Implementing Technology Readiness Levels in Digital Forensic Readiness: A Framework for Courtroom-Admissible Innovation
This article provides a comprehensive framework for implementing Technology Readiness Levels (TRLs) in digital forensic readiness, addressing the critical gap between technological innovation and legal admissibility.
Implementing Technology Readiness Levels in Digital Forensic Readiness: A Framework for Courtroom-Admissible Innovation
Abstract
This article provides a comprehensive framework for implementing Technology Readiness Levels (TRLs) in digital forensic readiness, addressing the critical gap between technological innovation and legal admissibility. Targeting forensic researchers, practitioners, and laboratory managers, we explore foundational TRL concepts adapted from NASA and other high-reliability fields, then present methodological approaches for applying these levels to digital forensic tools and processes. The content examines common implementation challenges including tool validation, courtroom compliance under Daubert/Frye standards, and cross-border jurisdictional issues, while providing optimization strategies for overcoming technical and legal barriers. Through comparative analysis of current forensic technologies and validation frameworks aligned with international standards like ISO/IEC 27037, this guide enables professionals to systematically advance digital forensic capabilities while ensuring evidence integrity and courtroom readiness.
Understanding Technology Readiness Levels: From NASA to Digital Forensics
Technology Readiness Levels (TRLs) are a systematic metric used to assess the maturity of a particular technology. Developed by the National Aeronautics and Space Administration (NASA) in the 1970s, the TRL scale provides a common framework for engineers, managers, and researchers to consistently evaluate and communicate the readiness of a technology for operational deployment [1] [2]. The scale ranges from TRL 1, representing basic principle observation, to TRL 9, indicating a system proven in successful mission operations [3].
This framework has evolved from its original seven-level NASA scale to the current nine-level system that has been widely adopted across multiple sectors including defense, energy, and European Union research programs [2] [4]. For digital forensic readiness research, the TRL framework offers a structured approach to quantify technological maturity in a field characterized by rapid evolution and increasing significance in criminal investigations [5] [6].
The Nine Technology Readiness Levels
The nine TRLs represent a progression from basic research to proven operational application. The following table summarizes the core definition and activities for each level according to the NASA framework.
Table 1: The Nine Technology Readiness Levels of the NASA Framework
| TRL | Description | Hardware Focus | Software Focus | Exit Criteria |
|---|---|---|---|---|
| TRL 1 | Basic principles observed and reported [7] | Scientific knowledge generation underpinning technology concepts [7] | Scientific knowledge generation underpinning software architecture and mathematical formulation [7] | Peer-reviewed publication of research underlying proposed concept [7] |
| TRL 2 | Technology concept and/or application formulated [7] | Invention begins; practical application identified but speculative [7] | Practical application identified; basic principles coded; experiments with synthetic data [7] | Documented description of application/concept addressing feasibility and benefit [7] |
| TRL 3 | Analytical and experimental critical function and/or characteristic proof of concept [7] | Analytical studies contextualize technology; laboratory demonstrations validate predictions [7] | Limited functionality development to validate critical properties using non-integrated components [7] | Documented analytical/experimental results validating predictions of key parameters [7] |
| TRL 4 | Component and/or breadboard validation in laboratory environment [7] | Low-fidelity breadboard built/operated to demonstrate basic functionality [7] | Key software components integrated/validated; begin architecture development [7] | Documented test performance demonstrating agreement with analytical predictions [7] |
| TRL 5 | Component and/or breadboard validation in relevant environment [7] | Medium-fidelity brassboard built/operated in simulated operational environment [7] | End-to-end software elements implemented/interfaced with existing systems [7] | Documented test performance demonstrating agreement with analytical predictions [7] |
| TRL 6 | System/subsystem model or prototype demonstration in a relevant environment [7] | High-fidelity prototype built/operated in relevant environment [7] | Prototype implementations demonstrated on full-scale realistic problems [7] | Documented test performance demonstrating agreement with analytical predictions [7] |
| TRL 7 | System prototype demonstration in an operational environment [7] | High-fidelity engineering unit built/operated in relevant environment [7] | Prototype software with all key functionality available; well-integrated with operational systems [7] | Documented test performance demonstrating agreement with analytical predictions [7] |
| TRL 8 | Actual system completed and "flight qualified" through test and demonstration [7] | Final product in final configuration demonstrated through test [7] | Software fully debugged/integrated; all documentation completed; V&V completed [7] | Documented test performance verifying analytical predictions [7] |
| TRL 9 | Actual system "flight proven" through successful mission operations [7] | Final product successfully operated in actual mission [7] | Software thoroughly debugged/integrated; all documentation completed; sustaining support in place [7] | Documented mission operational results [7] |
TRL Assessment Methodology and Protocols
Technology Readiness Assessment Process
Formal Technology Readiness Assessment (TRA) involves systematic evaluation of a technology against the parameters defined for each TRL level. The process requires documented evidence that a technology has achieved the required maturity before progressing to the next level [2]. The assessment examines program concepts, technology requirements, and demonstrated capabilities through rigorous testing and validation protocols [2].
For digital forensic technologies, this assessment must address unique challenges including rapid technological evolution, diverse device ecosystems, and legal admissibility requirements [5] [8]. The methodology should incorporate quantitative evaluation approaches, such as Bayesian networks, to measure the plausibility of hypotheses based on digital evidence [9].
Experimental Protocols for TRL Advancement
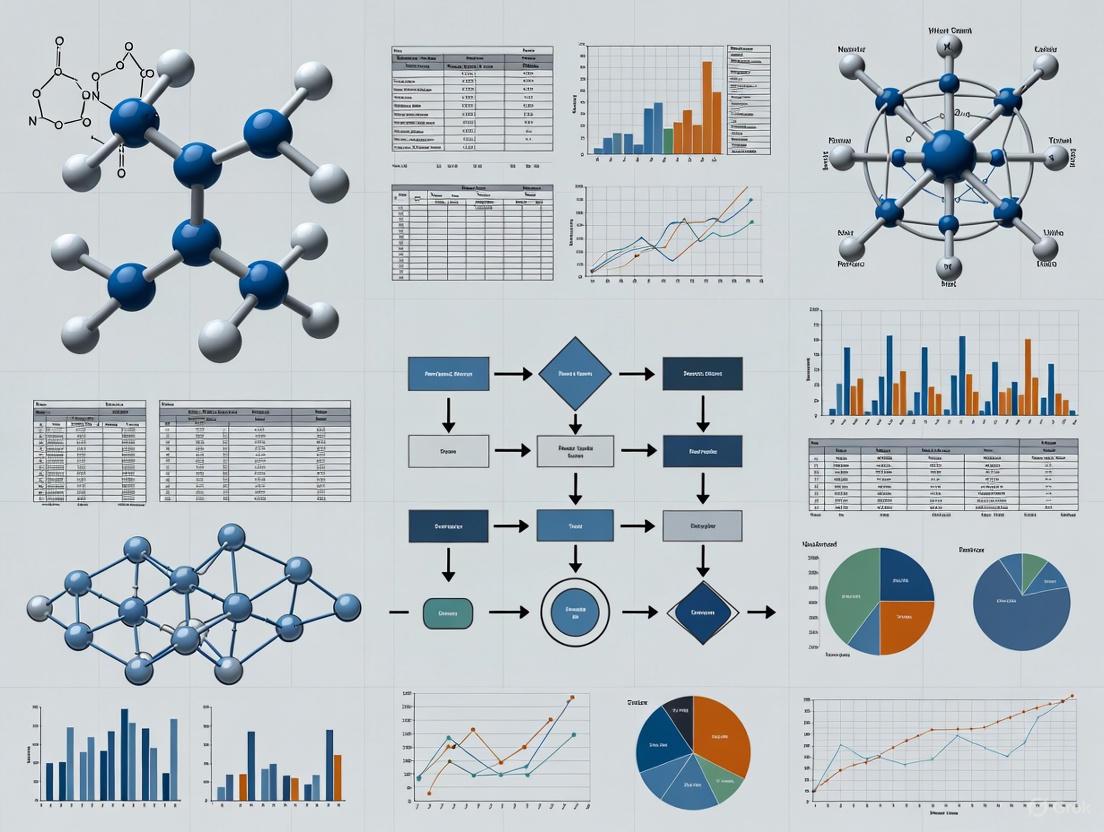
Advancing through TRL levels requires specific experimental protocols and validation methodologies. The following workflow illustrates the progressive validation requirements across the TRL spectrum:
TRL Progression Workflow
Key experimental protocols for critical transition points:
TRL 2 to TRL 3 Transition Protocol: Proof-of-Concept Validation
- Conduct analytical studies to place technology in appropriate context
- Develop laboratory demonstrations to validate analytical predictions
- Construct and operate limited functionality prototype
- For digital forensics: Validate core algorithms with synthetic datasets [7]
TRL 4 to TRL 5 Transition Protocol: Relevant Environment Testing
- Integrate basic technological components into representative system
- Test integrated model in simulated operational environment
- Establish performance benchmarks against requirements
- For digital forensics: Test with real device images in controlled forensic workstation environment [3]
TRL 6 to TRL 7 Transition Protocol: Operational Environment Demonstration
- Build high-fidelity engineering unit addressing scaling issues
- Demonstrate performance in actual operational environment
- Validate integration with collateral systems
- For digital forensics: Deploy in live investigative context with appropriate legal safeguards [7]
Application to Digital Forensic Readiness Research
Current State of Digital Forensic Technologies
Digital forensic research faces unique challenges in technology maturation. Current assessments indicate many digital forensic methods operate at intermediate TRLs (4-6), with limited standardization and quantitative validation [9]. A survey of legal practitioners indicates significant challenges in digital evidence processing, including backlogs, tool reliability, and interpretation complexities [6].
The emerging Internet of Things (IoT) forensics field operates at even lower TRLs (2-4), characterized by diverse proprietary platforms, volatile data storage, and limited forensic tool compatibility [8]. This creates a critical gap between technological innovation and judicial admissibility requirements.
Quantitative Assessment Framework
Advancing digital forensic technologies requires quantitative assessment methodologies. Bayesian networks provide a mathematical framework for evaluating hypothesis plausibility based on digital evidence [9]. The following equation formalizes this approach:
Bayesian Assessment for Digital Evidence
Bayes' Theorem for digital evidence evaluation:
[ \frac{Pr(H|E)}{Pr(\bar{H}|E)} = \frac{Pr(H)}{Pr(\bar{H})} \cdot \frac{Pr(E|H)}{Pr(E|\bar{H})} ]
Where the posterior odds ratio (left) equals the prior odds ratio multiplied by the likelihood ratio [9]. This approach enables quantitative assessment of digital evidence weight, supporting progression to higher TRLs through measurable reliability metrics.
Implementation Challenges in Digital Forensics
The "Valley of Death" between TRL 6 and TRL 7 presents particular challenges for digital forensic technologies [3]. This transition requires moving from laboratory validation to operational demonstration in real investigative contexts. Key barriers include:
- Legal and Ethical Constraints: Operational testing requires appropriate legal frameworks
- Dataset Availability: Limited access to realistic digital evidence corpora
- Tool Validation: Establishing error rates and reliability metrics for judicial acceptance
- Standardization: Developing consensus standards for forensic process validation
Research Reagent Solutions for Digital Forensic Readiness
Advancing TRLs in digital forensic research requires specialized "research reagents" - standardized tools, datasets, and methodologies that enable reproducible experimentation and validation.
Table 2: Essential Research Reagents for Digital Forensic TRL Advancement
| Research Reagent | Function | TRL Application Range | Implementation Example |
|---|---|---|---|
| Reference Digital Evidence Corpora | Provides standardized datasets for method validation and comparison | TRL 3-6 | NIST CFReDS (Computer Forensic Reference Data Sets) for controlled experimentation [9] |
| Forensic Process Automation Frameworks | Enables reproducible execution of forensic techniques across multiple trials | TRL 4-7 | Robot Framework implementations for digital forensic workflow automation |
| Bayesian Network Models | Quantifies evidentiary strength and hypothesis plausibility | TRL 4-8 | Custom Bayesian networks for specific digital evidence types (e.g., file system artifacts) [9] |
| Digital Forensic Tool Validation Suites | Measures tool reliability, error rates, and performance characteristics | TRL 5-8 | NIST Computer Forensic Tool Testing (CFTT) methodologies adapted for research contexts |
| Legal Admissibility Frameworks | Guides development of judicially acceptable evidence handling procedures | TRL 7-9 | Daubert standard compliance checklists for novel forensic techniques |
The NASA TRL framework provides a robust methodology for assessing and advancing technological maturity in digital forensic research. By implementing structured assessment protocols, quantitative evaluation methods, and standardized research reagents, the field can systematically address current limitations and bridge the gap between innovative research and operational deployment. The progression from theoretical concepts (TRL 1) to court-admissible methodologies (TRL 9) requires disciplined approach to validation, demonstration, and operational proof essential for integrating digital forensic advances into the criminal justice system.
The digital forensics field is in a state of rapid evolution, driven by technological advancements including cloud computing, artificial intelligence, and the proliferation of Internet of Things devices [10]. This acceleration creates a critical translation problem where research innovations struggle to mature into operationally ready tools that practitioners can reliably use in investigations and legal proceedings. The global digital forensics market reflects this urgency, projected to reach $18.2 billion by 2030 with a compound annual growth rate of 12.2% [10].
Technology Readiness Levels offer a proven framework for assessing technological maturity, originally developed by NASA in the 1970s for space exploration technologies [11]. The TRL scale provides a consistent metric for understanding technology evolution, ranging from basic principle observation to proven operational deployment [11]. This systematic approach to maturity assessment remains underutilized in digital forensics research, where a significant gap persists between academic prototypes and court-admissible tools.
The consequences of this research-practice gap are substantial. Law enforcement and judicial systems often struggle to adapt to technological changes, resulting in possible misinterpretations of digital evidence in criminal trials [5]. Operational, technical, and management constraints hinder the accurate processing of digital traces, creating a critical need for standardized forensic practices and rigorous validation procedures [5]. This application note establishes protocols for implementing TRLs specifically within digital forensics research contexts.
Technology Readiness Levels: A Standardized Framework
The TRL Scale and Definitions
Technology Readiness Levels comprise a nine-point scale that enables consistent comparison of technological maturity across different domains. The framework has been adapted by numerous organizations including the United States Department of Defense, the European Union, and various industrial sectors [11]. The standardized definitions and examples relevant to digital forensics are presented in Table 1.
Table 1: Technology Readiness Levels with Digital Forensics Examples
| TRL | Description | Digital Forensics Example |
|---|---|---|
| 1 | Basic principles observed and reported | Paper-based study of a novel artifact's properties in Windows registry or file system structures |
| 2 | Technology concept formulated | Speculative application of principles to envision new forensic analysis technique |
| 3 | Experimental proof of concept | Active R&D with laboratory measurements to validate analytical predictions about artifact behavior |
| 4 | Technology validated in lab | Component validation through designed investigation; analysis of technology parameter operating range |
| 5 | Technology validated in relevant environment | Validation of semi-integrated system/model in simulated forensic environment |
| 6 | Technology demonstrated in relevant environment | Prototype system verified and demonstrated in simulated operational environment |
| 7 | System model/prototype demonstration in operational environment | Prototype system verified in actual investigative environment with real data sources |
| 8 | System complete and qualified | Full system produced and qualified through testing in operational environments |
| 9 | Actual system proven in operational environment | System successfully deployed for multiple investigations and accepted as evidence in court proceedings |
The "Valley of Death" in Technology Development
A critical challenge in technology development occurs between TRL 4-7, often termed the "Valley of Death" where promising technologies frequently stall due to lack of coordinated support [11]. Universities and government funding sources typically focus on TRLs 1-4, while the private sector concentrates on TRLs 7-9, creating a funding and development gap that prevents many research innovations from reaching operational use [11]. This valley is particularly problematic in digital forensics, where the rapid pace of technological change demands efficient translation of research into practice.
Digital Forensics Challenges and TRL Alignment
Contemporary Digital Forensics Challenges
Digital forensics professionals face multifaceted challenges that underscore the need for a maturity assessment framework. These challenges directly impact the effective development and deployment of forensic technologies across the TRL spectrum:
Technical Challenges: Anti-forensic techniques including encryption, data hiding, steganography, and data wiping actively undermine forensic tools and methodologies [12]. According to a 2024 cybersecurity report, 68% of cybercriminals use encryption to hide evidence, creating significant decryption challenges for investigators [12].
Data Scale and Complexity: The proliferation of cloud storage and IoT devices has created investigative environments characterized by data fragmentation, jurisdictional complexity, and petabyte-scale unstructured data [10]. By 2025, over 60% of newly generated data will reside in the cloud, distributed across geographically dispersed servers [10].
Legal and Regulatory Constraints: Privacy laws and regulations differ worldwide, with regions like Europe (GDPR), the United States (CLOUD Act), and China (Cybersecurity Law) maintaining strict legal frameworks that complicate digital evidence collection and analysis [12].
Tool Development Limitations: Traditional forensic tools, designed for localized data, struggle with modern distributed environments and the increasing sophistication of anti-forensic techniques [12] [13].
TRL-Digital Forensics Challenge Mapping
Table 2: Mapping Digital Forensics Challenges to TRL Transition Points
| TRL Transition | Associated Digital Forensics Challenges | Risk Mitigation Strategy |
|---|---|---|
| TRL 3-4 (Lab to component validation) | Defining forensically relevant parameters and operating ranges | Establish baseline forensic artifact preservation metrics |
| TRL 4-5 (Lab to relevant environment) | Transitioning from controlled to simulated real-world conditions | Implement representative data sets from multiple sources (cloud, mobile, IoT) |
| TRL 6-7 (Relevant to operational environment) | Legal admissibility requirements, tool reliability testing | Engage legal experts early, conduct peer validation studies |
| TRL 8-9 (Qualified to proven system) | Court acceptance, standardization across jurisdictions | Publish validation studies, establish certification protocols |
TRL Assessment Protocols for Digital Forensics Research
TRL Assessment Workflow
The following experimental protocol provides a structured methodology for assessing Technology Readiness Levels in digital forensics research and development.
Phase 1: Foundation Protocol
Objective: Establish baseline requirements and success metrics for digital forensics technology development.
Materials:
- Forensic data sets (known ground truth)
- Standard reference materials (NIST CFReDS or similar)
- Documentation framework
Methodology:
- Use Case Definition: Clearly articulate the specific forensic problem being addressed (e.g., cloud data acquisition, IoT artifact extraction, encrypted data recovery).
- Core Artifact Identification: Identify the specific digital artifacts (registry entries, file system structures, memory patterns, network traces) relevant to the technology.
- Success Metric Establishment: Define quantitative and qualitative success metrics including:
- Artifact recovery rate (>95% for TRL 7+)
- False positive/negative rates (<2% for TRL 8+)
- Processing throughput (MB/sec, devices/hour)
- Evidence integrity preservation (hash verification)
- Requirements Documentation: Document functional, performance, and legal requirements including adherence to standards such as ISO 27037.
Deliverables: Requirements specification document, validation test plan, success criteria checklist.
Phase 2: Validation Protocol
Objective: Validate technology performance in increasingly realistic environments.
Materials:
- Controlled test environment
- Simulated case data sets
- Reference tools for comparison
- Performance monitoring framework
Methodology:
- Component Testing (TRL 4-5):
- Isolate individual technology components
- Validate against standardized data sets
- Establish parameter operating ranges
- Document failure modes and limitations
Integrated System Testing (TRL 5-6):
- Deploy technology in simulated operational environment
- Test with heterogeneous data sources (cloud, mobile, desktop)
- Validate against anti-forensic techniques (encryption, data hiding)
- Assess usability by trained examiners
Operational Pilot (TRL 6-7):
- Deploy in active investigative environment with supervision
- Process real case data alongside established tools
- Document evidence handling and chain of custody
- Assess performance under realistic constraints
Deliverables: Validation report, performance benchmarks, limitation documentation, user feedback analysis.
Phase 3: Integration Protocol
Objective: Establish technology readiness for operational deployment and court acceptance.
Materials:
- Multi-jurisdictional test environments
- Legal review framework
- Certification documentation
- Training materials
Methodology:
- Multi-Jurisdictional Testing (TRL 7-8):
- Validate technology across different legal frameworks
- Test with international data privacy requirements (GDPR, CLOUD Act)
- Verify performance with region-specific artifacts
Legal Admissibility Review (TRL 8):
- Document validation methodology for court presentation
- Establish expert witness qualification requirements
- Prepare challenge testing protocols (Daubert/Frye standards)
- Document known limitations and error rates
Court Validation (TRL 9):
- Successful evidence admission in multiple cases
- Peer recognition and adoption
- Integration into standard operating procedures
- Independent validation studies
Deliverables: Legal admissibility package, certification documentation, training curriculum, operational deployment guide.
The Digital Forensics Researcher's Toolkit
Essential Research Reagent Solutions
Table 3: Digital Forensics Research Toolkit: Essential Materials and Solutions
| Tool Category | Specific Examples | Research Function | TRL Application Range |
|---|---|---|---|
| Reference Data Sets | NIST CFReDS, Digital Corpora, M57-Patrol | Controlled validation environments for reproducible testing | TRL 3-7 |
| Forensic Processing Platforms | Belkasoft X, Autopsy, FTK, X-Ways | Integrated analysis environments for tool validation | TRL 4-8 |
| Specialized Acquisition Tools | Cellebrite UFED, Tableau TX1, Falcon Neo | Hardware and software for evidence acquisition from diverse sources | TRL 5-8 |
| Validation Frameworks | NIST OSF, DoD Cyber Crime Center CFReDS | Standardized testing protocols and metrics | TRL 4-8 |
| Anti-Forensic Challenge Sets | Encrypted containers, steganographic tools, data wiping utilities | Testing tool resilience against obfuscation techniques | TRL 5-8 |
| Legal Standards Documentation | ISO 27037, ASTM E2763, Daubert criteria | Ensuring legal compliance and admissibility requirements | TRL 7-9 |
Case Study: TRL Application in Digital Forensics Tool Development
Cloud Forensics Tool Maturation Pathway
The following case study illustrates a practical application of TRLs in digital forensics tool development, specifically addressing cloud data acquisition challenges.
Initial Research (TRL 1-3): Basic principles of cloud API interactions were observed and documented. A technology concept was formulated for using legitimate user credentials to access cloud data through simulated app clients, circumventing some jurisdictional challenges [13].
Laboratory Validation (TRL 4-5): Component validation established that the technique could successfully download and decrypt user data from social media platforms and cloud services using APIs. The technology was validated in a lab environment with controlled test accounts and data sets.
Relevant Environment Demonstration (TRL 6-7): A prototype system was demonstrated in a simulated but forensically relevant environment, processing data from multiple cloud services simultaneously. The tool successfully maintained evidence integrity while navigating service rate limits and authentication challenges.
Operational Deployment (TRL 8-9): The complete system was qualified in operational environments, addressing real case requirements. The technology was proven through successful deployment in multiple investigations, with evidence admitted in legal proceedings [13].
TRL Assessment Framework for AI-Based Analysis Tools
The integration of artificial intelligence in digital forensics presents particular TRL assessment challenges, especially regarding transparency and legal admissibility.
The systematic application of Technology Readiness Levels in digital forensics research provides a critical framework for bridging the persistent gap between academic innovation and operational deployment. As digital evidence becomes increasingly central to legal proceedings and criminal investigations, the need for rigorously validated, legally admissible tools has never been greater.
The TRL framework offers a standardized methodology for assessing technological maturity that can be adapted to the unique challenges of digital forensics, including rapid technological change, anti-forensic techniques, data scale and complexity, and legal admissibility requirements. By implementing the protocols and assessment methodologies outlined in this application note, digital forensics researchers can systematically advance their technologies from basic research to court-ready solutions.
Future directions for TRL development in digital forensics should include domain-specific adaptations for cloud forensics, IoT forensics, and AI-based analysis tools. Additionally, the integration of complementary frameworks such as Safe-by-Design principles can further enhance technology development by proactively addressing safety, security, and ethical considerations throughout the development lifecycle [14]. Through the consistent application of TRL assessment methodologies, the digital forensics community can accelerate the translation of research innovations into tools that effectively combat cybercrime and support the administration of justice.
This document provides a current state analysis of the Technology Readiness Level (TRL) landscape for digital forensic tools and methodologies. The analysis is framed within the context of implementing TRLs in digital forensic readiness research, offering researchers a structured framework to assess the maturity and operational deployment potential of emerging technologies. The field of digital forensics is undergoing rapid transformation, driven by technological advancements and increasingly sophisticated cyber threats [15]. The evolution from analyzing standalone computers to dealing with mobile devices, cloud environments, and the Internet of Things (IoT) has necessitated a more structured approach to technology assessment and adoption [16]. This document presents a detailed analysis of the current TRL landscape, standardized experimental protocols for validation, and visualizations of key workflows to aid researchers and development professionals in evaluating the maturity of digital forensic technologies.
Current TRL Analysis of Digital Forensic Domains
The maturity of digital forensic tools and techniques varies significantly across different sub-domains. The table below summarizes the assessed TRL for major areas as of 2025, providing a quantitative overview of the landscape.
Table 1: Technology Readiness Level (TRL) Analysis of Digital Forensic Domains (2025)
| Digital Forensic Domain | Assessed TRL (1-9) | Key Tools & Technologies | Primary Challenges & Limitations |
|---|---|---|---|
| Computer Forensics | 9 (Full Operational Deployment) | EnCase, FTK Imager, Autopsy, The Sleuth Kit [17] | High data volumes, SSD wear-leveling, full-disk encryption [16] [12] |
| Mobile Device Forensics | 8-9 (System Complete & Qualified) | Cellebrite, Magnet AXIOM, Belkasoft X [17] [13] | Hardware diversity, advanced encryption (iOS/Android), secure bootloaders, locked bootloaders [18] [13] |
| Cloud Forensics | 6-7 (Technology Demonstrated & Prototyped) | API-based tools (e.g., for Facebook, Instagram), Magnet AXIOM [17] [13] | Jurisdictional issues, data fragmentation, multi-tenancy, provider cooperation, legal access complexities [18] [13] |
| AI/ML for Media Analysis | 6-7 (Technology Demonstrated & Prototyped) | BelkaGPT, DeepPatrol, Yahoo OpenNSFW [19] [13] | Algorithmic bias, training data requirements, computational resource demands, potential for false positives/negatives [18] [13] |
| Blockchain & Cryptocurrency Forensics | 5-6 (Technology Validated & Demonstrated) | Specialized blockchain explorers, transaction graph analysis tools [20] | Anonymity features (privacy coins, mixers), cross-chain transactions, volume of data, regulatory gaps [20] |
| IoT & Vehicle Forensics | 4-5 (Technology Validated in Lab) | Custom hardware interpreters, proprietary protocol analyzers [16] | Hardware heterogeneity, lack of standardization, proprietary protocols, physical access challenges [16] |
Experimental Protocols for Tool and Methodology Validation
To ensure the reliability and admissibility of digital evidence, rigorous validation of tools and methodologies is essential. The following protocols provide a framework for researchers to assess the performance of digital forensic technologies systematically.
Protocol for Validating AI-Based Evidence Analysis Tools
Objective: To quantitatively evaluate the accuracy, efficiency, and reliability of an AI-powered tool in analyzing large volumes of digital media, specifically for identifying illicit content.
Materials & Reagents:
- Test Machine: Workstation with High-Performance GPU (e.g., NVIDIA RTX A6000 or equivalent).
