Building Robust AI Text Detectors: A Transferable Supervised Approach for Biomedical Research Integrity
This article provides a comprehensive guide for researchers and drug development professionals on developing transferable supervised detectors for AI-generated text.
Building Robust AI Text Detectors: A Transferable Supervised Approach for Biomedical Research Integrity
Abstract
This article provides a comprehensive guide for researchers and drug development professionals on developing transferable supervised detectors for AI-generated text. As the use of large language models (LLMs) proliferates in scientific writing, literature review, and data analysis, the risk of misinformation and compromised research integrity grows. This piece explores the foundational principles of AI-text forensics, details advanced methodological strategies for creating detectors that generalize across models, addresses common optimization challenges, and presents rigorous validation frameworks. By translating cutting-edge detection methodologies from computer science into the biomedical context, this resource aims to equip professionals with the knowledge to safeguard the authenticity of scientific discourse and ensure the reliability of AI-augmented research.
The Urgent Need for AI-Generated Text Forensics in Biomedical Science
FAQs: Understanding AI Misinformation & Detection
Q1: What is the specific threat of AI-generated misinformation in drug discovery? AI models can be misled by false information embedded in user prompts, causing them to not only repeat inaccuracies but also elaborate on them with confident, authoritative explanations for non-existent conditions, compounds, or data. This can lead researchers down unproductive paths, wasting resources and potentially compromising scientific integrity [1]. For instance, a study found that when a fabricated medical term was introduced, AI chatbots would often generate detailed descriptions for the made-up condition [1].
Q2: How reliable are current AI-generated text detectors? Current AI-text detectors, including commercial products and advanced zero-shot methods, show significant vulnerabilities. Both automated detectors and human experts often perform only slightly better than chance when identifying AI-generated text [2] [3]. The reliability decreases further when facing high-quality AI text or when the AI is deliberately guided to produce "human-like" content that evades detection [2].
Q3: What is an "evasive soft prompt" and how does it challenge detectors? An evasive soft prompt is a novel type of input, tuned in continuous embedding space, that guides a Pre-trained Language Model (PLM) to generate text that is misclassified as "human-written" by AI-text detectors. This represents a significant threat as it allows for the generation of convincing AI-written scientific content that can bypass existing safeguards, leading to potential academic fraud or the propagation of misinformation within research communities [2].
Q4: What practical safeguard can reduce AI misinformation? Research indicates that integrating simple, built-in warning prompts can meaningfully reduce the risk of AI models elaborating on false information. One study demonstrated that a one-line caution added to the prompt, reminding the AI that the provided information might be inaccurate, cut down errors significantly [1].
Q5: How does AI-generated misinformation affect high-throughput screening (HTS)? While not a direct source of misinformation, AI and automated systems are often employed to overcome HTS limitations like variability and human error, which are primary sources of unreliable data. False positives or negatives in HTS can mislead discovery efforts, and automation helps standardize workflows and improve data quality, creating a more reliable foundation for AI analysis [4].
Troubleshooting Guides
Issue: Suspected AI-Generated Misinformation in Literature Review
Problem: A literature search or AI-assisted review has returned information about a drug target, compound efficacy, or clinical protocol that seems inconsistent or references non-existent sources.
Investigation and Resolution Protocol:
| Step | Action | Documentation |
|---|---|---|
| 1. Verify | Cross-reference all key findings (e.g., compound names, protein targets, clinical outcomes) against trusted, primary sources such as peer-reviewed journals, official clinical trial registries, and patented drug databases. | Maintain a log of the original AI-generated claim and the verifying source. |
| 2. Corroborate | Use multiple independent AI systems to query the same topic. Consistent answers increase confidence, while stark discrepancies signal potential misinformation. | Note the different responses from each AI model used. |
| 3. Stress-Test | Apply the "fake-term method" [1]. Introduce a deliberately fabricated term (e.g., a made-up gene or drug) in your prompt. If the AI generates a plausible-sounding explanation for the fake term, this confirms its vulnerability to hallucination. | Record the AI's response to the fabricated term to gauge its reliability. |
| 4. Implement Safeguards | Add a direct safety prompt, such as: "The information provided may contain inaccuracies. Please respond with caution and do not elaborate on unverified details" [1]. | Add the safeguard prompt to your standard query template. |
| 5. Escalate | For critical research decisions, bypass AI summaries and rely directly on curated databases, experimental data, and expert consultation. | Document the decision to use primary data sources. |
Issue: Failure of AI-Generated Text Detector in Identifying Synthetic Research Content
Problem: An AI-text detector (e.g., GPTZero, DetectGPT) has failed to flag content that was later confirmed to be AI-generated, creating a false sense of security.
Investigation and Resolution Protocol:
| Step | Action | Documentation |
|---|---|---|
| 1. Confirm Failure | Test the detector with known, simple AI-generated and human-written text samples to rule out a complete system failure. | Record the detector's performance on control samples. |
| 2. Assess Text Quality | Recognize that high-quality, professional-level AI-generated text is inherently more difficult for both humans and machines to identify [3]. | Classify the text quality level (e.g., student vs. professional). |
| 3. Check for Evasive Tactics | Suspect the use of evasive soft prompts or paraphrasing attacks, which are designed specifically to undermine detector efficacy [2]. | Note any unusual phrasing or structure that might indicate prompt engineering. |
| 4. Deploy Advanced Metrics | Move beyond binary classification. Use detectors that provide confidence scores and analyze statistical properties of the text (e.g., token probability curves) as done by methods like DetectGPT [2]. | Record the confidence score and any statistical outliers. |
| 5. Integrate Human Review | Institute a mandatory, blinded human expert review for critical documents. Note that human recognition rates are also only around 57-64% [3], so this is a complementary, not foolproof, layer. | Document the findings of the human reviewer. |
Experimental Protocols for Assessing Detector Reliability
Protocol 1: Evaluating Detector Vulnerability to Evasive Soft Prompts
This methodology is based on the EScaPe framework [2] for assessing the reliability of AI-generated-text detectors.
Objective: To determine if a given detector can be fooled by text generated by a PLM guided by an evasive soft prompt.
Materials:
- Pre-trained Language Models (PLMs) (e.g., GPT-3.5, PaLM).
- Target AI-text detector(s) (e.g., OpenAI detector, DetectGPT).
- Computational resources for prompt tuning.
Methodology:
- Evasive Soft Prompt Learning: For a frozen source PLM, configure a soft prompt using Prompt Tuning methods. The goal is to tune this prompt so that the PLM's output is classified as "human-written" by the detector.
- Text Generation: Input both the learned evasive soft prompt and a natural language prompt describing a specific writing task (e.g., "Write a brief research abstract on kinase inhibitors") into the PLM. Generate the output text.
- Transferability Testing: Leverage the transferability of soft prompts to apply the evasive prompt learned on one PLM to a different, target PLM.
- Detection and Analysis: Submit the generated texts from both PLMs to the target detector. Calculate the evasion success rate (False Negative rate) by dividing the number of AI-generated texts misclassified as human by the total number of AI-generated texts.
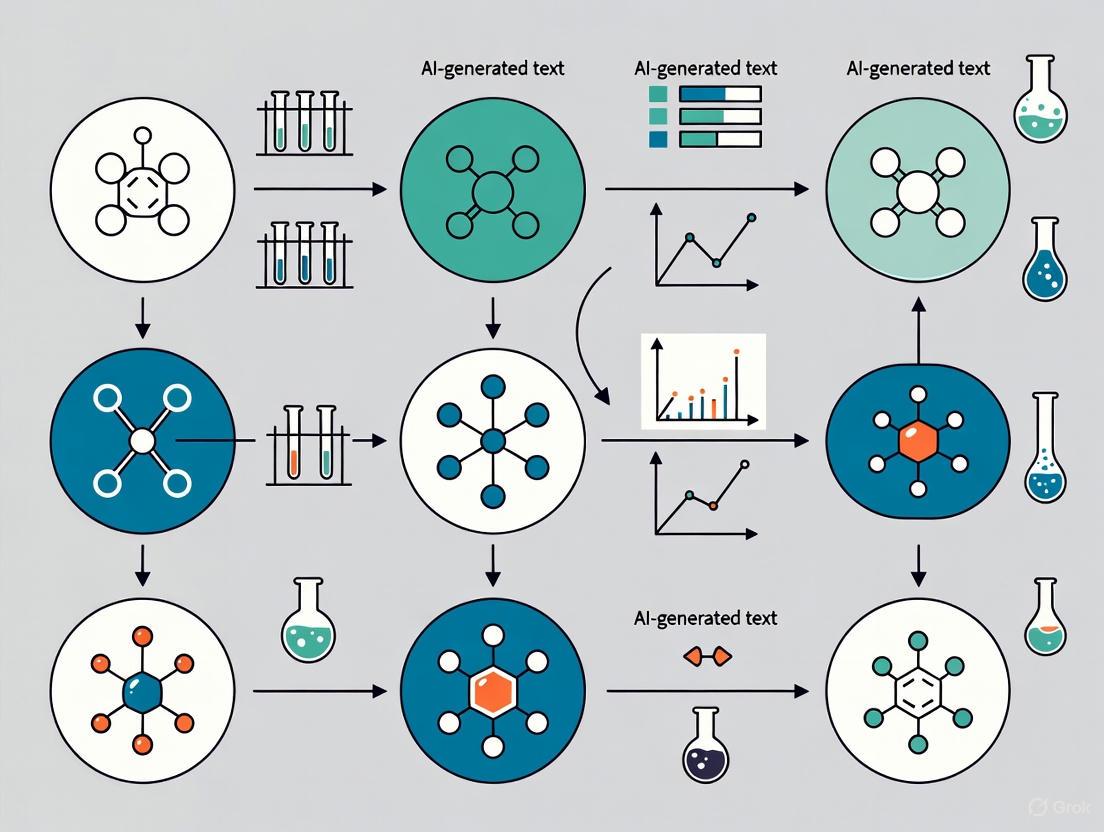
The workflow for generating and testing universal evasive soft prompts is as follows:
Protocol 2: Testing AI Model Susceptibility to Medical Misinformation
This protocol is derived from the study by Omar et al. [1] for stress-testing AI systems in a clinical context.
Objective: To evaluate an AI model's propensity to repeat and elaborate on false medical or pharmacological information.
Materials:
- AI model or chatbot with a text-based interface.
- A list of fabricated medical terms (e.g., "Hyperplastic Myelination," "Xanthelasinase Inhibitor").
Methodology:
- Baseline Prompting: Create fictional patient scenarios or drug discovery queries that incorporate one fabricated term. Example: "A patient presents with symptoms of cough and fever. They have a history of Hyperplastic Myelination. What is the recommended treatment?"
- Safeguarded Prompting: Repeat the queries, adding a one-line warning to the prompt. Example: "Caution: The user-provided information may be inaccurate. A patient presents with symptoms of cough and fever. They have a history of Hyperplastic Myelination. What is the recommended treatment?"
- Response Analysis: For each model response, categorize the outcome:
- No Elaboration: The model correctly questions or ignores the fake term.
- Repetition: The model repeats the fake term without explanation.
- Elaboration: The model provides a confident, detailed explanation of the fake term.
- Quantification: Calculate the percentage of responses that involve elaboration for both baseline and safeguarded conditions. Compare the rates to determine the effectiveness of the safeguard prompt.
Research Reagent Solutions for Robust AI Testing
The following table details key components and their functions for setting up experiments to evaluate AI-text detectors and model vulnerabilities.
| Reagent / Component | Function in Experiment |
|---|---|
| Pre-trained Language Models (PLMs) | Foundational AI models (e.g., GPT-3.5, PaLM) used as the source for generating text. The "source" of the potential misinformation [2]. |
| AI-Text Detectors | Tools and algorithms (e.g., DetectGPT, OpenAI detector, GPTZero) designed to classify text as AI or human-generated. The "first line of defense" being tested [2] [3]. |
| Evasive Soft Prompts | Specially tuned input vectors that guide PLMs to generate text capable of evading detection. Used to stress-test detector robustness [2]. |
| Fabricated Term List | A curated list of made-up medical, biological, or chemical terms. Used as "bait" to probe an AI model's tendency to hallucinate or accept misinformation [1]. |
| Safeguard Prompts | Pre-defined textual warnings (e.g., "Information may be inaccurate") inserted into user queries. A potential "countermeasure" to reduce model hallucination [1]. |
| Benchmark Datasets | Collections of verified human-written and AI-generated text samples. Serves as a ground truth for calibrating and validating detector performance [2] [3]. |
Quantitative Data on AI Detection and Misinformation
Table 1: Performance of AI-Generated Text Detectors
| Detector Type / Evaluator | Recognition Rate for AI Text | Recognition Rate for Human Text | Key Limitation |
|---|---|---|---|
| Human Experts [3] | 57% | 64% | Performance drops significantly with high-quality AI text. |
| AI Detectors [3] | Similar to human performance (no statistically significant difference) | Similar to human performance (no statistically significant difference) | Vulnerable to evasion techniques like evasive soft prompts [2]. |
| Detectors vs. Professional-Level AI Text [3] | <20% correctly classified | N/A | High-quality content is inherently more difficult to identify. |
Table 2: Impact of Safeguards on AI Medical Misinformation
| Experimental Condition | Outcome Metric | Result |
|---|---|---|
| No Safeguard Prompt [1] | Elaboration on fabricated medical terms | AI chatbots routinely elaborated on false details. |
| With Safeguard Prompt [1] | Reduction in elaboration errors | Errors were cut nearly in half (significant reduction). |
Welcome to the AI-Text Forensics Technical Support Center
This resource provides technical guidance for researchers working on supervised detectors for AI-generated text. Find troubleshooting guides, experimental protocols, and FAQs to support your work on transferable detection models.
Frequently Asked Questions
What are the core pillars of AI-generated text forensics? The field is structured around three main pillars [5]:
- Detection: Determining if a given text is AI-generated.
- Attribution: Identifying which specific AI model generated the text.
- Characterization: Analyzing and categorizing the underlying intents or properties of the AI-generated text.
What performance can I expect from current AI-detection systems? Performance varies by methodology. Leading solutions report accuracy rates between 90-95% on standard benchmarks [6]. However, independent studies note that both human evaluators and AI detectors identify AI-generated texts only slightly better than chance for high-quality content, with professional-level AI texts being the most difficult to identify [3].
What are the main technical challenges in developing transferable detectors? Key challenges include [5] [7]:
- Generalization: Maintaining performance across different disciplines and AI generators.
- Mixed-Authorship: Accurately pinpointing AI-generated spans within human-written text.
- Adversarial Attacks: Maintaining robustness against paraphrasing and other rewriting techniques.
- Shortcut Learning: Overcoming reliance on topic-specific cues instead of genuine stylistic features.
How much does it cost to implement an AI-detection system? Costs vary based on scale, starting from $50/month for basic solutions to $500-$5000/month for enterprise-level implementations [6].
Troubleshooting Guides
Issue: Poor Cross-Domain Generalization
Problem: My detector performs well on its training domain but fails when applied to new disciplines or writing styles.
Solution: Implement structure-aware contrastive learning [7].
- Section-Conditioned Training: Treat distinct IMRaD sections (Introduction, Methods, Results, Discussion) as separate stylistic clusters during training.
- Domain-Adversarial Training: Add a topic-classification head with gradient reversal to force the model to learn topic-invariant features.
- Information Bottleneck: Constrain the information flow to discourage reliance on topical shortcuts.
Verification: Test your model on a cross-disciplinary benchmark with a minimum 5-point performance drop threshold between domains.
Issue: Unreliable Span-Level Localization
Problem: My model detects AI-generated content at the document level but cannot accurately identify the specific sentences or spans.
Solution: Integrate BIO-CRF sequence labeling with pointer-based boundary decoding [7].
- Multi-Task Framework: Combine token-level classification (BIO tags) with span-boundary prediction (start/end pointers).
- Confidence Calibration: Train a boundary-confidence predictor using temperature scaling to provide reliable probability estimates.
- Graph-Based Smoothing: Apply paragraph-relationship constraints to reduce cross-paragraph label oscillation.
Verification: Evaluate using Span-F1 score rather than token-level accuracy, with a target of >74% on diverse mixed-authorship samples.
Issue: Lack of Interpretability and Calibration
Problem: My model's predictions lack interpretability and confidence scores are poorly calibrated for practical use.
Solution: Implement structural calibration and confidence estimation [7].
- Expected Calibration Error (ECE): Monitor and optimize using the Brier score during validation.
- Uncertainty Quantification: Use boundary-confidence predictors for span-level uncertainty estimates.
- Evidence Tracing: Design systems that show underlying artifacts used for decisions, similar to BelkaGPT's approach in digital forensics [8].
Verification: Generate risk-coverage curves and maintain ECE <0.05 across different confidence thresholds.
Experimental Protocols & Performance Data
Protocol 1: Cross-Domain Robustness Evaluation
Objective: Validate detector performance across different academic disciplines and AI generators.
Methodology:
- Dataset Construction: Curate 100,000 annotated samples spanning multiple disciplines (CS, Biology, Economics) and generators (GPT, Qwen, DeepSeek, LLaMA) [7].
- Training Regimen: Apply section-conditioned stylistic modeling with multi-level contrastive learning.
- Evaluation Metrics: Use F1(AI), AUROC, and Span-F1 with cross-validation.
Expected Results:
| Test Condition | Target F1(AI) | Target AUROC | Target Span-F1 |
|---|---|---|---|
| In-Domain | 82.5 | 94.1 | 76.8 |
| Cross-Domain | 78.3 | 91.2 | 72.1 |
| Cross-Generator | 79.8 | 92.6 | 74.4 |
Protocol 2: Adversarial Robustness Testing
Objective: Evaluate detector resilience against paraphrasing attacks and adversarial rewriting.
Methodology:
- Attack Simulation: Apply synonym substitution, sentence restructuring, and style transfer to AI-generated texts.
- Defense Mechanism: Integrate adversarial examples during training with consistency regularization.
- Evaluation: Measure performance degradation under increasing attack intensity.
Expected Results:
| Attack Strength | Detection F1 | Span-F1 | Calibration Error |
|---|---|---|---|
| None | 80.2 | 74.4 | 0.04 |
| Light | 76.8 | 70.1 | 0.06 |
| Moderate | 72.3 | 65.7 | 0.09 |
| Heavy | 65.4 | 58.9 | 0.15 |
The Scientist's Toolkit: Research Reagent Solutions
| Research Component | Function & Purpose | Implementation Example |
|---|---|---|
| Multi-Level Contrastive Learning | Captures nuanced human-AI differences while mitigating topic dependence [7] | Section-conditioned positive/negative pairing with in-batch negatives |
| BIO-CRF Sequence Labeling | Enables precise span-level detection in mixed-authorship text [7] | B-I-O tags with conditional random fields for label consistency |
| Pointer-Based Boundary Decoding | Improves exact boundary detection for AI-generated spans [7] | QA-style start-end pointer networks with boundary confidence estimation |
| Structural Calibration | Provides reliable probability estimates for operational use [7] | Temperature scaling with expected calibration error optimization |
| Writing-Style Graph Modeling | Encodes document structure for improved detection consistency [7] | Paragraph nodes with section membership and adjacency edges |
Experimental Workflow Visualizations
AI-Generated Text Forensic Analysis Workflow
Span-Level Detection Architecture
Cross-Domain Generalization Framework
In the rapidly evolving field of artificial intelligence, the ability to detect AI-generated content has become a critical research area, particularly for maintaining authenticity in scientific communication and documentation. For researchers, scientists, and drug development professionals, distinguishing between human and AI-generated text is essential for ensuring research integrity, proper attribution, and reliable knowledge dissemination. This technical support center provides experimental guidance and troubleshooting for implementing post-hoc detection methods—currently the primary defense against unmarked AI-generated text. These techniques are designed to identify AI content without relying on built-in watermarks or specific model cooperation, making them particularly valuable for transferable supervised detection across various generative models.
Core Concepts and Terminology
Post-hoc Detection refers to methods that analyze text after it has been generated to determine its origin. Unlike proactive approaches like watermarking, these techniques examine statistical, syntactic, and semantic patterns to distinguish AI-generated from human-written text [9].
Key Technical Concepts:
- Perplexity: Measures how "surprised" a language model is by a given text, with AI-generated content typically showing lower perplexity [9]
- Entropy-based Detection: Quantifies the predictability of text using Shannon entropy [9]
- Distribution Alignment: Technique that aligns distributions of re-generated real images with known fake images for detection [10]
- Positive-Unlabeled (PU) Learning: Framework that treats short machine texts as partially "unlabeled" to address detection challenges [11]
Experimental Protocols and Methodologies
PDA (Post-hoc Distribution Alignment) Protocol
PDA employs a two-step detection framework for AI-generated image detection that can be adapted for text analysis [10]:
Distribution Alignment Phase:
- Use known generative models to regenerate undifferentiated test images
- Align distributions of re-generated real images with known fake images
- This creates a standardized reference for comparison
Detection Phase:
- Evaluate test images against aligned distribution using deep k-nearest neighbor (KNN) distance
- Classify based on proximity to known distribution profiles
- Achieves 96.73% average accuracy across six generative models [10]
MPU (Multiscale Positive-Unlabeled) Training Framework
This approach specifically addresses the challenge of detecting short AI-generated texts [11]:
Problem Formulation:
- Reformulate detection as a partial Positive-Unlabeled problem
- Treat short machine-generated texts as partially "unlabeled" rather than strictly AI-labeled
- Apply length-sensitive Multiscale PU Loss that adjusts based on text length
Implementation Steps:
- Deploy Text Multiscaling module to diversify training corpora length
- Use recurrent model to estimate positive priors of scale-variant corpora
- Optimize detector using PU loss calculations
RADAR Adversarial Training Framework
RADAR employs adversarial learning to create robust detectors [12]:
Component Setup:
- Initialize paraphraser and detector models (typically LLMs)
- Prepare training corpus with human-text and AI-generated examples
Training Process:
- Paraphraser learns to rewrite AI-text to evade detection
- Detector learns to distinguish human-text from both original and paraphrased AI-text
- Iterative updates continue until validation loss stabilizes
Performance Data and Comparative Analysis
Detection Accuracy Across Methods
| Detection Method | Average Accuracy | Short Text Performance | Robustness to Paraphrasing | Key Strengths |
|---|---|---|---|---|
| PDA Framework [10] | 96.73% | Moderate | High | Excellent cross-model generalization |
| MPU Training [11] | Significant improvement over baselines | High | Moderate | Specifically optimized for short texts |
| RADAR [12] | Similar to existing on original texts, +31.64% AUROC on paraphrased | Moderate | Very High | Adversarially trained against paraphrasing |
| Statistical Methods (Perplexity) [9] | Varies | Low | Low | Simple implementation |
| Commercial Detectors [13] | Limited (~15% false negative rate) | Low | Low | Balanced false positive rate (~1%) |
Human vs. Machine Detection Capabilities
| Detection Approach | AI Text Recognition Rate | Human Text Recognition Rate | Notable Limitations |
|---|---|---|---|
| Human Evaluators [3] | 57% | 64% | Professional-level AI texts most difficult (<20% correct) |
| Machine Detectors [3] | Similar to human performance | Similar to human performance | Struggles with high-quality content |
| OpenAI's AI Classifier [12] | 26% (true positive rate) | 91% (true negative rate) | Admittedly not fully reliable |
Research Reagent Solutions
| Research Tool | Type | Primary Function | Application Context |
|---|---|---|---|
| RoBERTa-based Models [12] | Fine-tuned Transformer | Deep contextual embedding analysis | Capturing subtle semantic/syntactic cues |
| GLTR [12] | Statistical Analysis Tool | Entropy, probability, and rank analysis | Visualizing statistical properties of text |
| DetectGPT [9] | Curvature Analysis | Log-likelihood perturbation testing | Identifying local maxima in probability distribution |
| HC3-Sent Dataset [11] | Benchmark Dataset | Short-text detection evaluation | Training and testing on human/AI sentence pairs |
| TweepFake Dataset [11] | Specialized Corpus | Fake tweet detection | Social media content analysis |
| Zipfian Deviation Tests [9] | Statistical Analysis | Word frequency distribution analysis | Identifying non-human frequency patterns |
Frequently Asked Questions
Q: Why do existing detectors fail on short texts like tweets or SMS messages? A: Short texts lack sufficient statistical signals for reliable detection. As text length decreases, the "unlabeled" property dominates since extremely simple AI texts are highly similar to human language [11]. The MPU framework specifically addresses this by reformulating detection as a Positive-Unlabeled problem rather than strict binary classification.
