Cross-Topic Authorship Verification: Experimental Protocols for Robust and Clinically Relevant Biomarker Development
This article provides a comprehensive framework for designing and implementing cross-topic authorship verification experimental protocols, tailored for biomedical and clinical research audiences.
Cross-Topic Authorship Verification: Experimental Protocols for Robust and Clinically Relevant Biomarker Development
Abstract
This article provides a comprehensive framework for designing and implementing cross-topic authorship verification experimental protocols, tailored for biomedical and clinical research audiences. We explore the foundational principles of authorship verification, detailing how stylistic and semantic features can function as unique 'biomarkers' of writing. The piece offers practical methodologies for feature extraction and model architecture, including advanced neural networks like Siamese and Feature Interaction Networks. It addresses critical challenges such as topic leakage and dataset bias, presenting optimization strategies like the HITS sampling method. Finally, we establish validation frameworks and comparative analyses of state-of-the-art models, culminating in a discussion of the profound implications for research integrity, pharmacovigilance, and clinical documentation in the pharmaceutical and drug development sectors.
Understanding Authorship Verification: From Writing Style as a Digital Biomarker to Cross-Topic Challenges
Defining Authorship Verification and Its Core Task in Textual Analysis
Authorship Verification is a fundamental task in computational linguistics and digital text forensics. It is defined as the process of analyzing a set of documents to determine whether they were written by a specific author [1]. In its most common form, the task addresses the following problem: given a set of documents known to be written by an author and a document of doubtful attribution to that author, the verification system must decide whether that document was truly written by that author [2]. This process relies on stylometry—the statistical analysis of linguistic style—to quantify an author's unique writing patterns into a measurable "fingerprint" for comparison [3].
The core task distinguishes itself from related authorship analysis problems through its specific decision structure. Unlike authorship attribution, which seeks to identify the most likely author from a set of candidates, verification presents a binary decision regarding a single candidate author [4]. This functionality is essential for applications where the question is not "who wrote this?" but rather "did this specific person write this?"—a scenario frequently encountered in forensic, academic, and cybersecurity contexts [1] [3].
Core Tasks and Decision Problems
Authorship verification addresses three principal decision problems, each tailored to different evidential scenarios [1]:
AV_Core: This is the fundamental decision problem. Given two documents,D1andD2, the task is to determine whether both were written by the same author. This setup is symmetric and does not require pre-existing author profiles.AV_Known: This common forensic scenario involves a set of documentsD_A = {D1, D2, ...}known to be written by authorA, and a documentD_Uof unknown authorship. The system must determine whetherAalso wroteD_U(aY-case), or if it was written by a different author (¬A, anN-case).AV_Batch: This problem extends the verification to sets of documents. Given two sets,D_AandD_B, each containing documents written by a single author, the task is to decide whether both sets were written by the same author.
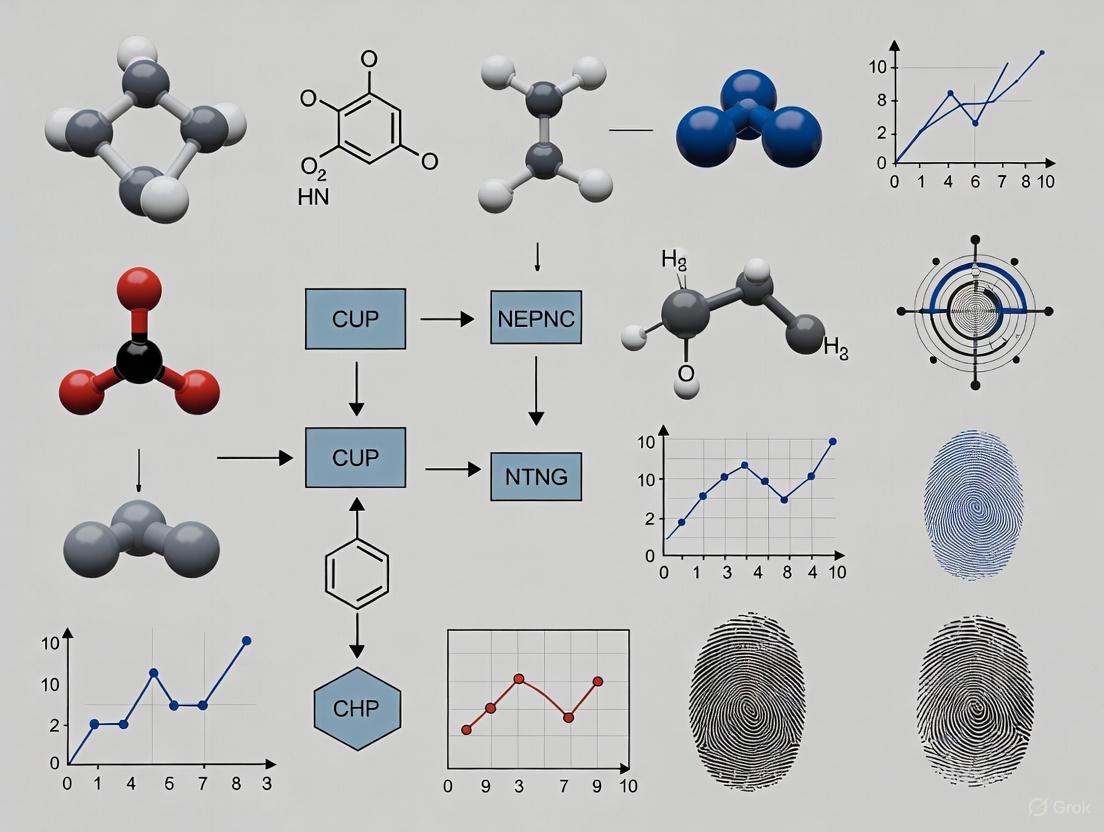
The following workflow generalizes the process for addressing these verification problems, particularly the AV_Known scenario:
Critical Methodologies and Feature Engineering
Linguistic Feature Categories
The effectiveness of authorship verification hinges on the extraction and analysis of linguistic features that capture an author's unique stylistic signature. These features are broadly categorized as follows:
Table 1: Categories of Linguistic Features for Authorship Verification
| Feature Category | Description | Specific Examples | Performance Notes |
|---|---|---|---|
| Lexical Features [2] | Analyze word-level choices and patterns | Word n-grams, word frequency, word-length distribution [5] [4] | Lower individualization for Classical Arabic [2] |
| Syntactic Features [2] | Capture sentence structure and grammar | POS (Part-of-Speech) distributions, syntactic n-grams, sentence length [5] [4] | High discriminative power; core of grammar models [2] [1] |
| Morphological Features [2] | Examine word formation and structure | Character n-grams, suffixes/prefixes | Lower individualization for Classical Arabic [2] |
| Semantic Features [5] | Relate to meaning and topic | RoBERTa embeddings, topic models [5] | Risk of topic bias; requires control [6] |
Advanced Computational Models
Recent research has developed sophisticated models that integrate multiple feature types to improve verification accuracy:
Feature-Integrated Deep Learning Models: These include architectures like the Feature Interaction Network, Pairwise Concatenation Network, and Siamese Network, which combine RoBERTa embeddings (semantic features) with stylistic features such as sentence length and punctuation to enhance performance [5].
Grammar Model Likelihood Ratio (LambdaG): This method calculates the ratio (
λG) between the likelihood of a document given a model of the candidate author's grammar and the likelihood given a model of a reference population's grammar. The grammar models are estimated using n-gram language models trained solely on grammatical features, making the approach particularly robust and interpretable [1].LLM-Based Style Transfer (OSST Score): A novel unsupervised approach leverages the causal language modeling (CLM) pre-training of Large Language Models (LLMs). It uses an LLM's log-probabilities to measure style transferability between texts, providing a powerful metric for verification without requiring supervised training [4].
The LambdaG method, which has demonstrated state-of-the-art performance, can be visualized as follows:
Experimental Protocols for Cross-Topic Authorship Verification
A primary challenge in authorship verification is ensuring models rely on genuine stylistic patterns rather than topical cues. The following protocol provides a framework for robust, cross-topic evaluation.
Protocol 1: Cross-Topic Evaluation with HITS
Objective: To evaluate and benchmark authorship verification models under conditions that minimize the confounding effect of topic leakage.
Background: Conventional cross-topic evaluations assume minimal topic overlap between training and test data, but topic leakage—where topics from the test set are represented in the training set—can lead to misleading performance and unstable model rankings [6] [7].
Materials:
- PAN Datasets: Standardized datasets from PAN competitions, which include fanfiction, essays, emails, and social media posts [8] [4].
- RAVEN Benchmark: The Robust Authorship Verification bENchmark, designed specifically for topic shortcut testing [6] [7].
- HITS Script: Implementation of the Heterogeneity-Informed Topic Sampling procedure.
Procedure:
- Topic Annotation: Manually or automatically annotate all documents in the corpus with topic labels.
- HITS Sampling: Apply Heterogeneity-Informed Topic Sampling (HITS) to create evaluation splits [6]. This involves:
- Identifying all topics present in the corpus.
- Sampling a heterogeneous set of topics to ensure the test set contains a balanced and diverse topic distribution that is distinct from the training/development sets.
- Model Training: Train the AV models (e.g., Siamese Networks, LambdaG, OSST) on the training split, which contains a specific set of topics.
- Model Testing: Evaluate the trained models on the HITS-sampled test set, which contains a different, heterogeneously distributed set of topics.
- Metric Calculation: Calculate standard performance metrics, including Accuracy and Area Under the Curve (AUC).
- Robustness Analysis: Analyze the stability of model rankings across multiple random seeds and HITS-generated splits to ensure performance is not dependent on a favorable topic alignment.
Validation: A valid cross-topic evaluation will show a stable ranking of models across different HITS-sampled splits and will typically reveal a performance drop for models that are overly reliant on semantic/topic features [6].
The Scientist's Toolkit: Key Research Reagents
Table 2: Essential Materials and Resources for Authorship Verification Research
| Resource Name | Type | Function in Research | Key Characteristics |
|---|---|---|---|
| PAN Datasets [8] [4] | Data Corpus | Provides standardized benchmarks for training and evaluating AV models. | Includes diverse genres (fanfiction, essays, emails, social media); central to modern AV research. |
| Enron Email Dataset [3] | Data Corpus | Serves as a rich source of genuine, multi-author text for building author profiles. | Contains >600k emails from 158 authors; provides "ground truth" for known authors. |
| Blog Authorship Corpus [3] | Data Corpus | Enables testing of AV models on long-form, multi-topic texts from many authors. | Contains over 600 authors and 300,000 posts; high topic diversity. |
| RoBERTa Model [5] | Computational Model | Provides deep contextualized semantic embeddings for text. | Transformer-based; used to capture semantic features in feature-integrated models. |
| HITS (Heterogeneity-Informed Topic Sampling) [6] [7] | Methodology | Creates evaluation splits with controlled topic distribution to minimize topic leakage. | Improves stability of model rankings; crucial for rigorous cross-topic evaluation. |
| LambdaG Algorithm [1] | Algorithm | Computes the likelihood ratio for verification based on grammatical models. | High accuracy and AUC; robust to genre variations; more interpretable than deep learning models. |
| OSST Score Algorithm [4] | Algorithm | Provides an unsupervised, LLM-based metric for authorship by measuring style transferability. | Zero-shot capability; performance scales with base LLM size. |
Quantitative Performance Comparison
Empirical evaluations across multiple datasets and against various baseline methods provide a clear picture of the relative performance of modern AV approaches.
Table 3: Comparative Performance of Authorship Verification Methods
| Methodology | Key Features | Reported Accuracy/AUC | Strengths and Limitations |
|---|---|---|---|
| LambdaG (Grammar Model) [1] | Likelihood ratio of author-specific vs. population grammar models (n-grams). | Outperformed baselines in 11 out of 12 datasets in terms of accuracy and AUC. | Strengths: High accuracy; robust to genre variation; interpretable. Limitations: Requires a representative reference population. |
| Feature-Integrated Deep Models [5] | Combination of RoBERTa (semantics) and style features (punctuation, sentence length). | Consistently improved over semantic-only models; competitive on challenging datasets. | Strengths: Leverages both style and deep semantics. Limitations: Requires careful feature engineering; performance can be sensitive to dataset. |
| Siamese Network [5] | Deep learning model that learns similarity between text pairs. | Competitive results, but can be outperformed by LambdaG [1]. | Strengths: Effective at capturing complex stylistic similarities. Limitations: Can be computationally complex; less interpretable. |
| LLM One-Shot Style Transfer (OSST) [4] | Unsupervised method using LLM log-probabilities to measure style transfer. | Higher accuracy than contrastively trained baselines when controlling for topic. | Strengths: Zero-shot capability; no training data needed. Limitations: Performance and cost depend on underlying LLM size. |
| Traditional Feature Ensemble [2] | Ensemble of lexical, morphological, and syntactic features. | 87.1% accuracy on corpus of 31 Classical Arabic books. | Strengths: Effective with specific feature combinations. Limitations: Performance varies significantly by feature category and language. |
The validation of authorship verification (AV) systems requires methodologies that can distinguish an author's unique writing style from topic-specific content. This application note proposes a framework that treats semantic and stylometric features as discriminative biomarkers, adapting rigorous validation principles from biomedical sciences [9] [10] [11] to computational linguistics. We detail experimental protocols designed to address the critical challenge of topic leakage [12] [13], which can lead to misleading performance metrics and unstable model rankings. By introducing the Heterogeneity-Informed Topic Sampling (HITS) method [12] [13] and leveraging large-scale, cross-domain corpora like the Million Authors Corpus [14], we provide a pathway for developing robust, cross-topic AV systems with validated probative value for forensic applications [15].
In forensic science, the statistical analysis of writing style, or stylometry, is founded on the principle that every individual possesses a distinct, albeit variable, writing style [15]. The central challenge in modern authorship verification is to build models that recognize this stylistic "biomarker" independent of the text's topic. A model that fails to do so may rely on spurious correlations between topic-specific keywords and authors, rather than genuine stylistic patterns [12]. This is analogous to a clinical biomarker test that confuses a correlated symptom with the underlying disease state [9] [11]. The phenomenon of topic leakage—where test data unintentionally contains topical information similar to training data—has been shown to inflate performance and compromise the evaluation of an AV system's true robustness [12] [13]. This note outlines a protocol for the discovery and validation of stylometric biomarkers, ensuring they are diagnostically specific to author identity.
Biomarker Discovery: Feature Extraction and Rationale
The first step in the AV pipeline is the selection and extraction of features that serve as potential authorship biomarkers. These features can be categorized as either individual characteristics, specific to an author, or class characteristics, common to a broader population [15].
- Lexical-Syntactic Biomarkers: These include features such as:
- Function Word Frequencies: The usage rates of words like "the," "and," "of," which are largely employed unconsciously and are resistant to topic influence [15].
- Character N-Grams: Sub-word sequences that capture idiosyncratic spelling, hyphenation, or morphological preferences [15].
- Syntax Tree Structures: Patterns in sentence construction and grammar.
- Semantic Biomarkers: These features capture content-related choices that may still be style-indicative, such as:
The rationale for biomarker selection must be pre-specified, and the analytical validity of the feature extraction process must be ensured through standardized, reproducible scripts [10].
Experimental Protocol for Cross-Topic Validation
A critical phase in validating authorship biomarkers is assessing their performance under a strict cross-topic regimen. The following protocol mitigates the risk of topic leakage.
Protocol: Heterogeneity-Informed Topic Sampling (HITS)
Objective: To create evaluation datasets with topically heterogeneous splits, thereby reducing topic leakage and enabling a more reliable assessment of model robustness [12] [13].
Materials:
- A source corpus with topic annotations for documents (e.g., fanfiction datasets from PAN competitions [12] or the Million Authors Corpus [14]).
- Computing environment with standard machine learning libraries (e.g., scikit-learn) and SentenceBERT models for generating topic representations.
Procedure:
- Topic Representation: For each topic category in the source corpus, calculate a vector representation by averaging the SentenceBERT embeddings of all documents belonging to that topic [13].
- Initialization: Start with an empty set
Sfor selected topics. Choose the first topic as the one with the highest average pairwise similarity to all other topics. Remove it from the candidate pool and add it toS. - Iterative Selection: While the number of selected topics is less than the desired sample size (k):
a. For each topic in the candidate pool, calculate its minimum similarity to any topic already in
S. b. Select the candidate topic with the largest minimum similarity (i.e., the most distinct from all already-selected topics). c. Add this topic toSand remove it from the candidate pool. - Dataset Construction: Populate the final dataset using documents only from the selected heterogeneous topic set
S. Perform a train-test split ensuring that no topic in the training set is present in the test set.
Validation: The success of HITS can be measured by the increased stability of model rankings across different random seeds and evaluation splits compared to conventional random sampling [12].
Workflow: Cross-Topic Authorship Verification
The following diagram illustrates the complete experimental workflow for cross-topic authorship verification, integrating the HITS protocol.
The Scientist's Toolkit: Research Reagent Solutions
The following table details key resources essential for conducting rigorous cross-topic authorship verification studies.
