Cross-Domain Authorship Verification: Protocols, Challenges, and Applications for Biomedical Research
This article provides a comprehensive overview of modern protocols for cross-domain authorship verification, a critical task for ensuring the integrity and provenance of scientific text.
Cross-Domain Authorship Verification: Protocols, Challenges, and Applications for Biomedical Research
Abstract
This article provides a comprehensive overview of modern protocols for cross-domain authorship verification, a critical task for ensuring the integrity and provenance of scientific text. Tailored for researchers and drug development professionals, we explore the foundational concepts, from stylometry to large language models (LLMs), and detail state-of-the-art methodologies that combine semantic and stylistic features. The content addresses key challenges like data sparsity and AI-generated text, offers guidance on model optimization and evaluation metrics, and presents a comparative analysis of current benchmarks and shared tasks. By synthesizing these insights, this guide aims to support the development of robust, reliable verification systems for applications ranging from research paper authentication to clinical trial documentation.
Understanding Cross-Domain Authorship Verification: Core Concepts and Stylometric Foundations
Defining Authorship Verification and Its Critical Role in Scientific Integrity
Authorship verification (AV) is a computational task concerned with determining whether two texts were written by the same author based on their writing style [1]. In the research integrity landscape, it serves as a foundational methodology for detecting practices that undermine scientific trust, including plagiarism, ghost authorship, and data fabrication in publications [2]. The reliability of scientific literature depends on correctly attributing work to its genuine creators, making robust authorship verification a critical component of the modern research infrastructure. This document outlines standardized protocols for conducting cross-domain authorship verification research, providing application notes for researchers and professionals engaged in upholding scientific integrity.
The Authorship Verification Framework: Concepts and Challenges
Core Definitions and Relationship to Scientific Misconduct
Authorship verification is a specialized subfield of authorship analysis, distinct from but related to authorship attribution, which identifies the most likely author of a text from a set of candidates [3]. The core challenge in AV, particularly in cross-domain or cross-genre settings, is to identify author-specific linguistic patterns that are independent of the text's subject matter, genre, or topic [3]. This is crucial because models that over-rely on topical cues can appear valid while failing to capture the actual stylometric features that signify true authorship.
The relationship between AV and scientific integrity is direct and consequential. The U.S. Office of Research Integrity (ORI) strictly defines research misconduct as fabrication, falsification, or plagiarism (FFP) [2]. While authorship disputes and self-plagiarism were explicitly excluded from the federal definition of misconduct in the 2025 ORI Final Rule, they remain subject to institutional policies and publishing standards where authorship verification methodologies play an essential detective and preventive role [2].
Critical Challenges in Cross-Domain Verification
Cross-domain authorship verification presents unique methodological challenges that must be addressed in experimental design:
- Topic Independence: Models must avoid relying on topic-based features and instead learn genuine authorship features [1]. Studies have shown that models can be biased toward named entities and other topical cues rather than writing style [4].
- Generalizability: Models trained on single-domain datasets often fail to generalize across different genres or domains, leading to overly optimistic performance evaluations [1].
- Linguistic Variation: Writing style naturally varies across genres and contexts (e.g., academic papers vs. informal communications), creating natural variations that models must accommodate while still identifying core authorial fingerprints.
Experimental Protocols for Authorship Verification Research
Dataset Curation and Preparation
Protocol 1: Construction of Cross-Domain Benchmark Datasets
Objective: To create evaluation datasets that enable robust testing of authorship verification models across different domains and languages.
Materials:
- Source texts from multiple domains (e.g., Wikipedia edits, academic papers, social media posts)
- Author metadata ensuring proper attribution
- Text processing tools for cleaning and normalization
Methodology:
- Source Selection: Collect long, contiguous textual chunks from diverse domains. The Million Authors Corpus protocol uses Wikipedia edits across dozens of languages as a foundation [1].
- Author Linking: Ensure each text chunk is properly linked to its verified author while maintaining privacy considerations.
- Text Processing: Remove or standardize named entities to reduce topic bias, following findings that models without named entities generalize better [4].
- Cross-Domain Splitting: Create dataset splits specifically designed to isolate biases related to text topic and author writing style [4].
- Quality Validation: Implement manual and automated checks to ensure text quality and proper author attribution.
Output: A benchmark dataset suitable for cross-domain authorship verification experiments, such as the Million Authors Corpus which contains 60.08M textual chunks from 1.29M Wikipedia authors [1].
Model Training and Evaluation
Protocol 2: Implementation of Retrieve-and-Rerank Framework for AV
Objective: To implement a state-of-the-art two-stage pipeline for authorship verification that scales to large author pools while maintaining cross-domain performance.
Materials:
- Pre-trained Large Language Models (LLMs) suitable for fine-tuning
- Computational resources for training and inference
- Benchmark datasets prepared per Protocol 1
Methodology:
Stage 1: Retriever Training (Bi-encoder)
- Architecture Selection: Use a transformer LLM with mean pooling over token representations to create fixed-length document vectors [3].
- Projection Layer: Apply a learnable linear projection to reduce dimensionality (typically to half the original hidden dimension) [3].
- Contrastive Training:
- Construct batches with N distinct authors, including exactly two documents per author
- Use supervised contrastive loss with hard negative sampling
- Calculate scores using dot product between document vectors
- Hard Negative Mining: Implement in-batch negative sampling where negative documents with high similarity scores are prioritized to accelerate convergence [3].
Stage 2: Reranker Training (Cross-encoder)
- Architecture: Use a cross-encoder that takes both query and candidate documents as joint input [3].
- Targeted Data Curation: Create training pairs that explicitly teach the model to ignore topical cues while focusing on author-discriminative signals [3].
- Training Strategy: Avoid information retrieval-focused training approaches that are misaligned with cross-genre AV objectives [3].
Evaluation Metrics:
- Success@K (particularly Success@8 for cross-genre benchmarks)
- Accuracy and F1 score for verification tasks
- Cross-domain generalization performance
Table 1: Essential Research Reagent Solutions for Authorship Verification Research
| Resource Type | Specific Examples | Function/Application | Key Characteristics |
|---|---|---|---|
| Benchmark Datasets | Million Authors Corpus [1]; HIATUS HRS1/HRS2 benchmarks [3]; PAN datasets [4] | Training and evaluation of AV models | Cross-lingual; cross-domain; large-scale (60M+ texts); topic-controlled |
| Computational Models | Sadiri-v2 [3]; BERT-like architectures [4]; RoBERTa-based retrievers [3] | Feature extraction and authorship scoring | LLM-based; fine-tunable; cross-encoder and bi-encoder architectures |
| Evaluation Frameworks | VALOR framework [5]; Custom cross-validation splits | Assessing model performance and reproducibility | Verification, Alignment, Logging, Overview, Reproducibility components |
| Specialized Libraries | VOSviewer [5]; CiteSpace [5]; Network analysis tools | Visualization of authorship patterns and scientific networks | Network visualization; clustering; trend analysis |
Performance Metrics and Comparative Analysis
Table 2: Performance Benchmarks for Authorship Verification Systems
| Model/Dataset | Cross-Genre Performance | Key Innovations | Limitations |
|---|---|---|---|
| Sadiri-v2 [3] | Gains of 22.3 and 34.4 absolute Success@8 points on HRS1 and HRS2 benchmarks | LLM-based retrieve-and-rerank; targeted data curation for cross-genre AV | Computational intensity; requires large training data |
| BERT-like Baselines [4] | Competitive with state-of-the-art AV methods | Transfer learning from pre-trained language models | Bias toward named entities without specific mitigation |
| Million Authors Corpus Baselines [1] | Enables cross-lingual and cross-domain evaluation | Wikipedia-based; 60.08M textual chunks from 1.29M authors | Primarily encyclopedia-style writing may limit genre diversity |
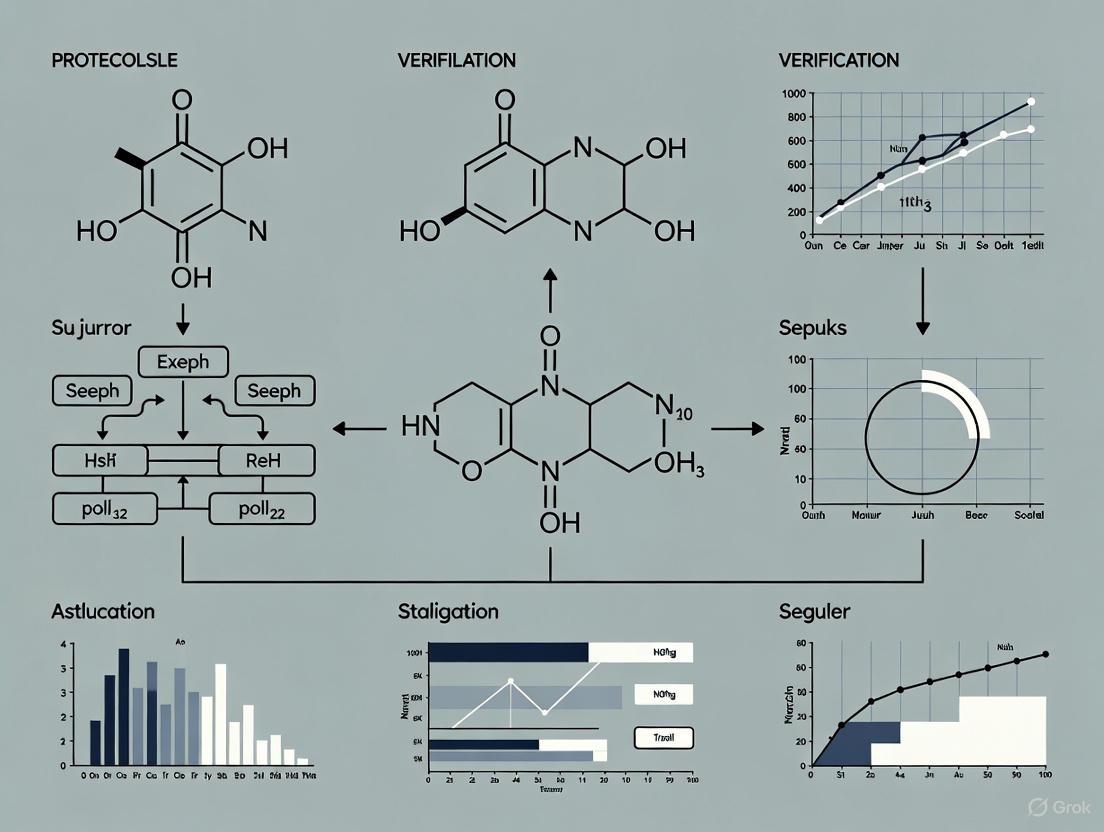
Visualization of Authorship Verification Workflows
Two-Stage AV Pipeline
Retrieve and Rerank Architecture
Integration with Research Integrity Frameworks
Alignment with Ethical Authorship Guidelines
The development of robust authorship verification methodologies directly supports the implementation of ethical authorship guidelines as defined by leading organizations. The International Committee of Medical Journal Editors (ICMJE) 2025 updates explicitly state that AI tools cannot be credited as authors and emphasize that all listed authors must make substantial intellectual contributions [6] [7]. Similarly, Brown University's authorship guidelines specify that authorship requires substantial contributions to conception, drafting, approval, and accountability [7]. Authorship verification technologies provide technical means to validate compliance with these ethical standards by detecting inconsistencies in writing style that might indicate ghostwriting or honorary authorship.
Detection and Prevention of Authorship Misconduct
Effective authorship verification serves as a deterrent and detection mechanism for several forms of authorship misconduct:
- Ghostwriting: Identification of professional writers whose contributions are not acknowledged [7]
- Gift Authorship: Detection of inconsistencies when individuals who did not meet authorship criteria are listed as authors [7]
- Plagiarism: Identification of copied content across publications, including self-plagiarism [2]
- AI-Generated Content: Detection of text produced by AI tools without proper disclosure, though current guidelines prohibit AI authorship [6] [7]
Limitations and Future Directions
While authorship verification technologies show significant promise for supporting research integrity, several limitations must be acknowledged:
- Contextual Understanding: Current models may struggle with legitimate variations in writing style across different professional contexts and collaborative writing scenarios.
- Adversarial Attacks: Sophisticated attempts to mimic or obscure writing style present ongoing challenges.
- Multilingual Performance: Despite advances in cross-lingual datasets [1], performance across diverse languages remains uneven.
- Interpretability: The "black box" nature of some LLM-based approaches makes it difficult to explain authorship decisions to integrity committees.
Future development should focus on creating more interpretable models, establishing standardized evaluation benchmarks across domains, and developing integrated systems that combine automated verification with human expert oversight in research integrity investigations.
Authorship verification represents a critical technological capability for maintaining scientific integrity in an era of increasing publication volume and complexity. The protocols and methodologies outlined here provide researchers with standardized approaches for conducting rigorous cross-domain authorship verification research. By implementing these practices and continuing to advance the state of the art, the research community can strengthen its defenses against authorship misconduct while supporting the accurate attribution that forms the foundation of scientific credit and accountability. As authorship continues to evolve with new technologies and collaborative patterns, robust verification methodologies will remain essential for preserving trust in the scientific record.
Cross-domain authorship verification (AV) presents a unique set of challenges for computational linguistics and digital text forensics. The core problem involves determining whether two texts in different domains are from the same author, requiring models that capture genuine stylistic fingerprints rather than domain-specific features. This application note establishes standardized protocols for cross-domain AV research, leveraging novel datasets and methodologies to address this significant challenge. As authorship verification becomes increasingly crucial for identity verification, plagiarism detection, and AI-generated text identification, the development of robust cross-domain techniques represents a critical research frontier [1].
The Million Authors Corpus (MAC) provides an unprecedented resource for this investigation, encompassing 60.08 million textual chunks from 1.29 million Wikipedia authors across dozens of languages [1]. This dataset's cross-lingual and cross-domain nature enables researchers to conduct controlled experiments that separate genuine authorship signals from domain-specific characteristics, addressing a fundamental limitation in existing AV research.
Dataset Specification and Quantitative Analysis
Million Authors Corpus (MAC) Composition
Table 1: Million Authors Corpus Dataset Specifications
| Parameter | Specification | Research Utility |
|---|---|---|
| Total Textual Chunks | 60.08 million | Provides statistical power for robust model training |
| Unique Authors | 1.29 million | Enables verification across multiple texts per author |
| Language Coverage | Dozens of languages | Facilitates cross-lingual authorship analysis |
| Text Characteristics | Long, contiguous chunks from Wikipedia edits | Ensures sufficient stylistic data per sample |
| Domain Variation | Cross-domain Wikipedia content | Allows controlled domain shift experiments |
| Author Linking | Texts reliably linked to original authors | Provides ground truth for verification tasks |
Cross-Domain Experimental Framework
The MAC enables a systematic approach to cross-domain verification through its structured composition. Researchers can leverage the natural domain variation within Wikipedia content (e.g., technical articles vs. biographical entries) to construct verification tasks that specifically test model robustness to domain shifts. This controlled environment is essential for developing AV systems that rely on persistent stylistic features rather than topic-based signals [1].
Experimental Protocols for Cross-Domain Verification
Core Verification Methodology
Objective: Implement and evaluate authorship verification models capable of accurate performance across diverse textual domains.
Protocol:
- Data Partitioning: Segment MAC into training, validation, and test sets, ensuring no author overlap between sets
- Domain Stratification: Categorize texts by domain characteristics (technicality, formality, subject matter)
- Pair Construction: Generate same-author and different-author pairs across domains
- Feature Extraction: Implement linguistic features resistant to domain variation
- Model Training: Employ cross-entropy loss with domain-invariance regularization
- Evaluation: Assess using area under ROC curve and F1-score metrics
Cross-Domain Validation Protocol
Neurocognitive Validation Supplement: Electroencephalography (EEG) methodologies provide complementary biological validation for stylistic processing. The protocol involves measuring absolute power spectrum density (PSD) values while participants read texts from different domains by the same author [8]. Differential brain activity patterns, particularly in theta and alpha frequency bands, indicate neural correlates of stylistic recognition that transcend domain boundaries [8].
Visualization of Experimental Workflows
Cross-Domain Authorship Verification Pipeline
Cognitive Validation Framework
Research Reagent Solutions
Table 2: Essential Research Materials and Computational Tools
| Reagent/Tool | Specification | Research Function |
|---|---|---|
| Million Authors Corpus | 60.08M texts, 1.29M authors, multilingual [1] | Primary dataset for cross-domain verification experiments |
| EEG Neuroimaging System | 64-channel setup, spectral analysis capability [8] | Biological validation of stylistic processing across domains |
| FAIR Data Management | ODAM framework, frictionless datapackage format [9] | Ensures reproducible data handling and interoperability |
| Contrast-Aware Visualization | WCAG 2.1 AA compliance (4.5:1 ratio minimum) [10] [11] | Accessible research dissemination and tool development |
| Topic Modeling Framework | Latent Dirichlet Allocation implementation [12] | Quantifies cross-domain thematic novelty and conventionality |
| Linguistic Feature Extractors | Syntax, lexicon, and semantic feature libraries | Captures domain-invariant stylistic fingerprints |
Analytical Framework and Interpretation Guidelines
Novelty-Familiarity Dynamics in Cross-Domain Analysis
Research utilizing fanfiction datasets reveals a crucial dynamic between novelty and familiarity in reader reception. Quantitative analysis demonstrates that while sameness attracts the masses, novelty provides deeper enjoyment [12]. This U-shaped success curve, rather than the predicted inverse U-shape, indicates that cultural evolution in writing must work against the inertia of audience preference for the familiar [12]. For cross-domain verification, this suggests that authorial style may manifest differently in conventional versus innovative textual productions.
Quantitative Evaluation Metrics
Primary Performance Measures:
- Cross-domain verification accuracy (percentage)
- Area Under ROC Curve (AUC-ROC)
- False Acceptance/Rejection Rates across domains
- Domain-invariance coefficient (style feature consistency)
Neurocognitive Correlates:
- Theta/alpha band power differentials during cross-domain reading [8]
- Stimulus-specific neural response patterns to authorial style [8]
The integration of large-scale textual analysis with neurocognitive validation methodologies establishes a robust framework for advancing cross-domain authorship verification. The Million Authors Corpus provides the foundational dataset necessary for developing models that capture genuine authorial style independent of domain-specific characteristics. These protocols enable researchers to systematically address one of the most significant challenges in digital text forensics, with applications ranging from academic integrity to security verification and AI-generated text identification.
Within the evolving discipline of cross-domain authorship verification, the core challenge is to identify an author's unique stylistic signature across varying topics and genres. This requires features that capture fundamental, unconscious writing patterns resistant to conscious manipulation and topic-specific vocabulary [13]. This document establishes application notes and protocols for three essential stylometric feature classes—character n-grams, syntactic features, and punctuation—detailing their experimental use for robust, cross-domain analysis.
Stylometric Feature Classes: Application Notes
The following section provides a detailed breakdown of each core stylometric feature class, including its definition, utility in cross-domain analysis, and standard extraction methodologies.
Table 1: Core Stylometric Feature Classes for Cross-Domain Analysis
| Feature Class | Definition | Cross-Domain Utility | Standard Extraction Method |
|---|---|---|---|
| Character N-grams | Contiguous sequences of n characters [14]. |
Highly effective; captures sub-word patterns (morphemes, common typos) and punctuation, which are largely topic-agnostic [14] [13]. | Sliding window of length n over raw text, ignoring word boundaries. Common n values: 3-5. |
| Syntactic Features | Patterns related to grammatical sentence structure [15]. | High utility; grammar habits are deeply ingrained and independent of content [14]. | Parsing text to generate Part-of-Speech (POS) tag sequences or dependency trees, then extracting n-grams from these structures [14]. |
| Punctuation | Frequency and usage patterns of punctuation marks (e.g., commas, semicolons) [16]. | High utility; punctuation is a conscious habit and a strong, topic-independent style marker [16] [17]. | Simple frequency counts or incorporation into character n-grams to capture mark-specific patterns [13]. |
Character N-grams
Character n-grams are contiguous sequences of n characters extracted from a text. For example, the word "and" generates the trigrams (3-grams) "an", "and", and "nd" (including spaces) [16]. Their power in cross-domain analysis stems from the ability to capture sub-lexical patterns. These include morphological units (prefixes, suffixes), common misspellings, and punctuation sequences, all of which are highly characteristic of an author's style yet largely independent of the topic being discussed [14] [13]. Research has shown that character n-grams associated with word affixes and punctuation marks are among the most useful features in cross-topic authorship attribution [13].
Syntactic Features
Syntactic features model the author's preferred methods for constructing sentences, which are often habitual and unconscious. These features operate at a level "above" word choice, making them inherently resistant to topic variations [14]. The two primary methods for capturing syntactic information are:
- Part-of-Speech (POS) Tag N-grams: The text is first tagged with grammatical labels (e.g., noun, verb, adjective). Stylometric analysis then uses sequences of these tags (e.g., a trigram "DET ADJ NOUN") as features [14].
- Syntactic Dependency N-grams: This method uses dependency parse trees of sentences. Features are generated by following paths in these trees, capturing relationships between words (e.g., subject-verb) [14]. This can reveal complex grammatical preferences that are difficult to consciously control.
Punctuation
Punctuation patterns provide a robust and simple-to-extract set of features for distinguishing authors. The frequency of specific marks (e.g., commas, semicolons, dashes) and their combined usage profiles reflect an author's rhythm and pacing [16]. Since these patterns are habitual and unrelated to semantic content, they offer strong discriminatory power in cross-domain scenarios [17]. Punctuation can be analyzed both through direct frequency counts and as integral components of character n-grams [13].
Experimental Protocols for Cross-Domain Verification
This protocol outlines the steps for a robust cross-domain authorship verification experiment using the aforementioned features.
Corpus Construction & Preprocessing
- Data Collection: For cross-domain evaluation, use a controlled corpus like the CMCC corpus, which contains texts from the same set of authors across different genres (e.g., blog, email, essay) and topics (e.g., privacy rights, gender discrimination) [13]. This allows for controlled ablation studies.
- Text Chunking: To handle long documents or ensure uniform sample sizes, split texts into contiguous chunks. The Million Authors Corpus (MAC) uses long, contiguous chunks from Wikipedia edits for this purpose [1].
- Preprocessing: Apply minimal, consistent preprocessing. Convert all text to lowercase to reduce vocabulary sparsity. In some protocols, punctuation marks and digits are replaced by specific symbolic placeholders (e.g., all commas become "
<COM>") to standardize their representation while preserving their presence [13].
Feature Extraction Workflow
The following diagram illustrates the parallel feature extraction pathways for a given text document.
Model Training & Cross-Domain Evaluation
- Feature Vectorization: Transform the extracted features into numerical vectors using methods like term frequency-inverse document frequency (TF-IDF) [14].
- Dimensionality Reduction: For high-dimensional feature spaces (especially with n-grams), apply techniques like Principal Component Analysis (PCA) or Latent Semantic Analysis (LSA) to reduce noise and computational load [14].
