Forensic Text Comparison Methodology: Principles, Validation, and Applications for Scientific Research
This article provides a comprehensive overview of Forensic Text Comparison (FTC), a scientific discipline for evaluating the strength of textual evidence.
Forensic Text Comparison Methodology: Principles, Validation, and Applications for Scientific Research
Abstract
This article provides a comprehensive overview of Forensic Text Comparison (FTC), a scientific discipline for evaluating the strength of textual evidence. Aimed at researchers and scientists, it explores the foundational Likelihood Ratio framework for quantitative evidence evaluation, details core methodological approaches including feature-based and score-based systems, and addresses critical challenges like topic mismatch and data scarcity. The content emphasizes the necessity of rigorous empirical validation under case-relevant conditions and discusses performance benchmarking, offering insights into the application of these methodologies in scientific and investigative contexts.
The Foundations of Forensic Text Comparison: From Idiolect to the Likelihood Ratio Framework
Defining Forensic Text Comparison and the Concept of Idiolect
Forensic Text Comparison (FTC) is a scientific methodology within forensic linguistics that aims to determine the likelihood that a specific individual authored a particular questioned text. It operates on the core premise that every individual possesses a unique and habitual language pattern, known as an idiolect [1] [2]. This technical guide explores the definition of idiolect, the methodological framework of FTC, and its application, providing researchers and scientists with a detailed overview of the current state of this interdisciplinary field.
The principle that an individual's language use is distinctive provides the theoretical foundation for applying linguistic analysis in legal and investigative contexts [1]. This review is situated within broader research on forensic text comparison methodology, which seeks to develop robust, reliable, and scientifically validated techniques for authorship analysis.
Core Concepts
The Concept of Idiolect
An idiolect is defined as an individual's unique and personal use of language. This encompasses their characteristic choices in vocabulary, grammar, and pronunciation [1] [2]. The term itself is derived from the Greek idio- (meaning 'own, personal') and -lect (from 'dialect') [1]. Crucially, an idiolect is not static; it evolves over a person's lifetime through experiences, such as learning new words or moving to a different geographical region [2].
In essence, while people within a speech community share a mutually intelligible language (a dialect), the specific way each person employs that language is unique to them. Idiolects represent the most granular level of linguistic variation, forming the building blocks of a language, which is itself a composite of mutually intelligible idiolects [1] [2].
Forensic Text Comparison
Forensic Text Comparison (FTC) is the practical application of idiolect theory in forensic science. It involves comparing a text of unknown authorship (the questioned text) with texts of known authorship from a suspect (the reference texts) [1]. The goal is to assess the strength of the evidence for whether the suspect authored the questioned text.
This process is analogous to other forensic comparative sciences. The analysis does not typically rely on a single, conspicuous marker but on a constellation of subtle, often subconscious, linguistic habits. These can include the use of prepositions, punctuation, and other features that an author does not consciously control [2]. FTC provides a framework for quantifying the degree of similarity or difference between these linguistic patterns.
Quantitative Features and Analytical Techniques
Forensic text comparison relies on the computational analysis of quantifiable linguistic features. The table below summarizes the primary categories of features and analytical techniques used in modern FTC research.
Table 1: Key Analytical Features and Techniques in Forensic Text Comparison
| Feature Category | Specific Examples | Analytical Technique | Function/Purpose |
|---|---|---|---|
| Lexico-Grammatical Features | Pronoun frequency, negations, sensory descriptions [3] | Multivariate Kernel Density (MVKD) [4] | Models an author's style as a vector of features for statistical comparison. |
| N-grams | Consecutive sequences of 'n' words or characters [3] [4] | N-gram Models [4] | Captures habitual phrases and syntactic patterns. |
| Psycholinguistic Features | Deception, emotion (anger, fear), subjectivity [3] | NLP Libraries (e.g., Empath) [3] | Infers psychological state and cognitive patterns from language use. |
| Stylistic Features | Overconfidence, hedging, exaggeration [3] | Machine Learning Classifiers (SVM, Random Forest) [3] | Identifies stylistic markers associated with deception or specific author traits. |
The performance of an FTC system is often evaluated using metrics like the log-likelihood-ratio cost (Cllr), which gauges the quality of the computed likelihood ratios [4]. Research indicates that a fusion of multiple techniques (e.g., combining MVKD and N-gram procedures) often yields superior performance and more reliable results than any single method alone [4].
Experimental Protocols in FTC Research
A Protocol for a Fused Forensic Text Comparison System
The following methodology is adapted from a study that demonstrated the efficacy of a fused system for estimating the strength of linguistic evidence using a likelihood ratio (LR) framework [4].
1. Objective: To estimate the strength of evidence for authorship by fusing LRs derived from multiple analytical procedures.
2. Materials and Data:
- Corpus: Chatlog messages from 115 authors.
- Text Samples: For each author, multiple groups of messages are sampled, with the token length progressively increased (e.g., 500, 1000, 1500, and 2500 tokens) to test the effect of data quantity.
3. Experimental Procedure:
- Step 1: Feature Extraction. For each author's set of messages, extract three independent sets of features:
- A vector of authorship attribution features (e.g., from Table 1).
- Word-based N-grams.
- Character-based N-grams.
- Step 2: Individual Likelihood Ratio Estimation. Calculate an LR for each author comparison using three different procedures:
- MVKD Procedure: Model each group of messages as a vector of authorship features.
- Word N-gram Procedure.
- Character N-gram Procedure.
- Step 3: Logistic-Regression Fusion. Fuse the three separately estimated LRs using logistic regression to obtain a single, more robust LR for each author comparison.
- Step 4: System Evaluation. Assess the performance of the individual procedures and the fused system using:
- Log-likelihood-ratio cost (Cllr): A single metric representing overall system accuracy.
- Tippett plots: Graphical representations of the distribution of LRs for ground-truth authors and non-authors.
A Protocol for Psycholinguistic NLP Analysis
This protocol outlines a methodology for identifying persons of interest by analyzing psycholinguistic features over time, as demonstrated in recent research [3].
1. Objective: To identify key suspects from a larger pool by reverse-engineering psycholinguistic features indicative of deceptive or emotional behavior.
2. Materials and Data:
- Corpus: A set of texts from multiple suspects (e.g., transcribed police interviews, emails).
- Ground Truth: Knowledge of the guilty parties (for validation).
3. Experimental Procedure:
- Step 1: Temporal Feature Tracking. For each suspect's text, calculate and track the following variables over the duration of the discourse or interview:
- Step 2: Topic and Entity Analysis.
- Apply Latent Dirichlet Allocation (LDA) to identify key topics.
- Analyze correlation to investigative keywords and phrases.
- Identify contradictory narratives within the text.
- Step 3: Data Integration and Suspect Ranking. Combine the outputs from the previous steps to create a subset of suspects who are highly correlated with the psycholinguistic and topical patterns of interest. This acts as a human feature reduction algorithm.
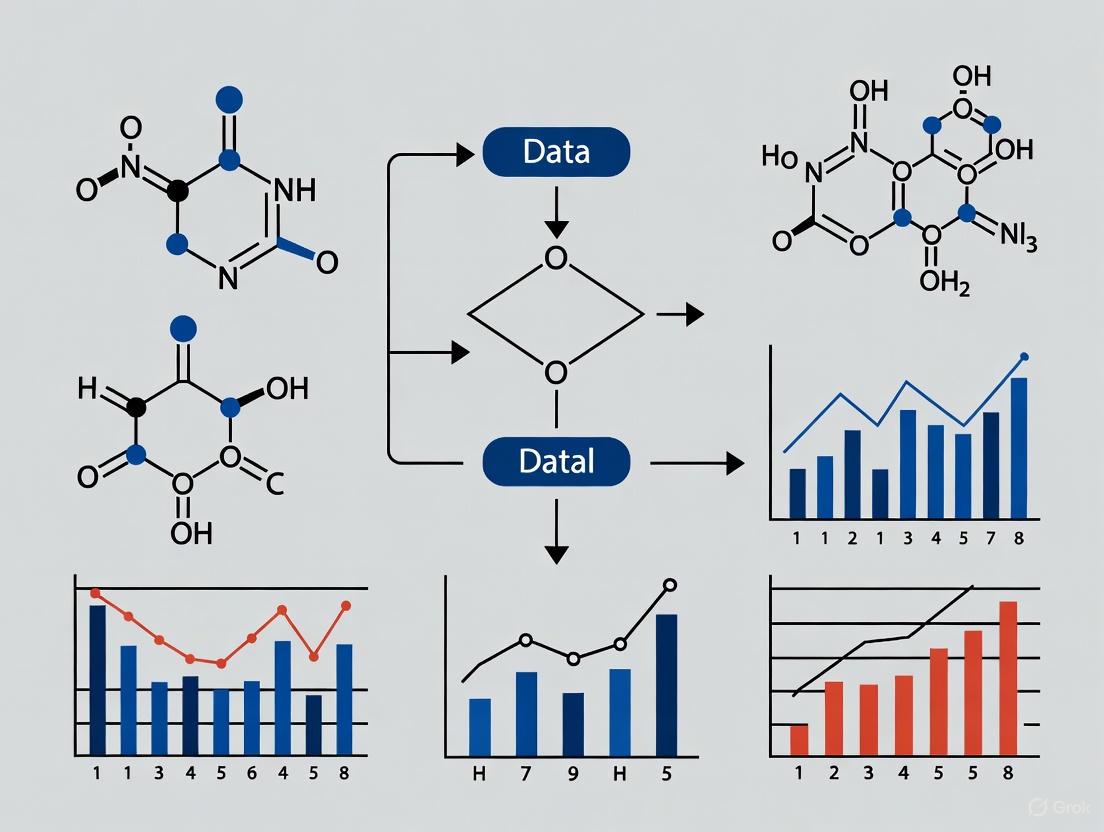
Visualization of Methodologies
The following diagrams illustrate the logical workflows of the core FTC methodologies described in this guide.
Fused Text Comparison System
Psycholinguistic Analysis Workflow
The Researcher's Toolkit
The following table details key reagents, software, and analytical solutions essential for conducting research in forensic text comparison.
Table 2: Essential Research Tools for Forensic Text Comparison
| Tool / Solution | Type | Primary Function in FTC |
|---|---|---|
| Empath [3] | Python Library | Analyzes text against built-in categories to generate and track features like deception and emotion over time. |
| LIWC (Linguistic Inquiry and Word Count) [3] | Software / Dictionary | Quantifies psychological and linguistic features in text, such as emotionality and cognitive processes. |
| MVKD (Multivariate Kernel Density) Procedure [4] | Statistical Model | Models an author's style as a multivariate distribution of linguistic features for likelihood ratio calculation. |
| N-gram Models (Word & Character) [3] [4] | Computational Linguistic Model | Captures frequent, habitual sequences of language elements that are characteristic of an author's idiolect. |
| Machine Learning Classifiers (e.g., SVM, Random Forest) [3] | Algorithm | Classifies texts based on learned stylistic patterns, often used for deception detection or authorship attribution. |
| LDA (Latent Dirichlet Allocation) [3] | Topic Modeling Algorithm | Discovers underlying thematic structures in a corpus of text, which can be used for narrative analysis. |
The Likelihood Ratio (LR) framework is widely recognized as the logically and legally correct method for the evaluation of forensic evidence [5]. Its adoption is being championed by scientific bodies and is becoming a regulatory requirement in an increasing number of jurisdictions. For instance, in the United Kingdom, the LR framework is slated for deployment across all major forensic science disciplines by October 2026 [5]. This framework provides a coherent and transparent method for quantifying the strength of evidence, moving away from categorical assertions towards a more nuanced and scientifically defensible interpretation. This guide explores the core principles of the LR framework, its application in forensic text comparison (FTC), and the empirical validation required for its defensible use, thereby situating it within the broader research agenda for robust forensic text comparison methodology.
Core Principles of the Likelihood Ratio
Fundamental Definition and Interpretation
At its heart, a Likelihood Ratio is a quantitative statement about the strength of evidence. It assesses the probability of the evidence under two competing propositions, typically the prosecution hypothesis ((Hp)) and the defense hypothesis ((Hd)) [5]. The LR is formally expressed in Equation (1):
[ LR = \frac{p(E|Hp)}{p(E|Hd)} ]
Here, (p(E|Hp)) is the probability of observing the evidence ((E)) given that the prosecution's hypothesis is true. Conversely, (p(E|Hd)) is the probability of the same evidence given that the defense's hypothesis is true [5]. The prosecution hypothesis in a typical FTC case might be that "the questioned and known documents were produced by the same author," while the defense hypothesis would be that "they were produced by different individuals" [5].
The value of the LR indicates the direction and strength of the evidence:
- LR > 1: The evidence supports (H_p).
- LR = 1: The evidence is neutral; it is equally probable under both hypotheses.
- LR < 1: The evidence supports (H_d) [5].
The further the LR is from 1, the stronger the evidence. For example, an LR of 10 means the evidence is ten times more likely if (Hp) is true than if (Hd) is true. Conversely, an LR of 0.1 means the evidence is ten times more likely if (H_d) is true [5].
The Role of the LR in Updating Beliefs: Bayes' Theorem
The LR is the key component in the logical process of updating prior beliefs about the hypotheses in light of new evidence. This process is formally described by the odds form of Bayes' Theorem, shown in Equation (2):
[ \underbrace{\frac{p(Hp)}{p(Hd)}}{\text{prior odds}} \times \underbrace{\frac{p(E|Hp)}{p(E|Hd)}}{\text{Likelihood Ratio (LR)}} = \underbrace{\frac{p(Hp|E)}{p(Hd|E)}}_{\text{posterior odds}} ]
This equation states that the prior odds (the fact-finder's belief about the hypotheses before considering the new evidence) multiplied by the LR yields the posterior odds (the updated belief after considering the evidence) [5].
It is critical to recognize the respective roles within this framework. The forensic scientist's task is to compute the LR based on the evidence. It is not the role of the forensic scientist to assign prior odds or to present the posterior odds, as these involve the fact-finder's domain and speak to the ultimate issue of guilt or innocence, which is the prerogative of the court [5]. The LR itself is a statement about the evidence, not the hypotheses.
Application of the LR Framework to Forensic Text Comparison
Forensic Text Comparison seeks to evaluate whether a questioned document originated from a particular known author. The complexity of textual evidence lies in the fact that a text encodes not only information about the author's idiolect but also about their social group, the topic, the genre, and the specific communicative situation [5]. The LR framework provides a structure for weighing the similarity and typicality of stylistic patterns observed in the texts.
Core Workflow in an FTC-LR System
The process of applying the LR framework in FTC involves a sequence of steps, from data preparation to the final calculation and validation of the LR. The workflow can be summarized as follows:
Diagram 1: Experimental workflow for an FTC-LR system.
Essential Research Reagent Solutions for FTC
To implement the workflow above, researchers and practitioners rely on a set of methodological "reagents" – essential components that ensure the analysis is scientifically sound.
Table 1: Essential Research Reagent Solutions for FTC-LR Analysis
| Item | Function in FTC-LR Analysis |
|---|---|
| Reference Data Corpora | Provides population-level data to estimate the typicality of features under (H_d). The data must be relevant to the case conditions (e.g., topic, genre) [5]. |
| Stylometric Features | Quantifiable aspects of writing style (e.g., "Average character number per word token," "Punctuation character ratio," vocabulary richness) used as measurements for comparison [6]. |
| Statistical Model | A computational model (e.g., Dirichlet-multinomial, Multivariate Kernel Density) used to calculate the probabilities (p(E|Hp)) and (p(E|Hd)) based on the extracted features [6]. |
| Calibration Model | A model, such as logistic regression calibration, applied to the output of the primary statistical model to ensure that the computed LRs are valid and well-calibrated [5]. |
| Validation Metrics | Performance measures like the log-likelihood-ratio cost (Cllr) and visualization tools like Tippett plots used to empirically test the accuracy and reliability of the LR system [5] [6]. |
Experimental Validation and Performance Metrics
The Critical Importance of Validation
A core tenet of the scientific method applied to forensic inference is empirical validation. It is not sufficient to simply use an LR model; the model's performance must be rigorously tested under conditions that reflect casework. Two main requirements for empirical validation are [5]:
- Reflecting the conditions of the case: The experimental setup must mimic the challenges of real casework (e.g., mismatched topics between documents, limited text length).
- Using relevant data: The data used for validation must be pertinent to the specific conditions of the case under investigation.
Failure to meet these requirements can mislead the trier-of-fact. For example, using a model validated on same-topic texts for a case involving texts on different topics (a "topic mismatch") would produce LRs of unknown validity and potentially over- or under-state the strength of the evidence [5].
Key Quantitative Metrics for System Performance
The performance of an LR-based system is quantitatively assessed using specific metrics that evaluate its discrimination ability and calibration.
Table 2: Key Performance Metrics for LR-Based Forensic Systems
| Metric | Description | Interpretation |
|---|---|---|
| Log-Likelihood-Ratio Cost (Cllr) | A single scalar measure that evaluates the overall performance of a forensic LR system, considering both discrimination and calibration [6]. | A lower Cllr value indicates better system performance. A perfect system has a Cllr of 0. Values below 1 are generally indicative of a system with some discrimination ability [6]. |
| Tippett Plots | A graphical tool that shows the cumulative distribution of LRs for same-source and different-source conditions [5]. | Allows for a visual assessment of system performance. A good system will show LRs >1 for same-source cases (supporting (Hp)) on the right and LRs <1 for different-source cases (supporting (Hd)) on the left, with a clear separation between the two curves. |
| Discrimination Accuracy | The rate at which the system correctly provides evidence supporting the true hypothesis. | For example, a discrimination accuracy of 94% means the system correctly assigns LRs >1 to same-source pairs and LRs <1 to different-source pairs 94% of the time [6]. |
Sample Experimental Protocol: Impact of Text Length
To illustrate a validated experiment, consider an investigation into how the amount of text influences the strength and accuracy of evidence in FTC.
1. Objective: To determine the effect of sample size on the performance of an LR-based authorship attribution system [6]. 2. Materials: Chatlog messages from 115 authors from a real archive of evidence [6]. 3. Feature Extraction: Stylometric features such as "Average character number per word token," "Punctuation character ratio," and vocabulary richness measures were extracted [6]. 4. Variable: Text length was manipulated at four levels: 500, 1000, 1500, and 2500 words [6]. 5. LR Calculation: LRs were calculated using the Multivariate Kernel Density formula, followed by logistic regression calibration [6]. 6. Performance Assessment: The primary metric was the log-likelihood-ratio cost (Cllr). Other assessments included credible intervals and equal error rates [6].
The results of this experiment are summarized in the table below, demonstrating a clear relationship between text length and system performance.
Table 3: Experimental Results: Impact of Text Length on FTC-LR System Performance [6]
| Sample Size (Words) | Discrimination Accuracy (Approx.) | Log-Likelihood-Ratio Cost (Cllr) |
|---|---|---|
| 500 | 76% | 0.68258 |
| 1000 | Information Not Specified | Information Not Specified |
| 1500 | Information Not Specified | Information Not Specified |
| 2500 | 94% | 0.21707 |
The data shows that a larger sample size is highly beneficial to FTC. It results in improved discriminability, an increase in the magnitude of LRs when (Hp) is true, and a decrease in the magnitude of LRs when (Hp) is false [6]. Furthermore, certain features like "Average character number per word token" were found to be robust across different sample sizes [6].
Advanced Considerations and Methodological Challenges
A significant challenge in some forensic disciplines is the tradition of examiners using subjective, categorical conclusions (e.g., "Identification," "Inconclusive," "Elimination"). Recent research has proposed methods to convert these categorical conclusions into LRs by statistically modeling examiner responses from black-box studies [7].
However, these methods face major hurdles to provide LRs meaningful for a specific case:
- Examiner-specific performance: A model trained on data pooled from multiple examiners may not represent the performance of the specific examiner in a given case, who may perform better or worse than the average [7].
- Case-specific conditions: The model must be trained on data that reflects the specific conditions of the case (e.g., quality of the evidence, type of material). LRs calculated under one set of conditions can differ substantially from those calculated under another [7].
A proposed solution is a Bayesian framework that uses population data as an informed prior, which is then updated with the specific examiner's own proficiency test data as it becomes available, gradually tailoring the model to the individual practitioner [7].
Presenting LRs for Maximum Understandability
A current frontier in LR research is how to best present LRs to legal decision-makers (e.g., judges, juries) to maximize comprehension. Existing empirical literature has explored the understanding of different formats, including:
- Numerical likelihood ratio values.
- Numerical random-match probabilities.
- Verbal strength-of-support statements.
A review of this literature concludes that there is no definitive answer on the "best" way to present LRs, highlighting a critical need for further research guided by robust methodologies [8]. Future studies must focus specifically on LR comprehension, using defined indicators like sensitivity, orthodoxy, and coherence to properly evaluate understanding [8].
The Likelihood Ratio framework provides a logically sound, transparent, and quantitative foundation for the evaluation of forensic evidence, including textual evidence. Its application in Forensic Text Comparison requires careful attention to statistical modeling, feature selection, and, most critically, empirical validation under casework-relevant conditions. While challenges remain—such as the integration of subjective examiner conclusions and the optimal communication of LR values to the courts—the LR framework represents the future of forensic science. It pushes the field towards greater scientific rigor, demonstrable reliability, and ultimately, a more robust and defensible administration of justice.
Forensic text comparison methodology research applies scientific principles and computational techniques to analyze written evidence, with the core objective of providing empirical support for one of two competing hypotheses: the prosecution's position (Hp) or the defense's position (Hd). This field integrates principles from psycholinguistics, computer science, and formal statistics to objectively evaluate linguistic evidence [3]. The process involves identifying and quantifying distinctive linguistic patterns to help triers of fact assess the strength of evidence in criminal cases, such as threats, forgeries, or anonymous communications.
The analytical framework is built upon a foundation of pattern-driven analysis, seeking symmetry between language (lingua) and the mind (psyche) [3]. By applying Natural Language Processing (NLP) and machine learning, researchers can extract measurable cues related to deception, emotion, and subjectivity from text sources like emails, instant messages, and transcribed interviews [3]. This technical guide details the methodologies and experimental protocols that underpin this rigorous scientific discipline.
Theoretical Foundation and Psycholinguistic Framework
Key Psycholinguistic Concepts in Hypothesis Formation
The theoretical foundation of forensic text comparison rests on the principle that language reflects cognitive and psychological states. Research demonstrates that deceptive communication, emotional arousal, and attempted deception manifest in predictable, quantifiable linguistic patterns [3].
- Deception Patterns: Deceptive language often exhibits subtle but measurable changes, including alterations in pronoun use, an increase in negations, and excessive use of sensory descriptions. These features are frequently too subtle for human detection but can be identified with computational assistance [3].
- Emotion and Subjectivity: The presence of specific emotions, such as anger and fear, as well as heightened subjectivity in narratives, can serve as proxies for deception or consciousness of guilt. For instance, overconfident individuals may tell more lies, and subjective language can influence perception and trustworthiness, even in the absence of factual information [3].
- Contradictory Narratives: Inconsistencies in a narrative over time or logical contradictions within a single statement are key indicators examined under both prosecution and defense frameworks.
Formal Statement of Core Hypotheses
The competing hypotheses are formally defined propositions regarding the source of a questioned text.
