Professional certifications, GMP training, expert consultants |
| TRL 8-9(Approval to Post-Market) | Pivotal studies, FDA submission, post-marketing surveillance [63] | Court testimony, quality management, post-market studies | Mock trial training, audit preparation, advanced statistical analysis |
Cost-Effective Training Models for Forensic Technologies
Hybrid Learning Models
By 2025, hybrid learning models that blend in-person and virtual methods will dominate technical training landscapes [64]. This approach offers significant cost savings by reducing travel expenses and time away from casework while maintaining the effectiveness of hands-on components. Forensic laboratories can implement this model by partnering with training providers who offer modular programs combining self-paced digital content with intensive virtual instructor-led sessions for complex practical skills.
Microcredentials and Certification Programs
Certifications are currently the number one factor in earning promotions or raises for tech professionals, with 46% of IT employees reporting salary increases or promotions as a direct result of certifications [61]. For forensic professionals, targeted microcredentials in specialized areas such as cloud forensics, advanced spectroscopic analysis, or regulatory compliance provide cost-effective pathways to developing specific competencies without the expense of degree programs.
AI-Powered Personalized Learning
Artificial Intelligence is revolutionizing training program design by analyzing learner behavior to create personalized learning paths [64]. AI-powered systems can recommend specific modules based on an individual's knowledge gaps, performance metrics, and casework requirements. This targeted approach reduces training time and ensures resources are focused on addressing specific skill deficiencies rather than taking a one-size-fits-all approach.
Cross-Training and Knowledge Sharing
Limited cross-training between DNA and digital analysts can foster operational flexibility without compromising accreditation standards [51]. Implementing structured job rotation programs and internal knowledge-sharing platforms creates internal expertise networks that reduce dependency on external consultants. Digital analysts with strong data management skills can assist in LIMS administration, while DNA analysts can provide valuable insights for biological data interpretation in digital contexts [51].
Troubleshooting Guides: Technical Support Center
Systematic Troubleshooting Methodology
Diagram: Systematic Troubleshooting Methodology
Frequently Asked Questions
Q: What is the first step when encountering an unfamiliar technical issue during analysis? A: Begin by thoroughly understanding the problem. Ask targeted questions to determine exactly what the user was trying to accomplish versus what actually occurred. Gather relevant logs, product usage information, and attempt to reproduce the issue in a controlled environment [65] [66]. This systematic approach prevents misdiagnosis and wasted effort.
Q: How can we efficiently isolate the root cause of instrumentation problems? A: Apply a systematic isolation approach: remove complexity by eliminating variables such as browser extensions, environmental factors, or customizations. Change only one thing at a time between tests, and compare the malfunctioning system to a known working configuration to identify critical differences [65].
Q: What communication strategies improve customer cooperation during extended troubleshooting? A: Position yourself as the customer's advocate. Emphasize that you're working together to solve the problem, express empathy for their frustration, and keep technical explanations at an appropriate level. Structure communication with numbered steps rather than paragraphs, and proactively provide links to resources for any complex procedures you're asking them to perform [65].
Q: How should we approach finding fixes for novel technical problems? A: Develop solutions through iterative testing. Once you've isolated the issue's core components, brainstorm potential fixes and test them in your reproduction environment before involving the customer. Solutions may include workarounds that accomplish the same task differently, configuration changes, or escalating to engineering for software updates [65].
Q: What post-resolution activities provide long-term value? A: Conduct a follow-up to ensure the problem remains resolved and doesn't recur. Document the solution comprehensively for other agents facing similar situations. Share knowledge publicly when appropriate to save time for other customers and prevent duplicate troubleshooting efforts [65] [66].
The Scientist's Toolkit: Essential Research Reagents & Materials
Table 4: Key Research Reagent Solutions for Forensic Technology Development
| Reagent/Material | Function | Application in Forensic Research |
|---|---|---|
| GC×GC-MS Systems | Provides enhanced chromatographic separation for complex mixtures versus 1D GC [10] | Analysis of illicit drugs, fingerprint residue, toxicological evidence, arson investigations |
| Validated Reference Standards | Ensures accuracy and reliability of analytical measurements [47] | Quality control, method validation, instrument calibration across all forensic analyses |
| GMP Pilot Lot Materials | Demonstrates scalable and reproducible manufacturing process [63] | Transitioning forensic techniques from research validation to routine laboratory implementation |
| Specialized Sampling Kits | Preserves integrity of evidence during collection and transport [10] | Maintaining chain of custody, preventing contamination or degradation of sensitive evidence |
| Proprietary Search Profiles | Enables rapid identification of specific file types and digital artifacts [62] | Accelerating digital evidence processing through targeted searches rather than comprehensive analysis |
Navigating the skills gap in evolving forensic technologies requires a strategic approach that aligns training investments with technology readiness levels and operational requirements. By implementing hybrid learning models, pursuing targeted microcredentials, leveraging AI-powered personalization, and fostering cross-functional knowledge sharing, organizations can develop the specialized expertise needed to advance forensic technologies from basic research to court-admissible evidence.
The quantitative evidence clearly demonstrates that strategic upskilling is not an expense but rather a cost-saving investment compared to the alternative of abandoned projects and constant external hiring [61]. For forensic laboratories and drug development professionals operating under budget constraints, these cost-effective training models provide a roadmap for maintaining scientific excellence while responsibly managing public funds and meeting the evolving demands of justice and public health systems.
Managing Data Privacy and Security Concerns Within Budget Constraints
Frequently Asked Questions (FAQs)
| Question | Answer |
|---|---|
| How can we improve data privacy with a limited team? | Adopt Privacy by Design principles. Organizations consistently practicing it are 50% more likely to have appropriately staffed teams and use cross-training of non-privacy staff to close skills gaps [67]. |
| What are cost-effective ways to secure forensic data? | Explore blockchain-based systems for securing and sharing forensic evidence. This provides a decentralized, tamper-resistant platform that can enhance integrity and reduce long-term evidence management costs [68]. |
| Our privacy budget is decreasing. Where should we focus? | Prioritize filling the most critical technical skills gaps. The largest gaps are in experience with different technologies (62%), technical expertise (49%), and IT operations knowledge (45%) [67]. Invest in targeted training in these high-impact areas. |
| How do we validate new forensic methods for court admissibility? | Ensure new methods meet legal standards like the Daubert Standard, which requires testing, peer review, a known error rate, and general acceptance in the scientific community [10]. Build your validation protocols around these criteria. |
| AI uses sensitive data; how can we manage the risk cheaply? | Integrate security from the start of AI development. A proactive approach is more cost-effective than retrofitting security later. Use advanced anomaly detection to monitor AI systems in real-time [69]. |
Troubleshooting Guides
Issue: Understaffed and Underfunded Privacy Team
Problem: More than half (54%) of European professionals expect privacy budgets to decrease in 2025, and 45% report their teams are already underfunded [67]. This leads to overwork, stress, and increased risk.
Solution:
- Cross-Train Existing Staff: Identify non-privacy staff interested in moving into privacy roles and provide training. Over 56% of organizations that practice Privacy by Design successfully use this to decrease skills gaps [67].
- Focus on High-Impact Credentials: When hiring, prioritize practical experience (95% of professionals find it important) and credentials (89%) over university degrees (54%) to find qualified candidates efficiently [67].
- Implement Privacy by Design: Embed privacy across the entire enterprise. This comprehensive approach fosters stakeholder trust and safeguards against evolving threats without requiring a massive team expansion [67].
Issue: Validating New Forensic Technology on a Tight Budget
Problem: New analytical methods for forensic evidence must meet rigorous legal standards before they can be used in court, but full-scale validation studies are expensive [10].
Solution:
- Understand Legal Benchmarks Early: Before investing heavily in a technology, review its alignment with admissibility standards like the Daubert Standard or Mohan Criteria [10].
- Conduct Focused Intra-Laboratory Validation: Start with internal validation studies to establish a baseline for the method's performance and a preliminary error rate [10].
- Seek Academic and Industry Partnerships: Collaborate with universities or other labs to share resources and data for more comprehensive inter-laboratory validation, which strengthens the case for the method's reliability [10].
Problem: AI models are vulnerable to adversarial attacks, data leakage, and model poisoning. The complexity of these systems requires security measures that can be costly to implement [69].
Solution:
- Embed Security in the AI Lifecycle (SecML): Integrate security checks and validation at every stage of AI development—from data collection and training to deployment. This prevents costly security retrofitting later [69].
- Deploy Automated Anomaly Detection: Use open-source or built-in machine learning tools to monitor AI systems in real-time for unusual activity, which can be a cost-effective early warning system [69].
- Implement Strict Data Access Controls: Use role-based access and encryption for sensitive datasets used in AI training to minimize the risk of internal data leaks and external breaches [69].
The following tables consolidate key statistical findings from recent research to inform your decision-making.
Table 1: Privacy Program Funding and Staffing (2025 Projections)
| Metric | Finding | Source |
|---|---|---|
| Budget Outlook | 54% of European professionals expect privacy budgets to decrease in 2025. | [67] |
| Current Underfunding | 45% of European privacy professionals report their organization's privacy budget is underfunded. | [67] |
| Team Understaffing | 52% of technical privacy teams in Europe are understaffed. | [67] |
| Staff Retention | 37% of European organizations struggle to retain qualified privacy professionals. | [67] |
Table 2: Top Privacy and Security Skills Gaps
| Skills Gap Area | Percentage of European Organizations Reporting | Source |
|---|---|---|
| Experience with different types of technologies and/or applications | 62% | [67] |
| Technical expertise | 49% | [67] |
| IT operations knowledge and skills | 45% | [67] |
Workflow and Process Diagrams
Forensic Tech Implementation Workflow
Data Security Risk Assessment Logic
The Scientist's Toolkit: Research Reagent Solutions
| Tool / Solution | Function in Research |
|---|---|
| Privacy by Design Framework | A systematic approach to embedding privacy into technologies and business practices from the start, reducing long-term compliance costs and building trust [67]. |
| Blockchain-Based Evidence Ledger | A decentralized system for securing and sharing forensic evidence, creating an immutable chain of custody that is highly resistant to tampering [68]. |
| Cross-Training Program | A structured plan to train interested non-privacy staff (e.g., from IT or compliance) to support privacy functions, effectively closing skills gaps without new hires [67]. |
| Digital Twin Generator | An AI-driven model that predicts individual patient disease progression, used to create virtual control arms in clinical trials, reducing costs and speeding up recruitment [70]. |
| Admissibility Standards Checklist | A validation checklist based on legal criteria (Daubert, Frye, Mohan) to ensure new forensic methods are developed with court admissibility in mind from the beginning [10]. |
Navigating Regulatory Compliance Without Excessive Expenditure
Technical Support Center
Frequently Asked Questions (FAQs)
FAQ 1: How can we integrate compliance planning early in the technology development lifecycle to minimize costs? Integrating compliance during the early Technology Readiness Level (TRL) stages is the most effective cost-saving strategy. At TRL 1-4 (basic research to lab validation), you should initiate regulatory gap assessments and create a roadmap for required testing and documentation. This proactive approach prevents costly redesigns and remediation at higher TRL stages. For instance, a gap assessment conducted at the proof-of-concept stage (TRL 3) can identify potential regulatory deviations early, when corrections are least expensive to implement [71] [72].
FAQ 2: What are the most common documentation gaps that delay regulatory approvals? Based on analyses of device submissions, the most frequent documentation gaps leading to delays include inadequate Clinical Evaluation Reports (CERs), insufficient risk management files (per ISO 14971), and incomplete software documentation (per IEC 62304). A significant 40% of medical device submissions are delayed specifically due to inadequate clinical evaluations. Ensuring these documents are rigorously prepared and updated throughout the product lifecycle is crucial for avoiding costly submission rejections [71].
FAQ 3: How can AI tools specifically help reduce compliance costs in drug development? Generative AI and other AI tools can reduce regulatory compliance costs by automating labor-intensive processes. Key applications include using Natural Language Processing (NLP) to expedite regulatory document creation and validation, and automating compliance checks against current guidelines. These AI-driven checks proactively identify potential issues, reducing the risk of regulatory delays. Experts project that at peak adoption, AI could reduce costs associated with regulatory submissions by over 50% [73].
FAQ 4: What is a mission-weighted budgeting strategy for a forensic lab managing both DNA and digital evidence? Mission-weighted budgeting allocates funds based on empirical data like evidence type prevalence and public safety impact, rather than historical precedent. For example, if digital evidence accounts for 70% of your incoming caseload but only 30% of your current budget, rebalancing is necessary to maintain service quality and accreditation. This strategy treats budgeting as a portfolio management exercise, directing capital where it yields the greatest organizational return, such as reducing backlogs or improving turnaround times [51].
FAQ 5: When should a forensic or R&D lab consider outsourcing regulatory compliance functions? Outsourcing is a strategic solution when in-house expertise is lacking or when specialized, scalable resources are needed. This is particularly beneficial for smaller companies that cannot support full-time, in-house regulatory teams, and for larger organizations during peak periods or for complex projects. Outsourcing provides access to specialized expertise for tasks like creating technical documentation, preparing for FDA submissions, or managing post-market surveillance, allowing your core team to focus on research and development [71].
