Defining End-User Requirements in Forensic Method Validation: A Strategic Framework for Researchers and Scientists
This article provides a comprehensive framework for defining and implementing end-user requirements in forensic method validation, a critical process for ensuring analytical methods are scientifically sound and legally defensible.
Defining End-User Requirements in Forensic Method Validation: A Strategic Framework for Researchers and Scientists
Abstract
This article provides a comprehensive framework for defining and implementing end-user requirements in forensic method validation, a critical process for ensuring analytical methods are scientifically sound and legally defensible. Tailored for researchers, scientists, and development professionals, it explores the foundational principles of establishing fitness-for-purpose, outlines methodological steps for requirement specification, addresses common challenges in the validation lifecycle, and presents collaborative models for efficient verification. By synthesizing current guidelines and best practices, this guide aims to enhance the robustness, reliability, and accreditation readiness of validated methods in forensic and biomedical research.
The Cornerstone of Reliability: Understanding End-User Requirements and Fitness for Purpose
Defining Fitness for Purpose in Forensic Science
Fitness for purpose is a foundational principle in forensic science, serving as the benchmark for the validity and admissibility of scientific evidence within the criminal justice system. It is formally defined as a method or process being "good enough to do the job it is intended to do, as defined by the specification developed from the end-user requirement" [1]. This concept moves beyond mere technical function, demanding that forensic science activities demonstrably fulfill the needs of all stakeholders—from the investigating officers to the courts—by producing reliable, accurate, and interpretable results upon which legal decisions can be based [1].
The legal and regulatory imperative for this principle is unequivocal. Courts are expected to consider the validity of the methods by which an expert's data were obtained [1]. Furthermore, demonstrating fitness for purpose through method validation is a central requirement for accreditation to international standards such as ISO/IEC 17025 and is mandated by the Forensic Science Regulator’s Codes of Practice and Conduct [1] [2]. This document provides an in-depth technical guide to defining and demonstrating fitness for purpose, framed within the critical context of establishing explicit end-user requirements for forensic method validation research.
The Regulatory and Standardization Framework
The landscape of forensic science is guided by a robust and evolving framework of international standards and regulatory codes, all of which anchor their requirements to the principle of fitness for purpose.
- ISO/IEC 17025: This is the cornerstone standard for testing and calibration laboratories. Accreditation to ISO/IEC 17025 includes an assessment that an organization's methods are valid and that the organization is competent to perform them [1]. The standard necessitates a process for validating methods to ensure they are fit for the intended purpose.
- The Forensic Science Regulator’s Code of Practice: In England and Wales, the Forensic Science Regulator Act 2021 established a statutory code of practice. This code requires forensic units to implement effective quality management systems, with validation of techniques being a key element to understand and manage the risk of a quality failure, the consequences of which can be profound for the administration of justice [2].
- Emerging ISO 21043 Series: Recognizing that generic standards like ISO 17025 may have limitations for forensic science, the International Organization for Standardization is developing the ISO 21043 series, a dedicated standard for forensic sciences [3]. This multi-part standard covers the entire forensic process, from vocabulary and crime scene investigation to analysis, interpretation, and reporting, providing a more tailored framework for ensuring quality and fitness for purpose [4].
A significant development in harmonizing practices globally is the Sydney Declaration (SD) for Forensic Sciences. This initiative outlines seven fundamental tenets, redefining forensic science as "the oriented research activity based on cases... that uses scientific principles to study traces… to understand anomalous events of public interest" [3]. The SD emphasizes that forensic science deals with a continuum of uncertainties and that its findings acquire meaning in context, thereby providing a principled foundation for defining fitness for purpose, particularly in regions like Africa that are building their forensic capabilities [3].
The Core Principle: Linking End-User Requirements to Fitness for Purpose
At its heart, demonstrating fitness for purpose is an evidence-based process that connects a method's performance to a clearly defined need. The "end-user requirement" is the critical starting point, acting as the specification against which fitness is measured [1].
Defining End-User Requirements
The end-user requirement captures what the different users of the method's output need it to reliably accomplish. In their simplest form, these requirements define the aspects of the method the expert will rely on for their critical findings in a statement or report [1]. Failure to define these requirements at the outset can lead to unfocused testing that amasses data which may not increase understanding or confidence in the method [1].
Identifying End-Users: The process involves identifying all parties who are users of the information. This typically includes:
- The Forensic Scientist/Expert: Requires the method to produce accurate, reliable, and interpretable data to form an objective opinion.
- Investigating Officers: Need intelligence and evidence that is actionable and reliable to guide an investigation.
- The Courts (Judge and Jury): Require evidence that is scientifically sound, understandable, and whose limitations are clear to aid in the administration of justice.
The Validation Process: A Structured Workflow
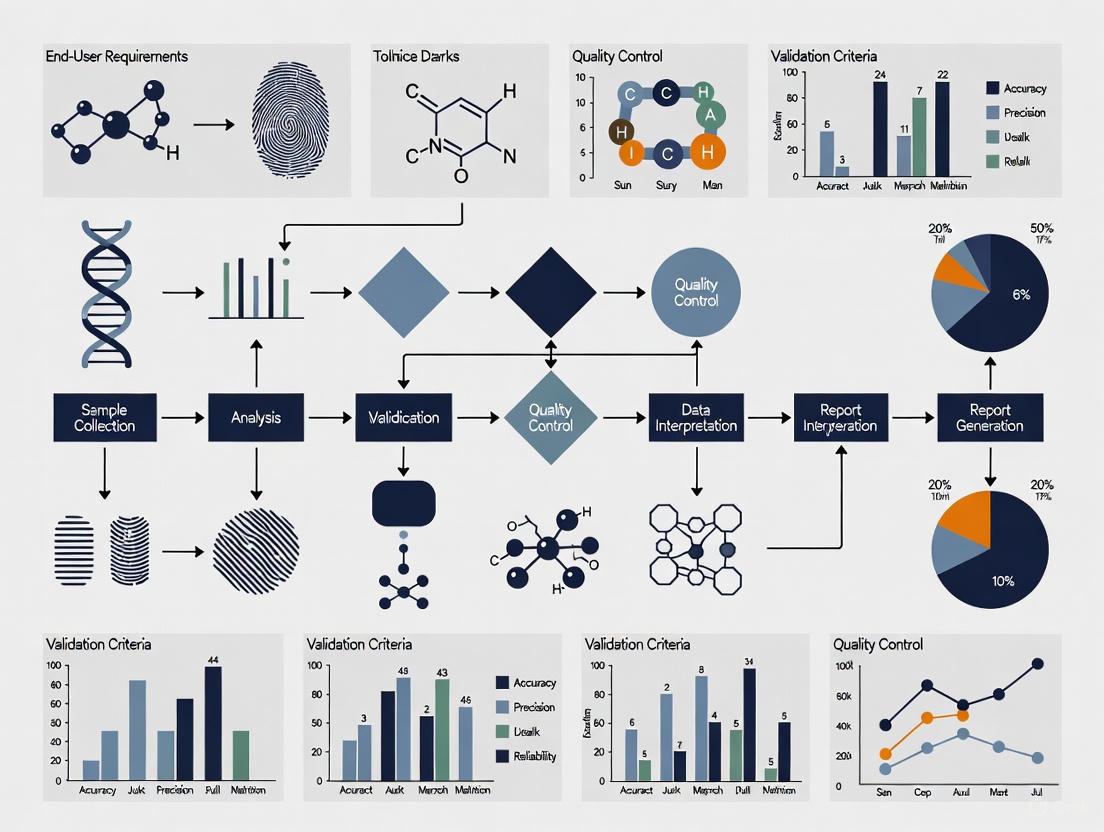
The process for validating a method, and thus demonstrating its fitness for purpose, follows a logical sequence. The framework published in the Forensic Science Regulator's Codes of Practice outlines the essential stages, which are visualized in the workflow below [1].
Figure 1: Forensic Method Validation Workflow. This diagram outlines the key stages for validating a forensic method, from defining requirements to implementation. Critical stages for defining fitness for purpose are highlighted.
Experimental Design for Validation Studies
The objective evidence that a method meets its acceptance criteria is the test data generated during the validation exercise. Therefore, the selection and design of tests are critical [1].
Core Methodological Principles
- Representative Test Data: Data for all validation studies must be representative of the real-life use the method will be put to. This requires test materials that replicate the range of materials encountered in casework, including degraded, mixed, or otherwise challenging samples [1] [5].
- Stress Testing: For a robust validation, the method must also be tested with data challenges that "stress test" it. This involves pushing the method beyond ideal conditions to understand its limitations and failure modes [1].
- Accuracy and Reliability: The validation must empirically assess the method's performance, testing for accuracy (how close the results are to the true value) and reliability (the consistency of results under defined conditions) [5].
- Calibration: The results should be well-calibrated to the expected result, meaning that the reported probabilities or confidence levels accurately reflect the true underlying probabilities [5].
Quantitative Frameworks for Validation Data
The design of a validation study must be tailored to the method's intended use. The table below summarizes key experimental parameters and metrics that should be considered.
Table 1: Key Experimental Parameters and Metrics for Validation Studies
| Parameter Category | Specific Metric | Methodology for Assessment | Link to Fitness for Purpose |
|---|---|---|---|
| Accuracy & Precision | Measurement uncertainty, False positive/negative rates, Repeatability (same conditions), Reproducibility (different conditions) | Repeated analysis of certified reference materials (CRMs) and control samples with known values by multiple practitioners over time. | Ensures results are both correct and consistent, which is fundamental for evidential reliability. |
| Specificity & Selectivity | Ability to distinguish target analyte from interferents or mixtures. | Challenging the method with samples containing known potential interferents and complex mixtures. | Demonstrates the method is targeted and robust in complex, real-world sample matrices. |
| Sensitivity | Limit of Detection (LoD), Limit of Quantitation (LoQ). | Analyzing a series of samples with decreasing concentrations of the target analyte to determine the lowest detectable and quantifiable level. | Defines the scope of the method and its applicability to traces with minimal material. |
| Robustness & Ruggedness | Performance under deliberate, small variations in method parameters (e.g., temperature, pH, analyst). | Introducing minor, predefined variations to the standard protocol and measuring the impact on the results. | Ensures the method remains reliable despite minor, inevitable fluctuations in the operational environment. |
Collaborative versus Traditional Validation Models
A significant development in validation strategy is the move towards collaborative models, which offer substantial efficiencies. The table below contrasts this with the traditional approach.
Table 2: Comparison of Traditional and Collaborative Validation Models
| Aspect | Traditional Independent Validation | Collaborative Validation Model |
|---|---|---|
| Core Principle | Each Forensic Science Service Provider (FSSP) independently designs and executes a full validation for its own use. | FSSPs work cooperatively to standardize methods and share validation data. An originating FSSP publishes a peer-reviewed validation for others to verify [6]. |
| Process | The FSSP follows all stages in Figure 1 independently. | Subsequent FSSPs review the published validation data. If it fits their purpose, they perform a verification to demonstrate competence, avoiding full re-validation [6]. |
| Resource Impact | High cost, time-consuming, and laborious, with significant redundancy across the community [6]. | Significant savings in time, cost, and labor. Allows smaller FSSPs to implement new technology more efficiently [6]. |
| Data Comparability | No benchmark for cross-comparison of results between FSSPs. | Emulation of a published validation provides an inter-FSSP study, building a shared body of knowledge and enabling direct cross-comparison of data [6]. |
| Business Case | High opportunity cost as resources are diverted from casework [6]. | Reduces activation energy for technology adoption and raises all FSSPs to the highest published standard simultaneously [6]. |
The methodology for a collaborative verification, following a published validation, is outlined in the diagram below.
Figure 2: Collaborative Method Verification Process. This workflow shows the steps for a laboratory to verify a method that has been previously validated and published by another organization.
The Scientist's Toolkit: Essential Research Reagents for Validation
While specific reagents vary by discipline, the conceptual "reagents" for a robust validation study are universal. These are the essential materials and resources required to execute the experimental protocols described in Section 4.
Table 3: Essential Research "Reagents" for Method Validation
| Tool / Material | Function in Validation | Critical Application Notes |
|---|---|---|
| Certified Reference Materials (CRMs) | Provides a ground truth with a known, certified value for assessing method accuracy and establishing calibration curves. | Must be traceable to a national or international standard. Used to test the method across the dynamic range of the assay. |
| Characterized Real-World Samples | Serves as representative test material to challenge the method with the complexity and variability encountered in casework. | Should include a portfolio of samples of varying quality, quantity, and composition (e.g., clean, degraded, mixed). |
| Proficiency Test (PT) Samples | Provides an external, blind assessment of the method's performance and the practitioner's competency in a controlled setting. | Participation in inter-laboratory PT schemes is a key requirement for accreditation and ongoing quality assurance. |
| Data Analysis & Statistical Software | Enables the quantitative analysis of validation data, calculation of metrics (e.g., LoD, precision), and assessment against acceptance criteria. | Software tools and scripts used must be verified and their use documented in the standard operating procedure. |
| Documented Standard Operating Procedure (SOP) | The definitive protocol against which the validation is performed. Ensures the validation study is conducted on the final, documented method. | The creation of a draft SOP is a recommended good practice before commencing any validation study [1]. |
Defining fitness for purpose is not an abstract exercise but a rigorous, evidence-based process that sits at the very heart of reliable and credible forensic science. It is achieved by systematically linking a method's performance, through robust experimental validation, to explicitly defined end-user requirements. The frameworks provided by standards such as ISO 17025, the new ISO 21043 series, and the principles of the Sydney Declaration offer a pathway to this demonstration.
The growing adoption of collaborative validation models presents a powerful opportunity to increase efficiency, standardize best practices, and enhance the comparability of forensic data across jurisdictions. As forensic science continues to evolve, with an increasing reliance on automated tools and complex data analysis, the principles outlined in this guide will become even more critical. Ultimately, a steadfast commitment to defining and demonstrating fitness for purpose is the primary safeguard for producing forensic evidence that is safe, impartial, and worthy of trust in the criminal justice system.
The Critical Role of End-User Requirements in Legal Admissibility and ISO 17025 Accreditation
Within the rigorous framework of forensic method validation research, end-user requirements represent the specific, documented needs and objectives that a forensic method must fulfill to be considered fit-for-purpose in the criminal justice system. These requirements form the fundamental criteria against which a method's performance is measured during validation, creating an unambiguous link between scientific procedure and legal utility. The Forensic Capability Network (FCN) defines validation as "a comprehensive scientific study which includes a series of tests that produces objective evidence that a finalised method, process, or equipment is fit for the specific purpose intended" [7]. In practice, this process begins with "determining and reviewing the end user requirements and specification" before any testing occurs [7].
The international standard ISO/IEC 17025:2017 establishes the foundational requirements for laboratory competence, impartiality, and consistent operation [8] [9] [10]. For forensic science service providers, accreditation to this standard demonstrates technical competence and provides the judicial system with confidence in the reliability of evidence presented. The standard's requirements for method validation create a structured pathway for incorporating end-user needs into formal scientific protocols, thereby ensuring that forensic methods not only produce scientifically sound results but also meet the practical and legal demands of their application [8].
The Intersection of End-User Requirements and ISO 17025
Method Validation as a Core ISO 17025 Requirement
ISO/IEC 17025 mandates that laboratories validate non-standard methods, laboratory-designed methods, and standard methods used outside their intended scope [8]. This process requires objective evidence that a method is fit for its intended purpose, which is fundamentally defined by its end-user requirements. The standard specifies that laboratories must use "appropriate methods and procedures for all laboratory activities" and evaluate "measurement uncertainty for all calibrations and testing where applicable" [8]. These requirements compel laboratories to formally document the performance characteristics needed from a method based on the specific forensic questions it must answer and the legal standards it must satisfy.
The management system requirements outlined in ISO 17025 emphasize the importance of a structured approach to laboratory operations, including documentation control, risk management, and continual improvement [9]. This framework ensures that end-user requirements are not merely considered during initial validation but are maintained throughout the method's lifecycle. As the FCN notes, "validation is a continuous iterative process" that requires periodic review and potentially re-validation when methods change or new information emerges about user needs [7].
Defining End-User Requirements for Forensic Applications
End-user requirements in forensic science encompass multiple dimensions that extend beyond basic technical performance. These requirements must address the needs of all stakeholders in the criminal justice process, from investigators to courts. The following table summarizes the core components of end-user requirements in forensic method validation:
Table 1: Core Components of End-User Requirements in Forensic Method Validation
| Requirement Category | Definition | Stakeholders Served |
|---|---|---|
| Technical Sensitivity | The minimum level of detection required for the analyte of interest | Forensic practitioners, investigators |
| Specificity/Selectivity | The ability to distinguish target analytes from interfering substances | Forensic practitioners, quality managers |
| Legal Reliability | The standard of proof required for admissibility in legal proceedings | Courts, legal professionals, oversight boards |
| Reporting Clarity | The format and content requirements for clear, unambiguous reporting | Legal professionals, juries, investigators |
| Operational Practicality | Considerations of time, cost, and equipment for implementation | Laboratory management, funding bodies |
| Uncertainty Quantification | The measurement uncertainty thresholds acceptable for the application | Quality managers, scientific peers |
The FCN emphasizes that validation must confirm that methods are "fit for the specific purpose intended" and that "any limitations are well understood and communicated appropriately" [7]. This necessitates a thorough understanding of how the method will be used in practice and what demands the legal system will place upon its results. Recent research has highlighted transparency as a "core principle and fundamental obligation of forensic science reporting," requiring disclosure of information about the "scientists' Authority, Compliance, Basis, Justification, Validity, Disagreements, and Context" [11]. These transparency obligations must be incorporated into the definition of end-user requirements from the outset.
Experimental Protocols for Defining and Validating Against End-User Requirements
Protocol for Establishing End-User Specifications
A systematic approach to defining end-user requirements ensures that all relevant criteria are captured and documented before method validation begins. The following protocol provides a structured methodology for establishing these specifications:
Stakeholder Identification and Analysis: Convene a panel representing all end-user groups, including forensic practitioners, investigators, prosecutors, defense attorneys, laboratory management, and quality assurance personnel. Document the specific needs and expectations of each group through structured interviews or surveys [7].
Regulatory and Legal Framework Review: Systematically identify all applicable standards, guidelines, and legal precedents that will govern method admissibility and implementation. This includes the ISO/IEC 17025 standard, the Forensic Science Regulator's Code (in the UK), relevant judicial rulings, and organizational policies [8] [7].
Technical Performance Parameter Definition: Based on stakeholder input and regulatory requirements, establish quantitative performance criteria for the method. This must include:
- Accuracy and Precision Requirements: Define acceptable thresholds for systematic and random error based on the method's intended application.
- Sensitivity and Detection Limits: Establish the required detection and quantification limits appropriate for the forensic context.
- Specificity Parameters: Document required discrimination power for the evidence type in question.
- Robustness and Ruggedness Criteria: Define acceptable performance boundaries under varying conditions [8].
Operational Requirement Specification: Document practical implementation requirements, including:
- Sample throughput and turnaround time expectations
- Equipment and facility requirements
- Personnel competency and training needs
- Data management and reporting formats
- Cost constraints and resource limitations [9]
Uncertainty and Reliability Thresholds: Establish acceptable measurement uncertainty targets and reliability standards based on the consequences of potential errors in the legal context. This includes defining statistical confidence levels required for reporting conclusions [8].
The output of this protocol is a comprehensive end-user requirement specification document that serves as the foundation for all subsequent validation activities.
Protocol for Validation Against End-User Requirements
Once end-user requirements are formally documented, a validation protocol must be designed to test the method against each requirement. The following experimental approach ensures comprehensive validation:
Validation Plan Development: Create a detailed plan that directly links each validation activity to specific end-user requirements. The plan should include:
- Experimental designs for testing each performance parameter
- Acceptance criteria for each requirement directly quoted from the specification document
- Statistical approaches for data analysis and interpretation
- Contingency procedures for addressing failures to meet requirements [7]
Technical Performance Verification: Execute experiments to verify the method meets all technical requirements:
- Accuracy and Precision Studies: Conduct replicate analyses of certified reference materials and quality control samples across multiple runs, operators, and instruments.
- Sensitivity Studies: Determine detection and quantification limits using serial dilutions of target analytes in relevant matrices.
- Specificity Assessment: Challenge the method with potentially interfering substances and similar but non-target materials.
- Robustness Testing: Deliberately introduce minor variations in procedure, reagents, equipment, or environmental conditions to establish method tolerance [8].
Operational Capability Demonstration: Conduct practical trials to verify operational requirements:
- Perform method trials in the actual operational environment with typical casework samples.
- Demonstrate that the method can be successfully executed by multiple operators with appropriate training.
- Verify that reporting formats meet stakeholder needs for clarity and comprehensiveness.
- Confirm that turnaround times can be met under normal operating conditions [9].
Uncertainty Quantification: Evaluate all significant sources of measurement uncertainty and calculate combined uncertainty estimates for the method. Verify that these estimates fall within the acceptable range defined in the end-user requirements [8].
Comparative Analysis (where applicable): Compare method performance with existing validated methods or reference methods to establish relative performance characteristics.
The following workflow diagram illustrates the integrated process of defining end-user requirements and validating methods against them:
Quantitative Frameworks for End-User Requirement Validation
The validation of methods against end-user requirements necessitates the collection and analysis of quantitative data to demonstrate compliance with established criteria. The following table presents a structured approach to data collection for requirement verification:
Table 2: Quantitative Data Collection Framework for End-User Requirement Validation
| Requirement Category | Data to Collect | Statistical Analysis Method | Acceptance Criteria |
|---|---|---|---|
| Accuracy | Mean recovery percentage from certified reference materials; comparison with reference method results | t-Tests; regression analysis; bias estimation | Recovery within 85-115%; no significant bias (p>0.05) |
| Precision | Replicate results across multiple runs, days, operators | Relative Standard Deviation (RSD); ANOVA | RSD <5% within run; <10% between runs |
| Sensitivity | Signal-to-noise ratios at lowest concentrations; replicate measurements of blanks | 3x standard deviation of blank; calibration curve parameters | Limit of Detection (LOD) sufficient for casework samples |
| Specificity | Results from analysis of potentially interfering substances; false positive/negative rates | Specificity and selectivity calculations; cross-reactivity assessment | No false positives in negative controls; correct identification in mixtures |
| Measurement Uncertainty | All significant uncertainty contributors; combined uncertainty estimates | Uncertainty budget development; coverage factor application | Combined uncertainty within pre-defined thresholds for legal applications |
Quantitative data analysis for requirement validation employs both descriptive and inferential statistical approaches. Descriptive statistics summarize the central tendency and dispersion of validation data, including measures such as mean, median, standard deviation, and relative standard deviation [12]. Inferential statistics enable conclusions beyond the immediate dataset, using techniques such as hypothesis testing, confidence intervals, and regression analysis to determine whether the method meets the established requirements [12]. For forensic applications, the evaluation of measurement uncertainty is particularly critical, as it provides judicial stakeholders with information about the reliability of reported results [8].
Successful validation against end-user requirements necessitates specific resources and tools. The following table details essential components of the validation toolkit:
Table 3: Essential Research Reagent Solutions for Method Validation
| Tool/Resource | Function in Validation | Application Example |
|---|---|---|
| Certified Reference Materials (CRMs) | Provide traceable standards for accuracy determination and calibration | CRM for blood alcohol concentration to validate forensic toxicology methods [8] |
| Proficiency Test Materials | Assess method and laboratory performance compared to peers | Collaborative testing program samples for DNA analysis methods [8] |
| Quality Control Materials | Monitor ongoing method performance and stability | Control samples with known drug concentrations for daily instrument verification [9] |
| Statistical Analysis Software | Perform required statistical calculations and uncertainty analysis | R, Python, or specialized packages for statistical evaluation of validation data [13] [12] |
| Document Management System | Maintain records of requirements, validation protocols, and results | Laboratory Information Management System (LIMS) for document control and version management [9] |
| Uncertainty Budget Templates | Structure the identification and quantification of uncertainty sources | Spreadsheet templates for systematic compilation of uncertainty contributors [8] |
Laboratories must ensure that reference materials and critical reagents are obtained from competent producers and are traceable to international standards where applicable [8]. The management of these resources should be incorporated into the laboratory's quality management system, with procedures for receipt, verification, storage, and use that prevent compromise of their integrity.
Legal Admissibility: The Consequence of Requirement-Driven Validation
The legal admissibility of forensic evidence hinges on the demonstration that methods used to generate it are scientifically valid and reliably applied. Recent U.S. Supreme Court decisions, including Smith v. Arizona, have "redefined the boundaries of forensic testimony and the Confrontation Clause," placing increased scrutiny on the validity and reliability of forensic methods [14]. Properly documented end-user requirements and validation against those requirements provide the foundational evidence needed to withstand such scrutiny.
The framework of transparency advocated by forensic science researchers requires "disclosing information about the scientists' Authority, Compliance, Basis, Justification, Validity, Disagreements, and Context" [11]. End-user requirement documentation directly supports this transparency by explicitly recording the methodological goals, performance standards, and limitations that define a method's appropriate application. This documentation becomes particularly crucial when forensic findings are challenged in legal proceedings, as it provides objective evidence that the method was designed and validated with the specific demands of the legal system in mind.
Validation that incorporates end-user requirements also addresses growing concerns about cognitive bias in forensic decision-making. As noted in discussions of independent audits, "troubling patterns of systemic deficiencies, questionable determinations, and possible bias" can undermine confidence in forensic results [14]. A requirement-driven validation approach establishes objective criteria for method performance and application, creating a barrier against subjective influences and ensuring that methods produce consistent, reliable results regardless of the specific practitioner or context.
The integration of end-user requirements into forensic method validation represents a critical nexus between scientific rigor and legal utility. The ISO/IEC 17025 standard provides the framework for this integration, mandating validation processes that objectively demonstrate methodological fitness for purpose. By systematically defining, documenting, and validating against end-user requirements, forensic science service providers not only satisfy accreditation requirements but also build a foundation for legal admissibility and professional credibility.
