From Lab to Courtroom: Integrating TRL Assessment into the Forensic Software Development Lifecycle
This article provides a comprehensive framework for integrating Technology Readiness Level (TRL) assessment into the forensic software development lifecycle.
From Lab to Courtroom: Integrating TRL Assessment into the Forensic Software Development Lifecycle
Abstract
This article provides a comprehensive framework for integrating Technology Readiness Level (TRL) assessment into the forensic software development lifecycle. Aimed at developers, forensic scientists, and laboratory managers, it bridges the gap between theoretical innovation and court-admissible digital tools. The content explores the foundational principles of TRL, outlines a methodological approach for its application in development, addresses common troubleshooting and optimization challenges, and establishes validation protocols for legal and scientific standards. By adopting a structured TRL-driven approach, organizations can enhance the reliability, admissibility, and effectiveness of digital forensic tools in an era of rapidly evolving cyber threats and complex data environments.
Understanding TRL and the Modern Digital Forensics Landscape
Technology Readiness Levels (TRLs) are a systematic metric used to assess the maturity of a particular technology during its development and acquisition phases. The framework establishes a unified scale from basic research (TRL 1) to full commercial application (TRL 9), enabling consistent discussion of technical maturity across different types of technology. Originally developed by NASA during the 1970s, the TRL scale has since been adopted by the U.S. Department of Defense, the European Space Agency (ESA), the European Union, and various other organizations and industries worldwide [1] [2].
This application note details the standardized definitions, assessment protocols, and integration methodologies for implementing TRL assessment within forensic software development lifecycle research. The structured approach facilitates risk management, funding decisions, and strategic planning for technology development and transition [1].
The 9-Level TRL Scale: Definitions and Applications
The following table summarizes the standardized definitions and characteristics for each of the nine Technology Readiness Levels.
Table 1: Technology Readiness Levels (TRLs) Definition Scale
| TRL | Description | Key Activities & Milestones | Outputs & Evidence |
|---|---|---|---|
| TRL 1 | Basic principles observed and reported [3] [4]. | Initial scientific research; translation of results into future R&D [3]. | Published research papers documenting underlying principles. |
| TRL 2 | Technology concept and/or application formulated [3] [4]. | Practical applications are postulated based on observed principles [3] [1]. | Specification of technology concept; no experimental proof. |
| TRL 3 | Analytical and experimental critical function and/or characteristic proof-of-concept [3] [4]. | Active R&D; analytical/lab studies; proof-of-concept model construction [3]. | Experimental proof-of-concept; validation of critical function. |
| TRL 4 | Component and/or breadboard validation in laboratory environment [3] [1]. | Multiple component pieces are integrated and tested in a lab [3]. | Basic technology validation in a laboratory environment [4]. |
| TRL 5 | Component and/or breadboard validation in relevant environment [3] [1]. | Rigorous testing of breadboard technology in simulated realistic environments [3]. | Technology basic validation in a relevant environment [4]. |
| TRL 6 | System/subsystem model or prototype demonstration in a relevant environment [3] [1]. | A fully functional prototype or representational model is tested [3]. | Technology model/prototype demonstration in a relevant environment [4]. |
| TRL 7 | System prototype demonstration in an operational environment [3] [1]. | Working model or prototype is demonstrated in a space/operational environment [3]. | Technology prototype demonstration in an operational environment [4]. |
| TRL 8 | Actual system completed and "flight qualified" through test and demonstration [3] [1]. | System is tested, "flight qualified," and ready for implementation [3]. | Actual technology completed and qualified through test and demonstration [4]. |
| TRL 9 | Actual system "flight proven" through successful mission operations [3] [1]. | Technology has been proven during a successful mission [3]. | Actual technology qualified through successful mission operations [4]. |
TRL Assessment Protocol for Forensic Software Development
Integrating TRL assessment within the forensic software development lifecycle requires a phased experimental and validation protocol. The following workflow delineates the key assessment activities for each major development phase.
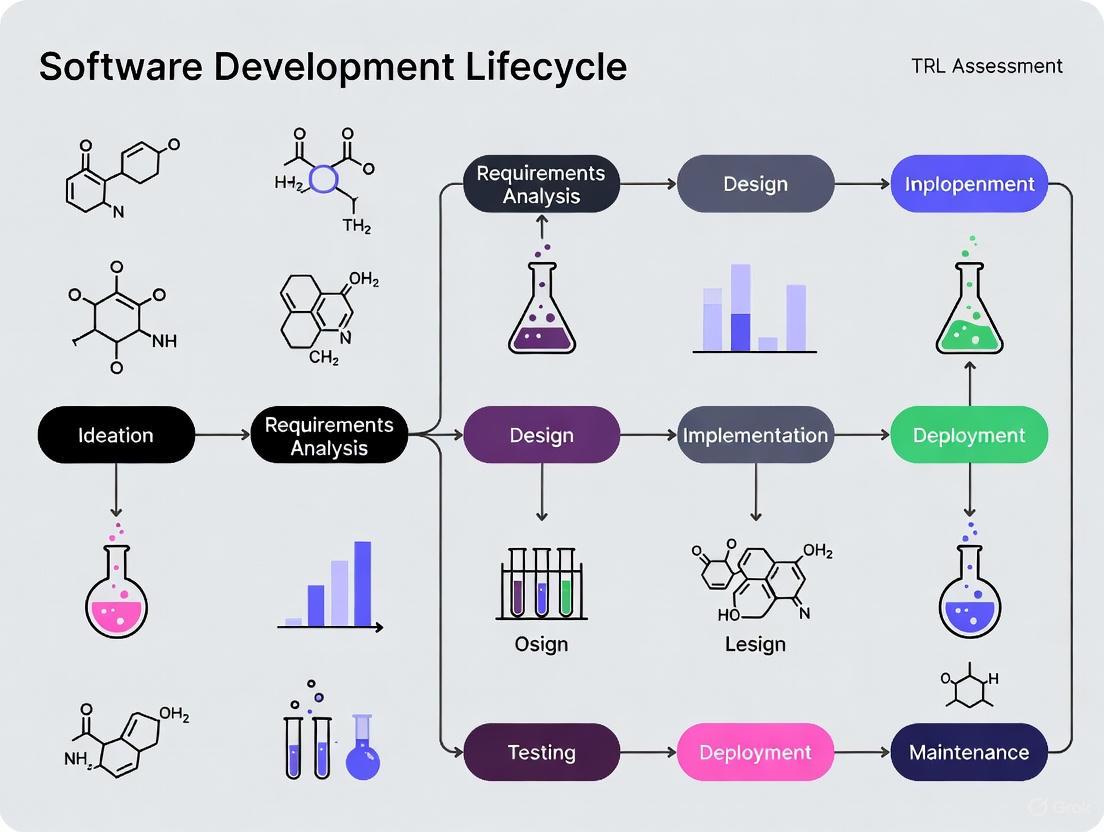
Diagram 1: TRL Assessment in Forensic Software Development Lifecycle
Phase 1: Foundational Research (TRL 1-2)
Objective: Establish scientific basis and formulate a practical technology concept for forensic application.
Experimental Protocol:
- Literature Review & Gap Analysis: Conduct a systematic review of existing digital forensics frameworks, secure software development lifecycles (S-SDLC), and cloud forensic challenges [5]. Map identified gaps to potential novel software solutions.
- Abuse Case Formulation: Define hypothetical misuse scenarios and adversarial requirements specific to the forensic context. These abuse cases will inform security and forensic-ready requirements [6].
- Feasibility Study: Perform analytical studies to determine if the core software concept can address the identified gaps and abuse cases. The output is a Technology Concept Document specifying potential application and theoretical performance benchmarks.
Phase 2: Proof-of-Concept & Laboratory Validation (TRL 3-4)
Objective: Demonstrate critical functional feasibility and validate core components in a controlled lab environment.
Experimental Protocol:
- Critical Function Prototyping: Develop a limited, non-integrated software module (e.g., a specific evidence collection algorithm or log parser) to prove a core concept. This constitutes the Proof-of-Concept (PoC) Model [3].
- Component Breadboarding & Lab Testing: Integrate multiple discrete software components (e.g., evidence collection, secure storage, integrity hashing) into a "breadboard" architecture. Test this integrated unit in a controlled laboratory environment using synthetic or historical non-sensitive data.
- Validation Metrics: Measure performance against predefined criteria from the feasibility study, such as data processing accuracy, integrity verification success rate, and error handling. Success leads to a TRL 4 Validation Report.
Phase 3: Relevant Environment Testing (TRL 5-6)
Objective: Validate the technology in environments that simulate real-world operational conditions.
Experimental Protocol:
- Relevant Environment Simulation: Create a high-fidelity test environment that mirrors a production forensic infrastructure. This includes replicating network configurations, cloud service APIs (e.g., from AWS or Azure), and data loads comparable to real casework [6].
- Alpha-Prototype Development: Build a fully functional, integrated software prototype that includes all major forensic and security features.
- Rigorous Functional & Security Testing: Subject the prototype to comprehensive testing in the simulated environment.
- Static Application Security Testing (SAST): Analyze source code for vulnerabilities [6].
- Dynamic Application Security Testing (DAST): Test the running application for runtime flaws [6].
- Forensic Readiness Drills: Simulate incident response scenarios to test the prototype's ability to collect, preserve, and report admissible digital evidence effectively.
Phase 4: Operational Demonstration & Qualification (TRL 7-8)
Objective: Demonstrate the system prototype in a live operational environment and complete final qualification.
Experimental Protocol:
- Controlled Field Demonstration (TRL 7): Deploy the system prototype within a limited, monitored segment of a live forensic laboratory or corporate IT environment. Use the system to process and analyze real digital evidence from a non-critical, approved case under strict supervision.
- Data Collection & Performance Analysis: Collect extensive performance data, including system reliability, evidence processing speed, resource utilization, and admissibility of generated outputs.
- Final System Qualification (TRL 8): The final software system undergoes formal qualification testing against all functional, security, and forensic requirements. This includes:
- Audit and Compliance Review: Ensuring compliance with standards like ISO/IEC 27034 or NIST SSDF [6].
- Final Security Assessment: Penetration testing and code review.
- Production Readiness Review: A formal gate review authorizing the system for full deployment.
Phase 5: Mission Operations (TRL 9)
Objective: Prove the actual system through successful use in full-scale mission operations.
Experimental Protocol:
- Full-Scale Deployment: Roll out the qualified system across the intended operational environments (e.g., multiple forensic labs, corporate security teams).
- Operational Monitoring & Feedback Loop: Implement continuous monitoring to track system performance, reliability, and the admissibility of evidence it helps to collect in real cases over an extended period.
- Post-Mission Analysis: Document the system's performance, lessons learned, and any identified areas for improvement. Successful performance in this phase confirms TRL 9 status.
The Scientist's Toolkit: Essential Research Reagents & Solutions
The following table details key tools, standards, and frameworks essential for conducting TRL assessments in forensic software development.
Table 2: Key Research Reagents & Solutions for TRL Assessment
| Tool/Reagent | Function/Description | Application in Forensic S-SDLC |
|---|---|---|
| Threat Modeling Frameworks | Systematic approach to identify and mitigate security threats during design [6]. | Informs security requirements and abuse cases at TRL 2-3; critical for "forensic-by-design" [5]. |
| SAST/DAST Tools | Static and Dynamic Application Security Testing tools to automatically scan for vulnerabilities [6]. | Core validation tools for component (TRL 4-5) and system-level (TRL 6-7) testing. |
| Software Bill of Materials (SBOM) | A nested inventory of all software components and dependencies [6]. | Manages supply-chain risk; essential for verification and audit at TRL 6-8. |
| Forensic Readiness Drills | Simulated incident response exercises to test evidence collection and handling procedures. | Validates the "forensic-ready" property of the software in relevant (TRL 6) and operational (TRL 7) environments. |
| Policy-as-Code Gates | Automated security and compliance checks embedded within the CI/CD pipeline [6]. | Enforces security standards continuously from TRL 4 onwards; gates deployment at TRL 8. |
| ISO/IEC 15288 & 12207 | International standards for systems and software engineering life cycle processes [5]. | Provides the overarching process framework for aligning FbD development with engineering best practices. |
Risk Management: Navigating the "Valley of Death"
A critical concept in TRL progression is the "Valley of Death"—the difficult transition from a validated prototype (TRL 6) to a system demonstrated in an operational environment (TRL 7) [2]. This phase requires a significant increase in funding, rigorous testing, and access to real-world deployment opportunities.
Diagram 2: Risk Profile and the TRL Valley of Death
Mitigation Strategies for Forensic Software:
- Incremental Demonstration: Use phased rollouts in progressively more realistic environments, such as internal lab networks before live forensic environments.
- Strategic Partnerships: Collaborate with end-user organizations (e.g., law enforcement digital forensics units) early to co-develop requirements and secure test opportunities.
- Targeted Funding: Seek grants or internal funding specifically earmarked for technology demonstration (TRL 6-7) to bridge this critical gap.
The digital forensics field is confronting unprecedented challenges that threaten its fundamental capacity to conduct effective investigations. The convergence of exponential data growth, the geographical and legal complexities of cloud computing, and the evidentiary ambiguities introduced by AI-generated media are creating critical impediments to justice and security [7] [8] [9]. These challenges are not merely operational but are deeply technical, demanding a more structured and rigorous approach to the development of forensic tools and methodologies. This application note frames these core challenges within the context of integrating Technology Readiness Level (TRL) assessment into the forensic software development lifecycle. By providing quantitative data, experimental protocols, and structured frameworks, this document aims to equip researchers and developers with the methodologies needed to advance forensic capabilities in the face of these evolving threats.
Quantitative Analysis of Core Challenges
The scale and impact of the primary challenges facing digital forensics can be quantitatively characterized to guide research and development priorities. The data underscores the necessity for a structured development approach to achieve admissible and actionable results.
Table 1: Quantitative Analysis of Digital Forensics Core Challenges
| Challenge Dimension | Key Metric | Impact on Digital Forensics | Structured Development Imperative |
|---|---|---|---|
| Data Volume & Variety [7] [8] | - Exponential data growth from IoT, mobile, and enterprise systems.- Evidence formats: Video, audio, logs, documents, IoT data streams. | - Creates major processing bottlenecks [7].- Increases risk of critical evidence being overlooked during manual review [8]. | - Requires development of scalable, AI-powered analytics for intelligent indexing and triage [8] [10].- Necessitates modular software architecture to handle diverse data parsers. |
| Cloud Complexity [7] [9] [10] | - Data distributed across multiple jurisdictions and platforms.- Differing data retention and access policies among providers. | - Lengthy evidence acquisition due to cross-border legal processes [7].- Introduces chain of custody gaps and potential legal challenges [8]. | - Demands tools with standardized APIs for cloud data extraction [10].- Requires cryptographic hashing and tamper-evident audit logs integrated early in the development lifecycle [8]. |
| AI-Generated Evidence [7] [9] | - Deepfake technology creates realistic fake video/audio.- "Cheapfakes" and other manipulated media are increasingly common. | - Undermines evidence integrity and trust in digital media [7].- Can be used for blackmail, fraud, and misinformation [7]. | - Drives need for integrated deepfake detection modules (e.g., analyzing pixel patterns, audio frequencies) [7] [9].- Tools must provide verifiable metrics on media authenticity for court admissibility. |
Experimental Protocols for Challenge Validation
To systematically evaluate and mitigate these challenges, rigorous experimental protocols are essential. The following methodologies provide a framework for validating the effectiveness of new forensic tools and techniques.
Protocol for Data Volume and Variety Processing
Objective: To quantify the efficiency and accuracy of a forensic tool in processing large, multi-format datasets and identifying relevant evidence.
Evidence Set Curation:
- Assemble a standardized corpus of digital evidence exceeding 10 TB in total size.
- Incorporate a wide variety of formats: disk images, mobile device backups, cloud export data (e.g., from Facebook, Instagram), CCTV footage, and IoT device logs [8] [10].
- Seed the corpus with known target artifacts, including documents, specific images, and communication records.
Tool Deployment and Configuration:
- Configure the tool under test using analysis presets tailored to the simulated case type (e.g., data theft, communication analysis) [10].
- Enable AI-powered features for object detection, face recognition, and text pattern analysis [10].
- For the control, run the same corpus through a baseline forensic tool without these automated features.
Metrics and Measurement:
- Processing Time: Measure the total time to ingest, index, and analyze the complete corpus.
- Recall and Precision: Calculate the percentage of seeded target artifacts correctly identified (recall) and the percentage of flagged items that are genuinely relevant (precision).
- System Resource Utilization: Monitor CPU, memory, and storage I/O throughout the process to assess scalability.
Protocol for Cloud Evidence Acquisition and Integrity
Objective: To verify the reliability and legal defensibility of a cloud forensics tool in acquiring evidence from various platforms while maintaining a secure chain of custody.
Test Environment Setup:
- Create controlled user accounts on multiple cloud platforms (e.g., a social media platform, a cloud storage service).
- Populate these accounts with a known set of data, including files, messages, and metadata.
Evidence Acquisition:
- Use the tool under test to simulate evidence collection via provider APIs, acting as a client application [10].
- The tool should acquire user data without altering the original evidence in the cloud.
Integrity and Logging Verification:
- Upon acquisition, the tool must automatically generate cryptographic hashes (e.g., SHA-256) for all collected files [8].
- Verify that a tamper-evident audit log is created, documenting every action with timestamps and user IDs [8].
- Validate the integrity of the evidence by comparing the generated hashes before and after the transfer to an evidence repository.
Protocol for AI-Generated Media Detection
Objective: To evaluate the efficacy of a forensic tool in distinguishing between authentic and AI-manipulated media.
Media Dataset Preparation:
- Compile a verified dataset containing both authentic media and AI-generated deepfakes/cheapfakes.
- The manipulated media should be generated using state-of-the-art tools (e.g., GANs, diffusion models) and should include various types: face-swapped videos, synthesized audio, and generated images.
Analysis and Detection:
- Process the entire dataset using the forensic tool's deepfake detection module.
- The tool should analyze the media for digital fingerprints of manipulation, such as:
Evaluation of Results:
- Construct a confusion matrix to determine the tool's true positive, false positive, true negative, and false negative rates.
- Calculate the accuracy and F1-score to quantify the tool's detection performance.
- The tool should generate a forensic report detailing the evidence for or against authenticity, suitable for expert testimony [7].
Technology Readiness Level (TRL) Assessment in Forensic SDLC
Integrating TRL assessment into a forensically-aware Software Development Lifecycle (SDLC) ensures that tools are not only functionally sound but also legally robust and reliable. The following workflow visualizes this integration, highlighting critical forensic validation gates.
The Scientist's Toolkit: Research Reagent Solutions
Advancing digital forensics requires a suite of specialized "research reagents"—both technical tools and procedural frameworks. The following table details essential components for developing and validating forensic solutions tailored to modern challenges.
Table 2: Key Research Reagents for Digital Forensics Development
| Category | Item/Technique | Function & Application in Forensic Research |
|---|---|---|
| Data Ingestion & Triage | AI-Powered Analysis Presets [10] | Pre-configured workflows to automate repetitive analysis tasks (e.g., hash filtering, YARA rule scanning, file carving), ensuring consistency and saving time in large-scale investigations. |
| Automated Metadata Tagging [8] | Intelligently indexes evidence upon ingestion, making files immediately searchable by time, location, person, or object. Crucial for managing evidence variety and velocity. | |
| Evidence Integrity | Cryptographic Hashing (e.g., SHA-256) [8] | Generates a unique digital fingerprint for a file or data set. Any alteration changes this hash, providing a primary means of verifying evidence integrity throughout the chain of custody. |
| Tamper-Evident Audit Logs [8] | Automatically records every action performed on a piece of evidence (upload, view, share), with timestamps and user IDs, creating an immutable record for courtroom validation. | |
| Advanced Analysis | Deepfake Detection Algorithms [7] [9] | Analyzes video and audio files for digital fingerprints of manipulation, such as inconsistencies in pixel patterns, audio frequencies, or lighting, to verify media authenticity. |
| Offline LLM (e.g., BelkaGPT) [10] | A Large Language Model that operates on isolated case data to process text-based artifacts (emails, chats), detecting topics and emotional tones without compromising data privacy. | |
| Validation & Standards | ISO/IEC 27037 Guidelines [7] | An international standard providing guidelines for identifying, collecting, and preserving digital evidence. Serves as a benchmark for developing legally admissible forensic tools. |
| Controlled Evidence Corpora | Standardized, well-documented datasets of digital evidence (including known deepfakes and authentic media) used for tool benchmarking, validation, and comparative performance analysis. |
The tripartite challenge of data volume, cloud complexity, and AI-generated evidence represents a fundamental inflection point for digital forensics. Overcoming these obstacles requires a departure from ad-hoc tool development and toward a structured, rigorous lifecycle model informed by TRL assessment. The quantitative data, experimental protocols, and integration framework provided in this application note establish a foundation for this transition. By adopting these structured development practices, researchers and forensic software developers can create solutions that are not only technologically advanced but also scalable, legally defensible, and capable of preserving evidential integrity in an increasingly complex digital ecosystem. This approach is critical for maintaining the pace of justice and upholding the probative value of digital evidence in 2025 and beyond.
The integration of digital forensic tools into the justice system carries profound implications for individual liberty and legal outcomes. Courts increasingly rely on digital evidence, yet its admissibility hinges entirely on the scientific validity and legal reliability of the tools and methods used to extract and analyze it [11] [12]. The legal standards for admissibility, particularly the Daubert Standard, establish a rigorous framework that demands forensic tools be empirically tested, peer-reviewed, have known error rates, and be widely accepted in the relevant scientific community [12] [13]. Failure to meet these standards can result in the exclusion of critical evidence or, worse, wrongful decisions based on flawed technical findings [11] [13]. This document provides detailed application notes and protocols for integrating Technology Readiness Level (TRL) assessment into the forensic software development lifecycle, ensuring that tools not only perform technically but also withstand legal scrutiny.
Legal and Scientific Foundations for Admissibility
Core Legal Standards
Forensic evidence in the United States is evaluated against a series of legal tests that determine its admissibility in court. The transition from the Frye standard to the Daubert standard represents a significant shift towards a more rigorous, scientific evaluation of evidence [11].
- Frye Standard: Originating from Frye v. United States (1923), this standard requires that the scientific technique or principle underlying the evidence be "sufficiently established to have gained general acceptance in the particular field to which it belongs" [11].
- Daubert Standard: Established in Daubert v. Merrell Dow Pharmaceuticals, Inc. (1993), this standard charges trial judges with the responsibility of being "gatekeepers" of scientific evidence. It provides a more flexible set of factors for judges to consider [11] [13]:
- Whether the theory or technique can be (and has been) tested.
- Whether it has been subjected to peer review and publication.
- The known or potential error rate.
- The existence and maintenance of standards controlling its operation.
- The degree of widespread acceptance within a relevant scientific community.
The Federal Rules of Evidence (FRE), particularly Rule 901, further govern the authentication of digital evidence, requiring that the proponent produce evidence sufficient to support a finding that the digital item is what the proponent claims it is [13].
The NRC and PCAST Reports: A Call for Reform
Two landmark reports have critically shaped the modern expectation for forensic science:
- 2009 National Research Council (NRC) Report: This report shattered the "myth of accuracy" surrounding many traditional forensic disciplines, revealing that many methods, with the exception of DNA analysis, lacked proper scientific validation and foundation [11].
- 2016 PCAST Report: The President's Council of Advisors on Science and Technology (PCAST) reinforced the NRC's findings, calling for stricter scientific validation of forensic feature-comparison methods and highlighting the need for empirical measurement of reliability [11].
These reports have collectively exposed systemic shortcomings, including flawed forensic methods, legal gaps, and issues with the scientific literacy of judges and attorneys, creating an urgent need for reforms that ensure unreliable forensic methods are excluded from judicial proceedings [11].
Validation Protocols and Experimental Methodologies
A robust validation framework is essential for demonstrating that a forensic tool produces reliable, accurate, and repeatable results. The following protocol, adapted from rigorous experimental designs in the field, provides a template for comprehensive tool validation [12].
Comprehensive Tool Validation Protocol
Objective: To quantitatively validate the performance and reliability of a digital forensic tool against established legal and scientific criteria.
Experimental Design:
- Controlled Testing Environment: Utilize isolated, forensically sterile workstations to prevent evidence contamination.
- Comparative Analysis: Compare the tool under test against a validated commercial counterpart (e.g., FTK, EnCase) or an accepted reference tool.
- Triplicate Testing: Conduct all experiments in triplicate to establish repeatability and calculate error rates.
- Blinded Analysis: Where possible, implement blinding to minimize examiner bias during result interpretation.
Test Scenarios & Data Preparation: Prepare controlled evidence samples containing known data artifacts. The testing must encompass at least the following three scenarios:
- Preservation and Collection of Original Data: Verify the tool's ability to create a forensically sound bit-for-bit copy of the original source without alteration, and generate accurate hash values (MD5, SHA-1, SHA-256) for integrity checking.
- Recovery of Deleted Files via Data Carving: Assess the tool's capability to recover files that have been deleted from the filesystem, using a pre-defined set of file types (documents, images, archives).