- Prosecution Hypothesis (Hp): The suspect is the author of the questioned text.
- Defense Hypothesis (Hd): The suspect is not the author of the questioned text; the questioned text originates from another source within a relevant population.
The role of the forensic text analyst is not to determine guilt or innocence, but to evaluate the linguistic evidence and calculate a likelihood ratio that expresses the strength of the evidence for one hypothesis over the other [3].
Quantitative Analysis of Psycholinguistic Features
The following table summarizes key psycholinguistic features and their typical interpretation in support of the prosecution or defense hypotheses, as identified in recent research [3].
Table 1: Quantitative Analysis of Psycholinguistic Features in Hypothesis Testing
| Feature Category | Specific Metric | Measurement Method | Typical Interpretation in Support of Hp | Typical Interpretation in Support of Hd |
|---|---|---|---|---|
| Deception | Deception over time | Python Empath library; statistical comparison with word embeddings [3] |
Sustained or elevated deception levels when discussing crime-related topics | Deception levels consistent with baseline or unrelated to crime topics |
| Emotion | Anger, Fear, Neutrality over time | N-gram analysis paired with emotion lexicons [3] | Increased fear or anger correlated with investigative keywords; unnatural neutrality | Emotional responses are contextually appropriate and not correlated with key crime terms |
| Subjectivity | Subjectivity vs. Objectivity | Lexical analysis (e.g., using LIWC) [3] | High subjectivity in factual accounts; contradictory narratives | Objective, consistent narrative without internal contradictions |
| Lexical Correlation | N-gram correlation | Pairwise correlation to investigative keywords and entities [3] | High correlation between suspect's language and specific crime-related entities/terms | Low correlation to key crime terms; language is generic |
| Narrative Consistency | Contradictory statements | Latent Dirichlet Allocation (LDA) for topic coherence; word vectors [3] | Fundamental contradictions in core narrative elements | Stable and coherent narrative throughout |
Experimental Protocols for Forensic Text Comparison
Protocol 1: NLP-Based Deception and Emotion Analysis
This protocol outlines the steps for a standardized evaluation of deception and emotion in suspect narratives, a common experimental approach in recent research [3].
Table 2: Key Research Reagent Solutions for NLP-Based Analysis
| Tool/Reagent | Type/Function | Brief Description of Role in Analysis |
|---|---|---|
| Empath Library | Python Library for NLP | Generates and analyzes lexical categories from text; used to calculate deception over time via statistical comparison with word embeddings [3]. |
| N-gram Models | Computational Linguistic Model | Identifies contiguous sequences of n words; used to track the frequency and context of investigative keywords and emotional language over time [3]. |
| LIWC (Linguistic Inquiry and Word Count) | Psycholinguistic Analysis Tool | Extracts features related to psychological states (e.g., emotion, subjectivity) from text, providing quantifiable data for machine learning [3]. |
| Latent Dirichlet Allocation (LDA) | Topic Modeling Algorithm | Discovers underlying thematic topics in a corpus of text; used to identify contradictory narratives or topic shifts [3]. |
| Word Embeddings (e.g., Word2Vec) | Word Vector Representation | Represents words in a high-dimensional space to measure semantic similarity; used for entity-to-topic correlation analysis [3]. |
- Data Collection and Preprocessing: Gather a corpus of text from the suspect(s) and, if available, from a relevant population sample. This can include transcribed police interviews, emails, or social media posts. Preprocess the text by tokenization, lemmatization, and removal of stop words.
- Feature Extraction:
- Calculate a deception score for each text segment using the
Empathlibrary. - Extract emotion scores (anger, fear, neutrality) using n-grams paired with established emotion lexicons.
- Compute subjectivity scores using a tool like LIWC.
- Perform entity and topic extraction using LDA to identify key themes and named entities.
- Calculate a deception score for each text segment using the
- Temporal Analysis: Plot the extracted features (deception, emotion, subjectivity) over the timeline of the text (e.g., interview sequence). This visualizes behavioral trends and predispositions.
- Correlation Analysis: Conduct a pairwise correlation between the suspect's use of specific keywords/entities and the central themes of the crime. A suspect highly correlated with key investigative terms may be of greater interest.
- Hypothesis Evaluation: Synthesize the results. A pattern of elevated deception, heightened fear or anger correlated with crime topics, and contradictory narratives may support the prosecution's position (Hp). A lack of these patterns may support the defense's position (Hd).
Protocol 2: Standardized LLM Evaluation for Forensic Timeline Analysis
Inspired by the NIST Computer Forensic Tool Testing Program, this protocol provides a framework for quantitatively evaluating the application of Large Language Models (LLMs) to forensic tasks, such as timeline analysis, which can support or challenge textual evidence [9].
- Dataset and Ground Truth Development: Create a standardized dataset that includes forensic timeline data (e.g., system logs, communication records). Establish a verified ground truth for this dataset.
- Timeline Generation and LLM Tasking: Process the data through a forensic timeline generator (e.g., log2timeline/plaso). Then, task an LLM (e.g., ChatGPT) with analyzing the timeline to answer specific investigative questions.
- Quantitative Evaluation with BLEU/ROUGE: Compare the LLM's output against the ground truth using quantitative metrics like BLEU (Bilingual Evaluation Understudy) and ROUGE (Recall-Oriented Understudy for Gisting Evaluation). These metrics assess the overlap and quality of the LLM-generated analysis versus the known facts [9].
- Hypothesis Support: The results determine the reliability of the LLM-generated analysis. Strong performance (high BLEU/ROUGE scores) indicates the tool can be used to generate credible insights that may support a case timeline for either Hp or Hd. Poor performance would undermine the credibility of such an analysis.
Case Study Application of the Framework
A research project successfully applied a psycholinguistic NLP framework to a fictional murder case with 18 suspects and two conspirators, whose identities were known only as ground truth [3]. The methodology involved analyzing separate, LLM-generated police interviews for each suspect.
- Initial Challenge: Initial analysis showed minimal variance in deception levels across all suspects, rendering this single metric ineffective [3].
- Application of Multi-Faceted Protocol: Researchers implemented a framework combining entity-to-topic correlation, deception detection, and emotion analysis.
- Outcome: By focusing on the correlation between a suspect's language and the key entities of the crime, and by analyzing emotional cues beyond deception, the methodology successfully identified the two guilty conspirators from the larger pool, thereby validating the prosecution's hypothesis (Hp) in the scenario [3]. This case demonstrates the necessity of a multi-feature approach rather than relying on a single linguistic metric.
The rigorous application of the core hypotheses framework is fundamental to the scientific validity of forensic text comparison. By employing standardized experimental protocols, quantitative analysis of psycholinguistic features, and a clear understanding of the prosecution and defense positions (Hp and Hd), researchers and forensic practitioners can provide objective, reliable, and actionable insights from linguistic evidence. The ongoing development of NLP and machine learning techniques, coupled with standardized evaluation methods, continues to enhance the field's precision and reliability, ensuring that its findings are robust and defensible.
Forensic text comparison methodology research represents a critical interdisciplinary frontier, integrating computational linguistics, psychology, and data science to address challenges in legal evidence analysis. This field has evolved from traditional qualitative document examination to sophisticated quantitative frameworks that disentangle the complex interplay of authorial style, genre conventions, and topical content in textual evidence. The burgeoning volume of digital communication in legal contexts—including emails, social media posts, and transcribed interviews—has created an urgent need for scientifically robust analytical protocols that can withstand judicial scrutiny [3].
Contemporary research focuses on developing transparent, replicable methodologies that account for the multifaceted nature of linguistic expression. The fundamental challenge lies in distinguishing between stable author-specific patterns, transient genre-appropriate conventions, and content-driven vocabulary selection. This whitepaper examines current technical approaches within the context of a broader thesis: that reliable forensic text comparison requires integrated multi-dimensional analysis rather than isolated feature examination. We present a comprehensive technical guide featuring experimental protocols, analytical frameworks, and visualization methodologies designed for researchers and forensic professionals engaged in developing validated text analysis procedures for legal applications [3] [10].
Theoretical Foundations
Psycholinguistic Underpinnings of Deceptive Communication
Psycholinguistics provides the theoretical foundation for understanding how cognitive processes manifest in linguistic output during deceptive communication. Research indicates that deception imposes additional cognitive load, resulting in measurable linguistic features including changes in pronoun distribution, verbal complexity, and emotional expression [3]. The Pythagorean concept of pattern-driven reality finds modern application in forensic text analysis, where computational methods detect subtle but consistent patterns linking psychological states to linguistic choices [3].
Forensic text comparison operates on the principle that individuals exhibit measurable patterns in their language use across multiple dimensions. The analytical challenge lies in distinguishing between three primary influences: author-specific patterns (relatively stable across an individual's texts), genre-constrained conventions (shared across documents serving similar functions), and topic-driven vocabulary (content-specific terminology). Research demonstrates that effective forensic analysis must account for all three dimensions simultaneously rather than in isolation [3].
Analytical Framework for Multi-Dimensional Text Analysis
A robust analytical framework for forensic text comparison must integrate three complementary perspectives: author attribution through stylistic analysis, genre classification through structural patterns, and topic modeling through content analysis. This tripartite approach enables researchers to isolate stable authorial fingerprints from variable contextual influences, thereby increasing the reliability of forensic conclusions [3] [11].
Table 1: Core Dimensions of Forensic Text Analysis
| Dimension | Key Features | Analytical Methods | Forensic Application |
|---|---|---|---|
| Author | Pronoun frequency, syntactic complexity, vocabulary richness, punctuation patterns | N-gram analysis, lexical richness metrics, function word frequency | Author attribution, identity verification |
| Genre | Text structure, formulaic expressions, register-appropriate vocabulary, document length | Structural templates, discourse markers, move analysis | Document classification, context assessment |
| Topic | Domain-specific terminology, semantic coherence, entity density, conceptual relationships | LDA topic modeling, word embeddings, entity extraction, knowledge graphs | Content verification, intent analysis |
Methodological Approaches
Quantitative Text Analysis Protocols
Modern forensic text analysis employs rigorous quantitative protocols to transform unstructured text into analyzable data structures. The MAXDictio module within MAXQDA provides comprehensive tools for quantitative content analysis, including vocabulary analysis, dictionary-based analysis, and visual text exploration [12]. These tools enable researchers to conduct systematic investigations of word frequencies, distributions, and patterns across document collections, forming the foundation for more advanced forensic comparisons [12].
The Word Tree visualization represents a particularly powerful methodology for exploring textual structure, displaying all combinations that lead to or from specific words of interest with frequency information [12]. This approach facilitates the identification of characteristic phrasing patterns that may distinguish individual authors or genre conventions. Advanced implementations incorporate lemmatization (summarizing words sharing the same stem), stop word lists for filtering common but uninformative terms, and integration with document variables or codes to segment analysis by relevant metadata [12].
Experimental Workflow for Forensic Text Comparison
A standardized experimental workflow ensures methodological consistency and reproducibility in forensic text comparison research. The following protocol outlines key stages in a comprehensive analysis:
Stage 1: Corpus Compilation and Preprocessing
- Document collection and metadata annotation
- Text normalization (lowercasing, punctuation handling)
- Tokenization and sentence boundary detection
- Linguistic annotation (part-of-speech tagging, syntactic parsing)
Stage 2: Feature Extraction and Selection
- Lexical feature extraction (character n-grams, word n-grams)
- Syntactic feature calculation (production rules, dependency relations)
- Semantic feature generation (entity density, topic distributions)
- Stylistic feature computation (readability metrics, cohesion indices)
Stage 3: Multi-Dimensional Analysis
- Author dimension: Stylometric fingerprinting using function words and character n-grams
- Genre dimension: Discourse structure analysis using move analysis and rhetorical patterns
- Topic dimension: Semantic field identification using topic models and word embeddings
Stage 4: Validation and Interpretation
- Cross-validation using known-author documents
- Statistical significance testing of distinctive features
- Likelihood ratio calculation for evidence weight assessment
- Results interpretation within forensic context
Diagram 1: Forensic Text Analysis Workflow
Advanced Visualization Methodologies
Effective visualization transforms complex textual patterns into interpretable visual representations, enabling researchers to identify relationships that might remain obscured in raw data. Modern text visualization tools employ multiple methodologies, each offering distinct analytical advantages [13].
Network graphs represent words or concepts as nodes and their relationships as edges, revealing structural patterns in discourse. Tools like InfraNodus use text network analysis algorithms to identify influential concepts and topical clusters, enabling researchers to explore relationships and gaps in textual data [13]. Timeline and frequency charts track the evolution of concepts across documents or narrative time, implemented in tools like Voyant Tools and MAXQDA through rank-frequency analysis and dispersion plots [13]. Embedding projections use dimensionality reduction techniques like t-SNE or UMAP to visualize semantic relationships in high-dimensional word vector spaces, while knowledge graphs instantiate entities and their typed relations based on domain ontologies, enabling logical reasoning over textual content [13].
Table 2: Text Visualization Tools for Forensic Analysis
| Tool | Primary Methodology | Key Features | Best Suited For |
|---|---|---|---|
| InfraNodus | AI-powered knowledge graphs, text network analysis | Interactive graph visualization, gap detection, AI-powered insights | Exploring conceptual relationships, identifying discourse gaps |
| Voyant Tools | Tag clouds, timeline analysis, frequency charts | Browser-based, timeline visualization, entity extraction | Initial text exploration, temporal pattern identification |
| MAXQDA | Coding representation, frequency visualization | Powerful coding features, code frequency analysis, thematic analysis | Systematic qualitative analysis, manual annotation |
| NotebookLM | AI-powered mindmaps | Mindmap generation, document chatting, structured overview | Document summarization, conceptual mapping |
Technical Implementation
Analytical Techniques for Deception Detection
Deception detection represents a critical application of forensic text analysis, employing specific linguistic features as indicators of deceptive communication. Research by Adkins et al. (2025) demonstrates that integrated analysis of deception cues, emotional markers, and subjectivity levels can effectively identify persons of interest in investigative contexts [3]. Their approach combines multiple NLP techniques to create a psycholinguistic profile based on temporal patterns in language use.
The Empath library provides a methodological framework for quantifying deception-related language through statistical comparison with word embeddings and built-in categories [3]. This approach identifies contextually relevant deception indicators in target text, normalizes token frequencies, and uses these normalized values as features for machine learning classification. Complementary research by Huang and Liu (2022) demonstrates that subjectivity-objectivity balance serves as a proxy for deception, with highly subjective communications often perceived as more trustworthy despite potential factual inaccuracies [3].
Diagram 2: Deception Detection Framework
Research Reagent Solutions for Text Analysis
Forensic text analysis relies on specialized computational tools and linguistic resources that function as "research reagents" in experimental protocols. These standardized components enable reproducible, validated analyses across different research contexts and document types.
Table 3: Essential Research Reagent Solutions for Forensic Text Analysis
| Reagent Category | Specific Tools/Resources | Function in Analysis | Implementation Example |
|---|---|---|---|
| Linguistic Feature Extractors | NLTK, SpaCy, Stanford CoreNLP | Tokenization, lemmatization, part-of-speech tagging, dependency parsing | Extracting syntactic complexity metrics for author profiling |
| Psychological Text Analyzers | LIWC, Empath Library | Quantifying psychological constructs, emotional tone, cognitive processes | Measuring deception indicators and emotional markers over time |
| Topic Modeling Frameworks | Gensim, Mallet, BERTopic | Identifying latent thematic structures, conceptual relationships | Distinguishing topic-driven vocabulary from author-specific style |
| Visualization Platforms | InfraNodus, Voyant Tools, MAXQDA | Creating interpretable visualizations of complex textual patterns | Generating knowledge graphs for conceptual relationship analysis |
| Machine Learning Classifiers | Scikit-learn, TensorFlow, PyTorch | Building predictive models for authorship attribution | Implementing ensemble methods with Logistic Regression, SVM, Random Forest |
Validation Frameworks and Statistical Interpretation
Robust validation represents the cornerstone of forensically sound text comparison methodology. The critical review by Yang et al. emphasizes that persistent challenges—including substrate variability, environmental influences, and database deficiencies—require rigorous validation protocols specifically designed for forensic applications [10]. Their analysis of analytical techniques for forensic paper comparison highlights the necessity of standardized validation approaches across the field.
Forensic text comparison must address two distinct validation requirements: methodological validation (establishing that a technique reliably measures what it claims to measure) and interpretive validation (establishing appropriate statistical frameworks for drawing inferences from results). Methodological validation requires demonstrating repeatability (consistent results under identical conditions) and reproducibility (consistent results across different laboratories and operators) [10]. Interpretive validation requires establishing appropriate statistical models for evaluating the strength of evidence, with likelihood ratio frameworks increasingly recognized as the most appropriate approach for forensic applications [3] [10].
Challenges and Future Directions
Despite significant methodological advances, forensic text comparison faces persistent challenges that require continued research attention. A primary limitation identified across multiple studies is the dependency on sufficient sample sizes for reliable model training, particularly for authorship attribution tasks where limited known samples from potential authors may be available [3] [10]. Additionally, the dynamic nature of language use across contexts and over time complicates the identification of stable authorial fingerprints.
Future research directions should prioritize the development of adaptive models that account for linguistic change across time and context, improved normalization techniques for cross-genre comparison, and standardized validation protocols specifically designed for forensic applications. The integration of psycholinguistic theory with computational methods represents a particularly promising avenue for enhancing deception detection capabilities, moving beyond surface-level patterns to model the cognitive processes underlying linguistic production [3]. Furthermore, research should address the ethical implications of automated text analysis in legal contexts, ensuring that methodologies remain transparent, interpretable, and forensically validated.
Forensic text comparison methodology research has evolved from qualitative examination to sophisticated multi-dimensional frameworks that simultaneously address authorial, generic, and topical influences on linguistic production. This whitepaper has presented current technical approaches, experimental protocols, and analytical frameworks that enable researchers to disentangle these complex interactions for reliable forensic analysis. The continued development of validated, transparent methodologies remains essential for advancing the scientific rigor of textual evidence analysis in legal contexts. As computational capabilities advance and linguistic theories evolve, forensic text comparison methodologies will continue to increase in discriminative power, provided they remain grounded in robust validation frameworks and ethical implementation practices.
Core FTC Methodologies: Feature-Based, Score-Based, and Psycholinguistic Approaches
Forensic Text Comparison (FTC) is a scientific discipline concerned with quantifying the strength of linguistic evidence for authorship attribution. Within the judicial system, there is increasing agreement that the strength of forensic evidence, including textual evidence, should be quantified and presented using a Likelihood Ratio (LR) [14]. The LR framework provides a coherent and transparent method for evaluating evidence under two competing propositions: typically, a prosecution hypothesis (e.g., the suspect is the author of the questioned text) and a defense hypothesis (e.g., the suspect is not the author) [15] [14]. The application of the LR framework to textual evidence represents a significant methodological advancement over traditional, non-probabilistic approaches to authorship analysis.
There are two conventional computational methods for calculating a Likelihood Ratio in FTC: score-based methods and feature-based methods [14]. Score-based methods reduce the multivariate data of a text (e.g., word counts) to a single, univariate similarity or distance score (e.g., Cosine distance, Burrows's Delta). The LR is then estimated based on the distributions of these scores from known and unknown sources [15] [14]. While computationally simpler and robust with limited data, this approach has a critical shortcoming: it inevitably loses information from the original multivariate feature space and does not directly assess the typicality of the evidence, only its similarity [14].
In contrast, feature-based methods directly compute LRs by assigning probabilities to the multivariate linguistic features themselves. This paper provides an in-depth technical guide on implementing two powerful classes of feature-based models—Poisson and Dirichlet-Multinomial models—which are theoretically more appropriate for the discrete, count-based nature of textual data and form a core part of modern forensic text comparison methodology research [15] [14] [16].
Table 1: Core Concepts in Forensic Text Comparison
| Concept | Description | Importance in FTC |
|---|---|---|
| Likelihood Ratio (LR) | A ratio of the probabilities of the evidence under two competing hypotheses (prosecution vs. defense). | Provides a quantitative, logically coherent measure of evidence strength for the court [14]. |
| Feature-Based Methods | Methods that compute LRs by directly modeling the multivariate distribution of linguistic features (e.g., word counts). | Preserves more information from the evidence and incorporates both similarity and typicality [14]. |
| Textual Typicality | The rarity or commonness of a set of linguistic features in a relevant population. | A key component of the LR; distinguishes feature-based from score-based methods [14]. |
| Bag-of-Words Model | A text representation model that discards word order and uses word frequencies as features. | A common, effective feature set for authorship attribution, forming the input for Poisson and DMM models [14] [16]. |
Theoretical Foundations of Poisson and Dirichlet-Multinomial Models
The Poisson Model for Count Data
The Poisson distribution is a discrete probability distribution that models the probability of a given number of events occurring within a fixed interval of time or space, assuming these events happen with a known constant mean rate and independently of the time since the last event [17]. Its probability mass function is given by:
(P(Y=k) = \frac{e^{-\lambda} \lambda^{k}}{k!})
where (k) is the number of occurrences (a non-negative integer) and (\lambda) is the expected number of occurrences, which is also the variance of the distribution [17].
In the context of FTC, the "events" are the occurrences of specific words or linguistic features in a text. A Poisson model is naturally suited for modeling word count data because it can handle discrete, non-negative counts and can capture the often over-dispersed nature of word frequency distributions [14]. When implemented within a Generalized Linear Model (GLM) framework, Poisson regression models the logarithm of the expected count as a linear function of predictor variables. This log-link function ensures that the predicted counts are always non-negative [17]. For LR estimation, a Poisson model allows for the direct calculation of the probability of observing a particular set of word counts in a questioned document, given a specific author, thereby incorporating both the similarity between documents and the typicality of the author's writing style within a population [15] [14].
The Dirichlet-Multinomial Model for Topic and Cluster Analysis
While the Poisson model is a univariate model for counts of individual features, the Dirichlet-Multinomial (DMM) model is a multivariate model often used for clustering short texts and discovering latent topics [16]. It is a generative model that assumes a document is generated by first drawing a topic mixture from a Dirichlet distribution, and then generating the words of the document from a multinomial distribution conditioned on that topic [16].
A key variant is the Dirichlet Multinomial Mixture (DMM) model, which assumes that each short text (e.g., a tweet or a message) belongs to a single topic [16]. This "one-topic-per-document" assumption is particularly effective for short text clustering, where the limited word co-occurrence information makes assigning multiple topics to a single document challenging [16]. The DMM model helps overcome the data sparsity and high-dimensionality problems inherent in short text analysis, making it a valuable tool for forensic analysts who often work with SMS messages, emails, or social media posts.
Experimental Protocols and Performance Benchmarking
Protocol for Poisson-based Likelihood Ratio Estimation
The implementation of a Poisson model for LR estimation in FTC involves a structured workflow, from data preparation to performance validation. The following diagram illustrates the core sequence of this protocol.
Data Collection and Preparation: The foundational step is gathering a large, representative corpus of texts to serve as a reference population. A seminal study by Carne & Ishihara (2020) utilized documents from 2,157 authors to ensure robust model training and evaluation [15] [14]. Texts are preprocessed using standard natural language processing (NLP) techniques, which may include tokenization, lowercasing, and removal of punctuation. The features are then extracted, typically using a bag-of-words model that discards word order and represents each document as a vector of word counts [14].
