Future-Proofing Digital Forensics: Robust Validation Strategies for Rapidly Evolving Tools in 2025
This article provides a comprehensive framework for researchers and forensic professionals to develop and implement robust validation strategies for digital forensics tools, which are evolving at an unprecedented pace.
Future-Proofing Digital Forensics: Robust Validation Strategies for Rapidly Evolving Tools in 2025
Abstract
This article provides a comprehensive framework for researchers and forensic professionals to develop and implement robust validation strategies for digital forensics tools, which are evolving at an unprecedented pace. It addresses the critical need to maintain scientific integrity and legal admissibility amidst the integration of AI, cloud computing, and disruptive technologies. Covering foundational principles, methodological applications, troubleshooting of common pitfalls, and comparative analysis techniques, the guide equips professionals to ensure their tool validation processes are as dynamic and resilient as the technologies they assess.
The Critical Need for Validation in a High-Velocity Digital Forensics Landscape
Frequently Asked Questions (FAQs)
What is forensic validation and why is it critical in digital forensics? Forensic validation is the fundamental process of testing and confirming that forensic techniques, tools, and methods yield accurate, reliable, and repeatable results [1]. It is a professional and ethical necessity because it ensures that forensic conclusions are supported by scientific integrity and are robust enough to stand in court [1]. In digital forensics, it is crucial for establishing scientific credibility and gaining legal acceptance under standards like Daubert [1]. Without it, findings can be severely undermined, leading to legal exclusion of evidence or miscarriages of justice [1].
What is the difference between tool, method, and analysis validation? Forensic validation encompasses three distinct but interconnected components [1]:
- Tool Validation: Confirms that the forensic software or hardware performs as intended, extracting and reporting data correctly without altering the original source.
- Method Validation: Confirms that the procedures and steps followed by a forensic analyst produce consistent outcomes across different cases, devices, and practitioners.
- Analysis Validation: Evaluates whether the interpreted data accurately reflects its true meaning and context, ensuring the software presents a valid representation of the underlying evidence.
How does the rapid evolution of technology impact forensic validation? The digital forensics field is evolving at an unprecedented pace due to advancements in cloud storage, AI, and mobile devices, with around 90% of all crimes now involving digital footprints [2] [3]. This demands continuous validation of tools and methods [1] [4]. Forensic tools are frequently updated, and without proper re-validation, they may introduce errors, omit critical data, or fail to handle new types of evidence from sources like IoT devices or encrypted applications [1] [2].
What are the core principles guiding forensic validation? The core principles are [1] [5]:
- Reproducibility: Results must be repeatable by other qualified professionals using the same method.
- Transparency: All procedures, software versions, logs, and chain-of-custody records must be thoroughly documented.
- Error Rate Awareness: The known error rates of forensic methods should be understood and disclosed.
- Peer Review: Validation processes should be reviewed by the broader forensic community to ensure scrutiny.
- Continuous Validation: Tools and methods must be frequently revalidated to keep pace with technological change.
Troubleshooting Guides
Issue 1: Inconsistent Results Between Forensic Tools
Problem: Two different forensic tools extracting data from the same source (e.g., a mobile phone) yield different results, casting doubt on the evidence's reliability [1].
Solution:
- Cross-Validation: Systematically compare the outputs across multiple, validated forensic tools to identify and investigate inconsistencies [1].
- Use Known Datasets: Test the tools against a "ground truth" dataset with a known and verified content to verify their parsing and extraction capabilities [1].
- Review Tool Logs: Scrutinize the logs and reports generated by each tool. Transparent and auditable logs are essential for understanding the tool's actions and identifying potential points of failure [1].
- Consult Testing Bodies: Refer to test findings from organizations like the National Institute of Standards and Technology (NIST) Computer Forensics Tool Testing (CFTT) program, which develops rigorous methodologies for tool testing [5].
Issue 2: Validating Tools in the Age of Artificial Intelligence (AI)
Problem: AI and Large Language Models (LLMs) in forensic tools can produce "black box" results that are difficult for an expert to explain or validate, challenging the principle of transparency [1] [4].
Solution:
- Do Not Blindly Trust: Treat AI-generated findings as leads, not conclusive evidence. Experts must not blindly trust automated results [1].
- Ground-Truth Verification: Use AI tools that ground their outputs in actual case artifacts. For example, an offline AI assistant like BelkaGPT processes only case-specific data, allowing an examiner to trace an AI-generated insight back to the original source evidence (e.g., a specific SMS or email) [4].
- Rigorous Interpretation: Validate and interpret AI-generated findings with the same rigor as traditional methods. This includes using the core principles of reproducibility and peer review to assess the AI's performance on your specific data [1].
Issue 3: Adhering to Standards and Ensuring Legal Admissibility
Problem: Ensuring that the validation process itself meets established legal and scientific standards to prevent evidence from being challenged or excluded in court.
Solution:
- Follow a Methodological Approach: Adopt a structured validation process that includes planning, execution, and thorough documentation to ensure thoroughness and repeatability [5]. The process should include requirements analysis, unit testing, integration testing, system testing, and validation testing against legal standards [5].
- Leverage Established Frameworks: Utilize guidelines and best practices from authoritative bodies such as SWGDE (Scientific Working Group on Digital Evidence) and the NIST CFTT program [6] [5].
- Implement Comprehensive Documentation: Maintain detailed documentation of the entire validation process, including the test plan, test cases, procedures, and results. This provides transparency and facilitates auditing [5]. Reports should disclose fundamental principles, methodology, limitations, and areas of scientific controversy to meet calls for increased transparency [7].
Experimental Protocols and Workflows
Protocol 1: Core Digital Forensics Tool Validation
This methodology is based on the NIST CFTT framework and general forensic validation principles [5].
Objective: To verify that a digital forensics tool (e.g., Cellebrite UFED, Magnet AXIOM) accurately acquires, extracts, and reports data from a digital source.
Materials:
- Device or forensic image for testing (e.g., a smartphone with known data).
- The forensic tool to be validated.
- A second, previously validated tool for cross-comparison.
- Hashing utility (e.g., within ProDiscover or FTK Imager).
- Write-blocking hardware.
Procedure:
- Preparation: Create a controlled test environment. Using a write-blocker, create a forensic image (e.g., .dd or .E01 file) of the source device.
- Integrity Verification: Generate a cryptographic hash (e.g., SHA-256) of the source evidence and the acquired image. The hashes must match to prove data integrity [1] [8].
- Tool Execution: Process the forensic image using the tool under test. Execute its key functions, such as file system parsing, data carving, and keyword searching.
- Output Analysis: Document all findings from the tool. Pay close attention to any errors, omissions, or unexplained anomalies in the report.
- Cross-Validation: Process the same forensic image using a second, validated tool. Compare the outputs from both tools for consistency.
- Documentation: Record every step, tool version, configuration, and result. This log is critical for transparency and reproducibility [1].
Protocol 2: Image and Video Authentication Examination
This protocol is derived from SWGDE's Best Practices for Image Authentication [6].
Objective: To determine if a questioned image or video is an accurate representation of the original data or if it has been manipulated.
Materials:
- The questioned image or video file.
- Forensic multimedia analysis tools (e.g., Amped Authenticate, Adobe Photoshop).
- Metadata extraction tools (e.g., ExifTool).
- Hashing algorithm utility.
Procedure:
- Evidence Integrity: Verify the integrity of the submitted file by comparing its hash value with any available original hash [8].
- Metadata Analysis: Extract and analyze all embedded metadata (EXIF, etc.) for inconsistencies, such as mismatched dates or editing software tags [8].
- Error Level Analysis (ELA): Perform ELA to identify areas of an image that may have been altered by showing different compression levels.
- Clone Detection: Use specialized algorithms to detect regions of an image that may have been copied and pasted (compositing) [6].
- Computer-Generated Imagery (CGI) Detection: Examine the image for tell-tale signs of CGI, such as unrealistic skin textures, inconsistencies in lighting and shadows, or anatomical inaccuracies [6].
- Format-Specific Artifacts: Look for artifacts specific to the file format and compression that may indicate tampering.
The Scientist's Toolkit: Essential Research Reagents & Materials
The following table details key resources and their functions in forensic validation research.
| Research Reagent / Material | Function in Forensic Validation |
|---|---|
| NIST CFTT Framework [5] | Provides standardized methodologies, test claims, and case categories for the objective testing of computer forensic tools. |
| SWGDE Guidelines [6] | Offers published best practices, standards, and technical notes for digital and multimedia forensics, such as image authentication. |
| Forensic Software Suites (e.g., Cellebrite, Magnet AXIOM, Belkasoft X) [1] [4] | The primary tools under test; used for data acquisition, parsing, and analysis from various digital sources. |
| Validated Hash Algorithms (e.g., SHA-256, MD5) [1] [8] | Creates a unique digital fingerprint for data to verify evidence integrity before and after examination. |
| Known Test Datasets & Images [1] [5] | Serves as "ground truth" evidence with verified content to test a tool's accuracy and performance. |
| Cross-Validation Tools [1] | A second, independently validated tool used to compare results and identify inconsistencies in the primary tool's output. |
The table below summarizes key quantitative requirements and metrics relevant to forensic validation and related digital evidence handling.
| Metric / Requirement | Standard / Threshold | Applicable Context |
|---|---|---|
| WCAG Text Contrast (Minimum) [9] | 4.5:1 (normal text), 3:1 (large text) | Accessibility of forensic software interfaces and generated reports. |
| WCAG Non-text Contrast (Minimum) [9] | 3:1 | Contrast for user interface components and graphical objects in software. |
| Average Data on a Smartphone [3] | >60,000 messages, >32,000 images, >1,000 videos | Illustrates the data volume and complexity faced in modern mobile forensics. |
| Forensic Result Reproducibility [5] | Must produce same results on same equipment (repeatable) and similar results on different systems (reproducible). | Core principle for scientific credibility and legal admissibility. |
Troubleshooting Guides
Guide 1: Troubleshooting Common Validation Gaps
Problem: A forensic tool update has altered how it parses a specific application's database, potentially creating inaccurate evidence.
| Symptom | Potential Cause | Diagnostic Action | Solution |
|---|---|---|---|
| Tool output differs from a known dataset. | Tool algorithm change; Data corruption. | Run tool against a control set of known data; Calculate hash values for integrity [1]. | Revert to a validated tool version; Use a different tool for cross-validation [1]. |
| An expert cannot explain the methodology behind a tool's output. | Over-reliance on "black box" automated tools, especially AI-based ones [10]. | Require the expert to document the tool's function and their own validation steps. | Ensure the expert's testimony reflects a reliable application of the methodology to the facts [11]. |
| Evidence is excluded due to unreliable application of method. | Failure to demonstrate the "good grounds" for the expert's opinion [12]. | Pre-trial Daubert hearing to review the expert's basis and application. | The proponent must show the testimony is based on sufficient facts/data per Rule 702 [11]. |
Guide 2: Troubleshooting Daubert and Rule 702 Challenges
Problem: A motion to exclude your digital forensic expert testimony has been filed under Daubert/Rule 702.
| Symptom | Potential Cause | Diagnostic Action | Solution |
|---|---|---|---|
| Court questions if the method is "product of reliable principles." | Use of a novel or non-peer-reviewed technique. | Identify published standards, peer-reviewed literature, or general acceptance for the method. | Cite the tool's forensic validation studies and its widespread use in the field [1]. |
| Opposing counsel argues the expert's opinion is incorrect. | Conflating the questions of admissibility and correctness [11]. | Distinguish the reliability of the method from the accuracy of the conclusion. | Argue that the "evidentiary requirement of reliability is lower than the merits standard of correctness" [11]. |
| Court failed to provide a rationale for admitting expert testimony. | Inadequate record for appellate review [12]. | Ensure all admissibility decisions and the reasoning behind them are documented. | Create a clear record showing the court fulfilled its gatekeeping role [12]. |
Frequently Asked Questions (FAQs)
On Validation and Error
Q1: What is the core purpose of forensic validation in a legal context? Forensic validation ensures that the tools and methods used to analyze evidence are accurate, reliable, and legally admissible. It acts as a fundamental safeguard against error and bias, helping to establish scientific credibility and gain acceptance under legal standards like Daubert [1].
Q2: What are the key components of a robust validation process? A robust validation process includes three key components [1]:
- Tool Validation: Confirming that the forensic software or hardware performs as intended without altering the source data.
- Method Validation: Verifying that the analytical procedures produce consistent outcomes across different cases and practitioners.
- Analysis Validation: Ensuring that the interpreted data accurately reflects its true meaning and context.
Q3: What is a real-world example of an operational error due to inadequate validation? In Florida v. Casey Anthony, the prosecution's digital forensic expert initially testified that 84 searches for "chloroform" were made on a computer. Through defense-led validation, it was shown the forensic software had grossly overstated this number; only a single search had occurred. This highlights how tool error can dramatically alter a case's narrative [1].
On Legal Admissibility
Q4: What was the significance of the 2023 amendment to Federal Rule of Evidence 702? The 2023 amendment clarified and emphasized two key points [11]:
- The proponent of expert testimony must prove its admissibility by a preponderance of the evidence (the "more likely than not" standard).
- The expert's opinion must reflect a reliable application of principles and methods to the case's facts. This was a textual change to reinforce that experts must "stay within the bounds" of what their basis and methodology can support.
Q5: How does the recent EcoFactor v. Google decision impact digital forensic experts? The May 2025 Federal Circuit decision in EcoFactor tightens the standard for expert testimony, particularly on the sufficiency of underlying data. The court ordered a new trial because the expert's opinion on royalty rates was contrary to the plain language of the license agreements he relied on. This signals that courts will more strictly exclude testimony not grounded in sufficient facts and data [12].
Q6: What is the difference between a question of admissibility and a question of weight? This is a critical distinction [11]:
- Admissibility: A question for the judge. Is the expert's testimony reliable enough to be presented to the jury? This is governed by Rule 702 and Daubert.
- Weight: A question for the jury. How much credibility should the jury give to the expert's testimony? Attacks on the expert's conclusions are typically matters of weight, but only after the testimony has been deemed admissible.
Experimental Protocols for Validation
Protocol 1: Validating a Digital Forensics Tool After an Update
Objective: To confirm that a forensic tool (e.g., Cellebrite UFED, Magnet AXIOM) accurately extracts and parses data after a software update.
Methodology:
- Create a Control Dataset: Using clean devices, generate a known set of artifacts (e.g., SMS messages, emails, app data) and document them thoroughly [1].
- Acquire Evidence: Use the updated tool to extract data from the control devices. Use hash values (e.g., SHA-256) to verify the integrity of the acquired image [1].
- Analyze and Compare: Run the tool's analysis on the extracted image. Compare the output against the known control dataset.
- Cross-Validate: Use a different, previously validated tool to analyze the same control dataset [1].
- Document Results: Record any discrepancies, tool version, and all steps taken. This documentation is crucial for transparency and court testimony [1].
Protocol 2: Establishing a Reliable Methodology for Expert Testimony
Objective: To build a methodology for expert analysis that meets the admissibility standards of Rule 702 and Daubert.
Methodology:
- Define the Scope: Clearly outline the boundaries of the examination based on the case facts.
- Select Tools and Methods: Choose tools and methods that are generally accepted in the field or have been peer-reviewed. Justify this selection.
- Apply the Method: Execute the analysis, ensuring every step is documented and reproducible by another qualified professional [1].
- Interpret Findings: Form an opinion based strictly on the output of the analysis, ensuring it "stays within the bounds" of what the methodology can support [11].
- Prepare for Testimony: Be ready to explain the "good grounds" for the opinion, including the tool's validation, the method's reliability, and the steps taken to ensure a reliable application to the facts [12].