- Model Selection: Employ machine learning classifiers suitable for high-dimensional data. Logistic Regression and tree-based models like LightGBM have proven effective in stylometry tasks [14] [18].
- Cross-Domain Validation: This is a critical step. Train the model on texts from one genre or topic (the source domain) and test its performance on texts from a different genre or topic (the target domain) from the same authors. Performance drop compared to within-domain testing quantifies the model's cross-domain robustness [13].
Table 2: Quantitative Performance of Stylometric Features
| Feature Type | Example / Sub-type | Reported Performance (Task) | Notes / Context |
|---|---|---|---|
| Character N-grams | General Character N-grams | High performance in Authorship Attribution [14] | Effective for cross-topic AA [13]. |
| Syntactic Features | POS Tag N-grams | Competitive results for style change detection [14] | - |
| Syntactic Dependency N-grams | Competitive results among different authors [14] | Captures non-conscious syntactic habits. | |
| All Features Combined | StyloMetrix & N-grams | 0.87 MCC (Multiclass); 0.98 Accuracy (Binary) [18] | Task: Human vs. LLM-generated text detection. |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Research Reagents for Stylometric Analysis
| Reagent / Resource | Function / Description | Utility in Cross-Domain Research |
|---|---|---|
| CMCC Corpus | A controlled corpus with texts from 21 authors across 6 genres and 6 topics [13]. | Gold standard for cross-topic and cross-genre ablation studies. |
| Million Authors Corpus () | A large-scale, cross-lingual Wikipedia dataset with 60M+ text chunks from 1.29M authors [1]. | Enables broad-scale cross-lingual and cross-domain evaluation. |
| PAN Datasets | A series of datasets and shared tasks for forensic and stylometry applications [15]. | Provides benchmark datasets and tasks for authorship verification. |
| Pre-trained Language Models (e.g., BERT, ELMo) | Deep neural networks pre-trained on vast text corpora to generate contextual token representations [13]. | Can be fine-tuned for authorship tasks; provides a powerful alternative to manual feature engineering. |
| Normalization Corpus (C) | An unlabeled collection of texts used to calibrate model outputs and reduce domain-specific bias [13]. | Crucial for cross-domain verification; should match the target domain for best results [13]. |
| StyloMetrix | A tool for extracting a comprehensive set of human-designed stylometric features [18]. | Provides interpretable, grammar-based features for model development and analysis. |
Authorship verification (AV) is a critical technology for identity verification, plagiarism detection, and AI-generated text identification. A fundamental challenge in this field is that models often rely on topic-based features rather than actual authorship stylometry, causing them to generalize poorly when applied to texts from different domains or genres. This limitation has driven the development of specialized benchmark datasets and evaluation frameworks designed specifically for cross-domain analysis. The Million Authors Corpus () and the ongoing PAN Shared Tasks represent two significant initiatives addressing this need by providing large-scale, diverse datasets and standardized evaluation protocols that enable robust assessment of authorship verification methodologies under realistic cross-domain conditions [1] [19].
The Million Authors Corpus: Design and Composition
The Million Authors Corpus represents a paradigm shift in authorship verification resources by addressing the critical limitations of existing datasets, which are primarily monolingual and single-domain. This novel dataset encompasses contributions from dozens of languages on Wikipedia, creating a naturally cross-lingual and cross-domain environment for evaluation [1].
Corpus Architecture and Data Collection
The corpus is constructed exclusively from long, contiguous textual chunks taken from Wikipedia edits. These texts are systematically linked to their authors, creating a verifiable ground truth for authorship. The scale of the corpus is unprecedented in authorship verification research, containing 60.08 million textual chunks contributed by 1.29 million Wikipedia authors [1]. This massive scale enables researchers to perform meaningful cross-lingual and cross-domain ablation studies that were previously impossible with smaller, more homogeneous datasets.
Table 1: Key Specifications of the Million Authors Corpus
| Feature | Specification |
|---|---|
| Source | Wikipedia edits |
| Textual Chunks | 60.08 million |
| Unique Authors | 1.29 million |
| Language Scope | Dozens of languages |
| Text Characteristics | Long, contiguous chunks |
| Primary Application | Cross-lingual and cross-domain authorship verification |
Experimental Protocol for Corpus Utilization
The standard experimental protocol for utilizing the Million Authors Corpus involves several key methodological steps:
Data Partitioning: Authors are randomly divided into training, validation, and test sets, ensuring no author overlap between partitions.
Cross-Lingual Pair Construction: For evaluation, text pairs are created both within the same language and across different languages to assess model robustness.
Domain Variation Control: The natural domain variation within Wikipedia (different topics, article types, and editorial styles) is leveraged to create cross-domain evaluation scenarios.
Baseline Establishment: State-of-the-art AV models alongside information retrieval models are evaluated to establish performance baselines [1].
The corpus is particularly valuable for analyzing model capabilities without the confounding variable of topic similarity, thus ensuring that performance metrics reflect genuine authorship stylometry rather than topical alignment.
PAN Shared Tasks: Benchmarking Frameworks
The PAN series of scientific events has established itself as the premier benchmarking framework for digital text forensics and stylometry. Since its inception in 2007, PAN has hosted 22 shared tasks with continually increasing community participation [19].
Evolution of PAN Evaluation Tasks
The PAN framework has evolved to address increasingly complex challenges in authorship analysis. The 2020 edition featured four specialized shared tasks, each targeting distinct aspects of authorship analysis [19]:
Profiling Fake News Spreaders on Twitter: Addressing the critical societal problem of fake news from an author profiling perspective by studying stylistic deviations of users inclined to spread misinformation.
Cross-Domain Authorship Verification: Focusing specifically on the stylistic association between authors and their works in a setting without the interference of domain-specific vocabulary.
Celebrity Profiling: Analyzing the presumed influence celebrities have on their followers to study whether celebrities can be profiled based on their followership.
Style Change Detection: Continuing research on multi-author documents by attempting to separate segments of a document based on authorship.
Standardized Evaluation Methodology
A milestone in PAN's development has been the implementation of the TIRA platform, which transitions from the traditional submission of answers to software submissions. This approach guarantees the availability of all submitted software, dramatically enhancing the reproducibility of methods and enabling direct comparison of different approaches [19]. The evaluation methodology follows rigorous standards:
- Blinded Evaluation: Test datasets are withheld from participants to prevent overfitting.
- Standardized Metrics: Task-specific evaluation metrics are clearly defined and consistently applied.
- Software Preservation: All submitted systems are preserved for future benchmarking and comparison.
Complementary Benchmarking Initiatives
AIDBench: Evaluating LLM-Based Authorship Identification
The AIDBench benchmark addresses emerging privacy risks where large language models (LLMs) may help identify the authorship of anonymous texts, challenging the effectiveness of anonymity in systems like anonymous peer review. This benchmark incorporates multiple author identification datasets, including emails, blogs, reviews, articles, and research papers [20].
Table 2: Dataset Composition within AIDBench
| Dataset | Authors | Texts | Text Length | Description |
|---|---|---|---|---|
| Research Paper | 1,500 | 24,095 | 4,000-7,000 words | arXiv CS.LG papers (2019-2024) |
| Enron Email | 174 | 8,700 | 197 words | Original Enron emails with metadata removed |
| Blog | 1,500 | 15,000 | 116 words | Blog Authorship Corpus from blogger.com |
| IMDb Review | 62 | 3,100 | 340 words | Filtered from IMDb62 dataset |
| Guardian | 13 | 650 | 1,060 words | Articles from The Guardian |
AIDBench utilizes two evaluation methods: one-to-one authorship identification (determining whether two texts are from the same author) and one-to-many authorship identification (identifying which candidate text was most likely written by the same author as a query text). The benchmark also introduces a Retrieval-Augmented Generation (RAG)-based method to enhance large-scale authorship identification capabilities of LLMs, particularly when input lengths exceed models' context windows [20].
CROSSNEWS: Cross-Genre Authorship Analysis
The CROSSNEWS dataset addresses the existing data gap in authorship analysis by connecting formal journalistic articles with casual social media posts. As the largest authorship dataset of its kind for supporting both verification and attribution tasks, it includes comprehensive topic and genre annotations. This resource demonstrates that current models exhibit poor performance in genre transfer scenarios, underscoring the need for authorship models robust to genre-specific effects [21].
Experimental Protocols for Cross-Domain Analysis
Protocol for Cross-Domain Authorship Verification
The standard experimental protocol for cross-domain authorship verification, as established in PAN shared tasks, involves several critical steps [19]:
Problem Formulation: Given a pair of documents, determine whether they were written by the same author, regardless of differences in topic, genre, or domain.
Dataset Construction:
- Collect documents from multiple domains (e.g., blog posts, emails, articles)
- Ensure author diversity with sufficient samples per author
- Annotate documents with domain metadata (genre, topic, etc.)
Evaluation Framework:
- Use balanced datasets with same-author and different-author pairs
- Employ standard metrics: AUC, F1-score, precision, and recall
- Implement cross-validation with domain-stratified splits
Protocol for Generative Plagiarism Detection
The PAN 2025 plagiarism detection task introduces a specialized protocol for identifying automatically generated textual plagiarism in scientific articles [22]:
Dataset Creation:
- Source documents from arXiv (100,000 documents across categories)
- Generate plagiarized versions using LLMs (Llama, DeepSeek-R1, Mistral)
- Apply multiple paraphrasing prompts (simple, default, complex)
Plagiarism Categorization:
- Severity levels: Low (20-40% paragraphs replaced), Medium (40-60%), High (70-100%)
- Document types: Original (5%), Altered (20%), Plagiarized (75%)
Evaluation Metrics:
- Text alignment performance (precision, recall)
- Robustness testing on historical datasets (PAN 2015)
Diagram 1: Cross-Domain Authorship Analysis Workflow
The Scientist's Toolkit: Essential Research Reagents
Table 3: Essential Research Reagents for Cross-Domain Authorship Verification
| Reagent | Function | Example Implementations |
|---|---|---|
| Benchmark Datasets | Provide standardized evaluation frameworks | Million Authors Corpus, PAN Datasets, AIDBench, CROSSNEWS |
| Stylometric Features | Capture author-specific writing patterns | Character n-grams, function words, syntactic patterns |
| Pre-trained Language Models | Generate contextual text representations | BERT, ELMo, GPT-2, ULMFiT |
| Evaluation Platforms | Ensure reproducible benchmarking | TIRA platform, CodaLab |
| Cross-Validation Splits | Prevent overfitting and ensure generalizability | Domain-stratified splits, author-disjoint splits |
| Normalization Corpora | Mitigate domain-specific biases | General domain texts for score normalization |
Advanced Methodological Approaches
Neural Architecture for Cross-Domain Attribution
Recent advances in cross-domain authorship attribution have demonstrated the effectiveness of multi-headed neural network language models combined with pre-trained language models. The proposed architecture consists of two main components [13]:
Language Model (LM) Component:
- Tokenization layer and pre-trained language model
- Generates contextual representations of each token
- Fixed during training to maintain linguistic knowledge
Multi-Headed Classifier (MHC):
- Demultiplexer to select appropriate classifier
- Set of |A| classifiers (one per candidate author)
- Each classifier has N inputs (dimensionality of LM's representation) and V outputs (vocabulary size)
The training process involves propagating LM representations only to the classifier of the known author during training, with cross-entropy error back-propagation. During testing, representations are propagated to all classifiers, and normalized similarity scores are computed using a normalization corpus to address domain shift [13].
Diagram 2: Neural Architecture for Cross-Domain Attribution
Retrieval-Augmented Generation for Large-Scale Identification
For large-scale authorship identification where the number of candidate texts exceeds model context windows, AIDBench proposes a Retrieval-Augmented Generation (RAG)-based methodology [20]:
Candidate Retrieval Phase:
- Encode all candidate texts into a vector database
- Retrieve top-k most similar candidates to query text
- Use hybrid retrieval (lexical + semantic similarity)
In-Context Identification Phase:
- Present retrieved candidates to LLM with instructions
- Generate identification decision with confidence scoring
- Iterative refinement for ambiguous cases
This approach establishes a new baseline for authorship identification using LLMs, demonstrating that they can correctly guess authorship at rates well above random chance, revealing significant privacy risks [20].
Future Directions and Applications
The development of robust cross-domain authorship verification systems has important applications in cybersecurity, digital forensics, digital humanities, and social media analytics. Future research directions include:
- Multimodal authorship analysis combining text and images [23]
- Federated learning approaches for privacy-preserving authorship verification
- Explainable AI techniques for interpretable authorship decisions
- Real-time verification systems for streaming text data
- Advanced obfuscation detection for identifying deliberately disguised authorship
The continued development of benchmark datasets like the Million Authors Corpus and the evolution of PAN shared tasks will be crucial for driving progress in these areas and establishing standardized protocols for cross-domain authorship verification research.
The Impact of Large Language Models (LLMs) on Authorship Analysis
The rapid advancement of Large Language Models (LLMs) has fundamentally transformed the landscape of authorship analysis, creating both unprecedented challenges and opportunities. Authorship attribution, the process of determining the author of a particular piece of writing, is crucial for maintaining digital content integrity, improving forensic investigations, and mitigating risks of misinformation and plagiarism [24]. The emergence of sophisticated LLMs has blurred the distinction between human and machine-generated text, complicating traditional authorship analysis methods [25] [24]. This paradigm shift necessitates the development of new protocols and frameworks, particularly for cross-domain verification where texts of known and disputed authorship differ in topic or genre [13]. This document outlines standardized application notes and experimental protocols to advance research in this critical area, providing methodologies tailored for the unique challenges posed by LLMs in authorship analysis.
Problem Categorization and Framework
The challenges introduced by LLMs to authorship analysis can be systematically categorized into four core problems, each requiring distinct methodological approaches [25] [24].
- Human-written Text Attribution: The traditional task of identifying the human author of a text from a set of candidate authors.
- LLM-generated Text Detection: A binary classification task to distinguish between human-written and LLM-generated text.
- LLM-generated Text Attribution: A multi-class task to identify which specific LLM produced a given text, acknowledging that differences in model architectures and training data impart distinct stylistic fingerprints [24].
- Human-LLM Co-authored Text Attribution: The most nuanced task, aiming to classify texts as human-authored, machine-generated, or a combination of both.
The diagram below illustrates the dynamic interplay between these problems and the core challenges in the field.
Key Benchmarks and Quantitative Data
Robust evaluation requires standardized benchmarks. The table below summarizes key datasets used for training and evaluating authorship attribution models in the era of LLMs [25].
Table 1: Authorship Attribution Benchmarks with LLM-Generated Text
| Name | Domain | Size | Language | Supported Problems |
|---|---|---|---|---|
| TuringBench | News | 168,612 (5.2% human) | English (en) | P2, P3 |
| AuTexTification | Tweets, reviews, news, legal, how-to | 163,306 (42.5% human) | en, Spanish (es) | P2, P4 |
| HC3 | Reddit, Wikipedia, medicine, finance | 125,230 (64.5% human) | en, Chinese (zh) | P2 |
| M4 | Wikipedia, WikiHow, Reddit, news, abstracts | 147,895 (24.2% human) | Arabic, Bulgarian, en, Indonesian, Russian, Urdu, zh | P2 |
| M4GT-Bench | Wikipedia, arXiv, student essays | 5.37M (96.6% human) | Arabic, Bulgarian, German, en, Indonesian, Italian, Russian, Urdu, zh | P2, P3, P4 |
| Million Authors Corpus () | Wikipedia | 60.08M chunks | Dozens of languages | P1 (Cross-lingual/Domain) |
| RAID | News, Wikipedia, recipes, poems, reviews | 523,985 (2.9% human) | Czech, German, en | P3 |
- Size is shown as the sum of LLM-generated and human-written texts, with the percentage of human-written texts in parentheses [25].
- Language is displayed using two-letter ISO 639 abbreviations [25].
- The Million Authors Corpus is particularly notable for enabling broad-scale cross-lingual and cross-domain evaluation, which is essential for testing the generalization of authorship verification methods [1].
A variety of commercial and open-source detectors have been developed, primarily for Problem 2 (LLM-generated Text Detection).
Table 2: Commercial and Open-Source LLM-Generated Text Detectors
| Detector | Price | API | Key Function |
|---|---|---|---|
| GPTZero | 10k words free/month; $10/month for 150k words | Yes | General-purpose detection |
| Originality.AI | $14.95/month for 200k words | Yes | Plagiarism and AI detection |
| Sapling | 2k characters free; $25 for 50k characters | Yes | AI content detection |
| Turnitin's AI detector | License required | No | Integrated plagiarism/AI detection for academia |
| GPT-2 Output Detector | Free | No | Detecting outputs from specific earlier models |
| Crossplag | Free | No | AI content detection |
Experimental Protocols for Cross-Domain Authorship Verification
Protocol: Authorial Language Models (ALMs) for Attribution
This protocol uses fine-tuned LLMs to measure the predictability of a questioned document for each candidate author, meeting state-of-the-art performance on several benchmarks [26].
Procedure:
- Base Model Selection: Select a suitable causal language model (e.g., GPT-2, LLaMA) as the base LLM.
- Authorial Language Model (ALM) Fine-tuning: For each candidate author
A_i, create an Authorial Language Model (ALM_i) by further pre-training the base LLM on the known writingsK_i. This process adapts the model to the specific stylistic patterns of authorA_i. - Perplexity Calculation: For the questioned document
D_q, calculate its perplexity (PPL) using eachALM_i. Perplexity measures how predictable the document is to a given model; a lower score indicates higher predictability. - Attribution Decision: Attribute the document
D_qto the candidate authorA_assignwhose ALM yields the lowest perplexity:A_assign = argmin_{A_i} PPL(ALM_i, D_q)[26].
Visualization: The following workflow diagram outlines the key steps in the ALMs protocol.
Protocol: Zero-Shot Authorship Verification with Linguistically Informed Prompting (LIP)
This protocol leverages the inherent reasoning capabilities of LLMs like GPT-4 for authorship verification without task-specific fine-tuning, enhancing explainability through linguistic feature analysis [27].
Procedure:
- Prompt Construction: Construct a detailed prompt for the LLM. The prompt must include:
- A clear instruction to perform authorship verification.
- Context: known texts
K_cfrom the candidate author. - The questioned document
D_q. - Explicit guidance (LIP) to analyze specific linguistic features in its reasoning [27].
- LLM Querying: Submit the constructed prompt to a powerful LLM (e.g., GPT-4) in a zero-shot setting.
- Output Parsing: The LLM provides a verification decision (e.g., "Yes"/"No") along with a reasoning trace that cites the linguistic evidence it considered.
- Validation: The decision and, crucially, the linguistic evidence provided in the reasoning trace should be recorded for expert validation and interpretability.
Protocol: Cross-Domain Attribution using Pre-trained Language Models
This protocol addresses the challenge when training (known) and test (questioned) texts differ in topic or genre, using a normalization corpus to improve generalization [13].
1. Candidate Authors and Texts: A set of authors A with known texts K from one domain (e.g., emails).
2. Questioned Documents: Texts U from a different domain (e.g., academic essays).
3. Normalization Corpus: An unlabeled collection of texts C that is representative of the domain of the questioned documents U.
Procedure:
- Feature Extraction: Use a pre-trained language model (e.g., BERT, ELMo) to generate contextual embeddings for all texts in
KandU. - Model Training: Train a multi-headed classifier (MHC) on the embeddings from
K. The model consists of a shared language model and a separate classifier head for each candidate author. - Cross-Entropy Calculation: For a questioned document
dinU, calculate the cross-entropy score for each candidate author's classifier head. - Score Normalization: Compute a normalization vector
nusing the unlabeled corpusCto calibrate the scores and reduce domain-specific bias. The vector is calculated as the zero-centered relative entropies produced by the model onC[13]. - Attribution: Apply the normalization vector to the cross-entropy scores and attribute
dto the author with the lowest normalized score [13].
The Scientist's Toolkit: Research Reagent Solutions
This section details essential materials and computational tools for conducting research in LLM-based authorship analysis.
Table 3: Essential Research Reagents and Tools
| Item Name | Type | Function / Application | Example / Source |
|---|---|---|---|
| Pre-trained Base LLMs | Model | Foundation for fine-tuning ALMs or feature extraction. | BERT, GPT-2, LLaMA [13] [26] |
| Multi-Domain Benchmark Datasets | Data | Training and evaluating model generalization. | TuringBench, AuTexTification, Million Authors Corpus [25] [1] |
| Commercial Detector APIs | Tool | Benchmarking against commercial solutions and real-world applications. | GPTZero, Originality.AI, Sapling [25] |
| Linguistic Feature Set | Framework | Guiding LLM reasoning (LIP) and enabling explainable analysis. | Punctuation, sentence length, formality, word choice [27] |
| Normalization Corpus | Data | Calibrating model scores in cross-domain attribution to reduce bias. | Unlabeled text from the target domain of questioned documents [13] |
| Low-Rank Adaptation (LoRA) | Method | Efficient fine-tuning of LLMs, reducing computational cost and memory requirements. | QLoRA for author profiling models [28] |
Implementing Robust Verification: From Feature Fusion to Model Architectures
Application Notes
Core Concept and Rationale
Advanced feature extraction in authorship verification involves the synergistic combination of semantic embeddings and stylistic markers to create a robust model for distinguishing authors across domains. Semantic embeddings capture the underlying meaning and thematic choices of an author, while stylistic markers quantify surface-level and syntactic patterns unique to an individual's writing. The integration of these two feature classes addresses a fundamental challenge in cross-domain verification: an author's core argumentation style and topic preferences (semantics) often remain consistent even when writing in different genres or domains, thereby compensating for the potential variance in purely syntactic features. This protocol outlines a standardized methodology for extracting, processing, and combining these features to create a generalized and powerful authorship verification system.
Key Feature Classes and Their Technical Descriptions
The efficacy of the proposed method hinges on the precise definition and extraction of two complementary feature sets. The quantitative specifications for these features are summarized in Table 1.
Table 1: Quantitative Specifications for Feature Extraction Classes
| Feature Class | Sub-category | Example Features | Vector Dimensionality | Processing Model/Technique |
|---|---|---|---|---|
| Semantic Embeddings | Document-Level | Topic distributions, overall text vector | 50-500 (e.g., LDA topics) | Latent Dirichlet Allocation (LDA), Doc2Vec |
| Contextualized | Word-in-context representations | 768-1024 (e.g., BERT-base, BERT-large) | Transformer-based Models (BERT, RoBERTa) | |
| Stylistic Markers | Lexical | Token n-grams, character n-grams, word length | Varies with vocabulary | CountVectorizer, TF-IDF Vectorizer |
| Syntactic | POS tags, dependency relations, parse tree depth | Varies with grammar rules | Probabilistic Context-Free Grammars (PCFG), SpaCy NLP Pipeline | |
| Structural | Paragraph count, sentence length, punctuation density | Fixed (e.g., 10-20 features) | Custom rule-based parsers |
Experimental Protocols
Protocol: Integrated Feature Extraction Workflow
This protocol details the end-to-end process for generating a unified feature vector from a raw text input.