Feature Selection and Model Training: The high dimensionality of text data (thousands of words) necessitates feature selection. A common approach is to select the N-most frequent words (e.g., N=400) across the corpus to create the feature vectors [14]. For the Poisson model, the parameters (e.g., the expected word counts λ for different authors) are estimated from the training data. The LR for a questioned document (Q) and a known document (K) from a suspect is then calculated by comparing the probability of observing the word counts in Q under the assumption that the author is the suspect (same source) versus the assumption that the author is a random member of the population (different source) [14]. This can be extended using more complex models like a two-level Poisson-gamma model to account for extra-Poisson variation [14].
Performance Validation: The performance of the LR system must be rigorously validated using a separate test set. The standard metric is the log-likelihood ratio cost (Cllr). This metric evaluates the system's overall performance by combining measures of its discrimination power (ability to distinguish between same-source and different-source comparisons) and its calibration (the accuracy of the LR values themselves) [15] [14]. A lower Cllr indicates better performance.
Protocol for Dirichlet-Multinomial Mixture for Short Text Clustering
The DMM protocol focuses on inferring the latent topic structure within a collection of short texts, which can help in organizing and understanding large volumes of forensic data, such as categorizing messages by theme or intent.
Data Preprocessing for Short Texts: Short texts present unique challenges, including sparse terms and a limited number of words per document, which leads to fewer word co-occurrences [16]. Preprocessing is critical and may involve more aggressive filtering (e.g., removing very rare words) and handling of noise like spelling errors, which is common in social media data [16].
Determining the Number of Topics (Clusters): A significant challenge with DMM and related topic models is that they typically require pre-specifying the number of topics, K, which is often unknown [16]. Advanced methods like Gibbs Sampling for DMM (GSDMM) can automatically infer the optimal number of topics, but at a high computational cost, especially if the initial maximum K is set too high [16].
Model Fitting and Cluster Refinement: The DMM model is fitted to the short text corpus, assigning each document to a single topic cluster. To enhance performance, a hybrid approach like the Topic Clustering based on Levenshtein Distance (TCLD) algorithm can be employed. After an initial clustering with DMM, TCLD evaluates the semantic relationships between documents using the Levenshtein Distance (a fuzzy string matching algorithm). It then decides whether to keep a document in its initial cluster, move it to a more appropriate cluster, or mark it as an outlier, thereby optimizing the final topic clusters [16].
Quantitative Performance Comparison
Empirical studies have directly compared the performance of feature-based and score-based methods under controlled conditions. The following table synthesizes key findings from a large-scale evaluation.
Table 2: Empirical Performance Comparison of FTC Methods
| Method Type | Specific Model | Data & Features | Performance (Cllr) | Key Findings |
|---|---|---|---|---|
| Feature-Based | One-level Poisson, Zero-inflated Poisson, Two-level Poisson-gamma [14] | 2,157 authors; Bag-of-words (N=400) [14] | Cllr = 0.14-0.2 lower than score-based (best settings) [14] | Outperforms score-based methods. Performance can be further improved with feature selection [15] [14]. |
| Score-Based | Cosine Distance [15] [14] | 2,157 authors; Bag-of-words (N=400) [14] | Baseline for comparison (Cllr ~0.09 higher than feature-based) [15] | Violates statistical assumptions of textual data (e.g., normality). Assesses only similarity, not typicality [14]. |
| Hybrid Topic Model | TCLD (DMM + Levenshtein Distance) [16] | Six English benchmark short-text datasets [16] | 83% improvement in Purity; 67% improvement in NMI vs. baseline models [16] | Effectively addresses outlier problem and determines optimal topic number in short texts [16]. |
The Scientist's Toolkit: Essential Research Reagents
Implementing the methodologies described requires a suite of computational tools and conceptual frameworks. The following table details the key components of the forensic text analyst's toolkit.
Table 3: Research Reagent Solutions for Forensic Text Modeling
| Tool / Reagent | Type | Function in FTC Research |
|---|---|---|
| Bag-of-Words Model | Conceptual / Representational | Represents text as a multivariate vector of word counts, serving as the primary input for both Poisson and DMM models [14] [16]. |
| Log-Likelihood Ratio Cost (Cllr) | Evaluation Metric | The standard metric for validating the performance and reliability of a forensic LR system, assessing both discrimination and calibration [15] [14]. |
| Gibbs Sampling | Computational Algorithm | A Markov Chain Monte Carlo (MCMC) method used for approximate inference in complex probabilistic models like GSDMM, to estimate model parameters and cluster assignments [16]. |
| Levenshtein Distance Algorithm | Computational Algorithm | Measures the similarity between two strings by calculating the minimum number of single-character edits required to change one string into the other. Used in hybrid models like TCLD for post-clustering refinement [16]. |
| Empath / LIWC | Software Library / Lexicon | NLP libraries used for psycholinguistic feature extraction (e.g., detecting deception, emotion). Can be used to generate specialized feature sets for analysis [3]. |
| LASSO / Fused LASSO | Statistical Penalization | Regularization techniques used in time-dependent Poisson models to achieve sparsity and identify words with stable discriminatory power over time, handling high-dimensional parameters [18]. |
Advanced Implementations and Future Directions
Time-Dependent Poisson Models
A significant advancement in Poisson modeling for text is the development of time-dependent Poisson reduced rank models. Political lexicon and writing style are not static; they evolve. This model allows the parameters representing word weights ((bj^{(k)})) to change over time ((t)) [18]. The model is formulated as: (Y{ijt} \sim \text{Poisson}(\mu{ijt}), \text{ where } \mu{ijt} = \exp(\alphaj + \beta{it} + \sum{k=1}^K b{j,t}^{(k)} f_{it}^{(k)})) To manage the high dimensionality of this formulation, estimation employs LASSO and Fused LASSO penalization techniques. This encourages sparsity (many word weights are zero) and temporal smoothness (word weights change gradually over time), allowing the model to automatically identify words that have a stable, discriminating effect on author or party positions across different time periods [18].
Integration with Psycholinguistic NLP Frameworks
The future of FTC methodology lies in the integration of sophisticated statistical models like Poisson and DMM with psycholinguistically informed NLP frameworks. Such frameworks move beyond simple word counts to analyze features like deception over time, emotion levels (e.g., anger, fear), and subjectivity in narratives [3]. By combining latent topic information from DMM models with psycholinguistic feature extraction tools (e.g., Empath), analysts can create a more nuanced profile of an author. This can help in identifying persons of interest by focusing on those whose communication is highly correlated with investigative keywords and who demonstrate linguistic patterns associated with deceptive or emotional states [3].
Handling Overdispersion with Negative Binomial
A key assumption of the standard Poisson model is that the mean equals the variance. Real-world text data often exhibits overdispersion, where the variance exceeds the mean. While a two-level Poisson-gamma model can account for this [14], a common and practical alternative is the Negative Binomial regression model, which can be viewed as a generalization of the Poisson model that incorporates extra-Poisson variation [17]. This model should be the go-to choice when overdispersion is detected in the count data, as it leads to more reliable and accurate confidence intervals for the model parameters.
Forensic Text Comparison (FTC) is a scientific discipline concerned with quantifying the evidence for authorship of textual materials. In the context of cybercrime, law enforcement, and intellectual property disputes, text messages are often the main medium of communication and may be the only available source of information leading to the identification of the wrongdoer(s) [19]. The foundational concept is that each person possesses a unique writing style, or idiolect, which manifests in author-specific characteristics within the text [19]. The core challenge for FTC is to develop methodologies that can quantitatively represent these stylistic patterns and reliably evaluate the strength of evidence for authorship attribution.
Score-based methods represent a significant methodological advancement within the likelihood ratio (LR) framework for FTC. These methods provide a structured paradigm for quantifying the strength of evidence by comparing the similarity between a questioned text and known author samples [19]. Within this framework, Cosine Distance and Burrows's Delta have emerged as two prominent score-generating functions for comparing paired text samples. Their efficacy lies in the ability to transform the multivariate structure of linguistic features into a univariate score, which can then be converted into a likelihood ratio—a statistically valid measure of evidence strength that helps the trier-of-fact (e.g., a judge or jury) assess whether the suspect and the author of an incriminating text are the same person [19] [20]. This technical guide explores the theoretical foundations, experimental protocols, and performance characteristics of these two core methods, positioning them within the broader research agenda to build demonstrably reliable systems for forensic authorship analysis.
Theoretical Foundations of Distance Measures in Stylometry
The Bag-of-Words Model and Feature Space
Score-based authorship attribution typically begins with the Bag-of-Words (BoW) model, a near-standard technique for representing textual data [19]. In this model, texts are converted into vectors in a high-dimensional space where each dimension corresponds to the normalized frequency of a specific word. The initial feature set usually comprises the N Most Frequent Words (MFW) from the entire corpus, excluding stop words. The relative frequencies of these MFW are often transformed using Z-score normalization to create a document-term matrix. This standardization is a critical step in Burrows's original Delta method and its variants, as it accounts for the overall vocabulary richness of individual documents and makes feature values comparable across texts [21].
The core assumption is that an author's stylistic signature is encoded in their consistent patterns of word preference—their tendency to over-use or under-use common words relative to other authors. The BoW model, while discarding information about word order, effectively captures these statistical patterns. The choice of N (the number of MFW) is an experimental parameter, with research indicating that system performance can be robust across a wide range of N values, particularly when using Cosine Distance [21].
Defining the Distance Measures
The similarity or dissimilarity between two text vectors is quantified using a distance measure, which serves as the score in a score-based LR system. The two measures central to this guide are:
Cosine Distance: This measure calculates the cosine of the angle between two text vectors in the high-dimensional feature space. It is computed as 1 minus the cosine similarity. The cosine similarity is the dot product of the two vectors divided by the product of their magnitudes (Euclidean norms). A key property of Cosine Distance is its insensitivity to vector magnitude; it focuses solely on the directional alignment of the vectors, which corresponds to the qualitative pattern of word usage [21]. This property makes it particularly effective for authorship tasks, where the "key profile" of an author's style—the pattern of over- and under-utilization of vocabulary—is more important than the actual amplitude of frequency deviations [21].
Burrows's Delta (Delta Bur): This is the original measure proposed by John Burrows, which has proven remarkably successful in computational stylistics [21]. It is defined as the mean of the absolute differences between the Z-scores of the MFW in two texts. Mathematically, for two texts A and B, Delta is (1/N) * Σ |Zi,A - Zi,B|, where the sum is taken over the N MFW. In essence, it is the Manhattan distance (L1 distance) between the Z-score vectors [21]. Unlike Cosine Distance, it is sensitive to the magnitudes of the Z-scores, making it potentially more susceptible to outliers—extreme Z-score values specific to single texts rather than all texts of a single author [21].
The Key Profile Hypothesis vs. The Outlier Hypothesis
Research into why these algorithms work has led to two competing hypotheses, which have significant implications for understanding the robustness of different distance measures.
The Outlier Hypothesis (H1): This posited that performance differences between measures were caused by single extreme Z-score values. It suggested that the positive effect of vector normalization (inherent in Cosine Distance) stemmed from the reduction of these outlier amplitudes [21].
The Key Profile Hypothesis (H2): This hypothesis, which has received stronger empirical support, argues that an author's stylistic signature manifests more in the qualitative combination of word preferences (the pattern) than in the actual amplitude of Z-scores [21]. A measure is successful if it emphasizes these structural differences without being overly influenced by amplitude variations.
Experiments have disproven H1 by showing that vector normalization, which drastically improves the performance of all Delta measures, hardly reduces the number of extreme Z-score values [21]. Conversely, H2 was confirmed by creating pure "key profile" vectors that only recorded whether a word frequency was above average (+1), unremarkable (0), or below average (-1). These ternary vectors performed almost as well as the full vector normalization, demonstrating that the profile of deviation across the MFW is the critical factor [21]. This finding explains the superior and robust performance of Cosine Distance, which intrinsically normalizes for vector length and is therefore a pure measure of the key profile.
Experimental Protocols for Forensic Validation
A General Workflow for Score-Based Authorship Analysis
The following workflow delineates the standard procedure for conducting a score-based authorship analysis, from data preparation to the calculation of a likelihood ratio. This process is visualized in Figure 1.
Figure 1: A generalized workflow for score-based forensic text comparison, showing the process from data collection to the calculation of a likelihood ratio.
Protocol 1: Implementing Cosine Distance with a BoW Model
This protocol details the steps for a specific experiment demonstrating the efficacy of Cosine Distance, as described in the research.
Objective: To estimate score-based likelihood ratios for linguistic text evidence using a Bag-of-Words model and Cosine Distance as the score-generating function [19].
Corpus:
- Source: The Amazon Product Data Authorship Verification Corpus was used.
- Synthesis: Two groups of documents were synthesized for each author. Each group contained documents of approximately 700, 1400, and 2100 words. This design allowed for 720 same-author comparisons and 517,680 different-author comparisons to test system validity [19].
Feature Engineering:
- Model: A Bag-of-Words model was implemented.
- Features: The Z-score normalized relative frequencies of the N most frequent words (N was varied in experiments, e.g., N=260).
- Vector Representation: Each text is represented as a high-dimensional vector of these normalized frequencies.
Score Calculation:
- The Cosine Distance between the vector of a questioned document (Q) and the vector of a known suspect document (K) is calculated.
- The Cosine Distance is defined as: 1 - ( (Q • K) / (||Q|| * ||K|| ) ), where '•' denotes the dot product and '|| ||' denotes the Euclidean norm (vector length).
Likelihood Ratio Estimation:
- Score Distributions: The distributions of same-author scores and different-author scores are compiled using a "common source method" [19].
- Model Fitting: The score distributions are approximated using parametric models (e.g., Normal, Log-normal, Gamma, Weibull). The best-fitting model is selected.
- Conversion: The calculated Cosine Distance score between K and Q is converted into a likelihood ratio using the fitted distributions. The LR is given by: LR = f(score | same-author) / f(score | different-author), where f is the probability density function.
Validation:
- Metric: System validity is assessed using the log-likelihood-ratio cost (Cllr). A lower Cllr indicates better system performance.
- Visualization: The strength and calibration of the derived LRs are visualized using Tippett plots.
Protocol 2: Comparing Delta Variants and the Key Profile
This protocol is based on experiments designed to test the key profile hypothesis by comparing different variants of Burrows's Delta.
Objective: To understand the performance differences between Burrows's Delta (Delta Bur), other Minkowski distances (Lp-Delta), and Cosine Delta (Delta Cos), and to test the outlier (H1) and key profile (H2) hypotheses [21].
Corpus:
- Composition: A corpus of 75 texts in German, with 25 different authors and 3 novels per author. Similar corpora in English and French were used for validation [21].
Feature Engineering:
- Model: The standard document-term matrix with Z-score normalization of MFW.
- Manipulations: Two specific data manipulations were applied:
- Vector Length Normalization: All feature vectors were normalized to a length of 1.
- Outlier Truncation (Clamping): All |Z-scores| > 2 were set to +2 or -2.
- Ternary Key Profiles: Vectors were converted to values of +1 (above average), 0 (unremarkable), or -1 (below average).
Score Calculation & Analysis:
- Distance Measures: Multiple Lp-Delta measures were calculated, including L1 (Manhattan, Delta Bur), L2 (Euclidean, Delta Q), and L4 (highly sensitive to outliers).
- Cosine Distance (Delta Cos) was also calculated.
- Task: All 75 texts were automatically clustered into 25 groups (one per author) based on the calculated distance matrices.
Evaluation:
- Metric: Clustering quality was estimated using the Adjusted Rand Index (ARI). An ARI of 100% signifies perfect author attribution, while 0% is random.
- Comparison: The performance of each distance measure, with and without data manipulations, was compared across a wide range of MFW (e.g., from 100 to 5000 words).
Performance Data and Comparative Analysis
Quantitative Performance of Cosine Distance
The following table summarizes key performance data for the Cosine Distance measure from experimental results, highlighting its effectiveness and the impact of document length.
Table 1: Performance of Cosine Distance with a Bag-of-Words Model (N=260 MFW) [19]
| Document Length (Words) | Log-Likelihood-Ratio Cost (Cllr) | Interpretation |
|---|---|---|
| 700 | 0.70640 | Moderate discrimination accuracy |
| 1,400 | 0.45314 | Good discrimination accuracy |
| 2,100 | 0.30692 | Very good discrimination accuracy |
The data demonstrates a clear trend: increasing the amount of available text consistently improves system performance. This is a fundamental principle in forensic text comparison, as larger sample sizes provide a more stable and representative estimate of an author's style [6] [19].
Comparative Performance of Delta Measures
Experiments comparing different distance measures provide clear evidence for the superiority of Cosine Distance and the value of normalization.
Table 2: Comparison of Distance Measure Performance (Clustering Quality via ARI) [21]
| Distance Measure | Key Characteristic | Performance with Standard Z-scores | Performance with Vector Normalization |
|---|---|---|---|
| Cosine Delta (Delta Cos) | Insensitive to vector magnitude | High and Robust (e.g., ARI >90%) | (Inherently normalized) |
| Burrows's Delta (L1) | Manhattan distance, sensitive to magnitude | Moderate (worse than Cosine) | Dramatically Improved (~matches Cosine) |
| Argamon's Delta Q (L2) | Euclidean distance, more sensitive to outliers | Poor (worse than L1) | Dramatically Improved (identical to Cosine) |
| L4 Delta | Highly sensitive to single outliers | Very Poor | Improved, but still worse than others |
The results in Table 2 strongly support the Key Profile Hypothesis (H2). The dramatic improvement seen in all measures after vector normalization—which does not reduce outliers but standardizes amplitudes—indicates that the pattern of word use, not the magnitude of frequency differences, is the primary carrier of authorship signal [21]. The robustness of Cosine Delta across a wide range of MFW makes it a particularly reliable choice.
The Scientist's Toolkit: Essential Research Reagents
The following table details key computational "reagents" essential for conducting experiments in score-based forensic text comparison.
Table 3: Essential Materials and Tools for Score-Based Forensic Text Comparison Research
| Item / Concept | Function in the Experimental Protocol |
|---|---|
| Reference Corpus | A collection of texts from many authors used to establish the background population and to select the N Most Frequent Words (MFW) for the model. Its relevance to the case context is critical for validation [20]. |
| Bag-of-Words (BoW) Model | The foundational data representation model that transforms unstructured text into a numerical matrix, allowing for quantitative analysis. It records word frequencies while discarding word order [19]. |
| Z-score Normalization | A statistical procedure that standardizes the frequency of each word across the corpus. It expresses each word's frequency in a text as the number of standard deviations it is from the mean frequency across all texts, ensuring comparability [21]. |
| Most Frequent Words (MFW) | The set of feature words (e.g., N=260, 500, 1000) used to represent the texts. These common, often function words (e.g., "the", "and", "of") are believed to be less topic-dependent and more reflective of subconscious stylistic habits [19] [21]. |
| Likelihood Ratio (LR) Framework | The statistical paradigm for quantifying the strength of evidence. It evaluates the probability of the evidence under two competing propositions: the same-author hypothesis and the different-author hypothesis [19] [20]. |
| Log-Likelihood-Ratio Cost (Cllr) | A primary metric for evaluating the performance and validity of an LR system. It penalizes both misleading and weak LRs, providing a single scalar measure of system quality. Lower values indicate better performance [19] [20]. |
| Tippett Plot | A graphical tool for visualizing the calibration and discrimination of a forensic evaluation system. It shows the cumulative proportion of LRs for same-source and different-source comparisons, allowing researchers to assess the validity of the computed LRs [19] [20]. |
The integration of multiple analytical procedures through logistic regression represents a paradigm shift in forensic text comparison (FTC) methodology. This approach, termed "fusion systems," enhances the reliability and evidential weight of textual evidence by combining diverse feature sets and analytical techniques into a single, statistically robust model. Within FTC research, this addresses a core challenge: deriving scientifically defensible and demonstrably reliable conclusions from complex, high-dimensional linguistic data. The fusion of systems via logistic regression provides a framework for quantifying the strength of evidence in a manner that is both transparent and empirically validated, which is critical for meeting the stringent requirements of legal admissibility [20].
Core Conceptual Framework
The Role of Logistic Regression as a Fusion Engine
Logistic regression serves as the mathematical engine for fusing multiple procedures in forensic text analysis. Its primary function is to combine multiple predictor variables—which may originate from distinct analytical techniques—into a single, unified probability model. The model outputs a likelihood ratio (LR) or a posterior probability, quantifying the strength of evidence for a particular proposition (e.g., that two documents were written by the same author) [20].
The standard logistic regression function for a two-class problem is: ( P(Y=1 | X) = \frac{1}{1 + e^{-(\beta0 + \beta1 X1 + \ ... \ + \betap Xp)}} ) Where ( P(Y=1 | X) ) is the posterior probability of class membership, ( \beta0 ) is the intercept, ( \beta1 ... \betap ) are regression coefficients, and ( X1 ... Xp ) are input features from the fused procedures [22].
The Imperative of Validation in Forensic Text Comparison
Empirical validation is a cornerstone of forensic fusion systems. Research demonstrates that validation must be performed by replicating the conditions of the case under investigation using relevant data; otherwise, the trier-of-fact may be misled. The calculated LRs should be assessed using metrics like the log-likelihood-ratio cost (( C_{llr} )) and visualized using Tippett plots to evaluate their discriminative power and calibration [20].
Technical Implementation: Fused Lasso Logistic Regression (FLLR)
Algorithm and Mathematical Formulation
For high-dimensional data common in forensic analysis, such as spectral data or n-gram frequencies, the Fused Lasso Logistic Regression (FLLR) is particularly effective. FLLR introduces two penalty terms to the standard logistic regression loss function [22]:
( \min{\beta0, \beta} \left{ \sum{i=1}^N \left[ yi (\beta0 + xi^T \beta) - \log(1 + e^{\beta0 + xi^T \beta}) \right] + \lambda1 \sum{j=1}^p |\betaj| + \lambda2 \sum{j=2}^p |\betaj - \beta_{j-1}| \right} )
The table below details the components of the FLLR objective function:
Table 1: Components of the Fused Lasso Logistic Regression Objective Function
| Component | Mathematical Expression | Function in the Model | ||
|---|---|---|---|---|
| Log-Likelihood | ( \sum{i=1}^N \left[ yi (\beta0 + xi^T \beta) - \log(1 + e^{\beta0 + xi^T \beta}) \right] ) | Measures the model's fit to the training data. | ||
| Lasso Penalty (λ₁) | ( \lambda1 \sum{j=1}^p | \beta_j | ) | Promotes sparsity by forcing irrelevant feature coefficients to exactly zero. |
| Fusion Penalty (λ₂) | ( \lambda2 \sum{j=2}^p | \betaj - \beta{j-1} | ) | Encourages smoothness by forcing coefficients of adjacent, correlated features to be similar. |
Advantages for Forensic Text Comparison
FLLR provides specific advantages for FTC research [22]:
- Grouping Property: It automatically identifies and selects/deselects groups of highly correlated variables (e.g., adjacent spectral peaks, syntactically similar n-grams) together, treating them as a single, interpretable unit.