- Targeted Artifact Searching: Evaluate the tool's search functionality and its ability to identify and parse specific forensic artifacts (e.g., browser history, registry entries, application logs) from a disk image.
Metrics and Data Analysis: Calculate the following key performance indicators for each test scenario:
Table 1: Key Validation Metrics and Their Calculations
| Metric | Description | Calculation Method |
|---|---|---|
| Accuracy | The proportion of true results (both true positives and true negatives) among the total number of cases examined. | (True Positives + True Negatives) / Total Artifacts |
| Error Rate | The proportion of incorrect results (false positives and false negatives) produced by the tool. | (False Positives + False Negatives) / Total Artifacts |
| Repeatability | The tool's ability to produce the same results under identical conditions over multiple trials. | Consistent results in all triplicate runs |
Validation Reporting: The final validation report must document the entire process, including the experimental setup, raw data, calculated metrics, and a definitive conclusion on the tool's reliability for its intended forensic purpose.
Protocol for Validating Explainable AI in Forensic Tools
With the rise of AI in digital forensics, a specialized validation protocol is required to address the "black box" problem and meet the demands of the Daubert standard and FRE 901 [13].
Objective: To validate that an AI-powered forensic tool adheres to the principles of Explainable AI (XAI) and produces forensically sound, court-admissible outputs.
The Four Principles of Explainable AI (per NIST) [13]:
- Explanation: The system must deliver accompanying evidence or reasons for all outputs.
- Meaningful: Explanations must be understandable to the end-user (e.g., the forensic examiner).
- Explanation Accuracy: The provided explanation must correctly reflect the system's process for generating the output.
- Knowledge Limits: The system must only operate under conditions for which it was designed or when it reaches a sufficient confidence in its output.
Validation Workflow:
- Input a diverse set of test data into the AI tool, including edge cases and known problematic data.
- Record all outputs and, crucially, the justifications and confidence scores provided by the tool for each decision.
- Audit the explanation accuracy by having a subject matter expert trace the tool's reasoning against its internal logic (if accessible) and the known ground truth of the test data.
- Test knowledge limits by inputting data outside the tool's intended scope and verifying that it appropriately withholds judgment or flags the input as unsuitable.
- Evaluate meaningfulness by having a certified forensic examiner, trained on the tool, review the explanations and confirm they are comprehensible and sufficient for articulating in a written report or courtroom testimony.
Integrating TRL Assessment into the Forensic SDLC
Integrating TRL assessment into the Software Development Life Cycle (SDLC) ensures that technological maturity and legal admissibility are core considerations from inception to deployment. The concept of forensic readiness must be embedded from the earliest planning phases [14].
Diagram 1: TRL integration in forensic SDLC
The diagram above illustrates how TRL assessment maps onto a forensically-ready SDLC. This integration ensures that every development phase includes activities specifically designed to advance the tool's technological maturity while building the evidence base required for legal admissibility.
Table 2: TRL Milestones and Forensic Admissibility Activities in the SDLC
| SDLC Phase | TRL Range | Key Activities for Legal Admissibility | Outputs for Courtroom Defense |
|---|---|---|---|
| Planning & Design | TRL 1-3 (Basic Research to Proof-of-Concept) | - Define legal requirements (Daubert, FRE).- Establish forensic readiness protocols.- Design for explainability, audit trails, and immutable logs. | - Admissibility Requirements Document.- Architecture diagrams showing data integrity measures. |
| Coding & Development | TRL 4-6 (Lab Validation to Prototype in Relevant Environment) | - Implement detailed logging and evidence provenance tracking.- Code modularly for testing and validation.- Integrate forensic markers for data tracing. | - Peer-reviewed technical papers on the method.- Source code documentation for transparency. |
| Testing & Validation | TRL 4-6 (Continued) | - Execute the validation protocols (Sections 3.1 & 3.2).- Conduct independent peer review.- Calculate accuracy and error rates. | - Comprehensive validation report with error rates.- Results of peer review.- Certification from standards bodies (if applicable). |
| Deployment & Maintenance | TRL 7-9 (System Proven in Operational Environment) | - Deploy with a certification package (all documentation).- Monitor performance in real cases.- Plan for updates and re-validation. | - Chain of custody documentation from real cases.- Testimony from other experts on widespread acceptance.- Audit logs from the tool's operational use. |
The Scientist's Toolkit: Essential Research Reagent Solutions
The following table details key components and their functions in building and validating forensically sound digital tools.
Table 3: Essential Research Reagents for Forensic Tool Development & Validation
| Item / Solution | Function in Development & Validation |
|---|---|
| Controlled Test Image Generator | Creates standardized, forensically-sound disk images with known artifacts (files, logs, deleted data) for controlled tool testing and benchmarking. |
| Hash Value Calculator (Reference) | Provides a ground-truth checksum (e.g., SHA-256) for verifying the absolute integrity of data during preservation and collection tests. |
| Data Carving Benchmark Suite | A collection of file system images with known deleted files to quantitatively measure a tool's file recovery capabilities and error rates. |
| Open-Source Forensic Tools (e.g., Autopsy, Sleuth Kit) | Serves as a reference or baseline for comparative analysis and validation of results, promoting transparency and peer review [12]. |
| Commercial Forensic Tools (e.g., FTK, EnCase) | Acts as a validated commercial benchmark against which the performance and output of new or open-source tools can be compared [12]. |
| Explainable AI (XAI) Framework | A software library or set of principles (per NIST) integrated into AI tools to ensure they provide understandable reasons for their outputs, which is critical for courtroom testimony [13]. |
| Standardized Validation Framework | A structured methodology (e.g., based on NIST Computer Forensics Tool Testing) that outlines a rigorous experimental design for testing tool reliability, repeatability, and error rates [12]. |
The adherence to rigorous, scientifically grounded validation protocols is no longer optional for digital forensic tools; it is a fundamental prerequisite for their admission as evidence in courts of law. By systematically integrating TRL assessment into the software development lifecycle, developers and researchers can create a verifiable trail of evidence that demonstrates a tool's reliability, validates its error rates, and ensures its operations are transparent and explainable. This structured approach directly addresses the critical factors of the Daubert standard and fulfills the urgent need for reform highlighted by the NRC and PCAST reports [11]. Ultimately, embracing this disciplined framework is essential for upholding the integrity of the justice system, ensuring that digital evidence serves as a pillar of truth rather than a source of judicial error.
The integrity of digital evidence, and by extension judicial outcomes, is fundamentally reliant on the reliability of the digital forensics tools used in investigations. The development of these tools, however, faces a unique convergence of challenges: the breakneck pace of technological change in platforms and devices, the absolute requirement for legal defensibility, and the methodological divide between modern agile development practices and traditional, plan-driven Software Development Life Cycle (SDLC) models [15] [16] [9]. This creates a critical gap where the urgent need for updated tools can compromise the rigorous validation they require.
Simultaneously, the field is grappling with an explosion of data volume, variety, and velocity, alongside sophisticated anti-forensic techniques and the complexities of cloud and IoT evidence [8] [10]. These pressures often force tool developers to choose between speed (Agile) and rigor (Traditional SDLC), a compromise that can introduce risk into the entire investigative process. This paper argues for the integration of Technology Readiness Level (TRL) assessment as a unifying framework to bridge this methodological gap. Integrating TRL provides a structured, evidence-based mechanism to guide forensic tools from conceptual, research-oriented prototypes to court-ready, legally defensible products, without sacrificing adaptability or thoroughness.
The Evolving Landscape and Pressing Challenges in Digital Forensics
The environment in which digital forensics tools operate is more dynamic and demanding than ever. Key trends for 2025 illuminate the specific pressures placed on development lifecycles:
- Data Complexity and Scale: Digital evidence is characterized by an exponential growth in volume, variety, and velocity [8]. Investigations now routinely involve petabyte-scale datasets from cloud sources, a vast array of IoT devices, and encrypted mobile platforms, pushing manual analysis to obsolescence [16] [10].
- The Anti-Forensics Challenge: Cybercriminals are increasingly employing sophisticated techniques to erase, obscure, or manipulate digital evidence. These methods include encryption, steganography, and data wiping, which deliberately aim to frustrate forensic analysis [10].
- The Cloud Forensics Hurdle: The distributed nature of cloud storage introduces significant obstacles for investigators, including data fragmentation across global servers, jurisdictional conflicts due to differing national laws, and a lack of visibility and control compared to traditional data sources [16] [17]. Legacy forensic workflows are often incompatible with cloud infrastructure, where data is in constant motion [17].
- The Demand for Automation and AI: To manage data scale and complexity, the field is rapidly adopting AI and machine learning. These technologies accelerate tasks like pattern recognition in logs, media analysis for explicit content, and processing communications via Natural Language Processing (NLP) [10]. However, these AI-driven tools introduce their own need for validation, as "black box" models and training data bias can undermine the credibility of evidence in court [16] [10].
Table 1: Key Market and Technical Drivers Shaping Forensic Tool Development
| Driver | Impact on Forensic Tool Development | Supporting Data |
|---|---|---|
| Market Growth | Increased investment and competition, necessitating faster development cycles. | Global digital forensics market projected to reach $18.2 billion by 2030 (CAGR 12.2%) [16]. |
| Cloud Data Proliferation | Tools must adapt to API-based collection, cross-jurisdictional data retrieval, and petabyte-scale analysis. | Over 60% of newly generated data will reside in the cloud by 2025 [16]. |
| AI Integration | Development requires new validation protocols for AI-generated findings to ensure legal admissibility. | AI can increase deepfake audio detection accuracy to 92% [16]. |
| Device Proliferation & Security | Tools must continuously update to handle new mobile, IoT, and vehicle systems with advanced encryption. | Tens of billions of IoT devices expected worldwide by 2025 [9]. |
Current SDLC Methodologies and Their Limitations in Forensics
Agile Methodology
Agile development, with its emphasis on iteration, customer collaboration, and responding to change, is highly effective for rapidly adapting to new forensic challenges. Its principles are showcased in the development of tools like LinkForensics, where developer-law enforcement collaboration and almost weekly feedback loops enabled the swift creation of an automated tool for identifying harmful link pathways—a process previously done manually [18]. This approach allows teams to "action [new requirements] immediately" [18], which is crucial in a field where exploit techniques change constantly.
However, the very strength of Agile—its flexibility—becomes a liability for ensuring the rigorous, repeatable validation required for courtroom evidence. An iterative cycle may prioritize a new feature without dedicating sufficient time to the extensive, documented testing needed to prove the tool's findings are forensically sound and reproducible.
Traditional SDLC and Secure-SDLC (S-SDLC)
Traditional SDLC models, and their secure counterparts like the Secure Software Development Life Cycle (S-SDLC), provide the structured rigor that Agile lacks. Methodologies such as McGraw's "Seven Touchpoints" integrate security activities—including security requirements, design, testing, and maintenance—throughout all phases of development [19]. This ensures that foundational practices like secure coding, penetration testing, and static analysis are not afterthoughts but are built into the process from the beginning [19]. This is essential for creating a "forensically ready" SDLC that produces a verifiable audit trail and ensures evidence integrity [20].
The limitation of these plan-driven models is their inherent inflexibility. They can be too slow to keep pace with the evolving threat landscape, potentially resulting in tools that are secure and reliable but obsolete by the time they are deployed.
The Systemic Gap
The core problem is a systemic one. Current development practices, whether Agile or Traditional, often lack techniques to "represent and reason about the systemic problems that are created by inadequate investment, by poor management leadership and by the breakdown in communication between development teams" [21]. The focus tends to be on technical execution rather than on a framework for ensuring that a tool progresses methodically from a research concept to a judicially robust product. This gap can lead to tools that are either rapidly delivered but not properly validated, or thoroughly validated but no longer relevant.
Technology Readiness Levels (TRL) as a Unifying Framework
The TRL framework, originally developed by NASA, provides a standardized scale to assess the maturity of a particular technology. Its integration into forensic software development can create a common language between developers, researchers, and legal professionals, objectively measuring progress toward a forensically sound product.
The framework's power lies in translating abstract goals like "courtroom readiness" into a series of concrete, evidence-based milestones. This bridges the Agile-Traditional SDLC divide by allowing for iterative development within a given TRL stage (an Agile strength), while requiring specific, rigorous deliverables to advance to the next level of maturity (a Traditional SDLC strength).
Table 2: Technology Readiness Levels (TRL) Adapted for Digital Forensics Tools
| TRL | Stage Definition | Forensic-Specific Validation Criteria | Primary SDLC Phase |
|---|---|---|---|
| 1-3: Research | Basic principles observed and formulated. Initial experimental proof-of-concept. | Concept validates a core forensic function (e.g., parsing a new file system). | Requirements & Design |
| 4-5: Development | Component and system validation in lab environment. | Tool reliably extracts/data carves from a controlled disk image. Output is consistent. | Implementation & Testing |
| 6-7: Prototyping | System prototype demonstrated in operational/realistic environment. | Tool processes evidence from a real, but non-case, device (e.g., donated phone). | Testing & Deployment |
| 8-9: Operation | System complete and qualified. Proven in operational environment. | Tool used successfully in actual investigations; results withstand peer review and legal discovery. | Deployment & Maintenance |
TRL Integration Logic
The following diagram visualizes how the TRL framework creates a bridge between Agile and Traditional SDLC methodologies, ensuring a continuous flow of validation and feedback throughout the development lifecycle.
Application Notes: TRL Integration Protocols for Forensic Tool Development
This section provides detailed, actionable protocols for integrating TRL assessment into the development of digital forensics tools.
Protocol 1: Establishing a TRL Assessment Baseline
Objective: To define the specific, measurable criteria a forensic tool must meet at each TRL stage. Methodology:
- Convene a Cross-Functional Panel: Assemble a team including digital forensics examiners, software developers, legal advisors (to address admissibility concerns), and quality assurance analysts.
- Define TRL Exit Criteria: For each TRL (1-9), the panel will document the required evidence of maturity. This moves beyond generic software metrics to forensic-specific validation.
- Example for TRL 5 (Component Validation): "The tool's data carving module must successfully recover 99.5% of specified file types (JPEG, PDF, SQLite) from a standardized NIST-based test image, producing a cryptographically hash-verifiable output log."
- Example for TRL 7 (System Demonstrated in Operational Environment): "The tool must complete a full extraction and analysis of a donated smartphone (e.g., Android 13, iOS 16) in a lab setting that mimics a real investigation, producing a report that aligns with the findings of an established commercial tool (e.g., Cellebrite, Oxygen Forensic Suite) for 95% of common artifacts."
- Documentation: All criteria must be documented in a TRL Assessment Handbook, which will serve as the objective benchmark for all maturity evaluations.
Protocol 2: TRL-Gated S-SDLC Integration
Objective: To embed TRL assessment gates into the Secure Software Development Life Cycle, ensuring security and forensic soundness are validated at each stage. Methodology:
- Map TRLs to SDLC Phases: Align TRL milestones with specific SDLC phases as shown in Table 2. For instance, completing the Design phase requires achieving at least TRL 3.
- Implement Phase-Gate Reviews: Before a project can proceed from one SDLC phase to the next, a formal review must be held. The gate review for moving from Testing to Deployment, for example, is conditional upon the tool achieving TRL 7.
- Incorporate Security Touchpoints: Integrate the security activities from models like McGraw's Seven Touchpoints [19] directly into the TRL criteria. Advancement to TRL 6, for example, requires passing a security-focused code review and static analysis.
Protocol 3: Agile-TRL Hybrid for Rapid Feature Development
Objective: To allow for Agile development of new features for a mature tool without compromising its overall validated state. Methodology:
- Feature-Specific TRL Tracking: When a new feature (e.g., support for a new messaging app) is added to a tool already at TRL 8, that feature is assigned its own, lower TRL (e.g., TRL 4).
- Sandboxed Iteration: The feature is developed and iterated upon using Agile sprints within a dedicated development branch. Its progression (TRL 4 → 5 → 6) is tracked independently.
- Promotion to Main Branch: The new feature is only merged into the main, TRL 8-certified branch of the tool once it has itself reached TRL 7, validated per the protocols in 5.1 and 5.2. This ensures the core tool's maturity is never degraded by new, unproven code.
The Scientist's Toolkit: Essential Research Reagents for Forensic Tool Validation
The following reagents and materials are critical for conducting the experiments and validation procedures required to advance a forensic tool's TRL.
Table 3: Key Research Reagents for Digital Forensics Tool Validation
| Reagent / Material | Function in Development & Validation | Example Use Case |
|---|---|---|
| NIST CFReDS Kit | Provides standardized, pre-built digital corpora for controlled testing and tool calibration. | Used in TRL 4-5 to establish baseline accuracy of file carving and parsing algorithms against a known-ground-truth dataset. |
| Donated Device Library | A collection of sanitized, real-world mobile phones, IoT devices, and hard drives from various manufacturers and OS versions. | Used in TRL 6-7 for operational testing in a realistic environment, ensuring tool compatibility with diverse hardware. |
| Forensic Software Toolsuite | Established commercial and open-source tools (e.g., Autopsy, Belkasoft X, Cellebrite) used for cross-validation. | Used as a reference standard at TRL 7 to verify that a new tool's output is forensically consistent with accepted industry tools. |
| Cryptographic Hash Generator | Software (e.g., sha256sum) to generate unique digital fingerprints for evidence files and tool outputs. |
Critical at all TRLs for proving evidence integrity and ensuring tool operations do not alter the source data. |
| Controlled Test Images | Custom disk images containing known artifacts, hidden data, and anti-forensic challenges (e.g., steganography, encrypted volumes). | Used to test and score a tool's effectiveness against specific threats and techniques during TRL 5-6 development. |
| Legal Admissibility Checklist | A document, developed in consultation with legal experts, outlining the technical requirements for courtroom evidence. | Guides development from TRL 1 to ensure the final product (TRL 9) meets the legal standards for discovery and testimony. |
The integration of the Technology Readiness Level framework into both Agile and Traditional SDLC models offers a pragmatic and systematic solution to the core challenges in modern digital forensics tool development. It provides a structured pathway to transform innovative research into legally defensible technology. By adopting TRL gating, the field can foster an environment where tools are developed with both the speed to react to new threats and the rigor to withstand judicial scrutiny. This bridges the critical gap between rapid innovation and the unwavering reliability required by the justice system, ultimately strengthening the integrity of digital evidence worldwide.
A Practical TRL Integration Framework for the Forensic SDLC
Technology Readiness Levels (TRL) are a systematic metric used to assess the maturity of a particular technology. The scale ranges from TRL 1 (basic principles observed) to TRL 9 (actual system proven in operational environment) [3] [1]. This application note details the activities, outputs, and validation criteria for TRL 1 through TRL 3 within the context of forensic science research and development. This early phase transforms a fundamental scientific observation into a validated proof-of-concept, establishing its potential for forensic application.
Integrating TRL assessment into the forensic software development lifecycle ensures that new tools meet rigorous scientific standards and practical investigative needs from the outset [14]. The objective of Phase 1 is to define precise forensic requirements and demonstrate analytical proof-of-concept, laying a foundation for future development and eventual integration into operational forensic workflows.
TRL Definitions and Phase 1 Objectives
The following table outlines the specific definitions and core focus for each TRL within Phase 1.
Table 1: Technology Readiness Levels 1-3: Definitions and Focus
| TRL | Official Definition | Phase 1 Focus in Forensic Context |
|---|---|---|
| TRL 1 | Basic principles observed and reported [1]. | Initial scientific research begins. Fundamental knowledge of a technique (e.g., a chemical reaction, a physical property, an algorithm) is documented for its potential forensic relevance. |
| TRL 2 | Technology concept and/or application formulated [1]. | Practical application of the basic principles is invented. A specific forensic use case is proposed (e.g., "This spectroscopic method could differentiate body fluid stains."). |
| TRL 3 | Analytical and experimental critical function and/or characteristic proof-of-concept [1]. | Active R&D is initiated. Analytical and laboratory studies validate the core concept. A proof-of-concept model confirms the technology's viability for the proposed forensic application. |
Defining Forensic Requirements: The Strategic Framework
The transition from TRL 1 to TRL 3 must be guided by a clear strategic framework aligned with the documented needs of the forensic community. The National Institute of Justice (NIJ) Forensic Science Strategic Research Plan, 2022-2026 provides critical guidance for defining these requirements [22].
Applied Research and Development Objectives
Forensic technology concepts should aim to fulfill one or more of the following applied research objectives [22]:
- Tools that increase sensitivity and specificity of forensic analysis.
- Methods to maximize the information gained from limited or degraded evidence.
- Nondestructive or minimally destructive methods that preserve evidence for further testing.
- Machine learning methods for the classification of forensic evidence.
- Rapid and reliable field-deployable technologies for use at crime scenes.
- Automated tools to support examiners' conclusions and reduce subjective bias.
Foundational Research Objectives
Concurrently, foundational research must assess the fundamental validity of the proposed method [22]:
- Understanding the fundamental scientific basis of the new forensic method.
- Quantifying measurement uncertainty associated with the analytical technique.
- Establishing the limitations of the evidence analyzed by the method, including its stability, persistence, and transfer properties.
Experimental Protocols for Analytical Proof-of-Concept
The following protocols provide a framework for achieving experimental proof-of-concept (TRL 3) in key areas of forensic science.
Protocol: Proof-of-Concept for Body Fluid Identification Using Novel Spectroscopy
This protocol outlines the steps to validate a novel spectroscopic method for differentiating body fluids, a common trace evidence type [23].
1. Objective: To demonstrate that a novel analytical technique (e.g., FTIR Spectroscopy) can reliably distinguish between dried stains of blood, semen, and saliva on a representative substrate (e.g., cotton cloth).
2. Materials and Reagents:
- Reference Materials: Purified samples of blood, semen, and saliva from approved ethical sources.
- Substrates: 5 cm x 5 cm squares of white 100% cotton cloth.
- Analytical Instrument: Fourier-Transform Infrared (FTIR) Spectrometer.
- Software: Multivariate statistical analysis software (e.g., PCA, PLS-DA).
3. Experimental Procedure:
- Sample Preparation (Day 1):
- Spot 10 µL of each reference body fluid onto separate, labeled cloth substrates (n=5 per fluid).
- Allow all spots to air-dry completely at room temperature for 24 hours.
- Data Acquisition (Day 2):
- Using the FTIR spectrometer, collect absorption spectra from each dried stain.
- Instrument Settings: Resolution: 4 cm⁻¹, Number of Scans: 64, Spectral Range: 4000 - 600 cm⁻¹.
- Ensure background scans are collected immediately before each sample set.
- Data Analysis (Day 3):
- Pre-process all spectra (e.g., baseline correction, vector normalization).
- Input processed spectral data into the multivariate software.
- Perform Principal Component Analysis (PCA) to visualize natural clustering of the three body fluid types.
- Develop a Partial Least Squares-Discriminant Analysis (PLS-DA) model and use cross-validation to calculate classification accuracy.
4. Success Criteria for TRL 3: The PLS-DA model must achieve a cross-validated classification accuracy of ≥95% in differentiating the three body fluids, demonstrating a robust proof-of-concept.
Protocol: Proof-of-Concept for Drug Analysis Using Chromatography
This protocol establishes a method for developing an initial proof-of-concept for separating and identifying compounds in a complex mixture, such as illicit drugs [24].
1. Objective: To develop a Gas Chromatography-Mass Spectrometry (GC-MS) method that separates and provides a preliminary identification of three common compounds in a simulated seized drug sample.
2. Materials and Reagents:
- Analytical Standards: Certified reference materials of caffeine, procaine, and heroin.
- Simulated Sample: A mixture of the three standards in methanol at approximately 100 µg/mL each.
- Solvents: HPLC-grade methanol and dichloromethane.
- Analytical Instrument: Gas Chromatograph coupled to a Mass Spectrometer (GC-MS).
3. Experimental Procedure:
- Method Development:
- Inject individual standards to determine their retention times and characteristic mass spectra.
- Optimize GC temperature ramp to achieve baseline separation of all three compounds.
- Sample Analysis:
- Inject 1 µL of the simulated sample mixture using the optimized method.
- GC Conditions: Inlet Temp: 250°C, Split Ratio: 10:1, Oven Program: 50°C (hold 1 min) to 300°C at 15°C/min.
- MS Conditions: Ion Source Temp: 230°C, Transfer Line: 280°C, Scan Range: 40-550 m/z.
- Data Interpretation:
- Analyze the total ion chromatogram (TIC) to confirm separation of three distinct peaks.
- For each peak, compare the generated mass spectrum to a reference spectral library (e.g., NIST) for identification. A match factor >80% is considered a preliminary identification.
4. Success Criteria for TRL 3: The method must successfully separate the three components in the mixture with a resolution (Rs) >1.5 between all peaks, and library search must yield a preliminary identification for each.
Workflow Visualization and Data Analysis
The logical progression from basic principle to validated proof-of-concept follows a defined pathway. The diagram below illustrates this workflow and the critical decision gates.
Quantitative Data Analysis and Success Metrics
At the culmination of TRL 3, experimental data must be evaluated against pre-defined quantitative metrics. The following table summarizes example success criteria for different types of forensic proof-of-concept studies.