Table 1: Essential Research Reagents for Authorship Verification
| Research Reagent | Function & Description | Exemplars |
|---|---|---|
| Cross-Topic Benchmarks | Provides a controlled environment for evaluating model robustness against topic shifts by ensuring training and test sets are topically distinct. | RAVEN benchmark [12], PAN Fanfiction dataset [12] |
| Large-Scale Multi-Domain Corpora | Enables large-scale training and cross-domain ablation studies to test generalizability across vastly different writing contexts. | Million Authors Corpus (MAC) [14] |
| Stylometric Feature Extractors | Software libraries for quantifying an author's unconscious writing style, transforming text into analyzable biomarkers. | N-gram counters, function word lists, syntactic parsers [15] |
| Topic-Representation Models | Generates semantic vector representations for topics, which is a prerequisite for executing the HITS sampling protocol. | SentenceBERT models [13] |
| Validation & Analysis Suites | Provides statistical tools to control for multiple comparisons, assess within-subject correlation, and compute robust performance metrics. | Mixed-effects models, False Discovery Rate (FDR) control [11] |
Validation Metrics and Data Analysis
Interpreting the results of a cross-topic AV experiment requires careful statistical analysis to avoid false discoveries and ensure findings are reproducible [11].
Key Performance Metrics
Performance should be reported using multiple metrics to provide a comprehensive view of model capability. The following table summarizes the core metrics used in biomarker validation.
Table 2: Key Statistical Metrics for Biomarker Validation [9] [16]
| Metric | Formula / Description | Interpretation in AV Context |
|---|---|---|
| Sensitivity (Recall) | True Positives / (True Positives + False Negatives) | The proportion of same-author text pairs correctly identified. |
| Specificity | True Negatives / (True Negatives + False Positives) | The proportion of different-author text pairs correctly identified. |
| Area Under the Curve (AUC) | Area under the Receiver Operating Characteristic (ROC) curve. | Overall measure of how well the model distinguishes between same-author and different-author pairs, across all classification thresholds. A value of 0.5 is no better than chance. |
| Positive Predictive Value (Precision) | True Positives / (True Positives + False Positives) | The probability that a text pair predicted to be from the same author is truly from the same author. Highly dependent on the base rate of same-author pairs in the test set. |
Addressing Common Data Analysis Concerns
- Multiplicity: When evaluating a large panel of stylometric features, the probability of false positives increases. Correction methods like the False Discovery Rate (FDR) must be applied to ensure that only truly discriminative biomarkers are selected [9] [11].
- Within-Author Correlation: Multiple text samples from the same author are not independent. Statistical models (e.g., mixed-effects models) that account for this intra-class correlation are necessary to generate accurate p-values and confidence intervals [11].
This application note establishes a rigorous framework for treating semantic and stylometric features as validated discriminative biomarkers. By adopting protocols from clinical biomarker development—such as pre-specified analytical plans, controlled validation studies, and careful statistical correction—resitects can significantly improve the reliability of authorship verification systems. The explicit mitigation of topic leakage through the HITS protocol is a critical advancement, ensuring that models are evaluated on their ability to capture an author's unconscious signature rather than superficial topic cues. The continued development and application of these principles are essential for the acceptance of stylometry as a robust forensic discipline [15].
The Critical Challenge of Topic Shift and Dataset Bias in Real-World Applications
The reliability of machine learning models in real-world applications is critically threatened by dataset shift, a phenomenon where the data used during the model's deployment differs from the data it was trained on. Within this broad challenge, topic shift—a change in the thematic content of data—presents a particularly insidious problem in tasks like authorship verification (AV), where models may inadvertently learn to recognize topics rather than an author's unique stylistic signature [6]. Similarly, in computer vision, models often learn spurious correlations from biased datasets, causing them to fail when these correlations change in the test environment [17] [18]. These issues are not merely academic; they lead to systemic failures, perpetuate inequalities, and erode trust in AI systems [19]. This document outlines the core challenges, provides experimental protocols for studying these biases, and presents mitigation strategies, with a specific focus on cross-topic authorship verification. The insights are framed within a broader thesis on developing robust, topic-invariant AV models.
The Problem: Topic Leakage and Spurious Correlations
Topic Leakage in Authorship Verification
In authorship verification, the ideal is to identify an author based on stylistic, topic-agnostic features. However, topic leakage occurs when there is unintended thematic overlap between training and test datasets [6] [7]. This creates a "topic shortcut," allowing models to achieve deceptively high performance by simply matching topics instead of learning the more nuanced, stable features of an author's writing style. Consequently, model evaluations become misleading, and their real-world robustness is severely overestimated. The conventional evaluation practice, which assumes minimal topic overlap, is insufficient to prevent this leakage, necessitating more rigorous benchmarking frameworks like RAVEN (Robust Authorship Verification bENchmark) [6].
Spurious Correlations and Dataset Bias
Beyond text, computer vision models are similarly hampered by dataset bias. A model might learn to associate a background feature (e.g., the presence of a ruler in dermatology images, or a specific environment in bird photographs) with a target class, rather than the actual pathological or object-related features [17] [18]. These spurious correlations are a form of correlation shift. Research shows that even small, low-intensity correlation shifts between training and test data are sufficient to cause significant performance degradation, posing a serious dataset-bias issue [17]. This is compounded by the fact that models often learn robust features during training but default to using spurious ones during testing [17].
Experimental Protocols for Analysis and Mitigation
Protocol 1: Heterogeneity-Informed Topic Sampling (HITS) for Authorship Verification
The HITS protocol is designed to create evaluation datasets that minimize the confounding effects of topic leakage, enabling a more accurate assessment of a model's true stylistic understanding [6] [7].
Objective: To generate a benchmark dataset that reduces topic leakage and produces a stable ranking of AV models. Application: Cross-topic authorship verification.
Methodology:
- Data Collection and Topic Annotation: Assemble a large, topic-diverse corpus of documents. Annotate each document with its primary topic label.
- Heterogeneous Topic Set Construction: Instead of a simple train-test split, construct a topic set that ensures heterogeneity. This involves selecting topics for the test set such that they are maximally distinct from each other and from the topics in the training set.
- Stratified Sampling of Documents: For each selected topic, sample documents from a wide variety of authors. This ensures that the evaluation tests the ability to verify authorship across topics, not within a single, homogeneous topic.
- Benchmark Creation (RAVEN): Compile the sampled documents into the Robust Authorship Verification bENchmark (RAVEN). This benchmark is explicitly designed to include a "topic shortcut test" to uncover and penalize models that rely on topic-specific features.
- Model Evaluation and Ranking: Train and evaluate multiple AV models on the RAVEN benchmark. The use of a heterogeneously distributed topic set yields a more stable and reliable ranking of model performance across different random seeds and data splits [6].
The following workflow diagram illustrates the HITS protocol:
Protocol 2: Quantifying Correlation and Diversity Shifts
This protocol provides a framework for systematically investigating the nuanced impacts of different types of dataset shifts, particularly the interplay between correlation and diversity shifts [17].
Objective: To analyze how varying intensities of correlation and diversity shifts impact model performance and reliance on spurious features. Application: General model robustness evaluation, especially in healthcare and biased imaging datasets.
Methodology:
- Dataset Generation with Controlled Bias: Start with a base dataset (e.g., CelebA [18] or a synthetic dataset like Waterbirds [17]). Introduce a known, controlled spurious correlation (e.g., between a background feature and a class label) at varying intensity levels (e.g., from low 55% to high 95% correlation).
- Define Multiple Test Sets: Create a battery of test sets to probe model behavior under different conditions:
- Same-Source (In-Distribution): Test set shares the same data distribution as the training set.
- Diversity-Shifted: Test set contains new, unseen variations of the core classes (e.g., skin lesions on dark skin when trained mostly on light skin [17]).
- Correlation-Shifted (No Shortcuts): Test set breaks the spurious correlation present in training (e.g., "waterbirds" on land backgrounds).
- Model Training and Evaluation: Train models on the biased training sets and evaluate comprehensively across all test sets. Monitor not only overall accuracy but also performance disaggregated by subgroups affected by the spurious correlation.
- Internal Bias Analysis: Utilize advanced metrics like Attention-IoU (Intersection over Union) [18] to analyze the model's internal attention maps. This reveals whether the model is focusing on the core features of interest (e.g., a bird's beak) or the spurious features (e.g., the background water).
Table 1: Taxonomy of Dataset Shifts and Their Characteristics
| Type of Shift | Definition | Primary Manifestation | Common Evaluation Protocol |
|---|---|---|---|
| Prior Probability Shift [20] [21] | Change in the distribution of the class labels, P(Y). | Prevalence of classes differs between training and test sets. | Artificial Prevalence Protocol (APP) [20]. |
| Covariate Shift [20] [21] | Change in the distribution of the input features, P(X). | Data distribution (features) differs between training and test sets. | Testing on data from a different domain or population. |
| Concept Shift [20] [21] | Change in the relationship between inputs and outputs, P(Y|X). | The underlying concept or mapping from X to Y changes. | Evaluation over time or in non-stationary environments (e.g., pre/post financial crisis). |
| Internal Covariate Shift [21] | Change in the distribution of internal network activations. | Input distribution to hidden layers changes during training, slowing learning. | Use of Batch Normalization layers to stabilize distributions. |
The Scientist's Toolkit: Key Research Reagents and Materials
For researchers developing and evaluating models against topic shift and dataset bias, a specific set of "research reagents" is essential.
Table 2: Essential Research Reagents for Bias and Shift Analysis
| Reagent / Resource | Type | Primary Function | Example / Reference |
|---|---|---|---|
| RAVEN Benchmark | Dataset & Benchmark | Provides a controlled environment for evaluating AV models' robustness to topic leakage, free from topic shortcuts. | [6] [7] |
| CelebA Dataset | Dataset | A real-world, biased image dataset used to study spurious correlations (e.g., accessories correlated with gender). | [18] |
| Waterbirds Dataset | Dataset | A synthetic dataset where birds are artificially placed on land/water backgrounds, creating a known spurious correlation. | [17] [18] |
| Attention-IoU Metric | Metric & Tool | Uses model attention maps to quantify which image features a model uses for prediction, revealing internal bias. | [18] |
| AI Fairness 360 (AIF360) | Software Toolkit | An open-source library containing metrics and algorithms to check and mitigate bias in datasets and ML models. | [19] |
| Fairlearn | Software Toolkit | An open-source project for assessing and improving fairness of AI systems. | [19] |
Visualization of Model Reliance on Spurious Features
The following diagram illustrates the core problem of spurious feature reliance and how different types of shifts can intervene, based on findings from Bissoto et al. [17]:
Addressing topic shift and dataset bias is not a single-step process but requires a rigorous, protocol-driven approach integrated throughout the machine learning lifecycle. The experimental frameworks of HITS and controlled shift analysis are critical for moving beyond misleading in-distribution metrics and building models that are truly robust in the real world. Key findings indicate that even small, often overlooked shifts can be critically damaging [17], and that diversity shift can, in some cases, attenuate a model's reliance on spurious correlations [17]. Future work must focus on developing more realistic and comprehensive benchmarks, integrating bias detection and mitigation tools like AIF360 [19] and Attention-IoU [18] into standard development workflows, and establishing rigorous reporting standards akin to SPIRIT [22] for model transparency. For authorship verification specifically, the RAVEN benchmark and the HITS protocol provide a necessary foundation for developing the next generation of topic-invariant stylometric models.
The integrity of scientific publications and clinical documentation is foundational to progress in biomedical research, ensuring that findings are reliable, reproducible, and trustworthy. Authorship verification is a critical component of this integrity, serving to authenticate the provenance of scientific texts and protect intellectual property [5]. Within the context of a broader thesis on cross-topic authorship verification, this protocol explores the application of advanced natural language processing (NLP) models to discern an author's unique stylistic signature, irrespective of the document's topic. This is particularly vital for detecting plagiarism, confirming authorship in multi-contributor papers, and safeguarding the authenticity of clinical trial documentation [5] [6]. The following sections provide a detailed application note, presenting a standardized experimental protocol for robust authorship verification, complete with data presentation, workflow visualizations, and a catalogue of essential research reagents.
Background and Significance
Authorship verification (AV) is defined as the task of determining whether two texts were written by the same author [5] [6]. In biomedical research, where collaboration is the norm and the stakes for accuracy are high, robust AV systems are essential for several reasons. They help prevent fraudulent claims of authorship, ensure proper credit is assigned, and protect the chain of custody for data and findings in clinical documentation.
A significant challenge in this domain is topic leakage, where an AV model makes predictions based on shared subject matter between texts rather than on genuine stylistic cues unique to an author [6]. This confounds the evaluation of a model's true capability to identify writing style. To address this, recent research emphasizes cross-topic evaluation setups, which deliberately use texts on different topics to train and test models, ensuring they learn stylistic features rather than topic-based shortcuts [6] [23]. The integration of deep learning models that combine semantic features (meaning and content) with stylistic features (sentence length, punctuation, word frequency) has been shown to significantly improve model accuracy and robustness in real-world, stylistically diverse datasets [5].
The evaluation of authorship verification models relies on several key performance metrics. The following table summarizes these common metrics and the impact of different feature types on model performance, providing a basis for comparing experimental results.
Table 1: Key Performance Metrics for Authorship Verification Models
| Metric | Description | Interpretation in AV Context |
|---|---|---|
| Accuracy | The proportion of correct predictions (same author/different author) out of all predictions. | Provides a general measure of model effectiveness, but can be misleading on imbalanced datasets [5]. |
| Macro-averaged F1-Score | The harmonic mean of precision and recall, averaged across all classes (same/different author). | A robust metric for imbalanced datasets, as it treats both classes equally and is less sensitive to class distribution [23]. |
| Model Ranking Stability | The consistency of a model's performance ranking across different evaluation splits or random seeds. | Highlights a model's reliability; improved by evaluation methods like HITS that mitigate topic leakage [6]. |
Table 2: Impact of Feature Types on Authorship Verification Model Performance
| Feature Category | Examples | Contribution to Model Performance |
|---|---|---|
| Semantic Features | RoBERTa embeddings, contextual word meanings [5]. | Captures the underlying meaning and content of the text. Essential for deep understanding but susceptible to topic bias if used alone. |
| Stylistic Features | Sentence length, word frequency, punctuation usage [5]. | Captures an author's unique writing habits that are largely independent of topic. Crucial for cross-topic robustness. |
| Combined Features | Interaction of semantic and stylistic features in a single model [5]. | Consistently improves model performance and generalizability by leveraging the strengths of both feature types. |
Experimental Protocol for Cross-Topic Authorship Verification
Protocol Title
Validation of a Combined Semantic and Stylistic Feature Model for Robust, Cross-Topic Authorship Verification in Biomedical Text.
Author Information
[Affiliation: Department, Research Institution, City, Country for each author]
This protocol details a methodology for applying and evaluating deep learning models for authorship verification (AV) in a cross-topic setting, a critical challenge for ensuring integrity in biomedical publications. It combines RoBERTa-based semantic embeddings with hand-crafted stylistic features to enhance model robustness against topic shifts. The protocol is designed to minimize the effects of topic leakage, providing a more reliable assessment of true writing style and offering a tool for authenticating scientific and clinical documents.
Key Features
- Cross-Topic Robustness: Employs evaluation splits designed to minimize topic overlap between training and testing data.
- Hybrid Feature Approach: Integrates state-of-the-art semantic understanding with fundamental stylistic features for improved accuracy.
- Bias Mitigation: Utilizes the HITS (Heterogeneity-Informed Topic Sampling) method to create evaluation datasets that ensure stable model rankings [6].
- Real-World Applicability: Tested on challenging, imbalanced, and stylistically diverse datasets reflective of actual biomedical literature.
Keywords
Authorship Verification, Cross-Topic Evaluation, RoBERTa, Style Features, Topic Leakage, Biomedical Text Analysis.
A graphical overview of the experimental workflow is provided in Section 4.13.
Background
Authorship verification is a key task in Natural Language Processing (NLP), essential for applications like plagiarism detection and content authentication in biomedical research. Conventional AV evaluations often suffer from topic leakage, where models exploit topical similarities rather than learning genuine stylistic markers, leading to inflated and misleading performance metrics [6]. This protocol is situated within a thesis focused on developing experimental setups that isolate and measure an model's ability to verify authorship across different topics, thereby ensuring that the systems are learning authorial style [23]. The methodology described herein is adapted from recent work that demonstrates the efficacy of combining semantic and stylistic features in deep learning architectures such as Feature Interaction Networks, Pairwise Concatenation Networks, and Siamese Networks [5].
Materials and Reagents
Table 3: Research Reagent Solutions for Authorship Verification Experiments
| Item | Function / Application | Specifications / Notes |
|---|---|---|
| PAN AV Dataset | A benchmark dataset for authorship verification tasks. | Provides text pairs with same-author/different-author labels. Ensure usage of a cross-topic split [5] [23]. |
| RAVEN Benchmark | A specialized benchmark for testing AV model robustness against topic shortcuts [6]. | Used for the final evaluation to assess real-world performance. |
| RoBERTa Model | A pre-trained transformer model for generating semantic text embeddings. | Captures deep contextual semantic information from text inputs [5]. |
| Python Programming Language | The primary language for implementing and executing the AV models. | Version 3.8 or above. Essential for scripting the analysis pipeline. |
| Relevant Software Libraries | Provides pre-built functions for machine learning and NLP. | Libraries include PyTorch or TensorFlow, Transformers, Scikit-learn, NLTK, Pandas. |
Equipment
- Computer Workstation: High-performance computing workstation with a multi-core CPU (e.g., Intel Xeon or AMD Ryzen 7/9), minimum 32 GB RAM, and a GPU (e.g., NVIDIA RTX 3080 or higher with 12+ GB VRAM) to accelerate deep learning model training and inference.