- Software Under Test: AI analysis tool (e.g., DeepPatrol or equivalent [19]).
- Reference Datasets: Curated dataset of known media files (videos and images) with verified content annotations.
- Control Software: Established, non-AI-based forensic media analyzer.
- Metrics Logging System: Software for recording processing times and results.
Procedure:
- System Setup: Install the AI tool and control software on the test machine. Ensure all drivers and dependencies are current.
- Dataset Preparation: Ingest the reference dataset. The dataset must include a known number of target files (e.g., containing specific objects or content) among a larger set of neutral files.
- Baseline Establishment: Run the control software on the dataset. Record the total processing time, the number of true positives, false positives, true negatives, and false negatives.
- Test Execution: Process the same dataset using the AI tool under test. Record the same metrics as in step 3.
- Data Analysis:
- Calculate precision and recall for both the control and AI tool.
- Compare the total processing time and time per file.
- Document any instances where the AI tool failed to process a file or produced an error.
- Validation: The tool's performance is considered validated for this specific task if it meets or exceeds pre-defined thresholds for accuracy (e.g., >95% precision and recall) and demonstrates a significant efficiency gain over the control without introducing unacceptable error rates [19].
Protocol for Cloud Evidence Acquisition and Verification
Objective: To acquire digital evidence from a cloud service provider (CSP) in a forensically sound manner that preserves the integrity of the evidence and maintains a legally defensible chain of custody.
Materials & Reagents:
- Legal Authority: A valid search warrant, subpoena, or production order specific to the CSP and data in question.
- Acquisition Workstation: Computer with trusted forensic software installed.
- Forensic Software: Tool capable of cloud data acquisition via CSP APIs (e.g., Magnet AXIOM, Belkasoft X [17] [13]).
- Write-Blocking Hardware: To prevent alteration of any local evidence.
- Secure Storage: Encrypted, tamper-evident storage for acquired evidence files.
Procedure:
- Legal Compliance Check: Verify that the legal authority is valid and encompasses the data to be acquired from the specific CSP.
- Tool Configuration: Configure the forensic software with the appropriate legal credentials and API keys as permitted by the CSP and the legal authority.
- Evidence Acquisition:
- Initiate the acquisition process from the workstation.
- The tool will interact with the CSP's API to download user data. All data transfers must occur over encrypted channels (e.g., TLS).
- Upon completion, the tool should generate a comprehensive log of all actions and a list of downloaded files.
- Integrity Verification: The acquisition tool should automatically generate a cryptographic hash (e.g., SHA-256) of the acquired evidence container.
- Chain of Custody Documentation:
- Record the date, time, investigator, tool used, legal authority, and the hash value in the case file.
- Transfer the evidence container to secure storage, documenting all transfers.
- Verification: The acquisition is verified by confirming that the tool's log shows no critical errors and that the hash value can be reproduced at a later time, proving the evidence's integrity [18] [13].
Visualization of Digital Forensic Workflows
The following diagrams, generated using Graphviz DOT language, illustrate core logical relationships and workflows in digital forensic tool validation and evidence handling.
TRL Assessment Workflow for Digital Forensic Tools
Digital Evidence Validation Protocol
The Scientist's Toolkit: Key Research Reagent Solutions
The following table details essential tools, platforms, and software that constitute the core "research reagents" for modern digital forensic investigations.
Table 2: Essential Digital Forensic Research Reagents & Platforms
| Tool/Platform Name | Category/Type | Primary Function in Research & Investigation |
|---|---|---|
| Volatility 3 [17] | Memory Forensics Framework | Open-source tool for analyzing RAM dumps to identify malware, rootkits, and system activity. Critical for investigating live systems. |
| Wireshark [17] | Network Protocol Analyzer | Captures and inspects network traffic in real-time. Essential for network forensics and understanding communication patterns. |
| Cellebrite UFED [17] | Mobile Forensic Solution | Extracts, decodes, and analyzes data from smartphones and tablets. Supports physical, logical, and cloud extraction from mobile devices. |
| Magnet AXIOM [17] | Integrated Forensic Suite | Recovers and analyzes evidence from computers, smartphones, and cloud sources. Provides a unified interface for complex, multi-source cases. |
| Belkasoft X [13] | Digital Forensic Platform | Analyzes data from computers, mobile devices, and cloud storage. Features AI modules (BelkaGPT) for processing text-based evidence. |
| EnCase Forensic [17] | Digital Forensic Suite | Provides disk imaging, evidence analysis, and comprehensive reporting. Widely used in law enforcement and corporate investigations for its court-admissibility. |
| FileTSAR [19] | Large-Scale Network Forensics | Tool for capturing and analyzing network traffic to reassemble files and data in large-scale enterprise network investigations. |
| DeepPatrol [19] | AI-Based Media Analysis | Uses deep learning to automatically detect and classify content in videos and images, significantly reducing manual review time. |
| The Sleuth Kit (+Autopsy) [17] | File System Analysis | Open-source library and GUI for analyzing disk images and recovering files. A fundamental tool for file system-level forensics. |
For researchers and professionals in digital forensics and drug development, the scientific validity of a technique is only one part of the challenge. The other is ensuring that evidence or data derived from these methods will be deemed admissible in a court of law. The concepts of "readiness" for court are formally defined by a set of legal criteria established in seminal cases: Daubert, Frye, and Mohan. These standards act as the legal gatekeepers, determining whether expert testimony based on novel scientific methods can be presented to a jury. Framing technology development within the context of these legal standards is crucial, as it aligns the scientific process with the judiciary's requirements for reliability and relevance. This document outlines the application of these legal foundations, integrating them with the structured assessment framework of Technology Readiness Levels (TRLs) to provide a comprehensive roadmap for achieving both technical and legal readiness.
Core Legal Standards Defining Scientific Admissibility
The Daubert Standard
Established in the 1993 U.S. Supreme Court case Daubert v. Merrell Dow Pharmaceuticals, Inc., this standard assigns the trial judge the role of a "gatekeeper" for scientific evidence [21]. Its purpose is to ensure that all expert testimony is not only relevant but also reliable. Under Daubert, the court's assessment is flexible, focusing on the methodology and reasoning underlying the expert's opinion rather than just the conclusion [21] [22].
The following table summarizes the five key factors judges consider under Daubert [21] [22]:
Table 1: The Five Factors of the Daubert Standard
| Factor | Description | Exemplary Question for Researchers |
|---|---|---|
| Testing & Falsifiability | Whether the theory or technique can be (and has been) tested. | Can the methodology be independently validated, and has it been? |
| Peer Review | Whether the method has been subjected to peer review and publication. | Have the principles and results been scrutinized by the broader scientific community? |
| Error Rate | The existence of a known or potential error rate and the standards controlling the technique's operation. | What is the established rate of false positives/negatives, and are there protocols to minimize error? |
| Standards & Controls | The existence and maintenance of standards controlling the technique's operation. | Are there documented, standardized protocols for applying the method? |
| General Acceptance | The extent to which the method is generally accepted within the relevant scientific community. | Is the technique widely regarded as reliable by other experts in the field? |
The Daubert standard was later clarified and expanded in two subsequent Supreme Court cases, General Electric Co. v. Joiner (1997) and Kumho Tire Co. v. Carmichael (1999), which together are known as the "Daubert Trilogy" [21] [22]. Kumho Tire specifically extended the judge's gatekeeping obligation to all expert testimony, including non-scientific technical and other specialized knowledge [21].
The Frye Standard
The Frye standard, originating from the 1923 case Frye v. United States, is the predecessor to Daubert [23]. This standard provides a more straightforward test, often called the "general acceptance" test. It holds that an expert opinion is admissible if the scientific technique on which it is based is "generally accepted" as reliable by the relevant scientific community [23] [24]. The focus is narrowly on the consensus within the field, without the explicit, multi-factor reliability assessment mandated by Daubert. While the federal courts and a majority of states have adopted Daubert, several key jurisdictions, including California, Illinois, New York, and Pennsylvania, continue to adhere to the Frye standard [23] [25].
The Mohan Standard
In Canada, the admissibility of expert evidence is governed by the standard set forth in R. v. Mohan [26] [27]. This test involves a four-threshold requirement for admissibility. The proposed expert evidence must be [26] [27]:
- Relevant to a material issue in the case.
- Necessary to assist the trier of fact (the judge or jury) in reaching a correct conclusion.
- Not excluded by any other exclusionary rule of evidence.
- Presented by a properly qualified expert.
The Supreme Court of Canada has further refined the application of Mohan into a two-stage process. First, the party proposing the evidence must meet the four threshold requirements. Second, the judge performs a cost-benefit analysis, or "gatekeeper" inquiry, to weigh the potential risks and benefits of admitting the evidence, considering factors such as its reliability and the potential for it to mislead the trier of fact [26].
Comparative Analysis of Admissibility Standards
The following table provides a direct comparison of the three primary standards to highlight their distinct focuses and applications.
Table 2: Comparative Analysis of Daubert, Frye, and Mohan Standards
| Feature | Daubert Standard | Frye Standard | Mohan Standard |
|---|---|---|---|
| Jurisdiction | U.S. Federal Courts; Majority of U.S. States [25] | A minority of U.S. States (e.g., CA, IL, NY, PA) [23] [25] | Canadian Courts [26] [27] |
| Core Question | Is the testimony based on reliable methodology and is it relevant? [21] | Is the scientific technique generally accepted in the relevant field? [23] | Is the evidence relevant, necessary, and presented by a qualified expert? [26] |
| Judge's Role | Active gatekeeper who assesses foundational reliability [22] | Gatekeeper who defers to the scientific community's consensus [23] | Gatekeeper who applies a threshold test and then a discretionary cost-benefit analysis [26] |
| Scope of Application | Applies to all expert testimony (scientific, technical, other specialized knowledge) [21] | Primarily applied to novel scientific evidence [23] | Applies to all expert opinion evidence [26] |
| Key Strengths | Flexible, case-specific analysis of reliability; allows for new, valid science [21] [25] | Bright-line rule; promotes uniformity and avoids "junk science" [23] | Balanced, principled approach that emphasizes necessity and prejudice [26] |
Integrating TRLs with Legal Admissibility: Application Notes for Researchers
For a technology to be "ready for court," its development must be pursued with both technical and legal admissibility in mind. Technology Readiness Levels (TRLs) provide a systematic framework for assessing maturity, from basic research (TRL 1) to full deployment (TRL 9) [1] [28]. The following diagram and table map the critical legal admissibility considerations onto this development lifecycle.
Table 3: TRL-Legal Integration Framework: Key Actions and Deliverables
| TRL Stage | Primary Legal Objective | Required Research Actions | Critical Documentation Deliverables |
|---|---|---|---|
| TRL 1-2Basic Principles | Establish a foundation for future "general acceptance" (Frye) and testing (Daubert). | Conduct foundational research; identify relevant scientific community; formulate technology concept. | Literature reviews; published papers on basic principles; hypothesis statements. |
| TRL 3-4Proof of Concept | Generate initial data on validity to satisfy Daubert's "testing" and "peer review" factors. | Develop and test proof-of-concept in lab; submit findings for peer-reviewed publication. | Lab study protocols; proof-of-concept model results; draft manuscripts; peer review reports. |
| TRL 5-7Validation & Prototyping | Address Daubert's "error rate" and "standards" factors; demonstrate reliability in real-world conditions. | Test prototype in relevant environment; quantify and analyze error rates; develop standard operating procedures (SOPs). | Validation study reports; error rate calculations; draft SOPs; performance benchmarks. |
| TRL 8-9System Complete | Solidify "general acceptance" and demonstrate that all Daubert/Mohan criteria are met. | Conduct final operational testing; obtain certifications; publish final results; train other labs on the method. | Finalized SOPs; certification documents; independent validation studies; training materials. |
Experimental Protocols for Demonstrating Legal Readiness
To systematically build a case for the admissibility of a novel technique, researchers should implement the following experimental protocols, designed to generate the evidence required by the legal standards.
Protocol for Validation and Error Rate Assessment (AddressingDaubert)
1. Objective: To empirically determine the false positive and false negative rates of the methodology under controlled conditions that simulate its intended operational use. 2. Materials: * A validated and agreed-upon reference dataset (e.g., known samples, ground-truthed digital images). * The experimental apparatus or software tool being validated. * Blinded samples for testing. 3. Methodology: * Sample Preparation: Create a test set comprising both positive and negative controls, along with unknown samples, ensuring the ground truth is known only to the study coordinator. * Blinded Analysis: Have one or more analysts apply the methodology to the test set without knowledge of the expected outcomes. * Data Collection: Record all results, including any indeterminate outcomes. 4. Data Analysis: * Calculate the rates of false positives, false negatives, and overall accuracy. * Perform statistical analysis (e.g., confidence intervals) to express the uncertainty of the error rate estimates. 5. Deliverable: A formal validation report detailing the study design, raw data, calculated error rates, and statistical analysis, ready for disclosure in legal proceedings.
Protocol for Establishing "General Acceptance" (AddressingFrye)
1. Objective: To document the degree to which the underlying principles and methodology are accepted within the relevant scientific community. 2. Materials: * Access to scientific literature databases (e.g., PubMed, IEEE Xplore, Google Scholar). * Survey tools for polling expert communities (if necessary). 3. Methodology: * Literature Review: Conduct a systematic review of peer-reviewed publications that utilize, validate, or critique the methodology. Document the number of publications, the prestige of the journals, and the conclusions drawn. * Citation Analysis: Track the adoption and citation of key papers to demonstrate influence and acceptance. * Standards and Guidelines: Identify any industry standards, guidelines from professional bodies (e.g., SWGDE, ASTM), or regulatory approvals that incorporate the method. 4. Deliverable: A "General Acceptance Dossier" containing the literature review summary, citation analysis, copies of key supportive publications, and references to relevant standards and guidelines.
1. Objective: To evaluate an organization's operational preparedness to conduct a digital forensic investigation that yields legally admissible evidence. 2. Methodology: * Scoping: Define the assessment's boundaries (e.g., specific systems, types of incidents). * Information Gathering: Collect and review all relevant policies (incident response, data retention, evidence handling), procedures, and existing incident response plans. * Gap Analysis: Interview key personnel and compare current capabilities against industry best practices (e.g., ISO/IEC 27037) and legal admissibility requirements. * Reporting: Document findings and provide prioritized recommendations for improvement. 3. Key Assessment Components: * Policies & Procedures: Existence and quality of evidence handling and preservation protocols. * Tools & Technologies: Validation status and adequacy of forensic tools (per Daubert protocols). * Skills & Expertise: Qualifications and training of the digital forensics team. * Documentation & Reporting: Robustness of practices for maintaining chain of custody and generating final reports. 4. Deliverable: A DFRA report that provides a roadmap for enhancing the organization's technical and procedural readiness for court.
The Scientist's Toolkit: Essential Reagents for Legal Readiness
This toolkit comprises the non-physical "reagents" and materials required to build a legally defensible scientific method.
Table 4: Essential Toolkit for Achieving Legal Readiness
| Toolkit Component | Function in Achieving Legal Readiness | Primary Legal Standard Addressed |
|---|---|---|
| Standard Operating Procedures (SOPs) | Documents the exact, repeatable methodology, ensuring consistency and allowing for scrutiny. Essential for demonstrating reliable application. | Daubert (Standards), Mohan (Reliability) |
| Validation Study Report | Provides the empirical evidence for the method's accuracy, precision, and error rate. The core document for proving reliability. | Daubert (Testing, Error Rate) |
| Peer-Reviewed Publications | Serves as objective, third-party endorsement of the method's validity and contributes directly to establishing "general acceptance." | Daubert (Peer Review), Frye (General Acceptance) |
| Chain of Custody Documentation | A log that tracks the possession, handling, and transfer of physical or digital evidence. Critical for authenticating evidence and proving its integrity. | All (Foundation for Admissibility) |
| Qualified Expert CV | Establishes the witness's credentials, demonstrating they have the requisite "knowledge, skill, experience, training, or education" to provide an opinion. | Daubert, Frye, Mohan |
| General Acceptance Dossier | A curated collection of literature, standards, and survey data that argues for the method's widespread adoption in the field. | Frye, Daubert (General Acceptance Factor) |
| Code/Algorithm Repository | For digital methods, a version-controlled repository allows for transparency, peer review, and independent verification of the underlying code. | Daubert (Testing, Scrutiny) |
For researchers, scientists, and professionals in drug development and other regulated industries, digital evidence is increasingly critical for protecting intellectual property, validating research integrity, and complying with rigorous quality standards. The concept of Technology Readiness Levels (TRL), a systematic metric for measuring technological maturity, provides an ideal framework for structuring digital forensic readiness [28]. Originally developed by NASA for space missions, the TRL scale divides technology development into 9 distinct stages, from basic principles (TRL 1) to a proven operational system (TRL 9) [29] [30].
This document applies this structured approach to digital forensic readiness, transforming it from an ad-hoc reactive function into a strategically managed capability. Digital Forensic Readiness is defined as the preparation of an organization to efficiently collect, preserve, and analyze digital evidence when incidents occur, with the goals of minimizing business disruption, reducing investigation costs, and ensuring legal admissibility [31]. By adopting a TRL-gated framework, organizations can methodically progress from basic forensic principles to a fully operational, proactive digital forensics system integrated within their quality and compliance infrastructure.
Technology Readiness Levels: A Framework for Forensic Capability Development
The TRL framework provides a common language for assessing the maturity of forensic capabilities, enabling objective evaluation and targeted investment. For digital forensic readiness, the nine levels can be grouped into three primary phases: conceptual research (TRL 1-3), development and validation (TRL 4-6), and deployment and operation (TRL 7-9) [30].
Table 1: Technology Readiness Levels for Digital Forensic Readiness
| TRL | Stage Description | Forensic Readiness Activities | Outputs & Evidence |
|---|---|---|---|
| TRL 1 | Basic principles observed and reported | Fundamental research on forensic techniques; literature review of forensic standards (ISO 27037, 27041) [32]. | Scientific publications; research papers on forensic artifact behavior. |
| TRL 2 | Technology concept formulated | Hypothesize forensic readiness concept; identify potential applications for IP protection and data integrity monitoring. | Documented concept paper linking forensic capabilities to organizational risks [31]. |
| TRL 3 | Experimental proof of concept | Validate key forensic hypotheses in lab environment; test evidence collection from key systems. | Proof-of-concept report; validated hypotheses for evidence collection [30]. |
| TRL 4 | Technology validated in lab | Build lab-scale forensic prototype; test evidence collection from isolated R&D systems. | Functional prototype; validated basic evidence collection capabilities [30]. |
| TRL 5 | Validation in relevant environment | Refine forensic components; test integration with other security systems in a simulated environment. | Integrated component testing report; refined forensic nodes [30]. |
| TRL 6 | Technology demonstrated in relevant environment | Full prototype demonstrated in operational research environment with real data. | System prototype demonstration report; validated in relevant environment [29]. |
| TRL 7 | System prototype in operational environment | Forensic system prototype tested in live operational environment (e.g., specific research division). | Operational prototype report; successful testing in real environment [28]. |
| TRL 8 | System complete and qualified | Full forensic readiness system finalized and qualified through testing; integrated with compliance workflows. | Final system documentation; qualification/certification records [28]. |
| TRL 9 | Actual system proven in operational environment | Continuous forensic readiness operations; successful evidence use in actual incidents or audits. | Incident reports; audit findings; continuous improvement records [28]. |
A critical concept in technology maturation is the "Valley of Death" – the gap between early innovation (TRL 3-4) and operational deployment (TRL 7-8) where many promising technologies fail [28]. In digital forensics, this often manifests as promising research concepts that never translate into operational capabilities. The structured TRL approach helps organizations navigate this valley by forcing explicit consideration of non-technical risks including market uncertainty, regulatory requirements, operational integration, and business model viability [28].
From Reactive to Proactive: A Maturity Model
Traditional digital forensics is predominantly reactive, initiating evidence collection after an incident has been detected. This approach often results in lost evidence, prolonged investigation times, and higher costs [31]. In contrast, proactive digital forensics embeds evidence collection capabilities into the IT infrastructure before incidents occur, enabling faster, more effective investigations and stronger cyber resilience [31] [33].
The relationship between proactive capabilities and maturity levels can be visualized as a progression from completely reactive to fully proactive operations. The following diagram illustrates this maturity pathway and its alignment with the TRL framework:
The transition across this maturity model requires systematic implementation of proactive capabilities. Research indicates that organizations implementing proactive forensic readiness frameworks can achieve significant operational improvements, including a 37.5% reduction in investigation time (from 4.0 to 2.5 hours) and a 19% improvement in log completeness (from 76% to 95%) [33].
Application Notes: Implementing a Proactive Forensic Readiness Framework
Core Principles and Strategic Alignment
Implementing a proactive digital forensic readiness framework requires foundationally aligning forensic capabilities with organizational risks and business objectives. The process begins not with tool acquisition, but with risk management – identifying what requires protection and where potential evidence resides [31]. For research organizations, this particularly involves protecting intellectual property, clinical trial data, and critical research infrastructure.
The forensic readiness implementation process should follow a structured, phased approach that systematically links business risks to technical evidence sources. The following workflow outlines this evidence mapping process:
This risk-based approach ensures forensic capabilities directly address the most critical business protection needs. For each identified risk scenario, organizations should define specific evidence requirements including file types, retention periods, metadata preservation needs, and supporting forensic documentation such as chain of custody procedures [31].
Experimental Protocol: Proactive Digital Forensics Implementation
The following detailed protocol provides a methodology for implementing and validating a Proactive Digital Forensics Standard Operating Procedure (P-DEFSOP), adapted from research demonstrating measurable improvements in forensic effectiveness [33].
Protocol Title: Implementation and Validation of a Proactive Digital Forensics Framework (P-DEFSOP)
Objective: To establish a proactive forensic capability that reduces investigation time, improves evidence completeness, and enables more effective incident response.
Materials & Requirements:
- IT infrastructure supporting critical business services
- Security Information and Event Management (SIEM) or similar log aggregation platform
- Forensic analysis workstations with appropriate tools
- Documented risk inventory and IT asset inventory
Procedure:
Forensic Readiness Assessment (Weeks 1-2)
- Conduct a gap analysis of current forensic capabilities against ISO 27037 guidelines for digital evidence handling [31].
- Map critical risks to business services, IT assets, and potential evidence sources using the workflow outlined in Section 4.1.
- Identify and document evidence sources for high-priority risks, including log files, endpoint telemetry, cloud audit logs, and backups [31].
Control Implementation & Configuration (Weeks 3-6)
- Implement or enhance logging configurations based on identified evidence requirements, focusing on completeness and integrity.
- Configure automated log collection to secure, centralized storage with appropriate access controls.
- Establish evidence handling policies addressing collection methods, preservation techniques, and chain of custody requirements [31].
- Define and document escalation criteria linking forensic monitoring to incident response procedures.
Testing & Validation (Weeks 7-10)
- Design red team/blue team simulation scenarios targeting high-risk areas identified in the risk assessment.
- Execute simulation exercises, capturing metrics for both the existing (reactive) process and the new P-DEFSOP framework.
- Measure and compare key performance indicators including:
- Log completeness rate (percentage of relevant events captured)
- Investigation time (time to reconstruct attack sequences and identify root cause)
- Evidence quality (ability to map events to adversarial tactics using frameworks like MITRE ATT&CK)
Training & Integration (Weeks 11-12)
- Conduct training for relevant staff on forensic preservation procedures and incident awareness.
- Integrate P-DEFSOP with existing security operations and incident response plans.
- Establish a continuous improvement process for refining forensic capabilities based on lessons learned from testing and actual incidents.
Validation Metrics: Successful implementation should demonstrate measurable improvements in forensic effectiveness. Comparative results from research implementations show the potential improvements achievable through this protocol:
Table 2: Quantitative Comparison of Reactive vs. Proactive Forensic Approaches
| Evaluation Metric | Reactive Model (Without P-DEFSOP) | Proactive Model (With P-DEFSOP) | Improvement |
|---|---|---|---|
| Log Completeness Rate | 76% | 95% | +19% |
| Missing/Corrupted Log Rate | 24% | 5% | -19% |
| Average Investigation Time | 4.0 hours | 2.5 hours | -37.5% |
| Evidence Mapping to ATT&CK | Fragmented, inconsistent | Systematic, comprehensive | Significant clarity improvement |
The Scientist's Toolkit: Essential Digital Forensic Research Reagents
Building and maintaining proactive digital forensic capabilities requires specific technical resources and frameworks. The following table details essential "research reagents" for digital forensic readiness:
Table 3: Essential Research Reagents for Digital Forensic Readiness
| Tool/Category | Function & Purpose | Implementation Example |
|---|---|---|
| Configuration Management Database (CMDB) | Provides dynamic inventory of IT assets, enabling linkage between business services and evidence sources [31]. | ServiceNow CMDB; custom asset management system. |
| Security Information & Event Management (SIEM) | Centralizes log collection and storage; enables proactive monitoring and automated alerting. | Splunk Enterprise Security; Elastic Security; Microsoft Sentinel. |
| Digital Forensic Frameworks | Provides standardized methodologies for evidence handling, ensuring legal admissibility. | ISO 27037 (Evidence Handling) [31]; ACPO Principles [34]. |
| MITRE ATT&CK Framework | Knowledge base of adversary behaviors; enables mapping of forensic artifacts to attack techniques. | Mapping log events to specific ATT&CK tactics and techniques [33]. |
| Timeline Reconstruction Tools | Enables forensic examiners to infer past activities by analyzing digital artifacts chronologically [32]. | Log2timeline/Plaso; custom event correlation scripts. |
| Evidence Preservation Tools | Creates forensically sound copies of digital evidence while maintaining integrity and chain of custody. | Forensic disk imagers (FTK Imager, Guymager); write blockers. |
| Open-Source Knowledge Bases | Community-driven resources documenting forensic techniques, weaknesses, and mitigations. | SOLVE-IT Digital Forensics Knowledge Base [34]. |
Digital forensic readiness is no longer a specialized IT function but a fundamental component of organizational resilience, particularly for research-driven industries where evidence integrity is paramount. By applying the structured, gated approach of Technology Readiness Levels, organizations can systematically evolve their capabilities from basic reactive measures to sophisticated proactive systems. This maturation process transforms digital forensics from an investigative tool used after incidents occur to an integrated business capability that reduces operational risk, supports regulatory compliance, and protects critical intellectual property. The quantitative improvements demonstrated in research – including nearly 40% faster investigations and significantly more complete evidence – provide compelling evidence for investing in this proactive approach [33].
A Step-by-Step Framework for Implementing TRLs in Digital Forensic Operations
The digital forensics field faces an unprecedented evolution, driven by the proliferation of digital devices, cloud computing, artificial intelligence (AI), and the Internet of Things (IoT). According to Grand View Research (2023), the global digital forensics market is projected to reach $18.2 billion by 2030, with a compound annual growth rate of 12.2% [10]. This rapid expansion necessitates a structured framework for assessing technological maturity from conceptualization to operational deployment. Technology Readiness Levels (TRLs), a measurement system originally developed by NASA in the 1970s, provide a standardized methodology for evaluating the maturity level of a particular technology [1] [28]. For digital forensics researchers and practitioners, the TRL framework offers a common language for tracking development progress, managing risk, and making strategic decisions about technology funding and deployment [35].