- Data-Dependent Binning: The fusion penalty naturally resolves the "peak misalignment" problem, analogous to dialectal or stylistic variation in text, by creating data-dependent bins where adjacent features receive identical coefficients.
- Enhanced Interpretability: The resulting model is more interpretable than those from other ℓ₁-regularization methods, as it produces a sparse set of coefficient profiles where only meaningful groups of features have non-zero weights.
Experimental Protocols and Quantitative Assessment
Dirichlet-Multinomial Model with Logistic Regression Calibration
A documented experimental protocol for FTC involves calculating likelihood ratios (LRs) via a Dirichlet-multinomial model, followed by logistic regression calibration. This two-stage fusion process ensures that the derived LRs are well-calibrated and forensically valid [20]. The workflow can be summarized as follows:
Quantitative Performance of Machine Learning Classifiers
Recent applied research in Fused Filament Fabrication (FFF) 3D printing, which employs a similar sensor-fusion and ML classification approach, provides a quantifiable performance benchmark for fused systems. The following table summarizes the accuracy of various classifiers in a multi-sensor fusion setup, distinguishing between "Healthy," "Partially clogged," and "Fully clogged" nozzle conditions [23].
Table 2: Performance Metrics of Machine Learning Classifiers in a Fused Sensor System [23]
| Machine Learning Model | Accuracy (%) | Key Strengths & Limitations |
|---|---|---|
| Gradient Boosting Classifier (GBC) | 99.92% | Best-performing model with perfect classification across all classes; suited for real-time deployment. |
| Random Forest (RF) | 99.84% | Exhibits high accuracy, robust for complex datasets. |
| Decision Tree (DT) | 99.51% | High accuracy and good interpretability. |
| Support Vector Machine (SVM) | Slightly Lower | Demonstrated slightly lower performance than tree-based models. |
| K-Nearest Neighbors (KNN) | Slightly Lower | Performance not on par with top-tier models. |
| Naïve Bayes (NB) | Lowest | Showed limitations in distinguishing between the conditions. |
The experimental setup for generating this data involved a Cartesian 3D printer equipped with a Rotary Encoder, Load Cell, and Thermocouple sensor, collecting 718,200 data points across the three conditions following a Taguchi L9 Design of Experiments (DoE) [23].
The Scientist's Toolkit: Essential Research Reagents & Materials
The implementation of a fused system for logistic regression in a research or casework context requires a suite of essential "research reagents" — which, in the context of computational forensics, translates to core data, software, and methodological components.
Table 3: Essential Research Reagents for Fused Systems with Logistic Regression
| Reagent / Material | Function in the Fused System |
|---|---|
| Relevant Text Corpora | Provides empirically validated, case-relevant data for system training and validation, crucial for avoiding misleading results [20]. |
| Dirichlet-Multinomial Model | Serves as a generative statistical model for calculating initial likelihood ratios based on text features before logistic regression calibration [20]. |
| Fused Lasso Logistic Regression (FLLR) | The core algorithm that performs feature selection, groups correlated features, and builds the classifier, especially for high-dimensional data [22]. |
| Logistic Regression Calibration | A post-processing step that adjusts the output of a base model (e.g., Dirichlet-multinomial) to produce well-calibrated likelihood ratios [20]. |
| Split Bregman (SB) Algorithm | An efficient computational algorithm used to solve the optimization problem posed by the FLLR, handling its non-smooth penalty terms [22]. |
| Validation Metrics (Cllr) | The log-likelihood-ratio cost is a primary metric for assessing the performance and accuracy of the calculated likelihood ratios [20]. |
| Visualization Tools (Tippett Plots) | Graphical tools for visualizing the distribution of LRs for both same-source and different-source hypotheses, aiding in the interpretation of system performance [20]. |
Fused systems that leverage logistic regression represent a significant advancement in forensic text comparison methodology. By combining multiple procedures—whether different feature sets or sequential statistical models—into a single, calibrated framework, these systems enhance the objectivity, reliability, and interpretability of textual evidence. The implementation of sophisticated techniques like Fused Lasso Logistic Regression directly addresses the unique challenges of high-dimensional, correlated linguistic data. As this field progresses, the rigorous empirical validation of these fused systems, using relevant data and casework conditions, remains paramount to their acceptance and success within the scientific and legal communities.
Forensic text comparison methodology research has evolved significantly with the integration of computational linguistics and artificial intelligence. Psycholinguistics, an interdisciplinary field bridging linguistics and psychology, provides the theoretical foundation for identifying measurable links between psychological states and linguistic output [3]. Within a forensic context, this involves applying Natural Language Processing (NLP) techniques to written or spoken text—such as emails, instant messages, or transcribed interviews—to identify patterns suggestive of deception or specific emotional states [3] [24]. The core objective is not to calculate guilt directly, but to create a data-driven subset of suspects from a larger population based on key psycholinguistic variables, thereby focusing investigative resources [3].
This technical guide outlines the core principles, methodologies, and experimental protocols for psycholinguistic analysis of deception and emotion, framing them within the rigorous demands of forensic text comparison.
Core Psycholinguistic Features in Forensic Analysis
The psycholinguistic framework for forensic analysis rests on several core features that serve as proxies for cognitive and emotional states. The table below summarizes the primary features and their forensic interpretations.
Table 1: Core Psycholinguistic Features for Deception and Emotion Analysis
| Feature Category | Specific Features | Forensic Interpretation & Significance |
|---|---|---|
| Deception-Associated | N-grams, Pronoun usage, Sensory details, Negations [3] [25] | Lower detail, fewer spontaneous corrections, more formulaic language; liars are less forthcoming and less convincing [26]. |
| Emotional | Anger, Fear, Sadness, Joy, Neutrality [27] [25] | Increased negative emotions like fear and anger may suggest stress or self-preservation in deceptive suspects [3]. |
| Stylometric & Structural | Vocabulary richness, Punctuation character ratio, Average characters per word, Syntactic structures [6] | Provides a unique authorial "fingerprint"; robust features for authorship attribution and comparison [6]. |
| Subjective Content | Subjectivity vs. Objectivity, Overconfidence [3] | High subjectivity and overconfidence have been correlated with dishonesty and a higher probability of untruthfulness [3]. |
Technical Methodologies and Experimental Protocols
Implementing a psycholinguistic analysis framework requires a structured pipeline, from data handling to model application. The following workflow and protocols detail this process.
Data Collection and Pre-processing Protocol
The initial phase involves gathering and preparing textual data for analysis.
- Data Sources: Data can be sourced from fictional scenarios generated by Large Language Models (LLMs) for experimental validation [3], or from real-world datasets such as real courtroom trial clips [26] [25], chat logs from criminal proceedings [6], or recorded police interviews [3].
- Pre-processing Steps: Text undergoes cleaning, normalization, and tokenization to enhance data quality [28]. This includes removing noise and irrelevant data, converting text to lowercase, and segmenting text into words or sentences. This step is crucial for the efficiency of subsequent feature extraction.
Feature Extraction and Modeling Protocol
This protocol details the process of converting raw text into quantifiable psycholinguistic features.
- Emotional Feature Extraction: Use a pre-trained large language model like RoBERTa for emotion classification [25]. The model is fine-tuned on a dataset annotated with emotional features (e.g., joy, sadness, anger, fear) to automatically generate emotional feature values from the target interrogation or text data [25].
- Deception and Stylometric Feature Extraction: Apply NLP libraries and techniques to extract relevant features.
- Model Integration and Training: Combine the extracted emotional, deception-related, and stylometric features. Feed this combined feature set into a machine learning classifier. The LieXBerta model, which uses XGBoost, demonstrates this approach, integrating RoBERTa-based emotion features with other inputs for deception detection [25].
Analysis and Validation Protocol
The final phase involves interpreting model outputs and validating the findings within a forensic context.
- Likelihood Ratio (LR) Framework: For authorship attribution, strength of evidence should be evaluated using a multivariate Likelihood Ratio framework [6]. This method quantifies the strength of evidence for one author versus another based on stylometric features.
- Performance Metrics: System performance is assessed using metrics like log-likelihood ratio cost (Cllr), discrimination accuracy, and F1-scores [25] [6]. For example, a well-trained model might achieve an accuracy of 87.5% in deception detection [25], while authorship attribution systems can reach 94% discrimination accuracy with sufficient text samples [6].
- Cross-Domain Generalization: Evaluate models on multiple, heterogeneous datasets to ensure performance is not limited to a single domain [26]. This is critical for real-world deployment where recording conditions and communication styles vary.
The Scientist's Toolkit: Essential Research Reagents
Successful experimentation in this field relies on a suite of computational tools, datasets, and algorithms.
Table 2: Essential Research Reagents for Psycholinguistic Analysis
| Reagent Category | Specific Tool / Dataset / Model | Function & Application |
|---|---|---|
| Software & Libraries | Empath [3] | Python library for analyzing lexical cues to deception via statistical comparison and word embeddings. |
| RoBERTa (LLM) [25] | A robustly optimized BERT model used for extracting nuanced emotional features from text. | |
| XGBoost [25] | A gradient boosting classifier that effectively integrates multiple feature types for final deception detection. | |
| OpenFace [26] | Tool for extracting facial Action Units (AUs); used in multimodal deception detection. | |
| Benchmark Datasets | Real-life Trial Deception Dataset [26] | Contains video clips from real courtroom proceedings with truthful/deceptive labels based on trial outcomes. |
| Bag-of-Lies [26] | A multimodal dataset with annotated deceptive and truthful samples, integrating video, audio, gaze, and EEG. | |
| MU3D (Miami University Deception Database) [26] | Features videos of participants giving truthful and deceptive opinions about liked/disliked persons. | |
| Core Algorithms | Multivariate Kernel Density Formula [6] | Used to estimate the strength of evidence (Likelihood Ratio) in forensic text comparison. |
| Latent Dirichlet Allocation (LDA) [3] | A topic modeling technique used to identify underlying thematic patterns in suspect narratives. | |
| Neural Networks (NN) [27] | Deep learning models proven highly effective in multi-class emotion detection tasks from text. |
The integration of psycholinguistics with advanced NLP and machine learning represents a significant advancement in forensic text comparison methodology. By leveraging structured protocols for analyzing deception, emotion, and stylometry, researchers and forensic professionals can derive more objective, data-driven insights from textual evidence. Future progress in the field hinges on overcoming challenges related to cross-domain generalization, model interpretability, and the development of more comprehensive, forensically realistic datasets. The methodologies outlined in this guide provide a technical foundation for developing robust, reliable, and scientifically defensible tools for the analysis of forensic text evidence.
The Impact of Sample Size on System Performance and Reliability
In forensic science, the requirement for valid and reliable methods is enshrined in many jurisdictions and highlighted by authoritative reports such as the 2009 National Academy of Sciences report and the 2016 President's Council of Advisors on Science and Technology [29]. Forensic Text Comparison (FTC), also referred to as forensic authorship analysis, is the discipline concerned with comparing textual documents to evaluate the strength of evidence for whether they originated from the same or different authors. A scientifically defensible FTC methodology relies on quantitative measurements, statistical models, and the Likelihood Ratio (LR) framework, all of which must be empirically validated [5].
The sample size—encompassing the number of authors in a reference population and the amount of text available per author—is a critical factor influencing this validation. It directly affects the fundamental metrics of system performance: validity (the system's ability to correctly discriminate between same-source and different-source authors) and reliability (the consistency of its results upon repeated testing) [29]. This guide examines the impact of sample size on FTC system performance and reliability, providing a technical framework for researchers to design robust validation experiments.
Core Concepts: Validity, Reliability, and the LR Framework
Validity vs. Reliability in Forensic Comparison
In the context of forensic comparison sciences:
- Validity refers to whether a method measures what it is intended to—that is, its ability to accurately separate same-source and different-source samples. A highly valid system achieves high discrimination accuracy [29].
- Reliability refers to the consistency of the results if the analyses were repeated by the same expert or system (repeatability) or by different experts and methods (reproducibility) [29].
It is crucial to recognize that high validity does not automatically guarantee high reliability. Advanced systems may yield better overall validity but not necessarily higher reliability, and sometimes the opposite is true [29].
The Likelihood Ratio (LR) as a Measure of Evidence Strength
The Likelihood Ratio (LR) framework is the logically and legally correct approach for evaluating forensic evidence, including textual evidence [5]. The LR quantifies the strength of the evidence under two competing hypotheses:
- Prosecution hypothesis ((H_p)): The questioned and known documents were written by the same author.
- Defense hypothesis ((H_d)): The questioned and known documents were written by different authors.
The LR is calculated as: [ LR = \frac{p(E|Hp, I)}{p(E|Hd, I)} ] where (p(E|Hp, I)) is the probability of observing the evidence (E) given that (Hp) is true, and (p(E|Hd, I)) is the probability of E given that (Hd) is true. The variable (I) represents relevant background information about the case [29]. An LR greater than 1 supports the prosecution's hypothesis, while an LR less than 1 supports the defense's hypothesis.
The Impact of Sample Size: Quantitative Evidence
The size and composition of the datasets used for system development and validation are paramount. The following tables summarize key findings from empirical studies on how sample size affects FTC system performance.
Table 1: Impact of the Number of Authors in a Reference Population on System Stability
| Number of Authors (Per Database) | Key Findings on System Performance & Reliability |
|---|---|
| Small number | Higher degree of uncertainty and inconsistency in output (poorer reliability); observed data does not adequately support density estimation, resulting in extrapolation [29]. |
| 30-40 authors | Overall validity (performance) reaches the same level as a system with 720 authors; variability of system performance starts to converge [30]. |
| 720 authors | Used as a benchmark for maximum stability; systems with 30-40 authors per database were able to match its performance level [30]. |
Table 2: Impact of Text Sample Size (per author) on Discriminatory Accuracy
| Text Sample Size (Words per Author) | Discrimination Accuracy (Cllr metric*) | Key Findings |
|---|---|---|
| 500 words | ~76% (Cllr = 0.68258) | Even small samples provide useful discrimination, but with lower accuracy [6]. |
| 1000 words | Data not specified in source | Intermediate performance [6]. |
| 1500 words | Data not specified in source | Intermediate performance [6]. |
| 2500 words | ~94% (Cllr = 0.21707) | Larger samples significantly improve discriminability, increase magnitude of correct LRs, and decrease magnitude of erroneous LRs [6]. |
*A lower Cllr value indicates better system validity. A Cllr of 0 represents perfect accuracy, while a Cllr of 1 indicates a non-informative system [29] [6].
Experimental Protocols for Assessing Sample Size Effects
To empirically validate the impact of sample size on an FTC system, researchers should adhere to structured experimental protocols. The following workflow outlines a comprehensive validation approach, emphasizing the conditions that must be replicated to ensure forensic relevance.
Defining Case Conditions and Data Selection
The first and most critical step is to define the specific conditions of the casework the system is intended to address. A failure to do so can mislead the trier of fact [5].
- Requirement 1: Reflect Case Conditions: Validation must replicate the conditions of the case under investigation. A common challenging condition in FTC is topic mismatch, where the known and questioned documents differ in subject matter, which can affect writing style [5].
- Requirement 2: Use Relevant Data: The data used for validation must be relevant to the case. This includes matching the genre (e.g., chat logs, reviews), topic, and linguistic variety of the texts [5]. Using a corpus like the Amazon Authorship Verification Corpus (AAVC), which contains reviews across 17 different topics, allows for controlled simulation of topic mismatch scenarios [5].
Text Pre-processing and Feature Extraction
- Text Pre-processing: The selected texts are often processed to control for variables. A common practice is to equalize document lengths, for instance, to 4 kB (approximately 700-800 words) [5] [6]. Other steps may include tokenization and normalization.
- Feature Extraction: Quantifiable stylometric features are extracted from the text. Robust features identified in research include [6]:
- Average character number per word token
- Punctuation character ratio
- Vocabulary richness measures
Model Training, LR Calculation, and System Evaluation
- Model Training & Calibration: A statistical model (e.g., a Dirichlet-multinomial model) is trained on features from known authors. The scores generated by the model are then calibrated using a method like logistic regression to convert them into interpretable LRs [29] [5].
- LR Calculation: The calibrated model is applied to comparisons between questioned and known texts, producing an LR for each comparison [5].
- System Evaluation: The system's performance is assessed using metrics that evaluate both validity and reliability. The primary metric is often the log-likelihood-ratio cost (Cllr), which evaluates both the discrimination and calibration of the LR system [29] [6]. Results are frequently visualized using Tippett plots, which show the cumulative distribution of LRs for both same-author and different-author comparisons [5]. The experiment should be repeated with varying sample sizes (number of authors and words per author) to directly measure the impact on system stability and accuracy [30] [6].
The Scientist's Toolkit: Essential Research Reagents
Table 3: Key Research Reagents and Materials for FTC Validation
| Reagent / Material | Function in FTC Research |
|---|---|
| Specialized Text Corpora (e.g., AAVC) | Provides controlled, topic-categorized text data essential for simulating real-world validation scenarios, particularly for testing topic mismatch [5]. |
| Stylometric Features (e.g., character-per-word, punctuation ratio) | Serves as quantifiable, measurable inputs for the statistical model; these features form the basis for calculating similarity and typicality [6]. |
| Statistical Models (e.g., Dirichlet-multinomial, Multivariate Kernel Density) | The computational engine that calculates the probability of the evidence under the competing hypotheses; it is used to generate scores for authorship [5] [6]. |
| Calibration Model (e.g., Logistic Regression) | Transforms the raw scores from the statistical model into well-calibrated Likelihood Ratios (LRs) that are interpretable as strength of evidence [29] [5]. |
| Performance Evaluation Metrics (e.g., Cllr, Tippett Plots) | Acts as the assessment tool to quantitatively measure system validity (Cllr) and visually demonstrate its reliability and evidential value (Tippett plots) [29] [5]. |
The empirical evidence is clear: sample size is a foundational parameter in developing valid and reliable forensic text comparison systems. Insufficient author numbers in reference databases lead to unstable and unreliable results, while inadequate text samples per author limit discriminatory power. The convergence of system reliability with 30-40 authors in a database provides a practical benchmark for researchers [30]. Furthermore, the continuous improvement in discriminability with text length, as demonstrated by the increase in accuracy from 76% with 500 words to 94% with 2500 words, underscores the critical need for substantial text samples [6].
Future research must focus on refining our understanding of "relevant data" and establishing minimum sample size requirements for different forensic text types and conditions. This requires the development of more comprehensive, forensically realistic text corpora and a deeper investigation into the interaction between sample size and other challenging factors like genre, topic, and author variability. By systematically adhering to rigorous validation protocols that prioritize both validity and reliability, the field of forensic text comparison can continue to strengthen its scientific foundation and its value to the justice system.
Navigating FTC Challenges: Topic Mismatch, Data Scarcity, and Cognitive Bias
Addressing Topic Mismatch as a Major Challenge in Authorship Analysis
Topic mismatch presents a fundamental challenge in the field of forensic authorship analysis, potentially undermining the reliability of methodologies used to attribute or verify the author of a text. Within forensic text comparison methodology research, this challenge arises when comparative texts diverge in their subject matter, leading to the conflation of an author's stable stylistic fingerprint with variable, topic-dependent lexical choices [31]. The pervasive influence of topic on vocabulary selection can artificially inflate or mask stylistic similarities, thereby compromising the analytical process. This whitepaper examines the nature of topic mismatch, explores advanced computational strategies to mitigate its effects, and provides detailed experimental protocols for researchers developing robust authorship analysis systems capable of operating effectively across diverse textual domains.
The Problem of Topic Variation in Authorship Analysis
Topic mismatch occurs when authorship analysis algorithms encounter texts with dissimilar subject matter, creating significant methodological hurdles. The primary risk involves algorithms latching onto topic-specific vocabulary rather than an author's genuine stylistic markers, which remain theoretically consistent across different writing subjects [31]. For instance, an author's emails regarding cybersecurity will naturally employ different terminology than their personal blog about culinary arts. Without proper controls, automated systems may interpret these lexical differences as evidence of different authorship rather than topic-induced variation.
The challenge intensifies with the proliferation of digital communication and the expanding application of authorship analysis to domains including forensic linguistics, cybersecurity, academic integrity verification, and digital content authentication [31]. Each domain presents unique topic variations that can confound traditional authorship attribution models. Furthermore, the emergence of AI-generated text adds complexity, as large language models (LLMs) can mimic stylistic features while introducing their own topic-based patterns that differ from human authorship [31].
Methodological Approaches to Mitigate Topic Mismatch
Traditional Machine Learning and Feature Engineering
Traditional machine learning approaches have historically relied on careful feature engineering to distill topic-independent stylistic signals. The table below summarizes the primary feature categories and their relative resilience to topic influence.
Table 1: Feature Categories for Topic-Resilient Authorship Analysis
| Feature Category | Specific Examples | Topic Resilience | Primary Function |
|---|---|---|---|
| Syntax-Based | Part-of-speech n-grams, parse tree structures, function word frequencies | High | Captures grammatical patterning largely independent of content [31] |
| Character-Level | Character n-grams, misspelling patterns, punctuation usage | Medium-High | Reflects subconscious orthographic habits [31] |
| Structural | Paragraph length, paragraph structure, discourse markers | Medium | Indicates organizational preferences [31] |
| Lexical | Vocabulary richness, word length distribution | Low-Medium | Requires careful normalization to separate style from topic [31] |
Research indicates that syntax-based features, particularly function words ("the," "and," "of") and part-of-speech patterns, demonstrate highest resilience to topic variation because they reflect grammatical patterning largely independent of content [31]. Character-level features like character n-grams also offer substantial robustness by capturing subconscious orthographic habits. Conversely, purely lexical features such as topic-specific nouns and verbs require careful handling through normalization techniques or combination with more stable feature sets.
Deep Learning and Representation Learning
Deep learning models, particularly convolutional neural networks (CNNs) and recurrent neural networks (RNNs), automatically learn hierarchical feature representations from raw text, potentially reducing reliance on manual feature engineering. These models can develop internal representations that disentangle content from style when properly regularized and trained on diverse corpora [31]. Research from 2015-2024 shows that style-based attention mechanisms and adversarial training techniques can further enhance model focus on stylistic rather than topical features [31].
The Role of Large Language Models (LLMs)
The advent of LLMs presents both opportunities and challenges for addressing topic mismatch. On one hand, LLMs' contextual understanding enables more nuanced separation of style and content through techniques like prompt engineering and fine-tuning on stylistic tasks [31]. Conversely, LLMs may inherit and amplify topic biases present in their training data, potentially introducing new forms of topic dependency. Current research (2024) explores using LLMs for data augmentation to create topic-balanced training sets and for generating style-consistent, topic-variant texts for model validation [31].