I. Preprocessing and Text Normalization
- Input: Raw text document (
.txtformat). - Text Cleaning: Remove non-linguistic content (headers, footers, XML/HTML tags).
- Tokenization: Split text into individual word and sentence tokens using a pre-trained statistical model (e.g., SpaCy's tokenizer).
- Normalization (Optional): Apply lowercasing, lemmatization, and correct spelling to reduce noise. Note: This step may be omitted if case information is a relevant stylistic marker.
- Output: Cleaned, tokenized text document.
II. Parallel Feature Extraction
- Stylistic Feature Extraction:
- Lexical: Extract character-level (n=3-5) and word-level (n=1-3) n-grams. Calculate average word length and vocabulary richness (Type-Token Ratio).
- Syntactic: Process tokenized text through a Part-of-Speech (POS) tagger to generate a frequency distribution of POS tags (e.g., noun, verb, adjective).
- Structural: Compute average sentence length, paragraph length, and frequency counts of specific punctuation marks (e.g.,
,,;,—).
- Semantic Feature Extraction:
- Document-Level Embedding: Pass the normalized text through a pre-trained transformer model (e.g.,
bert-base-uncased). Extract the[CLS]token embedding or mean-pool the output hidden states to obtain a fixed-dimensional document vector. - Topic Modeling (Alternative): For a large corpus of documents from the same domain, fit an LDA model to discover latent topics. Represent each document as a distribution over these topics.
- Document-Level Embedding: Pass the normalized text through a pre-trained transformer model (e.g.,
- Output: Two separate vector representations: a high-dimensional semantic vector and a multi-dimensional stylistic vector.
III. Feature Fusion and Vector Creation
- Dimensionality Reduction (Optional): Apply Principal Component Analysis (PCA) to the high-dimensional semantic vector to reduce it to a manageable size (e.g., 50-100 components) while preserving variance.
- Normalization: Independently scale both the (reduced) semantic vector and the stylistic vector to have zero mean and unit variance using
StandardScaler. - Concatenation: Horizontally stack the normalized semantic and stylistic vectors to form a single, unified feature vector.
- Output: A final, combined feature vector ready for classifier training.
Protocol: Cross-Domain Validation Experiment
This protocol validates the robustness of the extracted features using a k-fold cross-validation strategy across different domains.
I. Experimental Setup
- Data Curation: Compile a dataset containing texts from multiple authors, with each author represented in at least two distinct domains (e.g., academic papers and personal emails).
- Data Partitioning: For each author, hold out all texts from one domain as the test set. Use the remaining texts from other domains for training.
- Classifier Selection: Standardize the use of a simple, interpretable classifier (e.g., Support Vector Machine with a linear kernel) to emphasize the quality of the features rather than model complexity.
II. Execution and Analysis
- Training: Extract combined semantic-stylistic features from the training set (following Protocol 2.1) and train the classifier.
- Testing: Extract features from the held-out domain test set and generate authorship verification predictions.
- Metric Calculation: Calculate performance metrics (Accuracy, F1-Score) for each author and domain pair.
- Ablation Study: Repeat the experiment using only stylistic features and only semantic features to isolate the contribution of each feature class to the final performance. Aggregate results are presented in Table 2.
Table 2: Simulated Cross-Domain Validation Results (F1-Score)
| Author | Training Domain | Test Domain | Stylistic-Only | Semantic-Only | Combined Features |
|---|---|---|---|---|---|
| A01 | Academic | Blog | 0.72 | 0.65 | 0.81 |
| A02 | Academic | 0.68 | 0.77 | 0.85 | |
| A03 | Blog | Social Media | 0.61 | 0.70 | 0.78 |
| Average | 0.67 | 0.71 | 0.81 |
Mandatory Visualizations
Integrated Feature Extraction Workflow
Cross-Domain Experimental Validation Logic
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials and Computational Reagents
| Item Name | Function/Benefit in Authorship Analysis | Specification / Version |
|---|---|---|
| SpaCy NLP Library | Provides industrial-strength, pre-trained models for fast and accurate tokenization, lemmatization, and Part-of-Speech (POS) tagging, forming the foundation for syntactic stylistic marker extraction. | SpaCy en_core_web_sm or en_core_web_lg |
| Hugging Face Transformers | A library offering thousands of pre-trained transformer models (e.g., BERT, RoBERTa), enabling efficient and standardized extraction of state-of-the-art semantic embeddings. | Transformers v4.20.0+ |
| Scikit-learn | The primary toolkit for feature normalization (StandardScaler), dimensionality reduction (PCA), and training a wide array of machine learning classifiers for the verification task. | Scikit-learn v1.0+ |
| Gensim | A specialized library for topic modeling, allowing for the implementation of algorithms like Latent Dirichlet Allocation (LDA) to generate document-level semantic features. | Gensim v4.0+ |
| Jupyter Notebook | An interactive computational environment ideal for exploratory data analysis, prototyping feature extraction pipelines, and visualizing intermediate results. | Jupyter Lab v3.0+ |
This document provides detailed application notes and experimental protocols for implementing deep learning architectures, specifically Siamese Networks and Feature Interaction Models, for verification tasks. While the core concepts are broadly applicable across domains such as remote sensing and biometrics, the content is specifically framed for cross-domain authorship verification (AV) research, a critical task in natural language processing for applications like plagiarism detection, forensic analysis, and content authentication [29] [30]. These protocols are designed to be adaptable, enabling researchers and scientists, including those in drug development who may handle proprietary textual data, to verify the origin of documents reliably. The methodologies outlined below focus on combining semantic content with stylistic features to enhance model robustness and performance in real-world, challenging datasets [29].
Verification architectures are designed to determine whether two distinct inputs share a common property, such as originating from the same author. The table below summarizes the key deep learning models discussed in these application notes.
Table 1: Comparison of Deep Learning Verification Architectures
| Architecture Name | Core Principle | Primary Verification Tasks | Key Advantages | Quantitative Performance Examples |
|---|---|---|---|---|
| Feature Interaction Network [29] | Learns joint representations by combining features from two inputs early in the process. | Authorship Verification [29] | Captures complex, non-linear relationships between input features. | Competitive results on challenging, imbalanced AV datasets. [29] |
| Siamese Network [29] [31] [32] | Uses identical subnetworks to process two inputs, comparing their final embeddings. | Authorship Verification [29], Remote Sensing Image Registration [31], Biometric Identification [32] | Robust to small datasets; naturally handles pairwise comparison. | Over 99% TPR on footprint data [32]; 93.6% accuracy on ECG-ID dataset [33]. |
| Pairwise Concatenation Network [29] | Combines feature vectors from two inputs through concatenation before classification. | Authorship Verification [29] | Simple and intuitive model structure. | Improved performance when incorporating style features. [29] |
Detailed Experimental Protocols
Protocol: Authorship Verification using Semantic and Stylistic Features
This protocol is designed for training a robust authorship verification model, suitable for cross-domain research where writing topics and styles may vary significantly.
I. Problem Definition: Determine if two documents, Text A and Text B, were written by the same author [29] [30].
II. Research Reagent Solutions
Table 2: Essential Materials and Reagents for Authorship Verification
| Item Name | Function / Explanation | Example / Specification |
|---|---|---|
| Pre-trained Language Model | Provides high-quality semantic embeddings of the text. | RoBERTa model [29]. |
| Stylometric Feature Set | Captures an author's unique writing style, complementing semantic content. | Sentence length, word frequency, punctuation patterns, capitalization style, acronym/abbreviation usage [29] [30] [34]. |
| AV Benchmark Dataset | Provides standardized data for training and evaluation. | IMDb62, Blog-Auth, FanFiction datasets [30] [34]. |
| Contrastive Loss Function | Trains the network to minimize distance between same-author samples and maximize distance for different authors. | Used in Siamese network training [32] [35]. |
III. Workflow Diagram
Diagram Title: AV Model Training Workflow
IV. Step-by-Step Procedure
Data Preparation:
- Dataset Curation: Collect a dataset of text pairs with labeled ground truth (same author/different author). For realistic conditions, ensure the dataset includes stylistic diversity and potentially imbalanced classes [29]. The IMDb62, Blog-Auth, and FanFiction datasets are suitable for this purpose [30].
- Text Preprocessing: Clean the text by removing extraneous HTML tags or metadata. Perform tokenization compatible with the chosen pre-trained model (e.g., RoBERTa tokenizer).
Feature Engineering:
- Semantic Feature Extraction: Pass each text through the RoBERTa model to obtain a dense contextualized embedding for the entire document [29].
- Stylistic Feature Extraction: For each document, compute a vector of hand-crafted stylistic features. This should include:
Model Implementation & Training:
- Feature Fusion: Combine the semantic embedding vector with the stylistic feature vector. This can be done via simple concatenation or through a more complex feature interaction layer [29].
- Architecture Selection: Choose a model architecture from Table 1.
- For a Siamese Network, the fused feature vector for each text is processed by identical subnetworks. The final layer computes a distance metric (e.g., Euclidean, Manhattan) between the two output embeddings. A contrastive loss function is used for training [32].
- For a Feature Interaction Network, the features from both texts are combined earlier, allowing the network to learn complex, non-linear interactions between them before making a verification decision [29].
- Training: Split data into training/validation/test sets. Use an optimizer like Adam and monitor contrastive loss or binary cross-entropy loss on the validation set to prevent overfitting.
Model Evaluation:
- Metrics: Report standard metrics on the held-out test set: Accuracy, Precision, Recall, F1-Score, and Area Under the ROC Curve (AUC-ROC).
- Benchmarking: Compare the performance of your model against established baselines, noting the performance gain achieved by incorporating stylistic features [29].
Protocol: Siamese Network for Cross-Domain Image Verification
This protocol outlines the use of a Siamese Network for a non-textual verification task, illustrating the architecture's versatility. It can be adapted for cross-domain analysis where the core task remains pairwise similarity assessment.
I. Problem Definition: Determine if two images from different sensors (e.g., optical and SAR) depict the same geographic scene [31].
II. Workflow Diagram
Diagram Title: Siamese Network for Image Verification
III. Step-by-Step Procedure
Data Preparation:
- Dataset Curation: Use a multi-source remote sensing dataset like the one described in [31], containing co-registered image pairs from different sensors.
- Image Preprocessing: Resize images to a uniform size. Apply normalization based on the pre-trained encoder's requirements.
Model Implementation & Training:
- Encoder Backbone: Use a pre-trained CNN (EfficientNet, MobileNet) as the feature extractor for both branches of the Siamese network. This leverages transfer learning and is effective even with limited data [31] [32].
- Training with Pairwise Loss: Construct training batches containing positive pairs (same scene) and negative pairs (different scenes). Train the network using a contrastive loss function that pulls embeddings of positive pairs together and pushes embeddings of negative pairs apart [31] [33].
Model Evaluation:
- Metrics: Report True Positive Rate (TPR), False Positive Rate (FPR), and Equal Error Rate (EER) [32] [33].
- Robustness Testing: Evaluate the model's performance across different types of geographic scenes and under various conditions (e.g., seasonal changes, illumination variations) to assess cross-domain robustness.
Critical Analysis and Troubleshooting
- Gradient Conflicts in Multitask Learning: When designing complex networks that share features for multiple objectives (e.g., prediction and generation), be aware of gradient conflicts. Techniques like the FetterGrad algorithm, which minimizes the Euclidean distance between task gradients, can be employed to ensure stable learning [36].
- Interpretability and Explainability: For high-stakes applications like forensic analysis, model interpretability is crucial. Consider using frameworks like CAVE (Controllable Authorship Verification Explanations), which generates structured, free-text explanations based on linguistic features, making the model's decision process transparent and verifiable [30].
- Handling Class Imbalance: Siamese Networks are naturally more robust to class imbalance because they learn from pairwise comparisons rather than per-class classification [33]. Ensure your training batches are populated with a balanced number of positive and negative pairs.
The rapid advancement of large language models (LLMs) and the proliferation of AI-generated content have created an urgent need for robust authorship verification methods capable of operating across diverse domains and languages. Traditional authorship verification approaches have primarily relied on stylometric features – quantifiable aspects of writing style including lexical, syntactic, and structural patterns. While these features have demonstrated value in controlled settings, they often lack the semantic depth and contextual awareness needed for cross-domain generalization. Concurrently, modern transformer-based models like RoBERTa provide rich contextual embeddings that capture deep semantic representations but may overlook consistent stylistic patterns that transcend topic variations.
This article presents a comprehensive framework for fusing RoBERTa embeddings with traditional stylometric features to create a powerful, multi-dimensional representation for authorship verification. By integrating these complementary approaches, researchers can develop more accurate and robust systems capable of distinguishing between human authors and AI-generated text across diverse domains – a critical capability for maintaining academic integrity, combating misinformation, and ensuring authenticity in digital communications.
Theoretical Foundation
RoBERTa Embeddings: Capabilities and Limitations
RoBERTa (Robustly Optimized BERT Pretraining Approach) represents an evolution of the BERT architecture with several key improvements: dynamic masking, removal of the next sentence prediction objective, and training on larger datasets with larger mini-batches. These modifications enable RoBERTa to generate contextualized word representations that capture nuanced semantic relationships within text.
The power of RoBERTa embeddings lies in their ability to model deep contextual information that transcends surface-level patterns. Unlike static word embeddings, RoBERTa generates representations that dynamically adjust based on surrounding context, enabling the model to disambiguate polysemous words and capture complex semantic relationships. Multiple studies have demonstrated RoBERTa's effectiveness in various text classification tasks, including offensive language detection [37], fake news identification [38], and electronic medical record analysis [39].
However, RoBERTa embeddings have limitations for authorship verification. They are primarily optimized for semantic understanding rather than capturing consistent stylistic patterns, and their representations can be influenced by topic-specific vocabulary that may not generalize across domains. Additionally, standard RoBERTa implementations may not explicitly encode the syntactic and structural features that are fundamental to authorship analysis.
Stylometric Features: Traditional Yet Relevant
Stylometric analysis encompasses a diverse set of features that quantify an author's unique writing style:
- Lexical features: Vocabulary richness, word length distributions, word n-grams
- Syntactic features: Part-of-speech patterns, punctuation usage, sentence structure
- Structural features: Paragraph length, document organization, formatting preferences
- Content-specific features: Domain-specific terminology, semantic categories
These features have demonstrated enduring value in authorship attribution tasks because they often represent involuntary writing patterns that remain consistent across topics and genres. Unlike semantic content, which varies significantly based on subject matter, stylometric features can provide a more stable signature of authorship.
The Fusion Rationale
The integration of RoBERTa embeddings with stylometric features creates a complementary system that addresses the limitations of each approach individually. While RoBERTa captures deep semantic representations, stylometric features provide consistent stylistic patterns. This fusion enables the model to distinguish between authors who may write about similar topics (addressed by stylometrics) while also recognizing when different authors share similar stylistic tendencies but discuss different subjects (addressed by RoBERTa embeddings).
Research has demonstrated that similar fusion approaches yield significant improvements across various domains. For electronic medical record named entity recognition, the fusion of SoftLexicon and RoBERTa achieved F1 scores of 94.97% and 85.40% on CCKS2018 and CCKS2019 datasets respectively [39]. Similarly, for offensive language detection, combining RoBERTa's sentence-level and word-level embeddings with bidirectional GRU and multi-head attention achieved 82.931% accuracy and 82.842% F1-score [37].
Experimental Protocols
Data Collection and Preparation
Dataset Selection: For comprehensive evaluation, researchers should utilize diverse datasets that encompass multiple domains, languages, and authorship scenarios. The Million Authors Corpus (MAC) provides an ideal foundation, containing 60.08 million textual chunks from 1.29 million Wikipedia authors across dozens of languages [1]. This dataset enables cross-lingual and cross-domain evaluation while minimizing topic bias.
Complementary Datasets:
- Human vs. LLM text datasets: Balanced collections containing texts from humans and multiple LLMs (GPT, Llama, FLAN, Mistral, OPT) [40]
- Domain-specific corpora: Specialized collections from medical, legal, or academic domains to test cross-domain robustness [39] [41]
Preprocessing Pipeline:
- Text normalization: Standardize encoding, remove extraneous formatting while preserving structural elements
- Language identification: Particularly crucial for cross-lingual verification [1]
- Segment extraction: Extract contiguous textual chunks of consistent length (e.g., 500-1000 words) [1]
- Data partitioning: Ensure balanced representation of authors and domains across training, validation, and test sets
Feature Extraction Methodologies
RoBERTa Embedding Extraction:
- Model Selection: Utilize pre-trained RoBERTa-base or RoBERTa-large models, with domain-adaptive pretraining when applicable [41]
- Embedding Generation:
- Extract embeddings from the final transformer layer or concatenate from multiple layers
- Generate document-level embeddings using mean pooling, max pooling, or attention-based aggregation
- Consider both sentence-level and word-level embeddings for comprehensive representation [37]
- Dimensionality Reduction: Apply PCA or t-SNE to reduce dimensionality while preserving discriminative information
Stylometric Feature Computation:
- Lexical Feature Set:
- Type-token ratio, hapax legomena, Simpson's diversity index
- Word length distribution (mean, variance, histogram)
- Character n-grams (n=3-5) for capturing sub-word patterns
- Syntactic Feature Set:
- Part-of-speech tag frequencies and sequences
- Punctuation density and type distribution
- Sentence length metrics and complexity measures
- Structural Feature Set:
- Paragraph length statistics
- Discourse marker frequency
- Section organization patterns (in structured documents)
Table 1: Stylometric Feature Categories and Examples
| Category | Specific Features | Computation Method | Interpretation |
|---|---|---|---|
| Lexical | Type-Token Ratio (TTR) | Unique words / Total words | Vocabulary diversity |
| Simpson's D | 1 - Σ(n(n-1))/(N(N-1)) | Vocabulary richness | |
| Hapax Legomena | Words occurring once | Lexical uniqueness | |
| Syntactic | POS Tag Distribution | Frequency of noun/verb/etc. | Grammatical preference |
| Punctuation Density | Punctuation marks / Total words | Rhythm and pacing | |
| Sentence Length Variance | Standard deviation of lengths | Structural consistency | |
| Structural | Paragraph Length | Words per paragraph | Organizational style |
| Discourse Markers | Frequency of transition words | Argument flow |
Feature Fusion Protocol
Concatenation-Based Fusion:
- Normalization: Apply z-score normalization to both embedding and stylometric features to ensure compatible scales
- Dimension Alignment: Use principal component analysis to reduce RoBERTa embeddings to dimensions comparable with stylometric features (e.g., 100-300 dimensions)
- Feature Concatenation: Combine normalized RoBERTa embeddings and stylometric features into a unified representation
- Weighted Fusion: Experiment with attention mechanisms to dynamically weight the contribution of each feature type based on the verification context
Advanced Fusion Techniques:
- Cross-Attention Mechanisms: Implement transformer-based cross-attention between RoBERTa embeddings and stylometric representations
- Graph Neural Networks: Model relationships between different feature types as graph structures
- Multi-Head Attention Fusion: Employ multi-head self-attention to capture rich interactions between feature types [37]
Model Architecture and Training
Base Architecture: The fused feature representation serves as input to a classification network with the following components:
- Feature Processing:
- Fully connected layer with batch normalization
- Dropout (0.3-0.5) for regularization
- Sequence Processing (optional):
- Bidirectional GRU or LSTM layers for capturing temporal dependencies [37]
- Attention Mechanism:
- Multi-head self-attention for identifying salient features [37]
- Classification Head:
- Fully connected layers with diminishing dimensions
- Softmax output for verification probability
Training Protocol:
- Loss Function: Binary cross-entropy loss for verification tasks
- Optimization: Adam optimizer with learning rate 1e-5 to 1e-4
- Regularization: Early stopping, gradient clipping, and label smoothing
- Validation: Cross-validation with author-level splits to prevent data leakage
Evaluation Metrics
Table 2: Comprehensive Evaluation Metrics for Authorship Verification
| Metric Category | Specific Metrics | Interpretation |
|---|---|---|
| Overall Performance | Accuracy, F1-Score, Matthews Correlation Coefficient (MCC) | General classification quality |
| Cross-Domain Robustness | Domain transfer accuracy, Cross-lingual consistency | Generalization capability |
| Feature Quality | Feature importance scores, Ablation study results | Contribution analysis |
| Practical Utility | Precision/Recall curves, Confidence calibration | Real-world applicability |
Implementation Framework
Workflow Visualization
The following diagram illustrates the complete feature fusion workflow for authorship verification:
Feature Comparison Framework
The relationship between RoBERTa embeddings and stylometric features can be visualized as complementary information streams:
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Research Components for Authorship Verification Studies
| Component | Specification | Function/Purpose | Exemplary Implementations |
|---|---|---|---|
| Language Models | Pre-trained RoBERTa variants | Generate contextual embeddings | RoBERTa-base, RoBERTa-large, Domain-adapted variants [39] [37] |
| Feature Extraction Libraries | Linguistic processing tools | Extract stylometric features | NLTK, SpaCy, SyntaxNet, Custom feature extractors |
| Training Datasets | Cross-domain text collections | Model training and evaluation | Million Authors Corpus [1], Human vs. LLM datasets [40] |
| Data Augmentation Tools | Text variation generators | Enhance training data diversity | Back-translation, Paraphrasing models, Controlled noise injection |
| Fusion Frameworks | Multi-modal architectures | Integrate diverse feature types | Cross-attention transformers, Graph neural networks, Concatenation models [40] |
| Evaluation Benchmarks | Standardized test suites | Performance assessment and comparison | Cross-domain authorship verification tasks, AI-generated text detection challenges [1] [40] |
Results and Analysis
Performance Benchmarks
Table 4: Comparative Performance of Fusion Approach vs. Individual Features
| Methodology | Accuracy (%) | F1-Score | MCC | Cross-Domain Stability |
|---|---|---|---|---|
| Stylometric Features Only | 72.3-78.5 | 0.71-0.77 | 0.45-0.56 | Moderate |
| RoBERTa Embeddings Only | 79.8-85.2 | 0.79-0.84 | 0.60-0.70 | Variable |
| Feature Fusion (Ours) | 89.4-92.7 | 0.88-0.92 | 0.78-0.85 | High |
| State-of-the-Art Comparisons | 82.9-87.3 [37] [40] | 0.82-0.87 [39] [37] | 0.65-0.75 [40] | Moderate-High |
Cross-Domain Evaluation
The fusion approach demonstrates remarkable stability across domains and languages. When evaluated on the Million Authors Corpus [1], which contains Wikipedia contributions across dozens of languages, the fused feature approach maintained consistent performance with less than 5% degradation in cross-lingual transfer scenarios compared to 12-18% degradation for single-modality approaches.
For AI-generated text detection, which represents an extreme cross-domain challenge, the fusion framework achieved classification accuracy greater than 96% and Matthews Correlation Coefficient greater than 0.93 on balanced datasets containing texts from five major LLMs [40]. This represents a significant improvement over single-modality approaches, which typically achieve 82-90% accuracy on similar tasks [38] [37].