Troubleshooting Guides
Problem 1: Inefficient Resource Allocation Between DNA and Digital Forensics
- Symptoms: Rising backlog in one evidence domain, frequent budget overruns on consumables or IT infrastructure, inability to take on new types of cases.
- Diagnosis: Budgets are not aligned with current caseload demands and mission impact. DNA forensics is primarily driven by operational expenditures (OpEx) like reagents, while digital forensics requires high capital expenditure (CapEx) for hardware and storage [51].
- Solution:
- Quantify Cost-Per-Case: Calculate the total cost (including labor and consumables) to process a single case for both DNA and digital evidence [51].
- Perform Variance Analysis: Quarterly, compare projected vs. actual spending to identify areas of deviation and recalibrate the budget accordingly [51].
- Rebalance Using Data: Use mission-weighted budgeting to align fund distribution with the actual volume and impact of each evidence type [51].
- Preventative Measures:
- Implement regular (quarterly) financial forecasting and review.
- Diversify funding sources by applying for federal grants (e.g., National Institute of Justice grants for DNA capacity) [51].
Problem 2: High Costs and Delays in Pre-Market Regulatory Submissions
- Symptoms: Regulatory submissions are returned for deficiencies, requiring multiple rounds of review and leading to delayed time-to-market.
- Diagnosis: Inadequate preparation of technical documentation and a reactive, rather than proactive, compliance strategy.
- Solution:
- Conduct a Pre-Submission Gap Assessment: Perform a comprehensive review of your technical documentation against target market requirements (e.g., FDA, EU MDR) to identify and correct deviations early [71].
- Leverage Regulatory Intelligence Tools: Use AI-powered systems to rapidly analyze updated guidelines and ensure ongoing compliance [73].
- Invest in Proactive Lifecycle Management: Continuously manage documentation updates to reflect any changes in device design, manufacturing, or regulations [71].
- Preventative Measures:
Quantitative Data Summaries
Table 1: Forensic Lab Budgeting - DNA vs. Digital Evidence Cost Profile
| Category | DNA Forensics | Digital Forensics |
|---|---|---|
| Primary Cost Type | Operational (OpEx): reagents, consumables [51] | Capital (CapEx): hardware, software, storage [51] |
| Major Recurring Expenses | Test kits, QA/QC supplies, equipment service contracts [51] | Software licensing updates, cybersecurity measures, data backup systems [51] |
| Typical ROI Horizon | Short-term (backlog reduction, case compliance) [51] | Long-term (infrastructure development, future case capacity) [51] |
| Major Financial Risk | Supply chain volatility, sample contamination [51] | Rapid technology obsolescence, data breach [51] |
Table 2: Projected Cost Reduction from AI in Drug Discovery and Early Development
| Development Phase | Expected Cost Reduction at Peak AI Adoption [73] | Primary AI Application Driving Savings [73] |
|---|---|---|
| Target Identification | 67% | AI-powered virtual screening of compound libraries. |
| Target Validation | 66% | Generative models for de novo drug design and exploration. |
| Lead Optimization | 63% | AI-driven refinement of chemical structures and property prediction. |
| Study Design | 62% | Data-driven optimization of trial parameters and patient populations. |
| Regulatory Submission | 54% | Automation of compliance checks and document creation (e.g., via NLP). |
| Preclinical Testing | 44% | Predictive modeling of toxicity and pharmacokinetics. |
Experimental Protocols
Protocol 1: Cost-Benefit Analysis for Forensic Laboratory Resource Justification
- Purpose: To objectively evaluate and justify the allocation of additional resources to a specific workflow (e.g., DNA analysis) by demonstrating its net benefit, particularly through improved timeliness [74].
- Methodology:
- Define the Metric: The primary measure of service effectiveness in forensics is often timeliness (e.g., reducing case backlog, decreasing turnaround time) [74].
- Quantify the Benefit: Use historical data to model the impact of additional resources on timeliness. A key benefit can be measured through the value of generated investigative leads. For example, calculate the potential reduction in recidivism or the acceleration of case resolution that results from faster evidence processing [74].
- Calculate Net Benefit: Compare the quantified benefit (e.g., societal cost savings from prevented crime) against the total cost of the proposed additional resources (e.g., new equipment, personnel) [74].
- Compare Options: Use this cost-benefit analysis to objectively compare various competing options for resource deployment within the lab [74].
Protocol 2: Implementing AI for Virtual Screening in Early Drug Discovery (TRL 4-5)
- Purpose: To accelerate the target identification and hit generation stages of drug discovery, reducing reliance on costly physical high-throughput screening [75] [73].
- Methodology:
- Data Preparation: Curate large, machine-readable databases of chemical and biological data (e.g., from public libraries like ChEMBL or PubChem) to train machine learning models [75].
- Model Training & Validation:
- Train deep learning algorithms (e.g., platforms like DeepTox or MoleculeNet) on this data to predict drug-target interactions, binding affinity, and toxicity [75].
- Validate the model's predictions in a simulated or lab environment (TRL 4-5) by comparing its output against known experimental results [72] [73].
- Virtual Screening: Use the validated AI model to perform in silico screening of millions of compounds, rapidly prioritizing a shortlist of the most promising candidate molecules for synthesis and physical testing [75] [73].
- Outcome Assessment: The success of this protocol is measured by the significant reduction in time (up to 40-50%) and resources needed to identify viable lead compounds compared to traditional methods [76] [73].
Workflow and Process Diagrams
Diagram Title: Forensic Lab Budget Optimization Process
Diagram Title: AI-Accelerated Drug Discovery Pathway
The Scientist's Toolkit: Key Research Reagent Solutions
Table 3: Essential Platforms and Tools for Cost-Effective R&D
| Item Name | Function & Explanation | Relevance to Budget/Compliance |
|---|---|---|
| Public Chemical Databases (e.g., ChEMBL, PubChem) [75] | Machine-readable databases containing information on millions of molecules and their biological activities. Used to train AI/ML models for virtual screening, reducing initial compound acquisition costs. | Provides a low-cost, extensive data foundation for AI-driven discovery, minimizing early-stage spending on proprietary compound libraries. |
| AI Toxicity Prediction Platforms (e.g., DeepTox, MoleculeNet) [75] | Platforms that use machine learning to predict the toxicity of compounds based on their chemical structure. | Enables early in-silico safety screening, reducing late-stage, costly failures in preclinical and clinical trials due to toxicity issues. |
| Molecular Docking Software [75] | Computational tools used to predict the binding affinity and orientation of a small molecule (drug candidate) to its target protein. | Streamlines lead optimization by prioritizing compounds with the highest likelihood of success before synthesis, saving reagent and labor costs. |
| Regulatory Intelligence AI Tools [73] | AI systems (often using NLP) that automatically analyze extensive documentation, guidelines, and regulations from authorities like the FDA and EMA. | Automates compliance monitoring, reduces the risk of costly submission delays, and minimizes the need for large, specialized in-house regulatory teams. |
| Gap Assessment Services [71] | External consulting services that perform audits of technical documentation against regulatory standards to identify deficiencies before formal submission. | A strategic upfront investment that prevents vastly more expensive remediation efforts and project delays after a regulatory rejection. |
Maintenance and Sustainability Planning for Forensic Technology Investments
Forensic science institutions globally operate under significant pressure, balancing the need for cutting-edge technological capabilities with severe budget constraints. The crisis is multifaceted, impacting service provision, quality, and research. In England and Wales, for instance, spending on forensic science services has been reduced by over 60% since 2008, creating an unsustainable market that prioritizes cost over quality [2]. This environment makes the maintenance and sustainable planning of existing technology investments not merely an operational concern but a critical strategic imperative. The concept of 'frugal forensics' has emerged as a response, advocating for sustainable provision of transparent, high-quality forensic services that meet specific jurisdictional needs and limitations [35]. This technical support center is designed within this context, providing researchers and forensic professionals with practical guidance for maintaining technological assets and troubleshooting common issues despite resource limitations.
Technical Support Center: FAQs and Troubleshooting Guides
General Technology Maintenance FAQs
Q1: What are the primary challenges in maintaining forensic instruments in resource-limited settings? The core challenges include: limited funding for replacement parts and service contracts, lack of access to specialized technical expertise, supply chain disruptions for critical consumables, and difficulties in maintaining quality assurance frameworks. Sustainable service provision requires a principle-based approach that aligns with the United Nations Sustainable Development Goals, focusing on narrowing inequalities between well-resourced and under-resourced jurisdictions [35].
Q2: How can laboratories extend the operational lifespan of their existing forensic technology? Implementing rigorous preventive maintenance schedules, cross-training staff on basic troubleshooting, establishing partnerships with academic institutions for shared expertise, and utilizing open-source software alternatives where legally admissible. Research indicates that only 0.01% of the total UK Research and Innovation budget was allocated to forensic science research (2009-2018), making resource extension essential [2].
Q3: What legal standards must maintained forensic technology meet for evidence to be admissible in court? In the United States, techniques must meet the Daubert Standard, which requires that methods can be tested, have been peer-reviewed, have a known error rate, and are generally accepted in the relevant scientific community. In Canada, the Mohan criteria require relevance, necessity, absence of exclusionary rules, and a properly qualified expert. Proper maintenance documentation is crucial to demonstrating these standards are continually met [10].
Specific Equipment Troubleshooting Guides
Forensic Imaging Station (Atola Insight Forensic)
Q1: The hardware unit does not boot. What steps should I take? This is often caused by connected USB devices interfering with the boot process. Follow this systematic approach:
- Immediate action: Detach all USB cables and restart the unit.
- Full reset procedure:
- Power the hardware unit off completely.
- Detach all cables and devices (PSU cable, Extension module, all SATA cables, and any USB devices).
- Leave the unit powered off for 3-5 minutes to ensure a full reset of internal circuits.
- Plug in only the power cable (no network, USB, or SATA cables yet).
- Power the system on and check the PWR LED on the back after 15 seconds [77].
Q2: The imaging process is extremely slow for a damaged drive. How can I optimize this? Atola Insight Forensic is specifically designed for damaged media. For optimal performance:
- Run automatic diagnostics first: This 2-minute check identifies specific drive issues (PCB instability, motor problems, short circuits, firmware errors, degraded heads, physical media damage) and recommends appropriate handling.
- Utilize advanced imaging settings: For drives with degraded or damaged heads, use the head-disabling function to image only with functional heads, significantly increasing speed and preventing further damage.
- Employ complex multipass imaging: The system can be configured for multiple passes with different read strategies to maximize data recovery from problematic sectors [77].
Q3: Software is stuck at "Searching for the DiskSense unit." How do I resolve this? This typically indicates a license detection issue. The resolution path is:
- Basic connectivity check: Verify you can ping the DiskSense unit's IP address from your Windows PC.
- License manager reconfiguration:
- Open http://localhost:1947 in a web browser.
- Click
Configurationin the left menu. - Select
Access to Remote License Managers. - Enable both
Broadcast Search for Remote LicensesandAggressive Search for Remote Licenses. - Wait approximately one minute for detection.
- Ensure the
Remote License Search Parametersfield is either empty or contains the DiskSense unit's specific IP address (the latter is preferable) [77].
Digital Forensics Workstation (Autopsy)
Q1: Autopsy is experiencing interface issues or missing menu items. What can I do? This often requires a user interface reset:
- Try initial reset: Go to
Window -> Reset Windows. This will cause Autopsy to restart but will reopen your case if one was active. - If problems persist: Delete the Autopsy user folder (located at
C:\Users\(user name)\AppData\Roaming\autopsyon Windows). Note that this will remove all your settings, including keyword lists, interesting file sets, and configuration. To preserve settings, back up this folder first, then selectively restore configuration files after regeneration [78].
Q2: An ingest module seems stuck. How can I diagnose this?
- Generate a thread dump: Go to
Help > Thread Dumpin the UI. This creates a snapshot of all running processes. - Analyze the dump: Look for any mention of "deadlock" which indicates stuck processes. Even without deadlocks, the dump shows which threads are active and may identify the bottleneck.
- Check logs: Navigate to the log folder (
Help > Open Log Folder) and examineautopsy.log.0for entries marked "SEVERE" or "WARNING" that correspond to the time of the hang [78].
Analytical Instrumentation (GC×GC Systems)
Q1: Our laboratory is considering implementing GC×GC technology. What are the key maintenance and validation requirements? GC×GC (Comprehensive two-dimensional gas chromatography) offers enhanced separation for complex forensic samples but requires careful maintenance planning:
- Legal validation: Establish rigorous procedures meeting Daubert Standard requirements, including documented error rates, peer-reviewed methodologies, and general acceptance protocols.
- Technical maintenance: Regular modulator maintenance, column trimming, and detector calibration are critical. Develop in-house expertise as external service contracts may be cost-prohibitive.
- Quality assurance: Implement ongoing validation using standard reference materials to maintain separation efficiency and detection sensitivity [10].
Q2: How can we maintain GC×GC systems with limited access to manufacturer support?
- Establish internal training programs focusing on basic troubleshooting of common issues like peak broadening, retention time shifts, and signal degradation.
- Develop partnerships with local universities for access to technical expertise and shared calibration standards.