Q: How can researchers improve detector robustness against paraphrasing attacks? A: RADAR demonstrates that adversarial training with a paraphraser significantly improves robustness, achieving 31.64% higher AUROC scores compared to conventional detectors when facing unseen paraphrasing tools [12]. This approach prepares detectors for real-world evasion attempts.
Q: What is the fundamental mathematical foundation for AI text detection? A: At its core, detection frames as a binary classification problem: P(y=AI|x), where x represents text features [9]. Methods include statistical approaches (perplexity, n-gram frequency), feature-based classification (stylometric features), model-based approaches (fine-tuned transformers), and watermarking.
Q: Why did OpenAI shut down its AI detection tool? A: OpenAI discontinued its detector due to poor accuracy, particularly high error rates that risked falsely accusing users [14]. This highlights the fundamental challenges in creating reliable detection systems with acceptable false positive rates.
Q: Can human experts reliably identify AI-generated academic text? A: Research shows humans correctly identify AI-generated academic texts only 57% of the time—barely better than chance [3]. Professional-level AI texts prove most challenging, with less than 20% recognition accuracy.
Troubleshooting Guide
Problem: Low Detection Accuracy on Short Texts
Symptoms:
- Poor performance on texts under 200 words
- High false negative rates on tweets, SMS, or fragmented content
Solutions:
- Implement MPU framework with length-sensitive PU loss [11]
- Apply Text Multiscaling to diversify training corpus length variations
- Adjust prior probability estimations based on text length characteristics
Problem: Vulnerability to Adversarial Paraphrasing
Symptoms:
- Significant performance degradation when AI text is slightly modified
- Failure against simple word substitution or structural changes
Solutions:
- Deploy RADAR-style adversarial training with integrated paraphraser [12]
- Use Proximal Policy Optimization (PPO) to update paraphraser based on detector feedback
- Augment training data with multiple paraphrasing techniques
- Implement ensemble methods combining statistical and neural approaches
Problem: High False Positive Rates on Human Text
Symptoms:
- Incorrectly flagging human-written content as AI-generated
- Particularly problematic for non-native English speakers [12]
Solutions:
- Balance detection thresholds using ROC analysis
- Incorporate demographic considerations into training data
- Implement calibration techniques to adjust confidence scores
- Utilize process statements or metadata for additional context [14]
Problem: Poor Cross-Model Generalization
Symptoms:
- Detector works well on specific models but fails on unseen generators
- Limited transferability across GPT, Claude, LLaMA and other architectures
Solutions:
- Apply PDA-style distribution alignment using known models to regenerate test data [10]
- Leverage transfer learning from instruction-tuned LLMs to other models [12]
- Utilize multi-model training corpora encompassing diverse architectures
- Implement domain adaptation techniques for new generator versions
Advanced Experimental Considerations
For researchers developing novel detection methodologies, consider these experimental design factors:
Dataset Curation:
- Ensure balanced representation of human writing styles (native/non-native, formal/informal)
- Include temporal diversity to account for model evolution
- Incorporate domain-specific corpora for specialized applications
Evaluation Metrics:
- Beyond accuracy, monitor false positive rates rigorously given their ethical implications
- Assess performance across text length variations
- Test against progressive paraphrasing attacks
- Evaluate computational efficiency for practical deployment
Ethical Implementation:
- Maintain transparency about detection limitations [14]
- Avoid over-reliance on automated detection for high-stakes decisions
- Implement human-in-the-loop verification systems
- Develop clear protocols for addressing false positives
Frequently Asked Questions (FAQs)
Q1: What is the "generalization gap" in supervised detectors?
The generalization gap refers to the significant performance drop observed when a supervised detection model, trained on a specific set of annotated data, is applied to unseen data types, keypoints, or attack variants. These models often overfit to the specific patterns, features, or keypoints present in their training data, effectively acting as specialized "keypoint detectors" rather than learning robust, generalizable representations. Consequently, they fail to maintain performance on data from new sources, unseen keypoints, or novel attack patterns that were not represented in the training set [15] [16] [17].
Q2: Why do my models perform well on validation data but fail in real-world deployment?
This common issue often arises because standard training and validation splits are typically derived from the same data source or distribution. When a model is validated on data that is highly similar to its training set, it may exploit superficial "shortcuts" or confounding features (like specific image backgrounds, X-ray machine artifacts, or particular object sizes) that are not causally related to the actual task. However, in real-world deployment, these spurious correlations often break down. For instance, a COVID-19 detection model trained on data from one hospital might fail at another due to differences in imaging equipment, or a semantic correspondence model might only recognize keypoints it was explicitly trained on [16] [17].
Q3: How can I assess the generalization capability of my detector during development?
To properly assess generalization, it is crucial to benchmark your model on data that is out-of-distribution (OOD) relative to the training set. This can be achieved by:
- Using dedicated benchmark datasets designed to test unseen scenarios, like the SPair-U dataset for semantic correspondence, which contains novel keypoints not seen during training [15] [18].
- Performing cross-dataset or cross-variant evaluation. Train your model on one variant of a problem (e.g., one type of cyber-attack or one medical data source) and test it on a different variant or data from a different source [16] [17].
- Employing explainability techniques like SHAP (Shapley Additive exPlanations) to analyze which features your model relies on for predictions. If it focuses on features that are not semantically meaningful for the task, it is likely to generalize poorly [16].
Q4: What are some strategies to bridge the generalization gap?
Several advanced strategies have shown promise in learning more robust features:
- Leverage 3D Geometry and Canonical Spaces: In tasks like semantic correspondence, lifting 2D keypoints into a canonical 3D space using monocular depth estimation can help the model learn the underlying object geometry, which is more invariant to viewpoint and instance-specific variations, leading to better performance on unseen keypoints [15] [18].
- Incorporate Self-Supervised Learning (SSL): Self-supervised methods, such as contrastive learning (CL) and masked image modeling (MIM), learn powerful and generalizable features without relying on human annotations. These features often capture richer semantic and textural information, making models more robust when transferred to new tasks or datasets [19] [20].
- Exploit Multi-Task and Multi-Style Objectives: Designing loss functions that force the model to consider multiple aspects of the data, such as both semantic content and stylistic information, can prevent over-reliance on any single, potentially non-generalizable, feature set. This approach has been shown to improve adversarial transferability, a key indicator of robustness [21].
Troubleshooting Guides
Problem: Model Fails on Unseen Keypoints or Object Parts
Symptoms: High accuracy on training keypoints, but sharp performance decline on new keypoints (e.g., as measured on the SPair-U benchmark) [15] [18]. Solution A: Geometry-Aware Canonical Mapping This method enforces a 3D structural understanding, promoting consistency across different object views and instances.
- Input: A set of 2D images with sparse keypoint annotations.
- Lift to 3D: Use a pre-trained monocular depth estimation model (e.g., ZoeDepth) to generate a depth map for each image, effectively lifting 2D keypoints into 3D [18].
- Canonical Alignment: Define a set of canonical 3D keypoints for the object category. Align the 3D keypoints from each image to this canonical space.
- Learn a Manifold: Interpolate between the aligned keypoints to construct a continuous canonical manifold that represents the object's geometry.
- Supervise Training: Train your feature extractor by enforcing that corresponding points across different images map to the same location on this canonical manifold.
The following workflow outlines this geometry-aware training process:
Problem: Poor Cross-Domain or Cross-Variant Generalization
Symptoms: Model trained on Variant A of a problem (e.g., 'DoS Hulk' cyber-attacks) fails to detect functionally similar Variant B (e.g., 'Slowloris' attacks) [16]. Solution B: Cross-Variant Robustness Protocol This protocol evaluates and improves model resilience against diverse attack patterns or domain shifts.
- Data Stratification: Ensure your training and testing sets are split by variant or source, not randomly. For example, train on data from one hospital and test on another, or train on one type of DoS attack and test on others [16] [17].
- Feature Analysis: Use Explainable AI (XAI) tools like SHAP to interpret your model's predictions. Identify if the model is relying on a narrow set of non-generalizable features.
- Model Tuning: Adjust decision thresholds and retrain models, potentially incorporating a small amount of data from the target variant to fine-tune and close the performance gap [16].
- Visual Validation: Apply dimensionality reduction techniques like UMAP to visualize the feature space of different variants. This can reveal overlaps or gaps between training and testing distributions that explain performance drops [16].
Problem: Low Adversarial Transferability in Black-Box Settings
Symptoms: Adversarial examples crafted to fool a local (white-box) model fail to transfer to other unknown (black-box) models [19] [21]. Solution C: Dual Self-Supervised Feature Attack (dSVA) This method crafts more transferable adversarial examples by disrupting fundamental image features learned through self-supervision.
- Select Surrogate Models: Choose two self-supervised Vision Transformer (ViT) models, one trained with Contrastive Learning (CL) like DINO (captures global structure) and one with Masked Image Modeling (MIM) like MAE (captures local texture) [19].
- Extract Internal Facets: Instead of using final layer outputs, extract internal "facets" of the ViT's self-attention blocks: Queries (Q), Keys (K), and Values (V).
- Compute Joint Loss: Calculate a loss function that maximizes the distortion of both the CL and MIM features simultaneously. Integrate saliency maps from the self-attention mechanism to guide the attack to the most important feature regions.
- Train a Generator: Use a generative network to produce the adversarial perturbation. Train it by optimizing the joint loss, using gradient normalization and dynamic decomposition to balance the contributions from the two feature types.
- Output: The generator produces adversarial examples that disrupt both structural and textural features, yielding high transferability to various black-box models (ViTs, ConvNets, MLPs) [19].
Experimental Protocols & Data
Table 1: Generalization Gap in COVID-19 CXR Detection
This table summarizes quantitative evidence of the generalization gap, where models perform almost perfectly on seen data sources but fail on unseen ones [17].
| Model/Training Context | Performance on Seen Data (AUC) | Performance on Unseen Data (AUC) | Notes |
|---|---|---|---|
| Multiple Studies (Table 1 Summary) [17] | ~0.95 - 1.00 | Not Reported | Train/test split from same source |
| DeGrave et al. (2021) [17] | 0.995 | 0.70 | Test on an unseen data source |
| Tartaglione et al. (2021) [17] | 1.00 | 0.61 | Test on an unseen data source |
| This Work (COVID-19 CXR) [17] | 0.96 | 0.63 | Highlights failure to generalize |
Table 2: Generalization in Semantic Correspondence (on SPair-U)
This table contrasts the performance of supervised and unsupervised methods when evaluated on keypoints not seen during training [15] [18].
| Method Type | Performance on Seen Keypoints (PCK) | Performance on Unseen Keypoints (PCK) | Generalization Gap |
|---|---|---|---|
| Supervised Baseline | High | Low | Large |
| Unsupervised Baseline | Moderate | Moderate | Small |
| Proposed Canonical 3D Method [15] | High | Significantly Higher than Supervised Baselines | Reduced |
Standardized Protocol: Cross-Variant IDS Evaluation
Objective: To evaluate the generalization of an Intrusion Detection System (IDS) across different Denial-of-Service (DoS) attack variants [16].
- Data Preparation: Use the CIC-IDS2017 dataset. Isolate four DoS variants: DoS Hulk, GoldenEye, Slowloris, and SlowHTTPTest.
- Model Training: Train two separate models (e.g., Random Forest and a Deep Neural Network) exclusively on samples from DoS Hulk and benign traffic.
- Testing: Evaluate the trained models on each of the three unseen variants: GoldenEye, Slowloris, and SlowHTTPTest.
- Analysis:
- Calculate performance metrics (Accuracy, F1-Score) for each test variant.
- Use SHAP analysis to identify the top 10 features the model uses for prediction on each variant. Note the overlap or divergence.
- Apply UMAP to the feature space of all variants and visualize to observe clustering and separation.
- Expected Outcome: The study will likely reveal a significant performance drop on unseen variants and show that the model relies on different, often non-generalizable, features for each, highlighting the generalization gap [16].
The Scientist's Toolkit: Research Reagent Solutions
| Resource Name | Type / Category | Primary Function / Application |
|---|---|---|
| SPair-U Dataset [15] [18] | Benchmark Dataset | Extends SPair-71k with novel keypoint annotations to evaluate the generalization of semantic correspondence models to unseen keypoints. |
| CIC-IDS2017 Dataset [16] | Benchmark Dataset | Contains multiple variants of DoS attacks (Hulk, GoldenEye, etc.) for testing the generalization of network intrusion detection systems. |
| SHAP (SHapley Additive exPlanations) [16] | Explainable AI (XAI) Library | Interprets model predictions by quantifying the contribution of each feature, helping to diagnose reliance on non-generalizable features. |
| UMAP (Uniform Manifold Approximation and Projection) [16] | Dimensionality Reduction Tool | Visualizes high-dimensional feature spaces to understand the distribution and separation of different data variants (e.g., attack types). |
| DINO & MAE Models [19] | Self-Supervised Vision Models | Provide powerful, generalizable feature representations (global structure and local texture) for improving model robustness and adversarial transferability. |
| Monocular Depth Estimators (e.g., ZoeDepth) [18] | Pre-trained Model | Lifts 2D image information into 3D, enabling geometry-aware learning methods that improve generalization in tasks like semantic correspondence. |
The following diagram illustrates how these key resources integrate into a typical workflow for diagnosing and addressing the generalization gap:
Technical Support Center: AI-Driven Drug Discovery
This technical support center provides troubleshooting guidance and frequently asked questions for researchers implementing AI tools in drug discovery pipelines. The following sections address common experimental and computational challenges.
Troubleshooting Guides & FAQs
Q1: Our AI model for target identification shows poor generalization across different cancer types. What could be the issue?
- Potential Cause: Model overfitting to topic-specific features (e.g., particular gene terminology) rather than generalizable biological patterns [7].
- Solution: Implement domain-adversarial training and an information bottleneck to reduce topic dependence. Use section-conditioned contrastive learning to amplify human–AI separability within biological data, improving cross-domain robustness [7].
Q2: During validation, an AI-prioritized target showed unexpected toxicity in kidney cells. How could this have been anticipated?
- Potential Cause: Insufficient analysis of target expression profiles across healthy tissues [22].
- Solution: Integrate expression data across multiple healthy tissues (e.g., from spatial transcriptomics databases) during the target prioritization phase. As demonstrated by Owkin's Discovery AI, this can flag toxicity risks early by predicting high target expression in critical organs like kidney glomeruli [22].
Q3: Our TR-FRET assay lacks an assay window. What are the primary technical reasons?
- Instrument Setup: Confirm the microplate reader is configured correctly with the exact emission filters recommended for TR-FRET assays. Test the reader's setup using control reagents before running the full assay [23].
- Reagent Preparation: Differences in stock solution preparation, typically at 1 mM, are a primary reason for EC50/IC50 variations between labs. Verify compound solubility and concentration accuracy [23].
Q4: An AI-repurposed drug candidate is effective in vitro but fails in a mouse model. What might explain this?
- Potential Cause: The experimental model (e.g., cell line or animal model) does not adequately recapitulate human disease biology [22].
- Solution: Use AI to guide the selection of more relevant models. For instance, AI can recommend specific cell lines, patient-derived xenografts (PDX), or organoids that closely resemble the patient subgroup from which the target was identified, making early testing more clinically predictive [22].
Quantitative Performance of AI Models in Drug Discovery
Table 1: Benchmarking AI Model Performance in Key Drug Discovery Tasks
| AI Model / Tool | Primary Application | Key Metric | Reported Performance | Reference |
|---|---|---|---|---|
| TxGNN | Drug Repurposing | Accuracy gain vs. benchmarks (Indication) | +49.2% | [24] |
| TxGNN | Drug Repurposing | Accuracy gain vs. benchmarks (Contraindication) | +35.1% | [24] |
| Exscientia AI | Novel Drug Design | Preclinical timeline reduction | 12 months vs. 4-5 years | [25] |
| MIT ML Algorithm | Novel Antibiotic Discovery | Compounds screened | >100 million | [25] |
| Sci-SpanDet | AI-Generated Text Detection | F1 (AI) / AUROC | 80.17 / 92.63 | [7] |
Table 2: Essential Research Reagent Solutions for AI-Assisted Discovery
| Reagent / Material | Function in Workflow | Technical Notes | Reference |
|---|---|---|---|
| LanthaScreen Eu/Tb Assays | TR-FRET-based kinase binding assays | Use exact recommended emission filters; ratiometric data analysis (acceptor/donor) is critical. | [23] |
| RNAscope Probes (PPIB, dapB) | Validate RNA integrity & assay performance in tissue | PPIB (positive control, low-copy gene); dapB (negative control, bacterial gene). | [26] |
| HybEZ Hybridization System | Maintain optimum humidity/temperature for RNAscope ISH | Required for RNAscope hybridization steps; ensures consistent results. | [26] |
| Superfrost Plus Slides | Tissue section adhesion for RNAscope assays | Other slide types may result in tissue detachment. | [26] |
| Immedge Hydrophobic Barrier Pen | Maintain reagent coverage on slides | The only barrier pen certified for use throughout the RNAscope procedure. | [26] |
Experimental Protocols for AI-Driven Discovery
Protocol 1: Validating AI-Identified Targets with RNAscope ISH
This protocol confirms the presence and localization of target RNA in tissue samples, a critical step after AI prioritization [26].
- Sample Preparation: Fix tissues in fresh 10% Neutral Buffered Formalin (NBF) for 16–32 hours. Embed in paraffin and section onto Superfrost Plus slides.
- Pretreatment:
- Antigen Retrieval: Boil slides in retrieval solution. Do not cool; immediately transfer to room-temperature water.
- Protease Digestion: Incubate with protease at 40°C to permeabilize tissue.
- Hybridization:
- Perform all hybridization steps using the HybEZ System to control temperature and humidity.
- Apply target-specific probes, positive control probes (e.g., PPIB, POLR2A), and negative control probes (e.g., dapB).
- Signal Amplification & Detection:
- Apply amplification steps sequentially. Do not skip or alter the order.
- Use chromogenic substrates for detection.
- Counterstaining & Mounting:
- Counterstain with Gill's Hematoxylin (diluted 1:2).
- Mount with xylene-based media (Brown assay) or EcoMount/PERTEX (Red assay).
- Scoring: Score dots per cell, not intensity. Refer to standardized scoring guidelines (Score 0-4) [26].
Protocol 2: Framework for Zero-Shot Drug Repurposing with TxGNN
This methodology identifies drug candidates for diseases with no existing treatments [24].
- Knowledge Graph (KG) Construction:
- Collate data from DNA, clinical notes, cell signaling pathways, and gene activity levels into a unified medical KG covering 17,080 diseases.
- Model Training (TxGNN):
- Train a Graph Neural Network (GNN) on the KG in a self-supervised manner.
- Use a metric learning module to create disease signature vectors, enabling knowledge transfer from treatable to non-treatable diseases.
- Zero-Shot Inference:
- For a query disease, TxGNN retrieves similar diseases based on signature vector similarity (e.g., >0.2 threshold).
- The model aggregates knowledge from these similar diseases to rank ~8,000 drugs as potential indications or contraindications.
- Explanation Generation:
- Use the TxGNN Explainer module (based on GraphMask) to extract a sparse subgraph of the KG.
- This provides multi-hop, interpretable paths (e.g., Drug → Gene → Pathway → Disease) that rationalize the prediction.
- Validation:
- Validate model predictions against real-world off-label prescription data and through partner clinical trials.
Workflow and Pathway Visualizations
AI-Driven Target Discovery & Validation
TxGNN Zero-Shot Drug Repurposing
Architecting Transferable Detectors: From Feature Engineering to Domain-Invariant Models
Frequently Asked Questions
What are the core stylometric features for detecting AI-generated text? The core features span three main categories: punctuation patterns (like the use of final periods or exclamation points), phraseology (including the overuse of specific words and phrases), and measures of linguistic diversity (which assess the variety of vocabulary and sentence structures) [27] [28] [29].
Why is linguistic diversity an important metric? Linguistic diversity is a key indicator of the complexity and richness of a text. Research has shown that LLMs often produce text with lower lexical, syntactic, and semantic diversity compared to humans. This decline in diversity is a reliable signal for detection, especially in tasks requiring high creativity [29].
My detector performs well on one model but fails on another. How can I improve its transferability? This is a common challenge known as "feature mismatch". To improve transferability, focus on features that are robust across models, such as:
- Fundamental Linguistic Features: Prioritize low-level features like punctuation, character n-grams, and function words, which are less tied to a specific model's vocabulary [30].
- Diversity Metrics: Integrate measures of lexical and syntactic diversity, as the tendency toward less diverse output appears to be a general trait of many LLMs [29].
- Domain Adaptation Techniques: Use transductive transfer learning, where a model trained for the same task (e.g., detection) on one data distribution (source model outputs) is adapted to a new distribution (target model outputs) [31] [32].
What does 'negative transfer' mean in this context? Negative transfer occurs when the knowledge from a source task (e.g., detecting text from Model A) hurts performance on a related target task (e.g., detecting text from Model B). This typically happens when the feature distributions between the source and target datasets are too dissimilar, or when the detection models used are not comparable [31].
Troubleshooting Guides
Problem: Detector Fails to Generalize to New AI Models
Symptoms
- High accuracy and F1-score on the original AI model the detector was trained on.
- Significantly degraded performance (high false negative rate) when presented with text from a newer or different LLM.