This application note establishes a comprehensive mapping of contemporary digital forensic technologies to the nine TRL stages, with particular emphasis on the critical "Valley of Death" (TRLs 4-7) where many innovations fail to mature [28]. By providing explicit experimental protocols and validation criteria for each stage, this framework supports the broader thesis that systematic technology readiness assessment is essential for advancing digital forensic readiness in an era of increasingly complex cyber threats.
Technology Readiness Levels comprise a nine-level scale that enables consistent comparison of technological maturity across different types of innovation. Table 1 summarizes the core definition and purpose of each TRL, adapted for the digital forensics context.
Table 1: Technology Readiness Levels (TRLs) - Definitions and Digital Forensics Context
| TRL | Definition | Focus in Digital Forensics | Typical Funding Sources |
|---|---|---|---|
| TRL 1 | Basic principles observed and reported [1] | Fundamental research on binary data analysis, data structure theory, cryptographic principles | Basic research grants, academic funding [35] |
| TRL 2 | Technology concept formulated [28] | Application of principles to forensic challenges; invention of novel acquisition/analysis concepts | Early-stage research grants [35] |
| TRL 3 | Experimental proof of concept [1] | Validation of feasibility through laboratory experiments; initial prototype development | SBIR/STTR Phase I, proof-of-concept grants [35] [28] |
| TRL 4 | Technology validated in lab environment [1] | Component integration and testing in controlled forensic laboratory conditions | SBIR/STTR Phase II, seed funding [35] |
| TRL 5 | Technology validated in relevant environment [1] | Testing in simulated forensic environment with real-world data sets | SBIR/STTR Phase II, venture capital seed rounds [35] |
| TRL 6 | Technology demonstrated in relevant environment [1] | Full prototype testing in operational forensic laboratory setting | Later-stage venture capital, strategic partnerships [35] |
| TRL 7 | System prototype demonstration in operational environment [1] | Field testing in active investigative contexts with real casework | Venture capital, corporate investment [35] [28] |
| TRL 8 | System complete and qualified [1] | Technology integrated into standard forensic workflows; compliance testing | Corporate venture arms, government procurement [35] |
| TRL 9 | Actual system proven in operational environment [1] | Routine deployment in forensic investigations; established evidentiary reliability | Commercial revenue, government procurement [35] |
The progression from TRL 1 to TRL 9 represents a pathway from basic scientific observation to proven operational capability. For digital forensics technologies, this pathway must address not only technical functionality but also legal admissibility, ethical implementation, and integration with established investigative workflows [36] [37].
Figure 1: Technology Readiness Pathway for Digital Forensics, highlighting the critical "Valley of Death" (TRLs 4-7) where many innovations fail to transition to operational use [28].
Digital Forensics Technology Landscape
The contemporary digital forensics field encompasses a diverse technological landscape addressing multiple evidence sources and analytical approaches. Table 2 maps current digital forensic technologies to their approximate TRL levels, demonstrating the varied maturity across different subdomains.
Table 2: Current Digital Forensics Technologies Mapped to TRL Levels
| Technology Category | Example Technologies | Current TRL | Key Challenges | Primary Applications |
|---|---|---|---|---|
| AI-Powered Evidence Triage | Machine learning for log analysis, NLP for communication review [13] | 7-8 | Algorithmic bias, "black box" models undermining court credibility [10] | Large-scale data analysis, pattern recognition [13] |
| Cloud Forensics | API-based data acquisition, cross-platform evidence correlation [13] | 6-7 | Data fragmentation, jurisdictional conflicts, encryption [10] [13] | Investigation of cloud-based evidence distributed across servers [10] |
| IoT Device Forensics | Vehicle infotainment analysis, smart home device data extraction [10] [13] | 5-7 | Proprietary protocols, volatile data, diverse architectures [10] | Collision reconstruction (e.g., Tesla EDR data), smart home investigations [10] |
| Blockchain Forensics | Cryptocurrency transaction tracking, wallet identification [38] | 7-8 | Privacy coins, mixing services, cross-chain transactions | Money laundering investigation, ransomware payment tracking [38] |
| Deepfake Detection | AI-driven media authentication, neural network analysis [39] | 6-7 | Rapidly evolving generation techniques, quality improvements [39] | Authentication of audio/video evidence, combating disinformation [39] |
| Anti-Forensic Detection | Metadata analysis for tampering detection, steganography detection [13] | 7-8 | Increasing sophistication of data hiding techniques [13] | Identification of evidence tampering, recovery of hidden data [13] |
| Mobile Forensics | Advanced logical/physical extraction, cloud data acquisition [13] | 9 | Device encryption, secure boot processes, hardware security [13] | Ubiquitous in criminal investigations, corporate investigations [13] |
The TRL distribution in Table 2 demonstrates that while some digital forensic technologies have reached operational maturity (TRL 9), others remain in development and validation phases, particularly those addressing emerging technologies and complex anti-forensic techniques.
TRL-Specific Application Notes and Protocols
TRL 1-3: Basic Research to Proof of Concept
The initial TRL stages focus on establishing fundamental understanding and demonstrating feasibility through controlled experimentation.
TRL 1-2 Application Notes: At these stages, research focuses on observing fundamental principles and formulating technology concepts. Recent work has included studying the fundamental properties of generative adversarial networks (GANs) to understand deepfake generation patterns and conceptualizing detection methodologies [10]. Research into blockchain transaction patterns has enabled the formulation of concepts for tracking cryptocurrency movements across distributed ledgers [38].
TRL 3 Experimental Protocol: Deepfake Detection Proof of Concept
Objective: To validate the core hypothesis that AI-generated media contains detectable artifacts through experimental proof of concept.
Materials and Reagents:
- Dataset Curation: Collect 1,000 verified authentic videos and 1,000 AI-generated videos using open-source generation tools
- Computational Environment: High-performance workstation with GPU acceleration (minimum 8GB VRAM)
- Analysis Framework: Python with OpenCV, TensorFlow, and customized feature extraction libraries
Methodology: 1. Feature Extraction: Implement algorithms to extract potential artifact signatures from visual and audio streams, focusing on: - Facial micro-expressions and blink rate analysis - Blood flow patterns via subtle color variations - Audio-visual synchronization metrics - Compression artifact consistency 2. Model Development: Train basic machine learning classifiers (SVMs, Random Forests) on extracted features 3. Validation: Use k-fold cross-validation (k=5) to assess detection accuracy
Success Criteria: Statistical significance (p<0.05) in distinguishing authentic from synthetic media with accuracy exceeding 65% (significantly above random chance).
TRL 4-5: Laboratory to Relevant Environment Validation
These intermediate stages bridge the gap between theoretical concepts and practical applications, typically where the "Valley of Death" begins.
TRL 4 Application Notes: Technologies are validated in laboratory environments that simulate real-world conditions. For example, cloud forensic tools are tested with localized private cloud deployments that replicate major cloud service architectures [13]. IoT forensic methodologies are validated using controlled smart home test environments with representative device combinations [10].
TRL 5 Experimental Protocol: Cloud Forensic Tool Validation
Objective: To validate cloud forensic acquisition tools in a relevant simulated environment.
Materials and Reagents:
- Test Environment: Private cloud deployment mirroring API structures of major providers (AWS, Azure, Google Cloud)
- Target Applications: Social media simulators with representative data structures
- Forensic Tools: Custom-developed API-based acquisition tools and commercial alternatives
Methodology:
- Evidence Seeding: Populate test environment with known data quantities (1TB structured and unstructured data)
- Acquisition Testing: Execute acquisition tools against simulated cloud environments with:
- Varying network conditions (latency, packet loss)
- Different authentication scenarios (OAuth, API keys)
- Rate limiting and other API restrictions
- Data Verification: Compare acquired data to seeded ground truth using hash verification and content analysis
Success Criteria: Acquisition of >95% of seeded data without alteration, with comprehensive metadata preservation and proper error handling for network disruptions.
TRL 6-7: Relevant to Operational Environment Demonstration
These stages involve testing fully functional prototypes in increasingly realistic environments, representing the latter portion of the "Valley of Death."
TRL 6 Application Notes: A fully functional prototype is demonstrated in a relevant environment. For example, a complete digital forensics workstation with integrated AI triage capabilities is tested in a representative laboratory using real (but anonymized) case data [13]. The prototype must demonstrate end-to-end functionality from acquisition to reporting.
TRL 7 Experimental Protocol: AI-Powered Evidence Triage Field Test
Objective: To demonstrate a system prototype in an operational environment with real investigators.
Materials and Reagents:
- Test Data: Anonymized historical case data from 10 previous investigations (5 criminal, 5 corporate)
- Hardware: Standard issue forensic workstations deployed to participating laboratories
- Software: AI triage system with natural language processing and pattern recognition capabilities
Methodology:
- Baseline Establishment: Have experienced investigators process test cases using existing tools, recording time and key findings
- Prototype Deployment: Install AI triage system in operational forensic laboratories
- Controlled Comparison: Have the same investigators process the same cases using the AI triage system
- Metrics Collection: Record:
- Time to identify key evidence
- Percentage of relevant evidence identified
- False positive/negative rates
- User satisfaction and workflow integration
Success Criteria: Statistically significant reduction in processing time (>25%) while maintaining or improving evidence identification rates compared to baseline methods.
TRL 8-9: System Completion to Operational Deployment
The final TRL stages represent the transition from prototype to fully operational technology.
TRL 8 Application Notes: The technology is finalized and qualified through rigorous testing. For digital forensics, this includes not only technical testing but also validation against legal standards for evidence admissibility [36] [37]. Technologies at this stage have completed integration with established forensic workflows and have all necessary documentation for operational use.
TRL 9 Application Notes: The technology has been proven through successful operational deployment. Examples include established mobile forensics tools that are routinely used in criminal investigations [13] and forensic write-blocking hardware that has been validated through years of use in evidentiary contexts. Technologies at TRL 9 are included in standard operating procedures and have established training programs.
The Digital Forensics Researcher's Toolkit
Table 3 details essential research reagents, tools, and platforms that support development and validation across TRL stages.
Table 3: Essential Research Reagents and Tools for Digital Forensics Technology Development
| Tool/Reagent Category | Specific Examples | Primary Function | TRL Application Range |
|---|---|---|---|
| Reference Data Sets | NIST CFRePP, GovDocs1, M57-Patrol, DARPA TCE | Provide standardized data for development and validation | TRL 1-7 |
| Forensic Acquisition Tools | FTK Imager, Belkasoft Evidence Center, Cellebrite UFED | Create forensic images of digital evidence | TRL 3-9 |
| Analysis Platforms | Belkasoft X, Autopsy, Exterro FTK, Griffeye Analyze DI | Enable examination and interpretation of digital evidence | TRL 4-9 |
| Specialized Hardware | Tableau write blockers, forensic workstations, mobile device programmers | Maintain evidence integrity and enable device access | TRL 4-9 |
| Validation Frameworks | NIST CFTT, ISO/IEC 27037, NIST OSDFT | Provide methodologies for tool validation and verification | TRL 4-8 |
| AI/ML Libraries | TensorFlow, PyTorch, Scikit-learn, OpenCV | Enable development of advanced analysis capabilities | TRL 1-7 |
| Blockchain Analysis Tools | Chainalysis Reactor, Elliptic Explorer, TRM Labs | Facilitate cryptocurrency transaction tracking | TRL 5-9 |
Figure 2: Digital Forensics Toolchain Workflow, illustrating the integration pathway for technologies across different TRL stages into an operational forensic process.
Validation Framework and Admissibility Considerations
For digital forensic technologies, progression beyond TRL 7 requires rigorous validation to ensure evidentiary reliability and admissibility in legal proceedings. The chain of custody documentation must be meticulously maintained throughout technology development and testing [36]. Technologies at TRL 8-9 must demonstrate not only technical efficacy but also compliance with legal standards such as the federal rules of evidence [36].
Validation protocols should address:
- Repeatability: Consistent results across multiple operators and environments
- Accuracy: Minimum error rates in evidence identification and analysis
- Integrity Preservation: Ability to maintain evidence without alteration
- Documentation: Comprehensive logging of all operations performed
- Error Handling: Appropriate responses to unexpected conditions or inputs
Technologies intended for use in legal proceedings should undergo validation following established frameworks such as NIST's Computer Forensic Tool Testing (CFTT) program or ISO/IEC 27037 guidelines for the identification, collection, acquisition, and preservation of digital evidence [37].
The systematic mapping of digital forensic technologies to TRL stages provides researchers and practitioners with a structured framework for technology development, assessment, and deployment. This application note establishes clear benchmarks for each TRL stage, with specific experimental protocols and validation criteria tailored to digital forensics applications. By adopting this structured approach, the digital forensics community can more effectively navigate the "Valley of Death" between research and operational deployment, accelerating the translation of innovative concepts into tools that enhance investigative capabilities while maintaining rigorous standards of evidentiary reliability.
This application note provides a structured framework for assessing the maturity of cloud forensics tools, with a specific focus on technologies designed to overcome the profound challenges of cross-jurisdictional data acquisition. As organizations increasingly migrate to multi-cloud environments, digital investigators face a complex landscape of technical and legal hurdles. The volatile nature of cloud data, coupled with disparate data sovereignty laws, creates a pressing need for standardized maturity assessment of forensic tools [40] [41]. This document frames these challenges within a Technology Readiness Level (TRL) context, providing researchers and development professionals with a common metric for evaluating tool maturity from basic principle observation (TRL 1) to full operational deployment (TRL 9) [2] [42].
The TRL framework, originally developed by NASA and since adopted by the European Union and other research bodies, offers a disciplined approach for assessing where a technology stands within the development lifecycle [2] [1]. By applying this proven scale to cloud forensics, this note establishes experimental protocols and assessment criteria essential for advancing tools from conceptual stages to validated solutions capable of functioning within the intricate legal and technical constraints of modern multi-cloud environments [41].
Technology Readiness Levels (TRL) – Background and Definitions
Technology Readiness Levels represent a systematic metric for measuring the maturity of a particular technology. The scale consists of nine levels, ranging from basic principles observed (TRL 1) to actual system proven in operational environment (TRL 9) [2]. Each level represents a stage in the technology development cycle, providing a clear pathway for research and development progression.
Table 1: Technology Readiness Level Definitions and Correlations
| TRL | NASA Definition [2] [1] | European Union Definition [2] | Academic/Research Context [42] |
|---|---|---|---|
| 1 | Basic principles observed and reported | Basic principles observed | Basic scientific research begins; properties observed and reported |
| 2 | Technology concept and/or application formulated | Technology concept formulated | Conceptual ideas formed; no experimental proof yet |
| 3 | Analytical and experimental critical function and/or characteristic proof-of-concept | Experimental proof of concept | Initial experiments validate concept; proof-of-concept model constructed |
| 4 | Component and/or breadboard validation in laboratory environment | Technology validated in lab | Components integrated and tested in lab conditions; laboratory prototype available |
| 5 | Component and/or breadboard validation in relevant environment | Technology validated in relevant environment | Technology tested in simulated real-world environment |
| 6 | System/subsystem model or prototype demonstration in a relevant environment | Technology demonstrated in relevant environment | Prototype demonstrated in relevant but not fully operational setting |
| 7 | System prototype demonstration in a space environment | System prototype demonstration in operational environment | Near-final system tested in actual operational conditions |
| 8 | Actual system completed and "flight qualified" through test and demonstration | System complete and qualified | Final system completed and meets all specifications |
| 9 | Actual system "flight proven" through successful mission operations | Actual system proven in operational environment | Technology in use and proven in real-world operations |
The TRL framework provides management with a consistent metric for technology maturity assessment, facilitating decision-making concerning development progress and transition timing [2]. For cloud forensics tools, this translates to a clear pathway from basic research on data acquisition methods to fully validated systems capable of operating across jurisdictional boundaries while maintaining evidence integrity.
Cloud Forensics Challenges and Technical Requirements
Fundamental Challenges in Cloud Forensics
Cloud forensics presents a distinct set of challenges that differentiate it from traditional digital forensics and create complex requirements for tool development. These challenges manifest across technical, legal, and organizational dimensions, each introducing specific constraints that tools must overcome to achieve higher TRL ratings.
Table 2: Key Cloud Forensics Challenges and Tool Implications
| Challenge Category | Specific Challenges | Impact on Tool Development Requirements |
|---|---|---|
| Technical Challenges | Data volatility and ephemeral nature [40] | Tools require real-time evidence collection capabilities before data disappears |
| Data distribution across multiple virtual environments [40] | Tools must aggregate evidence from disparate sources and locations | |
| Multi-tenancy and shared resources [40] | Tools need precise data isolation capabilities to avoid privacy violations | |
| Encryption and access controls [40] [43] | Tools require lawful decryption capabilities or key management integration | |
| Legal & Jurisdictional Challenges | Cross-border data storage [40] [41] | Tools must incorporate jurisdictional awareness and compliance checking |
| Varying data protection laws [40] [44] | Tools need configurable policy enforcement based on data origin and location | |
| Differing law enforcement access protocols [43] | Tools should streamline legal request generation for multiple jurisdictions | |
| Organizational Challenges | Lack of standardized policies [40] | Tools must be adaptable to varying organizational and provider policies |
| Coordination with Cloud Service Providers [40] [44] | Tools require standardized APIs for provider integration | |
| Skills and expertise gaps [40] | Tools need intuitive interfaces that guide proper forensic procedures |
Cross-Jurisdictional Data Acquisition Complexities
Cross-jurisdictional data acquisition represents one of the most significant challenges in cloud forensics, often determining the success or failure of an investigation. Cloud service providers frequently operate globally, with data stored across multiple countries, each with distinct legal frameworks governing data access and privacy [40]. This creates a complex patchwork of requirements that tools must navigate, including:
- Data Sovereignty Conflicts: Laws requiring data to be stored within national borders may conflict with investigation requirements [40] [43].
- Mutual Legal Assistance Treaty (MLAT) Delays: Traditional legal channels for cross-border data requests can take months or years, during which evidence may be lost [43].
- Inconsistent Admissibility Standards: Courts in different jurisdictions apply varying standards for digital evidence admissibility [43].
- Provider-Specific Access Policies: Each cloud provider implements different procedures for law enforcement data requests [43].
These challenges collectively define the operational environment that cloud forensics tools must successfully navigate to achieve higher TRL ratings, particularly as they progress from laboratory validation (TRL 4) to relevant environment testing (TRL 5-6) and ultimately operational deployment (TRL 7-9).
TRL Application Framework for Cloud Forensics Tools
TRL Assessment Criteria for Cloud Forensics
Applying TRLs to cloud forensics tools requires tailoring the general technology readiness framework to address domain-specific capabilities. The assessment must evaluate both technical functionality and legal/operational compliance, with increasing rigor as tools advance through higher TRL levels.
Table 3: Cloud Forensics Tool TRL Assessment Criteria
| TRL | Technology Scope | Validation Environment | Cross-Jurisdictional Capabilities | Evidence Integrity Requirements |
|---|---|---|---|---|
| 1-2 | Basic data acquisition principles observed; application concepts formulated | Research environment | Understanding of jurisdictional issues documented | Theoretical framework for integrity preservation |
| 3 | Proof-of-concept for isolated data acquisition functions | Laboratory setting with single cloud platform | Identification of relevant legal frameworks | Basic hashing implementation for evidence verification |
| 4 | Integrated components working ad-hoc for data collection | Controlled lab with multiple cloud services | Simulation of basic jurisdictional compliance checks | Chain of custody documentation within single jurisdiction |
| 5 | Breadboard system validating complete acquisition workflow | Simulated multi-jurisdictional cloud environment | Testing against representative legal requirements from 2-3 jurisdictions | Integrity verification across data transmission between systems |
| 6 | Prototype system representing near-final configuration | Pilot deployment with real cloud providers | Operational with actual provider APIs and legal request processes | End-to-end integrity protection with admissible chain of custody |
| 7 | System prototype demonstration in operational environment | Field testing with law enforcement agencies | Handling actual cross-border requests with proper legal authority | Court-validated integrity measures across multiple cases |
| 8-9 | Complete system qualified and proven through successful operations | Multiple operational deployments across different organizations | Streamlined cross-jurisdictional processing with established legal precedent | Proven evidence integrity across diverse legal systems |
Experimental Protocols for TRL Advancement
Advancing cloud forensics tools through TRL stages requires structured experimental protocols that systematically increase complexity and real-world relevance. The following protocols provide methodologies for key transition points in the technology development cycle.
Protocol for TRL 3 to TRL 4 Transition: Laboratory Validation
Objective: Transition from proof-of-concept to laboratory-validated components integrated into an ad-hoc system.
Materials:
- Cloud service provider development sandboxes (AWS, Azure, GCP)
- Forensic workstation with write-blocking capabilities
- Evidence storage system with cryptographic hashing (SHA-256, MD5)
- Network monitoring tools (Wireshark, specialized forensic tools)
Methodology:
- Configure isolated laboratory environment representing single cloud architecture
- Implement basic data acquisition components for:
- Integrate components using ad-hoc integration methods
- Validate integration by:
- Acquiring data from multiple services within single provider
- Verifying data integrity through hash value maintenance [45]
- Documenting chain of custody through automated logging
- Measure success by:
- Data completeness (≥95% of target data acquired)
- Integrity maintenance (hash verification throughout process)
- Basic functionality in controlled environment
Success Criteria: Integrated components function together to acquire cloud evidence while maintaining integrity in laboratory setting.
Protocol for TRL 4 to TRL 5 Transition: Relevant Environment Testing
Objective: Validate technology in simulated real-world environment with relevant operational constraints.
Materials:
- Multi-cloud test environment (at least 2 different providers)
- Simulated legal constraints from different jurisdictions
- Specialized cloud forensics tools (Oxygen Forensic Detective, Magnet Axiom) [43] [45]
- Blockchain-based evidence logging system (experimental) [43] [45]
Methodology:
- Establish relevant environment simulating real-world conditions:
- Data distributed across multiple providers and regions
- Implementation of encryption-at-rest and in-transit
- Multi-tenant architecture with segregation requirements
- Deploy technology in simulated investigative scenario:
- Execute cross-provider data acquisition
- Apply jurisdictional rules for data handling
- Implement appropriate legal authority simulation (warrants, subpoenas)
- Validate performance by:
- Measuring acquisition time against data volatility windows
- Testing integrity preservation across jurisdictional boundaries
- Verifying compliance with simulated legal requirements
- Assess scalability with increasing data volumes (1GB to 1TB range)
Success Criteria: Technology performs core functions in simulated environment that closely approximates real operational conditions with multiple jurisdictions and providers.
Protocol for TRL 6 to TRL 7 Transition: Operational Environment Demonstration
Objective: Demonstrate prototype system in actual operational environment with real casework.
Materials:
- Production cloud environments with legal access authority
- Full chain of custody documentation system
- Court-admissible evidence processing workflow
- Integration with law enforcement incident response protocols
Methodology:
- Deploy system in operational environment with actual investigations
- Execute complete forensic processes:
- Legal authority establishment for cross-jurisdictional acquisition
- Coordination with cloud service provider legal teams [43]
- Data acquisition from distributed cloud infrastructure
- Evidence preservation adhering to jurisdictional requirements
- Analysis and reporting suitable for legal proceedings
- Monitor and measure:
- Legal compliance across all jurisdictions involved
- Evidence admissibility in subsequent proceedings
- System reliability under operational pressures
- Integration with existing investigative workflows
- Document any operational limitations or required workarounds
Success Criteria: System successfully supports actual investigations with evidence maintained to admissible standards across multiple jurisdictions.
Visualization of TRL Progression for Cloud Forensics
The following diagrams illustrate key workflows and relationships in the TRL assessment process for cloud forensics tools, particularly focusing on cross-jurisdictional data acquisition capabilities.
TRL Assessment Workflow
Cross-Jurisdictional Data Acquisition Process
The Scientist's Toolkit: Research Reagent Solutions
Advancing cloud forensics tools through TRL stages requires specialized tools, platforms, and methodologies. The following table details essential "research reagents" for developing and validating cloud forensics capabilities.
Table 4: Essential Research Reagents for Cloud Forensics Tool Development
| Tool/Category | Example Solutions | Primary Function | TRL Applicability |
|---|---|---|---|
| Cloud Provider APIs | AWS CloudTrail, Azure Log Analytics, GCP Operations API | Data access and log collection from cloud services | TRL 3-9 (Foundation for all acquisition) |
| Forensic Platforms | Oxygen Forensic Detective, Magnet Axiom, Cellebrite UFED [43] [45] | Integrated acquisition, analysis, and reporting | TRL 4-9 (Validation through deployment) |
| Evidence Integrity Tools | Hash algorithms (SHA-256, MD5), Write blockers, Blockchain ledgers [45] | Preserve evidence authenticity and prevent alteration | TRL 2-9 (Progressive implementation) |
| Legal Compliance Frameworks | ISO/IEC 27037, NIST SP 800-101, GDPR guidelines [45] | Ensure adherence to regulatory requirements | TRL 3-9 (Increasing complexity) |
| Test Environments | Provider sandboxes, Multi-cloud simulators, Isolated labs | Controlled validation environments | TRL 3-7 (Foundation for advancement) |
| Automation & AI | Machine learning classifiers, Natural language processing, Anomaly detection | Analyze large datasets and identify evidence | TRL 2-8 (Emerging capability) |
This application note establishes a structured framework for applying Technology Readiness Levels to cloud forensics tools, with particular emphasis on overcoming cross-jurisdictional data acquisition challenges. By defining clear assessment criteria and experimental protocols for each TRL stage, the framework provides researchers and development professionals with a standardized approach for technology maturation assessment.
The progression from lower TRLs (basic research) to higher TRLs (operational deployment) requires increasingly sophisticated handling of the technical and legal complexities inherent in cloud environments. Successfully advancing through these stages demands rigorous validation against both functional requirements and jurisdictional compliance, with each stage building upon the previous to ensure technologies are truly ready for operational use in digital investigations.
As cloud technologies continue to evolve and jurisdictional boundaries become increasingly significant in digital investigations, the disciplined application of TRLs provides an essential mechanism for ensuring forensic tools meet the rigorous standards required for legal admissibility and technical reliability across international boundaries.
The integration of Artificial Intelligence (AI) and Machine Learning (ML) into digital forensics represents a paradigm shift, offering transformative potential for enhancing investigative efficiency and accuracy. This application note provides a structured framework for assessing the maturity of AI-powered forensic tools through the lens of Machine Learning Technology Readiness Levels (MLTRL). Drawing on recent peer-reviewed studies and industry implementations, we detail a proven pathway from fundamental research (MLTRL 0) to deployed operational systems (MLTRL 8). The document includes a quantitative analysis of AI performance in forensic image analysis, standardized experimental protocols for tool validation, and a visual workflow for the MLTRL process. This structured approach aims to equip researchers, developers, and policymakers with a common language and rigorous methodology to advance the development, validation, and responsible deployment of AI in digital forensics, thereby strengthening overall digital forensic readiness.
The digital forensic landscape is characterized by escalating data volumes and increasingly sophisticated cyber threats. Traditional forensic methods, while foundational, often struggle with the scale and complexity of modern digital evidence, leading to investigative backlogs [46] [47]. AI and ML technologies offer promising solutions through their capacity for automated pattern recognition, anomaly detection, and rapid analysis of large datasets [48] [49].
However, the development and deployment of AI systems can be rushed, leading to technical debt, model failures, and unforeseen consequences if not managed with diligence [50]. The ad-hoc integration of AI into forensic workflows, without rigorous validation, poses risks to evidentiary integrity and legal admissibility. Therefore, a disciplined, systems-engineering approach is paramount. The Technology Readiness Level (TRL) framework, a well-established systems engineering protocol, provides a disciplined way to differentiate between technology maturity levels [51]. Originally developed by NASA, it has been widely adopted across research and industry.