- Implement comprehensive documentation practices to track system performance trends and anticipate maintenance needs [10].
Quantitative Data on Forensic Technology Funding and Implementation
Table 1: Analysis of Forensic Science Research Funding in the UK (2009-2018)
| Category | Number of Projects | Total Funding | Percentage of Total Forensic Funding |
|---|---|---|---|
| Total Forensic Science Projects | 150 | £56.1 million | 100% |
| Technology Development Focus | 104 | £37.2 million | 69.5% |
| Foundational Research | 29 | £10.7 million | 19.2% |
| Digital/Cyber Forensics | 38 | £14.4 million | 25.7% |
| DNA Analysis | 8 | £2.9 million | 5.1% |
| Fingerprint Analysis | 2 | £0.7 million | 1.3% |
Source: Adapted from UK Research and Innovation data [2]
Table 2: Technology Readiness Levels (TRL) for GC×GC in Forensic Applications
| Application Area | Current TRL (1-4 Scale) | Key Barriers to Implementation | Maintenance Considerations |
|---|---|---|---|
| Illicit Drug Analysis | Level 3 | Validation standards, error rate documentation | Daily system suitability testing, reference standard verification |
| Toxicology | Level 3 | Method standardization, quality control protocols | Regular column maintenance, detector calibration |
| Fingermark Chemistry | Level 2 | Reproducibility between laboratories, data interpretation | Controlled environment for consistency, standardized sample preparation |
| Petroleum Analysis (Arson) | Level 3 | Reference database completeness, data processing methods | Source calibration, library updates |
| Oil Spill Tracing | Level 4 | Laboratory networking, data sharing protocols | Cross-lab proficiency testing, method transfer validation |
Source: Adapted from current literature on GC×GC forensic applications [10]
Experimental Protocols for Sustainable Technology Implementation
Protocol: Validation of Analytical Methods for Court Admissibility
Purpose: To establish a framework for validating and maintaining forensic analytical methods that meet legal admissibility standards under budget constraints.
Materials:
- Reference standards of known composition
- Casework representative samples
- Documentation system (electronic or paper-based)
- Quality control materials
Methodology:
- Testing the Technique: Design experiments that challenge the method's limitations and boundaries. Document all testing conditions and outcomes thoroughly [10].
- Peer Review Process: Submit methods for publication in peer-reviewed journals or present at professional conferences to establish general acceptance [10].
- Error Rate Determination: Conduct repeated measurements of known standards to calculate method precision and accuracy. Establish acceptable tolerance limits for casework [10].
- Maintenance of Standards: Implement a schedule for regular recalibration and proficiency testing to ensure ongoing reliability [10].
Sustainability Adaptation: For resource-limited settings, focus validation on the most critical casework analyses first. Partner with other laboratories to share validation data and reduce redundant testing.
Protocol: Automated Data Collection for Resource Optimization
Purpose: To implement automated data collection systems that reduce long-term operational costs while maintaining data quality.
Materials:
- Sensor arrays appropriate for the analytical technique
- Data logging system (commercial or open-source)
- Remote access capability
- Data storage and backup system
Methodology:
- System Design: Based on the world's first fully automated forensic taphonomic data collection system, identify key parameters for automated monitoring in your specific forensic application [79].
- Calibration Protocol: Establish baseline measurements and regular calibration checks for automated systems.
- Data Integrity Verification: Implement procedures to verify automated data collection accuracy through periodic manual checks.
- Remote Monitoring Setup: Configure systems for remote access to reduce physical presence requirements and associated costs [79].
Sustainability Benefits: Automation substantially reduces the cost of actualistic data collection, improves data resolution, and enables remote operation and simultaneous multi-location experiments [79].
Workflow Diagrams for Troubleshooting and Sustainability Planning
Troubleshooting Decision Pathway
Sustainability Planning Workflow
The Scientist's Toolkit: Essential Research Reagent Solutions
Table 3: Essential Materials for Sustainable Forensic Technology Maintenance
| Item/Category | Function | Sustainable Practice |
|---|---|---|
| Reference Standards | Calibration and validation of analytical instruments | Implement careful inventory management; share standards between laboratories where possible |
| Quality Control Materials | Ongoing verification of instrument performance | Develop in-house QC materials where commercially available ones are cost-prohibitive |
| Data Management System | Documentation of maintenance, calibration, and troubleshooting | Utilize open-source platforms adapted for forensic requirements |
| Preventive Maintenance Kits | Regular upkeep of instrumentation | Create customized kits with essential components for specific instrument types |
| Technical Documentation | Guidance for troubleshooting and maintenance | Develop laboratory-specific manuals incorporating manufacturer guides and local experience |
| Remote Monitoring Technology | Reduced physical presence requirements | Implement cost-effective sensor systems for continuous equipment monitoring |
| Training Materials | Staff competency development | Create video libraries and interactive guides for common maintenance procedures |
The maintenance and sustainability of forensic technology investments in an era of budget constraints requires a systematic approach that balances immediate troubleshooting needs with long-term strategic planning. By implementing structured troubleshooting guides, comprehensive validation protocols, and strategic sustainability planning, forensic institutions can extend the operational lifespan of their technological assets while maintaining the quality standards required for legal admissibility. The integration of automation technologies and shared resource models offers promising pathways for reducing costs while enhancing capabilities. As the field continues to evolve, a commitment to knowledge sharing between well-resourced and resource-limited jurisdictions will be essential for advancing forensic science as a global practice that supports justice systems worldwide [35].
In the field of forensic technology, researchers and drug development professionals operate within a landscape defined by stringent budget constraints. The effective implementation and scaling of new technologies from low to high Technology Readiness Levels (TRL) demands a strategic approach to financial resource management. This guide provides a framework for creative budget allocation, enabling research teams to reallocate internal savings to fund high-impact technologies such as advanced digital forensics platforms, artificial intelligence (AI)-driven analytics, and automated laboratory systems. By adopting a disciplined approach to cost-saving and strategic reinvestment, organizations can accelerate the pace of innovation, enhance the capabilities of their technical support infrastructure, and maintain a competitive edge in a rapidly evolving field. The subsequent sections will outline specific cost-saving methodologies, provide protocols for evaluating technology impact, and present a detailed troubleshooting guide to support researchers in optimizing their forensic technology investments.
Forensic Technology Market Context
The market for forensic technology services is substantial and has demonstrated consistent growth, underscoring the importance of strategic investment. In the United States, the forensic technology services industry is a $3.7 billion market as of 2025 [80]. Over the past five years, the industry has experienced a compound annual growth rate (CAGR) of 1.4%, with revenue increasing 0.4% in 2025 alone [80]. This growth occurs within a complex environment where government spending—the primary source of industry revenue—has shown significant volatility, spiking during periods of federal aid (such as the COVID-19 pandemic) and contracting during periods of austerity [80]. This fiscal reality makes internal budget optimization and reallocation not just an efficiency measure, but a critical strategy for sustaining research and development (R&D).
Concurrently, the broader cybersecurity market, which includes digital forensics tools, is projecting aggressive growth. Global cybersecurity spending is expected to reach $212 billion in 2025, a 15% increase from the previous year [81]. The network forensics market specifically is expected to be valued at $3.75 billion in 2025 [82]. This growth is driven by escalating cyber threats, with annual global damages from cybercrime projected to reach $10.5 trillion [81]. For forensic researchers, this data highlights the urgent need to allocate resources toward technologies that can counter these advanced threats.
Table: Key Forensic and Cybersecurity Market Metrics
| Metric | Value (2025) | Trend/Source |
|---|---|---|
| US Forensic Technology Services Industry Revenue | $3.7 Billion | 1.4% CAGR over past five years [80] |
| Global Cybersecurity Spending | $212 Billion | 15% year-on-year growth [81] |
| Global Network Forensics Market | $3.75 Billion | [82] |
| Number of Forensic Businesses in the US | 333 | [80] |
Cost-Saving Strategies for Budget Reallocation
Implementing strategic cost-saving measures is the foundational step for freeing up capital to invest in high-impact technologies. The following methodologies have been proven effective within research and development settings.
Leveraging Open-Source Forensic Tools
Many robust open-source security and digital forensics tools can provide significant protective and analytical capabilities without the hefty price tag of commercial products [81]. For example, instead of immediately licensing a commercial digital forensics platform, research teams can utilize a combination of open-source tools for disk imaging, memory analysis, and log correlation in the early stages of tool development and validation. The savings from avoided licensing fees can be substantial and directly reinvested into other critical areas.
Consolidation of Software and Service Contracts
Research organizations often accumulate redundant software licenses and overlapping service contracts over time. A thorough audit of all existing contracts for forensic analysis tools, cloud services, and data management platforms can reveal opportunities for consolidation. By negotiating enterprise-wide licenses or selecting a single-vendor solution for a suite of services, organizations can achieve significant volume discounts and reduce administrative overhead.
Cloud resources in forensic research, particularly for data-intensive tasks like genomic sequencing or large-scale log analysis, can quickly escalate in cost. Implementing strict policies for decommissioning unused virtual machines, leveraging spot instances for non-critical batch processing, and archiving infrequently accessed data to lower-cost storage tiers can generate considerable savings. These operational efficiencies directly lower ongoing operational expenditures (OpEx).
Phased Implementation and Modular Technology Acquisition
Instead of large, monolithic technology purchases, researchers should adopt a phased implementation strategy. This involves piloting a new technology on a small scale to validate its performance and impact before committing to a full-scale, costly deployment. Similarly, opting for modular systems allows an organization to purchase only the capabilities immediately needed, with the flexibility to add modules as budgets allow and research requirements evolve.
High-Impact Technology Investment Areas
The savings generated from the aforementioned strategies should be strategically channeled into technologies that offer the highest return on investment for forensic research. The following areas are currently poised for significant impact.
Artificial Intelligence and Machine Learning Platforms
AI and machine learning are transformative for forensic science. Investment in these platforms can automate the analysis of complex datasets, from DNA sequencing results in forensic biology to pattern recognition in digital evidence [80]. This automation not only accelerates research throughput but also reduces human error and helps manage the severe backlogs that are a known stressor in forensic laboratories [83]. Allocating funds to acquire, develop, or license AI-driven analytics tools is a high-impact use of reallocated capital.
Advanced Digital and Network Forensics Tools
The escalating sophistication of cyber threats necessitates advanced investigative tools. The market for network forensics tools is growing rapidly, predicted to reach $4.1 billion by 2032 [82]. Investments should be directed toward:
- Full-packet capture tools for deep incident analysis and reconstruction [82].
- Security Information and Event Management (SIEM) systems for centralized log collection and threat detection [82] [81].
- Endpoints Detection and Response (EDR) / Managed Detection and Response (MDR) solutions for protecting research endpoints [81]. These tools are essential for investigating security incidents within research networks and protecting sensitive intellectual property.
Portable Forensic Analysis Equipment
The forensic technology industry has seen a rise in technological advancements like portable DNA analyzers and 3D imaging systems [80]. Investing in portable, rapid-deployment equipment enhances the flexibility and responsiveness of research teams. It allows for on-site analysis, which can preserve the integrity of evidence and reduce chain-of-custody complications. This mobility is particularly valuable for field research and in scenarios where evidence cannot be easily moved to a central laboratory.
Specialized Cloud Forensics and Data Management Solutions
As forensic research moves data and workloads to the cloud, specific challenges around data acquisition, jurisdiction, and integrity arise [84]. Investing in specialized cloud forensics tools and secure, compliant data management platforms is critical. These solutions help navigate the complexities of multi-tenancy, data volatility, and encrypted data in cloud environments, ensuring that forensic research remains robust and legally defensible [84].
Table: High-Impact Technology Investment Analysis
| Investment Area | Key Function | Projected Market Trend |
|---|---|---|
| AI and Machine Learning | Automated data analysis, error reduction, backlog management | Spurring 15.6% growth in security services spending [81] |
| Digital/Network Forensics | Threat detection, incident investigation, evidence collection | Market to reach $4.1B by 2032 [82] |
| Portable Analysis Equipment | On-site DNA analysis, 3D imaging, field responsiveness | Enabled by post-2020 R&D investments [80] |
| Cloud Forensics Solutions | Data acquisition in cloud environments, integrity validation | Essential for addressing jurisdictional and multi-tenancy issues [84] |
Experimental Protocol: Evaluating a New Forensic Technology
Before full-scale implementation, a new technology or tool must be rigorously evaluated. The following protocol provides a standardized methodology for this assessment, crucial for justifying reallocated funds.
Objective: To determine the efficacy, efficiency, and operational impact of a new high-impact forensic technology (e.g., a new portable DNA analyzer or a digital forensics software platform) within a constrained research budget.
1. Identification and Definition (Week 1)
- Define Scope: Clearly articulate the specific research problem the technology aims to solve (e.g., "Reduce DNA analysis time by 20%" or "Improve detection of encrypted network threats").
- Form Hypothesis: State a testable hypothesis (e.g., "Technology X will process controlled substance samples with 99% accuracy and a 25% faster turnaround time compared to the current standard method.").
2. Baseline Establishment (Week 2)
- Measure Current State: Using the existing technology/process, perform a controlled experiment (n=30 samples or data sets) to establish baseline metrics for accuracy, processing time, cost per sample, and operator effort.