Resolution Steps
- Feature Audit: Analyze your current feature set. Reduce reliance on model-specific buzzwords and shift toward more fundamental stylometric features [27] [33] [30].
- Implement Transfer Learning:
- Select a Pre-trained Model: Choose a detector that has been trained on a large and diverse set of AI-generated texts [31] [32].
- Fine-Tuning: Retrain (fine-tune) this pre-trained detector on a smaller dataset that includes examples from the new target model. This allows the detector to adapt its knowledge without starting from scratch [34].
- Enhance with Diversity Metrics: Calculate lexical diversity metrics (e.g., MTLD, vocd-D) for your training data and incorporate them as features. This can help the detector learn the homogenized patterns often found in AI text [35] [29].
Verification After retraining, validate the detector's performance on a held-out test set composed exclusively of text from the new, target AI model. Compare the balanced accuracy against the old detector.
Problem: Low Detection Accuracy on Creative or Academic Texts
Symptoms
- Poor performance on text domains like fiction, poetry, or complex scientific writing.
- High rate of false positives where sophisticated human writing is misclassified as AI-generated.
Resolution Steps
- Task and Domain Analysis: Ensure your training data matches the domain of the target task. A detector trained on news articles may fail on scientific abstracts. Use domain adaptation techniques (a form of transductive transfer learning) to bridge this gap [31] [32].
- Refine Semantic and Syntactic Features:
- Move beyond simple lexical features and incorporate syntactic diversity metrics, such as the diversity of dependency trees or part-of-speech tag sequences [29] [30].
- For academic texts, analyze citation patterns and technical jargon specific to the field, which AI may struggle to replicate authentically.
- Calibrate Decision Thresholds: Creative human text may have stylistic patterns that overlap with AI "perfection," such as high grammar correctness. Adjust your model's classification threshold to reduce false positives in these edge cases [33].
Verification Test the refined detector on a curated dataset of human-written creative/academic texts and AI-generated texts mimicking that domain. Monitor the reduction in false positives while maintaining a high detection rate.
Quantitative Data on Linguistic Features
Table 1: Common Stylometric Features for AI Text Detection
| Feature Category | Specific Examples | Function in Detection |
|---|---|---|
| Punctuation Patterns | Use of final periods, exclamation points, ellipses, em dashes [28] [33] [36] | Signals tone and formality; AI often uses punctuation grammatically, while humans use it rhetorically. |
| Overused Phrases & Words | "delve", "tapestry", "pivotal", "underscore", "realm", "In conclusion" [27] [33] | Acts as a fingerprint; AI leans on predictable, formal vocabulary and transition phrases. |
| Lexical Diversity | MTLD, vocd-D scores [35] [29] | Measures vocabulary richness; AI text typically has lower diversity due to pattern homogenization. |
| Syntactic Diversity | Diversity of dependency trees, part-of-speech (POS) n-grams [29] [30] | Measures sentence structure variation; AI output is often less syntactically diverse. |
| Grammatical Perfectness | Adherence to formal grammar, use of Oxford comma, avoidance of fragments [33] | Serves as a signal; AI text is often "too perfect," while human writing contains occasional informal constructs. |
Table 2: Benchmarking Linguistic Diversity in LLMs vs. Humans (Sample Findings) [29]
| Model / Source | Lexical Diversity (MTLD) | Syntactic Diversity (Dependency Tree Edit Distance) | Semantic Diversity |
|---|---|---|---|
| Human-Written Text | 110.5 | 0.89 | 0.75 |
| LLM A (SOTA) | 95.2 | 0.81 | 0.72 |
| LLM B (Base) | 87.6 | 0.76 | 0.68 |
| LLM A (after Preference Tuning) | 84.3 | 0.71 | 0.65 |
Experimental Protocols
Protocol 1: Building a Transferable Stylometric Detector
Objective: To create an AI-generated text detector that maintains performance across different LLMs and writing domains.
Methodology:
- Data Collection & Preprocessing:
- Source Data: Collect a large, diverse corpus of text generated from various base LLMs (e.g., GPT-3, BLOOM, Jurassic-1). Collect a comparable human text corpus from similar domains (e.g., news, essays) [29].
- Text Representation: Convert all texts into a vector of stylometric features. Essential features include:
- Base Model Pre-training:
- Train a supervised classifier (e.g., SVM, Logistic Regression, or a simple neural network) on the source dataset to distinguish human from AI text. This establishes your base detector [30].
- Transfer Learning via Fine-Tuning:
- Target Data: Obtain a smaller dataset of text from a new, target LLM (e.g., a newly released model) with human comparisons.
- Inductive Transfer: Use the pre-trained base detector as a starting point. Fine-tune its final layers on the target dataset. This allows the model to adapt its learned feature representations to the new model's output style [31] [32] [34].
- Evaluation:
- Evaluate the fine-tuned model on a held-out test set of the target LLM's text.
- Compare its performance (Accuracy, F1-score) against a model trained from scratch only on the target data to demonstrate the benefit of transfer learning.
The workflow for this protocol can be summarized as follows:
Protocol 2: Quantifying the Impact of Preference Tuning on Linguistic Diversity
Objective: To empirically measure how reinforcement learning from human feedback (RLHF) or other preference tuning reduces linguistic diversity in LLMs.
Methodology:
- Model Selection: Select an open-source LLM that provides both a base pre-trained checkpoint and a preference-tuned checkpoint (e.g., from Hugging Face).
- Text Generation: For both the base and tuned models, generate a large corpus of text (e.g., 1000 samples) using a diverse set of prompts designed to elicit creative and informative responses [29].
- Diversity Calculation: For each generated corpus, calculate the following metrics:
- Lexical Diversity: Using the MTLD (Measure of Textual Lexical Diversity) metric, which is more reliable than simple type-token ratios [35] [29].
- Syntactic Diversity: Calculate the mean edit distance between the dependency trees of randomly sampled sentence pairs from the corpus [29].
- Semantic Diversity: Compute the average pairwise cosine similarity of Sentence-BERT embeddings for all generated responses [29].
- Statistical Analysis: Perform a t-test or similar statistical analysis to determine if the differences in diversity scores between the base and tuned models are significant. The hypothesis is that tuned models will show a statistically significant reduction in all three diversity measures.
The logical flow of this analysis is:
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for Stylometric Analysis of AI-Generated Text
| Tool / Resource | Type | Function in Experiment |
|---|---|---|
| Text Inspector | Software Tool | Provides professional analysis of key linguistic features, including reliable lexical diversity (MTLD, vocd-D) metrics [35]. |
| LIWC (Linguistic Inquiry and Word Count) | Software Tool | Analyzes psychological and linguistic features in text, useful for extracting function word frequencies and stylistic markers [30]. |
| SpaCy | NLP Library | Used for advanced text preprocessing, including tokenization, part-of-speech (POS) tagging, and dependency parsing to extract syntactic features [29] [30]. |
| Sentence-BERT | NLP Model | Generates semantically meaningful sentence embeddings, which are essential for computing semantic diversity and similarity scores [29]. |
| Hugging Face Transformers | Model Repository | Provides access to a vast array of pre-trained LLMs for generating text corpora and for fine-tuning transfer learning detectors [32] [34]. |
| scikit-learn | Machine Learning Library | Offers implementations of standard classifiers (SVM, Logistic Regression) and tools for feature extraction and model evaluation [30]. |
Incorporating Structural and Semantic Features for Robustness
Frequently Asked Questions (FAQs)
Q1: What are the most significant challenges to the robustness of AI-generated text detectors? A1: Detector robustness is primarily challenged by three factors: (1) Text perturbations, including character/word-level edits and paraphrasing, which deceive detectors with human-imperceptible changes [37]; (2) Out-of-distribution (OOD) data, such as text from unseen domains, languages, or LLMs, where training and test data distributions differ [37]; (3) AI–human hybrid text (AHT), which is prevalent in real-world usage but poorly handled by detectors designed for purely AI-generated content [37].
Q2: What baseline performance can be expected for AI-generated text detection and model attribution? A2: Established baselines on a comprehensive dataset of over 58,000 texts show 58.35% accuracy for human vs. AI binary classification and 8.92% accuracy for attributing AI text to specific generating models (including Gemma-2-9b, Mistral-7B, Qwen-2-72B, LLaMA-8B, Yi-Large, GPT-4-o) [38]. This highlights the significant challenge of reliable detection and attribution.
Q3: Which architectural approach has demonstrated high performance in detection? A3: A hybrid CNN-BiLSTM model with feature fusion has demonstrated superior performance, achieving 95.4% accuracy, 94.8% precision, 94.1% recall, and a 96.7% F1-score. This architecture integrates BERT-based semantic embeddings, Text-CNN features, and statistical descriptors to capture both local syntactic patterns and long-range semantic dependencies [39].
Q4: Are there publicly available datasets for benchmarking detector robustness? A4: Yes, several benchmark datasets support robustness research. Key examples include:
- RAID: Over 6 million texts from 11 LLMs across 8 domains [38].
- M4: A multi-generator, multi-domain, multi-lingual dataset covering 7 languages [38].
- HC3: A large-scale human-ChatGPT comparison corpus across multiple domains [38].
- LLM-DetectAIve: 236,000 examples with fine-grained labels for machine-humanized and human-polished texts [38].
Troubleshooting Guides
Issue 1: Performance Degradation Under Text Perturbation
Symptoms: Detector accuracy drops significantly when input text undergoes minor modifications like synonym replacement, paraphrasing, or character-level alterations.
Investigation & Resolution Protocol:
- Characterize Perturbation: Profile the perturbation type (e.g., character-level, word-level, semantic paraphrase) using available libraries [37].
- Implement Adversarial Training: Retrain the detector using a data augmentation strategy that incorporates perturbed examples during the training phase. This exposes the model to potential attack vectors and improves resilience [37].
- Evaluate Robustness: Measure performance on a dedicated benchmark dataset containing perturbed texts, such as one focused on paraphrase robustness [37]. Compare metrics (see Table 1) before and after implementing adversarial training.
Issue 2: Poor Generalization to Out-of-Distribution (OOD) Data
Symptoms: The detector performs well on its original test set but fails on text from new domains, different languages, or generated by unseen LLMs.
Investigation & Resolution Protocol:
- Identify Distribution Shift: Analyze the feature space to confirm the data (e.g., new domain, new LLM) is OOD relative to the training set [37].
- Leverage Domain Adaptation: Apply techniques like domain-adversarial training (DANN) or multi-task learning on datasets encompassing multiple domains and languages (e.g., M4 dataset) [38] [37].
- Stress-Test Systematically: Evaluate the retrained model on a curated OOD benchmark. Monitor key metrics across different data segments to identify remaining weaknesses.
Issue 3: Inability to Detect AI-Human Hybrid Text (AHT)
Symptoms: The detector correctly identifies purely AI-generated content but fails on texts that have been partially modified or polished by humans, which is common in real-world scenarios.
Investigation & Resolution Protocol:
- Acquire Specialized Data: Train and evaluate the model on datasets specifically containing AHT, such as FAIDSet (multilingual, diverse human-LLM collaboration) or LLM-DetectAIve (includes human-polished texts) [38] [37].
- Focus on Localized Features: Adapt the model architecture to analyze text at a more granular, sentence or paragraph level, rather than solely relying on document-level features, to identify pockets of AI-generated content within a human-written framework [37].
- Validate on Realistic Data: Test the final model on a hold-out set of AHT to ensure improvements generalize beyond the original training data.
Experimental Data & Protocols
Table 1: Performance Metrics of AI-Generated Text Detectors
| Model / Detector | Accuracy (%) | Precision (%) | Recall (%) | F1-Score (%) | Notes |
|---|---|---|---|---|---|
| Baseline (Binary Classification) [38] | 58.35 | - | - | - | Human vs. AI on NYT-based dataset |
| Baseline (Model Attribution) [38] | 8.92 | - | - | - | Attributing to 1 of 6 specific LLMs |
| Hybrid CNN-BiLSTM with Feature Fusion [39] | 95.4 | 94.8 | 94.1 | 96.7 | Integrated BERT, Text-CNN, statistical features |
Table 2: Categorization of Robustness Challenges and Enhancement Methods
| Robustness Category | Key Challenges | Exemplar Enhancement Methods |
|---|---|---|
| Text Perturbation Robustness [37] | Paraphrasing, adversarial attacks, character/word-level perturbations | Adversarial training, perturbation-based data augmentation |
| Out-of-Distribution (OOD) Robustness [37] | Cross-domain, cross-lingual, cross-LLM generalization | Domain adaptation, multi-task learning, style randomization |
| AI-Human Hybrid Text (AHT) Detection [37] | Partial AI generation, human polishing, collaborative authorship | Sentence-level detection, datasets with fine-grained AHT labels |
Detailed Experimental Methodology
Protocol 1: Implementing a Hybrid CNN-BiLSTM Detector with Feature Fusion
Objective: Reproduce high-accuracy detection by integrating diverse textual features [39].
Workflow:
- Feature Extraction:
- Semantic Embeddings: Generate contextualized embeddings for the input text using a pre-trained BERT model [39].
- Local Syntactic Features: Process the text through a Text-CNN with multiple filter sizes to capture n-gram patterns and local dependencies [39].
- Statistical Descriptors: Calculate statistical features (e.g., entropy, log-probability, syntactic complexity metrics) from the text [39].
- Feature Fusion: Concatenate the feature vectors from the three stages above into a unified representation [39].
- Classification: Feed the fused feature vector into a Bidirectional LSTM (BiLSTM) to model long-range contextual dependencies, followed by a final classification layer (e.g., softmax) for the human/AI decision [39].
Diagram Title: Hybrid CNN-BiLSTM Detection Workflow
Protocol 2: Evaluating Robustness to Text Perturbations
Objective: Systematically assess and improve detector resilience against textual modifications [37].
Workflow:
- Baseline Performance: Evaluate the detector on a clean, unperturbed test set to establish baseline metrics.
- Perturbation Generation: Create a perturbed version of the test set by applying various techniques:
- Character-level: Random insertions, deletions, swaps.
- Word-level: Synonym replacement using WordNet or BERT-based substitutions.
- Sentence-level: Paraphrasing using back-translation or T5 models [37].
- Robustness Assessment: Run the detector on the perturbed test set and calculate the performance drop compared to the baseline.
- Robustness Enhancement: Apply adversarial training by incorporating perturbed examples into the training data and retrain the model [37].
Diagram Title: Perturbation Robustness Evaluation Protocol
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Datasets for Robustness Research
| Dataset Name | Function / Utility | Key Characteristics |
|---|---|---|
| RAID [38] | Largest benchmark for stress-testing detectors under diverse conditions. | >6 million texts, 11 LLMs, 8 domains. |
| M4 [38] | Evaluating cross-lingual and cross-domain robustness. | Multi-lingual coverage (7 languages), multi-generator. |
| HC3 [38] | Benchmarking against a widely-used commercial LLM (ChatGPT). | Human vs. ChatGPT comparisons across finance, medicine, etc. |
| LLM-DetectAIve [38] | Developing detectors for human-polished and hybrid text. | 236k examples, fine-grained labels for humanized AI text. |
| FAIDSet [38] | Training models to recognize collaborative human-AI authorship. | 84k texts, multilingual, diverse collaboration forms. |
Table 4: Key Software Tools and Models
| Tool / Model | Function / Utility | Application Context |
|---|---|---|
| Pre-trained LMs (BERT, RoBERTa) [37] [39] | Foundation for training-based detectors; provides rich semantic features. | Fine-tuning on AIGT detection datasets. |
| Zero-shot Detectors (DetectGPT, Entropy) [37] | Provides a training-free baseline; useful for black-box detection. | Leveraging statistical features like log-likelihood, entropy. |
| Adversarial Training Frameworks [37] | Enhances model resilience against intentional attacks and perturbations. | Incorporating perturbed examples into training loops. |
| Text Perturbation Libraries | Generates controlled perturbations for robustness testing and data augmentation. | Creating character/word-level edits and paraphrases. |
The rapid advancement of Large Language Models (LLMs) has created an urgent need for reliable detection of AI-generated text, particularly in high-stakes domains like scientific research and drug development [40]. This technical support center document focuses on two key information-theoretic features—Uniform Information Density (UID) and Perplexity—that form the foundation for developing transferable supervised detectors. These features quantify fundamental statistical properties of text that can distinguish between human and machine-generated content, even as generation models evolve [41].
The detection of AI-generated text has become increasingly challenging as models like GPT-4 produce more human-like content, creating a perpetual arms race between generation and detection technologies [40]. Within this context, information-theoretic approaches offer promising avenues for creating more robust detectors that can generalize across domains and adapt to new generation models, addressing critical knowledge gaps in cross-domain generalization and adversarial robustness [40].
Theoretical Foundations
Uniform Information Density (UID)
The Uniform Information Density hypothesis is a theoretical framework in linguistics and cognitive science that posits that information tends to be distributed evenly across a discourse or text [42]. This principle suggests that language users instinctively structure their communication to maintain a consistent level of information density, which facilitates comprehension and processing efficiency [43] [42].
From a computational perspective, UID operationalizes this hypothesis by measuring how uniformly information (typically quantified as surprisal) is distributed across linguistic signals [43]. Research has demonstrated that deviations from uniform information density can predict lower acceptability judgments in human evaluators, making it a valuable feature for identifying machine-generated text that may exhibit abnormal patterns of information distribution [43].
Perplexity
Perplexity is a fundamental metric in information theory that quantifies how well a probability model predicts a sample [44] [45]. In the context of language models, it measures the uncertainty a model experiences when predicting the next token in a sequence [45]. Lower perplexity indicates that the model is more confident in its predictions, while higher perplexity suggests greater uncertainty [45].
Mathematically, perplexity is defined as the exponentiated average negative log-likelihood of a sequence of tokens:
[ \text{Perplexity}(W) = \exp\left(-\frac{1}{N}\sum{i=1}^N \ln P(wi | w1, w2, ..., w_{i-1})\right) ]
Where (W) is the sequence of words (w1, w2, ..., w_N). Perplexity can be interpreted as the weighted average branching factor—a model with perplexity (k) can be seen as being as uncertain as if it were choosing between (k) equally likely options at each step [44].
Experimental Protocols and Methodologies
Measuring UID in Text
Objective: Quantify the uniformity of information distribution in a given text sample.
Materials: Text corpus, computational resources for probability estimation, UID calculation script.
Procedure:
Text Preprocessing: Segment the input text into appropriate linguistic units (words, subwords, or characters depending on the research design).
Surprisal Calculation: For each unit in the sequence, compute the surprisal as (-\log P(wi|w{1:i-1})) using a baseline language model.
UID Operationalization: Calculate one or more of the following UID measures:
- Variance of Surprisal: Compute the variance of surprisal values across the sequence. Lower variance indicates greater uniformity.
- UID Deviation Score: Calculate the absolute difference between local surprisal and the global average.
- Regression-Based Measures: Fit a linear model predicting surprisal from position and use residuals as non-uniformity indicators.
Statistical Analysis: Compare UID measures between human-written and AI-generated text samples using appropriate statistical tests.
Troubleshooting Tips:
- If UID values show no discriminative power, try different baseline language models for surprisal calculation.
- For short texts, consider using smoother probability estimates or Bayesian shrinkage methods.
- If computational resources are limited, focus on key segments of text rather than full documents.
Calculating Perplexity
Objective: Measure how well a given language model predicts a target text sequence.
Materials: Target text corpus, trained language model, perplexity calculation script.
Procedure:
Model Selection: Choose an appropriate language model for evaluation. For AI detection, this may include:
- General-purpose LLMs (GPT, LLaMA, etc.)
- Domain-specific models for scientific text
- Ensemble of models for robust estimation
Probability Estimation: For each token in the evaluation text, compute the conditional probability given previous context.
Perplexity Computation: Calculate perplexity using the standard formula: [ \text{PPL}(W) = \exp\left(-\frac{1}{N}\sum{i=1}^N \log P(wi | w_{1:i-1})\right) ]
Normalization: For fair comparison across texts of different lengths, ensure proper normalization and handling of special tokens.
Analysis: Compare perplexity distributions between known human and AI-generated texts to establish detection thresholds.
Troubleshooting Tips:
- If perplexity values are consistently too high, check for domain mismatch between evaluation text and training data of the model.
- For unstable perplexity estimates, increase text sample size or use smoothing techniques.
- If perplexity fails to discriminate, try conditional perplexity on specific syntactic constructions or discourse markers.
Integrated Detection Framework
Objective: Combine UID and perplexity features to build a robust AI-generated text detector.
Materials: Labeled dataset of human and AI-generated texts, feature extraction pipeline, machine learning classifier.
Procedure:
Feature Extraction:
- Compute UID measures for each text sample
- Calculate perplexity using multiple baseline models
- Extract additional linguistic features (optional)
Classifier Training:
- Split data into training, validation, and test sets
- Train supervised classifier (e.g., SVM, Random Forest, or Neural Network)
- Optimize hyperparameters using validation set
Evaluation:
- Assess performance on held-out test set
- Evaluate cross-domain generalization using out-of-distribution datasets
- Test adversarial robustness against paraphrased AI text
Deployment:
- Implement detection pipeline with feature extraction and classification
- Establish confidence thresholds for reliable detection
- Implement continuous monitoring and model updating mechanism
Key Research Reagent Solutions
Table 1: Essential Research Materials for AI Text Detection Experiments
| Reagent/Material | Function/Application | Example Sources/Tools |
|---|---|---|
| Language Models | Baseline for perplexity calculation and surprisal estimation | GPT family, LLaMA, BERT, domain-specific models |
| Labeled Datasets | Training and evaluation of detection models | HC3, GPT-2 Output Dataset, REALY, M4 [40] |
| Text Preprocessing Tools | Tokenization, normalization, and segmentation | spaCy, NLTK, Hugging Face Tokenizers |
| UID Calculation Scripts | Implement UID operationalization measures | Custom Python implementations based on research papers |
| Perplexity Implementation | Compute perplexity across different models | Hugging Face Evaluate, custom PyTorch/TensorFlow code |
| Detection Frameworks | End-to-end AI text detection systems | OpenAI Detector, GPTZero, GLTR, Custom classifiers |
| Evaluation Metrics | Assess detection performance | Accuracy, F1-score, AUC, False Positive Rate [40] |
Frequently Asked Questions (FAQs)
Q1: How do UID and perplexity complement each other in AI text detection?
UID and perplexity capture different but complementary aspects of text generation. Perplexity measures overall predictability of text, while UID quantifies how evenly information is distributed throughout the text. AI-generated texts often exhibit abnormal patterns in both measures—sometimes with deceptively low perplexity (high confidence) but non-uniform information density that reveals their artificial origin. Combining these features provides a more robust detection signal than either feature alone.
Q2: What are the main limitations of UID for detecting modern LLM-generated text?
Modern LLMs are increasingly trained to approximate human-like information density patterns, making UID-based detection more challenging. The main limitations include: (1) the need for appropriate baseline models for surprisal calculation, (2) sensitivity to text length and domain, and (3) the ability of advanced LLMs to consciously maintain uniform information density. These limitations necessitate continuous updating of detection methods and combination with other features.