The evolving landscape of forensic science, with increasing emphasis on transparency, cognitive bias mitigation, and scientific validity, makes requirement-driven validation increasingly essential. As oversight bodies and legal standards continue to evolve, the explicit linkage between end-user needs and methodological validation will likely become even more central to forensic practice. Forensic researchers and laboratory managers should therefore prioritize the development of robust processes for requirement definition and validation, ensuring that their methods meet both scientific and legal standards for reliability and relevance.
Within the framework of modern forensic science, the validation of new methods is not merely a scientific exercise but a critical process that ensures the reliability and admissibility of evidence in the legal system. Defining end-user requirements is the foundational step in method validation research, serving as the benchmark against which a method's performance, limitations, and fitness for purpose are measured [15] [7]. This process is intrinsically stakeholder-driven. A comprehensive understanding of the needs, constraints, and expectations of all entities involved—from the laboratory bench to the courtroom—is therefore paramount. The international standard ISO 21043, which outlines requirements for the entire forensic process, underscores the necessity of this multi-stakeholder approach [4]. Failures in adequately considering stakeholder requirements can lead to flawed methodologies, evidence exclusion in court, and ultimately, miscarriages of justice [16] [7]. This guide provides a technical roadmap for identifying these key stakeholders and systematically integrating their requirements into forensic method validation research.
Mapping the Stakeholder Ecosystem
The ecosystem for a validated forensic method comprises a diverse network of individuals and organizations, each with distinct roles, interests, and requirements. These stakeholders can be categorized into several core groups, as detailed in Table 1.
Table 1: Key Stakeholders in Forensic Method Validation and Their Requirements
| Stakeholder Category | Specific Roles / Sub-groups | Primary Requirements & Interests |
|---|---|---|
| Forensic Service Providers (FSPs) | - Forensic Laboratory Managers- DNA Analysts- Latent Print Examiners- Digital Evidence Examiners- Crime Scene Investigators- Medicolegal Death Investigators | - Technical: Method reliability, reproducibility, sensitivity, specificity, and defined error rates [16] [17].- Operational: Throughput, cost-effectiveness, compatibility with existing workflows, and clear standard operating procedures (SOPs) [7].- Quality & Compliance: Adherence to standards (e.g., ISO 21043, FSR Code), accreditation requirements, and robust documentation for validation [4] [15]. |
| Judicial System Actors | - Judges- Prosecuting Attorneys- Defense Attorneys- Juries | - Admissibility: Scientific validity and reliability under relevant legal standards (e.g., Daubert, Frye) [16].- Clarity & Transparency: Understandable and logically correct reporting of evidence, including clear statements of limitations and uncertainty (e.g., via Likelihood Ratios) [4] [17].- Scrutiny: Ability to meaningfully challenge evidence, including access to underlying data and algorithms [17]. |
| Research & Standardization Bodies | - National Institute of Standards and Technology (NIST)- Organization of Scientific Area Committees (OSAC)- ISO Committees- Scientific Research Communities | - Scientific Rigor: Empirically calibrated and validated methods under casework conditions [4].- Standardization: Development of uniform standards, best practices, and terminology to ensure consistency across disciplines and jurisdictions [4].- Innovation: Promotion of transparent, reproducible, and bias-resistant methods like those in the forensic-data-science paradigm [4]. |
| Oversight & Funding Entities | - The Forensic Science Regulator (FSR)- National Institute of Justice (NIJ)- Police and Government Agencies | - Accountability & Governance: Compliance with legal and quality standards [7].- Public Trust: Ensuring forensic evidence is reliable and impartial.- Resource Management: Efficient use of funding and resources, supporting a resilient workforce [18]. |
| The Subject of Analysis | - Defendant / Accused- Victim | - Rights & Fairness: Evidence that is obtained and processed fairly, and that is adequately reliable to avoid wrongful conviction [16].- Understanding: The ability to comprehend the evidence presented against them. |
Experimental Protocols for Eliciting Stakeholder Requirements
A structured, scientific approach is essential for gathering robust data on stakeholder needs. The following protocols outline methodologies for conducting this critical research.
Protocol for Semi-Structured Interviews with Criminal Justice Stakeholders
This qualitative method is ideal for exploring the complex, in-depth perspectives of key figures in the judicial system [17].
- Objective: To elicit detailed perspectives on interpretation and reporting practices, the use of computational algorithms, and the practical challenges of integrating new forensic methods into the legal process.
- Materials:
- Recruitment materials and informed consent forms.
- An interview protocol guide with open-ended questions and probes.
- High-quality audio/video recording equipment (e.g., Zoom platform).
- Transcription software and services.
- Qualitative data analysis software (e.g., NVivo).
- Methodology:
- Participant Solicitation: Identify and recruit participants via invitation based on their active engagement in forensic science policy and practice. Target a range of roles, including laboratory managers, prosecutors, defense attorneys, judges, and academic scholars [17].
- Data Collection: Conduct one-on-one, semi-structured interviews using a video-based virtual meeting platform. The semi-structured format allows for consistency while permitting flexibility to explore emerging themes.
- Data Analysis: Transcribe interviews verbatim. Employ a thematic analysis approach, which involves:
- Familiarization: Repeated reading of transcripts.
- Coding: Generating systematic codes for key phrases and ideas.
- Theme Development: Collating codes into potential themes and sub-themes that represent patterns of meaning across the dataset.
- Review and Refinement: Ensuring themes accurately reflect the coded data and the entire dataset.
- Outcome Measures: A rich, qualitative account of stakeholder values, concerns, and preferences, identifying both consensus and conflict points across different groups [17].
Protocol for National Surveys on Operational and Stress Factors
This quantitative method is effective for measuring the prevalence of specific issues, such as work-related stress, and its impact on operational requirements.
- Objective: To quantify work-related stress levels, organizational practices, and resource gaps among specific forensic professional groups, such as medicolegal death investigators (MDIs) or digital evidence examiners [18].
- Materials:
- A validated survey instrument, which may include standardized scales (e.g., for PTSD, depression, burnout, coping self-efficacy).
- A secure online survey platform (e.g., Qualtrics).
- Statistical analysis software (e.g., R, SPSS).
- Methodology:
- Sampling: Administer a cross-sectional survey to a large, national sample of the target professional group (e.g., 1,000 MDIs) [18].
- Measures: The survey should capture:
- Demographic and professional background.
- Frequency and duration of exposure to traumatic materials.
- Levels of stress, depression, and burnout using validated scales.
- Perceptions of organizational support and availability of wellness resources.
- Current agency mitigation practices and perceived barriers to wellness.
- Data Analysis: Use descriptive statistics to summarize findings. Employ inferential statistics (e.g., regression analysis) to identify relationships between variables, such as the correlation between organizational wellness culture and reduced burnout [18].
- Outcome Measures: Quantitative data on the prevalence of stressors, gaps in protective practices, and statistically significant factors that impact workforce resilience and, by extension, operational reliability.
Essential Research Reagents and Tools for Stakeholder Analysis
Table 2: Research Reagent Solutions for Stakeholder Requirement Studies
| Item / Tool | Function in Stakeholder Research |
|---|---|
| Qualitative Data Analysis Software (e.g., NVivo) | Facilitates the organization, coding, and thematic analysis of complex textual data from interviews and open-ended survey questions. |
| Video Conferencing Platform (e.g., Zoom) | Enables remote, face-to-face data collection via semi-structured interviews, allowing for a wider geographical reach of participants [17]. |
| Validated Psychometric Scales | Provides objective, quantitative measures of psychological constructs like stress, trauma, burnout, and coping self-efficacy within survey-based research [18]. |
| Statistical Analysis Software (e.g., R, SPSS, SAS) | Used to perform descriptive and inferential statistical analyses on quantitative survey data, identifying significant patterns and correlations. |
| Validation Plan Template | A structured document (as recommended by FCN) that guides the process of defining and documenting end-user requirements, acceptance criteria, and testing protocols [7]. |
Visualizing Stakeholder Relationships and Validation Workflows
The following diagrams, generated using Graphviz DOT language, illustrate the complex relationships within the stakeholder ecosystem and the iterative process of integrating their requirements into method validation.
Diagram 1: Forensic Method Stakeholder Ecosystem
Diagram 2: Requirement-Driven Validation Workflow
The journey of a forensic method from development to courtroom acceptance is paved by the requirements of its diverse stakeholders. A systematic approach to identifying these groups—encompassing forensic practitioners, judicial actors, standard-setting bodies, and oversight entities—and rigorously eliciting their needs is not optional but fundamental to scientific validity and legal robustness. By employing structured methodologies, such as semi-structured interviews and national surveys, researchers can capture the critical data necessary to define fitness-for-purpose. Integrating these end-user requirements into every stage of the validation lifecycle, as visualized in the provided workflows, ensures that forensic methods are not only scientifically sound but also legally defensible, operationally viable, and ultimately, trustworthy pillars of the justice system.
Translating Investigative Needs into Testable Technical Specifications
In forensic method validation research, the accuracy, reliability, and admissibility of scientific evidence depend fundamentally on a rigorous foundation of well-defined technical specifications. This process begins with the precise articulation of investigative needs—the complex problems and questions arising from forensic casework—and their systematic translation into testable technical specifications for analytical methods. This translation ensures that developed methods are not only scientifically sound but also legally defensible and practically applicable to real-world scenarios. The core challenge lies in transforming often-qualitative user requirements from various stakeholders—including laboratory analysts, legal professionals, and law enforcement investigators—into unambiguous, quantifiable parameters that can be systematically validated. This guide provides a structured framework for bridging this critical gap, enabling researchers and drug development professionals to create robust validation protocols that stand up to scientific and legal scrutiny.
Foundational Concepts: User Needs and Requirements
Understanding User Needs
User needs represent the fundamental desires, goals, and expectations of end-users when they interact with a product, system, or, in this context, a forensic method [19]. In forensic science, these needs extend beyond basic functionality to encompass critical factors such as reliability, reproducibility, sensitivity, specificity, and legal admissibility. A key challenge is that users may not always articulate these needs explicitly or may express them as solutions rather than underlying problems. The famous adage attributed to Henry Ford illustrates this point: "If I asked people what they wanted, they would have said faster horses" [20]. Therefore, the researcher's role involves deep investigation to uncover the real needs behind stated requests through careful observation and empathetic engagement with the forensic workflow.
Classifying User Requirements
User requirements can be systematically categorized to ensure comprehensive coverage of all critical aspects. Understanding these categories helps in structuring technical specifications that address the full spectrum of user needs [21]:
Table: Types of User Requirements in Forensic Method Development
| Requirement Type | Definition | Forensic Science Examples |
|---|---|---|
| Functional Requirements | Specific functionalities and behaviors the system must exhibit | Method must detect target analyte at concentrations ≤ 5 ng/mL; Must distinguish between structural isomers; Must generate interpretable output within 4 hours |
| Usability Requirements | Aspects related to user interaction efficiency and effectiveness | Method protocol must be executable by trained analysts with ≤ 2 hours training; Critical steps must have clear indicators; Error recovery must be possible without sample loss |
| User Interface Requirements | Visual design, layout, and presentation elements | Software interface must display chromatograms with adjustable scaling; Results must be exportable in standardized reporting formats; Alert thresholds must be visually distinct |
A Framework for Translating Needs into Specifications
The User Need Statement Framework
A powerful tool for initiating the translation process is the user need statement, a structured approach that captures who the user is, what they need, and why that need is important [20]. This three-part format follows the pattern: [A user] needs [need] in order to accomplish [goal].
In forensic contexts, this might translate to: "A forensic toxicologist needs to reliably quantify 12 common benzodiazepines and their metabolites in blood samples at concentrations as low as 0.5 ng/mL in order to provide conclusive evidence for impaired driving cases that meets Daubert standards."
This statement format offers multiple benefits for the validation process:
- Captures the user and the need: Distills complex research insights into a single, actionable sentence
- Aligns the team: Serves as a consistent reference point for all team members and stakeholders
- Identifies a benchmark for success: Provides a clear metric for validation before ideation and prototyping begin
From Needs to Technical Specifications
The transition from user need statements to testable specifications requires systematic decomposition of each need into measurable parameters. The following workflow diagram illustrates this translation process:
Specification Development Methodology
The translation process employs several critical techniques to ensure comprehensive specification development:
Stakeholder Analysis: Actively involve all relevant stakeholders—including laboratory analysts, quality managers, legal experts, and instrument specialists—throughout the requirement gathering process [21]. Conduct structured workshops and interviews to capture diverse perspectives and ensure alignment.
User Stories and Use Cases: Employ narrative formats to capture requirements from the user's perspective [21]. For example: "As a forensic chemist, I need to automatically flag potential isobaric interferences so that I can focus verification efforts on high-risk samples." These stories should include acceptance criteria that define when the requirement is satisfied.
Gap Analysis: Compare current capabilities with desired outcomes to identify specific technical hurdles [12]. This involves assessing existing instrumentation, methodology, and expertise against the requirements of the new method.
Quantitative Technical Specifications for Forensic Validation
Core Performance Parameters
For forensic method validation, user needs must be translated into specific, quantifiable parameters that can be systematically tested. The following table summarizes critical technical specifications derived from common investigative needs:
Table: Technical Specifications for Forensic Toxicology Method Validation
| Investigative Need | Technical Parameter | Testable Specification | Acceptance Criterion |
|---|---|---|---|
| Detect minute quantities of analyte | Sensitivity | Limit of Detection (LOD) | ≤ 0.1 ng/mL with signal-to-noise ratio ≥ 3:1 |
| Accurately measure concentration | Accuracy | Percent recovery of known standards | 85-115% across calibration range |
| Produce consistent results | Precision | Relative Standard Deviation (RSD) | Intra-day RSD ≤ 5%; Inter-day RSD ≤ 10% |
| Distinguish target from interferents | Specificity | Resolution from closest eluting interferent | Resolution factor ≥ 1.5 for all structurally similar compounds |
| Handle realistic sample volumes | Extraction Efficiency | Absolute recovery | ≥ 70% across low, medium, and high QC concentrations |
| Ensure method robustness | Ruggedness | RSD under varied conditions | ≤ 8% when operator, instrument, or day is changed |
Experimental Protocol for Key Parameters
For each technical specification, a detailed experimental protocol must be developed to ensure consistent testing and evaluation:
Protocol for Determining Limit of Detection (LOD) and Limit of Quantification (LOQ):
- Prepare a series of standard solutions at decreasing concentrations (e.g., 5, 1, 0.5, 0.1, 0.05, 0.01 ng/mL)
- Analyze each concentration in replicates (n=6) using the complete method
- Plot signal-to-noise ratio (S/N) versus concentration
- LOD = Concentration where S/N ≥ 3:1
- LOQ = Concentration where S/N ≥ 10:1 with precision ≤ 15% RSD
- Verify by independent preparation and analysis of standards at the determined LOD and LOQ concentrations
Protocol for Establishing Precision:
- Prepare quality control samples at three concentrations (low, medium, high) covering the calibration range
- Analyze six replicates of each QC level within a single analytical batch (intra-day precision)
- Repeat analysis of QC samples across three separate analytical batches (inter-day precision)
- Calculate mean, standard deviation, and relative standard deviation (%RSD) for each set
- Compare results against pre-defined acceptance criteria
The relationship between these experimental protocols and their role in method validation can be visualized as follows:
The Scientist's Toolkit: Essential Research Reagents and Materials
The translation of investigative needs into testable specifications requires specific materials and reagents that ensure methodological rigor and reproducibility. The following table catalogues essential components for forensic method development and validation:
Table: Essential Research Reagents for Forensic Method Development
| Reagent/Material | Technical Function | Application Example |
|---|---|---|
| Certified Reference Standards | Provides known identity and purity for quantification | Creating calibration curves for targeted analyte quantification |
| Stable Isotope-Labeled Internal Standards | Compensates for matrix effects and procedural losses | Correcting for extraction efficiency variations in complex biological matrices |
| Mass Spectrometry-Grade Solvents | Minimizes background interference and ion suppression | Mobile phase preparation for LC-MS/MS to maintain signal stability |
| Solid Phase Extraction Cartridges | Isolates and concentrates analytes from complex matrices | Extracting drugs of abuse from blood or urine samples prior to analysis |
| Derivatization Reagents | Enhances detection characteristics of target compounds | Improving chromatographic behavior or mass spectrometric response |
| Quality Control Materials | Monitors method performance over time | Inter-laboratory reproducibility assessment and longitudinal performance tracking |
Validation and Verification of Technical Specifications
Establishing Validation Protocols
Once technical specifications have been defined, rigorous validation protocols must be established to verify that each specification can be met consistently. This involves designing experiments that stress the method under conditions mimicking real-world scenarios. For forensic applications, this includes testing with case-type samples that may contain complex matrices, potential interferents, and analyte concentrations at the extremes of the measuring range.
The validation process should employ a combination of descriptive statistics to summarize data characteristics (mean, standard deviation, range) and inferential statistics to make generalizations about method performance [12]. For example, regression analysis demonstrates the relationship between instrument response and analyte concentration, while t-tests or ANOVA can determine if significant differences exist between results obtained under varying conditions.
Data Visualization for Method Validation
Appropriate data visualization is essential for interpreting validation data and demonstrating that technical specifications have been met. The selection of visualization methods should match the data type and analytical question [22]:
Table: Data Visualization Methods for Technical Specification Validation
| Analytical Question | Recommended Visualization | Application Example |
|---|---|---|
| Comparison of means between groups | Box plots or bar charts | Comparing extraction efficiency across different sample preparation methods |
| Distribution of continuous data | Histograms or dot plots | Assessing normality of calibration curve residuals |
| Relationship between variables | Scatter plots with regression lines | Demonstrating linearity of detector response across concentration range |
| Monitoring process over time | Control charts or line graphs | Tracking quality control results across multiple analytical batches |
The translation of investigative needs into testable technical specifications represents a critical pathway to forensically sound, legally defensible analytical methods. This process requires systematic decomposition of often-vague user requirements into discrete, measurable parameters that can be objectively validated. By employing the structured frameworks, classification systems, and visualization tools presented in this guide, researchers and drug development professionals can create validation protocols that not only meet scientific standards but also address the practical realities of forensic casework. The ultimate goal is to establish a clear, documented chain of logic connecting investigative needs to technical capabilities, ensuring that analytical methods produce reliable evidence that withstands scientific and legal scrutiny.
Inadequate definition of end-user requirements during the initial phases of forensic method validation introduces profound legal and scientific risks that compromise the entire judicial process. Poorly specified requirements lead to non-compliance with international standards, admissibility challenges of scientific evidence in legal proceedings, and fundamental failures in scientific reproducibility. Within forensic science research and practice, where methods must be demonstrably fit-for-purpose, the failure to precisely capture and validate against end-user needs creates cascading vulnerabilities across the criminal justice system. This technical guide examines these interconnected risks through quantitative analysis, experimental protocols, and conceptual frameworks, providing researchers and drug development professionals with structured approaches for mitigating liability through robust requirement definition.
The validation of forensic methods constitutes a comprehensive scientific study designed to produce objective evidence that a method, process, or piece of equipment is fit for its specific intended purpose [7]. Within this framework, the precise definition of end-user requirements establishes the foundational criteria against which all validation activities are measured. These requirements specify the operational context, performance thresholds, and analytical outputs necessary for a method to reliably support legal conclusions.
Inadequate requirement definition creates a latent vulnerability at the most critical phase of method development—the point at which scientific capability is formally linked to legal utility. When requirements are ambiguous, incomplete, or misaligned with actual forensic needs, the resulting validation gaps propagate through subsequent scientific processes, ultimately manifesting as legal challenges to evidence, reproducibility failures in independent verification studies, and operational breakdowns in casework applications. The following sections detail the specific legal and scientific consequences of these deficiencies, supported by quantitative data and analytical frameworks.
Legal Consequences of Inadequate Requirement Definition
Regulatory Non-Compliance and Legal Liability
Forensic science operates within a stringent regulatory landscape where method validation is mandated by codes of practice such as the Forensic Science Regulator's requirements [7]. Inadequate requirement definition directly violates the fundamental principle of establishing "objective evidence that a finalised method, process, or equipment is fit for the specific purpose intended" [7]. This failure constitutes regulatory non-compliance with cascading legal implications:
- Civil Liability: Organizations may face negligence claims when inadequate requirements lead to erroneous results causing harm. Legal liability arises from breaches of "duty of care" where entities fail to implement necessary precautions to protect stakeholders [23].
- Regulatory Penalties: Non-compliant organizations face civil and criminal liabilities, including fines, sanctions, and operational restrictions. Regulatory authorities may impose significant financial penalties or even revoke licenses and permits [23] [24].
- Contractual Disputes: Ambiguous requirements in forensic service contracts lead to disputes over performance, delivery, and intellectual property clauses, potentially resulting in litigation and damaged stakeholder relationships [25].
Table 1: Financial and Operational Consequences of Legal Non-Compliance
| Consequence Type | Specific Impact | Quantitative Measure |
|---|---|---|
| Financial Penalties | Cost of non-compliance | 2.71x higher than compliance costs (averaging $14.82M annually) [25] |
| Data breach costs | Global average of $4.88M per incident (2024) [25] | |
| Operational Disruption | Regulatory proceedings | 61% of companies faced ≥1 proceeding (avg. 3.9 proceedings) [25] |
| Litigation volume | Median of 6 lawsuits per company (42% expected increase) [25] |
Evidence Admissibility Challenges
In legal proceedings, the admission of forensic evidence hinges on its reliability, validity, and relevance. Courts increasingly scrutinize the methodological foundations of forensic evidence, particularly the rigor of validation processes [7]. Inadequately defined requirements create critical vulnerabilities in this admissibility framework:
- Interpretation Challenges: Methods lacking clear requirement boundaries enable contradictory interpretations of identical evidence, potentially leading to miscarriages of justice [4].
- Context Misalignment: Requirements that fail to specify operational conditions may produce valid results in laboratory settings that nevertheless misrepresent real-world forensic scenarios [26].
- Documentation Deficiencies: Inadequate documentation of requirement definition processes impedes the ability to demonstrate methodological rigor during legal challenges [23].
The implementation of ISO 21043 for forensic sciences further institutionalizes the necessity of precise requirement definition, emphasizing vocabulary standardization, interpretation protocols, and reporting consistency as essential components of legally defensible forensic practice [4].
Scientific Risks of Inadequate Requirement Definition
Reproducibility and Replicability Failures
The scientific credibility of forensic methods depends fundamentally on their reproducibility—the ability to consistently obtain the same results when studies are repeated under specified conditions. Inadequate requirement definition directly undermines this foundation by introducing methodological ambiguities that propagate through experimental workflows.
Table 2: Taxonomy of Reproducibility Types in Scientific Research
| Reproducibility Type | Core Definition | Validation Focus |
|---|---|---|
| Type A: Methods Reproducibility | Ability to implement identical computational procedures with same data/tools [27] | Verification of analytical pipelines |
| Type B: Results Reproducibility | Production of corroborating results using same experimental methods [27] | Direct replication studies |
| Type C: Inferential Reproducibility | Drawing qualitatively similar conclusions from independent replication [28] | Theoretical framework validation |
| Type D: Cumulative Reproducibility | New data from same laboratory produces same conclusion [27] | Internal consistency assessment |
| Type E: Independent Reproducibility | New data from different laboratory produces same conclusion [27] | External validity verification |
Research demonstrates alarming reproducibility failure rates across scientific domains. In preclinical cancer research, 47 of 53 published papers could not be validated despite attempts to consult original authors [27]. Similarly, large-scale replication efforts in psychology have confirmed only 40% of positive effects and 80% of null effects [27]. These systematic reproducibility failures frequently originate from poorly defined methodological requirements that permit uncontrolled variability across experimental implementations.
Methodological Limitations and Validation Gaps
Forensic method validation requires comprehensive testing of method limits, identification of potential error sources, and clear communication of limitations [7]. Inadequate requirement definition creates fundamental validation gaps:
- Uncalibrated Error Rates: Requirements that fail to specify acceptable error thresholds prevent meaningful measurement of method reliability and accuracy [26].
- Context Insensitivity: Methods validated against narrow requirements may perform poorly when applied to novel evidentiary materials or atypical casework scenarios [7].
- Instrumentation Dependencies: Requirements that omit specification of necessary equipment capabilities create interoperability challenges and introduce unquantified technical variability [26].
The conceptual relationship between requirement definition, validation activities, and scientific/legal risks can be visualized through the following workflow:
Experimental Protocols for Requirement Validation
Protocol 1: Digital Forensic Location Data Validation
The validation of location data in digital forensics exemplifies the critical importance of precise requirement definition. This protocol addresses the specific risk of misinterpretation between carved and parsed location data [26]:
Objective: To validate that location artifacts (GPS coordinates, Wi-Fi access points, cell tower data) accurately represent real-world device presence and movement patterns.
Required Materials:
- Forensic imaging tools (e.g., Cellebrite UFED, FTK Imager)
- Analytical software (e.g., Cellebrite Physical Analyzer, X-Ways)
- Reference devices with known location history
- Documentation framework for recording validation outcomes
Experimental Workflow:
- Data Extraction: Create forensic images of test devices with known location history using multiple extraction methods.
- Parsed Data Analysis: Extract location records from known database schemas (e.g., Cache.sqlite from Apple's RoutineD service on iOS devices).
- Carved Data Analysis: Perform pattern-based carving for location coordinates in unallocated space and app cache files.
- Corroborative Validation: Compare parsed and carved results against known device location history.
- Contextual Analysis: Examine source files and surrounding bytes for carved artifacts to determine semantic context.
- Error Quantification: Document false positive rates, coordinate precision variances, and timestamp misinterpretations.