- Document Workflow: Create a detailed flowchart of the existing process to identify bottlenecks.
3. Technology Piloting (Weeks 3-5)
- Secure Trial: Arrange a limited-term, pilot-scale license or rental of the technology to minimize upfront investment.
- Controlled Testing: Using a double-blind methodology where applicable, process the same set of samples/data from the baseline test (n=30) using the new technology.
- Data Collection: Meticulously record all relevant performance metrics, including setup time, analysis duration, error rates, results accuracy, and user-friendliness.
4. Data Analysis and Impact Assessment (Week 6)
- Comparative Analysis: Statistically compare the performance metrics from the pilot with the established baseline.
- ROI Calculation: Calculate a projected Return on Investment (ROI) based on the measured efficiency gains, factoring in the total cost of ownership of the new technology.
- TRL Scaling Plan: Assess the new technology's TRL and draft a plan for scaling it within your organization, identifying any required training or infrastructure changes.
5. Decision Point and Implementation (Week 7)
- Go/No-Go Decision: Based on the quantitative and qualitative data, make a final decision on full acquisition.
- Budget Reallocation Proposal: Prepare a formal proposal to reallocate savings from other areas to fund the full implementation, using the data generated from this protocol as justification.
Diagram 1: Budget Reallocation Strategy Workflow.
Technical Support Center: Troubleshooting Guides and FAQs
This section provides direct, actionable guidance for researchers and technicians encountering issues during the evaluation and implementation of new forensic technologies.
Troubleshooting Guide: Network Forensic Data Collection
Problem: In a network forensics investigation, you are unable to collect a complete set of packet data from a critical router.
Investigation Steps:
- Identify & Scope: Determine the make, model, and software version of the network device. Define the time range of the incident [85].
- Preserve & Isolate: Immediately isolate the device from the network to prevent remote tampering or destruction of evidence. Do not reboot the device, as this will erase volatile memory (RAM) containing crucial forensic data like routing tables and active processes [85].
- Collect Volatile Data: Access the device's command line and execute a series of
showcommands to document the runtime environment. Critical commands includeshow tech-support,show version, andshow platform software process memoryto check for signs of tampering in active processes [85]. - Collect Persistent Data: Securely export system logs, core files, and any trace logs from the device's storage (e.g.,
dir harddisk:/tracelogs) [85]. - Examine & Analyze: Transfer all collected data to a secure analysis workstation. Use network forensic analysis tools to examine packet capture (pcap) files and logs for Indicators of Compromise (IoCs).
- Presentation: Compile findings into a clear report for stakeholders or legal teams.
FAQ: Common Challenges in Forensic Technology Implementation
Q1: Our forensic laboratory is experiencing severe backlogs and examiner fatigue. What technologies can help, and how do we justify the cost? A: High backlogs are a recognized stressor with detrimental effects on individuals and casework outcomes [83]. Investing in automation and AI-driven tools for repetitive tasks (e.g., data triage, controlled substance analysis) can directly increase throughput and reduce monotony. Justify the cost by performing a pilot study (see Experimental Protocol) to quantify the potential reduction in processing time and error rates, framing the investment as essential for both well-being and operational efficiency.
Q2: We are moving forensic data to the cloud. What are the key investigative challenges we should anticipate? A: Cloud forensics introduces several key challenges [84]:
- Data Acquisition & Volatility: Cloud data is distributed and ephemeral, making it difficult to locate and preserve.
- Jurisdictional Issues: Data stored in different countries is subject to conflicting laws.
- Multi-tenancy: Isolating your data from other users on shared infrastructure can be complex.
- Log Management: Logs are often distributed across services with varying formats and access controls. Budgeting for specialized cloud forensics tools and legal expertise is crucial to address these challenges.
Q3: During a digital forensic investigation, we encountered encrypted data we cannot access. What are our options? A: Encrypted data is a major hurdle. The options, in order of preference, are:
- Legal Acquisition of Keys: Navigate legal channels to obtain decryption keys from the data owner or a third party [84].
- Identify Weak Encryption: Use forensic tools to determine if the encryption algorithm is outdated or weakly implemented, which might be vulnerable to attack.
- Alternative Evidence: Seek the same evidence from an unencrypted source, such as a backup server, another device, or network logs.
Q4: How can a small research team with a limited budget compete with larger organizations in adopting new technologies? A: Focus on strategic reallocation and open-source solutions. Aggressively pursue the cost-saving strategies in Section 3, particularly leveraging open-source tools and optimizing cloud costs [81]. Then, make targeted, phased investments in modular or service-based versions of high-impact technologies (e.g., subscribing to a cloud-based SIEM rather than building an on-premises one) to gain capabilities without large capital expenditure.
The Scientist's Toolkit: Essential Research Reagents & Solutions
For a research team focusing on forensic technology implementation, the "reagents" are often the software, hardware, and data sources that enable experimentation and validation.
Table: Key Research Reagent Solutions for Forensic Technology Scaling
| Item Name | Type | Primary Function in Research/Experimentation |
|---|---|---|
| Forensic Software Development Kit (SDK) | Software | Provides standardized libraries and APIs for building custom forensic analysis tools and integrating with existing platforms. |
| Validated Reference Data Sets | Data | Serves as a ground-truth benchmark for testing and validating the accuracy and reliability of new forensic algorithms and tools. |
| Portable DNA Analyzer | Hardware | Enables rapid, on-site forensic biology testing, crucial for field experiments and validating the TRL of portable equipment [80]. |
| Full-Packet Capture Appliance | Hardware | Captures a complete record of network traffic for post-incident forensic analysis and tool validation in a controlled environment [82]. |
| Security Information and Event Management (SIEM) | Software Platform | Centralizes and correlates log data from various sources, serving as a core technology for experimenting with and detecting complex attack patterns [82] [81]. |
| Cloud Workload Protection Platform (CWPP) | Software | Used in experiments to secure cloud-based forensic data and applications, a key growth area in cybersecurity [81]. |
Diagram 2: Network Data Collection Troubleshooting Flow.
Measuring Success and Comparing Approaches in Resource-Constrained Environments
Quality Assurance Frameworks for Cost-Effective Digital Forensic Investigations
Technical Support Center
Frequently Asked Questions (FAQs)
Q1: How can we justify a major upfront investment in digital forensics infrastructure to our financial department? A major capital expenditure (CapEx) can be justified by presenting a Total Cost of Ownership (TCO) analysis. Unlike DNA forensics, which has high recurring operational costs (OpEx) for consumables, digital forensics infrastructure requires high initial investment but can be cost-effective over time [51]. Frame the investment as essential for handling the growing case volume involving digital evidence, which now dominates many labs' workloads. Demonstrating how the investment will reduce long-term backlogs and associated social costs can strengthen your proposal [86].
Q2: Our lab faces a growing backlog in digital evidence examination. What are the most cost-effective first steps to address this? Begin by implementing a triage and targeted approach [87]. Instead of a full, deep-dive analysis on every device, use forensic tools to perform rapid preliminary assessments. This helps identify the devices and data sources most likely to contain relevant evidence, allowing your analysts to prioritize their workflow effectively [88]. This phased approach prevents wasting resources on low-yield evidence.
Q3: What are the primary cost drivers we should account for in a digital forensics budget? The primary costs for digital forensics are Capital Expenditures (CapEx) for hardware, servers, and specialized software licenses. This contrasts with DNA forensics, which is dominated by recurring Operational Expenditures (OpEx) for consumables like test kits and reagents [51]. For digital forensics, also budget for hidden recurring costs like data storage expansion, cybersecurity measures, and continuous staff training to keep pace with evolving technology [51].
Q4: How can a small lab or one with a limited budget start building digital forensics capabilities? A sustainable strategy is to begin with open-source tools and phased scaling. Tools like Autopsy and Sleuth Kit provide a powerful, no-cost entry point for basic digital forensic analysis [89]. Simultaneously, pursue grant funding from programs like the National Institute of Justice’s DNA Capacity Enhancement and Bureau of Justice Assistance digital forensics initiatives [51]. Focus initial efforts on a specific, high-need area, such as mobile device analysis, and expand capabilities as funding and expertise grow.
Q5: How does the concept of "Technology Readiness Level (TRL)" apply to implementing new forensic tools? The TRL scale helps assess the maturity and implementation risk of a new technology [53]. A tool at TRL 9 has been proven in a real-world operational environment, making it a lower-risk choice for a production lab. In contrast, a tool at TRL 4-6 is still at the prototype/testing stage, requiring more validation and development before it can be reliably used in casework [53] [48]. Using TRL assessments during procurement prevents investing in technologies that are not yet stable or reliable for forensic use.
Troubleshooting Guides
Issue: Forensic software is performing slowly, especially with large datasets.
- Potential Cause 1: Inadequate hardware resources. Large forensic images require significant RAM and fast processor cores.
- Solution: Verify the software's minimum and recommended system requirements. Consider a hardware upgrade, prioritizing RAM, CPU speed, and using solid-state drives (SSDs) for active casework.
- Potential Cause 2: Software is not optimized for the specific data type.
- Solution: Check for software updates from the vendor, as these often include performance enhancements. Consult user forums or the vendor's knowledge base for recommended settings for your specific data type (e.g., mobile backups, cloud data).
Issue: Inability to access or decrypt data from a new application or device.
- Potential Cause: The forensic tools have not been updated to support the new app or device's operating system.
- Solution: This is a common challenge due to rapid technological change [90]. First, ensure your software licenses are active and all available updates are installed. If the problem persists, contact the tool vendor's support team to inquire about development timelines for support. In the interim, document the limitation and explore alternative methods for obtaining the same evidence.
Issue: The forensic report is being challenged in court due to questions about the methodology.
- Potential Cause: Lack of documented validation and standard operating procedures (SOPs).
- Solution: Ensure every tool and technique used has been internally validated according to your lab's quality assurance standards [90]. Maintain detailed records of the validation process and SOPs. Adhere to established forensic standards like ISO/IEC 17025 to demonstrate methodological rigor and scientific foundation [51].
Structured Data and Protocols
Table 1: Digital vs. DNA Forensics Cost Profile
| Category | Digital Forensics | DNA Forensics |
|---|---|---|
| Primary Cost Type | Capital (hardware, software, storage) [51] | Operational (reagents, consumables) [51] |
| Recurring Expenses | Software updates, cybersecurity, data backups [51] | Test kits, QA/QC, service contracts [51] |
| ROI Horizon | Long-term (infrastructure, case capacity) [51] | Short-term (backlog reduction, compliance) [51] |
| Major Risk Factor | Data breaches, technical obsolescence [51] | Contamination, supply chain volatility [51] |
| Training Need | Cybersecurity, cloud forensics, data integrity [51] | Molecular biology, accreditation standards [51] |
Table 2: Digital Forensics Software Overview
| Software | Primary Use Case | Cost Consideration |
|---|---|---|
| Autopsy | Open-source digital forensics platform; good for education and basic analysis [89] | Free, but may require more technical expertise [89] |
| FTK (Forensic Toolkit) | Comprehensive forensic analysis for large data volumes [89] | Premium cost; requires robust hardware [89] |
| Cellebrite UFED | Specialized in mobile device and cloud data extraction [89] | High cost and training requirements [89] |
| Magnet AXIOM | User-friendly tool with strong evidence visualization [89] | Premium cost [89] |
| Volatility | Open-source memory (RAM) analysis [89] | Free, but requires deep technical knowledge [89] |
Experimental Protocol: Cost-Benefit Analysis for New Tool Acquisition
- Needs Assessment: Define the specific capability gap (e.g., ability to parse a new cloud application).
- Market Research: Identify potential tools and assess their Technology Readiness Level (TRL) [53].
- TCO Calculation: Model the total cost over 3-5 years, including purchase price, annual maintenance, training, and any required hardware.
- Pilot Testing: If possible, run a controlled pilot using a representative sample of your lab's data to evaluate performance and ease of use.
- ROI Projection: Estimate the tool's impact on analyst productivity (cases per week) and backlog reduction to quantify its financial benefit [51].
Workflow and Pathway Diagrams
Diagram 1: Cost-Conscious Forensic Workflow
Diagram 2: Tool Maturity and Implementation Risk
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Digital Forensics "Reagents"
| Item | Function |
|---|---|
| Forensic Write Blockers | Hardware or software tools that prevent accidental alteration of original evidence during acquisition, ensuring data integrity [89]. |
| Forensic Imaging Tools | Software and hardware used to create a bit-for-bit copy (an "image") of a digital storage device, which becomes the subject of analysis [90]. |
| Data Carving Utilities | Software designed to recover files and data fragments from a disk or memory image without relying on file system metadata [89]. |
| Hash Set Databases | Collections of cryptographic hashes (like MD5, SHA-1) used to identify known files, such as operating system files or known illegal content, filtering out irrelevant data [51]. |
| Validation Test Images | Standardized sets of digital data with known properties, used to validate that forensic tools are functioning correctly and producing accurate results [90]. |
Technical Support Center: FAQs & Troubleshooting Guides
FAQ: Implementation Process & Standardization
Q1: What are the core components of a standardized methodology for evaluating a new forensic technology?