Table 2: Example Success Criteria for TRL 3 in Forensic Proof-of-Concept Studies
| Analytical Technique | Proof-of-Concept Goal | Key Performance Metrics | TRL 3 Success Threshold |
|---|---|---|---|
| Multivariate Spectroscopy [23] | Differentiate biological stains | Classification Accuracy | ≥ 95% |
| Chromatography (GC-MS) [24] | Separate drug混合物 | Chromatographic Resolution (Rs) | > 1.5 between all critical pairs |
| Mass Spectrometry [24] | Identify explosive residue | Library Match Factor / Signal-to-Noise | > 80% / > 10:1 |
| Capillary Electrophoresis [24] | Detect trace DNA | Limit of Detection (LOD) | < 50 pg DNA |
The Scientist's Toolkit: Essential Research Reagents and Materials
The following table details key reagents, materials, and instruments essential for conducting proof-of-concept experiments in forensic analytical chemistry.
Table 3: Key Research Reagent Solutions and Materials for Forensic Proof-of-Concept Studies
| Item | Function / Application | Example in Protocol |
|---|---|---|
| Certified Reference Materials | Provides a ground-truth standard for method validation and calibration. | Purified drug standards (e.g., heroin, caffeine) for GC-MS identification [24]. |
| Body Fluid Standards (Ethically Sourced) | Used to develop and validate methods for body fluid identification. | Purified blood, semen, and saliva for spectroscopic differentiation [23]. |
| Fourier-Transform Infrared (FTIR) Spectrometer | Identifies organic functional groups and compounds by measuring infrared absorption. | Generating molecular "fingerprints" to classify unknown body fluids [23] [24]. |
| Gas Chromatograph-Mass Spectrometer (GC-MS) | Separates volatile mixtures (GC) and provides definitive identification of components (MS). | Separating and identifying compounds in a complex seized drug sample [24]. |
| Capillary Electrophoresis (CE) System | Separates ionic molecules like DNA fragments based on size and charge. | Creating a DNA profile from trace biological evidence [24]. |
| Multivariate Statistical Software | Analyzes complex, multi-dimensional data to find patterns and build classification models. | Performing PCA and PLS-DA on spectral data to differentiate body fluids [23]. |
Integrating Technology Readiness Level (TRL) assessment into the forensic software development lifecycle provides a structured framework for de-risking technology development and objectively evaluating maturity. Phase 2 (TRL 4-6) encompasses validation in laboratory and relevant environments, representing a critical transition from basic component testing to integrated prototype demonstration. This phase ensures that forensic software components and systems function reliably under controlled and realistic conditions before deployment in operational settings [25].
The rigorous application of standardized testing protocols during this phase is paramount for building confidence in the software's capabilities. For digital forensic tools, this directly correlates with the admissibility and defensibility of digital evidence in legal proceedings [25] [26]. This document outlines detailed application notes and experimental protocols for conducting component and prototype validation using forensic datasets, providing a roadmap for researchers and developers in the field.
Core Principles and Quantitative Metrics for Validation
Validation at TRL 4-6 is guided by core principles that ensure the process is systematic, thorough, and legally defensible. These principles include a methodological approach, reproducibility, validation against real-world scenarios, and thorough documentation [25]. Quantitative metrics are essential for objectively measuring a tool's performance against these principles and established benchmarks.
Table 1: Key Quantitative Validation Metrics for Forensic Software at TRL 4-6
| Metric Category | Specific Metric | TRL 4 (Lab) Target | TRL 5-6 (Relevant Environment) Target | Measurement Method |
|---|---|---|---|---|
| Data Integrity | Hash Verification Success Rate | 100% | 100% | SHA-1, MD5 hashing of source vs. image [27] |
| Processing Accuracy | File Carving Accuracy | >95% | >98% | Comparison against known file set [28] |
| Data Parsing Fidelity | >90% | >95% | Comparison of parsed data to raw database bytes [26] | |
| Performance | Data Processing Throughput (GB/hour) | Baseline | ≥20% improvement over baseline | Timed processing of standardized dataset [25] |
| Reliability | Test Result Reproducibility | 100% | 100% | Repeated tests in same environment (ISO 5725) [25] |
| Functional Coverage | Percentage of NIST CFTT Tests Passed | Baseline for tool category | >90% of relevant tests | Execution of CFTT test procedures [25] [29] |
The National Institute of Standards and Technology's Computer Forensics Tool Testing (CFTT) program provides a critical foundation for this testing, developing general tool specifications, test procedures, and test criteria [25] [29]. The principle of reproducibility, as defined by ISO 5725, requires that tests yield consistent and reproducible results, meaning the same findings are achieved whether the tool is used in the same lab or a different one [25].
Experimental Protocols
Protocol 1: Component-Level Validation of a Data Parsing Algorithm (TRL 4)
1. Objective: To validate the accuracy and reliability of a software component (e.g., a SQLite database parser) in an isolated laboratory environment.
2. Materials and Reagents:
- Test System: A dedicated, forensically sterile workstation with a configured write-blocker.
- Forensic Software Prototype: The version of the software containing the parser component to be tested.
- Reference Tool: An established, validated forensic tool (e.g., FTK, Autopsy) for result comparison [27] [28].
- CFReDS Dataset: A Computer Forensic Reference Data Set (CFReDS) from NIST, containing a known set of data artifacts with verified content [29].
- Custom Dataset: A laboratory-created dataset with a precisely known structure and content, including intentionally corrupted records to test error handling.
3. Methodology: 1. Preparation: Place the CFReDS and custom datasets on a test storage device. Create a forensic image of this device using a validated hardware imager, and verify the image integrity using a cryptographic hash (e.g., SHA-1) [27]. 2. Execution: * Process the forensic image through the prototype software's parser component. * Execute the same parsing operation using the reference tool. * For both runs, record all extracted database records, including deleted entries where applicable. 3. Data Analysis: * Compare the output of the prototype parser against the known ground truth of the datasets. * Quantify the number of correctly parsed records, missed records (false negatives), and incorrectly interpreted records (false positives). * Cross-validate the prototype's output against the output from the reference tool, noting any discrepancies. * Document the component's behavior when encountering corrupted or unexpected data structures.
4. Acceptance Criteria: The parser component must correctly extract no less than 95% of known records from the CFReDS dataset and demonstrate robust error handling without catastrophic failure. Results must be 100% reproducible upon repeated testing [25].
Protocol 2: Integrated Prototype Demonstration with Synthetic Forensic Datasets (TRL 5)
1. Objective: To demonstrate the performance of an integrated software prototype in a relevant environment using a synthetic, scenario-based forensic dataset that includes coherent background activity.
2. Materials and Reagents:
- Relevant Environment: A virtualized machine or dedicated test computer that simulates a typical user's device.
- Integrated Software Prototype: The complete forensic software application with all key components integrated.
- Synthetic Disk Image: A dataset generated using a framework like Re-imagen, which leverages Large Language Models (LLMs) to create realistic device usage scenarios, including "wear-and-tear" artifacts and background user activity [30].
- Analysis Plan: A predefined plan outlining the investigative scenario (e.g., "identify evidence of data exfiltration") and specific artifacts to target.
3. Methodology: 1. Scenario Setup: Utilize the Re-imagen framework to generate a synthetic disk image. The scenario should involve a specific evidential action (e.g., copying a confidential file to a USB) amidst normal, LLM-generated user persona activities (e.g., web browsing, email, document editing) [30]. 2. Blinded Analysis: Provide the integrated software prototype and the synthetic disk image to an analyst without disclosing the ground truth of the scenario. 3. Processing and Examination: The analyst uses the prototype to conduct a full investigation, including evidence acquisition, data carving, keyword searching, and timeline generation [28]. 4. Reporting: The analyst produces a report detailing the findings, including the evidence of the key evidential action and a reconstruction of user activity.
5. Validation: Compare the prototype-generated report against the known ground truth of the synthetic scenario. Evaluate not only the success in finding the key evidence but also the accuracy and coherence of the background activity reconstruction.
6. Acceptance Criteria: The prototype must correctly identify the key evidential actions and provide a timeline of activity that is consistent with the known scenario. The software should effectively distinguish between significant evidence and incidental background noise.
Protocol 3: Performance Benchmarking and Robustness Testing (TRL 6)
1. Objective: To benchmark the performance and robustness of the prototype against large-scale, multi-source datasets and to test its resilience against non-standard inputs.
2. Materials and Reagents:
- High-Performance Computing Node: A system with significant processing power and memory.
- Benchmarking Prototype: The software prototype configured for performance logging.
- NSRL Subset: A substantial subset of the National Software Reference Library (NSRL) Reference Data Set (RDS) to test file filtering capabilities [29].
- Multi-source Evidence Dataset: A large corpus comprising data from multiple device types (e.g., hard drives, smartphone images, cloud data exports).
3. Methodology: 1. Throughput Test: Process the multi-source evidence dataset with the prototype and record the time to complete key stages (e.g., ingestion, indexing, analysis). Compare against baseline performance metrics. 2. Scalability Test: Measure system resource utilization (CPU, RAM, storage I/O) while processing datasets of increasing size. 3. Robustness Test: Introduce datasets with known anomalies, such as non-standard file system features, intentionally corrupted partitions, or files with manipulated extensions. Document the prototype's ability to handle these gracefully. 4. Hash Filtering Efficiency Test: Process a disk image containing a known mixture of known-good (e.g., OS files from NSRL) and unknown files. Verify the prototype's accuracy in filtering and categorizing files.
4. Acceptance Criteria: The prototype must process data at a throughput meeting or exceeding project requirements, scale efficiently with dataset size, and maintain stability when encountering anomalous data. Hash filtering must achieve a false-positive rate of less than 0.1%.
Workflow Visualization
The Scientist's Toolkit: Research Reagent Solutions
The following table details essential materials and digital "reagents" required for the rigorous validation of forensic software at TRL 4-6.
Table 2: Key Research Reagents for Forensic Software Validation
| Reagent / Material | Function in Validation | Example Sources / Instances |
|---|---|---|
| CFReDS (Computer Forensic Reference Data Sets) | Provides simulated digital evidence with known content for testing tool accuracy and verifying findings [29]. | NIST |
| NSRL (National Software Reference Library) | Reference Data Set (RDS) of file profiles used to filter known files, testing the software's ability to identify unknown or relevant data [29]. | NIST |
| Synthetic Dataset Generation Frameworks | Creates realistic, scalable, and privacy-compliant datasets with coherent background activity for testing in relevant environments [30]. | Re-imagen |
| Validated Reference Tools | Provides a benchmark for comparing the output and performance of the prototype under test, ensuring parity with established methods [25] [27]. | Forensic Toolkit (FTK), EnCase, Autopsy |
| Forensic Hardware Interfaces | Ensures the integrity of original evidence during the testing process by preventing write operations to source media [27]. | Hardware write-blockers |
| Hash Algorithm Suites | Fundamental for verifying the integrity of evidence and forensic images throughout all testing phases [27]. | SHA-1, SHA-256, MD5 |
Technology Readiness Levels (TRLs) provide a systematic metric for assessing the maturity of a particular technology. The scale ranges from 1 (basic principles observed) to 9 (actual system proven in operational environment) [3]. This application note details the critical final phases of forensic software maturation—TRLs 7 through 9—where technologies transition from advanced prototypes to fully operational systems qualified for live investigations.
In digital forensics, this progression ensures that tools not only function technically but also meet the rigorous demands of evidentiary standards, chain-of-custody requirements, and operational workflows. The transition from TRL 6 to TRL 7 is often considered a critical chasm, marking the point where a product begins to be used in real conditions by users with higher expectations and lower tolerance for imperfections [31]. Successfully navigating this "valley of death"—where neither academia nor the private sector typically prioritizes investment—requires coordinated collaboration between developers, forensic examiners, and legal experts [32].
TRL Definitions and Progression Criteria
Detailed TRL Definitions for Forensic Software
TRL 7: System Prototype Demonstration in Operational Environment A TRL 7 technology has a working model or prototype demonstrated in an actual operational environment [3]. For forensic software, this represents a major step increase in maturity where a prototype system is verified in a real investigative context, though potentially with limited scope. The software must handle genuine evidence sources and produce forensically sound results under realistic conditions.
TRL 8: System Complete and Qualified At TRL 8, the technology has been tested and "flight qualified" and is ready for implementation into an already existing technology or technology system [3]. In forensic terms, this means the software has completed all validation testing, is fully documented, and is qualified for use in investigations that may produce evidence for legal proceedings.
TRL 9: Actual System Proven in Operational Environment TRL 9 represents the highest maturity level, where the actual system has been "flight proven" during a successful mission [3]. For forensic tools, this means successful deployment in multiple real investigations, potentially across different organizations, with demonstrated reliability and effectiveness in producing admissible digital evidence.
Quantitative Progression Metrics
Table 1: Key Progression Criteria for TRLs 7-9 in Digital Forensics
| TRL | Validation Environment | Minimum Case Threshold | Evidence Integrity Requirements | Performance Benchmarks |
|---|---|---|---|---|
| TRL 7 | Live investigative environment with supervised use | 3-5 controlled investigations | Write-blocking functionality verified; hash validation implemented | Processing speed ≥80% of production tools; false positive rate <15% |
| TRL 8 | Multiple operational environments across different organizations | 10+ diverse case types | Chain-of-custody logging automated; compliance with ISO 27043 standards | Processing speed ≥95% of industry standards; false positive rate <5% |
| TRL 9 | Full deployment across intended user base | 25+ successful investigations with evidence presented in legal proceedings | Zero unrecoverable errors in evidence processing; full audit trail compliance | 99.9% reliability in processing supported evidence types; user efficiency improved by ≥20% |
Experimental Protocols for TRL Validation
Protocol for TRL 7 Operational Demonstration
Objective: Validate that the forensic software prototype functions effectively in a live investigative environment under supervised conditions.
Materials and Setup:
- Forensic workstation meeting minimum system requirements
- Write-blocking hardware for evidence acquisition
- Test evidence samples representing common case types (disk images, mobile device backups, memory dumps)
- Comparison tools (commercial forensic suites for result validation)
Methodology:
- Environment Configuration: Install the prototype software on designated forensic workstations following standard operating procedures for tool validation.
- Evidence Processing: Process at least three different evidence types through the complete forensic workflow—from acquisition to analysis and reporting.
- Result Validation: Compare findings with those obtained from established tools (e.g., EnCase, Autopsy, X-Ways Forensics) [33].
- Performance Metrics Collection: Document processing times, resource utilization, and accuracy metrics.
- User Feedback Integration: Forensic examiners complete standardized assessment forms covering usability, reliability, and output quality.
Success Criteria:
- Software processes evidence without altering original data
- Key functionalities perform as specified in design requirements
- No critical errors that halt investigation processes
- Results are forensically sound and reproducible
Protocol for TRL 8 System Qualification
Objective: Qualify the complete forensic system for use in investigations that may yield evidence for legal proceedings.
Materials and Setup:
- Multiple forensic workstations across different organizational units
- Diverse evidence types including challenging scenarios (encrypted volumes, anti-forensic techniques)
- Documentation for legal compliance (validation protocols, error logging procedures)
Methodology:
- Multi-Site Deployment: Install the qualified software version across at least two independent forensic laboratories.
- Blinded Testing: Examiners process cases without developer support, using only official documentation.
- Stress Testing: Process large-scale evidence sets (>1TB) and complex scenarios (APTs, anti-forensic techniques) [34].
- Legal Compliance Review: Verify that output meets standards for evidence presentation, including comprehensive audit trails and chain-of-custody documentation.
- Interoperability Testing: Validate integration with existing forensic ecosystems (centralized repositories, evidence management systems).
Success Criteria:
- Consistent performance across different environments and operators
- Comprehensive documentation supporting legal admissibility
- Effective handling of edge cases and challenging evidence
- Successful integration with existing laboratory workflows
Protocol for TRL 9 Operational Provenance
Objective: Demonstrate that the system has been proven through successful mission operations across multiple investigations.
Materials and Setup:
- Production environments across multiple user organizations
- Real casework spanning the tool's intended application scope
- Long-term monitoring and feedback mechanisms
Methodology:
- Extended Deployment: Monitor tool performance across at least 25 investigations in real operational settings.
- Effectiveness Metrics: Track investigation outcomes, evidence quality, and time-to-resolution compared to previous methods.
- User Proficiency Assessment: Evaluate learning curves and proficiency levels across different examiner skill sets.
- Maintenance and Support Evaluation: Document system reliability, update effectiveness, and support response efficiency.
- Legal Precedent Establishment: Track successful evidence admission in legal proceedings and challenges overcome.
Success Criteria:
- Statistical significance in improved investigative outcomes
- Positive user feedback across diverse organizational contexts
- Successful defense of methodology and results in legal challenges
- Demonstrated cost-effectiveness and return on investment
Visualization of TRL Progression Workflow
The Forensic Scientist's Toolkit: Essential Research Reagents
Table 2: Key Digital Forensic Tools and Components for TRL Validation
| Tool/Category | Function in TRL Validation | Example Implementations |
|---|---|---|
| Forensic Platforms | Core analysis environment for evidence processing | Autopsy [33], EnCase [33], X-Ways Forensics [33] |
| Imaging & Extraction Tools | Evidence acquisition and data recovery validation | FTK Imager [33], Bulk Extractor [33], Cellebrite [33] |
| Memory Forensics Tools | Volatile memory analysis capability testing | MAGNET RAM Capture [33] |
| Specialized Analyzers | Validation of specific forensic capabilities | Belkasoft X (cloud/mobile) [33], ExifTool (metadata) [33] |
| Network Monitoring Tools | Network forensic capability validation | Nagios [33] |
| Integrated Environments | Complete forensic workflow validation | CAINE [33], Digital Forensics Framework [33] |
| Validation Systems | Tool output verification and reliability testing | Hash validation utilities, standardized test images |
| Evidence Management Systems | Chain-of-custody and evidence integrity validation | Centralized repository systems with audit logging |
Implementation Framework and Best Practices
Documentation Requirements for Qualification
Achieving TRL 8 requires comprehensive documentation that supports both technical operation and legal admissibility. This includes:
- Validation Protocols: Detailed test procedures demonstrating tool reliability under various conditions
- Error Analysis: Comprehensive documentation of known limitations, edge cases, and potential failure modes
- Standard Operating Procedures: Step-by-step guides for evidence processing, results interpretation, and tool maintenance
- Legal Compliance Documentation: Evidence supporting compliance with relevant standards such as ISO 27043 for forensic investigations [35]
Integration with Quality Management Systems
For sustainable operational deployment (TRL 9), forensic tools must integrate with laboratory quality management systems:
- Change Control Procedures: Documented processes for software updates and version management
- Training Programs: Certification paths for examiners, with proficiency testing requirements
- Performance Monitoring: Continuous monitoring of tool effectiveness, error rates, and reliability metrics
- Incident Response: Protocols for addressing tool failures, evidence processing errors, or legal challenges
The framework presented enables forensic software developers and laboratory managers to systematically advance tools from advanced prototypes to fully qualified systems capable of supporting legal proceedings. By adhering to these structured protocols and validation criteria, organizations can bridge the "valley of death" between research and operational deployment, ultimately enhancing the reliability and effectiveness of digital forensic investigations.
This application note provides a detailed framework for integrating DevSecOps practices into technology maturation using the Technology Readiness Level (TRL) scale. Designed for forensic software development lifecycle research, it outlines specific security and compliance protocols for each TRL stage, supported by experimental methodologies, visualization workflows, and a comprehensive toolkit for implementation. This structured approach ensures that security is embedded throughout the research and development process, creating a seamless pathway from basic research to forensically sound, operational technology.
The Technology Readiness Level (TRL) scale is a systematic metric that supports assessments of the maturity of a particular technology during its acquisition phase. It uses a scale from 1 to 9, with TRL 1 being the lowest (basic principles observed) and TRL 9 being the highest (actual system proven in operational environment) [1] [3]. Originally developed by NASA in the 1970s, this framework enables consistent and uniform discussions of technical maturity across different types of technology and has since been adopted by the U.S. Department of Defense, the European Space Agency, and the European Commission [1].
DevSecOps represents an evolution in software development that integrates security practices into every stage of the software development lifecycle (SDLC). It stands for Development, Security, and Operations, emphasizing "shifting security left" by building security practices into the development process rather than treating it as an afterthought [36] [37]. This approach fosters a culture of shared responsibility, automation, continuous monitoring, and collaboration among development, security, and operations teams to identify and fix vulnerabilities faster and more cost-effectively [36].
The integration of TRL assessment with DevSecOps practices creates a powerful framework for forensic software development, where evidence integrity, chain of custody, and regulatory compliance are paramount. This synergy ensures that as a technology advances through maturity levels, security and compliance are not retrospectively applied but are inherent properties of the technology itself.
TRL to DevSecOps Practice Mapping
Table 1: Mapping of DevSecOps Security and Compliance Activities to Technology Readiness Levels
| TRL | NASA Maturity Definition [1] [3] | DevSecOps Security Activities | Compliance & Forensic Checks |
|---|---|---|---|
| TRL 1 | Basic principles observed and reported | Threat modeling fundamentals; Initial security requirements brainstorming | Research ethics compliance; Data privacy principle identification |
| TRL 2 | Technology concept and/or application formulated | Security architecture review; Conceptual attack surface analysis | Regulatory landscape mapping (e.g., GDPR, HIPAA for forensic data) |
| TRL 3 | Analytical and experimental critical function proof-of-concept | Secure coding standards adoption; SAST tool introduction; Proof-of-concept security testing | Development of preliminary chain of custody documentation protocols |
| TRL 4 | Component validation in laboratory environment | Component security testing; Dependency scanning (SCA); Secure API testing | Lab environment security accreditation; Audit trail implementation |
| TRL 5 | Component validation in relevant environment | DAST testing; Environment hardening; Infrastructure as Code (IaC) scanning | Validation environment compliance certification; Evidence handling procedure validation |
| TRL 6 | System demonstration in relevant environment | Integrated security testing; Penetration testing; Container security scanning | Forensic soundness validation; Regulatory gap assessment (e.g., FedRAMP, SOC2) |
| TRL 7 | System prototype demonstration in operational environment | Runtime security monitoring (CADR); Incident response testing; Security automation | Operational compliance monitoring; Chain of custody integrity verification |
| TRL 8 | Actual system completed and qualified | Continuous security monitoring; Automated compliance scanning; Advanced threat detection | Full regulatory compliance audit; Admissibility standards validation |
| TRL 9 | Actual system proven through successful operations | Production security optimization; Threat intelligence integration; Security feedback loop | Continuous compliance reporting; Courtroom admissibility evidence collection |
Experimental Protocols for Integrated TRL-DevSecOps Implementation
Protocol 1: Early-Stage Security Integration (TRL 2-4)
Objective: To embed security and compliance considerations during the formative stages of forensic technology development.
Materials: Threat modeling templates, architectural diagramming tools, SAST tools (e.g., Snyk [38]), policy-as-code frameworks.
Methodology:
- Security Requirements Formulation (TRL 2)
- Conduct threat modeling workshops with cross-functional team including developers, security specialists, and forensic experts
- Document potential abuse cases specific to forensic evidence handling
- Define security requirements traceable to potential threats
- Create preliminary data integrity and chain of custody requirements
Proof-of-Concept Security Testing (TRL 3)
- Implement static application security testing (SAST) tools in developer environments
- Establish secure coding standards focusing on evidence integrity protection
- Conduct manual security review of critical proof-of-concept components
- Introduce automated security checks in initial build pipelines
Component Security Validation (TRL 4)
- Perform software composition analysis (SCA) to identify vulnerable dependencies
- Conduct focused penetration testing on individual components
- Validate secure isolation between components handling sensitive forensic data
- Implement automated security testing in laboratory environment builds
Success Metrics: Security requirements coverage (>90%), reduction in critical vulnerabilities introduced at early stages (>50%), evidence integrity protection mechanisms implemented.
Protocol 2: Mid-Stage Integration and Compliance (TRL 5-7)
Objective: To validate security controls and compliance requirements in increasingly realistic environments.
Materials: DAST tools (e.g., OWASP ZAP), container security tools (e.g., Aqua Security [38]), infrastructure as code scanning tools (e.g., Checkov [38]), compliance automation frameworks.
Methodology:
- Environment-Specific Security Testing (TRL 5)
- Perform dynamic application security testing (DAST) against integrated components
- Implement infrastructure as code security scanning using Checkov
- Validate security controls in simulated forensic investigation scenarios
- Test evidence preservation under system stress conditions
Integrated System Security (TRL 6)
- Conduct end-to-end penetration testing of the complete system
- Perform red team exercises simulating attacks on forensic integrity
- Validate security automation in continuous integration pipelines
- Test backup and recovery procedures for forensic data
Operational Environment Security (TRL 7)
- Implement Cloud Application Detection and Response (CADR) tools [36]
- Conduct incident response drills in operational environment
- Validate runtime security controls under realistic load
- Test security monitoring and alerting for forensic operations
Success Metrics: Mean time to detect (MTTD) security incidents (<1 hour), compliance requirement coverage (>95%), evidence integrity maintenance under attack (100%).
Protocol 3: Operational Readiness and Continuous Compliance (TRL 8-9)
Objective: To ensure sustained security and compliance during operational deployment of forensic technologies.