Experimental Framework for Topic Mismatch Evaluation
Cross-Topic Validation Protocol
A robust experimental framework is essential for properly evaluating authorship analysis methods under topic mismatch conditions. The following protocol provides a standardized approach:
Dataset Requirements:
- Curate or select a corpus containing multiple documents per author across distinctly different topics or domains
- Ensure balanced representation of topics across authors to prevent confounding
- Include both within-topic and cross-topic document pairs for comparison
- Recommended corpus size: Minimum 50 authors with at least 5 distinct topics each [31]
Experimental Procedure:
- Feature Extraction: Extract multiple feature types (syntactic, structural, character-level) using standardized preprocessing
- Model Training: Train authorship attribution models using two configurations:
- Within-Topic Training: Train and test on documents sharing the same topic
- Cross-Topic Training: Train on one set of topics, test on entirely different topics
- Performance Evaluation: Compare model accuracy, precision, and recall between within-topic and cross-topic conditions
- Feature Analysis: Analyze which feature types maintain discriminative power across topics using ablation studies
Table 2: Cross-Topic Validation Metrics Interpretation
| Performance Pattern | Interpretation | Recommended Action |
|---|---|---|
| High within-topic, high cross-topic | Model is robust to topic variation | Suitable for forensic applications |
| High within-topic, low cross-topic | Model is topic-sensitive | Requires feature engineering or different model architecture |
| Moderate but consistent across conditions | Model uses generalized features | May benefit from style-specific enhancements |
| Low in both conditions | Insufficient discriminative features | Needs fundamental methodology revision |
Psycholinguistic NLP Framework Integration
Incorporating psycholinguistic analysis provides an additional layer of topic resilience by focusing on cognitive patterns reflected in language. The following workflow integrates psycholinguistic features:
Diagram 1: Psycholinguistic NLP Analysis Workflow
This framework emphasizes temporal patterns in deception, emotion, and subjectivity that remain consistent across topics for individual authors. Research demonstrates that these psycholinguistic markers show greater cross-topic stability than purely lexical features [3]. Specifically:
- Deception over time calculated using libraries like Empath detects consistent linguistic patterns associated with truthfulness regardless of topic [3]
- Emotion and subjectivity trajectories track how authors express affect and opinion across different subjects
- N-gram correlation with investigative keywords focuses on stylistic implementation rather than topical content
Computational Toolkit and Reagent Solutions
The experimental protocols described require specific computational tools and analytical "reagents" to implement effectively. The table below details essential components for a robust authorship analysis pipeline.
Table 3: Research Reagent Solutions for Authorship Analysis
| Tool Category | Specific Tools/Libraries | Primary Function | Topic Resilience |
|---|---|---|---|
| Feature Extraction | Scikit-learn, NLTK, SpaCy | Extract syntactic, character-level, and structural features | Varies by feature type [31] |
| Deep Learning | TensorFlow, PyTorch, Transformers | Implement style-aware neural models with attention mechanisms | High (with proper regularization) [31] |
| Psycholinguistic Analysis | Empath, LIWC, Custom dictionaries | Quantify deception, emotion, subjectivity patterns | High [3] |
| Topic Modeling | Gensim (LDA), BERTopic | Identify and control for topic effects explicitly | N/A (diagnostic tool) |
| Data Augmentation | GPT APIs, Style transfer models | Generate topic-varied, style-consistent training data | High (when properly validated) [31] |
Implementation of these tools requires careful configuration to maximize topic resilience. For psycholinguistic analysis, the Empath library can be configured with custom categories relevant to specific forensic domains [3]. For deep learning approaches, style-aware attention mechanisms and adversarial training that explicitly penalizes topic-based predictions have shown promise in recent studies [31].
Integrated Methodological Workflow
Combining the previously described elements yields a comprehensive workflow for addressing topic mismatch in authorship analysis:
Diagram 2: Integrated Topic-Resilient Authorship Analysis
This integrated workflow emphasizes the multi-modal feature extraction approach that combines syntactic, character-level, and psycholinguistic features to build a comprehensive author profile that remains stable across topics. The cross-topic validation loop ensures that models are iteratively refined until they demonstrate sufficient topic independence for forensic application.
Future Research Directions
The field continues to evolve with several promising research trajectories for addressing topic mismatch. Cross-lingual authorship analysis presents particular challenges as topic and language effects become intertwined, requiring specialized methodologies [31]. Detection of AI-generated text necessitates approaches that can distinguish between human authorship styles and LLM outputs across diverse topics [31]. Additionally, development of more sophisticated psycholinguistic frameworks that integrate cognitive load indicators and narrative consistency metrics offers potential for enhanced topic resilience [3]. Each of these directions requires continued innovation in feature engineering, model architecture, and validation methodologies to advance the reliability of forensic authorship analysis across increasingly diverse textual domains.
Strategies for Optimizing Performance with Limited Text Samples
In forensic science, text comparison methodology is a critical discipline for analyzing written evidence in contexts such as questioned documents, anonymous communications, and digital forensics. A significant and frequently encountered challenge in this domain is the limitation of text samples available for analysis. Whether dealing with short threatening notes, forged signatures on legal documents, or abbreviated digital communications, forensic experts are often constrained by the quantity of text available for examination. This limitation directly impacts the statistical reliability and confidence of findings, as traditional text analysis methods typically require substantial corpora to establish meaningful patterns and differentiation criteria.
The fundamental challenge with limited text samples lies in achieving sufficient discriminating power while maintaining methodological rigor. As highlighted in forensic paper analysis, "persistent challenges—such as substrate variability, environmental influences, database deficiencies, and validation gaps—impede reliable forensic application" [10]. These challenges are exacerbated when working with minimal text, where the reduced feature set diminishes the analytical signal and increases vulnerability to confounding variables.
This guide synthesizes advanced computational and methodological approaches that enhance analytical performance when text samples are constrained. By integrating psycholinguistic features, optimized feature extraction protocols, and multi-technique integration, researchers can overcome sample size limitations and deliver forensically sound conclusions.
Theoretical Foundations of Text Comparison
Forensic text comparison operates on the principle that individuals exhibit consistent and distinctive patterns in their language use, which can be quantified and compared. These patterns manifest across multiple linguistic levels, from lexical choices and syntactic structures to semantic content and psychological markers.
Psycholinguistics provides a crucial theoretical framework for understanding these patterns. As defined by Adkins et al., "Psycholinguistics is an interdisciplinary area of research that bridges elements of linguistics with various branches of psychology. One of its goals is to identify and explain the links that exist between our psyche and the language we speak" [3]. This connection between psychological states and linguistic output enables the detection of subtle cues that remain consistent even in limited text samples.
The discriminatory potential of text comparison methods depends heavily on the feature extraction and representation techniques employed. In operational forensic contexts, two primary analytical paradigms have emerged:
- Text-focused approaches that analyze linguistic content and style directly from the text
- Substrate-focused approaches that examine the physical medium carrying the text [10]
Each paradigm offers distinct advantages for limited sample scenarios, with the optimal approach often involving strategic integration of both methodologies.
Methodological Framework for Limited Samples
Psycholinguistic Feature Extraction
Research demonstrates that psycholinguistic features remain detectable even in constrained text samples. Adkins et al. developed "a framework of NLP-based techniques that integrate emotion, subjectivity, narration analysis, n-gram correlation, and deception over time to act as a human feature reduction algorithm of sorts" [3]. This approach identifies suspects most highly correlated to a crime being investigated by focusing on persistent psychological patterns.
Key psycholinguistic markers for limited text analysis include:
- Deception cues: Measured over time using libraries like Empath to identify linguistic patterns associated with dishonesty
- Emotional markers: Specifically anger, fear, and neutrality levels in speech as indicators of psychological state
- Subjectivity indices: Degree of subjective versus objective language use as a potential deception indicator
- Contradictory narratives: Internal inconsistencies within the text that may suggest fabrication [3]
The temporal dynamics of these features provide critical analytical leverage when sample size is limited, as they represent underlying psychological processes rather than surface-level linguistic patterns.
Multi-Technique Integration
A singular analytical approach rarely suffices for limited text samples. Yang et al. emphasize that "given the complexity of paper and the inherent limitations of individual analytical methods, integrated multi-technique strategies are often necessary for comprehensive forensic characterization and robust differentiation" [10]. This principle applies equally to text analysis, where combining complementary techniques enhances discriminatory power.
Successful integration involves:
- Technique complementarity: Selecting methods that target different linguistic dimensions
- Feature-level fusion: Combining extracted features before pattern recognition
- Decision-level fusion: Integrating outputs from multiple analytical techniques
- Cross-validation: Using each technique to verify findings from others
This integrated approach addresses the fundamental challenge in limited sample analysis: "the reduced feature set diminishes the analytical signal and increases vulnerability to confounding variables" [10].
Corpus Expansion Strategies
When direct text samples are insufficient, strategic corpus expansion can provide necessary contextual and comparative data. This involves:
- Reference database utilization: Leveraging existing linguistic corpora for baseline comparisons
- Domain-specific collection: Gathering text from similar contexts to establish expected patterns
- Synthetic generation: Creating additional samples through controlled means (with appropriate validation)
The critical importance of comprehensive reference data is highlighted in forensic document analysis, where "database deficiencies" are noted as a significant impediment to reliable forensic application [10].
Experimental Protocols and Methodologies
Protocol 1: Psycholinguistic NLP Analysis
This protocol adapts the methodology described by Adkins et al. for deception and emotion detection in forensic text analysis [3].
Objective: To identify persons of interest from limited text samples using psycholinguistic profiling. Materials: Text samples (emails, instant messages, transcribed interviews), computational resources with Python and NLP libraries. Procedure:
- Text Preprocessing: Clean and normalize text data; segment into analyzable units if sufficient temporal data exists.
- Feature Extraction:
- Apply n-gram analysis (unigrams, bigrams, trigrams) paired with deception scores
- Calculate emotion vectors (anger, fear, neutrality) using lexicon-based approaches
- Compute subjectivity indices over time segments
- Extract entity-to-topic correlations
- Pattern Analysis:
- Apply Latent Dirichlet Allocation for thematic decomposition
- Generate word vectors for semantic analysis
- Compute pairwise correlations between feature sets
- Interpretation:
- Identify consistent psycholinguistic patterns across limited samples
- Rank features by discriminative power using statistical measures
- Generate confidence estimates for findings
Validation: Cross-validate with ground truth data where available; use bootstrapping methods to estimate reliability with small samples.
Protocol 2: Multi-Method Forensic Text Comparison
This protocol integrates multiple analytical techniques to overcome limitations of individual methods when sample size is constrained, adapting approaches from forensic paper analysis [10].
Objective: To maximize discriminating power for text comparison with limited samples through technique integration. Materials: Questioned text samples, known comparison samples, analytical instrumentation appropriate for selected techniques. Procedure:
- Primary Analysis Phase:
- Conduct spectroscopic examination (if physical substrate available)
- Perform linguistic profiling (stylometric analysis)
- Execute psycholinguistic assessment (per Protocol 1)
- Secondary Analysis Phase:
- Apply chemometric methods to integrated data sets
- Implement machine learning algorithms for pattern recognition
- Perform statistical validation on combined feature sets
- Data Integration:
- Normalize outputs from different techniques to common scale
- Apply weighted fusion based on technique reliability
- Generate combined discrimination score
Validation: Assess false positive and false negative rates using samples of known origin; establish confidence intervals for conclusions.
Quantitative Comparison of Analytical Techniques
Table 1: Performance Metrics of Text Analysis Techniques with Limited Samples
| Technique | Minimum Sample Size | Key Features Extracted | Discrimination Accuracy | Limitations |
|---|---|---|---|---|
| Psycholinguistic NLP | 150-200 words | Deception cues, emotion markers, subjectivity | 68.7% (50% similarity threshold) [3] | Requires quality textual data; context-dependent |
| N-gram Analysis | 100-150 words | Word patterns, phrase frequencies | Moderate to high (varies by domain) | Limited semantic understanding; corpus-dependent |
| Stylometric Analysis | 200-250 words | Sentence length, punctuation, readability metrics | High for authorship attribution | Requires comparable reference texts |
| Semantic Feature Extraction | 150-200 words | Topic models, entity relationships | 50% normalized similarity for 68.7% reactions [32] | Computationally intensive |
| Integrated Multi-Method | 100-150 words | Combined linguistic, psychological, physical features | Enhanced versus single methods [10] | Complex interpretation; requires expertise |
Table 2: Data Requirements and Processing Approaches for Limited Samples
| Constraint Type | Impact on Analysis | Mitigation Strategies | Validation Approach |
|---|---|---|---|
| Small word count (≤200 words) | Reduced feature extraction; statistical instability | Feature enrichment from related domains; bootstrap aggregation | Cross-validation; confidence interval reporting |
| Limited sample number (few exemplars) | Difficulty establishing representative patterns | Data augmentation; transfer learning; few-shot learning | Holdout validation; external benchmark comparison |
| Short text segments (e.g., SMS, tweets) | Context loss; limited linguistic context | Conversation threading; topic modeling; ensemble methods | Task-specific metrics; precision-recall analysis |
| Multi-modal constraints (text + substrate) | Integration challenges; conflicting signals | Weighted fusion; reliability-based selection | Separate modality assessment; integrated evaluation |
Implementation Workflow
The following workflow diagram illustrates the integrated approach for optimizing performance with limited text samples:
Figure 1: Integrated Workflow for Limited Text Sample Analysis. This diagram illustrates the sequential process for optimizing analytical performance with constrained text data, incorporating multiple feature dimensions and analytical techniques.
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 3: Research Reagent Solutions for Forensic Text Analysis
| Tool/Resource | Type | Primary Function | Application Context |
|---|---|---|---|
| Empath Library [3] | Software Library | Deception detection through statistical comparison with word embeddings | Identifying linguistic cues associated with deceptive communication |
| LIWC (Linguistic Inquiry and Word Count) | Analysis Tool | Psycholinguistic feature extraction from text | Quantifying psychological processes in written language |
| Transformer Models (BERT, RoBERTa) [3] | NLP Architecture | Contextual language understanding for credibility assessment | Deep semantic analysis of limited text samples |
| Latent Dirichlet Allocation (LDA) [3] | Algorithm | Thematic decomposition of text | Identifying latent topics in constrained text corpora |
| Word Embeddings (Word2Vec, GloVe) | NLP Technique | Semantic vector representations of words | Capturing meaning relationships in limited text |
| Named Entity Recognition (NER) System [33] | Information Extraction | Identifying and classifying entities in text | Structured information extraction from unstructured text |
| Chemometrics Software [10] | Statistical Tool | Multivariate analysis of complex datasets | Integrating multiple analytical technique outputs |
| Reference Text Corpora | Data Resource | Baseline linguistic patterns for comparison | Establishing normative patterns for specific domains |
Optimizing performance with limited text samples in forensic text comparison requires a paradigm shift from single-method approaches to integrated, multi-dimensional frameworks. By leveraging psycholinguistic features, implementing strategic technique integration, and applying rigorous validation protocols, researchers can overcome the constraints of small sample sizes. The methodologies outlined in this guide provide a roadmap for enhancing discriminating power while maintaining scientific rigor, ultimately strengthening the evidentiary value of text analysis in forensic applications. As the field evolves, continued refinement of these strategies—particularly through advanced machine learning and improved reference databases—will further augment our capability to derive meaningful insights from constrained textual evidence.
Forensic text comparison methodology research aims to provide scientifically valid and reliable means of attributing authorship to questioned texts, a task of paramount importance in judicial and national security contexts. The core challenge within this discipline lies in identifying and utilizing stylistic features that are not only distinctive to an author but also robust against variations in text type, topic, time, and text length. The selection of such resilient indicators forms the bedrock of defensible forensic text analysis, bridging the gap between theoretical stylometry and operational forensic practice. This technical guide provides an in-depth examination of the principles, experimental protocols, and feature categories that have demonstrated consistent discriminatory power across varying forensic scenarios, enabling researchers and practitioners to build more reliable authorship attribution systems.
The fundamental premise of robust stylometry rests on the concept of stylistic consistency. While content-based features may fluctuate with topic, an author's subconscious preferences for certain function words, syntactic structures, and other linguistic patterns tend to remain remarkably stable. The forensic application of these principles requires meticulous experimental design and validation to ensure that findings meet evidentiary standards. This guide synthesizes current research to establish a framework for selecting and validating stylometric features that maintain their discriminatory power across the challenging variations encountered in real-world forensic contexts.
Core Principles of Feature Robustness
Robust stylometric features share several key characteristics that make them suitable for forensic text comparison. First, they exhibit stability across domains, meaning their frequency and distribution patterns remain consistent for an author regardless of whether they are writing emails, chat messages, or formal documents. Second, they demonstrate resistance to topic influence, maintaining their statistical properties even when the subject matter changes significantly. Third, they show minimal sensitivity to text length, providing reliable measurements even with limited sample sizes, a common constraint in forensic casework.
The theoretical foundation for these properties stems from psycholinguistic research suggesting that while content vocabulary (nouns, specialized verbs) is consciously selected, function words (pronouns, prepositions, conjunctions) and certain syntactic patterns are produced automatically with little conscious control. This automaticity makes them reliable indicators of authorship because they reflect deeply ingrained linguistic habits rather than conscious stylistic choices adapted to specific communication contexts. The resilience of these features has been demonstrated across multiple languages and text types, supporting their utility in forensic applications [3] [34].
From a forensic methodology perspective, robust features must also be quantifiable, reproducible, and interpretable within a statistical framework. The likelihood ratio approach, which assesses the strength of evidence by comparing the probability of observing the evidence under competing hypotheses, has emerged as the preferred statistical framework for evaluating feature performance in forensic text comparison. This framework requires careful calibration of feature sets to ensure they provide statistically meaningful results that can withstand legal scrutiny [6].
Critical Stylometric Feature Categories
Character-Level Features
Character-level features analyze patterns below the word level, capturing subconscious orthographic preferences that are highly resistant to intentional manipulation and topic variation. These features have demonstrated particular robustness in cross-domain authorship attribution and perform well even with limited text samples.
Average characters per word: This simple ratio measures the typical word length used by an author, reflecting lexical complexity preferences. Experimental data has shown this feature to be consistently discriminative across text types and lengths, with one study reporting it as one of three most stable features across sample sizes ranging from 500 to 2500 words [6].
Character-type ratios: The proportions of vowels versus consonants, or specific punctuation marks to total characters, capture orthographic habits. The "punctuation character ratio" has been specifically identified as a robust feature maintaining discriminative power across varying sample sizes [6].
Special character frequency: The usage patterns of digits, hyphens, and capitalization can reveal individual stylistic preferences. These features have proven valuable in distinguishing between human-authored and AI-generated texts, with AI models often exhibiting distinct patterns in their usage [34] [35].
Lexical and Vocabulary Features
Vocabulary richness measures capture the diversity and sophistication of an author's lexicon, reflecting cognitive style and linguistic background. While some traditional vocabulary metrics are sensitive to text length, newer normalization approaches have improved their robustness.
Lexical diversity indices: Measures like Type-Token Ratio (TTR), Honore's Statistic, and Brunet's Index quantify vocabulary richness through different mathematical approaches. Research has identified specific implementations of vocabulary richness features that maintain stability across sample sizes, making them suitable for forensic applications [6].
Function word frequencies: The usage patterns of high-frequency words with little semantic content (prepositions, conjunctions, articles, pronouns) represent the most well-established robust feature category. Their subconscious selection and topic independence make them ideal for authorship analysis. Stylometric systems relying primarily on frequent word analysis are considered best practice in computational literary studies and have successfully distinguished between authors and between human and AI writers [36] [34].
Word length distribution: The statistical distribution of word lengths across multiple categories (1-letter words, 2-letter words, etc.) provides a more nuanced profile than simple averages. This multi-dimensional approach has proven effective in machine learning classification of human versus AI-generated texts [35].
Syntactic and Structural Features
Syntactic features capture patterns in how words are combined into phrases and sentences, reflecting deeply ingrained grammatical preferences that remain stable across writing contexts.
Part-of-speech patterns and ratios: The frequencies of specific parts of speech (nouns, verbs, adjectives, adverbs) and their ratios (e.g., noun-to-verb ratio) capture syntactic preferences. Bigram and trigram POS sequences have shown particular discriminative power, with studies using phrase patterns and part-of-speech bigrams achieving clear separation between human and AI-authored texts [34].
Sentence complexity measures: Metrics like average clause density, subordinate clause frequency, and sentence depth parse trees quantify syntactic complexity. In detection of AI-generated phishing emails, features such as clause density were identified as instrumental to model success, achieving 96% accuracy in classification tasks [35].
Syntactic constructions: Patterns like passive voice frequency, question formations, and conditional structures reveal grammatical preferences. These features have demonstrated value in psycholinguistic NLP frameworks for forensic text analysis, particularly in detecting deception and emotional states [3].
Experimental Protocols for Feature Validation
Cross-Domain Validation Protocol
A critical test for feature robustness involves validating performance across different genres or communication contexts. The following protocol establishes a systematic approach for this validation:
Corpus Construction: Compile a representative corpus containing multiple text types from the same authors (e.g., emails, formal reports, chat messages, creative writing). The corpus should include a minimum of 20-30 authors with at least 3-5 different text types per author to ensure statistical power [36].
Feature Extraction: Calculate the target stylometric features for each document in the corpus, ensuring proper normalization for text length variations. Implementation should use standardized NLP pipelines like SpaCy or NLTK for consistency [34] [35].
Stability Assessment: For each author and feature, calculate the coefficient of variation (CV) across different text types. Features with lower CV values (typically <0.3) demonstrate greater cross-domain stability. The experimental design should control for potential confounding variables such as topic, time between writing samples, and intended audience [6].
Discriminatory Power Testing: Employ machine learning classifiers (e.g., Random Forest, XGBoost) with cross-validation to assess whether the features maintain discriminative power across domains. Use metrics such as F1-score and AUC-ROC rather than simple accuracy, as they provide more robust performance assessment [35].
Statistical Analysis: Perform multivariate analysis of variance (MANOVA) to determine whether between-author differences are statistically significant compared to within-author variations across domains. This establishes whether the features provide sufficient discriminative power for forensic applications [6].
Text Length Resilience Protocol
Forensic texts often vary significantly in length, requiring features that maintain discriminative power across different sample sizes. The following protocol evaluates feature performance with varying text lengths:
Sample Preparation: From a reference corpus of known authorship, create text samples of varying lengths (e.g., 500, 1000, 1500, 2500 words). Ensure each length category contains a sufficient number of samples (minimum 30 per length) for statistical analysis [6].
Feature Extraction and Normalization: Extract target features from each sample, applying appropriate normalization techniques for features known to be length-sensitive. For vocabulary-based features, consider using mathematical transformations to reduce length dependence [6].
Performance Benchmarking: Using a likelihood ratio framework with multivariate kernel density formula, assess system performance at each text length level. Calculate log-likelihood ratio cost (Cllr) as the primary performance metric, with lower values indicating better performance [6].
Feature Stability Ranking: Rank features by their performance consistency across length categories, prioritizing those that maintain discriminative power even at lower word counts. Research has identified "Average character number per word token," "Punctuation character ratio," and specific vocabulary richness features as particularly robust across sample sizes [6].
Table 1: Performance Metrics of Stylometric Features Across Text Lengths
| Feature Category | 500 Words | 1000 Words | 1500 Words | 2500 Words | Stability Rating |
|---|---|---|---|---|---|
| Character-Level Features | 76% | 85% | 90% | 94% | High |
| Function Words | 72% | 82% | 88% | 93% | High |
| Vocabulary Richness | 65% | 78% | 85% | 91% | Medium-High |
| Syntactic Patterns | 68% | 80% | 86% | 92% | High |
| POS Bigrams | 70% | 83% | 88% | 93% | High |
Human vs. AI Discrimination Protocol
With the proliferation of AI-generated text, robust features must also discriminate between human and machine authorship. The following protocol validates this capability:
Feature Analysis: Apply Burrows' Delta method focusing on the most frequent words (typically 100-500 MFW) to identify stylistic differences. Use hierarchical clustering and multidimensional scaling (MDS) to visualize separation between human and AI texts [36].