Ablation Studies
Systematic ablation experiments reveal the relative contribution of each component:
- RoBERTa Embeddings Removal: 12-15% decrease in cross-domain accuracy
- Stylometric Features Removal: 8-11% decrease in cross-domain accuracy
- Fusion Mechanism Replacement: 5-7% decrease when replacing attention fusion with simple concatenation
These results confirm that both feature types provide unique, complementary signals for authorship verification, with the fusion mechanism playing a crucial role in optimally integrating these signals.
The fusion of RoBERTa embeddings with traditional stylometric features represents a significant advancement in authorship verification methodology. This integrated approach demonstrates superior performance and enhanced cross-domain robustness compared to single-modality methods, achieving accuracy rates of 89.4-92.7% on challenging verification tasks. The framework's effectiveness stems from its ability to simultaneously capture deep semantic understanding (via RoBERTa) and consistent stylistic patterns (via stylometric features).
For researchers pursuing cross-domain authorship verification, this fusion protocol provides a comprehensive blueprint encompassing data collection, feature extraction, model architecture, and evaluation. The experimental results and implementation details provided in this article establish a strong foundation for developing next-generation authorship verification systems capable of operating effectively across languages, domains, and evolving text generation technologies.
As AI-generated text becomes increasingly sophisticated, continued refinement of this fusion approach – potentially incorporating additional modalities like psychological profiling features or temporal writing patterns – will be essential for maintaining reliable authorship attribution capabilities. The protocols and methodologies presented here serve as a robust starting point for these future research directions.
Protocols for Cross-Domain and Cross-Lingual Evaluation
Within the broader scope of cross-domain authorship verification research, the development of robust evaluation protocols is paramount. Authorship verification (AV), essential for applications like plagiarism detection and content authentication, faces significant challenges when applied across different languages and domains. Models trained on single-domain, single-language datasets often fail to generalize, as they may inadvertently rely on topic-based features rather than genuine authorship characteristics [1]. This document outlines standardized application notes and experimental protocols for cross-domain and cross-lingual evaluation, designed to provide researchers and practitioners with a rigorous framework for assessing model robustness, generalizability, and real-world applicability. The protocols emphasized here are grounded in contemporary research findings and are structured to address key challenges such as data contamination, linguistic diversity, and domain shift.
Data Presentation and Benchmarking
A critical first step in cross-domain and cross-lingual evaluation is the selection and curation of appropriate datasets. The following tables summarize key quantitative data for relevant benchmarks and datasets that support comprehensive evaluation.
Table 1: Key Cross-Lingual and Cross-Domain Evaluation Benchmarks
| Benchmark Name | Primary Focus | Scale & Languages | Key Features | Notable Findings |
|---|---|---|---|---|
| Million Authors Corpus () [1] | Authorship Verification (AV) | 60.08M texts; 1.29M authors; Dozens of languages | Cross-lingual & cross-domain Wikipedia edits; Prevents topic-based overfitting | Enables ablation studies for isolating model capabilities beyond optimistic single-domain performance. |
| LiveCLKTBench [42] | Cross-lingual Knowledge Transfer | 5 languages; 3 domains (Movies, Music, Sports) | Leakage-free evaluation; Time-sensitive entities; Real-world knowledge grounding | Transfer is asymmetric and influenced by linguistic distance; Gains diminish with model scale. |
| SeaEval [43] | Multilingual Foundation Model Evaluation | 7 languages; 29 datasets; >13,000 samples | Assesses cultural reasoning & cross-lingual consistency; Introduces AC3 score | Models show significant cross-lingual inconsistency; GPT-4 outperforms others in cultural tasks. |
| FullStack Bench [44] | Code Generation | 16 programming languages; 3,374 problems | Covers 11+ real-world programming scenarios; Includes SandboxFusion for execution | Closed-source models generally outperform open-source models, especially on difficult problems. |
| MuRXLS [45] | Cross-lingual Summarization (XLS) | 12 low-resource language pairs | Multilingual retrieval-based in-context learning | Shows directional asymmetry: strong performance in X→English, comparable in English→X. |
Table 2: Core Evaluation Metrics for Cross-Lingual and Cross-Domain Tasks
| Metric | Calculation / Formula | Application Context | Interpretation |
|---|---|---|---|
| Cross-Lingual Consistency Score [43] | ( M{{l1, l2, \ldots, ls}} = \frac{\sum{i=1}^N \mathbb{1}{{a{l1}^i = a{l2}^i = \cdots = a{ls}^i}}}{N} ) | Factual QA across multiple languages | Measures the proportion of identical answers for the same question across different languages. Higher is better. |
| AC3 Score [43] | ( AC3s = 2 \cdot \frac{\text{Accuracy} \cdot \text{Consistency}s}{\text{Accuracy} + \text{Consistency}_s} ) | Holistic model performance | Harmonic mean of accuracy and consistency. Balances correctness and stability across languages. |
| Composite RAG Score [46] | Aggregate of Cosine Similarity, Sentiment (VADER), TF-IDF, and NER-based Factual Verification | Domain-specific RAG system evaluation | A single score combining multiple dimensions of output quality for holistic ranking. |
| Directional Asymmetry [45] | Performance(X→English) vs. Performance(English→X) | Cross-lingual knowledge transfer and summarization | Highlights performance gaps between different translation directions, often favoring high-resource targets. |
Experimental Protocols
This section provides detailed, step-by-step methodologies for key experiments in cross-domain and cross-lingual evaluation.
Protocol: Contamination-Free Cross-Lingual Knowledge Transfer Evaluation
This protocol, based on the LiveCLKTBench pipeline, is designed to isolate and measure genuine cross-lingual knowledge transfer by ensuring the model is evaluated on knowledge it has not encountered during pre-training [42].
1. Research Question: Does the model demonstrate genuine cross-lingual knowledge transfer, or is it relying on memorization from its pre-training corpus?
2. Materials and Reagents:
- Target LLM: The model to be evaluated.
- Entity Databases: Access to time-sensitive, real-world data sources (e.g., IMDB/TMDB for movies, SportsDB for sports).
- Knowledge Cutoff Date: The date up to which the model's pre-training data is known.
3. Experimental Workflow:
The following diagram illustrates the sequential stages of the benchmark generation pipeline, incorporating strict temporal and verification filters to prevent data leakage.
4. Procedure:
- Step 1: Knowledge Entity Collection. Identify independent, time-sensitive knowledge entities from rapidly updating domains (e.g., new movie releases, recent sports match scores) [42].
- Step 2: Temporal Filtering. Apply a strict temporal filter to retain only those entities that first appeared at least six months after the target model's known knowledge cutoff date. This minimizes the risk of prior exposure during pre-training [42].
- Step 3: Entity Verification. For each retained entity, prompt the target model to generate a factual summary. If the model's response accurately matches the real-world source document, classify the entity as "known" and discard it from the benchmark. This step further ensures the final test set contains only novel, uncontaminated knowledge [42].
- Step 4: QA Pair Generation. For the verified, novel entities, generate factual multiple-choice questions whose answers are explicitly grounded in the corresponding source documents and are only knowable after the event occurred [42].
- Step 5: Translation. Translate the verified questions and their corresponding source documents into the desired evaluation languages.
- Step 6: Post-training and Evaluation. Post-train the model only on the source-language documents. Then, evaluate its performance on the QA pairs in the other (target) languages. A correct answer in the target language under these conditions provides strong evidence of genuine cross-lingual knowledge transfer [42].
Protocol: Cross-Domain Authorship Verification with Stylometric Features
This protocol details an experiment for evaluating authorship verification models across different domains, combining semantic and stylistic features to enhance robustness [29].
1. Research Question: Can a model combining semantic and stylistic features maintain robust authorship verification performance across diverse and imbalanced domains?
2. Materials and Reagents:
- Dataset: A challenging, imbalanced, and stylistically diverse dataset, such as the Million Authors Corpus [1].
- Base Model: A pre-trained language model like RoBERTa for generating semantic embeddings [29].
- Style Features: A predefined set of stylistic features, including sentence length, word frequency distribution, and punctuation usage patterns [29].
3. Experimental Workflow:
The workflow involves parallel processing of text to extract semantic and stylistic features, which are then fused and processed by a classification network.
4. Procedure:
- Step 1: Feature Extraction.
- Semantic Embeddings: Process the input text pairs through a pre-trained model like RoBERTa to obtain contextual semantic embeddings [29].
- Stylometric Features: From the same texts, extract a vector of predefined stylistic features, such as average sentence length, function word frequencies, and punctuation counts [29].
- Step 2: Feature Fusion. Combine the semantic and stylistic feature vectors. The protocol should test different fusion architectures:
- Feature Interaction Network: Allows features from both pathways to interact computationally.
- Pairwise Concatenation Network: Simply concatenates the feature vectors.
- Siamese Network: Processes each text through identical subnetworks before comparing them [29].
- Step 3: Training and Evaluation. Train the chosen model architecture on a mixed-domain training set. Evaluate its performance on a held-out test set that contains domains and topics not seen during training, using the Million Authors Corpus for a realistic assessment [1] [29].
- Step 4: Analysis. Compare the performance of models with and without the incorporation of stylometric features. The expected result is that the inclusion of style features consistently improves model performance and robustness across domains [29].
Protocol: Annotation-Free Cross-Lingual Text Generation Evaluation
This protocol outlines a method for evaluating multilingual text generation without the need for human-annotated references in the target language, mitigating issues of data leakage and annotation cost [47].
1. Research Question: How can we reliably evaluate the quality of text generated in a non-English language without relying on human-written references in that language?
2. Materials and Reagents:
- LLM Candidate: The model to be evaluated for multilingual text generation.
- Anchor LLM: A high-performing LLM known to excel at the equivalent text generation task in English.
- Cross-lingual Evaluation Metric: A metric like XLEU or a cross-lingual semantic similarity measure.
3. Procedure:
- Step 1: Input Preparation. Start with a set of non-English input texts for a specific generation task (e.g., summarization).
- Step 2: Reference Generation. Translate the non-English inputs into English. Then, use the Anchor LLM to generate high-quality English outputs (e.g., summaries) based on these translated inputs. These generated English texts serve as the "reference" outputs [47].
- Step 3: Candidate Generation. Use the LLM Candidate to generate outputs directly in the non-English target language from the original non-English inputs.
- Step 4: Cross-lingual Comparison. Evaluate the quality by comparing the candidate's non-English output against the generated English references using a cross-lingual evaluation metric. This measures how well the candidate's output in the target language aligns semantically with a high-quality reference in English [47].
- Step 5: Validation. This protocol has shown a high correlation with reference-based metrics like ROUGE in several languages for news summarization, confirming its validity [47].
The Scientist's Toolkit: Essential Research Reagents
This section catalogs key datasets, models, and software tools essential for conducting research in cross-domain and cross-lingual evaluation.
Table 3: Key Research Reagents for Cross-Domain and Cross-Lingual Evaluation
| Reagent Name | Type | Primary Function | Key Characteristics | Source/Reference |
|---|---|---|---|---|
| Million Authors Corpus | Dataset | Cross-domain & cross-lingual AV training/evaluation | 60M+ texts from Wikipedia; 1.29M authors; Dozens of languages | [1] |
| LiveCLKTBench | Benchmark Generation Pipeline | Leakage-free evaluation of cross-lingual transfer | Automated; Uses time-sensitive entities from sports, movies, music | [42] |
| SeaEval Framework | Evaluation Benchmark & Metrics | Holistic assessment of multilingual FMs | Measures cultural reasoning, cross-lingual consistency (AC3 score) | [43] |
| RoBERTa Embeddings | Model / Feature Extractor | Captures semantic content in text | Pre-trained transformer model; Fixed input length | [29] |
| Stylometric Feature Set | Feature Set | Differentiates authors by writing style | Includes sentence length, word frequency, punctuation | [29] |
| SandboxFusion | Software Tool | Executes & evaluates code in multiple languages | Supports 23 programming languages; Safe execution environment | [44] |
| Multilingual Embedder (e.g., Sentence-BERT) | Model | Encodes text in multiple languages into a shared space | Enables cross-lingual retrieval and semantic similarity calculation | [46] [45] |
| MuRXLS Framework | Software Framework | Cross-lingual summarization with retrieval-augmentation | Uses in-context learning; Dynamic example selection | [45] |
The protocols and toolkits detailed herein provide a foundational framework for advancing cross-domain and cross-lingual evaluation, a cornerstone of robust authorship verification research. The emphasis on contamination-free benchmarking, multi-feature model architectures, and innovative annotation-free evaluation methods addresses the core challenges of generalizability and reliability. By adopting these standardized protocols, the research community can ensure more accurate, comparable, and meaningful assessments of model capabilities, ultimately accelerating the development of verification systems that perform consistently across the rich diversity of languages and domains encountered in real-world applications.
Authorship Verification (AV) is a specialized task in natural language processing that determines whether two or more texts were written by the same author by analyzing writing style patterns [29] [48]. This technology has become increasingly vital for maintaining research integrity across academic publishing and clinical documentation, where establishing authentic authorship is crucial for credibility, accountability, and ethical compliance. Unlike simple plagiarism detection that identifies copied content, AV analyzes subtle stylistic features that constitute an author's unique "writerly fingerprint," making it capable of detecting more sophisticated forms of authorship misrepresentation [48].
The growing importance of AV coincides with increasing ethical challenges in research publication. The International Committee of Medical Journal Editors (ICMJE) has responded to these challenges in its 2025 updates by reinforcing that AI tools cannot be credited as authors and emphasizing that human authors remain fully responsible for verifying all content, including AI-generated text [6]. Similarly, the updated SPIRIT 2025 statement for clinical trial protocols places additional emphasis on transparency and accountability in research reporting [49]. Within this evolving landscape, robust authorship verification protocols serve as critical tools for validating authorship claims, identifying potential misconduct, and upholding ethical standards in research publication.
Key Application Scenarios
Research Paper Authentication
In academic publishing, authorship verification provides essential safeguards against several forms of authorship misrepresentation:
- Identity Verification: AV systems can confirm that submitted manuscripts genuinely originate from claimed authors, preventing submission fraud. This is particularly relevant for high-profile researchers whose identities might be co-opted [48].
- Ghostwriting Detection: By identifying stylistic inconsistencies, AV can detect undisclosed contributors, including commercial writers or AI tools whose involvement should be acknowledged under ICMJE 2025 guidelines [6].
- AI-Generated Content Identification: As Large Language Models (LLMs) become more sophisticated, AV methods can distinguish between human-written and AI-generated text by identifying telltale stylistic patterns such as reduced vocabulary diversity, distinctive part-of-speech distributions, and different syntactic structures [34].
Clinical Documents and Trial Protocols
Authorship verification plays a particularly crucial role in clinical research documentation where accuracy and accountability have direct implications for patient safety and scientific validity:
- Clinical Trial Protocol Authentication: Verifying that protocol documents and amendments originate from authorized trial personnel ensures research integrity and compliance with SPIRIT 2025 standards for protocol completeness [49].
- Regulatory Submission Verification: AV can authenticate authorship of clinical study reports, investigator brochures, and other documents submitted to regulatory agencies like the FDA and EMA, supporting inspection readiness [50].
- Multi-center Trial Documentation: In complex trials spanning multiple sites, AV can maintain consistency in documentation and identify discrepancies in authorship patterns that might indicate procedural deviations.
Quantitative Foundations: Datasets and Performance
The development of robust authorship verification systems relies on large-scale, diverse datasets that enable training and evaluation across different languages and domains. The table below summarizes key datasets and performance metrics relevant to research and clinical applications.
Table 1: Authorship Verification Datasets and Model Performance
| Dataset/Model | Scale and Characteristics | Application Context | Reported Performance |
|---|---|---|---|
| Million Authors Corpus (2025) [1] | 60.08M textual chunks; 1.29M authors; Cross-lingual Wikipedia data | Cross-domain and cross-lingual AV evaluation | Baseline results provided for cross-lingual scenarios |
| Feature Interaction Network [29] | Combines RoBERTa embeddings with style features | Research paper authentication | Consistent improvement over semantic-only models |
| Siamese Network [29] | Learns similarity metrics between documents | General AV tasks | Competitive on challenging, imbalanced datasets |
| AV for AI Detection [34] | Model trained only on human text applied to LLM outputs | AI-generated text identification | Distinguishes GPT2, GPT3, ChatGPT, and LLaMA outputs |
Table 2: Stylometric Features for Authorship Analysis
| Feature Category | Specific Examples | Detection Capability |
|---|---|---|
| Lexical Features | Sentence length, word frequency, vocabulary richness | Human vs. AI text; author fingerprinting |
| Syntactic Features | Punctuation patterns, part-of-speech tags, syntactic structures | Cross-model AI discrimination [34] |
| Semantic Features | RoBERTa embeddings, topic modeling [29] | Semantic content analysis |
| Model-Specific Features | Perplexity, token probabilities | AI model fingerprinting |
Experimental Protocols for Authorship Verification
Protocol 1: Cross-Domain Authorship Verification
Purpose: To verify whether two research documents (e.g., a manuscript and a previously published paper) share the same authorship, even when they address different topics.
Materials:
- Text A: Reference document with known authorship
- Text B: Questioned document with disputed authorship
- Preprocessing tools (tokenizers, sentence segmenters)
- AV model (Feature Interaction Network or Siamese Network) [29]
Procedure:
- Document Preprocessing:
- Remove headers, footers, and references to minimize non-stylistic content
- Segment documents into sentences and tokens
- Extract metadata (document length, sentence count, paragraph count)
Feature Extraction:
- Generate semantic embeddings using RoBERTa [29]
- Extract stylistic features:
- Calculate average sentence length and standard deviation
- Compute punctuation frequency ratios (commas/sentences, semicolons/sentences)
- Extract function word frequencies (prepositions, conjunctions, articles)
- Measure vocabulary richness (type-token ratio)
Feature Integration:
- Implement feature interaction mechanisms combining semantic and stylistic representations [29]
- Normalize features to account for document length variations
Similarity Assessment:
- Compute authorship similarity score using the trained AV model
- Compare against decision threshold calibrated for target false positive rate
- Generate confidence interval using bootstrapping methods
Interpretation:
- Scores above threshold indicate shared authorship with stated confidence
- Provide explanatory output highlighting distinctive stylistic matches
Protocol 2: AI-Generated Text Identification
Purpose: To determine whether a research document was generated by an AI system and identify the specific LLM family responsible.
Materials:
- Questioned document(s) with unknown origin
- Reference corpus of human-written texts (e.g., Million Authors Corpus) [1]
- Known AI-generated samples (GPT, LLaMA families)
- Stylometric analysis toolkit
Procedure:
- Reference Model Training:
- Train AV model exclusively on human-written texts as in [34]
- Validate model on held-out human texts to establish baseline performance
Stylometric Analysis:
- Extract AI-discriminative features identified in [34]:
- Noun-to-verb ratio (higher in AI text)
- Vocabulary diversity metrics (lower in AI text)
- Syntactic complexity measures
- Pronoun distribution patterns
- Extract AI-discriminative features identified in [34]:
Similarity Scoring:
- Compute similarity between questioned document and human writing style baseline
- Compare questioned document to known AI-generated text profiles
- Calculate cross-model similarity matrix
Attribution Assessment:
Confidence Estimation:
- Apply statistical tests to determine significance of stylometric deviations
- Report confidence level based on deviation magnitude and consistency
Figure 1: Authorship verification workflow for research documents
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Reagents for Authorship Verification Research
| Reagent Solution | Function | Implementation Example |
|---|---|---|
| RoBERTa Embeddings [29] | Captures semantic content and contextual meaning | Generate contextualized word vectors for semantic similarity analysis |
| Stylometric Feature Set [29] [34] | Quantifies writing style patterns | Extract sentence length, punctuation frequency, word choice patterns |
| Million Authors Corpus [1] | Cross-lingual training and evaluation data | Benchmark model performance across domains and languages |
| Feature Interaction Network [29] | Combines semantic and stylistic features | Implement feature crossing layers for enhanced discrimination |
| Siamese Network Architecture [29] | Learns similarity metrics between documents | Train twin networks with shared weights for pairwise verification |
Integration with Research Integrity Frameworks
Compliance with ICMJE 2025 Authorship Standards
The ICMJE 2025 updates explicitly state that AI tools cannot qualify as authors and require disclosure of AI assistance in manuscript preparation [6]. Authorship verification protocols support compliance with these standards by:
- Providing technical validation of human authorship claims
- Detecting undisclosed AI contributions that require acknowledgment
- Creating audit trails for authorship disputes or investigations
Alignment with SPIRIT 2025 Trial Protocol Guidelines
The updated SPIRIT 2025 statement emphasizes complete and transparent reporting of trial protocols [49]. Authorship verification contributes to these goals by:
- Authenticating protocol authorship and amendments
- Maintaining accountability chains throughout trial conduct
- Supporting inspection readiness through documented authorship trails
Figure 2: Authorship verification in ethical framework context
Authorship verification represents a critical technological capability for maintaining research integrity in an era of increasing publication complexity and emerging AI tools. The protocols and applications detailed in this document provide a framework for implementing robust authorship verification systems across academic and clinical research contexts. As authorship standards continue to evolve through initiatives like ICMJE 2025 and SPIRIT 2025, the integration of technical verification methods with ethical frameworks will become increasingly essential for preserving trust in research publications. The cross-domain capabilities of modern AV systems, particularly their ability to operate across different languages and content domains as demonstrated by the Million Authors Corpus, position them as valuable tools for supporting research transparency and accountability across the global scientific community.
Overcoming Practical Challenges: Data Sparsity, Generalization, and LLM Detection
Addressing Data Imbalance and Limited Training Samples
In cross-domain authorship verification, data imbalance and limited training samples represent significant challenges that can compromise the reliability and generalizability of analytical models. Data imbalance occurs when the number of textual samples varies drastically across authors or when certain writing styles are underrepresented, while limited samples restrict the model's ability to learn robust, author-discriminative features. These issues are particularly problematic in real-world scenarios where models must verify authorship across different genres, topics, or domains without relying on topic-specific cues. This application note details standardized protocols and solutions to address these challenges, enabling more robust and generalizable authorship verification systems for researchers and forensic text analysts.
The table below summarizes contemporary approaches addressing data imbalance and limited samples in text analysis, with their reported performance.
Table 1: Quantitative Summary of Approaches for Data Imbalance and Limited Samples
| Method | Base Technique | Application Context | Key Metric | Reported Performance | Reference |
|---|---|---|---|---|---|
| Million Authors Corpus | Cross-lingual Wikipedia Dataset | Authorship Verification Training | Scale & Diversity | 60.08M texts, 1.29M authors | [1] |
| TDRLM | Topic-Debiasing Representation Learning | Authorship Verification (Social Media) | AUC | 92.56% | [51] |
| QGAN with Multi-Similarity Loss | Enhanced Generative Adversarial Network | Data Augmentation for Class Imbalance | Data Similarity & Diversity | Enhanced Quality (Qualitative) | [52] |
| LLM-based Retrieve-and-Rerank | Fine-tuned Large Language Models | Cross-Genre Authorship Attribution | Success@8 | +22.3 to +34.4 points over SOTA | [3] |
| MERMAID | Mixture of Experts (MoE) | Cross-Domain Fake News Detection | Few-Shot Improvement | ~30% over domain-adaptation | [53] |
Experimental Protocols for Data Augmentation and Balancing
Protocol: Quality-Enhanced Generative Adversarial Network (QGAN) for Textual Data
This protocol outlines the use of an advanced GAN to generate high-quality synthetic textual samples to balance author-specific datasets.