Materials: Continuous monitoring tools (e.g., Datadog [39]), secrets management tools (e.g., HashiCorp Vault [38]), identity and access management solutions (e.g., StrongDM [38]), compliance reporting automation.
Methodology:
- Production Security Hardening (TRL 8)
- Implement Zero Trust access controls using StrongDM for forensic systems
- Establish secrets management for all authentication credentials
- Deploy continuous vulnerability management with runtime context prioritization
- Automate compliance evidence collection for standards relevant to forensic work
Operational Proven Security (TRL 9)
- Establish security feedback loops from production incidents
- Implement threat intelligence integration for forensic-specific threats
- Conduct regular security posture assessments with remediation tracking
- Maintain continuous compliance monitoring with automated reporting
Forensic Soundness Validation
- Continuously validate chain of custody integrity mechanisms
- Monitor for evidence tampering attempts or anomalies
- Maintain comprehensive audit trails for all forensic operations
- Regular admissibility readiness assessments
Success Metrics: Mean time to remediate (MTTR) critical vulnerabilities (<7 days), compliance standard adherence (100%), successful forensic evidence admission in legal proceedings.
Integrated TRL-DevSecOps Workflow Visualization
TRL and DevSecOps Integration Workflow: This diagram illustrates the synergistic relationship between Technology Readiness Levels (yellow-to-red progression) and DevSecOps practices (blue phases). Security activities (white boxes) are mapped to specific TRLs using dotted red lines, demonstrating how security is embedded throughout the maturation process rather than applied as a final step.
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential DevSecOps Tools and Technologies for Forensic Software Development
| Tool Category | Example Solutions | Primary Function in Forensic Development | TRL Applicability |
|---|---|---|---|
| Static Application Security Testing (SAST) | Snyk [38], Datadog Code Security [39] | Analyzes source code for vulnerabilities before execution, ensuring evidence handling code integrity | TRL 3-9 |
| Software Composition Analysis (SCA) | Snyk [38], OSV.dev [39] | Identifies vulnerabilities in open-source dependencies, critical for maintaining chain of custody | TRL 4-9 |
| Dynamic Application Security Testing (DAST) | OWASP ZAP [40], Aqua Security [38] | Tests running applications for vulnerabilities, validates forensic API security | TRL 5-9 |
| Infrastructure as Code Security | Checkov [38], Datadog Cloud Security [39] | Scans IaC templates for misconfigurations, ensures secure forensic environment deployment | TRL 5-9 |
| Container Security | Aqua Security [38], Datadog Workload Protection [39] | Secures containerized forensic applications, provides runtime protection | TRL 6-9 |
| Secrets Management | HashiCorp Vault [38] | Manages credentials and sensitive information, protects forensic system authentication | TRL 7-9 |
| Access Control | StrongDM [38] | Implements Zero Trust and least privilege access for forensic systems | TRL 7-9 |
| Continuous Monitoring | Datadog Cloud SIEM [39], CADR tools [36] | Provides runtime security monitoring, detects threats to forensic integrity | TRL 8-9 |
The integration of Technology Readiness Levels with DevSecOps practices creates a robust framework for developing forensically sound software technologies. By embedding security and compliance checks at every maturity level, researchers and developers can ensure that technologies not only advance in functionality but also mature in their security posture and regulatory compliance.
This approach is particularly critical in forensic software development, where evidence integrity and legal admissibility are paramount. The protocols and methodologies outlined in this application note provide a concrete pathway for implementing this integrated approach, with specific activities and tools mapped to each technology maturation stage.
Future research directions include developing TRL-specific security metrics for forensic technologies, automating compliance evidence collection across the TRL spectrum, and creating specialized DevSecOps tools for domain-specific forensic applications. As cyber threats continue to evolve, this integrated approach will become increasingly essential for developing trustworthy digital forensic technologies.
Integrating Technology Readiness Level (TRL) assessment into the forensic software development lifecycle provides a structured framework for evaluating tool maturity, robustness, and evidentiary reliability. This systematic approach enables researchers and developers to quantitatively measure progression from basic research (TRL 1-3) to prototype validation (TRL 4-6) and operational deployment (TRL 7-9). The rigorous evaluation protocols outlined in this document establish performance benchmarks for digital forensics tools, creating a standardized methodology for assessing capabilities across diverse investigative scenarios. By applying these experimental frameworks, development teams can identify capability gaps, verify functional requirements, and validate forensic soundness throughout the development pipeline, ultimately accelerating the transition of research innovations into court-admissible solutions.
Tool Comparative Analysis: Open-Source and Commercial Platforms
Table 1: Digital Forensics Tool Capability Matrix for TRL Assessment
| Tool Name | Primary Function | Supported Platforms | Key Strengths | TRL Range | Ideal Assessment Context |
|---|---|---|---|---|---|
| Autopsy [33] [41] [42] | Disk/File System Analysis | Windows, Linux, macOS | Open-source, modular architecture, timeline analysis, file recovery [33] [42] | 4-7 | Basic forensic workflow validation, educational research |
| Volatility [42] [43] [44] | Memory Forensics | Cross-platform (Python) | RAM analysis, malware detection, open-source with plugin ecosystem [42] [44] | 6-8 | Incident response protocol testing, runtime artifact analysis |
| Cellebrite UFED [41] [42] [43] | Mobile Device Forensics | iOS, Android, Windows Mobile | Physical extraction, encrypted app decoding, cloud data acquisition [41] | 8-9 | Validation against closed-system mobile platforms |
| Magnet AXIOM [33] [41] [42] | Cross-Device Analysis | Computers, mobiles, cloud | Unified workflow, AI categorization, cloud integration [33] [41] | 7-9 | Integrated digital evidence processing validation |
| EnCase Forensic [33] [41] [43] | Enterprise Computer Forensics | Windows, macOS, Linux | Deep filesystem analysis, court-admissible reporting [33] [41] | 8-9 | Evidence processing workflow benchmarking |
| FTK [41] [42] | Large-Scale Data Analysis | Windows, macOS, Linux | High-speed processing, facial recognition, robust indexing [41] [42] | 7-9 | Big data forensic processing capability testing |
| The Sleuth Kit [33] [42] | Disk Image Analysis | Windows, Linux, macOS | Command-line tools, filesystem support, data carving [33] [42] | 5-7 | Core forensic algorithm development |
| Wireshark [41] [43] [44] | Network Protocol Analysis | Cross-platform | Deep packet inspection, live capture, extensive protocol support [41] [44] | 8-9 | Network forensic and incident response testing |
Experimental Protocols for Tool Assessment
Protocol 1: Evidence Acquisition and Integrity Verification
Objective: To validate the ability of a forensic tool to create a forensically sound bit-for-bit copy of a source storage device while preserving evidence integrity and generating verifiable audit trails.
Materials:
- Test machine with write-blocker hardware
- Source storage device (HDD/SSD, 50-100GB recommended)
- Forensic acquisition tool (e.g., FTK Imager, dd)
- Target storage media for image files
- Hash verification utility (e.g., HashMyFiles [44])
Methodology:
- Pre-Acquisition Baseline: Generate MD5 and SHA-256 hash values for the source device prior to acquisition using a trusted hash utility.
- Forensic Imaging: Connect the source device to the test machine via a write-blocker. Using the tool under test, create a forensic image (raw/dd format) of the entire source device.
- Integrity Verification: Upon completion, generate MD5 and SHA-256 hash values for the resulting image file. Compare these values against the pre-acquisition baseline.
- Performance Metrics: Record acquisition time, compression ratio (if applicable), and any errors encountered during the process.
- Documentation: The tool should automatically generate an audit log containing acquisition parameters, hash values, and technician details.
TRL Assessment Criteria:
- TRL 4-5: Successful creation of a forensically sound image in a laboratory environment.
- TRL 6-7: Reliable imaging of multiple storage technologies (HDD, SSD, NVMe) with verified integrity.
- TRL 8-9: Court-validated acquisition process with robust audit trails in operational environments.
Protocol 2: Deleted File Recovery and File Carving
Objective: To evaluate the tool's capability to recover deleted files and reconstruct files from disk fragments using both file system metadata and content-based carving techniques.
Materials:
- Forensic workstation with test tool installed
- Standardized test disk image with pre-defined deleted files
- Reference dataset of files (documents, images, archives)
- Stopwatch or timing software
Methodology:
- Test Preparation: Utilize a standardized forensic test image containing a known set of recently deleted files and files with wiped metadata.
- File Recovery: Using the tool under test, execute a recovery process to identify and recover deleted files based on file system artifacts.
- Data Carving: Conduct a content-based carving operation targeting specific file signatures (JPEG, PDF, ZIP) in unallocated space.
- Analysis: Compare recovered files against original reference files using hash verification. Document the recovery success rate, file integrity, and any corruption.
- Performance Metrics: Measure recovery accuracy, processing time, and resource utilization (CPU, RAM).
TRL Assessment Criteria:
- TRL 4-5: Basic recovery of recently deleted files with intact metadata.
- TRL 6-7: Advanced carving of fragmented files from multiple file systems.
- TRL 8-9: Reliable recovery in complex scenarios (encrypted, damaged, or overwritten storage).
Protocol 3: Mobile Application Artifact Extraction
Objective: To assess the tool's ability to extract, decode, and interpret data artifacts from mobile applications, including encrypted or protected content.
Materials:
- Test mobile devices (iOS and Android)
- Target applications (e.g., WhatsApp, Signal, Telegram)
- Commercial mobile forensic tool (e.g., Cellebrite UFED, Oxygen Forensic Detective [41] [42])
- Open-source alternatives where available
- Data analysis workstation
Methodology:
- Device Preparation: Configure test devices with standardized datasets including messages, media files, and application data.
- Data Extraction: Perform logical, file system, or physical extraction using the tool under test based on device accessibility and capabilities.
- Artifact Decoding: Process the extracted data to parse and interpret application-specific databases and cache files.
- Data Verification: Compare tool output against known reference data to verify decoding accuracy and completeness.
- Reporting: Evaluate the tool's ability to generate comprehensive reports suitable for further analysis or presentation.
TRL Assessment Criteria:
- TRL 4-5: Logical extraction and basic decoding of common application data.
- TRL 6-7: File system extraction and decoding of encrypted application databases.
- TRL 8-9: Physical extraction and comprehensive interpretation of artifacts from latest application versions.
Protocol 4: Memory Forensics for Malware Detection
Objective: To validate the tool's capability to acquire and analyze volatile memory (RAM) for the detection of sophisticated malware, rootkits, and unauthorized processes.
Materials:
- Test system with controlled malware samples (in isolated environment)
- Memory acquisition tool (e.g., Magnet RAM Capture [33] [44], Belkasoft RAM Capturer [44])
- Memory analysis framework (e.g., Volatility [42] [43] [44])
- Analysis workstation
Methodology:
- Baseline Establishment: Execute a clean system snapshot to establish a baseline of normal processes and network connections.
- Malware Introduction: Introduce known malware samples into the test environment and allow execution.
- Memory Acquisition: Use the tool under test to capture the system's physical memory while the malware is active.
- Malware Analysis: Analyze the memory dump to identify malicious processes, injected code, network connections, and other indicators of compromise.
- Effectiveness Metrics: Document detection accuracy, analysis depth, and time required for identification.
TRL Assessment Criteria:
- TRL 4-5: Basic process listing and network connection enumeration.
- TRL 6-7: Detection of code injection and rootkit techniques.
- TRL 8-9: Identification of advanced persistent threats (APTs) with minimal false positives.
Forensic Tool TRL Assessment Workflow
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 2: Digital Forensics Research Reagent Solutions
| Research Reagent | Function | Example Tools & Specifications |
|---|---|---|
| Forensic Write Blockers | Prevents modification of source media during acquisition, ensuring evidence integrity [42] | Hardware write blockers (Tableau, WiebeTech), software write blockers (USB Write Blocker [44]) |
| Reference Disk Images | Standardized datasets for tool validation and comparative performance testing [45] | Computer Forensic Reference Datasets (CFREDS), Digital Corpora, custom test images |
| Hash Verification Tools | Generate cryptographic hashes to verify evidence integrity and identify known files [33] [44] | HashMyFiles [44], built-in hashing in FTK Imager [33], MD5/SHA-256/SHA-512 algorithms |
| Memory Acquisition Tools | Capture volatile memory (RAM) for analysis of running processes and malware [33] [44] | Magnet RAM Capture [33], Belkasoft RAM Capturer [44], WinPmem |
| File Carving Utilities | Recover files from unallocated space using file signature recognition without filesystem metadata [33] [42] | Bulk Extractor [33] [44], Foremost, Scalpel, Photorec |
| Metadata Extraction Tools | Read and analyze metadata embedded within files for timeline and provenance analysis [33] [44] | ExifTool [33] [44], FOCA |
| Packet Capture Tools | Record and analyze network traffic for network forensic investigations [41] [43] [44] | Wireshark [41] [44], TCPdump, NetworkMiner [44] |
| Forensic Linux Distributions | Pre-configured operating systems bundling multiple forensic tools for immediate deployment [33] [44] | CAINE [33] [44], PALADIN [41] [44], SIFT Workstation [44] |
TRL Integration Framework for Development Lifecycle
TRL Mapping to Development Lifecycle
The integration of TRL assessment protocols within the forensic software development lifecycle establishes a rigorous framework for evaluating tool maturity and reliability. The experimental methodologies detailed in this document provide reproducible processes for benchmarking performance across critical forensic functions including evidence acquisition, data recovery, mobile artifact extraction, and malware detection. Implementation of these standardized assessment protocols enables research teams to quantitatively measure development progress, identify capability gaps, and validate forensic soundness throughout the development pipeline. This systematic approach accelerates the translation of basic research into operational solutions while ensuring the resulting tools meet the exacting standards required for digital evidence in legal proceedings. Future methodology refinements will address emerging challenges in cloud forensics, IoT device analysis, and artificial intelligence applications within digital investigations.
Overcoming Common Hurdles in TRL-Based Forensic Development
Mitigating AI and Machine Learning Biases in Forensic Algorithms During Mid-TRL Stages
Artificial intelligence is revolutionizing forensic science, from DNA analysis to digital evidence examination. However, these systems introduce a critical risk: algorithmic bias [46]. When AI systems perpetuate or amplify historical prejudices, they threaten the fundamental principles of forensic integrity and equal justice under the law. For marginalized communities, the consequences can be severe—including erroneous forensic conclusions that lead to wrongful convictions or exonerations [46].
AI bias in forensic algorithms stems from a fundamental truth: algorithms are only as fair as the data they learn from [46]. When AI systems train on historical forensic data that reflect explicit or systemic biases, they inevitably perpetuate those same injustices. The problem is compounded when AI developers, often working outside the forensic science domain, make design choices without fully grasping the legal and ethical implications of their systems [46].
The Technology Readiness Level (TRL) framework provides a crucial structure for addressing bias systematically throughout development. Mid-TRL stages (TRL 4-6) represent a critical window for intervention—where technologies have proven viable in laboratory settings but have not yet been deployed in operational environments [3]. At TRL 4, multiple component pieces are tested with one another; TRL 5 involves more rigorous testing in near-realistic environments; and TRL 6 requires a fully functional prototype [3].
Understanding AI Bias: Typology and Forensic Implications
AI bias manifests in three primary forms that present distinct challenges for forensic applications:
- Algorithmic bias emerges from the design and structure of machine learning algorithms themselves, such as optimization functions that prioritize overall accuracy while ignoring performance disparities across demographic groups [47].
- Data bias results from training datasets that are unrepresentative, incomplete, or contain historical patterns of discrimination [47]. In forensic contexts, this might include fingerprint databases that overrepresent certain demographic groups or crime lab processing statistics that reflect historical policing biases.
- Cognitive bias encompasses human prejudices and assumptions that influence AI development decisions, from problem definition through data collection to model interpretation, often reflecting unconscious biases of development teams [47].
In forensic applications, these biases can become embedded in seemingly objective analyses. For example, a facial recognition system might perform differently across demographic groups due to unrepresentative training data, potentially leading to misidentification [47]. Similarly, DNA mixture interpretation algorithms might develop biases if trained predominantly on specific population groups.
Table 1: AI Bias Typology in Forensic Contexts
| Bias Type | Primary Source | Forensic Manifestation | Potential Impact |
|---|---|---|---|
| Algorithmic Bias | Model architecture and optimization functions | Disparate performance across demographic groups | Differential error rates in evidence analysis |
| Data Bias | Unrepresentative or historically skewed training data | Systematic errors with specific evidence types | Over/under-representation of certain patterns |
| Cognitive Bias | Developer assumptions and problem framing | Blind spots in forensic application design | Failure to account for relevant contextual factors |
Mid-TRL Bias Mitigation Framework
TRL 4 (Component Validation) Protocols
At TRL 4, where multiple component pieces are tested with one another, bias mitigation focuses on data curation and component-level fairness validation [3]. The primary objective is to ensure that individual algorithm components do not introduce or amplify biases before integration.
Data Curation Protocol:
- Dataset Auditing: Implement statistical measures to identify representation gaps across protected attributes (race, gender, age, socioeconomic status) using the following metrics:
- Demographic parity ratios
- Feature distribution comparisons
- Missing data patterns analysis
- Data Preprocessing: Apply techniques to address identified biases:
Component Testing Protocol:
- Performance Disparity Assessment: Test each algorithm component across demographic groups using:
- Stratified k-fold cross-validation
- Confidence interval analysis for error rates
- Statistical significance testing for performance differences
- Bias Metric Establishment: Define acceptable performance differential thresholds for each component, typically not exceeding 5% disparity in false positive/negative rates across protected groups.
Table 2: Quantitative Bias Metrics for TRL 4 Validation
| Metric | Calculation | Acceptable Threshold | Measurement Frequency |
|---|---|---|---|
| Disparate Impact Ratio | (Selection Rate for Protected Group) / (Selection Rate for Reference Group) | 0.8 - 1.25 | Each development sprint |
| Equalized Odds Difference | ∣FPRGroup A - FPRGroup B∣ + ∣TPRGroup A - TPRGroup B∣ | < 0.05 | Component integration |
| Average Odds Difference | (FPRGroup A - FPRGroup B + TPRGroup A - TPRGroup B) / 2 | < 0.05 | Component integration |
| Statistical Parity Difference | P(Ŷ=1⎮Group A) - P(Ŷ=1⎮Group B) | < 0.05 | Each data version |
TRL 5 (Integrated Testing) Protocols
At TRL 5, described as "breadboard technology" undergoing rigorous testing in near-realistic environments, the focus shifts to integrated system performance and adversarial debiasing [3].
Environmental Testing Protocol:
- Simulated Forensic Scenarios: Develop testing environments that mirror real-world operational conditions while controlling for bias variables:
- Create matched pairs of test cases that differ only in protected attributes
- Implement blinding procedures to prevent evaluator bias
- Introduce realistic noise and confounding factors
- Cross-Environment Validation: Test integrated systems across multiple simulated environments representing different demographic contexts and operational conditions.
Adversarial Debiasing Implementation:
- Architecture Design: Implement a dual-network framework where:
- Primary network performs the core forensic analysis task
- Adversarial network attempts to predict protected attributes from the primary network's internal representations [47]
- Optimization Strategy: Balance task performance and fairness through multi-objective loss functions that penalize the primary network when the adversary successfully predicts protected attributes.
TRL 6 (Prototype Demonstration) Protocols
At TRL 6, where a "fully functional prototype or representational model" exists, bias mitigation emphasizes explainability and stakeholder validation [3].
Explainable AI (XAI) Implementation:
- Interpretability Framework: Develop model explanations that are accessible to forensic examiners:
- Implement feature importance rankings for key predictions
- Generate counterfactual explanations ("What would change this outcome?")
- Create confidence metrics with clear calibration references
- Decision Transparency: Ensure every risk score or forensic recommendation is traceable and understandable, enabling human reviewers to assess and challenge AI reasoning [46].
Stakeholder Validation Protocol:
- Domain Expert Review: Engage forensic scientists, legal professionals, and ethicists in prototype evaluation through structured workshops and scenario testing.
- Affected Community Feedback: Incorporate perspectives from potentially impacted communities through consultative panels and usability testing with diverse participants.
Experimental Protocols for Bias Detection
Cross-Group Performance Analysis
Objective: Systematically evaluate whether AI forensic algorithms perform consistently across different demographic groups.
Materials:
- Stratified test datasets representing relevant protected attributes
- Performance metrics pipeline (accuracy, precision, recall, F1-score)
- Statistical analysis software (R, Python with scikit-learn)
Procedure:
- Partition test data by protected attributes (race, gender, age, socioeconomic status)
- Calculate performance metrics separately for each subgroup
- Compute disparity metrics comparing subgroup performance to reference groups
- Conduct statistical significance testing (t-tests, ANOVA) on observed differences
- Document effect sizes for significant disparities
Interpretation: Performance disparities exceeding pre-established thresholds (typically 5% difference in error rates) indicate potential algorithmic bias requiring mitigation.
Adversarial Bias Detection
Objective: Identify subtle biases that may not manifest in overall performance metrics but could disproportionately impact specific subgroups.
Materials:
- Trained forensic AI model
- Adversarial probing framework
- Gradient-based attribution tools
Procedure:
- Freeze weights of the trained forensic model
- Train a simple classifier to predict protected attributes from the model's internal representations
- Evaluate the adversary's performance—high accuracy indicates the model's representations encode information about protected attributes
- Use gradient-based attribution to identify which features contribute most to protected attribute prediction
- Iteratively retrain the primary model to minimize adversary performance while maintaining task accuracy
Interpretation: Successful reduction of adversary accuracy without degrading primary task performance indicates reduced encoding of protected attributes in the model.
Visualization Framework for Bias Mitigation
The following diagrams illustrate the integrated bias mitigation workflow across mid-TRL stages, following the specified color palette and contrast requirements.
Bias Mitigation Workflow Across Mid-TRL Stages
Bias Detection Experimental Protocol
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Research Materials for AI Bias Mitigation in Forensic Algorithms
| Tool/Category | Specific Implementation | Function in Bias Mitigation |
|---|---|---|
| Bias Testing Frameworks | AI Fairness 360 (AIF360), Fairlearn, Aequitas | Comprehensive metric calculation and disparity detection across protected attributes |
| Data Validation Tools | Google Facets, Pandas Profiling, Great Expectations | Dataset representation analysis and imbalance detection |
| Model Interpretation | SHAP, LIME, Captum | Explainable AI implementation for forensic transparency |
| Adversarial Testing | Adversarial Robustness Toolbox, TextFooler | Bias detection through stress-testing and adversarial examples |
| Statistical Analysis | Scipy, Statsmodels, R Statistical Environment | Significance testing for performance disparities |
| Benchmark Datasets | NIST Forensic Science Standards, Public Safety Canada Data | Standardized testing against representative samples |
| Visualization Libraries | Matplotlib, Seaborn, Plotly | Bias metric communication and stakeholder reporting |
Implementation Considerations for Forensic Contexts
Forensic-Specific Bias Challenges
Forensic algorithms present unique challenges for bias mitigation that extend beyond conventional machine learning applications:
- Contextual Bias: Forensic examiners may be influenced by extraneous contextual information, and AI systems can amplify these effects if not properly constrained [46].
- Black Box Problem: Complex models that cannot explain their decisions are fundamentally unsuitable for forensic applications, where transparency is a cornerstone of evidence admissibility [46].
- Feedback Loops: If forensic conclusions influence policing patterns that generate new training data, self-reinforcing bias cycles can develop, where certain communities become increasingly overrepresented in forensic datasets [46].
Governance and Documentation Framework
Effective bias mitigation requires systematic governance integrated throughout the forensic software development lifecycle:
- Algorithmic Impact Assessments: Conduct mandatory evaluations for all forensic AI systems prior to TRL 4 advancement, documenting potential bias risks and mitigation strategies.
- Version Control for Models: Maintain detailed records of model architectures, training data profiles, and performance metrics across iterations to enable bias tracking over time.
- Continuous Monitoring Protocols: Implement automated systems to track AI performance across demographic groups in real-time, with alert thresholds for emerging disparities [47].
Mitigating AI bias in forensic algorithms during mid-TRL stages represents both a technical challenge and an ethical imperative. By implementing structured protocols at TRL 4 (component validation), TRL 5 (integrated testing), and TRL 6 (prototype demonstration), developers can identify and address biases before they become embedded in operational systems. The experimental frameworks and visualization tools presented here provide a pathway for building forensic AI systems that enhance rather than undermine the pursuit of justice. As regulatory frameworks evolve worldwide, with stricter oversight for high-risk AI applications [46], proactive bias mitigation will become increasingly essential for forensic algorithm development. Through deliberate action—including diverse training data, explainable models, human oversight, continuous monitoring, and regulatory compliance—AI can become a force for greater fairness and accuracy in forensic science.
Solving Data Access and Privacy Challenges for Testing in Relevant Environments (TRL 5-6)
Within the framework of a forensic software development lifecycle, the Technology Readiness Level (TRL) scale provides a critical methodology for assessing the maturity of investigative technologies. TRL 5 is defined as "Component and/or breadboard validation in relevant environment," where basic technological components are integrated with realistic supporting elements for testing in a simulated environment [2] [48]. TRL 6 advances to "System/subsystem model or prototype demonstration in a relevant environment," requiring a representative model or prototype system to be tested in conditions that closely approximate the final operational setting [2] [3]. For forensic software, this relevant environment necessitates using realistic, often sensitive, digital evidence to validate tool functionality under operational conditions.