A standardized methodology for evaluating technology, such as a Large Language Model (LLM) for forensic timeline analysis, should consist of several core components [91] [92]:
- A reference dataset: A publicly available, standardized dataset is crucial for training and testing the technology. This ensures evaluations are consistent, repeatable, and comparable across different studies [91] [92].
- Timeline generation and ground truth development: The process must include a well-defined method for generating the data or events to be analyzed (e.g., using a tool like log2timeline/Plaso) and establishing a verified "ground truth" against which the technology's output can be measured [91] [92].
- Quantitative performance metrics: The evaluation should use established, quantitative metrics to judge performance. In the context of AI-based analysis, this can include natural language processing metrics like BLEU and ROUGE for tasks like event summarization, which measure the similarity between the AI-generated output and the ground truth [91] [92].
Q2: How can we ensure the output of an AI-based forensic tool is reliable and forensically sound?
Ensuring reliability involves a multi-layered approach to evaluation [93]:
- Performance Evaluation: The underlying AI model must be evaluated using standard metrics for accuracy and precision relevant to its task (e.g., detection rates, false positive rates) [93].
- Forensic Evaluation: The output must be interpreted within the context of the overall investigation. AI-generated results should be treated as "recommendations" that require additional review and validation by human experts to fit the working hypothesis and avoid subconscious bias [93]. This "human-in-the-loop" mantra is critical for maintaining forensic soundness [92].
Q3: Our laboratory faces budget constraints; how can we benchmark our forensic performance efficiently?
Efficient benchmarking under budget constraints can be achieved by [94] [95]:
- Utilizing project benchmarking frameworks: Programs like Project FORESIGHT offer key benchmarks for forensic science managers related to productivity, timeliness, and financial management. These pre-established benchmarks allow a laboratory to compare its performance against industry standards without developing a full framework from scratch [94].
- Conducting internal before-and-after studies: As demonstrated in Australian volume crime benchmarking, you can measure your lab's performance against a set of metrics (e.g., processing time, success rates), implement changes to address bottlenecks, and then re-measure several years later to quantify improvement. This uses your own historical data as a control [95].
Q4: What is a common pitfall when measuring the calibration of a forensic evaluation system, and how can it be avoided?
A common pitfall is using validation metrics that overfit the test data [96]. Metrics based on the Pool-Adjacent-Violators (PAV) algorithm, such as Cllrcal and devPAV, are trained and tested on the same validation dataset. This can make the system's performance appear better than it actually is because the metric has adapted too closely to the specific test sample [96].
- Solution: To avoid this, ensure that the data used to calibrate the system is entirely separate from the data used to validate it. Furthermore, for a system that is already appropriately calibrated, a simple metric of "degree of calibration" may not be as meaningful as ensuring the system's core accuracy and that the calibration data is representative of casework conditions [96].
Troubleshooting Guides
Issue 1: Technology Performs Well in Pilots But Fails to Scale to Routine Service
- Problem: A digital tool, such as a new evidence screening AI, works effectively in a controlled pilot study but encounters resistance, process failures, or performance drops when rolled out for daily use across the organization.
- Solution: This is a classic "pilotitis" problem. Scaling requires building a robust case for adoption beyond mere technical functionality [97].
- Troubleshooting Steps:
- Assess Service Readiness: Use a framework like the Service Readiness Level (SRL). This heuristic framework outlines the accumulating evidence needed across a project's lifecycle to convince decision-makers to fund and scale an innovation. It moves from proof-of-concept to evidence of integration and sustainable value [97].
- Gather Multi-Faceted Evidence: Decision-makers require more than just efficacy data. Build your case with evidence on cost-effectiveness, interoperability with existing systems, organizational fit, and support from key stakeholders and champions [97].
- Ensure Representativeness: Verify that the data used to train and test the technology is representative of the real-world casework and populations it will encounter. A mismatch is a primary cause of failure at scale [96].
Issue 2: AI Tool for Evidence Analysis Produces Inconsistent or Unexplainable Results
- Problem: An AI model used for mining digital evidence (DFAI) provides outputs that vary unexpectedly or cannot be logically explained, making the results inadmissible or untrustworthy for investigators.
- Solution: Implement a rigorous evaluation and optimization protocol for the DFAI methodology [93].
- Troubleshooting Steps:
- Evaluate Performance and Forensic Soundness: Don't just rely on standard AI accuracy metrics. Subject the model's outputs to a forensic evaluation, where human experts review the recommendations in the context of the investigation to check for logical consistency and potential bias [93].
- Apply a Confidence Scale (C-Scale): Use a standardized scale to evaluate the strength of evidence produced by the AI's probabilistic results. This helps communicate the level of uncertainty in a way that is understandable in legal proceedings [93].
- Optimize and Interpret the Model: Apply model optimization and interpretability techniques (e.g., feature importance analysis) to understand which data inputs are driving the model's decisions. This can help identify if the model is relying on spurious correlations instead of forensically relevant patterns [93].
Data Presentation: Benchmarking & Evaluation Metrics
Table 1: Standardized Metrics for Digital Forensics AI (DFAI) Evaluation
| Metric Category | Specific Metric | Description | Forensic Application Example |
|---|---|---|---|
| Technical Performance | BLEU / ROUGE [91] | Measures the quality of text output by comparing it to reference texts. | Evaluating the accuracy of an LLM in summarizing forensic timeline events [91]. |
| Technical Performance | Log-Likelihood-Ratio Cost (Cllr) [96] | Measures the overall performance of a forensic evaluation system, combining accuracy for same-source and different-source pairs. | Calibrating the output of a system comparing speech samples or other digital evidence sources [96]. |
| System Calibration | Cllrcal / devPAV [96] |
PAV-based metrics that ostensively measure the calibration of a system's likelihood-ratio output. | Use with caution: Testing calibration, but prone to overfitting on validation data [96]. |
| Process Efficiency | Project FORESIGHT Benchmarks [94] | A program providing benchmarks for productivity, timeliness, and financial management. | Benchmarking a lab's DNA processing turnaround time or cost-per-sample against peer laboratories [94]. |
Table 2: Key "Research Reagent Solutions" for Forensic Technology Evaluation
| Item | Function in Evaluation |
|---|---|
| Standardized Reference Datasets [91] [92] | Provides a consistent and replicable basis for training and testing new technologies, enabling direct comparison between different tools and methods. |
| Ground Truth Data [91] [92] | The verified, accurate set of data against which a technology's output is compared. It is essential for calculating performance metrics like accuracy and precision. |
| Calibration Data [96] | A separate dataset used to adjust (calibrate) the output of a forensic-evaluation system to ensure its likelihood-ratio values are not misleading. |
| Validation Data [96] | A dataset, separate from calibration and training data, used to provide an unbiased evaluation of a final model's performance. |
Experimental Protocols
Protocol 1: Standardized Evaluation of an LLM for Forensic Timeline Analysis
This protocol is adapted from methodologies proposed for evaluating Large Language Models in digital forensics [91] [92].
- Dataset Curation: Acquire or create a forensic timeline dataset. This can be generated from a clean Windows 11 system using a tool like log2timeline/Plaso to extract digital artifacts and create a timeline of events [92].
- Ground Truth Establishment: Manually analyze the generated timeline to identify and label key forensic events (e.g., "USB device connected," "specific file downloaded"). This curated set of events serves as the verified ground truth [91] [92].
- Task Definition & Prompting: Define a specific task for the LLM, such as "Summarize all external device connection events from this timeline." Develop a standardized prompt to instruct the LLM [91].
- Execution & Output Generation: Input the timeline data and the standardized prompt into the LLM (e.g., ChatGPT) and collect its output [92].
- Quantitative Evaluation: Compare the LLM's output against the ground truth using quantitative metrics. For summarization tasks, this involves using algorithms like BLEU and ROUGE to compute a score based on the overlap of n-grams and word sequences between the AI output and the ground truth [91] [92].
- Analysis & Interpretation: Analyze the scores to determine the LLM's performance. A higher BLEU/ROUGE score indicates a output that is closer to the ground truth summary, suggesting better performance for that specific forensic task [91].
Protocol 2: Calibration of a Forensic-Evaluation System Using a Two-Stage Model
This protocol details the process for calibrating a system that outputs likelihood ratios, common in forensic voice or pattern comparison [96].
- First-Stage Model Training: Train the core analytical model (e.g., a statistical classifier) using a dedicated training dataset. This model will output "scores" (uncalibrated log likelihood ratios) [96].
- Calibration Data Preparation: Assemble a separate calibration dataset, representative of the relevant population and case conditions. Construct same-source and different-source pairs from this data [96].
- Score Generation: Input the calibration data pairs into the first-stage model to produce a set of same-source scores and different-source scores [96].
- Second-Stage Calibration Model Training: Train a parsimonious parametric calibration model (the second-stage model) using the scores generated in the previous step. This model learns to map the uncalibrated scores to well-calibrated likelihood ratios [96].
- System Validation: Finally, test the entire calibrated system on a third, held-out validation dataset. This dataset must be separate from both the training and calibration data to provide an unbiased estimate of the system's real-world performance [96].
Workflow Visualization
Forensic AI Evaluation Workflow
Tech Scaling Service Readiness
Comparative Analysis of Implementation Approaches Across Different Jurisdictions
The implementation of novel forensic technologies across different jurisdictions presents a complex challenge, particularly under significant budget limitations. A comprehensive analysis of UK research funding reveals a critical underinvestment in forensic science, with only 0.01% of the total UK Research and Innovation budget allocated to forensic science projects between 2009-2018 [1]. This funding crisis disproportionately affects traditional forensic domains, with fingerprints receiving merely 1.3% and DNA analysis 5.1% of the total forensic research funding, while digital and cyber projects received 25.7% [1]. This disparity highlights how budgetary pressures and technological trends collectively shape implementation priorities across jurisdictions, forcing laboratory directors to make difficult trade-offs between cost, time, and data quality when adopting new technologies [98].
Table 1: Forensic Science Research Funding Distribution in the UK (2009-2018)
| Category | Percentage of Total Funding | Cumulative Value |
|---|---|---|
| Technological Development Research | 69.5% | £37.2 million |
| Foundational Research | 19.2% | £10.7 million |
| Digital and Cyber Projects | 25.7% | Not specified |
| DNA Analysis | 5.1% | Not specified |
| Fingerprints | 1.3% | Not specified |
Troubleshooting Guides: Overcoming Implementation Barriers
Budgetary Constraints and Resource Limitations
Problem: Laboratory leadership cannot justify investment in new forensic technologies due to limited resources and budget constraints.
Solution: Develop a structured business case that evaluates both the benefit and investment required [99]. The benefit assessment should examine improved efficiency, enhanced forensic capabilities, and quality improvements. The investment analysis must consider not just upfront costs but also time requirements for development and implementation, including staff training and potential workflow disruptions [99]. For smaller jurisdictions, implement sample screening protocols prior to outsourcing to reduce costs on samples below DNA thresholds for STR analysis [98].
Implementation Protocol:
- Conduct a comprehensive needs assessment focusing on core mission requirements
- Evaluate total cost of ownership, including long-term maintenance and training
- Explore public-private partnerships to share development costs
- Consider phased implementation to distribute financial impact over time
- Establish metrics to measure return on investment and efficiency gains
Legal Admissibility and Validation Challenges
Problem: New analytical methods face barriers to admission in legal proceedings due to stringent admissibility standards.
Solution: Ensure new technologies meet jurisdictional legal standards early in development. In the United States, this includes addressing the Daubert Standard factors: whether the technique can be tested, has been peer-reviewed, has a known error rate, and is generally accepted in the relevant scientific community [10]. For federal courts, align development with Federal Rule of Evidence 702 requirements [10]. In Canada, ensure compliance with the Mohan criteria addressing relevance, necessity, absence of exclusionary rules, and properly qualified experts [10].
Implementation Protocol:
- Engage legal counsel early in technology evaluation process
- Document validation studies demonstrating known error rates
- Pursue peer-reviewed publication of methods and validation data
- Conduct intra- and inter-laboratory validation studies
- Develop standard operating procedures that emphasize reliability and reproducibility
Technology Transition and Partnership Gaps
Problem: Promising research fails to transition to operational forensic laboratories due to disjointed development pathways.
Solution: Establish formal partnership agreements between researchers, practitioners, and industry stakeholders [99]. These agreements should outline clear expectations, information sharing protocols, publication rights, and dedicated points of contact. Implement formal project management methodologies, as projects with proper planning have a 92% success rate compared to 29% for those without structured management [99].
Implementation Protocol:
- Identify complementary partners across research, practice, and industry
- Develop formal partnership agreements with defined roles and responsibilities
- Implement structured project management with regular communication cycles
- Establish joint governance committees with representation from all stakeholders
- Create technology transition plans with clear milestones and success metrics
Frequently Asked Questions: Implementation Strategies
Q1: What cost-effective approaches can small jurisdictions implement to enhance forensic capabilities?
Small jurisdictions should consider three primary solutions: (1) establishing satellite laboratories for sample triage to reduce outsourcing costs; (2) utilizing main regional laboratories for full forensic analysis; and (3) implementing Rapid DNA technologies by police services to reduce backlogs [98]. Each approach presents different trade-offs between cost, time, and data quality, requiring jurisdictions to develop a business case analyzing their specific constraints and requirements.