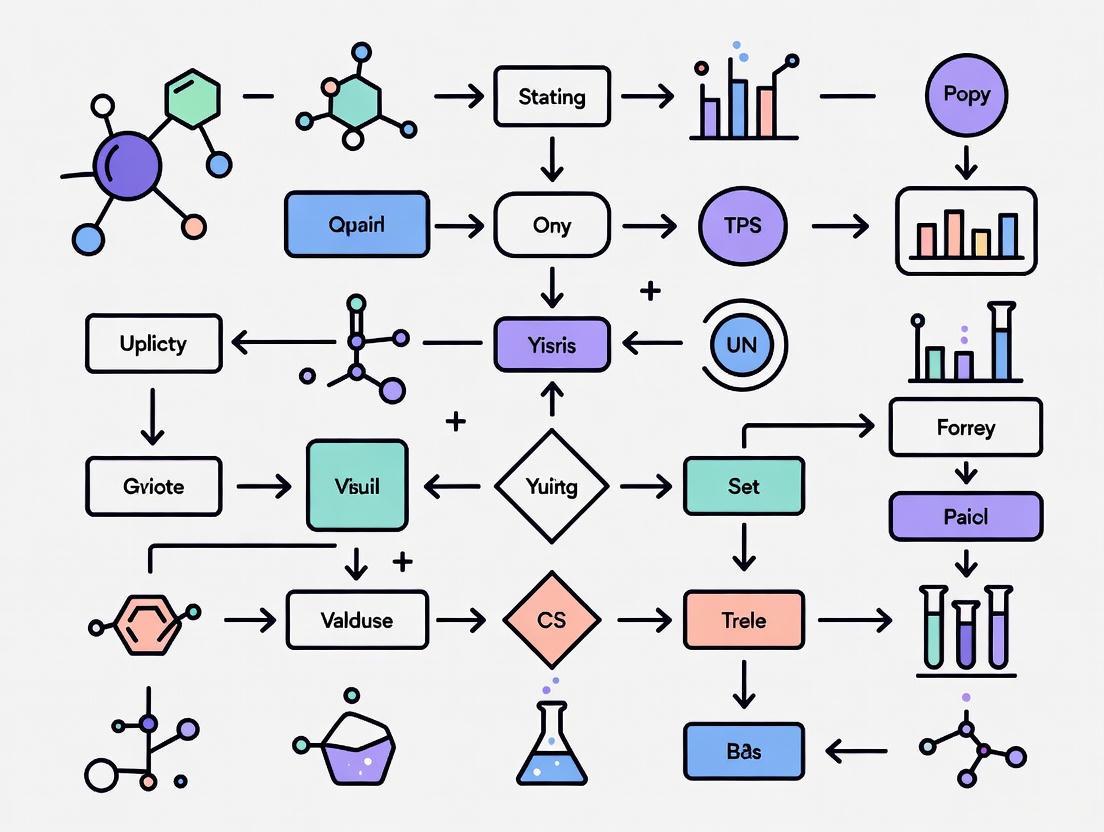
Workflow Visualization
Digital Forensics Admissibility Workflow
The Scientist's Toolkit: Essential Research Reagents for Digital Forensics
This table details key solutions and materials essential for conducting validated digital forensic research and analysis.
| Item | Function & Purpose |
|---|---|
| Validated Forensic Suites (e.g., Cellebrite, Magnet AXIOM, Belkasoft) | Core software for acquiring, analyzing, and reporting on digital evidence. Regular validation ensures their accuracy and reliability in court [1] [4]. |
| Hash Value Algorithms (e.g., SHA-256, MD5) | Cryptographic functions used to verify the integrity of digital evidence, proving it was not altered during the acquisition or analysis process [1]. |
| Control Datasets | Known sets of digital artifacts used to test and validate the output of forensic tools, helping to identify errors after tool updates [1]. |
| Cross-Validation Tools | A second, independent forensic tool used to verify the results of the primary tool, identifying potential tool-specific errors or omissions [1]. |
| AI-Assisted Analysis Tools (e.g., BelkaGPT) | Offline AI tools that help analyze massive volumes of text-based evidence (chats, emails) for patterns and topics, while maintaining evidence integrity and privacy [4]. |
| Comprehensive Logging Systems | Meticulous documentation of all procedures, tool versions, and analyst actions. This ensures transparency, reproducibility, and provides a clear audit trail [1]. |
Your Technical Support Center
This guide provides troubleshooting support for researchers and scientists validating digital forensics tools in a landscape being reshaped by AI, complex cloud environments, and advanced encryption.
Troubleshooting Guides
Issue 1: Inability to Access or Analyze Cloud Data for an Investigation Researchers often face hurdles when forensic data resides in complex, distributed cloud environments [10] [13].
Troubleshooting Steps:
- Identify Data Jurisdiction: First, determine the cloud service provider (CSP) and the geographic location of the data servers. Cross-border data laws can severely restrict access [10] [13].
- Formalize Legal Request: Collaborate with your legal department to submit a formal data request to the CSP, ensuring compliance with relevant regulations like GDPR or the U.S. CLOUD Act [10] [13].
- Leverage Cloud APIs: Use forensic tools that can interact with cloud APIs (e.g., from AWS, Azure, GCP) to extract log and metadata, rather than relying on physical disk imaging [13].
- Preserve Ephemeral Data: Prioritize collecting volatile data from temporary resources like containers, as they can be destroyed quickly based on automated policies [13].
Validation Protocol: To validate a new cloud forensic tool, create a controlled test environment within a major cloud platform. Populate it with sample data fragments across different services (e.g., object storage, virtual machines) and run the tool. A valid tool should successfully identify and reassemble these data fragments from different locations via API calls, providing a coherent evidence timeline.
Issue 2: AI Tool Fails to Properly Identify Deepfake Media in Clinical Trial Data The proliferation of AI-generated synthetic media is a major challenge, and analysis tools must be constantly updated [10].
Troubleshooting Steps:
- Verify Training Data: Confirm that the AI model powering your tool was recently trained on a diverse and current dataset of deepfakes. Outdated models cannot detect new generation techniques [10].
- Check for Algorithm Transparency: Be aware that "black box" AI models can undermine the credibility of findings in a scientific or legal context. Seek tools that provide some level of explainability for their decisions [10].
- Cross-Reference with Metadata: Do not rely solely on the AI's output. Perform a manual check of the file's digital metadata (e.g., EXIF data) for inconsistencies in creation times and device signatures.
- Update or Supplement Tooling: If the tool consistently fails, it may be necessary to procure a more advanced tool or use specialized, validated services for deepfake detection, which have achieved accuracy rates up to 92% in controlled tests [10].
Validation Protocol: To test a deepfake detection tool, assemble a verified dataset containing both authentic and AI-generated images/videos. The dataset should include samples generated by the latest publicly available AI models. Run the tool against this dataset and measure its accuracy, precision, and recall. A robust tool must perform with high accuracy (e.g., >90%) to be considered valid for research integrity purposes [10].
Issue 3: Encrypted Data Obstructs Critical Forensic Timeline Strong encryption can render data unrecoverable without the keys, halting an investigation [14] [15] [16].
Troubleshooting Steps:
- Attempt Key Recovery: Before technical attacks, always investigate if the password or key is available from the user, involved parties, or associated password managers [15].
- Assess Encryption Type: Identify the encryption technology used. Note that techniques like Honey Encryption can deceive brute-force attacks by producing plausible-looking but incorrect data, confusing the investigator [14].
- Evaluate Computational Feasibility: For strong, modern encryption (e.g., AES-256), brute-force decryption is often computationally infeasible and can take an extremely long time, even with sophisticated software [15].
- Consider Alternative Evidence: If the data cannot be decrypted, pivot to analyzing unencrypted metadata, cloud access logs, or communication records from the same individual to build an alternative timeline [13].
Validation Protocol: To validate a tool's capability against encrypted data, create encrypted containers or disks using different algorithms (e.g., AES-256, Blowfish) and key strengths. A tool's validity should not be measured solely on its ability to crack encryption (which is often impossible), but on its ability to correctly identify the encryption in use, safely mount encrypted drives for imaging when keys are available, and integrate with other investigative workflows.
Frequently Asked Questions (FAQs)
Q1: How can we trust the results from an AI-based forensics tool when the technology is changing so fast? Trust is built through continuous validation. AI models, especially "black box" systems, can lack transparency [10]. Establish a routine where you test new AI tools against a benchmark dataset with known outcomes before applying them to live research data. Focus on tools that provide details on their training data and algorithms.
Q2: Our data is spread across multiple cloud providers (multi-cloud). What is the biggest forensic challenge this creates? The primary challenge is fragmentation and complexity [17] [13]. Data is distributed across different platforms with varying security controls, logging formats, and data access APIs. This makes it difficult to get a unified view of evidence. Furthermore, legal jurisdictions for data stored in different geographic regions can complicate and delay evidence collection [10] [13].
Q3: With the rise of quantum computing, is our current encrypted data safe? There is a growing concern about the "harvest now, decrypt later" threat, where adversaries collect encrypted data today to decrypt it later when quantum computers become powerful enough [18]. This is driving the transition to post-quantum cryptography (PQC). NIST has released new PQC standards, and organizations are now beginning to inventory and plan upgrades for their cryptographic systems [18].
Q4: What is the most common misconception about digital evidence? A common misconception is that anything stored on a digital device can always be retrieved [15]. In reality, overwritten or physically damaged data can be permanently lost. Furthermore, opening files directly on a suspect device can change file metadata (like "last accessed" times), potentially tampering with evidence and rendering it inadmissible. Only trained investigators with proper tools should handle original evidence [15].
Quantitative Data on the Changing Landscape
Table 1: The State of AI Adoption and Impact (2025) This table summarizes key data on how organizations are using AI, highlighting both its broadening use and the challenges in scaling it effectively [19].
| Metric | Value | Implication for Researchers |
|---|---|---|
| Organizations using AI | 88% | AI tools are becoming standard, making their validation critical. |
| Organizations scaling AI | ~33% | Most are still in early phases, so best practices are still emerging. |
| Experiencing EBIT impact | 39% | Measuring tangible value from AI remains a challenge for many. |
| AI-driven innovation | 64% | The primary benefit is often qualitative improvement in capabilities. |
| Expecting workforce decrease | 32% | AI is expected to impact staffing models, potentially automating some tasks. |
Table 2: Emerging Encryption Technologies & Trends This table outlines advanced encryption methods that are redefining what is possible to secure and, therefore, to forensically examine [14] [16] [18].
| Technology | Core Principle | Research & Forensic Consideration |
|---|---|---|
| Homomorphic Encryption | Allows computation on encrypted data without decrypting it first [14]. | Could allow analysis of private genomic/patient data without violating privacy, but also prevents direct forensic inspection of the underlying data. |
| Honey Encryption | Deceives attackers by returning plausible-looking fake data when wrong keys are used [14]. | Could misdirect an investigation by providing false leads and wasting computational resources. |
| Multi-Party Computation (MPC) | Splits data into parts for separate servers; no single server has the complete dataset [14]. | Complicates evidence gathering as data is inherently fragmented and requires cooperation from multiple entities. |
| Post-Quantum Crypto (PQC) | Algorithms designed to be secure against attacks from both classical and quantum computers [18]. | Preparing for a future where current encryption standards may be broken, ensuring long-term data confidentiality. |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Digital Forensics "Reagents" for Tool Validation This table details key materials and tools required for rigorous experimentation and validation of digital forensics methodologies.
| Item | Function in Validation |
|---|---|
| Forensic Disk Images | A pristine, bit-for-bit copy of a storage device. Used as a standardized, repeatable baseline to test and compare the data extraction and analysis capabilities of different tools. |
| Verified Data Set (e.g., for AI/Deepfakes) | A collection of digital files (images, video, documents) where the ground truth (e.g., authentic vs. synthetic) is known. Essential for benchmarking the accuracy and reliability of AI-based analysis tools. |
| Cloud API Simulator | A controlled environment that mimics the APIs of major cloud providers (AWS, Azure, GCP). Allows for safe, legal, and repeatable testing of cloud forensic tools without interacting with live, production systems. |
| Encrypted Test Vectors | A set of files and containers encrypted with known algorithms (AES, RSA, etc.) and passwords. Critical for validating a tool's ability to handle, identify, and support the analysis of encrypted data. |
| Log Generator | Software that produces standardized, synthetic log data simulating various application and security events. Used to test the performance and parsing accuracy of tools that perform timeline reconstruction and anomaly detection. |
Workflow: Tool Validation in a Changing Landscape
The following diagram maps the logical workflow for validating a digital forensics tool against the challenges posed by AI, cloud, and encryption. This process emphasizes adaptability and continuous testing.
In the rapidly evolving field of digital forensics, the validation of tools and methodologies is paramount for ensuring the reliability of evidence in criminal investigations and legal proceedings. This technical support center resource analyzes documented failures in digital evidence validation through a series of case studies, extracting critical troubleshooting guidance for researchers and forensic professionals. The content is structured to directly address common experimental and operational challenges, providing actionable protocols to strengthen validation frameworks against technological obsolescence and methodological flaws.
Case Analysis: Documented Failures in Digital Evidence
The following table summarizes key real-world instances where digital evidence validation failures compromised judicial outcomes.
| Case | Nature of Digital Evidence | Validation Failure | Consequence | Quantitative Impact |
|---|---|---|---|---|
| David Camm [20] | Phone call logs & email metadata | Flawed timeline analysis; misinterpreted digital timestamps | Wrongful conviction; two trials over a decade | Multiple erroneous timestamps led to wrongful incarceration for years [20] |
| Amanda Knox [20] | Phone records & internet browsing history | Forensic tools failed to correctly interpret phone records; data misread | Wrongful implication and conviction | Initial claim of 84 searches for "chloroform"; validated result: 1 search [1] |
| Casey Anthony [1] | Computer search history | Forensic software (tool validation error) grossly overstated search term frequency | Misleading evidence presented to jury | |
| FBI Audio Evidence [20] | Audio recording for voice analysis | Flawed forensic techniques; unreliable voice matching on poor-quality audio | Risk of wrongful conviction; suspect acquitted | Reliance on unvalidated audio analysis technique [20] |
| "Phantom" IP Address [20] | IP address logs for cybercrime location | Relying solely on IP logs without validating for spoofing | Wrongful arrest | IP address was spoofed, not from accused's device [20] |
Troubleshooting FAQs: Addressing Common Validation Challenges
1. Our forensic tool extracted data, but the output seems inconsistent with the device's activity log. How do we troubleshoot this?
This indicates a potential tool validation failure. The core issue is that the forensic tool may not have accurately parsed the data structure from the specific device or operating system version [1].
- Step 1: Verify Tool Version and Scope. Confirm that your tool version is certified for the evidence source (e.g., specific smartphone model and OS version). Check the vendor's release notes for known issues or parsing limitations [1].
- Step 2: Cross-Validate with a Secondary Tool. Use a different forensic tool or a custom script to extract and parse the same data set. Compare the outputs for discrepancies [1].
- Step 3: Examine Raw Hexadecimal Data. Use a hex editor to view the raw data from the evidence image. Manually verify the data structure and compare it against the tool's parsing results to identify where the misinterpretation occurred [1].
- Solution: Implement a rigorous tool validation protocol before use on evidence, testing tools against known datasets with verified answers [1].
2. How can we definitively determine if a key audio file has been edited or tampered with before we base our analysis on it?
This is a core function of audio authentication services. The process involves a methodological analysis to detect anomalies.
- Step 1: Check File Metadata and Hash Value. Analyze the file's header, container structure, and creation metadata for inconsistencies. Calculate a hash value upon receipt to ensure integrity during your examination [20].
- Step 2: Waveform and Spectral Analysis. Visually inspect the audio waveform for abrupt silences, unnatural clipping, or abrupt transitions. Use spectral analysis to look for gaps in the frequency background that suggest splices [20].
- Step 3: Electrical Network Frequency (ENF) Analysis. Compare the embedded power grid frequency in the recording with a database of historical ENF data. Inconsistent ENF patterns can indicate editing or composite recording [20].
- Solution: Establish a standard operating procedure for audio authentication that includes these technical checks to validate the integrity of audio evidence before deep-content analysis [20].
3. Our investigation hinges on a file's metadata (e.g., creation timestamp), but the defense is challenging its reliability. How do we defend our interpretation?
This challenge attacks the analysis validation component. Your defense must demonstrate that your interpretation is accurate and accounts for variables.
- Step 1: Acknowledge and Explain Inherent Variables. Proactively address factors that affect metadata: time zone configurations, clock drift of the source device, system updates that alter timestamps, and user-driven changes [21].
- Step 2: Corroborate with Multiple Data Sources. Do not rely on a single metadata point. Corroborate the timeline using network logs, application artifacts, and metadata from other related files to build a consistent narrative [21].
- Step 3: Document Your Validation Methodology. Detail the steps taken to validate the metadata, including the tools used and their known error rates, and your reasoning for dismissing alternative explanations [1] [22].
- Solution: Build a multi-faceted timeline of events. The strength of your conclusion comes from the convergence of multiple validated data points, not from a single piece of metadata [21].
Experimental Protocol: Implementing a Core Validation Strategy
This protocol provides a detailed methodology for cross-tool validation, a critical experiment to ensure result reliability.
Objective: To validate the accuracy and completeness of data extracted from a digital evidence source by comparing the outputs of multiple forensic tools.
Principle: Forensic findings must be reproducible and not an artifact of a single tool's functionality or bug [1].
Materials & Reagents:
- Evidence Source: A forensically sound image (e.g.,
.ddor.E01file) of the device under investigation. - Primary Forensic Tool: Your standard tool (e.g., Cellebrite UFED, Magnet AXIOM, MSAB XRY).
- Secondary Forensic Tool(s): At least one alternative tool from a different vendor or an open-source alternative (e.g., Autopsy).
- Hardware: A dedicated, forensically sterile examination workstation.
- Hashing Utility: (e.g.,
md5deep,HashMyFiles) to verify data integrity.
Step-by-Step Methodology:
Evidence Integrity Verification:
- Before any processing, calculate the hash value (MD5, SHA-1) of the evidence image and verify it matches the hash taken at the time of acquisition. Document this match [1].
Tool Configuration and Execution:
- Primary Tool Analysis: Process the evidence image through your primary tool using a standard parsing profile. Export a detailed report of key artifacts (e.g., call logs, messages, specific files).
- Secondary Tool Analysis: Process the same evidence image through the secondary tool(s), using a comparable parsing profile. Export a similar report.
Data Comparison and Analysis:
- Artifact Count: Compare the number of artifacts recovered for each category (e.g., SMS, photos, emails) between the tools. Note any significant discrepancies.
- Content Fidelity: For a sample of critical artifacts, perform a deep comparison. Check for consistency in content, timestamps, and associated metadata.
- Error Logging: Document any parsing errors or warnings reported by each tool.
Interpretation and Reporting:
- Consistency: If tool outputs are consistent, this strengthens the validity of the findings.
- Inconsistency: If discrepancies are found, do not default to the primary tool. Investigate the root cause by checking raw data or using a third tool. Document the investigation and justify the final conclusion based on all available data [1].
Workflow Visualization: Digital Evidence Validation Framework
The following diagram illustrates the logical workflow for a comprehensive digital evidence validation process, integrating technology, methodology, and analysis checks.