The transition through TRL 5-6 presents a significant challenge known as the "Valley of Death," where promising technologies often falter due to the steeply rising costs and effort required to advance from laboratory validation to operational demonstration [2]. This challenge is particularly acute in forensic software development, where testing with realistic data introduces complex privacy, legal, and integrity concerns that must be systematically addressed to ensure both technological maturity and regulatory compliance.
Data Access and Privacy Challenges at TRL 5-6
Primary Challenges in Forensic Software Validation
Data Sensitivity and Evidentiary Integrity: Forensic investigations involve direct handling of digital evidence that may contain personally identifiable information (PII), financial records, intimate communications, or other sensitive content. During TRL 5-6 testing, this creates a fundamental tension between validation requirements and privacy obligations [49] [50]. The software must be proven effective against realistic data patterns while protecting individual privacy and maintaining the chain of custody integrity that is foundational to forensic admissibility [25].
Regulatory Compliance Conflicts: At TRL 5-6, developers must validate that their tools can process evidence in accordance with legal standards, yet using actual case data for testing may violate the very regulations the tools are designed to uphold, such as GDPR, HIPAA, or emerging AI laws [51] [50]. This creates a circular dependency where tools cannot be certified for use without testing on sensitive data, but such testing may be legally prohibited without certified tools.
Reproducibility Versus Anonymization: The scientific principle of reproducibility requires that testing processes can be replicated to validate findings [25]. However, effective data anonymization for privacy protection often destroys the very patterns and relationships that forensic tools are designed to detect, particularly in complex digital evidence such as communication networks or metadata relationships.
Quantitative Analysis of Validation Challenges
Table 1: Data Privacy and Access Challenges at TRL 5-6
| Challenge Category | Impact on TRL 5-6 Progression | Common Consequences |
|---|---|---|
| Data Sensitivity | Limits access to realistic test datasets; restricts validation completeness | Inadequate testing against edge cases; undiscovered tool limitations [49] |
| Regulatory Compliance | Creates legal barriers to data sharing; increases development timeline | Extended validation cycles; increased costs for legal compliance [51] |
| Evidentiary Integrity | Requires maintenance of chain of custody during testing | Complex test environment setup; specialized secure infrastructure needed [25] [50] |
| Reproducibility Requirements | Conflicts with anonymization needs; limits open research validation | Reduced peer review capability; constrained scientific scrutiny [25] |
Experimental Protocols for Secure TRL 5-6 Testing
Synthetic Data Generation with Forensic Fidelity
Objective: Create scientifically valid synthetic datasets that maintain the statistical properties and complex relationships of authentic digital evidence without containing real sensitive information.
Methodology:
- Pattern Extraction from Anonymous Sources: Utilize publicly available datasets, anonymized research data, or deprecated case files (with appropriate authorization) to extract statistical patterns, metadata structures, and data relationships characteristic of forensic evidence.
- Generative Modeling for Evidence Creation: Implement generative adversarial networks (GANs) or transformer-based models to create synthetic digital artifacts that replicate the functional characteristics of real evidence without containing actual sensitive content.
- Forensic Validation of Synthetic Datasets: Verify that synthetic data triggers the same tool responses as authentic data would, ensuring that:
- File system artifacts maintain proper metadata structures
- Network data preserves protocol compliance and timing patterns
- Mobile device data replicates application hierarchies and database relationships
- Cross-Validation with Limited Authentic Data: Where possible and legally permissible, validate synthetic dataset efficacy by comparing tool performance between synthetic and a minimal set of properly anonymized authentic data samples.
Privacy-Preserving Data Processing Protocols
Objective: Enable validation of forensic tools against authentic evidence while implementing technical safeguards to prevent privacy violations.
Methodology:
- Differential Privacy Implementation:
- Integrate differential privacy mechanisms into test data processing pipelines
- Quantify and document the privacy budget (ε) for each test iteration
- Measure the impact of privacy noise on tool performance metrics
- Homomorphic Encryption Testing:
- Implement homomorphic encryption schemes to allow tool operation on encrypted test data
- Validate tool functionality against encrypted datasets while measuring performance overhead
- Compare results between encrypted and unencrypted processing to verify consistency
- Data Minimization and Segmentation:
- Implement strict data access controls limiting exposure to only necessary data elements
- Segment test datasets to prevent reconstruction of complete evidentiary contexts
- Automate data purging protocols after test completion
Forensic Readiness Integration in SDLC
Objective: Embed forensic readiness capabilities directly into the software development lifecycle to ensure tools generate appropriate audit trails and maintain evidentiary integrity during testing and operational deployment [14].
Methodology:
- Instrumentation for Audit Trail Generation:
- Implement comprehensive logging of all tool operations during testing
- Capture system state snapshots at critical decision points
- Ensure timestamps and operator actions are immutably recorded
- Chain of Custody Simulation:
- Design test protocols that mimic operational evidence handling procedures
- Implement digital signatures for all test data transactions
- Validate that testing processes maintain an unbroken chain of custody documentation
- Integrity Verification Automation:
- Integrate automated checksum verification throughout test execution
- Implement write-blocking functionality validation for acquisition testing
- Verify hash value maintenance for all processed evidence items [25]
Implementation Framework and Visualization
Secure Testing Environment Architecture
The following diagram illustrates the secure data flow and privacy controls required for TRL 5-6 testing of forensic software:
Secure Testing Environment Architecture: This diagram illustrates the controlled data flow and privacy-preserving components required for valid TRL 5-6 testing of forensic software while maintaining data protection and evidentiary standards.
Research Reagent Solutions for Forensic Software Testing
Table 2: Essential Testing Components for Forensic Software at TRL 5-6
| Component Category | Specific Solutions | Function in TRL 5-6 Validation |
|---|---|---|
| Data Generation Tools | Synthetic data generators (GANs, rule-based), Data anonymization pipelines | Creates realistic but privacy-compliant test datasets that maintain forensic characteristics without sensitive content [49] |
| Privacy-Preserving Technologies | Differential privacy frameworks, Homomorphic encryption libraries, Secure multi-party computation | Enables testing with controlled real data while minimizing privacy risks and maintaining regulatory compliance [51] |
| Validation Frameworks | NIST Computer Forensics Tool Testing (CFTT) methodologies, ISO/IEC 17025 compliant testing protocols | Provides standardized methodologies for tool validation ensuring reliability and adherence to international quality standards [25] |
| Audit and Integrity Tools | Immutable logging systems, Digital signature applications, Hash verification utilities | Maintains chain of custody documentation and ensures integrity of testing processes for evidentiary purposes [14] [25] |
| Compliance Verification | Regulatory assessment checklists, Data protection impact assessments, Legal compliance frameworks | Ensures testing methodologies align with relevant regulations (GDPR, HIPAA, EU AI Act) and forensic standards [51] [50] |
Addressing data access and privacy challenges at TRL 5-6 is not merely a technical obstacle but a fundamental requirement for developing forensically sound and legally admissible digital tools. By implementing the structured protocols and frameworks outlined in this application note, developers can create a rigorous pathway for validating forensic software while maintaining compliance with privacy regulations and evidentiary standards.
The integration of TRL assessment directly into the forensic software development lifecycle provides a measurable framework for tracking progress toward operational readiness while systematically managing the unique risks associated with digital evidence processing. This approach enables researchers to bridge the "Valley of Death" between laboratory prototypes and field-deployable tools, ensuring that forensic technologies meet both technical requirements and legal admissibility standards before deployment in investigative contexts.
Managing Technical Debt and Legacy Code in Long-Term Forensic Software Projects
Technical debt, the implied cost of future rework caused by choosing expedient solutions over sustainable approaches, represents a critical challenge in forensic software development [52]. For long-term forensic projects, this debt accumulates as architectural weaknesses, outdated dependencies, and legacy code that can compromise evidentiary integrity, analytical accuracy, and system security. Research indicates that technical debt constitutes 20-40% of the entire technology estate value before depreciation, creating a significant drag on development productivity and innovation capacity [53]. Within forensic applications, where software failures can impact legal proceedings and public safety, unmanaged technical debt introduces unacceptable risks including security vulnerabilities, evidence contamination, and system reliability issues.
The integration of Technology Readiness Level (TRL) assessment into the forensic software development lifecycle provides a structured framework for quantifying technical debt impact across maturation stages. This approach enables researchers and development teams to prioritize debt reduction efforts based on both technological maturity and forensic reliability requirements. As organizations increasingly rely on software for mission-critical forensic analysis, establishing robust protocols for technical debt management becomes essential for maintaining scientific rigor and legal defensibility.
Quantitative Impact Assessment
The financial and operational implications of technical debt in software systems are substantial, with particular significance for forensic applications where reliability is paramount. The following table summarizes key quantitative findings from recent industry studies:
Table 1: Quantitative Impact of Technical Debt and Legacy Systems
| Metric | Impact Level | Source/Context |
|---|---|---|
| Technical debt as percentage of IT estate | 20-40% of total technology value [53] | McKinsey research on technology estates |
| Developer time spent on technical debt | 23-33% of total development time [54] [52] | Industry surveys across multiple sectors |
| IT budget consumed by technical debt | 25-40% of total IT budget [55] [56] | Survey of technology executives |
| U.S. accumulated technical debt | $1.52 trillion (2022) [56] | IT-CISQ 2022 Report |
| Legacy system prevalence in banks | 70% still rely on legacy systems (2025) [56] | Global banking technology assessment |
| Project cost increase due to tech debt | 10-20% additional cost on projects [53] | McKinsey analysis |
| Reduction in development speed | 30% slower due to technical debt [54] | Industry performance measurements |
| Modernization failure rate | 40% higher for high-tech debt organizations [53] | Comparison of top vs. bottom performers |
For forensic software projects, these quantitative impacts translate directly into increased operational risk, reduced analytical reliability, and potential compromise of evidentiary integrity. The 2022 breach of the U.S. federal court system's Case Management/Electronic Case Files (CM/ECF) system demonstrates how legacy system vulnerabilities can expose sensitive legal data, forcing courts to revert to paper filing systems and creating substantial operational disruption [57]. This incident, stemming from a system originally developed in the late 1990s, illustrates the critical security implications of unaddressed technical debt in forensic and legal environments.
Application Notes: Technical Debt Management Framework
Establishing a Technical Debt Balance Sheet
Creating a comprehensive technical debt balance sheet provides the foundation for effective management. This financial-style accounting enables forensic software teams to document assets, data, and their links to business value, facilitating informed decision-making about debt reduction priorities [53]. The balance sheet should catalog technical debt at the asset level (applications, databases, etc.) and categorize by debt type, as remediation strategies differ significantly across categories.
Table 2: Technical Debt Categorization Framework for Forensic Software
| Debt Category | Forensic Software Impact | Remediation Approach |
|---|---|---|
| Architectural Debt | Compromises system integration and evidence chain integrity | Structured modernization with API-first design |
| Code Debt | Reduces analytical accuracy and introduces variability | Refactoring with peer review and forensic validation |
| Infrastructure Debt | Creates security vulnerabilities and availability risks | Cloud migration with forensic-grade security |
| Documentation Debt | Hinders reproducibility and expert testimony | Automated documentation generation |
| Test Debt | Allows undetected defects in analytical algorithms | Test-driven development with comprehensive coverage |
| Dependency Debt | Introduces known vulnerabilities into evidence processing | Regular dependency scanning and updates |
Implementation of this categorization at a large technology company revealed that just 10-15 assets typically drive the majority of technical debt, and only four debt types accounted for 50-60% of the total impact [53]. This concentration effect enables targeted remediation efforts that maximize return on investment while addressing the most critical forensic reliability concerns.
TRL-Integrated Assessment Protocol
Integrating technical debt assessment with Technology Readiness Level evaluation creates a multidimensional framework for prioritizing forensic software improvements. The following protocol establishes a standardized approach for this integrated assessment:
Protocol 1: TRL-Technical Debt Integrated Assessment
Application Portfolio Inventory: Catalog all software assets supporting forensic workflows, documenting core functionalities, dependencies, and evidentiary applications.
TRL Assignment: Classify each asset according to standard Technology Readiness Levels (1-9), with particular attention to validation in relevant forensic environments (TRL 6-7).
Technical Debt Quantification: Apply the balance sheet approach to quantify technical debt for each asset, using both automated analysis tools and expert assessment.
Impact Mapping: Diagram relationships between technical debt items and forensic reliability metrics, including evidence integrity, analytical precision, and reproducibility.
Prioritization Matrix: Position assets within a TRL-Debt matrix, prioritizing high-debt applications at critical maturity levels (typically TRL 6-8) for remediation.
This integrated assessment enables forensic software teams to focus resources on applications where technical debt most significantly impacts maturation potential and operational reliability. Research indicates that companies adopting this systematic approach have successfully eliminated over 665 applications/platforms and achieved nearly 30% reduction in their enterprise landscape complexity [54].
Experimental Protocols for Technical Debt Remediation
Architectural Observability and Static Analysis Protocol
Static analysis provides powerful capabilities for identifying technical debt in forensic software, particularly for detecting security vulnerabilities, code quality issues, and architectural weaknesses that may compromise evidentiary analysis [58]. The following protocol details a comprehensive approach to static analysis implementation:
Protocol 2: Static Analysis for Forensic Software Assessment
Tool Selection and Configuration:
- Select static analysis tools compatible with the forensic software technology stack (e.g., SonarQube, CodeClimate, CAST).
- Configure analysis rulesets to prioritize forensic-specific concerns including data integrity, chain of custody, and audit trail completeness.
- Establish quality gates based on forensic reliability requirements rather than general software metrics.
Baseline Assessment:
- Execute initial full codebase scan to establish technical debt baseline.
- Identify critical vulnerabilities (e.g., input validation failures, potential evidence contamination points).
- Quantify debt using standardized metrics (e.g., SQALE method) to enable tracking.
Binary Analysis Integration:
- Perform binary code analysis to detect vulnerabilities that may be obfuscated in source code.
- Analyze third-party dependencies for known vulnerabilities and compatibility issues.
- Document any discrepancies between source and binary analysis results.
Forensic Quality Validation:
- Map identified issues to potential forensic reliability impacts.
- Prioritize remediation based on both severity and evidentiary criticality.
- Establish continuous monitoring with automated alerts for new debt introduction.
The implementation of this protocol for the Unreal IRCD security investigation demonstrated how static analysis can detect critical vulnerabilities—in this case, a backdoor that allowed remote command execution—even when deliberately obfuscated in source code [58]. For forensic applications, this capability is essential for maintaining analytical integrity and preventing evidence manipulation.
Legacy System Modernization Protocol
Legacy system modernization presents particular challenges for forensic software, where established tools may contain validated analytical methods but rely on outdated technologies. The following protocol provides a structured approach to modernization while preserving forensic reliability:
Protocol 3: Forensic Legacy System Modernization
Forensic Requirement Analysis:
- Document all forensic-specific functionalities, including analytical algorithms, evidence handling procedures, and reporting capabilities.
- Identify regulatory and legal compliance requirements specific to jurisdiction and application.
- Establish validation criteria for modernized system equivalence.
Modernization Approach Selection:
- Evaluate refactoring, rearchitecting, rebuilding, and replacement options against forensic reliability requirements.
- Select approach based on technical debt severity, forensic criticality, and resource constraints.
- For complex systems, consider strangler fig pattern with parallel operation during transition.
Incremental Implementation:
- Decompose system into modular components based on forensic functionality.
- Establish continuous integration pipeline with forensic-specific testing protocols.
- Implement component-by-component modernization with validation at each stage.
Forensic Validation:
- Conduct parallel processing comparison between legacy and modernized systems.
- Validate analytical equivalence using standardized test datasets.
- Document all functional and performance differences for regulatory compliance.
This protocol's application in financial services organizations has demonstrated the potential for 30-40% reduction in IT maintenance costs and 50% faster time-to-market for enhanced capabilities [56], while in forensic contexts, the primary benefit is sustained analytical reliability amidst technological evolution.
Visualization: Technical Debt Management Workflow
The following diagram illustrates the integrated technical debt management workflow within the forensic software development lifecycle, highlighting critical decision points and quality gates:
Diagram 1: Technical Debt Management in Forensic Software Development
This workflow emphasizes the continuous nature of technical debt management, with monitoring processes feeding back into initial assessment to create a cycle of continuous improvement. The integration of TRL assessment enables prioritization based on both technological maturity and forensic criticality, ensuring resources focus on applications where technical debt most significantly impacts evidentiary reliability.
Research Reagent Solutions
The effective management of technical debt in forensic software requires specialized tools and methodologies. The following table catalogs essential "research reagents" for technical debt identification, quantification, and remediation:
Table 3: Technical Debt Management Research Reagent Solutions
| Tool/Category | Primary Function | Forensic Application |
|---|---|---|
| SonarQube | Static code analysis and quality gate enforcement | Detect code smells and vulnerabilities in evidence processing algorithms [52] |
| CAST | Architectural debt quantification and structural analysis | Assess system-level dependencies in complex forensic workflows [52] |
| CodeClimate | Automated code review and maintainability metrics | Maintain code quality across distributed forensic development teams [52] |
| Zenhub | GitHub-native technical debt tracking and visualization | Integrate debt management with existing development workflows [52] |
| Stepsize | In-editor technical debt annotation and prioritization | Enable developer-level debt documentation without workflow disruption [52] |
| CodeSonar | Binary and source code static analysis for security | Detect vulnerabilities in compiled components and third-party dependencies [58] |
| vFunction | Architectural observability and modernization assessment | Identify architectural drift in long-term forensic codebases [55] |
| TRL Assessment Framework | Technology maturity evaluation across development stages | Prioritize debt reduction based on implementation readiness [54] |
| SQALE Method | Technical debt quantification in time/cost metrics | Standardize debt measurement across diverse forensic applications [52] |
These tools form a comprehensive toolkit for addressing technical debt across the forensic software lifecycle. Leading organizations typically allocate 15-20% of IT budgets to technical debt reduction, creating a structured investment in long-term reliability [54]. For forensic applications, this investment directly supports evidentiary integrity and analytical reproducibility—foundational requirements for legally defensible software systems.
Technical debt management represents a critical discipline for maintaining the long-term reliability, security, and evidentiary integrity of forensic software systems. By integrating TRL assessment with structured technical debt quantification, development teams can prioritize remediation efforts based on both technological maturity and forensic criticality. The protocols and methodologies presented provide a roadmap for systematic debt reduction while preserving the analytical reproducibility required for legal proceedings.
As forensic software continues to evolve in complexity and application scope, proactive technical debt management transitions from operational optimization to essential practice. The quantitative impact data demonstrates the substantial costs of neglected debt, while the experimental protocols provide actionable approaches for maintaining forensic reliability throughout the software lifecycle. Through implementation of these structured approaches, research and development teams can balance innovation velocity with long-term reliability, ensuring forensic software remains scientifically valid and legally defensible throughout its operational lifespan.
Digital forensics faces unprecedented complexity due to the convergence of cloud, mobile, and Internet of Things (IoT) ecosystems. The number of mobile devices worldwide is expected to reach 18.22 billion in 2025, while IoT devices are projected to almost double from 15.9 billion in 2023 to over 32.1 billion by 2030 [59]. This proliferation creates investigative challenges across interconnected platforms with differing operating systems, data formats, and security protocols. For researchers and developers, successfully navigating this landscape requires both advanced technical methodologies and a structured framework for assessing technological maturity throughout the forensic software development lifecycle.
Integrating Technology Readiness Level (TRL) assessment provides a critical framework for evaluating the maturity of forensic tools and methodologies. The established TRL scale, ranging from level 1 (basic principles observed) to level 9 (actual system proven in operational environment), offers a disciplined approach to technology development [60]. This paper establishes application notes and experimental protocols framed within TRL assessment, enabling forensic researchers to systematically advance tools from conceptualization to operational deployment in complex cross-platform environments.
Quantitative Landscape of Cross-Platform Forensics
Table 1: Global Device Proliferation and Data Generation Forecast
| Platform Category | 2025 Projected Volume | 2030 Projected Volume | Primary Data Challenges |
|---|---|---|---|
| Mobile Devices | 18.22 billion devices [59] | N/A | Advanced encryption, diverse OS variants, secure app data |
| IoT Devices | N/A | 32.1 billion devices [59] | Protocol fragmentation, volatile storage, limited processing |
| 5G Network Subscriptions | Dominant network technology by 2027 [59] | 6.3 billion subscriptions [59] | High-speed data transmission, network slicing complexity |
| Cloud Storage | Over 60% of newly generated data [16] | N/A | Jurisdictional fragmentation, petabyte-scale analysis |
Table 2: Technology Readiness Levels (TRL) in Forensic Development
| TRL Level | Description | Forensic Application Example |
|---|---|---|
| 1-3 (Basic Research) | Basic principles observed, technology concept formulated | Research into novel data extraction techniques for new IoT protocols |
| 4-5 (Technology Development) | Laboratory validation of component/subsystem | Developing prototype tool for specific IoT device family extraction |
| 6-7 (Technology Demonstration) | System/subsystem model or prototype demonstration in relevant environment | Field testing forensic tool on multiple IoT devices in simulated smart home |
| 8-9 (System Operation) | Actual system completed and qualified through test and demonstration | Tool deployed in operational investigations with documented legal acceptance |
Experimental Protocols for Cross-Platform Data Acquisition
Protocol: Integrated Mobile and Cloud Evidence Collection
Objective: To establish a standardized methodology for acquiring synchronized data from mobile devices and their associated cloud services, addressing jurisdictional and technical challenges.
Materials:
- Forensic workstation with specialized mobile acquisition software (e.g., Oxygen Forensic Detective, Belkasoft X)
- Cloud analysis toolkit capable of API-based data collection
- Write-blocking hardware for physical acquisitions
- Network isolation equipment for device analysis
Procedure:
- Device Identification and Isolation: Identify target mobile device and immediately isolate from networks to prevent remote data wiping [7]. Document device state, model, and hardware identifiers.
- Physical Acquisition: Attempt physical extraction using supported methods (logical, file system, or physical acquisition) based on device security status [10].
- Cloud Evidence Mapping: Identify cloud services associated with the device through installed application inventory and network connection history.
- API-Based Collection: Using legitimate credentials obtained through investigative means, employ cloud forensic tools to simulate app clients and download user data from services like Facebook, Instagram, or Telegram via their APIs [10].
- Data Correlation: Synchronize timestamps and user activities between device-resident data and cloud-derived evidence to create comprehensive activity timeline.
- Verification: Validate data completeness through hash comparison and transaction logging throughout acquisition process.
TRL Assessment Metrics: For this protocol, TRL 6 is achieved when the methodology successfully demonstrates synchronized data acquisition from at least three mobile platforms and their associated cloud services in a lab environment. TRL 9 requires documented success in multiple operational investigations with evidence admitted in judicial proceedings.
Protocol: Multi-Platform IoT Evidence Acquisition
Objective: To develop a standardized approach for capturing volatile and persistent data from diverse IoT devices including wearables, smart home appliances, and industrial sensors.
Materials:
- IoT protocol analyzers for Zigbee, Z-Wave, Bluetooth LE
- Network traffic interception tools
- Specialized hardware for IoT device interface extraction
- Data preservation storage with chain-of-custody documentation
Procedure:
- Device Ecosystem Mapping: Identify all IoT devices within investigation scope and document their interconnections and communication protocols [61].
- Network Traffic Capture: Deploy network monitoring tools to capture device-to-device and device-to-cloud communications, focusing on 5G and WiFi interfaces [59].
- Physical Memory Acquisition: Where possible, perform direct memory extraction from IoT devices using manufacturer interfaces (JTAG, SWD) or removable storage.
- Volatile Data Prioritization: Employ live forensic techniques to capture RAM content and network connections before device isolation, prioritizing most volatile data first [7].
- Gateway Device Analysis: Extract data from IoT hub devices or smartphones that control IoT ecosystems, as these often contain centralized logging information.
- Data Normalization: Convert various IoT data formats into standardized timeline for correlation analysis.
TRL Assessment Metrics: Progression to TRL 7 requires successful demonstration of the protocol across three distinct IoT device categories (e.g., wearable, smart home, industrial sensor) in a relevant environment. Advancement to TRL 8 requires validation in actual smart home or enterprise IoT environments with evidence supporting judicial proceedings.
Visualization of Forensic Workflows
Cross-Platform Forensic Acquisition Pathway
TRL Progression in Forensic Tool Development
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Forensic Research Tools and Platforms
| Tool Category | Representative Solutions | Primary Function | TRL Consideration |
|---|---|---|---|
| Mobile Forensic Platforms | Oxygen Forensic Detective, Cellebrite UFED | Physical and logical mobile device extraction | TRL 9 (Proven in operational use) |
| Multi-Platform Analysis Suites | Belkasoft X, Cellebrite Pathfinder | Cross-device data correlation and analysis | TRL 8-9 (Field validated) |
| Cloud Forensic Tools | Guardian Investigate, API-based collectors | Cloud data acquisition via service APIs | TRL 6-7 (Expanding deployment) |
| IoT Protocol Analyzers | Zigbee/Z-Wave sniffers, specialized IoT toolkits | IoT device communication interception | TRL 4-6 (Varies by device type) |
| Virtualization Platforms | Corellium iOS/Android virtualization | Mobile device emulation for testing | TRL 7 (Advanced research applications) |
| AI-Powered Analysis | BelkaGPT, AI-based media analysis | Large dataset processing and pattern recognition | TRL 5-7 (Varying maturity) |
Advanced Methodologies: Addressing Cross-Platform Complexity
Protocol: AI-Enhanced Cross-Platform Data Correlation
Objective: To leverage artificial intelligence and machine learning for identifying patterns and connections across disparate data sources from mobile, cloud, and IoT platforms.