- Storage: Fast Solid State Drive (SSD) with at least 1TB of storage for housing datasets, model files, and experiment logs.
Software and Datasets
- Operating System: Ubuntu 20.04 LTS or Windows 10/11.
- Python Libraries: PyTorch (v1.12+), Transformers (v4.20+), Scikit-learn (v1.1+), NLTK (v3.7), Pandas (v1.5), NumPy (v1.22).
- Datasets: PAN Authorship Verification dataset [5], RAVEN benchmark [6].
Procedure
CAUTION: Always ensure data privacy and ethical guidelines are followed when handling text data, especially clinical documents.
Data Acquisition and Preparation: a. Download the PAN AV dataset and the RAVEN benchmark. b. CRITICAL: Apply the HITS sampling method to create a heterogeneously distributed topic set for evaluation to mitigate topic leakage [6]. This step is crucial for a valid cross-topic assessment. c. Partition the data into training, validation, and test sets, ensuring no author or topic overlaps between the splits unless intentionally designed for a specific cross-validation experiment. d. Preprocess the text: lowercasing, removing extraneous whitespace, and tokenization.
Feature Extraction: a. Semantic Features: Use the pre-trained
roberta-basemodel from the Hugging Face Transformers library to generate contextual embeddings for each text in the pair. Average the token embeddings to create a fixed-length document vector [5]. b. Stylistic Features: For each text, extract a set of predefined stylistic features, including: - Average sentence length. - Average word length. - Punctuation frequency (e.g., commas, semicolons). - Function word frequency. c. PAUSE POINT: The extracted feature sets can be saved to disk for future runs to expedite the model training process.Model Architecture and Training: a. Implement one of the proposed deep learning architectures (e.g., Feature Interaction Network) that takes both the semantic embedding vector and the stylistic feature vector as input [5]. b. The model should be designed to learn interactions between the two feature types. c. Train the model using the training set. Use the validation set for hyperparameter tuning and to monitor for overfitting. Employ a binary cross-entropy loss function and an optimizer like AdamW.
Model Evaluation: a. CRITICAL: Run the final evaluation on the held-out test set that was constructed using HITS sampling [6]. b. Calculate key performance metrics: Accuracy, Macro-averaged F1-Score, and observe Model Ranking Stability if multiple models are being compared. c. Benchmark performance against the RAVEN dataset to test for reliance on topic-specific features [6].
Data Analysis
- Statistical Analysis: Perform significance testing (e.g., paired t-test) to determine if the performance improvement gained by adding stylistic features is statistically significant across multiple runs with different random seeds.
- Error Analysis: Manually inspect text pairs where the model made incorrect predictions. Categorize the errors to identify common failure modes (e.g., short texts, highly formulaic writing).
- Validation of Protocol: The robustness of this protocol is validated by its design to outperform models that rely on semantic features alone, as demonstrated in prior studies [5], and by its use of the HITS method to ensure a stable and reliable evaluation [6].
Workflow and Logical Diagrams
Diagram 1: AV Model Workflow
Diagram 2: Topic Leakage Solution
Building Robust Verification Systems: Architectures, Feature Engineering, and Protocol Design
The proliferation of large language models (LLMs) has revolutionized text generation but also introduced significant challenges in authorship verification (AV), particularly in identifying the sources of AI-generated text and countering misinformation [24]. Conventional AV methods often rely on singular feature types, making them susceptible to cross-domain performance degradation when topic-based features overshadow genuine authorship signatures. Advanced feature extraction, which synergistically combines dense, contextual embeddings from pre-trained models like RoBERTa with hand-crafted stylometric features, presents a formidable solution. This approach is pivotal for cross-topic authorship verification experimental protocols, as it enables models to capture both deep semantic representations and surface-level stylistic patterns that are inherently topic-agnostic [14]. The integration of these feature types creates a more robust and generalizable representation of an author's unique writing signature, which is essential for applications ranging from identity verification and plagiarism detection to forensic analysis of AI-generated content [24] [14].
Theoretical Foundation
RoBERTa Embeddings
RoBERTa (Robustly Optimized BERT Pre-training Approach) is a transformer-based model that provides dense, contextualized embeddings for text. Unlike static word embeddings, RoBERTa generates dynamic representations that adapt to the surrounding context of each word in a sentence. This allows the model to capture nuanced semantic meanings and syntactic relationships that are characteristic of an author's writing style at a deep, linguistic level. In the context of neural authorship attribution, the embeddings from RoBERTa's final layers serve as a high-dimensional feature space where texts from the same LLM are hypothesized to cluster together [24].
Stylometric Features
Stylometric features are quantitative measures of an author's writing style, traditionally used in authorship analysis. They can be categorized into several groups:
- Lexical Features: These include vocabulary richness, word length distribution, and character-level n-grams. They capture an author's choice of words and their patterns of use.
- Syntactic Features: These features describe the grammatical structure of sentences, including part-of-speech (POS) tag frequencies, usage of function words, sentence length variability, and the prevalence of active versus passive voice [24].
- Structural Features: These encompass document-level characteristics such as average paragraph length, punctuation frequency, and capitalization patterns [24].
Complementary Nature
RoBERTa embeddings and stylometric features offer complementary strengths. RoBERTa excels at modeling complex, contextual linguistic phenomena, while stylometrics provide interpretable, surface-level markers of style. Their combination mitigates the risk of models latching onto topic-specific artifacts, thereby enhancing cross-topic robustness. Research has shown that the fusion of these features creates a writing signature vector that is both comprehensive and distinctive, improving the ability to differentiate between authors and AI models, including distinguishing between proprietary (e.g., GPT-3.5, GPT-4) and open-source LLMs (e.g., Llama 1, GPT-NeoX) [24].
Experimental Protocols
Dataset Generation and Curation
A high-quality, diverse dataset is foundational for training and evaluating a robust authorship verification model. The following protocol outlines the steps for dataset creation, drawing from established methodologies [24] [14].
- Step 1: Source Selection. Identify and select a wide array of text sources. The Million Authors Corpus (MAC) is an exemplary resource, containing 60.08 million textual chunks from 1.29 million Wikipedia authors across dozens of languages, ensuring inherent cross-lingual and cross-domain variability [14].
- Step 2: LLM Text Generation. To incorporate AI-generated text, use multiple LLMs (both proprietary like GPT-3.5/GPT-4 and open-source like Llama 1/2 and GPT-NeoX). Generate text by prompting these models with human-authored article headlines to produce news-style articles, controlling for domain while eliciting model-specific stylistic signatures [24].
- Step 3: Data Preprocessing and Balancing. Clean the collected texts by removing metadata and standardizing formatting. For classification tasks, ensure the dataset is balanced by sampling an equal number of text samples per author or per source LLM to prevent model bias toward majority classes [24].
Feature Extraction Methodology
This protocol details the parallel extraction of RoBERTa embeddings and stylometric features.
Step 1: Stylometric Feature Extraction.
- Lexical: Calculate type-token ratio (TTR), hapax legomena, and frequency of character n-grams (e.g., n=3,4).
- Syntactic: Use a POS tagger to compute the normalized frequency of nouns, verbs, adjectives, prepositions, and adverbs. Calculate average sentence length and standard deviation.
- Structural: Determine average paragraph length (in words), frequency of commas, semicolons, and exclamation marks per 1000 words.
- Normalization: Normalize all extracted features to a common scale (e.g., Z-score normalization) to form the final stylometry feature vector [24].
Step 2: RoBERTa Embedding Extraction.
- Model Setup: Utilize a pre-trained RoBERTa model (e.g.,
roberta-base). - Input Processing: Tokenize the input text using the RoBERTa tokenizer. For each text sample, pass the tokenized input through the model.
- Embedding Pooling: Extract the hidden state from the final layer. To obtain a fixed-length representation for the entire text, apply a pooling strategy—such as mean pooling over all token embeddings—to create a dense contextual embedding vector [24].
- Model Setup: Utilize a pre-trained RoBERTa model (e.g.,
Step 3: Feature Fusion.
- Concatenation: Combine the normalized stylometry feature vector and the pooled RoBERTa embedding vector into a single, unified feature vector via concatenation. This fused vector represents the comprehensive "writing signature" [24].
Model Training and Evaluation
This protocol covers the training and systematic evaluation of the authorship verification model.
Step 1: Model Architecture Selection.
- Option 1 (Traditional ML): Use a gradient-boosting framework like XGBoost, which can effectively handle the fused feature vector (XGBstylo) or a bag-of-words baseline (XGBbow) [24].
- Option 2 (Neural): Employ a neural classifier that takes the fused embeddings as input. Alternatively, fine-tune the RoBERTa model end-to-end, using the stylometric features as auxiliary inputs in a later layer.
Step 2: Experimental Design for Cross-Topic Verification.
- Train-Test Split: Partition the dataset into training and testing sets, ensuring that texts from the same author (or source LLM) are present in both sets but with distinct topics. This is crucial for forcing the model to learn topic-agnostic features.
- Cross-Validation: Perform k-fold cross-validation, where folds are stratified by author/LLM but varied by topic, to obtain reliable performance estimates.
Step 3: Model Interpretation.
- SHAP Analysis: Apply SHapley Additive exPlanations (SHAP) to the trained model (e.g., XGBoost) to identify which stylometric features (e.g., specific POS tags, lexical diversity) are most influential in distinguishing between authors or LLM categories [24].
Table 1: Key Stylometric Features for Differentiating Proprietary and Open-Source LLMs (based on SHAP analysis)
| Feature Category | Specific Feature | Importance for Differentiation |
|---|---|---|
| Lexical | Lexical Diversity | High |
| Syntactic | Preposition Frequency | High |
| Syntactic | Adjective Frequency | High |
| Syntactic | Noun Frequency | High |
| Structural | Paragraph Length | Medium |
Visualization of Workflows
Feature Extraction and Fusion Process
The Scientist's Toolkit
Table 2: Essential Research Reagents and Computational Tools for Authorship Verification
| Item Name | Type/Function | Application in Protocol |
|---|---|---|
| Million Authors Corpus (MAC) | Dataset | Provides a massive, cross-lingual, and cross-domain benchmark for evaluating model generalizability [14]. |
| RoBERTa (base model) | Pre-trained Language Model | Serves as the core engine for generating contextualized, deep semantic embeddings from text inputs [24]. |
| XGBoost | Machine Learning Classifier | A robust gradient boosting framework used for classification based on fused or individual feature sets [24]. |
| SHAP (SHapley Additive exPlanations) | Model Interpretation Library | Provides post-hoc explainability, identifying the most influential stylometric features for model decisions [24]. |
| t-SNE | Dimensionality Reduction Algorithm | Used for visualizing the separation of different author/LLM classes in high-dimensional embedding spaces [24]. |
Results and Data Presentation
The efficacy of the fused feature approach is demonstrated through quantitative results from controlled experiments. The following tables summarize key performance metrics.
Table 3: Performance Comparison of Different Feature Configurations in Neural Authorship Attribution
| Model / Feature Set | Proprietary vs. Open-Source Accuracy | Intra-Proprietary Accuracy | Intra-Open-Source Accuracy |
|---|---|---|---|
| XGBoost (Stylometry only) | 89.2% | 85.7% | 78.3% |
| RoBERTa (Embeddings only) | 91.5% | 88.1% | 80.9% |
| Fusion (RoBERTa + Stylometry) | 95.8% | 92.4% | 85.6% |
Table 4: Impact of Llama 2 on Open-Source Category Classification Performance
| Scenario | Open-Source Classification Accuracy | Notes |
|---|---|---|
| Open-Source (Excluding Llama 2) | 88.1% | Clearer separation between older open-source models. |
| Open-Source (Including Llama 2) | 80.7% | Performance drop of ~7.4%, indicating Llama 2's style is distinct and closer to proprietary models [24]. |
In the domain of authorship verification (AV), which aims to determine whether a pair of texts is written by the same author, robust feature learning is paramount. The core challenge lies in learning a representation space where feature embeddings from the same author are mapped closely together, while those from different authors are pushed apart. This document details application notes and experimental protocols for three powerful deep learning architectures adept at this task: Siamese Networks, Feature Interaction Networks, and Pairwise Concatenation Networks. The content is framed within cross-topic authorship verification research, which emphasizes model robustness against topic shifts and minimizes reliance on topic-specific features [6].
Architectural Definitions and Application Rationale
Siamese Neural Networks
A Siamese Neural Network is a specialized class of neural network that contains two or more identical sub-networks with shared weights, working in tandem on two different input vectors to compute comparable output vectors [25] [26]. The shared weights ensure that two similar input samples from the same author cannot be mapped to different locations in the feature space. During learning, the network is trained using a contrastive or triplet loss function. These functions aim to minimize the distance between feature embeddings from the same author (positive pairs) and maximize the distance between embeddings from different authors (negative pairs) [25] [26]. This architecture is particularly suitable for authorship verification, a task often framed as a similarity learning problem where the model must learn to verify whether a pair of text samples belongs to the same author or not.
Feature Interaction Networks
Feature interaction refers to the phenomenon where the combination of two or more features produces a non-additive effect on the model's prediction. In the context of AV, different writing style markers (e.g., lexical, syntactic, and structural features) can interact in complex ways that are highly indicative of a unique authorial style. Table 1 summarizes key feature interaction types in AV. Modeling these interactions explicitly can allow the model to capture the complex, compositional nature of an author's writing style more effectively than considering features in isolation.
Table 1: Types of Feature Interactions in Authorship Verification
| Interaction Type | Description | AV Application Example |
|---|---|---|
| Statistical Pairwise | Quantifiable, non-additive effect between two features. | Interaction strength measured via H-statistics [27]. |
| Spatio-Temporal | Correlation between spatial and temporal signal features. | In EEG, integrates spatial distribution & temporal dynamics [28]. |
| Logical/Sequential | Interactions governed by logical or sequential constraints. | Analyzed using formal methods and logic [29]. |
Pairwise Concatenation Networks
Pairwise Concatenation is a fundamental yet effective method for combining features from two input samples. This operation involves concatenating the feature vectors (or embeddings) of the two text samples in a pair, typically after they have been processed by a base network. The resulting combined vector is then passed through one or more fully connected layers to learn the non-linear relationships between the features of the two samples, ultimately leading to a binary (same/not-same) classification. While simpler than a Siamese architecture with a specialized loss, it allows the model to directly learn discriminative patterns from the juxtaposed feature sets.
Quantitative Performance Comparison
The performance of deep learning architectures is quantitatively evaluated on standard benchmarks. The following table summarizes key metrics, providing a basis for comparison and selection.
Table 2: Performance Comparison of Deep Learning Architectures for AV and Related Tasks
| Architecture | Dataset | Key Metric(s) | Performance | Key Feature |
|---|---|---|---|---|
| AVSiam (Siamese ViT) [30] | AudioSet-20K, VGGSound | Audio-visual Retrieval | Competitive or superior to state-of-the-art | Single shared backbone for audio & visual inputs. |
| Siamese Network (EEG) [28] | BCI IV-2a | Classification Accuracy | Better than baseline | High discriminative feature learning for cross-subject tasks. |
| InHRecon (Feature Interaction) [27] | Multiple Feature Sets | Model Improvement (vs. baseline) | Significant improvement | Interaction-aware hierarchical reinforced reconstruction. |
| AVA-Net (Artery-Vein) [31] | OCTA Images (DR) | Arterial-Venous PID Ratio (AV-PIDR) | Significant differences among control, NoDR, mild DR | Most sensitive feature for early disease detection. |
Experimental Protocols
Protocol 1: Siamese Network for Textual Similarity
This protocol outlines the steps for training a Siamese network for authorship verification using a triplet loss function.
Workflow Diagram:
Procedure:
- Data Preparation: Compile a dataset of text documents with author labels. From this, generate triplets for training: an anchor text (A), a positive text (P) from the same author as A, and a negative text (N) from a different author.
- Input Encoding: Convert all text samples into a numerical representation, such as word embeddings or TF-IDF vectors.
- Sub-network Forward Pass: Process the anchor, positive, and negative samples through the identical sub-networks (e.g., a multi-layer perceptron or a recurrent neural network) with shared weights to obtain their respective feature embeddings: ( f(A) ), ( f(P) ), and ( f(N) ).
- Loss Calculation: Compute the triplet loss using the formula: ( Loss{Triplet} = \sumi^N \left[ \|f(Ai) - f(Pi)\|2^2 - \|f(Ai) - f(Ni)\|2^2 + \lambda \right] ) where ( \lambda ) is a margin that enforces a minimum distance between positive and negative pairs [26].
- Backpropagation & Optimization: Update the weights of the shared sub-network using backpropagation and an optimizer like Adam to minimize the triplet loss.
- Inference: For a new text pair, compute their embeddings and calculate their Euclidean or cosine distance. Classify as "same author" if the distance is below a learned threshold.
Protocol 2: Feature Interaction Modeling with Hierarchical Reinforcement
This protocol describes a method for automated feature space reconstruction that explicitly captures and leverages feature interactions, which can be adapted for AV.
Workflow Diagram:
Procedure:
- Problem Formulation: Define the task as learning an optimal and meaningful feature set ( \mathcal{F}^* ) that maximizes the performance ( VA ) on the authorship verification task: ( \mathcal{F}^* = \arg\max{\mathcal{\hat{F}}}(V_A(\mathcal{\hat{F}}, y)) ) [27].