This table details key "research reagent solutions" and their functions in the context of digital forensics validation.
| Tool / Material | Primary Function | Role in Validation |
|---|---|---|
| Forensic Write Blockers | Hardware/software to prevent evidence alteration during acquisition. | Ensures the integrity of the source evidence, which is the foundation of all subsequent validation [23]. |
| Hashing Algorithms (MD5, SHA-256) | Generate unique digital fingerprints for data. | Core to verifying evidence integrity throughout the investigative process; any change alters the hash [1] [23]. |
| Cross-Validation Software Suite | Multiple forensic tools from different vendors (e.g., Cellebrite, Magnet AXIOM). | Allows for comparative analysis to identify tool-specific errors or omissions, a key validation practice [1]. |
| Forensic Image Files (.E01, .dd) | Bit-for-bit copies of digital storage media. | Serve as the standardized, pristine input for all tool testing and validation experiments [23]. |
| Known Test Datasets | Curated datasets with pre-identified artifacts and known answers. | The "control group" for testing and validating forensic tools and methods against expected results [1]. |
| Hex Editors | Software to view and manipulate raw hexadecimal data of a file. | Enables manual verification of tool output by inspecting the raw data structure, bypassing tool interpretation [24]. |
| Standard Operating Procedure (SOP) Documents | Detailed, step-by-step protocols for forensic processes. | Ensures method validation by enforcing consistency, reproducibility, and adherence to best practices [22] [23]. |
Building a Dynamic Validation Framework: From Tool Testing to AI Interpretation
In digital forensics, validation is the fundamental process of testing and confirming that forensic techniques and tools yield accurate, reliable, and repeatable results. For researchers and professionals, establishing a rigorous validation protocol is critical for ensuring the scientific integrity and legal admissibility of digital evidence, especially given the rapid evolution of digital technologies and tools [1].
A comprehensive validation framework encompasses three distinct but interconnected components:
- Tool Validation: Ensuring forensic software or hardware performs as intended without altering source data.
- Method Validation: Confirming investigative procedures produce consistent outcomes across different cases and practitioners.
- Analysis Validation: Evaluating whether interpreted data accurately reflects its true meaning and context [1].
The V3 Validation Framework: Verification, Analytical Validation, and Clinical Validation
The V3 Framework, developed by the Digital Medicine Society (DiMe) and adapted for forensic contexts, provides a structured approach to building evidence that supports the reliability and relevance of digital measures and tools [25]. This holistic framework is particularly valuable for validating novel tools incorporating artificial intelligence and machine learning.
Core Components of the V3 Framework
Table 1: The Three Components of the V3 Validation Framework
| Component | Definition | Primary Focus | Key Question |
|---|---|---|---|
| Verification | Ensures digital technologies accurately capture and store raw data [25]. | Technical performance of data acquisition systems. | Does the tool correctly record and preserve the raw source data? |
| Analytical Validation | Assesses the precision and accuracy of algorithms that transform raw data into meaningful metrics [25]. | Data processing algorithms and their outputs. | Does the algorithm correctly and reliably process raw data into a meaningful output? |
| Clinical Validation | Confirms that digital measures accurately reflect the relevant biological or functional states for their intended context of use [25]. | Biological/functional relevance and real-world applicability. | Does the output accurately represent the real-world phenomenon it claims to measure? |
Essential Research Reagents and Tools
Table 2: Digital Forensics Tools and Their Functions in Validation Research
| Tool Name | Primary Function | Role in Validation |
|---|---|---|
| Autopsy | Digital forensics platform and graphical interface for comprehensive device analysis [26]. | Validates method reproducibility through timeline analysis, hash filtering, and keyword search capabilities. |
| Cellebrite UFED | Extracts and analyzes data from mobile devices, cloud services, and computers [26]. | Serves as a reference tool for cross-validation and tool output comparison. |
| Magnet AXIOM | Collects, analyzes, and reports evidence from multiple digital sources [26]. | Enables validation of analytical workflows across different data types and sources. |
| Bulk Extractor | Scans files, directories, or disk images to extract specific information without parsing file systems [26]. | Provides independent verification of data extraction completeness and accuracy. |
| FTK Imager | Creates forensic images of digital media while preserving original evidence integrity [26]. | Establishes baseline for tool verification by ensuring evidence integrity before analysis. |
| ExifTool | Reads, writes, and edits metadata in various file types [26]. | Validates metadata extraction and interpretation across different file formats. |
| X-Ways Forensics | Analyzes file systems, individual files, and disk images with support for multiple file systems [26]. | Enables cross-tool validation through its support for diverse file systems and hashing functions. |
Troubleshooting Guides and FAQs
Tool Validation Issues
Q: How do I handle inconsistent results between different forensic tools analyzing the same evidence?
A: Inconsistent tool outputs indicate a potential tool validation failure. Follow this protocol:
- Establish a baseline: Use a forensic imager like FTK Imager to create a verified bit-for-bit copy of the evidence [26].
- Calculate hash values (MD5, SHA-256) for the evidence before and after imaging to confirm data integrity [1].
- Run controlled tests with known datasets on both tools to identify parsing discrepancies.
- Document all variations including software versions, operating environments, and configuration settings [1].
- Escalate to vendor support with detailed documentation of the inconsistencies for investigation.
Q: What should I do when a tool update breaks existing validation?
A: Tool updates require revalidation:
- Maintain previous versions of tools alongside new versions during transition periods.
- Perform comparative testing using standardized test cases with both versions.
- Document version-specific behaviors and update validation protocols accordingly.
- Implement continuous validation practices where tools are regularly tested against benchmark datasets [1].
Method Validation Challenges
Q: How can I ensure my analytical methods remain valid when dealing with encrypted applications?
A: Encryption challenges require method adaptation:
- Document method limitations explicitly when encryption prevents complete data access.
- Focus on accessible artifacts such as metadata, cache files, and behavioral data.
- Use multiple complementary tools to extract and correlate available evidence.
- Validate against known scenarios where ground truth is established to verify method effectiveness on accessible data points.
- Peer review methods to ensure they meet current professional standards despite limitations [1].
Q: What is the proper response when quality control checks fail during method validation?
A: Failed QC checks require immediate action:
- Stop all analytical work using the method until the issue is resolved.
- Investigate root causes including reagent integrity, instrument calibration, analyst competency, and environmental factors.
- Implement corrective actions based on root cause analysis.
- Revalidate the method after corrections to demonstrate restored performance.
- Document everything including the failure, investigation, corrective actions, and revalidation results.
Analysis Validation Problems
Q: How should I address potential AI algorithm "black box" issues in newer forensic tools?
A: Unexplainable AI outputs require rigorous validation:
- Demand transparency from vendors about training data, algorithms, and potential biases.
- Conduct ground truth testing where algorithm outputs are compared against manually verified results.
- Establish known error rates for the specific tool and context of use [1].
- Use alternative methods to verify AI-generated findings rather than relying solely on automated results [1].
- Document all verification steps to demonstrate due diligence in addressing black box limitations.
Q: What steps are necessary when digital evidence authenticity is challenged due to deepfake potential?
A: Deepfake challenges require enhanced validation protocols:
- Implement deepfake detection tools that identify subtle inconsistencies in media files.
- Use cryptographic verification where possible (digital signatures, blockchain timestamps).
- Corroborate with multiple evidence sources to establish consistency across different data types.
- Document chain of custody meticulously to eliminate opportunities for evidence tampering.
- Consult specialized tools for media authentication and maintain expertise in emerging manipulation techniques [2].
Case Examples: Validation Failures and Solutions
Case Study 1: Florida vs. Casey Anthony (2011)
Problem: A digital forensics expert initially testified that 84 searches for "chloroform" had been conducted on the Anthony family computer, suggesting extensive planning. This number was later challenged through rigorous validation [1].
Validation Solution: Defense experts forensically validated the actual search data and discovered the forensic software had grossly overstated the number of searches. Their analysis confirmed only a single instance of the search term had occurred [1].
Lesson: Never trust tool outputs without independent validation. Always verify critical findings through multiple methods and tools.
Case Study 2: Massachusetts vs. Karen Read (2025)
Problem: Mobile device timestamps and data artifacts required careful interpretation as operating system logs could be misleading without proper context [1].
Validation Solution: Cellebrite Senior Digital Intelligence Expert Ian Whiffin conducted tests across multiple devices to ensure the accuracy of his conclusions, demonstrating the necessity of thorough validation processes in forensic analysis [1].
Lesson: Context is critical in digital forensics. Validate tool outputs against known device behaviors and environmental factors.
Core Principles of Forensic Validation
Regardless of the specific tools or methods being validated, all forensic validation protocols should adhere to these core principles [1]:
- Reproducibility: Results must be repeatable by other qualified professionals using the same method.
- Transparency: All procedures, software versions, logs, and chain-of-custody records must be thoroughly documented.
- Error Rate Awareness: Forensic methods should have known error rates that can be disclosed in reports and during testimony.
- Peer Review: Validation processes should be reviewed by the broader forensic community.
- Continuous Validation: Because technology evolves rapidly, tools and methods must be frequently revalidated.
Frequently Asked Questions (FAQs)
Q1: Why can't I just rely on the results from a single, reputable digital forensics tool? Digital forensics tools, while sophisticated, are not infallible. They can suffer from parsing errors, software bugs, or unsupported data formats [27]. Relying on a single tool introduces the risk of basing critical conclusions on inaccurate or misleading data. Using multiple tools to corroborate findings acts as a quality control measure, ensuring that the results are consistent and reliable, which is a cornerstone of scientific and legal integrity [27] [1].
Q2: A hash verification failed during my evidence acquisition. What does this mean and what should I do? A failed hash verification means that the digital fingerprint of your copy does not match the original evidence. This indicates that the data was altered during the acquisition process, compromising its integrity [28] [29]. You must not proceed with analysis on this compromised copy.
- Action Plan:
- Stop and Document: Immediately halt the process and document the error.
- Check the Hardware: Investigate potential hardware issues, such as a faulty write-blocker or bad sectors on the source drive.
- Re-acquire the Evidence: Repeat the acquisition process using different hardware or a different tool if possible. Continue until you achieve a matching hash value.
Q3: How do I create a known-data set for testing my forensic tools? A known-data set is a curated collection of files with documented content and properties, used as a ground truth for validation.
- Methodology:
- Define Scope: Assemble a set of files that represent the data types you commonly encounter (e.g., documents, images, databases, application-specific files).
- Generate Baseline Hashes: Calculate and record the hash values (using SHA-256 or SHA-3) for every file in this set. This is your "known good" baseline [28] [29].
- Document Properties: Record other metadata, such as file sizes, timestamps, and the presence of specific keywords or data artifacts.
- Test Tool Output: Run your forensic tool against this known set. Compare the tool's reported hashes, recovered files, and parsed data against your baseline. Any discrepancy requires investigation [1].
Q4: Two different tools are reporting different timestamps for the same system event. How can I determine which is correct? This is a classic scenario for cross-tool corroboration. Discrepancies often arise from how tools interpret underlying data structures or time zone settings [27].
- Troubleshooting Guide:
- Consult a Third Tool: Introduce a third, forensically sound tool to analyze the same data. The result that appears in two out of three tools is more likely to be correct.
- Validate Against System Logs: Examine other system artifacts or logs that might record the same event to see which timestamp aligns.
- Check Time Zone Configurations: Ensure all tools are configured with the same time zone settings (e.g., UTC vs. local time) for the analysis [27].
- Research the Artifact: Investigate the technical documentation for the specific database or log file from which the timestamp was extracted to understand how the time value is stored [27].
Technical Guides & Experimental Protocols
Guide: Implementing Cross-Tool Corroboration
Cross-tool corroboration is the practice of verifying digital evidence by analyzing it with multiple independent forensic tools and comparing the results [27] [1].
Detailed Methodology:
- Evidence Acquisition: Create a forensic image (e.g.,
.E01or.ddfile) of the digital evidence. Verify the integrity of this image with a hash value (e.g., SHA-256) before proceeding [28]. - Tool Selection: Select at least two forensically recognized tools from different vendors (e.g., Magnet AXIOM, Autopsy, Cellebrite Physical Analyzer) for analysis [30].
- Parallel Processing: Load the forensic image into each selected tool. Process the data using similar parameters.
- Data Point Comparison: Systematically compare the outputs for key data points. The table below outlines critical artifacts to check.
Table: Key Artifacts for Cross-Tool Corroboration
| Artifact Category | Specific Data Points to Compare | Common Sources of Discrepancy |
|---|---|---|
| File System Metadata | File creation, modification, access timestamps; deleted file records [27]. | Different interpretations of $STANDARD_INFORMATION vs. $FILE_NAME attributes in NTFS. |
| Application Data | Parsed browser history, chat messages (WhatsApp, Signal), social media activity [30]. | Tools may have different parsers for evolving application database schemas. |
| Location Data | GPS coordinates, Wi-Fi access point locations, timestamps of location events [27]. | Misinterpretation of carved data (see diagram below) versus parsed data from known databases [27]. |
| System Events | User logins, application executions, shutdown times [27]. | Variances in decoding Windows Event Logs or system cache files. |
- Resolve Discrepancies: If inconsistencies are found, use the troubleshooting steps outlined in FAQ A4. Document the resolution process thoroughly.
- Report Findings: The final report should transparently state which tools were used, note any discrepancies found, and explain how they were resolved, reinforcing the reliability of the final conclusions [1].
Diagram: Cross-Tool Corroboration Workflow
Guide: Hash Verification for Evidence Integrity
Hash verification uses cryptographic algorithms to generate a unique digital fingerprint (hash value) for a set of data. This ensures the data has not been altered from its original state [28] [29].
Detailed Methodology:
- Algorithm Selection: Prefer robust, modern algorithms like SHA-256 or SHA-3. Avoid deprecated algorithms like MD5 and SHA-1 for critical applications due to known vulnerabilities [28] [29].
- Initial Hash Generation: After creating a forensic image of the original evidence, use a trusted tool to calculate its hash value. This value must be documented and preserved.
- Verification Hash Generation: Each time the evidence is accessed or copied for analysis, calculate a new hash value of the copy.
- Comparison: Compare the verification hash with the initial hash. If the values are identical, the evidence is intact. The table below compares common hashing algorithms.
Table: Comparison of Common Hashing Algorithms
| Algorithm | Output Length (bits) | Security Status | Recommended Use |
|---|---|---|---|
| MD5 | 128 | Deprecated (vulnerable to collisions) | Not recommended for new systems [28]. |
| SHA-1 | 160 | Deprecated (vulnerable to collisions) | Inadequate for modern cryptography [28]. |
| SHA-256 | 256 | Secure (part of SHA-2 family) | Recommended for current applications; industry standard [28] [29]. |
| SHA-512 | 512 | Secure (part of SHA-2 family) | Recommended for heightened security needs [29]. |
| SHA-3 | Variable | Secure (newest standard) | Recommended for future-proofing applications [29]. |
Diagram: Hash Verification Process for Data Integrity
Guide: Known-Data Set Testing for Tool Validation
Known-data set testing, also referred to as validation data set testing in machine learning, involves using a curated set of data with a known "ground truth" to evaluate the performance and accuracy of a forensic tool or method [31] [1].
Detailed Methodology:
- Data Set Curation: Create a controlled data environment, such as a clean virtual machine or a storage device. Populate it with files of various types (documents, images, databases). Introduce specific, documented user activities (e.g., web browsing, file deletions, application use) and known data artifacts.
- Establish Ground Truth: Before using the tool under test, thoroughly document the entire known-data set. This includes:
- A complete file listing with paths.
- SHA-256 hashes of all files.
- A log of all performed activities with correct timestamps.
- A list of specific keywords and data artifacts known to be present.
- Tool Processing: Process the known-data set with the forensic tool you are validating. Use standard procedures to image the drive and analyze its contents.
- Output Analysis: Compare the tool's output against your ground truth. Key aspects to validate include:
- Documentation and Re-validation: Document any false positives (data reported that isn't present) or false negatives (missing known data). This process is not one-time; it must be repeated when the tool is updated or when new data types need to be supported [1].
Diagram: Known-Data Set Testing Workflow
The Scientist's Toolkit: Essential Research Reagents & Materials
Table: Key Digital Forensics Tools and Functions for Validation
| Tool Name | Primary Function | Role in Validation Protocols |
|---|---|---|
| Magnet AXIOM | Comprehensive digital forensics suite for computers, mobile devices, and cloud data [30]. | Used in cross-tool corroboration to verify artifacts recovered by other tools. Its AI-powered categorization can be tested with known-data sets. |
| Cellebrite Physical Analyzer | Advanced mobile forensics tool for data extraction and decoding from smartphones and tablets [30]. | Critical for validating mobile artifact parsing. Known-data sets on mobile devices test its recovery of deleted data from new OS versions. |
| Autopsy | Open-source digital forensics platform with a user-friendly interface [30]. | An accessible tool for researchers to perform cross-tool checks and validate findings from commercial tools using the same evidence image. |
| Volatility | Open-source framework for advanced memory (RAM) forensics analysis [30]. | Used to validate the presence of runtime artifacts and volatile system state against disk-based evidence. |
| FTK Imager | Forensic imaging and preview tool by Exterro [30]. | A core reagent for creating forensic images and verifying their integrity via hash values before any analysis begins. |
| Wireshark | Network protocol analyzer for deep packet inspection [30]. | Used to validate network-related artifacts found on a endpoint device by comparing them against actual network traffic captures. |
FAQs on AI and Machine Learning in Digital Forensics
Q1: Why is the "black box" nature of some AI models a problem for digital forensics? The "black box" problem refers to the inability to understand how a complex AI model arrives at a specific decision or prediction. In digital forensics, this is critical because courts require evidence to be reliable and its origins understandable. Forensic conclusions must withstand legal scrutiny under standards like the Daubert Standard, which evaluates the scientific validity and known error rates of methods. Using an unexplainable AI output can lead to evidence being excluded or miscarriages of justice [1].
Q2: What are the most common interpretability methods for machine learning models? The most common model-agnostic methods (applicable to any AI model) are:
- SHAP (SHapley Additive exPlanations): Based on game theory, it assigns each feature in a dataset an importance value for a particular prediction [33].
- LIME (Local Interpretable Model-agnostic Explanations): Approximates a complex "black box" model with a simpler, interpretable model (like a linear model) around a specific prediction to explain it [34] [33].