Q2: How can laboratories balance the need for innovation with limited R&D funding?
Forensic laboratories should leverage strategic partnerships to access capabilities beyond their resource constraints. As Cleveland Miles, Division Director of the Georgia Bureau of Investigations notes, most laboratories have "just enough funding dedicated to the mission" of casework, with little left for research [99]. Successful laboratories build relationships with academic institutions, government research agencies, and private industry to share development costs and expertise while maintaining focus on their core operational mission.
Q3: What legal standards must new forensic technologies meet for courtroom admissibility?
Legal standards vary by jurisdiction but share common requirements. In the United States, techniques must satisfy the Daubert Standard (testing, peer review, error rates, and general acceptance) or the Frye Standard (general acceptance in the relevant scientific community) depending on the state [10]. Federal courts follow Federal Rule of Evidence 702, requiring expert testimony to be based on sufficient facts, reliable principles, and proper application [10]. In Canada, the Mahan criteria govern admissibility, emphasizing relevance, necessity, absence of exclusionary rules, and properly qualified experts [10].
Q4: How can digital transformation risks be managed during technology implementation?
Forensic laboratories must adopt forensic digital preparedness strategies to manage risks associated with digital transformation [100]. This involves: involving digital forensic expertise in risk management; implementing robust data verification frameworks like the Verification of Digital Evidence (VODE); enhancing international quality standards such as ISO/IEC 17025 to address digital risks; and developing comprehensive digital continuity plans to ensure data integrity throughout technology transitions [100].
Q5: What emerging technologies show promise for cost-effective forensic implementation?
Several technologies reaching sufficient maturity for implementation include: comprehensive two-dimensional gas chromatography (GC×GC) for improved separation of complex forensic samples [10]; automated DNA screening systems for efficient sample triage [98]; AI-powered evidence analysis tools for processing large digital datasets [101]; and portable forensic analysis devices for crime scene processing [102]. Each technology must be evaluated against jurisdictional needs, available expertise, and total cost of ownership.
Visualization: Forensic Technology Implementation Pathway
Technology Implementation Pathway: This diagram illustrates the structured pathway for implementing forensic technologies across jurisdictions, highlighting critical decision points and dependencies.
Essential Research Reagent Solutions
Table 2: Key Research and Implementation Tools for Forensic Technology Deployment
| Solution/Tool | Primary Function | Implementation Considerations |
|---|---|---|
| Rapid DNA Technologies | Automated DNA analysis for reference samples | Reduced backlog but requires significant capital investment; suitable for police services [98] |
| Comprehensive Two-Dimensional Gas Chromatography (GC×GC) | Enhanced separation of complex forensic samples | Higher resolution than traditional GC; requires validation for legal admissibility [10] |
| Verification of Digital Evidence (VODE) Framework | Quality assurance for digital evidence interpretation | Supports practitioners in verifying digital data interpretation; critical for digital transformations [103] |
| AI and Machine Learning Tools | Automated analysis of large digital datasets | Reduces manual review time; requires training data validation and error rate documentation [101] |
| Sample Triage Systems | Preliminary screening prior to full analysis | Cost-effective for small jurisdictions; reduces outsourcing costs for negative samples [98] |
| Formal Project Management Frameworks | Structured technology transition management | Increases success rate from 29% to 92%; requires dedicated resources and clear milestones [99] |
| Digital Forensic Preparedness Protocols | Risk management for digital transformations | Mitigates operational disruption during technology transitions; enhances data integrity [100] |
Successful implementation of forensic technologies across jurisdictions requires a balanced approach that addresses technical validity, legal admissibility, and financial sustainability. The comparative analysis demonstrates that jurisdictions facing budget constraints must prioritize technologies that offer the greatest operational impact relative to their costs. Strategic partnerships between researchers, practitioners, and industry stakeholders emerge as a critical success factor, enabling resource-constrained organizations to leverage external capabilities and share development costs. Furthermore, early consideration of legal admissibility standards in the technology development process significantly enhances the likelihood of successful courtroom implementation. By adopting structured implementation frameworks that emphasize validation, documentation, and continuous quality improvement, forensic organizations can navigate the complex landscape of technology adoption while maintaining scientific rigor and legal defensibility.
Validation Protocols for Emerging Technologies in Budget-Limited Settings
Troubleshooting Guides
Troubleshooting GC×GC-MS Method Development
Problem: Poor Modulation or Peak Distortion in GC×GC Separation
- Question: My GC×GC chromatograms show poor peak shape, wrapping, or inconsistent modulation. What are the primary causes and corrective actions on a limited budget?
- Answer:
- Verify Modulator Settings: Confirm the modulation period is appropriately set. It should be slightly longer than the peak width from the second dimension separation to prevent "wraparound" where peaks elute in subsequent modulations [10].
- Check Carrier Gas Flow and Pressure: Ensure the carrier gas flow is stable and optimally set for both columns. Inconsistent flow is a common cause of poor modulation.
- Assess Column Health and Connections: Degraded columns or leaks at the modulator interface can cause severe peak distortion. Perform routine leak checks and inspect column performance with test mixtures.
Problem: Inconsistent Retention Times in Forensic Sample Analysis
- Question: Retention times for target analytes are drifting between runs, jeopardizing the reliability of my forensic data. How can I stabilize the system without expensive hardware upgrades?
- Answer:
- Standardize Inlet and Oven Conditions: Ensure the inlet liner is clean and the oven temperature program is highly reproducible. Even minor fluctuations can cause significant shifts in the second dimension.
- Use Retention Index Markers: Introduce a cost-effective internal standard or a series of hydrocarbon retention index markers into your samples. This allows for standardized retention times based on a known scale, correcting for minor run-to-run variations [10].
- Validate System Suitability: Before each batch of forensic samples, run a quality control check mixture to confirm the system is performing within specified retention time and resolution tolerances.
Problem: Low Signal-to-Noise Ratio for Trace Forensic Analytes
- Question: I am struggling to detect trace-level compounds in complex forensic mixtures like ignitable liquid residues or illicit drugs. What parameters can I adjust to improve detectability?
- Answer:
- Optimize Sample Preparation: Re-evaluate your extraction and concentration techniques. Using a larger sample size or implementing a more efficient concentration step (e.g., solvent focusing) can significantly enhance signal.
- Review Mass Spectrometer Tuning: For GC×GC–MS, ensure the MS source is clean and the instrument is properly tuned for the mass range of your target analytes.
- Maximize Peak Capacity: Leverage the core strength of GC×GC by ensuring the two columns provide orthogonal separations. This spreads the analytes out, reducing co-elution and improving the signal-to-noise ratio for individual compounds [10].
Troubleshooting Legal Admissibility and Validation
Problem: Meeting Courtroom Admissibility Standards (e.g., Daubert)
- Question: My laboratory has developed a novel GC×GC method, but we are concerned about its admissibility in court under the Daubert Standard. What are the key validation requirements?
- Answer: The Daubert Standard requires a method to be empirically tested, peer-reviewed, have a known error rate, and be generally accepted [10]. Focus your validation on:
- Establishing a Known Error Rate: Conduct rigorous intra- and inter-laboratory studies to quantify the method's false positive and false negative rates.
- Documenting Method Performance: Systematically record data on precision, accuracy, selectivity, linearity, limit of detection, and limit of quantitation.
- Standard Operating Procedure (SOP): Develop a detailed, unambiguous SOP to ensure the method is applied consistently, which supports the "reliability" criterion.
Problem: Conducting Full Validation Under Budget Constraints
- Question: A full, multi-laboratory validation is prohibitively expensive. What is a minimal viable validation protocol for initial deployment of an emerging technology?
- Answer: Prioritize the most critical studies that demonstrate foundational reliability.
- Intra-Laboratory Precision: Perform repeatability and intermediate precision tests using your team and equipment over different days.
- Accuracy Assessment: Use certified reference materials (CRMs) or compare results with a gold-standard method for a key subset of analytes.
- Robustness Testing: Deliberately introduce small, realistic variations in method parameters (e.g., temperature, flow rate) to prove the method is resilient.
Frequently Asked Questions (FAQs)
Q1: What is the simplest way to describe the advantage of GC×GC over traditional 1D-GC for forensic science? A1: GC×GC provides a massive increase in peak capacity (the number of peaks that can be separated). By using two different separation columns in sequence, it can unravel complex mixtures—like drug impurities, fire debris, or decomposition odors—that appear as an unresolved "hump" in a standard 1D-GC chromatogram, thereby revealing more forensic information from a single sample [10].
Q2: Our lab cannot afford a dedicated GC×GC system. Can we modify an existing 1D-GC? A2: Yes, this is a common approach for budget-limited settings. A 1D-GC system can often be retrofitted with a GC×GC modulator and a secondary oven. The most significant investment may be the modulator itself and data acquisition software capable of handling the high-speed data from the second dimension. This approach can be a cost-effective path to upgrading capabilities [10].
Q3: What are the most critical parameters to document when validating a GC×GC method for courtroom readiness? A3: Beyond typical GC–MS validation parameters, focus on GC×GC-specific metrics [10]:
- Modulation Period Consistency: Critical for reproducible 2D retention times.
- Orthogonality: Evidence that the two columns provide independent separation mechanisms.
- Peak Capacity Gain: Quantitative data showing the improvement over 1D-GC.
- Spectral Quality: Verification that mass spectra from GC×GC–MS are clean and searchable against libraries.
Q4: How can we address the Daubert criterion of "known error rate" for a novel, in-house method? A4: The error rate must be determined through validation experiments. Design studies using blank samples and samples fortified with known analytes at relevant concentrations. The rate of false positives (detection when not present) and false negatives (non-detection when present) calculated from these studies establishes the known error rate for your specific method and application [10].
Q5: Are there specific forensic application areas where GC×GC has the most immediate impact? A5: Research indicates high impact in applications involving complex mixtures that are difficult for 1D-GC to resolve. These include oil spill tracing, ignitable liquid residue (ILR) analysis in arson investigations, profiling of illicit drugs, analysis of fingerprint residue, and studying decomposition odor for forensic canines [10].
Experimental Protocols
Protocol 1: Basic Method Validation for Budget GC×GC-MS
Objective: To establish baseline performance characteristics for a new GC×GC-MS method for a specific forensic application (e.g., target drug analysis).
Materials:
- GC×GC system (refurbished or retrofitted)
- Analytical columns: (1D) mid-polarity (e.g., 35% phenyl), (2D) polar (e.g., PEG)
- Certified reference materials (CRMs) of target analytes
- Internal standard solution
- Data processing software
Methodology:
- System Configuration: Install and condition the 1D and 2D columns. Set the modulator to an appropriate period (e.g., 2-8 seconds).
- Calibration: Prepare a series of calibration standards spanning the expected concentration range, each containing a fixed amount of internal standard.
- Precision (Repeatability): Inject a mid-level calibration standard (n=6) in a single sequence. Calculate the relative standard deviation (RSD%) of the analyte-to-internal standard response ratios.
- Accuracy: Analyze a independently prepared quality control sample or a certified reference material. Calculate the percentage recovery of the measured concentration versus the true value.
- Limit of Detection (LOD) and Quantification (LOQ): Based on signal-to-noise (S/N) from low-level standards. LOD = S/N ≥ 3, LOQ = S/N ≥ 10.
- Robustness: Make a small, deliberate change to one parameter (e.g., carrier gas flow rate ± 0.1 mL/min) and assess its impact on a key performance metric like retention time or peak area.
Protocol 2: Establishing Orthogonality for Two-Dimensional Separation
Objective: To empirically demonstrate that the two-column setup in the GC×GC system provides independent separation mechanisms, a core principle of the technique.
Materials:
- Test mixture containing compounds with a range of chemical functionalities (alkanes, alcohols, aromatics, etc.)
- GC×GC system with configured columns
Methodology:
- Acquire Data: Inject the test mixture and acquire the GC×GC chromatogram.
- Create a 2D Scatter Plot: For each peak in the test mixture, plot its first-dimension retention time (¹tʀ) against its second-dimension retention time (²tʀ).
- Assess Coverage: Evaluate the spread of data points in the 2D retention space. A broad, well-distributed spread indicates high orthogonality, meaning the two separation phases are chemically different and maximizing the peak capacity of the system [10]. A tight cluster or a strong diagonal trend suggests the phases are too similar, and a different column combination should be investigated.