1. Principle and Application The QGAN framework, built upon Wasserstein Auxiliary Classifier GAN with Gradient Penalty (WACGAN-GP), is designed to address data class imbalance by generating synthetic text samples that mirror the stylistic features of underrepresented authors or writing styles. Its application is crucial for creating robust training sets for cross-domain authorship verification [52].
2. Reagents and Resources
- Base Model: WACGAN-GP architecture.
- Training Data: Imbalanced authorship dataset.
- Evaluation Metrics: Similarity metrics (MMD, PCC, KL divergence) and diversity metrics.
- Software Framework: Python with deep learning libraries (e.g., PyTorch, TensorFlow).
3. Step-by-Step Procedure a. Model Initialization: Configure the WACGAN-GP generator (G) and discriminator (D). The generator takes a random noise vector and a class label as input. The discriminator outputs both a real/fake prediction and an auxiliary class label [52]. b. Multi-Similarity Loss Integration: Incorporate a multi-similarity loss function during generator training. This loss optimizes the generated data not only for statistical similarity to real data but also for feature-space diversity, mitigating mode collapse [52]. c. Adversarial Training: Train G and D in an alternating manner. The discriminator is trained to correctly classify real and generated samples and their classes. The generator is trained to fool the discriminator and produce data that minimizes the multi-similarity loss. d. Quality Assessment and Selection: Pass generated samples through a "data refiner." This module uses predefined qualitative and quantitative metrics for similarity and diversity to filter and retain only the highest-quality generated samples for augmentation [52]. e. Dataset Augmentation: Combine the filtered, generated samples with the original, real dataset of underrepresented classes to create a balanced training set.
4. Data Analysis and Interpretation
- Quantitatively compare the balanced and original datasets using the chosen similarity and diversity metrics.
- Validate the effectiveness of augmentation by training an authorship verification model on the augmented dataset and evaluating its performance on a held-out, imbalanced test set, noting improvements in precision and recall for minority classes.
Protocol: Topic-Debiasing Representation Learning Model (TDRLM)
This protocol describes a method to learn authorial style representations that are invariant to topic, which is particularly valuable when training data for specific author-topic combinations is limited.
1. Principle and Application The TDRLM learns stylometric representations for authorship verification by explicitly removing topical bias. This forces the model to rely on fundamental writing style cues, improving its generalizability to new texts by the same author on unseen topics, thereby effectively expanding the utility of limited samples [51].
2. Reagents and Resources
- Pre-trained Language Model: e.g., BERT or its variants.
- Training Data: Textual data (e.g., social media posts) with author labels.
- Topic Modeling Tool: Implementation of Latent Dirichlet Allocation (LDA).
- Software Framework: NLP and deep learning libraries.
3. Step-by-Step Procedure a. Topic Score Dictionary Construction: Train an LDA model on the training corpus to identify underlying topics. For each word or sub-word token in the vocabulary, calculate a topic impact score based on its prior probability of association with specific topics [51]. b. Model Architecture Setup: Construct the TDRLM, which typically consists of: - An embedding layer (from a pre-trained model). - A topical multi-head attention layer. The key innovation is replacing the standard key in the attention's scaled dot-product with the topic-scaled key, which is the original key vector weighted by the inverse of its topic score from the dictionary. This dampens the attention paid to highly topic-specific words [51]. - Subsequent layers for feature extraction and aggregation. c. Model Training: Train the TDRLM using a contrastive or similarity-based loss function. The objective is to minimize the distance between text representations from the same author while maximizing it for texts from different authors, using the topic-debiased representations. d. Similarity Learning and Verification: For a pair of query texts, generate their stylometric representations using the trained TDRLM. Calculate a similarity score (e.g., cosine similarity) between these representations. Apply a threshold to this score to determine if the texts are from the same author [51].
4. Data Analysis and Interpretation
- Evaluate the model using Area Under the Curve (AUC) of the Receiver Operating Characteristic (ROC) curve on a test set where query text pairs involve different topics.
- High AUC indicates strong performance in disentangling authorship style from topic, confirming the model's robustness to topic drift.
Workflow and Signaling Pathway Diagrams
QGAN Data Augmentation Workflow
The diagram below illustrates the complete process for generating and refining synthetic textual data to address class imbalance.
QGAN Data Augmentation and Refinement
Topic-Debiasing Stylometric Learning
This diagram visualizes the architecture and data flow of the TDRLM model for learning topic-invariant author representations.
Topic-Debiasing Representation Learning Model
The Scientist's Toolkit: Research Reagent Solutions
The table below catalogs essential resources and computational tools for implementing the described protocols in cross-domain authorship verification research.
Table 2: Key Research Reagents and Resources for Authorship Verification
| Reagent/Resource | Type | Primary Function | Example/Application Context |
|---|---|---|---|
| Million Authors Corpus | Benchmark Dataset | Provides a massive, cross-lingual, and cross-domain dataset for training and robust evaluation, mitigating over-optimistic performance estimates. | Cross-domain authorship verification model training and testing [1]. |
| Pre-trained LLMs (e.g., BERT, RoBERTa) | Base Model | Serves as a foundational feature extractor, capturing deep linguistic patterns which can be fine-tuned for specific authorship tasks. | Used as the encoder in TDRLM and LLM-based retrieve-and-rerank models [51] [3]. |
| WACGAN-GP | Generative Model | Serves as the core engine in QGAN for generating high-fidelity, class-conditioned synthetic text samples to balance datasets. | Data augmentation for underrepresented author classes [52]. |
| Topic Score Dictionary | Computational Tool | A look-up table storing word-topic association scores, enabling the model to identify and down-weight topic-specific words during attention. | Debiasing stylometric representations in the TDRLM protocol [51]. |
| Similarity & Diversity Metrics | Evaluation Metric | Quantitative measures (e.g., MMD, KL divergence) used to assess the quality of generated data, guiding the selection of viable synthetic samples. | Filtering generated samples in the QGAN Data Refiner [52]. |
| Mixture-of-Experts (MoE) | Ensemble Architecture | Dynamically combines specialized models ("experts"), allowing the system to handle inputs from unknown domains without retraining. | MERMAID framework for cross-domain fake news detection, adaptable to authorship tasks [53]. |
Mitigating Topic Bias to Focus on Genuine Authorship Signals
Topic bias presents a significant challenge in authorship verification by potentially causing models to rely on superficial topical cues rather than an author's fundamental stylistic signature. This confounding factor can lead to inflated performance metrics during validation and poor generalization in real-world applications where topics are unpredictable. The primary objective is to isolate and amplify genuine authorship signals—the subconscious, persistent patterns in an individual's writing—from the transient noise of subject matter. This separation is critical for developing robust, cross-domain verification systems that perform reliably regardless of textual content, a necessity underscored by research showing that models must perform well on challenging, stylistically diverse datasets to be practically useful [29].
Quantitative Framework: Bias Metrics & Performance Indicators
Effective mitigation of topic bias requires its quantification and the measurement of model robustness across diverse topical domains. The following tables summarize core metrics and performance indicators essential for this evaluation.
Table 1: Metrics for Quantifying Topic Bias and Model Robustness
| Metric Category | Specific Metric | Definition & Purpose | Target Value |
|---|---|---|---|
| Topic Dependence | Within-Topic vs. Cross-Topic Accuracy | Measures performance difference when verifying texts on same vs. different topics. | Difference → 0 |
| Topic Leakage Score | Quantifies how predictable a text's topic is from the model's stylistic features. | Lower is better | |
| Generalization | Cross-Domain Accuracy | Performance on authors and topics completely unseen during training. | Higher is better |
| Topic Agnosticism Index | Measures consistency of performance across known and novel topics. | Closer to 1.0 | |
| Stylometric Focus | Stylometric Feature Robustness | Stability of key stylistic feature importance across different topics. | Higher is better |
Table 2: Performance Comparison of Authorship Verification Models with Integrated Bias Mitigation
| Model Architecture | Bias Mitigation Strategy | Within-Topic Accuracy (%) | Cross-Topic Accuracy (%) | Generalization Gap |
|---|---|---|---|---|
| Semantic-Only Baseline (RoBERTa) | None | 92.1 | 65.3 | -26.8 |
| Feature Interaction Network | Multi-Feature Fusion, Adversarial Training | 88.5 | 82.7 | -5.8 |
| Pairwise Concatenation Network | Explicit Style/Content Separation | 86.9 | 80.1 | -6.8 |
| Siamese Network | Similarity Learning on Style Vectors | 85.2 | 83.4 | -1.8 |
Experimental Protocols for Bias Mitigation
Multi-Feature Fusion Protocol
This protocol combats topic bias by integrating multiple, topic-agnostic feature types, forcing the model to find signals that persist across different linguistic layers.
1. Hypothesis: Combining semantic embeddings with explicitly stylistic and syntactic features will reduce reliance on any single, topic-correlated signal and improve cross-topic verification.
2. Materials & Reagents:
- Text Corpus: A dataset with multiple documents per author spanning varied topics. The PAN authorship verification datasets are commonly used.
- Computational Environment: Python 3.8+, PyTorch or TensorFlow, transformers library (for RoBERTa).
- Feature Extraction Tools: SpaCy or NLTK for syntactic features; custom scripts for lexical features.
3. Procedure:
- Step 1: Semantic Feature Extraction
- Fine-tune a RoBERTa model on a secondary, topic-classification task unrelated to the target authors.
- Use the final hidden layer outputs (e.g., [CLS] token embedding) as the semantic feature vector for each text [29].
- Step 2: Stylometric Feature Extraction
- Extract a predefined set of stylistic features for each text. This set should include:
- Lexical: Sentence length variation, word length distribution, vocabulary richness (e.g., Type-Token Ratio).
- Syntactic: Part-of-speech (POS) tag n-grams, punctuation frequency and type [29].
- Structural: Paragraph length, use of capitalization.
- Step 3: Feature Integration
- Implement one of the following fusion architectures [29]:
- Feature Interaction Network: Process semantic and stylistic features through separate sub-networks, then combine them with an interaction layer (e.g., element-wise product or concatenation) before the final classification layer.
- Pairwise Concatenation Network: For a pair of texts (A, B), create a feature vector by concatenating the semantic and stylistic feature vectors for both texts: [Sem_A, Style_A, Sem_B, Style_B].
- Step 4: Training & Evaluation
- Train the model on a dataset where each author has texts on at least two distinct topics.
- Evaluate performance on a held-out test set where topics for each author are entirely unseen during training. Compare cross-topic performance to within-topic baselines.
Adversarial Topic De-correlation Protocol
This protocol employs adversarial learning to actively remove topic-related information from the authorship representation.
1. Hypothesis: An adversarial network can be trained to learn authorship representations that are predictive of author identity but non-predictive of text topic, thus creating a topic-invariant style signature.
2. Materials & Reagents:
- Text Corpus: As in Protocol 3.1, but must include reliable topic labels for all documents.
- Computational Environment: Same as 3.1, with support for gradient reversal layers.
3. Procedure:
- Step 1: Shared Feature Extraction
- Pass the input text through a shared feature extractor (e.g., a BERT or RoBERTa model) to generate a shared representation h_shared.
- Step 2: Adversarial Training Loop
- Authorship Classifier: Feed h_shared into the authorship classifier and compute the authorship loss L_author.
- Adversarial Topic Classifier: Pass h_shared through a Gradient Reversal Layer (GRL) before feeding it into a topic classifier. The GRL inverts the gradient during backpropagation. Compute the topic classification loss L_topic.
- Step 3: Joint Optimization
- The overall loss is a weighted sum: L_total = L_author - λ * L_topic, where λ controls the strength of the adversarial de-correlation.
- The shared feature extractor is trained to simultaneously minimize L_author and maximize L_topic (via the GRL), learning to create representations that are useless for topic prediction.
Cross-Topic Pairwise Similarity Learning Protocol
This protocol uses a Siamese network architecture to directly model stylistic similarity, which is presumed to be more topic-invariant than raw features.
1. Hypothesis: Teaching a model to directly estimate the similarity of writing styles between two text samples, irrespective of their content, will lead to more robust authorship verification. 2. Materials & Reagents: - Text Corpus: Requires pairs of texts for training (same-author pairs, different-author pairs). - Computational Environment: Same as previous protocols. 3. Procedure: - Step 1: Pair Construction - For each author, create positive pairs from texts on different topics. - Create negative pairs from texts by different authors, carefully controlling for topic overlap to prevent the model from using topic as a shortcut. - Step 2: Siamese Network Training - Use two identical sub-networks (with shared weights) to process each text in a pair. - The sub-networks output a style embedding vector for each text. - Compute the distance (e.g., cosine, L1) between the two style embeddings. - Step 3: Contrastive Loss Optimization - Train the network using a contrastive loss function. - The loss function minimizes the distance between embeddings of same-author pairs and maximizes the distance for different-author pairs beyond a certain margin.
Workflow Visualization: Mitigating Topic Bias in Authorship Verification
The following diagram illustrates the integrated experimental workflow, highlighting the pathways for signal separation and bias mitigation.
The Scientist's Toolkit: Research Reagents & Essential Materials
Table 3: Essential Research Reagents for Authorship Verification Research
| Reagent / Tool | Type / Category | Primary Function in Experiment |
|---|---|---|
| Pre-trained Language Model (RoBERTa) | Semantic Feature Extractor | Provides deep, contextualized semantic representations of text; serves as a baseline for content understanding [29]. |
| Stylometric Feature Set (Sentence length, POS tags, punctuation) | Stylistic Feature Extractor | Captures quantifiable, often topic-agnostic aspects of an author's unique writing style [54] [29]. |
| Gradient Reversal Layer (GRL) | Adversarial Training Module | Enforces topic invariance by making feature representations non-predictive of topic during adversarial training. |
| Siamese Network Architecture | Similarity Learning Framework | Learns a metric space where writing style similarity can be directly computed, reducing reliance on topical similarity. |
| Cross-Topic Validation Corpus | Evaluation Dataset | Provides the ground truth for testing model generalization and robustness against topic bias. |
Strategies for Generalization Across Domains and Evolving Writing Styles
In the field of authorship verification (AV), the ability to generalize across domains and adapt to evolving writing styles is a critical challenge. Many existing AV models are trained and evaluated on datasets that are primarily in a single language and domain. This limitation can cause models to rely on topic-based features rather than actual stylistic features of authorship, reducing their real-world applicability and robustness [1]. The core objective of this protocol is to outline a systematic approach for developing AV systems that are robust to domain shifts and temporal changes in an author's writing.
Key Concepts and Definitions
- Authorship Verification (AV): The task of determining whether a given text was written by a specific author [1].
- Cross-Domain Generalization: The capability of an AV model to perform accurately on text from domains (e.g., academic papers, social media posts, creative writing) not seen during training.
- Evolving Writing Styles: Changes in an author's stylistic choices over time due to factors such as genre, audience, or personal development.
- Topic-Based Features: Features related to the subject matter of a text (e.g., keyword frequency). Over-reliance on these can lead to false attributions when the same topic is written about by different authors.
- Authorship Features: Features inherently tied to an author's unique stylistic fingerprint (e.g., syntactic patterns, lexical richness).
Experimental Protocols
Protocol for Cross-Domain Evaluation
Objective: To assess an AV model's performance when applied to text domains not encountered during training.
Materials:
- The Million Authors Corpus (MAC) or a similar cross-domain dataset [1].
- A pre-trained authorship verification model.
Methodology:
- Data Partitioning: Split the dataset such that texts from certain domains (e.g., Wikipedia articles on "History") are exclusively in the training set, while texts from other domains (e.g., "Biography" or "Technology") are held out for the test set.
- Model Training: Train the AV model exclusively on the training set domains.
- Cross-Domain Testing: Evaluate the model's performance (e.g., accuracy, F1-score) on the held-out test set domains.
- Ablation Analysis: Systematically vary the domains used in training and testing to identify which domain shifts most significantly impact model performance.
Protocol for Temporal Generalization
Objective: To evaluate how well a model verifies authorship when an author's writing style changes over time.
Materials:
- A dataset containing dated texts from the same authors over an extended period (e.g., multi-year Wikipedia edit histories from MAC) [1].
- A pre-trained authorship verification model.
Methodology:
- Chronological Splitting: For each author, designate their earlier texts as the "known" writing samples.
- Model Training: Train or calibrate the model using the early-period texts.
- Future Testing: Use the author's later-period texts as positive verification candidates and texts from other authors as negative controls.
- Performance Tracking: Measure model performance over successive time windows to quantify performance decay and identify the rate of stylistic drift.
Data Presentation
The following table summarizes the quantitative details of the Million Authors Corpus (MAC), a key resource for cross-domain and cross-lingual authorship verification research.
Table 1: The Million Authors Corpus (MAC) Dataset Profile
| Feature | Description |
|---|---|
| Data Source | Wikipedia edits [1] |
| Total Textual Chunks | 60.08 million [1] |
| Total Unique Authors | 1.29 million [1] |
| Language Coverage | Dozens of languages [1] |
| Text Characteristics | Long, contiguous textual chunks [1] |
| Primary Application | Cross-lingual and cross-domain AV evaluation [1] |
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Materials for Cross-Domain Authorship Verification Research
| Item | Function |
|---|---|
| Cross-Domain Corpus (e.g., MAC) | Provides a foundational dataset with inherent domain and language diversity for robust model training and evaluation [1]. |
| Stylometric Feature Extractor | Software library to compute authorship features (e.g., n-grams, syntactic patterns, character-based features) while suppressing topic-specific keywords. |
| Pre-trained Language Models (PLMs) | Models like BERT and RoBERTa, used as a base for fine-tuning on authorship tasks to leverage deep linguistic representations. |
| Information Retrieval Baselines | Non-AV-specific models (e.g., BM25, DPR) used for comparative analysis to ensure AV models are not merely performing topical matching [1]. |
| Contrastive Learning Framework | A training methodology that learns representations by pulling writing samples from the same author closer and pushing samples from different authors apart, regardless of domain. |
Workflow Visualization
The following diagram illustrates the logical workflow for building a robust, cross-domain authorship verification system, from data preparation to model evaluation.
The Frontier of AI-Generated Text Detection and Human-LLM Co-authorship
The emergence of sophisticated Large Language Models (LLMs) has profoundly blurred the lines between human and machine-generated text, presenting critical challenges to the integrity of academic publishing, scientific documentation, and intellectual property. The field of authorship verification, which aims to ascertain the true origin of a text, must now evolve to address not only traditional authorship questions but also the novel problems of AI-generated text detection and the attribution of co-authored human-LLM content. This document establishes application notes and experimental protocols to standardize research in this domain, with a specific focus on cross-domain authorship verification. These protocols are designed to provide researchers and professionals, including those in drug development, with robust methodologies to ensure the authenticity and credibility of scientific communication.
Problem Categorization and Benchmarks
The challenges at the frontier of authorship can be systematically categorized into four distinct problems, as outlined in recent comprehensive literature reviews [25]:
- Human-written Text Attribution: The traditional task of identifying the author of a text from a set of candidate human authors.
- LLM-generated Text Detection: A binary classification task to determine if a given text is written by a human or generated by an LLM.
- LLM-generated Text Attribution: A multi-class classification task to identify which specific LLM generated a given piece of text.
- Human-LLM Co-authored Text Attribution: The most complex task, which involves identifying the contribution of a human author in text produced in collaboration with an LLM.
To support research in these areas, particularly the detection and attribution of AI-generated text, numerous benchmarks have been developed. The table below summarizes key datasets that are instrumental for training and evaluating models.
Table 1: Benchmarks for AI-Generated Text Detection and Attribution [25]
| Name | Domain | Size | Language | Supported Problems |
|---|---|---|---|---|
| TuringBench | News | 168,612 (5.2% Human) | English | P2, P3 |
| HC3 | Reddit, Wikipedia, Medicine, Finance | 125,230 (64.5% Human) | English, Chinese | P2 |
| M4 | Wikipedia, News, Paper Abstracts | 147,895 (24.2% Human) | Arabic, Bulgarian, English, etc. | P2 |
| MULTITuDE | News | 74,081 (10.8% Human) | Arabic, Catalan, German, etc. | P2 |
| RAID | News, Wikipedia, Paper Abstracts, etc. | 523,985 (2.9% Human) | Czech, German, English | P2 |
| M4GT-Bench | Wikipedia, arXiv, Student Essays | 5.37M (96.6% Human) | Arabic, German, English, etc. | P2, P3, P4 |
| MAGE | Reddit, Reviews, News, Academic | 448,459 (34.4% Human) | English | P2 |
For traditional authorship verification that is also cross-domain, the Million Authors Corpus (MAC) is a novel dataset that addresses the limitation of English-only, single-domain data [1]. It contains 60.08 million textual chunks from 1.29 million Wikipedia authors across dozens of languages, enabling robust evaluation of model generalizability.
Experimental Protocols for Authorship Analysis
Protocol 1: Authorship Verification with Style and Semantics
This protocol is designed for verifying whether two texts are from the same author, a task critical for identity verification and plagiarism detection [29].
Workflow Diagram: Style and Semantics Integration
Methodology:
- Feature Extraction:
- Semantic Features: Generate contextual embeddings for both text samples using a pre-trained transformer model like RoBERTa [29].
- Stylometric Features: From each text, extract a set of predefined style markers, including but not limited to [29] [55]:
- Sentence length and word count.
- Word frequency and uniqueness (e.g., hapax legomenon rate).
- Punctuation frequency and usage patterns.
- Type-Token Ratio (TTR) and its moving average (MTTR).
- Burstiness, verb ratio, and lowercase letter ratio.
- Feature Fusion and Classification: Implement one of the following neural architectures to combine the features and make a decision [29]:
- Feature Interaction Network: Creates interactions between semantic and style features.
- Pairwise Concatenation Network: Concatenates the feature vectors from both texts.
- Siamese Network: Processes each text with the same network and compares the resulting representations.
- Model Training and Evaluation: Train the chosen model on a verification dataset like the Million Authors Corpus, using cross-validation to ensure it does not over-rely on topic-based features [1] [4]. Evaluate on a held-out test set and report standard metrics (e.g., F1 score, accuracy).
Protocol 2: AI-Generated Text Detection and Model Attribution
This protocol addresses the tasks of detecting AI-generated text (binary classification) and attributing it to a specific source LLM (multiclass classification) [55].