Machine Learning Validation: Implement classifiers (XGBoost, Random Forest) using the identified robust features to quantify discrimination accuracy. Studies have reported accuracy up to 99.8% using random forest classifiers with integrated stylometric features [34] [35].
Cross-Model Generalization: Test feature performance on texts generated by LLMs not included in the original training corpus to assess generalizability beyond specific models. Research shows that while different LLMs have distinct stylistic signatures, robust features can capture underlying patterns common to AI-generated text [36] [34].
Data Presentation and Analysis
Table 2: Performance Comparison of Stylometric Detection Systems
| Study | Feature Types | Classification Method | Accuracy | Application Context |
|---|---|---|---|---|
| Zaitsu et al. (2025) [34] | Phrase patterns, POS bigrams, function word unigrams | Random Forest | 99.8% | Human vs. AI discrimination (Japanese) |
| Phishing Email Detection [35] | 47 stylometric features (imperative verbs, clause density, pronouns) | XGBoost | 96% | AI-generated phishing email detection |
| Forensic Text Comparison [6] | Character-level, punctuation, vocabulary richness | Multivariate Kernel Density (LR Framework) | 94% (2500 words) | Authorship attribution in chatlogs |
| Creative Writing Analysis [36] | Most Frequent Words (MFW) | Burrows' Delta with clustering | Clear separation | Human vs. AI creative writing |
The quantitative results presented in Table 2 demonstrate that robust stylometric features consistently achieve high discrimination accuracy across diverse application contexts. The performance variation across studies highlights the importance of feature selection tailored to specific forensic tasks. For instance, the near-perfect discrimination (99.8%) achieved in Japanese text analysis underscores the language-independent potential of carefully selected feature sets [34]. Similarly, the 96% accuracy in detecting AI-generated phishing emails demonstrates the operational utility of these features in cybersecurity applications [35].
The research consistently shows that integrated feature sets combining multiple linguistic levels (character, lexical, syntactic) outperform single-category approaches. This multimodal strategy captures complementary aspects of authorship style, creating a more comprehensive stylistic fingerprint. Furthermore, the stability of performance across languages (English, Japanese) and text types (creative writing, chat logs, emails) provides strong evidence for the robustness of the identified feature categories [34] [6] [35].
Visualization of Experimental Workflows
Workflow for Validating Robust Stylometric Features illustrates the comprehensive validation pathway for establishing feature robustness. The process begins with a diverse input corpus containing both human-authored and AI-generated texts, progresses through multi-level feature extraction, subjects these features to rigorous testing across three validation domains, and culminates in the identification of features demonstrating consistent performance across all tests.
Essential Research Reagents and Tools
Table 3: Essential Research Reagents for Stylometric Analysis
| Tool/Resource | Type | Primary Function | Application Context |
|---|---|---|---|
| Burrows' Delta | Statistical Metric | Measures stylistic similarity using most frequent words | Computational literary analysis, authorship attribution [36] |
| Empath Library | Python Library | Analyzes text against psychological categories | Deception and emotion detection in forensic text [3] |
| Multivariate Kernel Density | Statistical Method | Estimates likelihood ratios for evidence strength | Forensic text comparison framework [6] |
| NLTK/Spacy | NLP Toolkit | Text processing, feature extraction | General-purpose stylometric analysis [36] [35] |
| XGBoost/Random Forest | Machine Learning Algorithm | Classification and feature importance ranking | AI-generated text detection, authorship verification [34] [35] |
The research reagents detailed in Table 3 represent essential components of the modern stylometric analysis toolkit. These tools enable researchers to implement the experimental protocols described in previous sections and validate feature robustness according to established forensic standards. The combination of traditional statistical approaches like Burrows' Delta with modern machine learning algorithms represents the current state-of-the-art in forensic text comparison methodology [36] [35].
Specialized resources like the Empath library facilitate the integration of psycholinguistic principles into stylometric analysis, enabling detection of deceptive patterns and emotional states that may be relevant to forensic investigations [3]. Similarly, the multivariate kernel density approach within the likelihood ratio framework provides a statistically rigorous method for evaluating evidence strength, meeting the demanding standards of forensic applications [6].
The selection of robust stylometric features resilient to variation represents a cornerstone of reliable forensic text comparison methodology. Through rigorous experimental validation across domains, text lengths, and authorship types (human vs. AI), researchers can identify features with stable discriminative power suitable for evidentiary applications. The integration of character-level, lexical, and syntactic features within a multivariate statistical framework provides the most promising path forward for advancing the field.
As AI-generated text becomes increasingly sophisticated, the development and validation of robust stylometric features will grow even more critical for maintaining the integrity of forensic text analysis. Future research should focus on expanding validation protocols to include cross-linguistic applications, further refining feature normalization techniques for short texts, and developing standardized reference databases to support reliable forensic practice. Through continued methodological refinement and validation, robust stylometric features will maintain their essential role in the forensic text comparison toolkit.
Mitigating Cognitive and Reasoning Biases in Forensic Analysis
Forensic science has undergone significant transformation, with increased scrutiny on the scientific validity of its results [37]. A critical challenge in this field is cognitive bias, a class of effects through which an individual's preexisting beliefs, expectations, motives, and situational context influence the collection, perception, and interpretation of evidence during a criminal case [38]. These biases operate subconsciously, making them challenging to recognize and control, and they can affect even highly skilled, ethical practitioners [38]. This is particularly true for forensic text comparison (FTC), where the complexity of textual evidence requires rigorous methodology to ensure objective analysis [5]. This technical guide provides a comprehensive framework for identifying and mitigating cognitive biases in forensic analysis, with specific application to forensic text comparison methodology research.
Theoretical Framework: Understanding Cognitive Bias in Forensic Science
The Psychological Underpinnings of Cognitive Bias
Human cognition employs two distinct thinking systems [39]. System 1 thinking is fast, reflexive, intuitive, and low-effort, emerging from innate predispositions and learned patterns. In contrast, System 2 thinking is slow, effortful, and intentional, operating through logic and conscious rule application. Cognitive biases often originate from the overreliance on System 1 thinking, particularly in complex decision-making environments like forensic analysis [39].
Dror's Six Expert Fallacies
Cognitive neuroscientist Itiel Dror identified six expert fallacies that increase vulnerability to cognitive bias, which are particularly relevant to forensic mental health assessments and textual analysis [39]:
- The Unethical Practitioner Fallacy: The false belief that only unscrupulous professionals driven by greed or ideology are susceptible to bias.
- The Incompetence Fallacy: The misconception that biases result solely from incompetence and that technically competent evaluations are immune.
- The Expert Immunity Fallacy: The assumption that expertise itself provides protection against cognitive bias, when in fact expertise can sometimes create cognitive blind spots.
- The Technological Protection Fallacy: The overreliance on technology, algorithms, or actuarial tools as complete solutions to bias, neglecting their potential limitations and embedded biases.
- The Bias Blind Spot: The tendency to perceive others as vulnerable to bias while believing oneself to be immune.
- The Simple Solution Fallacy: The belief that general awareness or vigilance alone is sufficient to mitigate bias, without implementing structured external strategies.
Table 1: Dror's Six Expert Fallacies in Forensic Analysis
| Fallacy Name | Core Misconception | Implication for Forensic Practice |
|---|---|---|
| Unethical Practitioner | Bias reflects poor character | Fails to recognize cognitive bias as universal human trait |
| Incompetence | Bias stems only from lack of skill | Overlooks bias in technically proficient work |
| Expert Immunity | Expertise provides protection | Creates blind spots from overconfidence in experience |
| Technological Protection | Technology eliminates bias | Ignores algorithmic limitations and embedded biases |
| Bias Blind Spot | "I am less biased than others" | Prevents self-assessment and implementation of safeguards |
| Simple Solution | Vigilance alone is sufficient | Neglects need for structured, procedural countermeasures |
Dror categorizes eight specific sources of cognitive bias in forensic decision making [38]:
- Category A (Case-Specific Factors): Data (the evidence itself), reference materials, task-irrelevant contextual information, and task-relevant contextual information.
- Category B (Practitioner-Specific Factors): Base rate expectations, organizational factors, and education/training.
- Category C (Human Factors): Fundamental human cognitive architecture and brain function.
Methodological Approaches to Bias Mitigation
Linear Sequential Unmasking-Expanded (LSU-E)
Linear Sequential Unmasking-Expanded (LSU-E) is a structured protocol designed to minimize cognitive contamination by controlling the sequence and timing of information disclosure to forensic practitioners [37] [38]. The strength of LSU-E lies in its application of three evaluation parameters for any piece of information [38]:
- Biasing Power: The information's perceived strength of influence on the analysis outcome.
- Objectivity: The information's perceived extent of variability in meaning to different individuals.
- Relevance: The information's perceived relevance to the specific analytical task.
Diagram 1: Linear Sequential Unmasking-Expanded (LSU-E) Workflow
The Likelihood-Ratio Framework for Forensic Text Comparison
For forensic text comparison, the Likelihood-Ratio (LR) framework provides a statistically robust and logically sound method for evaluating evidence, helping to minimize subjective interpretation [5]. The LR framework quantitatively expresses the strength of evidence by comparing two competing hypotheses [5]:
LR = p(E|Hp) / p(E|Hd)
Where:
- p(E|Hp): Probability of the evidence assuming the prosecution hypothesis (similarity)
- p(E|Hd): Probability of the evidence assuming the defense hypothesis (typicality)
This framework forces explicit consideration of alternative explanations and provides transparent, quantifiable measures of evidential strength. Empirical validation is critical and must replicate case conditions using relevant data [5].
Blind Verification and Evidence Lineups
Blind verification ensures that those performing secondary analyses maintain independence from the original examiner's conclusions [38]. This prevents confirmatory bias where subsequent analysts might be influenced by knowing the initial results.
Evidence lineups involve presenting several known-innocent samples alongside the suspect sample during comparative analyses [38]. This approach counteracts the inherent assumption of guilt that can occur when only a single suspect sample is provided, forcing analysts to make genuine comparisons rather than simple match/no-match decisions.
Practical Implementation for Forensic Practitioners
Practitioner-Implementable Bias Mitigation Strategies
Individual practitioners can implement specific actions to minimize cognitive bias, even without formal laboratory protocols [38]:
Table 2: Practitioner-Implementable Bias Mitigation Actions
| Source of Bias | Practical Mitigation Actions |
|---|---|
| Data (Evidence) | Educate submitters about masking features not relevant to analysis; request avoidance of potentially biasing context in submissions. |
| Reference Materials | Analyze evidence before reference materials; request multiple reference materials in "lineups"; document evaluation criteria prior to analysis. |
| Task-Irrelevant Context | Avoid reading unnecessary submission documentation; if exposed, document what was learned and when; communicate need to avoid cognitive contamination. |
| Task-Relevant Context | Document what contextual information was received, when, and its potential impact on analysis; distinguish between relevant and irrelevant information. |
| Base Rate Expectations | Consciously consider alternative outcomes at each analysis stage; reorder notes to support pseudo-blinding techniques. |
| Organizational Factors | Examine laboratory protocols for sources of undue influence; advocate for policies that support cognitive independence. |
| Education & Training | Request ongoing training about cognitive bias; review educational materials for consistency with bias mitigation best practices. |
| Personal & Human Factors | Document justification for analytical decisions contemporaneously; recognize symptoms of stress and fatigue; practice self-care. |
Validation in Forensic Text Comparison
For forensic text comparison methodology research, proper validation is essential. The research must [5]:
- Reflect case conditions under investigation, including challenging factors like topic mismatch between documents.
- Use relevant data to the case, accounting for linguistic variables such as genre, formality, and author emotional state.
Without proper validation addressing these requirements, the trier-of-fact may be misled in their final decision [5].
Experimental Protocols for Forensic Text Analysis
Psycholinguistic NLP Framework for Deception Detection
Advanced forensic text analysis can employ psycholinguistic Natural Language Processing (NLP) frameworks to identify patterns suggestive of deception or emotional states [3]. The experimental protocol involves:
Phase 1: Feature Extraction
- Apply n-gram analysis paired with deception, emotion, and subjectivity tracking over time
- Use Python libraries like Empath to calculate deception levels
- Quantify anger, fear, and neutrality levels in speech over time
- Measure correlation to investigative keywords and phrases
- Identify contradictory narratives
Phase 2: Pattern Analysis
- Implement Latent Dirichlet Allocation for topic modeling
- Utilize word embeddings for semantic analysis
- Calculate pairwise correlations between entities and topics
- Apply statistical models to identify significant deviations from baseline behavior
Phase 3: Interpretation
- Focus on forensic temporal predisposition to certain behaviors
- Create subsets of suspects based on key variables rather than calculating guilt
- Integrate findings with case context using appropriate safeguards
Quantitative Requirements for Validation Studies
Table 3: Minimum Validation Requirements for Forensic Text Comparison Methods
| Validation Component | Minimum Standard | Enhanced Protocol |
|---|---|---|
| Sample Size | Sufficient to achieve statistical power | Larger samples representing population diversity |
| Topic Variability | Include some cross-topic comparisons | Deliberate mismatch on challenging topics |
| Author Pool | Multiple authors with different backgrounds | Representative of casework demographic variation |
| Text Length | Realistic lengths comparable to casework | Multiple length categories with minimum thresholds |
| Statistical Measures | Log-likelihood-ratio cost (Cllr) | Tippett plots with confidence intervals |
| Error Rates | Clear documentation of false positive/negative rates | Cross-validation under different conditions |
The Scientist's Toolkit: Essential Research Reagents
Table 4: Essential Methodological Tools for Forensic Text Comparison Research
| Tool Category | Specific Solution | Research Function |
|---|---|---|
| Statistical Frameworks | Likelihood-Ratio Framework | Quantitatively evaluates evidence strength under competing hypotheses [5] |
| Validation Metrics | Log-Likelihood-Ratio Cost (Cllr) | Measures system performance across discrimination and calibration [5] |
| Data Visualization | Tippett Plots | Graphically represents system performance and error rates [5] |
| Psycholinguistic Analysis | Empath Library | Calculates deception levels and emotional content in text [3] |
| Topic Modeling | Latent Dirichlet Allocation (LDA) | Identifies underlying thematic structures in textual evidence [3] |
| Stylometric Features | N-grams, Character/POS n-grams | Captures author-specific stylistic patterns [5] |
| Author Verification | Dirichlet-Multinomial Model | Statistical approach for authorship attribution with calibration [5] |
| Information Management | LSU-E Worksheets | Facilitates implementation of sequential unmasking protocols [38] |
Diagram 2: Forensic Text Comparison Methodology with Bias Controls
Mitigating cognitive and reasoning biases in forensic analysis requires a multifaceted approach combining theoretical understanding, methodological rigor, and practical safeguards. For forensic text comparison methodology research, this entails implementing structured protocols like Linear Sequential Unmasking-Expanded, adopting the Likelihood-Ratio framework for evidence evaluation, conducting proper validation with relevant data, and empowering individual practitioners with actionable bias mitigation strategies. By systematically addressing cognitive biases at both institutional and individual levels, forensic science can enhance the reliability, validity, and scientific defensibility of textual evidence analysis, ultimately contributing to more just and accurate legal outcomes.
Ensuring Validity: Benchmarking FTC Systems and Assessing Performance
The Critical Role of Empirical Validation with Case-Relevant Data
Forensic Text Comparison (FTC) involves the analysis of textual evidence to address questions of authorship, playing a critical role in legal proceedings. The 2009 National Academy of Sciences report highlighted a critical need for scientific validation across many forensic disciplines, noting that much evidence was presented without meaningful validation, error rate determination, or reliability testing [40]. In response, the field of forensic linguistics has increasingly moved toward quantitative, statistically grounded methodologies that meet modern evidentiary standards for scientific reliability [5].
A fundamental requirement for scientific validity in forensic science involves empirical validation performed by replicating case conditions using relevant data. This paper examines the critical importance of these validation requirements specifically within FTC, demonstrating how overlooking case-specific factors can mislead legal decision-makers and undermine the reliability of forensic conclusions [5] [20]. We explore the theoretical framework, methodological approaches, and practical implementation of empirically validated FTC, with particular attention to the challenging factor of topic mismatch between documents.
Methodological Framework: The Likelihood Ratio Approach
Theoretical Foundation
The Likelihood Ratio (LR) framework provides the logical and legal foundation for evaluating forensic evidence, including textual evidence. The LR quantitatively expresses the strength of evidence by comparing two competing hypotheses [5]:
- Prosecution Hypothesis (Hp): The known and questioned documents were produced by the same author
- Defense Hypothesis (Hd): The known and questioned documents were produced by different authors
The LR is calculated as:
LR = p(E|Hp) / p(E|Hd)
where p(E|Hp) represents the probability of observing the evidence (E) if the prosecution hypothesis is true, and p(E|Hd) represents the probability of the same evidence if the defense hypothesis is true [5].
Interpretation Framework
The LR provides a continuous measure of evidentiary strength [5]:
- LR > 1: Evidence supports Hp
- LR = 1: Evidence has no diagnostic value
- LR < 1: Evidence supports Hd
The magnitude of the LR indicates the strength of support, with values further from 1 providing stronger evidence. This framework enables transparent, reproducible evaluations that are intrinsically resistant to cognitive biases when properly implemented [5].
Table 1: Likelihood Ratio Interpretation Guide
| LR Value | Interpretation | Evidentiary Strength |
|---|---|---|
| >10,000 | Very strong support for Hp | Extremely strong |
| 1,000-10,000 | Strong support for Hp | Strong |
| 100-1,000 | Moderately strong support for Hp | Moderately strong |
| 10-100 | Moderate support for Hp | Moderate |
| 1-10 | Limited support for Hp | Limited |
| 1 | No diagnostic value | None |
| 0.1-1 | Limited support for Hd | Limited |
| 0.01-0.1 | Moderate support for Hd | Moderate |
| <0.01 | Strong support for Hd | Strong |
The Critical Validation Requirements
Core Principles
Empirical validation in FTC must satisfy two fundamental requirements to be forensically relevant [5]:
- Reflect Case Conditions: Validation experiments must replicate the specific conditions of the case under investigation, including document type, length, register, and particularly topic alignment
- Use Relevant Data: Validation must employ data relevant to the case, including appropriate reference populations and comparable textual genres
These requirements ensure that validation studies accurately represent the challenges present in actual casework, providing meaningful information about method performance under realistic conditions.
Consequences of Inadequate Validation
When validation overlooks these requirements, the trier-of-fact (judge or jury) may be misled about the evidentiary value of the analysis. For example, validation using topically similar texts may overestimate performance when applied to casework involving topically dissimilar texts, potentially leading to incorrect weight being assigned to the evidence [5].
Experimental Design for Validation Studies
Addressing Topic Mismatch
Topic mismatch presents a significant challenge in FTC, as authors may employ different writing styles across different topics or domains. The complex nature of textual evidence encodes multiple layers of information including authorship, social group membership, and communicative situation [5]. Experimental designs must therefore account for these variables through careful experimental design.
Corpus Selection and Preparation
The Amazon Authorship Verification Corpus (AAVC) provides a suitable dataset for validation studies, containing 21,347 product reviews from 3,227 authors across 17 different product categories (topics) [5]. Key characteristics include:
- Document length control (approximately 700-800 words per review)
- Multiple documents per author (5+ reviews from most authors)
- Naturally occurring topic variation
- Real-world writing conditions
Table 2: Amazon Authorship Verification Corpus Structure
| Characteristic | Specification | Forensic Relevance |
|---|---|---|
| Number of Authors | 3,227 | Sufficient population diversity |
| Number of Documents | 21,347 | Adequate sample size |
| Topics/Categories | 17 | Enables topic mismatch studies |
| Document Length | ~700-800 words | Controlled length variable |
| Authors per Document | 5+ (majority) | Enables within-author comparisons |
| Genre | Product reviews | Real-world communicative context |
Experimental Protocols
Dirichlet-Multinomial Model Implementation
The statistical analysis employs a Dirichlet-multinomial model followed by logistic regression calibration [5]:
- Feature Extraction: Quantitative measurement of linguistic features from target documents
- Model Calculation: Computation of likelihood ratios using the Dirichlet-multinomial model
- Calibration: Application of logistic regression to calibrate raw LR outputs
- Performance Assessment: Evaluation using log-likelihood-ratio cost (Cllr) and Tippett plots
Validation Experimental Conditions
Simulated experiments should compare two conditions [5]:
- Condition 1 (Proper Validation): Replicates case conditions using relevant data with appropriate topic alignment/mismatch
- Condition 2 (Inadequate Validation): Uses convenience data without regard to case-specific conditions
Quantitative Results and Performance Metrics
Evaluation Metrics
System performance is evaluated using [5]:
- Log-likelihood-ratio cost (Cllr): A comprehensive performance measure that evaluates both discrimination and calibration
- Tippett Plots: Visual representations of the distribution of LRs for same-author and different-author comparisons
- Error Rates: Quantification of misleading evidence rates under both prosecution and defense hypotheses
Representative Findings
Studies demonstrate significantly different performance outcomes between properly validated systems and those validated without regard to case conditions. When topic mismatch is present in casework but absent from validation studies, the reported error rates may substantially underestimate actual casework error rates, potentially misleading the trier-of-fact [5].
Table 3: Performance Comparison Under Different Validation Conditions
| Validation Condition | Cllr Value | Misleading Evidence Rate | Evidentiary Strength Accuracy |
|---|---|---|---|
| Case-relevant validation | Lower | Realistically estimated | Higher |
| Convenience data validation | Higher | Underestimated | Lower |
| Topic-mismatch addressed | Appropriate for casework | Properly quantified | Case-appropriate |
| Topic-mismatch ignored | Misleading for casework | Potentially misleading | Potentially overstated |
The Scientist's Toolkit: Research Reagent Solutions
Table 4: Essential Materials and Methodological Components for FTC Validation
| Component | Function | Implementation Example |
|---|---|---|
| Reference Corpus | Provides population-appropriate data for comparison | Amazon Authorship Verification Corpus (AAVC) with 17 topics [5] |
| Statistical Model | Quantifies evidence strength using probability theory | Dirichlet-multinomial model with logistic regression calibration [5] |
| Validation Framework | Assesses system performance under case-like conditions | Paired experiments with/without case-relevant conditions [5] |
| Performance Metrics | Quantifies discrimination and calibration | Log-likelihood-ratio cost (Cllr) and Tippett plots [5] |
| Feature Set | Measures author-specific writing patterns | Linguistic features resistant to topic variation |
| Calibration Method | Adjusts raw scores to reflect actual evidentiary strength | Logistic regression calibration to improve well-calibration [5] |
Implementation Workflow
The following workflow diagram illustrates the complete process for empirically validated forensic text comparison:
Future Research Directions
Several critical research challenges require attention to advance FTC validation [5]:
- Determining Specific Casework Conditions: Systematic identification of which case conditions and mismatch types most significantly impact performance and therefore require validation
- Defining Relevant Data: Establishing clear criteria for what constitutes "relevant data" for different case types and conditions
- Data Quality and Quantity: Determining the minimum quality and quantity of data required for robust validation under various conditions
Addressing these challenges will contribute significantly to developing scientifically defensible and demonstrably reliable forensic text comparison methodologies suitable for courtroom application.