Validation Metrics:
- Coordinate precision tolerance: ≤10 meters for high-confidence locations
- Timestamp synchronization: ≤60 seconds for correlated events
- False positive rate: ≤5% for carved location artifacts
This protocol demonstrates how explicitly defined accuracy requirements enable meaningful validation and prevent the presentation of misleading digital evidence in legal proceedings [26].
Protocol 2: Method Transfer Verification Between Laboratories
The transfer of validated methods between laboratories represents a critical point where inadequate requirement definition creates reproducibility failures:
Objective: To verify that a forensic method validated in one laboratory produces equivalent results when implemented in a different laboratory setting.
Required Materials:
- Standardized reference materials with known properties
- Identical or comparable analytical instrumentation
- Detailed method documentation including acceptance criteria
- Statistical analysis package for comparative analysis
Experimental Workflow:
- Documentation Review: The receiving laboratory reviews all method requirements, including equipment specifications, reagent qualifications, and procedural tolerances.
- Training and Knowledge Transfer: Personnel from the implementing laboratory receive training from the originating laboratory.
- Blinded Sample Analysis: Both laboratories analyze identical reference materials using the transferred method.
- Statistical Comparison: Results are compared using pre-defined equivalence criteria (e.g., statistical significance threshold of p<0.05, Cohen's d<0.5 for effect size).
- Proficiency Assessment: Implementing laboratory analysts demonstrate competency through successful analysis of proficiency test materials.
Validation Metrics:
- Inter-laboratory correlation coefficient: ≥0.95
- Mean difference between results: ≤5% of measured value
- Success rate on proficiency tests: ≥90%
This verification protocol directly addresses the "reproducibility crisis" documented across scientific disciplines by ensuring that methodological requirements contain sufficient specificity to enable successful implementation across different laboratory environments [27].
The Scientist's Toolkit: Essential Research Reagent Solutions
Table 3: Essential Research Reagent Solutions for Forensic Method Validation
| Reagent/Material | Function in Validation | Critical Quality Attributes |
|---|---|---|
| Certified Reference Materials | Provide ground truth for method accuracy assessment | Documented purity, traceable certification, stability data |
| Negative Control Matrices | Establish baseline signals and interference thresholds | Representative composition, documented lot variability |
| Proficiency Test Panels | Assess analyst competency and method robustness | Blind coding, realistic concentrations, stability documentation |
| Internal Standard Solutions | Correct for analytical variability and instrument drift | Isotopic purity, chemical stability, compatibility with analytes |
| Quality Control Materials | Monitor method performance over time | Defined acceptance ranges, long-term stability |
| Inhibitor Testing Materials | Identify sample-specific interferences | Representative inhibitor profiles, concentration gradients |
The selection and qualification of these research reagents must be explicitly guided by end-user requirements that specify the necessary analytical sensitivity, specificity, and reliability needed for casework applications. Each reagent must be documented according to ISO 21043 standards for forensic vocabulary and reporting requirements [4].
Inadequate definition of end-user requirements creates interconnected legal and scientific risks that undermine the validity and reliability of forensic science. The consequences extend beyond individual casework to impact systemic trust in criminal justice outcomes. Robust requirement definition establishes the necessary foundation for method validation, reproducibility verification, and legal defensibility.
Forensic researchers and drug development professionals must implement structured approaches to requirement definition that explicitly link scientific capabilities to operational needs. This includes the development of comprehensive validation protocols, standardized documentation practices, and reproducibility assessments throughout the method lifecycle. By addressing these fundamental requirements, the forensic science community can enhance scientific credibility, reduce legal vulnerabilities, and fulfill its essential role in the justice system.
From Concept to Criteria: A Step-by-Step Methodology for Defining and Documenting Requirements
Conducting a Stakeholder Analysis to Capture All End-User Needs
In forensic science, the validity of a method is fundamentally determined by its fitness for purpose [1]. This principle places the accurate identification and understanding of end-user needs at the very foundation of reliable forensic method validation research. Forensic science is an applied discipline where scientific principles are employed to obtain results that investigating officers and courts can expect to be reliable [1]. The process of validation involves providing objective evidence that a method, process, or device is fit for its specific intended purpose, ensuring results can be relied upon within the criminal justice system [1]. When courts assess the reliability of expert opinion, they explicitly consider "the extent and quality of the data on which the expert's opinion is based, and the validity of the methods by which they were obtained" [1].
Stakeholder analysis serves as the critical bridge between technical method development and real-world applicability. Without systematic identification of all relevant stakeholders and their requirements, forensic methods risk being technically sound but practically inadequate. The goal of validation is for both the user of the method (the forensic unit) and the user of any information derived from it (the end user) to be confident about whether the method is fit for purpose while understanding its limitations [1]. This confidence can only be established when stakeholder needs are comprehensively captured and translated into measurable requirements. In the context of evolving international standards like ISO 21043, which covers the entire forensic process from recovery to reporting, the formalization of stakeholder needs becomes increasingly paramount [4].
Defining Stakeholders in the Forensic Ecosystem
Primary Stakeholder Categories
The forensic science ecosystem comprises multiple stakeholder groups with varying needs and expectations. Properly classifying these groups ensures comprehensive coverage during requirements gathering.
Table 1: Key Stakeholder Categories in Forensic Method Validation
| Stakeholder Category | Key Representatives | Primary Needs and Concerns |
|---|---|---|
| End Users of Information | Investigating Officers, Prosecutors, Defense Attorneys, Judges, Juries | Reliable, interpretable results; understanding of limitations; adherence to legal standards; clarity in reporting [1] [4] |
| Method Operators | Forensic Practitioners, Laboratory Analysts, Digital Forensic Examiners | Robust, reproducible protocols; clear operating procedures; adequate training; competent tools; quality control mechanisms [1] [5] |
| Method Developers | In-house Developers, Tool Vendors, Research Scientists, Software Engineers | Detailed technical specifications; performance parameters; resource constraints; integration capabilities [1] [5] |
| Oversight Bodies | Accreditation Bodies, Forensic Science Regulator, Quality Managers | Compliance with standards (ISO 17025); validation records; competency frameworks; quality assurance [1] [29] |
| Indirect Stakeholders | Victims, Defendants, General Public | Impartiality; scientific rigor; procedural fairness; privacy considerations [29] |
The Stakeholder Identification Process
Identifying stakeholders is an iterative process that should begin during the initial planning phase of method development or adoption. The first step involves brainstorming a comprehensive list of all individuals, groups, or organizations affected by the implementation and outputs of the forensic method. This includes those who provide input to the process, are involved in its operation, or use its results for decision-making.
Following initial identification, categorization and prioritization are essential. A power-interest grid can be a valuable tool for this purpose, helping to classify stakeholders based on their level of influence over the project and their interest in its outcomes. This analysis guides the development of an appropriate engagement strategy for each group. High-power, high-interest stakeholders, for instance, require close management and active involvement, while those with low power and low interest may simply need monitoring. The final component is documenting stakeholder attributes, including their specific roles, expectations, potential influence on the project, and key concerns related to the method's performance and output.
Methodologies for Eliciting End-User Requirements
Research and Engagement Techniques
Capturing the authentic voice of the customer requires structured and multifaceted research approaches. No single method can fully illuminate all aspects of user needs; a combination of techniques provides the most robust understanding.
- Observational Techniques: Methods like job shadowing and ethnography involve spending significant time with device users in their actual working environment [30]. This approach allows researchers to witness firsthand the challenges, workarounds, and contextual factors that users might not think to verbalize in an interview setting.
- Interviewing Techniques: Individual interviews and focus groups provide a direct channel for understanding user perspectives [31] [30]. These structured conversations should explore users' current workflows, pain points with existing methods, and desired outcomes from a new solution.
- Usability Techniques: Contextual inquiries or cognitive walkthroughs involve asking users to perform specific tasks while verbalizing their thought process [30]. This technique is particularly effective for understanding the cognitive load associated with a method and identifying interface or process improvements.
- Market Research Techniques: A competitive analysis of similar products or methods can reveal established user expectations and identify gaps in current market offerings [30]. Reviewing validation records from adopted methods used in other organizations can also provide valuable insights [1].
A Framework for Remote Engagement
The COVID-19 pandemic necessitated the development of robust remote engagement frameworks, which remain valuable for reaching geographically dispersed stakeholders. One such framework, developed for security research projects, consists of four key steps designed to assure high-quality user requirement collection in online settings [31].
Stakeholder Engagement Framework
This systematic approach ensures that requirements are not only gathered but also evaluated, prioritized, and technically assessed. The framework offers a structured methodology that is easily adaptable to different forensic contexts and project types, while mitigating drawbacks associated with remote collaboration such as reduced informal networking opportunities [31].
Translating Stakeholder Needs into Technical Requirements
Distinguishing User Needs from Requirements
A critical step in the process is the formal translation of broadly-stated user needs into specific, testable technical requirements. This translation forms the foundation for both method development and subsequent validation.
Table 2: Translation from User Needs to Technical Requirements
| User Need (Stakeholder Perspective) | Technical Requirement (Validation Perspective) | Acceptance Criteria |
|---|---|---|
| "As a digital forensic examiner, I need to efficiently extract data from mobile devices." | The method must successfully extract a minimum of 95% of user-generated data (SMS, contacts, images) from supported iOS and Android devices. | Data extraction completeness is measured against a known reference set and meets the 95% threshold across 20 test devices. |
| "As a forensic biologist, I need to distinguish between multiple contributors in a DNA mixture." | The probabilistic genotyping software must accurately estimate the number of contributors in mixtures of 2-4 individuals with 98% accuracy. | Performance is validated using 100 simulated mixtures with known ground truth; contributor number is correctly estimated in ≥98 instances. |
| "As a reporting officer, I need to understand the limitations of the method for court testimony." | The method documentation must clearly state limitations regarding sample quality, known interferences, and statistical uncertainty. | A limitations section is included in the validation report and standard operating procedure, reviewed and approved by quality assurance. |
| "As a laboratory manager, I need the method to be executable by trained staff within a reasonable timeframe." | The method must be completed by a competent practitioner within 4 hours for 90% of standard casework samples. | 30 samples are processed by different practitioners; processing time is recorded and analyzed for compliance. |
The distinction between needs and requirements is crucial: user needs describe what the user wants to achieve, focusing on the problem to be solved (e.g., "accurately identify lung nodules"), while requirements specify what the software or method must do to meet those needs (e.g., "detect lung nodules with a sensitivity of 95%") [32]. User needs are written from the user's perspective, typically starting with "User needs to...", while requirements are written from a technical viewpoint, usually beginning with "Software must..." or "The method must..." [32].
Establishing Acceptance Criteria and Testable Specifications
The translation process culminates in establishing clear acceptance criteria—the measurable standards against which the method's performance will be validated. Well-defined acceptance criteria should be Specific, Measurable, Achievable, Relevant, and Time-bound (SMART) where applicable. For a novel digital forensic method, this might involve specifications for data recovery rates, processing speed, accuracy metrics, and defined limitations. The objective evidence that a method meets its acceptance criteria is the test data generated during validation, making the design of these tests critical [1]. The data for all validation studies must be representative of real-life use and include challenges that can stress-test the method to understand its boundaries [1].
Experimental Protocols for Requirements Validation
Protocol for General Method Validation
For general validation conducted prior to a method's introduction into live casework, a rigorous experimental protocol is required.
- Experimental Design: The validation plan must include a technical specification of how the method is expected to operate, testable end-user requirements, and defined acceptance criteria [5]. The experimental design should incorporate a range of test materials that represent the expected casework spectrum, including challenging scenarios that push methodological boundaries.
- Test Material Selection: Data for validation studies must be representative of the real-life use the method will be put to [1]. If the method has not been tested before, the validation must include data challenges that can stress-test the method [1]. This includes using authentic samples that cover the expected variation in sample quality and type.
- Performance Metrics: The validation should systematically test the accuracy, reliability, reproducibility, sensitivity, specificity, and robustness of the method [29] [5]. These metrics should be directly traceable to the established user needs and technical requirements.
- Environmental Conditions: Validation should take place in the environment where the method will operate, using the same software, hardware, and consumables intended for routine use [5]. Practitioners involved in validation testing must be competent in applying the method.
- Documentation and Reporting: A comprehensive validation report must document the results, including any limitations and caveats for the method's use [1] [5]. The report should clearly demonstrate how the test data shows compliance with the acceptance criteria.
The Researcher's Toolkit: Essential Materials for Validation Studies
Table 3: Essential Research Reagents and Materials for Forensic Validation
| Item/Category | Function in Validation | Example Application in Forensic Science |
|---|---|---|
| Reference Materials | Provide ground truth for accuracy assessment | Certified DNA standards, known synthetic drug mixtures, digital reference images with known artifacts [29] |
| Mock Casework Samples | Simulate real-world evidence under controlled conditions | Created bloodstains on various fabrics, prepared digital devices with known data sets, synthetic microbial mixtures [29] |
| Calibration Standards | Ensure analytical instrument accuracy and precision | Mass spectrometry calibration solutions, color calibration cards for imaging, frequency standards for audio analysis |
| Negative Controls | Detect contamination, false positives, or background interference | Sterile swabs from evidence collection kits, blank extraction samples, clean storage media for digital forensics [29] |
| Positive Controls | Verify that the method produces expected results with known inputs | Samples with known analytical results, reference algorithms with certified outputs, confirmed microbial strains [29] |
Implementing the Analysis: From Theory to Practice
The Validation Workflow Integrating Stakeholder Needs
The complete workflow for method validation, integrating stakeholder analysis, can be visualized as a continuous process where stakeholder needs inform every stage.
End-to-End Validation Workflow
This workflow, adapted from the framework published in the Forensic Science Regulator's Codes, shows the logical sequence of stages in method validation [1]. The process begins with stakeholder analysis and requirement definition, progresses through technical specification and testing, and culminates in a validation report that documents the method's fitness for purpose. While represented linearly, the process is often iterative, with lessons learned at later stages potentially requiring revisiting earlier phases.
Addressing Common Implementation Challenges
Several challenges commonly arise when implementing stakeholder analysis in forensic method validation. Incorrect or changing requirements pose a significant risk, potentially jeopardizing project success or increasing development costs [31]. A structured change control process is essential for managing requirement evolution while maintaining validation integrity. Limited stakeholder availability, particularly among end-users like investigators or prosecutors, can hinder requirements gathering. Creative engagement strategies, including the remote framework previously discussed, can help overcome these limitations [31].
The lack of validation training and expertise among forensic practitioners represents another barrier [5]. Organizations should invest in developing these competencies, potentially making method validation a formal part of practitioner competency requirements. Finally, the increasing reliance on machine-generated results and complex analytical tools necessitates particularly rigorous validation, as the accuracy and reliability of these "black box" systems may not be immediately apparent [5]. For tools adopted from vendors, forensic units must review available validation records to ensure they are fit for purpose, even when the tool itself is not subject to full re-validation by the laboratory [1].
A meticulously conducted stakeholder analysis is not merely an administrative prerequisite but a scientific imperative for developing forensically sound methods. In an era of increasing methodological complexity and scrutiny, the systematic identification of end-user needs provides the foundational justification for validation parameters and acceptance criteria. The process ensures that the resulting validated methods are not only scientifically robust but also practically relevant and legally defensible. As international standards continue to evolve and emerging technologies transform forensic practice, the principles outlined in this guide will remain essential for maintaining the integrity, reliability, and relevance of forensic science within the criminal justice system.
In forensic method validation research, the precise structuring of requirements is not merely a procedural step but a scientific and legal imperative. Defensible forensic results, which can seriously impact the liberties of individuals or even justify a government's military response, rely on methods that are scientifically robust and legally admissible [33]. The process begins with a clear articulation of what the method must accomplish (functional requirements) and how well it must perform (non-functional requirements), leading to the establishment of objective, data-driven acceptance criteria. These criteria form the foundation for validation studies, providing the measurable benchmarks that demonstrate a method is fit-for-purpose within the stringent context of forensic science and drug development.
Core Concepts: Functional and Non-Functional Requirements
Requirements analysis is an essential process that helps determine whether a system or project will meet its objectives. To make this analysis effective, requirements are generally divided into two primary categories: functional and non-functional [34].
Functional Requirements: Defining What the System Does
Functional requirements define the specific features and operations a system must perform to meet business and user needs. They describe what the system should do and how it should interact with users or other systems, focusing on system behavior and functionality that can be directly observed and tested in the final product [34] [35].
In the context of forensic method validation, functional requirements translate to the specific analytical tasks the method must perform. For a microbial forensics method, this might include the ability to identify a specific bacterial species, detect the presence of a particular toxin, or determine the genetic lineage of a pathogen [33].
Non-Functional Requirements: Defining How the System Performs
Non-functional requirements define how a system should operate, focusing on performance, reliability, and user experience rather than specific features. They ensure the system is efficient, secure, and maintainable over time [34] [35]. These requirements shape the user experience by ensuring efficiency, reliability, and smooth operation, and are verified via performance, security, and usability testing [34].
For forensic methods, non-functional requirements are particularly critical as they directly impact the legal defensibility of the results. They include parameters such as sensitivity, specificity, reproducibility, and robustness—all of which must be rigorously validated [33] [36].
Table 1: Core Differences Between Functional and Non-Functional Requirements
| Aspect | Functional Requirements | Non-Functional Requirements |
|---|---|---|
| Definition | What the system should do, its exact features, tasks, or operations [34] | How the system should perform, its qualities or attributes like speed, security, or usability [34] |
| Purpose | Focus on the behavior and features of the system [34] | Focus on the performance, usability, and overall quality of the system [34] |
| Measurement | Easily measured by verifying outputs or results [34] | Harder to measure, often validated against benchmarks, metrics, or SLAs [34] |
| Impact on Development | Drive the core design and features of the system [34] | Influence the system architecture and performance optimization [34] |
| User Perspective | Directly visible to users and tied to business needs [34] | Shape the user experience by ensuring efficiency and reliability [34] |
| Evaluation | Validated through functional testing (unit, integration, or acceptance tests) [34] | Verified via performance, security, and usability testing [34] |
The Interrelationship in Forensic Context
The relationship between functional and non-functional requirements in forensic method development is symbiotic. While functional requirements define the fundamental purpose of the method, non-functional requirements establish the necessary quality standards that make the results admissible in legal proceedings [37]. For example, a DNA testing method's functional requirement might be to identify specific STR markers, while its non-functional requirements would mandate that the results be reproducible, with known error rates and defined sensitivity limits [36].
Acceptance Criteria as the Bridge to Validation
Acceptance criteria serve as the critical bridge between requirements and validation, providing the measurable standards against which a method's performance is judged.
Defining Acceptance Criteria in Analytical Method Validation
In analytical science, acceptance criteria are internal values used to assess the consistency of the process at less critical steps [38]. They define the allowable contribution of method error in product performance and become crucial when building product knowledge, process understanding, and the associated long-term product lifecycle control [39].
The fundamental principle for establishing effective acceptance criteria is that method error should be evaluated relative to the specification tolerance for two-sided limits or margin for one-sided limits [39]. This approach answers the critical question: "How much of the specification tolerance is consumed by the analytical method?"
Regulatory Context and Importance
Regulatory guidance documents emphasize that acceptance criteria must be consistent with the intended use of the method [39]. The U.S. Pharmacopeia (USP) <1225> states that "the validation target acceptance criteria should be chosen to minimize the risks inherent in making decisions from bioassay measurements and to be reasonable in terms of the capability of the art" [39].
Well-defined acceptance criteria are mandatory to correctly validate an analytical method and understand its contribution when quantitating product performance or releasing a batch. Methods with excessive error will directly impact product acceptance out-of-specification (OOS) rates and provide misleading information regarding product quality [39].
Structured Framework for Forensic Method Validation
The validation of forensic methods follows a structured framework with distinct phases, each with specific objectives and requirements.
Categories of Validation
Microbial forensics and other forensic disciplines recognize three primary categories of validation [33]:
Developmental Validation: The acquisition of test data and the determination of conditions and limitations of a newly developed method for analyzing samples. This should address specificity, sensitivity, reproducibility, bias, precision, false positives, and false negatives [33].
Internal Validation: An accumulation of test data within an operational laboratory to demonstrate that established methods and procedures are carried out within predetermined limits in the laboratory [33].
Preliminary Validation: An early evaluation of a method that will be used to investigate a biocrime or bioterrorism event when fully validated methods are not available. This is particularly important for responding to emerging threats expeditiously while maintaining scientifically valid approaches [33].
Core Principles of Forensic Validation
Across all forensic disciplines, several core principles underpin proper validation [37]:
- Reproducibility: Results must be repeatable by other qualified professionals using the same method.
- Transparency: All procedures, software versions, logs, and chain-of-custody records must be thoroughly documented.
- Error Rate Awareness: Forensic methods should have known error rates that can be disclosed in reports and during testimony.
- Peer Review: Validation processes should be reviewed and ideally published to allow scrutiny from the broader forensic community.
- Continuous Validation: Because technology evolves rapidly, tools and methods must be frequently revalidated.
Quantitative Acceptance Criteria for Method Validation Parameters
Establishing quantitative acceptance criteria for each validation parameter is essential for demonstrating method reliability.
Recommended Acceptance Criteria for Key Validation Parameters
Based on pharmaceutical industry best practices and forensic requirements, the following acceptance criteria provide a foundation for method validation [39]:
Table 2: Recommended Acceptance Criteria for Analytical Method Validation
| Validation Parameter | Recommended Evaluation Method | Acceptance Criteria |
|---|---|---|
| Specificity | Measurement - Standard (units) in the matrix of interest; Specificity/Tolerance * 100 | Excellent Results <= 5%, Acceptable Results <= 10% [39] |
| Repeatability | Repeatability % Tolerance = (Stdev Repeatability*5.15)/(USL-LSL) for two-sided spec limits | ≤ 25% of tolerance for analytical methods; ≤ 50% of tolerance for bioassays [39] |
| Bias/Accuracy | Bias % of Tolerance = Bias/Tolerance * 100 | ≤ 10% of tolerance for both analytical methods and bioassays [39] |
| LOD (Limit of Detection) | LOD/Tolerance * 100 | ≤ 5% is Excellent and ≤ 10% is Acceptable [39] |
| LOQ (Limit of Quantitation) | LOQ/Tolerance * 100 | ≤ 15% is Excellent and ≤ 20% is Acceptable [39] |
| Linearity | Plot of residuals from regression line; no systematic pattern | No statistically significant quadratic effect in regression evaluation [39] |
Advanced Approaches to Establishing Acceptance Criteria
Conventional approaches to setting acceptance criteria, such as applying ±3 standard deviations of existing data, have limitations as they reward poor process control and punish good control [38]. More advanced methodologies include:
Integrated Process Modeling (IPM): Using manufacturing data and experimental data from small scale to derive intermediate acceptance criteria based on pre-defined out-of-specification probabilities while considering manufacturing variability in process parameters [38].
Monte Carlo Simulation: Incorporating random variability caused by process parameters to predict out-of-specification probability for a given set of process parameter set-points [38].
Variance Transmission: Applying error propagation using known regression models across multiple process steps to estimate expected variance at each process step [38].
These advanced approaches ensure that acceptance criteria provide a direct link to drug substance or product limits and consider the uncertainty around process parameters and material attributes.
Experimental Protocols for Validation Studies
Rigorous experimental protocols are essential for generating validation data that withstands scientific and legal scrutiny.
Protocol for Specificity and Selectivity Testing
Objective: To demonstrate that the method accurately measures the analyte in the presence of potential interferents.
Experimental Design:
- Prepare samples containing the target analyte at the specification concentration.
- Spike samples with likely interferents (e.g., related compounds, matrix components, degradation products) at appropriate levels.
- Analyze all samples and calculate recovery of the target analyte.
- For identification methods, demonstrate 100% detection rate with reported confidence limits [39].
Data Analysis: Calculate specificity as (Measurement - Standard) in units, then express as percentage of tolerance. Results should meet the acceptance criteria of ≤5-10% of tolerance [39].
Protocol for Precision and Repeatability Studies
Objective: To determine the precision of the method under repeatable conditions.
Experimental Design:
- Prepare a minimum of six independent test samples of a homogeneous matrix.
- Analyze samples under the same conditions (same analyst, same instrument, same day).
- Calculate the mean, standard deviation, and relative standard deviation (%RSD).
- For intermediate precision, repeat studies on different days, with different analysts, or different instruments [39].
Data Analysis: Calculate repeatability as a percentage of tolerance: (Stdev Repeatability * 5.15)/(USL - LSL) for two-sided specification limits. The result should be ≤25% of tolerance for analytical methods [39].
Protocol for Quantitative Matching of Forensic Evidence
Objective: To develop objective methods for matching fractured surfaces using quantitative measures.
Experimental Design:
- Generate fractured surfaces under controlled conditions.
- Map surface topography using three-dimensional microscopy at appropriate scales (typically >50-70 μm for metals to capture non-self-affine characteristics) [40].
- Perform spectral analysis of the topography to extract unique features.
- Use multivariate statistical learning tools to classify matching and non-matching specimens [40].
Data Analysis: Employ statistical models to produce likelihood ratios for classification and estimate misclassification probabilities. The imaging scale should be greater than about 10-times the self-affine transition scale to avert signal aliasing [40].
The Scientist's Toolkit: Essential Research Reagent Solutions
Implementing validation protocols requires specific materials and reagents designed to produce reliable, defensible results.