This case study adapts the Machine Learning Technology Readiness Level (MLTRL) framework [50] [52] to the specific requirements of digital forensics. We demonstrate its application through a recent pilot study on AI-based crime scene image analysis [46], provide detailed protocols for validation, and outline the essential toolkit for researchers. This structured approach ensures that AI forensic tools are not only technologically advanced but also robust, reliable, and responsible before they are integrated into critical investigative workflows.
The MLTRL Framework Adapted for Digital Forensics
The MLTRL framework defines a principled process for advancing ML and AI technologies from basic research to deployed systems. For digital forensics, this framework ensures that tools meet the stringent standards required for legal proceedings, including transparency, reliability, and fairness.
The table below summarizes the nine MLTRL stages as adapted for AI-based digital forensic tools.
Table 1: Machine Learning Technology Readiness Levels for Digital Forensic Tools
| MLTRL | Stage Name | Description & Key Activities in a Forensic Context | Key Forensic Deliverables |
|---|---|---|---|
| 0 | First Principles | Idea generation and literature review on a novel AI forensic application (e.g., new deepfake detection algorithm). Mathematical foundations are established. | Research proposal, initial literature review on both AI technique and forensic relevance. |
| 1 | Goal-Orientated Research | Low-level experiments on sample or synthetic data to analyze specific algorithm properties. Data readiness is assessed. | Report on initial findings, data availability, and early proof-of-concept code. |
| 2 | Proof of Principle (PoP) | R&D in simulated environments with benchmark datasets. Formal research requirements with verification & validation (V&V) steps are documented. | Research Requirements Document, PoP report, and initial ethics checklist. |
| 3 | System Development | Code is refactored for production. Focus on interoperability, reliability, unit testing, and documentation. Architecture for dataflow and interfaces is designed. | Well-architected codebase, unit tests, and technical design documentation. |
| 4 | Proof of Concept (PoC) | Application-driven development begins. The technology is tested on authentic and representative forensic data (e.g., real but anonymized disk images). | PoC report with quantitative performance metrics (e.g., accuracy, precision, recall) on relevant data. |
| 5 | ML Capability | The model is integrated into a broader software platform (e.g., as an API within a forensic suite). It is no longer a standalone model. | Demo or API endpoint accessible to other teams; integration test results. |
| 6 | Application Development | The full application is developed for deployment in a relevant forensic environment. Extensive testing for robustness and edge cases is conducted. | A shippable application, end-to-end validation report, and user documentation. |
| 7 | System Demonstration | The full system is demonstrated in a real operational environment (e.g., a live digital forensics lab). Feedback from forensic investigators is gathered. | Field test report, user feedback analysis, and updated standard operating procedures (SOPs). |
| 8 | System Complete | The AI tool is proven to work in its final form and is deployed into the target forensic platform. It is ready for full-scale operational use. | Deployed system, final validation report, and training materials for investigators. |
This framework provides a common nomenclature for cross-functional teams (researchers, developers, forensic examiners, legal experts) to collaborate effectively [50] [51]. The graduation between levels is marked by gated reviews, ensuring that ethical, legal, and functional requirements are met before further investment is made.
Case Study: AI in Forensic Image Analysis
A 2025 pilot study published in a peer-reviewed forensic science journal provides a concrete example of assessing AI tools at a mid-level MLTRL stage [46]. The study independently evaluated three general-purpose AI models (ChatGPT-4, Claude, and Gemini) for analyzing 30 crime scene images.
Quantitative Performance Analysis
The resulting AI-generated reports were rigorously assessed by ten forensic experts. The findings demonstrate the promising potential of AI as a decision support tool, while also highlighting key performance variations.
Table 2: Quantitative Results from AI Forensic Image Analysis Pilot Study [46]
| Performance Metric | Overall Findings | Variation by Crime Scene Type | Performance by AI Tool |
|---|---|---|---|
| Observation Accuracy | Demonstrated high accuracy in descriptive observations. | Homicide scenes: Average score of 7.8/10 [46]. | Performance varied, but all tools maintained the primacy of human expert judgment [46]. |
| Evidence Identification | Faced significant challenges in correctly identifying and interpreting evidence. | Arson scenes: Average score of 7.1/10 [46]. | Not explicitly detailed in the provided excerpt. |
| Primary Role | Serves as a rapid initial screening mechanism to assist, not replace, comprehensive expert analysis [46]. | Performance is context-specific, requiring careful implementation. | - |
| Key Benefit | Enhances efficiency in scenarios involving multiple evidence points or high-volume caseloads [46]. | - | - |
MLTRL Assessment of the Pilot Study
Based on the study's description, it can be positioned at MLTRL 4 (Proof of Concept) and approaching MLTRL 5 (ML Capability). The study used "real" crime scene images (authentic data) to generate quantitative evaluations, which is characteristic of MLTRL 4. The research also investigated "AI–human collaboration" frameworks, indicating a move towards integrating AI as a capability within a broader investigative system, a key aspect of MLTRL 5 [46] [50].
The study concluded that current AI tools function optimally as assistive technologies, a finding that underscores the importance of the MLTRL framework in managing expectations and guiding development toward effective human-AI collaboration [46].
Experimental Protocols for Validating AI Forensic Tools
To ensure the reliability and admissibility of evidence processed by AI tools, rigorous validation is required. The following protocol, inspired by the cited studies, provides a template for benchmarking an AI tool for multimedia forensics (e.g., image, video, or audio analysis).
Protocol: Benchmarking AI for Multimedia Evidence Analysis
1. Objective: To quantitatively evaluate the performance and robustness of an AI model designed to analyze and report on multimedia evidence.
2. Experimental Design:
- Type: Comparative analysis against expert human examiners and/or established ground truth.
- Controls: A set of multimedia files with previously verified and documented content (ground truth).
- Blinding: Expert assessors should be blinded to the source (AI vs. human) of the generated reports where feasible to reduce bias.
3. Materials & Dataset Curation:
- Dataset: A minimum of 100+ unique multimedia files (images/videos/audio) representing various forensic-relevant scenarios (e.g., different lighting conditions, compression levels, occlusions). The dataset should be split into training/validation/test sets.
- Ground Truth: Each file must be meticulously annotated by a panel of certified forensic experts. Annotations should include object labels, timestamps, transcriptions (for audio), and any other relevant metadata.
- AI Model: The AI tool under test (e.g., a custom CNN for object detection, an NLP model for report generation).
- Baseline: Existing commercial forensic tools or manual analysis methods for comparison.
- Hardware: Workstations with sufficient GPU power for model inference (e.g., NVIDIA RTX series).
4. Step-by-Step Procedure: 1. Model Training (if applicable): Train the AI model on the designated training set. Use the validation set for hyperparameter tuning. 2. Inference & Report Generation: Present the held-out test set of multimedia files to the AI model. The model will process each file and generate an analysis report (e.g., listing detected objects, individuals, activities). 3. Expert Analysis: The same test set is analyzed by a control group of human forensic experts who generate their own reports. 4. Data Collection: Collect all AI-generated and human-generated reports. Anonymize them for blinding. 5. Expert Assessment: A separate panel of assessors (forensic experts) evaluates all reports against the established ground truth. They score each report using a standardized rubric (see Metrics). 6. Statistical Analysis: Perform statistical tests (e.g., t-tests, ANOVA) to compare the performance metrics of the AI tool against the baseline and human performance.
5. Key Metrics:
- Accuracy & Precision: Percentage of correct identifications and consistency of results.
- Recall: Ability to identify all relevant elements (minimizing false negatives).
- False Positive/Negative Rate: Critical for assessing the risk of missing evidence or misidentifying artifacts.
- Processing Time: Speed of analysis compared to manual methods.
- Robustness: Performance degradation when analyzing low-quality or manipulated media (e.g., deepfakes).
The Scientist's Toolkit: Essential Research Reagents & Materials
Developing and validating AI forensic tools requires a suite of specialized software, data, and hardware. The following table details key components of the research toolkit.
Table 3: Essential Research Toolkit for AI Forensic Tool Development
| Tool Category | Specific Examples | Function & Application in AI Forensic Research |
|---|---|---|
| Specialized Forensic Software | EnCase [46], FTK (Forensic Toolkit) [46], Amped FIVE [46] | Used for evidence acquisition, preservation, and as a baseline for comparing the performance of new AI tools. Provides court-validated workflows. |
| Data Curation & Annotation Tools | LabelImg, VGG Image Annotator, Prodigy | Create high-quality, labeled datasets for training and testing supervised ML models. Critical for establishing reliable ground truth. |
| ML/Deep Learning Frameworks | TensorFlow, PyTorch, Scikit-learn | Core libraries for building, training, and testing AI models for tasks like classification, object detection, and anomaly detection. |
| Benchmark Datasets | NIST Forensics Dataset, COCO, custom-curated organizational datasets | Provide standardized, often pre-annotated data for model training and for comparative benchmarking against other published research. |
| Model Evaluation & Explainability Libraries | MLflow, Weights & Biases, SHAP, LIME | Track experiments, monitor performance metrics, and interpret model decisions. Vital for debugging and for demonstrating transparency in court. |
| Hardware Accelerators | NVIDIA GPUs (e.g., A100, RTX 4090), Google TPUs | Significantly speed up the training and inference of complex deep learning models, reducing development cycle times. |
The implementation of the MLTRL framework provides a critical roadmap for navigating the complex journey of developing AI and ML tools for digital forensics. By adhering to this structured approach, researchers and developers can systematically advance from theoretical concepts to court-admissible solutions, ensuring technical robustness, forensic validity, and ethical responsibility at each stage.
Future work must focus on several key areas to further mature the field. Firstly, the development of standardized validation frameworks and benchmark datasets specific to forensic AI is essential to ensure consistency and reliability across studies [46]. Secondly, addressing the "black box" nature of many AI models through enhanced explainable AI (XAI) techniques is crucial for maintaining transparency and upholding legal standards of evidence [46] [48]. Finally, the establishment of robust ethical guidelines and legal standards governing the use of AI in criminal justice will be fundamental to building trust and ensuring the fair and just application of these powerful technologies [46] [49]. The MLTRL framework, as detailed in this application note, provides the foundational structure upon which these future advancements can be built.
Developing TRL Assessment Protocols for Digital Evidence Management Systems (DEMS)
Digital Evidence Management Systems (DEMS) are platforms designed to collect, store, organize, manage, and securely share digital evidence throughout the lifecycle of a legal case or investigation [53]. The effective operation of these systems is critical for modern law enforcement and judicial processes, as digital evidence plays a role in nearly 90% of criminal cases [54]. The challenges facing digital forensics and evidence management in 2025 are substantial, characterized by an explosion in the volume, variety, and velocity of digital evidence [55] [56]. Additional complexities arise from the need to maintain a secure chain of custody, ensure data security against cyber threats, comply with evolving legal standards, and enable interoperability across agencies [55] [57].
The Technology Readiness Level (TRL) scale is a methodological tool developed by NASA to assess the maturity of a particular technology. It is a nine-level scale, with TRL 1 being the lowest (basic principles observed) and TRL 9 being the highest (actual system proven in successful operational deployment) [1] [58]. This scale provides a disciplined, standardized measurement for evaluating technology maturity and is widely used across government and industry for research and development management [28]. This document outlines application notes and protocols for adapting and applying the TRL scale to assess the maturity of DEMS technologies within digital forensic readiness research.
Technology Readiness Levels (TRL) Framework
The standard TRL scale provides a baseline for assessment. The following table details the standardized definitions and descriptions for each level [1] [28] [58].
Table 1: Standard Technology Readiness Levels (TRLs) and Descriptions
| TRL | Level Name | Description | Supporting Evidence |
|---|---|---|---|
| 1 | Basic Principles Observed and Reported | Lowest level of technology readiness. Scientific research begins translation into applied R&D. | Published research identifying technology's basic properties. |
| 2 | Technology Concept Formulated | Practical applications are invented based on observed principles. Applications are speculative. | Publications outlining the proposed application and supporting analysis. |
| 3 | Analytical & Experimental Proof of Concept | Active R&D is initiated. Analytical and laboratory studies validate analytical predictions. | Results of laboratory tests to measure parameters of interest. |
| 4 | Component Validation in Lab Environment | Basic technological components are integrated and tested in a laboratory. A "low-fidelity" prototype. | Results from testing laboratory-scale breadboard(s). |
| 5 | Component Validation in Relevant Environment | Fidelity increases. Components are integrated with realistic supporting elements for testing in a simulated environment. | Results from testing a breadboard system in a simulated operational environment. |
| 6 | System/Subsystem Model Demonstrated in Relevant Environment | A representative model or prototype is tested in a relevant environment. A major step up in demonstrated readiness. | Results from laboratory testing of a prototype near the desired configuration. |
| 7 | System Prototype Demonstration in Operational Environment | A system prototype is demonstrated in its intended operational environment (e.g., a pilot police district). | Results from testing a prototype system in an operational environment. |
| 8 | Actual System Completed and Qualified | The technology is proven to work in its final form and under expected conditions. | Results of testing the final system under the expected range of operational conditions. |
| 9 | Actual System Proven in Successful Mission Operations | The technology is used in its final form under full mission conditions. | Operational reports confirming successful, sustained use. |
TRL Assessment Protocol for DEMS
This protocol provides a detailed methodology for assessing the TRL of a specific DEMS. The process involves evaluating the system against a set of DEMS-specific criteria at each level.
DEMS-Specific TRL Assessment Criteria
The generic TRL scale must be contextualized with criteria relevant to DEMS functionalities. The assessment should focus on the system's capabilities in handling core digital evidence management challenges [55] [53] [54].
Table 2: DEMS-Specific Criteria for TRL Assessment
| TRL | Evidence Ingestion & Integration | Data Security & Integrity | Chain of Custody & Audit | Analysis, Sharing & Collaboration |
|---|---|---|---|---|
| 1-3 | Paper studies on data formats; concept for unified ingestion. | Research on encryption methods for evidence files. | Theoretical models for cryptographically hashed audit trails. | Concept for AI-powered analysis (e.g., object detection). |
| 4-5 | Lab integration of components for ingesting video, mobile data; basic metadata tagging. | Components tested with AES-256 encryption at rest; role-based access control in lab. | Lab-scale breadboard generates a basic, tamper-evident action log. | Lab test of speech-to-text transcription on controlled datasets. |
| 6-7 | Representative prototype ingests mixed formats (CCTV, bodycam) in simulated agency IT environment. | System prototype uses multi-factor authentication, encryption in simulated ops. Functional redaction tools. | Prototype demonstrates full, automated chain-of-custody tracking in operational pilot. | AI analysis (face detection) and secure, view-only sharing demonstrated in pilot. |
| 8-9 | Final system qualified, ingesting from all required sources; interoperable with other certified systems. | Security suite (encryption, MFA, monitoring) validated against CJIS/GDPR requirements. | System "flight qualified"; audit logs deemed court-admissible over long-term use. | AI/ML tools and cross-agency sharing workflows are proven in successful, ongoing operations. |
Experimental Protocol for TRL Validation
For each proposed TRL, specific validation experiments are required to provide objective evidence of maturity.
Table 3: Experimental Protocols for Key DEMS TRL Milestones
| Target TRL | Validation Experiment | Methodology | Success Criteria |
|---|---|---|---|
| TRL 4/5 | Lab & Relevant Environment Component Integration | 1. Integrate evidence ingestion modules for bodycam and mobile data extraction in a lab environment.2. Develop a working breadboard with integrated encryption and logging module.3. Test the breadboard in a simulated agency network with historical, anonymized data. | 1. Successful ingestion of 95% of test data without corruption.2. Automated generation of a SHA-256 hash for each file.3. System remains stable for 72 hours of continuous operation. |
| TRL 6/7 | Pilot Demonstration in Operational Environment | 1. Deploy a system prototype in a single police department or lab unit.2. Ingest live data from body-worn cameras and CCTV feeds for 30 days.3. Actively use AI redaction tools and secure sharing portals with prosecutors. | 1. System successfully processes >99% of incoming evidence without critical failure.2. Chain of custody logs are generated for 100% of user interactions.3. User feedback indicates functional performance meets >90% of operational needs. |
| TRL 8/9 | Final System Qualification & Operational Mission | 1. Conduct independent security penetration testing and CJIS compliance audit.2. Deploy the finalized system across multiple, disparate agencies.3. Monitor system performance and evidence admissibility in court over 12 months. | 1. System passes security audit with no critical vulnerabilities.2. Evidence managed by the system is successfully admitted in court without chain-of-custody challenges.3. System achieves 99.9% uptime and is fully integrated into standard operating procedures. |
The Scientist's Toolkit: Research Reagent Solutions
The following table details key "research reagents" – essential software, hardware, and data components required for the development and testing of DEMS technologies.
Table 4: Essential Research Reagents for DEMS Development and TRL Testing
| Item | Function in DEMS R&D | Example/Specification |
|---|---|---|
| Forensic Data Corpora | Provides standardized, realistic datasets for testing evidence ingestion, analysis, and indexing algorithms. | Anonymized datasets containing mixed formats: bodycam video, mobile device images, social media logs, and email archives. |
| CJIS-Compliant Cloud/On-Prem Infrastructure | Offers a secure, compliant hardware and networking foundation for developing and testing DEMS prototypes. | Infrastructure meeting the U.S. Criminal Justice Information Services (CJIS) Security Policy standards for access control and encryption. |
| AI/ML Model Training Suites | Enables the development and validation of intelligent DEMS features like automated redaction, object detection, and transcription. | Software platforms (e.g., TensorFlow, PyTorch) with curated libraries for computer vision and natural language processing tasks. |
| Chain of Custody & Hashing Libraries | Provides the core software components to build tamper-evident audit trails and verify evidence integrity. | Software Development Kits (SDKs) for implementing cryptographic hashing (e.g., SHA-256) and secure, timestamped logging. |
| Interoperability Testing Frameworks | Validates a DEMS's ability to exchange data and function with other case management and forensic tools. | A suite of test protocols and simulated endpoints based on standards like the National Information Exchange Model (NIEM). |
Workflow and Logical Pathway Visualization
The following diagram illustrates the high-level logical pathway for progressing a DEMS technology from low to high technology readiness, highlighting key decision gates and objectives.
DEMS TRL Progression and Gating Criteria
The following diagram details the specific experimental workflow for validating a DEMS at the critical TRL 6/7 stage, where a prototype is demonstrated in an operational environment.
TRL 6/7 Experimental Validation Workflow
The increasing sophistication of cyber threats necessitates a proactive and structured approach to digital forensic investigations. Technology Readiness Levels (TRLs) provide a systematic framework for measuring the maturity of developing technologies, originally pioneered by NASA and now widely adopted across government, industry, and research sectors [59]. Meanwhile, ISO/IEC 27037 provides international standards specifically for the identification, collection, acquisition, and preservation of digital evidence [60] [61]. Integrating these two frameworks creates a powerful methodology for building forensic readiness capabilities that are both technically mature and legally admissible. This integration is particularly crucial for organizations operating in complex digital environments, including cloud services, IoT ecosystems, and critical infrastructure, where the integrity of digital evidence can determine legal outcomes [62] [63].
The synergy between TRLs and ISO/IEC 27037 enables organizations to methodically advance their forensic capabilities from theoretical concepts to fully operational systems while maintaining compliance with international standards. This integrated approach ensures that as forensic technologies evolve, they remain grounded in the rigorous evidence handling procedures required for legal proceedings. For researchers and practitioners, this combination provides a clear pathway from research and development to court-admissible digital evidence handling, addressing both technical implementation and legal compliance considerations throughout the technology development lifecycle.
Theoretical Foundations and Framework Integration
Technology Readiness Levels (TRLs) in Context
Technology Readiness Levels represent a systematic measurement system that supports assessments of the maturity of a particular technology and provides a consistent comparison of maturity between different types of technology [59]. The TRL scale consists of nine distinct levels:
- TRL 1-3 (Basic Research to Proof of Concept): Encompass basic principles observation, technology concept formulation, and experimental proof of concept.
- TRL 4-6 (Technology Development to Prototyping): Include technology validation in laboratory environments and representative environments.
- TRL 7-9 (System Demonstration to Operational Deployment): Cover system prototype demonstration in operational environments, complete system qualification, and actual system proven in operational environment [59].
For digital forensic readiness, this framework enables organizations to objectively assess where their capabilities fall on the spectrum from conceptual research to fully operational systems.
ISO/IEC 27037 Digital Evidence Standards
ISO/IEC 27037:2012 provides specific guidelines for handling digital evidence, focusing on the identification, collection, acquisition, and preservation of potential digital evidence [60] [61]. The standard establishes four critical phases for digital evidence handling:
- Identification: Search, recognition, documentation, and collection of digital evidence based on priority, value, and volatility [60].
- Collection: Gathering relevant digital devices and data using forensically sound methods, including both static and live acquisition approaches [60].
- Acquisition: Creating duplicate copies of digital evidence without altering original data, typically through forensic imaging with write-blocking techniques [60].
- Preservation: Maintaining evidence integrity through chain of custody documentation and secure storage procedures [60].
This international standard ensures that digital evidence maintains its integrity from crime scene to courtroom, addressing the fundamental requirement for legal admissibility.
Conceptual Integration Framework
The integration of TRLs with ISO/IEC 27037 creates a unified model for developing forensic capabilities that are both technically robust and legally compliant. This integration operates on the principle that technology maturity and evidentiary standards must advance concurrently throughout the development lifecycle. The framework ensures that as forensic technologies progress through higher TRLs, they incorporate the standardized handling procedures required by ISO/IEC 27037, resulting in court-admissible digital evidence.
Table: Correlation Between TRL Stages and ISO/IEC 27037 Evidence Handling Priorities
| TRL Stage | Technology Focus | ISO/IEC 27037 Emphasis | Compliance Objective |
|---|---|---|---|
| TRL 1-3(Basic Research) | Basic principles, concept formulation, experimental proof of concept | Evidence type identification, theoretical handling protocols | Establish foundational knowledge of potential evidence sources |
| TRL 4-6(Technology Development) | Component validation, laboratory testing, prototype development | Collection methodology validation, acquisition tool testing | Develop standardized procedures for evidence acquisition |
| TRL 7-9(System Demonstration) | System prototyping, operational environment testing, deployment | Chain of custody implementation, preservation protocol validation | Ensure end-to-end evidence integrity in operational contexts |
Integrated TRL and ISO/IEC 27037 Implementation Protocol
Phase 1: Foundational Research (TRL 1-3)
Protocol 1.1: Digital Evidence Source Mapping
- Objective: Identify potential sources of digital evidence within the organizational infrastructure and determine their investigative value.
- Methodology:
- Conduct a comprehensive inventory of IT assets, including servers, network devices, cloud instances, and endpoints [31].
- Map business risks to specific digital evidence sources using a structured risk inventory process [31].
- Categorize evidence sources by volatility and priority using the guidelines established in ISO/IEC 27037 for evidence identification [60].
- Document potential evidence sources in a centralized configuration management database (CMDB) with forensic tagging capabilities [31].
Protocol 1.2: Basic Forensic Tool Evaluation
- Objective: Assess available forensic tools for their ability to maintain evidence integrity per ISO/IEC 27037 requirements.
- Methodology:
- Establish testing criteria based on ISO/IEC 27041 guidelines for tool assurance [61].
- Evaluate tools for ability to create verifiable forensic images using accepted hashing algorithms.
- Test write-blocking functionality and documentation capabilities.
- Validate tool output against known reference data sets to establish error rates.
Phase 2: Technology Development and Validation (TRL 4-6)
Protocol 2.1: Evidence Collection Mechanism Development
- Objective: Implement and validate technical mechanisms for automated evidence collection that maintain ISO/IEC 27037 compliance.
- Methodology:
- Deploy centralized logging solutions (SIEM) to collect and correlate evidentiary data [62] [64].
- Implement secure storage solutions with access controls for preserving collected evidence [64].
- Configure monitoring tools to detect suspicious activities while maintaining evidentiary integrity [64].
- Establish cryptographic hashing procedures to verify evidence integrity throughout collection process [60].
Protocol 2.2: Forensic Readiness Integration Testing
- Objective: Validate the integration of forensic capabilities with existing IT infrastructure and security controls.
- Methodology:
- Conduct controlled incident simulations to test evidence collection procedures [62].
- Verify chain of custody documentation meets legal requirements for admissibility.
- Test evidence preservation across heterogeneous environments (cloud, on-premises, hybrid).
- Validate forensic tool functionality in relevant operational environments.
Phase 3: Operational Implementation (TRL 7-9)
Protocol 3.1: Full-System Forensic Validation
- Objective: Demonstrate end-to-end forensic readiness in operational environments with complete ISO/IEC 27037 compliance.
- Methodology:
- Execute comprehensive incident response drills with actual evidence collection and preservation [62].
- Validate evidence handling procedures across complete lifecycle from identification to presentation.
- Test interoperability between forensic tools and existing security infrastructure.
- Verify adherence to legal standards for evidence admissibility (Daubert Standard, Federal Rule of Evidence 702) [65].
Protocol 3.2: Continuous Compliance Monitoring
- Objective: Establish ongoing monitoring and maintenance of forensic readiness capabilities.
- Methodology:
- Implement regular audits of forensic processes against ISO/IEC 27037 requirements [61].
- Conduct periodic tool validation following ISO/IEC 27041 guidelines [61].
- Update evidence handling procedures based on changes to legal standards or organizational infrastructure.
- Maintain staff competency through continuous training and skill development [62] [64].
Visualization of Integrated Workflows
TRL and ISO/IEC 27037 Integration Pathway
Digital Evidence Handling Workflow
Research Reagents and Tools for Forensic Readiness
The implementation of integrated TRL and ISO/IEC 27037 frameworks requires specific technical tools and methodological approaches. The following table details essential components for establishing standards-compliant forensic readiness capabilities.
Table: Essential Research Reagents and Tools for Forensic Readiness Implementation
| Tool/Category | Primary Function | ISO/IEC 27037 Alignment | TRL Application Range |
|---|---|---|---|
| SIEM Systems(e.g., Splunk, ArcSight) | Centralized log collection, correlation, and analysis | Supports evidence identification and collection through comprehensive monitoring | TRL 4-9 (Laboratory testing to operational deployment) |
| Forensic Imaging Tools(e.g., FTK Imager, EnCase) | Create bit-for-bit copies of digital evidence | Directly implements acquisition requirements through verified imaging | TRL 6-9 (Prototype demonstration to operational use) |
| Write Blockers(Hardware & Software) | Prevent modification of original evidence during acquisition | Ensures integrity during evidence acquisition as required by standard | TRL 7-9 (System demonstration to operational use) |
| Cryptographic Hashing Tools(e.g., SHA-256, SHA-3) | Verify integrity of digital evidence through hash values | Provides mechanism for evidence integrity verification | TRL 4-9 (Laboratory testing to operational deployment) |
| Chain of Custody Documentation Systems | Track evidence handling throughout investigation lifecycle | Implements preservation requirements through detailed documentation | TRL 5-9 (Technology validation to operational use) |
| Digital Forensic Workstations | Specialized hardware for evidence analysis and processing | Provides platform for compliant evidence examination and interpretation | TRL 6-9 (Prototype demonstration to operational use) |
| Evidence Storage Solutions | Secure preservation of digital evidence | Addresses preservation requirements through protected storage | TRL 5-9 (Technology validation to operational use) |
Quantitative Assessment Framework
TRL Assessment Criteria for Forensic Technologies
The progression through Technology Readiness Levels for forensic capabilities can be quantitatively measured using specific assessment criteria aligned with ISO/IEC 27037 requirements.