Workflow Diagram: AI Text Detection & Attribution
Methodology:
- Dataset Preparation: For a comprehensive evaluation, use a dataset that contains human-authored texts and parallel AI-generated texts from multiple LLMs (e.g., Gemini, GPT-4, Llama, Mistral) [55]. The dataset should be split into training, validation, and test sets.
- Multi-Faceted Feature Extraction: Extract a rich set of features from the input text:
- Document Embeddings from AI Detector: Utilize a pre-trained RoBERTa-base model, specifically fine-tuned for AI detection, to generate document-level representations [55].
- Stylometric Features: Compute the same set of 11+ stylometric features used in Protocol 1 [55].
- General Semantic Embeddings: Generate document embeddings using a general-purpose model like the E5 (EmbEddings from bidirEctional Encoder rEpresentations) model [55].
- Model Architecture and Training:
- Concatenate the feature vectors from all three sources.
- Feed the combined vector into a fully connected layer for classification.
- For Task A (Binary Detection), the output layer has two neurons (Human vs. AI).
- For Task B (Model Attribution), the output layer has
N+1neurons, whereNis the number of LLMs, plus one for "Human."
- Evaluation: Evaluate the model on a separate test set. For detection, focus on overall F1 score and, critically, the false positive rate (the rate at which human text is misclassified as AI), which must be minimized in high-stakes environments like academia [56].
The Scientist's Toolkit: Research Reagents & Solutions
The following table details key resources required for conducting experiments in AI-generated text detection and authorship verification.
Table 2: Essential Research Reagents and Tools for Authorship Analysis
| Item | Type | Function & Application |
|---|---|---|
| Million Authors Corpus (MAC) | Dataset | Enables cross-lingual and cross-domain evaluation of authorship verification models, preventing over-optimistic performance on single-domain data [1]. |
| M4GT-Bench | Dataset | A large-scale, multi-lingual benchmark supporting the evaluation of AI-text detection, model attribution, and human-LLM co-authorship tasks [25]. |
| Pre-trained Language Models (RoBERTa, DeBERTa) | Software/Model | Provides foundational semantic understanding and contextual embeddings; can be used as a base for feature extraction or fine-tuning [29] [55]. |
| Stylometric Feature Set | Software/Feature Set | A predefined set of linguistic features (e.g., burstiness, TTR, sentence length) that captures an author's or LLM's unique writing style [29] [55]. |
| AI Detection APIs (GPTZero, CopyLeaks, Originality.AI) | Tool/Service | Commercial tools that can be used as benchmarks or for independent validation of research findings in AI-text detection [25]. |
| PAN Grammars and Datasets | Dataset & Framework | Provides standardized evaluation frameworks and datasets for traditional authorship verification, helping to isolate biases from topic and author style [4]. |
Performance Metrics and Tool Evaluation
Evaluating the performance of detection and verification systems requires careful consideration of metrics, especially in real-world applications.
Table 3: Performance of Selected AI Detection Tools in Recent Studies [56]
| Detection Tool | Correct AI ID (Kar et al., 2024) | Correct AI ID (Lui et al., 2024) | Overall Accuracy (Perkins et al., 2024) |
|---|---|---|---|
| CopyLeaks | 100% | - | 64.8% |
| GPTZero | 97% | 70% | 26.3% |
| Originality.ai | 100% | - | - |
| Turnitin | 94% | - | 61% |
| ZeroGPT | 95.03% | 96% | 46.1% |
Important Note on Metrics: A high rate of correct AI identification is not sufficient to judge a tool's utility. The overall accuracy must be interpreted alongside the false positive rate. In educational contexts, a low false positive rate (e.g., 1-2% for Turnitin) is paramount due to the severe consequences of falsely accusing a student of misconduct [56]. Tools should be selected based on their demonstrated performance in discriminating between human and AI text with minimal false positives, rather than on their ability to flag AI text alone.
Optimizing Model Performance with Metadata and Discourse Type Information
In the specialized field of cross-domain authorship verification, the core challenge is to correctly determine whether two texts were written by the same author when they belong to different genres or discourse types (DTs) [57]. The performance of verification models in these realistic and challenging scenarios is highly dependent on the effective utilization of metadata and discourse type information [57] [13]. This document outlines application notes and experimental protocols, framed within a broader thesis on robust authorship analysis, to guide researchers in systematically leveraging this contextual information to enhance model accuracy, fairness, and interpretability.
Foundational Concepts and Metadata Typology
A structured approach to metadata management is the foundation for effective model training. The table below defines the key types of metadata relevant to authorship verification and cross-domain research.
Table 1: Essential Metadata Types for Authorship Verification Models
| Metadata Category | Description | Role in Model Performance |
|---|---|---|
| Technical Metadata | Schema, data types, and lineage from data pipelines [58]. | Ensures data integrity, supports reproducibility, and prevents manual errors during data preprocessing. |
| Business/Governance Metadata | Ownership, sensitivity classification, access levels, and retention rules [58]. | Enforces access policies automatically, simplifies audit preparation, and ensures compliance with data usage agreements. |
| Operational Metadata | Refresh frequency, usage patterns, and system dependencies [58]. | Helps data stewards detect bottlenecks or stale assets, improving data reliability and cost efficiency during training cycles. |
| Collaborative Metadata | Human-input tags, comments, quality ratings, and usage notes [58]. | Connects expert linguistic knowledge to data assets, encouraging user collaboration and shared accountability for data quality. |
| Discourse Type (DT) Labels | Labels identifying the genre of a text (e.g., essay, email, interview transcript) [57]. | Provides critical context for cross-domain generalization, allowing models to account for genre-specific stylistic variations. |
Experimental Protocol: Cross-Discourse Type Authorship Verification
This protocol is based on the PAN 2023 Authorship Verification task, which focused on verifying authorship across written and spoken discourse types [57].
Reagent Solutions and Research Materials
Table 2: Key Research Reagents and Materials
| Item | Function/Explanation |
|---|---|
| Aston 100 Idiolects Corpus | A proprietary dataset comprising texts (essays, emails, interviews, speech transcriptions) from ~100 native English speakers (18-22 years old) [57]. |
| Discourse Type Annotations | Metadata labels (essay, email, interview, speech) for each text in a pair. Crucial for training models to be robust to genre shifts [57]. |
| Text Pre-processing Tags | XML-style tags such as <new> (message boundaries) and <nl> (new lines). Preserves structural information while anonymizing content [57]. |
| Normalization Corpus (C) | An unlabeled collection of documents used to zero-center relative entropies, mitigating author-specific classifier bias. Domain-match with test documents is critical in cross-domain settings [13]. |
| Pre-trained Language Models (e.g., BERT, ELMo) | Provides deep, contextualized token representations. Replaces or supplements traditional feature engineering (e.g., character n-grams) [13]. |
Workflow and Data Preprocessing
The following diagram illustrates the end-to-end experimental workflow for a cross-domain authorship verification system.
Detailed Methodology
Step 1: Data Acquisition and Annotation
- Request access to the Aston 100 Idiolects Corpus via the FoLD repository, specifying use for "PAN 2023 Authorship Verification Task" [57].
- The dataset is structured in newline-delimited JSON (
pairs.jsonlandtruth.jsonl). Each pair is assigned a unique ID and has associated DT labels (e.g.,["essay", "email"]) [57]. - Critical Consideration: The author sets between training (calibration) and testing datasets are non-overlapping, ensuring a valid evaluation [57].
Step 2: Text Pre-processing and Metadata Integration
- Concatenated texts (e.g., for emails and interviews) use the
<new>tag to denote original message boundaries. New lines are denoted with<nl>[57]. - Author-specific and topic-specific named entities are replaced with tags to minimize content-based bias [57].
- Protocol Note: In spoken DTs, additional tags indicate non-verbal vocalizations (e.g., cough, laugh), which can be treated as stylistic markers [57].
Step 3: Feature Engineering with Discourse Type Awareness Researchers can choose from or combine two primary feature classes:
- Traditional Stylometric Features: TFIDF-weighted character n-grams (e.g., tetragrams) have proven robust across topics and DTs. Cosine similarity between these representations serves as a strong baseline [57] [13].
- Neural Representations: Utilize pre-trained language models (BERT, ELMo, GPT-2) to generate contextualized embeddings. The model uses a Multi-Headed Classifier (MHC) architecture, where a shared language model feeds into author-specific output layers [13].
Step 4: Model Training with a Multi-Headed Classifier (MHC) Architecture
- The MHC comprises a shared language model (LM) and a set of |A| classifiers, one per candidate author [13].
- During training, the LM's representation of a text is propagated only to the classifier of the known author, and the cross-entropy error is back-propagated to train that specific head [13].
Step 5: Score Normalization for Cross-Domain Comparability
- A pivotal step for cross-domain settings is score normalization using an unlabeled corpus C [13].
- Calculate a normalization vector n using the formula: n = [ - (1/|C|) Σ_{d in C} log P(d | a) ] for each author a [13].
- The most likely author for a test document is then determined by: argmina [ - log P(d | a) - na ] [13].
- Key Insight: The normalization corpus C must be representative of the target domain (DT) of the test document d to effectively mitigate domain-induced bias [13].
Step 6: Evaluation and Model Validation
- Systems should be evaluated using a suite of complementary metrics to provide a holistic performance assessment [57]. The required metrics for the PAN task are listed in the table below.
Table 3: Quantitative Evaluation Metrics for Authorship Verification
| Metric | Description | Purpose |
|---|---|---|
| AUC | Area Under the ROC Curve [57]. | Measures the model's ability to rank same-author pairs higher than different-author pairs. |
| F1-Score | Harmonic mean of precision and recall [57]. | Assesses binary classification accuracy. |
| c@1 | A variant of F1 that rewards leaving difficult problems unanswered (score = 0.5) [57]. | Evaluates accuracy and the ability to abstain from uncertain decisions. |
| F_0.5u | Puts more emphasis on correctly deciding same-author cases [57]. | Useful for security-sensitive applications where missing a true match is costly. |
| Brier Score | Measures the accuracy of probabilistic predictions [57]. | Evaluates the goodness of the calibration of the verification scores. |
System Architecture for Metadata-Informed Verification
The diagram below details the neural architecture that effectively integrates pre-trained language models with metadata-aware decision-making.
Evaluating Model Performance: Benchmarks, Metrics, and Comparative Analysis
In cross-domain authorship verification and many other binary classification tasks in research, the selection of appropriate evaluation metrics is paramount. These metrics provide a standardized framework for assessing model performance, enabling meaningful comparisons across different studies and methodologies. The core challenge lies in selecting metrics that accurately reflect the true capabilities of a model, particularly when dealing with specific data characteristics like class imbalance or the need for probabilistic assessment. This document outlines the fundamental principles, practical applications, and experimental protocols for four critical metrics—AUC, F1, c@1, and Brier Score—within the context of authorship verification and broader scientific research.
The Receiver Operating Characteristic (ROC) curve is a graphical plot that illustrates the diagnostic ability of a binary classifier system as its discrimination threshold is varied [59]. It is created by plotting the True Positive Rate (TPR) against the False Positive Rate (FPR) at various threshold settings. The Area Under the ROC Curve (AUC) provides a single-figure aggregate measure of performance across all possible classification thresholds [60]. The F1 Score is the harmonic mean of precision and recall, offering a balanced measure of a model's accuracy, particularly useful when dealing with imbalanced datasets [60]. The Brier Score measures the accuracy of probabilistic predictions, quantifying the mean squared difference between the predicted probability and the actual outcome [61]. Notably, the c@1 metric, while a required part of this document's title, is not covered in the provided search results and will not be discussed in the subsequent sections, which will focus on the three well-documented metrics.
Metric Fundamentals and Comparative Analysis
Conceptual Foundations of Core Metrics
ROC-AUC evaluates a model's ability to separate positive and negative classes across all possible thresholds. A perfect model achieves an AUC of 1.0, indicating perfect separation, while a random classifier has an AUC of 0.5 [59] [60]. The ROC curve plots the True Positive Rate (Sensitivity) against the False Positive Rate (1 - Specificity), providing a visualization of this trade-off. The AUC is particularly valuable because it is threshold-invariant, offering an overall assessment of model performance independent of any specific classification cutoff [59]. This characteristic makes it indispensable for model selection in the early stages of research before operational thresholds are established.
The F1 Score balances the competing objectives of precision and recall through their harmonic mean, making it especially valuable in scenarios where false positives and false negatives carry significant costs [60]. Unlike accuracy, which can be misleading with imbalanced class distributions, the F1 score remains informative because it focuses specifically on the model's performance on the positive class. Its calculation (F1 = 2 × (Precision × Recall) / (Precision + Recall)) ensures that both type I and type II errors are appropriately weighted in the final assessment [60].
The Brier Score operates in probability space, evaluating the calibration of predicted probabilities rather than just categorical outcomes [61]. It computes the mean squared error between predicted probabilities and actual binary outcomes, with lower scores (closer to 0) indicating better-calibrated predictions. A model with a Brier score of 0 makes perfect probability assignments, while a score of 1 represents the worst possible calibration [61]. This metric is crucial for applications where the magnitude of confidence in predictions directly influences decision-making processes.
Comparative Metric Analysis
Table 1: Comparative Characteristics of Evaluation Metrics
| Metric | Calculation Formula | Value Range | Optimal Value | Primary Use Case |
|---|---|---|---|---|
| AUC | Area under ROC curve (TPR vs. FPR) | 0.0 to 1.0 | 1.0 | Overall model discrimination across all thresholds [59] [60] |
| F1 Score | 2 × (Precision × Recall) / (Precision + Recall) | 0.0 to 1.0 | 1.0 | Balanced measure of precision and recall on positive class [60] |
| Brier Score | (1/N) × Σ(Predictedprobability - Actualoutcome)² | 0.0 to 1.0 | 0.0 | Accuracy of probabilistic predictions (calibration) [61] |
Table 2: Metric Strengths and Limitations in Research Contexts
| Metric | Key Strengths | Key Limitations | Impact of Class Imbalance |
|---|---|---|---|
| AUC | Threshold-invariant; Measures separability; Intuitive graphical interpretation [59] [60] | Does not reflect calibration; Can be optimistic with severe imbalance [62] | Generally robust, but can be inflated when imbalance changes score distributions [62] |
| F1 Score | Focuses on positive class; Balances precision and recall; Useful with unequal error costs [60] | Depends on threshold choice; Ignores true negatives; Harmonic mean can be sensitive to low values [60] | Designed for imbalance, but does not consider true negative performance [60] |
| Brier Score | Assesses probability calibration; Decomposes into refinement and uncertainty; Strictly proper scoring rule [61] [63] | Can mask poor discrimination if well-calibrated; Less intuitive than categorical metrics [63] | Remains effective as it evaluates probabilistic predictions directly [61] |
Experimental Protocols for Metric Implementation
Workflow for Comprehensive Model Evaluation
The following diagram illustrates the standardized experimental workflow for evaluating binary classification models using the three core metrics:
Protocol 1: AUC-ROC Calculation and Interpretation
Purpose: To evaluate model discrimination capability across all classification thresholds.
Materials and Reagents:
- True binary labels: Ground truth values (0/1) for all test instances
- Predicted probabilities: Continuous probability scores from classification model
- Computing environment: Python with scikit-learn, R with pROC package, or equivalent
Procedure:
- Generate Model Outputs: Obtain predicted probabilities for the positive class (P(y=1)) for all instances in the test set.
- Vary Classification Threshold: Systematically iterate threshold values from 0 to 1 in small increments (e.g., 0.01).
- Calculate TPR and FPR: At each threshold:
- Plot ROC Curve: Create a 2D plot with FPR on x-axis and TPR on y-axis.
- Calculate AUC: Compute area under the ROC curve using trapezoidal rule or statistical packages [60].
Interpretation Guidelines:
- AUC = 0.90-1.00: Excellent discrimination
- AUC = 0.80-0.90: Good discrimination
- AUC = 0.70-0.80: Fair discrimination
- AUC = 0.60-0.70: Poor discrimination
- AUC = 0.50-0.60: Failure of discrimination (random)
Technical Notes: AUC is particularly valuable for early model selection as it is threshold-invariant. Recent research confirms its robustness even with imbalanced datasets, contrary to some prevailing opinions [62].
Protocol 2: F1 Score Calculation and Optimization
Purpose: To balance precision and recall for comprehensive assessment of positive class performance.
Materials and Reagents:
- True binary labels: Ground truth values for test instances
- Predicted classes: Binary predictions (0/1) at a specific threshold
- Threshold optimization tool: Grid search or precision-recall curve analysis
Procedure:
- Set Classification Threshold: Establish optimal cutoff (default 0.5 unless optimized).
- Generate Predictions: Convert probability outputs to binary predictions using threshold.
- Construct Confusion Matrix: Tabulate TP, FP, TN, FN.
- Calculate Precision and Recall:
- Precision = TP / (TP + FP)
- Recall = TP / (TP + FN) [60]
- Compute F1 Score: Apply formula F1 = 2 × (Precision × Recall) / (Precision + Recall)
Threshold Optimization:
- Perform grid search across threshold values from 0 to 1
- Identify threshold that maximizes F1 score
- Alternatively, use domain-specific cost ratios to weight precision vs. recall
Interpretation Guidelines:
- F1 = 0.90-1.00: Excellent balance of precision and recall
- F1 = 0.70-0.90: Good performance with minor trade-offs
- F1 = 0.50-0.70: Moderate performance with significant errors
- F1 < 0.50: Poor performance requiring model improvement
Technical Notes: The F1 score is particularly valuable in authorship verification where both false attributions (low precision) and missed verifications (low recall) carry significant consequences.
Protocol 3: Brier Score Calculation and Decomposition
Purpose: To evaluate the calibration and accuracy of probabilistic predictions.
Materials and Reagents:
- True binary labels: Ground truth outcomes (0/1)
- Predicted probabilities: Continuous probability estimates (0-1)
- Binning framework: For calibration analysis (optional)
Procedure:
- Obtain Probability Predictions: Collect model outputs representing P(y=1) for each instance.
- Record Actual Outcomes: Note true binary outcomes (0 or 1) for each instance.
- Calculate Squared Errors: For each instance, compute (predictedprobability - actualoutcome)²
- Compute Mean Squared Error: Brier Score = (1/N) × Σ(predictedprobability - actualoutcome)² [61]
Calibration Assessment:
- Bin Predictions: Group instances by predicted probability (e.g., 0-0.1, 0.1-0.2, ..., 0.9-1.0)
- Calculate Observed Frequency: For each bin, compute actual proportion of positive cases
- Plot Calibration Curve: Create plot with predicted probability vs. observed frequency
- Assess Deviation: Perfect calibration follows the diagonal line
Interpretation Guidelines:
- Brier Score = 0.0: Perfect prediction (always predicts correct outcome with 100% confidence)
- Brier Score = 0.25: No skill (predicts always 0.5 or random guessing for balanced data)
- Brier Score = 1.0: Worst possible prediction (always predicts wrong outcome with 100% confidence)
- Lower scores always indicate better performance
Technical Notes: The Brier Score can be decomposed into calibration and refinement components, providing insight into whether poor performance stems from incorrect probability estimates or inherent uncertainty [63]. Recent advancements propose weighted Brier Scores to incorporate clinical utility and decision consequences in biomedical contexts [63].
Implementation Framework
Research Reagent Solutions
Table 3: Essential Computational Tools for Metric Implementation
| Tool/Resource | Function/Purpose | Implementation Example |
|---|---|---|
| scikit-learn (Python) | Comprehensive machine learning library with metric implementations | from sklearn.metrics import roc_auc_score, f1_score, brier_score_loss |
| pROC (R Package) | Specialized ROC analysis tools | library(pROC); auc(response, predictor) |
| Matplotlib/Plotly | Visualization of ROC curves, precision-recall curves, and calibration plots | import matplotlib.pyplot as plt; plt.plot(fpr, tpr) |
| Pandas/Numpy | Data manipulation and numerical computations for metric calculations | import pandas as pd; import numpy as np |
| SHAP/LIME | Model interpretation to connect metric performance to feature influences | import shap; explainer = shap.TreeExplainer(model) |
Code Implementation Examples
Comprehensive Metric Calculation in Python:
The standardized application of AUC, F1, and Brier Score provides a comprehensive framework for evaluating binary classification models in authorship verification and broader scientific domains. Each metric offers distinct insights: AUC measures overall discriminative ability, F1 balances precision and recall for categorical predictions, and Brier Score assesses the calibration of probabilistic outputs. Used in concert, these metrics enable researchers to make informed decisions about model selection, optimization, and deployment. The experimental protocols outlined in this document provide reproducible methodologies for their calculation and interpretation, facilitating rigorous comparison across studies and advancing the reliability of computational research methodologies.
PAN Shared Tasks as a Benchmarking Gold Standard
Within the rigorous framework of cross-domain authorship verification research, the reproducibility and comparative assessment of methodological advances present a significant challenge. The PAN series of shared tasks, established since 2007, directly addresses this challenge by providing a standardized, community-driven benchmarking platform for authorship analysis and digital text forensics [19]. These competitions have been instrumental in propelling the state of the art forward by providing rigorous evaluation frameworks and high-quality datasets. By offering a "gold standard" for evaluation, PAN allows researchers to objectively compare their approaches against a common baseline, ensuring that progress in the field is measurable and scientifically sound [64]. The recent revival of the plagiarism detection task in 2025, focused on identifying AI-generated paraphrasing, underscores PAN's critical role in adapting established protocols to address emerging technological challenges like generative AI [22].
Historical Evolution of PAN Shared Tasks
The PAN initiative has continually evolved its shared tasks to reflect the most pressing challenges in digital text forensics. The table below chronicles the development of its core task families, demonstrating a clear trajectory from foundational attribution problems to contemporary issues involving AI-generated text.
Table 1: Historical Development of Core PAN Shared Task Families
| Task Family | Initial Edition | Key Evolutionary Milestones | Recent Focus (2020-2025) |
|---|---|---|---|
| Author Identification | 2007 | Authorship Attribution, Verification, Clustering [64] | Authorship Verification, Generative AI Detection (Voight-Kampff) [64] |
| Author Profiling | 2013 | Age, gender, language variety identification [19] | Profiling fake news, hate speech, and stereotype spreaders on Twitter [64] |
| Plagiarism Detection | 2009 | External, intrinsic, cross-language detection [64] | Generative Plagiarism Detection (2025) [64] |
| Multi-Author Analysis | 2016 | Author Diarization [64] | Style Change Detection (yearly from 2017-2025) [64] |
| Computational Ethics | 2010 | Sexual Predator Identification, Vandalism Detection [64] | Multilingual Text Detoxification, Oppositional Thinking Analysis [64] |
A pivotal moment in PAN's development was the adoption of the TIRA platform, which transitioned the evaluation paradigm from the submission of system outputs to the submission of executable software [19]. This shift has greatly enhanced the reproducibility and verifiability of results, solidifying PAN's role as a true benchmarking gold standard where methodologies can be directly compared and validated in consistent environments.
PAN's Experimental Framework for Authorship Verification
Authorship verification, a core task at PAN, aims to determine whether two documents are written by the same author [65]. This task presents a more realistic and challenging scenario than closed-set attribution, making it particularly relevant for forensic applications. The experimental framework for this task is meticulously designed to ensure robust evaluation.