Empirical validation using case-relevant data is not merely best practice but a fundamental requirement for scientifically sound forensic text comparison. The Likelihood Ratio framework provides a mathematically rigorous approach for evaluating evidence, but its validity depends entirely on proper validation under conditions that reflect actual casework. Through replication of case conditions, use of relevant data, and comprehensive performance assessment using metrics like Cllr, forensic linguists can provide transparent, reproducible, and reliable evidence that meets modern scientific and legal standards. As the field continues to develop, addressing the research challenges of casework conditions, data relevance, and data requirements will further strengthen the scientific foundations of forensic text comparison.
In forensic text comparison (FTC), the Likelihood Ratio (LR) framework is widely recognized as the logically and legally correct method for evaluating the strength of evidence [5]. However, producing an LR is only one part of a scientifically defensible methodology; rigorously evaluating the performance of the system generating these LRs is equally critical. The Log-Likelihood-Ratio Cost (Cllr) and Tippett Plots have emerged as fundamental metrics for this validation, enabling researchers to assess both the discrimination and calibration of forensic inference systems [41] [5]. As the field moves towards more automated and semi-automated LR systems, the use of these metrics provides a standardized way to communicate system reliability and foster transparency—key requirements for evidence presented in court [41] [42].
This guide details the role, calculation, and interpretation of Cllr and Tippett Plots, framing them within the essential process of empirical validation for FTC methodologies. Validation must be performed by replicating the conditions of the case under investigation and using data relevant to the case; failure to do so can mislead the trier-of-fact [5] [20]. Cllr and Tippett Plots, when used together, provide a comprehensive picture of how well a forensic text comparison system performs under these requisite conditions.
Understanding the Log-Likelihood-Ratio Cost (Cllr)
Definition and Mathematical Formulation
The Log-Likelihood-Ratio Cost (Cllr) is a scalar metric that evaluates the overall performance of a forensic system that outputs Likelihood Ratios [41]. It was initially introduced in the context of speaker verification and later adapted for forensic speaker recognition, though its use extends to any method producing LRs, including forensic text comparison [41]. Cllr is defined by the following equation:
In this formula:
- ( N{H1} ) is the number of samples for which the prosecution hypothesis (( H_1 )) is true.
- ( N{H2} ) is the number of samples for which the defense hypothesis (( H_2 )) is true.
- ( LR{H1} ) are the LR values predicted by the system for samples where ( H_1 ) is true.
- ( LR{H2} ) are the LR values predicted by the system for samples where ( H_2 ) is true [41].
Cllr possesses a valuable probabilistic and information-theoretical interpretation. It can be conceptualized as a measure of the average cost, in information terms, incurred when the system's LRs are used to update prior odds to posterior odds. It is a strictly proper scoring rule, meaning it fosters incentives for practitioners to report accurate and truthful LRs—a critical aspect in a field where inaccurate LRs can significantly impact the criminal justice system [41].
Interpretation of Cllr Values
The Cllr metric provides a single number that summarizes system quality, with lower values indicating better performance.
Key Interpretation Guidelines:
- Cllr = 0: Indicates a perfect system. This occurs only when all ( H1 )-true LRs are infinity and all ( H2 )-true LRs are zero.
- Cllr = 1: Represents an uninformative system, equivalent to a system that always returns LR = 1, providing no evidential value [41].
- Cllr < 1: The system provides useful discrimination. The closer the value is to zero, the better the system's performance.
However, interpreting values between 0 and 1 can be challenging. A review of 136 publications on automated LR systems found that Cllr values lack clear universal patterns and depend heavily on the forensic area, specific analysis, and dataset used [41]. Therefore, while a lower Cllr is always better, what constitutes a "good" Cllr is context-dependent. For instance, in a forensic text comparison study using chatlog messages, a fused system achieved a Cllr of 0.15, which was considered a high level of performance [4].
Cllr-min and Cllr-cal: Decomposing Performance
A powerful feature of Cllr is that it can be decomposed into two components that separately assess discrimination and calibration [41].
Cllr-min: This value is obtained after applying the Pool Adjacent Violators (PAV) algorithm to the evaluation set, which mimics 'perfect' calibration. The resulting Cllr-min is an assessment of the system's discrimination power—its ability to distinguish between ( H1 )-true and ( H2 )-true samples. A low Cllr-min indicates good discrimination [41].
Cllr-cal: This is the difference between the original Cllr and Cllr-min (( Cllr\text{-}cal = Cllr - Cllr\text{-}min )). It represents the calibration cost, measuring how much performance is lost due to imperfect calibration. Calibration refers to the correctness of the assigned LR value—whether it under- or overstates the evidential strength [41].
This decomposition allows researchers to diagnose the specific weaknesses of a system. A large Cllr-cal indicates an LR system that tends to overstate or understate the strength of evidence, even if its underlying discriminatory power (Cllr-min) is good.
Tippett Plots for Visual Performance Assessment
Principles and Construction
While Cllr provides a single scalar value, a Tippett Plot offers a visual representation of the distribution of Likelihood Ratios for both ( H1 )-true and ( H2 )-true conditions [5] [4]. It is a crucial tool for gaining a more comprehensive understanding of system performance beyond a single number.
A Tippett Plot is a cumulative distribution function graph that shows:
- The proportion of ( H_2 )-true (or different-author) comparisons that yield an LR greater than or equal to a given value (typically plotted on the left y-axis).
- The proportion of ( H_1 )-true (or same-author) comparisons that yield an LR less than a given value (typically plotted on the right y-axis) [5].
The LR values are plotted on a logarithmic x-axis, which allows for a clear view of the behavior across several orders of magnitude, from strongly supporting ( H2 ) to strongly supporting ( H1 ).
Interpreting Tippett Plots
The interpretation of a Tippett Plot focuses on the separation between the two curves and their position relative to the extremes of the graph.
- Well-Performing System: The curve for ( H1 )-true trials rises sharply on the right side of the plot (high LR values), while the curve for ( H2 )-true trials falls sharply on the left side (low LR values). A large gap between the two curves indicates good discrimination [5].
- Misleading Evidence: The points where the curves cross the y-axes are particularly informative. The point where the ( H2 )-true curve meets the left y-axis indicates the proportion of misleading evidence for the prosecution (i.e., ( H2 )-true cases where LR > 1). Conversely, the point where the ( H1 )-true curve meets the right y-axis shows the proportion of misleading evidence for the defense (i.e., ( H1 )-true cases where LR < 1) [5].
Tippett Plots make the trade-offs in a system's performance immediately visible and are an indispensable complement to the Cllr metric.
Experimental Protocols and Performance Data
Example Protocol: Forensic Text Comparison with Topic Mismatch
A critical requirement for validation is that experiments must reflect real casework conditions [5]. The following protocol, derived from a study on forensic text comparison, investigates the impact of topic mismatch between known and questioned documents.
1. Hypothesis Formulation:
- ( H_1 ): The source-questioned and source-known documents were produced by the same author.
- ( H_2 ): The source-questioned and source-known documents were produced by different authors [5].
2. Data Collection and Preparation:
- Data Source: Collect a corpus of texts from multiple authors.
- Topic Manipulation: For same-author comparisons (( H1 )), ensure the known and questioned documents cover mismatched topics. For different-author comparisons (( H2 )), also use documents on mismatched topics to reflect the challenging condition of cross-topic comparison [5].
- Text Length Control: Control for the number of word tokens per author (e.g., 500, 1000, 1500, 2500 tokens) to analyze its effect on performance [4].
3. LR System and Feature Extraction:
- Feature Sets: Extract multiple sets of features from the texts. Common approaches in FTC include:
- LR Calculation: Calculate LRs for each feature set separately using their respective statistical models (e.g., Dirichlet-multinomial model for N-grams) [5] [4].
- Fusion: Improve performance by fusing the LRs from different feature sets using logistic regression calibration to obtain a single, more robust LR per comparison [4].
4. Performance Assessment:
- Calculate Cllr, Cllr-min, and Cllr-cal for the derived LRs.
- Generate Tippett Plots to visualize the distribution of LRs for ( H1 )-true and ( H2 )-true conditions [5] [4].
- Use Empirical Cross-Entropy (ECE) plots to generalize the assessment to unequal prior odds [41].
Quantitative Performance Data
The table below summarizes example Cllr values from published research to provide a benchmark for what performance might be expected in FTC. These values highlight the impact of text length and methodological choices.
Table 1: Example Cllr Values from Forensic Text Comparison Research
| Study Context | Model / System Description | Cllr Value | Notes | Source |
|---|---|---|---|---|
| Chatlog Messages (115 authors) | Fusion of MVKD & N-gram systems | 0.15 | Performance with 1500 word tokens | [4] |
| Chatlog Messages (115 authors) | MVKD system (single procedure) | >0.15 | Outperformed single N-gram procedures | [4] |
| General LR Systems | Uninformative system baseline | 1.00 | System always returns LR=1 | [41] |
| General LR Systems | Perfect system theoretical value | 0.00 | All LRs are perfectly discriminating | [41] |
Table 2: Impact of Text Length on FTC System Performance (Fused System) [4]
| Number of Word Tokens | Achieved Cllr |
|---|---|
| 500 | >0.15 |
| 1000 | >0.15 |
| 1500 | 0.15 |
| 2500 | ~0.15 (stable) |
Visualizing Workflows and Logical Relationships
Cllr Calculation and Decomposition Workflow
The following diagram illustrates the logical process of calculating and decomposing the Cllr metric from a set of evaluated Likelihood Ratios.
Tippett Plot Interpretation Logic
The diagram below outlines the key logical steps and relationships involved in interpreting a Tippett Plot to assess a forensic system's performance.
The Scientist's Toolkit: Essential Research Reagents and Materials
The following table details key components, or "research reagents," required for conducting a robust validation of a forensic text comparison system using Cllr and Tippett Plots.
Table 3: Essential Research Reagents for FTC System Validation
| Tool / Material | Function / Explanation | Critical Considerations |
|---|---|---|
| Relevant Text Corpus | Serves as the empirical data for validation. Must be relevant to casework conditions (e.g., genre, topic). | Data should replicate the conditions of the case under investigation (e.g., topic mismatch). Using irrelevant data can mislead performance assessment [5] [20]. |
| Ground Truth Labels | Authoritative information on the true author of each text. | Essential for categorizing comparisons as H1-true or H2-true. Errors here invalidate all subsequent performance metrics. |
| Feature Extraction Algorithms | Convert raw text into quantifiable features for analysis (e.g., N-grams, stylometric features). | Different feature types (MVKD, word N-grams, character N-grams) capture different aspects of authorship and can be fused for better performance [4]. |
| Likelihood Ratio Model | The core statistical model (e.g., Dirichlet-multinomial, kernel density) that calculates LRs from features. | The model must be appropriate for the feature data type and volume. Performance varies significantly between models [5] [4]. |
| Pool Adjacent Violators (PAV) Algorithm | A non-parametric transformation used to decompose Cllr into Cllr-min and Cllr-cal. | Critical for diagnosing whether poor performance stems from discrimination or calibration failures [41]. |
| Validation Software Scripts | Code (e.g., in Python, R) to calculate Cllr, generate Tippett Plots, and create ECE Plots. | Enables reproducible and standardized performance assessment. The Forensic Science Regulator mandates such empirical validation [41] [5] [42]. |
| Logistic Regression Calibration | A method to fuse LRs from multiple systems and improve overall calibration. | Can significantly enhance performance by combining the strengths of different underlying feature sets [4]. |
Forensic text comparison methodology research is dedicated to developing scientifically robust techniques for analyzing textual evidence, a cornerstone of investigations involving cybercrime, fraud, and disputed authorship. The core challenge lies in quantifying the strength of evidence presented by a text, such as an incriminating message or a forged document. Two principal methodological paradigms have emerged to meet this challenge: feature-based approaches and score-based approaches [19] [43]. Feature-based methods directly utilize linguistic properties to compute the probability of the evidence under competing hypotheses, often within a likelihood ratio framework. In contrast, score-based methods first reduce the multidimensional feature data into a single, comparable similarity score between texts, which is then converted into a likelihood ratio [19] [44]. This paper provides an in-depth technical guide to these methodologies, comparing their theoretical foundations, experimental protocols, and performance in forensic applications.
Theoretical Foundations
The Likelihood Ratio Framework
At the heart of modern forensic text comparison lies the likelihood ratio (LR) framework. It provides a coherent and logical method for evaluating evidence by comparing the probability of the evidence under two competing hypotheses: the prosecution hypothesis (e.g., the suspect and offender texts originate from the same author) and the defense hypothesis (e.g., they originate from different authors) [19]. The LR is calculated as:
- LR = P(E | Hp) / P(E | Hd)
Where P(E | Hp) is the probability of observing the evidence E given the prosecution hypothesis Hp is true, and P(E | Hd) is the probability of E given the defense hypothesis Hd is true. An LR greater than 1 supports Hp, while an LR less than 1 supports Hd [43]. The fundamental difference between feature-based and score-based methods lies in how they compute these probabilities.
Feature-Based Approaches
Feature-based approaches operate directly on a set of quantified linguistic features extracted from the text. In a typical implementation, the text is represented by a feature vector, and the system calculates the likelihood ratio by directly modeling the distribution of these feature vectors in relevant populations. This approach integrates feature extraction with probability calculation, requiring a comprehensive model for the multivariate distribution of the feature vectors under both same-author and different-author conditions [6]. The strength of the evidence is thus directly tied to the chosen feature set and the statistical model used to describe its behavior.
Score-Based Approaches
Score-based approaches decouple the comparison from the probability calculation. This two-stage process first involves calculating a similarity score between the feature vectors of two texts. In the second stage, this score is converted into a likelihood ratio by comparing it to distributions of scores derived from known same-author and different-author comparisons [19] [44]. A key advantage of this method is its ability to handle high-dimensional feature spaces by reducing them to a univariate score, simplifying the subsequent statistical modeling [19]. As noted in research, the choice between these methods is not a matter of inherent superiority but is "simply a matter of the available information" [43].
Methodological Protocols
Feature Extraction Techniques
The first step in both paradigms is the extraction of stylometric features from the text data. These features aim to capture an author's unique idiolect, or writing style.
Table 1: Common Stylometric Feature Categories
| Feature Category | Description | Examples |
|---|---|---|
| Lexical | Features based on word usage and vocabulary. | Word n-grams, vocabulary richness, word length distribution, punctuation character ratio [45] [46] [6]. |
| Syntactic | Features related to sentence structure and grammar. | Part-of-speech n-grams, sentence length, function word frequencies [45]. |
| Structural | Features concerning the overall layout and organization of the text. | Paragraph length, presence of greetings/signatures, use of capitalization [45]. |
| Content-Specific | Features tailored to a specific domain or topic. | Specific keywords or phrases relevant to the investigative context [3] [45]. |
| Character-Based | Features derived from sub-word character sequences. | Character n-grams, average characters per word [6]. |
Experimental Workflow: Feature-Based System
The following diagram illustrates the logical workflow for a feature-based likelihood ratio system, commonly used in multivariate kernel density approaches [6].
Protocol Steps:
- Text Preprocessing: The questioned (Q) and known (K) text samples are cleaned and prepared (e.g., removing metadata, standardizing encoding).
- Feature Vector Formation: A predefined set of stylometric features (e.g., from Table 1) is extracted from both Q and K, forming a multivariate feature vector that represents the stylistic profile [6].
- Probability Density Estimation: The system estimates the probability density of the observed feature vector under both Hp (same author) and Hd (different authors). This often employs multivariate density estimation techniques, such as Kernel Density Estimation, which smooths the distribution of features from a reference population to calculate the probability of the evidence [6].
- Likelihood Ratio Calculation: The final LR is computed as the ratio of the two probability densities obtained in the previous step.
Experimental Workflow: Score-Based System
The score-based approach, as implemented with a bag-of-words model, follows a different pathway, as shown below [19] [44].
Protocol Steps:
- Text Representation: The Q and K texts are converted into a numerical representation. A common method is the bag-of-words model, where texts are represented by vectors of word frequencies (often normalized, e.g., Z-score) [19] [44] [46].
- Score Calculation: A similarity or distance score is computed between the vector representations of Q and K. Studies have trialed Euclidean, Manhattan, and Cosine distance measures, with Cosine consistently demonstrating superior performance [19] [44].
- Score Distribution Modeling: The system is trained using a background corpus of text samples from many authors. Distributions of scores from known same-author comparisons and known different-author comparisons are modeled. Parametric models (e.g., Normal, Log-normal, Gamma, Weibull) are often fitted to these score distributions [19].
- Score-to-LR Conversion: The score obtained from comparing Q and K is converted into an LR. The numerator P(Score | Hp) is the probability density of that score from the same-author distribution, and the denominator P(Score | Hd) is its density from the different-author distribution [19].
Comparative Performance Analysis
Experimental studies provide quantitative insights into the performance of both methods under varying conditions.
Table 2: Performance Comparison of Feature-Based and Score-Based Methods
| Method | Key Metric | Performance Findings | Experimental Conditions |
|---|---|---|---|
| Score-Based (Bag-of-Words) | Log-Likelihood-Ratio Cost (Cllr)* | Cllr of 0.45314 achieved [19] [44]. Lower Cllr indicates better performance. | Document length: 1400 words; Cosine distance; N=260 most frequent words [19] [44]. |
| Feature-Based (Stylometric) | Discrimination Accuracy | ~94% accuracy (Cllr = 0.21707) achieved [6]. | Document length: 2500 words; Features: character-based, punctuation, vocabulary richness [6]. |
| Feature-Based (Stylometric) | Discrimination Accuracy | ~76% accuracy (Cllr = 0.68258) achieved [6]. | Document length: 500 words; Features: character-based, punctuation, vocabulary richness [6]. |
| Both Methods | Effect of Document Length | Performance improves significantly with longer documents for both paradigms [19] [6]. | A clear positive correlation between the number of words available and system validity [19] [6]. |
Cllr is a key metric for assessing the overall performance and calibration of a likelihood ratio system, where a lower value indicates better performance.
Critical Factors Influencing Performance
- Document Length: The amount of text available is a critical factor. Studies consistently show that longer documents lead to more reliable comparisons, as they provide a more stable estimate of an author's style [19] [6]. For instance, one experiment showed that Cllr improved from 0.70640 to 0.30692 as document length increased from 700 to 2100 words in a score-based system [19].
- Feature and Model Choice: In score-based systems, the choice of distance metric is crucial, with the Cosine measure consistently outperforming Euclidean and Manhattan distances [19] [44]. In feature-based systems, robust features like "Average character number per word token" and "Punctuation character ratio" have been identified as effective across different sample sizes [6].
- Dimensionality and Data Scarcity: Score-based methods offer a practical advantage in high-dimensional settings. When the number of features is large relative to the available background data, reducing the feature space to a single score simplifies modeling and can mitigate overfitting [19]. This makes score-based approaches relatively robust and stable even with a limited quantity of background data [19] [44].
The Scientist's Toolkit: Essential Research Reagents
Table 3: Key Reagents and Tools for Forensic Text Comparison Research
| Tool / Reagent | Type / Category | Function in Research |
|---|---|---|
| Bag-of-Words Model | Text Representation Model | Converts unstructured text into a numerical vector based on word frequencies, serving as the input for score-based and some feature-based systems [19] [46]. |
| N-most Frequent Words (N) | Feature Selection Parameter | Defines the vocabulary size for the Bag-of-Words model. Optimal N (e.g., 260) can be determined empirically to balance information and noise [19]. |
| Cosine Distance | Similarity Metric | A function for calculating the similarity between two text vectors in a score-based system, often outperforming other metrics like Euclidean distance [19] [44]. |
| Likelihood Ratio (LR) | Statistical Measure | The core output of a forensic text comparison system, quantifying the strength of the evidence for one hypothesis over another [19] [43] [6]. |
| Log-Likelihood-Ratio Cost (Cllr) | Performance Metric | A single metric used to evaluate the discrimination accuracy and calibration of a likelihood ratio system, allowing for comparative validation [19] [6]. |
| Stylometric Features | Linguistic Proxies | Quantifiable aspects of writing style (e.g., punctuation ratio, vocabulary richness) that serve as the input features for authorship attribution models [45] [6]. |
| Kernel Density Estimation | Statistical Model | A non-parametric method used in feature-based systems to estimate the probability density of a multivariate feature vector for LR calculation [6]. |
| Empath Library | Psycholinguistic Tool | A Python library used to analyze text against psychological categories, such as deception, which can be integrated as features in a forensic framework [3]. |
The comparative analysis of feature-based and score-based methods reveals that neither is universally superior; each possesses distinct strengths that suit different forensic contexts. Feature-based methods, which directly model the distribution of linguistic features, can be highly powerful when the feature set is well-understood and sufficient data exists for robust multivariate modeling. Conversely, score-based methods offer a robust and practical framework for handling high-dimensional feature spaces, such as those generated by bag-of-words models, by reducing the complexity to a univariate score. The empirical evidence underscores the importance of document length and the careful selection of features or similarity metrics for both paradigms. Ultimately, the choice of methodology depends on the specific nature of the textual evidence, the available background data, and the required balance between model complexity and operational practicality. Future research should continue to refine both approaches, exploring hybrid models and validating their performance across diverse and challenging real-world scenarios.
Forensic text comparison (FTC) methodology research is increasingly pivotal for evaluating digital evidence in judicial proceedings, requiring scientifically defensible and demonstrably reliable approaches [5]. The field demands empirical validation through quantitative measurements, statistical models, and the likelihood-ratio framework to ensure transparency, reproducibility, and resistance to cognitive bias [5]. Recent advancements in artificial intelligence have introduced Multimodal Large Language Models (MLLMs) as transformative tools capable of processing and interpreting complex textual and visual evidence. A comprehensive benchmarking study reveals that MLLMs show "emerging potential for forensic education and structured assessments" though limitations in visual reasoning and open-ended interpretation preclude independent application in live forensic practice [47]. This technical guide examines the systematic benchmarking of MLLMs within forensic text comparison, providing detailed experimental protocols, performance metrics, and implementation frameworks to standardize evaluation methodologies across the discipline.
Fundamentals of Forensic Text Comparison
Forensic text comparison constitutes a specialized domain within forensic linguistics focused on authorship verification and document analysis. The core framework involves:
- Quantitative Measurements: Extracting measurable features from textual evidence, including lexical patterns, syntactic structures, and semantic content [5]
- Statistical Models: Implementing probabilistic methods to compute similarity metrics and typicality assessments between questioned and known documents [5]
- Likelihood-Ratio Framework: Providing a logically sound approach for evaluating evidence strength by comparing probabilities under competing hypotheses [5]
The complexity of textual evidence arises from multiple influencing factors including authorship idiolect, social group characteristics, and communicative situations [5]. Topic mismatch between compared documents presents particular challenges, as writing style varies significantly across different subjects and contexts [5]. Traditional FTC methodologies have faced criticism regarding validation gaps and subjective interpretation, creating opportunities for MLLM integration to enhance objectivity and scalability.