- Anchors: Provides explanations through high-precision, easy-to-understand "if-then" rules that "anchor" the prediction, meaning changes to other features won't affect the outcome [33].
Q3: How can I validate the output of an AI-based forensic tool? Validation ensures tools are accurate, reliable, and legally admissible. The process should include [1]:
- Tool Validation: Confirming the software/hardware performs as intended without altering source data.
- Method Validation: Verifying that forensic procedures produce consistent outcomes across different cases and practitioners.
- Analysis Validation: Ensuring the interpreted data accurately reflects the true meaning and context of the evidence. Key practices involve using cryptographic hashing to confirm data integrity, comparing tool outputs against known datasets, and cross-validating results with multiple tools.
Q4: Our AI tool flagged an image as synthetic. What steps should we take? An automated flag is a starting point, not a conclusion. Your protocol should include:
- Human Review: A certified forensic specialist must manually validate the finding [35].
- Provenance Analysis: Check metadata for creation logs, device identifiers, or AI model parameters that indicate synthetic origin [35].
- Cross-Tool Validation: Use a different, independently validated tool to analyze the same image.
- Contextual Correlation: Correlate the finding with other digital artifacts (e.g., browser history, application logs) to build a holistic timeline [4].
Q5: What is the role of a human expert when using automated AI forensics? AI serves as a powerful assistant, but the human expert is indispensable. The expert is responsible for [35]:
- Oversight and Validation: Providing final judgment on AI-generated alerts and conclusions.
- Contextual Understanding: Interpreting findings within the broader context of the investigation.
- Legal Testimony: Explaining and defending the methodology and findings in court based on their "knowledge, skill, experience, training, or education."
Interpretability Methods at a Glance
The table below summarizes three key interpretability methods, helping you select the right approach for your validation needs.
| Method | Core Principle | Best For | Key Advantages | Key Limitations |
|---|---|---|---|---|
| SHAP (SHapley Additive exPlanations) | Assigns each feature a contribution value for a prediction based on game theory [33]. | Global & local explanation; understanding overall feature importance. | Solid theoretical foundation; provides contrastive explanations [33]. | Computationally expensive for non-tree models [33]. |
| LIME (Local Interpretable Model-agnostic Explanations) | Creates a local, interpretable model to approximate the black-box model's prediction for a single instance [34] [33]. | Understanding individual predictions. | Easy to use; provides a fidelity measure for explanation reliability [33]. | Explanations can be unstable for very similar data points [34] [33]. |
| Anchors | Generates high-precision "if-then" rules that anchor a prediction [33]. | Creating human-readable, rule-based explanations for specific cases. | Explanations are very easy to understand; highly efficient [33]. | Runtime depends on model performance; settings require configuration [33]. |
Experimental Protocol for Validating AI Forensic Tools
This detailed protocol provides a methodological framework for researchers to validate the outputs of AI-driven forensic tools, ensuring scientific rigor and legal defensibility.
1. Hypothesis and Scope Definition
- Objective: Clearly state what the AI tool is supposed to detect (e.g., "This tool accurately identifies AI-generated deepfake videos.").
- Constraints: Define the tool's operational limits, such as supported file formats, required metadata, and expected error rates.
2. Creation of a Controlled Validation Dataset
- Curation: Assemble a dataset with known inputs and expected outputs. This must include:
- Positive Samples: Confirmed instances of the target (e.g., verified deepfake videos).
- Negative Samples: Confirmed authentic media.
- Ambiguous Samples: Challenging cases to test the tool's limits.
- Data Integrity: Use cryptographic hashes (e.g., SHA-256) to ensure the dataset remains unaltered throughout testing [1].
3. Execution of Tool Testing
- Blinded Analysis: To prevent bias, the analyst should run the tool without knowing which samples are positive or negative.
- Process Documentation: Meticulously record the tool's name, version, and all settings and parameters used during analysis [1].
4. Interpretation and Cross-Validation
- Primary Analysis: Record the tool's raw outputs (e.g., "85% probability of being synthetic").
- Cross-Validation: Process the same dataset with a different, independently validated tool or method to identify discrepancies [1].
- Interpretability Application: Use methods like SHAP or LIME on a subset of results to understand which features (e.g., pixel patterns, metadata) influenced the AI's decision [34] [33].
5. Statistical and Holistic Review
- Performance Metrics: Calculate standard metrics (Accuracy, Precision, Recall, F1-Score) to quantify performance.
- Error Analysis: Manually investigate all false positives and false negatives to identify patterns or weaknesses in the AI model.
- Contextualization: Integrate findings with other evidence to assess the tool's practical utility in a real investigation [4].
The Digital Forensic Scientist's Toolkit
This table lists essential "research reagents" and their functions for conducting rigorous AI validation in a digital forensics context.
| Tool / Resource | Primary Function in Validation |
|---|---|
| Interpretability Libraries (SHAP, LIME) | Provides model-agnostic functions to "open" the black box and explain individual AI predictions [33]. |
| Validated Forensic Suites (e.g., Belkasoft X, Cellebrite) | Industry-standard tools for acquiring and analyzing digital evidence; serve as a benchmark for cross-validation [4] [1]. |
| Cryptographic Hashing Tools | Generate unique digital fingerprints (hashes) for data to ensure integrity and prove evidence has not been altered from collection through analysis [1]. |
| Controlled Datasets | Act as the "ground truth" for testing and calibrating AI tools, containing known positive, negative, and edge-case samples. |
| Legal Standards Framework (Daubert, FRE 901) | Provides the legal criteria for evaluating the admissibility of scientific evidence, guiding the entire validation methodology [35] [1]. |
Workflow for AI Output Validation
The diagram below outlines a logical, step-by-step workflow for validating a finding from an AI-based forensic tool, incorporating cross-validation and human expertise.
Troubleshooting Common Scenarios
Scenario 1: Inconsistent results between two different AI forensic tools.
- Investigation Steps:
- Verify Input Consistency: Ensure both tools analyzed the exact same evidence file (use hash verification) [1].
- Check Tool Versions: An outdated tool version may lack the latest detection models. Document all versions [1].
- Analyze with a Third Method: Use a fundamental, non-AI technique (e.g., manual metadata examination) to break the tie.
- Leverage Interpretability: Run SHAP or LIME on both tools' outputs to see if they are focusing on different features, which explains the discrepancy [33].
Scenario 2: An AI model's explanation (e.g., from LIME) is unstable.
- Problem: Slight changes in input data lead to vastly different explanations.
- Solutions:
- Use a More Robust Method: Consider switching to SHAP, which has a more solid theoretical foundation and may offer more stable explanations for your model type [33].
- Aggregate Explanations: Don't rely on a single explanation. Run the interpretability method multiple times with slight perturbations and look for consistently important features.
- Validate the Validator: Ensure the dataset used to generate explanations (for LIME) is representative and of high quality.
Developing and Using Custom Scripts and Open-Source Tools for Independent Verification
Frequently Asked Questions (FAQs)
1. What are the primary benefits of using open-source tools for verification in digital forensics? Open-source tools offer significant advantages, including cost-effectiveness due to no licensing fees, high customizability to fit specific research needs, and transparency into their inner workings which is crucial for validation and peer review [36]. Furthermore, the collaborative nature of their development often leads to rapid problem-solving and innovation [36].
2. How can I verify the results from an AI-driven forensic tool, like an offline LLM? Independent verification of AI tools is critical. For LLMs like BelkaGPT, a key methodology is to ground all AI outputs in actual case artifacts [4]. You should cross-reference the AI's findings—such as detected topics or emotional tones in communications—with the original, raw data (e.g., SMS, emails) [4]. Establishing a baseline with known data and comparing the tool's output against manual analysis or other tools can further validate its accuracy.
3. Our investigation involves data from a cloud application. What is a common method for acquiring this data for verification? A prevalent technique is to use tools that simulate application clients via their official APIs [4]. By providing valid user account credentials (e.g., for legal access), these tools can download user data from servers of applications like Facebook or Telegram. The server perceives this as a legitimate user request, which can help circumvent certain jurisdictional and technical barriers to data acquisition [2] [4].
4. What are the best practices for ensuring the integrity of evidence when using custom scripts? Always work on a forensic copy of the original data. Your custom scripts should incorporate robust logging to document every action performed on the data. Furthermore, using checksums (e.g., SHA-256) at every stage of processing—before, during, and after analysis—provides a verifiable chain of integrity for the evidence [4].
5. We are encountering sophisticated anti-forensic techniques. What verification strategies can we employ? To counter anti-forensics, employ a layered verification approach. Use advanced file recovery tools to retrieve deleted data and perform deep metadata analysis to detect inconsistencies that indicate tampering [4]. For data hiding techniques like steganography, utilize specialized counter-steganography tools to uncover information concealed within image or other files [4].
6. How can we efficiently handle the verification of evidence from a large volume of IoT devices? Automation is essential. Implement analysis presets in your forensic tools tailored to different IoT device types to streamline repetitive tasks [4]. Establish standardized workflows for evidence extraction and processing to ensure consistency and reduce human error across the large dataset [4].
Troubleshooting Common Scenarios
Scenario 1: Inconsistent Output from an Open-Source Analysis Script
- Problem: A custom Python script for parsing log files yields different results on different machines, threatening the reproducibility of your experiment.
- Investigation & Solution:
- Environment Check: First, verify that all dependencies (e.g., Python version, library versions like
pandasorlxml) are identical across environments. Use virtual environments and dependency files (e.g.,requirements.txt) to lock the versions. - Data Input Verification: Confirm that the input log files are exact binary copies. Recaculate their hash values (MD5, SHA-1) and compare them to ensure no corruption or difference.
- Code Review: Check for paths or operations in the script that are not platform-agnostic (e.g., hard-coded Windows paths used on a Linux system).
- Environment Check: First, verify that all dependencies (e.g., Python version, library versions like
- Preventive Protocol: Containerize the script and its environment using Docker to guarantee consistent execution across all research setups [36].
Scenario 2: Failed Acquisition from a Mobile Device with Advanced Encryption
- Problem: A modern smartphone resists standard data extraction methods, preventing access to critical evidence for verification.
- Investigation & Solution:
- Methodology Assessment: Do not rely on a single acquisition method. Explore alternative methods supported by your forensic platform, such as logical, file system, physical, and cloud extractions [4].
- Tool Capability Check: Ensure your forensic tools are updated to the latest version, as they frequently add support for new device models and security patches.
- Brute-Force Considerations: In a secure, controlled lab environment, some tools offer brute-force unlocking capabilities. These should only be attempted in a manner that minimizes the risk of data corruption and is legally compliant [4].
- Preventive Protocol: Maintain a toolkit with multiple forensic acquisition tools and stay informed on the latest bypass techniques through continuous training [4].
Scenario 3: Suspected Deepfake Media in Evidence
- Problem: A video file submitted as evidence is suspected of being a deepfake, potentially compromising the investigation's integrity.
- Investigation & Solution:
- Tool-Based Detection: Utilize specialized deepfake detection software that can identify subtle AI-generated artifacts. These tools analyze inconsistencies in video frames, audio frequencies, and pixel patterns that are invisible to the human eye [2].
- Metadata & Provenance Analysis: Scrutinize the file's metadata for signs of manipulation or editing software. Establish the file's provenance—its origin and chain of custody—to identify any gaps or anomalies.
- Multi-Tool Correlation: Do not rely on a single tool's output. Verify findings across multiple detection platforms and correlate them with other digital evidence from the case.
- Preventive Protocol: Develop a standard operating procedure (SOP) for the automatic screening of all image and video evidence through a trusted deepfake detection tool as part of the initial evidence intake process [2].
Experimental Protocols for Tool Verification
Protocol 1: Validation of an AI-Powered Evidence Triage Tool
- Objective: To independently verify the accuracy and reliability of an AI tool (e.g., BelkaGPT) in identifying relevant information from a large text corpus.
- Methodology:
- Create a Ground Truth Dataset: Curate a dataset of text artifacts (e.g., emails, chats) where the relevant information (e.g., specific keywords, names, transaction amounts) has been manually and meticulously identified and tagged.
- Execute Tool Analysis: Process the ground truth dataset with the AI tool, using its standard analysis functions (e.g., topic detection, entity extraction).
- Compare and Calculate Metrics: Compare the tool's output against the manual ground truth. Calculate standard metrics such as:
- Precision: (True Positives) / (True Positives + False Positives)
- Recall: (True Positives) / (True Positives + False Negatives)
- F1-Score: The harmonic mean of precision and recall.
- Validation Criterion: The tool should meet or exceed pre-defined thresholds for these metrics (e.g., F1-Score > 0.9) to be considered sufficiently reliable for your research context.
Protocol 2: Performance Benchmarking of Open-Source Forensic Tools
- Objective: To compare the efficiency and resource utilization of different open-source tools when performing a common task, such as disk imaging or file carving.
- Methodology:
- Standardized Test Environment: Perform all tests on identical hardware and software configurations to ensure a fair comparison.
- Controlled Dataset: Use a standardized, publicly available forensic disk image (e.g., from CFReDS) as the input for all tools.
- Measure Key Metrics: For each tool, execute the task multiple times and record:
- Task Completion Time
- CPU and Memory Utilization (average and peak)
- Output Integrity (e.g., hash of the resulting image)
- Number of Artifacts Successfully Recovered (for carving tools)
- Data Analysis: Compile the results into a structured table for clear comparison, identifying the trade-offs between speed, resource use, and effectiveness.
The Scientist's Toolkit: Essential Research Reagents
The table below catalogs key categories of open-source tools and resources essential for the independent verification of digital forensic processes.
| Tool/Resource Category | Function/Explanation | Key Examples |
|---|---|---|
| Formal Verification Tools | Mathematically proves the correctness of a hardware design or algorithm against a set of properties (assertions). Crucial for verifying core forensic functions. | SymbiYosys [37] |
| Hardware Simulation | Simulates HDL code for testing and verification. Allows researchers to test forensic techniques on known hardware behavior. | Verilator, Icarus Verilog [37] |
| Testbench Frameworks | Provides an environment for building and executing automated tests for hardware and low-level software. | cocotb, VUnit, OSVVM [37] |
| Verification IP (VIP) & Test Generators | Generates randomized, realistic input data to thoroughly test systems under verification. | AAPG, riscv-dv [37] |
| Build Systems & CI | Automates the build and testing process, ensuring that verification checks are run consistently. | FuseSoc, LibreCores CI [37] |
| Log Monitoring & Analysis | Aggregates and analyzes logs from various sources, which is vital for troubleshooting complex, multi-tool forensic workflows. | ELK Stack, Graylog [36] |
The following table quantifies the color contrast ratios for the specified palette, which must be considered when generating diagrams for publication to ensure accessibility [38] [39] [40]. The WCAG enhanced (AAA) requirement is a minimum of 7:1 for standard text [38] [40].
| Foreground Color | Background Color | Contrast Ratio | Passes WCAG AAA? |
|---|---|---|---|
| #4285F4 (Blue) | #F1F3F4 (Light Grey) | 2.76:1 | No |
| #EA4335 (Red) | #FFFFFF (White) | 4.21:1 | No |
| #FBBC05 (Yellow) | #202124 (Black) | 15.23:1 | Yes |
| #34A853 (Green) | #FFFFFF (White) | 3.02:1 | No |
| #4285F4 (Blue) | #FFFFFF (White) | 4.34:1 | No |
| #EA4335 (Red) | #F1F3F4 (Light Grey) | 3.13:1 | No |
| #34A853 (Green) | #202124 (Black) | 9.05:1 | Yes |
Workflow Visualization
The DOT script below generates a diagram illustrating the core workflow for independent tool verification.
Verification Workflow for Forensic Tools
The DOT script below generates a diagram showing how open-source tools integrate into a modern DFIR lab setup.
Open-Source Tool Integration in a DFIR Lab
Navigating Common Pitfalls and Optimizing Validation Workflows for Efficiency
FAQs: Addressing Common Analytical Challenges
FAQ 1: Why can the same event show different timestamps across various digital artifacts?
Timestamps can be inconsistent due to several technical factors. A primary reason is the use of different time standards; for example, a timestamp from a Facebook server (time field) is a reliable Unix millisecond timestamp in UTC, whereas the client_time field is set by the user's local device and can be altered by timezone settings or an incorrect system clock [41]. Furthermore, the act of timestamp tampering itself can create inconsistencies. In a live tampering scenario, adversaries often struggle to manipulate all related artifacts consistently, leaving behind first-order traces (inconsistencies within the targeted data) and second-order traces (evidence of the tampering tool's use) [42].
FAQ 2: How can I validate a carved geolocation hit to avoid false positives?
Carved geolocation data, extracted from raw data patterns like unallocated space, should be treated as an investigative lead rather than direct evidence. To validate a carved location coordinate and timestamp [27]:
- Corroborate with Parsed Data: Check if the location exists in any parsed, structured databases on the device (e.g.,
Cache.sqliteorLocal.sqliteon iOS) [43] [27]. - Inspect the Source Context: If the forensic tool provides the source file for the carved data, examine the surrounding bytes to determine if they belong to a known, structured record or if the carving algorithm mistakenly paired unrelated data fragments [27].
- Seek Supporting Artifacts: Look for other evidence that supports the location, such as related app usage, photos, or messages from the same time period.
FAQ 3: What is the practical difference between UTC and local time in device logs?
The key difference is consistency versus user context. UTC (Coordinated Universal Time) is a global standard and does not change with time zones or daylight saving time. Timestamps set by online services (e.g., Facebook server time) are often in UTC, making them highly reliable for establishing a baseline sequence of events [41]. Local time is the time set on the device by the user and is relative to a specific time zone. System events and user activity logs on the device itself often use local time. Incorrect local time settings are a common source of timestamp inconsistency, and validation requires understanding which time standard a specific artifact uses [27].