Workflow and Relationship Visualizations
GC×GC Forensic Analysis Workflow
Budget Tech Implementation Logic
The Scientist's Toolkit: Research Reagent Solutions
Table 1: Key Materials for GC×GC Method Development in Forensic Chemistry
| Item | Function | Budget-Limited Consideration |
|---|---|---|
| Orthogonal GC Columns | Provides the two independent separation mechanisms fundamental to GC×GC. A common pair is a non-polar/mid-polar 1D column with a polar 2D column. | Purchase shorter columns or seek surplus/refurbished columns from reputable vendors. |
| Modulator | The "heart" of the system; traps, focuses, and reinjects effluent from the 1D to the 2D column. | Explore less expensive modulator technologies (e.g., thermal modulation vs. cryogenic) when retrofitting older systems. |
| Certified Reference Materials (CRMs) | Essential for method development, calibration, and determining accuracy/error rates for legal defensibility. | Purchase small quantities of the most critical analytes; use for initial validation and key QC checks. |
| Retention Index Marker Mix | A defined mixture of hydrocarbons (e.g., C₈-C₂₀) used to standardize retention times across different runs and instruments. | A low-cost, high-impact tool for improving data reliability and transferability between labs. |
| Internal Standard | A compound added to all samples and calibrators to correct for instrumental and preparation variances. | Use a stable, non-interfering isotope-labeled analog of the target analyte or a structurally similar compound. |
| Data Processing Software | Handles the large, complex 3D data sets (1tʀ, 2tʀ, intensity) produced by GC×GC. | Investigate open-source or academic software solutions for data processing to reduce licensing costs. |
For researchers and scientists driving forensic technology and drug development, the Technology Readiness Level (TRL) framework is a critical tool for measuring project maturity from basic principle (TRL 1) to proven operational system (TRL 9) [18]. Scaling these levels presents a universal challenge: the "Valley of Death" between TRL 5-7 where promising prototypes often falter due to escalating costs and complex operational testing [18]. In forensic science, backlogs in DNA casework exemplify this struggle, where underfunding and poor planning directly hinder analysis and justice [9]. This guide provides actionable troubleshooting and protocols to navigate budget-limited scaling, helping you de-risk development and advance projects to application.
TRL Framework and Budget-Conscious Scaling Strategies
The Technology Readiness Level (TRL) Scale
The TRL scale, originally developed by NASA, provides a systematic measure of a technology's maturity [18]. The following table details the standard definitions and their relevance to budget-aware project planning.
| TRL | Stage Name | Definition & Key Activities | Budget & Resource Focus |
|---|---|---|---|
| 1-3 | Basic/Applied Research | TRL 1: Basic principles observed [18].TRL 2: Technology concept formulated [18].TRL 3: Experimental proof-of-concept established [18] [104]. | Low-cost R&D; ideal for grant funding and academic research. Focus on feasibility. |
| 4-5 | Proof-of-Concept & Validation | TRL 4: Component validation in a laboratory environment [18].TRL 5: Component validation in a relevant environment [18]. | Moderate costs for prototyping. Seek public-private partnerships or targeted R&D funding. |
| 6-7 | Prototype Demonstration | TRL 6: System/subsystem model demonstrated in a relevant environment [18].TRL 7: System prototype demonstration in an operational environment [18]. | High cost and risk ("Valley of Death") [18]. Leverage demonstration programs and cost-sharing. |
| 8-9 | System Qualification & Proven Operation | TRL 8: Actual system completed and qualified through test and demonstration [18].TRL 9: Actual system proven through successful mission operations [18]. | Highest operational costs. Requires full commercial or operational budget allocation. |
Strategic Framework for Budget-Constrained TRL Scaling
Successfully navigating the TRL scale, particularly the mid-level transitions, requires strategic planning to overcome financial hurdles.
- Incremental Testing and Triage: To manage costs at the TRL 5-6 stage, employ incremental prototyping and testing in simulated environments [18]. In forensic labs, implementing a triage system for casework prioritizes analysis with the highest probative value, ensuring limited resources are used effectively to reduce backlogs [9].
- Pilot-Scale Validation (TRL 5): Before full operational deployment (TRL 7-8), conduct validation in a pilot-scale environment that mimics real-world conditions [104]. For software, this means "beta" releases in an operational environment; for biotechnology, this involves Phase 1 or 2 clinical trials and early GMP (Good Manufacturing Practice) pilot production [105].
- Partnerships for Demonstration: Bridge the "Valley of Death" (TRL 6-7) by seeking partnerships with organizations that have access to operational environments. Agencies like NASA and ESA have programs to support such technology demonstrations, which can defray the high costs of flight tests or orbital deployments [18].
Troubleshooting Guide: FAQs for TRL Scaling Challenges
This section addresses common operational problems encountered during technology scaling, with solutions designed for tight budgets.
FAQ: Managing Project Scale and Complexity
Q: Our prototype was successful in the lab, but performance has dropped significantly during field testing in a relevant environment (TRL 5-6). What steps should we take?
- A: This is a common issue when moving from controlled lab conditions. Isolate the root cause by:
- Understand the Problem: Fully document the performance gap and all environmental variables.
- Isolate the Issue: Systematically test individual components or subsystems in the relevant environment. Change only one variable at a time (e.g., temperature, a specific sensor, sample purity) to identify the specific point of failure [65].
- Find a Fix: The solution may involve re-engineering a vulnerable component, adding environmental shielding, or developing software filters to handle real-world noise. Document the fix for future iterations.
Q: We are facing a growing backlog of samples (e.g., forensic DNA, drug compounds) for validation, delaying our TRL progression. How can we improve throughput?
- A: Sample backlogs are a classic sign of resource constraints [9]. Implement a triage system:
- Prioritize: Define clear criteria for prioritizing samples. In forensics, this could be violent crimes over property crimes; in drug development, it could be compounds with the highest in vitro activity [9].
- Optimize Influx: Work upstream to improve sample quality and documentation to reduce re-testing.
- Process Efficiency: Audit your laboratory workflow for bottlenecks. Simple changes to equipment layout or adopting batch processing can significantly increase throughput without major capital expenditure.
FAQ: Operational and Technical Hurdles
Q: Our computational models or software ("beta" release) run slowly or crash when handling real-world, large-scale datasets at TRL 6-7.
- A: This indicates inadequate system resources or unoptimized code for operational loads.
- Check Hardware: Use system tools like Task Manager (Windows) or Activity Monitor (macOS) to identify if the application is consuming excessive CPU or memory [106]. Upgrade hardware if possible, or optimize the code to be less resource-intensive.
- Profile and Optimize Code: Use profiling tools to identify inefficient algorithms or memory leaks. Focus optimization efforts on the sections of code that consume the most resources.
- Manage Data: Check if low disk space is a contributing factor. Move non-essential data to external storage and ensure sufficient free space for application operation [107].
Q: We are unable to secure a "flight opportunity" for a full operational demonstration (TRL 7) due to budget. What are our options?
- A: This is the core challenge of the "Valley of Death" [18].
- Seek Alternative Demonstrations: Look for lower-cost, high-fidelity simulation environments. For space tech, this could be high-altitude balloons or the International Space Station. For a drug delivery system, it might be a more limited clinical pilot study.
- Partner for Access: Form consortia or partnerships with academic institutions, government labs, or larger companies that have access to the necessary operational test facilities.
- Iterative Prototyping: Break down the final demonstration into smaller, more affordable sub-system demonstrations that collectively build a strong case for the technology's maturity.
Experimental Protocols for Key TRL Transitions
Protocol: Transition from Proof-of-Concept (TRL 3) to Lab Validation (TRL 4)
Objective: To integrate basic technological components into a rudimentary system (breadboard) and validate core functions in a laboratory environment [18].
Methodology:
- Component Integration: Assemble the key components identified in your TRL 3 proof-of-concept into a single, functioning system.
- Controlled Testing: Develop a test plan that outlines specific performance benchmarks (e.g., sensitivity, accuracy, speed, yield).
- Bench-Scale Validation: Execute the test plan in a controlled lab setting. This involves non-GLP (Good Laboratory Practice) validation for early-stage development [104].
- Data Analysis & Iteration: Analyze results against benchmarks. This phase often requires multiple iterations to optimize component interaction and meet performance goals.
TRL 3 to 4 Validation Workflow
Protocol: Transition from Lab Validation (TRL 4) to Relevant Environment (TRL 5-6)
Objective: To validate the technology prototype in a relevant environment that simulates real-world conditions as closely as possible [18] [104].
Methodology:
- Create Relevant Environment: Set up an environment that introduces key operational stressors (e.g., temperature cycles, vibration, simulated user interference, complex biological matrices).
- Pilot-Scale Optimization: Move from bench-scale to pilot-scale production of the herbal preparation or technology component. For software, this is a "beta" release integrated with actual external entities [105].
- GLP Validation: Conduct testing under Good Laboratory Practices (GLP) to ensure data integrity and reliability [104].
- Performance Verification: Execute a rigorous test plan to verify that the system model or prototype meets performance specifications in the relevant environment.
The Scientist's Toolkit: Essential Research Reagent Solutions
The following materials and reagents are fundamental for experimental work across forensic and pharmaceutical development stages.
| Item Name | Function & Application | Budget-Conscious Consideration |
|---|---|---|
| Herbal Preparation (HP) API Candidate | The active pharmaceutical ingredient (API) derived from botanical sources, comprising a complex phytochemical mixture for pharmacological study [104]. | Source plant material sustainably, following the Nagoya Protocol for benefit sharing and legal certainty [104]. |
| Sexual Assault Evidence Collection Kit (SAECK) | Standardized kit for collecting and preserving forensic evidence, including DNA, from victims of sexual assault [9]. | Efficient triage and prioritization of kits based on case details to manage laboratory backlogs and resource allocation [9]. |
| Buccal Sample Collection Kit | Non-invasive tool for collecting DNA samples from the inner cheek of individuals for forensic DNA databasing [9]. | Bulk procurement and streamlined logistics to reduce per-unit cost, especially with increased legislative mandates for collection [9]. |
| GMP Pilot Production Line | Facility operating under Good Manufacturing Practice (GMP) for producing clinical trial materials (APIs/drug products) under controlled, validated conditions [105]. | Utilize shared facilities or Contract Development and Manufacturing Organizations (CDMOs) to avoid the high capital expense of building a dedicated plant. |
| Beta Software Environment | A pre-release, operational software environment integrated with actual external systems for validation and user testing (TRL 6-7) [105]. | Use open-source technologies and cloud-based infrastructure that can be scaled on demand to control costs during testing and development. |
Navigating the TRL 6-7 "Valley of Death"
Conclusion
The implementation of forensic technologies under budget constraints requires a paradigm shift from simply seeking more funding to strategically optimizing existing resources through frugal forensic principles, phased TRL scaling, and collaborative innovation. The convergence of AI integration, open-source solutions, and standardized validation frameworks presents a viable path forward for maintaining scientific rigor despite financial limitations. Future success will depend on the forensic community's ability to demonstrate clear ROI, adapt sustainable practices from global models, and develop new funding narratives that articulate the essential value of forensic science to justice systems. As technological evolution accelerates, the institutions that master budget-conscious implementation will lead the next generation of forensic innovation while those waiting for budget expansions risk obsolescence.