Materials:
- AI-powered forensic platforms with natural language processing capabilities
- High-performance computing resources for large dataset analysis
- Labeled training data for algorithm validation
- Statistical analysis software for result verification
Procedure:
- Data Normalization: Convert all acquired evidence into standardized formats while preserving original metadata.
- Feature Extraction: Employ NLP algorithms to process text-based communications (emails, chats, documents) across platforms, extracting entities, relationships, and temporal markers [10].
- Pattern Recognition: Utilize machine learning models to flag anomalies in system logs, detect suspicious activity patterns, or identify hidden connections across datasets [9].
- Predictive Analysis: Apply historical data analysis to forecast potential evidence locations or identify system vulnerabilities [9].
- Human Validation: Implement expert review of AI-generated findings to mitigate algorithmic bias and ensure investigative accuracy.
- Documentation: Comprehensively document AI methodologies, training data provenance, and decision pathways for judicial scrutiny.
TRL Assessment Metrics: AI methodologies reach TRL 7 when they successfully demonstrate enhanced evidence identification compared to manual methods in simulated complex cases. TRL 9 requires documented operational success with transparent algorithm performance that withstands legal challenge.
The integration of TRL assessment throughout the forensic software development lifecycle provides researchers with a structured framework for advancing tools from conceptualization to judicial acceptance. As mobile, cloud, and IoT ecosystems continue to converge and evolve, the protocols and methodologies outlined in these application notes provide a foundation for addressing cross-platform complexity. The quantitative benchmarks, experimental protocols, and visualization frameworks enable systematic progression of forensic capabilities, while the identified research reagents establish the essential toolkit for contemporary digital forensic investigation. Through continued refinement of these approaches based on TRL assessment, the field can maintain investigative efficacy despite rapidly accelerating technological change.
Ensuring Ethical AI Use and Algorithmic Transparency for Courtroom Acceptance
The integration of artificial intelligence (AI) into legal proceedings represents a paradigm shift in forensic science and legal practice. Newly approved Federal Rule of Evidence 707 establishes that machine-generated evidence offered without an expert witness must satisfy the same reliability standards as traditional expert testimony under Rule 702 [62]. This legal development, coupled with the foundational Daubert Standard requiring that scientific evidence be tested, peer-reviewed, have a known error rate, and enjoy general acceptance in the scientific community, creates a demanding admissibility framework for AI systems [63]. Simultaneously, legal ethics opinions from organizations like the National Center for State Courts have clarified that technological competence with AI is now an ethical requirement for both judges and lawyers [64].
This application note provides a structured framework for researchers and developers to navigate these complex requirements by integrating Technology Readiness Level (TRL) assessment directly into the forensic software development lifecycle. The protocols outlined enable systematic progression from basic research to court-admissible AI tools through continuous validation and transparency documentation.
Legal and Ethical Framework for AI in Court
Legal Standards for Evidence Admissibility
Table 1: Legal Standards Governing AI Evidence Admissibility
| Legal Standard | Jurisdiction | Key Requirements | Application to AI Systems |
|---|---|---|---|
| Daubert Standard | U.S. Federal Courts | Testing, peer review, known error rates, general acceptance [63] | Requires validation studies, publication, error rate quantification, and community adoption |
| Federal Rule 702 | U.S. Federal Courts | Testimony based on sufficient facts/data, reliable principles/methods, reliable application [63] | Demands appropriate training data, validated algorithms, and proper implementation |
| Frye Standard | Some U.S. States | General acceptance in relevant scientific community [63] | Focuses on widespread acceptance of specific AI methodologies in forensic science |
| Mohan Criteria | Canada | Relevance, necessity, absence of exclusionary rules, properly qualified expert [63] | Emphasizes proper expertise and genuine need for AI evidence in specific cases |
| FRE 707 | U.S. Federal Courts | AI evidence without human expert must satisfy Rule 702 requirements [62] | Directly regulates machine-generated evidence without accompanying expert testimony |
Ethical Requirements for Legal AI Systems
Judicial ethics rules impose additional constraints on AI systems used in legal contexts. The Model Code of Judicial Conduct imposes a duty of technological competence on judicial officers [64], while the Model Rules of Professional Conduct extend similar requirements to attorneys [64]. Specific ethical considerations include:
- Ex Parte Communication Concerns: AI-generated material could be viewed as improper external influence on judicial decision-making [64]
- Confidentiality Requirements: Inputting confidential case information into public AI systems risks unauthorized data retention and use [65] [64]
- Bias and Fairness: Judges must be aware of potential biases in AI technology that could violate rules against acting with bias or prejudice [64]
- Supervision Obligations: Judicial officers and law firm partners must ensure staff use AI technologies appropriately and ethically [64]
Technology Readiness Assessment Framework
TRL Definitions for Forensic AI Systems
Table 2: Technology Readiness Levels for Forensic AI Development
| TRL | Stage Definition | Validation Requirements | Documentation Outputs |
|---|---|---|---|
| TRL 1-2 | Basic principles observed and formulated | Proof-of-concept testing on benchmark datasets | Research publications; initial algorithm descriptions |
| TRL 3 | Experimental analytical proof of concept | Lab-scale validation on simulated forensic data | Technical reports; initial bias assessment |
| TRL 4 | Component validation in laboratory environment | Testing with historical case data in controlled setting | Component validation reports; error rate estimates |
| TRL 5 | System validation in relevant environment | Testing in operational forensic laboratory | System validation studies; comparative performance analysis |
| TRL 6 | System demonstrated in relevant environment | Pilot deployment in multiple laboratory settings | Operational protocols; initial training materials |
| TRL 7 | System prototype demonstration in operational environment | Extended deployment with casework parallel testing | Standard operating procedures; maintenance protocols |
| TRL 8 | System complete and qualified | Multi-site validation studies with diverse case types | Comprehensive validation portfolios; Daubert documentation |
| TRL 9 | Actual system proven in operational environment | Successful deployment in routine casework with legal challenges | Court admission records; continuous monitoring reports |
Integrated Development and Validation Workflow
Experimental Protocols for AI Validation
Protocol 1: Algorithmic Transparency Documentation
Purpose: Establish comprehensive documentation of AI system functionality, training data, and limitations to satisfy Daubert and FRE 707 requirements.
Materials:
- AI system with complete version documentation
- Training datasets with provenance records
- Explainable AI (XAI) tools (LIME, SHAP, or proprietary equivalents)
- Model card and datasheet templates [66]
Procedure:
- Data Provenance Documentation
- Catalog all training datasets with sources, collection methods, and preprocessing steps
- Document known biases, gaps, or limitations in training data using standardized datasheets [66]
- Statistically characterize dataset composition and demographic representations
Model Architecture Transparency
- Document model type, architecture, and key parameters
- For black-box models, implement and document post-hoc explanation methods (LIME, SHAP) [66]
- Generate feature importance rankings and decision boundary analyses
Performance Limitation Mapping
- Identify edge cases and failure modes through adversarial testing
- Document known scenarios where model performance degrades
- Establish guardrails and rejection criteria for low-confidence predictions
Model Card Generation
- Prepare standardized model card reporting performance across different demographic groups and use cases [66]
- Document intended uses and contraindications for application
- Include maintenance schedules and retraining protocols
Deliverables: Complete model documentation package including datasheets for datasets, model cards, explanation methodologies, and limitation statements suitable for legal discovery.
Protocol 2: Forensic Tool Validation Testing
Purpose: Systematically validate AI tools according to SWGDE standards and Daubert requirements for known error rates and reliability.
Materials:
- Reference datasets with ground truth annotations
- Testing framework compatible with Computer Forensic Tool Testing (CFTT) methodology [67]
- Statistical analysis software for error rate calculation
- Performance benchmarking infrastructure
Procedure:
- Test Dataset Curation
- Assemble representative datasets covering expected operational scenarios
- Ensure dataset diversity across demographic, environmental, and technical variables
- Establish ground truth through expert consensus or validated methods
Accuracy and Precision Assessment
- Conduct repeated measurements across operational conditions
- Calculate precision, recall, F1 scores, and confidence intervals
- Perform receiver operating characteristic (ROC) analysis for classification systems
Error Rate Quantification
- Establish false positive and false negative rates across relevant conditions
- Document conditions that significantly impact error rates
- Compare performance against existing methods and random chance
Robustness and Stress Testing
- Test performance degradation with noisy, incomplete, or adversarial inputs
- Validate system behavior under edge cases and boundary conditions
- Assess stability across multiple software and hardware environments
Bias and Fairness Auditing
- Conduct disparity analysis across protected characteristics
- Implement fairness metrics (demographic parity, equalized odds)
- Document and mitigate identified biases
Deliverables: Comprehensive validation report including error rates, performance characteristics, limitation statements, and comparative analyses suitable for Daubert hearings.
Protocol 3: Operational Readiness Assessment
Purpose: Evaluate AI system performance in operational forensic environments and establish protocols for legal challenges.
Materials:
- Deployed AI system in operational environment
- Case tracking and performance monitoring system
- Legal challenge response protocol templates
- Continuous validation framework
Procedure:
- Pilot Deployment Design
- Establish parallel testing protocol comparing AI results with conventional methods
- Implement blinding procedures to prevent confirmation bias
- Deploy across multiple sites with varying case volumes and types
Performance Monitoring
- Track decision accuracy, processing time, and resource utilization
- Monitor for drift in model performance over time
- Document system failures and implementation challenges
Legal Challenge Preparedness
- Maintain complete case-specific documentation for discovery
- Prepare expert witnesses with comprehensive system knowledge
- Establish protocol for explaining system functionality in court
Continuous Validation
- Implement ongoing testing with new case data
- Establish criteria for system retraining or recalibration
- Monitor legal and regulatory developments impacting system use
Deliverables: Operational readiness report, legal challenge response protocol, continuous monitoring plan, and system maintenance documentation.
The Scientist's Toolkit: Essential Research Reagents
Table 3: Key Research Reagents for Forensic AI Development
| Tool Category | Specific Solutions | Function | Legal Relevance |
|---|---|---|---|
| Explainable AI (XAI) | LIME, SHAP, What-If Tool, AI Explainability 360 | Provide post-hoc explanations for model predictions [66] | Addresses Daubert requirement for understandable methodology [63] |
| Bias Detection | Fairness metrics (demographic parity, equalized odds), adversarial debiasing | Identify and mitigate discriminatory algorithm outputs [66] | Supports judicial ethics requirements for impartiality [64] |
| Validation Frameworks | CFTT methodology, SWGDE testing protocols [67] | Standardized testing for digital forensic tools | Establishes known error rates for Daubert compliance [63] |
| Transparency Documentation | Datasheets for Datasets, Model Cards [66] | Standardized documentation of data and model characteristics | Creates discoverable documentation for legal challenges [62] |
| Version Control | Git, DVC, MLflow | Reproducible model development and deployment | Ensures consistent evidence generation across cases |
Implementation Pathway to Courtroom Acceptance
The pathway to courtroom acceptance requires parallel progress in both technical maturity and legal integration. While TRL 1-3 focuses primarily on algorithmic development, TRL 4-6 must incorporate increasing legal scrutiny through Daubert compliance planning and FRE 707 requirements analysis [62] [63]. At TRL 7-9, legal integration becomes the primary focus, with systems undergoing actual legal challenges and refinement based on courtroom experience.
This integrated approach ensures that forensic AI systems mature technically while simultaneously building the documentation, validation, and transparency frameworks required for courtroom acceptance under evolving evidence standards and ethical requirements.
Benchmarking, Legal Admissibility, and Measuring Success
The integration of Technology Readiness Level (TRL) assessment into the forensic software development lifecycle necessitates robust, repeatable, and defensible validation benchmarks. For digital forensic tools, validation is paramount to ensure that the evidence produced is reliable, accurate, and admissible in judicial proceedings [68]. This document provides detailed application notes and protocols for establishing these critical validation benchmarks, focusing on the comparative evaluation of tool performance against standardized forensic datasets. The proposed framework is designed to provide researchers and developers with a structured methodology to quantitatively assess tool capabilities, measure progress against objective criteria, and systematically elevate the TRL of forensic software solutions.
The Critical Need for Standardized Benchmarks in Forensic Science
The current digital forensic landscape is marked by a rapid proliferation of tools, each claiming unique capabilities. However, the decision to use a specific tool in casework extends beyond its advertised features; practitioners must be able to answer a series of critical questions, from "What does that tool do?" to "Should I use the tool?" [68]. Without standardized benchmarks, answering these questions becomes a subjective endeavor, introducing significant risks into investigations and potential challenges to evidence in court.
Existing research highlights several key limitations that standardized benchmarking seeks to address:
- Inconsistent Evaluation Conditions: Studies often evaluate tools on different datasets or under varying conditions, making it difficult to soundly quantify their performance [69]. A tool's performance may be inflated due to favorable training or test data rather than its inherent algorithmic superiority.
- Overfitting and Poor Transferability: Many detection methods experience a significant performance decrease when exposed to data with different distributions or unseen manipulation techniques, a critical failure mode for real-world applications [69].
- Insufficient Evaluation Metrics: A narrow focus on metrics like accuracy or AUC fails to provide a comprehensive view of performance. Essential practical considerations such as time/space complexity, robustness to perturbations, and generalization ability are often overlooked [69].
The establishment of standardized benchmarks directly supports TRL advancement by providing the objective, repeatable testing required to move a technology from a laboratory prototype (low TRL) to a proven, court-ready solution (high TRL).
Core Components of a Forensic Validation Benchmark
A comprehensive validation benchmark must consist of several interconnected components, each designed to test a specific aspect of tool performance in a structured and reproducible manner.
Standardized Forensic Datasets
The foundation of any benchmark is a collection of standardized datasets. These datasets should be diverse, representative of real-world evidence, and contain ground-truth information to enable accurate performance measurement.
Table 1: Characteristics of Exemplary Standardized Forensic Datasets
| Dataset Name | Domain | Total Real Samples | Total Fake/Manipulated Samples | Manipulation Methods | Perturbations/Challenges |
|---|---|---|---|---|---|
| Celeb-DF-v2 [69] | Deepfake Detection | 358,790 | 2,116,768 | Autoencoder-based | N/A |
| DeeperForensics-1.0 [69] | Deepfake Detection | 509,128 | 508,944 | Autoencoder-based | 7 types |
| FaceForensics++ [69] | Deepfake Detection | 509,914 | 1,321,408 | Autoencoder, GAN, Graphic-based | N/A |
| DFDC [69] | Deepfake Detection | 5,635,501 | 29,075,744 | 2 Autoencoder, 3 GAN, 1 Graphic-based | 19 types |
| ForgeryNet [69] | Deepfake Detection | 2,848,548 | 1,054,671 | Autoencoder, 2 GAN-based | 36 types |
| Proposed ID Test Set [69] | Deepfake Detection | N/A | N/A | >12 methods | Multiple |
These datasets vary in scale and complexity. For a robust benchmark, it is recommended to use a challenging "Imperceptible and Diverse" (ID) test set, which contains hard samples selected from public and private sources, synthesized by various manipulation approaches and distorted by common perturbations to better simulate a realistic media environment [69].
Quantitative Performance Metrics
A multi-faceted set of metrics is essential to evaluate tools from different perspectives. Relying on a single metric provides an incomplete picture of a tool's practical utility.
Table 2: Key Performance Metrics for Forensic Tool Evaluation
| Metric Category | Specific Metrics | Description and Interpretation |
|---|---|---|
| Detection Ability | AUC (Area Under ROC Curve), Accuracy | Measures the core ability to correctly identify forensic artifacts or manipulations. AUC is threshold-independent and often more robust. |
| Generalization | Cross-Dataset Performance | Evaluates performance when a model trained on one dataset (e.g., FaceForensics++) is tested on another (e.g., DFDC). Indicates robustness to domain shift. |
| Robustness | Performance under Perturbations | Measures the drop in performance when test data is subjected to common distortions like compression, noise, or blurring. |
| Efficiency | Inference Time, Memory Consumption | Critical for practical application, especially when dealing with large-scale data (e.g., terabytes of drive images or hours of video) [69]. |
| Practicability | Feature-based Accuracy [70] | In contexts like browser forensics, measures the tool's ability to retrieve a comprehensive set of evidentiary artifacts (e.g., history, cookies, downloads). |
Experimental Protocols
A standardized benchmark must define clear experimental protocols to ensure fair and repeatable comparisons. Key protocols include:
- Intra- and Inter-Dataset Evaluation: Models should be trained and tested on splits of the same dataset (intra) and also tested on completely held-out datasets (inter) to rigorously assess generalization [69].
- Uniform Training Data: To ensure a fair comparison of algorithms, all tools or models should be (re-)trained on the same dataset, rather than using pre-trained models from various sources, which confounds algorithm quality with training data advantage [69].
- Statistical Significance: Results should be reported over multiple runs to account for variability, and claims of superiority should be supported by statistical testing.
Application Note: A Sample Benchmarking Workflow
This section outlines a detailed, step-by-step protocol for executing a tool validation benchmark, using the deepfake detection domain as a primary example. The workflow is generalizable to other forensic sub-fields.
Figure 1: A standardized workflow for forensic tool validation benchmarking.
Protocol 1: Comprehensive Tool Performance Benchmarking
Objective: To fairly compare the performance of multiple forensic tools or algorithms against a standardized dataset suite using a comprehensive set of metrics.
Materials and Reagents:
Table 3: Research Reagent Solutions for Benchmarking
| Item Name | Function / Relevance | Exemplars / Specifications |
|---|---|---|
| Standardized Datasets | Provides the ground-truthed, representative data required for objective evaluation. | FaceForensics++ [69], DFDC [69], Custom ID Test Set [69] |
| Computational Environment | Ensures consistent and reproducible runtime performance measurements. | Hardware: Intel i7 CPU, 16GB RAM. Software: Windows 10 64-bit, Python. [71] |
| Evaluation Framework | The software backbone for running experiments, calculating metrics, and logging results. | Custom Python scripts, OpenSource forensic platforms. |
| Tool/Library Hash Sets | Used for validating file integrity and identifying known files (e.g., CSAM). | Project VIC (VICS), CAID [71] |
Procedure:
- Define Benchmark Scope: Clearly articulate the forensic task being evaluated (e.g., deepfake detection, browser artifact recovery). Select the standardized datasets (from Table 1) that are appropriate for the task. For a rigorous test, include a challenging set with diverse manipulations and perturbations [69].
- Select Tools and Algorithms: Choose a representative set of state-of-the-art tools or algorithms for evaluation. This may include commercial tools (e.g., OS Forensic [70]), open-source algorithms, and novel research models.
- Implement Uniform Training: For machine learning-based tools, re-implement and (re-)train all models on an identical, shared training dataset. This critical step isolates the performance contribution of the algorithm from that of its training data [69].
- Execute Evaluation Runs:
- For each tool and each test dataset, run the inference or analysis process.
- For intra-class evaluation, test on a held-out split of the training dataset.
- For inter-class evaluation (generalization test), test on completely unseen datasets.
- Record all results, including raw predictions, inference times, and memory usage.
- Calculate Performance Metrics: For each tool-dataset pair, compute the full suite of metrics outlined in Table 2 (e.g., AUC, Accuracy, Cross-Dataset Performance, Inference Time).
- Analyze and Compare Results:
- Synthesize quantitative data into structured tables for direct comparison.
- Identify trade-offs (e.g., a tool with high accuracy but low speed).
- Assess the TRL based on performance; consistent high performance across diverse, challenging datasets indicates a higher TRL.
- Report Findings: Generate a comprehensive report detailing the methodology, results, and conclusions. The report should enable other researchers to replicate the benchmark and practitioners to make informed tool selection decisions.
Protocol 2: Evaluating Generalization and Robustness
Objective: To specifically assess a tool's ability to generalize to unseen data and its robustness against common data perturbations.
Procedure:
- Cross-Dataset Testing: Train tools on one primary dataset (e.g., FaceForensics++). Subsequently, evaluate the trained models on one or more completely different datasets (e.g., Celeb-DF-v2, DFDC) without any fine-tuning. The drop in performance (e.g., AUC reduction) is a key indicator of generalization capability [69].
- Perturbation Analysis: Take a clean, validated test set and systematically apply a series of realistic perturbations, such as:
- JPEG compression at various quality levels
- Addition of Gaussian noise
- Resolution scaling
- Brightness/contrast adjustments Measure the tool's performance on these perturbed datasets. A robust tool will show minimal performance degradation.
Case Studies in Benchmarking
Case Study 1: Deepfake Detection
A comprehensive study implemented 11 popular deepfake detection approaches and evaluated them under uniform conditions on a collected dataset with samples from over 12 manipulation methods [69]. The study performed 644 experiments, training 92 models.
Key Findings:
- Significant Performance Drop: The detection ability of all approaches dropped significantly on a realistic and challenging dataset, indicating that performance fails to meet the requirements for real-world applications [69].
- No Significant Overall Difference: Under strictly uniform evaluation conditions, the overall performance of popular methods showed no significant difference, contrary to claims in individual studies that did not control for training data [69].
- Trade-offs are Inevitable: No single method showed comprehensive superiority. For instance, Multiple-attention achieved the best AUC but had high time complexity, while Patch-based methods offered a good balance of detection ability and low inference time [69].
This case underscores the importance of fair benchmarks; without them, perceived performance differences may be illusory.
Case Study 2: Browser History Forensic Tools
A performance evaluation of four forensic tools (Browser History Examiner (BHE), Browser History View (BHV), RS Browser, and OS Forensic) analyzed 39 features across five web browsers [70].
Key Findings:
- Wide Performance Variance: The accuracy of the tools in retrieving comprehensive browser data varied significantly: OS Forensic (89.74%), RS Browser (71.79%), BHE (61.54%), and BHV (33.33%) [70].
- Feature-Based Accuracy is Critical: The benchmark used a feature-based accuracy metric, which is a practical measure of a tool's ability to recover a wide array of digital evidence, directly impacting its utility in an investigation [70].
This case demonstrates how benchmarking can provide objective data to guide practitioners in selecting the most effective tool for a specific task.
Integration with the TRL Assessment Framework
The validation benchmarks described herein are not merely performance snapshots; they are active instruments for measuring and elevating a technology's TRL within the forensic software development lifecycle.
Figure 2: The role of progressive benchmarking in advancing Technology Readiness Levels (TRL).
- TRL 1-3 (Basic/Applied Research): Initial benchmarks focus on proving the core concept works on small, controlled lab-scale datasets.
- TRL 4-6 (Technology Development & Demonstration): Tools are subjected to the full benchmarking protocol (Protocol 1). Success here—demonstrating strong performance and generalization on standardized datasets—validates the technology in a relevant environment and elevates it to TRL 6.
- TRL 7-9 (System Demonstration & Deployment): The highest TRLs are achieved when a tool proves its efficacy in an operational setting. This is measured by benchmarking against the most challenging, realistic datasets (e.g., the ID test set) and demonstrating robust performance under real-world conditions, such as those simulated by the DFDC or ForgeryNet datasets [69]. A tool like OS Forensic, which demonstrated high accuracy in a practical browser analysis task, exhibits characteristics of a high-TRL solution [70].
The establishment of rigorous, standardized validation benchmarks is a cornerstone of credible forensic science and a critical enabler for the systematic integration of TRL assessment into software development. By adopting the protocols and frameworks outlined in this document, researchers and developers can move beyond anecdotal evidence and subjective tool comparisons. The consistent application of fair-minded, comprehensive, and practical evaluation, using diverse datasets and multi-faceted metrics, provides the objective evidence needed to gauge true progress, build court-defensible tools, and ultimately enhance the reliability and trustworthiness of digital evidence in the judicial system.
Application Notes: Integrating Legal Admissibility into the Forensic SDLC
For researchers and developers in digital forensics, the transition from a functional tool to one whose evidence is admissible in court presents a significant challenge. The Daubert Standard, a legal benchmark for the admissibility of expert testimony and scientific evidence in federal U.S. courts, demands a rigorous, methodical approach to development [72]. This framework outlines how to integrate these legal requirements into a Technology Readiness Level (TRL)-based Software Development Life Cycle (SDLC), ensuring that every development artifact contributes to demonstrating the tool's scientific validity and reliability.
The core challenge is that courts must assess the reliability and relevance of expert testimony, which includes evidence generated by forensic software [72]. The 1993 Supreme Court case Daubert v. Merrell Dow Pharmaceuticals established the judge as a "gatekeeper" and provided five key factors for assessing evidence [72] [73]:
- Testability: Whether the theory or technique can be (and has been) tested.