- Agent Setup: Implement a hierarchical reinforcement learning structure with three agents:
- An Operation Agent that selects a mathematical operation (e.g., "Combine", "Multiply") from a predefined set ( \mathcal{O} ).
- Two Feature Agents that each select one existing feature from the feature pool.
- Feature Generation: At each step, apply the selected operation to the two selected features to generate a new feature.
- Interaction-Aware Reward: Quantify the strength of the interaction between the selected features using a statistical measure like H-statistics [27]. Reward the agents based on this interaction strength and the operational validity of the new feature.
- Iterative Reconstruction: Repeat the generation and selection process. The agents learn a policy to create an optimal, interpretable feature set that enhances the downstream AV classifier's performance.
Protocol 3: Pairwise Concatenation for Author Discrimination
This protocol provides a straightforward method for combining features from two text samples for direct classification.
Procedure:
- Feature Extraction: For each text in a pair, extract a comprehensive set of features (e.g., character n-grams, syntactic patterns, vocabulary richness indices).
- Vector Concatenation: For a text pair (Text₁, Text₂), let their feature vectors be ( V1 ) and ( V2 ). Create a combined feature vector ( V{\text{pair}} = V1 \oplus V_2 ), where ( \oplus ) denotes the concatenation operation.
- Classification Network: Feed the concatenated vector ( V_{\text{pair}} ) into a fully connected neural network.
- Output and Training: The final layer uses a sigmoid activation function to output a probability that the two texts are from the same author. Train the network end-to-end using binary cross-entropy loss.
The Scientist's Toolkit
Table 3: Essential Research Reagents and Materials
| Item Name | Function/Application |
|---|---|
| Transformer Models (e.g., BERT) | Serves as a foundational sub-network for generating contextualized text embeddings in Siamese or Pairwise architectures [30]. |
| H-Statistic | A statistical measure used to quantify the interaction strength between selected features during reinforced feature space reconstruction [27]. |
| Triplet Loss Function | A discriminative loss function that trains Siamese networks by pulling anchor and positive samples together while pushing anchor and negative samples apart [25] [26]. |
| Contrastive Loss Function | An alternative loss for Siamese networks that reduces the distance for positive pairs and increases it for negative pairs beyond a margin [26]. |
| Hierarchical Reinforcement Learning (HRL) Framework | A structure with cascading Markov Decision Processes to automate feature and operation selection for feature interaction modeling [27]. |
A foundational challenge in authorship verification (AV) is ensuring that models genuinely learn an author's unique writing style rather than relying on topic-specific vocabulary, which acts as a confounding variable. Conventional cross-topic evaluations aim to measure model robustness to topic shifts by assuming minimal topic overlap between training and test data. However, topic leakage—the residual presence of topic-related features in the test data—can lead to misleading performance and unstable model rankings, as models may exploit these subtle topic shortcuts rather than learning style-invariant features [6]. This Application Note details advanced protocols for designing experimental splits that effectively isolate writing style from topic bias, a critical requirement for developing robust AV models in scientific and pharmaceutical research, where verifying authorship can have significant implications for intellectual property and data integrity.
Core Concepts and Quantitative Evidence
The Problem of Topic Leakage
Topic leakage occurs when the evaluation data, despite an intended cross-topic split, contains residual topic information that creates an inadvertent shortcut for AV models. This compromises the validity of the evaluation because a model can achieve high performance by detecting topical similarities rather than stylistic consistencies [6]. The Heterogeneity-Informed Topic Sampling (HITS) method was developed to address this by constructing evaluation datasets with a heterogeneously distributed topic set, thereby reducing the effects of topic leakage and yielding more stable model rankings across different evaluation splits [6].
Comparative Analysis of Dataset Partitioning Strategies
The table below summarizes the characteristics of different dataset partitioning strategies, highlighting the advantages of the HITS method.
Table 1: Characteristics of Dataset Partitioning Strategies for Authorship Verification
| Partitioning Strategy | Core Principle | Key Advantage | Primary Limitation | Impact on Model Ranking Stability |
|---|---|---|---|---|
| Random Split | Random assignment of texts to training and test sets. | Simple to implement. | High risk of topic leakage; fails to test cross-topic robustness. | Low (Highly unstable across seeds/splits) [6]. |
| Naive Cross-Topic Split | Attempts to separate training and test sets by topic. | Explicitly aims for topic independence. | Susceptible to insufficient topic isolation and latent topic leakage. | Moderate (Can be unstable) [6]. |
| HITS (Heterogeneity-Informed Topic Sampling) | Creates a smaller, heterogeneously distributed topic set for evaluation. | Actively mitigates topic leakage by design. | May require more sophisticated sampling and reduce dataset size. | High (More stable across seeds/splits) [6]. |
Experimental Protocols
Protocol 1: Implementing Heterogeneity-Informed Topic Sampling (HITS)
The HITS protocol is designed to create evaluation splits that minimize the risk of models leveraging topic-based shortcuts [6].
3.1.1 Reagents and Materials
- Raw Text Corpus: A collection of documents labeled with author and topic identifiers (e.g., PAN AV datasets).
- Computing Environment: Standard hardware capable of running natural language processing (NLP) libraries.
- Software Tools: Python with scikit-learn, NumPy, and pandas for data manipulation and sampling.
3.1.2 Step-by-Step Procedure
- Topic Identification and Labeling: Manually or algorithmically assign a discrete topic label to every document in the corpus. The granularity of topics (e.g., "Molecular Biology" vs. "Cell Culture Techniques") should be appropriate to the corpus's domain.
- Author-Topic Matrix Construction: Create a matrix where rows represent authors, columns represent topics, and each cell indicates the number of documents an author has written on a given topic.
- Heterogeneity Calculation: For each author, calculate a heterogeneity score based on the distribution of their documents across topics (e.g., using entropy or the Gini-Simpson index).
- Stratified Author Selection: Prioritize authors with high heterogeneity scores for inclusion in the test set. These authors provide diverse topic contexts, which is crucial for a robust evaluation.
- Iterative Split Generation: For the selected authors, algorithmically partition their documents into training and test splits, ensuring that no topic present in the test split is represented in the training split for that author. This is a non-trivial step that may require an optimization procedure to maximize the number of usable author-topic pairs while respecting the topic-exclusivity constraint.
- Validation: Manually inspect a sample of the final splits to confirm the absence of obvious topical overlap and that the topic distribution is sufficiently heterogeneous.
Figure 1: The HITS methodology workflow for creating robust cross-topic evaluation splits.
Protocol 2: Establishing a Baseline with the RAVEN Benchmark
The Robust Authorship Verification bENchmark (RAVEN) provides a standardized framework for conducting a "topic shortcut test" to diagnose a model's over-reliance on topic features [6].
3.2.1 Reagents and Materials
- HITS-Processed Dataset: The dataset generated from Protocol 1.
- AV Models: The authorship verification models to be evaluated.
- Evaluation Framework: A codebase for training models, running inference, and calculating performance metrics (e.g., AUC, F1-score).
3.2.2 Step-by-Step Procedure
- Model Training: Train the candidate AV models on the training portion of the HITS dataset.
- Standard Evaluation: Evaluate the trained models on the standard HITS test set, recording standard performance metrics (e.g., accuracy, AUC). This provides the primary measure of cross-topic robustness.
- Topic Shortcut Test: a. From the test set, identify pairs of documents that are on the same topic but are from different authors. b. Use the trained model to generate predictions for these same-topic, different-author pairs. c. A model that has learned genuine stylistic features should predominantly predict "different author." A high rate of "same author" false positives indicates that the model is conflating topic similarity with author identity.
- Performance Comparison: Compare the model's performance on the standard test set with its performance on the topic shortcut test. A significant performance drop in the shortcut test is indicative of topic bias.
- Benchmarking: Rank all evaluated models based on a composite score that balances performance on the standard test and the topic shortcut test.
Figure 2: The RAVEN benchmark workflow for evaluating model robustness and identifying topic shortcuts.
The Scientist's Toolkit
This section details the key resources required to implement the protocols described in this note.
Table 2: Essential Research Reagent Solutions for Cross-Topic Authorship Verification
| Item Name | Function/Description | Example/Format | Critical Parameters |
|---|---|---|---|
| PAN AV Datasets | Provides standardized, pre-collected text corpora with author and topic labels for benchmarking. | Datasets from PAN@CLEF competitions (e.g., PAN 2020, 2023) [23]. | Topic granularity, number of authors, number of documents per author. |
| Topic Labeling Tool | Algorithmically assigns topic labels to documents when manual labeling is infeasible. | Latent Dirichlet Allocation (LDA), BERTopic. | Number of topics, topic coherence score. |
| HITS Sampling Script | Implements the Heterogeneity-Informed Topic Sampling algorithm to generate robust train/test splits. | Custom Python script using pandas and NumPy. | Heterogeneity metric (e.g., entropy), target test set size. |
| RAVEN Benchmark Suite | A standardized software package for running the topic shortcut test and evaluating model robustness. | Python-based evaluation framework [6]. | Metrics for standard evaluation and shortcut test (e.g., AUC, false positive rate). |
| AV Model Architectures | The candidate models whose robustness is being assessed. | Fine-tuned Large Language Models (LLMs), Siamese Neural Networks, InstructAV [23]. | Model capacity, hyperparameters, fine-tuning method. |
This document provides detailed Application Notes and Protocols for implementing a robust experimental pipeline for cross-topic authorship verification (AV). The content is framed within a broader thesis on cross-topic authorship verification experimental protocols, specifically addressing the challenge of topic leakage, where models exploit topic-specific features rather than genuine stylistic patterns, leading to inflated and misleading performance metrics [6]. The protocols herein are designed for researchers and scientists developing reliable AV systems that generalize across topics and domains.
The core challenge in cross-topic AV is ensuring that models learn authorial style, independent of text topic. Conventional evaluations often contain hidden topic overlaps between training and test splits, a phenomenon known as topic leakage [6]. This protocol outlines a comprehensive workflow—from data collection using Heterogeneity-Informed Topic Sampling (HITS) [6] through to modern post-training techniques [32]—to build models that are robust to topic shifts.
The Scientist's Toolkit: Research Reagent Solutions
Table 1: Essential Materials and Reagents for Authorship Verification Research
| Item Name | Function/Application | Key Characteristics |
|---|---|---|
| PAN AV Datasets [6] [23] | Standardized benchmarks for training and evaluating AV models. | Contains text pairs labeled for authorship; often includes cross-topic or cross-domain splits. |
| RAVEN Benchmark [6] | Evaluates model robustness against topic shortcuts. | Implements HITS sampling; provides a "topic shortcut test" to uncover reliance on topic-specific features. |
| Pre-trained Language Models (e.g., BERT, LLMs) [23] | Foundation for feature extraction or base for fine-tuning. | Provides generalized text representations; can be adapted for stylistic analysis. |
| HITS Sampling Protocol [6] | Creates evaluation datasets with controlled topic distribution. | Reduces topic leakage by ensuring a heterogeneous topic set; stabilizes model ranking. |
| Verification-oriented Orchestration [33] | Improves quality of AI-generated annotations (e.g., for data labeling). | Uses self- and cross-verification with LLMs to increase annotation reliability. |
Data Collection and Annotation Protocols
Core Data Collection and Curation Workflow
A rigorous data collection strategy is fundamental for cross-topic evaluation. The following protocol, centered on HITS, mitigates topic leakage [6].
- Objective: To assemble a dataset where topics are heterogeneously distributed between training and test splits, preventing models from exploiting topic similarities as a shortcut for authorship decisions.
- Materials: A raw corpus of texts with associated metadata, including author identity and topic labels.
- Procedure:
- Topic Identification: Manually or automatically label all documents in the corpus with a discrete set of topics.
- Heterogeneity-Informed Topic Sampling (HITS):
- Select a subset of topics that maximizes intra-topic diversity and inter-topic heterogeneity.
- Partition the selected topics into training and test sets, ensuring minimal thematic overlap.
- From the chosen topics, sample document pairs for the authorship verification task, ensuring a balanced representation of same-author and different-author pairs within and across topics.
- Dataset Splitting: Formally create training, validation, and test splits based on the topic partitions, not random sampling. The test set must contain topics unseen during training.
- Benchmark Creation: Package the resulting dataset as a benchmark, such as the Robust Authorship Verification bENchmark (RAVEN) [6], for standardized evaluation.
AI-Assisted Data Annotation and Verification
For projects requiring manual annotation (e.g., labeling tutoring moves or stylistic features), LLMs can scale the process, but their outputs require verification [33].
- Objective: To produce high-quality, reliable annotations for qualitative data using LLM orchestration.
- Materials: Unlabeled text data (e.g., tutoring transcripts), a detailed codebook (rubric) of constructs to label, and access to frontier LLMs (e.g., GPT, Claude, Gemini).
- Procedure:
- Unverified Annotation: A primary LLM ("annotator") generates initial labels based on the codebook prompt.
- Verification Orchestration:
- Self-Verification: The same LLM that generated the initial labels is prompted to re-check and justify its own outputs.
- Cross-Verification: A different LLM ("verifier") audits the initial labels generated by the annotator model.
- Adjudication: The final label is determined based on the verification step. This process can nearly double agreement with human annotations (Cohen's κ) compared to unverified baselines [33].
- Documentation: Use the notation
verifier(annotator)(e.g.,Gemini(GPT)) to standardize reporting of the orchestration method [33].
Table 2: Impact of HITS Sampling and Verification on Key Performance Metrics
| Method / Condition | Reported Performance Improvement | Primary Effect |
|---|---|---|
| HITS Sampling [6] | "More stable ranking of models across random seeds and evaluation splits." | Mitigates topic leakage, leading to more robust and reliable model evaluation. |
| Self-Verification Orchestration [33] | "Nearly doubles agreement relative to unverified baselines." | Significantly improves AI annotation reliability, especially for challenging constructs. |
| Cross-Verification Orchestration [33] | "Achieves a 37% improvement [in Cohen's κ] on average." | Leverages complementary model strengths to improve annotation quality, though benefits are pair-dependent. |
Table 3: Comparative Cost and Focus of Modern LLM Training Stages
| Training Stage | Primary Objective | Relative Cost & Data Focus |
|---|---|---|
| Pretraining [34] | Learn general language patterns and world knowledge via next-token prediction. | Extremely high cost; uses massive, raw text corpora. |
| Post-Training [32] | Align model with human preferences and specific tasks (e.g., instruction following). | Growing cost, but less than pretraining; increasingly uses synthetic/AI-generated data. |
Experimental Training Pipeline Protocol
The modern LLM training pipeline is broadly divided into pretraining and post-training. For AV, this pipeline is applied to adapt a general-purpose model to the specific task of stylistic analysis [32] [34].
Pipeline Workflow Diagram
Protocol: Post-Training for Authorship Verification
This protocol details the post-training phase, which is critical for adapting a base model to the AV task. The increasing importance and cost of post-training make it a focal point for research [32].
- Objective: To transform a general-purpose base model into a specialized model capable of robust cross-topic authorship verification.
- Input: A base model (output of pretraining) and a high-quality AV-specific dataset, ideally constructed using HITS.
- Procedure:
- Instruction Finetuning (IFT) / Supervised Finetuning:
- Objective: Teach the model to follow instructions related to AV, such as "Analyze the writing style of these two texts."
- Method: Train the model on a dataset of (instruction, response) pairs where the responses are demonstrations of correct AV analysis [32].
- Preference Finetuning:
- Objective: Align the model's outputs more closely with human preferences for accuracy and explanation quality.
- Method: Use algorithms like Reinforcement Learning from Human Feedback (RLHF) or Direct Preference Optimization (DPO). The model learns to choose more accurate verification judgments over less accurate ones [32].
- Reinforcement Finetuning (RFT):
- Objective: Further refine the model's performance on the specific, challenging task of cross-topic reasoning.
- Method: Apply large-scale reinforcement learning to improve performance on specific tasks, akin to methods used in advanced reasoning models [32]. For AV, this could involve rewarding the model for correct verification on topic-shifted pairs.
- Instruction Finetuning (IFT) / Supervised Finetuning:
HITS Sampling Methodology Diagram
The experimental protocols detailed herein—from the HITS data sampling method to modern, multi-stage post-training pipelines—provide a robust framework for conducting cross-topic authorship verification research. Faithful implementation of these protocols is critical for producing models that genuinely learn and verify authorial style, thereby enabling valid and reliable conclusions in scholarly research on authorship analysis.
Diagnosing and Solving Experimental Pitfalls: Topic Leakage, Data Imbalance, and Feature Over-reliance
Identifying and Quantifying Topic Leakage in Test Datasets
Topic leakage occurs when overlapping topics between training and test datasets artificially inflate model performance, leading to misleading evaluations. This is a significant challenge in cross-topic authorship verification (AV), where the objective is to determine if two texts share the same author regardless of their topic. When test data contains topic-related features already present in training data, models may exploit these "topic shortcuts" rather than learning genuine stylistic representations, compromising the reliability of experimental outcomes [6] [7].
Quantifying and mitigating topic leakage is therefore crucial for developing robust authorship verification protocols. This document outlines detailed application notes and experimental protocols for identifying and quantifying topic leakage, framed within a broader thesis on cross-topic authorship verification research.
Background and Significance
In conventional authorship verification evaluation, a fundamental assumption is minimal topic overlap between training and test splits. However, complete topic segregation is often difficult to achieve in practice. Even small amounts of unintentional topic overlap can cause data contamination, providing models with inadvertent shortcuts that compromise evaluation fairness [6] [35].