FAQ 4: How can I establish event order when timestamps are unreliable or have been tampered with?
When explicit timestamps are untrustworthy, investigators can leverage implicit timing information. This method involves creating distinct time domains for different sources of timing information (like a database's sequence numbers or log file line numbers) and then connecting these timelines based on causal relationships observed in the evidence. This technique creates a "hyper timeline," which is a rich partial order of events that can help order events without reliable timestamps and identify inconsistencies caused by tampering [44].
Troubleshooting Guides
Guide 1: Resolving Conflicting Timestamps
Conflicting timestamps for the same event across different data sources can undermine an investigation. Follow this protocol to diagnose and resolve these conflicts.
Step-by-Step Methodology:
- Identify and Document All Sources: List every artifact containing a timestamp for the event in question. Common sources include file system metadata (MAC times), application-specific databases, browser history, and cloud service logs [43] [41].
- Classify the Timestamp Type: Categorize each timestamp according to the table below to understand its inherent reliability.
| Timestamp Type | Description | Common Source | Reliability & Notes |
|---|---|---|---|
| Server Time | Set by a remote server | Online services (e.g., Facebook, email servers) [41] | High; based on UTC, independent of device settings. |
| Client Time | Set by the user's device | Device-generated logs, some app data [41] | Lower; susceptible to user manipulation or incorrect timezone settings. |
| Embedded (Logical) | Implicit sequence data | Database sequence numbers, log file line numbers [44] | High for relative ordering; provides sequence but not absolute time. |
| File System Time | Filesystem metadata | OS-level 'last modified', 'accessed', etc. | Variable; easily altered by user or system processes. |
- Check for Time Zone and DST Offsets: Determine if each timestamp is recorded in UTC or local time. Apply consistent time zone offsets when comparing timestamps from different sources [27].
- Analyze for Causal Impossibilities: Look for logical inconsistencies, such as an email being sent before it was drafted. Such impossibilities can indicate timestamp tampering or system errors [42] [44].
- Cross-Validate with Implicit Timing: Use implicit timing information, like sequence numbers in databases, to establish a relative order of events and validate or challenge the explicit timestamps [44].
Guide 2: Validating Geolocation Artifact Accuracy
Inaccurate geolocation data can misdirect an investigation. This guide provides a method to validate the reliability of a location artifact.
Step-by-Step Methodology:
Determine the Data Origin and Method:
Distinguish Between Parsed and Carved Data:
- Parsed Data: Extracted from known database schemas (e.g.,
gmm_storage.dbon Android orCache.sqliteon iOS). This is generally more reliable [43] [27]. - Carved Data: Recovered by scanning raw data for patterns. Always validate carved hits against parsed data to check for false positives, where unrelated data fragments are mistakenly interpreted as a location record [27].
- Parsed Data: Extracted from known database schemas (e.g.,
Corroborate with Supporting Evidence: A single location artifact is less reliable than a cluster of mutually supporting evidence. Seek out [43] [41]:
- Location history from other apps.
- Photos with embedded GPS coordinates.
- Network connection logs (Wi-Fi SSIDs, cell tower IDs).
- Communication artifacts (chats, emails) that reference the location.
Contextualize the Finding: Ask critical questions about the artifact. Does the location make sense given the user's other activities at that time? Could the data be residual (e.g., a cached location from a previous visit) rather than proof of physical presence? [27]
The diagram below illustrates this multi-layered validation workflow.
The Scientist's Toolkit: Essential Research Reagents & Materials
This table details key tools and methodologies referenced in the troubleshooting guides for validating digital timestamps and geolocation artifacts.
| Tool / Material | Function / Description | Use Case in Validation |
|---|---|---|
| Structured Database Parsers | Forensic tools (e.g., Magnet AXIOM, Cellebrite PA) that decode known database schemas to extract records [43]. | Extracting reliable "parsed" location data and application-specific timestamps from device images. |
| Data Carving Algorithms | Algorithms that scan raw data (unallocated space) for patterns matching coordinates/timestamps [27]. | Identifying potential location "leads" not found in structured databases; requires rigorous validation. |
| Hash Value Analysis | Using cryptographic hashes (e.g., SHA-256) to create a unique fingerprint for a digital evidence file [1]. | Verifying the integrity of evidence before and after imaging, ensuring data was not altered. |
| Hyper-Timeline Construction | A method that integrates implicit timing information (e.g., sequence numbers) with explicit timestamps to create a partial event order [44]. | Ordering events when timestamps are unreliable and detecting inconsistencies indicative of tampering. |
| Cross-Artifact Corroboration | An analytical process of seeking multiple, independent evidentiary sources that support a single conclusion [43] [27]. | Strengthening the validity of a timestamp or location fix by finding supporting data from different apps or system processes. |
| Live Tampering Simulation | A qualitative research method where participants attempt to manipulate evidence on a running system [42]. | Understanding the practical challenges and trace evidence left by adversaries, informing reliability assessments. |
Experimental Protocol: Validating a Carved Geolocation Artifact
This protocol provides a detailed methodology for testing the hypothesis that a carved geolocation hit represents a true device location, as referenced in Troubleshooting Guide 2.
Objective: To determine the evidentiary validity of a geolocation coordinate pair and timestamp recovered via data carving.
Materials and Software:
- A forensic image of a mobile device (Android or iOS).
- A digital forensics suite with data carving and database parsing capabilities (e.g., Magnet AXIOM, Cellebrite Physical Analyzer).
- Documentation tools.
Procedure:
Isolation and Documentation:
- Use your forensic tool's carving feature to locate a geolocation coordinate of interest.
- Document the precise latitude, longitude, timestamp, and, if available, the source file or offset within the image.
Parsed Data Correlation:
- Using the same forensic tool, navigate to and examine parsed location history databases native to the device's operating system.
- For iOS, this includes
Cache.sqliteandLocal.sqlitefrom thecom.apple.routinedcache [43]. - For Android, examine databases like
gmm_storage.dbfor Google Maps [43]. - Search for the carved coordinate (or coordinates very close to it) within these parsed databases. Note any associated timestamps.
Contextual Source Analysis:
- If the forensic tool allows, export the source sector or file snippet from which the data was carved.
- Perform a hex and textual analysis of the surrounding data. Look for indicators of a known database structure, file header, or other meaningful data patterns that confirm the carved data is a coherent record rather than a numerical coincidence [27].
Cross-Artifact Corroboration:
- Conduct a targeted search for other user activities that could be associated with the location and time in question.
- This includes: app usage logs, social media check-ins, sent messages, photos taken, or network connections (Wi-Fi or cellular) that are geographically relevant [41].
Data Interpretation and Conclusion:
- If the carved data is confirmed by a matching record in a parsed database with a consistent timestamp, and/or is supported by other corroborating artifacts, then the hypothesis is supported. The location can be considered reliable.
- If the carved data has no match in parsed databases, the source context is nonsensical, and no supporting artifacts exist, then the hypothesis is rejected. The data is likely a false positive and should not be relied upon as evidence [27].
The logical relationships and decision points in this protocol are shown below.
Technical Support Center
Troubleshooting Guides & FAQs
FAQ 1: How can I validate forensic findings when data wiping tools have been used?
- Issue: Suspected use of disk wiping tools (e.g., Drive Wiper, File Shredder) has rendered data recovery difficult [46].
- Solution:
- Low-Level Disk Analysis: Use forensic tools to perform a physical image of the storage media and analyze it at the hex level. Wiping tools often overwrite data with specific patterns; identifying these patterns can confirm the wiping activity.
- Artifact Correlation: Scrutinize system logs, prefetch files, and registry entries for execution traces of known wiping tools. Even if the target data is gone, the artifacts of the wiping software itself can be compelling evidence [4].
- Metadata Analysis: Examine the metadata of existing files for anomalies. Wiping processes can sometimes leave timestamp inconsistencies or other metadata artifacts that indicate their occurrence [4].
FAQ 2: What methodologies can reliably detect steganography?
- Issue: A file (e.g., an image) is suspected of containing hidden data via steganography using tools like Hidden Tear or Stego Watch [46].
- Solution:
- Statistical Analysis: Employ steganalysis tools to detect statistical deviations in the file. For instance, analyze the Chi-square (χ²) analysis for LSB (Least Significant Bit) steganography in image files.
- Hash Comparison: Compare the hash of the suspect file against a known-clean version of the same file. Any discrepancy indicates modification.
- Visual Inspection: Use specialized software to view the bit planes of an image. Hidden data can often create visual patterns or noise in the least significant bit planes.
- File Header and Structure Analysis: Check for inconsistencies in the file header, trailer, or file size that are atypical for the stated file format.
FAQ 3: How should I proceed when evidence is protected by strong encryption?
- Issue: Critical evidence is located within an encrypted container or volume [46].
- Solution:
- Identify Encryption Type: Determine if the encryption is symmetric (e.g., AES) or asymmetric (e.g., RSA) [47]. This informs the potential attack vectors.
- Key Recovery Attempts:
- Memory Dump Analysis: Analyze RAM captures for decryption keys that may have been resident in memory.
- Disk Forensics: Search for key files, password fragments in temporary files, or swap files.
- Brute-Force/Dictionary Attacks: Utilize high-performance computing resources or cloud clusters to attempt password cracking, if legally permissible [4].
- Alternative Data Sources: Identify and extract related, unencrypted metadata (e.g., file names, sizes, timestamps) that might be stored outside the container and can still provide contextual clues.
FAQ 4: What are the best practices for handling malware that uses anti-forensic techniques?
- Issue: Malware, including trojans or ransomware, is designed to disable forensic tools or erase its own traces [46].
- Solution:
- Live Forensics: Before powering down a system, use trusted, pre-prepared toolkits to capture volatile data (RAM, network connections, running processes).
- Sandbox Analysis: Execute the malware in an isolated, instrumented sandbox environment to observe its behavior, including any file wiping, encryption, or communication with command-and-control servers.
- YARA Rules: Create and use custom YARA rules to scan memory and disk images for indicators of compromise (IOCs) related to the malware's code or behavior [4].
- Logging and Monitoring: Implement and analyze centralized logs from endpoints and network security tools to reconstruct the attack timeline before the system was compromised.
Table 1: Common Anti-Forensic Techniques and Validation Methodologies
| Anti-Forensic Technique | Example Tools | Primary Challenge | Recommended Validation Methodologies |
|---|---|---|---|
| Disk Wiping [46] | Drive Wiper, File Shredder | Data irrecoverability; proving intent. | Low-level disk analysis for overwrite patterns [4]; artifact correlation of tool execution. |
| Steganography [46] | Hidden Tear, Stego Watch | Hidden data is visually undetectable. | Statistical steganalysis (e.g., Chi-square test); file hash comparison; visual bit-plane inspection. |
| File Encryption [46] | Various (e.g., VeraCrypt, BitLocker) | Inaccessible data content. | Key recovery from memory/disk; cryptographic identification; contextual metadata analysis [47]. |
| Data Compression [46] | WinZip, PKZIP | Reduced file size and altered structure. | File signature analysis; header verification; decompression and integrity checking. |
| Malware [46] | Trojans, Ransomware | Evidence destruction or tool interference. | Live forensics & volatile memory analysis; sandbox behavioral analysis; YARA rule scanning [4]. |
Table 2: AI and Automation Applications in Countering Anti-Forensics
| Technology | Function in Validation | Example Implementation |
|---|---|---|
| Machine Learning / Pattern Recognition [4] | Flags anomalies in system logs or detects suspicious activity patterns that may indicate anti-forensic tool usage. | ML models trained on logs from systems where wipers or steganography tools were executed. |
| Natural Language Processing (NLP) [4] | Processes vast communication datasets (emails, chats) to find discussions, plans, or commands related to obfuscation activities. | Offline AI assistants (e.g., BelkaGPT) analyzing case artifacts for topics like "hiding files" or "cleaning logs". |
| Automated Forensic Tools [4] | Executes repetitive tasks like hash calculation, data carving, and predefined anti-forensic signature searches at scale. | Custom analysis presets in forensic platforms (e.g., Belkasoft X) to run a standardized anti-forensic sweep. |
Experimental Protocols
Protocol 1: Validating Evidence Integrity Post Data-Wiping Attempt
- Objective: To confirm the use of a data-wiping tool and recover potential residual artifacts.
- Materials: A forensic workstation, write-blocker, forensic imaging tool (e.g., FTK Imager, dc3dd), and analysis suite (e.g., Belkasoft X, Autopsy).
- Methodology:
- Acquisition: Create a forensic bit-stream image of the target storage device using a write-blocker.
- Signature Analysis: Scan the image for known file signatures (headers/footers) of suspected wiping tools.
- Timeline Analysis: Build a system activity timeline from log files, registry hives, and prefetch files to pinpoint the execution time of the wiping utility.
- Data Carving: Use file carving techniques on the unallocated space and slack space to recover fragments of files potentially overwritten by the wiping process.
- Hash Verification: Compare hashes of system files before and after the suspected wiping event to identify altered components.
- Validation: The experiment is validated by successfully correlating the execution artifact of a wiping tool with the corresponding pattern of data sanitization on the disk.
Protocol 2: Detecting and Extracting Data Hidden via Steganography
- Objective: To identify the use of steganography and extract the concealed payload.
- Materials: Suspect carrier file, known-clean version of the same file (if available), steganalysis tool (e.g., StegExpose, Aletheia), hex editor.
- Methodology:
- Statistical Tests: Run the suspect file through steganalysis tools to calculate metrics like Chi-square for LSB steganography.
- Hash Comparison: Compute and compare the hash of the suspect file with the hash of the known-clean file.
- Visualization: Use a steganalysis tool to visualize the LSB plane of an image; random noise may indicate hidden data.
- File Structure Examination: Analyze the file in a hex editor for appended data after the official end-of-file (EOF) marker or inconsistencies in the internal file structure.
- Validation: Successful extraction of a non-native file (e.g., a ZIP archive or text file) from within the carrier file confirms the presence of steganography.
Workflow & Relationship Diagrams
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Digital Forensics Reagents for Anti-Forensics Research
| Research Reagent (Tool/Category) | Function in Experimental Protocol |
|---|---|
| Forensic Imaging Tools (e.g., FTK Imager, dc3dd) | Creates a bit-for-bit copy of digital evidence, ensuring data integrity for all subsequent analysis. The foundation of Protocol 1. |
| Integrated Forensic Suites (e.g., Belkasoft X, Autopsy, EnCase) | Provides a centralized platform for analysis, including data carving, timeline building, and artifact parsing, as used across all FAQs and protocols [4]. |
| Steganalysis Suites (e.g., StegExpose, Aletheia) | Specialized reagents for performing statistical tests and visual analysis required for detecting hidden data in Protocol 2. |
| Hex Editors (e.g., WinHex, HxD) | Allows for low-level inspection and manipulation of files and disk sectors, crucial for verifying file structures and finding wipe patterns. |
| Volatile Memory Analysis Tools (e.g., Volatility, Rekall) | Essential for live forensics and key recovery attempts from RAM, as outlined in FAQ 3 and FAQ 4. |
| YARA Rule Scanners | A specialized reagent for creating custom signatures to scan for malware IOCs or specific anti-forensic tool artifacts, as applied in FAQ 4 and automated workflows [4]. |
| Password Cracking Tools (e.g., Hashcat, John the Ripper) | Used in encryption challenges (FAQ 3) to attempt key recovery via brute-force or dictionary attacks. |
Automating Repetitive Validation Tasks to Manage Large Data Volumes and Accelerate Workflows
Troubleshooting Guides
Guide 1: Troubleshooting Automated Forensic Tool Validation Pipelines
Problem: Automated validation pipeline for a mobile forensics tool fails to generate reference data after a new application update.
Explanation: Mobile applications update frequently, changing their data structures and breaking existing validation tests. Automated systems must detect these updates and trigger new reference data generation to keep tool validation current [48].
Solution:
- Step 1: Implement Update Detection: Integrate a monitoring service that tracks application versions in official stores (e.g., Google Play) using their APIs. Configure the service to trigger an alert upon detecting a new version [48].
- Step 2: Automate Data Synthesis: Use an open-source framework like Puma to automatically generate new forensic reference data. The framework should create a clean environment, install the updated application, execute predefined user scenarios, and collect the resulting device data [48].
- Step 3: Execute Regression Tests: Feed the newly generated reference data into your forensic analysis tool. Run automated test suites to compare the tool's output against the expected results from the reference dataset.
- Step 4: Review and Report: Analyze the test report for discrepancies. If the tool's performance has degraded, document the issue for developers. Update the official reference dataset only after the tests pass successfully.
The following workflow diagrams the automated validation process triggered by a mobile application update:
Guide 2: Resolving Inefficient Evidence Processing in Large-Scale Data Investigations
Problem: Forensic tool processing is slow, creating a bottleneck when dealing with large data volumes (e.g., multi-terabyte drives), which delays analysis and causes case backlogs [49].
Explanation: The sheer volume of digital evidence can overwhelm manual processing workflows. Automation addresses this by streamlining repetitive tasks, utilizing hardware during off-hours, and allowing examiners to focus on analysis [49].
Solution:
- Step 1: Audit and Identify Repetitive Tasks: List all repetitive, time-consuming steps in your current workflow (e.g., hashing, data carving, running YARA rules, exporting data to specialized tools) [4] [49].
- Step 2: Develop Automated Workflows: Use workflow automation solutions to chain these tasks into a single, repeatable process. Create analysis presets tailored to specific case types to ensure Standard Operating Procedures (SOP) are followed [4] [49].
- Step 3: Leverage Parallel Processing: Configure your automation software to use multiple processing nodes. This allows different forensic tools and scripts to run simultaneously on the same evidence, drastically reducing total processing time [49].