- Peer Review: Whether it has been subjected to peer review and publication.
- Error Rate: The known or potential rate of error.
- Standards: The existence and maintenance of standards controlling its operation.
- General Acceptance: Whether it is generally accepted in the relevant scientific community [72] [73].
Later rulings in General Electric Co. v. Joiner and Kumho Tire Co. v. Carmichael clarified that the trial judge's discretion is broad and that the standard applies to all expert testimony, not just "scientific" knowledge [72] [74]. This legal landscape directly informs the following protocols, designed to produce the necessary evidence for withstanding a Daubert challenge—a motion to exclude expert testimony [72].
Experimental Protocols for Daubert-Aligned Tool Validation
A rigorous, evidence-based validation methodology is fundamental for proving a tool's reliability. The following protocol, adapted from contemporary research, provides a template for generating quantitative data on tool performance.
Comparative Tool Validation Protocol
1. Objective: To quantitatively compare the performance of a forensic tool (Device Under Test - DUT) against a commercially accepted reference tool across core forensic functions, establishing known error rates and reliability.
2. Experimental Design & Materials:
- Test Environment: Two identical, forensically sterile workstations with controlled operating systems [75].
- Reference Materials: A pre-configured forensic sample disk image containing:
- Preserved original data structures (e.g., NTFS, EXT4).
- A catalog of known deleted files for recovery.
- Embedded target artifacts (e.g., specific keywords, database entries).
- Tool Selection:
3. Methodology: Each experiment is performed in triplicate to establish repeatability metrics [75].
- Experiment A: Data Preservation & Collection
- Procedure: Mount the control disk image. Use both the reference tool and the DUT to create a forensic image, generating hash values (MD5, SHA-1) for the output.
- Data Collection: Record the hash values from both tools and verify against the known-good hash of the control image. Document the time taken for the imaging process.
- Experiment B: Data Carving & File Recovery
- Procedure: Use both tools to perform data carving on the disk image to recover the set of known deleted files.
- Data Collection: Count the total number of files successfully recovered by each tool. Differentiate between intact files and corrupted/unreadable files.
- Experiment C: Targeted Artifact Search
- Procedure: Execute a targeted search for the embedded artifacts using both tools' search functionalities (e.g., keyword search, file signature analysis).
- Data Collection: Record the number of true positives (correctly identified artifacts), false positives (incorrectly flagged data), and false negatives (missed artifacts).
4. Data Analysis:
- Error Rate Calculation: Calculate the error rate for each experiment. For example, in Experiment C, the false positive rate is (False Positives / (True Positives + False Positives)) * 100.
- Statistical Comparison: Use statistical tests (e.g., t-test) to compare the performance metrics (e.g., number of files recovered, accuracy) between the DUT and the reference tool. A lack of significant difference demonstrates comparable reliability [75] [12].
The workflow for this validation protocol is systematic and iterative, as shown in the following diagram.
Validation Workflow for Daubert Compliance
Quantitative Results from Comparative Studies
The following table summarizes typical quantitative outcomes from the aforementioned experimental protocol, providing a benchmark for expected performance data required for a Daubert defense.
Table 1: Sample Quantitative Results from Forensic Tool Validation Experiments [75] [12]
| Experiment | Performance Metric | Commercial Tool (Reference) | Open-Source DUT | Statistical Significance (p-value) |
|---|---|---|---|---|
| A: Data Preservation | Hash Value Accuracy (SHA-1 match) | 100% | 100% | N/A |
| Imaging Process Time (minutes) | 24.5 ± 1.2 | 26.8 ± 1.5 | > 0.05 | |
| B: Data Carving | Files Recovered (Intact) | 145 ± 3 | 142 ± 4 | > 0.05 |
| Files Recovered (Corrupted) | 5 ± 1 | 7 ± 2 | > 0.05 | |
| C: Artifact Search | True Positive Rate (TPR) | 98.5% | 97.8% | > 0.05 |
| False Positive Rate (FPR) | 1.2% | 1.5% | > 0.05 |
The Scientist's Toolkit: Research Reagent Solutions
In the context of digital forensics research, "research reagents" refer to the essential software, hardware, and data resources required to conduct valid and repeatable experiments.
Table 2: Essential Digital Forensics Research Materials
| Item | Function / Rationale | Exemplars |
|---|---|---|
| Reference Disk Images | Provides a ground-truth, reproducible dataset for testing tool accuracy in data extraction, carving, and search. Critical for establishing error rates. | NIST CFTT Forensic Image Database, Custom-built images with known content. |
| Commercial Reference Tools | Acts as a benchmark for performance and output quality. Demonstrates that the DUT meets or exceeds the capabilities of legally accepted solutions. | FTK (AccessData), EnCase (Guidance Software), Forensic MagiCube [75]. |
| Open-Source DUTs | The tool undergoing validation. Its transparency allows for peer review of its underlying methodology, a key Daubert factor. | Autopsy, The Sleuth Kit, ProDiscover Basic [75] [12]. |
| Forensic Workstations | A controlled, consistent hardware environment to ensure that performance metrics are comparable and not influenced by external variables. | Identically configured systems with hardware write-blockers. |
| Testing Standards | Provides a formal methodology for testing, ensuring experiments are repeatable and the results are scientifically sound. | NIST Computer Forensics Tool Testing (CFTT) standards [75]. |
An Integrated Framework for Daubert-Compliant Development
Moving beyond isolated validation, achieving legal admissibility requires a holistic framework integrated across the entire SDLC. The following diagram illustrates a three-phase framework that aligns basic forensic processes with rigorous validation and readiness planning.
Integrated Framework for Daubert Compliance
Phase 1: Basic Forensic Process (SDLC Integration) This phase involves building foundational forensic capabilities directly into the software itself, as part of the development process [14].
- Planning & Design: Define incident response protocols and build in logging, monitoring, and immutable audit trails from the outset [14].
- Development & Testing: Treat security and traceability as core requirements. Modularize error handling and embed forensic markers. Testing must include validation of forensic capture to confirm every critical action leaves a reliable trail [14].
- Deployment & Maintenance: Use deployment pipelines to automate the bundling of reference builds and configuration snapshots. In maintenance, employ continuous monitoring and disciplined patch tracking to close gaps [14].
Phase 2: Result Validation (Daubert Evidence Generation) This phase directly maps development and testing artifacts to the five Daubert factors, creating the evidence required for legal defense [75].
- Testability: The comparative validation protocol (Section 2.1) provides direct evidence that the tool's functions can be and have been tested [72] [75].
- Peer Review: Publishing the tool's methodology and validation results in scientific journals subjects the techniques to scrutiny, fulfilling this factor [72] [75].
- Known Error Rate: The quantitative data generated from experiments (Table 1) establishes a known or potential error rate for the tool's techniques [72] [75].
- Existence of Standards: Adhering to international standards like ISO/IEC 27037:2012 for evidence handling and using NIST CFTT methodologies demonstrates the use of maintained standards [75].
- General Acceptance: Widespread use of the tool by law enforcement or adoption in other studies contributes to general acceptance. A robust validation framework accelerates this process [72] [75].
Phase 3: Digital Forensic Readiness This is the organizational posture that ensures an entity is prepared to use its digital assets effectively as evidence. It involves proactive planning for evidence collection and preservation in the event of an incident, ensuring that data generated by systems is collected in a manner that is legally admissible [14].
Protocol for a Daubert Challenge Defense Dossier
When facing a legal challenge, a pre-assembled dossier of evidence is critical. This protocol details the compilation of that dossier.
1. Objective: To create a comprehensive and pre-emptive evidence package that demonstrates a forensic tool's adherence to the Daubert standard, ready for submission in response to a Daubert challenge.
2. Dossier Components:
- Section 1: Tool & Methodology Description
- A white paper detailing the tool's underlying scientific principles (e.g., file system theory, data carving algorithms).
- Detailed documentation of the tool's operational standards and controls.
- Section 2: Evidence of Empirical Testing
- Full reports from the Comparative Tool Validation Protocol (Section 2.1), including all raw data and statistical analyses.
- Documentation of any testing in accordance with NIST CFTT or other recognized standards.
- Section 3: Evidence of Peer Review and Acceptance
- Copies of peer-reviewed publications that discuss the tool's methodology or present validation studies.
- Testimonials or case studies from independent, reputable experts or organizations in the digital forensics community.
- A list of other legal proceedings where the tool's evidence has been admitted.
- Section 4: Documentation of SDLC & Quality Controls
- Artifacts from the SDLC demonstrating rigorous development practices: version control histories, code review logs, and quality assurance test results.
- Documentation of the chain of custody procedures and integrity verification methods (e.g., hashing) built into the tool's workflow.
By systematically implementing these application notes and experimental protocols, researchers and developers can transform digital forensic tools from merely functional to legally robust, successfully overcoming the admissibility hurdle.
This application note provides a detailed analysis of two critical domains in digital forensics—cloud forensics and deepfake detection—through the framework of Technology Readiness Levels (TRL). The TRL scale, originally developed by NASA, is a systematic metric that assesses the maturity of a particular technology, ranging from 1 (basic principles observed) to 9 (system proven in operational environment). Integrating TRL assessment into the Forensic Software Development Lifecycle (SDLC) provides researchers and development teams with a standardized method for evaluating project progression, identifying maturation bottlenecks, and making data-driven decisions for resource allocation [14] [76]. This structured approach is vital for transforming theoretical research (low TRL) into field-deployable, reliable tools (high TRL) that meet the evolving demands of modern digital investigations. The following analysis quantitatively evaluates the current state of these technologies and provides experimentally validated protocols to advance their TRL status.
Cloud Forensics Tools TRL Assessment
Market Context and Technical Challenges
The global cloud digital forensics market, valued at approximately $11.21 billion in 2024, is projected to experience a compound annual growth rate (CAGR) of ≈16.53%, reaching an estimated $36.9 billion by 2031 [77]. This rapid growth is driven by accelerated cloud adoption; over 60% of newly generated enterprise data is expected to reside in cloud environments by 2025 [16]. However, this expansion introduces significant forensic complexities, including data fragmentation across geographically dispersed servers, legal jurisdictional conflicts, and the inherent volatility of cloud data, which can disappear within minutes due to automated scaling and updates [78] [16] [77]. These challenges necessitate specialized tools and methodologies beyond traditional digital forensics.
Quantitative TRL Assessment of Cloud Forensic Tools
The following table summarizes the TRL assessment for current cloud forensic tools and platforms based on their operational capabilities and market deployment.
Table 1: TRL Assessment of Cloud Forensics Tools and Platforms
| Technology Category | Example Platforms | Key Capabilities | Current TRL | Key Limitations |
|---|---|---|---|---|
| Cloud-Native Security Platforms | SentinelOne Singularity Cloud Native Security, Singularity XDR [78] | Agentless onboarding, real-time compliance scoring (CIS, MITRE, NIST), IaC scanning for Terraform/CloudFormation, Kubernetes security from build to production. | 9 (System Proven) | Platform-specific data schemas can complicate cross-provider correlation. |
| AI-Driven Forensic Automation | Innefu’s Argus, Intelelinx [79] | Automated evidence triage, cross-data correlation (telecom + device artifacts), fusion-center workflows for hidden network discovery. | 8 (System Complete) | "Black box" AI models can undermine courtroom credibility; training data bias may amplify errors. |
| Cloud Workload Protection | SentinelOne Singularity Cloud Workload Security [78] | AI-powered runtime protection for VMs/containers, deep workload telemetry, stable eBPF agent, prevention of container drift. | 9 (System Proven) | Primarily focused on runtime; limited forensic data for pre-execution attack stages. |
Experimental Protocol for Validating Cloud Forensic Tools
This protocol provides a methodology for quantitatively evaluating the efficacy of cloud forensic tools, thereby establishing a baseline for their TRL.
Objective: To measure the performance of a cloud forensic tool in detecting, acquiring, and preserving evidence from a simulated security incident in a multi-cloud environment.
Materials & Reagents:
- Testbed Platforms: AWS, Microsoft Azure, and Google Cloud Platform accounts.
- Tool Under Test (TUT): The cloud forensic platform being evaluated (e.g., SentinelOne, Innefu Argus).
- Data Generation Tools: Scripts to simulate user activity, API calls, and data transactions.
- Evidence Preservation System: A secure, forensically sound storage solution with hash-checking capabilities.
- Analysis Workstation: A dedicated system with network access to all cloud platforms and the TUT.
Methodology:
- Baseline Configuration: Configure the TUT according to vendor specifications across all three cloud platforms. Document all settings.
- Artifact Seeding: Execute a pre-defined set of activities across the cloud environments, including:
- Unauthorized IAM role creation.
- S3/GCS/Blob Storage data exfiltration.
- Spin-up of cryptocurrency mining instances.
- Log deletion and trace obfuscation attempts.
- Incident Triggering: Simulate a breach by executing a script that mimics attacker behaviors, such as lateral movement and data encryption.
- Evidence Acquisition & Preservation:
- Initiate the TUT's evidence collection process.
- Simultaneously, perform a manual, provider-native log collection as a control.
- Generate SHA-256 hashes for all collected evidence files.
- Analysis & Timeline Reconstruction:
- Use the TUT to analyze the collected data and generate an incident timeline.
- Manually reconstruct a timeline using the control data.
- Metrics Measurement:
- Data Acquisition Completeness: Percentage of seeded artifacts successfully collected.
- Evidence Integrity: Verification that hashes remain unchanged throughout the process.
- Time to Resolution: Total time from incident trigger to complete timeline reconstruction.
- Analyst Workload: Person-hours required for the manual vs. TUT-assisted reconstruction.
Workflow Diagram:
Cloud Forensic Tool Validation Workflow
Deepfake Detection Tools TRL Assessment
Threat Landscape and Evolving Challenges
Deepfake technology represents a rapidly advancing threat vector, with recent attacks demonstrating alarming sophistication and financial impact. Cases include a $622,000 Zoom call scam using real-time face-swapping and a €220,000 loss by a UK firm from a voice clone of its CEO, created from just three seconds of audio [80]. The technology is becoming more accessible; open-source tools have democratized creation, and a survey indicates that while 57% of people believe they can spot deepfakes, only 24% can actually identify high-quality synthetic media [80]. This creates a critical detection gap that advanced tools must bridge.
Quantitative TRL Assessment of Deepfake Detection Tools
The following table summarizes the TRL assessment for current deepfake detection methodologies.
Table 2: TRL Assessment of Deepfake Detection Methodologies
| Detection Methodology | Example Techniques | Reported Efficacy | Current TRL | Key Limitations |
|---|---|---|---|---|
| AI-Based Media Authentication | Deepfake audio detection algorithms (NIST, 2024) [16] | Up to 92% accuracy on known datasets. | 7 (Prototype Demonstration) | Performance degrades on novel, unseen generative models; requires continuous retraining. |
| Behavioral & Liveness Detection | Eye blink analysis, lip sync inconsistency, unnatural head movements detection [80] | Effective against low-mid sophistication fakes in controlled studies. | 6 (Technology Demonstration) | Struggles with high-fidelity, real-time deepfakes; can be bypassed by advanced generators. |
| Multi-Modal Correlation Engines | Fusion of audio waveform analysis, video facial action units, and text sentiment analysis. | Emerging technology; no standardized benchmarks yet. | 4 (Component Validation) | High computational cost; lack of large-scale, labeled multi-modal datasets for training. |
Experimental Protocol for Deepfake Detection Tool Validation
This protocol is designed to rigorously test the performance of deepfake detection tools against a graded suite of synthetic media.
Objective: To quantitatively evaluate the detection accuracy and false-positive rate of a deepfake detection tool across multiple media types and attack sophistication levels.
Materials & Reagents:
- Deepfake Dataset: A curated library containing:
- Video Deepfakes: Ranging from low-quality face-swaps to high-fidelity, real-time synthesized video.
- Audio Deepfakes: Clips from open-source tools and professional-grade voice generators.
- Genuine Media: A verified set of authentic video and audio recordings for false-positive testing.
- Tool Under Test (TUT): The deepfake detection software or API.
- Analysis Server: A high-performance computing unit to run the TUT.
- Metrics Dashboard: Custom software to log results, calculate accuracy, precision, recall, and F1-scores.
Methodology:
- Dataset Curation & Labeling: Assemble and label the deepfake dataset. Include various creation methods (e.g., GANs, Diffusion Models) and perturbation levels (e.g., compression, noise).
- Tool Configuration: Calibrate the TUT as per its operational guidelines.
- Blinded Testing: Submit each item from the dataset to the TUT in a blinded fashion, recording the tool's classification (real/fake) and confidence score.
- Multi-Modal Testing:
- Test video-only, audio-only, and combined audio-video clips.
- For audio-video clips, evaluate the tool's ability to detect inconsistencies between the modalities.
- Adversarial Robustness Testing: Expose the TUT to adversarial examples—deepfakes specifically crafted to evade detection.
- Performance Benchmarking:
- Calculate accuracy, precision, recall, and F1-score.
- Plot Receiver Operating Characteristic (ROC) curves.
- Measure computational latency and throughput.
Workflow Diagram:
Deepfake Detection Tool Validation Workflow
Integrated TRL Advancement Protocols
SDLC Integration Protocol for Forensic Tool Development
Integrating TRL tracking into the Forensic SDLC ensures that security, traceability, and evidence-handling requirements are embedded from the planning phase through maintenance [14].
Objective: To provide a phase-gated process for developing forensic tools where advancement to each subsequent SDLC phase is contingent upon achieving specific TRL criteria.
Protocol:
- Planning & Analysis (Target TRL 2-3):
- Activities: Define forensic requirements (e.g., data types, logging standards), conduct threat modeling, establish chain-of-custody protocols.
- TRL Gate: Advance to Design only upon formal documentation of requirements and a feasibility analysis demonstrating basic principles.
- Architecture Design (Target TRL 4):
- Activities: Design system architecture with immutable audit trails, select algorithms for forensic analysis, specify evidence preservation methods (e.g., hashing).
- TRL Gate: Advance to Development after successful validation of critical components in a lab environment.
- Development (Target TRL 5-6):
- Activities: Code with embedded forensic markers, implement modular error handling, integrate automated static security analysis.
- TRL Gate: Advance to Testing upon integration of components into a prototype that can be tested in a simulated forensic environment.
- Testing & QA (Target TRL 7):
- Activities: Execute the experimental protocols defined in Sections 2.3 and 3.3 in a simulated operational environment. Validate forensic capture and evidence integrity.
- TRL Gate: Advance to Deployment after the prototype successfully passes all testing protocols and demonstrates reliable performance.
- Deployment & Maintenance (Target TRL 8-9):
- Activities: Deploy tool in a pilot operational setting (e.g., a SOC). Implement continuous monitoring and anomaly detection.
- TRL Gate: Achieve TRL 9 after successful long-term operation in the real environment, with documented effectiveness in actual forensic investigations.
Workflow Diagram:
Forensic SDLC with TRL Gates
The Scientist's Toolkit: Essential Research Reagents
This table catalogs the key materials, tools, and datasets required for conducting experiments and advancing the TRL in cloud forensics and deepfake detection.
Table 3: Essential Research Reagents for Digital Forensics R&D
| Reagent Category | Specific Examples | Function in R&D |
|---|---|---|
| Cloud Forensic Platforms | SentinelOne Singularity CWS/CNS, Innefu Argus [79] [78] | Provides the core platform for testing automated evidence collection, threat detection, and compliance reporting capabilities in cloud environments. |
| Deepfake Detection APIs | Tools validated per NIST standards (e.g., for 92% accuracy audio detection) [16] | Serves as a benchmark or component for testing and developing new multi-modal detection algorithms. |
| Curated Deepfake Datasets | Video and audio libraries with graded sophistication levels, including adversarial examples. | Essential for training machine learning models and conducting blinded performance evaluations of detection tools. |
| Multi-Cloud Testbeds | Configured accounts on AWS, Azure, GCP with orchestrated penetration testing tools. | Creates a realistic, controlled environment for simulating cloud attacks and validating forensic tool acquisition and analysis. |
| Forensic Data Corpora | Anonymized real-world evidence from cloud breaches, mobile devices, and network intrusions. | Provides ground-truthed data for validating tool accuracy and ensuring court-admissible evidence handling. |
The integration of robust technology maturity assessments into the forensic software development lifecycle (SDLC) is critical for ensuring the reliability, validity, and admissibility of digital evidence in legal proceedings. Technology Readiness Levels (TRL) provide a systematic framework for evaluating the developmental stage of forensic tools, while alternative models like the Capability Maturity Model (CMM) focus on organizational processes. This article establishes a comparative framework for TRL and alternative maturity models, contextualized within forensic tool development. It includes structured protocols for implementation, visualization of workflows, and a toolkit for researchers and forensic scientists to enhance methodological rigor in both academic and applied settings [63] [81].
Maturity Models: A Comparative Analysis
Maturity models are essential for assessing the progression and reliability of technologies and processes. Below, we compare TRL with other prominent models, highlighting their focus, application, and relevance to forensic tool development.
Table 1: Comparative Analysis of Technology Maturity Models
| Model | Primary Focus | Scale Structure | Ideal Application Context | Key Forensic Relevance |
|---|---|---|---|---|
| Technology Readiness Levels (TRL) | Maturity of a specific technology or tool | 1–9 (Basic Research to Deployment) | High-risk, regulated environments (e.g., forensic instrumentation) [81] | Provides evidence of validation for courtroom admissibility standards (e.g., Daubert) [63] |
| Capability Maturity Model (CMM) | Maturity of organizational development processes | 1–5 (Initial to Optimizing) | Organizational workflow improvement (e.g., lab QA processes) [81] | Enhances standardization and reproducibility in forensic lab operations [82] |
| Minimum Viable Product (MVP) | Market validation via rapid user feedback | Functional product iterations | Low-risk, commercial software development [81] | Limited use due to stringent legal reliability requirements [63] |
| Lean Startup | Business hypothesis-driven experimentation | Build-Measure-Learn cycles | Early-stage product-market fit validation [81] | Less applicable to regulated forensic tool development |
Key Comparative Insights:
- TRL is paramount for tools requiring demonstrated scientific validity under legal standards (e.g., Daubert or Frye in the U.S., Mohan in Canada), which demand known error rates and peer-reviewed validation [63].
- CMM complements TRL by ensuring that the organizational processes (e.g., ISO/IEC 17025 for forensic labs) surrounding tool usage are mature, reproducible, and auditable [82] [83].
- MVP and Lean Startup are generally less suitable for core forensic tools due to the imperative for pre-deployment validation and minimal post-release uncertainty [81].
Experimental Protocols for Maturity Assessment
Protocol for TRL Assessment of a Forensic Tool
Objective: Systematically evaluate a forensic tool (e.g., a comprehensive two-dimensional gas chromatography (GC×GC) system for drug analysis) against the 9-level TRL scale [63].
Workflow:
- TRL 1–3 (Basic Research):
- Conduct laboratory experiments to validate fundamental principles (e.g., separation efficiency of GC×GC for novel illicit drugs).
- Publish findings in peer-reviewed journals (e.g., Journal of Separation Science) [63].
TRL 4–5 (Lab Validation):
- Integrate the GC×GC system with a mass spectrometer (MS) in a controlled lab environment.
- Test the integrated system against certified reference materials and perform repeatability studies.
TRL 6–7 (Prototyping & Field Testing):
- Deploy a prototype in a operational forensic lab (e.g., for casework on controlled substances).
- Document performance metrics (e.g., false-positive/negative rates, analysis time) under real-world conditions [63].
TRL 8–9 (System Complete & Deployment):
- Finalize the tool for routine casework.
- Execute intra- and inter-laboratory validation studies to establish reproducibility and error rates, fulfilling Daubert criteria [63].
Deliverables: A TRL assessment report, including peer-reviewed publications, lab/field test data, and validation certificates.
Protocol for CMM Integration in a Forensic Lab
Objective: Achieve CMM Level 3 (Defined) for forensic software development processes [82] [81].
Workflow:
- Process Definition:
Training & Implementation:
Monitoring & Optimization:
Deliverables: Defined SOPs, training records, audit reports, and a documented process improvement plan.
Visualization of Maturity Integration Workflow
The following diagram illustrates the integration of TRL and CMM within a secure SDLC for forensic tool development.
Diagram 1: Integration of TRL and CMM within a Secure SDLC for Forensic Tools
The Scientist's Toolkit: Essential Reagents & Materials
Table 2: Key Research Reagent Solutions for Forensic Tool Development
| Reagent/Material | Function/Application | Example in Forensic Context |
|---|---|---|
| Static Application Security Testing (SAST) Tools | Analyzes source code for vulnerabilities without executing the program [84] [85] | Scanning a digital forensics tool's codebase for potential buffer overflow vulnerabilities. |
| Dynamic Application Security Testing (DAST) Tools | Analyzes running applications for vulnerabilities (e.g., API security flaws) [84] [85] | Testing the web interface of a forensic evidence management system for injection flaws. |
| Software Composition Analysis (SCA) Tools | Identifies known vulnerabilities in third-party and open-source libraries [84] [85] | Detecting a vulnerable Log4j component in a forensic image analysis software package. |
| Threat Modeling Frameworks (e.g., STRIDE) | Structured approach to identify and mitigate security threats during design [84] | Modeling threats to a mobile forensics tool to prevent data tampering (integrity violation). |
| Reference Data Sets | High-quality, known data for education, training, and tool testing [86] | Using NIST's forensic reference data sets to validate the accuracy of a new data carving tool. |
| Application Security Posture Management (ASPM) | Centralizes visibility into application security health across the SDLC [84] | Correlating findings from SAST, DAST, and SCA tools in a forensic software factory dashboard. |
A hybrid framework integrating TRL for rigorous, evidence-based tool validation and CMM for mature, reproducible organizational processes provides a robust foundation for managing forensic tool maturity. This approach directly addresses the stringent requirements of legal admissibility standards by ensuring tools are both technically validated and developed within a controlled, high-quality environment. The provided protocols, workflows, and toolkit equip forensic researchers and developers to systematically advance tools from concept to court-admissible deployment, thereby enhancing the reliability and integrity of digital forensic science.