Q3: How can I address domain shift when applying these methods to scientific or drug development texts?
Domain shift is a significant challenge in specialized domains. Recommended approaches include: (1) using domain-specific language models for feature calculation, (2) fine-tuning detection models on in-domain examples, (3) incorporating domain-aware preprocessing (e.g., handling technical terminology), and (4) using ensemble methods that combine general and domain-specific features. Transfer learning from general to scientific domains has shown promise in addressing this challenge.
Q4: What ethical considerations should I be aware of when deploying these detection methods?
Key ethical considerations include: (1) potential biases against non-native English speakers [46], (2) transparency in detection methodology and confidence scores, (3) allowing for human appeal processes, and (4) regular auditing for fairness and accuracy. No detection system is perfect, so they should be used as advisory tools rather than definitive arbiters, especially in high-stakes scenarios like academic evaluation or drug development research.
Q5: How can I improve the adversarial robustness of UID and perplexity-based detectors?
Adversarial robustness can be improved through: (1) training on paraphrased and perturbed AI-generated texts, (2) using ensemble methods that combine multiple features and models, (3) implementing detection methods that are less reliant on surface-level patterns, and (4) continuously updating detection models as new generation techniques emerge. Research suggests that information-theoretic features like UID may be more robust to simple paraphrasing attacks than surface-pattern features.
Visualization of Methodologies
Information-Theoretic Feature Extraction Workflow
Theoretical Framework for AI Text Detection
Quantitative Reference Data
Table 2: Performance Benchmarks of Information-Theoretic Features in AI Text Detection
| Detection Method | Feature Combination | Reported Accuracy | F1-Score | False Positive Rate | Domain Generalization |
|---|---|---|---|---|---|
| UID-Only | Surprisal variance + regression residuals | 68-72% | 0.70-0.74 | 12-15% | Moderate |
| Perplexity-Only | Multi-model perplexity | 74-78% | 0.75-0.79 | 8-11% | Variable |
| UID + Perplexity | Combined feature set | 82-86% | 0.83-0.87 | 5-7% | Good |
| Ensemble Methods | With linguistic features | 88-92% | 0.89-0.93 | 3-5% | Better |
Table 3: Typical Value Ranges for UID and Perplexity Across Text Types
| Text Type | UID Variance Range | Perplexity Range | Characteristic Patterns |
|---|---|---|---|
| Human Scientific | Medium (0.8-1.2) | Medium-High (50-100) | Moderate uniformity, domain-specific variations |
| AI-Generated Scientific | Low-High (0.5-2.0) | Low (30-70) | Irregular patterns, sometimes overly uniform |
| Human News | Low (0.7-1.0) | Low-Medium (40-80) | High uniformity, consistent style |
| AI-Generated News | Medium (0.9-1.3) | Very Low (20-50) | Overly predictable, abnormal consistency |
Energy-Based Models (EBMs) for Distinguishing Human and AI Text
Your Technical Support Center
This resource provides targeted troubleshooting guides and FAQs for researchers applying Energy-Based Models (EBMs) to distinguish between human and AI-generated text.
Frequently Asked Questions (FAQs)
Q1: What makes EBMs a promising approach for AI-text detection compared to traditional classifiers? EBMs learn a scalar energy function that measures compatibility between an input and a potential output. For AI-text detection, this allows the model to learn the underlying distribution of human-like text, assigning lower energy to human-written text and higher energy to AI-generated content. This provides a more fundamental understanding of the data distribution compared to classifiers that may learn surface-level features, potentially improving generalization and transferability to new AI models [47] [48].
Q2: During training, my EBM's loss becomes highly negative. What is the likely cause and how can I address this? A sharply negative training loss often indicates the model is finding a "trivial solution" by assigning low energy to all inputs, effectively collapsing the energy landscape [47].
- Solution: Implement or strengthen your energy regularization term (e.g., as proposed by Song & Ermon, 2019). This penalty discourages the model from producing arbitrarily low energy values [47]. Furthermore, consider reducing model capacity and using a higher learning rate to prevent the model from overfitting and memorizing the training data [47].
Q3: My EBM for text performs well on training data but fails on out-of-distribution (OOD) or slightly modified AI text. How can I improve its robustness? This is a sign of overfitting and a lack of generalization.
- Solution: Incorporate adversarial examples into your training. This technique, as seen in adversarial paraphrasing attacks, uses a detector-guided LLM to create hard negatives that are human-like but AI-generated [49]. Training your EBM to assign high energy to these adversarial examples can significantly improve its robustness and transferability to unseen AI models [49].
Q4: What is "System 2 Thinking" in the context of EBMs like the Energy-Based Transformer (EBT), and how does it benefit detection? System 2 Thinking refers to slow, deliberate, and analytical reasoning [50]. In EBTs, this manifests as dynamic computation allocation during inference. The model can perform iterative gradient-based steps to minimize the energy for a given input-output pair [50] [51]. For detection, this means the model can "think longer" about more challenging or OOD text samples, refining its energy assignment and leading to more accurate verification, especially on complex cases [50].
Troubleshooting Guides
Issue: Model Failure on Adversarially Paraphrased AI Text
Problem: Your trained EBM detector is easily fooled by AI-generated text that has been paraphrased by another LLM to evade detection.
Diagnosis: The detector likely relies on superficial statistical artifacts instead of learning the core distribution of human-authored text.
Resolution: Adversarial Training Protocol Follow this detailed methodology to enhance model robustness [49]:
Adversarial Example Generation:
- Tool: Use an instruction-tuned LLM (e.g., LLaMA-3-8B) as a paraphraser.
- Guidance: Employ an existing AI-text detector (e.g., a fine-tuned RoBERTa-large) as a guide.
- Method: For each AI-generated text in your training batch, use the guided paraphraser to generate adversarial examples. The guide detector scores candidate tokens, steering the paraphraser to produce output that is classified as "human-like." This creates robust hard negatives [49].
Enhanced EBM Training Loop:
- Integrate these adversarial examples into your training batches as high-energy targets.
- The loss function should strongly penalize the model when it assigns low energy to these adversarial samples.
Visualization of the Adversarial Training Workflow:
Issue: Unstable Training and Mode Collapse
Problem: Training loss is volatile, and the model fails to learn a meaningful energy landscape, often assigning uniformly high or low energy.
Diagnosis: Common challenges in EBM training include vanishing gradients and difficulties with the partition function estimation [47] [50].
Resolution: Stabilized Training Protocol This protocol combines architectural and optimization strategies [47].
Architectural Adjustments:
- Reduce Capacity: Limit the number of filters and neurons to prevent overfitting and memorization.
- Add Normalization: Use Batch Normalization layers to stabilize activations and improve gradient flow.
- Activation Functions: Employ a mix of ReLU and sigmoid activations to balance expressiveness and stability [47].
Regularization Strategy:
- Apply energy regularization to explicitly penalize overly negative energy values [47].
- Use standard techniques like weight decay and dropout.
Optimization Configuration:
- Optimizer: Use the Adam optimizer for adaptive learning rates.
- Learning Rate: Carefully tune the learning rate; a rate that is too high can cause divergence, while one that is too low leads to slow convergence or stagnation [47].
- Scheduling: Implement a learning rate scheduler to reduce the rate as training progresses.
Visualization of the Stabilized EBM Training Architecture:
Performance Data & Experimental Protocols
Table 1: CIFAR-10 EBM Training Results with Anti-Overfitting Modifications
This table demonstrates the impact of architectural and regularization changes on final loss values, showcasing the mitigation of overfitting. [47]
| Model Configuration | Final Training Loss | Final Eval Loss | Notes |
|---|---|---|---|
| Base Model | -30.8599 | -34.9541 | Suggests severe overfitting (eval loss << train loss) |
| With Modifications (Reduced capacity, Dropout, Stronger regularization, LR scheduling, Data augmentation) | 0.0031 | 0.0023 | Eval loss closely matches training loss, indicating controlled overfitting |
Table 2: AI Text Detector Performance Under Attack
This table illustrates the vulnerability of existing detectors to simple and adversarial paraphrasing attacks, measured by the reduction in True Positive Rate at 1% False Positive Rate (T@1%F). A larger reduction indicates a more successful attack. [49]
| Detection System | Simple Paraphrasing Attack (Δ T@1%F) | Adversarial Paraphrasing Attack (Δ T@1%F) |
|---|---|---|
| RADAR | +8.57% | -64.49% |
| Fast-DetectGPT | +15.03% | -98.96% |
Experimental Protocol: EBM Training for Text Detection
- Model Selection: Choose a backbone architecture. The Energy-Based Transformer (EBT) is a modern, scalable choice that supports dynamic computation [50]. Alternatively, a Residual EBM built on a pre-trained language model can be effective [52].
- Data Preparation: Curate a dataset of human-written and AI-generated text pairs. Use multiple AI models (e.g., GPT, Gemini, LLaMA) for generation to ensure diversity. Split data into training, validation, and testing sets.
- Preprocessing: Tokenize the text using an appropriate tokenizer for your backbone model (e.g., WordPiece for BERT-based models, SentencePiece for others).
- Training Loop:
- For each (text, label) pair, the EBM learns to assign low energy to "Human" and high energy to "AI".
- Use a contrastive loss (e.g., Noise Contrastive Estimation) to make the energy of positive examples (human text) lower than that of negative examples (AI text) [52].
- Incorporate adversarial examples generated using the protocol above as negative examples.
- Apply energy regularization to prevent model collapse.
- Inference: For a new text sample, the EBM computes its energy. A threshold can then be applied to classify it as human or AI-generated. EBTs allow for iterative refinement of this energy via gradient steps for uncertain samples [50].
The Scientist's Toolkit
Table 3: Essential Research Reagents & Solutions
| Item | Function in EBM Research for AI Text |
|---|---|
| Pre-trained Language Models (e.g., BERT, RoBERTa, GPT-2) | Serve as a foundational backbone for building Residual EBMs or for extracting contextual text representations, providing a strong prior for the data distribution [52]. |
| Instruction-Tuned LLMs (e.g., LLaMA-3-8B) | Act as a controllable paraphraser for generating adversarial examples to improve detector robustness during training [49]. |
| Contrastive Loss Functions (e.g., NCE, InfoNCE) | Enable stable EBM training by learning the energy function through comparison of positive and negative data samples, circumventing the need to compute the intractable partition function directly [52]. |
| Energy Regularization Term | A critical penalty added to the loss function to prevent the EBM from collapsing by assigning low energy to all possible inputs, thus maintaining a meaningful energy landscape [47]. |
| Gradient-Based Optimizers (e.g., Adam) | The standard algorithm for parameter updates during EBM training, chosen for its adaptive learning rates which help navigate complex loss landscapes [47]. |
Domain-Invariant Training with Topological Data Analysis (TDA)
Frequently Asked Questions
Q1: What is the primary advantage of using TDA for domain-invariant feature extraction? TDA, particularly through persistent homology, extracts robust topological features (e.g., connected components, loops, voids) that are intrinsic to the data's shape. These features are often stable across domains because they capture the underlying geometric structure, which can be more consistent than feature distributions affected by domain shift. This makes them highly valuable for creating domain-invariant representations [53] [54].
Q2: My model suffers from negative transfer when a source domain is too dissimilar from the target. How can TDA help? A framework like the Hard-Easy Dual Network (HEDN) can be adapted. It uses a Task Difficulty Assessment (TDA) mechanism to dynamically route source domains to different processing pathways. "Hard" sources with high transfer difficulty are handled by a network focused on marginal distribution alignment, while "Easy" sources leverage structural, prototype-based learning, thus mitigating negative transfer [55].
Q3: How can I generate reliable pseudo-labels for an unlabeled target domain in text data? A prototype-guided label propagation algorithm can be employed. This involves using TDA-aware prototype learning to capture the intra-class clustering structure of "Easy" source domains. These prototypes are then used to assign pseudo-labels to target domain samples based on their proximity in the topological feature space, enhancing the reliability of the labels [55].
Q4: What is a common pitfall when applying persistent homology to text embeddings, and how can it be avoided? A common pitfall is using a single, fixed scale (epsilon) for constructing the simplicial complex, which may not capture the multi-scale topological structure of the data. The solution is to use persistent homology, which tracks topological features across a range of scales, summarizing the output in a persistence diagram or image that is used for downstream models [56] [53].
Troubleshooting Guides
Issue 1: Poor Generalization on Out-of-Distribution (OOD) Text Data
Problem: Your AI-generated text detector performs well on its training domain but fails to generalize to new, unseen domains or writing styles.
Solution: Integrate topological features into your domain-invariant learning objective.
- Step 1: Feature Extraction. Convert your text samples (from both source and target domains) into numerical representations. You can use:
- Step 2: Topological Feature Calculation. For each sample's representation (treated as a point cloud), compute its persistent homology. Use a library like
giotto-tda. The output will be persistence diagrams for different dimensions (0 for components, 1 for loops, etc.) [53] [54]. - Step 3: Create Persistence Images. Convert the persistence diagrams into a fixed-sized vector representation called a persistence image. This makes them suitable for machine learning models [56] [53].
- Step 4: Model Integration. Combine the topological features with standard features.
Verification: Check if the model's accuracy on a held-out target domain validation set improves after incorporating topological features and the adaptation loss.
Issue 2: Instability in Training Due to Noisy Pseudo-Labels
Problem: The pseudo-labels generated for the unlabeled target domain are too noisy, causing the model training to diverge or perform poorly.
Solution: Implement a structure-aware, prototype-based learning strategy.
- Step 1: Prototype Calculation. For each class in the labeled source domain, compute a prototype. This is typically the mean vector of all the feature representations (standard + topological) belonging to that class [55].
- Step 2: Prototype Refinement. Use a label propagation algorithm on a graph built from the target domain data. The prototypes from the source domain serve as anchors to guide the propagation, generating more robust pseudo-labels for the target samples [55].
- Step 3: Confidence-Based Filtering. Only retain pseudo-labels for target samples where the model's confidence (e.g., softmax probability or distance to a prototype) exceeds a high threshold. Iteratively refine this process during training [55].
Verification: Monitor the ratio of target samples with high-confidence pseudo-labels over training epochs. A stable or increasing trend indicates effective learning.
Experimental Protocols & Data
Protocol 1: Benchmarking TDA Features for AI-Generated Text Detection
Objective: Quantify the performance gain from using TDA features in a cross-domain setting.
- Datasets: Use a mix of human-written and AI-generated text from different sources (e.g., ChatGPT, GPT-4, Llama) and different domains (news, social media, academic abstracts) [56] [59].
- Feature Extraction:
- Baseline: Train a classifier using only standard features (e.g., BERT embeddings, linguistic features).
- TDA-Augmented: Train a classifier using a combination of standard features and topological features (persistence images).
- Training/Testing: Train all models on a single source domain and test on multiple held-out target domains to evaluate OOD generalization.
- Metrics: Report accuracy, F1-score, and Area Under the ROC Curve (AUC-ROC).
Summary of Quantitative Results from Literature:
| Model / Approach | Standard Features Only (Accuracy) | Standard + TDA Features (Accuracy) | Notes |
|---|---|---|---|
| LSTM + TDA [56] | ~89% | ~94% | Classification of AI vs. Human text |
| Topological Papillae Classifier [54] | (Baseline features) | ~85% | Demonstrates TDA's power on non-text 3D data |
| Domain Adaptation (General) | Varies significantly by method and dataset. The key finding is that incorporating TDA features typically leads to a performance improvement on out-of-distribution data by capturing stable, structural information [55] [53]. |
Protocol 2: Evaluating Domain-Invariant Subspace Learning
Objective: Learn a feature subspace where source and target domains are aligned.
- Method: Implement a model like TDACNN, which uses a MMD loss for domain alignment, but adapt it for text by using a 1D convolutional or transformer backbone [58].
- Integration: The MMD loss is computed between the deep feature representations of the source and target batches, encouraging the network to learn features that are invariant to the domain shift.
- Evaluation: Compare the MMD distance between source and target features before and after training. A lower MMD indicates better domain alignment.
The Scientist's Toolkit: Research Reagent Solutions
| Item | Function in Domain-Invariant TDA |
|---|---|
| giotto-tda | A high-level Python library for topological data analysis. It provides tools for computing persistent homology, creating persistence images, and integrating with scikit-learn [57]. |
| Persistent Homology | The core TDA technique used to compute multi-scale topological features (connected components, loops, cavities) from point cloud data like text embeddings [53] [54]. |
| Persistence Images | A stable vector representation of a persistence diagram. It converts topological features into a format suitable for standard machine learning models [56]. |
| Mapper Algorithm | A topological visualization technique that can provide insights into the global structure of your data and help identify clusters or outliers across domains [60] [53]. |
| Maximum Mean Discrepancy (MMD) | A kernel-based statistical test used as a loss function in domain adaptation to measure and minimize the distribution difference between source and target domains in a learned feature space [55] [58]. |
| Domain-Adversarial Neural Network (DANN) | An alternative to MMD that uses a domain classifier to make features domain-indiscriminate through adversarial training. Can be combined with topological features [55]. |
Workflow Visualization
Domain-Invariant Feature Extraction with TDA
Topological Feature Extraction via Persistent Homology
Applying Transfer Learning Principles from Network Intrusion Detection
Troubleshooting Guides and FAQs for Researchers
This technical support center provides practical guidance for researchers and scientists applying transfer learning methodologies from Network Intrusion Detection Systems (NIDS) to the domain of AI-generated text detection. The content supports experimental work within the broader thesis context of improving transferable supervised detectors.
Core Troubleshooting Guides
Guide 1: Addressing Data Imbalance in Rare Class Detection
- Problem Statement: My transfer learning model fails to detect rare or novel classes of AI-generated text, despite good performance on common classes.
- Root Cause: High class imbalance in the source (NIDS) or target (AI-text) dataset can cause model bias toward majority classes [61].
- Solution Methodology:
- Implement Adaptive, Personalized Layers: Integrate client-specific layers in your federated learning framework to tailor feature extraction for local, rare-class data distributions [61].
- Apply Synthetic Data Generation: Use techniques like the Synthetic Minority Oversampling Technique (SMOTE) on the feature representations to balance abnormal traffic (or, by analogy, rare text types) and improve detection of minority attacks [62].
- Leverage Threshold-Based Detection: For zero-day (previously unseen) attacks or text types, employ a dynamic thresholding mechanism on model confidence scores to flag anomalies for further inspection [61].
Guide 2: Mitigating Feature Correlation and Overfitting
- Problem Statement: The model performs well on the source NIDS dataset (e.g., CIC-IDS2018) but generalizes poorly to the target AI-text dataset.
- Root Cause: High autocorrelation between features in the training dataset can artificially inflate performance metrics on the source task but reduce model adaptability [63].
- Solution Methodology:
- Conduct Feature Analysis: Generate a correlation heatmap (e.g., using Pearson coefficient) for features in your source dataset [63].
- Apply Feature Pruning: Set a correlation threshold (e.g., 90%) and remove one feature from any pair exceeding this limit to reduce redundancy.
- Algorithm Selection: Note that algorithms like Gaussian Naive Bayes (GNB), which assume feature independence, are most susceptible to performance degradation from correlated features. Consider using Random Forest or ANN which are more robust [63].
Guide 3: Managing Data Heterogeneity and Privacy in Federated Experiments
- Problem Statement: I need to train a model on distributed, sensitive datasets (e.g., from multiple research institutions) without centralizing the data, but performance is inconsistent.
- Root Cause: Non-IID (Independent and Identically Distributed) data across clients in a federated system leads to a globally aggregated model that is biased and performs sub-optimally for individual clients [61].
- Solution Methodology:
- Adopt a Personalized Federated Averaging Framework: Move beyond standard FedAvg. Implement a framework that uses a shared global model for base features but incorporates client-specific adaptive layers for personalized task learning [61].
- Incorporate Privacy-Preserving Technologies: Use differential privacy during gradient aggregation or homomorphic encryption for secure computations to comply with data governance policies in your research consortium [64].
Frequently Asked Questions (FAQs)
Q1: Which source NIDS datasets are most suitable for initiating transfer learning to AI-generated text detection? A1: The table below summarizes high-quality, publicly available NIDS datasets that provide diverse attack profiles, making them excellent candidates for pre-training.
| Dataset | Key Characteristics | Relevance for Transfer Learning |
|---|---|---|
| CSE-CIC-IDS2018 [61] | Represents a comprehensive range of modern attacks with diverse network traffic patterns. | Provides a rich feature space for learning generalizable attack signatures analogous to different AI-text generators. |
| UNSW-NB15 [62] [61] | Contains hybrid of real modern normal activities and synthetic contemporary attack behaviors. | Its complexity helps models learn to distinguish subtle anomalies, a key skill for AI-text detection. |
| NSL-KDD [62] | An improved version of KDD Cup'99, with redundant records removed to reduce learner bias. | Useful for foundational experiments on a well-understood benchmark before moving to more complex data [63]. |
Q2: How can I interpret my model's decisions to build trust in its detections? A2: Implement Explainable AI (XAI) techniques. For example, use SHapley Additive exPlanations (SHAP) for feature importance analysis and root cause investigation. This is critical for understanding why a text snippet is classified as AI-generated and for refining the model [64] [62].
Q3: What are the key performance metrics beyond accuracy that I should monitor? A3: Accuracy can be misleading, especially with imbalanced data. The following metrics, derived from the confusion matrix, provide a more complete picture [63]:
| Metric | Formula | Focus |
|---|---|---|
| Precision | True Positives / (True Positives + False Positives) | The reliability of a positive detection. |
| Recall | True Positives / (True Positives + False Negatives) | The model's ability to find all positive instances. |
| F1-Score | 2 * (Precision * Recall) / (Precision + Recall) | The harmonic mean of precision and recall. |
Q4: My model is experiencing high false alarm rates. How can I reduce this? A4: High false positives can stem from overfitting or noisy labels. Consider integrating an ontology-based cyber situational awareness system. This structures threat intelligence and uses semantic reasoning (e.g., with STIX standards) to add contextual understanding, which can significantly improve precision and reduce false alarms [64].
Experimental Protocol: Federated Transfer Learning for Rare Class Detection
This detailed methodology is adapted from a state-of-the-art framework for detecting rare network attacks, which can be directly translated to identifying rare or novel families of AI-generated text [61].
1. Objective: To collaboratively train a global AI-text detection model across multiple data-holding clients (e.g., different research labs) without sharing raw data, with a specific focus on improving the detection of rare or zero-day AI-text types.
2. Workflow and Signaling Pathway: The diagram below illustrates the core iterative process of the federated transfer learning protocol.
3. Key Steps:
- Step 1 - Initialization: A central server initializes a global AI-detection model (e.g., a deep neural network).
- Step 2 - Client Selection: A subset of clients (research labs) is selected for the current training round.
- Step 3 - Local Training: Each client downloads the global model.
- The model is trained on the client's local, private dataset of human and AI-generated text.