- Step 4: Schedule Unattended Execution: Queue large processing jobs to run overnight or during weekends. This ensures your hardware is fully utilized, and examiners return to fully processed data ready for analysis [49].
Frequently Asked Questions (FAQs)
FAQ 1: How can automation help our lab comply with accreditation standards like ISO 17025?
Automation directly supports accreditation by enforcing Standard Operating Procedures (SOPs) and ensuring consistency. Automated workflows are repeatable and predictable, minimizing human error and creating a clear, auditable trail for every case processed. This demonstrates to accrediting bodies that your lab maintains rigorous, consistent standards [49].
FAQ 2: We are concerned that automation will replace the need for skilled forensic examiners. Is this true?
No, the goal of automation is to empower skilled examiners, not replace them. Automation handles repetitive, time-consuming tasks, freeing up examiners to focus on the complex, cognitive work that requires human expertise: deep-dive analysis, interpreting results, validating findings, and building a case. Automation makes examiners more efficient and effective [49].
FAQ 3: What is the most critical factor for successfully implementing workflow automation?
The most critical factor is clearly defining the problems you need to solve and mapping your existing processes. Before investing in any solution, identify specific bottlenecks, repetitive tasks, and use cases (e.g., ICAC, major crimes, corporate incidents). A clear understanding of your current workflow ensures the automation solution you choose is the right fit for your organization's unique needs [50].
FAQ 4: Can automation tools keep up with the fast-paced changes in mobile devices and applications?
Yes, but it requires a proactive approach. The digital forensics community is developing methods for continuous validation. This includes automated frameworks that can generate new reference data whenever a mobile application updates. By integrating these automated testing workflows, tools can be continuously validated against the latest software versions, ensuring their accuracy remains current [48].
The Scientist's Toolkit: Essential Research Reagents & Materials
The table below summarizes key digital forensics tools and platforms that function as essential "research reagents" for developing and testing automated validation workflows.
| Tool/Framework Name | Primary Function in Validation | Brief Explanation |
|---|---|---|
| Puma Framework [48] | Automated Reference Data Generation | An open-source mobile data synthesis framework that automatically generates forensic reference data triggered by application updates, essential for tool testing. |
| Belkasoft X [4] [26] | Integrated Forensic Analysis & AI | A digital forensics tool that supports automation presets, AI-based media analysis, and data extraction from a wide array of sources (mobile, cloud, computer). |
| Magnet AXIOM [26] | Evidence Collection & Analysis | A digital forensics tool used to collect, analyze, and report evidence from computers, smartphones, and cloud services, often integrated into automated workflows. |
| Magnet AUTOMATE [49] | Workflow Orchestration | A workflow automation solution designed to automate repetitive forensic tasks across different tools, streamlining processing and alleviating lab backlogs. |
| Autopsy [26] | Open-Source Forensic Platform | An open-source digital forensics platform that provides modules for timeline analysis, keyword search, and data recovery, useful for building custom automated processes. |
| YARA Rules [4] | Pattern Matching | A tool used to identify and classify malware and other suspicious artifacts based on textual or binary patterns; often run automatically during evidence processing. |
Experimental Protocol: Automated Reference Data Generation for Mobile App Updates
This protocol details the methodology for automatically generating digital forensic reference data, a critical process for validating tools against rapidly changing mobile applications [48].
Objectives and Preparation
- Primary Objective: To establish a continuous, automated workflow that generates validated reference data sets for digital forensics tools in response to mobile application updates.
- Materials:
- Puma Framework: The open-source mobile data synthesis software [48].
- Clean Room Environment: Dedicated, isolated hardware or virtual machines to prevent data contamination.
- Test Mobile Devices: Physical devices or emulators with a clean OS installation.
- Application Package (APK/IPA): The specific version of the mobile application to be tested.
Step-by-Step Procedure
- Update Detection Trigger: The automated system continuously monitors application stores via their public APIs. Upon detecting a new version release, the system triggers the validation workflow [48].
- Environment Provisioning: The automation server provisions a clean testing environment, ensuring no residual data from previous tests could skew the results.
- Application Installation and Seeding: The target application is installed on the clean device. The framework then executes a predefined set of user scenarios (e.g., sending messages, making transactions, changing settings) to create realistic and structured data within the app [48].
- Forensic Image Acquisition: A physical or file system acquisition of the device is performed immediately after data seeding is complete.
- Data Extraction and Hashing: The acquired image is processed. The framework extracts relevant application artifacts, calculates cryptographic hashes (e.g., SHA-256) of all generated data, and records the complete state of the device and application [26] [48].
- Dataset Curation and Storage: The collected data, hashes, and logs are packaged into a structured reference dataset. This dataset is versioned and stored in a dedicated repository for tool validation.
Quantitative Metrics for Validation
The following table outlines the key quantitative data points to collect and verify during the protocol execution to ensure the integrity and usefulness of the generated reference dataset.
| Metric | Purpose | Example/Target |
|---|---|---|
| Data Volume Processed [49] | To gauge processing load and scalability. | ~1.7TB of data [49] |
| Processing Time Reduction [49] | To measure efficiency gains from automation. | 94% reduction in downtime [49] |
| Artifact Recovery Rate | To validate the tool's ability to extract data. | >98% of seeded messages recovered |
| Hash Verification Mismatch | To ensure data integrity and absence of corruption. | 0 mismatches |
Expected Outcomes and Analysis
- Successful Workflow: A fully automated process from update detection to reference dataset creation, enabling continuous validation.
- Validation Report: A comprehensive report detailing any discrepancies found when the forensic tool analyzes the new reference data, highlighting areas requiring tool adjustment or recalibration.
- Accelerated Research Cycle: By integrating this protocol, researchers can rapidly validate and refine their digital forensics tools, ensuring they remain effective against the latest software versions.
Technical Support Center: FAQs & Troubleshooting Guides
Frequently Asked Questions (FAQs)
FAQ 1: How does the tiered validation framework adapt to different types of digital evidence? The framework applies proportional scrutiny, meaning the validation intensity is scaled based on the evidence's potential impact on the investigation's outcome. High-impact evidence, such as data from novel cloud services or AI-generated media (deepfakes), undergoes rigorous, multi-layered validation (Tier 3). In contrast, well-understood, low-risk data from standardized sources may only require baseline verification (Tier 1) [2] [4].
FAQ 2: What are the most significant challenges when validating tools for cloud forensics, and how does tiered validation address them? Key challenges include data fragmentation across multiple jurisdictions, differing cloud provider policies, and encryption [2] [4]. Tiered validation addresses this by mandating that tools for cloud evidence extraction undergo enhanced validation protocols. This includes testing against simulated multi-platform environments and verifying the tool's ability to handle API-based data acquisition and decryption processes effectively [4].
FAQ 3: How can researchers validate the output of AI-assisted forensic tools, like integrated LLMs, to prevent bias? AI tools, such as offline LLMs (e.g., BelkaGPT), must be validated for their grounding in case artifacts. The validation process involves checking the AI's outputs against known, verified datasets to ensure it does not introduce hallucinations or biases. Furthermore, its performance in tasks like topic detection and emotional tone analysis should be consistently benchmarked [4].
FAQ 4: What is the role of automation in a tiered validation strategy? Automation is crucial for managing the data volume in modern investigations [4]. Within a tiered validation framework, automated preset analyses and unattended task execution are first validated themselves. Once certified, these automated workflows can be trusted to handle repetitive, large-scale data processing, allowing researchers to focus their scrutiny on complex, high-priority evidence requiring manual, in-depth review [4].
Troubleshooting Common Experimental Issues
Issue 1: Inconsistent results when a forensic tool analyzes data from different IoT devices.
- Problem: The tool's parser or acquisition method is not universally compatible across various device firmware versions.
- Solution:
- Isolate the specific device model and firmware version causing the failure.
- Validate the tool's capabilities against that specific device configuration in a controlled lab environment.
- Apply a higher validation tier (Tier 3) to the tool's functionality for that specific device, documenting the limitations until a parser update is available [4].
Issue 2: A tool fails to detect a known deepfake during an authenticity verification experiment.
- Problem: The tool's detection algorithms are not trained on the latest deepfake generation techniques.
- Solution:
- Document the specific deepfake creation method used (e.g., GAN architecture, video source).
- This failure should trigger a re-validation of the tool against an updated dataset containing contemporary deepfake variants, elevating it to a high-priority validation status.
- The tool's performance metrics against deepfakes must be continuously monitored and updated as a part of its maintenance cycle [2].
Issue 3: Acquired cloud data is incomplete or misses key metadata.
- Problem: The tool's API client simulation does not successfully request all available data scopes, or the cloud service's API has been updated.
- Solution:
- Verify that the tool is using the most recent API version for the target cloud service.
- Compare the acquired data against a known-good acquisition from another validated tool or a manual API query.
- The validation protocol for cloud forensics tools must include checks for completeness and metadata integrity for each major API version change [4].
Experimental Protocols & Data Presentation
Detailed Methodology for a Key Experiment: Validating AI-Powered Media Analysis
Objective: To evaluate the efficacy and accuracy of an AI-assisted forensic tool in identifying and categorizing specific objects (e.g., weapons) within a large image dataset.
Protocol:
- Dataset Curation: Assemble a standardized dataset of images, including a mix of positive cases (containing the object of interest), negative cases, and challenging examples (e.g., obscured objects, varying lighting conditions).
- Tool Configuration: Initialize the forensic tool (e.g., Belkasoft X with AI modules) and configure its analysis presets to scan for the target objects [4].
- Blinded Analysis: Run the tool against the dataset in a blinded manner, where the experimenter does not know the ground truth for each image during the automated analysis phase.
- Result Compilation: Collect the tool's outputs, including hit rates, false positives, and false negatives.
- Manual Verification: Have human experts manually review and tag the entire dataset to establish the ground truth.
- Data Comparison: Compare the tool's results against the manual verification data to calculate key performance metrics.
Table 1: Quantitative Results from AI Media Analysis Validation
| Performance Metric | Tool A Result | Tool B Result | Minimum Acceptance Threshold |
|---|---|---|---|
| True Positive Rate (Recall) | 98.5% | 92.1% | >95% |
| False Positive Rate | 1.2% | 4.7% | <3% |
| Precision | 97.8% | 94.5% | >95% |
| F1-Score | 98.1% | 93.3% | >95% |
| Average Processing Time (per image) | 0.8s | 1.5s | <2.0s |
Tiered Validation Levels and Criteria
Table 2: Tiered Validation Framework Specifications
| Validation Tier | Scrutiny Level | Evidentiary Impact Criteria | Recommended Application Examples |
|---|---|---|---|
| Tier 1 | Baseline Verification | Low risk; well-established, standardized data sources; minimal case impact. | Hash value calculation, basic file recovery, logical data extraction from standardized phones. |
| Tier 2 | Intermediate Scrutiny | Moderate risk; common sources with some complexity; supportive role in case. | SQLite database parsing, analysis of common app artifacts, basic timeline generation. |
| Tier 3 | Enhanced / Proportional Scrutiny | High risk; novel or complex sources; central or conclusive to case outcome. | Cloud API data acquisition, deepfake detection, encrypted container analysis, AI/LLM output validation [2] [4]. |
Workflow Visualization
Tiered Validation Decision Workflow
AI-Powered Media Analysis Protocol
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Digital Forensics Research Materials & Tools
| Item Name / Solution Category | Primary Function in Research & Validation |
|---|---|
| Forensic Software Platform | Provides the core environment for data acquisition, analysis, and reporting. Used as the test bed for validating new parsers and analysis techniques against known datasets [4]. |
| Controlled Reference Datasets | Collections of digital artifacts with known properties (ground truth). Essential for benchmarking tool performance, calculating accuracy metrics, and training AI models. |
| Cloud Service Simulators/APIs | Allow researchers to test and validate cloud forensics tools in a controlled, repeatable environment without relying on live production data [4]. |
| Anti-Forensic Challenge Sets | Datasets containing obfuscated, encrypted, or deliberately hidden data. Used to stress-test tools and validate their effectiveness against evolving anti-forensic techniques [4]. |
| Large Language Models (LLMs) | Offline, forensically-trained LLMs (e.g., BelkaGPT) are used to automate the analysis of large volumes of text-based evidence, requiring validation of their topic detection and summarization accuracy [4]. |
Benchmarking and Comparative Analysis of Modern Digital Forensics Platforms
Establishing Benchmarks for Tool Performance, Accuracy, and Reliability in 2025
Frequently Asked Questions (FAQs)
Q1: What is forensic validation, and why is it a critical practice in 2025? Forensic validation is the fundamental process of testing and confirming that digital forensic tools and methods produce accurate, reliable, and repeatable results [1]. It encompasses three key components [1]:
- Tool Validation: Verifying that forensic hardware and software perform as intended without altering the original evidence.
- Method Validation: Confirming that analytical procedures yield consistent outcomes across different cases and practitioners.
- Analysis Validation: Ensuring that the interpreted data accurately reflects the true meaning and context of the evidence. This practice is critical because, without it, the credibility of forensic findings can be severely undermined, leading to legal evidence being excluded, miscarriages of justice, and operational errors based on flawed data [1]. It is both an ethical and professional necessity.
Q2: My team is using a tool validated last year. Why are we getting inconsistent results with a new mobile operating system update? Digital forensics faces unique challenges due to the rapid evolution of technology [1]. New operating systems, applications, and encryption methods can render previous tool validations obsolete. This situation underscores the need for continuous validation, a core principle where tools and methods must be frequently revalidated to account for technological changes [1]. You should initiate a new validation cycle focused specifically on the new OS version.
Q3: What are the core principles we should follow when designing a validation benchmark? When establishing benchmarks, your protocols should be built on the following core principles [1]:
- Reproducibility: Results must be repeatable by other qualified professionals using the same method.
- Transparency: All procedures, software versions, and chain-of-custody records must be thoroughly documented.
- Error Rate Awareness: The known error rates of forensic methods should be understood and disclosed.
- Peer Review: Validation processes should be scrutinized by the broader forensic community.
- Continuous Validation: Commit to frequent re-validation as technology evolves.
Q4: A critical measurement from our analysis tool seems anomalous. How should we troubleshoot this? Follow this structured troubleshooting guide:
- Verify Tool Configuration: Confirm that all tool settings and environment variables (e.g.,
CONTRAST__AGENT__LOGGER__LEVELfor logging) are correctly configured [51]. - Check Data Integrity: Use hash values (like SHA-256) to ensure the evidence data has not been altered since collection [1].
- Cross-Validate with Alternate Tools: Use a different forensic tool to parse the same dataset and compare the outputs for inconsistencies [1].
- Review Logs: Examine the detailed application and agent logs (as configured via variables like
CONTRAST__AGENT__LOGGER__PATH) for any errors or warnings during processing [51]. - Consult Known Test Cases: Run the tool against a controlled dataset with a known, expected output to verify its baseline functionality [1].
- Verify Tool Configuration: Confirm that all tool settings and environment variables (e.g.,
Troubleshooting Guides
Guide 1: Resolving Inconsistent Tool Outputs
Symptoms: Two tools extracting data from the same source yield different results; a tool update parses data differently than a previous version.
Required Materials:
| Research Reagent Solution | Function |
|---|---|
| Forensic Write-Blocker | Prevents alteration of original evidence during the imaging process. |
| Multiple Forensic Suites (e.g., Cellebrite, Magnet AXIOM, XRY) | Used for cross-validation to identify tool-specific parsing errors [1]. |
| Validated Hash Algorithm (e.g., MD5, SHA-1, SHA-256) | Generates unique digital fingerprints to verify data integrity [1]. |
| Standardized Test Image | A controlled dataset with a known structure and content for tool verification [1]. |
Methodology:
- Evidence Preservation: Create a forensic image (bit-for-bit copy) of the evidence source using a write-blocker. Generate a hash value for the original source and the image, confirming they match [1].
- Tool Configuration: Document the exact version and configuration of each tool used in the experiment.
- Parallel Processing: Process the same forensic image through each of the different forensic tools.
- Data Comparison: Systematically compare the outputs from each tool, focusing on key data points (e.g., extracted artifacts, parsed database files, recovered deleted items).
- Root Cause Analysis: Identify the source of discrepancy. Is it a bug in one tool's parser? Does one tool support a specific file type that another does not? Document these findings.
The following workflow outlines the structured methodology for this guide:
Guide 2: Validating a New Tool or Version Against a Legacy System
Symptoms: Introducing a new forensic tool into your workflow; validating a tool update before deploying it in a live investigation.
Methodology:
- Define Validation Scope: Identify the specific functionalities to test (e.g., SQLite database parsing, cloud artifact recovery, file decryption capabilities).
- Establish a Ground Truth Dataset: Create or obtain a dataset where the content and structure are fully known and documented.
- Run Controlled Experiments: Process the ground truth dataset with both the new tool/version and a previously validated legacy tool.
- Quantitative and Qualitative Analysis:
- Measure performance metrics (see table below).
- Compare the completeness and accuracy of the extracted data.
- Error Analysis: Document any false positives (data reported but not present) or false negatives (data present but not reported).
Expected Outcomes and Metrics: The following table summarizes key quantitative benchmarks to establish during tool validation.
| Benchmark Metric | Description | Target Threshold |
|---|---|---|
| Data Parsing Accuracy | Percentage of known artifacts in a test set correctly extracted and interpreted. | ≥ 98% for core supported artifacts [1]. |
| Tool Performance | Time taken to process a standardized evidence image. | Should be within 15% of the performance of the previous stable version. |
| System Resource Usage | CPU and RAM consumption during processing. | Must not exceed 80% of system resources on recommended hardware. |
| Error Rate | Rate of false positives and false negatives, as identified against a ground truth dataset. | Must be known, documented, and approaching 0% for critical artifacts [1]. |
The logical relationship of the validation process is demonstrated below:
Comparative Analysis of Leading Commercial and Open-Source Platforms (e.g., Cellebrite, Magnet AXIOM, Belkasoft X)
Digital forensics platforms are essential for investigating digital evidence from computers, mobile devices, and cloud services. The landscape is divided between established commercial tools, known for their robust support and court acceptance, and flexible open-source tools, prized for transparency and customization. The choice between them depends on the specific requirements of the investigation, including budget, required platforms, and the necessity for court-admissible reporting [52] [53].