Table: TRL Assessment Metrics for Digital Forensic Readiness Capabilities
| TRL | Technology Demonstration Environment | ISO/IEC 27037 Compliance Metrics | Evidence Admissibility Threshold |
|---|---|---|---|
| 1-2 | Basic principles observed and formulated | Theoretical understanding of evidence requirements | Conceptual awareness of legal standards |
| 3-4 | Analytical and experimental proof of concept | Laboratory validation of evidence handling procedures | Development of foundational procedures |
| 5-6 | Component validation in relevant environment | Pilot implementation of collection and preservation | Procedure validation in simulated legal context |
| 7 | System prototype demonstration in operational environment | Full implementation of evidence handling chain | Successful mock trial demonstration |
| 8-9 | System complete and qualified through successful operations | Continuous compliance with all evidence standards | Established history of court admissibility |
Performance Metrics for Integrated Framework
Organizations implementing the integrated TRL and ISO/IEC 27037 framework should track specific performance indicators to measure implementation effectiveness.
Table: Key Performance Indicators for Integrated Forensic Readiness
| Performance Domain | Metric | Measurement Method | Target TRL 9 Performance |
|---|---|---|---|
| Evidence Integrity | Hash verification success rate | Percentage of successful hash validations during acquisition | ≥99.9% verification success |
| Collection Efficiency | Mean time to collect evidence | Time from incident identification to complete evidence collection | ≤2 hours for critical systems |
| Procedural Compliance | ISO/IEC 27037 adherence score | Audit-based assessment of standard implementation | ≥95% compliance with all controls |
| Legal Admissibility | Court acceptance rate | Percentage of evidence submissions accepted without challenge | ≥98% acceptance in legal proceedings |
| Investigation Impact | Business disruption index | Measure of operational impact during evidence collection | ≤15% performance degradation during collection |
The integration of Technology Readiness Levels with ISO/IEC 27037 creates a robust framework for developing digital forensic capabilities that are both technically mature and legally compliant. This integrated approach provides researchers and practitioners with a structured methodology for advancing forensic technologies from conceptual research to operational deployment while maintaining adherence to international standards for digital evidence handling. The protocols and assessment frameworks presented in this document offer practical guidance for implementing this integrated model across various organizational contexts.
For the research community, this integration opens several promising avenues for further investigation, including the development of TRL assessment criteria specific to emerging technologies such as IoT forensics, cloud environments, and blockchain analysis. Additionally, the continuous evolution of both technological landscapes and legal standards necessitates ongoing research into adaptive frameworks that can maintain the synergy between technical maturity and evidentiary requirements. By employing the integrated protocols and assessment tools outlined in these application notes, researchers can systematically advance the field of digital forensic readiness while ensuring the legal viability of their technological innovations.
Overcoming Implementation Challenges: From Technical Hurdles to Courtroom Compliance
This document provides a structured framework for forensic science researchers and laboratory professionals to identify, assess, and overcome common barriers to the implementation of Technology Readiness Levels (TRLs). By integrating TRLs with forensic science priorities, these protocols support the transition of novel technologies from validation to casework application.
Common TRL Implementation Barriers and Mitigation Strategies
Forensic laboratories face specific challenges when integrating new technologies, which can stall progress at various TRL stages. The table below summarizes these barriers and evidence-based mitigation strategies.
Table 1: TRL Implementation Barriers and Corresponding Mitigation Protocols
| Barrier Category | Specific Implementation Barrier | Proposed Mitigation Strategy | Relevant TRL Stage |
|---|---|---|---|
| Data & Technical Foundations [66] [65] | Lack of robust, impartial data to inform probabilities and validate methods. | Establish intra- and inter-laboratory validation studies; develop standardized databases accessible to the community [66] [65] [67]. | TRL 4-6 (Technology Validation) |
| Legal & Regulatory Adherence [65] | Method not meeting admissibility standards (e.g., Daubert, Frye, Mohan). | Early and continuous alignment of R&D with legal criteria: peer-reviewed publication, error rate analysis, and general acceptance [65]. | TRL 6-8 (System Demonstration) |
| Workforce & Skills [68] | Critical shortages in IT and data science talent; insufficient training on new technologies. | Invest in continuous professional development, reskilling programs (aim for >35% adequate training), and foster academia-practitioner partnerships [68] [67]. | All Stages (TRL 1-9) |
| Resources & Integration [68] | High complexity and failure rate (84%) in system integration projects; legacy system incompatibility. | Prioritize technologies with open standards and APIs; conduct pilot implementations with cost-benefit analyses before full-scale deployment [68] [67]. | TRL 7-9 (System Integration & Deployment) |
| Organizational Culture & Processes [66] [69] | Reticence toward new methodologies; regional differences in regulatory frameworks and workflows. | Develop evidence-based best practice guides; implement strong organizational quality systems and change management processes [66] [67] [69]. | All Stages (TRL 1-9) |
Experimental Protocol for TRL Assessment and Legal Readiness
This protocol provides a detailed methodology for advancing a technology from a validated prototype to a legally admissible tool, covering TRL 4 through 7.
Protocol Title: Integrated Technical and Legal Readiness Assessment for Novel Forensic Technology
1.0 Objective: To systematically evaluate a novel analytical technology's maturity and reliability, ensuring its readiness for implementation in forensic casework and its admissibility in legal proceedings.
2.0 Pre-Assessment Requirements:
- Technology: A technology that has undergone initial R&D and is a functional prototype (TRL 3-4). Example: Comprehensive two-dimensional gas chromatography-mass spectrometry (GC×GC–MS) for illicit drug analysis [65].
- Documentation: Preliminary standard operating procedure (SOP), initial validation data, and a literature review of similar applications.
3.0 Step-by-Step Procedure:
Step 3.1: Intra-Laboratory Validation (TRL 4).
- Action: Conduct a rigorous internal validation study.
- Methodology:
- Analyze a minimum of three replicates across a minimum of five concentration levels to establish linearity and dynamic range.
- Determine key performance metrics: Limit of Detection (LOD), Limit of Quantitation (LOQ), precision (repeatability and reproducibility), and accuracy using certified reference materials.
- Challenge the method with complex, forensically relevant matrices (e.g., seized drug mixtures, biological samples on fabric) to assess selectivity and robustness [65] [67].
- Deliverable: A comprehensive validation report with quantitative error rate analysis.
Step 3.2: Peer-Review and Publication (Aligning with Daubert).
- Action: Submit the validation study and methodology for independent peer review.
- Methodology: Prepare a manuscript detailing the technology's principles, methodology, validation data, and results. Submit to a reputable, peer-reviewed forensic science journal [65].
- Deliverable: A published, peer-reviewed article establishing "general acceptance" within the scientific community.
Step 3.3: Inter-Laboratory Validation (White-Box Study, TRL 5-6).
- Action: Coordinate a multi-laboratory study to identify sources of error and assess reproducibility.
- Methodology:
- Provide identical SOPs, training materials, and blinded test samples to a minimum of three independent laboratories.
- Design the study to measure both the accuracy of results and the human factors involved in operating the technology. This is a "white-box" study to understand decision-making processes [67].
- Deliverable: A statistical analysis report on inter-laboratory precision and a qualitative report on operational challenges and human factors.
Step 3.4: Development of Standardized Practices (TRL 6).
- Action: Draft a standard practice guide or propose a standard to a Standards Development Organization (SDO) like the ASTM International or the Academy Standards Board (ASB) [70].
- Methodology: Use data from Steps 3.1 and 3.3 to define best practices for evidence handling, analysis, interpretation, and reporting using the technology.
- Deliverable: A draft standard submitted to an SDO or an internal best practice recommendation.
Step 3.5: Pilot Implementation in a Mock Casework Setting (TRL 7).
- Action: Integrate the technology into a live laboratory environment for a pilot study.
- Methodology:
- Process a set of mock casework samples alongside current "gold standard" methods (e.g., traditional GC-MS).
- Evaluate not just analytical results, but also operational metrics: throughput, cost-per-sample, user-friendliness, and integration with Laboratory Information Management Systems (LIMS) [67].
- Deliverable: A cost-benefit and operational impact analysis report.
Workflow Diagram: TRL Progression with Legal & Technical Gates
The following diagram visualizes the integrated pathway for advancing forensic technologies, embedding critical legal and technical checkpoints.
Forensic TRL Progression with Key Gates
The Scientist's Toolkit: Essential Research Reagents & Materials
Successful TRL implementation relies on both physical materials and structured data resources. This table details key components for developing and validating forensic technologies.
Table 2: Essential Research Materials and Resources for Forensic Technology Development
| Item/Category | Function/Application in R&D | Implementation Context |
|---|---|---|
| Certified Reference Materials (CRMs) | Provides ground truth for method validation; essential for establishing accuracy, precision, and traceability. | Used in intra-laboratory validation (TRL 4) to determine key metrics like LOD, LOQ, and measurement uncertainty [67]. |
| Complex Mock Evidence Samples | Challenges the technology with forensically relevant, complex matrices to test selectivity and robustness. | Created in-house to simulate real casework (e.g., drug mixtures on currency, biological stains on fabric) during TRL 4-6 testing [65]. |
| Standardized Databases | Provides data for the statistical interpretation of evidence weight; supports objective, data-driven conclusions. | Developed and curated to be "accessible, searchable, and interoperable" as part of foundational research (TRL 2-4) and for ongoing casework (TRL 8-9) [67]. |
| Validation & Proficiency Test Kits | Allows for measurement of accuracy, reliability, and identification of sources of error via inter-laboratory studies. | Procured from commercial providers or developed collaboratively for use in white-box and black-box studies at TRL 5-6 [67]. |
| Forensic Data Integrity Tools | Ensures data integrity and chain of custody; critical for maintaining evidence admissibility in a digital environment. | Implemented as part of laboratory information management systems (LIMS), especially crucial for digital forensics and data management at higher TRLs (7-9) [69]. |
Digital forensics faces a critical challenge: the field is undergoing a fundamental paradigm shift from methods based on human perception and subjective judgement towards those grounded in relevant data, quantitative measurements, and statistical models [71]. This shift is essential to address the explosion in data complexity, characterized by high-volume, multi-format evidence from diverse sources such as mobile devices, Internet of Things (IoT) gadgets, and cloud storage [72] [73] [74]. This document outlines Application Notes and Protocols for applying Technology Readiness Levels (TRLs)—a systematic measurement system for assessing technology maturity—to digital forensic readiness research, providing a structured pathway from basic concept to court-ready implementation [51] [1].
Technology Readiness Levels (TRLs): A Forensic Framework
Technology Readiness Levels (TRLs) are a methodological tool used to assess the maturity level of a particular technology, with ratings ranging from TRL 1 (basic principles observed) to TRL 9 (actual system proven in operational environment) [51] [1]. The table below adapts the standard TRL scale, originally defined by NASA and other agencies, to the specific context of developing solutions for high-volume, multi-format evidence processing [1] [75].
Table 1: Technology Readiness Levels for Digital Evidence Processing Solutions
| TRL | Description | Evidence Processing Milestones & Validation Criteria |
|---|---|---|
| TRL 1 | Basic principles observed and reported. | Scientific review of data complexity challenges (e.g., encryption, heterogeneous formats). Initial literature survey on forensic data science principles [71] [1]. |
| TRL 2 | Technology concept and/or application formulated. | Proposal of a practical application based on initial principles (e.g., a conceptual model for a unified evidence processing engine). Application is speculative with no experimental proof [1]. |
| TRL 3 | Analytical and experimental critical function and/or characteristic proof-of-concept. | Active R&D begins. Laboratory studies prove the viability of key functions, such as parsing a new, complex data format. A proof-of-concept model is constructed [1]. |
| TRL 4 | Component and/or breadboard validation in laboratory environment. | Multiple component pieces (e.g., data extraction modules, analysis algorithms) are tested together in a lab setting. A minimum viable prototype is demonstrated [1] [75]. |
| TRL 5 | Component and/or breadboard validation in relevant environment. | The prototype undergoes rigorous testing in simulations that mirror realistic digital environments (e.g., using forensically created device images) [1]. |
| TRL 6 | System/sub-system model or prototype demonstration in a relevant environment. | A fully functional prototype or representational model of the complete evidence processing system is demonstrated in a forensically sound lab environment [1]. |
| TRL 7 | System prototype demonstration in an operational environment. | The working model is demonstrated in a "space environment," which for forensics means a mock casework scenario with legally defensible evidence handling procedures [1]. |
| TRL 8 | Actual system completed and "qualified" through test and demonstration. | The system is tested, "flight qualified," and ready for implementation. It is integrated into an existing digital forensic workflow and validated against industry standards [1]. |
| TRL 9 | Actual system "flight proven" through successful mission operations. | The technology has been successfully used in multiple real-world casework investigations, with its evidence admitted and upheld in court [1]. |
Experimental Protocols for TRL Advancement
The following protocols provide detailed methodologies for key experiments critical to advancing the maturity of evidence processing technologies.
Protocol: Validation of a Forensic Data Processing Component (TRL 4)
Objective: To validate the functionality and accuracy of a single evidence processing component (e.g., a parser for a new mobile messaging application) within a controlled laboratory environment.
Materials:
- Test Machine: Computer with forensically wiped drives and controlled access.
- Forensic Workstation: Equipped with required forensic software suites.
- Reference Data Set: A forensically created image of a mobile device containing known data (messages, files, etc.) from the target application.
- Component Under Test: The software library or module for parsing the application data.
- Write-Blocker: To ensure the integrity of the reference data set.
- Hashing Tool: For verifying data integrity (e.g., tool to generate MD5/SHA hashes) [72] [73].
Methodology:
- Integrity Verification: Using the hashing tool, generate an MD5 hash of the reference data set prior to testing. Document this hash.
- Data Mounting: Connect the storage containing the reference data set to the forensic workstation via a write-blocker.
- Component Execution: Run the component under test, targeting the reference data set. The component should extract and output structured data from the target application.
- Output Analysis: Compare the component's output against the known data in the reference set. Metrics for comparison must include:
- Recall: Percentage of known records successfully extracted.
- Precision: Percentage of extracted records that are accurate and not corrupt.
- Fidelity: Preservation of original metadata (timestamps, sender/recipient info, etc.).
- Integrity Check: Re-calculate the MD5 hash of the reference data set to confirm it was not altered during the test [72] [73].
Protocol: System-Level Demonstration in a Simulated Operational Environment (TRL 6-7)
Objective: To demonstrate the performance of an integrated evidence processing system prototype using a complex, multi-format data set under near-real-world conditions.
Materials:
- Integrated System Prototype: The full evidence processing pipeline, including data ingestion, processing, and analysis modules.
- Complex Data Corpus: A simulated "crime scenario" data set comprising:
- Multiple mobile device images (iOS and Android).
- Cloud storage exports (e.g., iCloud, Google Drive).
- Network traffic captures (PCAP files).
- IoT device data (e.g., smartwatch data dump).
- Control Group Data: Known data and ground truth events hidden within the complex corpus.
- Performance Monitoring Tools: Software for tracking system resource usage (CPU, memory, storage I/O) and processing times.
Methodology:
- Baseline Establishment: Document the ground truth of the control group data and expected system findings.
- System Exercise: Ingest the entire complex data corpus into the integrated system prototype.
- Processing & Analysis: Execute the full processing workflow, from data normalization and feature extraction to automated analysis and report generation.
- Performance Metrics Collection:
- Throughput: Volume of data processed per unit time.
- Accuracy: System's success in identifying and correctly interpreting the ground truth events.
- Scalability: System behavior and processing time as data volume increases.
- Resource Utilization: CPU and memory usage throughout the processing run.
- Forensic Soundness Audit: The process must be documented to prove the chain of custody and the integrity of all evidence processed, ensuring adherence to digital forensics best practices [72] [73] [76].
Visualization of Workflows and Relationships
The following diagrams, generated with Graphviz DOT language, illustrate core workflows and logical relationships in this research domain.
Digital Forensic Intelligence Cycle
TRL Progression in Digital Forensics
The Scientist's Toolkit: Research Reagent Solutions
The following table details essential materials, tools, and software used in advanced digital forensic research for tackling data complexity.
Table 2: Essential Research Tools for Digital Evidence Processing
| Tool/Reagent | Type | Primary Function in Research |
|---|---|---|
| Forensic Write-Blockers | Hardware | Creates a one-way data bridge to prevent alteration of original evidence during the imaging process, ensuring forensic soundness [72]. |
| Hex Editors & File Analysis Tools | Software | Allows for low-level inspection of file structures and data carving, crucial for reverse-engineering unknown file formats and recovering deleted data [74]. |
| Mobile Forensic Suites (e.g., Cellebrite, Magnet AXIOM) | Software Platform | Provides a structured environment for acquiring, decoding, and analyzing data from mobile devices; used as a baseline for validating new extraction and analysis techniques [72]. |
| Reference Data Sets | Data | Curated, ground-truthed collections of digital evidence (e.g., device images, cloud data) used for controlled testing, validation, and benchmarking of new processing algorithms [72] [76]. |
| Statistical Analysis Environment (e.g., R, Python/Pandas) | Software | Enables the application of quantitative data analysis and statistical models (e.g., Likelihood Ratios) to digital evidence, moving beyond subjective interpretation [71]. |
| Cryptographic Hashing Tools | Software | Generates unique digital fingerprints (e.g., MD5, SHA-256) for data sets, which is a fundamental practice for verifying evidence integrity throughout an investigation [72] [73]. |
| Virtualization Platforms | Software | Allows for the creation of isolated, reproducible testing environments to safely analyze malware-contaminated evidence or test processing tools without risk to the host system [74]. |
Anti-forensics techniques represent a critical challenge in digital investigations, encompassing methods deliberately used to obstruct forensic analysis, remove digital artifacts, and eliminate evidence that could tie attackers to an incident [77]. In the era of Industry 4.0, with expanding attack surfaces from technologies like IoT, cloud computing, and big data, these techniques have become increasingly sophisticated, contributing to case backlogs and dropped prosecutions when digital evidence cannot be properly recovered or analyzed [69]. The development of structured countermeasures is essential for maintaining investigative capabilities. This application note establishes a framework for assessing the maturity of these countermeasures using Technology Readiness Levels (TRLs), providing researchers and developers with standardized protocols and evaluation criteria to advance the field of digital forensic readiness.
Key Anti-Forensic Techniques and Detection Methodologies
File System Anti-Forensics
Attackers employ several technical methods to evade detection on NTFS file systems. Timestomping involves altering file metadata timestamps to times prior to the incident, thereby disrupting timeline analysis and delaying detection. File wiping utilizes specialized tools to overwrite file data and metadata, aiming to prevent recovery of deleted files that would normally persist in the Master File Table (MFT) even after "permanent" deletion [77].
Table 1: Key Anti-Forensics Techniques and Their Impact
| Technique | Primary Objective | Forensic Impact | Common Tools |
|---|---|---|---|
| Timestomping | Alter timeline analysis | Compromises event reconstruction, evades time-based filters | Manual OS commands, dedicated timestamp modifiers |
| File Wiping | Permanent evidence eradication | Prevents file recovery, destroys MFT records | SDelete, Eraser, File Shredder |
| Artifact Manipulation | Obscure system activity | Hides execution traces, compromises evidence integrity | Registry editors, log cleaners |
Experimental Protocol: Detecting Timestomping
Principle: Identify discrepancies between user-modifiable and system-protected timestamp attributes to detect intentional timestamp manipulation.
Materials:
- Forensic image of target storage device
- MFT parsing utility (e.g., MFTECmd.exe)
- istat command-line tool
- Write-blocker hardware device
Procedure:
- Evidence Acquisition: Using a write-blocker, create a forensic image of the target storage device to ensure evidence integrity.
- MFT Extraction: Parse the $MFT file from the forensic image using MFTECmd.exe to extract file records and metadata.
- Timestamp Comparison: For each file record, compare the $STANDARDINFO ($SI) creation time with the $FILENAME ($FN) creation time using istat. The $SI attribute is user-modifiable, while the $FN attribute is kernel-protected.
- Anomaly Identification: Flag files where the $SI creation time is chronologically earlier than the $FN creation time as potential timestomping incidents.
- Secondary Verification: Examine the $Extend\$UsnJrnl ($J) file for "BasicInfoChange" update reason codes associated with the flagged files to confirm metadata manipulation.
- Resolution Analysis: Check for timestamp values ending with seven zero sub-seconds, indicating potential low-precision tool usage.
Interpretation: Consistent discrepancies between $SI and $FN timestamps across multiple files indicate systematic timestomping. Correlation with $J update records provides additional forensic evidence of intentional manipulation.
Experimental Protocol: Investigating File Wiping
Principle: Identify evidence of secure deletion despite the absence of file records in the Master File Table.
Materials:
- Forensic image of target storage device
- MFT parsing utility
- $UsnJrnl analysis tool
- File carving software
Procedure:
- MFT Analysis: Parse the $MFT file and identify records with "unused" flags that show recent status changes.
- Entry Sequence Examination: Review MFT entry numbers versus birth timestamps. Flag files with historically early timestamps but high entry numbers indicating recent creation.
- $UsnJrnl Scrutiny: Extract and analyze records from $Extend\$UsnJrnl ($J) looking for sequences of file rename operations followed by deletion events.
- Pattern Recognition: Identify characteristic wiping patterns including multiple rapid rename operations preceding deletion.
- Data Carving: Attempt file recovery through data carving techniques focused on unallocated space corresponding to the suspected wiping timeframe.
- Log Correlation: Cross-reference findings with Windows Event logs for unusual process activity during the identified timeframe.
Interpretation: Correlated evidence between $UsnJrnl deletion sequences and MFT record reuse patterns provides strong indicators of file wiping, even when original file data is unrecoverable.
TRL Roadmap for Anti-Forensics Countermeasures
Implementing Technology Readiness Levels (TRLs) enables structured development and maturation of countermeasures against anti-forensic techniques. The following roadmap outlines the progression from basic research to operational deployment.
Table 2: TRL Roadmap for Anti-Forensics Countermeasures
| TRL | Stage Definition | Development Activities | Validation Metrics |
|---|---|---|---|
| 1-2 | Basic Principles Observed | Research fundamental anti-forensic methods, document artifact behavior | Published papers on technique mechanisms, initial hypothesis formulation |
| 3-4 | Experimental Proof of Concept | Develop detection algorithms, lab testing on controlled samples | Successful detection in isolated environments, false positive/negative rates |
| 5-6 | Technology Validation in Relevant Environment | Testing with real-case scenarios, integration with forensic tools | Detection accuracy >90%, performance benchmarks with large datasets |
| 7-8 | System Demonstration in Operational Environment | Pilot deployment in forensic labs, interoperability testing | Success rate in actual investigations, user feedback, chain of custody maintenance |
| 9 | Actual System Proven in Operational Environment | Full deployment, continuous monitoring and improvement | Court admission success, sustained detection efficacy, industry adoption |
Maturity Assessment Framework
Digital forensic readiness maturity extends beyond technical solutions to encompass people, processes, and technology. The People-Process-Technology (PPT) framework provides indicators for assessing organizational preparedness against anti-forensics challenges [69].
Table 3: Maturity Indicators for Digital Forensic Organizations
| Domain | Level 1 (Initial) | Level 3 (Defined) | Level 5 (Optimized) |
|---|---|---|---|
| People | Ad-hoc training, basic skills | Specialized anti-forensics training, certified staff | Continuous skill development, research contributions |
| Process | Basic chain of custody, inconsistent methods | Standardized procedures for common scenarios | Adaptive processes for new techniques, quality assurance |
| Technology | Basic forensic tools, limited capabilities | Specialized detection tools, automated analysis | Integrated systems, predictive capabilities, R&D investment |
The Scientist's Toolkit: Research Reagent Solutions
Table 4: Essential Digital Forensic Research Materials
| Tool/Resource | Function | Application Context |
|---|---|---|
| MFTECmd.exe | Parses MFT records for metadata analysis | Timestomping detection, file system timeline reconstruction |
| istat | Compares timestamp attributes between $SI and $FN | Validation of timestamp consistency, identification of manipulation |
| $UsnJrnl Parser | Extracts file system journal entries | Tracking file operations, detecting wiping patterns |
| Write Blocker | Prevents evidence modification during acquisition | Maintaining evidence integrity, ensuring legal defensibility |
| Cryptographic Hash Tools | Verifies evidence authenticity through hash matching | Chain of custody maintenance, evidence preservation verification |
Standardized Protocols for Evidence Handling
International standards provide critical frameworks for forensically sound evidence handling. The ISO/IEC 27037 guidelines outline four essential phases for digital evidence management: identification, collection, acquisition, and preservation [78]. These protocols form the foundation for effective anti-forensics countermeasures implementation.
Identification Protocol: Search for and recognize relevant evidence, documenting device priorities based on value and volatility. In anti-forensics contexts, this includes identifying potential evidence sources that may have been targeted for manipulation.
Collection Protocol: Gather digital devices containing potential evidence using static acquisition where possible. For systems that cannot be powered down (critical infrastructure), implement live acquisition procedures prioritizing volatile data.
Acquisition Protocol: Create forensic images using write blockers to prevent data alteration. Generate hash values to verify evidence integrity, recognizing that certain cryptographic hash functions may have known weaknesses requiring more robust alternatives.
Preservation Protocol: Maintain chain of custody documenting all evidence handling, transfers, and storage. Meticulous documentation at each phase is essential for evidence admissibility in legal proceedings involving anti-forensics techniques.
As anti-forensics techniques continue evolving alongside Industry 4.0 technologies, a structured approach to developing countermeasures becomes increasingly essential. The TRL roadmap provides a validated framework for advancing detection and response capabilities from basic research to operational deployment. By implementing the protocols, maturity models, and experimental methodologies outlined in this application note, digital forensic organizations can systematically enhance their readiness against anti-forensics challenges. Future work should focus on adapting these frameworks to emerging technologies including IoT, smart vehicles, and cloud environments where traditional forensic approaches may be insufficient.
The application of Technology Readiness Levels (TRLs) provides a structured framework for assessing the maturity of technologies, from basic research (TRL 1) to full operational deployment (TRL 9) [2]. This systematic approach is increasingly vital for digital forensic technologies, particularly those designed for the complex landscape of cross-border evidence handling. The European Union's adoption of new e-Evidence rules in 2023 highlights the growing imperative for standardized, mature digital evidence solutions that can navigate diverse legal systems while preserving evidentiary integrity [79].
For researchers and developers in digital forensics, the TRL framework offers a common language to communicate technological maturity to stakeholders, including grant funders, judicial authorities, and international partners. By adopting this standardized scale, research and development efforts can be more strategically aligned with the stringent requirements of international legal compliance and operational deployment [80].
Technology Readiness Levels: Framework and Adaptation
Core TRL Definitions and Historical Context
Originally developed by NASA in the 1970s, TRLs create a consistent metric for assessing technological maturity across different types of innovation [2]. The scale ranges from 1 (basic principles observed) to 9 (actual system proven in operational environment), providing a structured pathway for technology development. This framework has since been adopted globally by space agencies, defense departments, and research funding bodies, including the European Union's Horizon Europe program [80].