Table 3: Essential Research Reagents and Materials for Forensic Validation
| Item | Function | Application Context |
|---|---|---|
| Well-Characterized DNA Samples | Validation reference material for sensitivity and precision studies | Forensic DNA analysis to verify that a DNA testing method is robust, reliable and reproducible [36] |
| Integrated Process Models (IPM) | Mathematical framework linking multiple unit operations | Pharmaceutical process validation to predict out-of-specification probability and set acceptance criteria [38] |
| Three-Dimensional Microscopy Systems | High-resolution topographic mapping of fracture surfaces | Forensic fracture matching to quantitatively characterize surface features [40] |
| Monoclonal Antibody Production Systems | Well-characterized model for impurity clearance studies | Downstream process validation for biopharmaceutical manufacturing [38] |
| Statistical Software Packages | Data analysis and calculation of validation parameters | All validation studies for determining specificity, sensitivity, reproducibility, bias, and precision [33] |
| Hash Value Algorithms | Data integrity verification | Digital forensics to confirm evidence integrity before and after imaging [37] |
The rigorous structuring of functional and non-functional requirements, coupled with scientifically defensible acceptance criteria, forms the foundation of admissible forensic method validation. By implementing the frameworks, experimental protocols, and quantitative measures outlined in this guide, researchers and drug development professionals can ensure their methods generate reliable, defensible results that withstand both scientific scrutiny and legal challenges. The integration of advanced approaches such as integrated process modeling and statistical learning techniques continues to raise the standard for forensic method validation, ultimately enhancing the reliability of evidence in legal proceedings and the safety of pharmaceutical products.
Integrating Risk Assessment to Inform Requirement Stringency
Within the rigorous framework of forensic method validation research, the definition of end-user requirements is paramount. These requirements, which dictate the stringency of validation criteria, cannot be established arbitrarily. This technical guide outlines a systematic approach for integrating formal risk assessment models to objectively determine the level of stringency required for analytical procedures. By anchoring requirement stringency to potential impacts on judicial outcomes, data integrity, and public safety, research scientists and drug development professionals can ensure that validated methods are not only scientifically sound but also forensically fit-for-purpose. This document provides in-depth methodologies, structured data presentation, and visual workflows to standardize this critical integration process.
Risk Assessment Framework and Scoring System
A quantitative risk assessment matrix is the cornerstone of this approach, serving to evaluate and prioritize potential failures in a forensic analytical method. The matrix assesses risk based on two independent axes: the severity of a failure's consequence and the probability of its occurrence.
Table 1: Severity of Failure Consequences
| Severity Level | Description | Impact on Forensic Integrity |
|---|---|---|
| Critical | Failure could lead to misinterpretation of core facts, wrongful conviction/acquittal, or direct public harm. | High; compromises the fundamental justice and safety outcomes of the case. |
| Major | Failure causes significant data loss or erodes confidence in results, requiring substantial re-analysis. | Medium; undermines the reliability of the evidence but may not directly dictate the verdict. |
| Minor | Failure introduces minor inefficiencies or deviations with no tangible impact on the final reported result. | Low; manageable impact on laboratory workflow without affecting evidential value. |
Table 2: Probability of Occurrence
| Probability Level | Description | Likelihood Score |
|---|---|---|
| Frequent | Expected to occur repeatedly in most operations. | 5 |
| Probable | Likely to occur several times over the method's lifecycle. | 4 |
| Occasional | Likely to occur sometime over the method's lifecycle. | 3 |
| Remote | Unlikely but possible to occur. | 2 |
| Improbable | So unlikely, it can be assumed occurrence may not be experienced. | 1 |
The overall Risk Priority Number (RPN) is calculated by assigning a numerical score to each level (e.g., Critical=5, Major=3, Minor=1) and multiplying the Severity and Probability scores. This quantitative output directly informs the stringency of validation requirements.
Linking Risk to Validation Stringency
The calculated risk level must be mapped directly to specific, heightened validation requirements. This ensures that the methodological controls are commensurate with the potential impact of failure.
Table 3: Risk-Based Validation Requirements
| Risk Priority Level | Recommended Validation Stringency | Specific Requirement Examples |
|---|---|---|
| High Risk (RPN 16-25) | Extreme Stringency | - Accuracy/Precision: ±5% allowable bias; RSD < 3% [41].- LOD/LOQ: Must be empirically demonstrated and be fit-for-purpose.- Robustness: Testing required across ≥5 deliberate parameter variations.- Documentation: Full video/electronic data trail. |
| Medium Risk (RPN 9-15) | Elevated Stringency | - Accuracy/Precision: ±10% allowable bias; RSD < 5% [41].- LOD/LOQ: Can be based on signal-to-noise or historical data.- Robustness: Testing required across 3 deliberate parameter variations. |
| Low Risk (RPN 1-8) | Standard Stringency | - Accuracy/Precision: ±15% allowable bias; RSD < 10% [41].- LOD/LOQ: Can be calculated or literature-based.- Robustness: Testing is recommended but not mandatory. |
Visual Workflow for Risk-Informed Stringency
The following diagram illustrates the logical process of integrating risk assessment to define requirement stringency.
Experimental Protocols for Key Risk Assessments
This section provides detailed methodologies for experiments critical to quantifying risk and validating method robustness.
Protocol for Robustness Testing
Objective: To determine the method's reliability when subjected to small, deliberate variations in key operational parameters.
- Parameter Selection: Identify critical parameters (e.g., pH of mobile phase, column temperature, incubation time).
- Experimental Design: Use a one-factor-at-a-time (OFAT) approach. For each parameter, define a "nominal" value and a "varied" value (e.g., nominal pH = 7.4, varied pH = 7.2 and 7.6).
- Analysis: Execute the analytical method in triplicate for each parameter state.
- Data Analysis: Compare the results (e.g., peak area, retention time, quantitative result) from the varied conditions to the nominal condition. Calculate the relative standard deviation (RSD) and any significant shifts.
- Acceptance Criterion: The method is considered robust if all results under varied conditions remain within the pre-defined precision and accuracy limits established for the method [41].
Protocol for Limit of Detection (LOD) and Quantification (LOQ) Determination
Objective: To empirically establish the lowest concentration level that can be reliably detected and quantified.
- Sample Preparation: Prepare a series of blank samples and samples containing the analyte at concentrations near the expected detection limit.
- Analysis: Analyze at least five independent replicates of the blank and the low-concentration samples.
- Calculation:
- LOD based on Signal-to-Noise: Typically, a signal-to-noise ratio of 3:1 is acceptable for LOD [41].
- LOD/LOQ based on Standard Deviation: LOD = 3.3 * σ / S, LOQ = 10 * σ / S, where σ is the standard deviation of the response of the blank, and S is the slope of the calibration curve.
- Verification: The calculated LOD and LOQ should be verified by analyzing samples at those concentrations to confirm they meet the detection and quantification criteria with sufficient precision and accuracy.
The Scientist's Toolkit: Essential Research Reagents and Materials
The following reagents and materials are critical for implementing the validation protocols described in this guide.
Table 4: Research Reagent Solutions for Forensic Validation
| Item | Function in Validation |
|---|---|
| Certified Reference Material (CRM) | Provides a ground-truth standard with known purity and concentration for establishing method accuracy and calibration. |
| Internal Standard | A structurally similar analog added to samples to correct for analytical variability and improve precision in quantitation. |
| Matrix-Matched Calibrators | Standards prepared in a sample-like matrix to account for matrix effects, which is crucial for accurate quantitation in complex biological samples. |
| Quality Control Materials | Samples with known low, medium, and high analyte concentrations, used to monitor the stability and performance of the analytical method over time. |
| Stable Isotope-Labeled Analytes | Used as internal standards in mass spectrometry to compensate for sample preparation losses and ionization suppression, enhancing data reliability. |
Data Integrity and Presentation Standards
For forensic method validation, the presentation of data must be clear, consistent, and unambiguous. Adherence to the following standards is critical.
Guidelines for Table Construction
All tables summarizing validation data must conform to these principles to ensure readability and comprehension [41] [42]:
- Titles and Headers: Use clear, descriptive titles and column headers. Headers should align with their column's data content [43].
- Alignment: Numerical data should be right-aligned to facilitate comparison; textual data should be left-aligned [43].
- Number Formatting: Use consistent decimal places and appropriate thousand separators for large numbers to enhance readability [41].
- Gridlines: Apply gridlines sparingly. Subtle horizontal lines are often sufficient; vertical lines can typically be omitted to reduce visual clutter [41] [42].
- Notes: Use footnotes with superscript letters (e.g., a, b, c) to explain abbreviations, specific experimental conditions, or statistical significance [42].
Ensuring Visual Accessibility in Diagrams
All graphical representations, including the diagrams in this document, must adhere to WCAG 2.1 AA contrast ratio thresholds to be accessible to all users [44] [45]. The color palette specified for this document has been tested against these requirements.
- Normal Text: Requires a contrast ratio of at least 4.5:1 against the background [45] [46].
- Large Text: Requires a contrast ratio of at least 3:1 [45] [46].
- Graphical Objects: User interface components and visual elements require a contrast ratio of at least 3:1 [45].
Developing a Validation Plan Aligned with Defined Specifications
In forensic method validation, confidence in results is gained through validation studies, which provide objective evidence that a testing method is robust, reliable, and reproducible [36]. The process involves performing laboratory tests to verify that a particular instrument, software program, or measurement technique is working properly [36]. A validation plan aligned with defined specifications serves as the critical bridge between theoretical user needs and an operational, quality-assured forensic method.
The success or failure of the entire project heavily relies on the initial user requirements collection [31]. If these requirements are incorrect, misinterpreted, or changed during a project, it can jeopardize successful completion of a solution in its development or foster additional costs [31]. This technical guide outlines a structured framework for developing validation plans specifically within the context of forensic method validation research, ensuring solutions meet end-user needs while maintaining scientific rigor and regulatory compliance.
Core Principles of Validation Planning
Defining Validation Scope and Objectives
The main goal of a validation protocol is to define the test scripts required to ensure that equipment or a method is fit for purpose—capable of producing reliable results that can withstand scientific and legal scrutiny [47]. In forensic contexts, this translates to establishing documented evidence to prove "fitness for use" of a system, ensuring that a facility and its equipment function as required for approval by regulatory agencies [47].
A fundamental principle involves qualifying only critical systems and critical components [47]. This requires performing a component impact assessment to develop a critical components list and qualifying only those systems and components within the system that are essential for operation or have direct impact or contact with the product or analytical outcome [47]. This targeted approach prevents unnecessary qualification of non-essential elements, balancing thoroughness with practical resource allocation.
Foundational Concepts
Table 1: Key Validation Concepts in Forensic Science
| Concept | Definition | Importance in Forensic Validation |
|---|---|---|
| Reliability | Consistency of results under specified conditions | Ensures methods produce dependable outcomes across multiple trials [36] |
| Reproducibility | Ability to duplicate results using the same methodology | Critical for verifying findings across different laboratories [36] |
| Robustness | Capacity to remain unaffected by small variations in method parameters | Determines method resilience in real-world operating conditions [36] |
| Accuracy | Closeness of measurements to true values | Fundamental for credible forensic conclusions [36] |
| Precision | Degree of agreement among repeated measurements | Essential for establishing statistical confidence in results [36] |
| Sensitivity | Lowest detectable amount of analyte that can be reliably measured | Defines procedural limitations for casework samples [36] |
Framework for Validation Plan Development
Pre-Validation Phase: Requirements Gathering and Analysis
Effective validation planning begins with comprehensive understanding of user needs. Research in the security domain shows that without involvement of stakeholders, the solution is likely to have lower acceptance and application in practice [31]. The requirements collection process typically consists of two main steps: (a) the identification step and (b) the evaluation step [31].
For forensic applications, the following pre-validation activities are essential:
- Conduct User Research: Gain insights into target users' needs, goals, and preferences through surveys, interviews, observations, or usability testing [21]. In forensic contexts, users include analysts, laboratory managers, and legal stakeholders.
- Develop Deep Context Understanding: Understand the user's context, workflows, and pain points to ensure documented requirements address their specific needs [21]. For forensic methods, this includes understanding evidence handling protocols and chain-of-custody requirements.
- Stakeholder Involvement: Collaborate closely with users, business analysts, subject matter experts, and other stakeholders to gather and validate requirements [21]. Regularly seek feedback and clarification to ensure accurate capturing of needs and expectations.
Validation Protocol Structure
A comprehensive validation protocol should detail the following elements [47]:
- Product Characteristics: Specifications showing what the system is designed to achieve/produce
- Production Equipment: Details of equipment necessary for the method
- Test Scripts and Methods: Steps involved in conducting tests
- Test Parameters and Acceptance Criteria: Definition of acceptable test results
- Test Checksheets: Documentation for recording test results
- Final Approval: Documentation that the validation process has been successfully carried out
Experimental Protocols and Methodologies
Validation Experiment Design
Validation experiments in forensic science typically examine precision, accuracy, and sensitivity, which all play a factor on the 3 R's of measurements: reliability, reproducibility, and robustness [36]. The Scientific Working Group on DNA Analysis Methods (SWGDAM) recommends that a total of at least 50 samples be examined as part of a careful validation study [36].
Table 2: Core Validation Experiments for Forensic Methods
| Experiment Type | Protocol Description | Acceptance Criteria | Key Measurements |
|---|---|---|---|
| Precision Studies | Repeated analysis of identical samples across multiple runs, operators, and instruments | Coefficient of variation < predetermined threshold based on method requirements | Standard deviation, variance, CV% [36] |
| Accuracy Assessment | Comparison of results with reference materials or alternative validated methods | Results within established uncertainty range of reference values | Bias, recovery percentages [36] |
| Sensitivity Determination | Analysis of dilution series to establish limits of detection and quantification | Consistent detection at or below intended operational thresholds | Limit of Detection (LOD), Limit of Quantification (LOQ) [36] |
| Robustness Testing | Deliberate variations of critical method parameters | Method performance remains within acceptable ranges despite variations | Parameter tolerance ranges [47] |
| Reproducibility Studies | Inter-laboratory testing using standardized protocols | Statistically equivalent results across participating laboratories | Inter-lab variance, statistical significance [36] |
Protocol Execution Framework
The execution of validation protocols follows a structured approach [47]:
Pre-Execution Checklist:
- Review the protocol and confirm what is to be tested and how
- Ensure correct version of protocols are used and fully approved
- Verify equipment readiness and availability
- Review safety procedures
- Collect necessary calibrated test instruments
- Notify specialists needed to assist with testing
Execution Phase:
- Do not make assumptions during testing
- Ensure all piping and utility connections are correctly identified and tagged
- Record all data/entries directly on the protocol page
- Maintain neat and legible entries following Good Documentation Practices
- Avoid leaving any blank lines or spaces
- Complete IQ protocol before OQ, and OQ before PQ
- Close all deviations before signing any protocol as complete
- Initial, sign, and date all entries at the point of execution without pre or post-dating
Visualization of Validation Workflow
End-to-End Validation Process
Figure 1: End-to-End Validation Workflow from Requirements to Implementation
Requirements Collection Framework
Figure 2: Four-Stage Framework for User Requirements Collection
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 3: Essential Research Reagent Solutions for Forensic Validation
| Item Category | Specific Examples | Function in Validation | Quality Requirements |
|---|---|---|---|
| Reference Standards | Certified Reference Materials (CRMs), Standard Reference Materials (SRMs) | Establishing accuracy and calibration curves; traceability to international standards | Documented purity, stability, and uncertainty values [36] |
| Control Materials | Positive controls, negative controls, internal standards | Monitoring assay performance; detecting contamination | Well-characterized, consistent performance, appropriate storage conditions [47] |
| Calibration Verification Materials | Materials with known values different from calibrators | Verifying calibration stability throughout analytical batch | Commutable with patient samples, value-assigned [36] |
| Quality Control Materials | Commercial QC materials, in-house prepared pools | Monitoring precision and reproducibility across runs | Stable, homogeneous, representative of test sample matrix [47] |
| Sample Preparation Reagents | Extraction kits, purification columns, buffers | Isolating and purifying analytes from complex matrices | Lot-to-lot consistency, minimal interference, high recovery [47] |
| Detection Reagents | Enzymes, antibodies, fluorescent probes, primers | Enabling signal generation and detection | Specificity, sensitivity, minimal background noise [36] |
Implementation Considerations for Forensic Laboratories
Addressing Common Validation Challenges
Forensic DNA laboratories face various challenges when implementing new methodologies, including lack of resources available to perform validation experiments and the existence of diverse opinions with respect to validation protocols, sample numbers and definition of appropriate and effective experiments [36]. These variables can contribute to extensive validation studies that include unnecessary or excessive tests without the benefit of additional confidence [36].
To address these challenges:
- Develop a Validation Plan: Avoid embarking on validation without a clear plan. Without a validation plan, labs become "weary and woeful wanderers that lose valuable time and expend unnecessary labor and reagent costs" [36].
- Avoid Over-Qualification: There can be a tendency, especially among novice technicians and engineers to qualify all components in a system. However, the qualification process is enormously time-consuming and expensive [47].
- Use Risk Management Tools: Apply system impact assessments, component impact assessments and risk management tools in a scientifically robust manner to support decisions about what to validate to avoid over-qualifying [47].
- Leverage Existing Data: Use commissioning data wherever possible to reduce testing duplication, with quality assurance department approval [47].
Regulatory and Quality Considerations
Validation builds confidence for the court as well as aiding quality assurance and control activities in the lab [36]. Since reliable analytical data are highly desirable in courts of law debating the innocence or guilt of a defendant, validation information underpinning DNA typing measurements is often scrutinized by the court in order to assess admissibility of evidence [36].
Key regulatory resources include:
- FBI's DNA Advisory Board Quality Assurance Standards: Section 8 describes the primary aspects of forensic DNA validation studies [36].
- SWGDAM Revised Validation Guidelines: Provide further detail and recommend that a total of at least 50 samples be examined as part of a careful validation study [36].
- NIST STRBase Validation Section: Contains helpful information and links to workshop materials on validation [36].
There is no single "perfect" approach to validating a project—multiple right answers and approaches exist [47]. The key point is being able to explain rationale to auditors or supervisors. As long as rationale is sound and logical, even if others disagree, they can understand the decision, which typically prevents penalties [47].
Within forensic science and drug development, the implementation of new analytical methods is a cornerstone of progress. The process for establishing that these methods are fit-for-purpose, however, diverges significantly based on their novelty. Requirement specification must be meticulously tailored to distinguish between a novel method, requiring full foundational validation, and an adopted method, where the focus shifts to verification within a new laboratory context [6]. This guide provides a technical framework for defining these end-user requirements, ensuring scientific rigor, regulatory compliance, and operational efficiency. The core distinction lies in the burden of proof: novel methods must generate comprehensive validity evidence, while adopted methods must demonstrate successful replication of existing, published validation data [6].
Comparative Framework: Novel vs. Adopted Method Validation
The choice between developing a novel method and adopting an existing one has profound implications for resource allocation, timeline, and technical strategy. The following table summarizes the core differences in requirement specification for each pathway.
Table 1: Core Requirement Specification for Novel versus Adopted Methods
| Aspect | Novel Method (Full Validation) | Adopted Method (Verification) |
|---|---|---|
| Primary Objective | Provide original, objective evidence that the method is fit for its intended use [6]. | Demonstrate that the laboratory can successfully reproduce the method and its published performance parameters [6]. |
| Technical Scope | Comprehensive. Encompasses all relevant performance characteristics (e.g., specificity, accuracy, precision, LOD, LOQ, robustness). | Abbreviated. Focuses on key parameters to confirm the method operates as expected in the new environment (e.g., precision, accuracy). |
| Development Workload | High. Involves significant method development, optimization, and experimentation [6]. | Low to Moderate. Eliminates method development work; centered on following a established protocol [6]. |
| Data Source | Primarily original data generated in-house. | Primarily existing data from a peer-reviewed publication or a collaborating laboratory, supplemented by limited in-house verification data [6]. |
| Resource & Cost Implication | High cost, time-consuming, and labor-intensive [6]. | Significant cost and time savings due to shared data and eliminated development work [6]. |
| Key Output | A complete validation report, suitable for peer-reviewed publication, establishing the method's validity [6]. | A verification report, reviewing and accepting the original data and confirming successful implementation locally [6]. |
Experimental Protocols for Validation
Protocol for Novel Method Validation
A robust validation protocol for a novel method must be designed to generate defensible evidence of its reliability.
3.1.1 Primary Objective: To establish and document the complete performance characteristics of a new analytical method, ensuring it meets predefined criteria for its intended application in forensic science or drug development.
3.1.2 Detailed Methodology:
- Define Intended Use and Validation Parameters: Clearly articulate the method's purpose. Select and define the performance parameters (metrics) required for validation, which typically include:
- Specificity/Selectivity: Demonstrate the ability to unequivocally assess the analyte in the presence of expected components.
- Accuracy: Measure the closeness of agreement between a test result and the accepted reference value. This is often established using spike/recovery experiments for biomarkers or analysis of certified reference materials.
- Precision: Quantify the degree of agreement among a series of measurements. This includes:
- Repeatability: Precision under the same operating conditions over a short interval (e.g., 10 replicates of low, mid, and high concentration samples in one run).
- Intermediate Precision: Precision within-laboratory variations (e.g., different days, different analysts, different equipment). A minimum of 3 runs over 3 different days is standard.
- Limit of Detection (LOD) & Limit of Quantification (LOQ): Determine the lowest amount of analyte that can be detected and quantified with acceptable accuracy and precision, respectively, often via signal-to-noise ratio or standard deviation of the response.
- Linearity and Range: Establish that the method provides results directly proportional to analyte concentration within a specified range. Prepare a minimum of 5 concentration levels, analyzed in duplicate.
- Robustness/Ruggedness: Demonstrate the method's capacity to remain unaffected by small, deliberate variations in method parameters (e.g., temperature, pH, flow rate).
Experimental Design and Sample Preparation: Create a detailed experimental plan specifying the number of calibration standards, quality control (QC) samples, and authentic samples. For a precision and accuracy study, a common design is to prepare QC samples at three concentrations (low, medium, high) and analyze a minimum of five replicates of each per run for a minimum of three runs.
Data Analysis and Acceptance Criteria: Predefine all acceptance criteria prior to experimentation. For instance, for a bioanalytical method, accuracy (mean % nominal) and precision (% relative standard deviation, %RSD) for QC samples should typically be within ±15% (±20% at LLOQ).
Protocol for Adopted Method Verification
The verification protocol is not a repetition of the full validation but a targeted confirmation of its applicability.
3.2.1 Primary Objective: To provide objective evidence that a previously validated method performs as specified when implemented in the user's laboratory, using the specified instrumentation and personnel.
3.2.2 Detailed Methodology:
- Review of Published Validation Data: Obtain the complete peer-reviewed validation study. Critically review the protocol, results, and acceptance criteria to ensure they are applicable to the intended use in your laboratory [6].
Verification of Key Parameters: The scope is abbreviated. A typical verification includes:
- Precision and Accuracy: This is the core of most verification studies. Analyze a limited set of QC samples (e.g., low and high concentration, n=3-5 each) in a single run or over a limited number of runs to demonstrate that the method's performance meets the original published criteria [6].
- System Suitability: Perform tests to ensure that the system (instrumentation, reagents, columns) is functioning appropriately and meets the specifications outlined in the original method.
Documentation and Equivalence Assessment: Document all procedures and results. The in-house verification data should be compared directly to the original published data. Successful verification is achieved when the performance is statistically comparable or falls within the original study's performance ranges, leading to formal acceptance of the method [6].
Workflow Visualization of Method Implementation
The following diagram illustrates the critical decision points and activities in the lifecycle of method implementation, highlighting the divergent paths for novel versus adopted methods.
The Scientist's Toolkit: Essential Research Reagents & Materials
Successful method validation and verification rely on a foundation of high-quality, traceable materials. The following table details key reagents and their critical functions in ensuring data integrity.
Table 2: Key Research Reagent Solutions for Method Validation
| Reagent / Material | Function in Validation/Verification |
|---|---|
| Certified Reference Material (CRM) | Provides a substance with one or more property values that are certified by a procedure establishing traceability to an accurate realization of the unit. Serves as the primary standard for establishing method accuracy and calibration [6]. |
| Quality Control (QC) Samples | Biologically relevant samples spiked with known quantities of the analyte. Used to continuously monitor the method's precision and accuracy during the validation and in every subsequent analytical run. |
| Internal Standard (IS) | A chemically similar analog of the analyte added to all samples, calibrators, and QCs at a fixed concentration. Used to correct for variability in sample preparation and instrument response, improving precision and accuracy. |
| Matrix Blank | The biological fluid (e.g., plasma, urine) or sample material known to be free of the target analyte. Essential for demonstrating method specificity and for assessing potential background interference. |
| System Suitability Test Solutions | Standard preparations used to verify that the analytical system (e.g., chromatograph, detector) is performing adequately at the start of and during the analysis, as per predefined criteria (e.g., retention time, peak shape, signal-to-noise). |
Navigating Challenges: Solutions for Incomplete Requirements and Validation Pitfalls
In forensic method validation research, the integrity of the entire analytical process hinges on two foundational elements: precisely defined end-user requirements and the use of truly representative test data. Vague requirements and unrepresentative test data are not merely operational oversights; they represent critical failures that can compromise the validity of a method, leading to scientifically unsound results with serious legal and public health consequences. In fields such as forensic toxicology and drug detection, where results can directly impact individual liberties and public safety, the rigorous definition of needs and the conditions under which a method must perform is a scientific and ethical imperative [48].
This guide provides a detailed technical exploration of these two common pitfalls. It outlines their implications, provides structured frameworks for mitigation, and presents experimental protocols designed to ensure that validated methods are both robust and fit for their intended purpose in the real world.
The Pitfall of Vague Requirements
Definition and Consequences
Vague requirements in method validation refer to the absence of clear, measurable, and comprehensive specifications for what the method must achieve. This lack of clarity often manifests in undefined performance criteria, unclear scope of application, or poorly understood operational conditions [49]. The consequences are severe: methods may be validated against inappropriate parameters, leading to a false sense of security. When a method's purpose and performance limits are not explicitly defined, it becomes impossible to properly validate it, creating a significant risk of analytical failure during casework [48]. This deficiency can result in legal challenges, exclusion of evidence, and ultimately, miscarriages of justice [37].