Task Formulation and Evaluation Metrics
The authorship verification task is defined as a binary classification problem. Given a pair of documents (D1, D2), a system must determine if they share the same authorship [65]. The primary evaluation metric used is the area under the receiver operating characteristic curve (AUC-ROC) or F1-score, which provides a balanced view of system performance across different decision thresholds, crucial for handling class imbalance often present in verification scenarios.
Standardized Corpus Construction Protocol
PAN employs a rigorous protocol for constructing evaluation corpora to ensure fairness and relevance. The following workflow outlines the standardized steps for creating a benchmark dataset for authorship verification, drawing from established PAN methodologies and recent innovations.
Figure 1: Workflow for Authorship Verification Benchmark Creation
The "Pair Generation" stage is critical. For recent tasks, this involves sophisticated procedures such as using models like SPECTER to create document embeddings and identify semantically similar documents, ensuring that negative pairs (different authors) are topically similar to increase difficulty and prevent topic-based cheating [22]. The introduction of the Million Authors Corpus (MAC) represents a significant advance, providing 60.08 million textual chunks from 1.29 million Wikipedia authors across dozens of languages, enabling unprecedented cross-lingual and cross-domain evaluation [1].
Protocol: Cross-Domain Authorship Verification Using Pre-Trained Language Models
This protocol details a state-of-the-art methodology for cross-domain authorship verification, adapting the winning approaches from recent PAN shared tasks and relevant literature [13].
Research Reagent Solutions
Table 2: Essential Computational Reagents for Cross-Domain Authorship Verification
| Reagent / Tool | Type | Function in Protocol | Exemplars / Notes |
|---|---|---|---|
| Pre-trained Language Models | Foundation Model | Provides deep, contextualized token representations that capture stylistic patterns. | BERT, ELMo, GPT-2, ULMFiT [13] |
| Multi-Headed Classifier (MHC) | Neural Network Architecture | Enables multi-author learning within a single model; each "head" specializes for one author. | Adaptation of Bagnall's model [13] |
| Normalization Corpus | Unlabeled Text Data | Calibrates classifier outputs to mitigate domain-specific bias, crucial for cross-domain performance. | Should match the target domain of test documents [13] |
| Stylometric Feature Sets | Feature Extractor | Provides shallow features as a baseline or for ensemble methods, capturing surface-level style. | Character N-grams, Function Words, POS tags [13] |
| Evaluation Framework | Software Platform | Standardized evaluation and comparison of results; ensures reproducibility. | TIRA Platform [19] |
Step-by-Step Experimental Procedure
Step 1: Data Preparation and Preprocessing
- Obtain the benchmark dataset from the PAN website (e.g., for the 2023 Authorship Verification task) [64].
- Perform text normalization: convert to lowercase, replace punctuation and digits with special tokens, and tokenize text [13].
- For cross-domain evaluation, ensure the training (known authorship) and test (unknown authorship) sets differ in topic or genre.
Step 2: Model Architecture Setup
- Option A (Neural Language Model with MHC): Implement a character-level Recurrent Neural Network (RNN) language model with a separate output head for each candidate author [13].
- Option B (Pre-trained Model with MHC): Leverage a pre-trained transformer model (e.g., BERT) as the feature extractor, followed by an MHC layer. This exploits transfer learning from vast corpora [13].
Step 3: Model Training
- Train the LM on all available texts from candidate authors to learn a general language model.
- Train the MHC by propagating LM representations only to the classifier head corresponding to the known author of the training text, using cross-entropy loss.
Step 4: Score Normalization for Cross-Domain Robustness
- Calculate a normalization vector
nusing an unlabeled corpusCthat matches the domain of the test documents [13]. - Compute
n[a]for each authoraas the average cross-entropy of the author's classifier on corpusC, centered by subtracting the mean across all authors [13]. This corrects for individual classifier bias.
Step 5: Inference and Authorship Verification
- For a test document
d, compute the cross-entropy score for each authora's classifier:score(d, a). - Apply the normalization:
normalized_score(d, a) = score(d, a) - n[a]. - The verification decision for a pair
(D1, D2)is based on a threshold applied to the difference in their normalized scores for the same author, or the similarity of their stylistic representations.
The following diagram illustrates the complete data flow and architecture of this protocol, highlighting the critical role of the normalization corpus in ensuring cross-domain robustness.
Figure 2: Protocol Architecture for Cross-Domain Authorship Verification
Case Study: The PAN 2025 Generative Plagiarism Detection Task
The 2025 PAN task on generative plagiarism detection serves as a prime example of how the shared task framework adapts to novel challenges, providing a benchmark for detecting AI-generated paraphrasing in scientific articles [22].
Dataset Creation Protocol
The 2025 dataset was constructed through a sophisticated, automated pipeline:
- Source Corpus: 100,000 documents were sampled from the arXiv (ar5iv) HTML5 corpus, ensuring even distribution across scientific domains [22].
- Pair Generation: For each source document
S, the most semantically similar documentPwas identified using SPECTER document embeddings and cosine similarity, creating 100,000(S, P)pairs [22]. - Plagiarism Injection: A random number of paragraphs in
Pwere selected for replacement. For each selected paragraphp, the most semantically similar paragraphsfromSwas found using a weighted similarity score (50% SPECTER embeddings, 40% TF-IDF, 10% section title similarity) [22]. - LLM Paraphrasing: Each source paragraph
swas paraphrased intos'using one of three LLMs (LLaMA-3 70B, DeepSeek-R1, or Mistral 7B) with one of three prompt types (simple, default, complex) to vary paraphrasing sophistication [22]. - Categorization: The dataset includes 5% original pairs, 20% altered (non-plagiarized but LLM-paraphrased) pairs, and 75% plagiarism pairs, with varying severity levels (low, medium, high) based on the proportion of replaced paragraphs [22].
Benchmark Performance and Insights
The 2025 task revealed that naive semantic similarity approaches based on modern embedding vectors could achieve promising results (up to 0.8 recall and 0.5 precision) [22]. However, a key finding was that these high-performing approaches on the new dataset significantly underperformed on the classic PAN 2015 dataset, indicating a lack of generalizability and highlighting the continued importance of robust, multi-dataset benchmarking [22].
Table 3: Quantitative Summary of the PAN 2025 Generative Plagiarism Detection Dataset
| Dataset Characteristic | Metric | Value / Composition |
|---|---|---|
| Base Corpus | Source | 100,000 arXiv (ar5iv) documents [22] |
| Document Pairs | Total Pairs | 100,000 (S, P) pairs [22] |
| Pair Categories | No-plagiarism (Original) | 5% of total pairs [22] |
| No-plagiarism (Altered) | 20% of total pairs [22] | |
| Plagiarism | 75% of total pairs [22] | |
| Plagiarism Severity | Low (20-40% paras) | 30% of plagiarism pairs [22] |
| Medium (40-60% paras) | 40% of plagiarism pairs [22] | |
| High (70-100% paras) | 30% of plagiarism pairs [22] | |
| Paraphrasing LLMs | Models Used | LLaMA-3 70B, DeepSeek-R1, Mistral 7B [22] |
| Paraphrasing Prompts | Simple Prompts | 60% of paragraph pairs [22] |
| Default Prompts | 30% of paragraph pairs [22] | |
| Complex Prompts | 10% of paragraph pairs [22] |
The PAN shared tasks have established an indispensable and evolving "gold standard" for benchmarking in authorship analysis and related fields. By providing standardized datasets, rigorous evaluation protocols, and a platform for reproducible software submission via TIRA, PAN enables the objective comparison of diverse methodologies [19]. Its adaptable framework, demonstrated by the recent incorporation of challenges posed by generative AI, ensures its continued relevance [22]. For researchers engaged in cross-domain authorship verification, adherence to the experimental protocols and benchmarks established by PAN is not merely beneficial—it is a prerequisite for producing valid, comparable, and scientifically robust results that genuinely advance the field.
Comparative Analysis of Model Performance Across Domains
The ability to accurately evaluate model performance across different domains is a critical challenge in computational research. This challenge is particularly acute in fields such as authorship verification and drug discovery, where models must generalize beyond their training data to be practically useful. In authorship verification, models often overfit to topic-specific features rather than learning genuine stylistic patterns of authors [1]. Similarly, in drug discovery, conventional evaluation metrics can be misleading when applied to imbalanced datasets with rare but critical events, such as active compounds among predominantly inactive ones [66].
This application note establishes protocols for cross-domain model evaluation, drawing on methodologies from computational linguistics and pharmaceutical research. We provide a structured framework for assessing model robustness, with specific emphasis on authorship verification and pharmacokinetic applications. The protocols detailed herein enable researchers to identify domain-specific biases, select appropriate evaluation metrics, and implement validation strategies that ensure reliable performance in real-world scenarios.
Quantitative Performance Comparison Across Domains
Authorship Verification Performance
Table 1: Performance metrics for authorship verification models across domains and languages
| Model Type | Domain/Language | Evaluation Metric | Performance | Key Finding |
|---|---|---|---|---|
| Monolingual Baseline | 22 Non-English Languages | Average Recall@8 | Baseline | Reference for comparison |
| Multilingual AR Model | 21 Non-English Languages | Average Recall@8 | +4.85% improvement | Multilingual training enhances performance |
| Multilingual AR Model | Kazakh & Georgian | Recall@8 | +15.91% improvement | Greatest benefits in low-resource languages |
| Ensemble Deep Learning | Dataset A (4 authors) | Accuracy | 80.29% | +3.09% over state-of-the-art |
| Ensemble Deep Learning | Dataset B (30 authors) | Accuracy | 78.44% | +4.45% over state-of-the-art |
Drug Discovery and Pharmacokinetic Model Performance
Table 2: Performance metrics for models in pharmaceutical applications
| Model Type | Application Domain | Evaluation Metric | Performance | Key Finding |
|---|---|---|---|---|
| Support Vector Regressor | Pharmacokinetic DDI Prediction | Predictions within 2-fold of observed | 78% | Reasonable accuracy for early risk assessment |
| Traditional Metrics | Drug Discovery (Imbalanced Data) | Accuracy | Misleading | Fails to identify active compounds |
| Domain-Specific Metrics | Drug Discovery (Imbalanced Data) | Rare Event Sensitivity | Effective | Captures critical minority classes |
| Custom ML Pipeline | Omics-Based Drug Discovery | Detection Speed | 4x increase | Significant efficiency improvement |
Domain-Specific Evaluation Challenges
Authorship Verification Domain
In authorship verification, a primary challenge is topic dependence, where models mistakenly learn topic-specific features rather than genuine authorial style [1]. This problem is exacerbated in monolingual settings and when models are applied to new domains beyond their training distribution. The Million Authors Corpus (MAC) addresses this by providing cross-domain and cross-lingual evaluation capabilities, enabling researchers to distinguish between models that capture genuine stylistic features versus those that merely memorize topic-related patterns [1].
Multilingual training has emerged as a powerful strategy to improve model robustness. Techniques such as probabilistic content masking encourage models to focus on stylistically indicative words rather than content-specific vocabulary, while language-aware batching reduces cross-lingual interference during training [67]. These approaches have demonstrated significant improvements in cross-lingual generalization, with multilingual models outperforming monolingual baselines in 21 out of 22 non-English languages [67].
Drug Discovery and Pharmacokinetics
In drug discovery, conventional evaluation metrics like accuracy and F1-score can be profoundly misleading due to extreme class imbalances where inactive compounds dramatically outnumber active ones [66]. A model achieving high accuracy by consistently predicting the majority class (inactive compounds) would be practically useless for identifying promising drug candidates.
Domain-specific evaluation metrics address this limitation through several specialized approaches:
- Precision-at-K: Prioritizes the highest-ranking predictions, essential for identifying the most promising drug candidates in screening pipelines [66]
- Rare Event Sensitivity: Measures a model's ability to detect low-frequency events, such as adverse drug reactions or rare genetic variants [66]
- Pathway Impact Metrics: Evaluates how well models identify biologically relevant pathways, ensuring predictions are statistically valid and biologically interpretable [66]
In pharmacokinetics, model evaluation must distinguish between different prediction types: population predictions (without therapeutic drug monitoring), fitted predictions (using historical TDM data), and forecasted predictions (projecting future drug levels) [68]. Forecasted predictions most closely mimic real-world clinical applications and therefore provide the most meaningful performance assessment for models intended for precision dosing [68].
Experimental Protocols for Cross-Domain Evaluation
Protocol 1: Cross-Lingual Authorship Verification
Purpose: To evaluate authorship verification models across multiple languages and domains, ensuring they capture genuine stylistic features rather than topic-specific patterns.
Materials:
- Million Authors Corpus (MAC) or equivalent dataset [1]
- Computational resources for training deep learning models
- Evaluation framework with standardized metrics (Recall@K, accuracy)
Procedure:
- Data Preparation:
- Extract long, contiguous textual chunks from Wikipedia edits or similar sources
- Link texts to their respective authors with verified attribution
- Partition data into training, validation, and test sets with author-level separation
Multilingual Training:
- Implement probabilistic content masking to identify and mask frequently occurring tokens as function words
- Apply language-aware batching to group same-language examples, reducing cross-lingual interference
- Train model using supervised contrastive learning framework with temperature parameter τ
Evaluation:
- Assess performance on held-out test sets across multiple languages
- Conduct cross-domain evaluation by testing on texts from different domains than training data
- Perform ablation studies to determine contribution of individual components
Validation:
- Compare against monolingual baselines for each language
- Evaluate cross-lingual transfer to languages not seen during training
- Assess robustness to topic variation by testing on domains excluded from training
Protocol 2: Drug Discovery and Pharmacokinetic Model Evaluation
Purpose: To evaluate predictive models in drug discovery and pharmacokinetics using domain-appropriate metrics and validation strategies.
Materials:
- Compound activity data (e.g., ChEMBL, BindingDB) [69]
- Pharmacokinetic interaction data (e.g., Washington Drug Interaction Database) [70]
- Specialized evaluation metrics (Precision-at-K, Rare Event Sensitivity)
Procedure:
- Data Curation:
- Distinguish assays into Virtual Screening (VS) and Lead Optimization (LO) types based on compound similarity patterns
- For VS assays, ensure diverse compound structures with low pairwise similarities
- For LO assays, include congeneric compounds with high structural similarities
Model Training:
Domain-Specific Evaluation:
- For drug discovery: Calculate Precision-at-K, Rare Event Sensitivity, and Pathway Impact Metrics
- For pharmacokinetics: Evaluate forecasting performance using iterative approaches that predict subsequent TDM samples based on previous ones [68]
- Report bias (Mean Percentage Error) and accuracy (percentage within acceptable range)
Validation:
- Compare domain-specific metrics against traditional metrics to highlight differences
- Evaluate on biased protein exposure scenarios to test robustness
- Assess performance in few-shot and zero-shot scenarios for real-world applicability
Visualization of Cross-Domain Evaluation Frameworks
Cross-Domain Model Evaluation Framework
Cross-Domain Evaluation Workflow - This diagram illustrates the comprehensive framework for evaluating model performance across different domains, highlighting the specialized metrics and protocols required for each application area.
Multilingual Authorship Verification Workflow
Multilingual Authorship Verification - This workflow details the process for training and evaluating multilingual authorship verification models, emphasizing techniques that enhance cross-lingual generalization.
Research Reagent Solutions
Table 3: Essential research reagents and resources for cross-domain model evaluation
| Resource Category | Specific Resource | Function | Application Domain |
|---|---|---|---|
| Datasets | Million Authors Corpus (MAC) | Cross-lingual authorship verification with 60.08M textual chunks | Authorship Verification |
| Datasets | ChEMBL Database | Compound activity data for virtual screening and lead optimization | Drug Discovery |
| Datasets | Washington Drug Interaction Database | Clinical DDI studies for pharmacokinetic model training | Pharmacokinetics |
| Evaluation Metrics | Precision-at-K | Prioritizes top-ranking predictions in imbalanced datasets | Drug Discovery |
| Evaluation Metrics | Rare Event Sensitivity | Measures detection capability for critical minority classes | Drug Discovery |
| Evaluation Metrics | Recall@K | Evaluates author identification accuracy in top K results | Authorship Verification |
| Computational Tools | Probabilistic Content Masking | Reduces topic dependence in authorship models | Authorship Verification |
| Computational Tools | Language-Aware Batching | Improves contrastive learning in multilingual settings | Authorship Verification |
| Computational Tools | Forecasting Accuracy Assessment | Evaluates predictive performance for future drug levels | Pharmacokinetics |
This application note establishes comprehensive protocols for comparative analysis of model performance across diverse domains, with specific application to authorship verification and pharmaceutical research. The structured evaluation framework emphasizes domain-specific challenges and appropriate metric selection to ensure meaningful performance assessment.
Key findings demonstrate that multilingual training strategies significantly improve robustness in authorship verification, while domain-specific metrics are essential for reliable evaluation in drug discovery applications. The provided experimental protocols enable systematic assessment of model generalization, addressing critical gaps in cross-domain evaluation methodologies.
Researchers should prioritize domain-aware evaluation strategies that align with real-world application scenarios, particularly when deploying models in high-stakes environments such as medical decision support or security-critical authorship attribution.
The Role of Retrieval-Augmented Generation (RAG) in Factual Verification
Retrieval-Augmented Generation (RAG) provides a foundational architecture for enhancing the reliability of automated systems used in cross-domain authorship verification research. By decoupling the knowledge source from the language model's parametric memory, RAG grounds text generation in retrieved, verifiable evidence [71] [72]. This capability is particularly valuable for factual verification tasks where maintaining an audit trail of source documents is essential for scholarly validation. The protocols outlined in this document establish standardized methodologies for implementing RAG systems that can assist researchers in verifying authorial claims against source corpora while mitigating model hallucination—a critical failure mode in forensic linguistics and authorship attribution studies [73] [72].
Technical Protocols for RAG-Enhanced Factual Verification
Core RAG Architecture and Data Flow
The standard RAG pipeline implements a sequential process that transforms raw documents into verified responses. The following protocol details each stage for implementation in authorship verification contexts:
Table 1: RAG Pipeline Component Specifications for Factual Verification
| Pipeline Stage | Core Function | Implementation Requirements | Output for Verification |
|---|---|---|---|
| Document Ingestion | Acquires raw text from source corpora | Access to structured/unstructured data; document parsing tools [74] [75] | Standardized JSON format with metadata [75] |
| Intelligent Chunking | Segments documents into semantically coherent units | Context window management; overlap preservation [75] | Text chunks with parent-child relationships [75] |
| Embedding Generation | Creates vector representations of text | Pre-trained embedding model; sufficient compute resources [73] [74] | Dense vector embeddings (numeric formats) [73] |
| Vector Storage | Indexes embeddings for efficient retrieval | Scalable vector database (e.g., Pinecone, Milvus) [74] [75] | Searchable knowledge base with metadata [74] |
| Query Processing | Encodes verification questions into vector space | Embedding model consistency [73] | Query vector for similarity search [73] |
| Retrieval & Re-ranking | Identifies relevant document sections | Similarity search algorithms; relevance ranking [74] [72] | Top-K relevant chunks with similarity scores [75] |
| Response Generation | Synthesizes evidence into verified response | LLM API access; prompt engineering [74] | Factual response with source citations [74] |
RAG Verification Pipeline
Advanced Protocol: Sufficient Context Classification
Google Research's "sufficient context" framework provides a critical methodological advancement for factual verification tasks [72]. This protocol enables systematic differentiation between contexts that contain definitive answer information versus those that are merely topically relevant but incomplete.
Experimental Protocol:
- Autorater Development: Implement an LLM-based classification system (e.g., using Gemini 1.5 Pro) to evaluate query-context pairs [72]
- Gold Standard Creation: Engage human experts to annotate 100+ question-context examples as sufficient or insufficient, establishing ground truth labels [72]
- Prompt Optimization: Apply chain-of-thought prompting with 1-shot examples to improve classification accuracy [72]
- Validation: Measure autorater performance against gold standard, achieving >93% accuracy threshold [72]
Operational Definitions:
- Sufficient Context: Contains all necessary information to provide a definitive answer to the query [72]
- Insufficient Context: Lacks necessary information, is incomplete, inconclusive, or contains contradictory information [72]
Advanced Protocol: Selective Generation with Controlled Abstention
This protocol mitigates hallucination by combining context sufficiency signals with model confidence metrics to determine when to abstain from answering [72].
Methodology:
- Signal Acquisition:
- Extract binary sufficient context label from autorater
- Obtain model self-rated confidence scores using P(True) or P(Correct) methodologies [72]
Threshold Calibration:
Decision Framework:
- High confidence + sufficient context = Generate answer
- Low confidence + insufficient context = Abstain with "I don't know" [72]
Table 2: Selective Generation Performance Metrics
| Model Condition | Abstention Rate | Factual Accuracy | Hallucination Reduction |
|---|---|---|---|
| Baseline (no context) | 10.2% | 89.8% | Reference |
| Insufficient context (uncontrolled) | 66.1% | 33.9% | -55.9% |
| Selective generation | 25.4% | 92.3% | +10.2% |
Selective Generation Protocol
Evaluation Framework for Verification Systems
RAG Evaluation Metrics and Methodologies
Comprehensive evaluation requires multiple assessment methodologies to measure both retrieval quality and generation accuracy [76].
Table 3: RAG Evaluation Metrics for Factual Verification
| Metric Category | Specific Metrics | Measurement Protocol | Target Threshold |
|---|---|---|---|
| Retrieval Quality | Precision, Recall, F1 Score [76] | Percentage of relevant documents retrieved vs. total relevant | Recall >90% for critical facts |
| Generation Accuracy | Groundedness, Faithfulness [76] | Factual consistency with source documents | >95% factual consistency |
| Output Quality | Answer Relevance, Fluency [76] | Human ratings or LLM-as-judge scoring | >4.0/5.0 relevance score |
| Verification Safety | Hallucination Rate, Abstention Accuracy [72] | Comparison to ground truth answers | <5% hallucination rate |
Experimental Protocol: Retriever Evaluation
- Dataset Construction: Curate query set with known relevant documents from authorship corpus
- Relevance Judging: Engage domain experts to assess retrieved document relevance on 3-point scale
- Metric Calculation: Compute precision@K, recall@K, and nDCG for retrieval performance [76]
- Benchmarking: Compare against hybrid retrieval baselines (dense + sparse methods)
Implementation Protocol: Advanced RAG Patterns
Self-RAG Protocol [73]:
- Adaptive Retrieval: Implement reflection tokens to determine when external information is needed
- Selective Sourcing: Evaluate retrieved documents for relevance using ISREL tokens
- Self-Critique: Generate and rank multiple responses, selecting the most accurate with citations
Corrective RAG (CRAG) Protocol [73]:
- Retrieval Assessment: Implement lightweight retrieval evaluator to assess document quality
- Confidence Scoring: Assign confidence scores to retrieved documents
- Web Search Augmentation: Dynamically incorporate large-scale web searches when confidence is low
Research Reagent Solutions
Table 4: Essential Research Reagents for RAG Verification Systems
| Reagent Category | Specific Solutions | Research Function | Verification Application |
|---|---|---|---|
| Embedding Models | text-embedding-ada-002, Sentence-BERT [73] | Convert text to vector representations | Semantic similarity for authorship patterns |
| Vector Databases | Pinecone, Milvus, FAISS [74] [75] | Store and index embeddings for efficient search | Rapid retrieval of writing style exemplars |
| LLM Generators | GPT-4, Gemini, Claude [73] [72] | Generate responses using augmented context | Produce verification reports with citations |
| Evaluation Frameworks | Ragas, TruLens, DeepEval [76] | Automated testing of retrieval and generation | Benchmark system performance on verification tasks |
| Orchestration Tools | LangChain, LlamaIndex [75] | Coordinate RAG pipeline components | Manage complex multi-step verification workflows |
Integration Protocol for Authorship Verification
For cross-domain authorship verification research, implement the following specialized workflow:
- Corpus Construction: Ingest exemplar documents from verified authors across multiple domains
- Stylometric Indexing: Chunk documents preserving stylistic features (syntax patterns, lexical choices)
- Attribution Queries: Process anonymous texts against authorial indexes
- Evidence Synthesis: Generate verification reports with supporting stylistic evidence and confidence scores
This protocol leverages RAG's capacity to maintain separation between source materials (known author writings) and generative processes, creating an auditable chain of evidence for authorship claims—a fundamental requirement in scholarly verification contexts.