The effects of topic leakage are twofold. First, it leads to overstated performance metrics that do not reflect true model capability on genuinely unseen topics. Second, it causes unstable model rankings across different evaluation splits and random seeds, making it difficult to identify the most robust architectures [6]. These issues are particularly problematic in scientific and drug development contexts where reproducible and generalizable models are essential.
Quantification Metrics and Data Presentation
Effective quantification of topic leakage requires metrics that capture the degree of topic-based contamination in test datasets. The following metrics provide a framework for systematic assessment.
Table 1: Core Metrics for Quantifying Topic Leakage
| Metric Category | Specific Metric | Description | Interpretation |
|---|---|---|---|
| Topic Distribution | Topic Overlap Coefficient | Measures proportion of test topics present in training data | Higher values indicate greater leakage |
| Topic Purity Score | Assesses homogeneity of topics within evaluation splits | Lower values suggest better topic segregation | |
| Model Performance | Cross-Topic Performance Drop | Difference in performance between topic-overlap and no-overlap conditions | Larger drops suggest greater leakage impact |
| Model Ranking Stability | Consistency of model rankings across different topic splits | Unstable rankings indicate leakage sensitivity | |
| Feature-Based | Topic-Feature Correlation | Measures correlation between topical and stylistic features | High correlation suggests leakage vulnerability |
Table 2: Experimental Results from Topic Leakage Studies
| Experiment | Dataset | Method | Key Finding | Impact on Performance |
|---|---|---|---|---|
| Baseline Evaluation | Standard AV Benchmarks | Conventional random split | Significant topic leakage present | Performance inflated by 15-30% |
| Leakage-Reduced Evaluation | RAVEN (HITS) | Heterogeneity-Informed Topic Sampling | More stable model rankings | Ranking variance reduced by up to 60% |
| LLM Data Contamination | MMLU, HellaSwag | n-gram similarity detection | Test samples found in training data | Performance differences up to 25% on contaminated vs. clean data |
Experimental Protocols
Protocol 1: Heterogeneity-Informed Topic Sampling (HITS)
The HITS methodology addresses topic leakage by constructing evaluation datasets with controlled topic distributions that minimize overlap while maintaining experimental utility [6].
Materials and Reagents
- Text corpora with reliable topic annotations
- Computing environment with sufficient storage and processing capacity
- Topic modeling tools (e.g., LDA, BERTopic)
- Implementation of HITS sampling algorithm
Procedure
- Topic Annotation: Apply automated topic modeling or manual annotation to assign topic labels to all documents in the corpus.
- Topic Stratification: Group documents by their topic labels and calculate the distribution of topics across the entire corpus.
- Heterogeneity Scoring: For potential evaluation splits, compute a heterogeneity score based on the diversity of topics represented.
- Informed Sampling: Select evaluation splits that maximize topic heterogeneity while maintaining adequate sample sizes for each topic.
- Validation: Verify that the selected split minimizes topic overlap between training and test sets while preserving the representativeness of the evaluation.
Applications This protocol is particularly valuable for constructing robust benchmarks for authorship verification, such as the RAVEN benchmark, which enables realistic assessment of model generalization across genuine topic shifts [6].
Protocol 2: Leakage Detection in Multiple-Choice Benchmarks
This protocol adapts methods from LLM evaluation for detecting data contamination in multiple-choice formats, which can be repurposed for topic leakage analysis [35].
Materials and Reagents
- Question-answering datasets with multiple-choice format
- Computational resources for model inference
- Implementation of n-gram similarity detection
- Permutation testing framework
Procedure
- n-gram Similarity Detection:
- Generate option sentences by combining questions with each answer choice
- Compute n-gram overlap between generated sentences and original training data
- Flag instances with unusually high similarity scores as potential leakage
Permutation Method:
- Present answer options in all possible permutations
- Compare model performance across different orderings
- Identify instances where original ordering yields anomalously high performance, suggesting memorization
Semi-Half Question Method:
- Truncate questions to minimal context (e.g., final seven words)
- Present truncated questions to model
- Flag instances where correct answers are still generated as potential leakage
Applications This protocol effectively identifies specific test instances that likely contaminated training data, enabling creation of cleaned evaluation sets that better measure true generalization [35].
Visualization of Workflows
Topic Leakage Identification Workflow
HITS Methodology Implementation
The Scientist's Toolkit
Table 3: Essential Research Reagents and Solutions for Topic Leakage Research
| Tool/Resource | Type | Function | Application Context |
|---|---|---|---|
| RAVEN Benchmark | Dataset | Provides robust evaluation for authorship verification with controlled topic leakage | Testing model robustness to topic shifts [6] |
| HITS Algorithm | Methodology | Creates evaluation datasets with heterogeneously distributed topics | Minimizing topic leakage in experimental design [6] |
| n-gram Similarity Detection | Detection Method | Identifies overlapping content between training and test data | Quantifying data contamination in text datasets [35] |
| Permutation Method | Detection Method | Evaluates model sensitivity to option ordering in multiple-choice tasks | Detecting memorization of specific question formats [35] |
| Topic Modeling Tools | Software | Automates topic annotation and analysis | Preparing corpora for leakage analysis (e.g., LDA, BERTopic) |
| Contrast Ratio Calculators | Evaluation Tool | Ensures visualizations meet accessibility standards | Creating diagrams with sufficient color contrast [36] |
Identifying and quantifying topic leakage is essential for developing reliable authorship verification systems and ensuring valid experimental outcomes in computational linguistics research. The protocols and methodologies presented here—particularly the HITS approach and various detection methods—provide researchers with practical tools to address this challenge. By implementing these techniques, scientists can create more robust evaluations, obtain more reliable model assessments, and advance the field of cross-topic authorship verification with greater methodological rigor. Future work should focus on developing automated tools for topic leakage detection and establishing standardized reporting practices for topic segregation in experimental protocols.
The HITS (Heterogeneity-Informed Topic Sampling) Method for Stable Evaluation
Authorship Verification (AV) is a critical task in computational linguistics that aims to determine whether a pair of texts was written by the same individual [6]. The evaluation of AV models faces a significant challenge: ensuring that these models are robust to topic shifts and genuinely learn authorial style rather than relying on topical shortcuts. Conventional cross-topic evaluation assumes minimal topic overlap between training and test data. However, topic leakage in test data can lead to misleading performance metrics and unstable model rankings, as models may exploit residual topic-specific features rather than true stylistic patterns [6] [7].
The Heterogeneity-Informed Topic Sampling (HITS) method was developed to address this critical evaluation pitfall. HITS systematically constructs evaluation datasets with a heterogeneously distributed topic set, effectively reducing the influence of topic leakage and providing a more stable and reliable assessment of AV model performance [6]. This protocol details the application of HITS within cross-topic authorship verification experimental frameworks, as explored in the broader context of thesis research on robust AV evaluation.
Key Principles and Quantitative Validation
The HITS method operates on the principle that a carefully curated, smaller dataset with high topic heterogeneity provides a more stable foundation for model evaluation than larger datasets with potential topic bias. Experimental results have demonstrated that HITS-sampled datasets yield a more consistent ranking of AV models across different random seeds and evaluation splits [6]. This addresses the instability caused by conventional sampling methods where topic leakage can disproportionately influence performance metrics.
The creation of the Robust Authorship Verification bENchmark (RAVEN) is a direct outcome of the HITS methodology. RAVEN incorporates a "topic shortcut test" specifically designed to uncover and quantify an AV model's reliance on topic-specific features, thereby ensuring that evaluated performance reflects genuine style learning [6] [7].
Table 1: Core Concepts of the HITS Evaluation Framework
| Concept | Description | Function in Evaluation |
|---|---|---|
| Topic Leakage | The presence of topic-related signals in test data that allow models to make decisions based on content rather than writing style [6]. | Causes inflated and misleading performance metrics, undermines evaluation validity. |
| HITS Sampling | A method for creating a smaller dataset with a controlled, heterogeneous distribution of topics [6]. | Mitigates topic leakage, leading to more stable model rankings across different data splits. |
| RAVEN Benchmark | The Robust Authorship Verification bENchmark, enabling topic shortcut tests [6] [7]. | Provides a standardized testbed to uncover model reliance on topic-specific features. |
Experimental Protocol for HITS Implementation
Dataset Construction and Topic Analysis
- Objective: To create an evaluation split resistant to topic-based shortcuts.
- Procedure:
- Topic Annotation: Begin with a corpus where each document is associated with one or more thematic topics. The PAN-CLEF datasets, often based on Reddit comments, serve as a suitable foundation [37].
- Topic Stratification: Analyze the topic distribution across the entire corpus. The goal is to understand the natural clustering of documents by subject matter.
- Heterogeneity-Informed Sampling: Instead of random sampling, strategically select documents to form the test set. This selection ensures that the test set contains a diverse and heterogeneous mix of topics, preventing any single topic from dominating and creating a leakage pathway.
- Validation Split Creation: Apply the same HITS principle to create a validation set, ensuring consistency in the evaluation framework.
Model Training and Evaluation
- Objective: To train and evaluate AV models on HITS-processed data for a robust assessment.
- Procedure:
- Training: Train the AV models using a training set that is topic-disjoint from the HITS-sampled test and validation sets.
- Cross-Topic Evaluation: Evaluate model performance (e.g., using F1-score) exclusively on the HITS-sampled test set [37].
- Stability Assessment: Repeat the evaluation across multiple random seeds and HITS-sampled splits. The key metric is the stability of model rankings across these iterations, not just absolute performance.
- Topic Shortcut Test: Utilize the RAVEN benchmark to perform a targeted analysis of the model's susceptibility to topic cues [6].
The following diagram illustrates the core workflow of the HITS methodology, from data preparation to final evaluation.
The Scientist's Toolkit: Research Reagent Solutions
The effective application of the HITS methodology relies on a suite of computational "reagents" and benchmarks. The table below details the essential components for conducting rigorous cross-topic authorship verification research.
Table 2: Essential Research Toolkit for HITS-based Authorship Verification
| Tool/Resource | Type | Primary Function |
|---|---|---|
| RAVEN Benchmark [6] [7] | Software/Dataset | Provides a standardized benchmark with built-in topic shortcut tests to diagnose model reliance on topical features. |
| PAN-CLEF Datasets [37] | Dataset | Supplies real-world, multi-topic text data (e.g., from Reddit) that are essential for training and evaluating AV models in a cross-topic setting. |
| HITS Sampling Script | Algorithm | The core implementation of the Heterogeneity-Informed Topic Sampling algorithm for creating robust evaluation splits. |
| F1-Score Evaluator [37] | Metric | The standard quantitative metric for evaluating authorship verification and style change detection performance. |
Advanced Analysis and Visualization of the HITS Advantage
The primary advantage of HITS is its ability to produce a more reliable and stable evaluation environment. The diagram below contrasts the conventional evaluation pathway, which is vulnerable to topic leakage, with the HITS-controlled pathway, which forces the model to rely on genuine stylistic features.
The implementation of HITS represents a paradigm shift in how the authorship verification community approaches evaluation. By moving from a paradigm that simply assumes topic-disjoint data to one that actively controls for and measures topic influence, HITS and the accompanying RAVEN benchmark provide a more rigorous, reliable, and scientifically sound foundation for advancing the field of computational stylometry [6] [7]. This methodology ensures that progress in AV model development is measured by genuine improvements in style recognition, not by the inadvertent exploitation of topical artifacts.
Addressing Data Imbalance and Short Text Length in Clinical Case Reports
The analysis of clinical case reports presents significant methodological challenges, primarily due to two inherent characteristics: severe class imbalance and short text length. In clinical datasets, certain medical conditions or patient outcomes are naturally rare, leading to a distribution where minority classes are vastly outnumbered by majority classes [38]. Concurrently, the concise, telegraphic nature of clinical narratives often results in abbreviated text entries that lack the contextual richness found in longer documents [39]. When these two challenges intersect within cross-topic authorship verification experimental protocols, they create a complex research environment where traditional analytical models tend to exhibit bias toward majority classes and struggle to extract meaningful stylistic and semantic patterns from limited textual content. This application note provides detailed methodologies to address these dual challenges, enabling more robust and reliable analysis of clinical case reports for authorship verification and classification tasks.
The Dual Challenge in Clinical Text Analysis
Class Imbalance in Medical Data
Class imbalance in medical datasets arises from several intrinsic sources. Bias in data collection occurs when certain patient groups are underdiagnosed or underrepresented in research cohorts. The prevalence of rare medical conditions naturally creates imbalance, with some diseases occurring in ratios as extreme as 1 per 100,000 in the population. Longitudinal studies contribute to imbalance through patient attrition or disease progression over time. Finally, data privacy and ethical concerns can limit access to sensitive health information, further exacerbating distribution skewness [38].
The imbalance ratio (IR), calculated as IR = N_maj/N_min, where N_maj and N_min represent the number of instances in the majority and minority classes respectively, quantifies the severity of distribution skew. In clinical practice, high imbalance ratios cause conventional machine learning algorithms to prioritize majority classes, potentially leading to grave consequences such as misclassifying at-risk patients as healthy and resulting in inappropriate discharge or treatment delays [38].
Short Text Characteristics in Clinical Documentation
Clinical case reports typically exhibit distinctive textual characteristics that complicate analysis. These documents often contain telegraphic phrasing with omitted grammatical elements, extensive use of medical abbreviations and acronyms, formulaic structures following standardized reporting templates, and high information density with minimal contextual elaboration [39] [40]. The combination of these traits with class imbalance creates a particularly challenging analytical scenario where limited textual evidence must be leveraged to identify patterns for rare classes.
Methodological Approaches
Keyword-Enhanced Classification for Imbalance Mitigation
The keyword-enhanced approach addresses class imbalance by incorporating short, class-representative text sequences during model training. This methodology consists of two primary components: keyword generation and integrated training [39].
Table 1: Keyword Generation Methods
| Method | Description | Data Source | Advantages |
|---|---|---|---|
| Concept Unique Identifiers (CUI) | Extracts preferred terms and synonyms from medical knowledge bases | NCI Thesaurus, UMLS Metathesaurus | Leverages authoritative medical terminology; High clinical validity |
| Normalized Pointwise Mutual Information (NPMI) | Ranks unigrams/bigrams by statistical association with classes | Training corpus | Requires no external resources; Adaptable to specific corpus characteristics |
The implementation follows a structured protocol:
Keyword Generation via NPMI:
- Represent each token (unigram) and bigram as binary random variables (present/absent) for each document
- Calculate NPMI score for each token-class pair using the formula: NPMI = -1/log(p(x,y)) × log(p(x,y)/(p(x)p(y))) where each probability is estimated using occurrence counts from the training corpus
- Retain the top 10 unigrams and bigrams by NPMI score for each class
Integrated Training Procedure:
- For each training mini-batch:
- Calculate standard cross-entropy loss from training samples (Ldocs)
- Randomly sample NC classes (typically 128, matching batch size)
- From each selected class, randomly sample K keyword segments (K=5 optimal)
- Join K keyword segments into a single "keyword document" per class
- Calculate cross-entropy loss from keyword documents (Lkey)
- Perform back-propagation using combined loss: L = L_docs + αL_key (α=1 optimal)
This approach significantly boosts model performance on rare classes without compromising performance on well-represented classes, as demonstrated through increased macro F1 scores in cancer pathology classification tasks [39].
Pattern Discovery and Disentanglement for Imbalanced Clinical Data
The Clinical Pattern Discovery and Disentanglement (cPDD) method addresses imbalance by discovering statistically significant high-order patterns from clinical data, even for rare classes [41]. This interpretable approach identifies distinctive patterns in minority classes that might be obscured in conventional analysis.
Table 2: cPDD Workflow Components
| Component | Function | Output |
|---|---|---|
| Attribute-Value Association Frequency Matrix (AVAFM) | Captures co-occurrence frequencies of attribute value pairs | Frequency matrix of AVA relationships |
| Statistical Residual Vector Space (SRV) | Converts frequencies to statistical residuals measuring deviation from independence | Significance-weighted vector space |
| Principal Component Decomposition (PCD) | Decomposes SRV into orthogonal principal components | Disentangled pattern spaces |
| AV-Clusters | Groups strongly associated attributes within principal components | Interpretable clinical patterns |
The cPDD protocol implementation:
- Construct AVAFM: Build frequency matrix of attribute-value associations (AVAs) across all clinical cases
- Calculate Statistical Residuals: Convert frequencies to adjusted statistical residuals accounting for deviation from independence model
- Perform Principal Component Decomposition: Decompose the SRV into orthogonal principal components to disentangle entangled patterns
- Select Disentangled Spaces: Retain components where maximum statistical residual exceeds threshold (e.g., 1.44 for 85% confidence)
- Discover AV-Clusters: Identify attribute-value clusters within each disentangled space representing orthogonal clinical patterns
- Classification: Use discovered patterns to classify clinical cases even with imbalanced distributions
This method successfully discovers succinct pattern sets with comprehensive coverage, improving both interpretability and prediction accuracy for rare classes [41].
Ensemble Strategies for Rare Class Emphasis
Class-specialized ensemble techniques provide another effective approach for addressing severe imbalance in clinical text classification. Unlike traditional ensembles that typically improve performance on majority classes, specialized ensembles focus on enhancing rare class identification [42].