Best Practices for Defining Precise Requirements
To avoid this pitfall, laboratories must adopt a systematic approach to requirement definition.
- Engage All Stakeholders Early: The process should involve not just the developers of the method, but also the end-users (e.g., forensic examiners, laboratory technicians), quality assurance personnel, and representatives from management. This ensures that all operational, regulatory, and business needs are captured [50].
- Develop a Detailed Validation Protocol: Before any experimentation begins, a comprehensive validation protocol must be created and approved. This document is the cornerstone of a successful validation project [49]. It should unequivocally state:
- The method's intended purpose and scope.
- The analytes to be detected and/or measured.
- The sample matrices to which the method applies.
- All performance parameters to be assessed (e.g., accuracy, precision, LOD, LOQ).
- Pre-defined acceptance criteria for each parameter, which must be specific, measurable, and justified [51] [48].
- Adhere to Established Standards: Leverage existing standards and guidelines to ensure no critical requirement is overlooked. Key documents include ANSI/ASB Standard 036 (for forensic toxicology) and the ISO 17025 standard for testing and calibration laboratories [48]. These provide minimum requirements and a structured framework for validation.
Table 1: Key Performance Parameters and Acceptance Criteria for Forensic Method Validation
| Performance Parameter | Definition | Common Acceptance Criteria (Example) |
|---|---|---|
| Accuracy | The closeness of agreement between a measured value and a known reference value. | Mean recovery of 85-115% for spiked samples. |
| Precision | The closeness of agreement between a series of measurements under specified conditions. | Relative Standard Deviation (RSD) ≤ 15% for replicate analyses. |
| Limit of Detection (LOD) | The lowest concentration of an analyte that can be detected, but not necessarily quantified. | Signal-to-noise ratio ≥ 3:1. |
| Limit of Quantification (LOQ) | The lowest concentration of an analyte that can be quantified with acceptable precision and accuracy. | Signal-to-noise ratio ≥ 10:1; accuracy and precision at LOQ within ±20%. |
| Specificity/Selectivity | The ability to unequivocally assess the analyte in the presence of potential interferents. | No interference ≥ 20% of the analyte response at the LOQ. |
| Linearity and Range | The ability to obtain results directly proportional to analyte concentration over a specified range. | Correlation coefficient (r²) ≥ 0.99 over the validated range. |
Experimental Protocol: Establishing Method Linearity and Range
1. Objective: To demonstrate that the analytical method produces results that are directly proportional to the concentration of the analyte in a given sample within a specified range.
2. Materials and Reagents:
- Certified reference standard of the target analyte.
- Appropriate blank matrix (e.g., drug-free whole blood).
- Solvents and reagents of analytical grade.
3. Procedure: a. Prepare a minimum of five to eight calibration standards spanning the entire expected concentration range (e.g., from LOQ to 150% of the expected maximum concentration). b. Analyze each calibration standard in triplicate using the fully developed analytical method. c. Plot the mean instrument response for each standard against its nominal concentration. d. Perform a linear regression analysis on the data to determine the slope, y-intercept, and correlation coefficient (r²).
4. Acceptance Criteria: The method is considered linear if the r² value is ≥ 0.99 and the residuals are randomly distributed. The range is validated if all back-calculated concentrations fall within ±15% of the nominal value (±20% at the LOQ) [49] [48].
The Pitfall of Unrepresentative Test Data
The Critical Role of a Representative Matrix
The use of unrepresentative test data during validation, particularly the reliance on a calibration matrix that does not match the casework samples, is a pervasive and critical error. A common example in forensic toxicology is using aqueous calibration standards for a method intended to quantify substances in whole blood [48]. The sample matrix (e.g., blood, urine, tissue) contains numerous other constituents that can significantly alter the analytical response, a phenomenon known as the matrix effect. Failure to account for this during validation means the method's performance with real case samples is unknown and unreliable. The reported results, along with their associated uncertainty values, cannot be trusted [48].
Best Practices for Ensuring Representative Testing
- Validate with Fortified Real Matrices: The core practice for overcoming this pitfall is to use the actual sample matrix from the intended population for validation studies. This involves collecting blank matrices from multiple sources, fortifying them with known quantities of the analyte, and using these to assess key parameters like accuracy, precision, and recovery [48].
- Conduct Comprehensive Interference Studies: The method must be challenged with a wide variety of potentially interfering substances that could be present in case samples. This includes other drugs, metabolites, and endogenous blood components. The goal is to prove that the method is specific for the target analyte [48].
- Implement Rigorous In-Run Quality Control: During routine operation, every batch of case samples must include quality control (QC) samples. These should include blank matrix, and fortified matrix samples at low, medium, and high concentrations. This ongoing practice continuously verifies that the method is performing as validated and that matrix effects have not emerged [48].
Table 2: Essential Quality Control Samples for Batch Analysis
| QC Sample Type | Composition | Function in the Batch |
|---|---|---|
| Blank Matrix | Unfortified sample matrix from a minimum of 6 different sources. | Confirms the absence of endogenous interference at the retention times of the analyte and internal standard. |
| Lower Limit QC (LLOQ QC) | Matrix fortified at the Lower Limit of Quantification. | Verifies the method's performance at the lowest reportable concentration. |
| Low QC | Matrix fortified with analyte at a low concentration (e.g., 2-3x LLOQ). | Monitors accuracy and precision near the lower end of the calibration curve. |
| Medium QC | Matrix fortified with analyte at a mid-range concentration. | Monitors accuracy and precision in the middle of the calibration curve. |
| High QC | Matrix fortified with analyte at a high concentration (e.g., 75-85% of the ULOQ). | Monitors accuracy and precision at the upper end of the calibration curve. |
Experimental Protocol: Assessing Matrix Effects in LC-MS/MS
1. Objective: To evaluate the potential for ionization suppression or enhancement caused by the sample matrix in liquid chromatography-tandem mass spectrometry (LC-MS/MS) methods.
2. Materials and Reagents:
- Post-extraction blank blood matrix from at least 6 different sources.
- Neat standard solution of the analyte and internal standard (IS) at a known concentration.
- Mobile phase.
3. Procedure: a. Extract the blank matrix samples using the validated sample preparation procedure. b. After extraction, add a known amount of analyte and IS to the extracted blank samples (Post-extracted Spiked A). c. Also, prepare samples by adding the same amount of analyte and IS to pure mobile phase (Neat Solution B). d. Analyze all samples and compare the peak areas of the analyte and IS in the post-extracted spiked samples (A) to those in the neat solutions (B).
4. Calculation and Acceptance Criteria: Matrix Effect (%) = (Peak Area of A / Peak Area of B) x 100%. A value of 100% indicates no matrix effect. Values significantly lower indicate suppression, while higher values indicate enhancement. The method may require optimization if the matrix effect is consistent and pronounced (e.g., <85% or >115%) and impacts precision at the LLOQ [48].
Integrated Workflow for Robust Method Validation
The following workflow integrates the principles outlined above into a logical sequence for developing and validating a forensic analytical method, emphasizing the clear definition of requirements and the use of representative data at every stage.
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 3: Key Reagents and Materials for Forensic Method Validation
| Item | Function and Importance |
|---|---|
| Certified Reference Standards | Pure, well-characterized analyte material used for preparing calibration standards and QC samples. Essential for establishing accuracy and traceability. |
| Blank Matrices from Multiple Donors | Drug-free samples of the biological matrix (e.g., whole blood, urine). Used to prepare fortified QC samples and to assess specificity and matrix effects. Sourcing from multiple donors is critical for robustness. |
| Stable Isotope-Labeled Internal Standards | For LC-MS/MS methods, these are used to correct for losses during sample preparation and for variations in ionization efficiency due to matrix effects. |
| Quality Control Materials | Characterized samples with known concentrations of the analyte, used to monitor the method's performance during validation and in every batch of casework samples. |
| Appropriated Certified Calibrators | Pre-made calibration standards from a reputable source, used to establish the analytical curve and ensure the instrument's response is accurate across the working range. |
In forensic method validation research, the precise definition of end-user requirements is a cornerstone of scientific rigor and legal admissibility. Requirements engineering provides the structured framework necessary to ensure that validated methods are fit-for-purpose, reproducible, and reliable. The skills gap in this specific domain poses a significant risk, not just to project timelines, but to the fundamental integrity of forensic science. This guide details the core competencies and practical methodologies that practitioners must master to define, validate, and verify requirements within the stringent context of forensic method validation, such as the standards outlined in ANSI/ASB Standard 036 for forensic toxicology [52].
Core Concepts: Verification, Validation, and Quantitative Foundations
Distinguishing Verification and Validation
In forensic method development, the distinction between verification and validation is paramount. These are not synonymous terms but complementary processes [53].
- Verification answers the question, "Did we build the method right?" It is the process of checking that the developed analytical method correctly implements all specified design inputs and requirements. This ensures the method meets its specifications [53].
- Validation answers the question, "Did we build the right method?" It is the process of ensuring that the method conforms to defined user needs and intended uses, demonstrating that it is fit for its intended purpose in a real-world forensic context [53].
The following diagram illustrates the distinct pathways and key questions for requirements verification and validation:
Quantitative Data Analysis for Requirement Metrics
Quantitative data analysis is indispensable for establishing objective, measurable requirements. Training must equip practitioners to use statistical tools to define and validate method performance characteristics [54] [55].
The table below summarizes the two primary branches of statistical analysis used in this process:
| Analysis Branch | Primary Question | Key Techniques | Role in Requirement Engineering |
|---|---|---|---|
| Descriptive Statistics [54] [56] | What is the nature of our sample data? | Mean, Median, Mode, Standard Deviation, Skewness [54] | Summarizes initial method performance data; identifies patterns, errors, and outliers to inform requirement reasonableness [54]. |
| Inferential Statistics [54] [55] | What can we predict about the method's performance in the population? | T-tests, ANOVA, Correlation, Regression Analysis [54] [55] | Generalizes findings from a limited validation study to broader application; tests hypotheses about method robustness, precision, and accuracy [54]. |
Requirement Engineering Techniques for Forensic Validation
Core Validation Techniques
A robust requirements validation strategy employs a combination of techniques to ensure completeness, consistency, and accuracy [57] [58].
The following table details key techniques and their application in a forensic research context:
| Technique | Description | Application in Forensic Method Validation |
|---|---|---|
| Requirements Reviews & Inspections [57] [58] | A structured process where a group systematically analyzes the requirements document for errors and ambiguities. | A team of toxicologists, lab managers, and QA reviewers checks the Software Requirements Specification (SRS) for a new drug screening method to ensure all required analytes and acceptance criteria are defined. |
| Test Case Generation [57] | Deriving test cases from requirements to check for testability. If a requirement is difficult to test, it is likely poorly defined. | For a requirement stating "the method must distinguish analyte A from its isomer B," a test case is designed using samples containing both to confirm the resolution meets the specified threshold. |
| Prototyping [57] [58] | Creating a working model or simulation of the system to visualize and test requirements. | Developing a simplified version of a data analysis algorithm to demonstrate its output to forensic scientists early in the development cycle, gathering feedback on usability and interpretation. |
| Automated Consistency Analysis [57] | Using CASE tools to automatically check formal requirement specifications for inconsistencies, missing cases, or type errors. | Using a requirements management tool to check for conflicting requirements between the sensitivity needed for low-concentration analytes and the required linear dynamic range. |
| Traceability [57] [53] | Tracing requirements throughout the entire development life cycle to ensure they are met and changes are managed. | Using a Requirements Traceability Matrix (RTM) to link a user need (e.g., "detect fentanyl and 10 major metabolites") to specific design inputs, test protocols, and validation results. |
Implementing a Validation Workflow
A structured workflow for requirement validation integrates these techniques into a coherent process, as shown in the following diagram:
Experimental Protocol: A Requirements Validation Workshop
This detailed protocol is designed to train practitioners in applying validation techniques through a hands-on, collaborative workshop focused on a realistic forensic science scenario.
Pre-Workshop Preparation
- Select a Case Study: Choose a well-defined forensic method validation project, such as validating a new LC-MS/MS method for a novel synthetic opioid.
- Develop Artifacts: Prepare a draft Requirements Document (e.g., an SRS) intentionally seeded with common issues: ambiguous terms (e.g., "high sensitivity"), missing acceptance criteria for precision, and conflicting requirements between specificity and throughput.
- Form Teams: Divide participants into multidisciplinary teams of 4-5, mimicking real-world composition: a research scientist, a laboratory analyst, a quality assurance officer, and a representative from the end-user community (e.g., a medical examiner).
Workshop Execution (3-Hour Session)
Module 1: Foundation (30 minutes)
- Briefing: Introduce the case study and the seeded defects.
- Concepts: Briefly recap verification vs. validation and the techniques to be used.
Module 2: Technical Application (90 minutes)
- Team Exercise: Teams work through the draft SRS using provided checklists [57]. The checklist prompts teams to flag requirements that are not:
- Complete: Covers all user needs and system responses.
- Consistent: No internal conflicts.
- Unambiguous: Only one interpretation.
- Testable: Can be verified through inspection, demonstration, or test.
- Facilitator Role: Rotate among teams, guiding them to convert vague requirements into measurable ones (e.g., changing "high sensitivity" to "LOQ ≤ 0.1 ng/mL").
- Team Exercise: Teams work through the draft SRS using provided checklists [57]. The checklist prompts teams to flag requirements that are not:
Module 3: Analysis and Reporting (60 minutes)
- Findings Consolidation: Each team documents their findings in a standardized problem report, categorizing issues and proposing specific corrective actions [58].
- Team Presentations: Each team presents their top 3 critical findings to the entire group, justifying their analysis.
- Group Discussion: Facilitate a discussion on the root causes of the identified issues and the impact they would have had if undiscovered until the testing phase.
The Scientist's Toolkit: Research Reagent Solutions
This table lists essential materials and tools used in requirement engineering experiments and their functions.
| Tool / Material | Function in Requirement Engineering |
|---|---|
| Requirements Management Software (e.g., Jama Connect, DOORS) [53] | Provides a centralized platform for documenting, tracing, and managing changes to requirements throughout the system lifecycle, ensuring version control and audit trails. |
| Checklists for Validation [57] | A pre-defined list of criteria (completeness, clarity, feasibility) used to systematically ensure every requirement meets predetermined standards. |
| Prototyping Tool / Simulator [57] | Creates a working model or simulation of the system to visualize requirements, gather early user feedback, and test feasibility before full-scale development. |
| Formal Notation & Analysis Tool [57] | Allows requirements to be structured in a formal, mathematical language so that automated tools can check for inconsistencies, missing cases, and type errors. |
The rigorous application of requirement engineering principles is not an administrative burden but a scientific necessity in forensic method validation. By systematically training practitioners in the distinct processes of verification and validation, and by equipping them with a robust toolkit of techniques—from structured reviews and prototyping to quantitative analysis and traceability—we can directly address the critical skills gap. This investment in human expertise ensures that forensic methods are built right from the outset, are demonstrably fit for their intended purpose, and ultimately uphold the highest standards of scientific evidence and public trust.
Optimizing Test Data Selection to Robustly Challenge Method Limits
Within the framework of defining end-user requirements for forensic method validation research, the process of selecting test data to rigorously challenge analytical methods is paramount. This practice ensures that methods are not only technically valid but also fit-for-purpose in real-world scenarios, directly supporting the core thesis that end-user needs must drive validation design. The fundamental reason for performing method validation is to ensure confidence and reliability in forensic toxicological test results by demonstrating the method is fit for its intended use [52]. In high-dimensional data sets, practical experiments often pose challenges, where more variables than observations are recorded and data may be present that do not follow the structure of the data majority [59]. Optimizing test data selection involves strategically designing experiments and samples to probe the limits of quantification, detection, specificity, and robustness under controlled, stressful, or marginal conditions.
Foundational Principles of Method Validation
Method validation in a forensic context, particularly toxicology, follows established standards to ensure analytical reliability. According to ANSI/ASB Standard 036, which outlines minimum standards for forensic toxicology, validation demonstrates that a method is fit for its intended purpose, providing confidence in test results for sub-disciplines including postmortem toxicology, human performance toxicology, and drug-facilitated crimes [52]. The selection of test data must therefore be aligned with the specific analytical questions and operational constraints of the end-user environment.
A key challenge in modern laboratories is handling complex data sets. Robust statistical methods are essential for high-dimensional data where the number of variables exceeds the number of observations, and where outlying observations that do not follow the data majority's structure are common [59]. A robust validation strategy incorporates such potential anomalies into the test data selection process, ensuring the method remains reliable even when confronted with non-ideal samples.
Experimental Design for Challenging Method Limits
A Systematic Approach to Test Data Selection
A systematic, diagrammed process ensures all critical performance characteristics are assessed with appropriate, challenging data, directly addressing end-user requirements for reliability at the method's boundaries.
Core Experimental Protocols
Protocol for Limits of Detection and Quantification (LOD/LOQ)
This protocol details the procedure for establishing the lowest levels of analyte that can be reliably detected and quantified, a core requirement for defining a method's operational range.
Objective: To determine the Limit of Detection (LOD) and Limit of Quantification (LOQ) for the target analyte in a specific matrix.
Materials:
- Prepared blank matrix (e.g., drug-free blood, urine).
- Primary analyte standard of known purity and concentration.
- Internal standard.
- All reagents and solvents per the analytical method.
- Instrumentation (e.g., LC-MS/MS, GC-MS) with calibrated detectors.
Procedure:
- Prepare a series of low-concentration calibrators in the blank matrix, spanning a range expected to be near the detection and quantification limits.
- Analyze a minimum of 10 replicate samples of the blank matrix and each low-level calibrator.
- For the LOD, calculate the standard deviation (σ) of the response for the blank and low-level samples. The LOD is typically estimated as 3σ (for signal-to-noise approaches, a 3:1 ratio is standard).
- For the LOQ, establish the lowest concentration that can be quantified with acceptable precision and accuracy (typically ±20%). This is often estimated as 10σ or the concentration yielding a signal-to-noise ratio of 10:1.
- Confirm the LOD and LOQ by analyzing independent prepared samples at these concentrations. The precision (Relative Standard Deviation) at the LOQ should be ≤20% and accuracy (Relative Error) should be within ±20%.
Data Analysis: The quantitative data from the replicate analyses should be summarized in a table for easy comparison of mean calculated concentration, standard deviation, %RSD, and %Accuracy at each level.
Protocol for Robustness Testing via Deliberate Parameter Variation
This protocol challenges the method's resilience to small, deliberate changes in operational parameters, simulating real-world laboratory variations.
Objective: To assess the method's robustness by introducing controlled, small variations to key method parameters and observing the impact on analytical results.
Materials:
- Quality Control samples at low, mid, and high concentrations.
- Standard analytical reagents and equipment.
Procedure:
- Identify critical method parameters susceptible to minor fluctuations (e.g., column temperature (±2°C), mobile phase pH (±0.2 units), flow rate (±5%), extraction time (±10%)).
- Using a experimental design (e.g., a Plackett-Burman or fractional factorial design), systematically vary these parameters around their nominal values.
- Analyze QC samples in replicate under each set of modified conditions.
- Compare the results (accuracy, precision, retention time, resolution) to those obtained under nominal conditions.
Data Analysis: The effect of each parameter variation on the quantitative outputs should be evaluated. A robust method will show minimal impact on accuracy and precision from these slight perturbations. The data can be effectively visualized using a bar chart to compare the mean QC results under each condition against the nominal value.
Quantitative Data Analysis and Visualization
Quantitative data from method validation experiments must be summarized clearly to demonstrate performance. When comparing quantitative variables, like results from different experimental conditions or groups, the data should be summarized for each group, and the difference between the means and/or medians should be computed [22]. The following table structures are recommended for summarizing validation data.
Table 1: Example Structure for Summarizing LOD/LOQ Experiment Data
| Analyte | Spiked Concentration (ng/mL) | Mean Calculated Concentration (ng/mL) | Standard Deviation (ng/mL) | %RSD | %Accuracy |
|---|---|---|---|---|---|
| Analyte A | 0.5 (LOD) | 0.48 | 0.12 | 25.0 | 96.0 |
| Analyte A | 1.5 (LOQ) | 1.53 | 0.25 | 16.3 | 102.0 |
| Analyte A | 5.0 | 4.95 | 0.41 | 8.3 | 99.0 |
Table 2: Example Structure for Robustness Testing Data (Variation of Column Temperature)
| QC Level | Nominal Temp. Result (ng/mL) | Reduced Temp. Result (ng/mL) | Increased Temp. Result (ng/mL) | % Change (Reduced) | % Change (Increased) |
|---|---|---|---|---|---|
| Low QC | 2.95 | 2.87 | 3.02 | -2.7% | +2.4% |
| Mid QC | 49.80 | 48.90 | 50.55 | -1.8% | +1.5% |
| High QC | 195.50 | 192.20 | 198.10 | -1.7% | +1.3% |
For effective data visualization, boxplots are an excellent choice for comparing the distribution of results, such as QC data under different robustness conditions. A boxplot summarizes data using five numbers: the minimum, first quartile (Q1), median (Q2), third quartile (Q3), and maximum, and can identify potential outliers [22]. This allows for a clear visual comparison of the central tendency and spread of data across different groups.
Advanced Quantitative Techniques
For more complex data analysis, especially with high-dimensional data, robust statistical methods are necessary. A two-step approach to classification can be effective, and robust regression techniques can be applied to predict outcomes based on complex spectral data, such as FTIR spectra used to monitor engine oil degradation [59]. Furthermore, strategies for outlier explanation are crucial for investigating why an observation is outlying, turning anomalous data points into insights about method performance [59].
The Scientist's Toolkit: Essential Research Reagents and Materials
The following table details key materials and solutions required for executing the validation experiments described in this guide.
Table 3: Key Research Reagent Solutions for Method Validation Studies
| Item Name | Function / Purpose in Validation |
|---|---|
| Certified Reference Material (CRM) | Provides a traceable standard of known purity and concentration for accurate calibration and to establish the analytical measurement function. |
| Matrix-Matched Calibrators | Calibrators prepared in the same biological matrix as the sample (e.g., blood, urine) to compensate for matrix effects and ensure accurate quantification. |
| Quality Control (QC) Materials | Independent samples at low, mid, and high concentrations used to monitor the precision and accuracy of the analytical run across the reportable range. |
| Stable Isotope-Labeled Internal Standards | Corrects for variability in sample preparation and instrument response, improving the precision and robustness of the method. |
| Extraction Solvents & Sorbents | For sample clean-up and pre-concentration of the analyte via techniques like Solid-Phase Extraction (SPE) or Liquid-Liquid Extraction (LLE). |
| Mobile Phase Components | High-purity solvents and buffers used in chromatographic separation; their consistency is critical for method robustness. |
Workflow for LOD/LOQ Determination
The detailed experimental pathway for determining a method's sensitivity limits is visualized in the following workflow, which integrates the protocol and data analysis steps.
Balancing Comprehensive Testing with Practical Resource Constraints
In forensic method validation research, the tension between comprehensive testing and practical resource constraints represents a fundamental challenge for researchers, scientists, and drug development professionals. The end-user requirements for forensic methodologies extend beyond mere technical feasibility to encompass reliability, admissibility, and practical implementability within real-world operational constraints. This whitepaper establishes a framework for balancing scientific rigor with resource limitations, drawing upon established scientific guidelines and practical implementation strategies.
The National Institute of Standards and Technology (NIST) and other standards bodies emphasize that validation must demonstrate a method is fit for its intended purpose, requiring researchers to make strategic decisions about testing scope, sample sizes, and methodological depth while working within finite budgets, timelines, and technical capabilities [60]. This balance is particularly critical in forensic science, where methods must withstand judicial scrutiny under standards such as Daubert while remaining practically implementable in operational forensic laboratories.
Theoretical Framework: Scientific Guidelines for Forensic Method Validation
Foundation in Bradford Hill Principles
The evaluation framework for forensic feature-comparison methods draws inspiration from the Bradford Hill Guidelines for causal inference in epidemiology, adapted to address the unique requirements of forensic science [60]. This guidelines approach provides a structured yet flexible methodology for establishing scientific validity without mandating rigid, one-size-fits-all testing protocols.