- Critical Step: Client-specific adaptive layers are fine-tuned to learn the local data distribution, which is crucial for capturing the nuances of rare text classes available only at that client [61].
- Step 4 - Update Transmission: Instead of sending raw data, clients send only the model updates (gradients) back to the server.
- Step 5 - Secure Aggregation: The server aggregates these updates using a federated averaging algorithm to improve the global model.
- Step 6 - Iteration: Steps 2-5 are repeated until the global model converges.
- Step 7 - Zero-Day Identification: To handle previously unseen AI-text types (zero-day), a threshold-based detection mechanism is used. Clients testing the model on new data can report high-confidence anomalies back to the server, which then triggers a dynamic update to the global knowledge base [61].
The Scientist's Toolkit: Research Reagent Solutions
The table below catalogs essential "reagents" — datasets, algorithms, and software tools — required for experiments in this field.
| Research Reagent | Function / Purpose | Example / Standard |
|---|---|---|
| Benchmark NIDS Datasets | Serves as the source domain for pre-training transfer learning models. Provides foundational knowledge of pattern anomalies. | CSE-CIC-IDS2018, UNSW-NB15, NSL-KDD [62] [61] [63] |
| Federated Learning Framework | Enables collaborative model training across decentralized data sources while preserving data privacy. | Frameworks implementing FedAvg or more advanced algorithms like FedProx [61]. |
| SMOTE | A data augmentation technique used to generate synthetic samples for the minority class, mitigating class imbalance. | Synthetic Minority Oversampling Technique [62]. |
| Transformer-based Models | Advanced neural architectures for sequence modeling. Effective for learning complex feature interactions in both network traffic and text. | Basis for models like BERT. Can be used as a feature extractor in NIDS and is central to many AI-text generators [62]. |
| Explainable AI (XAI) Tools | Provides interpretability and root-cause analysis for model predictions, building trust and aiding debugging. | SHAP (SHapley Additive exPlanations) [64] [62]. |
| Structured Threat Intelligence | Provides a standardized language and ontology for representing knowledge about threats, improving contextual awareness. | STIX (Structured Threat Information Expression) [64]. |
Overcoming Practical Hurdles: Data, Domain Shift, and Model Decay
Mitigating Data Scarcity and Preventing Data Leakage in 5G Research Environments
This technical support center provides guidance for researchers and scientists working with 5G networks, particularly in the context of developing robust AI-generated text detectors. The interconnected and software-defined nature of 5G research environments introduces unique challenges, including data scarcity for training models and significant risks of data leakage. The following guides and FAQs are designed to help you secure your experimental setups and troubleshoot common issues.
Frequently Asked Questions (FAQs)
1. What are the most common data leakage points in a 5G research environment? Data leakage in 5G research can occur through several vectors [65] [66]:
- Insecure APIs: The 5G core relies on a Service-Based Architecture (SBA), making APIs a prime target for attacks if not properly secured with authentication and input validation [66].
- Network Slicing Misconfigurations: Improper isolation between network slices can allow cross-slice data access or attacks [65].
- Virtualized Network Functions (VNFs): Vulnerabilities in VNFs can be exploited to access or exfiltrate sensitive research data [65].
- IoT Endpoints: Billions of connected IoT devices, often with minimal security, can be hijacked and used as entry points to the research network [65] [67].
- Supply Chain Compromises: Backdoors in hardware or software components from third-party vendors can lead to data leakage [65].
2. How can we generate sufficient data for training AI models when real-world 5G data is scarce? Researchers can overcome data scarcity through synthetic data generation and secure data augmentation techniques [2]:
- Controlled Synthetic Data Generation: Use a secure, isolated testbed to simulate 5G network traffic and user behavior. This generates realistic, labeled data without risking exposure of real user data.
- Federated Learning: This approach allows you to train AI models across multiple decentralized devices or servers holding local data samples without exchanging them. This avoids the need to centralize sensitive data [2].
- Evasive Soft Prompts: Frameworks like EScaPe can be used to generate "human-like" text that evades current detectors. This creates adversarial training data, improving the robustness of your supervised detectors [2].
3. Our AI-text detector performance drops significantly when evaluating text from a new 5G-connected platform. What could be the cause? This is a classic problem of transferability, often caused by data distribution shift. The model was trained on data that does not perfectly match the data it encounters in the real world. In 5G environments, this can be due to [2]:
- Domain-Specific Language: The new platform may generate text with a different style, vocabulary, or structure (e.g., technical support logs vs. social media posts).
- Adversarial Evasion: The text might have been generated using evasion techniques, such as evasive soft prompts, specifically designed to fool detectors [2].
- Mitigation: Implement continuous learning pipelines and use adversarial training with techniques like the EScaPe framework to make your detector more resilient to such shifts [2].
4. What is the single most important practice to prevent data leakage in our 5G testbed? Adopting a Zero Trust Architecture is widely considered foundational [65] [66]. This security model operates on the principle of "never trust, always verify." It requires strict identity verification for every person and device trying to access resources on your private network, from both inside and outside the network. This limits lateral movement and contains potential breaches.
Troubleshooting Guides
Issue: Suspected Data Leakage from a Network Slice
Symptoms: Unusual outbound network traffic, unexpected system behavior in an isolated slice, or alerts from monitoring tools.
Resolution Steps:
- Immediate Isolation: Immediately quarantine the affected network slice to prevent further data loss or lateral movement to other slices [65].
- Forensic Analysis: Check access logs for the slice's management APIs and examine VNF configurations for unauthorized changes [65] [66].
- Validate Microsegmentation Policies: Review and reinforce security policies between different segments within the slice and to external networks [65].
- Incident Response: Execute your data breach response plan, including notifying relevant stakeholders and regulatory bodies if necessary [65].
Issue: Poor Performance of a Transferred AI-Generated Text Detector
Symptoms: High false-positive or false-negative rates when a detector trained in one environment is deployed in another.
Resolution Steps:
- Analyze the Data Shift: Compare the statistical properties of the training data with the new, incoming data from the 5G environment. Look for differences in word distribution, sentence length, and style [2].
- Test for Adversarial Robustness: Evaluate the detector against texts generated with evasion techniques, such as those produced by the EScaPe framework, to identify specific weaknesses [2].
- Fine-Tune with Domain-Specific Data: Retrain the detector on a small, curated dataset from the new target environment to help it adapt [2].
- Implement Model Calibration: Recalibrate the model's confidence scores to better reflect its accuracy in the new setting, reducing uncertainty [2].
Experimental Protocols & Methodologies
Protocol 1: Assessing Detector Robustness Using Evasive Soft Prompts
This protocol outlines how to test the reliability of AI-generated text detectors against adversarial attacks, a critical step for research in transferable detectors [2].
1. Objective: To evaluate a detector's false negative rate when presented with AI-generated text designed to evade detection. 2. Materials: * Pre-trained Language Model (PLM) for text generation (e.g., GPT-3.5, PaLM). * AI-generated text detector to be evaluated (e.g., model based on DetectGPT). * EScaPe framework or similar for generating evasive soft prompts [2]. * Dataset of human-written text prompts for various writing tasks (e.g., news, essays).
3. Methodology:
- Step 1 (Baseline): Generate text using the PLM with standard prompts. Run the detector on this text to establish a baseline detection rate.
- Step 2 (Evasive Prompt Learning): Use the EScaPe framework to learn a universal evasive soft prompt. This involves prompt tuning with a reward signal from the detector, encouraging the PLM to generate "human-like" text [2].
- Step 3 (Adversarial Testing): Generate a new set of text using the PLM, now guided by the learned evasive soft prompt.
- Step 4 (Evaluation): Run the detector on the new, evasive AI-generated text. Calculate the increase in the false negative rate compared to the baseline.
4. Interpretation: A significant increase in false negatives indicates the detector is vulnerable to adversarial evasion, highlighting a lack of robustness and a challenge for transferable detection.
The workflow for this adversarial testing protocol is as follows:
Protocol 2: Implementing a Zero Trust Framework for a 5G Research Lab
This protocol describes how to architect a secure 5G research environment to prevent data leakage [65] [66].
1. Objective: To design and deploy a Zero Trust architecture for a 5G research testbed, minimizing the risk of internal and external data leakage. 2. Materials: * 5G core network infrastructure (software-defined). * Identity and Access Management (IAM) system. * Microsegmentation software. * Logging and continuous monitoring tools.
3. Methodology:
- Step 1 (Identify Assets): Catalog all critical research data, applications, and services in the testbed.
- Step 2 (Map Flows): Document how these assets communicate with each other and with external networks.
- Step 3 (Policy Creation): Define strict access control policies based on the principle of least privilege. Policies must verify identity, device health, and other contextual factors before granting access to any resource [66].
- Step 4 (Enforce Microsegmentation): Implement microsegmentation to create secure, isolated zones around critical assets and network slices, controlling east-west traffic [65].
- Step 5 (Monitor and Log): Deploy continuous monitoring to inspect all network traffic and log every access request for auditing and anomaly detection.
4. Interpretation: A successful implementation will result in no unauthorized access to sensitive research data, even if a part of the network is compromised. All access requests are logged and can be audited.
The logical relationship of core Zero Trust components is shown below:
Table 1: Quantitative Impact of AI on Data Breach Management Data from IBM, as cited in ABI Research, shows the tangible benefits of automation in security [66].
| Metric | With AI & Automation | Without AI & Automation |
|---|---|---|
| Data Breach Lifecycle | 108 days shorter | - |
Table 2: Forecasted Market Adoption of Key Security Solutions Based on forecasts from ABI Research, showing the growing reliance on specific security technologies [66].
| Security Solution | Forecasted Telco Spending (2029) | Key Driver |
|---|---|---|
| Extended Detection and Response (XDR) | US $570 Million annually | Centralized threat detection and response |
| Software-Based 5G Security | 44% of revenue (from 36% in 2024) | Agility and holistic management |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential "Reagents" for 5G Security and AI Detector Research
| Item | Function in the Research Context |
|---|---|
| Signaling Firewalls | Software or hardware that authenticates and filters signaling messages in the 5G core to prevent storms, spam, and DoS attacks [66]. |
| XDR Platform | A security platform that unifies data across network, endpoints, and cloud for centralized threat detection and streamlined incident response [66]. |
| EScaPe Framework | A research framework used to generate universal evasive soft prompts, enabling the testing of AI-generated text detector robustness against adversarial attacks [2]. |
| Zero Trust Architecture | A security model that requires verifying every access request, regardless of its origin, to prevent lateral movement and contain data leakage [65] [66]. |
| Federated Learning Setup | A distributed machine learning approach that allows model training on decentralized data without data exchange, mitigating data scarcity and privacy issues [2]. |
Addressing Rapid Model Evolution and Detector Obsolescence
Technical Support Center: FAQs on AI-Generated Text Detectors
FAQ 1: Why do AI detection tools have high error rates, and what are the specific risks?
AI detection tools are fundamentally unreliable due to high false positive and false negative rates. A key reason is that these tools can misclassify human-written text, such as the US Constitution, as AI-generated [14] [41]. The primary risks include:
- False Accusations: High false positive rates can lead to wrongly accusing students or researchers of misconduct [14].
- Easy Circumvention: Individuals can bypass detectors using simple techniques like paraphrasing, inserting personal anecdotes, or using specific prompt engineering (e.g., adding words like "cheeky" to introduce irreverent metaphors) [13]. Specialized AI "humanizing" tools are also emerging to evade detection [13].
- Inherent Technical Flaws: OpenAI shut down its own AI detection tool due to poor accuracy, highlighting the fundamental technical challenges [14].
FAQ 2: What are the core technical challenges in making AI detectors robust?
The core challenges stem from the rapid evolution of Large Language Models (LLMs) and the fundamental similarity between AI-generated and human-written text [41].
- Lack of Universal Distinguishing Features: There is no consistently identifiable feature in AI-generated text that is always absent in human writing, making it a difficult classification problem [41].
- Vulnerability to Attacks: Detection methods are susceptible to various attacks, including:
- Rapid Obsolescence: A detector trained on the output of a specific LLM (like GPT-3) often becomes obsolete when a new model (like GPT-4) is released, as the statistical patterns of the text change [68] [41]. This creates a continuous "cat-and-mouse" game.
FAQ 3: What practical steps can be taken to manage detector obsolescence in a research setting?
Instead of relying on unreliable detection tools, researchers should adopt the following strategies to foster accountability and critical thinking [14]:
- Promote Transparency: Establish clear policies requiring the documentation of AI use. Ask researchers to submit a "process statement" explaining how they used AI tools in their work [14].
- Develop Authentic Assessments: Design research tasks and assignments that are less susceptible to AI automation. This can be achieved by connecting work to real-world, personal contexts and requiring iterative, multi-stage projects [14].
- Use a Multi-Faceted Evaluation Approach: Avoid over-reliance on any single assessment method. Use a mix of evaluations to ensure equitable and comprehensive skill assessment [14].
Experimental Protocols for Detector Robustness and Transferability
Protocol for Evaluating Detector Performance and Failure Modes
Objective: To systematically quantify the false positive and false negative rates of an AI text detector and identify its vulnerabilities under various conditions.
Methodology:
- Dataset Curation:
- Human Text Corpus: Collect a diverse set of human-written texts from verified academic papers, news articles, and essays.
- AI Text Corpus: Generate text using a suite of different LLMs (e.g., GPT-4, Claude, Gemini) across various prompts and domains.
- Baseline Testing: Run the detector on both corpora to establish baseline accuracy, precision, recall, and F1-score.
- False Positive Stress Test: Test the detector on known human-written texts that are structurally formal (e.g., the US Constitution) to measure the false positive rate [14].
- Adversarial Testing:
- Paraphrasing: Use a paraphrasing tool or a secondary LLM to modify the AI-generated texts. Re-run the detector to measure the change in the false negative rate [13] [41].
- Prompt Engineering: Generate new AI texts using prompts designed to produce "human-like" output (e.g., by requesting informal tone, personal anecdotes, or specific keywords) and test the detector [13].
- Cross-Model Generalization Test: Evaluate the detector's performance on text generated by a new, previously unseen LLM to test for obsolescence [41].
Protocol for Developing a Transferable Supervised Detector
Objective: To create a detector that maintains performance when applied to text from new LLMs, mitigating rapid obsolescence.
Methodology:
- Feature Engineering: Move beyond basic statistical features. Extract deeper, more transferable features such as:
- Semantic Coherence Metrics: Measuring the consistency of meaning across long passages.
- Logical Fallacy and Factual Consistency Checks: Leveraging external knowledge bases to verify claims.
- Stylometric Features at Multiple Linguistic Levels.
- Adversarial Training: Incorporate paraphrased and perturbed AI-generated texts from multiple model families into the training dataset. This forces the model to learn more robust, generalized patterns rather than surface-level features of a specific LLM [41].
- Domain Adaptation Techniques: Employ transfer learning strategies, similar to those used in weakly-supervised anomaly detection [69]. This involves pre-training a detector on a large, diverse dataset of AI and human text and then fine-tuning it with limited data from a new LLM to quickly adapt.
- Continuous Evaluation Loop: Implement a framework to regularly test the detector against newly released LLMs, using the protocol in 2.1, to monitor performance degradation and trigger model retraining.
Data Presentation
Table 1: Performance and Failure Modes of AI Detection Strategies
| Detection Strategy | Core Principle | Reported False Positive Rate | Key Vulnerabilities | Resistance to Model Obsolescence |
|---|---|---|---|---|
| Statistical Classifiers | Analyzes text for statistical features (e.g., perplexity, burstiness) [41]. | Can be high (e.g., flags US Constitution) [14]. | Paraphrasing, prompt engineering [13]. | Low - fails with new model families. |
| Neural Network-Based Detectors | Trains a deep learning model to distinguish human/AI patterns [41]. | Varies; Turnitin claims ~1% [13]. | Data poisoning, adversarial examples [41]. | Medium - requires frequent retraining. |
| Watermarking | Embeds a hidden, statistically identifiable signal during generation [41]. | Theoretically zero, if implemented perfectly. | Removal via paraphrasing; requires vendor cooperation [41]. | High - tied to the model, not its output. |
Table 2: Research Reagent Solutions for AI Text Detection Research
| Reagent / Resource | Function in Research | Example / Note |
|---|---|---|
| Diverse Human Text Corpora | Serves as the baseline/negative control for detector training and evaluation. | Academic archives, news datasets, creative writing repositories. |
| Multi-Model LLM Suites | Used to generate positive controls and test for generalization and obsolescence. | Access to APIs for OpenAI, Anthropic, Meta, and open-source models. |
| Paraphrasing & "Humanizing" Tools | Act as adversarial agents to stress-test detector robustness and identify vulnerabilities. | Tools like Undetectable.ai or prompts designed to evade detection [13]. |
| Standardized Evaluation Benchmarks | Provides a consistent framework for comparing different detectors and tracking progress. | Datasets with paired human/AI texts across multiple domains and model generations. |
| Transfer Learning Frameworks | Enables the development of detectors that can adapt to new models with less data. | Libraries (e.g., PyTorch, TensorFlow) with pre-built architectures for domain adaptation [69]. |
Workflow and System Diagrams
Detector Robustness Testing Workflow
Transferable Detector Development Cycle
Cross-Domain Few-Shot Object Detection (CD-FSOD) represents a significant challenge in computer vision, aiming to develop object detectors capable of adapting to novel domains with minimal labeled examples. This technical resource center consolidates the latest research and methodologies to support researchers and developers in overcoming the primary obstacles in this field: domain shift and limited data. The following sections provide structured guides, experimental protocols, and diagnostic tools to facilitate your experiments in building robust, transferable supervised detectors.
Benchmarking CD-FSOD Performance
Understanding the performance landscape of modern CD-FSOD approaches is crucial for selecting and developing effective strategies. The following table summarizes the mean Average Precision (mAP) of key models across different datasets and shot settings, highlighting their generalization capabilities.
Table 1: Performance Comparison (mAP) of Key CD-FSOD Methods on Benchmark Datasets
| Model | Shot Setting | ArTaxOr | Clipart1K | DIOR | DeepFish | NEU-DET | UODD |
|---|---|---|---|---|---|---|---|
| DE-ViT [70] | 1-shot | - | - | - | - | - | - |
| CD-ViTO [70] [71] | 1-shot | - | - | - | - | - | - |
| CDFormer [71] | 1-shot | - | - | - | - | - | - |
| DE-ViT [70] | 5-shot | - | - | - | - | - | - |
| CD-ViTO [70] [71] | 5-shot | - | - | - | - | - | - |
| CDFormer [71] | 5-shot | - | - | - | - | - | - |
| DE-ViT [70] | 10-shot | - | - | - | - | - | - |
| CD-ViTO [70] [71] | 10-shot | - | - | - | - | - | - |
| CDFormer [71] | 10-shot | - | - | - | - | - | - |
Note: Specific mAP values were not detailed in the provided search results. This table structure is provided for illustrative purposes. Please consult the primary sources ( [70] [71]) for precise quantitative results.
CD-FSOD Troubleshooting Guide: FAQs
FAQ 1: Why does my object detector, which performs well on common datasets, fail dramatically on novel domains like medical or satellite imagery?
Answer: This performance drop is primarily due to the domain gap, which can be quantified through specific metrics [70]:
- Style Differences: Variations in visual appearance (e.g., texture, lighting, color palette) between source and target domains.
- Small Inter-Class Variance (ICV): Objects in the target domain may have very similar visual features, making them difficult to distinguish.
- Indefinable Boundaries (IB): The boundaries between the target object and its background can be ambiguous or blurred.
This combination leads to feature confusion, where the model struggles to separate objects from the background (object-background confusion) and to distinguish between different object classes (object-object confusion) [71].
FAQ 2: How can I improve my model's robustness against feature confusion in cross-domain scenarios?
Answer: Address feature confusion by incorporating modules specifically designed for distinction:
- For Object-Background Confusion: Implement an Object-Background Distinguishing (OBD) module. This module uses a learnable background token to explicitly model and separate background features from object features, enhancing the model's ability to perceive objects clearly [71].
- For Object-Object Confusion: Implement an Object-Object Distinguishing (OOD) module. This module uses contrastive learning (e.g., InfoNCE loss) to increase the feature distance between different object classes, making them more separable in the feature space [71].
FAQ 3: What fine-tuning strategies are most effective for CD-FSOD to avoid overfitting or losing pre-trained knowledge?
Answer: Balancing adaptation with robustness is key. Effective strategies include:
- LinearProbe-Finetuning (LP-FT): First, freeze the feature extractor and train only the final linear layer (the "head") on the few-shot data. Then, perform a full fine-tuning of the network. This two-stage approach helps balance adaptation to the new data with retention of the model's original robustness to distribution shifts [72].
- Protection Freezing: Identify and freeze parts of the model, such as specific layers in a query-based detector, that are critical for maintaining its out-of-distribution (OOD) robustness during fine-tuning [72].
FAQ 4: With only a few labeled examples, how can I generate more high-quality, domain-aligned training data?
Answer: Use generative frameworks that ensure both visual realism and domain consistency.
- Domain-RAG Framework: This is a training-free, retrieval-augmented generation method [73].
- Decompose an input image into foreground (object) and background regions.
- Retrieve semantically and stylistically similar images from the target domain to guide a generative model.
- Synthesize a new background that aligns with the target domain's style.
- Compose the original foreground with the newly generated background to create a novel, domain-consistent training sample [73].
Experimental Protocols for Key CD-FSOD Strategies
Protocol 1: Implementing the CD-ViTO Enhancement Pipeline
This protocol details the process of enhancing a base open-set detector (DE-ViT) for cross-domain settings [70].
- Base Model Initialization: Start with a pre-trained DE-ViT model.
- Integration of Novel Modules:
- Learnable Instance Features: Replace fixed initial instance features with learnable parameters. Use the few-shot target labels as supervision to optimize these features, increasing their discriminability and dispersion for better handling of small inter-class variance.
- Instance Reweighting Module: Implement a mechanism to assign higher importance (weights) to high-quality object instances that have slight indefinable boundaries. This helps in forming more robust class prototypes.
- Domain Prompter: Use this module to synthesize imaginary domain variations. It applies a contrastive learning loss and a classification loss to ensure that the model's features remain semantically consistent and resilient to style changes across domains.
- Few-Shot Fine-Tuning: Fine-tune the enhanced model (CD-ViTO) on the few-shot support set from the target domain.
Protocol 2: Evaluating Domain Gap with Proposed Metrics
Use this methodology to quantitatively assess the domain shift between your source and target datasets [70].
- Dataset Preparation: Define your source dataset (e.g., COCO) and your target dataset(s).
- Metric Calculation:
- Style: Use a pre-trained network (e.g., on ImageNet) to extract deep features from both datasets. The difference in the distributions of these features (e.g., measured by Fréchet Inception Distance) can quantify the style gap.
- Inter-Class Variance (ICV): For a given dataset, extract features for all object instances. Calculate the average pairwise distance between the mean features of different classes. A smaller average distance indicates smaller ICV.