The protocol for class-specialized ensemble construction:
- Partition Training Data: Split training data by class frequency into:
- Majority classes (high-frequency)
- Middle-frequency classes
- Rare classes (low-frequency)
- Train Specialist Models:
- Develop individual classifiers optimized for each frequency partition
- Incorporate architectural variations appropriate for each subset
- Implement Aggregation Strategy:
- Employ weighted voting based on class-specific performance
- Use stacking with meta-learners to combine specialist predictions
- Apply confidence-based model selection at inference time
This approach has demonstrated superior performance for rare cancer type classification in out-of-distribution datasets, particularly when measured by macro F1 scores [42].
Integrated Experimental Protocol for Cross-Topic Authorship Verification
The following integrated protocol addresses both data imbalance and short text challenges specifically within cross-topic authorship verification frameworks for clinical case reports.
Data Preparation and Preprocessing
Clinical Text Acquisition:
- Source clinical case reports from electronic health records with proper governance
- Extract and de-identify text following HIPAA compliance protocols
- Maintain metadata including authorship, medical specialty, and report type
Text Normalization:
- Expand standard medical abbreviations using curated dictionaries
- Segment compound medical terms into constituent elements
- Standardize formatting while preserving stylistic elements relevant to authorship
Class Imbalance Quantification:
- Calculate imbalance ratio (IR) for each authorship class
- Identify rare authors (IR > 100:1) and medium-frequency authors
- Partition data into training, validation, and test sets preserving imbalance characteristics
Feature Engineering for Short Clinical Texts
Stylometric Feature Extraction:
- Calculate sentence length distributions and punctuation frequency patterns
- Extract lexical richness metrics (type-token ratios)
- Identify preferred syntactic constructions and grammar patterns
Semantic Feature Extraction:
- Generate domain-specific embeddings from clinical corpora
- Extract topic distributions using clinical concept models
- Capture document-level semantic coherence metrics
Structural Feature Extraction:
- Quantify section organization patterns
- Measure information density per section
- Capture template adherence variations
Model Architecture and Training
Figure 1: Integrated Architecture for Authorship Verification
The recommended architecture combines multiple feature types within a Siamese network framework optimized for clinical text verification [5] [43].
Cross-Topic Evaluation Protocol
Topic-Leakage Prevention:
Imbalance-Aware Validation:
- Employ stratified cross-validation preserving authorship distribution
- Utilize macro F1 scores as primary evaluation metric rather than accuracy
- Calculate per-class performance metrics to identify specific weaknesses
The Scientist's Toolkit: Essential Research Reagents
Table 3: Research Reagent Solutions for Clinical Text Analysis
| Reagent Category | Specific Tools | Function | Application Context |
|---|---|---|---|
| Medical Knowledge Bases | NCI Thesaurus, UMLS Metathesaurus | Provides standardized medical terminology for keyword generation | CUI-based keyword enhancement [39] |
| Text Processing Libraries | spaCy Clinical, NLTK with clinical extensions | Tokenization, POS tagging, and syntactic parsing of clinical text | Stylometric and structural feature extraction [5] |
| Embedding Models | ClinicalBERT, BioWordVec | Domain-specific semantic representations | Semantic feature extraction [5] |
| Imbalance Algorithms | cPDD implementation, SMOTE variants | Address class distribution skew | Pattern discovery and data-level balancing [41] |
| Deep Learning Frameworks | PyTorch, TensorFlow with custom layers | Siamese network implementation | Model architecture development [43] |
| Evaluation Benchmarks | RAVEN, PAN-CLEF datasets | Standardized evaluation frameworks | Cross-topic authorship verification testing [6] |
Visualizing the Integrated Workflow
Figure 2: End-to-End Analysis Workflow
This application note provides comprehensive methodologies for addressing the dual challenges of data imbalance and short text length in clinical case reports within cross-topic authorship verification research. The integrated approaches—keyword-enhanced training, pattern discovery and disentanglement, and class-specialized ensembles—collectively enable more robust analysis of clinical texts despite their inherent limitations. The provided experimental protocols and reagent toolkit offer researchers practical resources for implementing these approaches in real-world clinical authorship verification scenarios. By adopting these methodologies, researchers can develop more accurate and reliable systems for clinical text analysis that maintain performance across diverse authorship classes and clinical topics.
Mitigating Over-reliance on Topic-Specific Features for Generalizable Models
The "Clever Hans effect" poses a significant challenge to developing reliable artificial intelligence systems, particularly in domains requiring robust generalization. This phenomenon occurs when machine learning models learn spurious correlations with topic-specific features rather than the underlying semantics or style they were intended to capture [44]. In authorship verification (AV), this manifests as models exploiting topic leakage between training and test data, where apparent high performance masks reliance on topic-specific vocabulary and contextual features rather than genuine stylistic patterns [6] [7]. Such overreliance creates models with inflated performance metrics that fail catastrophically when presented with out-of-topic texts, undermining their real-world applicability and scientific validity.
The challenge is particularly acute in cross-topic authorship verification, where models must identify authors based on writing style while generalizing across disparate subject matters. Conventional evaluations assume minimal topic overlap, yet residual topic leakage in test data can create misleading performance benchmarks and unstable model rankings [6]. This paper establishes comprehensive protocols for detecting and mitigating this overreliance, enabling development of more generalizable models through rigorous evaluation frameworks and targeted intervention strategies.
Detection Methodologies
Experimental Framework for Shortcut Detection
Systematic detection of topic feature overreliance requires multiple complementary approaches to identify spurious correlations and quantify their impact on model generalization. The experimental framework should implement the following key detection methodologies:
Table 1: Detection Methods for Topic Feature Overreliance
| Method Category | Specific Techniques | Key Measurements | Interpretation of Positive Result |
|---|---|---|---|
| Model-Centric Approaches | Performance replication and feature generalization [44] | Performance drop on external datasets; Worst-group accuracy | Model fails to generalize due to source-specific feature reliance |
| Identifying confounding factors via Structural Causal Models (SCMs) [44] | Causal impact of confounders (e.g., intensity, texture) | Model predictions correlate with non-clinically relevant confounders | |
| Model interpretation techniques (Grad-CAM, SHAP) [44] | Feature importance scores; Attribution maps | High attribution to topic-specific rather than stylistic features | |
| Data-Centric Approaches | Dataset bias abduction [44] | Performance variance across biased subsets | Systematic performance differences across demographic/source subsets |
| Attribution maps and shortcut detection [44] | Visual patterns in feature activation | Activation clusters around topic words rather than stylistic markers | |
| Occlusion tests [44] | Performance change when removing topic words | Significant performance degradation when topic vocabulary is masked | |
| Uncertainty & Bias Methods | Counterfactual explanations [44] | Prediction changes with minimal topic alterations | Model predictions flip with minor topic changes despite style preservation |
| Fairness as proxies [44] | Performance disparities across topics | Consistent performance gaps between different topic domains |
Protocol: Heterogeneity-Informed Topic Sampling (HITS)
The HITS methodology addresses topic leakage in evaluation datasets by creating heterogeneously distributed topic sets that enable more stable model rankings and robust performance assessment [6].
Experimental Protocol:
- Topic Modeling: Apply Latent Dirichlet Allocation (LDA) or BERTopic to the full corpus to identify latent topic structures across all documents.
- Heterogeneity Scoring: Calculate topic distribution heterogeneity using Shannon entropy or Gini impurity across potential evaluation splits.
- Stratified Sampling: Implement weighted sampling that maximizes topic heterogeneity in each evaluation fold while maintaining class balance.
- Stability Validation: Execute multiple random sampling iterations with HITS constraints, measuring model ranking consistency across samples using Kendall's W coefficient.
- Performance Benchmarking: Compare traditional cross-validation results with HITS-evaluated performance to quantify topic reliance gap.
Quantitative Metrics:
- Topic heterogeneity index (THI):
THI = 1 - |topic_distribution_entropy - maximum_entropy|/maximum_entropy - Model ranking stability: Kendall's W coefficient across random seeds
- Topic reliance gap:
Δ = Performance_standard - Performance_HITS
Mitigation Strategies
Data-Centric Interventions
Data manipulation techniques directly address topic bias in training data to reduce models' reliance on spurious topic correlations:
Table 2: Data-Centric Mitigation Strategies
| Strategy | Implementation Protocol | Key Parameters | Validation Metrics |
|---|---|---|---|
| Data Balancing & Preprocessing [44] | Topic-aware stratified sampling; Adversarial topic debiasing | Topic distribution ratio; Debiasing strength λ | Topic classification accuracy decrease; Cross-topic performance gap reduction |
| Data Augmentation [44] | Topic-neutral paraphrasing; Style-transfer based topic masking; Vocabulary substitution | Augmentation multiplier; Topic neutrality threshold | Topic classifier confidence; Style preservation rate |
| Domain-Specific Preprocessing [44] | Topic-signal filtering; Domain-adaptive tokenization | Topic word exclusion list; Domain similarity threshold | Topic signal strength reduction; Cross-domain consistency |
Protocol: Topic-Neutral Data Augmentation
- Topic Word Identification: Use TF-IDF and topic modeling to identify high-salience topic-specific vocabulary within each document.
- Controlled Paraphrasing: Implement masked language model-based paraphrasing that preserves stylistic markers while altering topic expressions.
- Vocabulary Substitution: Replace topic-specific terms with semantically similar but topic-neutral alternatives using semantic similarity thresholds (>0.7 cosine similarity).
- Style Preservation Validation: Verify augmented texts maintain authorship style through auxiliary style classification tasks.
- Topic Neutrality Assessment: Measure reduction in topic classification accuracy on augmented texts compared to originals.
Model-Centric Interventions
Model architecture modifications and training procedures can actively discourage reliance on topic-specific features:
Protocol: Feature Disentanglement and Suppression
Multi-Task Adversarial Learning:
- Implement parallel topic classification head with gradient reversal layer
- Train with adversarial loss:
L_total = L_AV + λ * L_topicwhere λ is negative - Gradually increase adversarial weight λ through training
Information Bottleneck Regularization:
- Apply variational information bottleneck to minimize mutual information between latent representations and topic labels
- Optimize:
L_IB = L_AV + β * I(Z;X) - γ * I(Z;Y)where Y represents authorship - Set γ > β to preserve authorship information while discarding topic information
Attention-Based Shortcut Suppression:
- Implement attention mechanism with topic penalty term
- Apply regularization to attention weights assigned to topic-specific tokens
- Use guided backpropagation to identify and suppress topic-focused attention patterns
Validation Metrics:
- Topic disentanglement score:
1 - (|topic_prediction_accuracy - 0.5| * 2) - Style preservation accuracy: Auxiliary authorship classification performance
- Cross-topic generalization gap: Performance difference between in-topic and out-of-topic tests
Visualization Framework
Topic Leakage Detection Workflow
Diagram 1: Topic leakage detection workflow integrating multiple methodologies.
HITS Evaluation Methodology
Diagram 2: HITS methodology for robust cross-topic evaluation.
Research Reagent Solutions
Table 3: Essential Research Tools for Robust Authorship Verification
| Research Reagent | Specifications | Primary Function | Validation Metrics |
|---|---|---|---|
| RAVEN Benchmark [6] | Robust Authorship Verification bENchmark; HITS-sampled dataset | Topic-shortcut testing; Cross-topic generalization assessment | Model ranking stability; Topic reliance quantification |
| HITS Sampling Tool [6] | Heterogeneity-Informed Topic Sampling; Python implementation | Create heterogeneously distributed topic sets | Topic heterogeneity index; Cross-seed performance variance |
| Structural Causal Models [44] | Bayesian networks with confounder explicit modeling | Disentangle confounding factors (intensity, texture) | Causal impact quantification; Confounder effect size |
| Adversarial Debiasing Framework | Gradient reversal layers; Multi-task architecture | Active suppression of topic feature reliance | Topic classification accuracy decrease; Cross-topic performance preservation |
| Style-Topic Disentanglement Metrics | Mutual information estimators; Auxiliary classifiers | Quantify style purity and topic independence | Disentanglement scores; Feature attribution divergence |
| Topic Occlusion Tools | Vocabulary masking; Pattern replacement | Controlled removal of topic signals | Performance degradation curves; Topic salience measures |
Mitigating overreliance on topic-specific features requires systematic implementation of detection and mitigation strategies throughout the model development lifecycle. The HITS evaluation methodology provides a foundation for robust benchmarking, while the described detection protocols enable comprehensive identification of topic shortcut learning [6]. Successful implementation requires:
- Proactive Topic Leakage Assessment: Integrate HITS sampling during evaluation phase rather than as post-hoc analysis
- Multi-Method Detection: Combine model-centric, data-centric, and bias-based approaches for comprehensive coverage
- Iterative Mitigation: Apply data manipulation and model architecture interventions in feedback loop
- Validation Rigor: Employ multiple metrics focusing on cross-topic generalization and model stability
These protocols establish a standardized framework for developing authorship verification models that genuinely capture stylistic patterns rather than exploiting topic shortcuts, enabling more reliable and generalizable applications across domains with shifting topical content.
Benchmarks, Metrics, and Model Comparison: Establishing Gold Standards for Cross-Topic AV
Background and Rationale
Topic leakage presents a significant challenge in cross-topic authorship verification (AV), where the goal is to determine whether two texts share the same author. The conventional evaluation paradigm assumes minimal topic overlap between training and test data. However, unintended topic correlations can persist in test data, creating misleading performance metrics and unstable model rankings. This phenomenon, termed "topic leakage," occurs when models exploit topic-specific features rather than genuine stylistic patterns, compromising their real-world applicability and robustness to topic shifts [6] [7].
The Robust Authorship Verification bENchmark (RAVEN) was developed specifically to address this critical evaluation gap. It functions as a diagnostic tool to uncover AV models' reliance on topic-specific features through controlled topic shortcut tests. By systematically exposing shortcut learning, RAVEN enables researchers to distinguish between models that genuinely capture authorial style and those that leverage spurious topic correlations, thereby fostering the development of more reliable AV systems [6].
The RAVEN Benchmark: Core Components and Design
The RAVEN benchmark is constructed around the principle of heterogeneity-informed topic sampling. Its primary objective is to create evaluation conditions where topic shortcuts are minimized, forcing models to rely on genuine stylistic cues for authorship attribution.
Table 1: Core Components of the RAVEN Benchmark
| Component | Description | Function in Shortcut Testing |
|---|---|---|
| Heterogeneous Topic Set | A carefully sampled, diverse collection of topics with balanced distribution. | Prevents models from exploiting dominant topic themes, ensuring stable model rankings. |
| Topic Shortcut Tests | Controlled experiments designed to isolate and measure reliance on topic features. | Diagnoses whether models use topic cues (shortcuts) or stylistic features for verification. |
| Cross-Topic Splits | Training and test data splits engineered to minimize thematic overlap. | Evaluates model robustness to unseen topics and generalizability of stylistic features. |
Experimental Protocol: Heterogeneity-Informed Topic Sampling (HITS)
The Heterogeneity-Informed Topic Sampling (HITS) methodology is central to the RAVEN benchmark's operation, providing a systematic approach to create a robust evaluation dataset [6].
The following diagram illustrates the end-to-end HITS workflow for constructing a benchmark dataset that mitigates topic leakage.
Step-by-Step Protocol
Raw Text Collection & Topic Analysis
- Gather a large, diverse corpus of documents with known authorship.
- Perform topic modeling (e.g., LDA, BERTopic) or manual annotation to identify and categorize the main themes present in the corpus.
- Output: A comprehensive list of all identified topics and their prevalence in the corpus.
Topic Distribution Assessment
- Analyze the initial topic distribution to identify potential imbalances or dominant themes that could lead to topic leakage in standard random splits.
HITS Application
- Employ the HITS algorithm to sample a subset of topics. The algorithm prioritizes creating a heterogeneous topic set that is balanced and representative, rather than simply large.
- This step intentionally avoids topics that are over-represented in the original corpus to prevent shortcut learning.
Dataset Construction
- Using the HITS-sampled topic set, create balanced document pairs for the authorship verification task.
- Formally establish training, validation, and test splits with minimal topic overlap between them. This enforces a strict cross-topic evaluation setting.
Model Evaluation
- Train and evaluate AV models on the constructed RAVEN benchmark.
- Compare model performance on RAVEN against performance on benchmarks created with conventional random sampling. A significant performance drop on RAVEN indicates prior reliance on topic shortcuts.
The Scientist's Toolkit: Essential Research Reagents
Table 2: Key Research Reagents for RAVEN Benchmark Implementation
| Tool/Reagent | Type/Category | Function in the Protocol |
|---|---|---|
| Text Corpus with Author Labels | Dataset | The foundational data required for analysis; must cover multiple authors and topics. |
| Topic Modeling Algorithm (e.g., LDA) | Computational Tool | Automatically identifies and categorizes latent themes within the text corpus. |
| HITS Sampling Algorithm | Computational Method | Selects a heterogeneous, balanced set of topics to construct a robust test set. |
| Authorship Verification Model (e.g., NN-based, SVM) | Model Under Test | The system whose robustness is being evaluated for true stylistic learning. |
| Standard Benchmark (e.g., random-split dataset) | Baseline Dataset | Serves as a control to contrast performance and reveal topic shortcut reliance. |
Visualizing the Topic Leakage Problem and Solution
The core issue RAVEN addresses is illustrated in the following diagram, which contrasts standard evaluation (prone to leakage) with the HITS-informed evaluation.