The integration of Technology Readiness Level (TRL) assessment into the forensic software development lifecycle provides a structured framework for evaluating technical maturity, guiding investment, and de-risking the transition from research to operational use [87] [1]. Originally developed by NASA, the TRL framework offers a standardized scale from 1 to 9 to consistently gauge the maturity of a technology, enabling clearer communication among researchers, developers, and funding bodies [1]. For forensic science, particularly in digital forensics and tool development, this model allows for the parallel tracking of technical maturity, cost-effectiveness (ROI), investigator efficiency, and evidence reliability throughout development. This Application Note details protocols for quantifying these critical success metrics at key TRL stages, providing researchers and developers with a standardized approach to validate and demonstrate the value of emerging forensic technologies.
Technology Readiness Levels (TRLs) – Definitions and Forensic Context
The following table outlines the standard TRL definitions and their specific interpretation within the context of forensic software development. This adaptation aligns the general engineering maturity stages with the specific validation and operational needs of forensic tools [87] [1].
Table 1: TRL Definitions for Forensic Software Development
| TRL | General Definition | Forensic Software Development Context |
|---|---|---|
| 1 | Basic principles observed and reported [1] | Initial research on a novel forensic technique (e.g., a new data parsing algorithm). Scientific principles are studied and documented. |
| 2 | Technology concept formulated [1] | Practical application of the research is formulated. A concept for a software tool is proposed to leverage the new technique. |
| 3 | Experimental proof of concept [1] | Critical functions of the proposed software are validated in isolation. A rudimentary script or module proves the core functionality. |
| 4 | Technology validated in lab [1] | Software components are integrated and validated in a laboratory setting. A functional prototype operates on controlled, sample datasets. |
| 5 | Technology validated in relevant environment [1] | The software prototype is tested with forensically relevant data types and environments (e.g., a simulated casework image). |
| 6 | Technology demonstrated in relevant environment [1] [87] | A fully functional prototype of the software is demonstrated in a simulated operational environment, such as a mock digital forensics lab. |
| 7 | System prototype demonstration in operational environment [1] | The software is tested in a real operational environment by a limited set of users, such as in a pilot study with a partner law enforcement agency. |
| 8 | System complete and qualified [1] | The software system is fully developed, tested, and certified for use. It meets all technical and forensic standards (e.g., compliance with ISO 17025). |
| 9 | Actual system proven in operational environment [1] | The software is successfully used in active casework across multiple agencies, with its effectiveness proven through successful case outcomes. |
The progression of a forensic software tool from basic research (TRL 1) to proven operational use (TRL 9) can be visualized as a structured pathway. The following diagram illustrates this developmental logic and the key activities associated with major TRL phases.
Quantitative Metrics for Success
Measuring Return on Investment (ROI)
Calculating ROI for forensic software requires a comprehensive account of both costs and benefits, including direct financial gains and strategic value [88] [89]. A standard ROI formula should be employed:
ROI (%) = [(Total Benefits - Total Costs) / Total Costs] × 100 [88]
For a more security-focused application, Return on Security Investment (ROSI) can be calculated using a risk-based model, such as:
ROSI = (Risk Reduction Value – Cost of Security Controls) ÷ Cost of Security Controls [90]
Table 2: Forensic Software ROI Calculation Framework
| Cost Factors | Description & Measurement | Benefit Factors | Description & Quantification |
|---|---|---|---|
| Direct Costs | Software licensing, hardware, initial implementation [88]. | Fraud & Loss Prevention | Value of prevented incidents. Calculate using reduction in fraud rate × average loss per incident [88]. |
| Hidden Costs | Integration with existing systems, employee training, compliance adjustments [88]. | Operational Efficiency | Time savings × fully burdened personnel cost. Measure reduction in evidence processing time [91]. |
| Ongoing Costs | Licensing/subscription fees, maintenance, dedicated personnel [88]. | Risk Reduction | Calculate reduction in Annual Loss Expectancy (ALE). ALE = Probability of Incident × Financial Impact [90]. |
| Development Costs | R&D, prototyping, and testing efforts amortized over the tool's lifecycle. | Compliance & Legal | Avoided fines and legal fees due to adherence to standards (e.g., ISO 17025). Estimate from historical data or industry benchmarks [88]. |
A critical component of ROI in software development is the cost savings achieved by identifying and fixing defects early in the lifecycle. The following diagram illustrates the exponential cost of remediation as a vulnerability moves through the development and deployment stages, underscoring the value of early detection facilitated by tools and processes integrated at lower TRLs.
Measuring Investigator Efficiency
Investigator efficiency metrics focus on the tool's impact on workflow and productivity. These are crucial for justifying adoption at higher TRLs (7-9).
Table 3: Investigator Efficiency Metrics
| Metric | Measurement Protocol | TRL Focus |
|---|---|---|
| Evidence Processing Time | Measure mean time from evidence intake to analyst review for standardized data sets (e.g., 128GB disk image) before and after tool implementation. | TRL 7-9 |
| Automation Rate | Calculate the percentage of analytical steps that are fully automated versus those requiring manual intervention. Track reduction in manual steps across tool versions. | TRL 4-7 |
| User Error Rate | Record the frequency of operational errors or missteps during defined testing scenarios. Use pre-release beta testing and post-deployment user surveys. | TRL 6-8 |
| Tool Usability (SUS Score) | Administer the System Usability Scale (SUS) to a panel of investigators after a controlled usability study [87]. The SUS provides a standardized score from 0-100. | TRL 6-8 |
Measuring Evidence Reliability Gains
Evidence reliability is paramount in forensic science. Metrics must demonstrate that the tool produces accurate, repeatable, and defensible results.
Table 4: Evidence Reliability Metrics
| Metric | Measurement Protocol | TRL Focus |
|---|---|---|
| Analysis Accuracy | Use ground-truthed reference datasets with known content. Measure rates of true positives, true negatives, false positives, and false negatives. | TRL 4-7 |
| Result Reproducibility | Conduct repeated analyses of the same evidence by different analysts or on different system configurations. Calculate coefficient of variation for quantitative outputs. | TRL 5-8 |
| Data Integrity | Use cryptographic hashing (e.g., SHA-256) to verify that the tool does not alter original evidence throughout the analysis process. Document hash verification passes/fails. | TRL 4-9 |
| Standard Compliance | Audit tool outputs and documentation against relevant standards (e.g., ISO 17025, NIST guidelines). Report the percentage of required criteria met. | TRL 7-9 |
Experimental Protocols for Metric Validation
Protocol: Controlled Processing Efficiency Trial
Objective: To quantitatively compare the evidence processing throughput and analyst time required by a new software tool against a legacy or baseline method.
- Materials:
- Test Tool: The forensic software under evaluation (TRL 6-7).
- Control Tool: Currently deployed legacy software or manual method.
- Standardized Evidence Corpora: A collection of 3-5 forensically created disk/images (e.g., using FTK Imager) of varying sizes (64GB, 128GB, 256GB) and complexities (different file systems, encryption, file types).
- Hardware: Identical, forensically validated workstations for all tests.
- Participants: 5-10 certified digital forensic analysts with comparable expertise.
- Workflow:
- Preparation: Configure all workstations and ensure all tools are properly installed.
- Familiarization: Allow analysts a set time to familiarize themselves with the test tool's interface if needed.
- Assignment & Execution: Assign each evidence corpus to each analyst using both the test and control tools in a randomized, counterbalanced order to mitigate learning effects. Analysts will process the evidence according to a standard operating procedure (SOP) up to a predefined stage (e.g., completion of file system carving).
- Data Collection: Use automated logging and manual timesheets to record the total processing time and any analyst idle/wait time.
- Data Analysis:
- Calculate the mean processing time for each tool across all analysts and evidence sets.
- Perform a paired t-test to determine if the difference in mean processing times is statistically significant (p < 0.05).
- Report the percentage change in processing time: [(Control Time - Test Time) / Control Time] × 100.
Protocol: Accuracy and Reliability Assessment against a Ground-Truthed Dataset
Objective: To validate the analytical accuracy and reproducibility of the software tool.
- Materials:
- Test Tool: The forensic software under evaluation (TRL 5-7).
- Ground-Truthed Dataset: A publicly available, standardized dataset like the CFReDS (Computer Forensic Reference DataSets) from NIST, which contains known artifacts and a detailed manifest.
- Workflow:
- Baseline Establishment: Review the dataset manifest to establish the ground truth (e.g., number of specific file types, presence of specific keywords, existence of particular registry keys).
- Tool Execution: Run the test tool against the dataset using a predefined analysis profile. Repeat the analysis three times to assess intra-tool consistency.
- Result Extraction: Document all findings generated by the tool.
- Comparison: Compare the tool's findings against the ground truth manifest.
- Data Analysis:
- Calculate standard accuracy metrics:
- Precision = True Positives / (True Positives + False Positives)
- Recall = True Positives / (True Positives + False Negatives)
- F1-Score = 2 × (Precision × Recall) / (Precision + Recall)
- Document all false positives and false negatives for further investigation.
- Confirm that all three analysis runs produced identical result sets for reproducible outputs.
- Calculate standard accuracy metrics:
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 5: Key Research Reagents and Materials for Forensic Software Validation
| Item / Solution | Function in Validation | Example Sources / Specifications |
|---|---|---|
| Standardized Forensic Images (CFReDS) | Provides ground-truthed, known datasets for controlled accuracy and reliability testing. | National Institute of Standards and Technology (NIST) |
| Forensic Workstation | A consistent, high-performance hardware platform for conducting efficiency and reliability trials, ensuring results are not hardware-dependent. | Specifications: CPU (≥ 8 cores), RAM (≥ 32GB), fast storage (NVMe SSD), hardware write-blockers. |
| Cryptographic Hashing Tool | Verifies the integrity of evidence before and after processing by the tool under test, ensuring data integrity is maintained. | Software: sha256sum (Linux), Get-FileHash (PowerShell). Standard: NIST FIPS 180-4. |
| System Usability Scale (SUS) | A standardized, reliable questionnaire for measuring the perceived usability of the software tool from the investigator's perspective. | Source: Digital.gov or other usability research repositories. |
| Statistical Analysis Software | Used to perform significance testing on experimental data (e.g., t-tests, ANOVA) and calculate confidence intervals for metrics. | Software: R, Python (with SciPy/StatsModels), SPSS, SAS. |
Conclusion
Integrating TRL assessment into the forensic software development lifecycle is not merely a procedural change but a fundamental shift towards greater reliability, accountability, and efficacy. This structured approach ensures that digital forensic tools evolve from promising prototypes to court-ready solutions capable of confronting modern challenges like AI-generated deepfakes, petabyte-scale cloud data, and sophisticated cybercrimes. The key takeaways underscore that a TRL-driven methodology fosters robust validation, mitigates development risks, and explicitly builds a bridge to legal admissibility. Future directions must focus on creating shared, standardized forensic datasets for testing, developing TRL pathways for AI-specific tools, and fostering closer collaboration between developers, forensic scientists, and the legal community to keep pace with technological change and uphold the integrity of digital evidence.
References
- 1. Technology readiness level [https://en.wikipedia.org/wiki/Technology_readiness_level]
- 2. Technology Readiness Levels (TRL) in Space Projects | TTMS [https://ttms.com/technology-readiness-levels-trl-in-space-projects-explanation-and-significance/]
- 3. Technology Readiness Levels [https://www.nasa.gov/directorates/somd/space-communications-navigation-program/technology-readiness-levels/]
- 4. Eligibility of technology readiness levels (TRL) [https://www.ukri.org/councils/stfc/guidance-for-applicants/check-if-youre-eligible-for-funding/eligibility-of-technology-readiness-levels-trl/]
- 5. An improved forensic-by-design framework for cloud ... [https://www.sciencedirect.com/science/article/abs/pii/S2666281721002407]
- 6. What Is SDLC Security? [https://www.paloaltonetworks.com/cyberpedia/what-is-secure-software-development-lifecycle]
- 7. 7 Challenges Facing Digital Forensics Teams in 2025 [https://agt-technology.com/7-challenges-facing-digital-forensics-teams-in-2025/]
- 8. Digital Evidence Management Challenges in 2025 and Smart ... [https://digitalevidence.ai/blog/digital-evidence-management-challenges-in-2025-and-smart-solutions]
- 9. CEO Lee Reiber: The Digital Forensics Landscape in 2025 [https://www.oxygenforensics.com/en/resources/digital-forensics-trends-2025/]
- 10. Top 6 Trends Shaping Modern DFIR in 2025 [https://belkasoft.com/dfir-trends-2025]
- 11. The admissibility of forensic evidence in US courts and ... [https://www.sciencedirect.com/science/article/abs/pii/S135503062500139X]
- 12. The admissibility of digital evidence from open-source ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12431127/]
- 13. Evaluating the use of AI in digital evidence and courtroom ... [https://www.magnetforensics.com/blog/evaluating-the-use-of-ai-in-digital-evidence-and-courtroom-admissibility/]
- 14. Forensic Readiness in the Software Development Life Cycle [https://hoop.dev/blog/forensic-readiness-in-the-software-development-life-cycle/]
- 15. Digital Forensics Round-Up, November 05 2025 [https://www.forensicfocus.com/news/digital-forensics-round-up-november-05-2025/]
- 16. Key Trends in Digital Forensics 2025: Chanllenges and ... [https://www.salvationdata.com/knowledge/key-trends-in-digital-forensics-for-2025/]
- 17. Digital Forensics in the Cloud: Best Practices for U.S.-Based ... [https://lineal.com/blog/digital-forensics-in-the-cloud-best-practices-for-u-s-based-investigations/]
- 18. Supporting investigators with an agile digital forensics tool [https://www.cameraforensics.com/blog/2024/10/01/supporting-investigators-with-an-agile-digital-forensics-tool/]
- 19. Towards the Integration of Security Practices in Agile ... [https://www.mdpi.com/2076-3417/13/7/4578]
- 20. Why Forensics Belongs in the SDLC [https://hoop.dev/blog/why-forensics-belongs-in-the-sdlc/]
- 21. are software failures symptomatic of systemic problems? [https://www.sciencedirect.com/science/article/abs/pii/S0925753501000868]
- 22. Forensic Science Strategic Research Plan, 2022-2026 ... [https://nij.ojp.gov/topics/articles/forensic-sciences-strategic-research-plan-2022-2026]
- 23. Unlocking the potential of forensic traces: Analytical ... [https://www.sciencedirect.com/science/article/pii/S1355030622000417]
- 24. Forensic Applications of Analytical Chemistry [https://www.labmanager.com/forensic-applications-of-analytical-chemistry-34257]
- 25. Validating and Testing Forensics Software [https://www.geeksforgeeks.org/techtips/validating-and-testing-forensics-software/]
- 26. Digital Forensic Validation: Principles, Methods, and ... [https://www.linkedin.com/pulse/digital-forensic-validation-principles-methods-examples-james-henning-xbjye]
- 27. Digital Forensics Life Cycle [https://www.startertutorials.com/blog/digital-forensics-life-cycle.html]
- 28. What Are the 5 Stages of a Digital Forensics Investigation? [https://ermprotect.com/blog/what-are-the-5-stages-of-a-digital-forensics-investigation/]
- 29. Digital Forensics | NIST [https://www.nist.gov/itl/ssd/digital-forensics]
- 30. Re-imagen: Generating coherent background activity in ... [https://www.sciencedirect.com/science/article/pii/S266628172400129X]
- 31. Technology Readiness Scale for Sustainable Scientific ... [https://cerfacs.fr/coop/trl-scientific-computing]
- 32. What are Technology Readiness Levels (TRL)? - TWI [https://www.twi-global.com/technical-knowledge/faqs/technology-readiness-levels]
- 33. A Guide to Digital Forensics and Cybersecurity Tools (2025) [https://www.forensicscolleges.com/blog/resources/guide-digital-forensics-tools]
- 34. Forensic Logging Requirements [https://www.compact.nl/articles/forensic-logging-requirements/]
- 35. Mapping digital forensic application requirement ... [https://www.sciencedirect.com/science/article/pii/S2665910720300864]
- 36. DevSecOps in 2025: Principles, Technologies & Best ... [https://www.oligo.security/academy/devsecops-in-2025-principles-technologies-best-practices]
- 37. What is DevSecOps? - Developer Security Operations ... [https://aws.amazon.com/what-is/devsecops/]
- 38. 8 DevSecOps Tools for Modern Security-First Teams in 2025 [https://www.strongdm.com/blog/devsecops-tools]
- 39. Key learnings from the 2025 State of DevSecOps study [https://www.datadoghq.com/blog/devsecops-2025-study-learnings/]
- 40. DevSecOps Lifecycle - Understand Key Phases [https://www.practical-devsecops.com/devsecops-life-cycle/?srsltid=AfmBOoo21Qpr83_8eBpds16P_EQJN2jB6iveCazsRLyFdZKmeJhexbvb]
- 41. Top 10 Digital Forensics Tools in 2025: Features, Pros, ... [https://www.cotocus.com/blog/top-10-digital-forensics-tools-in-2025-features-pros-cons-comparison/]
- 42. 10 Useful Digital Forensics Software in 2025 [https://www.salvationdata.com/knowledge/digital-forensics-software/]
- 43. Digital-Forensics-Tools-and-Techniques-in-2025 [https://www.jaroeducation.com/blog/digital-forensics-tools-and-techniques/]
- 44. (FREE) Open-Source Digital Forensics Tools [https://www.linkedin.com/pulse/free-open-source-digital-forensics-tools-empowering-2025-henning-qur4e]
- 45. Validation and verification of computer forensic software ... [https://www.sciencedirect.com/science/article/pii/S1742287609000358]
- 46. AI Bias in Legal Tech: Prevention Guide 2025 [https://www.anytimeai.ai/blog/ai-bias-in-legal-tech-prevention-guide-2025/]
- 47. How to Prevent AI Bias in 2025 [https://nwai.co/how-to-prevent-ai-bias-in-2025/]
- 48. Technology Readiness Level (TRL) - Overview [https://acqnotes.com/acqnote/tasks/technology-readiness-level]
- 49. Digital transformation risk management in forensic science ... [https://www.sciencedirect.com/science/article/pii/S0379073820303480]
- 50. How to Develop Digital Forensic Case Management Software [https://www.zealousys.com/blog/digital-forensic-case-management-software-development/]
- 51. AI Technology Readiness Levels (TRLs): From Concept to ... [https://espiolabs.com/blog/posts/ai-technology-readiness-levels-guide]
- 52. The Top Technical Debt Management Tools 2025 | Zenhub Blog [https://www.zenhub.com/blog-posts/the-top-technical-debt-management-tools-2025]
- 53. Tame tech debt to modernize your business [https://www.mckinsey.com/capabilities/tech-and-ai/our-insights/breaking-technical-debts-vicious-cycle-to-modernize-your-business]
- 54. How to Manage Technical Debt? A Step-by-Step Blueprint ... [https://www.netguru.com/blog/managing-technical-debt]
- 55. How to Manage Technical Debt in 2025 [https://vfunction.com/blog/how-to-manage-technical-debt/]
- 56. 2025 Legacy Code Stats: Costs, Risks & Modernization [https://www.pragmaticcoders.com/resources/legacy-code-stats]
- 57. When Legacy Systems Fail: Lessons from the Federal ... [https://www.isms.online/cyber-security/when-legacy-systems-fail-lessons-from-the-federal-courts-breach/]
- 58. A New Era of Software Forensics with Static Analysis [https://codesecure.com/our-white-papers/a-new-era-of-software-forensics-with-static-analysis/]
- 59. 3 Solutions for Mobile Forensics Challenges in 2025 [https://www.oxygenforensics.com/en/resources/mobile-forensics-challenges-2025-solutions/]
- 60. Technology Readiness Levels (TRLs) in the Era of Co- ... [https://www.mdpi.com/2571-5577/7/2/32]
- 61. IoT Forensics Readiness - influencing factors [https://www.sciencedirect.com/science/article/pii/S2666281724000878]
- 62. Federal Rule of Evidence 707 Approved by Judicial ... [https://www.nelsonmullins.com/insights/blogs/red-zone/news/safeguarding-the-courtroom-from-ai-generated-evidence-federal-rule-of-evidence-707-approved-by-judicial-conference]
- 63. Are We Ready for It? A Review of Forensic Applications and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12012292/]
- 64. AI & the courts: Judicial and legal ethics issues [https://www.ncsc.org/resources-courts/ai-courts-judicial-and-legal-ethics-issues]
- 65. Rule 10.430. Generative artificial intelligence use policies [https://courts.ca.gov/cms/rules/index/ten/rule10_430]
- 66. Algorithmic Transparency [https://medium.com/data-science-collective/algorithmic-transparency-f05e290795e8]
- 67. Minimum Requirements for Testing Tools Used in Digital ... [https://www.swgde.org/documents/published-complete-listing/18-q-001-minimum-requirements-for-testing-tools-used-in-digital-and-multimedia-forensics/]
- 68. Commentary:- Can I use that tool? [https://www.sciencedirect.com/science/article/pii/S2666281724001707]
- 69. Towards Benchmarking and Evaluating Deepfake Detection [https://arxiv.org/html/2203.02115]
- 70. Performance Evaluation of four Different Forensic Tools ... [https://www.isroset.org/journal/IJSRMS/full_paper_view.php?paper_id=3655]
- 71. Triage Investigator: Fast Forensic Evidence Collection & ... [https://www.adfsolutions.com/triage-investigator?srsltid=AfmBOoqK4K_Au1Uy3om4GiZ18nuLjRwh8upj7JeB9Z5MOV6CJLjkVixy]
- 72. The Daubert Standard | Expert Testimony, Admissibility ... [https://www.expertinstitute.com/resources/insights/the-daubert-standard-a-guide-to-motions-hearings-and-rulings/]
- 73. Daubert standard [https://en.wikipedia.org/wiki/Daubert_standard]
- 74. Daubert in Detail: How the Admissibility Standard for ... [https://www.faro.com/en/Resource-Library/Article/Daubert-in-Detail]
- 75. The admissibility of digital evidence from open-source forensic ... [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0331683]
- 76. What Is the Software Development Lifecycle (SDLC)? [https://www.paloaltonetworks.com/cyberpedia/sdlc-software-development-lifecycle]
- 77. Cloud Digital Forensics: Beyond Tools, Techniques, and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10819343/]
- 78. What is Cloud Forensics? Definition, Tools & Best Practices [https://www.sentinelone.com/cybersecurity-101/cloud-security/what-is-cloud-forensics/]
- 79. Digital Forensics: Techniques, Tools, and Real-World ... [https://innefu.com/digital-forensics-techniques-tools-and-real-world-applications-for-police-defence-national-security-agencies/]
- 80. 7 Alarming Deepfake Attacks Examples You Need to Know [https://breacher.ai/blog/deepfake-attack-examples/]
- 81. TRL vs Other Maturity Models: A Comparative Analysis [https://www.mcginniscommawill.com/posts/2025-04-11-trl-vs-other-models/]
- 82. Indicators for maturity and readiness for digital forensic ... [https://www.sciencedirect.com/science/article/abs/pii/S0167404821000614]
- 83. Maturity Models for Testing and Calibration Laboratories [https://www.mdpi.com/2071-1050/15/4/3480]
- 84. What Is a Secure Software Development Lifecycle (SDLC)? [https://www.oligo.security/academy/what-is-a-secure-software-development-lifecycle-sdlc]
- 85. Embedding Security Into Key SDLC Phases [https://www.legitsecurity.com/blog/a-complete-guide-to-the-secure-software-development-lifecycle]
- 86. A Solid Foundation? NIST Publishes Review of Digital ... [https://complexdiscovery.com/a-solid-foundation-nist-publishes-review-of-digital-forensics-methods/]
- 87. Adaptation of the technology readiness levels for impact ... [https://www.sciencedirect.com/science/article/pii/S2405844024059619]
- 88. Calculate Identity Verification Software ROI [https://regulaforensics.com/blog/calculate-identity-verification-software-roi/]
- 89. How to Evaluate the ROI of Your Software Security Program [https://www.blackduck.com/blog/evaluating-roi-software-security.html]
- 90. Threat Modeling ROI: How to Measure the Business Value ... [https://www.securitycompass.com/blog/measuring-threat-modeling-roi/]
- 91. The ROI of Digital Forensics: Demonstrating the Value to ... [https://www.hexordia.com/blog/dfir-workflow]