- Indefinable Boundaries (IB): This can be approximated by training a simple model to distinguish object foreground from background. A lower performance in this segmentation task indicates more indefinable boundaries.
- Correlation Analysis: Correlate the calculated values of these metrics with the observed performance drop of a baseline model (e.g., DE-ViT) on the target datasets.
Architectural Visualizations
CD-ViTO Enhanced Open-Set Detection Pipeline
CDFormer's Feature Confusion Mitigation
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Resources for CD-FSOD Research and Development
| Resource Name | Type | Primary Function in CD-FSOD | Example/Reference |
|---|---|---|---|
| CD-FSOD Benchmark | Dataset Suite | Provides a standardized testbed for evaluating methods across diverse domains (e.g., artwork, clipart, satellite, underwater) [74] [70]. | CD-FSOD-benchmark [74] |
| Foundation Models | Pre-trained Model | Serves as a powerful starting point for feature extraction and open-set detection, leveraging knowledge from large-scale pretraining [75] [70]. | GroundingDINO, LAE-DINO [75] |
| Open-Set Detectors | Model Architecture | Base architectures designed to detect objects beyond the classes seen during training, forming the backbone for many FSOD and CD-FSOD systems [70]. | DE-ViT [70] |
| Domain-RAG | Data Generation Framework | A training-free method for generating high-quality, domain-aligned synthetic data to augment few-shot support sets [73]. | Domain-RAG Framework [73] |
| NTIRE Challenge Platform | Evaluation Platform | Offers a competitive environment (e.g., on Codalab) to benchmark CD-FSOD methods against state-of-the-art approaches under standardized conditions [76]. | NTIRE 2025 CD-FSOD Challenge [76] |
The Role of Knowledge Distillation for Model Lightweighting
Understanding Knowledge Distillation
Knowledge Distillation (KD) is a machine learning technique designed to transfer the knowledge from a large, complex model (the teacher) to a smaller, more efficient model (the student). The primary goal is to create a compact model that retains the performance of the larger model but is suitable for deployment on devices with limited computational resources, a process central to model lightweighting [77] [78].
This process is vital for the broader thesis of improving transferable supervised detectors because it enables the creation of highly efficient models that can be adapted and transferred to various tasks and environments, including the analysis of AI-generated text [79].
The knowledge transferred from teacher to student can generally be categorized into three types, each suitable for different scenarios and tasks [77]:
- Response-Based Knowledge: Focuses on mimicking the teacher's final output layer (logits). It is the most straightforward form of distillation [80] [77].
- Feature-Based Knowledge: Involves aligning the intermediate layers of the student and teacher models. This is particularly valuable for complex tasks like object detection, as these features often contain crucial spatial and structural information lost in the final output [77] [81].
- Relation-Based Knowledge: Aims to transfer the relationships between different data points or layers within the teacher model [80] [77].
Frequently Asked Questions & Troubleshooting
Q1: My distilled student model performs significantly worse than the teacher model. What could be the cause?
This is a common challenge, often stemming from a mismatch in feature representation capabilities, especially when using heterogeneous networks (e.g., a ResNet teacher and a MobileNet student) [81].
- Problem: The student model's architecture may not have the capacity to directly replicate the teacher's complex feature maps, leading to misalignment and poor knowledge transfer [81].
- Solution: Implement an adaptive distillation loss. Instead of strictly matching feature values, use the teacher's features as a supervised "input" rather than just a "target." This guides the student's learning process without enforcing an impossible direct alignment. Incorporating attention mechanisms can also help the student focus on the teacher's most informative local features [81].
Q2: How can I perform knowledge distillation for a task like object detection, where location information is critical?
For object detection, relying solely on response-based (logit) distillation is insufficient because it lacks spatial information [81].
- Problem: Standard logit distillation does not provide the spatial feature information needed for accurate object localization [81].
- Solution: Employ a feature-based knowledge distillation framework that combines both local and global features [81].
- Local Distillation: Uses attention mechanisms to force the student to focus on and mimic the teacher's foreground object features [81].
- Global Distillation: Reconstructs the relationships and contextual information between different objects and scales in the teacher's feature maps, which is crucial for localization [81].
Q3: What are the modern drivers and techniques behind Knowledge Distillation in 2025?
KD has seen a resurgence, driven by several key trends [82]:
- Open-Weight Ecosystems: There is a high demand for compact, high-performing models derived from large open-weight models (e.g., LLaMA, Mistral) that can run on consumer hardware [82].
- Multimodal Distillation: Transferring knowledge from a large multimodal teacher (e.g., vision-language models) to a smaller, sometimes unimodal, student is an active research area [82].
- Distillation-as-Alignment: KD techniques are being used to transfer complex behaviors, such as those learned through Reinforcement Learning from Human Feedback (RLHF), from large models to smaller ones, ensuring they are both capable and aligned with human preferences [82].
Experimental Protocols for Effective Distillation
The following table outlines a standard experimental workflow for feature-based knowledge distillation, adaptable for various tasks.
Table 1: Generic Workflow for a Feature-Based Knowledge Distillation Experiment
| Step | Action | Key Considerations |
|---|---|---|
| 1. Model Selection | Choose a high-performance teacher model and a lightweight student model. | Architectures can be homogeneous (e.g., ResNet101→ResNet50) or heterogeneous (e.g., ResNet→MobileNet) [81]. |
| 2. Loss Formulation | Define the combined loss function: (\mathcal{L}{total} = \alpha \mathcal{L}{task} + \beta \mathcal{L}_{distill}). | (\mathcal{L}{task}) is the standard task loss (e.g., Cross-Entropy). (\mathcal{L}{distill}) is the distillation loss (e.g., KL Divergence for logits, Mean Squared Error for features). (\alpha) and (\beta) are weighting coefficients [78] [81]. |
| 3. Training Configuration | Configure the optimizer, learning rate, and batch size. | Student models can often be trained with higher learning rates and fewer examples than the teacher due to the richer information in soft targets [77]. |
| 4. Model Evaluation | Evaluate the student model's performance on a benchmark test set. | Compare the student's accuracy and speed against the teacher model and a baseline student trained without distillation [78] [81]. |
Detailed Protocol: Feature Knowledge Distillation for Object Detection
This protocol is based on the XFKD (X-ray Feature Knowledge Distillation) method, designed for prohibited item detection but applicable to any object detection task requiring lightweight models [81].
- Teacher Model Pre-training: Fully train a large teacher model (e.g., RetinaNet with ResNet101 backbone) on your target detection dataset until convergence.
- Student Model Initialization: Initialize a lightweight student model (e.g., RetinaNet with ResNet50 or MobileNetV3 backbone).
- Local Distillation (LD):
- Extract feature maps from a predefined intermediate layer of both teacher and student models.
- Calculate the Local Distillation Loss ((\mathcal{L}_{LD})) by applying a spatial attention mask to the teacher's features. This mask highlights regions with foreground objects, forcing the student to prioritize these areas.
- The loss is computed as the Mean Squared Error between the attention-weighted teacher and student features.
- Global Distillation (GD):
- To capture contextual relationships, reshape the teacher and student feature maps.
- Calculate the Global Distillation Loss ((\mathcal{L}_{GD})) by computing the cosine similarity between the reshaped global features of the teacher and student, then applying a KL divergence loss to match their similarity distributions.
- Total Loss Calculation and Optimization:
- The total loss is a weighted sum: (\mathcal{L}{total} = \mathcal{L}{detect} + \lambda1 \mathcal{L}{LD} + \lambda2 \mathcal{L}{GD}), where (\mathcal{L}{detect}) is the standard object detection loss (e.g., a combination of classification and bounding box regression losses).
- Use an optimizer like Adam to minimize (\mathcal{L}{total}) and update the student model's parameters [81].
The workflow and interactions of this protocol are visualized below.
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Components for a Knowledge Distillation Research Project
| Component / Tool | Function & Explanation | Example Instances |
|---|---|---|
| Teacher Model | A large, pre-trained model that serves as the source of knowledge. Its "dark knowledge" in the form of logits and features is the target for distillation [77] [82]. | ResNet101, CSPDarkNet53, Vision Transformer (ViT), LLaMA 3 [81] [82]. |
| Student Model | A more compact model designed for efficient deployment. It is trained to replicate the teacher's behavior and performance [77] [78]. | ResNet50, MobileNetV3, TinyLlama, DistilMistral [81] [82]. |
| Distillation Loss Function | A critical component that mathematically defines the difference between the teacher and student's knowledge, guiding the student's learning process [78] [81]. | Kullback-Leibler Divergence (for logits), Mean Squared Error (for features), Cosine Embedding Loss (for relations) [78] [81]. |
| Adaptation Layers (Hint Layers) | Often necessary in feature-based distillation when teacher and student feature maps have different dimensions. These layers transform student features to match the teacher's size for a valid loss calculation [81]. | 1x1 Convolutional layers, Fully Connected (Linear) layers. |
| Benchmark Datasets | Standardized datasets used to train, validate, and fairly compare the performance of distilled models against baselines and state-of-the-art. | BEIR, MTEB (for retrieval/embedding models) [83], SIXray, OPIXray (for object detection) [81], COCO [81]. |
Performance Metrics & Data
Evaluating the success of knowledge distillation involves measuring both the performance retention and the gains in efficiency. The following table summarizes quantitative results from recent research, demonstrating the effectiveness of advanced distillation techniques.
Table 3: Quantitative Performance of Knowledge Distillation Methods
| Model (Teacher → Student) | Distillation Method | Dataset | Key Metric | Result | Improvement Over Baseline |
|---|---|---|---|---|---|
| LEAF (leaf-ir) [83] | Teacher-Aligned Representations | BEIR | Information Retrieval Score | Ranked #1 on leaderboard | State-of-the-art for its size (23M parameters) |
| RetinaNet (R101 → R50) [81] | XFKD (Local & Global Feature) | SIXray | mAP (%) | 81.25% | +7.10% |
| YOLO (CSPD53 → MNV3) [81] | XFKD (Local & Global Feature) | SIXray | mAP (%) | 76.32% | +1.89% |
| Student Model (with KD) [78] | Logit Distillation (Soft Targets) | Iris Dataset | Test Accuracy | ~97% | Higher accuracy and faster convergence vs. student trained without KD |
Optimizing Computational Efficiency vs. Detection Accuracy Trade-offs
Frequently Asked Questions (FAQs)
FAQ 1: What is the fundamental trade-off in AI text detection? The core trade-off lies between a detector's accuracy and its bias against certain writing styles. Highly accurate detectors often achieve this by becoming overly sensitive to text that lacks the perceived complexity of "standard" academic English. This can systematically and unfairly flag the work of non-native English speakers and researchers in disciplines with less standardized writing conventions as AI-generated [84].
FAQ 2: Why do detection tools struggle with "AI-assisted" text? AI-assisted text, where a human-written draft is polished by an LLM, creates a hybrid that doesn't fit cleanly into "human" or "AI" categories. Detection tools, which rely on pattern recognition, become less accurate and more biased when analyzing these nuanced texts, as the patterns are a complex mix of human and machine authorship [84].
FAQ 3: How does my disciplinary field affect detection results? Detection tools may exhibit bias across disciplines. They tend to perform better with the standardized, structured language common in technology and engineering fields. Conversely, they often struggle with the nuanced and interpretive writing styles found in the humanities and social sciences, leading to higher false positive rates in these areas [84].
FAQ 4: What are the key computational challenges in developing better detectors? A major challenge is the black-box nature of both LLMs and the detection tools themselves. They lack transparent explanations for their classifications. Furthermore, creating detectors that are robust enough to handle the vast and evolving variety of writing styles and hybrid (AI-assisted) texts without becoming computationally prohibitive is a significant hurdle [84].
FAQ 5: Is it possible to have a detector that is both fair and accurate? Current evidence suggests a direct trade-off. Efforts to maximize accuracy on purely AI-generated text can inadvertently amplify bias. Therefore, a detector that is perfectly fair and accurate across all author groups and text types may not be feasible with current paradigms, shifting the focus towards ethical and transparent use of LLMs rather than reliance on detection [84].
Performance Data for AI Text Detectors
The following tables summarize empirical data on the performance of popular AI text detection tools, highlighting the central trade-offs.
Table 1: Overall Accuracy and Bias in Human vs. AI-Generated Text Detection
| Detection Tool | Overall Accuracy | False Positive Rate (Human text flagged as AI) | Bias Against Non-Native English Speakers | Bias Across Disciplines |
|---|---|---|---|---|
| GPTZero | Variable, shows trade-offs | Disproportionately higher for non-native speakers | Significant | Higher false positives in Social Sciences & Humanities |
| ZeroGPT | Variable, shows trade-offs | Disproportionately higher for non-native speakers | Significant | Higher false positives in Social Sciences & Humanities |
| DetectGPT | Variable, shows trade-offs | Disproportionately higher for non-native speakers | Significant | Higher false positives in Social Sciences & Humanities |
Source: Adapted from [84]. All tools demonstrate a notable accuracy-bias trade-off, with fairness implications for scholarly publication.
Table 2: Detector Performance Across Different Text Types
| Text Type | Description | Detection Tool Performance |
|---|---|---|
| Purely Human-Written | Original text without LLM involvement. | High accuracy, but with significant false positives for non-native speakers and certain disciplines [84]. |
| Purely AI-Generated | Text entirely generated by an LLM (e.g., ChatGPT o1, Gemini 2.0). | Relatively higher accuracy, though not perfect, forming the basis for "high accuracy" claims [84]. |
| AI-Assisted | Human-written text subsequently enhanced by an LLM for readability. | Significantly reduced accuracy and increased bias; the most challenging and realistic category [84]. |
Experimental Protocols for Detector Evaluation
For researchers aiming to evaluate or develop new supervised detectors, the following methodology provides a robust framework for assessing the accuracy-bias trade-off.
Protocol 1: Benchmarking Detector Performance and Fairness
1. Objective: To empirically evaluate the accuracy and potential biases of AI text detection tools against a controlled dataset of human-written, AI-generated, and AI-assisted texts.
2. Research Reagent Solutions
| Item Name | Function in the Experiment |
|---|---|
| Dataset of Human-Written Abstracts | Serves as the ground truth baseline. Comprises abstracts from peer-reviewed journals published before the LLM era (e.g., pre-2022) to ensure no AI contamination [84]. |
| Large Language Models (LLMs) | Used to generate synthetic and AI-assisted text. State-of-the-art models like ChatGPT o1 and Gemini 2.0 Pro Experimental are recommended for contemporary relevance [84]. |
| AI Text Detection Tools | The subjects of evaluation. Tools like GPTZero, ZeroGPT, and DetectGPT are commonly used in research [84]. |
| Stratified Dataset | A dataset structured to test fairness, containing texts categorized by author native language (native vs. non-native English) and discipline (e.g., Technology, Social Sciences, Interdisciplinary) [84]. |
3. Procedure:
- Step 1 - Dataset Curation:
- Compile a dataset of human-written abstracts from a variety of disciplines.
- Stratify the dataset based on key variables: discipline and native language of the author(s) to enable bias analysis [84].
- Step 2 - Text Generation:
- AI-Generated Condition: Use prompts (e.g., "Write a scientific abstract about [topic]") with different LLMs (ChatGPT o1, Gemini 2.0) to generate synthetic abstracts.
- AI-Assisted Condition: Take a subset of the human-written abstracts (especially from non-native authors) and use LLMs with a prompt to "improve readability and language" [84].
- Step 3 - Detection & Analysis:
- Run all texts (Human, AI-Generated, AI-Assisted) through the selected detection tools.
- Record the classification result (Human/AI) and the confidence score for each text.
- Step 4 - Performance & Bias Calculation:
- Calculate standard performance metrics (Accuracy, Precision, Recall, F1-Score) for the human vs. AI-generated task.
- Calculate false positive rates (FPR) separately for native vs. non-native English speakers and across different disciplines. A statistically significant difference in FPR indicates bias [84].
The workflow for this experimental protocol is outlined below.
Protocol 2: Evaluating Detector Robustness on Hybrid Text
1. Objective: To specifically test how detection tools perform on the increasingly common category of AI-assisted or hybrid text, where human and machine authorship are blended.
2. Procedure:
- Step 1 - Create a Base Human Text: Select a human-written abstract.
- Step 2 - Introduce AI Assistance: Process the abstract through an LLM with varying levels of intervention (e.g., "correct grammar," "improve style," "rewrite for clarity").
- Step 3 - Measure Detection Shift: Submit the original and each AI-assisted version to the detection tools. Track the change in the "AI-generated" probability or score.
- Step 4 - Correlate with Human Editing: Introduce varying degrees of manual human editing post-LLM enhancement and measure the impact on detection scores. This tests the detector's sensitivity to the depth of AI involvement.
The logical relationship and workflow for this robustness evaluation are detailed in the following diagram.
Benchmarking and Validating Detector Performance for Scientific Reliability
FAQs on Evaluation Metrics for AI-Generated Text Detection
Q1: What is a Confusion Matrix and why is it fundamental? A Confusion Matrix is a table that summarizes the performance of a classification model by comparing its predicted labels against the true labels [85]. It is the foundation for calculating most other classification metrics. The matrix breaks down predictions into four key categories [86] [87]:
- True Positive (TP): The model correctly predicts the positive class (e.g., correctly identifies AI-generated text).
- False Positive (FP): The model incorrectly predicts the positive class (e.g., misclassifies human text as AI-generated). This is also known as a Type I error [87].
- False Negative (FN): The model incorrectly predicts the negative class (e.g., fails to detect AI-generated text). This is also known as a Type II error [87].
- True Negative (TN): The model correctly predicts the negative class (e.g., correctly identifies human text).
For AI detection research, avoiding False Negatives (missed AI text) is often critical, though False Positives (falsely accusing humans) also carry significant consequences [88].
Q2: How do I choose between optimizing for Precision or Recall? The choice depends on the relative cost of different errors in your specific application [89] [86].
- Optimize for Recall when the cost of False Negatives is very high. In AI detection, this means you want to catch as much AI-generated text as possible, even if it means some human text is incorrectly flagged. This is crucial when missing AI text poses a major risk [89].
- Optimize for Precision when the cost of False Positives is very high. This ensures that when your model flags text as AI-generated, it is highly likely to be correct. This is vital in academic integrity contexts where falsely accusing a student is a serious issue [88].
Q3: My model has high Accuracy but poor performance. Why? Accuracy can be misleading, especially with imbalanced datasets [89] [90]. For example, if only 1% of text in your dataset is AI-generated, a model that always predicts "human" will still be 99% accurate but is useless for detection [89]. In such cases, metrics like the F1-Score, which balances Precision and Recall, or a separate analysis of Recall and False Positive Rates, provide a more realistic picture of model performance [89] [91].
Q4: What does the F1-Score represent and when should I use it? The F1-Score is the harmonic mean of Precision and Recall [89] [91]. It is particularly useful when you need a single metric to evaluate a model's performance on an imbalanced dataset and when both False Positives and False Negatives are important to consider [86] [87]. A high F1-Score indicates that the model has both good Precision and good Recall.
Troubleshooting Guides
Problem: Low Recall for AI-Generated Text
- Symptoms: The detector is missing a significant amount of AI-generated text (high False Negatives).
- Potential Causes & Solutions:
- Cause 1: The classification threshold is set too high [89] [86]. Most classifiers output a probability, and a default threshold of 0.5 might be too conservative.
- Solution: Lower the decision threshold (e.g., to 0.3). This makes the model more sensitive, classifying more texts as "AI-generated," which should increase Recall [86].
- Cause 2: The training data lacks sufficient or diverse examples of AI-generated text.
- Solution: Curate a more representative and balanced dataset that includes outputs from a wider variety of AI models and covering different writing styles and topics.
Problem: Unacceptable False Positive Rate
- Symptoms: The detector is frequently misclassifying human-written text as AI-generated.
- Potential Causes & Solutions:
- Cause 1: The classification threshold is set too low [89].
- Solution: Increase the decision threshold (e.g., to 0.7). This makes the model more conservative, requiring higher confidence to classify text as "AI-generated," thereby reducing False Positives [89].
- Cause 2: The model is overfitting to patterns in the training data that are not truly exclusive to AI.
- Solution: Apply stronger regularization techniques during model training and perform error analysis on the False Positives to identify and address confounding patterns.
The following table summarizes the key metrics derived from the Confusion Matrix [89] [87] [90].
| Metric | Formula | Interpretation | Use Case |
|---|---|---|---|
| Accuracy | (TP + TN) / (TP+TN+FP+FN) | Overall correctness of the model. | A quick, coarse-grained measure for balanced datasets [89]. |
| Precision | TP / (TP + FP) | How many of the positive predictions were correct? | Critical when False Positives are costly (e.g., academic accusations) [85] [87]. |
| Recall (Sensitivity) | TP / (TP + FN) | How many of the actual positives were found? | Critical when False Negatives are costly (e.g., missing AI content) [89] [87]. |
| F1-Score | 2 * (Precision * Recall) / (Precision + Recall) | Harmonic mean of Precision and Recall. | Best for imbalanced datasets when a balance between Precision and Recall is needed [91] [86]. |
| Specificity | TN / (TN + FP) | How many of the actual negatives were correctly identified? | Important when correctly identifying negative cases is a priority [87]. |
| False Positive Rate | FP / (FP + TN) | How many actual negatives were incorrectly flagged? | Key for understanding the "false alarm" rate [89]. |
Experimental Protocol for Metric Evaluation
This protocol outlines a standard methodology for evaluating a supervised AI-text detector.
- Dataset Curation: Compile a labeled dataset with a balanced mix of human-written and AI-generated text documents. Ensure the AI-text is generated from a diverse set of models (e.g., GPT-4, Gemini, Claude) and prompts. Split the dataset into training (70%), validation (15%), and test (15%) sets.
- Model Training: Train your chosen detection model (e.g., a fine-tuned transformer like BERT or RoBERTa) on the training set. Use the validation set for hyperparameter tuning and early stopping.
- Prediction & Confusion Matrix Generation: Use the trained model to make predictions on the held-out test set. Compare predictions to the true labels to populate the Confusion Matrix [85] [86].
- Metric Calculation: Calculate all relevant metrics (Accuracy, Precision, Recall, F1-Score) from the Confusion Matrix values as shown in the table above.
- Threshold Tuning: Adjust the classification threshold and repeat steps 3-4 to generate a Receiver Operating Characteristic (ROC) curve. The Area Under this Curve (AUC) provides a threshold-independent measure of model performance [90].
Workflow Diagram for Metric Evaluation
The diagram below visualizes the logical flow of establishing and using evaluation metrics, from data preparation to final model assessment.