Table 1: Technology Readiness Levels (TRLs) with Digital Forensics Interpretation
| TRL | Original Definition (EU/NASA) | Digital Forensics Interpretation |
|---|---|---|
| 1 | Basic principles observed and reported | Basic research on digital evidence principles, data integrity concepts |
| 2 | Technology concept formulated | Novel forensic technique hypothesized, potential application identified |
| 3 | Experimental proof of concept | Critical function validation in controlled lab environment |
| 4 | Technology validated in lab | Basic forensic components integrated and tested in laboratory setting |
| 5 | Technology validated in relevant environment | Component validation in simulated cross-border judicial environment |
| 6 | Technology demonstrated in relevant environment | System prototype demonstration with representative cross-border data |
| 7 | System prototype demonstration in operational environment | Full system prototype tested in real legal setting with actual case data |
| 8 | System complete and qualified | End-to-end cross-border evidence system qualified for legal use |
| 9 | Actual system proven in operational environment | System successfully deployed and operating in multiple jurisdictions |
TRL Adaptation for Digital Forensics and Implementation Science
Standard TRL frameworks require adaptation for domain-specific applications. Recent research has modified TRLs for implementation science (TRL-IS), with changes including "the removal of laboratory testing, limiting the use of 'operational' environment and a clearer distinction between level 6 (pilot in a relevant environment) and 7 (demonstration in the real world prior to release)" [81]. This adaptation offers valuable insights for digital forensics, particularly in distinguishing between simulated judicial environments (TRL 6) and actual operational legal settings (TRL 7).
The TRL-IS framework demonstrated good inter-rater reliability (ICC = 0.90) when tested across case studies, suggesting that similarly adapted scales for digital forensics could provide consistent maturity assessments across different research teams and institutions [81].
Cross-Border Evidence Handling: Legal and Technical Landscape
Regulatory Framework and Compliance Requirements
Cross-border digital evidence management operates within a complex legal landscape characterized by differing national laws, data protection regimes, and jurisdictional requirements [82]. The European Union's e-Evidence Regulation, adopted in 2023, establishes direct channels for judicial authorities to request electronic evidence from service providers in other Member States, with strict timelines for compliance (as quick as 8 hours in emergency cases) [79].
Key regulatory challenges include:
- Data Localization Laws: Many countries require that data be stored within national borders, creating conflicts for cross-border investigations [82].
- Differing Privacy Standards: Variations in personal data definitions and protection levels, particularly between GDPR standards and other regulatory frameworks [82].
- Jurisdictional Complexity: Traditional mutual legal assistance treaties (MLATs) are often too slow for digital evidence, necessitating new frameworks like the EU e-Evidence Regulation [79].
Technical Requirements for Cross-Border Evidence Systems
Technologies supporting cross-border evidence handling must address several critical technical requirements rooted in forensic science principles:
- Chain of Custody Integrity: Detailed documentation tracking evidence from collection through analysis to presentation in court, including who accessed evidence, when, and for what purpose [36].
- Evidence Authenticity Verification: Use of cryptographic hash functions (despite noted weaknesses in some algorithms) to verify that evidence has not been altered [60].
- Secure Data Transmission: Encryption and secure transfer protocols that maintain evidence integrity while complying with cross-border data transfer regulations [82].
- Forensic Soundness: Tools and processes that preserve "data in the state in which it was first discovered" without diminishing evidentiary value through technical or procedural errors [60].
Application Notes: TRL-Based Development Pathway
TRL Progression Framework for Cross-Border Evidence Technologies
The following workflow illustrates the systematic development pathway from basic research to operational deployment of cross-border evidence handling technologies:
Experimental Protocols for TRL Validation
Protocol 1: Chain of Custody Integrity Testing (TRL 4-5)
Objective: Validate that digital evidence handling systems maintain an unbroken chain of custody in laboratory environments.
Methodology:
- Evidence Ingestion: Process standardized test datasets including encrypted files, cloud storage artifacts, and mobile device images
- Transfer Simulation: Implement cross-border transfers using secure protocols with automated chain of custody logging
- Integrity Verification: Apply multiple hash algorithms (SHA-256, SHA-3) to verify evidence integrity at each transfer point
- Tamper Detection: Introduce controlled alteration attempts and measure system detection capabilities
Validation Metrics:
- Zero evidence alterations undetected by hash verification
- Complete audit trail for all evidence access and transfers
- Compliance with ISO/IEC 27037 standards for evidence handling [60]
Protocol 2: Cross-Border Compliance Testing (TRL 6)
Objective: Demonstrate system functionality in simulated cross-border judicial environment with multiple regulatory frameworks.
Methodology:
- Regulatory Simulation: Create test environment incorporating GDPR, CCPA, and EU e-Evidence Regulation requirements [82] [79]
- Multi-jurisdictional Data Transfer: Execute preservation and production orders across simulated national boundaries
- Legal Representative Interface: Test communication with legally appointed representatives as required by EU Directive on Representatives [79]
- Emergency Procedure Validation: Validate 8-hour response capability for emergency production orders
Validation Metrics:
- Successful processing of at least 95% of test regulatory scenarios
- All cross-border transfers completed within mandated timelines
- Proper notification of enforcing authorities for content and traffic data requests
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Research Materials and Solutions for Digital Forensic Development
| Research Reagent | Function | Implementation Example |
|---|---|---|
| Cryptographic Hash Libraries | Verify evidence integrity through digital fingerprinting | SHA-256, SHA-3 algorithms for demonstrating unaltered evidence state [60] |
| Write-Blocker Devices | Prevent alteration of original evidence during acquisition | Hardware/software tools creating forensic images without modifying source data [60] |
| Standardized Evidence Datasets | Controlled testing and validation across development phases | Reference datasets including encrypted files, cloud artifacts, and mobile data for reproducible experiments |
| Regulatory Compliance Checklists | Ensure adherence to international data protection standards | GDPR, CCPA, and EU e-Evidence Regulation requirements verification [82] [79] |
| Chain of Custody Documentation Systems | Chronological evidence tracking from collection to court | Automated logging of all evidence access, transfers, and analyses [36] |
| Cross-Border Transfer Protocols | Secure data exchange between jurisdictions | Encrypted transmission methods compliant with mutual legal assistance frameworks |
Implementation Framework: From Technology to Operational Use
The pathway from research to operational deployment requires systematic progression through TRL stages with appropriate validation at each level. The following framework illustrates the critical relationships between technology components, legal compliance, and international standards:
Operational Integration Pathway
Successful implementation of cross-border evidence technologies requires parallel development across three critical domains:
Technical Maturation: Progressive validation from laboratory components (TRL 4-5) to integrated systems (TRL 6-7) and finally to qualified operational systems (TRL 8-9)
Legal Compliance Integration: Early incorporation of regulatory requirements, particularly the EU e-Evidence Regulation's provisions for production orders, preservation orders, and legal representative designation [79]
International Standardization: Alignment with established frameworks including ISO/IEC 27037 for evidence handling and right to fair trial principles for evidentiary reliability [83] [60]
The application of Technology Readiness Levels to cross-border evidence handling technologies provides a crucial framework for systematic development and maturation. By establishing clear milestones from basic research (TRL 1-3) through operational deployment (TRL 8-9), researchers and developers can create solutions that simultaneously address technical capabilities, legal compliance, and international interoperability requirements. The adapted TRL framework for digital forensics enables structured innovation in a field where technological advancement must continuously align with evolving legal standards and the fundamental requirements of evidentiary integrity.
Technology Readiness Levels (TRLs) are a systematic metric used to assess the maturity of a particular technology. Developed by NASA, the scale ranges from 1 (basic principles observed) to 9 (actual system proven in operational environment) [2]. This framework provides consistent, uniform discussions of technical maturity across different types of technology. Within digital forensics, integrating TRL assessments addresses a critical challenge: the field must adopt cutting-edge tools to handle evolving cyber threats while ensuring these tools are reliable, validated, and forensically sound for legal proceedings [46] [47]. The overarching goal is to create a standardized methodology for evaluating and transitioning new forensic technologies from conceptual research to court-admissible implementation.
The digital forensics discipline faces escalating complexity from increasing data volumes, variety of evidence sources, and sophisticated anti-forensic techniques [55] [56]. Meanwhile, legal standards for evidence integrity—including maintaining chain of custody, ensuring data authenticity, and following standardized procedures—remain stringent [55]. Embedding TRL assessments into established forensic workflows creates a structured pathway for innovation without compromising evidentiary requirements. This integration enables researchers and practitioners to objectively evaluate emerging technologies—such as artificial intelligence for evidence analysis [46] or automated forensic platforms [84]—at each development stage, ensuring only sufficiently mature technologies advance to operational use in casework.
TRL Integration Framework for Digital Forensics
Mapping TRLs to Forensic Development Stages
The integration of Technology Readiness Levels into digital forensics requires careful mapping between generic technology development stages and specific forensic validation requirements. The table below outlines this correspondence, highlighting key activities and outputs at each readiness level relevant to forensic applications.
Table 1: TRL Mapping for Digital Forensic Technologies
| TRL | NASA Definition [1] [2] | Forensic Application Stage | Key Forensic Activities & Deliverables |
|---|---|---|---|
| 1 | Basic principles observed and reported | Foundational Research | Literature review of forensic principles; Identification of potential investigative applications |
| 2 | Technology concept and/or application formulated | Applied Concept Development | Formulation of forensic use cases; Theoretical model of evidence analysis application |
| 3 | Analytical and experimental critical function proof-of-concept | Core Function Validation | Laboratory testing of isolated functions; Preliminary validation on controlled datasets |
| 4 | Component validation in laboratory environment | Component Integration | Testing of individual tool components with forensic datasets; Basic interoperability checks |
| 5 | Component validation in relevant environment | Forensic Validation | Testing in simulated case environment; Validation against known case standards [37] |
| 6 | System demonstration in relevant environment | Integrated System Testing | Full prototype testing with mixed evidence types; Integration with existing forensic workflows [85] |
| 7 | System prototype demonstration in operational environment | Controlled Operational Assessment | Pilot deployment in live investigative context; Assessment of chain of custody integration [55] |
| 8 | Actual system completed and qualified | Full Forensic Validation | Complete documentation and testing for legal admissibility; Compliance with standards (e.g., ISO/IEC 27043) [37] |
| 9 | Actual system proven through successful operations | Court-Validated Implementation | Successful use in multiple investigations; Evidence admitted in judicial proceedings [55] |
Integrated Workflow Design
Embedding TRL assessments requires modifying existing forensic processes to include explicit technology evaluation checkpoints. The following diagram illustrates a streamlined workflow integrating TRL assessment gates into digital forensic investigations:
This workflow ensures that technologies progress through appropriate validation stages before being relied upon for critical investigative outcomes. At each assessment gate, technologies must demonstrate sufficient maturity before advancing to subsequent forensic phases, maintaining the integrity of both the technology evaluation process and the overall investigation.
Experimental Protocols for TRL Assessment
Protocol 1: Component-Level Validation (TRL 4-5)
Objective: To validate that individual components of a digital forensic tool function correctly in laboratory and simulated operational environments.
Materials:
- Test Forensic Workstation: Configured with standard forensic tools and write-blockers
- Reference Datasets: Certified forensic images with known artifacts and metadata
- Control Samples: Clean baseline systems for comparison testing
- Measurement Tools: Software for recording processing accuracy, speed, and resource utilization
Methodology:
- Component Isolation: Deploy the technology component in an isolated laboratory environment with controlled reference datasets [46].
- Function Verification: Execute predefined tests to verify specific functions (e.g., data parsing, pattern matching, metadata extraction) against expected outcomes.
- Performance Benchmarking: Measure processing speed, resource consumption, and accuracy metrics using standardized forensic datasets [85].
- Error Handling Assessment: Introduce corrupted or non-standard data formats to evaluate error detection and recovery capabilities.
- Documentation Review: Verify that component design, implementation, and testing documentation meets forensic standards for transparency [37].
Success Criteria: Technology must demonstrate ≥95% accuracy in core functions, proper error handling without systemic failures, and comprehensive documentation before advancing to TRL 6.
Protocol 2: Integrated System Validation (TRL 6-7)
Objective: To evaluate the complete forensic technology system in an integrated environment with representative case data and operational constraints.
Materials:
- Integrated Forensic Platform: Combination of new technology and existing tools (e.g., Magnet Graykey, Cellebrite Physical Analyzer) [84]
- Mixed Evidence Datasets: Multiple evidence types (mobile, cloud, computer) from simulated cases
- Chain of Custody Documentation: Standardized forms and digital tracking systems
- Performance Monitoring Tools: System-wide monitoring for integration issues
Methodology:
- Workflow Integration: Incorporate the technology into established forensic workflows, ensuring compatibility with existing tools and procedures [84].
- End-to-End Testing: Process mixed evidence types through the complete investigative lifecycle from acquisition to reporting.
- Interoperability Verification: Test data exchange between the new technology and existing systems using standard formats (JSON, CSV) [85].
- Chain of Custody Validation: Verify that the technology maintains proper evidence integrity tracking throughout processing [55].
- Scalability Testing: Evaluate performance with increasing data volumes and complexity to identify operational limits.
Success Criteria: System must maintain evidence integrity, demonstrate seamless interoperability with existing tools, and process case-realistic data volumes within operational timeframes.
Protocol 3: Operational Readiness Assessment (TRL 8-9)
Objective: To validate the technology in actual operational environments and establish its reliability for courtroom evidence presentation.
Materials:
- Live Case Data: Appropriate evidentiary materials from active investigations (with proper legal authorization)
- Legal Framework Documentation: Relevant statutes, standards, and precedents for evidence admissibility
- Expert Review Panel: Multi-disciplinary team including forensic analysts, legal experts, and domain specialists
- Validation Test Suite: Comprehensive tests for forensic soundness, accuracy, and reliability
Methodology:
- Controlled Field Deployment: Implement the technology in live investigative contexts under close supervision of experienced examiners.
- Evidence Admissibility Review: Assess whether the technology's processes and outputs meet jurisdictional standards for scientific evidence [46].
- Comparative Analysis: Compare results from the new technology with established methods using the same evidence sources.
- Reliability Testing: Execute extended operation under realistic caseload conditions to identify potential failure modes.
- Documentation Audit: Verify comprehensive documentation of all validation activities, error incidents, and corrective actions.
Success Criteria: Technology must successfully process evidence in live investigations, withstand legal challenges to its methodology, and produce outputs deemed admissible by relevant judicial standards.
Implementation Toolkit
Research Reagent Solutions
Table 2: Essential Materials for TRL Integration in Digital Forensics
| Category | Specific Solution | Function in TRL Assessment | Implementation Notes |
|---|---|---|---|
| Reference Datasets | Certified forensic images (NIST CFReDS) | Provides standardized materials for controlled testing at TRL 4-6 | Include multiple evidence types (mobile, cloud, computer) with verified ground truth |
| Validation Tools | Automated test harnesses | Executes repeatable test sequences for benchmarking performance | Customize for specific forensic functions (e.g., file carving, memory analysis) |
| Integration Frameworks | Magnet Automate [84], ADF Integrated Workflow [85] | Enables technology integration into existing forensic ecosystems | Use drag-and-drop workflow builders to incorporate new tools into established processes |
| Chain of Custody Systems | Digital evidence management systems [55] | Tracks evidence integrity throughout technology validation | Must provide tamper-evident audit logs with cryptographic hashing |
| Legal Compliance Checklists | ISO/IEC 27043 [37], ASTM E2678-09 | Ensures technologies meet international forensic standards | Adapt requirements to specific jurisdictional rules of evidence |
| Performance Metrics | Processing speed, accuracy rates, resource utilization | Quantifies technology effectiveness at each TRL level | Establish baseline metrics from existing tools for comparison |
Implementation Considerations
Successful integration of TRL assessments requires addressing several practical considerations. Workflow Disruption should be minimized by aligning assessment gates with existing forensic process milestones [85] [84]. Resource Allocation must account for the comprehensive testing required at higher TRLs, particularly for operational validation. Legal and Ethical Compliance necessitates early engagement with legal experts to ensure assessment protocols meet admissibility requirements [55] [37]. Finally, Documentation Standards should be established to create the comprehensive records needed for courtroom presentation of both the technology's validation and its specific application in cases.
Integrating TRL assessments into digital forensic workflows provides a structured pathway for adopting innovative technologies while maintaining the rigorous standards required for legal proceedings. The framework presented enables objective evaluation of technology maturity from basic research through courtroom validation. As digital evidence continues to grow in volume and complexity [55] [56], such systematic approaches to technology adoption become increasingly essential for effective investigations. Future work should focus on developing domain-specific TRL criteria for emerging forensic domains including AI-assisted analysis [46] and IoT forensics, further strengthening the bridge between forensic research and operational practice.
Measuring Success: Validation Frameworks and Comparative TRL Analysis
Technology Readiness Levels (TRLs) provide a systematic metric for assessing the maturity level of a particular technology, originally developed by NASA in the 1970s and since adopted across numerous fields including digital forensics [86] [1]. The scale ranges from TRL 1 (basic principles observed) to TRL 9 (actual system proven through successful deployment) [1] [35]. In digital forensics, this framework enables researchers and practitioners to communicate development progress clearly and manage the transition from theoretical research to operational digital forensic tools and methods [86]. The validation of these methods is a cornerstone of forensic science, ensuring that results presented in legal contexts are reliable, reproducible, and scientifically sound [87].
For digital forensic research, implementing TRLs addresses a critical need: establishing objective criteria to evaluate when a novel forensic technique, tool, or methodology has sufficiently matured for use in casework and court proceedings. This document provides detailed application notes and protocols for establishing validation metrics that quantify TRL progression specifically within digital forensic contexts, supporting the implementation of a rigorous framework for technology development and assessment.
Technology Readiness Levels: Framework and Definitions
The TRL Scale
The TRL framework consists of nine distinct levels that represent a technology's progression from basic research to commercial deployment [1]. Table 1 outlines the standardized definitions and characteristics for each TRL, adapted for digital forensic applications.
Table 1: Technology Readiness Levels (TRLs) in Digital Forensic Contexts
| TRL | Definition | Description in Digital Forensics | Key Activities |
|---|---|---|---|
| TRL 1 | Basic principles observed and reported | Initial research into fundamental forensic principles or mechanisms [86] | Theoretical studies of technology's basic properties [86] |
| TRL 2 | Technology concept and/or application formulated | Practical applications are invented based on observed principles; applications are speculative [86] | Applied research focused on specific forensic application; analytical studies [86] |
| TRL 3 | Experimental proof of concept | Active R&D begins with analytical and laboratory studies to validate predictions [1] | Construction of proof-of-concept model; validation of separate elements [86] |
| TRL 4 | Technology validated in lab | Basic technological components are integrated and tested in simulated environment [86] [88] | Component/subsystem validation in laboratory environment [86] |
| TRL 5 | Technology validated in relevant environment | Technology is tested in conditions that simulate real-world digital forensic scenarios [35] | Rigorous testing of breadboard technology in simulated operational environment [1] |
| TRL 6 | Prototype demonstrated in relevant environment | Full-scale prototype is tested under real-world conditions with close-to-expected performance [35] | Testing prototype/model in high-fidelity laboratory environment or simulated operational environment [1] [88] |
| TRL 7 | Prototype demonstrated in operational environment | Working model or prototype is demonstrated in an actual digital forensic operational setting [86] | System prototype demonstration in operational environment [1] |
| TRL 8 | System complete and qualified | Technology has been tested and "qualified" for implementation in casework [1] | Technology proven to work in final form under expected conditions [86] |
| TRL 9 | Actual system proven through successful deployment | Technology is successfully used in operational casework and ready for full deployment [86] | Actual application of technology in its final form in real cases [1] |
TRL Progression Pathway
The following diagram illustrates the logical progression pathway through Technology Readiness Levels in digital forensic development:
Validation Metrics Framework for Digital Forensics
Core Validation Principles
Validation in digital forensics involves demonstrating that a method used for analysis is fit for its specific purpose and that results can be relied upon [87]. The UK Government's guidance on method validation in digital forensics defines validation as "the process of providing objective evidence that a method, process or device is fit for the specific purpose intended" [87]. This process requires establishing objective evidence that the method meets acceptance criteria derived from end-user requirements [87].
For digital forensic tools and methods, validation must demonstrate:
- Repeatability: Obtaining the same results when using the same method on identical test items in the same laboratory by the same operator using the same equipment within short intervals of time [89]
- Reproducibility: Obtaining the same results when using the same method on identical test items in different laboratories with different operators utilizing different equipment [89]
- Fitness for Purpose: The method is good enough to do the job it is intended to do, as defined by specifications developed from end-user requirements [87]
Quantitative Validation Metrics by TRL
Table 2 outlines specific, quantifiable validation metrics mapped to each TRL, providing measurable indicators of progression in digital forensic technology development.
Table 2: Quantitative Validation Metrics for TRL Progression in Digital Forensics
| TRL | Technical Validation Metrics | Process Validation Metrics | Performance Thresholds |
|---|---|---|---|
| TRL 1-2 | Peer-reviewed publications; Citation impact; Theoretical proofs | Research methodology documentation; Literature review completeness | Hypothesis formulation; Concept specification |
| TRL 3 | Experimental success rate (%); Proof-of-concept functionality score; Algorithm accuracy on controlled datasets | Protocol development status; Experimental design rigor | ≥70% success in controlled experiments; Basic functionality demonstrated |
| TRL 4 | Component integration success rate; Interface reliability; Error rates in lab environment | Standard Operating Procedure (SOP) draft completion; Lab validation protocols | ≥85% component integration success; Error rate <5% in lab tests |
| TRL 5 | System performance in simulated environment; False positive/negative rates; Processing speed benchmarks | Testing protocol validation; Quality control measures established | Performance ≥90% of target in simulation; Error rate <2% |
| TRL 6 | Prototype reliability metrics; User acceptance scores; Real-world condition performance | Full SOP implementation; Training program development | ≥95% reliability in relevant environment; User acceptance ≥80% |
| TRL 7 | Operational environment success rate; Scalability metrics; Resource utilization efficiency | Casework implementation plan; Proficiency testing program | ≥98% operational success; Meets scalability requirements |
| TRL 8-9 | Casework success rate; Legal challenges sustained; Long-term reliability statistics | Full accreditation achieved; Continuous improvement process | ≥99% casework reliability; Zero successful Daubert challenges |
Experimental Protocols for TRL Validation
Protocol 1: TRL 3-4 Progression Validation
Objective: Validate proof-of-concept and laboratory integration of digital forensic method.
Materials and Reagents:
- Controlled digital test images (e.g., from DFTT or NIST CFTT)
- Reference hardware configurations
- Forensic workstations with write-blockers
- Analysis software tools
Procedure:
- Establish Baseline Metrics: Define quantitative performance targets for the method (e.g., data recovery percentage, processing speed, accuracy rates)
- Prepare Test Environment: Configure laboratory setting with controlled digital evidence specimens
- Execute Proof-of-Concept Testing: Conduct minimum of three independent test runs using the method [89]
- Integrate Components: For TRL 4, combine technological components and test interoperability
- Collect Performance Data: Record success/failure rates, error occurrences, and performance deviations
- Analyze Results: Compare outcomes against predefined acceptance criteria
Validation Criteria: Method must demonstrate ≥70% success rate in controlled experiments for TRL 3, and ≥85% component integration success for TRL 4 with comprehensive error documentation.
Protocol 2: TRL 5-6 Progression Validation
Objective: Validate technology in relevant and simulated operational environments.
Materials and Reagents:
- Realistic digital evidence datasets representing casework scenarios
- Multiple hardware platforms and configurations
- Simulated operational environments (e.g., corporate network, mobile device collections)
- Validation testing frameworks
Procedure:
- Design Relevant Test Scenarios: Create simulated environments that closely mirror real-world digital forensic contexts
- Implement Testing Protocol: Execute method across multiple environments with different operators
- Stress Testing: Subject method to edge cases, large datasets, and adverse conditions
- Performance Benchmarking: Compare results against existing validated methods or gold standards
- Document Limitations: Identify and record all method constraints and failure conditions
- Independent Verification: Engage second examiner or laboratory to verify reproducibility [89]
Validation Criteria: Method must achieve ≥90% of performance targets in simulated environments for TRL 5, and ≥95% reliability with ≥80% user acceptance for TRL 6.
Protocol 3: TRL 7-9 Progression Validation
Objective: Validate method in operational environments and through full deployment.
Materials and Reagents:
- Actual casework materials (appropriately authorized)
- Production forensic environments
- Multiple examiner teams
- Legal and regulatory framework documentation
Procedure:
- Pilot Deployment: Implement method in limited operational context with close monitoring
- Performance Monitoring: Track success rates, error frequencies, and resource utilization
- Proficiency Testing: Assess multiple examiners' performance using the method
- Legal Compliance Review: Ensure method meets evidentiary standards (e.g., Daubert criteria) [89]
- Scalability Assessment: Evaluate method performance under varying workloads and case types
- Longitudinal Study: Monitor method performance over time (minimum 3-6 months)
Validation Criteria: Method must demonstrate ≥98% operational success rate for TRL 7, and ≥99% casework reliability with successful withstand of legal challenges for TRL 8-9.
The Digital Forensic Researcher's Toolkit
Essential Research Reagent Solutions
Table 3 details key research materials, tools, and resources essential for conducting TRL validation studies in digital forensics.
Table 3: Essential Research Reagents and Resources for Digital Forensic Validation
| Tool/Resource | Function | Application in TRL Validation | Example Sources |
|---|---|---|---|
| Controlled Digital Test Images | Provide standardized datasets with known content for method testing | TRL 3-6: Performance benchmarking and validation testing | DFTT (Digital Forensics Tool Testing), NIST CFTT [89] |
| Forensic Hardware Platforms | Representative target devices for method validation | TRL 4-7: Testing method across various hardware configurations | Commercial mobile devices, storage media, embedded systems |
| Write-Blocking Hardware | Ensure evidence integrity during acquisition process | TRL 4-9: Validating method does not alter original evidence | Hardware write-blockers for various interfaces (SATA, IDE, USB) |
| Reference Forensic Software | Established tools for comparative validation | TRL 5-8: Benchmarking performance against validated methods | Commercial and open-source digital forensic tools |
| Validation Testing Frameworks | Structured approaches for test design and execution | All TRLs: Ensuring comprehensive validation coverage | ISO17025 guidelines, FSR Codes of Practice [87] |
| Performance Metrics Software | Quantitative measurement of method characteristics | All TRLs: Collecting objective validation data | Custom scripts, commercial testing suites, benchmarking tools |
Validation Workflow and Decision Framework
The following diagram illustrates the complete validation workflow and decision framework for TRL assessment in digital forensics:
Compliance with Legal and Regulatory Standards
Digital forensic validation must address legal standards for admissibility of scientific evidence, particularly the Daubert standard which evaluates:
- Whether the method has undergone empirical testing
- Whether the method has been subjected to peer review
- The known or potential error rate of the method
- The existence and maintenance of standards controlling the technique's operation
- Whether the method has attracted widespread acceptance within a relevant scientific community [89]
Validation documentation should explicitly address each of these criteria, with particular attention to establishing known error rates through rigorous testing at appropriate TRLs (typically TRL 5-7). The validation process should generate the objective evidence needed to support testimony regarding the reliability of the digital forensic method [87].