Comparative Analysis Tables
Table 1: High-Level Comparison of Digital Forensics Platforms
| Platform | Primary Use Case | Key Strengths | Common Limitations | Licensing Model |
|---|---|---|---|---|
| Cellebrite UFED [52] | Mobile & Cloud Forensics | Extensive device support; physical extraction; court-accepted [52] | Very expensive; requires regular updates [52] | Commercial, Custom Pricing [53] |
| Magnet AXIOM [52] | Computer, Mobile & Cloud Forensics | Artifact visualization; unified platform; AI analysis [52] [53] | High system resource demands [52] | Commercial, Subscription [53] |
| Belkasoft X [52] | Computer, Mobile & RAM Forensics | All-in-one platform; live RAM & cloud acquisition [52] [26] | Smaller artifact library; complex interface [52] | Commercial, Perpetual/Subscription [53] |
| EnCase Forensic [52] | Disk & OS-Level Forensics | Deep file system analysis; court-approved for years [52] [53] | Steep learning curve; high cost [52] | Commercial, Annual License [52] |
| Oxygen Forensic Detective [52] | Mobile, IoT & App Forensics | Deep app & cloud analysis; IoT & drone support [52] [53] | High resource demand; costly subscription [52] | Commercial, Custom Pricing [53] |
| Autopsy [53] | General Computer Forensics | Cost (free); modular plugins; strong community [26] [53] | Less intuitive interface; limited scalability [53] | Open Source (GPLv2) |
Table 2: Technical Specification and Support Comparison
| Platform | Mobile OS Support | Cloud Service Support | Computer OS Support | Standout Technical Feature |
|---|---|---|---|---|
| Cellebrite UFED | iOS, Android (Extensive) [52] | Yes [52] | Limited [53] | Device unlocking & encryption bypass [52] |
| Magnet AXIOM | iOS, Android [53] | Yes (Integrated) [52] | Windows, macOS [53] | Magnet.AI for content classification [52] |
| Belkasoft X | iOS, Android [52] | Yes [52] | Windows, macOS, Linux [52] | Integrated RAM & database analysis [52] |
| EnCase Forensic | Via acquisition [52] | Limited | Windows, macOS, Linux [52] | Deep file system & registry analysis [52] |
| Oxygen Forensic Detective | iOS, Android (40,000+ devices) [53] | Yes (Extensive) [52] | Windows [53] | Facial recognition & IoT forensics [53] |
| Autopsy | Via plugins [26] | Limited | Windows, macOS, Linux [53] | Open-source code for full transparency [26] |
Troubleshooting Guides and FAQs
This section addresses common technical and methodological issues encountered when using these platforms in a research environment.
General Workflow and Validation Troubleshooting
Q1: Our forensic tool produced an unexpected result. How can we validate if it's a tool error or a true artifact?
A: Implement a multi-tool validation protocol.
- Action 1: Cross-verify with a different tool category. Process the same evidence sample with a tool from a different vendor (e.g., verify a Cellebrite finding with Magnet AXIOM or an open-source tool like Autopsy) [54].
- Action 2: Use a known-data test set. Create or use a pre-validated dataset with known artifacts (e.g., a smartphone image with a specific number of deleted SMS messages). Run your tool against this control to test its parsing accuracy [1].
- Action 3: Check for tool updates and known issues. Consult the vendor's release notes and knowledge base for fixed bugs related to your artifact. For open-source tools, check the community issue tracker [52] [55].
- Action 4: Examine the raw data. Use hexadecimal viewers or file system parsers to look for the underlying data structure supporting the artifact. This helps determine if the tool is misinterpreting valid data or reporting a false positive [54].
Q2: What is the foundational methodology for validating a new forensic tool or a major version update in a research context?
A: Follow a structured, documented validation process based on scientific principles [56].
- Step 1: Tool Functionality Verification. Confirm the tool installs and operates correctly in your environment. Test basic acquisition (e.g., creating a disk image) and hashing to ensure data integrity [1].
- Step 2: Known-Data Testing. Use a "ground truth" dataset with known contents (specific files, registry entries, SQLite records). Execute the tool's key functions (indexing, parsing, searching) and verify the output matches expectations [1].
- Step 3: Comparative Analysis. Process a complex, real-world evidence sample (e.g., a modern smartphone backup) with the new tool and one or more already-validated tools. Compare the outputs for consistency in artifact recovery and reporting [54] [1].
- Step 4: Error Rate Assessment. Document any false positives (artifacts reported but not present) and false negatives (known artifacts missed by the tool). This establishes a preliminary error rate for the method [1].
- Step 5: Documentation and Peer Review. Compile a validation report detailing the testing environment, methodology, datasets, results, and any anomalies. Have this report reviewed by another researcher to ensure objectivity [56].
Platform-Specific Troubleshooting
Q3: We are experiencing performance issues (slow processing, crashes) with Magnet AXIOM when handling large datasets. What steps can we take?
A: This is a common issue due to the tool's high system requirements [52].
- Check System Resources: Ensure the workstation meets or exceeds the recommended specifications, particularly RAM (32GB+) and CPU cores. Monitor resource usage during processing to identify bottlenecks [52].
- Optimize AXIOM Processing: Use the "Artifact Selector" to process only relevant artifacts instead of a full extraction. This reduces processing load and time [53].
- Split the Data: For very large cases, consider breaking the evidence into logically separate AXIOM cases (e.g., by device or date range) to improve manageability [54].
Q4: Our Cellebrite UFED cannot physically extract data from a new high-security Android device. What are the next steps?
A: Physical extraction is a key strength but has limitations [52].
- Verify Support: Check the official Cellebrite UFED Support List for the specific device model and OS version. New or updated devices may not be immediately supported [52].
- Alternative Methods: Attempt a logical extraction or a full file system extraction if available. These can still yield significant data [52].
- Cloud Extraction: If the device is synced with a cloud account (Google or iCloud), use UFED's cloud extraction capabilities as an alternative data source [52].
- Maintain Updates: Cellebrite frequently releases updates to support new devices. Ensure your license and tools are current [52] [1].
Q5: The open-source tool Autopsy is not parsing a specific application's database correctly. How can we address this?
A: Open-source tools benefit from community-driven development.
- Identify the Module: Determine which Autopsy module is responsible for parsing the application data.
- Community Resources: Search the Autopsy community forums and GitHub repository for existing issues or solutions related to the application.
- Custom Artifact Creation: Leverage Autopsy's modularity. If you have programming resources, develop a custom ingest module to parse the specific database structure. This is a core advantage of open-source platforms for research [54].
- Cross-Reference: Use a commercial tool's free trial to parse the same data and compare the results, which may provide insight into the correct database schema [54].
Experimental Protocols for Tool Validation
Protocol: Comparative Artifact Recovery Rate Analysis
Objective: To quantitatively compare the artifact recovery capabilities of two or more digital forensics platforms (e.g., a commercial tool vs. an open-source tool) from a standardized evidence sample.
Materials:
- Test Devices: A wiped and re-imaged smartphone (e.g., Android 13) or computer.
- Evidence Generation Script: A script to populate the device with a known set of artifacts (SMS, calls, browser history, specific app data, deleted files).
- Tools Under Test: The digital forensics platforms to be compared (e.g., Magnet AXIOM, Belkasoft X, Autopsy).
- Validation Tool: A hex editor and SQLite browser for raw data inspection.
Methodology:
- Baseline Creation: Using the script, populate the test device with a known number of artifacts (
N_total). Document all created items meticulously. - Forensic Imaging: Create a bit-for-bit forensic image (e.g.,
.ddor.E01file) of the test device. Calculate and record the acquisition hash (MD5/SHA-1) for integrity [1]. - Parallel Processing: Process the identical forensic image separately through each tool under test. Use default recommended settings for each tool.
- Data Extraction & Tallying: For each tool, execute a full analysis and generate a report. Tally the number of each type of artifact recovered (
N_recovered). - Calculation: For each tool and artifact type, calculate the recovery rate:
Recovery Rate (%) = (N_recovered / N_total) * 100. - Statistical Analysis: Present results in a comparative table. Discuss statistically significant differences in recovery rates for different artifact types.
Protocol: Robustness Testing Against Encrypted and Damaged Media
Objective: To evaluate a tool's ability to handle non-standard storage media, including encrypted drives and storage devices with bad sectors.
Materials:
- Storage Media: Multiple identical HDDs/SSDs.
- Encryption Tool: BitLocker (Windows) or FileVault (macOS).
- Data Damage Tool: A utility to programmatically introduce bad sectors into a disk image.
- Tools Under Test: Selected digital forensics platforms.
Methodology:
- Sample Preparation:
- Phase 1 (Encryption): Encrypt one set of drives using a known password.
- Phase 2 (Damage): Take another set of drives and use the damage tool to introduce a controlled percentage of bad sectors.
- Acquisition Challenge: Present the encrypted and damaged drives to the tools under test for acquisition.
- Metrics for Evaluation:
- For Encrypted Drives: Record success/failure in mounting the drive, prompting for a password, and successfully acquiring a decrypted image.
- For Damaged Drives: Record the tool's behavior: does it halt, skip sectors, or fill with zeros? Document the completion rate and any error logging.
- Analysis: Compare tool performance based on the defined metrics, highlighting strengths and weaknesses in handling challenging acquisition scenarios.
Visualization of Workflows
Digital Forensics Tool Validation Workflow
Digital Forensics Tool Validation Workflow
Multi-Tool Cross-Verification Logic
Multi-Tool Cross-Verification Logic
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 3: Key Research Reagent Solutions for Digital Forensics Validation
| Item Name | Function in Research & Validation |
|---|---|
| Forensic Write Blocker (Hardware) | A critical hardware interface that prevents data modification during evidence acquisition, ensuring evidence integrity for all subsequent experiments [54]. |
| Validated Forensic Imaging Software (e.g., FTK Imager, Magnet Acquire) | Creates bit-for-bit copies (images) of digital storage media. Serves as the standardized evidence source for all tool testing [26] [54]. |
| Known-Data Test Set | A pre-configured digital evidence sample (disk image, mobile backup) with a documented, known set of artifacts. Acts as the "ground truth" control for testing tool accuracy [1]. |
| Hash Value Generator (e.g., MD5, SHA-256) | A cryptographic algorithm that generates a unique digital fingerprint for a file or disk image. Used to verify data integrity has not changed throughout an experiment [1]. |
| Hex Editor & SQLite Browser | Low-level data analysis tools. The hex editor allows inspection of raw data, while the SQLite browser is essential for examining the database structures common in mobile and application forensics [54]. |
| Standardized Case Management System | Software to document all steps, parameters, tool versions, and results for each validation experiment. Ensures reproducibility and meets legal standards for transparency [54]. |
Frequently Asked Questions (FAQs)
Q1: What are the most significant challenges when extracting data from modern mobile devices? Modern mobile devices present challenges due to hardware-based encryption, secure boot processes, and the constant evolution of operating systems. Traditional forensic methods often cannot bypass these security measures, requiring specialized tools capable of dealing with advanced encryption and recovering data from secure apps and deleted file spaces [2].
Q2: How does cloud forensics differ from traditional disk forensics? Cloud forensics involves dealing with data distributed across multiple platforms, devices, and geographical locations. Key challenges include navigating different cloud providers' policies on data retention, encryption, and access rights. This requires more nuanced approaches and specialized tools compared to traditional forensic methods designed for local storage [2].
Q3: Why is tool validation particularly important for IoT forensics? The Internet of Things (IoT) encompasses a wide range of devices—from wearables to smart home appliances—each with unique operating systems, data formats, and storage protocols. This lack of standardization means a tool that works for one device may not work for another, making rigorous and continuous validation essential for ensuring evidence integrity [2].
Q4: What role does AI play in modern digital forensics tools? Artificial Intelligence (AI) and Machine Learning (ML) dramatically enhance an investigator's ability to process large data volumes. AI-powered tools can automatically flag relevant information, identify anomalies, uncover patterns in seemingly unrelated data, and even make predictive assessments about potential leads, moving investigations from a manual review process to an automated, intelligence-driven one [2].
Q5: How can investigators verify the authenticity of video and audio evidence? With the rise of deepfakes, verifying media authenticity is crucial. Investigators must use advanced techniques and tools that can identify subtle inconsistencies in video frames, audio frequencies, or pixel patterns that indicate manipulation. This ensures that falsified materials do not compromise the integrity of an investigation [2].
Troubleshooting Guides
Issue 1: Incomplete Data Extraction from Mobile Devices
- Problem: The forensic tool fails to extract a complete set of data, such as chat messages from encrypted apps or files from a locked device.
- Solution:
- Verify Tool Compatibility: Check the tool's documentation to ensure it supports the specific device model and operating system version.
- Update Tool and Definitions: Ensure you are using the latest version of the forensic software, as updates frequently include support for new devices and apps.
- Try Multiple Tools: Use a different forensic tool (e.g., switch from Cellebrite to Magnet AXIOM) to perform a second extraction. Different tools may use distinct extraction methods and bypasses.
- Prevention: Maintain a library of multiple, up-to-date forensic tools and establish a protocol for cross-verifying extractions from high-priority devices [2] [26].
Issue 2: Data Volatility and Integrity in Cloud Acquisition
- Problem: Data within a cloud environment can be altered or deleted by other processes or users during the acquisition process, challenging evidence integrity.
- Solution:
- Use API-Based Acquisition: Whenever possible, use tools that leverage cloud service provider APIs, as they can often create a logical snapshot of the data at the time of the request.
- Document the Chain of Custody: Meticulously document the date, time, and method of acquisition. This includes recording the specific API calls made.
- Preserve with Cloud-Native Tools: Utilize tools like Belkasoft X, which are designed for cloud data extraction and can help in preserving evidence in a forensically sound manner from various cloud services [2] [26].
Issue 3: Inability to Parse Proprietary Data Formats from IoT Devices
- Problem: A forensic tool acquires raw data from an IoT device but cannot parse it into a human-readable format, rendering it useless for analysis.
- Solution:
- Hex View and Manual Analysis: Use a forensic tool's hex viewer to inspect the raw data structure and look for known file headers or plaintext strings.
- Identify the Data Schema: Research the device's SDK or data sheets to understand its proprietary data format.
- Develop a Custom Parser: Use a modular, open-source forensic platform like the Digital Forensics Framework (DFF) or Autopsy, which allows for the development and integration of custom scripts or plugins to parse unique data formats [26].
Issue 4: False Positives in AI-Powered Analysis
- Problem: An AI/ML feature in a forensic tool flags irrelevant data as significant, leading investigators down an incorrect path.
- Solution:
- Calibrate the Algorithm: Retrain or fine-tune the AI model with a dataset that is representative of your specific investigative context to reduce bias.
- Adjust Confidence Thresholds: Increase the confidence threshold for alerts within the tool to filter out weaker, less reliable matches.
- Human-in-the-Loop Verification: Never rely solely on automated flags. Establish a protocol where all AI-generated leads must be verified through traditional analytical methods by an investigator [2].
Experimental Protocols for Tool Validation
Protocol 1: Comparative Efficacy Testing for Mobile Data Extraction
Objective: To quantitatively compare the data extraction capabilities of different forensic tools against a standardized set of mobile devices.
- Setup: Create a controlled test environment with multiple identical mobile device models (e.g., 5x Samsung Galaxy S24). Install a standardized dataset including contacts, SMS, MMS, images, and data from popular apps (WhatsApp, Signal, Instagram).
- Procedure:
- For each tool in the test (e.g., Cellebrite UFED, Magnet AXIOM, X-Ways Forensics), perform a full physical/logical extraction on each of the test devices.
- Document the extraction time, success rate, and any errors encountered.
- Data Analysis:
- Use a checksum (e.g., SHA-256) to verify the integrity of the extracted images.
- Compare the parsed output from each tool against the known dataset. Calculate the percentage of data successfully recovered by each tool.
- Record the results in a structured table for comparison.
Table: Mobile Tool Extraction Efficacy
| Forensic Tool | Device Model | OS Version | Extraction Type | Data Types Recovered | Success Rate | Extraction Time | Notes |
|---|---|---|---|---|---|---|---|
| Cellebrite UFED 7.5 | Samsung S24 | Android 14 | Physical | SMS, MMS, Calls, App Data | 98% | 45 min | Full file system access |
| Magnet AXIOM 6.5 | Samsung S24 | Android 14 | Logical | SMS, Calls, Photos | 85% | 15 min | App data partially parsed |
| X-Ways Forensics 4.5 | Samsung S24 | Android 14 | Logical | SMS, Calls | 80% | 25 min | Relies on ADB backup |
Protocol 2: Fidelity and Performance Analysis for Cloud Evidence
Objective: To assess the accuracy and completeness of cloud forensic tools in replicating cloud-stored data structures.
- Setup: Configure a test enterprise cloud environment (e.g., Microsoft 365, Google Workspace). Populate it with a known set of data: user accounts, emails, calendar entries, and files stored in cloud drives.
- Procedure:
- Use different cloud forensic tools (e.g., Belkasoft X, Oxygen Forensic Cloud Extractor) to acquire data from the test environment.
- Perform acquisitions via different methods: provider API, browser session, and network traffic capture.
- Data Analysis:
- Compare the acquired data from each tool/method against the known dataset for fidelity.
- Assess the tool's ability to preserve folder hierarchies, metadata (like "last modified" timestamps), and shared permissions.