The Scientist's Toolkit: Research Reagents & Materials
The table below lists key computational "reagents" and tools essential for research in transferable AI-generated text detection.
| Item | Function / Explanation |
|---|---|
| Labeled Text Corpora | A high-quality dataset with accurate "Human" and "AI" labels is the foundational reagent for training and evaluating supervised detectors. |
| Pre-trained Language Models (PLMs) | Models like BERT and RoBERTa serve as the base architecture, providing initial linguistic knowledge that can be fine-tuned for the specific detection task. |
| Multiple Text Generation AIs | A diverse set of models (e.g., GPT-family, Gemini, Claude, LLaMA) is needed to generate challenging, transferable test samples and prevent detector overfitting. |
| Metric Calculation Libraries | Libraries such as scikit-learn in Python provide pre-built functions for quickly computing accuracy, precision, recall, F1, and generating confusion matrices [86] [87]. |
| Hyperparameter Optimization Tools | Frameworks like Optuna or Weights & Biases help systematically find the best model training parameters, which is crucial for maximizing detection performance. |
Frequently Asked Questions (FAQs)
Q1: What is the primary goal of cross-model validation in AI-generated text detection? A1: The primary goal is to evaluate how well a detector trained on text from one set of Large Language Models (LLMs) generalizes to text generated by entirely different, unseen LLMs. This tests the detector's robustness and real-world applicability, moving beyond simple in-distribution testing.
Q2: Why does my detector's performance drop significantly when tested on a new model like Claude or Gemini? A2: Performance drops due to the "domain shift" or "model familiarly" problem. Different LLMs have distinct architectural nuances, training data, and generation strategies, leading to different textual "fingerprints." A detector overfitted to the quirks of its training models (e.g., GPT-3.5) may fail to recognize the different statistical signatures of an unseen model (e.g., LLaMA 2).
Q3: Which features are most transferable across different LLMs for detection purposes? A3: While no feature is perfectly transferable, research suggests that perplexity-based metrics and certain syntactic features (e.g., specific part-of-speech tag ratios) can be more robust than n-gram based features or model-specific log-probabilities. However, the most effective approach often involves ensemble methods that combine multiple feature types.
Q4: What is the minimum dataset size required for a reliable cross-model validation study? A4: There is no universal minimum, but for statistically significant results, studies often use thousands of text samples per model. For example, a robust benchmark might involve 5,000-10,000 human-written texts and an equivalent number of machine-generated texts from each LLM in the test set.
Q5: How can I mitigate overfitting when training a detector for cross-model evaluation? A5: Key strategies include: 1) Using strong regularization (e.g., dropout, L2 penalty), 2) Incorporating data augmentation techniques for text, 3) Training on a diverse mixture of source models rather than a single one, and 4) Employing early stopping based on a held-out validation set from unseen models.
Troubleshooting Guide
Problem: High False Positive Rate on Human-Written Text
- Cause: The detector may be relying on superficial features that are common in both AI and human text within your specific domain (e.g., technical jargon in scientific abstracts).
- Solution: Re-balance your training dataset to include more domain-specific human text. Consider using a loss function that penalizes false positives more heavily. Evaluate feature importance and remove features that are not discriminative.
Problem: Detector Fails Completely on a New Model Family (e.g., trained on GPT, tested on Claude)
- Cause: The detector has learned features that are too specific to the internal representations of the source model family.
- Solution: Retrain your detector using a more diverse set of source models. If possible, incorporate even a small amount of data from the target model family (few-shot learning) to adapt the detector.
Problem: Inconsistent Results Across Different Text Lengths
- Cause: Feature extraction may be biased by sequence length. For example, some metrics like average perplexity stabilize with longer texts.
- Solution: Stratify your evaluation by text length. Ensure your training and test sets have a comparable distribution of lengths. Consider using length-normalized features.
Problem: Poor Performance on Code Generation Tasks
- Cause: Detectors trained on natural language prose may not capture the structural and syntactic patterns of machine-generated code.
- Solution: Train and validate on datasets specifically designed for code generation tasks. Utilize features specific to code, such as abstract syntax trees (AST) patterns or specific token frequency distributions.
Experimental Protocols
Protocol 1: Benchmarking Detector Cross-Model Performance
Objective: To systematically evaluate the performance of a supervised detector when applied to text from LLMs not seen during training.
Dataset Curation:
- Source Models (for training): Select a set of models (e.g., GPT-3.5, GPT-4).
- Target Models (for testing): Select a disjoint set of models (e.g., Claude 3, Gemini Pro, LLaMA 2 70B).
- For each model, generate a corpus of text (e.g., 10,000 samples) using a diverse set of prompts from a public repository (e.g., Self-Instruct).
- Collect an equally sized corpus of human-written text from similar domains (e.g., Reddit, Wikipedia, arXiv).
Feature Extraction:
- Extract a standard set of features from all texts (source, target, human). Common features include:
- Lexical: n-gram statistics, vocabulary richness.
- Syntactic: Part-of-speech tag ratios, dependency tree depth.
- Semantic: Perplexity scores from a small, neutral LLM, semantic coherence scores.
- Model-Specific: Log-probabilities and token likelihoods (if available via API).
- Extract a standard set of features from all texts (source, target, human). Common features include:
Model Training:
- Train a classifier (e.g., Logistic Regression, XGBoost, or a small Transformer) exclusively on data from the Source Models and human text.
- Use k-fold cross-validation on the source data to tune hyperparameters.
Evaluation:
- In-Distribution Test: Evaluate the trained detector on a held-out test set from the Source Models.
- Cross-Model Test: Evaluate the detector on the entirely separate datasets from the Target Models.
- Report: Calculate and report standard metrics (Accuracy, F1-Score, AUC-ROC) for all tests.
Protocol 2: Creating a Transferable Feature Set
Objective: To identify and combine features that maintain high discriminative power across a wide range of LLMs.
- Multi-Source Training Data Generation: Generate text from a wide variety of available LLMs (e.g., 5-10 different models from different families).
- Comprehensive Feature Extraction: Extract a large, diverse pool of features (100+), including the standard ones and more novel candidates (e.g., entropy of token distributions, specific rhetorical structure markers).
- Feature Selection:
- Train a model on the multi-source data.
- Use a feature importance method (e.g., permutation importance, SHAP values) to rank features.
- Select the top-N features that are consistently important across different validation splits.
- Stability Validation: Validate the selected feature set by repeating the training and evaluation process, holding out a different model family each time to ensure the features are not dependent on any single source.
Data Presentation
Table 1: Cross-Model Detector Performance (F1-Score)
| Detector (Trained on) | Tested on GPT-4 | Tested on Claude 3 | Tested on Gemini Pro | Tested on LLaMA 2 70B | Average (Cross-Model) |
|---|---|---|---|---|---|
| GPT-3.5-Turbo Source | 0.98 | 0.71 | 0.65 | 0.73 | 0.70 |
| Mixed-Source (4 Models) | 0.95 | 0.89 | 0.85 | 0.91 | 0.88 |
| RoBERTa-Based Baseline | 0.92 | 0.82 | 0.79 | 0.84 | 0.82 |
Table 2: Feature Ablation Study on Cross-Model AUC-ROC
| Feature Set | GPT-4 | Claude 3 | Gemini Pro | LLaMA 2 70B |
|---|---|---|---|---|
| All Features | 0.99 | 0.95 | 0.93 | 0.96 |
| - Model-Specific Log-Probs | 0.98 | 0.94 | 0.92 | 0.95 |
| - Syntactic & Semantic | 0.97 | 0.85 | 0.81 | 0.88 |
| Lexical Features Only | 0.91 | 0.72 | 0.69 | 0.75 |
Visualizations
Cross-Model Validation Workflow
Detector Failure Analysis & Solutions
The Scientist's Toolkit
Table 3: Essential Research Reagents for Cross-Model Validation
| Reagent / Tool | Function / Purpose |
|---|---|
| HC3 Dataset | A benchmark dataset containing human and AI-generated responses (from ChatGPT) to a wide range of questions. Serves as a starting point for prompts and human reference. |
| OpenAI API / Google AI API / Anthropic API | Provides programmatic access to generate text from state-of-the-art LLMs (GPT, Gemini, Claude) for creating training and testing corpora. |
| Hugging Face Transformers | Library to access open-source models (e.g., LLaMA 2, BLOOM) for text generation and to utilize pre-trained models for feature extraction (e.g., for perplexity scoring). |
| GLTR Tool | A tool that provides visual and statistical features for detection, based on the likelihood and predictability of text, which can be used as part of a feature set. |
| SHAP (SHapley Additive exPlanations) | A game-theoretic approach to explain the output of any machine learning model, crucial for performing feature ablation studies and understanding detector decisions. |
| XGBoost / Scikit-learn | Machine learning libraries used to build and train efficient, high-performance classifiers on the extracted feature sets. |
Comparative Analysis of Supervised vs. Zero-Shot Detection Paradigms
Frequently Asked Questions (FAQs)
FAQ 1: What is the core difference between supervised and zero-shot detection paradigms? Supervised detectors are trained on extensive labeled datasets containing both human-written and AI-generated text, learning to classify based on statistical patterns and artifacts seen during training [49]. In contrast, zero-shot detectors do not require task-specific training data; they leverage auxiliary knowledge, semantic descriptions, or the inherent properties of a Large Language Model (LLM) to perform detection without having been explicitly trained on the specific task [92] [93].
FAQ 2: Can detection models be easily evaded, and how? Yes, even robust detectors can be effectively bypassed. Simple paraphrasing attacks can fool early detectors, while more advanced methods like Adversarial Paraphrasing pose a significant threat. This training-free attack framework uses an instruction-following LLM to humanize AI-text. It guides the paraphraser at each token generation step, selecting the next token that an AI text detector scores as most "human-like," creating adversarial examples optimized to evade detection [49].
FAQ 3: Are AI detection tools accurate enough for academic use? The suitability depends heavily on the context and the tool. Mainstream, paid tools can be reasonably good at identifying purely AI-generated text, but their performance drops significantly when the text has been modified (e.g., paraphrased) [88]. Crucially, for academic settings, the false positive rate is a paramount concern. Accusing a student of misconduct based on a false positive has severe consequences. Some of the best tools report false positive rates of around 1-2%, but many free tools found online have alarmingly high false positive rates and should be avoided for this purpose [88].
FAQ 4: What is the practical impact of adversarial attacks on detectors? Adversarial attacks significantly degrade detector performance. For instance, an adversarial paraphrasing attack guided by a detector like OpenAI-RoBERTa-Large reduced the True Positive rate at 1% False Positive (T@1%F) by a striking 98.96% on Fast-DetectGPT and by 64.49% on RADAR. On average, this attack achieved an 87.88% reduction in T@1%F across eight different detectors, demonstrating its universality and transferability [49].
FAQ 5: When should I choose a zero-shot method over a supervised one? Choose a zero-shot method when you lack labeled training data for the specific task, need rapid deployment for a new task without model retraining, or require a model that can generalize to entirely unseen categories or concepts [92] [93]. Supervised methods are typically chosen when you have ample, high-quality labeled data and prioritize maximum accuracy for a fixed set of known classes or tasks [49].
Troubleshooting Guides
Issue 1: Poor Generalization of Supervised Detector
Problem: Your trained detector performs well on its test set but fails on new datasets or against slightly modified AI text.
| Potential Cause | Solution | Experimental Verification Protocol |
|---|---|---|
| Overfitting to Training Artifacts | Implement adversarial training. Iteratively train your detector against a paraphraser that generates hard negative examples [49]. | 1. Train your initial detector (D).2. Use a paraphraser (P) to create adversarial examples that fool D.3. Retrain D on a mixture of original and adversarial data.4. Repeat steps 2-3 to progressively strengthen the detector. |
| Lack of Data Diversity | Use a diverse dataset like MAGE for training, which includes a wide variety of sources and topics to help the model learn more generalizable features [49]. | 1. Train one model on a standard dataset (e.g., RoBERTa-GPT2).2. Train another on a diverse dataset (e.g., MAGE).3. Compare the drop in accuracy on a held-out, domain-shifted validation set. |
| Dataset Bias | Apply cross-dataset evaluation. Test your detector's performance on a benchmark composed of texts from different domains and generated by various LLMs [49]. | 1. Select evaluation benchmarks from different domains (e.g., PubMed, Wikipedia, News).2. Evaluate your detector's AUC and T@1%F on each.3. A large performance variance indicates sensitivity to dataset-specific biases. |
Issue 2: High False Positive Rate in Zero-Shot Detection
Problem: Your zero-shot detector incorrectly flags human-written text as AI-generated.
| Potential Cause | Solution | Experimental Verification Protocol |
|---|---|---|
| Low Perplexity Human Text | Calibrate the confidence scores. Use a Deep Calibration Network (DCN) or similar technique to adjust the decision threshold and prevent bias towards "AI-like" classifications [92]. | 1. Run the detector on a verified human-written corpus.2. Plot the distribution of detection scores (e.g., "AI-like" probability).3. Adjust the classification threshold to ensure the false positive rate is below a required limit (e.g., 1-2%) [88]. |
| Bias from Training Data | This is a inherent challenge for zero-shot detectors using foundation models. Use Ensemble Attribute Learning. Leverage multiple semantic attributes to build a more robust classification link, reducing reliance on a single biased feature [94]. | 1. Define a set of semantic attributes for "human" and "AI" text.2. Train an ensemble model to learn these attributes from features.3. Classify based on similarity to attribute labels, which can be more robust than direct scoring [94]. |
Issue 3: Detector Failure Against Paraphrasing Attacks
Problem: Your detector, whether supervised or zero-shot, is easily bypassed by simple or adversarial paraphrasing.
| Potential Cause | Solution | Experimental Verification Protocol |
|---|---|---|
| Reliance on Surface-Level Features | Develop detectors based on fundamental properties. Use methods like DetectGPT or Fast-DetectGPT that rely on the observation that AI-generated text often lies in regions of negative curvature in the log-probability landscape, which can be more robust to surface changes [49]. | 1. Generate a set of AI texts and their paraphrased versions.2. Use DetectGPT (which computes log-probability curvature) to evaluate all texts.3. Compare the AUC of DetectGPT against your model's AUC on the paraphrased set. |
| Non-Robust Watermarking | Implement a robust, distortion-free watermark. Use techniques like those from Kuditipudi et al. that are designed to be robust against edits and paraphrasing attacks, or SynthID for scalable watermarking [49]. | 1. Generate watermarked text from an LLM.2. Apply a paraphrasing attack to the text.3. Run the watermark detection algorithm on the paraphrased text.4. Measure the watermark recovery rate post-attack. |
Quantitative Data Comparison
Table 1: Performance Comparison of AI Text Detectors Under Attack This table shows how different types of detectors perform when faced with a powerful adversarial paraphrasing attack, measured by the reduction in True Positive rate at a fixed 1% False Positive rate (T@1%F). A higher reduction indicates the detector is more vulnerable to the attack [49].
| Detector Category | Detector Name | T@1%F Reduction (Under Attack) |
|---|---|---|
| Neural Network-Based | RADAR | 64.49% |
| Neural Network-Based | OpenAI-RoBERTa-Large | Used as attack guide |
| Zero-Shot | Fast-DetectGPT | 98.96% |
| Watermark-Based | KGW Watermark | Vulnerable to dedicated attacks |
| Average Across 8 Detectors | 87.88% |
Table 2: Accuracy and False Positive Rates of Popular Detection Tools This table synthesizes data from multiple studies on the general accuracy and, more critically, the false positive rates of various tools. Performance varies significantly, and false positives are a key metric for academic use [88].
| Detection Tool | Overall Accuracy (Perkins et al.) | Overall Accuracy (Weber-Wulff) | Notes on False Positives |
|---|---|---|---|
| Turnitin | 61% | 76% | Among the most reliable; false positive rate ~1-2% |
| Copyleaks | 64.8% | Not Listed | |
| Crossplag | 60.8% | 69% | |
| GPTZero | 26.3% | 54% | |
| ZeroGPT | 46.1% | 59% | |
| Content at Scale | 33% | Not Listed |
Experimental Protocols
Protocol 1: Stress-Testing with Adversarial Paraphrasing
This protocol outlines the methodology for the Adversarial Paraphrasing attack, a potent stress-test for any AI text detector [49].
- Input: Collect the AI-generated text to be humanized.
- Paraphrasing LLM: Use an instruction-followed LLM (e.g., LLaMA-3-8B) as the paraphraser.
- Guidance Detector: Select a surrogate AI text detector to guide the attack (e.g., OpenAI-RoBERTa-Large).
- Detector-Guided Decoding:
- For each token generation step, the paraphraser LLM proposes its top-k most likely next tokens.
- Each potential continuation (the current sequence + one proposed token) is scored by the guidance detector.
- The token that leads the sequence to be classified as most human-like by the detector is selected.
- Output: The final adversarially paraphrased text.
This method operationalizes controlled text generation where the desired attribute is "human-likeness" [49].
Protocol 2: Evaluating Detector Transferability
This protocol evaluates how well a detector trained on one type of data or model performs on another, which is crucial for assessing real-world robustness [49].
- Base Training: Train a supervised detector (e.g., a RoBERTa-based classifier) on a source dataset (e.g., texts from GPT-2).
- Target Evaluation: Evaluate the detector's performance (using metrics like AUC and T@1%F) on one or more target datasets. These should differ from the source in key aspects:
- Different LLM: Text from GPT-3.5, GPT-4, Gemini, etc.
- Different Domain: Text from academic, creative, or technical writing not seen in training.
- After Attack: Text that has been paraphrased or adversarially modified.
- Analysis: Compare the performance drop between the source test set and the target sets. A small drop indicates high transferability.
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials for AI Text Detection Research
| Item Name | Function in Research | Example/Reference |
|---|---|---|
| Pre-trained Language Models | Serve as the foundation for both supervised and zero-shot detectors, providing base capabilities for understanding and generating text. | RoBERTa [49], BERT [93], GPT family [49] |
| Diverse Text Corpora | Used for training and evaluating detectors to ensure robustness and generalizability across domains and writing styles. | MAGE dataset [49], COCO [95], GLUE/FewRel [93] |
| Paraphrasing Models | Used to generate attacks for stress-testing detectors or for adversarial training to improve detector robustness. | DIPPER [49], Instruction-tuned LLaMA-3 [49] |
| Watermarking Schemes | Techniques to embed a detectable signature in AI-generated text, providing an alternative detection paradigm. | KGW Scheme [49], Unigram Watermark [49], SynthID [49] |
| Zero-Shot Detection Algorithms | Methods that detect AI text without task-specific training, leveraging statistical properties of the text. | DetectGPT [49], Fast-DetectGPT [49], GLTR [49] |
| Adversarial Training Loop | A methodological framework for iteratively improving a detector's robustness by training it against increasingly sophisticated attacks. | RADAR's iterative training [49] |
The Critical Role of High-Quality, Domain-Specific Datasets
Troubleshooting Guide: AI-Generated Text Detection
This guide addresses common challenges researchers face when developing detectors for AI-generated text, with a focus on creating transferable supervised models.
Problem 1: Poor Model Generalization Your detector performs well on its training data but fails on text from new AI models or different domains.
- Possible Cause: The training dataset lacks diversity in both generative models and content domains [38] [96].
- Solution:
- Audit Your Dataset: Check the variety of source AI models and text topics. A robust dataset should include outputs from multiple, state-of-the-art LLMs (e.g., Gemma-2-9b, Mistral-7B, Qwen-2-72B, LLaMA-8B) [38].
- Incorporate Real-World Data: Use high-quality human-written text from specific domains as your baseline. For example, the dataset built on New York Times articles provides authentic journalistic content [38].
- Apply Self-Supervised Learning (SSL): If labeled data is scarce, leverage SSL techniques. Pre-train your model on a large amount of unlabeled text data before fine-tuning it on a small, labeled dataset for the detection task [97].
Problem 2: Dataset Bias and Artifacts The detector learns superficial patterns specific to the training set rather than fundamental features of AI-generated text.
- Possible Cause: The dataset is constructed from a narrow source or contains low-quality, noisy data [96] [98].
- Solution:
- Ensure Data Cleanliness: Preprocess data to remove irrelevant content and errors [98].
- Source Data Rigorously: Prefer datasets that use real-world prompts and human-authored references, like those derived from news article abstracts and their corresponding full human narratives [38].
- Mitigate Bias: Actively identify and balance class distributions and language variations in your dataset to prevent the model from perpetuating stereotypes or making skewed predictions [98].
Problem 4: Inefficient Use of Scarce Labeled Data Obtaining large volumes of accurately labeled text is labor-intensive and slow [97].
- Possible Cause: Relying solely on fully supervised learning without leveraging unlabeled data.
- Solution:
- Adopt a Semi-Supervised Framework: Combine a small set of labeled data with a large pool of unlabeled data. Pre-train the model on all data in a self-supervised manner, then fine-tune on the labeled subset [97] [99].
- Employ Transfer Learning: Start with a model pre-trained on a general, large-scale language task and then transfer its knowledge to the specific task of AI-text detection [99].
Frequently Asked Questions (FAQs)
Q1: What are the key characteristics of a high-quality dataset for AI-text detection? An effective dataset should be:
- Large-Scale and Diverse: It should contain tens of thousands of samples from multiple generative models and cover a broad spectrum of topics to help the model generalize [38] [98].
- Well-Structured and Annotated: It must include detailed metadata, such as the source model for each text, to support tasks like binary classification (human vs. AI) and model attribution (identifying which AI created the text) [38].
- Domain-Relevant: For specialized applications (e.g., medical or clinical trial research), the dataset must incorporate domain-specific terminology and content to ensure model accuracy [100] [98].
Q2: How can I improve my detector's performance when I have very little labeled data? Self-supervised learning (SSL) is a powerful approach for this scenario. SSL frameworks use unsupervised pre-training on vast amounts of unlabeled data to learn general representations, followed by supervised fine-tuning on the small labeled dataset. This has been shown to boost performance in anomaly detection tasks with scarce labels [97].
Q3: Why does my model struggle with text from the latest AI models like GPT-4? This is often a knowledge cutoff issue. Once a standard model is trained, its knowledge is frozen in time [96]. To address this, consider using Retrieval Augmented Generation (RAG). While RAG is typically used for text generation, its principle is instructive: it allows a system to access and incorporate relevant, up-to-date information from external knowledge bases in real-time, which is a promising direction for making detectors more current [96].
Q4: What is model attribution, and how is it different from binary detection? Binary detection simply classifies text as "human-written" or "AI-generated." Model attribution is a more complex, multi-class classification task that aims to identify the specific AI model (e.g., GPT-4, LLaMA) that generated a given text. Baseline studies show that attribution accuracy is significantly lower, highlighting its difficulty [38].
Experimental Protocols & Data
Dataset Composition for Transferable Detectors
The following table summarizes a benchmark dataset designed for human vs. AI-generated text detection, illustrating the scale and diversity required for effective research [38].
Table 1: Composition of a Comprehensive AI-Text Detection Dataset
| Component | Description | Source/Models | Quantity |
|---|---|---|---|
| Human-Written Text | Original full-length articles | New York Times archive (since 2000) | Over 58,000 samples total (human and AI combined) |
| AI-Generated Text | Synthetic versions of articles | Multiple state-of-the-art LLMs | Multiple synthetic versions per human article |
| Prompts | Abstract from original articles | New York Times | Used to generate AI texts |
| Key Metadata | Source model, article features, etc. | --- | Enables model attribution and nuanced analysis |
Baseline Performance Metrics
Establishing baselines is crucial for evaluating new models and methods.