Additionally, laboratories should implement ongoing quality assurance procedures including:
- Periodic revalidation of methods (typically quarterly or biannually) [89]
- Proficiency testing of examiners
- Comprehensive documentation of all validation activities
- Clear statements of method limitations for court presentation
This document provides a structured comparative analysis of contemporary digital forensic technologies, assessing their maturity against the Technology Readiness Level (TRL) scale. The TRL framework, originally developed by NASA, is a systematic metric for assessing the maturity of a particular technology [1] [11]. It operates on a scale from 1 (basic principles observed) to 9 (actual system proven in successful mission operation) [11]. This application of the TRL scale offers researchers and scientists a standardized benchmark to gauge the development and deployment readiness of tools essential for digital forensic readiness, a field increasingly challenged by data volume, encryption, and anti-forensic techniques [56] [13].
Technology Readiness Levels (TRL) Framework
The following table details the nine-level TRL framework, which serves as the basis for the subsequent technology assessment [1] [11].
Table 1: Technology Readiness Levels (TRL) Definition
| TRL | Title | Description |
|---|---|---|
| 1 | Basic Principles Observed | Scientific research begins and is translated into applied R&D [1]. |
| 2 | Technology Concept Formulated | Practical applications are identified, but remain speculative and without experimental proof [1]. |
| 3 | Experimental Proof of Concept | Active R&D is initiated, including analytical and laboratory studies to validate predictions [1] [11]. |
| 4 | Technology Validated in Lab | Component parts are tested together in a laboratory environment [1] [11]. |
| 5 | Technology Validated in Relevant Environment | A breadboard technology is tested in a simulated, realistic environment [1]. |
| 6 | Technology Demonstrated in Relevant Environment | A fully functional prototype or representational model is verified in a simulated environment [1] [11]. |
| 7 | System Prototype Demonstration in Operational Environment | A working prototype is demonstrated in its intended operational environment [1] [11]. |
| 8 | System Complete and Qualified | The technology is deemed "flight qualified" and ready for implementation into existing systems [1] [11]. |
| 9 | Actual System Proven in Operational Environment | The technology is successfully deployed and proven in its real-world, mission environment [1] [11]. |
TRL Assessment of Digital Forensic Technologies in 2025
The digital forensics field is characterized by technologies at varying stages of maturity. The table below provides a comparative TRL assessment of key technology categories based on their current state of development and deployment as of 2025.
Table 2: TRL Assessment of Current Digital Forensic Technologies
| Technology Category | Assessed TRL | Key Examples & Characteristics | Justification for TRL |
|---|---|---|---|
| AI & Machine Learning for Media Analysis | TRL 7-8 | • Deepfake detection tools (e.g., AlchemiX) analyzing physical cues and audio timing [39].• Neural networks for categorizing objects in images (e.g., weapons, explicit material) [13]. | Tools are demonstrated in operational environments (e.g., by law enforcement at INTERPOL conferences) but are still evolving against new threats, preventing a TRL 9 rating [39] [13]. |
| Cloud Forensics Tools | TRL 8 | • Tools that use provider APIs to simulate app clients and download user data from services like Facebook or Telegram [13]. | Technology is "complete and qualified," capable of interfacing with live cloud services in a forensically sound manner, though jurisdictional challenges remain [13]. |
| Integrated Forensic Platforms | TRL 9 | • Commercial suites like Belkasoft X, Cellebrite, and Magnet AXIOM [13] [90]. | These are "actual systems proven in operational environment," widely used by law enforcement and corporate investigators globally for countless real-world cases [90]. |
| Open-Source Forensic Tools | TRL 8 | • Tools like Autopsy, ALEX (Android Logical Extractor), and TaskHunter [39] [90]. | Systems are "complete and qualified," with robust communities for support and validation. They are regularly used in investigations but may lack the formal support of commercial TRL 9 platforms [39] [90]. |
| IoT & Vehicle Forensics | TRL 7 | • Extraction of data from vehicle infotainment systems (e.g., Tesla EDR data) [10] [13].• Analysis of drone flight logs and GPS data [13]. | A "system prototype" is demonstrated in operational environments, as evidenced by its use in court cases, but methodologies are often device-specific and not yet universally standardized [10]. |
| Proactive DFIR & Threat Hunting | TRL 6 | • Open-source tools like TaskHunter for detecting scheduled task abuse in Windows [39].• QELP for rapid ESXi log parsing to surface compromise indicators [39]. | Technology is "demonstrated in a relevant environment." These tools are effective for triage in enterprise settings but are often part of a larger, manual investigative process [39]. |
Experimental Protocols for Technology Validation
To ensure the validity and reliability of digital forensic tools at various TRLs, standardized experimental protocols are essential. The following workflows outline key validation methodologies.
Protocol for Deepfake Media Authentication
This protocol details the process for validating deepfake detection tools, which are critical for maintaining evidence integrity.
Diagram 1: Deepfake Media Authentication Workflow
Objective: To verify the authenticity of a digital media file (video/audio) by detecting AI-generated manipulations or deepfakes [18] [10]. Procedure:
- Data Collection & Preservation: Create a forensically sound copy of the suspect media file. Record its hash value (e.g., SHA-256) to ensure integrity [90].
- File Format & Metadata Analysis: Use tools like ExifTool to read, write, and edit metadata in various files. Analyze the file's header structure, creation timestamps, and software signatures for inconsistencies [90].
- Tool-based Deepfake Detection: a. AI-Driven Forensic Analysis: Process the file through specialized deepfake detection tools (e.g., AlchemiX). These tools use neural networks to identify subtle, pixel-level artifacts left by generative AI models [39]. b. Physical/Biological Cue Analysis: The tool checks for non-naturalistic physiological signals, such as inconsistent blinking patterns, heartbeat signals, or lighting reflections on surfaces [39]. c. Audio-Visual Synchronization Check: The tool analyzes the timing and coherence between audio waveforms and lip movements for discrepancies [39].
- Manual Expert Review: A digital media forensics expert manually reviews the tool's findings, focusing on any flagged anomalies. This step provides critical context and validates the AI's output [18].
- Findings Consolidation: Generate a comprehensive report detailing the analysis steps, tools used, findings, and a final conclusion on the media's authenticity with a stated confidence level [56].
Protocol for Integrated Mobile & Cloud Evidence Acquisition
This protocol describes a standardized method for acquiring evidence from a mobile device and its associated cloud data, a common scenario in modern investigations.
Diagram 2: Mobile & Cloud Evidence Acquisition Workflow
Objective: To acquire a complete set of digital evidence from a mobile device and its linked cloud services in a forensically sound manner, addressing data fragmentation [18] [13]. Procedure:
- Device Isolation & Preservation: Immediately isolate the mobile device from all networks (cellular, Wi-Fi, Bluetooth) using a Faraday bag. This prevents remote wiping or data alteration [13].
- Logical/File System Extraction: Use a forensic tool (e.g., Cellebrite, Belkasoft X, or the open-source ALEX) to perform a logical and/or file-system extraction from the mobile device. This captures data such as call logs, messages, installed apps, and local files [39] [13] [90].
- Cloud Data Acquisition via API: Using the same or a complementary forensic platform, provide valid user credentials to access the device user's cloud accounts (e.g., iCloud, Google, social media). The tool simulates an application client and uses the provider's APIs to download available data, such as backups, messages, and photos, which may not be stored on the device itself [13].
- Data Correlation & Timeline Creation: Import both the device extraction and cloud acquisition results into a unified forensic platform. The platform parses the data, merges related artifacts (e.g., linking a cloud-stored image with a local messaging app database), and generates a consolidated timeline of user activity [13] [90].
The Scientist's Toolkit: Key Research Reagent Solutions
The following table catalogs essential tools and "reagents" for conducting digital forensic research and investigations, as referenced in the protocols and TRL assessment.
Table 3: Essential Digital Forensics Research Reagents & Tools
| Tool / Reagent Name | Type | Primary Function in Research & Analysis |
|---|---|---|
| Belkasoft X [13] [90] | Integrated Forensic Platform | All-in-one tool for acquiring, analyzing, and reporting evidence from computers, mobile devices, and cloud services. Supports AI-based analysis and timeline creation. |
| Cellebrite [39] [90] | Mobile Forensic Suite | Specialized in extracting and decoding data from mobile devices, including bypassing lock screens and recovering deleted data from smartphones. |
| Magnet AXIOM [90] | Integrated Forensic Platform | Acquires and analyzes evidence from computers, smartphones, and cloud data. Known for its user-friendly interface and powerful artifact parsing. |
| Autopsy [90] | Open-Source Platform | Graphical interface for digital forensics. Used for timeline analysis, hash filtering, keyword search, and web artifact extraction from disk images. |
| ALEX [39] | Open-Source Tool | Cross-platform Android Logical Extractor for ADB-based extractions from Android, WearOS, and FireOS devices. |
| ExifTool [90] | Metadata Analysis | Reads, writes, and edits meta information in a wide variety of files, crucial for verifying the provenance and authenticity of media and documents. |
| FTK Imager [90] | Forensic Imaging Tool | Creates forensically sound images (bit-for-bit copies) of digital storage media without altering the original data. |
| Deepfake Detection Tools (e.g., AlchemiX) [39] | Specialized AI Utility | Employs AI models to detect subtle inconsistencies in video frames, audio frequencies, and pixel patterns indicative of AI-generated manipulation. |
| Bulk Extractor [90] | Data Carving Tool | Scans disk images, files, or directories and extracts information without parsing the file system, useful for finding emails, URLs, and other specific data types. |
| TaskHunter [39] | Proactive Threat Hunting | Open-source PowerShell tool that hunts stealthy scheduled task abuse and persistence mechanisms on Windows systems. |
For researchers and scientists developing digital forensic methodologies, establishing the legal admissibility of novel techniques is paramount. The Daubert and Frye standards serve as the primary legal gatekeepers for expert testimony and scientific evidence in United States courts. Within the framework of Technology Readiness Levels (TRL) for digital forensic readiness research, validation against these standards represents a critical milestone for transitioning from laboratory development (lower TRLs) to court-ready implementation (higher TRLs). This protocol provides detailed application notes for systematically testing digital forensic methods against these legal criteria, ensuring your research meets the rigorous demands of the judicial system.
Core Legal Standards: Daubert vs. Frye
The choice between Daubert and Frye standards often depends on jurisdiction, but both aim to ensure the reliability of expert testimony.
The Frye Standard
Originating from the 1923 case Frye v. United States, this standard focuses on general acceptance within the relevant scientific community [91]. Its application is more rigid, often excluding novel scientific techniques until they achieve widespread acceptance. The core question under Frye is: "Is the method generally accepted by the relevant scientific community?" [92]. This standard remains in use in several state courts, including California, Illinois, and New York [91].
The Daubert Standard
Established in the 1993 Supreme Court case Daubert v. Merrell Dow Pharmaceuticals, Inc., this standard grants judges a gatekeeping role to evaluate the reliability and relevance of expert testimony [92]. Daubert is more flexible, allowing newer scientific techniques to be admitted if they meet specific reliability criteria. It is used in federal courts and has been adopted by the majority of states, including Florida and Texas [91]. The standard is tied to Federal Rule of Evidence 702, which requires that expert opinions be based on sufficient facts, use reliable methods, and apply those methods reliably to the case [92].
Table 1: Core Differences Between Daubert and Frye Standards
| Feature | Daubert Standard | Frye Standard |
|---|---|---|
| Core Focus | Methodological reliability and relevance [92] | General acceptance within the scientific community [91] |
| Judicial Role | Active gatekeeper with detailed review of methodology [92] | Determines admissibility based on community consensus [91] |
| Treatment of Novel Science | More accommodating if method proves reliable [92] | Cautious; excludes methods until consensus forms [91] |
| Primary Jurisdiction | Federal courts and many states [91] | Several states, including California and New York [91] |
| Key Evaluation Criteria | Testability, error rates, peer review, standards, acceptance [92] | Acceptance by relevant scientific field [91] |
Experimental Protocol for Daubert Validation
This section outlines a detailed protocol for validating digital forensic methodologies against the Daubert standard's multi-factor test.
Protocol Objectives and Scope
- Primary Objective: To systematically evaluate a digital forensic method against each Daubert factor to establish foundational admissibility for expert testimony.
- Secondary Objective: To generate quantitative and qualitative metrics that demonstrate methodological rigor under Federal Rule of Evidence 702 [92].
- Application Level: Designed for digital forensic techniques at TRL 5-7 (technology validation in relevant environments).
Materials and Reagents
Table 2: Essential Research Reagents and Materials
| Item | Specification/Function | Evidentiary Purpose |
|---|---|---|
| Reference Datasets | Certified digital forensic corpora (e.g., NIST CFReDS) | Provides sufficient facts and data for method validation [92] |
| Analysis Software | Tool with documented error rates and testing protocols | Enables application of reliable principles and methods [92] |
| Statistical Analysis Package | Platform such as R or ILLMO with empirical likelihood methods [93] | Supports estimation of effect sizes and confidence intervals |
| Documentation Framework | Standardized template for recording methodology and results | Ensures reliable application of methods to case facts [92] |
| Peer-Review Mechanism | Access to relevant scientific publications and conferences | Provides venue for scrutiny and acceptance by scientific community [92] |
Experimental Procedure
Step 1: Testability Validation
Design controlled experiments to test hypotheses generated by your digital forensic method. For example, if developing a file carving technique, create experiments to determine:
- Whether the method can be tested against known datasets
- Whether it has been subjected to falsification attempts
- The conditions under which it produces reliable results [92]
Step 2: Error Rate Determination
Establish the known or potential error rate of your methodology using statistical analysis:
Execute statistical tests, such as t-tests for comparing experimental conditions, to quantify differences and their significance [93]. For instance, compare your method's performance against established techniques using metrics like accuracy and precision.
Step 3: Peer Review Assessment
- Submit methodology and results to peer-reviewed publications in digital forensics
- Present findings at academic and professional conferences
- Document the peer review process and subsequent revisions [92]
Step 4: Standards and Controls Verification
- Identify and implement relevant industry standards (e.g., ISO/IEC 27043 for digital forensic investigations [63])
- Document control mechanisms for methodological application
- Establish quality assurance procedures for consistent implementation [92]
Step 5: General Acceptance Evaluation
- Survey the relevant scientific community through expert interviews
- Review citations and adoption of similar methodologies
- Document usage in comparable legal contexts [92]
Data Analysis and Interpretation
Analyze the collected data using both traditional and modern statistical methods. While traditional methods like t-tests establish statistical significance, modern approaches focus on estimating effect size and providing confidence intervals for these estimates [93]. For non-parametric data or when normality assumptions are violated, consider using empirical likelihood (EL) methods, which allow for significance testing and confidence interval estimation without questionable distributional assumptions [93].
Table 3: Quantitative Metrics for Daubert Compliance
| Daubert Factor | Measurement Metric | Target Threshold |
|---|---|---|
| Testability | Number of hypothesis-testing experiments conducted | Minimum 3 independent validation studies |
| Error Rate | False positive/negative rates with confidence intervals | ≤5% with 95% confidence interval |
| Peer Review | Number of peer-reviewed publications | Minimum 1 publication in reputable journal |
| Standards | Compliance with relevant ISO/IEC standards (e.g., 27043 [63]) | Full implementation of required controls |
| General Acceptance | Adoption rate in relevant community surveys | >50% awareness and >25% utilization |
Experimental Protocol for Frye Validation
This protocol focuses on establishing general acceptance for digital forensic methods in Frye jurisdictions.
Protocol Objectives
- Primary Objective: To document and demonstrate general acceptance of the methodology within the relevant scientific community.
- Application Level: Appropriate for more established techniques at TRL 6-8 (system demonstration and completion).
Experimental Procedure
Step 1: Literature Review and Survey
Conduct a comprehensive review of:
- Academic publications in digital forensics
- Professional guidelines and standards
- Textbooks and educational materials
- Survey practitioners in the field [91]
Step 2: Expert Testimony Collection
- Gather declarations from recognized experts in digital forensics
- Document usage in previous legal proceedings
- Collect statements from professional organizations [92]
Step 3: Methodology Comparison
- Compare your method with generally accepted techniques
- Document similarities and improvements
- Establish lineage from accepted principles [91]
Data Analysis and Interpretation
The analysis for Frye validation is predominantly qualitative, focusing on consensus demonstration rather than statistical metrics. Create a comprehensive matrix documenting acceptance across different segments of the relevant community.
Integrated Validation Workflow
For comprehensive admissibility validation, implement this integrated workflow that addresses both standards:
Impact on Digital Forensic Readiness
Implementing these validation protocols directly enhances digital forensic readiness (DFR) within organizations. A holistic DFR framework, such as one based on ISO/IEC 27043, proactively ensures that digital processes are designed with potential forensic investigations in mind [63]. By validating methods against admissibility standards early in development, researchers can:
- Reduce challenges to digital evidence in legal proceedings
- Increase stakeholder confidence in forensic findings
- Establish scientific rigor in digital forensic methodologies
- Create reproducible and defensible analytical processes
The integration of Technology Readiness Levels with legal admissibility validation provides a structured pathway for transitioning digital forensic research from theoretical concepts to court-ready solutions, ultimately strengthening the entire ecosystem of digital evidence handling.
Error rate analysis has emerged as a critical component in digital forensics, serving as the foundation for building defensible evidence suitable for courtroom presentation. The Daubert Standard, established by the 1993 US Supreme Court case, explicitly identifies the "known or potential rate of error" as a key factor for determining the admissibility of scientific evidence [94] [95]. Within digital forensics, error rate analysis provides the empirical basis for demonstrating methodological reliability, fulfilling legal requirements while enhancing the scientific rigor of the discipline. This framework is particularly vital as courts increasingly scrutinize digital evidence derived from both commercial and open-source forensic tools [94].
The evolving digital landscape, characterized by artificial intelligence (AI)-generated content and sophisticated anti-forensic techniques, has intensified the need for transparent error management [96]. A proactive approach to error analysis transforms potential vulnerabilities into opportunities for systemic improvement, ultimately strengthening forensic conclusions against legal challenges. Recent research indicates that properly validated digital forensic processes can achieve reliability comparable to established forensic disciplines, though this requires structured protocols and continuous monitoring [97] [94]. This document outlines standardized protocols for quantifying, analyzing, and controlling error rates throughout the digital forensic lifecycle, with particular emphasis on meeting legal admissibility standards.
Theoretical Framework and Definitions
Conceptual Foundation of Forensic Errors
A precise understanding of error typologies is essential for effective error rate analysis. In digital forensics, errors can be categorized across multiple dimensions, including their origin, detectability, and impact on forensic conclusions. The Netherlands Forensic Institute (NFI) classification system for Quality Issue Notifications (QINs) provides a robust framework that can be adapted to digital evidence contexts [95]. This system emphasizes that errors extend beyond mere technical failures to encompass procedural deviations, contextual biases, and interpretive inaccuracies.
Analytical errors occur during the technical processing of digital evidence, such as improper data carving or hash collisions. Interpretive errors arise during evidence analysis, including incorrect reasoning about the significance of recovered artifacts or misapplication of analytical techniques. Contextual errors involve the influence of extraneous information on analytical judgment, potentially leading to confirmation bias. Understanding these distinctions is crucial for developing targeted error control measures. Research indicates that a multicomponent view of digital forensics, addressing people, processes, and tools, provides the most comprehensive approach to error mitigation [47].
Legal Standards and Requirements
The Daubert Standard establishes four primary criteria for evaluating scientific evidence, with error rates representing a pivotal consideration alongside testing, peer review, and general acceptance [94]. Courts applying Daubert examine whether digital forensic methods have "established error rates or are capable of providing accurate results" [94]. This legal framework necessitates that forensic practitioners not only implement robust methodologies but also maintain detailed records of performance metrics and validation studies.
Complementing Daubert, the Federal Rules of Evidence 901 and 902 govern the authentication of digital evidence, requiring demonstrating that evidence "is what it purports to be" [96]. The emergence of AI-generated synthetic media, including deepfakes, has intensified authentication challenges, elevating the importance of comprehensive error analysis in establishing evidentiary reliability [96]. International standards such as ISO/IEC 27037:2012 provide additional guidance for identification, collection, and preservation of digital evidence, creating a global framework for forensic reliability [96] [94].
Quantitative Error Rate Data
Rigorous error rate analysis requires establishing baseline metrics through controlled studies and operational data collection. The following tables summarize current findings on error frequencies across forensic domains and digital forensic tool performance.
Table 1: Documented Error Rates in Forensic Disciplines
| Forensic Discipline | Error Type | Reported Rate | Context and Source |
|---|---|---|---|
| Digital Forensics (Open-Source Tools) | Data Carving Errors | 0.5-2.0% | Varies by file system complexity and tool validation [94] |
| Digital Forensics (Commercial Tools) | Artifact Search Inaccuracy | 0.2-1.5% | Dependent on search parameters and data fragmentation [94] |
| Forensic DNA Analysis | Contamination Incidents | 0.4-0.7% | NFI data (2008-2012); includes all sample types [95] |
| Forensic DNA Analysis | Analytical Process Failures | 0.08-0.12% | NFI data; excludes contamination [95] |
| Medical Genetic Testing | Overall Diagnostic Error | 0.2% | Familial Hypercholesterolemia screening [95] |
Table 2: Digital Forensic Tool Performance Comparison
| Tool Category | Tool Examples | Preservation Accuracy | Deleted File Recovery Rate | Targeted Search Reliability |
|---|---|---|---|---|
| Commercial Tools | FTK, Forensic MagiCube | 99.8-100% | 95-98% (varies by file type) | 98.5-99.5% [94] |
| Open-Source Tools | Autopsy, ProDiscover Basic | 99.5-100% | 92-97% (varies by file type) | 97.5-99.0% [94] |
| Validation Requirement | All tool categories | NIST CFTT standards | Repeatability testing (triplicate minimum) | Known artifact control references [94] |
The data reveals that properly validated digital forensic tools, both commercial and open-source, can achieve comparable reliability levels to other established forensic disciplines. The observed variance in error rates highlights the context-dependent nature of digital evidence analysis, where factors such as storage media condition, encryption, and file system integrity significantly impact performance metrics [94]. This quantitative foundation enables practitioners to establish realistic expectations and implement appropriate safeguards.
Experimental Protocols for Error Rate Analysis
Tool Validation and Performance Testing
Objective: To quantitatively assess the accuracy and reliability of digital forensic tools through controlled experimentation, establishing documented error rates for courtroom defensibility.
Materials Required:
- Test Workstations: Minimum two identical systems with standardized specifications
- Reference Data Set: Controlled collection of files spanning multiple formats (documents, images, archives)
- Forensic Write Blockers: Hardware write-blocking devices for evidence integrity
- Commercial Tools: FTK, Forensic MagiCube, or equivalent commercial suites
- Open-Source Tools: Autopsy, ProDiscover Basic, Sleuth Kit
- Hash Verification Software: For integrity checking throughout the process
Methodology:
- Test Scenario Design: Implement three distinct forensic scenarios:
- Preservation and Collection: Creating forensically sound images of original data from varied sources (HDD, SSD, mobile devices)
- Deleted File Recovery: Data carving for common file formats with known fragmentation levels
- Targeted Artifact Searching: Identification of specific evidentiary patterns (keywords, registry entries, internet history)
Controlled Environment Setup: Configure test workstations with clean operating system installations. Populate with reference data set, documenting all file system metadata and cryptographic hashes (MD5, SHA-1, SHA-256) for baseline establishment.
Experimental Execution: Perform each test scenario in triplicate to establish repeatability metrics. Utilize both commercial and open-source tools on identical evidence sources to enable comparative analysis.
Error Rate Calculation: Calculate tool-specific error rates using the formula: Error Rate = (Number of Incorrect Outcomes / Total Number of Operations) × 100 Incorrect outcomes include false positives (incorrectly reported matches), false negatives (missed evidence), and data integrity failures.
Statistical Analysis: Compute confidence intervals (typically 95%) for error rate estimates using binomial distribution statistics. Document all anomalies, performance variations, and tool failures regardless of perceived significance [94].
Anti-Contamination and Integrity Protocols
Objective: To minimize and monitor for evidence contamination throughout the forensic process, preserving the integrity of the chain of custody.
Materials Required:
- Dedicated Forensic Workstations: Isolated from production networks
- Write-Blocking Hardware: For all evidence acquisition procedures
- Cryptographic Hashing Tools: For integrity verification at each process stage
- Clean Room Environments: For physically contaminated media examination
- Quality Issue Notification (QIN) System: Electronic tracking for all quality incidents
Methodology:
- Pre-Analytical Controls: Document the condition of all digital evidence prior to analysis, including photographical evidence of physical interfaces and connections. Establish and verify cryptographic baselines (hash values) before any evidence handling.
Process Segregation: Implement temporal and spatial separation between different cases to prevent cross-contamination. Utilize dedicated tools and storage media for each case where practicable.
Integrity Monitoring: Apply cryptographic hashing at every transfer point and after each significant analytical operation. Compare hashes to establish continuous integrity throughout the forensic lifecycle.
Contamination Detection: Introduce known clean control samples into the analytical process to monitor for contamination events. Regularly test forensic workstations for malware or configuration changes that could impact results.
Quality Incident Documentation: Record all quality issues, however minor, in the QIN system. Categorize incidents by type (administrative, analytical, technical), root cause, and impact on casework. Implement corrective actions for all documented issues [95].
Visualization of Error Analysis Framework
The following diagram illustrates the integrated framework for digital forensic error analysis, showing the relationship between process phases, error control points, and legal requirements.
The visualization demonstrates a systematic approach where preparation phases feed into operational controls, which subsequently support legal defensibility. Each stage contains specific activities that contribute to comprehensive error management, with interconnections showing how validation outcomes inform courtroom presentation.
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 3: Digital Forensic Research Reagents and Materials
| Tool Category | Specific Solutions | Function and Application | Validation Requirements |
|---|---|---|---|
| Forensic Imaging Tools | FTK Imager, dc3dd, Guymager | Creates bit-for-bit copies of digital evidence while preventing evidence alteration | NIST CFTT compliance testing; write-blocking verification [94] |
| Hash Verification Tools | md5deep, HashCalc | Generates cryptographic hashes to verify evidence integrity throughout lifecycle | NIST FIPS 180-4 compliance; collision resistance testing [94] |
| Memory Forensics Tools | Volatility, Rekall | Analyzes volatile memory (RAM) for artifacts not present on storage media | Memory structure documentation; profile validation [98] |
| File Carving Tools | Foremost, PhotoRec, Scalpel | Recovers files without relying on file system metadata | File format signature library; fragmentation resistance testing [94] |
| Mobile Forensics Tools | Cellebrite, Oxygen Forensic | Extracts and analyzes data from mobile devices and smartphones | Chipset compatibility verification; extraction method documentation [47] |
| AI Detection Tools | Deepfake detection algorithms | Identifies AI-generated synthetic media through artifact analysis | Validation against known datasets; error rate quantification [96] |
| Blockchain Analysis | Blockchain explorers, tracing tools | Tracks cryptocurrency transactions for financial investigations | Address clustering verification; transaction graph validation [47] |
Defensible Documentation and Courtroom Presentation
The Forensic Readiness Framework
Organizational forensic readiness represents a proactive approach to evidence management that significantly enhances courtroom defensibility. This framework encompasses governance structures, technical infrastructure, and standardized procedures designed to ensure evidence integrity before incidents occur [96]. In the context of error rate management, forensic readiness involves implementing cryptographic hashing at evidence ingestion, maintaining comprehensive provenance metadata, and establishing chain of custody protocols that withstand legal scrutiny [96].