MLLM Benchmarking Methodology
Experimental Design Principles
Robust benchmarking of MLLMs for forensic applications requires adherence to two critical validation requirements derived from forensic science standards [5]:
- Reflecting Case Conditions: Experimental parameters must replicate the specific conditions of forensic casework, including document types, quality variations, and comparison challenges
- Using Relevant Data: Training and evaluation datasets must demonstrate direct relevance to the forensic context under investigation
Benchmarking experiments should employ the likelihood-ratio framework, where the likelihood ratio (LR) equals p(E|Hp) divided by p(E|Hd), representing the probability of evidence given prosecution and defense hypotheses respectively [5]. This framework quantitatively expresses evidence strength while maintaining logical and legal correctness.
Dataset Composition and Preparation
The comprehensive benchmarking study evaluated MLLMs using "847 examination-style forensic questions drawn from various academic literature, case studies, and clinical assessments, covering nine forensic subdomains" [47]. Dataset construction should prioritize:
- Domain Representation: Covering multiple forensic subdomains including questioned documents, threat assessment, and communicative competence
- Modality Balance: Incorporating both text-only and image-based evidentiary materials
- Complexity Stratification: Including straightforward factual questions alongside complex inference tasks requiring multi-step reasoning
Table 1: Benchmark Dataset Composition
| Component | Specification | Forensic Relevance |
|---|---|---|
| Total Questions | 847 | Comprehensive coverage across subdomains |
| Question Types | Text-only, image-based, and multimodal | Reflects diverse evidence formats in casework |
| Source Materials | Academic literature, case studies, clinical assessments | Ensures real-world relevance and complexity |
| Forensic Subdomains | 9 distinct specialties | Tests domain-specific reasoning capabilities |
Model Selection and Evaluation Metrics
The benchmarking study examined "eleven state-of-the-art MLLMs, including proprietary (GPT-4o, Claude 4 Sonnet, Gemini 2.5 Flash) and open-source (Llama 4, Qwen 2.5-VL) models" [47]. Evaluation requires both automated and manual assessment methodologies:
- Accuracy Metrics: Percentage of correct responses against established ground truth
- Reasoning Quality: Evaluation of chain-of-thought processes for logical coherence
- Domain Performance: Stratified analysis across forensic subdomains to identify specialized capabilities
- Visual Reasoning: Separate assessment for image interpretation and multimodal inference tasks
Performance analysis should employ "direct and chain-of-thought prompting" with "automated scoring verified through manual revision" to ensure comprehensive evaluation [47].
Experimental Protocols and Workflows
Core Benchmarking Protocol
The standardized experimental protocol for benchmarking MLLMs in forensic contexts involves sequential stages:
- Question Curation: Assembling examination-style questions representing authentic forensic challenges
- Prompt Engineering: Implementing both direct and chain-of-thought prompting strategies
- Response Collection: Executing model inferences across standardized hardware/software platforms
- Blinded Assessment: Evaluating responses against ground truth through automated and manual scoring
- Statistical Analysis: Computing performance metrics across models and subdomains
Diagram 1: MLLM Benchmarking Workflow (76 characters)
Forensic Text Comparison Protocol
For authorship verification tasks, the experimental protocol must address topic mismatch challenges:
- Document Pairing: Establishing questioned and known document pairs with controlled topic relationships
- Feature Extraction: Implementing psycholinguistic NLP frameworks analyzing deception, emotion, and subjectivity over time [3]
- Similarity Calculation: Computing similarity metrics using n-grams, word vectors, and pairwise correlations [3]
- Likelihood Ratio Computation: Applying Dirichlet-multinomial models with logistic-regression calibration [5]
- Performance Validation: Assessing LR accuracy using log-likelihood-ratio cost and Tippett plots [5]
Diagram 2: Forensic Text Comparison Protocol (82 characters)
Benchmarking Results and Performance Analysis
Quantitative Performance Metrics
The comprehensive evaluation revealed that "performance improved consistently with newer model generations" across forensic domains [47]. Key findings included:
- Prompting Efficacy: "Chain-of-thought prompting improved accuracy on text-based and choice-based tasks for most models, though this trend did not hold for image-based and open-ended questions" [47]
- Reasoning Limitations: "Visual reasoning and complex inference tasks revealed persistent limitations, with models underperforming in image interpretation and nuanced forensic scenarios" [47]
- Domain Stability: "Model performance remained stable across forensic subdomains, suggesting topic type alone did not drive variability" [47]
Table 2: MLLM Performance Analysis in Forensic Benchmarking
| Evaluation Dimension | Performance Finding | Implication for Forensic Application |
|---|---|---|
| Generational Improvement | Consistent gains with newer models | Supports continued investment in MLLM development |
| Chain-of-Thought Prompting | Improved text/choice task accuracy | Recommended for factual forensic queries |
| Visual Reasoning | Persistent limitations in image interpretation | Constrains use in image-based evidence analysis |
| Domain Adaptation | Stable performance across subdomains | Enables broad application across forensic specialties |
| Open-Ended Questions | Limited performance gains with CoT | Requires specialized approaches for complex reasoning |
Forensic Text Comparison Performance
In psycholinguistic analysis for deception detection, research demonstrates that "through the application of n-grams paired with deception, emotion, and subjectivity over time, we were able to identify and measure cues that can be used to better identify persons of interest" [3]. Successful methodologies have employed:
- Entity-Topic Correlation: Mapping relationships between investigative entities and key topics
- Temporal Pattern Analysis: Tracking deception and emotion markers across time-series data
- N-gram Correlation: Identifying significant word patterns associated with deceptive communication [3]
Validation experiments using the Amazon Authorship Verification Corpus (AAVC) demonstrate the critical importance of using relevant data and replicating case conditions, with significant performance differences observed between matched and mismatched topic conditions [5].
Research Reagent Solutions
The experimental framework for benchmarking MLLMs requires specific computational resources and software tools:
Table 3: Essential Research Reagents for MLLM Benchmarking
| Reagent Category | Specific Tools/Resources | Function in Experimental Protocol |
|---|---|---|
| Proprietary MLLMs | GPT-4o, Claude 4 Sonnet, Gemini 2.5 Flash [47] | Benchmarking against state-of-the-art commercial models |
| Open-Source MLLMs | Llama 4, Qwen 2.5-VL [47] | Enabling customizable, transparent model inspection |
| Forensic Datasets | AAVC, Custom Forensic Question Sets [5] [47] | Providing domain-relevant evaluation benchmarks |
| NLP Libraries | Empath, LIWC, Custom Psycholinguistic Frameworks [3] | Enabling deception, emotion, and subjectivity analysis |
| Statistical Analysis | Dirichlet-Multinomial Models, Logistic Regression Calibration [5] | Computing likelihood ratios and validating performance |
| Visualization Tools | Tippett Plots, Performance Dashboards [5] | Communicating results and supporting interpretation |
Implementation Framework
Integration Pathways
The benchmarking results inform specific integration pathways for MLLMs in forensic practice:
- Forensic Education: Utilizing MLLMs for training and reinforcement of factual knowledge [47]
- Structured Assessments: Deploying MLLMs for preliminary analysis of well-defined evidential questions [47]
- Investigative Support: Employing psycholinguistic NLP frameworks to identify persons of interest from larger candidate pools [3]
- Analytical Triangulation: Using MLLM outputs alongside traditional forensic methods to enhance analytical robustness
Validation and Quality Assurance
Forensic implementation requires rigorous validation protocols addressing:
- Domain-Targeted Fine-Tuning: Adapting general-purpose MLLMs to forensic specificities [47]
- Task-Aware Prompting: Developing optimized prompt strategies for different forensic question types [47]
- Transparency Standards: Ensuring interpretability of MLLM outputs for judicial scrutiny [5]
- Bias Mitigation: Implementing safeguards against demographic and contextual biases
Diagram 3: Forensic MLLM Validation Framework (84 characters)
Benchmarking emerging MLLMs establishes their evolving role in forensic text comparison methodology research while delineating current limitations. The comprehensive evaluation framework demonstrates that MLLMs show promising capabilities for structured forensic assessments but require further development for complex reasoning tasks. Future research priorities include developing multimodal forensic datasets, implementing domain-targeted fine-tuning, and establishing task-aware prompting strategies to enhance reliability and generalizability. The systematic benchmarking approach outlined in this guide provides a foundation for the cautious integration of MLLMs into forensic practice, contributing to more scalable, objective, and scientifically validated text comparison methodologies. As these tools continue to evolve, their potential to transform forensic analysis while maintaining rigorous scientific and legal standards represents a significant advancement for the field.
The evolution of forensic text comparison (FTC) from an expert-opinion-based discipline to a quantitative, computational science necessitates the development of robust, standardized evaluation methodologies. It has been argued in forensic science that the empirical validation of a forensic inference system must replicate the conditions of the case under investigation and use relevant data [5]. The current lack of such standardized protocols in FTC constitutes a significant scientific drawback, potentially misleading the trier-of-fact and undermining the reliability of evidence presented in legal contexts [5]. This whitepaper delineates the core components, experimental protocols, and visualization frameworks required to advance the field through rigorous standardization, thereby enhancing the transparency, reproducibility, and scientific defensibility of forensic text analysis.
Core Components of a Standardized Framework
Quantitative Foundations and the Likelihood-Ratio Framework
A scientific approach to forensic evidence analysis rests on several key elements: the use of quantitative measurements, statistical models, the likelihood-ratio (LR) framework, and empirical validation [5]. The LR framework provides a logically and legally sound method for evaluating the strength of forensic evidence, quantifying how much more likely the evidence is under the prosecution hypothesis (e.g., the defendant authored the questioned document) compared to the defense hypothesis (e.g., a different author wrote it) [5]. This framework forces the explicit consideration of the similarity of the texts and the typicality of this similarity within a relevant population.
Defining "Relevant Data" and Casework Conditions
A central tenet of validation is using data relevant to the case. For FTC, "relevance" is multi-faceted and must account for the complex nature of textual evidence, which encodes information about authorship, the author's social group, and the communicative situation [5]. A critical challenge is managing mismatches between known and questioned documents. Topic mismatch is a primary concern, as it is a common and challenging condition in real casework that can significantly impact the performance of authorship attribution methods [5]. Future research must determine the specific casework conditions and mismatch types that require validation, what truly constitutes relevant data, and the necessary quality and quantity of that data [5].
Methodologies for Dataset Creation and Ground Truth
Developing a standardized dataset is the cornerstone of reproducible research. The methodology must ensure that the dataset is representative, of high quality, and accompanied by reliable ground truth.
Workflow for Standardized Dataset Generation
The process for creating a forensic text dataset, inspired by standardized testing paradigms like the NIST Computer Forensic Tool Testing (CFTT) Program, involves several critical, sequential stages [9] [48]. The workflow below outlines the key steps from defining case parameters to final dataset validation.
Experimental Protocol for Dataset Generation
Objective: To construct a standardized dataset for evaluating forensic text comparison methodologies under controlled, forensically relevant conditions.
Define Use Case and Hypotheses:
- Clearly articulate the forensic question (e.g., authorship verification, deception detection).
- Define the prosecution (Hp) and defense (Hd) hypotheses for the evaluation.
Source Data Collection:
Establish Ground Truth:
Introduce Controlled Mismatches:
- To simulate real-world challenges, deliberately create document pairs with specific mismatches, with topic mismatch being a primary case [5].
- This allows for testing the robustness of FTC methods against known adverse conditions.
Data Curation and Preprocessing:
- Apply consistent preprocessing: tokenization, lowercasing, removal of metadata identifiers (anonymization), and text normalization.
- Partition the data into training, validation, and test sets, ensuring no author overlaps between sets.
Validation and Documentation:
- Perform quality checks to ensure data integrity and alignment with ground truth.
- Create comprehensive documentation detailing the dataset's composition, collection methods, and known limitations [48].
Validation Protocols and Quantitative Evaluation
Once a standardized dataset is established, rigorous validation protocols are required to assess the performance of FTC methods.
Workflow for Method Validation and Interpretation
The validation of a Forensic Text Comparison method involves a structured process from feature extraction to the final interpretation of results within the Likelihood-Ratio framework. The following workflow details this sequence.
Experimental Protocol for Method Validation
Objective: To empirically validate the performance and reliability of a forensic text comparison method using a standardized dataset and quantitative metrics.
Feature Extraction:
- Extract quantitative features from the text. In psycholinguistic NLP frameworks, this may include:
Statistical Modeling and LR Calculation:
Performance Evaluation:
- Assess the computed LRs using quantitative metrics:
- Cllr (Log-Likelihood-Ratio Cost): A single scalar metric that evaluates the overall quality of the LR system, considering both discrimination and calibration [5].
- Tippett Plots: Visualizations that show the cumulative proportion of LRs for both same-author and different-author pairs, providing a clear view of the method's performance and error rates [5].
- BLEU and ROUGE Metrics: For tasks involving summarization or generation (e.g., in LLM-based timeline analysis), these metrics can quantitatively evaluate output against a ground truth reference [9] [48].
- Assess the computed LRs using quantitative metrics:
Interpretation and Reporting:
- Report the strength of the evidence according to the LR scale. The forensic scientist's role is to present the LR, not to opine on the ultimate issue of guilt or innocence, which remains the province of the trier-of-fact [5].
Quantitative Evaluation Metrics
Table 1: Key Quantitative Metrics for Validating Forensic Text Comparison Methods.
| Metric | Description | Interpretation | Application Context |
|---|---|---|---|
| Likelihood Ratio (LR) | Ratio of the probability of the evidence given the prosecution hypothesis to the probability given the defense hypothesis [5]. | LR > 1 supports Hp; LR < 1 supports Hd. Distance from 1 indicates strength. | Core metric for evaluating evidence in all FTC tasks. |
| Cllr (Cost of LLR) | A single measure that evaluates the overall performance of an LR-based system, considering both discrimination and calibration [5]. | Lower Cllr values indicate better system performance. A perfect system has Cllr = 0. | Primary metric for validating the reliability and accuracy of the entire FTC methodology. |
| Tippett Plot | A graphical representation showing the cumulative distribution of LRs for both same-source and different-source hypotheses [5]. | Visualizes empirical validity, error rates, and the separation between the two distributions. | Used to demonstrate method performance across a range of LRs and to identify potential issues. |
| BLEU / ROUGE | BLEU (Bilingual Evaluation Understudy) and ROUGE (Recall-Oriented Understudy for Gisting Evaluation) are algorithms for evaluating the quality of generated text against references [48]. | Higher scores indicate better overlap with reference texts (e.g., ground truth summaries). | Evaluating LLM-based forensic tasks, such as event summarization or timeline analysis [48]. |
The Scientist's Toolkit: Essential Research Reagents
The following table details key analytical "reagents" and their functions in conducting forensic text comparison research.
Table 2: Essential Research Reagents for Forensic Text Comparison Experiments.
| Reagent / Tool | Function / Description | Application in FTC |
|---|---|---|
| N-gram Models | Contiguous sequences of 'n' items (words, characters) from a given text sample. | Basic lexical feature for authorship attribution and stylistic analysis [3]. |
| Psycholinguistic Feature Libraries (e.g., LIWC, Empath) | Software libraries that map text to psychological and topical categories (deception, emotion, subjectivity) [3]. | Quantifying non-lexical cues indicative of cognitive state, deception, or emotional tone [3]. |
| Likelihood-Ratio (LR) Framework | A statistical framework for evaluating the strength of evidence under two competing hypotheses [5]. | The core logical and legal framework for interpreting the results of a forensic text comparison [5]. |
| Dirichlet-Multinomial Model | A statistical model commonly used for text classification and authorship verification [5]. | Used for calculating likelihood ratios based on the distribution of linguistic features [5]. |
| Standardized Forensic Dataset | A curated collection of texts with known authorship and metadata, designed for testing and validation. | Serves as the benchmark for empirical validation, ensuring tests are performed on relevant data [5] [48]. |
| Validation Metrics (Cllr, Tippett Plots) | Specific metrics and visualizations for assessing the performance of an LR-based system [5]. | Used for the empirical validation and demonstration of the reliability of the FTC method [5]. |
| Large Language Models (LLMs) | AI models capable of generating and understanding natural language. | Used for generating simulated forensic scenarios or as a tool for analysis (e.g., timeline summarization), requiring rigorous evaluation [3] [48]. |
Conclusion
Forensic Text Comparison has evolved into a rigorous, quantitative science centered on the Likelihood Ratio framework, which provides a transparent and logically sound method for evaluating evidence. The methodology's strength lies in its diverse toolkit—encompassing feature-based models, score-based systems, and psycholinguistic analysis—and its commitment to empirical validation under conditions that mirror real-world casework. Critical challenges such as topic mismatch and data scarcity necessitate ongoing optimization of features and models. For researchers and scientists, the future of FTC involves the development of more sophisticated, validated systems, the cautious integration of emerging technologies like MLLMs, and the establishment of robust, standardized benchmarking datasets. These advances will further solidify FTC's role in providing scientifically defensible and reliable evidence for biomedical, clinical, and forensic investigations.
References
- 1. Idiolect [https://en.wikipedia.org/wiki/Idiolect]
- 2. What Is An Idiolect? [https://www.babbel.com/en/magazine/what-is-an-idiolect]
- 3. A psycholinguistic NLP framework for forensic text analysis ... [https://www.frontiersin.org/journals/artificial-intelligence/articles/10.3389/frai.2025.1669542/full]
- 4. Strength of linguistic text evidence: A fused forensic ... [https://pubmed.ncbi.nlm.nih.gov/28735218/]
- 5. Validation in Forensic Text Comparison: Issues and ... [https://www.mdpi.com/2226-471X/9/2/47]
- 6. Strength of forensic text comparison evidence from stylometric ... [https://researchportalplus.anu.edu.au/en/publications/strength-of-forensic-text-comparison-evidence-from-stylometric-fe/]
- 7. Commentary on: Aggadi N, Zeller K, Busey T. Quantifying ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12584119/]
- 8. What is the best way to present likelihood ratios? A review ... [https://www.sciencedirect.com/science/article/pii/S1355030625001261]
- 9. Towards a standardized methodology and dataset for ... [https://www.sciencedirect.com/science/article/pii/S2666281725001222]
- 10. Analytical approaches for forensic paper comparison and ... [https://www.sciencedirect.com/science/article/abs/pii/S0379073825001288]
- 11. Text Data Visualization | What It Is and How To Use It [https://www.displayr.com/text-analytics-visualization/]
- 12. Quantitative Text Analysis (MAXDictio) [https://www.maxqda.com/quantitative-text-analysis]
- 13. The Best Text Visualization Tools in 2025 [https://infranodus.com/docs/text-visualization-tools]
- 14. Likelihood ratio estimation for authorship text evidence [https://www.sciencedirect.com/science/article/abs/pii/S0379073822000986]
- 15. Feature-Based Forensic Text Comparison Using a Poisson ... [https://aclanthology.org/2020.alta-1.4/]
- 16. Hybrid topic modeling method based on dirichlet multinomial ... [https://journalofbigdata.springeropen.com/articles/10.1186/s40537-024-00930-9]
- 17. Poisson Regression: The Ultimate Guide to Modeling Count ... [https://abhic159.medium.com/poisson-regression-the-ultimate-guide-to-modeling-count-data-like-a-pro-1a746276619d]
- 18. Time-dependent Poisson reduced rank models for political ... [https://www.sciencedirect.com/science/article/abs/pii/S0167947319301586]
- 19. Score-based likelihood ratios for linguistic text evidence ... [https://www.sciencedirect.com/science/article/abs/pii/S0379073821003005]
- 20. Validation in Forensic Text Comparison: Issues and ... [https://research.manchester.ac.uk/en/publications/validation-in-forensic-text-comparison-issues-and-opportunities]
- 21. Outliers or Key Profiles? Understanding Distance ... [https://dh2016.adho.org/abstracts/253]
- 22. Classification of spectral data using fused lasso logistic regression - ScienceDirect [https://www.sciencedirect.com/science/article/abs/pii/S0169743915000088]
- 23. Nozzle Clogging Detection in FFF 3D Printing Using Machine Learning Approach: A Comparative Investigation | International Journal of Precision Engineering and Manufacturing [https://link.springer.com/article/10.1007/s12541-025-01284-9]
- 24. A psycholinguistic NLP framework for forensic text analysis ... [https://pubmed.ncbi.nlm.nih.gov/41195198/]
- 25. A deception detection model by using integrated LLM with ... [https://www.nature.com/articles/s41598-025-17741-4]
- 26. SVC 2025: the First Multimodal Deception Detection ... [https://arxiv.org/html/2508.04129v1]
- 27. Detection of emotion by text analysis using machine learning [https://www.frontiersin.org/journals/psychology/articles/10.3389/fpsyg.2023.1190326/full]
- 28. Textual emotion recognition to improve real-time ... [https://www.nature.com/articles/s41598-025-25363-z]
- 29. Balancing validity and reliability as a function of sampling ... [https://www.sciencedirect.com/science/article/abs/pii/S1355030624001023]
- 30. Stability of Forensic Text Comparison System [https://researchportalplus.anu.edu.au/en/publications/stability-of-forensic-text-comparison-system/]
- 31. [2505.15422] Trends and Challenges in Authorship Analysis [https://arxiv.org/abs/2505.15422]
- 32. Inferring experimental procedures from text-based ... [https://www.nature.com/articles/s41467-021-22951-1]
- 33. A comprehensive and quantitative comparison of text-mining ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5831415/]
- 34. Stylometry can reveal artificial intelligence authorship, but humans... [https://pubmed.ncbi.nlm.nih.gov/41144514/]
- 35. Evaluating spam filters and Stylometric Detection of AI- ... [https://www.sciencedirect.com/science/article/pii/S0957417425006669]
- 36. Stylometric comparisons of human versus AI-generated ... [https://www.nature.com/articles/s41599-025-05986-3]
- 37. A practical approach to mitigating cognitive bias effects in ... [https://www.sciencedirect.com/science/article/pii/S2589871X24001165]
- 38. Reducing the impact of cognitive bias in decision making [https://pmc.ncbi.nlm.nih.gov/articles/PMC10319185/]
- 39. A Forensic Science-Based Model for Identifying and ... [https://jaapl.org/content/early/2025/05/05/JAAPL.250019-25]
- 40. Quantitative matching of forensic evidence fragments using ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11381546/]
- 41. An overview of log likelihood ratio cost in forensic science [https://pmc.ncbi.nlm.nih.gov/articles/PMC11031735/]
- 42. Consensus on validation of forensic voice comparison [https://www.sciencedirect.com/science/article/pii/S1355030621000083]
- 43. Common or specific source, features or scores; it is all a ... [https://arxiv.org/html/2409.05403v1]
- 44. Score-based likelihood ratios for linguistic text evidence ... [https://pubmed.ncbi.nlm.nih.gov/34481115/]
- 45. Comparing writing style feature-based classification methods ... [https://springerplus.springeropen.com/articles/10.1186/s40064-016-1841-1]
- 46. Comparison of different feature extraction methods for ... [https://bmcmedinformdecismak.biomedcentral.com/articles/10.1186/s12911-022-01753-5]
- 47. Benchmarking Multimodal Large Language Models for Forensic ... [https://sciety-discovery.elifesciences.org/articles/by?article_doi=10.1101/2025.07.06.25330972]
- 48. Towards a standardized methodology and dataset for ... [https://arxiv.org/html/2505.03100v1]