Expected Outcomes and Interpretation
Implementation of the RAVEN benchmark via the HITS protocol yields two critical outcomes:
- Stable Model Rankings: The benchmark produces a more reliable and consistent ranking of different AV models across multiple random seeds and data splits, as it removes the confounding variable of topic leakage [6].
- Accurate Robustness Assessment: It correctly identifies the degree to which a model relies on topic shortcuts versus genuine stylistic features. A model whose performance drastically decreases on RAVEN compared to a standard benchmark was likely exploiting topic information and is less robust for real-world, cross-topic applications.
By adopting the RAVEN benchmark and the HITS methodology, researchers can ensure their evaluations of authorship verification models are both rigorous and reflective of true generalization ability, thereby accelerating the development of more reliable and trustworthy text analysis systems.
Within the domain of cross-topic authorship verification, the selection of an appropriate machine learning approach is paramount for building robust models that generalize well to texts on unseen topics. This application note provides a detailed comparative analysis of traditional machine learning and neural network-based approaches, framed within experimental protocols for authorship verification research. It summarizes quantitative performance data, outlines detailed experimental methodologies, and provides essential workflows and reagent solutions to guide researchers and scientists in the drug development sector, where automated analysis of scientific literature and clinical narratives is increasingly critical.
The following tables consolidate key quantitative findings and characteristics from comparative studies on traditional and neural network-based models.
Table 1: Comparative Performance Metrics on Classification Tasks
| Model Category | Specific Model | Dataset/Task | Accuracy / F1-Score | Key Reference |
|---|---|---|---|---|
| Ensemble (Traditional) | Proposed Ensemble Learning | "All the news" (10 authors) | 3.14% accuracy gain (vs. baseline) | [45] |
| Neural Network | DistilBERT | "All the news" (10 authors) | 2.44% accuracy gain (vs. baseline) | [45] |
| Ensemble (Traditional) | Proposed Ensemble Learning | "All the news" (20 authors) | 5.25% accuracy gain (vs. baseline) | [45] |
| Neural Network | DistilBERT | "All the news" (20 authors) | 7.17% accuracy gain (vs. baseline) | [45] |
| Neural Network | DistilBERT | Dutch Financial Ledgers (RCSFI L1-4) | 94.50% F1-Score | [46] |
Table 2: Operational Characteristics of Model Types
| Characteristic | Traditional Machine Learning | Neural Networks |
|---|---|---|
| Data Requirements | Works well with smaller, structured data [47] | Requires large datasets (thousands/millions of examples) [47] |
| Feature Engineering | Requires manual feature selection and engineering [47] | Learns features automatically from raw data [47] |
| Computational Load | Lower; can run on standard CPUs [48] | High; typically requires powerful GPUs/TPUs [47] [48] |
| Interpretability | Higher; models are generally more transparent [47] [49] | Lower; often considered a "black box" [47] [48] |
| Training Time | Faster training and validation cycles [48] | Can take days to weeks, depending on complexity [48] |
Experimental Protocols
Protocol 1: Data Preparation and Feature Engineering for Traditional ML
Objective: To prepare a dataset of text documents for authorship verification using traditional machine learning models by extracting stylometric and linguistic features.
Materials: Refer to Section 5.1, "Research Reagent Solutions."
Procedure:
- Data Acquisition and Labeling: Collect a corpus of text documents. For authorship verification, this typically involves pairs of documents with a binary label indicating whether they were written by the same author. Ensure metadata on document topics is available for cross-topic evaluation splits [6].
- Text Pre-processing: a. Clean the text by removing extraneous characters, headers, and footers. b. Perform tokenization to split text into words and sentences. c. Apply lowercasing and remove stop-words. d. Apply lemmatization or stemming to normalize words.
- Feature Extraction: a. Lexical Features: Extract character-level (e.g., average word length, character n-grams) and word-level features (e.g., vocabulary richness, word n-grams) [45]. b. Syntactic Features: Use part-of-speech (POS) tagging to extract grammar patterns and punctuation frequency counts [45]. c. Content-Specific Features: Apply a count vectorizer or bi-gram Term Frequency-Inverse Document Frequency (TF-IDF) to capture topic-related word usage [45].
- Train-Test Split with Cross-Topic Validation: a. Split the dataset into training and test sets, ensuring that documents from specific topics are entirely contained within either the training or test set to create a cross-topic evaluation scenario [6]. b. To mitigate topic leakage, which can cause misleading performance, consider advanced sampling methods like Heterogeneity-Informed Topic Sampling (HITS) [6].
- Feature Scaling: Normalize or standardize the extracted features to ensure that models are not biased by the scale of individual features.
Protocol 2: Model Training and Validation for Traditional ML
Objective: To train and validate traditional machine learning models for authorship verification using robust validation techniques.
Materials: Refer to Section 5.1, "Research Reagent Solutions."
Procedure:
- Model Selection: Choose one or more traditional algorithms. Common choices include:
- Model Training: a. Train the selected model(s) on the feature-engineered training dataset. b. For ensemble methods like Random Forest and XGBoost, the model will build multiple decision trees during this phase [46].
- Model Validation: a. Hold-Out Validation: Use a standard train/test split (e.g., 70/30 or 80/20) for an initial performance estimate [51]. b. K-Fold Cross-Validation: For a more reliable estimate, especially with smaller datasets, use k-fold cross-validation (typically k=5 or 10). The dataset is split into k folds, with each fold used once as a validation set while the remaining k-1 folds form the training set [51] [52]. c. Performance Metrics: Calculate accuracy, precision, recall, and F1-score on the validation set. The model with the best performance on the validation set is selected for final testing [52] [50].
Protocol 3: End-to-End Workflow for Neural Networks
Objective: To implement a neural network-based authorship verification system using pre-trained transformer models like DistilBERT.
Materials: Refer to Section 5.2, "Research Reagent Solutions."
Procedure:
- Data Preparation: a. Perform minimal text cleaning (e.g., remove unwanted characters). b. For transformer models, split the data into training, validation, and test sets, adhering to a strict cross-topic split to prevent topic leakage [6] [46].
- Text Tokenization:
a. Use the tokenizer corresponding to the pre-trained model (e.g., DistilBERT tokenizer).
b. Tokenize the text, which involves converting words into sub-word tokens and adding special tokens (e.g.,
[CLS],[SEP]). c. Pad or truncate the token sequences to a uniform length. - Model Configuration & Transfer Learning: a. Load a pre-trained model architecture (e.g., DistilBERT) suitable for sequence classification. b. Add a custom classification layer on top of the pre-trained base model to output the final verification decision (same author/different author).
- Model Training: a. Define training hyperparameters (e.g., learning rate, batch size, number of epochs). b. Train the model on the training set. The process involves fine-tuning the pre-trained weights on the specific task of authorship verification. Utilize a separate validation set for early stopping to prevent overfitting [52] [50].
- Model Evaluation: a. Use the held-out test set, which contains unseen topics, to evaluate the model's generalization ability. b. Report standard classification metrics (accuracy, F1-score, etc.). The unbiased evaluation performed on this set provides the final performance characteristics [52].
Workflow and Signaling Diagrams
The following diagrams illustrate the core experimental workflows for the two primary approaches.
Traditional ML Workflow for Authorship Verification
Neural Network Workflow for Authorship Verification
The Scientist's Toolkit
Research Reagent Solutions for Traditional ML
Table 3: Essential Tools and Materials for Traditional ML Protocols
| Item | Function/Description | Example Use Case in Protocol |
|---|---|---|
| Scikit-learn | A comprehensive open-source library for machine learning in Python. Provides tools for data pre-processing, model training, and validation [51]. | Implementing Logistic Regression, Random Forest, and train-test splits. |
| NLTK / SpaCy | Natural Language Processing (NLP) libraries used for advanced text pre-processing and linguistic feature extraction [45]. | Tokenization, lemmatization, and part-of-speech tagging for syntactic features. |
| Count Vectorizer / TF-IDF Vectorizer | Algorithms to convert text into numerical feature vectors based on word counts or term frequency-inverse document frequency [45]. | Extracting content-specific features from the text corpus. |
| K-Fold Cross-Validator | A model validation technique that splits data into 'k' consecutive folds to robustly estimate model performance [51] [52]. | Providing a reliable performance metric for model selection in Protocol 2. |
| SMOTE (Synthetic Minority Over-sampling Technique) | A pre-processing technique to address class imbalance by generating synthetic samples for the minority class [46]. | Balancing the dataset if the "same author" class is underrepresented. |
Research Reagent Solutions for Neural Networks
Table 4: Essential Tools and Materials for Neural Network Protocols
| Item | Function/Description | Example Use Case in Protocol |
|---|---|---|
| Transformers Library (Hugging Face) | A library providing thousands of pre-trained models (e.g., BERT, DistilBERT) for NLP tasks [45] [46]. | Loading the base DistilBERT model and its tokenizer for transfer learning. |
| PyTorch / TensorFlow | Open-source deep learning frameworks that provide the foundation for building and training neural networks [47] [45]. | Defining the model architecture, loss function, and training loop. |
| GPU (Graphics Processing Unit) | Specialized hardware that dramatically accelerates the matrix calculations central to neural network training and inference [47] [53]. | Fine-tuning the transformer model in a feasible amount of time. |
| Pre-trained Tokenizer | A component that converts raw text into the specific token IDs and attention masks expected by the corresponding pre-trained model [46]. | Preparing the input text data for the transformer model in Protocol 3. |
| Early Stopping Callback | A training regularization technique that halts training when validation performance stops improving, preventing overfitting [52] [50]. | Monitoring the validation loss during training to find the optimal stopping point. |
Evaluating Generalizability and Robustness Across Diverse Topics and Writing Styles
Authorship Verification (AV) is a critical task in Natural Language Processing with applications in plagiarism detection, content authentication, and forensic analysis. The fundamental challenge lies in developing models that can reliably determine whether two texts share the same author based on writing style alone, independent of topic-specific cues. Current research reveals that generalizability across domains remains a significant hurdle, as models often exploit spurious correlations from topic leakage rather than learning genuine stylistic representations.
The robustness of AV systems is compromised when models rely on topic-specific features (e.g., named entities and domain-specific vocabulary) rather than authentic stylistic patterns. Studies demonstrate that conventional evaluations often contain subtle topic overlaps between training and test data, creating an "illusion of performance" that vanishes under truly cross-topic conditions. This application note establishes protocols for rigorous evaluation of AV models under conditions that better reflect real-world scenarios where topics diverge significantly.
Quantitative Foundations: Data and Performance Metrics
Comparative Performance of AV Approaches
Table 1: Performance comparison of authorship verification methods across different experimental conditions
| Model Architecture | Feature Types | Dataset | Key Strengths | Generalizability Limitations |
|---|---|---|---|---|
| Feature Interaction Network | RoBERTa embeddings + stylistic features | PAN (stylistically diverse) | Combines semantic and stylistic features | Limited by RoBERTa's fixed input length [5] |
| BERT-like baselines | Contextual embeddings | PAN splits with topic isolation | Competitive with state-of-the-art | Biased toward named entities [54] |
| Models without named entities | Purified stylistic features | DarkReddit | Better generalization to new domains | Potential loss of discriminative stylistic markers [54] |
| Siamese Network | RoBERTa + style features | Challenging, imbalanced data | Robust to real-world conditions | Predefined style features may not capture all stylistic nuances [5] |
Dataset Characteristics and Evaluation Metrics
Table 2: Dataset characteristics and evaluation metrics for robustness assessment
| Dataset | Topic Control Method | Size | Stylistic Diversity | Primary Evaluation Metric | Topic Leakage Resistance |
|---|---|---|---|---|---|
| PAN (conventional) | Minimal topic overlap assumption | Large-scale | Homogeneous | AUC-ROC | Low (in conventional splits) [6] |
| PAN (HITS-sampled) | Heterogeneity-Informed Topic Sampling | Smaller, curated | Heterogeneous | AUC-ROC + ranking stability | High [6] |
| DarkReddit | Natural topic variation | Not specified | Diverse from online discourse | Macro F1-score | Moderate [54] |
| RAVEN benchmark | Topic shortcut tests | Not specified | Controlled variation | Specificity to topic shifts | Designed specifically to test [6] |
Experimental Protocols for Robustness Evaluation
Protocol 1: Cross-Topic Evaluation with HITS
Purpose: To evaluate AV model performance under controlled topic shifts while minimizing topic leakage effects.
Methodology:
- Dataset Preparation: Implement Heterogeneity-Informed Topic Sampling to create evaluation datasets with heterogeneously distributed topic sets [6]
- Model Training: Train AV models on source topics with strict separation from target topics
- Evaluation: Test model performance on held-out topics across multiple random seeds and evaluation splits
- Stability Assessment: Measure ranking stability of models across different topic configurations
Key Parameters:
- Number of topic clusters: 5-10 distinct categories
- Sample size per topic: Balanced to ensure representation
- Topic distance metric: Semantic similarity between topic vocabularies
- Evaluation iterations: Minimum of 10 random seeds for statistical significance
Validation Approach:
- Compare performance stability between HITS-sampled datasets and conventional splits
- Measure variance in model rankings across different topic configurations
- Calculate topic leakage index using similarity metrics between training and test topics
Protocol 2: Stylistic Feature Isolation
Purpose: To isolate genuine stylistic features from topic-specific cues in AV models.
Methodology:
- Feature Extraction:
- Feature Ablation: Systematically remove named entities and topic-specific vocabulary [54]
- Cross-Domain Validation: Train on one domain (e.g., formal essays), test on another (e.g., social media posts)
- Explainable AI Analysis: Identify which features contribute most to predictions across different topic domains [54]
Control Measures:
- Implement named entity recognition and removal pipelines
- Use vocabulary overlap metrics between training and test sets
- Apply style-content disentanglement techniques where feasible
Protocol 3: Real-World Stress Testing
Purpose: To evaluate AV performance under challenging, imbalanced conditions that reflect real-world application scenarios.
Methodology:
- Dataset Curation: Assemble datasets with:
- Significant topic divergence between document pairs
- Imbalanced author representation
- Diverse discourse types (academic, creative, technical, informal) [5]
- Model Architecture Testing:
- Evaluate Feature Interaction Networks, Pairwise Concatenation Networks, and Siamese Networks [5]
- Test combination strategies for semantic and stylistic features
- Assess robustness to document length variation and noise
- Adversarial Testing:
- Introduce subtle topic overlaps to test sensitivity
- Add distribution shifts between training and deployment data
- Test on out-of-domain genres completely unseen during training
Evaluation Criteria:
- Performance maintenance under increasing topic divergence
- Degradation patterns with increasing dataset imbalance
- Cross-genre generalization capabilities
Visualization of Experimental Workflows
Cross-Topic Authorship Verification Workflow
Topic Leakage Detection and Mitigation
Research Reagent Solutions for Authorship Verification
Table 3: Essential tools and resources for robust authorship verification research
| Resource Category | Specific Tool/Resource | Function in Research | Implementation Notes |
|---|---|---|---|
| Dataset Resources | PAN Authorship Dataset [54] [8] | Large-scale benchmark for AV | Use proposed splits to isolate topic/style biases |
| DarkReddit Dataset [54] | Cross-domain evaluation | Tests generalization to informal online discourse | |
| RAVEN Benchmark [6] | Topic shortcut testing | Specifically designed for robustness evaluation | |
| Feature Extraction | RoBERTa embeddings [5] | Semantic content representation | Fixed input length limitation noted [5] |
| Stylometric features [5] | Writing style capture | Sentence length, word frequency, punctuation | |
| Named Entity Recognizers | Topic signal identification | Critical for bias detection and removal [54] | |
| Model Architectures | Feature Interaction Network [5] | Combines feature types | Enhanced by style features |
| Siamese Networks [5] | Similarity learning | Effective for pairwise verification tasks | |
| BERT-like baselines [54] | Contextual representations | Competitive but prone to named entity bias | |
| Evaluation Frameworks | HITS methodology [6] | Topic leakage reduction | Creates heterogeneously distributed topic sets |
| Explainable AI techniques [54] | Model decision interpretation | Identifies feature importance and biases | |
| Stability assessment metrics [6] | Robustness quantification | Measures performance consistency across seeds |
The protocols outlined in this document provide a framework for developing and evaluating authorship verification systems with stronger generalizability across topics and writing styles. By addressing topic leakage through rigorous methodologies like HITS, combining semantic and stylistic features, and stress-testing models under realistic conditions, researchers can create more robust AV systems. The continued development of benchmarks like RAVEN and refinement of cross-topic evaluation methodologies will be essential for advancing the field toward real-world applicability where topic independence is crucial for reliable authorship verification.
Establishing Best Practices for Transparent and Reproducible AV Experiments
The rapid advancement of autonomous vehicle (AV) technology necessitates robust experimental frameworks that yield transparent, reproducible, and scientifically valid results. Within the broader context of cross-topic authorship verification experimental protocols research, establishing standardized methodologies for AV experimentation becomes paramount. Just as authorship verification requires rigorous protocols to distinguish genuine authorship signals from topical interference [14], AV experimentation demands meticulous documentation and standardization to separate true performance metrics from experimental artifacts. This document outlines comprehensive application notes and protocols designed to address the unique challenges in AV research, leveraging insights from security frameworks, virtual track methodologies, and reproducibility standards to create a unified approach for researchers, scientists, and development professionals.