Table: Bradford Hill-Inspired Guidelines for Forensic Method Validation
| Guideline | Application to Forensic Validation | Resource Considerations |
|---|---|---|
| Plausibility | Theoretical basis for the method's discriminatory power | Focus resources on methods with sound theoretical foundations |
| Construct & External Validity | Sound research design and methods | Balance controlled studies with real-world applicability |
| Intersubjective Testability | Replication and reproducibility | Prioritize multi-site collaborations to share validation burden |
| Group to Individual Inference | Valid methodology to reason from population data to specific cases | Develop statistical frameworks that maximize information from limited samples |
Daubert Framework Considerations
For forensic methods to be admissible in judicial proceedings, they must satisfy the Daubert standard, which emphasizes empirical testing, peer review, known error rates, and general acceptance within the scientific community [60]. These requirements directly impact resource allocation decisions during method validation:
- Testability and Error Rate Determination: Requires significant investment in controlled studies with appropriate sample sizes
- Peer Review Publication: Necessitates complete documentation and independent verification
- Standards Development: Demands consensus-building across institutions and practitioners
- General Acceptance: Involves demonstration and knowledge transfer within the scientific community
Core Methodological Approaches
Tiered Validation Strategy
A tiered approach to method validation optimizes resource allocation by establishing minimum requirements for implementation while defining pathways for ongoing refinement:
Level 1: Foundational Validation
- Minimum sample sets for preliminary reliability assessment
- Single-laboratory studies establishing basic performance characteristics
- Literature review establishing theoretical plausibility
Level 2: Multi-site Reprodubility Studies
- Interlaboratory comparisons to establish transferability
- Expanded sample sets covering expected variation
- Initial error rate estimation with confidence intervals
Level 3: Continuous Performance Monitoring
- Ongoing proficiency testing during operational implementation
- Refined error rate estimation with accumulated casework
- Adaptive validation based on emerging patterns and technologies
Experimental Design for Resource-Constrained Environments
Efficient experimental design maximizes information yield from limited resources through strategic planning and statistical optimization:
Table: Resource-Optimized Experimental Protocols
| Validation Component | Comprehensive Approach | Resource-Constrained Alternative |
|---|---|---|
| Sample Size | Large-scale representative samples (1000+) | Sequential testing with stopping rules; ~100-200 samples with statistical projection |
| Error Rate Estimation | Blind proficiency testing with multiple examiners | Bayesian methods incorporating prior information; bootstrap resampling techniques |
| Reproducibility Assessment | Multi-laboratory studies with full method transfer | Split-sample analysis with centralized evaluation; virtual collaboration platforms |
| Specificity Testing | Exhaustive challenge with similar materials | Targeted challenge based on risk assessment; computational modeling of interferents |
Quantitative Framework and Data Presentation
Establishing quantitative benchmarks is essential for standardized assessment of method performance across resource environments. The following parameters represent minimum data requirements for defensible validation:
Key Performance Metrics
Table: Essential Quantitative Metrics for Forensic Method Validation
| Performance Metric | Minimum Acceptable Threshold | Target Performance | Resource-Smart Assessment Method |
|---|---|---|---|
| Analytical Sensitivity | Detection at forensically relevant concentrations | 95% detection at minimum relevant level | Serial dilution with statistical confidence intervals |
| Precision/Reproducibility | CV < 15% for intra-lab; < 20% inter-lab | CV < 10% intra-lab; < 15% inter-lab | Nested design with minimal replicates |
| Specificity/Selectivity | No false positives in 20 challenge samples | No false positives in 50 challenge samples | Targeted interference testing based on likely contaminants |
| Accuracy/Bias | Recovery 85-115% | Recovery 90-110% | Standard reference materials when available; spike recovery |
| Robustness | Function within specified operational parameters | Tolerant to minor variations in procedure | Forced degradation studies; parameter deliberately varied |
| Limit of Detection | Statistically different from blank (p<0.05) | 3:1 signal-to-noise ratio | Bootstrapping methods with limited replicates |
Implementation Protocols
Structured Experimental Workflows
The following diagrams illustrate resource-optimized experimental workflows for forensic method validation:
Validation Workflow for Resource-Constrained Environments
Resource Allocation Strategy
Forensic Method Validation Resource Allocation
The Scientist's Toolkit: Essential Research Reagent Solutions
Table: Key Research Reagent Solutions for Forensic Method Validation
| Reagent Category | Specific Examples | Function in Validation | Resource Optimization Tips |
|---|---|---|---|
| Reference Standards | Certified reference materials (CRMs), internal standards | Establish accuracy, precision, and quantification | Use in-house standards calibrated against CRMs; share standards across projects |
| Quality Control Materials | Positive controls, negative controls, proficiency samples | Monitor method performance and reproducibility | Create large batches of in-house QC materials; implement statistical quality control |
| Sample Matrices | Blank matrices, authentic case samples | Assess specificity, interference, and real-world applicability | Use artificial matrices when possible; bank authentic samples for multiple validations |
| Calibrators | Serial dilutions for calibration curves | Establish quantitative relationship and dynamic range | Prepare master stocks; use multi-point calibration with fewer replicates |
| Stability Materials | Forced degradation samples, stability check samples | Evaluate method robustness and sample stability | Focus on worst-case conditions; use predictive modeling to reduce testing time |
Signaling Pathways in Method Validation Decision-Making
The decision pathway for forensic method validation involves multiple checkpoints to ensure scientific rigor while respecting resource limitations:
Method Validation Decision Pathway
Balancing comprehensive testing with practical resource constraints requires a strategic, tiered approach that prioritizes scientific defensibility while making efficient use of available resources. By implementing the structured frameworks, experimental protocols, and resource allocation strategies outlined in this technical guide, forensic researchers and drug development professionals can establish method validity that satisfies both scientific standards and practical implementation requirements.
The key to successful validation lies not in exhaustive testing of every possible parameter, but in strategic risk-based assessment that focuses resources on the most critical validation elements while establishing mechanisms for continuous performance monitoring during operational implementation. This approach ensures that forensic methods meet end-user requirements for reliability, admissibility, and practical utility within real-world constraints.
Strategies for Managing Evolving Requirements and Method Updates
In the high-stakes field of forensic science, particularly within microbial forensics and drug development, the management of evolving requirements and method updates is not merely an administrative task but a fundamental scientific imperative. Method validation provides the foundational framework that ensures forensic evidence can generate reliable, accurate, and defensible results that seriously impact investigations, individual liberties, and even potential military responses to biological attacks [33]. The process of validation connotes confidence in a test or process, requiring strict delineation of steps to avoid misinterpretation and misapplication of methods. In this context, requirements management transcends simple documentation to become a dynamic process that must continuously address emerging threats, technological advancements, and evolving scientific standards.
The nascent field of microbial forensics demands explicit descriptions of what constitutes validation, as failing to properly validate a method or misinterpreting results from a microbial forensic analysis may have severe consequences [33]. With the international implementation of standards like ISO 21043, which provides requirements and recommendations designed to ensure the quality of the forensic process, forensic-service providers must adopt strategies that maintain both scientific rigor and regulatory compliance [4]. This technical guide outlines a comprehensive framework for managing evolving requirements within forensic method validation research, providing researchers, scientists, and drug development professionals with actionable strategies to navigate this complex landscape.
Foundational Concepts: Validation Categories and International Standards
Core Validation Categories in Forensic Sciences
Validation in microbial forensics and related disciplines is categorized into three distinct types, each serving a specific purpose in the method lifecycle. These categories form a hierarchical structure that ensures methods progress from theoretical development to operational implementation while maintaining scientific integrity throughout the process [33].
Developmental Validation: This initial phase involves the acquisition of test data and the determination of conditions and limitations of a newly developed method for analyzing samples. The development and validation processes are intimately intertwined and should be considered together early in the development process. Developmental validation must be appropriately documented and should address specificity, sensitivity, reproducibility, bias, precision, false positives, and false negatives [33].
Internal Validation: Once a method or process has been developed and initially validated, it may be transferred to an operational laboratory for implementation. Internal validation is an accumulation of test data within an operational laboratory to demonstrate that established methods and procedures are carried out within predetermined limits in the laboratory. The laboratory must monitor and document its reproducibility and precision and define reportable ranges of the procedure using controls [33].
Preliminary Validation: In scenarios where a fully validated method is unavailable for a novel threat, preliminary validation serves as an early evaluation of a method that will be used to investigate a biocrime or bioterrorism event. This validation acquires limited test data to enable the evaluation of a method for its investigative-lead value, with the intent of identifying key parameters and operating conditions [33].
ISO 21043 and the Forensic-Data-Science Paradigm
The introduction of ISO 21043 as a new international standard for forensic science represents a significant advancement in quality assurance. This standard provides requirements and recommendations designed to ensure the quality of the forensic process across multiple parts: (1) vocabulary; (2) recovery, transport, and storage of items; (3) analysis; (4) interpretation; and (5) reporting [4]. From the perspective of the forensic-data-science paradigm, conformity with ISO 21043 requires methods that are transparent and reproducible, intrinsically resistant to cognitive bias, use the logically correct framework for interpretation of evidence (the likelihood-ratio framework), and are empirically calibrated and validated under casework conditions [4].
Table 1: Core Elements of Method Validation Based on Quality Assurance Guidelines
| Validation Element | Key Requirements | Documentation Standards |
|---|---|---|
| Developmental Validation | Assess specificity, sensitivity, reproducibility, bias, precision, false positives, false negatives [33] | Complete documentation of all test data and conditions |
| Internal Validation | Testing using known samples; monitoring reproducibility and precision; defining reportable ranges [33] | Laboratory records demonstrating performance within predetermined limits |
| Preliminary Validation | Acquisition of limited test data for investigative support; identification of key parameters [33] | Documentation of expert panel review and recommendations for additional studies |
| Ongoing Validation | Qualifying tests for analysts; modification documentation for analytical procedures [33] | Records of analyst proficiency and documented approval for modifications |
Strategic Framework for Managing Evolving Requirements
The Validation Plan as a Living Document
A critical strategy for managing evolving requirements begins with the construction of a comprehensive "validation plan" that serves as a dynamic framework rather than a static document. Preparation of this plan starts by defining the criteria that will be used to evaluate the performance of a method, guiding those who may develop and/or implement a new method and providing a record of what was addressed during validation [33]. Since generating a universal list of criteria for all possible methods is impractical due to the multitude of diverse processes and myriad targets to be assessed, the validation plan must be adaptable yet comprehensive.
Two primary and overarching criteria that transcend all methodological variations are reliability and reproducibility. Additional criteria such as specificity, sensitivity, accuracy, and precision apply to most analytical methods, while more specialized criteria are required for collection tools and methods concerning recovery, stability, and yield [33]. The experimental validation design should accumulate performance data on each of the method parameters to enable proper inferences based on the results of the analysis. A well-constructed validation plan defines the range of conditions under which the process may be applied so that the interpretation of the analytical results is effective and useful and, equally important, the conditions under which the results or the standard interpretation is not effective or reliable are understood [33].
Implementation of Continuous Monitoring and Adaptive Control
The future of requirements management points toward intelligent, adaptive, self-optimizing systems that transition from human-driven, reactive processes to AI-driven, proactive frameworks [61]. This paradigm shift enables requirements to exist as living, executable entities that can auto-detect inconsistencies and redundancies, generate initial drafts based on domain models and historical patterns, and update themselves when related code, data models, or business rules change [61]. Implementation of this approach involves several key components:
Natural Language + Model-Driven Engineering: Analysts describe outcomes in natural language; the system maps them to formal, machine-readable requirements, creating a seamless transition from human intent to computational execution [61].
Automated Change Impact Analysis: The system monitors code commits, database changes, and API contract updates to trigger requirement updates, ensuring that methodological evolution maintains synchronization with all dependent systems [61].
Continuous Refinement Loops: Requirements evolve alongside the product, with AI suggesting modifications based on telemetry, user feedback, and changing business goals, creating a responsive ecosystem that adapts to new information [61].
Digital Twin for Requirements: Every requirement has a virtual representation within a system model that allows stakeholders to simulate impact before implementation, enabling risk simulation and "what-if" scenarios to test requirements against edge cases, failure modes, and scaling conditions [61].
AI-Driven Gap Analysis and Ethical Oversight
A crucial strategy for managing evolving requirements involves leveraging artificial intelligence to maintain methodological integrity while adapting to new challenges. AI-driven gap analysis supports requirements gathering by proactively identifying omissions and recommending domain-specific inclusions through several mechanisms [61]:
Domain Knowledge Graphs: AI cross-references requirements against industry standards, regulatory frameworks, and competitive benchmarks, ensuring comprehensive coverage of relevant domains.
NFR Coverage Checks: Automated detection of missing non-functional requirements, particularly in critical areas such as security, accessibility, and sustainability, prevents oversights that could compromise method validity [61].
Bias & Ambiguity Detection: Automated flagging of unclear terms, vague criteria, and assumptions maintains methodological clarity and precision as requirements evolve [61].
Beyond technical compliance, the future framework incorporates ethical and strategic control, where every requirement is evaluated not only for feasibility and performance but also for its ethical, societal, and strategic implications [61]. This involves implementing ethical review pipelines with automated checks against ethical guidelines, human rights impacts, and sustainability targets, alongside strategic alignment scoring that evaluates requirements against long-term organizational goals and national priorities [61].
Data Presentation and Quantitative Assessment in Method Validation
Structured Comparison of Quantitative Data
In forensic method validation research, effective presentation of quantitative data is essential for demonstrating method performance and facilitating comparison between different methodological approaches. When comparing quantitative variables in different groups, the data should be summarised for each group separately, with the difference between the means and/or medians computed when two groups are being compared [22]. This approach enables researchers to assess the practical significance of methodological changes alongside statistical significance.
The use of appropriately structured tables is particularly valuable in method validation as they provide a systematic overview of results and allow presentation of exact numerical values and information with different units side-by-side [62]. Well-constructed tables help readers assess the generalizability of findings and understand associations between variables, with subsequent tables presenting details of associations/comparisons between variables, often showing crude findings followed by models adjusted for confounding factors [62]. A good table draws attention to the data rather than the table itself, enabling readers to form opinions about results through visual inspection alone [62].
Table 2: Quantitative Comparison of Method Performance Metrics Across Validation Studies
| Performance Metric | Method A (Legacy) | Method B (Updated) | Difference | Acceptance Threshold |
|---|---|---|---|---|
| Sensitivity (%) | 92.5 | 96.8 | +4.3 | ≥95% |
| Specificity (%) | 94.2 | 95.1 | +0.9 | ≥95% |
| False Positive Rate | 5.8 | 4.9 | -0.9 | ≤5% |
| Reproducibility (CV%) | 8.7 | 6.2 | -2.5 | ≤7% |
| Sample Throughput (samples/hour) | 12 | 18 | +6 | ≥15 |
| Limit of Detection (ng/μL) | 0.05 | 0.02 | -0.03 | ≤0.03 |
| Recovery Efficiency (%) | 85.3 | 92.7 | +7.4 | ≥90% |
Visualization Strategies for Method Performance Data
Beyond tabular presentation, effective visualization of method performance data provides critical insights into distribution characteristics, trends, and comparative effectiveness. Several visualization approaches are particularly valuable in forensic method validation research:
Boxplots: These visualizations summarize data distributions using five numbers (minimum, first quartile, median, third quartile, and maximum) and are excellent for comparing variations in samples of a population, particularly for non-parametric data [22] [62]. Boxplots express median and quartiles of data using a box shape, with whiskers extending as lines representing the range of data, and individual points representing outliers [62].
Back-to-back stemplots: Particularly useful for small amounts of data when comparing two groups, these visualizations enable researchers to retain original data while facilitating direct comparison between methodological approaches [22].
2-D Dot Charts: These charts place a dot for each observation, separated for each level of the qualitative variable, enabling comparison across any number of groups while maintaining visibility of individual data points [22].
The strategic use of these visualization methods enables researchers to communicate complex methodological comparisons effectively, supporting the interpretation of validation results and facilitating informed decisions about method adoption and refinement.
Experimental Protocols for Validation Studies
Protocol for Developmental Validation
The developmental validation process requires a systematic approach to establish the fundamental performance characteristics of a new method. The following protocol provides a framework for conducting comprehensive developmental validation studies:
Define Objective Performance Criteria: Establish clear metrics for specificity, sensitivity, reproducibility, bias, precision, false positives, and false negatives before initiating validation studies [33].
Determine Required Controls: Identify and document appropriate positive, negative, and internal controls that will be used to monitor method performance throughout validation [33].
Establish Reference Databases: Document any reference database used during method development and validation, ensuring traceability and transparency in data sources [33].
Conduct Sensitivity Testing: Systematically evaluate method performance across the anticipated dynamic range, establishing limits of detection and quantification under controlled conditions.
Assess Specificity: Challenge the method with related interferents and substances to establish discrimination capabilities and potential cross-reactivity.
Evaluate Reproducibility and Precision: Conduct intra-day and inter-day testing with multiple replicates across different operators to quantify method variability [33].
Document All Procedures and Results: Maintain comprehensive records of all experimental conditions, raw data, and statistical analyses to support method defensibility.
Protocol for Internal Validation
Upon transfer of a developed method to an operational laboratory, internal validation confirms that the established method performs consistently within the new environment:
Verify Performance with Known Samples: Test the procedure using samples with established characteristics to confirm method performance in the operational setting [33].
Establish Laboratory-Specific Parameters: Define reportable ranges of the procedure using appropriate controls specific to the laboratory's instrumentation and reagents [33].
Qualify Analytical Personnel: Ensure each analyst or examination team successfully completes a qualifying test for the procedure before introduction into sample analysis [33].
Implement Ongoing Monitoring: Establish procedures for continuous monitoring and documentation of reproducibility and precision during routine operation [33].
Document Modifications: Record any material modifications made to analytical procedures and subject them to validation testing commensurate with the modification [33].
Visualization of Method Validation Workflows
Effective visualization of complex validation workflows enhances understanding, promotes consistency, and facilitates communication across multidisciplinary teams. The following diagrams illustrate key processes in managing evolving requirements and method validation.
Figure 1: Method Validation and Update Lifecycle
Figure 2: Continuous Monitoring Framework
Figure 3: Requirements Evolution Workflow
The Scientist's Toolkit: Essential Research Reagents and Materials
Successful implementation of method validation strategies requires access to appropriate research tools and materials. The following table details key resources essential for conducting robust validation studies in forensic and pharmaceutical research contexts.
Table 3: Essential Research Reagents and Materials for Method Validation Studies
| Category | Specific Items | Function in Validation | Quality Requirements |
|---|---|---|---|
| Reference Materials | Certified reference standards, Characterized microbial strains, DNA quantitation standards [33] | Establish method accuracy and calibration; provide benchmark for performance assessment | Traceable to national or international standards; documented purity and stability |
| Quality Control Materials | Positive controls, Negative controls, Internal standards [33] | Monitor method performance during validation; detect deviations and contamination | Well-characterized; stable under storage conditions; representative of sample matrix |
| Sample Collection Tools | Swabs, Filters, Containers, Transport media [33] | Evaluate recovery efficiency and sample stability; validate collection procedures | Demonstrated compatibility with analytical methods; validated sterilization procedures |
| Nucleic Acid Analysis | PCR primers/probes, Extraction kits, Enzymes, Quantitation assays [33] | Assess specificity, sensitivity, and reproducibility of molecular methods | Documented sequence verification; optimized reaction conditions; minimal batch variation |
| Data Analysis Tools | Statistical software, Reference databases, Interpretation guidelines [33] [4] | Support quantitative assessment of performance metrics; ensure consistent interpretation | Transparent algorithms; validated statistical methods; regularly updated databases |
Future Directions: The Evolution of Requirements Management
The future of requirements management in forensic method validation points toward increasingly intelligent, adaptive systems that fundamentally transform how methods are developed, validated, and maintained. Over the next five years, the field will likely experience a paradigm shift from human-driven, tool-assisted, reactive approaches to AI-driven, human-guided, proactive frameworks [61]. This transformation will manifest through several key developments:
Self-Driving Requirements: Requirements will evolve from static documents to dynamic, executable assets capable of auto-detecting inconsistencies, generating initial drafts based on domain models and historical patterns, and updating themselves when related code, data models, or business rules change [61].
Live Traceability with Business Metrics: The concept of traceability will expand beyond connecting requirements to code and test cases to linking them directly to live business and operational metrics, enabling real-time monitoring of how well requirements are being met in production and whether intended business value is being achieved [61].
Ethical and Strategic Control Pipelines: Automated ethical review pipelines will evaluate requirements not only for feasibility and performance but also for ethical, societal, and strategic implications, using predictive modeling to foresee long-term effects on security, privacy, and societal trust [61].
These advancements will collectively transform requirements from administrative artifacts into strategic assets that actively contribute to method reliability, regulatory compliance, and scientific validity in forensic and pharmaceutical research contexts.
Beyond the Checklist: Collaborative Models and Framework Evaluation for Robust Validation
Leveraging Collaborative Validation to Standardize and Share Requirements
In forensic science, the traditional paradigm of individual forensic science service providers (FSSPs) independently validating methods is increasingly unsustainable. This isolated approach leads to a "tremendous waste of resources in redundancy" and misses a significant opportunity to combine talents and share best practices [6]. This technical guide proposes a collaborative method validation model as a superior framework, designed to standardize techniques, enhance efficiency, and, most critically, ensure that methodologies are robustly validated against empirically defined end-user requirements. The foundational principle of this model is that FSSPs performing the same tasks with the same technology should work cooperatively to develop, validate, and share common methodologies [6].
The imperative for this shift is driven by several factors. Technology is advancing in capability, complexity, and cost, while the primary mission of FSSPs remains casework. Every resource allocated to method validation is, consequently, diverted from active casework [6]. Furthermore, the legal system requires scientific methods that are reliable and broadly accepted, adhering to standards such as Daubert [6]. A collaborative model directly supports these legal and operational requirements by building a consolidated, cross-laboratory body of objective evidence for each method's validity.
The Collaborative Validation Model: Core Principles and Workflow
The collaborative validation model transforms a traditionally siloed activity into a coordinated, community-driven effort. Its core operational principle is that an originating FSSP conducts a full, peer-reviewed validation of a method and publishes its work, enabling subsequent FSSPs to conduct a much more abbreviated verification process, provided they adhere strictly to the published method parameters [6].
Key Definitions and Process Flow
- Validation: The provision of objective evidence that a method's performance is adequate for its intended use and meets specified requirements [6]. It demonstrates that the results are reliable and fit for purpose.
- Verification: The process by which a second FSSP reviews, accepts, and confirms the original published data and findings, thereby eliminating significant method development work [6].
The workflow of this model, from initial development to laboratory implementation, is illustrated in the following diagram:
Alignment with End-User Requirements
A critical success factor for any forensic method is its fitness for purpose, which is determined by the needs of its end-users. The collaborative model provides a structured mechanism to define and standardize these requirements. A study on field-based molecular detection systems for wildlife forensics exemplifies how end-user requirements can be formally captured [63]. The key requirements identified through stakeholder consultation, which align with the drivers for many forensic applications, are summarized in the table below.
Table 1: Exemplary End-User Requirements for a Field-Based Forensic System [63]
| Requirement Category | Specific User Need |
|---|---|
| Performance | ≥95% accuracy |
| Speed | Results within one hour from start of analysis |
| Ease of Use | Simple to use with minimal training |
| Key Species | Assays for high-priority species (e.g., elephant, rhinoceros, pangolin, rosewood, tiger) |
| Sample Throughput | Capability to test 1-5 samples per analysis |
Integrating such clearly defined requirements from the outset ensures that collaborative validations are not merely technically sound but also practically relevant. This direct linkage between validation data and user needs is a cornerstone of the model, increasing trust and adoption across diverse laboratories [6] [63].
Experimental Protocols for Collaborative Validation
The collaborative approach is structured around a phased validation process. This ensures a comprehensive evidence base is established for a method before it is deployed in casework.
The Three Phases of Forensic Method Validation
Validation for forensic applications is broken down into three consecutive phases, which can be distributed across the collaborative network [6]:
- Phase One (Developmental Validation): This initial phase involves high-level research, general procedure development, and proof of concept. It is frequently conducted by research scientists and published in peer-reviewed journals.
- Phase Two (Internal Validation): This phase is typically performed by the originating FSSP. It involves defining the specific protocol and establishing performance characteristics such as sensitivity, specificity, reproducibility, and limitations using samples that mimic evidence.
- Phase Three (Collaborative Verification): In this phase, subsequent FSSPs verify the method by repeating a subset of the validation experiments, confirming that they can achieve the performance standards set by the originating FSSP when following the published protocol exactly.
Detailed Protocol for an Internal Validation Study
The following protocol provides a template for an originating FSSP conducting an internal validation for a DNA-based species identification assay, incorporating the end-user requirements from Table 1.
Table 2: Detailed Experimental Protocol for Internal Validation of a DNA Assay
| Experiment | Methodology | Key Parameters Measured | Acceptance Criteria (Example) |
|---|---|---|---|
| Specificity | Test the assay against a panel of DNA from non-target species (e.g., 20 common related and unrelated species). | Number of false-positive or false-negative results. | 100% specificity across the tested panel [63]. |
| Sensitivity | Serially dilute DNA from a known target species and perform the assay in replicates (n=5 per dilution). | The minimum detectable DNA concentration (limit of detection). | Consistent detection at or below a predefined threshold (e.g., 0.1 ng/µL). |
| Accuracy | Analyze a set of blinded samples (n=30) of known origin, including target and non-target species. | Percentage of samples correctly identified. | ≥95% accuracy, aligning with end-user requirements [63]. |
| Precision & Reproducibility | Run the assay on reference samples across multiple days, by different analysts, and using different instrument lots (if applicable). | Inter- and intra-run variability. | Coefficient of variation (CV) < 5% for quantitative measures; 100% concordance for qualitative identifications. |
| Robustness | Deliberately vary protocol parameters within a reasonable range (e.g., incubation temperature ±2°C, reaction volume ±10%). | Success of the assay under modified conditions. | The assay produces the correct result despite minor deviations. |
| Time-to-Result | Time the entire process from sample preparation to result interpretation for multiple replicates. | Average time and standard deviation. | Less than 60 minutes, meeting the end-user speed requirement [63]. |
Data Presentation and Analysis
A core tenet of the collaborative model is the transparent presentation of validation data to facilitate evaluation and adoption by other laboratories.
The following table illustrates how summary data from a validation study should be presented to allow for easy comparison and verification by subsequent FSSPs.
Table 3: Summary of Validation Data for a Gorilla Chest-Beating Rate Study (Illustrative Example) [22]
| Group | Mean Rate (beats/10h) | Standard Deviation | Sample Size (n) |
|---|---|---|---|
| Younger Gorillas (<20 years) | 2.22 | 1.270 | 14 |
| Older Gorillas (≥20 years) | 0.91 | 1.131 | 11 |
| Difference (Younger - Older) | 1.31 | - | - |
This clear presentation of means, standard deviations, and sample sizes provides the foundational data for other researchers to understand the method's ability to distinguish between groups.
Data Comparison and Benchmarking
A significant advantage of mirroring a published validation is the availability of benchmark data for comparison. When a second FSSP conducts its verification, the results form an inter-laboratory study. The following diagram visualizes this comparative process, which strengthens the collective confidence in the method.
This process of direct cross-comparison adds to the total body of knowledge, supports all FSSPs using the technology, and helps identify any laboratory-specific deviations early in the implementation phase [6].