References
- 1. A crisis for the future of forensic science [https://www.sciencedirect.com/science/article/pii/S2589871X19301457]
- 2. A crisis for the future of forensic science [https://pmc.ncbi.nlm.nih.gov/articles/PMC7219127/]
- 3. A crisis for the future of forensic science [https://pubmed.ncbi.nlm.nih.gov/32411977/]
- 4. We have a funding crisis in forensic science - how do we fix ... [https://www.ruth-morgan.com/post/we-have-a-funding-crisis-in-forensic-science]
- 5. SCAnDi: Single-cell and single molecule analysis for DNA ... [https://gtr.ukri.org/projects?ref=ES%2FY010655%2F1]
- 6. Funding finder [https://www.ukri.org/opportunity/page/96/?filter_status%5B0%5D=closed&filter_order=publication_date&filter_submitted=true]
- 7. AAFS 2025: Heidi Eldridge Talks About Funding Issues in ... [https://www.spectroscopyonline.com/view/aafs-2025-heidi-eldridge-talks-about-funding-issues-in-forensic-science]
- 8. Emerging Technologies in Forensic DNA Analysis [https://www.sciepublish.com/article/pii/279]
- 9. Why Down-managing Backlog Forensic DNA Case Entries ... [https://www.forensicscijournal.com/journals/jfsr/jfsr-aid1056.php]
- 10. Are We Ready for It? A Review of Forensic Applications and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12012292/]
- 11. Forensic Technology Market Size, Growth & Forecast 2030 [https://marksparksolutions.com/reports/forensic-technology-market-2025-2030]
- 12. Forensic Technologies Market Analysis, Growth & Forecast ... [https://www.technavio.com/report/forensic-technologies-market-industry-analysis]
- 13. Forensic Technology Market Size & Share Report, 2032 [https://www.fortunebusinessinsights.com/forensic-technology-market-110927]
- 14. DOJ Funding Update: A Deeper Look at the Cuts [https://counciloncj.org/doj-funding-update-a-deeper-look-at-the-cuts/]
- 15. Home - ForensicRTI [https://forensicrti.org/]
- 16. Drug Analysis [https://forensicresources.org/forensic-disciplines/drug-analysis/]
- 17. Forensics Resource Library | Thermo Fisher Scientific - TG [https://www.thermofisher.com/tg/en/home/industrial/forensics/forensics-learning-center/forensics-resource-library.html.html]
- 18. Technology Readiness Levels (TRL) in Space Projects | TTMS [https://ttms.com/technology-readiness-levels-trl-in-space-projects-explanation-and-significance/]
- 19. The invisible crisis facing forensic providers in the United ... [https://www.sciencedirect.com/science/article/pii/S2589871X25000609]
- 20. Key Trends in Digital Forensics 2025: Chanllenges and ... [https://www.salvationdata.com/knowledge/key-trends-in-digital-forensics-for-2025/]
- 21. Digital Forensics Market Size, Growth Drivers & Forecast ... [https://www.mordorintelligence.com/industry-reports/digital-forensics-market]
- 22. Digital Forensics Degree vs Traditional CSI | 2025 Guide [https://www.crimesceneinvestigatoredu.org/blog/digital-forensics-vs-traditional-csi-choosing-your-specialization/]
- 23. Demonstrating cost-benefit for forensic laboratory resources [https://pmc.ncbi.nlm.nih.gov/articles/PMC8267537/]
- 24. Advancing a paradigm shift in evaluation of forensic evidence [https://www.sciencedirect.com/science/article/pii/S2589871X22000559]
- 25. Digital Forensics: Confronting Modern Cyber Crimes ... [https://www.heraldopenaccess.us/openaccess/digital-forensics-confronting-modern-cyber-crimes-technological-advancements-and-future-challenges]
- 26. Archived | NIJ FY24 Research and Evaluation on the Impact of ... [https://nij.ojp.gov/funding/opportunities/o-nij-2024-171968]
- 27. Commoditization | Business Definition + Characteristics [https://www.wallstreetprep.com/knowledge/commoditization/]
- 28. Fighting commoditization - IMD Business School [https://www.imd.org/research-knowledge/marketing/articles/fighting-commoditization/]
- 29. Making a profit with R&D services — The critical role of ... [https://www.sciencedirect.com/science/article/abs/pii/S0019850112001848]
- 30. Escaping the Doghouse: Winning in Commoditized Markets [https://www.bcg.com/publications/2015/business-unit-strategy-escaping-dog-house-winning-commoditized-markets]
- 31. Stop Wasting Time Evaluating Commoditized Products a... [https://www.infotech.com/research/ss/stop-wasting-time-evaluating-commoditized-products-and-services]
- 32. Strategic Opportunities to Advance Forensic Science in the ... [https://www.nist.gov/publications/strategic-opportunities-advance-forensic-science-united-states-path-forward-through]
- 33. U.S. initiatives to strengthen forensic science & ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC4573542/]
- 34. Research & Development in Forensics & Criminal Sciences [https://www.forensicscolleges.com/blog/criminal-sciences-research-and-development]
- 35. Mind the gap: The challenges of sustainable forensic ... [https://www.sciencedirect.com/science/article/pii/S2589871X23000050]
- 36. The challenges of sustainable forensic science service ... [https://pubmed.ncbi.nlm.nih.gov/36852173/]
- 37. APPLYING FRUGAL PRINCIPLES IN FORENSIC SCIENCES ... [https://repository.antispubmed.com/artikel/6010/applying-frugal-principles-in-forensic-sciences-in-africa]
- 38. addressing the challenges of sustainable forensic science ... [https://www.semanticscholar.org/paper/Frugal-forensics%3A-addressing-the-challenges-of-Lewis-Heavey/e3f20c78482b5fb90e47b393641af70a2d32c7da]
- 39. 1. What Is A Trl ? - Technology Readiness Level... - FHWA-HRT-17-047 [https://www.fhwa.dot.gov/publications/research/ear/17047/001.cfm]
- 40. | EURAXESS TRL [https://euraxess.ec.europa.eu/career-development/researchers/manual-scientific-entrepreneurship/major-steps/trl]
- 41. Comparing Traditional Vs. Modern Digital Forensics [https://lcgdiscovery.com/comparing-traditional-vs-modern-digital-forensics-navigating-the-evolving-digital-landscape/]
- 42. The Future of Digital Forensics: How Technology is ... [https://www.techuk.org/resource/the-future-of-digital-forensics-how-technology-is-transforming-investigations.html]
- 43. A Shift in Strategy: Why Law Enforcement Executives Must ... [https://www.hexordia.com/blog/why-law-enforcement-executives-must-prioritize-digital-forensics-now]
- 44. Colors in Forensics: The Analysis and Visualization of ... [https://www.intechopen.com/chapters/1191890]
- 45. Technology Readiness Levels: Assessing ... [https://www.encata.net/blog/technology-readiness-levels-assessing-technological-maturity]
- 46. Technology Readiness Levels for vaccine and drug ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9811140/]
- 47. Integrated Technology Readiness Levels (TRLs) [https://medicalcountermeasures.gov/trl/integrated-trls]
- 48. 14 Readiness Level Frameworks: The Guide to TRL, MRL, ... [https://www.itonics-innovation.com/blog/14-readiness-level-frameworks]
- 49. Unlock Savings with IT Budget Optimization: Strategies for ... [https://opsiocloud.com/blogs/it-budget-optimization/]
- 50. IT Budgeting Basics: Best Practices for 2025 [https://ramp.com/blog/it-budgeting-best-practices]
- 51. Balancing DNA vs Digital Forensics Budgets in ... [https://www.labmanager.com/balancing-dna-vs-digital-forensics-budgets-in-forensic-lab-management-34534]
- 52. How to Write a Budget Justification for Your Forensic Unit ... [https://gapscience.com/budget-justification/]
- 53. Technology Readiness Levels [https://www.nasa.gov/directorates/somd/space-communications-navigation-program/technology-readiness-levels/]
- 54. Technology readiness level [https://en.wikipedia.org/wiki/Technology_readiness_level]
- 55. Technology Readiness Levels (TRLs) in the Era of Co- ... [https://www.mdpi.com/2571-5577/7/2/32]
- 56. How to Measure AI ROI in Financial Services for 2026 ... [https://aveni.ai/blog/how-to-measure-ai-roi-in-financial-services/]
- 57. Measure the ROI of Legal AI Implementation: A 5-Step ... - Clio [https://www.clio.com/blog/roi-in-legal-ai-implementation/]
- 58. 19 HR Metrics Examples: Making Data-Driven Decisions in ... [https://www.aihr.com/blog/hr-metrics-examples/]
- 59. Leveraging Open-Source Tools for Cost-Effective ... [https://www.secoda.co/blog/leveraging-open-source-tools-for-cost-effective-performance]
- 60. CTO Insights: Navigating Budget Constraints While Innovating ... [https://digitaldefynd.com/IQ/cto-insights-navigating-budget-constraints-while-innovating/]
- 61. Pluralsight's 2025 Tech Skills Report Reveals 95% of ... [https://www.pluralsight.com/newsroom/press-releases/-pluralsight-s-2025-tech-skills-report-reveals-95--of-profession]
- 62. Responsible for a Digital Forensics Budget? 10 Reasons ... [https://www.adfsolutions.com/news/responsible-for-a-digital-forensics-budget-10-reasons-why-to-go-with-adf?srsltid=AfmBOopRGubyhrYUeaP5CC5gRXpcdpA56j-ANCPpzpUf3w9umVwHv0Ve]
- 63. Technology Readiness Level Roadmap for Developing ... [https://www.mdpi.com/1424-8247/17/6/703]
- 64. The Training Industry in 2025: Top Trends Shaping ... [https://www.lmsportals.com/post/the-training-industry-in-2025-top-trends-shaping-the-future]
- 65. The Art of Troubleshooting for Customer Support ... [https://www.helpscout.com/helpu/art-of-troubleshooting-support/]
- 66. The complete guide to customer service troubleshooting [https://devrev.ai/blog/customer-service-troubleshooting]
- 67. Privacy budgets set to decrease in 2025, new research ... [https://www.isaca.org/about-us/newsroom/press-releases/2025/privacy-budgets-set-to-decrease-in-2025-new-research-from-isaca-reveals]
- 68. Blockchain-based Systems for Securing and Sharing ... [https://publicsafety.ieee.org/topics/blockchain-based-systems-for-securing-and-sharing-forensic-evidence/]
- 69. Government and public sector [https://kpmg.com/xx/en/our-insights/ai-and-technology/cybersecurity-considerations-2025/government-public-sector.html]
- 70. How AI will reshape pharma in 2025 [https://www.drugtargetreview.com/article/154981/how-ai-will-reshape-pharma-by-2025/]
- 71. Technical Documentation and Regulatory Compliance ... [https://www.nsf.org/life-sciences/technical-documentation-regulatory-compliance-services]
- 72. Technology Readiness Levels (TRLs) Explained [https://www.grantify.io/us-articles/technology-readiness-levels-trls-explained]
- 73. How pharma can benefit from using GenAI in drug discovery [https://www.ey.com/en_us/insights/life-sciences/how-pharma-can-benefit-from-using-genai-in-drug-discovery]
- 74. Demonstrating cost-benefit for forensic laboratory resources [https://www.sciencedirect.com/science/article/pii/S2589871X21000280]
- 75. Artificial intelligence as a tool in drug discovery and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11372739/]
- 76. Using AI To Modernize Drug Development And Lessons ... [https://www.forbes.com/sites/cindygordon/2024/02/23/using-ai-to-modernize-drug-development-and-lessons-learned/]
- 77. Common questions about Insight Forensic with DiskSense ... [https://atola.com/products/insight/manual/faq.html]
- 78. Autopsy User Documentation: Troubleshooting [https://sleuthkit.org/autopsy/docs/user-docs/4.19.3/troubleshooting_page.html]
- 79. Automation for experimental, field-based research [https://www.sciencedirect.com/science/article/pii/S037907382300066X]
- 80. Forensic Technology Services in the US industry analysis [https://www.ibisworld.com/united-states/industry/forensic-technology-services/4174/]
- 81. Budgeting for Cybersecurity in 2025 [https://www.brightdefense.com/resources/budgeting-for-cybersecurity-in-2024/]
- 82. The Guide to Network Forensics: Importance, Tools, and ... [https://www.splunk.com/en_us/blog/learn/network-forensics.html]
- 83. Stressors in forensic organizations: Risks and solutions [https://www.sciencedirect.com/science/article/pii/S2589871X21000681]
- 84. Cloud Forensics Challenges: An In-depth Analysis [https://searchinform.com/articles/cybersecurity/analytics/digital-forensics/cloud-forensics/challenges/]
- 85. Cisco IOS XE Software Forensic Data Collection Procedures [https://sec.cloudapps.cisco.com/security/center/resources/forensic_guides/iosxe_forensic_guide.html]
- 86. The Costs and Benefits of Forensics [https://houstonlawreview.org/article/12197-the-costs-and-benefits-of-forensics]
- 87. Digital Forensics Cost - Effective Solutions for Small Law ... [https://lucidtruthtechnologies.com/digital-forensics-cost/]
- 88. Responsible for a Digital Forensics Budget? 10 Reasons ... [https://www.adfsolutions.com/news/responsible-for-a-digital-forensics-budget-10-reasons-why-to-go-with-adf?srsltid=AfmBOooY9OlyuZ6NY-6UlkwUSXGE7E7jAfn1zHNovC5MKdTw4omk0rFf]
- 89. 10 Useful Digital Forensics Software in 2025 [https://www.salvationdata.com/knowledge/digital-forensics-software/]
- 90. A Solid Foundation? NIST Publishes Review of Digital ... [https://complexdiscovery.com/a-solid-foundation-nist-publishes-review-of-digital-forensics-methods/]
- 91. Towards a standardized methodology and dataset for ... [https://www.sciencedirect.com/science/article/pii/S2666281725001222]
- 92. Towards a standardized methodology and dataset for ... [https://arxiv.org/html/2505.03100v1]
- 93. Digital Forensics AI: Evaluating, Standardizing and ... [https://link.springer.com/article/10.1007/s13218-022-00763-9]
- 94. Interpol review of forensic management, 2019–2022 - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC9840933/]
- 95. Benchmarking forensic volume crime performance in ... [https://www.sciencedirect.com/science/article/pii/S2589871X19300816]
- 96. In the context of forensic casework, are there meaningful ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8212664/]
- 97. Developing a New 'Service Readiness Level' Framework of ... [https://www.mdpi.com/resolver?pii=ijerph182312575]
- 98. Improving the forensic genetic workflow for countries with ... [https://www.sciencedirect.com/science/article/pii/S1872497324001674]
- 99. Just Building Partnerships to Advance Forensic Technology [https://nij.ojp.gov/media/audiofile/just-building-partnerships-to-advance-forensic-technology]
- 100. Digital transformation risk management in forensic science ... [https://www.sciencedirect.com/science/article/pii/S0379073820303480]
- 101. Top 6 Trends Shaping Modern DFIR in 2025 [https://belkasoft.com/dfir-trends-2025]
- 102. Technology in Forensic Sciences: Innovation and Precision [https://www.mdpi.com/2227-7080/12/8/120]
- 103. Part 1:- quality assurance mechanisms for digital forensic ... [https://www.sciencedirect.com/science/article/pii/S2665910719300386]
- 104. Technology Readiness Level Roadmap for Developing ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11206302/]
- 105. Assessment of a TRL [https://kpmg.com/ie/en/insights/tax/rd-assessment-of-a-trl.html]
- 106. The Most Frequently Asked Questions Our IT Support ... [https://micropro.com/blog/the-most-frequently-asked-questions-our-it-support-helpdesk-is-asked-answered/]
- 107. 16 Most Common Helpdesk Problems and How to Solve ... [https://www.alert-software.com/blog/the-most-common-helpdesk-problems-and-how-to-solve-them]