- Measure the time and computational resources required for each acquisition method.
Table: Cloud Tool Acquisition Fidelity
| Forensic Tool | Cloud Service | Acquisition Method | Data Fidelity | Metadata Preserved | Hierarchy Maintained | Acquisition Time |
|---|---|---|---|---|---|---|
| Belkasoft X | Google Workspace | API | High | Yes | Yes | 30 min |
| Cloud Extractor A | Microsoft 365 | Browser Session | Medium | Partial | Yes | 75 min |
| Tool B | Dropbox | Network Capture | Low | No | No | 120 min |
Experimental Workflow Visualization
The diagram below outlines the core logical workflow for validating a digital forensics tool, from definition to final reporting.
Digital Forensics Tool Validation Workflow
The Scientist's Toolkit: Research Reagent Solutions
Table: Essential Digital Forensics Tools and Their Functions
| Tool Name | Category | Primary Function | Key Application in Research |
|---|---|---|---|
| Cellebrite UFED | Mobile Extraction | Extracts data from mobile devices, even locked or encrypted ones. | Acquiring comprehensive evidence from smartphones for efficacy comparison studies [26]. |
| Magnet AXIOM | Multi-Source Analysis | Collects, analyzes, and reports evidence from computers, mobiles, and the cloud. | Used in experiments to test integrated analysis capabilities across diverse evidence sources [26]. |
| Belkasoft X | Multi-Source Analysis | Gathers and analyzes evidence from computers, mobile devices, and cloud services. | Validating tool performance in extracting and correlating artifacts from multiple evidence types [26]. |
| Autopsy | Forensic Platform | Open-source platform for analyzing disk images and file systems; highly modular. | Serves as a baseline or extensible framework for developing and testing custom parsers in research [26]. |
| FTK Imager | Disk Imaging | Creates forensically sound copies (images) of digital media without altering data. | The foundational step for preserving evidence integrity in controlled experiments involving hard drives [26]. |
| Bulk Extractor | Data Carving | Scans disk images and extracts information without parsing the file system. | Useful for recovering specific data types (emails, URLs) from corrupted drives or unallocated space in tests [26]. |
| ExifTool | Metadata Analysis | Reads, writes, and edits metadata in a wide variety of files. | Critical for validating the preservation and accuracy of file metadata in forensic tool output [26]. |
Evaluating Emerging Forensic-as-a-Service (FaaS) Models Through a Validation Lens
FaaS Technical Support Center
This guide provides troubleshooting and methodological support for researchers validating emerging Forensic-as-a-Service (FaaS) models. FaaS provides cloud-based, on-demand forensic services through a subscription model, allowing customers and justice agencies to leverage specialized expertise [57].
Frequently Asked Questions (FAQs)
Q1: What core technologies ensure evidence integrity in FaaS platforms? Maintaining the chain of custody for digital evidence is a primary concern in cloud-based forensics. Validation protocols must verify that the FaaS provider uses technologies like blockchain and AI to secure samples from tampering and manipulation, ensuring the probity and ultimate admissibility of the forensic opinion [57].
Q2: How do data sovereignty laws impact FaaS validation? The distributed nature of cloud storage introduces significant legal challenges. Researchers must validate a FaaS provider's ability to navigate conflicts in data sovereignty laws (e.g., EU GDPR vs. U.S. CLOUD Act) for cross-border evidence retrieval, a process that can otherwise cause major delays [10].
Q3: What are the key challenges in validating AI-powered forensic tools? AI is a double-edged sword in digital forensics. While it can accelerate data analysis and improve deepfake detection accuracy, it also introduces validation challenges. These include a lack of algorithmic transparency ("black box" models) and potential biases in training data, which can undermine the credibility of evidence in court and amplify forensic errors [10].
Q4: Which FaaS service segments should our validation framework prioritize? The global FaaS market can be segmented by type and end-user. A robust validation strategy should initially focus on high-demand segments, though all service types require rigorous testing protocols [58].
Table 1: Global Digital Forensic Laboratory-as-a-Service Market Segmentation
| Segment Type | Key Categories | Primary End-Users |
|---|---|---|
| By Service Type | Mobile Forensics, Computer Forensics, Network Forensics [58] | Government & Law Enforcement Agencies [58] |
| By End-User | Banking, Financial Services, and Insurance (BFSI), Information Technology, Telecom [58] |
Troubleshooting Guides
Issue 1: Inconsistent Forensic Results from AI Models
- Problem: AI-driven forensic tools produce variable or non-reproducible results, complicating validation.
- Solution:
- Protocol: Implement a standardized input dataset with known ground truth for all model testing phases.
- Action: Scrutinize the model's training data for representativeness and bias. Insist on provider documentation regarding data provenance and model architecture to address the "black box" problem [10].
- Verification: Run the standardized dataset through multiple versions of the AI tool and compare outputs for consistency.
Issue 2: Evidence Processing Timeouts in Cloud Environments
- Problem: Forensic analysis jobs in FaaS platforms fail due to execution timeouts, especially with large datasets.
- Solution:
- Protocol: Profile the time required for evidence acquisition, processing, and analysis against the FaaS platform's service level agreements (SLAs).
- Action: Configure timeouts at multiple levels. Ensure the function's
hard_timeoutand the gateway'sread_timeoutandwrite_timeoutvalues are set sufficiently high to accommodate complex analyses [59]. - Verification: Use the FaaS provider's logging and monitoring tools to confirm that jobs are completing fully and identify the specific stage where timeouts occur.
Issue 3: Data Acquisition Failures from Heterogeneous IoT Devices
- Problem: Cannot extract data from the diverse ecosystem of IoT devices (e.g., smart home sensors, vehicle systems) for forensic investigation.
- Solution:
- Protocol: Develop a pre-acquisition checklist that includes identifying the device's make, model, hardware version, and security protocols.
- Action: Move beyond traditional data decryption tools. Validation must extend to integrating proprietary vehicular security protocols and analyzing over-the-air (OTA) update logs [10].
- Verification: Test acquisition tools on a calibrated lab environment containing representative IoT devices before use in active investigations.
Experimental Protocol for FaaS Tool Validation
Objective: To systematically evaluate the accuracy, efficiency, and reliability of a new AI-powered evidence triage tool offered via a FaaS platform.
Sample Preparation:
- Create a standardized forensic corpus containing a known mix of data types (documents, images, emails, logs). Artificially inject pre-defined "evidence" patterns and "anomalies" into the corpus.
- Ensure the dataset is large enough (terabyte-scale) to stress-test the cloud service's capabilities [10].
Tool Configuration & Execution:
- Subscribe to the target FaaS tool and configure it according to the vendor's specifications.
- Process the standardized corpus through the tool. Record the exact time of ingestion and the time when results are delivered.
Data Analysis & Metric Collection:
- Accuracy: Calculate the tool's precision (percentage of correctly identified items from all items flagged) and recall (percentage of all known evidence items that were correctly flagged) [10].
- Efficiency: Measure the total processing time and compute the throughput (GB processed per hour).
- Resource Utilization: If available, monitor the computational resources allocated by the FaaS platform during the analysis.
Reporting:
- Document all parameters, results, and observations. The final report should conclude on the tool's suitability for use in a legal context based on the measured metrics.
The Scientist's Toolkit: Key Research Reagent Solutions
Table 2: Essential Digital Forensics Research Materials
| Item / Solution | Function in Validation |
|---|---|
| Standardized Forensic Datasets | Calibrated, ground-truthed digital evidence corpora for benchmarking tool accuracy and performance [10]. |
| Cloud Evidence Acquisition Tools | Specialized software and APIs for legally sound data collection from diverse cloud service providers [10]. |
| IoT Device Lab | A curated collection of common IoT devices (smartphones, wearables, smart home sensors) for testing physical and logical extraction methods [10]. |
| Blockchain Verification Tool | Software to independently verify the integrity and chain of custody hashes recorded by the FaaS provider [57]. |
FaaS Validation Workflow and Architecture
FaaS Validation Workflow
FaaS System Architecture
Conclusion
In an era defined by technological disruption, static validation protocols are obsolete. A successful digital forensics practice must be built upon a dynamic, principled, and continuous validation strategy that keeps pace with tool evolution. The integration of AI demands new validation rigour to ensure explainability and avoid bias, while the complexities of cloud and mobile ecosystems require more nuanced methodological checks. The future will be shaped by automated validation workflows, the development of international standards for cross-border investigations, and a professional culture that treats validation not as an optional step, but as an ethical imperative. By adopting the strategies outlined across foundational, methodological, troubleshooting, and comparative intents, researchers and forensic professionals can ensure their findings remain scientifically sound, legally defensible, and critically trusted.
References
- 1. What is forensic validation and how is it used? [https://www.envistaforensics.com/knowledge-center/insights/articles/forensic-validation-pay-attention-to-the-man-behind-the-curtain/]
- 2. CEO Lee Reiber: The Digital Forensics Landscape in 2025 [https://www.oxygenforensics.com/en/resources/digital-forensics-trends-2025/]
- 3. Future of Digital Forensics: Innovations for 2025 [https://www.cognyte.com/blog/digital-forensics-investigations/]
- 4. Top 6 Trends Shaping Modern DFIR in 2025 [https://belkasoft.com/dfir-trends-2025]
- 5. Validating and Testing Forensics Software [https://www.geeksforgeeks.org/techtips/validating-and-testing-forensics-software/]
- 6. Best Practices for Image Authentication - SWGDE [https://www.swgde.org/documents/published-complete-listing/18-i-001-best-practices-for-image-authentication/]
- 7. A transparent approach: Openness in forensic science ... [https://www.sciencedirect.com/science/article/pii/S2589871X24000214]
- 8. Best Practices for Digital Imaging in Forensic Investigations [https://www.linkedin.com/advice/1/what-best-practices-using-digital-imaging-forensic-o5jff]
- 9. Understanding WCAG 2 Contrast and Color Requirements [https://webaim.org/articles/contrast/]
- 10. Key Trends in Digital Forensics 2025: Chanllenges and ... [https://www.salvationdata.com/knowledge/key-trends-in-digital-forensics-for-2025/]
- 11. Unpacking Rule Changes on Expert Testimony [https://dicellolevitt.com/unpacking-rule-changes-on-expert-testimony/]
- 12. Federal Circuit Tightens Standard for Patent Damages ... [https://www.whitecase.com/insight-alert/federal-circuit-tightens-standard-patent-damages-experts]
- 13. Impact of Cloud Services on Digital Forensic Investigations [https://www.hcltech.com/blogs/impact-of-cloud-services-on-digital-forensic-investigations]
- 14. Exploring New Encryption Technology in 2025 [https://concentric.ai/advances-in-encryption-technology/]
- 15. Digital Evidence: FAQs [https://www.forensicsciencesimplified.org/digital/faqs.html]
- 16. Encryption in 2025: Trends & Best Practices [https://ciphertex.com/2025/07/21/encryption-in-2025-trends-best-practices/]
- 17. Thales 2025 Global Cloud Security Study Reveals ... [https://cpl.thalesgroup.com/about-us/newsroom/thales-2025-cloud-security-study-reveals-ai-tool-sprawl-security-gap]
- 18. Compliance Trends of 2025 [https://www.encryptionconsulting.com/compliance-trends-of-2025/]
- 19. The State of AI: Global Survey 2025 [https://www.mckinsey.com/capabilities/quantumblack/our-insights/the-state-of-ai]
- 20. When Digital Forensics Goes Wrong: Cases of ... [https://eclipseforensics.com/when-digital-forensics-goes-wrong-cases-of-misinterpreted-evidence/]
- 21. The Fragile Nature of Digital Evidence—and How It Can ... [https://www.simmonswagner.com/the-fragile-nature-of-digital-evidence-and-how-it-can-be-challenged/]
- 22. Reliability validation enabling framework (RVEF) for digital ... [https://www.sciencedirect.com/science/article/pii/S266628172300063X]
- 23. Digital Forensics and Incident Response: A Guide to Cyber ... [https://www.digitalguardian.com/blog/digital-forensics-and-incident-response-guide-cyber-investigation]
- 24. Certificate in Digital Forensics Fundamentals [https://www.qa.com/en-us/course-catalogue/courses/certificate-in-digital-forensics-fundamentals-qaidigfor/]
- 25. Validation framework for in vivo digital measures - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC11751004/]
- 26. A Guide to Digital Forensics and Cybersecurity Tools (2025) [https://www.forensicscolleges.com/blog/resources/guide-digital-forensics-tools]
- 27. Digital Forensic Validation: Principles, Methods, and ... [https://www.linkedin.com/pulse/digital-forensic-validation-principles-methods-examples-james-henning-xbjye]
- 28. Why Hash Values Are Crucial in Digital Evidence Authentication [https://blog.pagefreezer.com/importance-hash-values-evidence-collection-digital-forensics]
- 29. Verification Hash - an overview | ScienceDirect Topics [https://www.sciencedirect.com/topics/computer-science/verification-hash]
- 30. Digital-Forensics-Tools-and-Techniques-in-2025 [https://www.jaroeducation.com/blog/digital-forensics-tools-and-techniques/]
- 31. Training, validation, and test data sets [https://en.wikipedia.org/wiki/Training,_validation,_and_test_data_sets]
- 32. 7 data testing methods, why you need them & when to use ... [https://www.ibm.com/think/insights/data-testing-methods]
- 33. Three Interpretability Methods to Consider When ... [https://towardsdatascience.com/three-interpretability-methods-to-consider-when-developing-your-machine-learning-model-5bf368b47fac/]
- 34. Interpretability Methods in Machine Learning: A Brief Survey [https://www.twosigma.com/articles/interpretability-methods-in-machine-learning-a-brief-survey/]
- 35. Beyond The Screen, Part 7: Forensic Readiness For The AI ... [https://lcgdiscovery.com/beyond-the-screen-part-7-forensic-readiness-for-the-ai-era/]
- 36. Open Source Testing Tools Comprehensive Guide [https://www.radview.com/blog/open-source-testing-tools-guide/]
- 37. ben-marshall/awesome-open-hardware-verification [https://github.com/ben-marshall/awesome-open-hardware-verification]
- 38. Text has enhanced contrast | ACT Rule | WAI [https://www.w3.org/WAI/standards-guidelines/act/rules/09o5cg/]
- 39. Elements must meet minimum color contrast ratio thresholds [https://dequeuniversity.com/rules/axe/4.8/color-contrast]
- 40. Color contrast - Accessibility - MDN Web Docs - Mozilla [https://developer.mozilla.org/en-US/docs/Web/Accessibility/Guides/Understanding_WCAG/Perceivable/Color_contrast]
- 41. Using Geolocation Artifacts and Timeline Analysis to Solve ... [https://www.forensicfocus.com/webinars/using-geolocation-artifacts-and-timeline-analysis-to-solve-the-case-a-digital-forensics-case-study/]
- 42. Strategies and Challenges of Timestamp Tampering for ... [https://arxiv.org/html/2501.00175v1]
- 43. Geolocation Artifacts: How to Find Them on Mobile Devices [https://www.magnetforensics.com/blog/how-to-uncover-geolocation-artifacts-for-mobile-device-investigations/]
- 44. Integrating implicit timing information into digital forensic ... [https://www.sciencedirect.com/science/article/pii/S266628172400074X]
- 45. Device Tracking Using Browser-Based Artifacts (Part 1) [https://www.sans.org/blog/big-brother-forensics-device-tracking-using-browser-based-artifacts-part-1]
- 46. Five Anti-Forensic Techniques Used to Cover Digital ... [https://www.eccouncil.org/cybersecurity-exchange/computer-forensics/anti-forensic-techniques-used-to-cover-digital-footprints/]
- 47. What is Data Obfuscation? [https://www.crowdstrike.com/en-us/cybersecurity-101/data-protection/data-obfuscation/]
- 48. Automatically generating digital forensic reference data ... [https://www.sciencedirect.com/science/article/pii/S2666281725001258]
- 49. Why Automation in Digital Forensics? [https://www.magnetforensics.com/blog/why-automation-in-digital-forensics/]
- 50. Buyer's guide for digital forensics workflow automation ... [https://www.magnetforensics.com/resources/buyers-guide-for-digital-forensics-workflow-automation-solutions/]
- 51. Configure the Node.js agent - Contrast Documentation [https://docs.contrastsecurity.com/en/node-js-configuration.html]
- 52. Top 10 Paid Digital Forensic Tools in 2025: Features, Pros ... [https://hawkeyeforensic.com/top-10-paid-digital-forensic-tools-in-2025-features-pros-cons/]
- 53. Top 10 Digital Forensics Tools in 2025: Features, Pros ... [https://www.scmgalaxy.com/tutorials/top-10-digital-forensics-tools-in-2025-features-pros-cons-comparison/]
- 54. Digital Forensics Tools: The Ultimate Guide (2024) [https://www.magnetforensics.com/blog/digital-forensics-tools-the-ultimate-guide-2024/]
- 55. Troubleshooting - FCS Wiki - Forensic Comparison Software [https://wiki.forensic-software.com/en/public/troubleshoot]
- 56. Validation of forensic tools and methods: A primer for the ... [https://www.marshall.edu/cyber/2022/07/11/validation-of-forensic-tools-and-methods-a-primer-for-the-digital-forensics-examiner/]
- 57. Forensics- as - a and Digital Insurance: A Roadmap for... Service [https://government.economictimes.indiatimes.com/blog/forensics-as-a-service-and-digital-insurance-a-roadmap-for-futuristic-entrepreneurship/120433272]
- 58. Global Digital Forensic Laboratory as Market a ... Service Strategic [https://www.datainsightsmarket.com/reports/global-digital-forensic-laboratory-as-a-service-market-17592]
- 59. Troubleshooting - OpenFaaS [https://ericstoekl.github.io/faas/troubleshooting/]