The Scientist's Toolkit: Research Reagent Solutions
Successful implementation of a collaboratively validated method requires access to standardized, high-quality materials. The following table details essential reagents and their functions in a typical molecular forensic workflow.
Table 4: Key Research Reagent Solutions for Molecular Forensic Validation
| Item | Function |
|---|---|
| Commercial DNA Extraction Kits | Purify DNA from complex sample matrices (e.g., blood, tissue, processed goods) while removing inhibitors that can affect downstream analysis. |
| PCR Master Mix | A pre-mixed solution containing enzymes, nucleotides, and buffers for the Polymerase Chain Reaction (PCR), ensuring consistent amplification of target DNA sequences. |
| Species-Specific Primers/Probes | Short, synthetic DNA sequences designed to bind to and detect unique genomic regions of a target species (e.g., elephant, rhinoceros) [63]. |
| Positive Control DNA | Genomic DNA from a verified specimen of the target species, used to confirm the assay is functioning correctly in each run. |
| Negative Control (Nuclease-Free Water) | A control containing no DNA, used to detect contamination in reagents or during the setup process. |
| Standard Reference Materials | Certified materials of known origin and composition, essential for validating the accuracy of quantitative and qualitative methods. |
The collaborative validation model represents a paradigm shift from isolated, redundant effort to efficient, standardized, and scientifically robust practice. By leveraging the work of originating FSSPs, the forensic community can dramatically reduce the time and cost of implementing new technologies. This guide has outlined the core principles, detailed experimental protocols, and essential tools required to execute this model effectively. The framework ensures that methods are not only technically valid but also directly aligned with the defined requirements of end-users, thereby enhancing the reliability, admissibility, and overall impact of forensic science in the legal system. Widespread adoption of this collaborative approach will empower researchers, scientists, and drug development professionals to standardize best practices, accelerate innovation, and steward resources more effectively.
The integration of externally validated methods is a critical process in forensic research and drug development, ensuring reliability while conserving resources. This guide details a formal pathway for the review and adoption of external validation data, rigorously framed within the principle of defining and verifying fitness for purpose against specific end-user requirements. Success hinges not on the mere availability of external data, but on systematic, evidence-based confirmation that it meets the precise needs of the intended application within a local context. The following sections provide a detailed procedural framework, experimental protocols for verification, and essential tools for implementation.
In forensic science and drug development, the validity of a method is the foundation of reliable results and, consequently, judicial and scientific credibility. Validation provides the objective evidence that a method is fit for its specific intended purpose [1]. While developmental validation is required for novel methods, many techniques are adopted or adapted from other organizations. This process of reviewing and leveraging pre-existing validation data is a sophisticated verification pathway that demands meticulous scrutiny.
The core challenge lies in the transition from a theoretical claim of validity to a demonstrated, practical validity within a new operational environment. As guided by the Forensic Science Regulator's Codes of Practice, simply possessing external validation records is insufficient; the implementing organization must critically review these records to ensure the validation was fit for purpose [1]. This process is fundamentally governed by the end-user requirement—a formal specification of what the method must reliably accomplish. This guide establishes the framework for this critical verification pathway.
Conceptual Foundation: Fitness for Purpose and End-User Requirements
Defining Fitness for Purpose
At its core, "fitness for purpose" means that a method is "good enough to do the job it is intended to do, as defined by the specification developed from the end-user requirement" [1]. This is a practical, not a theoretical, standard. It acknowledges that a method may be valid for one application but not for another, based on the specific demands of the output.
The Centrality of End-User Requirements
The end-user requirement (EUR) is the cornerstone of the entire verification pathway. It is a detailed document that captures what different users of the method's output require for it to be trustworthy and actionable [1]. For forensic methods, this directly relates to the critical findings an expert will rely on for a statement or report. The EUR shifts the focus from "is the method valid in general?" to "does this validation data demonstrate the method is valid for my needs?".
The initial step in the verification pathway is, therefore, the determination of the local EUR. This requirement should be documented before any external data is reviewed, ensuring an objective and unbiased assessment.
The Verification Pathway: A Step-by-Step Procedural Framework
The following diagram outlines the complete end-to-end process for reviewing and adopting external validation data, from defining needs to final implementation.
Determination of End-User Requirements and Specification
The pathway begins with the forensic unit formally defining its needs. This involves identifying all end-users (e.g., reporting scientists, investigators, courts) and documenting their specific, testable requirements [1]. These may pertain to:
- Functional Requirements: What the method must do (e.g., "The method must extract and quantify Substance X from blood plasma at a concentration of 1 ng/mL.").
- Performance Criteria: Required levels of accuracy, precision, sensitivity, and specificity.
- Operational Constraints: Compatibility with existing laboratory equipment, software, or throughput needs.
Identification, Acquisition, and Critical Review of External Data
Once the EUR is established, the organization can identify and acquire relevant external validation data from sources such as method developers, commercial vendors, or scientific literature [1]. The subsequent review is a two-stage process:
- Stage 1 - Sufficiency of Data: Determine if the available data is comprehensive, covering all parameters relevant to the EUR (e.g., selectivity, matrix effects, accuracy, precision, limits of detection/quantification) [64].
- Stage 2 - Robustness of Validation Design: Critically assess the quality of the external validation study itself. This involves evaluating whether the test material and data challenges used in the original validation were representative and robust enough to stress-test the method under conditions that match the local end-user requirements [1]. A dataset that is too simple may not predict real-world performance.
Risk Assessment, Gap Analysis, and Setting Acceptance Criteria
The review will identify gaps between the external validation data and the local EUR. A formal risk assessment is conducted to evaluate the implications of these gaps [1]. For example, a gap in testing for a specific matrix effect may pose a high risk if that matrix is central to the local caseload.
Based on this analysis, the organization establishes definitive, quantitative acceptance criteria for the verification study. These criteria are the benchmarks that will determine the success or failure of the local validation effort.
The Verification Study and Final Assessment
For an adopted method, the requirement moves from full re-validation to verification. The verification study is a limited set of experiments designed to demonstrate local competence and fill critical gaps identified in the analysis [1]. This typically involves testing the method in the local environment with a representative data set. The outcomes of this study are then objectively assessed against the pre-defined acceptance criteria. If the criteria are met, the method is deemed validated and an implementation plan is created.
Experimental Protocols for Verification Testing
The specific experiments in a verification study are dictated by the gaps identified during the critical review. The table below summarizes core validation parameters and corresponding experimental protocols.
Table 1: Key Validation Parameters and Experimental Protocols for Verification
| Validation Parameter | Experimental Protocol Description | Typical Acceptance Criteria |
|---|---|---|
| Selectivity/Specificity | Analyze samples from at least six independent sources (e.g., different donors) that are free of the analyte and potentially interfering substances. In forensic toxicology, this confirms the method distinguishes the analyte from other compounds [64]. | No significant interference (<20% of the lower limit of quantification response for the analyte). |
| Accuracy and Precision | Analyze quality control (QC) samples at multiple concentrations (low, medium, high) across multiple analytical runs (e.g., 5 runs per concentration). Accuracy (mean relative error) and precision (coefficient of variation) are calculated [64]. | Accuracy within ±15%; Precision within 15% CV. |
| Matrix Effects | Post-column infuse the analyte while injecting extracted blank samples from different sources. Ion suppression/enhancement is observed as a deviation in the baseline signal. Quantify by comparing analyte response in post-extraction spiked samples to neat solutions [64]. | Internal standard-normalized matrix factor CV <15%. |
| Lower Limit of Quantification (LLOQ) | Analyze multiple replicates (n≥5) of the LLOQ sample. The analyte response should be distinguishable from blank response and meet predefined precision and accuracy limits [64]. | Signal-to-noise ratio >5; Accuracy within ±20%; Precision within 20% CV. |
| Carryover | Inject a blank sample immediately following a high-concentration sample. Measure any residual analyte signal in the blank. | Carryover in blank should be ≤20% of LLOQ. |
The Scientist's Toolkit: Essential Research Reagents and Materials
The successful execution of verification studies relies on a suite of essential materials and reagents. The following table details key components of this "toolkit."
Table 2: Essential Research Reagent Solutions and Materials for Validation Studies
| Item | Function in Validation |
|---|---|
| Certified Reference Material (CRM) | Provides a traceable and certified quantity of the target analyte to establish method accuracy and serve as the primary standard for calibration [64]. |
| Stable Isotope-Labeled Internal Standard (IS) | Accounts for variability and losses during sample preparation and corrects for matrix effects in mass spectrometry-based assays, improving precision and accuracy [64]. |
| Control Matrices (e.g., Blank Plasma, Urine) | Serves as the foundation for preparing calibration standards and quality control (QC) samples. Used in selectivity and matrix effect experiments to ensure the method is specific to the analyte [64]. |
| Quality Control (QC) Samples | Prepared at low, medium, and high concentrations within the calibration range and analyzed alongside unknown samples. They are the primary tool for monitoring analytical run acceptance and method performance over time [64]. |
| Specialized Buffers and Mobile Phases | Critical for sample preparation (e.g., protein precipitation, liquid-liquid extraction) and chromatographic separation. Their consistent composition is vital for method robustness and reproducibility. |
The verification pathway for external validation data is a disciplined, evidence-based process that is integral to modern forensic and bioanalytical science. It moves beyond passive acceptance to active, critical confirmation of fitness for purpose. By rigorously defining end-user requirements, conducting a thorough gap analysis against external data, and executing a targeted verification study, organizations can ensure the reliability of their methods, maintain regulatory compliance, and uphold the highest standards of scientific integrity. This pathway efficiently leverages existing scientific work while providing the documented objectivity required by courts and accrediting bodies.
Comparative Analysis of Validation Frameworks and Guideline Efficacy
Within both forensic science and drug development, validation frameworks serve as the critical foundation for ensuring that analytical methods, processes, and equipment are fit for their intended purpose. This analysis is situated within a broader thesis on defining end-user requirements in forensic method validation research. The core premise is that the efficacy of any validation guideline is intrinsically linked to its ability to formally capture and address the specific needs of the end-user, whether that end-user is a forensic practitioner, a judicial body, or a patient relying on a biosimilar therapeutic. This guide provides an in-depth technical comparison of validation frameworks across these disciplines, summarizing quantitative data, detailing experimental protocols, and visualizing the logical workflows that underpin robust validation practices.
Comparative Analysis of Validation Principles
Validation, though discipline-specific, is universally defined as a comprehensive scientific study that produces objective evidence demonstrating a method, process, or piece of equipment is fit for its intended purpose [7]. The following tables summarize the core principles and quantitative data from forensic and pharmaceutical regulatory domains.
Table 1: Core Principles of Validation Across Disciplines
| Principle | Forensic Science Validation [15] [7] | Biosimilar Development Validation [65] [66] |
|---|---|---|
| Primary Goal | Ensure methods are reliable, mitigate miscarriages of justice [7] | Demonstrate biosimilarity to a reference product [65] |
| Core Focus | Method's fitness for purpose within the Criminal Justice System [7] | Comparative analytical assessment to detect product differences [66] |
| Key Driver | Forensic Science Regulator's Code; accreditation requirements [7] | U.S. Food and Drug Administration (FDA) guidance and regulations [65] |
| Role of End-User Requirements | Explicitly determined and reviewed at the start of the validation process [7] | Implicit in the requirement for the product to be "highly similar" and have "no clinically meaningful differences" [67] |
Table 2: Key Quantitative and Qualitative Metrics in Biosimilar Assessment (as of 2025)
| Assessment Type | Detects Product Differences | FDA Stated Sensitivity | Resource Intensity | Status in FDA Draft Guidance |
|---|---|---|---|---|
| Comparative Analytical Assessment (CAA) | Structural and functional characteristics | Generally more sensitive than CES [66] [68] | Lower | Often sufficient as primary evidence [66] |
| Comparative Efficacy Study (CES) | Clinical efficacy endpoints | Less sensitive than CAA for many products [67] | High, "resource-intensive" [67] | Not routinely required; justified only in specific circumstances [68] |
The data in Table 2 highlights a significant evolution in regulatory thinking. The U.S. FDA's 2025 draft guidance represents a paradigm shift, moving away from a default requirement for resource-intensive Comparative Efficacy Studies (CES) toward a streamlined approach that prioritizes sensitive Comparative Analytical Assessments (CAA) for therapeutic protein products [66] [67] [68]. This evolution is driven by advances in analytical technologies that can now characterize products with a high degree of specificity and sensitivity [68].
Defining End-User Requirements in Forensic Method Validation
In forensic science, the validation process is explicitly framed around the end-user. The process begins with "Determining and reviewing the end user requirements and specification" [7]. This initial, critical step ensures that the method is validated against the actual needs of the criminal justice system, which requires evidence that is "adequate, relevant, and reliable" for court proceedings [7].
End-user requirements in this context translate into a method's acceptance criteria, which are set and assessed before the validation exercise begins. The entire validation process—including risk assessment, testing the method's limits, and identifying potential for error—is conducted to give the court, investigators, and practitioners confidence in the forensic results [7]. This formal, documented process provides the objective evidence needed to support the reliability of forensic evidence presented in court, thereby mitigating the risk of miscarriages of justice [7].
Experimental Protocols for Validation
Protocol for Streamlined Biosimilarity Assessment
The following protocol is derived from the FDA's 2025 draft guidance for a streamlined biosimilar development pathway [66] [67] [68].
- Objective: To demonstrate that a proposed therapeutic protein biosimilar is highly similar to a reference product without conducting a comparative efficacy study (CES).
- Step 1: Conduct a Comprehensive Comparative Analytical Assessment (CAA). This is the foundation of the streamlined approach. The CAA must utilize state-of-the-art analytical techniques to structurally and functionally characterize both the proposed biosimilar and the reference product. The assessment must show that the products are manufactured from clonal cell lines, are highly purified, and can be well-characterized. The relationship between the product's quality attributes and its clinical efficacy must be well-understood and evaluable by the assays used [66] [68].
- Step 2: Perform a Human Pharmacokinetic (PK) Similarity Study. An appropriately designed human study must be conducted to demonstrate PK similarity between the proposed biosimilar and the reference product. This study must be feasible and clinically relevant for the product in question [66].
- Step 3: Conduct an Immunogenicity Assessment. A robust assessment of the immune response potential of the proposed biosimilar must be performed. This is critical for addressing residual uncertainty regarding safety, as differences in immunogenicity can signal clinically meaningful differences [66] [68].
- Step 4: Early and Frequent Engagement with Regulators. Sponsors are strongly encouraged to engage with the FDA early in the product development process to confirm that the planned CAA, PK study, and immunogenicity assessment are sufficient and that a CES is not needed [66] [68].
Protocol for Forensic Method Validation
This protocol outlines the generic workflow for validating a forensic science method, as defined by the Forensic Capability Network (FCN) [7].
- Objective: To produce objective evidence through a series of tests that a finalized forensic method is fit for its specific intended purpose within the criminal justice system.
- Step 1: Determine and Review End-User Requirements. The first step is to formally define and document the specifications and requirements of the end-user, which includes the court, investigators, and forensic practitioners [7].
- Step 2: Perform a Risk Assessment. Conduct a risk assessment of the method to identify potential points of failure or error that could impact the results [7].
- Step 3: Set Acceptance Criteria. Based on the end-user requirements, define clear, objective acceptance criteria that the method must meet to be deemed valid [7].
- Step 4: Produce a Validation Plan. Create a detailed plan outlining the experiments, tests, and materials to be used in the validation exercise [7].
- Step 5: Execute the Validation Exercise. Trained and competent practitioners, representative of the eventual users, perform the validation tests according to the plan. This includes testing the method's limits and identifying potential for error [7].
- Step 6: Produce a Validation Report and Statement of Completion. Document the results, analyze them against the acceptance criteria, and produce a final report with a statement on the method's validity [7].
- Step 7: Develop an Implementation Plan. Create a plan for rolling out the validated method into operational use, which includes training staff and establishing ongoing quality control procedures [7].
Workflow Visualization
The following diagram illustrates the logical sequence and iterative nature of the forensic method validation process, mapping directly onto the experimental protocol in section 4.2.
Forensic Method Validation Workflow
The streamlined biosimilarity assessment pathway, derived from FDA draft guidance, is visualized below. This pathway highlights the reduced reliance on clinical efficacy studies.
Streamlined Biosimilar Assessment Pathway
The Scientist's Toolkit: Key Research Reagent Solutions
The following table details essential materials and their functions in the context of the comparative analytical assessment (CAA) for biosimilars, a cornerstone of the modern validation framework.
Table 3: Key Reagents and Materials for Comparative Analytical Assessment
| Item / Reagent Solution | Function in Validation Framework |
|---|---|
| Clonal Cell Lines | Provides a consistent and defined biological factory for producing the proposed biosimilar and is a prerequisite for the streamlined FDA pathway [66]. |
| Reference Product | The licensed biologic product against which the proposed biosimilar is compared; serves as the benchmark for all analytical and functional comparisons [67]. |
| Advanced Analytical Assays | A suite of highly sensitive methods (e.g., mass spectrometry, chromatography, capillary electrophoresis) used to structurally characterize and compare the products, forming the core of the CAA [68]. |
| In Vitro Bioassays | Assays designed to model in vivo functional effects and evaluate the relationship between specific quality attributes and clinical efficacy [68]. |
| Pharmacokinetic (PK) Assays | Bioanalytical methods used to measure drug concentration in biological matrices from the PK study, crucial for demonstrating similarity in human absorption and exposure [66]. |
| Immunogenicity Assays | Assays (e.g., anti-drug antibody detection) used to assess the immune response potential of the proposed biosimilar compared to the reference product [66] [68]. |
The comparative analysis reveals a convergent evolution in validation frameworks across forensic science and drug development: a definitive shift towards evidence-based, scientifically rigorous assessments that prioritize objective, analytically-derived data over traditional, often more resource-intensive, studies. The efficacy of modern guidelines, such as the FDA's 2025 streamlined approach for biosimilars, is directly tied to their ability to leverage technological advancements in analytical methods. Furthermore, the forensic validation paradigm powerfully demonstrates that anchoring the entire validation process to formally defined end-user requirements is not merely a procedural step, but the fundamental mechanism for ensuring that a method is truly fit-for-purpose, thereby upholding the integrity of the criminal justice system and ensuring the reliability of scientific evidence presented within it.
Establishing Benchmarks for Objective Evidence and Performance Metrics
This technical guide provides a comprehensive framework for establishing robust benchmarks and performance metrics for forensic method validation, aligned with global regulatory standards and end-user requirements. With increasing judicial scrutiny of forensic evidence, driven by landmark reports from the National Research Council (NARC) and the President's Council of Advisors on Science and Technology (PCAST), the demand for scientifically valid, reliable, and legally admissible forensic methods has never been greater [16]. This document synthesizes current guidelines from the International Council for Harmonisation (ICH), the National Institute of Justice (NIJ), and the International Organization for Standardization (ISO) to provide forensic researchers, scientists, and drug development professionals with a structured approach to developing, validating, and implementing forensic methods that meet rigorous scientific and legal standards. By adopting a lifecycle approach that integrates the Analytical Target Profile (ATP) concept from ICH Q14 and the validation parameters from ICH Q2(R2), stakeholders can ensure their methods produce objective, reproducible, and forensically defensible results [69].
Recent critiques of forensic science have revealed significant flaws in widely accepted forensic techniques, highlighting the urgent need for standardized benchmarks and performance metrics [16]. The 2009 NRC report "Strengthening Forensic Science in the United States: A Path Forward" and the 2016 PCAST report "Forensic Science in Criminal Courts: Ensuring Scientific Validity of Feature-Comparison Methods" fundamentally challenged the scientific validity of many traditional forensic methods, with the exception of DNA analysis and some fingerprint examination techniques [16]. These reports compelled the forensic community to re-evaluate methods against stricter scientific standards, particularly emphasizing demonstrable validity, reliability, and known error rates.
In response to these challenges, regulatory bodies and standards organizations have developed frameworks to strengthen forensic practice. The NIJ's Forensic Science Strategic Research Plan, 2022-2026 establishes priorities for advancing forensic science through applied research, foundational validation studies, and workforce development [70]. Simultaneously, the adoption of ISO 21043 as an international standard for forensic sciences provides requirements and recommendations designed to ensure quality throughout the forensic process, including recovery, analysis, interpretation, and reporting of evidence [4]. For forensic method validation research, defining clear end-user requirements through structured benchmarks is no longer optional—it is an ethical, scientific, and legal necessity.
Regulatory Frameworks and Standards
International Guidelines: ICH Q2(R2) and Q14
The International Council for Harmonisation (ICH) provides harmonized technical guidelines that have become the global gold standard for analytical procedure validation. ICH Q2(R2), "Validation of Analytical Procedures," outlines fundamental performance characteristics that must be evaluated to demonstrate a method is fit for its purpose [69]. The recent revision modernizes previous principles by expanding its scope to include modern technologies and emphasizing a science- and risk-based approach to validation.
Complementing Q2(R2), ICH Q14, "Analytical Procedure Development," provides a framework for systematic, risk-based analytical procedure development. It introduces the Analytical Target Profile (ATP) as a prospective summary of a method's intended purpose and desired performance criteria [69]. This represents a shift from a prescriptive, "check-the-box" approach to a more scientific, lifecycle-based model that continues throughout a method's entire useful life.
Key Modernization Aspects of ICH Q2(R2) and Q14:
- Lifecycle Management: Validation is not a one-time event but continues throughout the method's entire lifecycle [69]
- Science- and Risk-Based Approach: Methods are developed and validated based on scientific understanding and risk assessment rather than prescriptive checklists [69]
- Enhanced Approach: Allows for more flexibility in post-approval changes through a risk-based control strategy [69]
- Inclusion of New Technologies: Explicitly includes guidance for modern techniques like multivariate analytical procedures [69]
Forensic-Specific Standards: ISO 21043 and NIJ Strategic Plan
ISO 21043 is a comprehensive international standard for forensic sciences structured in five parts: (1) vocabulary, (2) recovery, transport, and storage of items, (3) analysis, (4) interpretation, and (5) reporting [4]. This standard emphasizes methods that are transparent, reproducible, resistant to cognitive bias, and use the logically correct framework for interpretation of evidence (the likelihood-ratio framework) [4].
The NIJ's Forensic Science Strategic Research Plan, 2022-2026 outlines five strategic priorities with specific objectives for advancing forensic science [70]:
Table: NIJ Strategic Research Priorities for Forensic Science
| Strategic Priority | Key Objectives |
|---|---|
| I. Advance Applied R&D | Develop methods/technologies to overcome current barriers; optimize workflows; improve evidence identification/collection [70] |
| II. Support Foundational Research | Assess fundamental scientific basis of forensic disciplines; measure accuracy/reliability; understand evidence limitations [70] |
| III. Maximize Research Impact | Disseminate research products; support implementation; assess program effectiveness [70] |
| IV. Cultivate Workforce | Foster next-generation researchers; facilitate research in public labs; advance workforce capabilities [70] |
| V. Coordinate Across Community | Assess field needs; engage federal partners; facilitate information sharing [70] |
Legal Admissibility Standards
In United States courts, the admissibility of forensic evidence is governed primarily by the Daubert standard, which requires judges to assess whether scientific testimony is based on reliable methodology and valid reasoning [16]. Under Daubert, courts evaluate factors including:
- Testing and falsifiability of the method
- Known or potential error rates
- Peer review and publication
- General acceptance in the relevant scientific community [16] [37]
The Frye standard, which preceded Daubert in many jurisdictions, focused primarily on general acceptance in the relevant scientific community [16]. However, both standards require rigorous validation to ensure forensic evidence meets threshold reliability requirements for admissibility.
Core Validation Parameters and Performance Metrics
Fundamental Validation Parameters
ICH Q2(R2) outlines specific performance characteristics that must be evaluated to demonstrate a method is fit for purpose. The exact parameters depend on the type of method (e.g., identification, quantitative impurity test, limit test) but include these core concepts [69]:
Table: Core Analytical Method Validation Parameters
| Parameter | Definition | Typical Benchmark |
|---|---|---|
| Accuracy | Closeness of test results to true value | Typically ±15% of known value for quantitative assays [69] |
| Precision | Degree of agreement among individual test results | RSD ≤15% for repeatability; ≤20% for intermediate precision [69] |
| Specificity | Ability to assess analyte unequivocally in presence of potential interferents | No interference from blank matrix or similar compounds [69] |
| Linearity | Ability to obtain results proportional to analyte concentration | R² ≥0.98 across specified range [69] |
| Range | Interval between upper and lower analyte concentrations with suitable precision, accuracy, and linearity | Established based on intended use [69] |
| LOD | Lowest amount of analyte that can be detected | Signal-to-noise ratio ≥3:1 [69] |
| LOQ | Lowest amount of analyte that can be quantified with acceptable accuracy and precision | Signal-to-noise ratio ≥10:1 [69] |
| Robustness | Capacity to remain unaffected by small, deliberate variations in method parameters | Maintains accuracy and precision under varied conditions [69] |
Forensic-Specific Performance Metrics
Beyond general analytical validation parameters, forensic methods require additional, discipline-specific metrics:
Interpretation Frameworks The likelihood-ratio framework is increasingly recognized as the logically correct approach for interpreting forensic evidence and expressing its strength [4]. This framework compares the probability of the evidence under two competing propositions (typically prosecution and defense scenarios) and provides a transparent, quantitative measure of evidentiary weight.