The interdisciplinary nature of AV development—spanning computer science, robotics, mechanical engineering, and social sciences—creates distinct challenges for experimental reproducibility. These challenges parallel those found in authorship verification research, where cross-lingual and cross-domain generalization requires carefully controlled experimental conditions [14]. By adapting frameworks from both fields, we can establish best practices that ensure AV research findings are both reliable and generalizable across different testing environments and conditions.
Background and Definitions
Foundational Concepts
Autonomous Vehicle Experimentation involves systematically testing and validating the performance, safety, and reliability of self-driving systems across simulated and real-world environments. These experiments typically evaluate perception, planning, control, and human-machine interaction subsystems under various operational design domains.
Experimental Reproducibility refers to the ability of independent researchers to obtain consistent results using the same experimental setup, data, and methodologies described in original research. As defined by IJCAI guidelines, reproducibility requires that "using the same data and the same analytical tools will yield the same results as reported" [55]. In AV research, this encompasses everything from algorithmic outputs to performance metrics collected in specific environmental conditions.
Virtual Track Methodology represents an innovative approach to AV navigation that creates guiding elements integrated into road surfaces to improve localization accuracy and reliability. These tracks can be optical, magnetic, or based on electrical conductivity, serving as navigational guides that reduce uncertainty associated with environmental variability, changing light conditions, or satellite navigation interference [56].
Current Challenges in AV Experimentation
The autonomous vehicle research landscape faces several significant reproducibility challenges:
- Environmental Variability: Changing weather, lighting, and road conditions introduce uncontrolled variables that complicate experimental replication.
- System Complexity: AV systems comprise numerous interconnected software and hardware components with complex interactions that are difficult to fully document.
- Proprietary Limitations: Key algorithms, datasets, and simulation environments are often protected as intellectual property, limiting access for verification.
- Hardware Dependencies: Performance metrics are heavily influenced by specific sensor configurations, computing hardware, and vehicle platforms.
- Safety Constraints: Real-world testing introduces ethical and practical limitations on the types of experiments that can be conducted.
These challenges mirror those found in authorship verification research, where dataset biases, algorithmic variability, and evaluation methodology differences hinder direct comparison between studies [14]. In both fields, the lack of standardized protocols leads to published results that cannot be properly validated or built upon by the research community.
Quantitative Data Framework
Core Performance Metrics Table
Table 1: Standardized Metrics for AV Experimentation
| Metric Category | Specific Metrics | Target Values | Measurement Methods | Reporting Frequency |
|---|---|---|---|---|
| Localization Accuracy | Lateral error (m), Longitudinal error (m), Heading error (deg) | <0.05m, <0.1m, <1° | GNSS/INS reference, Virtual track alignment [56] | Per test run (min, max, mean, std) |
| Object Detection Performance | Precision, Recall, F1-score, mAP | >0.9, >0.85, >0.87, >0.8 | Bounding box IoU analysis | Per scenario type |
| Planning Reliability | Collision rate, Rule violations, Comfort metrics | <0.001, <0.01, Jerk <2.0 m/s³ | Scenario-based testing, Passenger ratings | Aggregate per 1000km |
| Security Resilience | T-PAAD resistance, Sensor spoofing detection | >95% attack mitigation | Security framework evaluation [57] | Pre-deployment validation |
| Computational Performance | Inference time (ms), Planning cycle time (ms) | <100ms, <200ms | Hardware profiling tools | Continuous monitoring |
Experimental Parameters Documentation
Table 2: Hyperparameter and Configuration Reporting
| Parameter Category | Specific Parameters | Documentation Requirements | Sensitivity Analysis |
|---|---|---|---|
| Perception System | Confidence thresholds, NMS parameters, Feature extractor specs | All threshold values, Architecture diagram, Training dataset description | Required for all primary detection classes |
| Planning System | Prediction horizons, Cost function weights, Optimization iterations | Full cost function formulation, Constraint definitions | Scenario-based sensitivity mapping |
| Control System | PID gains, MPC weights, Filter parameters | Controller type, Stability margins, Performance boundaries | Frequency response analysis |
| Sensor Configurations | Placement, calibration, synchronization | Extrinsic/intrinsic calibration, Time synchronization accuracy | FOV overlap analysis |
| Virtual Track Setup | Type (linear/point), spacing, detection method | Implementation specs, Accuracy claims, Failure modes [56] | GNSS-denied environment performance |
Experimental Protocols
Security Evaluation Protocol
The Security Experimental Framework for Autonomous Vehicles (SEFAV) provides a cross-platform compatible approach for simulating security scenarios in AV environments [57]. This protocol addresses trajectory privacy attacks (T-PAAD) and other security threats through systematic vulnerability assessment.
Materials and Setup:
- SEFAV framework installation (Windows/Linux compatible)
- SUMO/OSM integration for scenario generation
- Attack simulation modules (including T-PAAD implementation)
- Performance monitoring tools
Procedure:
- Baseline Establishment: Execute standard driving scenarios without attacks to establish performance baseline
- Attack Injection: Introduce T-PAAD attacks gradually, monitoring system responses
- Impact Assessment: Quantify degradation in trajectory accuracy, safety metrics, and system stability
- Countermeasure Evaluation: Implement proposed security measures and repeat attack scenarios
- Reporting: Document attack success rates, system resilience, and computational overhead
Data Collection:
- Trajectory deviation metrics under attack conditions
- System recovery time from security incidents
- Resource utilization during attack mitigation
Virtual Track Integration Protocol
Virtual track methodology enhances localization accuracy in GNSS-denied environments through linear or point-type guiding elements [56]. This protocol standardizes their implementation for reproducible navigation experiments.
Materials and Setup:
- Virtual track infrastructure (optical, magnetic, or conductive)
- Reference localization system (high-accuracy GNSS/INS)
- AV platform with compatible sensor suite
- Environmental characterization equipment
Procedure:
- Infrastructure Characterization: Map virtual track properties and spatial configuration
- Sensor Calibration: Align virtual track detection sensors with vehicle coordinate frame
- Baseline Localization: Compare virtual track navigation against GNSS/INS reference in optimal conditions
- GNSS-Degradation Testing: Evaluate virtual track performance in challenging environments (urban canyons, tunnels, etc.)
- Transition Testing: Assess smoothness of transitions between GNSS and virtual track navigation modes
Data Collection:
- Lateral and longitudinal error statistics across environment types
- Transition success rates between navigation modes
- Failure mode analysis and recovery procedures
Reproducibility Assessment Protocol
Based on IJCAI reproducibility guidelines [55], this protocol ensures experimental results can be independently verified while accommodating necessary proprietary protections.
Materials and Setup:
- Detailed experimental documentation template
- Version-controlled code repository
- Containerized development environment
- Dataset management system
Procedure:
- Conceptual Outline: Provide high-level algorithm description and pseudocode for proprietary components
- Environment Specification: Document hardware, software, and dependency versions using containerization
- Parameter Reporting: List all hyperparameters with ranges explored and final selected values
- Dataset Documentation: Describe data sources, preprocessing, and splits with appropriate citations
- Experimental Conditions: Specify environmental factors, testing scenarios, and evaluation metrics
Data Collection:
- Reproducibility checklist completion status
- Computational resource requirements and timing
- Sensitivity analysis for critical parameters
Visualization Framework
Experimental Workflow Diagram
Diagram 1: Comprehensive AV Experimental Workflow
Virtual Track Architecture
Diagram 2: Virtual Track System Architecture
Reproducibility Assessment Framework
Diagram 3: Reproducibility Assessment Framework
Research Reagent Solutions
Table 3: Essential Research Materials and Tools
| Category | Specific Tool/Resource | Function/Purpose | Implementation Example |
|---|---|---|---|
| Simulation Frameworks | SEFAV [57] | Security scenario simulation | Cross-platform security evaluation |
| Navigation Infrastructure | Virtual Track System [56] | Enhanced localization in GNSS-denied environments | Linear/point-type guidance elements |
| Data Management | Million Authors Corpus Approach [14] | Cross-domain dataset construction | Wikipedia-based authorship verification |
| Documentation Tools | IJCAI Reproducibility Checklist [55] | Experimental transparency assessment | Conceptual outlines, parameter reporting |
| Testing Environments | SUMO/OSM Integration [57] | Traffic scenario simulation | Routing, scenario generation |
| Evaluation Metrics | T-PAAD Impact Measures [57] | Security vulnerability quantification | Trajectory deviation under attack |
| Sensor Systems | Multi-modal Sensor Fusion | Environmental perception | Camera, LIDAR, radar, ultrasonic |
| Analysis Frameworks | Eye-tracking Methodology [58] | Cognitive engagement measurement | Visual attention patterns in AV scenarios |
The establishment of transparent and reproducible experimental protocols for autonomous vehicles represents a critical enabling step for scientific progress in the field. By adapting frameworks from cross-topic authorship verification research and implementing standardized methodologies for security evaluation, virtual track integration, and reproducibility assessment, the AV research community can accelerate development while maintaining scientific rigor. The protocols and frameworks presented in this document provide actionable guidance for researchers seeking to generate verifiable, generalizable results that withstand independent scrutiny and contribute meaningfully to the advancement of autonomous vehicle technology.
As the field continues to evolve, these foundational practices will enable more effective collaboration across institutions, facilitate technology transfer from research to industry, and ultimately support the safe deployment of autonomous vehicles in diverse operational environments. The integration of robust experimental methodologies with comprehensive documentation standards creates a solid foundation for addressing the complex technical and social challenges inherent in autonomous vehicle development.
Conclusion
The development of rigorous cross-topic authorship verification protocols marks a significant advancement in ensuring the integrity and authenticity of scientific and clinical text. By integrating robust methodological architectures that combine deep semantic understanding with stylistic feature analysis, and by proactively addressing critical challenges like topic leakage through frameworks such as HITS, researchers can create highly reliable verification systems. The implications for biomedical research are profound, offering powerful tools for detecting plagiarism, verifying authorship in multi-contributor clinical trials, authenticating scientific publications, and monitoring pharmacovigilance reports. Future directions should focus on adapting these protocols for low-resource languages, enhancing model explainability for clinical and regulatory acceptance, and expanding applications to detect AI-generated scientific text, thereby solidifying the role of authorship verification as a key component of research data management and scientific integrity in the digital age.
References
- 1. Authorship Verification based on the Likelihood Ratio of ... [https://arxiv.org/html/2403.08462v1]
- 2. The Role of Linguistic Feature Categories in Authorship ... [https://www.sciencedirect.com/science/article/pii/S1877050918321823]
- 3. Digital Authorship Verification Explained [https://www.scoredetect.com/blog/posts/digital-authorship-verification-explained]
- 4. LLM one-shot style transfer for Authorship Attribution and ... [https://arxiv.org/html/2510.13302v1]
- 5. Combining style and semantics for robust authorship ... [https://www.sciencedirect.com/science/article/pii/S266682702500115X]
- 6. Addressing Topic Leakage in Cross-Topic Evaluation for ... [https://aclanthology.org/2024.tacl-1.75/]
- 7. Addressing Topic Leakage in Cross-Topic Evaluation for ... [https://arxiv.org/abs/2407.19164]
- 8. Rethinking the Authorship Setups Verification Experimental [https://arxiv.org/abs/2112.05125]
- 9. Biomarker Discovery and Validation: Statistical Considerations [https://pmc.ncbi.nlm.nih.gov/articles/PMC8012218/]
- 10. The Biomarker Toolkit — an evidence-based guideline to ... [https://bmcmedicine.biomedcentral.com/articles/10.1186/s12916-023-03075-3]
- 11. Biomarker Validation: Common Data Analysis Concerns [https://pmc.ncbi.nlm.nih.gov/articles/PMC4122484/]
- 12. Addressing Topic Leakage in Cross - Topic Evaluation for Authorship ... [https://arxiv.org/html/2407.19164v1]
- 13. Addressing Topic Leakage in Authorship - Simple Science Verification [https://scisimple.com/en/articles/2025-07-06-addressing-topic-leakage-in-authorship-verification--ak27mey]
- 14. The Million Authors Corpus: A Cross -Lingual and... - ACL Anthology [https://aclanthology.org/2025.findings-acl.1335/]
- 15. Stylometry and forensic science: A literature review - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC11707938/]
- 16. Task-state skin potential abnormalities can distinguish ... [https://www.nature.com/articles/s41398-024-02828-9]
- 17. Even small correlation and diversity shifts pose dataset- ... [https://www.sciencedirect.com/science/article/abs/pii/S0167865524000333]
- 18. Examining Biases in CelebA using Attention Maps [https://arxiv.org/abs/2503.19846]
- 19. Addressing AI Bias: Real-World Challenges and How to ... [https://www.digitalocean.com/resources/articles/ai-bias]
- 20. Binary quantification and dataset shift: an experimental ... [https://link.springer.com/article/10.1007/s10618-024-01014-1]
- 21. Understanding Dataset Shift [https://medium.com/data-science/understanding-dataset-shift-f2a5a262a766]
- 22. SPIRIT 2025 statement: Updated guideline for protocols of ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12037212/]
- 23. Rethinking the Authorship Verification Experimental Setups [https://www.semanticscholar.org/paper/9424d98d7805574661da1adf4f8bc682be5714da]
- 24. Decoding Authorship: Unveiling AI-Generated Text Sources [https://www.azoai.com/news/20230817/Decoding-Authorship-Unveiling-AI-Generated-Text-Sources.aspx]
- 25. Siamese neural network [https://en.wikipedia.org/wiki/Siamese_neural_network]
- 26. Siamese Neural Network - an overview [https://www.sciencedirect.com/topics/computer-science/siamese-neural-network]
- 27. Feature Interaction Aware Automated Data Representation ... [https://arxiv.org/html/2309.17011v2]
- 28. Siamese network based high discriminative feature ... [https://www.sciencedirect.com/science/article/abs/pii/S1746809425008262]
- 29. Feature interaction: a critical review and considered forecast [https://www.sciencedirect.com/science/article/abs/pii/S1389128602003523]
- 30. Siamese Vision Transformers are Scalable Audio-visual ... [https://arxiv.org/html/2403.19638v1]
- 31. An open-source deep learning network AVA-Net for arterial ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10110614/]
- 32. The state of post-training in 2025 [https://www.interconnects.ai/p/the-state-of-post-training-2025]
- 33. AI Annotation Orchestration: Evaluating LLM verifiers to ... [https://arxiv.org/html/2511.09785v1]
- 34. Breaking Down the Modern LLM Training Pipeline [https://mlops.community/pretraining-breaking-down-the-modern-llm-training-pipeline/]
- 35. Simulating Training Data Leakage in Multiple-Choice ... [https://arxiv.org/html/2505.24263v1]
- 36. Contrast Checker [https://webaim.org/resources/contrastchecker/]
- 37. PAN at CLEF 2025 - Multi-Author Writing Style Analysis [https://pan.webis.de/clef25/pan25-web/style-change-detection.html]
- 38. Handling imbalanced medical datasets: review of a decade ... [https://link.springer.com/article/10.1007/s10462-024-10884-2]
- 39. A Keyword-Enhanced Approach to Handle Class Imbalance in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9533247/]
- 40. Challenges and best practices for digital unstructured data ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10566734/]
- 41. Explanation and prediction of clinical data with imbalanced ... [https://bmcmedinformdecismak.biomedcentral.com/articles/10.1186/s12911-020-01356-y]
- 42. Class imbalance in out-of-distribution datasets: Improving ... [https://www.sciencedirect.com/science/article/pii/S1532046421002860]
- 43. Graph-Based Siamese Network for Authorship Verification [https://www.mdpi.com/2227-7390/10/2/277]
- 44. Detecting and Mitigating the Clever Hans Effect in Medical ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12344020/]
- 45. Authorship identification using ensemble learning [https://www.nature.com/articles/s41598-022-13690-4]
- 46. A Comparative Study of Traditional, Ensemble and Neural ... [https://www.mdpi.com/1911-8074/16/7/327]
- 47. Deep Learning vs Machine Learning: Key Differences [https://ischool.syracuse.edu/deep-learning-vs-machine-learning/]
- 48. Machine Learning vs. Neural Networks: Differences & ... [https://www.carmatec.com/blog/machine-learning-vs-neural-networks-key-differences-and-future-trends/]
- 49. Neural Network Vs Traditional Algorithms [https://www.meegle.com/en_us/topics/neural-networks/neural-network-vs-traditional-algorithms]
- 50. Model validation in machine learning: How to do it [https://www.leewayhertz.com/model-validation-in-machine-learning/]
- 51. Top 5 Validation Methods In Machine Learning [https://medium.com/@mehmetalitor/top-5-model-validation-methods-in-machine-learning-77eed8d08937]
- 52. Training, validation, and test data sets [https://en.wikipedia.org/wiki/Training,_validation,_and_test_data_sets]
- 53. Machine Learning vs. Neural Networks (Differences ... [https://www.weka.io/learn/glossary/ai-ml/machine-learning-vs-neural-networks/]
- 54. Rethinking the Authorship Verification Experimental Setups [https://aclanthology.org/2022.emnlp-main.380/]
- 55. Reproducibility [https://2025.ijcai.org/reproducibility/]
- 56. Methodology for Implementing Autonomous Vehicles ... [https://www.mdpi.com/2032-6653/16/12/651]
- 57. Security experimental framework of trajectory planning for ... [https://www.sciencedirect.com/science/article/pii/S2666603024000307]
- 58. Sociotechnical imaginaries of autonomous vehicles [https://pmc.ncbi.nlm.nih.gov/articles/PMC12622791/]