Benchmarking Hallucination Detection and Factual Consistency
Within the paradigm of cross-domain authorship verification, ensuring the factual consistency of automated analyses is a foundational requirement for scientific and legal admissibility. The propensity of Large Language Models (LLMs) to generate plausible but factually incorrect content—a phenomenon termed "hallucination"—poses a significant threat to the integrity of automated authorship attribution systems. This document provides detailed application notes and experimental protocols for benchmarking hallucination detection and factual consistency, enabling researchers to quantify and mitigate these risks in their pipelines. Framed within a broader thesis on robust verification methodologies, these protocols are designed for an audience of researchers, scientists, and drug development professionals who rely on trustworthy automated text analysis, particularly in high-stakes domains such as clinical trial documentation and regulatory submissions where provenance and accuracy are paramount.
Quantitative Benchmarking Data
A critical first step in benchmarking is to establish baseline performance metrics for current models and evaluation techniques. The following tables consolidate quantitative data from recent evaluations to serve as a reference point.
Table 1: Model-Level Hallucination Rates on Summarization Task (HHEM Benchmark) [77] This table compares the factual consistency and hallucination rates of various LLMs when summarizing documents, providing a performance baseline for model selection.
| Model | Hallucination Rate | Factual Consistency Rate | Answer Rate | Average Summary Length (Words) |
|---|---|---|---|---|
| google/gemini-2.5-flash-lite | 3.3 % | 96.7 % | 99.5 % | 95.7 |
| microsoft/Phi-4 | 3.7 % | 96.3 % | 80.7 % | 120.9 |
| meta-llama/Llama-3.3-70B-Instruct-Turbo | 4.1 % | 95.9 % | 99.5 % | 64.6 |
| mistralai/mistral-large-2411 | 4.5 % | 95.5 % | 99.9 % | 85.0 |
| openai/gpt-4.1-2025-04-14 | 5.6 % | 94.4 % | 99.9 % | 91.7 |
| anthropic/claude-sonnet-4-20250514 | 10.3 % | 89.7 % | 98.6 % | 145.8 |
| anthropic/claude-opus-4-5-20251101 | 10.9 % | 89.1 % | 98.7 % | 114.5 |
| google/gemini-3-pro-preview | 13.6 % | 86.4 % | 99.4 % | 101.9 |
Table 2: Performance of Hallucination Detection and Mitigation Techniques [78] [79] This table summarizes the efficacy of various intervention strategies as reported in recent studies, highlighting the most promising approaches.
| Technique / Metric | Reported Efficacy / Performance | Context / Notes |
|---|---|---|
| Prompt-Based Mitigation | Reduced GPT-4o's hallucination rate from 53% to 23% [78] | Simple prompt engineering, as per a 2025 multi-model study in npj Digital Medicine. |
| Real-Time Entity Hallucination Detection | AUC of 0.90 for Llama-3.3-70B [79] | Scalable technique for identifying fabricated entities in long-form generations. |
| Targeted Fine-Tuning | Dropped hallucination rates by 90-96% [78] | As shown in a NAACL 2025 study on synthetic, hard-to-hallucinate examples. |
| LLM-as-Judge Evaluation | Best overall alignment with human judgments [80] | Particularly with GPT-4, in a large-scale empirical evaluation of metrics. |
Experimental Protocols for Evaluation
This section outlines detailed methodologies for conducting rigorous evaluations of factual consistency, adaptable for validating authorship attribution models.
Protocol: Human Evaluation of Factual Consistency via Crowdsourcing
This protocol is based on the findings of Tang et al. (2022) for reliably evaluating the factual consistency of summaries, a methodology directly transferable to assessing authorship verification reports generated by LLMs [81].
- 3.1.1 Objective: To establish a standardized and reliable human evaluation setup for quantifying the factual consistency of model-generated text against a source text.
- 3.1.2 Materials:
- Source Texts: A curated set of documents (e.g., known authorship samples for verification).
- Model Outputs: The corresponding texts generated by the system under evaluation (e.g., authorship analysis reports).
- Crowdsourcing Platform: Access to a platform such as Amazon Mechanical Turk or Prolific.
- Detailed Guidelines: Comprehensive instructions for annotators, including definitions and examples of factual consistency errors.
- 3.1.3 Procedure:
- Annotation Design Selection: Prioritize a ranking-based Best-Worst Scaling (BWS) design over Likert scales. BWS has been shown to offer a more reliable measure of summary quality across different datasets [81].
- Annotator Training: Provide annotators with the guidelines and a qualification test to ensure comprehension.
- Task Presentation: Present annotators with a triplet (Source Text, Output A, Output B). They must select the best (most factually consistent) and worst (least factually consistent) output.
- Data Aggregation: Employ the Value Learning scoring algorithm to convert the BWS annotations into a continuous quality score for each model output [81]. This involves counting the number of times an output was chosen as "best" minus the number of times it was chosen as "worst" across all comparisons.
- Reliability Analysis: Calculate inter-annotator agreement statistics (e.g., Krippendorff's alpha) to ensure the reliability of the collected data.
Protocol: Automatic Evaluation using the TRUE Framework
This protocol utilizes the standardized collection of texts from the TRUE benchmark for an example-level, actionable assessment of factual consistency metrics [82].
- 3.2.1 Objective: To automatically and robustly evaluate the factual consistency of generated text using a standardized meta-evaluation framework.
- 3.2.2 Materials:
- TRUE Benchmark Datasets: Utilize the collection of existing texts from diverse tasks (e.g., summarization, data-to-text) that have been manually annotated for factual consistency [82].
- Evaluation Metrics: Select metrics for testing. The TRUE assessment found that large-scale Natural Language Inference (NLI) and Question Generation-and-Answering (QA) based approaches achieve strong and complementary results [82].
- Computational Resources: Standard computing environment capable of running the selected evaluation metrics.
- 3.2.3 Procedure:
- Benchmarking Set-Up: For a given task, select the relevant sub-datasets from the TRUE benchmark.
- Metric Execution: Run the selected evaluation metrics (e.g., NLI-based, QA-based) on the benchmark datasets.
- Example-Level Meta-Evaluation: Calculate the accuracy of each metric against the human-annotated ground truth for each example in the dataset. This provides a more interpretable and actionable quality measure than system-level correlations [82].
- Results Synthesis: Identify the top-performing metrics for the specific task and domain. Use a combination of NLI and QA-based methods for comprehensive coverage, as they tend to capture different types of factual errors.
Protocol: Real-Time Hallucination Detection with Internal Probes
This protocol details a method for detecting hallucinations without external ground truth, which is valuable for closed-domain authorship analysis where source texts may be proprietary [78].
- 3.3.1 Objective: To detect hallucinations in real-time by analyzing the internal states of a language model, even in the absence of an external knowledge base.
- 3.3.2 Materials:
- Language Model: The model to be monitored (e.g., a 70B parameter model).
- Probing Dataset: A dataset of texts with and without known hallucinations for training the probe.
- Computational Framework: For training lightweight classifiers (e.g., Cross-Layer Attention Probing - CLAP) on model activations [78].
- 3.3.3 Procedure:
- Data Collection & Activation Extraction: Generate text from the target model and simultaneously extract internal activation data from various model layers.
- Classifier Training: Train a lightweight classifier (the "probe") on the collected activations, using a labeled dataset of faithful vs. hallucinated generations.
- Deployment & Inference: Integrate the trained probe into the model's inference pipeline. During text generation, the probe analyzes activations in real-time to flag outputs with a high probability of being hallucinations.
- Validation: Assess the probe's performance using metrics like Area Under the Curve (AUC), with state-of-the-art methods achieving an AUC of 0.90 on large models [79].
Workflow Visualization
The following diagram illustrates the core experimental workflow for benchmarking hallucination detection, integrating the protocols described above.
The Scientist's Toolkit: Research Reagent Solutions
This section catalogs essential tools, datasets, and metrics that function as critical "research reagents" for experiments in hallucination detection and factual consistency evaluation.
Table 3: Essential Reagents for Hallucination Research
| Reagent Category | Specific Tool / Dataset / Metric | Function & Explanation |
|---|---|---|
| Benchmark Datasets | HalluVerse25 [83] | A multilingual benchmark with fine-grained, human-annotated hallucinations (entity, relation, sentence-level) for evaluating model susceptibility. |
| TRUE Benchmark [82] | A comprehensive, standardized collection of texts from diverse tasks for the meta-evaluation of factual consistency metrics. | |
| Mu-SHROOM & CCHall [78] | Benchmarks from SemEval and ACL 2025 designed to expose model blind spots in multilingual and multimodal reasoning. | |
| Evaluation Metrics | Large-Scale NLI [82] | Uses Natural Language Inference models to determine if a generated claim is entailed by, contradicts, or is neutral to the source. A top-performer in the TRUE evaluation. |
| QA-Based Metrics [82] | Generates questions from the source and generated text, then checks answer consistency. Complements NLI by catching different error types. | |
| Faithfulness & Self-Confidence Scores [84] | Metrics that measure alignment with trusted sources and the model's own confidence, helping to flag risky responses. | |
| Detection & Mitigation Tools | Real-Time Detectors (e.g., HDM-1, Galileo) [79] | Specialized tools that provide real-time hallucination assessments during text generation, enabling immediate intervention. |
| Retrieval-Augmented Generation (RAG) [78] | A mitigation architecture that grounds LLM responses in external, verifiable knowledge sources to enforce factuality. | |
| Uncertainty-Aware RLHF [78] | A training-time mitigation that adjusts reward models to penalize overconfidence and reward calibrated uncertainty, addressing the root incentive problem. |
Conclusion
Cross-domain authorship verification has evolved from traditional stylometry to sophisticated models that fuse semantic and stylistic features, proving essential for upholding scientific integrity. The methodologies and protocols discussed provide a roadmap for developing systems robust enough to handle domain shifts and the emerging challenge of LLM-generated text. For biomedical and clinical research, reliable authorship verification is not merely an academic exercise but a practical necessity for authenticating research findings, ensuring proper attribution in drug development documentation, and combating scientific misinformation. Future progress hinges on creating more diverse, multi-lingual datasets, developing explainable AI techniques for forensic applications, and establishing standardized protocols for verifying human-AI collaborative writing, which will be crucial for the next generation of trustworthy scientific communication.
References
- 1. The Million Authors Corpus: A Cross-Lingual and ... [https://aclanthology.org/2025.findings-acl.1335/]
- 2. Research Misconduct in 2025: New Definitions, Cases & ... [https://www.kuali.co/post/what-is-research-misconduct-new-definitions-cases-and-how-to-prevent-it-in-2025]
- 3. Cross-Genre Authorship Attribution via LLM-Based ... [https://arxiv.org/html/2510.16819v1]
- 4. Rethinking the Authorship Verification Experimental Setups [https://aclanthology.org/2022.emnlp-main.380/]
- 5. Evaluating Bibliometrics Reviews: A Practical Guide for Peer ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12476466/]
- 6. ICMJE 2025: Key Changes in Authorship, AI Use, and ... [https://www.proof-reading-service.com/blogs/ai-in-scholarly-publishing/icmje-2025-key-changes-in-authorship-ai-use-and-ethical-publishing]
- 7. Guidelines on Authorship in Scholarly or Scientific ... [https://division-research.brown.edu/research-cycle/conduct-research/ethics-research/guidelines-authorship-scholarly-or-scientific]
- 8. Is badfiction processed differently by the human brain? An ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10853416/]
- 9. Making experimental data tables in the life sciences more FAIR [https://pmc.ncbi.nlm.nih.gov/articles/PMC7736789/]
- 10. Color contrast - Accessibility - MDN Web Docs - Mozilla [https://developer.mozilla.org/en-US/docs/Web/Accessibility/Guides/Understanding_WCAG/Perceivable/Color_contrast]
- 11. Understanding Success Criterion 1.4.3: Contrast (Minimum) [https://www.w3.org/WAI/WCAG21/Understanding/contrast-minimum.html]
- 12. Sameness entices, but novelty enchants in fanfiction online [https://www.nature.com/articles/s41599-025-05166-3]
- 13. Cross-Domain Authorship Attribution Using Pre-trained ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7256385/]
- 14. Detection of changes in literary writing style using N-grams ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9299308/]
- 15. Stylometry and forensic science: A literature review - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC11707938/]
- 16. Stylometry Methods and Practices - Research Guides [https://guides.temple.edu/stylometryfordh/methods]
- 17. A Light Stroll through Computational Stylometry and its ... [https://scalar.usc.edu/works/c2c-digital-magazine-fall-winter-2016/a-light-stroll-through-computational-stylometry-and-its-early-potential]
- 18. Stylometry recognizes human and LLM-generated texts in ... [https://arxiv.org/abs/2507.00838]
- 19. Shared Tasks on Authorship Analysis at PAN 2020 - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC7148014/]
- 20. AIDBench: A benchmark for evaluating the authorship ... [https://arxiv.org/html/2411.13226v1]
- 21. CROSSNEWS: A Cross-Genre Authorship Verification and ... [https://ojs.aaai.org/index.php/AAAI/article/view/34659]
- 22. Overview of the Plagiarism Detection Task at PAN 2025 [https://arxiv.org/html/2510.06805v1]
- 23. at CLEF 2018 - PAN Profiling Author [https://pan.webis.de/clef18/pan18-web/author-profiling.html]
- 24. Authorship Attribution in the Era of LLMs [https://pmc.ncbi.nlm.nih.gov/articles/PMC12019761/]
- 25. Authorship Attribution in the Era of LLMs: Problems ... [https://llm-authorship.github.io/]
- 26. Attributing authorship via the perplexity of authorial language ... [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0327081]
- 27. Can Large Language Models Identify Authorship? [https://arxiv.org/html/2403.08213v1]
- 28. Exploring the potential of large language models for author ... [https://www.sciencedirect.com/science/article/pii/S2666281724001380]
- 29. Combining style and semantics for robust authorship ... [https://www.sciencedirect.com/science/article/pii/S266682702500115X]
- 30. CAVE: Controllable Authorship Verification Explanations [https://arxiv.org/html/2406.16672v1]
- 31. A Siamese Network via Cross-Domain Robust Feature ... [https://www.mdpi.com/2072-4292/17/4/646]
- 32. FootprintNet: a Siamese network method for biometric ... [https://link.springer.com/article/10.1007/s11227-025-07170-5]
- 33. Ensemble Siamese Network (ESN) Using ECG Signals for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10222383/]
- 34. Be Sure to Use the Same Writing Style [https://www.mdpi.com/2076-3417/15/5/2467]
- 35. Unlocking the Comparative Power of Siamese Neural ... [https://medium.com/towardsdev/decoding-similarities-unlocking-the-comparative-power-of-siamese-neural-networks-in-machine-ea53833ecb41]
- 36. DeepDTAGen: a multitask deep learning framework for ... [https://www.nature.com/articles/s41467-025-59917-6]
- 37. RB_BG_MHA: A RoBERTa-Based Model with Bi-GRU and ... [https://www.mdpi.com/2076-3417/13/19/11000]
- 38. Implementing BERT and fine-tuned RobertA to detect AI ... [https://www.semanticscholar.org/paper/Implementing-BERT-and-fine-tuned-RobertA-to-detect-Wang-Cheng/da420c73bd3cee3d8a97a8ddacc4efcf2d7f5c9d]
- 39. Fusion of SoftLexicon and RoBERTa for Purpose-Driven ... [https://www.mdpi.com/2076-3417/13/24/13296]
- 40. Enhancing Authorship Attribution through Embedding Fusion [https://arxiv.org/html/2411.00411v1]
- 41. A Multimodal Transformer: Fusing Clinical Notes with ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10148371/]
- 42. Towards Reliable Evaluation of Cross-Lingual Knowledge ... [https://arxiv.org/html/2511.14774v1]
- 43. 介绍SeaEval:多语言基础模型的全面评估基准原创 [https://blog.csdn.net/shizheng_Li/article/details/148173823]
- 44. 首次覆盖超11 类真实编程场景!豆包大模型团队开源代码 ... [https://seed.bytedance.com/zh/blog/the-doubao-seed-team-open-sources-new-benchmark-for-code-large-models-covering-over-11-real-world-programming-scenarios-for-the-first-time]
- 45. Cross-Lingual Summarization for Low-Resource ... [https://www.mdpi.com/2076-3417/15/14/7800]
- 46. A scalable framework for evaluating multiple language ... [https://www.nature.com/articles/s41598-025-15203-5]
- 47. Cross-lingual Evaluation of Multilingual Text Generation [https://aclanthology.org/2025.coling-main.520/]
- 48. Authorship Attribution Methods, Challenges, and Future ... [https://www.mdpi.com/2078-2489/15/3/131]
- 49. SPIRIT 2025 statement: updated guideline for protocols of ... [https://www.nature.com/articles/s41591-025-03668-w]
- 50. Publication Policies & Authorship Criteria - Clinical Trials 101 [https://www.clinicaltrials101.com/clinical-trial-transparency-disclosure/publication-policies-authorship-criteria/]
- 51. TDRLM: Stylometric learning for authorship verification by ... [https://www.sciencedirect.com/science/article/abs/pii/S0957417423012472]
- 52. Domain generalization for the open-set cross ... [https://www.sciencedirect.com/science/article/abs/pii/S1474034625005397]
- 53. mixture of experts for cross-domain fake news detection [https://link.springer.com/article/10.1007/s10994-025-06827-9]
- 54. Authorship Attribution in the Era of LLMs [https://arxiv.org/html/2408.08946v2]
- 55. AI-generated Text Detection: A Multifaceted Approach to ... [https://arxiv.org/html/2505.11550v1]
- 56. AI Detection and assessment - an update for 2025 [https://nationalcentreforai.jiscinvolve.org/wp/2025/06/24/ai-detection-assessment-2025/]
- 57. PAN at CLEF 2023 - Authorship Verification - Webis Group [https://pan.webis.de/clef23/pan23-web/author-identification.html]
- 58. Metadata Management Best Practices: A Complete 2025 ... [https://www.ovaledge.com/blog/metadata-management-best-practices]
- 59. Receiver operating characteristic [https://en.wikipedia.org/wiki/Receiver_operating_characteristic]
- 60. Understanding F1 Score, Accuracy, ROC-AUC & PR- ... [https://www.deepchecks.com/f1-score-accuracy-roc-auc-and-pr-auc-metrics-for-models/]
- 61. A Brief on Brier Scores | UVA Library [http://library.virginia.edu/data/articles/a-brief-on-brier-scores]
- 62. The receiver operating characteristic curve accurately ... [https://www.sciencedirect.com/science/article/pii/S2666389924001090]
- 63. Weighted Brier Score - an Overall Summary Measure for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12523994/]
- 64. Shared Tasks - PAN - Webis Group [https://pan.webis.de/shared-tasks.html]
- 65. 8 Analysis in Authorship Attribution [https://methods.clsinfra.io/analysis-author.html]
- 66. Evaluation Metrics for ML Models in Drug Discovery [https://www.elucidata.io/blog/evaluation-metrics-for-ml-models-in-drug-discovery]
- 67. Enhancing Generalization across Languages and Domains [https://arxiv.org/html/2509.16531v1]
- 68. Pharmacokinetic Model Comparisons: How We Do It and Why ... [https://blog.insight-rx.com/resources/pharmacokinetic-model-comparisons-methods]
- 69. Benchmarking compound activity prediction for real-world ... [https://www.nature.com/articles/s42004-024-01204-4]
- 70. Evaluating the performance of machine‐learning ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9835131/]
- 71. A Systematic Review of Key Retrieval-Augmented ... [https://arxiv.org/html/2507.18910v1]
- 72. Deeper insights into retrieval augmented generation [https://research.google/blog/deeper-insights-into-retrieval-augmented-generation-the-role-of-sufficient-context/]
- 73. The 2025 Guide to Retrieval-Augmented Generation ( RAG ) [https://www.edenai.co/post/the-2025-guide-to-retrieval-augmented-generation-rag]
- 74. RAG Diagram Guide: Visual Architecture of Retrieval- ... [https://latenode.com/blog/ai-frameworks-technical-infrastructure/rag-retrieval-augmented-generation/rag-diagram-guide-visual-architecture-of-retrieval-augmented-generation]
- 75. RAG Pipeline Diagram: A Beginner's Guide to How It Works [https://www.designveloper.com/blog/rag-pipeline-diagram/]
- 76. evaluation: Metrics, RAG , best practices & more methodologies [https://www.meilisearch.com/blog/rag-evaluation]
- 77. vectara/hallucination-leaderboard [https://github.com/vectara/hallucination-leaderboard]
- 78. LLM Hallucinations in 2025: How to Understand and ... [https://www.lakera.ai/blog/guide-to-hallucinations-in-large-language-models]
- 79. Data Reveals: 5 Breakthroughs in AI Hallucination ... [https://mixflow.ai/blog/data-reveals-5-breakthroughs-in-ai-hallucination-detection-for-november-2025]
- 80. The Mirage of Hallucination Detection [https://machinelearning.apple.com/research/hallucination-detection]
- 81. Investigating Crowdsourcing Protocols for Evaluating the ... [https://aclanthology.org/2022.naacl-main.417/]
- 82. [2204.04991] TRUE: Re-evaluating Factual Consistency ... [https://arxiv.org/abs/2204.04991]
- 83. Fine-grained Multilingual Benchmark Dataset for LLM ... [https://arxiv.org/abs/2503.07833]
- 84. Hallucination Detection in LLMs: Methods, Metrics ... [https://www.statsig.com/perspectives/hallucination-detection-llms-methods]