Error Rate Quantification The Daubert standard specifically identifies known or potential error rates as a key factor in assessing scientific validity [16] [37]. This requires:
- Empirical measurement of false positive and false negative rates
- Black-box studies to measure accuracy and reliability of forensic examinations
- White-box studies to identify sources of error and human factors [70]
Cognitive Bias Resistance Methods should be designed to minimize contextual and confirmation biases through:
- Sequential unmasking techniques
- Linear sequential examination protocols
- Blind verification procedures [4]
Experimental Protocols and Methodologies
Method Validation Protocol: TD-ESI-MS/MS for Psychoactive Substances in Hair
A recent study demonstrates comprehensive validation of a high-throughput screening method for psychoactive substances in hair matrices, following ANSI/ASB 036 Standard and ICH Q2(R1) guidelines [71]. This dual-platform workflow integrates thermal desorption-electrospray ionization-tandem mass spectrometry (TD-ESI-MS/MS) for rapid screening and ultra-performance liquid chromatography-tandem mass spectrometry (UPLC-MS/MS) for confirmatory quantification.
Experimental Workflow:
Method Validation Parameters and Results:
Table: TD-ESI-MS/MS Method Validation Data for Selected Analytes [71]
| Analyte | LOD (ng/mg) | Linear Range (ng/mg) | Intra-Day Precision (% RSD) | Inter-Day Precision (% RSD) | Matrix Effect (%) |
|---|---|---|---|---|---|
| Etomidate (ETO) | 0.1 | 0.02-12.5 | <15.2 | <16.8 | <12.3 |
| Amphetamine (AMP) | 0.1 | 0.02-12.5 | <14.7 | <16.1 | <10.5 |
| Ketamine (KET) | 0.1 | 0.02-12.5 | <13.9 | <15.3 | <11.8 |
| Cocaine (COC) | 0.1 | 0.02-12.5 | <12.8 | <14.2 | <9.7 |
| Δ9-THC | 0.1 | 0.02-12.5 | <16.3 | <18.1 | <15.2 |
| Tramadol (TRA) | 0.2 | 0.02-12.5 | <17.8 | <19.3 | <16.9 |
The validation study demonstrated acceptable performance across all parameters, with sensitivity exceeding Society of Hair Testing (SoHT) decision thresholds (0.2 ng/mg) for regulated substances. The method achieved an analysis time of approximately 1 minute per sample, enabling high-throughput screening with sensitivity >85.7% and specificity >89.7% for the 17 target analytes [71].
Digital Forensics Validation Protocol
In digital forensics, validation encompasses three critical components [37]:
- Tool Validation: Ensuring forensic software/hardware performs as intended without altering source data
- Method Validation: Confirming procedures produce consistent outcomes across different cases and practitioners
- Analysis Validation: Evaluating whether interpreted data accurately reflects true meaning and context
Core Principles for Digital Forensics Validation:
- Reproducibility: Results must be repeatable by other qualified professionals using the same method
- Transparency: All procedures, software versions, logs, and chain-of-custody records must be documented
- Error Rate Awareness: Methods should have known error rates disclosed in reports and testimony
- Continuous Validation: Regular revalidation required due to rapid technological evolution [37]
Implementation Framework: From Validation to Practice
Lifecycle Approach to Method Validation
The modernized approach to method validation emphasizes continuous lifecycle management rather than one-time validation events [69]. This approach integrates development, validation, and ongoing monitoring through these key stages:
The Scientist's Toolkit: Essential Research Reagent Solutions
Table: Essential Materials and Reagents for Forensic Method Development and Validation
| Item/Category | Function/Purpose | Example Applications |
|---|---|---|
| Certified Reference Materials | Provide traceable, quality-controlled standards for method calibration and accuracy assessment | Quantification of target analytes; establishing calibration curves [71] |
| Blank Matrix Materials | Enable assessment of specificity, selectivity, and matrix effects by providing interferent-free baseline | Method development and validation for biological samples [71] |
| Quality Control Materials | Monitor method performance over time; detect analytical drift or degradation | Ongoing verification of accuracy and precision during sample analysis [71] |
| Sample Preparation Kits | Standardize extraction, purification, and concentration procedures across laboratories | Hair sample decontamination and pulverization; DNA extraction [71] |
| Chromatographic Columns | Separate complex mixtures into individual components for identification and quantification | UPLC-MS/MS analysis of drugs and metabolites in biological samples [71] |
| Mass Spectrometry Reagents | Optimize ionization efficiency and fragmentation patterns for target compounds | Mobile phase preparation for LC-MS/MS; TD-ESI optimization [71] |
Data Interpretation and Reporting Frameworks
Effective implementation of validated methods requires standardized approaches to data interpretation and reporting. The forensic-data-science paradigm emphasizes methods that are [4]:
- Transparent and reproducible
- Intrinsically resistant to cognitive bias
- Based on the logically correct framework for interpretation (likelihood-ratio framework)
- Empirically calibrated and validated under casework conditions
ISO 21043 provides specific guidance on vocabulary, interpretation, and reporting to ensure consistency and clarity in communicating forensic findings [4]. This includes standard methods for expressing the weight of evidence using likelihood ratios or verbal scales, and evaluation of expanded conclusion scales beyond simple identification or exclusion [70].
Establishing benchmarks for objective evidence and performance metrics in forensic science requires a systematic, lifecycle approach that integrates global regulatory standards, scientific rigor, and practical implementation frameworks. By adopting the principles outlined in ICH Q2(R2) and Q14, ISO 21043, and the NIJ Strategic Research Plan, forensic researchers and drug development professionals can develop methods that not only meet analytical performance standards but also withstand legal scrutiny under Daubert and related admissibility standards.
The future of forensic method validation will increasingly emphasize transparency, reproducibility, and quantitative expression of evidentiary weight. As the field continues to evolve in response to the NRC and PCAST critiques, the integration of advanced technologies—from high-resolution mass spectrometry to artificial intelligence—must be accompanied by robust validation frameworks that ensure reliability while acknowledging limitations. Through continued collaboration between researchers, practitioners, standard-setting organizations, and the legal community, forensic science can strengthen its scientific foundation and enhance its contribution to the justice system.
The integration of Artificial Intelligence (AI) and Machine Learning (ML) is fundamentally reshaping the paradigm for defining end-user requirements in forensic method validation research. This transformation moves beyond mere automation, demanding new validation frameworks that address the unique characteristics of AI-driven methodologies. For forensic researchers and drug development professionals, this evolution necessitates a rigorous, forward-looking approach to requirement definition that ensures scientific validity, reproducibility, and forensic integrity while leveraging the unprecedented analytical power of AI [72] [73]. The core challenge lies in defining requirements not just for the forensic output, but for the entire AI lifecycle—from data curation and model training to performance benchmarking and operational deployment. This technical guide delineates the critical impact of AI and ML on these requirement definitions, providing structured data, experimental protocols, and visualization tools essential for developing robust, validated forensic AI systems.
AI-Driven Shifts in Validation Requirement Definition
The adoption of AI in forensic science necessitates a critical evolution in how end-user requirements are defined for method validation. The following table summarizes the core shifts from traditional to AI-centric requirement definitions.
Table 1: Evolution of Key Requirement Definitions in Forensic Method Validation
| Requirement Domain | Traditional Focus | AI-Driven Focus & New Requirements |
|---|---|---|
| Accuracy & Precision | Determined through repeated runs of a standardized protocol on reference materials [74]. | Must include model performance metrics (e.g., F1-score, AUC-ROC) on held-out test sets, along with robustness testing against data drift and adversarial examples [75] [73]. |
| Reproducibility | Focus on inter-operator and inter-laboratory consistency using the same method [74]. | Expanded to include computational reproducibility: consistent outputs from the same data and model, requiring detailed documentation of software environment, random seeds, and version control [76]. |
| Explainability & Transparency | Based on a clear, documented chain of analytical steps and expert interpretation [77]. | Requires "explainable AI" (XAI) techniques. The model's decision-making process must be interpretable and defensible in court, moving beyond "black box" predictions [76] [75]. |
| Specificity & Selectivity | Validated against known interferents and complex mixtures in controlled experiments [74]. | Requires rigorous testing on diverse, real-world datasets to demonstrate performance across different populations, evidence types, and conditions. Must proactively address algorithmic bias [72] [76]. |
| Limits of Detection | Defined by signal-to-noise ratios in analytical instrumentation [74]. | Translated into probabilistic frameworks. Requirements must define the confidence thresholds for a positive identification and the minimum data quality/quantity for reliable model inference [74] [73]. |
Defining Requirements for Core Forensic AI Applications
DNA Analysis and Probabilistic Genotyping
AI and ML, particularly deep learning networks, are revolutionizing forensic DNA analysis by interpreting complex mixed DNA samples that challenge traditional methods [74]. Key requirement definitions must encompass:
- Data Requirements: Specification of training data must include volume, diversity of DNA mixtures (number of contributors, degradation levels, stutter ratios), and allele frequency representation across populations to ensure a robust model [74] [73].
- Performance Requirements: Validation must demonstrate that the AI system meets or exceeds the accuracy of current probabilistic genotyping software (PGS) and human experts, with defined confidence intervals for Likelihood Ratio (LR) outputs [74].
- Validation Protocol: A key experiment for validating an AI-based DNA mixture interpreter is summarized below.
Table 2: Experimental Protocol for Validating AI-Based DNA Mixture Interpretation
| Protocol Component | Detailed Specification |
|---|---|
| Aim | To benchmark the accuracy, reproducibility, and sensitivity of a novel AI model (e.g., a Convolutional Neural Network) for determining the number of contributors (NoC) in complex DNA mixtures against established methods. |
| Materials & Inputs | - Sample Set: In silico and laboratory-generated DNA mixtures (2-5 contributors) with varying DNA template amounts (0.1-2.0 ng), degradation indices (DIs from 1 to 50), and known ground-truth profiles.- Control: Standard capillary electrophoresis (CE) data processed with conventional PGS. |
| Methodology | 1. Data Preprocessing: Raw electropherograms (EPGs) are normalized, baseline-corrected, and encoded into a structured input tensor.2. Model Training & Tuning: The CNN is trained on a subset of data. Hyperparameters (learning rate, network depth) are optimized via cross-validation.3. Blinded Testing: The finalized model predicts the NoC and contributor profiles on a held-out test set. Results are compared to ground truth and PGS outputs.4. Sensitivity Analysis: Model performance is assessed as a function of input DNA quantity and quality. |
| Key Metrics | - NoC Assignment Accuracy (%)- LR Calibration and Discrimination (Log-Loss, AUC)- Computational Time per Sample (seconds) |
| Validation Criteria | The AI model must achieve >95% NoC accuracy on 2-4 person mixtures and demonstrate non-inferiority to existing PGS in LR reliability for single-source and simple mixtures. |
Digital Evidence and Computer Vision
In digital forensics, AI requirements must focus on scalability and analytical depth. For computer vision applications in traumatic injury analysis, requirement definition shifts towards quantitative image interpretation [75].
- Scalability Requirements: Systems must process and analyze terabyte-scale datasets from diverse sources (e.g., hard drives, cloud storage, video footage) within forensically relevant timeframes [77].
- Feature Extraction Requirements: Models must be validated for their ability to accurately detect, segment, and classify specific forensic patterns—such as wound morphology in images—with high pixel-level accuracy (>90% for clearly defined wounds like stab injuries) [75].
Pattern, Trace Evidence, and Toxicological Analysis
AI applications in pattern recognition (e.g., fingerprints, toolmarks) and toxicology require a stringent focus on minimizing bias and ensuring explainability.
- Bias Mitigation Requirements: Defined requirements must mandate that models are trained on demographically representative datasets and are continuously monitored for performance disparities across different groups [76]. For instance, the Department of Justice (DOJ) emphasizes rigorous testing for accuracy and potential biases [76].
- Explainability Requirements: For court admissibility, a requirement must be set that any AI-based pattern matching system provides a human-interpretable rationale for its conclusions, such as highlighting corresponding feature points rather than just a similarity score [76] [77].
The Scientist's Toolkit: Key Reagents and Materials for AI Validation
Developing and validating AI-based forensic methods requires a suite of computational and data "reagents." The following table details these essential components.
Table 3: Research Reagent Solutions for AI Forensic Method Development
| Item | Function in Development & Validation |
|---|---|
| Curated Benchmark Datasets | Serves as the ground-truth standard for training and blind-testing AI models. Must be representative, annotated by multiple experts, and encompass a wide range of scenarios (e.g., various DNA mixture ratios, image qualities) [75] [73]. |
| Synthetic Data Generators | Provides augmented or simulated data (e.g., using Generative Adversarial Networks - GANs) to increase training set size and diversity, test model robustness to rare events, and address class imbalances [74]. |
| Model Architectures (e.g., CNN, RNN) | Pre-defined, modular neural network designs serve as the core analytical engine for specific data types (CNNs for images/EPGs, RNNs for sequential data) [73]. |
| Explainability AI (XAI) Libraries | Software tools (e.g., SHAP, LIME) used to fulfill the explainability requirement by generating visualizations and metrics that interpret the model's decision-making process [76]. |
| Performance Metric Suites | A standardized collection of software functions for calculating validation metrics (e.g., accuracy, precision, recall, F1-score, AUC, calibration plots) to objectively benchmark model performance [74] [73]. |
| Version Control Systems (e.g., Git) | Essential for maintaining reproducibility requirements by tracking every change in code, model parameters, and training data throughout the experimental lifecycle [76]. |
Workflow Visualization for AI Method Validation
The following diagram illustrates the integrated, iterative workflow for defining requirements and validating AI-based forensic methods, highlighting the critical feedback loops.
The validation of specific AI models, such as those for DNA profiling, follows a more granular technical process. The diagram below details this protocol from data preparation to final validation.
The impact of AI and ML on requirement definition for forensic method validation is profound and enduring. Success in this new era demands that researchers and protocol designers explicitly define requirements for data quality, computational reproducibility, model explainability, and bias mitigation from the outset. The frameworks, protocols, and toolkits outlined in this guide provide a foundational roadmap for embedding these AI-centric considerations into the bedrock of forensic research and development. As AI technologies continue to evolve—with trends like agentic AI and quantum computing on the horizon [78]—the processes for defining validation requirements must remain agile and forward-looking. By adopting these structured approaches, the forensic science community can harness the power of AI to enhance analytical capabilities while steadfastly upholding the highest standards of scientific rigor and justice.
Conclusion
Defining precise end-user requirements is not a preliminary step but the foundational pillar of a scientifically defensible and legally robust forensic method validation. This synthesis of core intents demonstrates that success hinges on a clear, documented process that captures stakeholder needs, translates them into testable acceptance criteria, and proactively addresses implementation challenges through risk assessment and collaborative models. For biomedical and clinical research, these principles are directly transferable, ensuring that developed methods are not only technically sound but also truly fit for their intended diagnostic or analytical purpose. Future progress depends on standardizing requirement specifications across organizations, enhancing training for practitioners in validation science, and developing agile frameworks that can keep pace with rapidly advancing technologies like AI and complex instrumentation.
References
- 1. Method validation in digital forensics (accessible) [https://www.gov.uk/government/publications/method-validation-in-digital-forensics/method-validation-in-digital-forensics-accessible]
- 2. [Withdrawn] Draft statutory Code version 2 (accessible) - GOV.UK [https://www.gov.uk/government/publications/forensic-science-regulator-draft-statutory-code-v2-for-comment/draft-statutory-code-version-2-accessible]
- 3. Quality management system in forensic : An African... science [https://pmc.ncbi.nlm.nih.gov/articles/PMC11070588/]
- 4. A guide to ISO 21043 Forensic Sciences from the ... [https://www.sciencedirect.com/science/article/pii/S1355030625000887]
- 5. Why validate? - RELI [https://www.reliresearch.co.uk/blog/blog-post-why-validate]
- 6. Collaborative versus traditional method validation approach [https://pmc.ncbi.nlm.nih.gov/articles/PMC7452674/]
- 7. Validation | FCN [http://www.fcn.police.uk/what-we-do/validation]
- 8. Comprehensive Guide to ISO/IEC 17025 Accreditation ... [https://www.labmanager.com/comprehensive-guide-to-iso-iec-17025-accreditation-prep-for-forensic-labs-34639]
- 9. ISO 17025 Compliance Requirements for Labs [https://www.1lims.com/blog/iso-17025-compliance-requirements-for-labs]
- 10. ISO 17025 – Main guidelines [https://advisera.com/17025academy/what-is-iso-17025/]
- 11. Transparent reporting in forensic Science: Exploring its ... [https://www.sciencedirect.com/science/article/pii/S2589871X25000592]
- 12. Top 6 Visualizations for Quantitative Data Analysis Methods [https://chartexpo.com/blog/quantitative-data-analysis-methods]
- 13. Data Analysis and Visualization - Research ... [https://guides.library.txstate.edu/research-data/analysis-visualization]
- 14. 2025 Conference Agenda [https://www.nafsb.org/2025-conference-agenda]
- 15. Guideline for the Validation of Forensic Science Methods [https://www.anzpaa.org.au/products/products/guideline-for-the-validation-of-forensic-science-methods]
- 16. The admissibility of forensic evidence in US courts and ... [https://www.sciencedirect.com/science/article/abs/pii/S135503062500139X]
- 17. Probabilistic reporting and algorithms in forensic science [https://pmc.ncbi.nlm.nih.gov/articles/PMC8850671/]
- 18. Safeguarding Forensic Science Professionals [https://nij.ojp.gov/topics/articles/safeguarding-forensic-science-professionals]
- 19. What are User Needs? — updated 2025 | IxDF [https://www.interaction-design.org/literature/topics/user-needs?srsltid=AfmBOoonKFYssZljeXM0ESpDong6bgSxBT4DvaWtCUvb0tT46vBHa9td]
- 20. User Need Statements: The 'Define' Stage in Design Thinking [https://www.nngroup.com/articles/user-need-statements/]
- 21. Comprehensive Guide to User Requirements for Software ... [https://qat.com/guide-user-requirements/]
- 22. 14 Comparing quantitative data between individuals [https://bookdown.org/pkaldunn/SRM-Textbook/BetweenQuantData.html]
- 23. The Legal Implications of Inadequate Risk Mitigation | SBN [https://sbnsoftware.com/blog/what-are-the-legal-implications-of-inadequate-risk-mitigation/]
- 24. Understanding The Consequences Of Non-Compliance [https://financialcrimeacademy.org/consequences-of-non-compliance/]
- 25. List of Common Legal Risks (Complete Guide) [https://www.metricstream.com/learn/legal-risk.html]
- 26. Digital Forensic Validation: Principles, Methods, and ... [https://www.linkedin.com/pulse/digital-forensic-validation-principles-methods-examples-james-henning-xbjye]
- 27. Statistical Perspectives on Reproducibility: Definitions and ... [https://link.springer.com/article/10.1007/s42519-025-00459-x]
- 28. An Overview of Scientific Reproducibility - PubMed Central - NIH [https://pmc.ncbi.nlm.nih.gov/articles/PMC6701706/]
- 29. Validation and Reference Materials for Microbial Forensics [https://www.ncbi.nlm.nih.gov/books/NBK234870/]
- 30. How to Define User Needs During Design Controls [https://www.greenlight.guru/blog/user-needs-design-controls]
- 31. Collection of End User Requirements and Use Cases ... [https://www.mdpi.com/2078-2489/13/5/255]
- 32. User Needs vs Requirements [https://innolitics.com/articles/user-needs-vs-requirements/]
- 33. Criteria for Validation of Methods in Microbial Forensics [https://pmc.ncbi.nlm.nih.gov/articles/PMC2547046/]
- 34. Functional and Non Functional Requirements [https://www.geeksforgeeks.org/software-engineering/functional-vs-non-functional-requirements/]
- 35. Functional vs Non-Functional Requirements [https://www.ironhack.com/us/blog/functional-vs-non-functional-requirements-understanding-the-core-differences-and]
- 36. What Is Validation? | Thermo Fisher Scientific - US [https://www.thermofisher.com/us/en/home/industrial/forensics/human-identification/forensic-dna-analysis/forensic-dna-data-interpretation/valid-validation-software/what-is-validation.html]
- 37. What is forensic validation and how is it used? [https://www.envistaforensics.com/knowledge-center/insights/articles/forensic-validation-pay-attention-to-the-man-behind-the-curtain/]
- 38. Specification-driven acceptance criteria for validation of ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9537461/]
- 39. Establishing Acceptance Criteria for Analytical Methods [https://www.biopharminternational.com/view/establishing-acceptance-criteria-analytical-methods]
- 40. Quantitative matching of forensic evidence fragments using ... [https://www.nature.com/articles/s41467-024-51594-1]
- 41. Understanding the anatomy and proper construction of tables [https://www.decisionfoundry.com/misc/articles/understanding-the-anatomy-and-proper-construction-of-tables/]
- 42. APA Tables and Figures - Purdue OWL [https://owl.purdue.edu/owl/research_and_citation/apa_style/apa_formatting_and_style_guide/apa_tables_and_figures.html]
- 43. Data Table Design UX Patterns & Best Practices [https://www.pencilandpaper.io/articles/ux-pattern-analysis-enterprise-data-tables]
- 44. Text has enhanced contrast | ACT Rule | WAI [https://www.w3.org/WAI/standards-guidelines/act/rules/09o5cg/]
- 45. Color contrast - Accessibility - MDN Web Docs - Mozilla [https://developer.mozilla.org/en-US/docs/Web/Accessibility/Guides/Understanding_WCAG/Perceivable/Color_contrast]
- 46. Contrast Checker [https://webaim.org/resources/contrastchecker/]
- 47. Equipment Validation Protocol | Step by Step Writing Guide [https://www.getreskilled.com/validation/validation-protocol/]
- 48. Accredited Forensics Laboratories Are Not Properly ... [https://www.chromatographyonline.com/view/accredited-forensics-laboratories-are-not-properly-validating-and-controlling-their-blood-alcohol-determination-methods]
- 49. The Hidden Risks in Analytical Method Validation - [https://pharmuni.com/2025/05/16/the-hidden-risks-in-analytical-method-validation/]
- 50. Avoiding Critical Mistakes in Forensic Audits [https://www.linkedin.com/pulse/avoiding-critical-mistakes-forensic-audits-best-2025-singh-ph-d-4saef]
- 51. Method Validation vs Method Verification: Which is Better ... [https://www.labmanager.com/method-validation-vs-method-verification-which-is-better-for-use-in-laboratories-33982]
- 52. Standard Practices for Method Validation in Forensic ... [https://www.aafs.org/asb-standard/standard-practices-method-validation-forensic-toxicology]
- 53. Requirements Verification and Validation for Product Teams [https://www.jamasoftware.com/requirements-management-guide/requirements-validation-and-verification/requirements-verification-and-validation-for-product-teams/]
- 54. Quantitative Data Analysis Methods & Techniques 101 [https://gradcoach.com/quantitative-data-analysis-methods/]
- 55. Quantitative Data Analysis. A Complete Guide [2025] [https://www.6sigma.us/six-sigma-in-focus/quantitative-data-analysis/]
- 56. Quantitative Data Analysis: A Comprehensive Guide [https://hevodata.com/learn/quantitative-data-analysis/]
- 57. Requirements Validation Techniques - Software Engineering [https://www.geeksforgeeks.org/software-engineering/software-engineering-requirements-validation-techniques/]
- 58. Requirement validation: Benefits & Best Practices [https://testsigma.com/blog/requirement-validation/]
- 59. Robust statistical methods for high-dimensional data, with ... [https://www.sciencedirect.com/science/article/pii/S0003267023009832]
- 60. Scientific guidelines for evaluating the validity of forensic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10576079/]
- 61. Perspective on the Future of Requirements Management ... [https://medium.com/@chameleon13/perspective-on-the-future-of-requirements-management-next-5-years-fbcc5b801441]
- 62. Utilizing tables, figures, charts and graphs to enhance the ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10394528/]
- 63. Defining end user requirements for a field-based molecular ... [https://www.sciencedirect.com/science/article/pii/S0379073819302257]
- 64. Update of Standard Practices for New Method Validation ... [https://db.cngb.org/data_resources/literature/28714407]
- 65. Scientific Considerations in Demonstrating Biosimilarity to ... [https://www.fda.gov/regulatory-information/search-fda-guidance-documents/scientific-considerations-demonstrating-biosimilarity-reference-product-updated-recommendations]
- 66. FDA Issues Draft Guidance with Updated ... [https://www.akingump.com/en/insights/blogs/eye-on-fda/fda-issues-draft-guidance-with-updated-recommendations-for-assessing-the-need-for-comparative-efficacy-studies-in-biosimilar-development]
- 67. FDA Proposes To Eliminate Comparative Clinical ... [https://www.arnoldporter.com/en/perspectives/advisories/2025/11/fda-proposes-to-eliminate-biosimilar-comparative-studies]
- 68. FDA rethinks need for comparative efficacy studies ... [https://www.hoganlovells.com/en/publications/fda-rethinks-need-for-comparative-efficacy-studies-for-certain-biosimilars]
- 69. ICH and FDA Guidelines for Analytical Method Validation [https://www.labmanager.com/ich-and-fda-guidelines-for-analytical-method-validation-34252]
- 70. Forensic Science Strategic Research Plan, 2022-2026 ... [https://nij.ojp.gov/topics/articles/forensic-sciences-strategic-research-plan-2022-2026]
- 71. TD-ESI-MS/MS for High-Throughput Screening of 13 ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12116117/]
- 72. The future of forensics: How AI can transform investigations [https://washingtondc.jhu.edu/news/ai-in-forensics/]
- 73. Artificial Intelligence in Forensic Sciences: A Systematic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11513614/]
- 74. Machine learning applications in forensic DNA profiling [https://www.sciencedirect.com/science/article/pii/S1872497323001692]
- 75. Artificial intelligence and computer vision in forensic sciences [https://link.springer.com/article/10.1007/s00194-025-00775-3]
- 76. DOJ Report on AI in Criminal Justice: Key Takeaways [https://counciloncj.org/doj-report-on-ai-in-criminal-justice-key-takeaways/]
- 77. The Role of AI in Forensics [https://marymount.edu/blog/the-role-of-ai-in-forensics/]
- 78. The future of AI: trends shaping the next 10 years [https://www.ibm.com/think/insights/artificial-intelligence-future]