A critical component of forensic readiness involves AI-aware evidence lifecycles that address emerging challenges such as synthetic media manipulation. This requires extending traditional preservation procedures to include synthetic-media detection checkpoints and provenance analysis capabilities [96]. Organizations should implement policies mandating preservation of creation logs, application metadata, and device identifiers, as these artifacts become essential for authenticating evidence against claims of AI manipulation [96].
Testimony Preparation and Communication
Effective courtroom presentation of digital evidence requires careful preparation that addresses both technical findings and potential error sources. Forensic experts should develop visual aids and demonstrative exhibits that clearly explain complex technical processes to lay audiences while maintaining scientific accuracy [99]. AI-powered trial technology can assist in creating dynamic visualizations of forensic processes and analysis results, helping jurors understand the methodological rigor applied to error control [99].
When addressing error rates in testimony, experts should:
- Present documented error rates within appropriate contextual limitations
- Explain quality control measures implemented to minimize errors
- Distinguish between potential error rates observed in validation studies and their application to the specific case
- Avoid overstating conclusions while confidently presenting methodologically sound findings [95]
The Sedona Conference guidance on responsible use of forensic experts emphasizes transparency about methodological limitations and the importance of human expert oversight even when using AI-assisted forensic tools [96]. This balanced approach satisfies Daubert requirements while building credibility with the court.
Error rate analysis and control represents a fundamental pillar of defensible digital forensics practice. As the field confronts emerging challenges from AI-generated synthetic media, quantum computing threats to cryptographic verification, and increasingly sophisticated anti-forensic techniques, the systematic approach outlined in this document provides a sustainable foundation for legal admissibility [96]. The integration of rigorous tool validation, comprehensive quality control, and transparent documentation enables forensic practitioners to present compelling digital evidence that withstands legal scrutiny.
Future developments in error rate management will likely focus on standardized validation protocols for AI-assisted forensic tools, quantum-resistant hashing algorithms for long-term evidence preservation, and cross-jurisdictional frameworks for error rate communication [96] [47]. By embracing error rate analysis as a continuous improvement mechanism rather than a defensive necessity, the digital forensics community can further enhance its scientific foundations while maintaining the trust of the judicial system.
Technology Readiness Levels (TRLs) are a systematic metric used to assess the maturity of a particular technology, with levels ranging from 1 (basic principles observed) to 9 (actual system proven in operational environment) [1]. While TRLs were originally developed by NASA and have been widely adopted across various sectors, their application within forensic science presents unique challenges due to the field's stringent legal and reliability requirements [65] [2]. The forensic science community operates within a framework where technological validity is scrutinized against legal standards for evidence admissibility, including the Daubert Standard and Federal Rule of Evidence 702 in the United States, and the Mohan Criteria in Canada [65].
For digital forensic readiness research, implementing standardized TRL assessment protocols is particularly crucial. Digital transformations in forensic laboratories can undermine core forensic principles and processes without proper preparation and validation [100]. The 2022-2026 Forensic Science Strategic Research Plan emphasizes advancing applied research and development while supporting foundational research to assess the fundamental scientific basis of forensic analysis [67]. This application note provides a structured framework for inter-laboratory validation of TRL assessment protocols specifically designed for the forensic community, addressing the need for standardized, legally defensible technology evaluation.
Technology Readiness Levels in Forensic Context
TRL Fundamentals and Adaptations
TRLs provide a consistent metric for comparing technology maturity across different types of research and development efforts. The standard nine-level TRL scale progresses from basic research (TRL 1-3) through technology development (TRL 4-6) to operational deployment (TRL 7-9) [1]. Several domains have adapted the original NASA scale for their specific contexts. The European Union has established parallel definitions that closely align with NASA's usage, while medical countermeasure diagnostics use an adapted scale focusing on clinical validation and FDA approval milestones [75] [2].
For forensic science, TRL assessment must incorporate additional dimensions beyond technical functionality, including legal admissibility, error rate quantification, and reproducibility across laboratory environments. The fundamental challenge lies in bridging the gap between analytical chemistry advancements and the rigorous standards required for courtroom evidence [65].
Forensic-Specific TRL Framework
Table 1: Technology Readiness Level Definitions Adapted for Forensic Science Applications
| TRL | General Definition | Forensic-Specific Criteria | Legal Admissibility Considerations |
|---|---|---|---|
| 1-2 | Basic principles observed and formulated | Basic principles translated to forensic applications; literature review establishes potential forensic relevance | Preliminary assessment of scientific foundation for eventual legal acceptance |
| 3-4 | Experimental proof of concept and laboratory validation | Forensic proof-of-concept established; key parameters defined for forensic evidence types | Initial evaluation against relevant legal standards (Daubert, Frye, Mohan) |
| 5-6 | Validation in relevant environment and prototype demonstration | Validation in simulated forensic operational environment; prototype testing with standard reference materials | Development of initial validation data addressing legal requirements for error rates and reliability |
| 7-8 | System demonstration in operational environment and completion | Demonstration in operational forensic laboratory; successful analysis of case-type samples | Comprehensive validation meeting legal standards; establishment of proficiency testing protocols |
| 9 | Actual system proven in operational environment | Successful implementation in multiple forensic laboratories; acceptance in casework and courtroom proceedings | Successful admission of evidence in legal proceedings; established precedent for technology use |
Inter-Laboratory Validation Protocol
Protocol Design Principles
The inter-laboratory validation protocol for forensic TRL assessment is designed with four core principles: (1) Legal Defensibility - ensuring all procedures meet admissibility standards; (2) Reproducibility - establishing consistent results across different laboratory environments; (3) Standardization - creating uniform assessment criteria; and (4) Practical Utility - providing actionable guidance for technology implementation decisions [65] [67].
The protocol addresses the need for "increased intra- and inter-laboratory validation, error rate analysis, and standardization" identified as crucial for implementing new technologies like comprehensive two-dimensional gas chromatography (GC×GC) in forensic practice [65]. Similarly, the Forensic Science Strategic Research Plan prioritizes "standard methods for qualitative and quantitative analysis" and "interlaboratory studies" as key objectives [67].
Phase 1: Pre-Validation Preparation
3.2.1 Technology Characterization
- Define the specific forensic application and evidence type(s)
- Document analytical principles and theoretical foundations
- Identify potential sources of uncertainty and error
- Establish preliminary acceptance criteria for each TRL
3.2.2 Participating Laboratory Selection
- Select a minimum of three independent forensic laboratories
- Ensure representation of different laboratory sizes and resource levels
- Verify participating laboratories meet quality standards (e.g., ISO/IEC 17025)
- Document laboratory capabilities and instrumentation
3.2.3 Test Plan Development
- Create detailed test protocols for each TRL assessment milestone
- Define standardized sample types and reference materials
- Establish data collection and reporting requirements
- Develop statistical analysis plan for inter-laboratory comparisons
Phase 2: Multi-Laboratory TRL Assessment
3.3.1 TRL 4-5 Assessment: Component and Breadboard Validation
- Distributed testing of core technology components across participating laboratories
- Evaluation of analytical sensitivity, specificity, and reproducibility
- Assessment of false positive/negative rates using standardized samples
- Documentation of operational requirements and limitations
3.3.2 TRL 6 Assessment: Prototype Demonstration
- Deployment of functional prototypes in participating laboratories
- Testing with standardized sample sets simulating casework materials
- Evaluation of user interface and workflow integration
- Assessment of training requirements and operational complexity
3.3.3 TRL 7-8 Assessment: Operational Environment Demonstration
- Extended testing in operational forensic laboratory settings
- Analysis of authentic case-type samples alongside conventional methods
- Evaluation of sample throughput, cost efficiency, and reliability
- Documentation of error rates and performance under varying conditions
Phase 3: Data Analysis and TRL Assignment
3.4.1 Statistical Analysis
- Calculation of inter-laboratory reproducibility and variability
- Determination of measurement uncertainty for key parameters
- Statistical comparison with existing standard methods
- Analysis of error rates and confidence intervals
3.4.2 TRL Scoring Matrix
- Composite scoring based on technical performance metrics
- Evaluation against legal admissibility criteria
- Assessment of operational practicality and implementation barriers
- Final TRL assignment with confidence rating
Experimental Workflow and Signaling Pathways
The following diagram illustrates the complete inter-laboratory validation workflow for forensic TRL assessment, showing the sequence of activities and decision points from protocol development through final TRL assignment.
Inter-Laboratory TRL Validation Workflow
Research Reagent Solutions for Forensic TRL Validation
Table 2: Essential Research Reagents and Materials for Forensic TRL Validation Studies
| Reagent/Material | Specifications | Application in TRL Validation | Quality Control Requirements |
|---|---|---|---|
| Standard Reference Materials | NIST-traceable certified reference materials with documented uncertainty | Calibration and performance verification across TRL levels; establishes measurement traceability | Certificate of analysis; stability data; homogeneity testing |
| Proficiency Test Samples | Blind samples with known ground truth; simulated casework samples | Assessment of method accuracy and reproducibility in inter-laboratory studies; error rate determination | Documented preparation protocols; homogeneity testing; stability verification |
| Quality Control Materials | Positive, negative, and sensitivity controls specific to forensic analyte | Daily performance monitoring; detection limit determination; false positive/negative rate assessment | Pre-established acceptance criteria; stability documentation |
| Data Analysis Software | Validated algorithms for statistical analysis and data interpretation | Standardized data processing across participating laboratories; objective performance metrics | Validation documentation; version control; error handling protocols |
| Documentation Templates | Standardized forms for data recording, reporting, and deviation tracking | Consistent data collection across multiple sites; facilitates comparative analysis | Template validation; revision control; user instruction documentation |
Implementation Guidelines
Integration with Quality Management Systems
Successful implementation of TRL assessment protocols requires integration with existing laboratory quality management systems, particularly those based on ISO/IEC 17025 standards [100]. Forensic laboratories should establish documented procedures for technology validation that incorporate TRL assessment at each stage of method development and implementation. This includes:
- Defining TRL gateways for technology adoption decisions
- Establishing documentation requirements for each TRL level
- Incorporating TRL assessment into method validation protocols
- Training personnel on TRL concepts and assessment procedures
Addressing Legal Admissibility Requirements
TRL assessment protocols must specifically address the legal standards for evidence admissibility, including the Daubert criteria of testing, peer review, error rates, and general acceptance [65]. The inter-laboratory validation process should generate the necessary data to demonstrate:
- Scientific Validity: Through rigorous testing across multiple laboratories
- Error Rate Quantification: Through statistical analysis of inter-laboratory data
- Standardization: Through establishment of uniform protocols and acceptance criteria
- Peer Review: Through publication of validation studies and independent verification
Digital Forensic Readiness Considerations
For digital forensic technologies, TRL assessment must address unique challenges including data integrity, cybersecurity, and the handling of digital evidence [100]. The protocol should be augmented with:
- Digital evidence handling procedures specific to the technology being assessed
- Cybersecurity assessment of technology components
- Data integrity verification protocols
- Compatibility evaluation with existing digital forensic workflows
Standardized TRL assessment protocols for inter-laboratory validation provide a critical framework for advancing forensic technology while maintaining the rigorous standards required for legal admissibility. The structured approach outlined in this application note enables objective evaluation of technology maturity across multiple laboratory environments, generating the necessary data for informed implementation decisions. As the forensic science community continues to face evolving technological challenges and opportunities, consistent TRL assessment will support the valid and reliable adoption of new capabilities that enhance forensic practice.
The protocol addresses key priorities identified in the Forensic Science Strategic Research Plan, including "foundational validity and reliability of forensic methods," "measurement of the accuracy and reliability of forensic examinations," and "supporting the implementation of methods and technologies" [67]. By establishing uniform standards for technology readiness assessment, the forensic community can accelerate the adoption of innovative solutions while maintaining the scientific rigor and legal defensibility that underpin public trust in forensic science.
Conclusion
Implementing Technology Readiness Levels in digital forensic readiness provides a systematic pathway for transforming innovative research into legally defensible, operationally reliable tools and methodologies. By adopting the comprehensive framework outlined across our four core intents—from foundational understanding through validation—forensic organizations can effectively bridge the critical gap between technological advancement and courtroom admissibility. The future of digital forensics demands this disciplined approach as emerging challenges including AI-generated evidence, cloud data fragmentation, and sophisticated anti-forensic techniques continue to evolve. Future directions should focus on developing standardized TRL assessment protocols specific to digital forensics, establishing inter-laboratory validation communities, and creating adaptive frameworks that can keep pace with rapid technological change while maintaining strict compliance with evolving legal standards across jurisdictions.
References
- 1. Technology Readiness Levels [https://www.nasa.gov/directorates/somd/space-communications-navigation-program/technology-readiness-levels/]
- 2. Technology readiness level [https://en.wikipedia.org/wiki/Technology_readiness_level]
- 3. Technology Readiness Levels (TRL) in Space Projects | TTMS [https://ttms.com/technology-readiness-levels-trl-in-space-projects-explanation-and-significance/]
- 4. Overview of the Technology Readiness Level (TRL) system [https://ig.space/commslink/overview-of-the-nasa-technology-readiness-level-trl-program/]
- 5. From digital trace to evidence: Challenges and insights ... [https://www.sciencedirect.com/science/article/pii/S1355030625000905]
- 6. A survey of prosecutors and investigators using digital evidence [https://pmc.ncbi.nlm.nih.gov/articles/PMC10311201/]
- 7. Technology Readiness Levels (TRLs) [https://esto.nasa.gov/trl/]
- 8. Challenges in Digital Forensics for the Internet of Things [https://westoahu.hawaii.edu/cyber/forensics-weekly-executive-summmaries/challenges-in-digital-forensics-for-the-internet-of-things/]
- 9. Quantitative evaluation of the results of digital forensic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8112825/]
- 10. Key Trends in Digital Forensics 2025: Chanllenges and ... [https://www.salvationdata.com/knowledge/key-trends-in-digital-forensics-for-2025/]
- 11. What are Technology Readiness Levels (TRL)? - TWI [https://www.twi-global.com/technical-knowledge/faqs/technology-readiness-levels]
- 12. Current Challenges in Digital Forensics Investigations [https://www.mailxaminer.com/blog/current-challenges-in-digital-forensics-investigations/]
- 13. Top 6 Trends Shaping Modern DFIR in 2025 [https://belkasoft.com/dfir-trends-2025]
- 14. Fusing technology readiness levels (TRLs) and safe-by- ... [https://link.springer.com/article/10.1007/s10669-025-10027-0]
- 15. Unveiling the Dynamic Landscape of Digital Forensics [https://www.mdpi.com/2073-431X/13/12/333]
- 16. Comparing Traditional Vs. Modern Digital Forensics [https://lcgdiscovery.com/comparing-traditional-vs-modern-digital-forensics-navigating-the-evolving-digital-landscape/]
- 17. Digital-Forensics-Tools-and-Techniques-in-2025 [https://www.jaroeducation.com/blog/digital-forensics-tools-and-techniques/]
- 18. CEO Lee Reiber: The Digital Forensics Landscape in 2025 [https://www.oxygenforensics.com/en/resources/digital-forensics-trends-2025/]
- 19. Improving the Collection of Digital Evidence [https://nij.ojp.gov/topics/articles/improving-collection-digital-evidence]
- 20. Emerging Trends and Technologies in Digital Forensics [https://www.enterprisesecuritymag.com/news/tracing-the-digital-trail-emerging-trends-and-technologies-in-digital-forensics-nid-4230-cid-59.html]
- 21. Daubert Standard | Wex | LII / Legal Information Institute [https://www.law.cornell.edu/wex/daubert_standard]
- 22. Daubert standard [https://en.wikipedia.org/wiki/Daubert_standard]
- 23. The Frye Standard | Expert Testimony, Admissibility, History [https://www.expertinstitute.com/resources/insights/admitting-expert-testimony-under-the-frye-standard-the-ultimate-guide/]
- 24. Frye standard [https://en.wikipedia.org/wiki/Frye_standard]
- 25. Daubert vs. Frye: A State-by-State Comparison [https://www.expertinstitute.com/resources/insights/daubert-versus-frye-a-national-look-at-expert-evidentiary-standards/]
- 26. Legal Requirements for Qualified Expert Evidence - Criminal Law... [https://criminalnotebook.ca/index.php/Legal_Requirements_for_Qualified_Expert_Evidence]
- 27. Kelly-Frye, Daubert, Mohan, and Why You Need to ... [https://www.axon.com/resources/kelly-frye-daubert-mohan-and-why-you-need-to-understand-these-cases]
- 28. A Tool to Navigate Hype Cycles: Technology Readiness ... [https://www.forbes.com/sites/shalinjyotishi/2025/01/27/tool-to-navigate-hype-cycles-technology-readiness-levels/]
- 29. and Manufacturing Technology : Improve... - Plexus Readiness Levels [https://www.plexus.com/blog/manufacturing-readiness-levels-aerospace-defense/]
- 30. : Assessing Technology Maturity Readiness Levels Technological [https://www.encata.net/blog/technology-readiness-levels-assessing-technological-maturity]
- 31. Your point of departure for forensic readiness [https://www.nccgroup.com/research-blog/your-point-of-departure-for-forensic-readiness/]
- 32. SoK: Timeline based event reconstruction for digital forensics [https://www.sciencedirect.com/science/article/pii/S266628172500071X]
- 33. Enhancing Traditional Reactive Digital Forensics to a ... [https://www.mdpi.com/2076-3417/15/18/9922/review_report]
- 34. Digital Forensics Round-Up, September 17 2025 [https://www.forensicfocus.com/news/digital-forensics-round-up-september-17-2025/]
- 35. Technology Readiness Levels (TRLs) Explained [https://www.grantify.io/us-articles/technology-readiness-levels-trls-explained]
- 36. What is the Chain of Custody in Digital Forensics? [https://online.champlain.edu/blog/chain-custody-digital-forensics]
- 37. Mapping digital forensic application requirement ... [https://www.sciencedirect.com/science/article/pii/S2665910720300864]
- 38. The Future of Digital Forensics: New Technologies, Methods, [https://www.linkedin.com/pulse/future-digital-forensics-new-technologies-methods-challenges-ahm5e]
- 39. Digital Forensics Round-Up, November 05 2025 [https://www.forensicfocus.com/news/digital-forensics-round-up-november-05-2025/]
- 40. Cloud Forensics Challenges: An In-depth Analysis [https://searchinform.com/articles/cybersecurity/analytics/digital-forensics/cloud-forensics/challenges/]
- 41. Cloud Forensics for Digital Investigators 2025 [https://www.investigatesc.com/cloud-forensics/]
- 42. ( Technology ) | Aalto University Readiness Level TRL [https://www.aalto.fi/en/services/technology-readiness-level-trl]
- 43. 5 Solutions for Today's Cloud Forensics Challenges [https://www.oxygenforensics.com/en/resources/cloud-forensics-challenges-solutions/]
- 44. What is Cloud Forensics? Definition, Tools & Best Practices [https://www.sentinelone.com/cybersecurity-101/cloud-security/what-is-cloud-forensics/]
- 45. How Is Digital Evidence Preserved in Modern Investigations? [https://www.amu.apus.edu/area-of-study/criminal-justice/resources/how-is-digital-evidence-preserved/]
- 46. AI as a decision support tool in forensic image analysis: A pilot study on integrating large language models into crime scene investigation workflows - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC12046100/]
- 47. Digital Forensics: Confronting Modern Cyber Crimes ... [https://www.heraldopenaccess.us/openaccess/digital-forensics-confronting-modern-cyber-crimes-technological-advancements-and-future-challenges]
- 48. Enhancing Cyber Forensics with AI and Machine Learning: A Study on Automated Threat Analysis and Classification | IIETA [https://www.iieta.org/journals/ijsse/paper/10.18280/ijsse.130412]
- 49. 6 Ways AI Can Revolutionize Digital Forensics [https://www.darkreading.com/application-security/6-ways-ai-can-revolutionize-digital-forensics]
- 50. Technology readiness levels for machine learning systems [https://www.nature.com/articles/s41467-022-33128-9]
- 51. Technology Readiness Levels (TRLs) in the Era of Co- ... [https://www.mdpi.com/2571-5577/7/2/32]
- 52. Technology Readiness Levels (TRL) in AI development [https://towardsai.net/p/l/technology-readiness-levels-trl-in-ai-development]
- 53. Digital Evidence Management Tips to Beat Court Backlog [https://www.rev.com/blog/digital-evidence-management]
- 54. Digital Evidence Management: The Ultimate Guide to ... [https://vidizmo.ai/blog/digital-evidence-management-guide]
- 55. Digital Evidence Management Challenges in 2025 and Smart ... [https://digitalevidence.ai/blog/digital-evidence-management-challenges-in-2025-and-smart-solutions]
- 56. 7 Challenges Facing Digital Forensics Teams in 2025 [https://agt-technology.com/7-challenges-facing-digital-forensics-teams-in-2025/]
- 57. Digital investigations opportunities and challenges: 2025 ... [https://www.nccgroup.com/newsroom/digital-investigations-opportunities-and-challenges-2025-cyber-trends-and-predictions/]
- 58. Technology Readiness Levels (TRLs) - AiDA - Mitre [https://aida.mitre.org/trl/]
- 59. 14 Readiness Level Frameworks: The Guide to TRL, MRL, ... [https://www.itonics-innovation.com/blog/14-readiness-level-frameworks]
- 60. Standards and best practices for digital forensics [https://www.unodc.org/cld/en/education/tertiary/cybercrime/module-4/key-issues/standards-and-best-practices-for-digital-forensics.html]
- 61. Digital Forensic Standards and Best Practices [https://eclipseforensics.com/digital-forensic-standards-and-best-practices/]
- 62. Forensic Readiness: A Crucial Element of Cybersecurity [https://www.sisainfosec.com/blogs/forensic-readiness-a-crucial-element-of-cybersecurity/]
- 63. Holistic digital forensic readiness framework for IoT- ... [https://www.sciencedirect.com/science/article/pii/S2665910720300669]
- 64. Building a Digital Forensic Readiness Framework - Jadala Ajay [https://jadala-ajay16.medium.com/building-a-digital-forensic-readiness-framework-preparing-your-business-for-cyber-incidents-7d58cf3dea6c]
- 65. Are We Ready for It? A Review of Forensic Applications and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12012292/]
- 66. Current state and barriers to global adoption of forensic ... [https://www.sciencedirect.com/science/article/pii/S1355030625001200]
- 67. Forensic Science Strategic Research Plan, 2022-2026 ... [https://nij.ojp.gov/topics/articles/forensic-sciences-strategic-research-plan-2022-2026]
- 68. 50 Statistics Every Technology Leader Should Know in 2025 [https://www.integrate.io/blog/data-transformation-challenge-statistics/]
- 69. Indicators for maturity and readiness for digital forensic ... [https://www.sciencedirect.com/science/article/abs/pii/S0167404821000614]
- 70. OSAC Standards Bulletin - January 2025 | NIST [https://www.nist.gov/magazine/osac-standards-bulletin/january-2025]
- 71. Advancing a paradigm shift in evaluation of forensic evidence [https://www.sciencedirect.com/science/article/pii/S2589871X22000559]
- 72. Uncovering hidden digital evidence: Mobile device forensics [https://www.hka.com/article/uncovering-digital-evidence-mobile-forensics/]
- 73. Digital forensics and eDiscovery: An introduction for ... [https://thomasmurray.com/insights/digital-forensics-and-ediscovery-introduction-beginners]
- 74. The Evolution of Digital Forensics [https://online.champlain.edu/blog/evolution-digital-forensics]
- 75. TECHNOLOGY READINESS LEVELS (TRLs) FOR ... [https://medicalcountermeasures.gov/trl/trls-for-medical-devices]
- 76. Digital forensic intelligence for illicit drug analysis in forensic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10582396/]
- 77. Anti-Forensics Techniques [https://www.cynet.com/attack-techniques-hands-on/anti-forensics-techniques/]
- 78. Standards and best practices for digital forensics [https://sherloc.unodc.org/cld/es/education/tertiary/cybercrime/module-4/key-issues/standards-and-best-practices-for-digital-forensics.html]
- 79. EU breaks down digital borders: New e-Evidence rules ... [https://www.whitecase.com/insight-alert/eu-breaks-down-digital-borders-new-e-evidence-rules-facilitate-cross-border]
- 80. What are TRLs? Technology Readiness Levels Explained [https://bigbangpartnership.co.uk/what-are-trls-technology-readiness-levels-explained/]
- 81. Adaptation of the technology readiness levels for impact ... [https://www.sciencedirect.com/science/article/pii/S2405844024059619]
- 82. Cross-Border Digital Evidence Management Solutions [https://vidizmo.ai/blog/cross-border-digital-evidence-management-solutions]
- 83. The right to a fair trial as a conceptual framework for digital ... [https://www.sciencedirect.com/science/article/pii/S0267364923000110]
- 84. Build Streamlined Workflows Across Your Entire DF Toolkit ... [https://www.magnetforensics.com/resources/build-streamlined-workflows-across-your-entire-df-toolkit-with-magnet/]
- 85. From Data Extraction to Courtroom: ADF's Workflow for ... [https://www.adfsolutions.com/adf-blog/from-data-extraction-to-courtroom-adf-solutions-integrated-workflow-for-digital-forensic-investigations?srsltid=AfmBOorh7ud40Mk_c7kRG9CuZ5SmwvOBL4YEym5949dYmMR1Riom4bhP]
- 86. TLR – Technology – Explained - InDro Robotics Readiness Levels [https://indrorobotics.ca/tlr-technology-readiness-levels-explained/]
- 87. Method validation in digital forensics (accessible) [https://www.gov.uk/government/publications/method-validation-in-digital-forensics/method-validation-in-digital-forensics-accessible]
- 88. | EURAXESS TRL [https://euraxess.ec.europa.eu/career-development/researchers/manual-scientific-entrepreneurship/major-steps/trl]
- 89. Validation of Forensic Tools- A Quick Guide for the DFIR ... [https://joshbrunty.github.io/2021/11/01/validation.html]
- 90. A Guide to Digital Forensics and Cybersecurity Tools (2025) [https://www.forensicscolleges.com/blog/resources/guide-digital-forensics-tools]
- 91. The Daubert Standard vs. The Frye Standard and How ... [https://www.brandonjbroderick.com/daubert-standard-vs-frye-standard-and-how-they-impact-personal-injury-cases]
- 92. Navigating Daubert vs. Frye Standards | Get The Facts [https://www.mlpime.com/daubert-standard/]
- 93. Comparing experimental conditions using modern statistics [https://link.springer.com/article/10.3758/s13428-020-01471-8]
- 94. The admissibility of digital evidence from open-source forensic ... [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0331683]
- 95. Error rates in forensic DNA analysis: Definition, numbers, ... [https://www.sciencedirect.com/science/article/abs/pii/S1872497314000908]
- 96. Beyond The Screen, Part 7: Forensic Readiness For The AI ... [https://lcgdiscovery.com/beyond-the-screen-part-7-forensic-readiness-for-the-ai-era/]
- 97. Understanding 'error' in the forensic sciences: A primer [https://www.sciencedirect.com/science/article/pii/S2589871X24000172]
- 98. 🔬 Digital Forensics in 2025: From Post-Breach Panic to ... [https://www.linkedin.com/pulse/digital-forensics-2025-from-post-breach-panic-proactive-satish-padhy-ig3bf]
- 99. Trial Tech Essentials: AI for Courtroom Presentations [https://www.nexlaw.ai/blog/ai-trial-tech-courtroom/]
- 100. Digital transformation risk management in forensic science ... [https://www.sciencedirect.com/science/article/pii/S0379073820303480]