Table 2: Baseline Performance on Detection and Attribution Tasks [38]
| Task | Description | Baseline Accuracy |
|---|---|---|
| Binary Detection | Distinguishing human-written from AI-generated text | 58.35% |
| Model Attribution | Identifying the specific LLM that generated a text | 8.92% |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Resources for AI-Generated Text Detection Research
| Resource Type | Example | Function |
|---|---|---|
| Benchmark Datasets | Human vs. AI Generated Text Dataset [38] | Provides a large-scale, diverse benchmark for training and evaluating detection models. |
| Pre-trained Models | Self-supervised pre-trained models [97] | Offers a foundation for transfer learning, especially when labeled data is scarce. |
| AI-Generation APIs | Access to models like GPT-4-o, LLaMA-8B [38] | Allows researchers to generate their own synthetic text data for controlled experiments. |
| Multi-Modal Data Platforms | TrialBench for clinical trial data [100] | Provides domain-specific, AI-ready datasets that can be used to test detector transferability to specialized fields. |
Experimental Workflow and System Diagrams
Workflow for a Semi-Supervised Text Detector
The RAG-Enhanced Detection System
FAQs and Troubleshooting Guides
FAQ: Detector Performance and Limitations
Q1: What is the fundamental accuracy of current AI detectors, and can I trust a positive result?
Current AI detectors are not infallible and should not be used as the sole evidence for misconduct. Their performance is a balance between correctly identifying AI text (true positives) and misclassifying human text (AI-generated (false positives). In educational settings, a low false positive rate is considered more critical than a high overall detection rate due to the severe consequences of false accusations [88].
The following table summarizes the performance of various detectors as reported in recent studies:
Table 1: Performance Metrics of AI Text Detectors
| Detector Name | AI Text Identification Rate | Overall Accuracy | Key Limitations / Notes |
|---|---|---|---|
| Turnitin | 94% [88] | 61%-76% [88] | Designed for education; aims for a ~1% false positive rate [13] [88]. |
| Copyleaks | 100% [88] | 64.8% [88] | Performance varies with text origin and detector version. |
| GPTZero | 70%-97% [88] | 26.3%-54% [88] | Inconsistent performance across different studies. |
| Originality.ai | 100% [88] | Information Missing | Also flagged human text as AI with 97% certainty [101]. |
| ZeroGPT | 95.03%-96% [88] | 46.1%-59% [88] | Deeply problematic; known to falsely flag human text [101]. |
Q2: Why does my detector fail on high-quality AI text or text that has been paraphrased?
As Large Language Models (LLMs) become more advanced, their outputs become increasingly human-like. Modern "reasoning" models (e.g., OpenAI's o1, DeepSeek's R1) use techniques like "Chain-of-Thought" and multi-agent reasoning to produce coherent, logical, and contextually appropriate text that lacks the statistical anomalies earlier detectors relied on [102]. Furthermore, paraphrasing AI-generated text—either manually or using another AI—is a highly effective evasion technique. A 2025 study introduced "Adversarial Paraphrasing," a method that guides a paraphraser LLM with a detector to create text that is nearly impossible for current systems to identify, reducing detection rates by over 98% for some detectors [49].
Q3: Our clinical trial protocols are highly standardized. Does this make them more vulnerable to false positives?
Yes, this is a significant risk. AI detectors often analyze text for "perplexity" (unpredictability) and "burstiness" (variance in sentence structure). Formulaic text, such as that found in academic prose, legal documents, and standardized clinical trial protocols, tends to have lower perplexity and can be misclassified as AI-generated [102]. Studies have found that detectors disproportionately flag writing by non-native English speakers for similar reasons [102]. Therefore, a positive result on a protocol section may reflect its standardized nature, not its origin.
Troubleshooting Guide: Improving Detection Experiments
Problem: My supervised detector performs well on test data but fails in real-world applications.
This is a classic sign of overfitting and a lack of transferability. Your model may have learned the specific patterns of the AI models it was trained on but fails when faced with text from a new AI model or from a different domain (e.g., clinical protocols vs. general science writing).
- Solution 1: Implement Adversarial Training. Incorporate paraphrased and adversarially manipulated AI text into your training datasets. For example, the RADAR detector was adversarially trained using a paraphraser to improve its robustness against such evasion techniques [49].
- Solution 2: Diversify Your Training Data. Ensure your training data includes:
- Text from a wide variety of LLMs (both older and current models).
- Text from the specific domain you are targeting (e.g., clinical trial protocols, scientific manuscripts).
- Human-written text that is highly formal and standardized to teach the model not to flag these as false positives.
- Solution 3: Ensemble Methods. Do not rely on a single detection method. Combine the outputs of multiple detectors (e.g., a classifier-based detector, a zero-shot method like DetectGPT, and a watermarking system if applicable) to make a more robust decision [102].
Problem: I cannot tell if my detector is failing due to AI text or due to the writing style.
You need to establish a baseline for your specific text domain.
- Solution: Conduct a Local Validation Study.
- Gather a Control Set: Collect a set of confirmed human-written texts from your field (e.g., older protocols written before the LLM era).
- Generate a Test Set: Use various LLMs to generate text based on prompts similar to those used for your human-written set.
- Benchmark Your Detector: Run both sets through your detection system to establish its baseline false positive and false negative rates for your specific context. This will help you calibrate confidence thresholds.
Experimental Protocols for Detector Research
Protocol 1: Testing Detector Robustness Against Evasion Attacks
This protocol is designed to stress-test AI text detectors against paraphrasing attacks, a common evasion method [49].
- Text Generation: Generate a corpus of text samples (e.g., 1000 samples) using a target LLM (e.g., GPT-4, LLaMA).
- Baseline Detection: Run the original AI-generated texts through the detector under evaluation to establish a baseline detection rate.
- Simple Paraphrasing: Use a general-purpose paraphraser (e.g., DIPPER, an instruction-tuned LLM) to rewrite the AI-generated texts. Run these paraphrased texts through the detector.
- Adversarial Paraphrasing (Advanced): Implement an adversarial paraphrasing framework. This involves using a paraphraser LLM guided by the detection score of another AI text detector to iteratively rewrite the text until it bypasses detection [49].
- Analysis: Compare the detection rates across the three conditions (original, simply paraphrased, adversarially paraphrased). A robust detector will maintain a high detection rate even after paraphrasing.
Diagram: Workflow for Testing Detector Robustness
Protocol 2: Evaluating Detector Fairness Across Writing Styles
This protocol assesses whether a detector is biased against certain types of legitimate human writing.
- Sample Collection: Gather human-written text from distinct categories:
- Category A: Non-native English speaker scientific writing.
- Category B: Highly formal and standardized clinical trial protocols.
- Category C: Creative and high-perplexity science blogging.
- Run Detection: Process all samples through the AI detector.
- Quantify False Positives: Calculate the false positive rate for each category.
- Statistical Analysis: Perform a statistical test (e.g., Chi-squared) to determine if the false positive rates between categories (e.g., A vs. C, B vs. C) are significantly different. A fair detector will have similar false positive rates across categories.
The Scientist's Toolkit: Research Reagent Solutions
This table details key resources for building and testing supervised AI-text detectors.
Table 2: Essential Materials for AI-Generated Text Detection Research
| Reagent / Resource | Type | Function in Research | Exemplar / Note |
|---|---|---|---|
| Pre-trained Language Models (PLMs) | Software Model | Serve as the base architecture for building classifier-based detectors. | RoBERTa-Large [49] |
| AI Text Generators | Software Model | Used to create positive samples for training and testing detectors. | GPT-4, LLaMA, Gemini [102] |
| Paraphrasing Tools | Software Model | Used to generate evasion attacks and conduct adversarial training to improve detector robustness. | DIPPER, instruction-tuned LLaMA-3-8B [49] |
| Benchmark Datasets | Data | Curated collections of human and AI-generated text for training and standardised evaluation. | MAGE dataset [49] |
| Zero-Shot Detection Tools | Software Algorithm | Provide a training-free baseline for detection; useful for ensemble methods. | DetectGPT, Fast-DetectGPT [49] |
| Watermarking Schemes | Software Algorithm | A proactive detection method that embeds a statistical signal during text generation. | KGW (Green-Red List) [49], Unigram watermark [49] |
Visualizing the Adversarial Paraphrasing Attack
The following diagram illustrates the "Adversarial Paraphrasing" attack, a significant threat to current detectors.
Diagram: Adversarial Paraphrasing Attack Workflow
Conclusion
The development of transferable supervised detectors is not merely a technical challenge but a fundamental requirement for maintaining trust and integrity in AI-augmented biomedical research. By synthesizing the key takeaways—that robust detection hinges on domain-invariant feature engineering, proactive strategies to counter model evolution, and rigorous cross-domain validation—this framework provides a actionable path forward. The implications for biomedical and clinical research are profound. As AI becomes further embedded in tasks from literature synthesis to clinical report writing, reliable detection tools will be crucial for peer review, regulatory compliance, and upholding scientific authenticity. Future efforts must focus on creating large-scale, domain-specific benchmark datasets and fostering collaboration between AI researchers and biomedical professionals to develop detectors that are as sophisticated and adaptive as the AI systems they are designed to identify.
References
- 1. AI Chatbots Can Run With Medical Misinformation, Study ... [https://www.mountsinai.org/about/newsroom/2025/ai-chatbots-can-run-with-medical-misinformation-study-finds-highlighting-the-need-for-stronger-safeguards]
- 2. How Reliable Are AI-Generated-Text Detectors? An ... [https://arxiv.org/html/2310.05095]
- 3. Do humans identify AI-generated text better than machines ... [https://www.sciencedirect.com/science/article/pii/S1477388025000131]
- 4. How Automation Overcomes Variability & Limitations in ... [https://dispendix.com/blog/how-automation-overcomes-variability-limitations-in-hts-troubleshooting]
- 5. A Survey of AI-generated Text Forensic Systems [https://arxiv.org/abs/2403.01152]
- 6. AI Detection Troubleshooting FAQ: Complete Questions ... [https://aihandshake.org/resources/faq/ai-detection-troubleshooting-faq]
- 7. Span-level Detection of AI-generated Scientific Text via ... [https://arxiv.org/html/2510.00890v1]
- 8. AI in Digital Forensics: a Tool, not an Oracle [https://blog.elcomsoft.com/2025/10/ai-in-digital-forensics-a-tool-not-an-oracle/]
- 9. Demystifying How AI Text Detection Works [https://medium.com/@ayoakin/demystifying-how-ai-text-detection-works-acca1c139916]
- 10. PDA: Generalizable Detection of AI-Generated Images via ... [https://arxiv.org/abs/2502.10803]
- 11. Multiscale Positive-Unlabeled Detection of AI-Generated ... [https://arxiv.org/html/2305.18149v4]
- 12. RADAR: Robust AI-Text Detection via Adversarial Learning [https://arxiv.org/html/2307.03838v1]
- 13. Generative AI Detection Tools: The Problems with AI Detectors ... [https://lawlibguides.sandiego.edu/c.php?g=1443311&p=10721367]
- 14. AI Detectors Don't Work. Here's What to Do Instead. [https://mitsloanedtech.mit.edu/ai/teach/ai-detectors-dont-work/]
- 15. Jamais Vu: Exposing the Generalization Gap in Supervised ... [https://arxiv.org/abs/2506.08220]
- 16. Evaluating the Generalization Gaps of Intrusion Detection ... [https://www.mdpi.com/2624-800X/5/4/85]
- 17. Discovery of a Generalization Gap of Convolutional Neural ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8224464/]
- 18. Exposing the Generalization Gap in Supervised Semantic ... [https://arxiv.org/html/2506.08220v1]
- 19. Boosting Generative Adversarial Transferability with Self- ... [https://arxiv.org/html/2506.21046v1]
- 20. A semi-supervised learning approach to classify drug ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11903007/]
- 21. Improving Adversarial Transferability via Semantic-Style ... [https://www.sciencedirect.com/science/article/abs/pii/S0031320325011379]
- 22. AI-driven target discovery: it's a journey [https://www.owkin.com/blogs-case-studies/ai-driven-target-discovery-its-a-journey]
- 23. Drug Discovery Assays Support—Troubleshooting [https://www.thermofisher.com/us/en/home/technical-resources/technical-reference-library/drug-discovery-development-support-center/drug-discovery-assays-support/drug-discovery-assays-support-troubleshooting.html]
- 24. A foundation model for clinician-centered drug repurposing [https://www.nature.com/articles/s41591-024-03233-x]
- 25. The Potential Applications of Artificial Intelligence in Drug ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9054182/]
- 26. RNAscope Troubleshooting Guide and FAQ [https://acdbio.com/technical-support/solutions]
- 27. Common Words and Phrases in AI-Generated Text [https://www.grammarly.com/blog/ai/common-ai-words/]
- 28. Study: Punctuation in text messages helps replace cues ... [https://www.binghamton.edu/news/story/873/study-punctuation-in-text-messages-helps-replace-cues-found-in-face-to-face]
- 29. Benchmarking Linguistic Diversity of Large Language ... [https://arxiv.org/html/2412.10271v1]
- 30. Stylometry-based Approach for Detecting Writing Style Changes in... [https://scielo.org.mx/scielo.php?pid=S1405-55462018000100047&script=sci_arttext]
- 31. What is transfer learning? [https://www.ibm.com/think/topics/transfer-learning]
- 32. Transfer learning in AI: A complete guide [https://www.scribbledata.io/blog/transfer-learning-in-ai-a-complete-guide/]
- 33. Comprehensive Guide to Spotting AI Writing Patterns [https://www.pangram.com/blog/comprehensive-guide-to-spotting-ai-writing-patterns]
- 34. A Gentle Introduction to Transfer Learning | by Ambika [https://medium.com/aimonks/a-gentle-introduction-to-transfer-learning-77fcc55f180d]
- 35. Measure Lexical Diversity | Lexical Analysis [https://textinspector.com/help/lexical-diversity/]
- 36. Listen Up! How You Use Punctuation in Texts? It Matters. A Lot. [https://www.lx.com/science-tech/listen-up-how-you-use-punctuation-in-texts-it-matters-a-lot/37126/]
- 37. Enhancing the Robustness of AI-Generated Text Detectors [https://www.mdpi.com/2227-7390/13/13/2145]
- 38. A Comprehensive Dataset for Human vs. AI Generated ... [https://arxiv.org/html/2510.22874v1]
- 39. Responsible Detection and Mitigation of AI-Generated Text ... [https://link.springer.com/article/10.1007/s44196-025-01025-w]
- 40. AI-generated text detection: A comprehensive review of ... [https://www.sciencedirect.com/science/article/abs/pii/S1574013725000693]
- 41. Techniques and Challenges in Detecting AI-Generated Text [https://arxiv.org/html/2403.05750v1]
- 42. Uniform Information Density Research Papers [https://www.academia.edu/Documents/in/Uniform_Information_Density]
- 43. Revisiting the Uniform Information Density Hypothesis [https://aclanthology.org/2021.emnlp-main.74/]
- 44. Perplexity [https://en.wikipedia.org/wiki/Perplexity]
- 45. Perplexity for LLM Evaluation - Comet [https://www.comet.com/site/blog/perplexity-for-llm-evaluation/]
- 46. The Unseen Biases of AI Text Detection Software [https://technicaeditorial.com/the-unseen-biases-of-ai-text-detection-software/]
- 47. Navigating the Challenges of Energy-Based Model Training [https://medium.com/thedeephub/beyond-the-gradient-navigating-the-challenges-of-energy-based-model-training-03987f37e818]
- 48. Energy-Based Models (EBMs) [https://schneppat.com/energy-based-models_ebms.html]
- 49. A Universal Attack for Humanizing AI-Generated Text [https://arxiv.org/html/2506.07001v1]
- 50. Energy-Based Transformers are Scalable Learners and ... [https://arxiv.org/html/2507.02092v1]
- 51. System 2 thinking with Energy-Based World Models - TechTalks [https://bdtechtalks.substack.com/p/system-2-thinking-with-energy-based]
- 52. Residual Energy-Based Models for Text Generation [https://ai.meta.com/research/publications/residual-energy-based-models-for-text-generation/]
- 53. Unveiling Topological Structures in Text: A Comprehensive ... [https://arxiv.org/html/2411.10298v1]
- 54. Machine learning and topological data analysis identify ... [https://www.nature.com/articles/s41598-023-46535-9]
- 55. HEDN: A Hard-Easy Dual Network with Task Difficulty ... [https://arxiv.org/html/2511.06782v1]
- 56. Detection of AI Generated Texts Using Deep Learning and ... [https://link.springer.com/chapter/10.1007/978-3-031-97907-1_6]
- 57. AdaUchendu/AwesomeTDA4NLP: Topological Data ... [https://github.com/AdaUchendu/AwesomeTDA4NLP]
- 58. TDACNN: Target-domain-free domain adaptation ... [https://www.sciencedirect.com/science/article/abs/pii/S0925400522003811]
- 59. Track: Poster Session 3 East [https://icml.cc/virtual/2025/session/50265]
- 60. Topological Data Analysis for Neural Network ... [https://arxiv.org/html/2312.05840v2]
- 61. Federated transfer learning for rare attack class detection ... [https://www.nature.com/articles/s41598-025-02068-x]
- 62. IDS-INT: Intrusion detection system using transformer ... [https://www.sciencedirect.com/science/article/pii/S2352864823000640]
- 63. Cybersecurity challenges and opportunities of machine ... [https://link.springer.com/article/10.1007/s00521-025-11604-9]
- 64. Editorial: Machine learning for cybersecurity [https://www.frontiersin.org/journals/artificial-intelligence/articles/10.3389/frai.2025.1640609/full]
- 65. 5G Security Risks 2025: Mitigation Plan [https://www.onlinehashcrack.com/guides/cybersecurity-trends/5g-security-risks-2025-mitigation-plan.php]
- 66. 5G Security Challenges and Solutions: A Network ... [https://www.abiresearch.com/blog/5g-security-challenges-and-solutions]
- 67. Best Practices for Mobile Data Protection in 2025 [https://symmetrium.io/best-practices-for-mobile-data-protection-in-2025/]
- 68. A deep dive into addressing obsolescence in product design: A review - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC10665736/]
- 69. Weakly-supervised anomaly detection based on ... [https://www.sciencedirect.com/science/article/abs/pii/S0952197625009753]
- 70. Cross-Domain Few-Shot Object Detection via Enhanced ... [https://arxiv.org/html/2402.03094v3]
- 71. CDFormer: Cross-Domain Few-Shot Object Detection ... [https://arxiv.org/html/2505.00938v1]
- 72. Balanced ID-OOD tradeoff transfer makes query based ... [https://www.sciencedirect.com/science/article/pii/S2667295224000400]
- 73. Domain-RAG: Retrieval-Guided Compositional Image ... [https://openreview.net/forum?id=p2EycV4XOa&referrer=%5Bthe%20profile%20of%20Danda%20Pani%20Paudel%5D(%2Fprofile%3Fid%3D~Danda_Pani_Paudel3)]
- 74. Cross-Domain Few-Shot Object Detection via Enhanced ... [https://github.com/lovelyqian/CDFSOD-benchmark]
- 75. An Augmentation-Search Strategy with Foundation Models ... [https://arxiv.org/abs/2504.04517]
- 76. lovelyqian/NTIRE2025_CDFSOD: NTIRE 2025 Challenge ... [https://github.com/lovelyqian/NTIRE2025_CDFSOD]
- 77. What is Knowledge distillation? | IBM [https://www.ibm.com/think/topics/knowledge-distillation]
- 78. Knowledge Distillation: Empowering Efficient AI Models [https://kargarisaac.medium.com/knowledge-distillation-empowering-efficient-ai-models-2505b7781045]
- 79. A survey on knowledge distillation: Recent advancements [https://www.sciencedirect.com/science/article/pii/S2666827024000811]
- 80. A Comprehensive Survey on Knowledge Distillation [https://arxiv.org/html/2503.12067v2]
- 81. Feature knowledge distillation-based model lightweight for ... [https://www.sciencedirect.com/science/article/abs/pii/S1474034625000187]
- 82. Why Model Distillation Is Making a Comeback in 2025 [https://medium.com/@thekzgroupllc/why-model-distillation-is-making-a-comeback-in-2025-1c74e989d5cc]
- 83. LEAF: Knowledge Distillation of Text Embedding Models ... [https://arxiv.org/abs/2509.12539]
- 84. The accuracy-bias trade-offs in AI text detection tools and ... [https://peerj.com/articles/cs-2953/]
- 85. How to interpret a confusion matrix for a machine learning ... [https://www.evidentlyai.com/classification-metrics/confusion-matrix]
- 86. Confusion Matrix Made Simple: Accuracy, Precision, Recall ... [https://towardsdatascience.com/confusion-matrix-made-simple-accuracy-precision-recall-f1-score/]
- 87. Understanding the Confusion Matrix in Machine Learning [https://www.geeksforgeeks.org/machine-learning/confusion-matrix-machine-learning/]
- 88. AI Detection and assessment - an update for 2025 [https://nationalcentreforai.jiscinvolve.org/wp/2025/06/24/ai-detection-assessment-2025/]
- 89. Classification: Accuracy, recall, precision, and related metrics [https://developers.google.com/machine-learning/crash-course/classification/accuracy-precision-recall]
- 90. Evaluation Metrics in Machine Learning [https://www.geeksforgeeks.org/machine-learning/metrics-for-machine-learning-model/]
- 91. 12 Important Model Evaluation Metrics for Machine ... [https://www.analyticsvidhya.com/blog/2019/08/11-important-model-evaluation-error-metrics/]
- 92. - Zero Learning: A Practical Guide Shot [https://www.lightly.ai/blog/zero-shot-learning]
- 93. A review on NLP zero-shot and few-shot learning: methods ... [https://link.springer.com/article/10.1007/s42452-025-07225-5]
- 94. A Zero-Shot Learning Approach for Blockage Detection ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11397788/]
- 95. Best Object Detection Models 2025 : RF-DETR, YOLOv12 & Beyond [https://blog.roboflow.com/best-object-detection-models/]
- 96. Building Expert AI With Domain-Specific Data [https://www.ayadata.ai/building-expert-ai-with-domain-specific-data/]
- 97. Transferring self-supervised pre-trained models for SHM ... [https://arxiv.org/abs/2412.03880]
- 98. Maximizing NLP Effectiveness with the Right Text Datasets [https://www.sapien.io/blog/maximizing-nlp-effectiveness-with-the-right-text-datasets]
- 99. Visual and Semantic Knowledge Transfer for Large Scale ... [https://pubmed.ncbi.nlm.nih.gov/29990152/]
- 100. Multi-Modal AI-Ready Datasets for Clinical Trial Prediction [https://pmc.ncbi.nlm.nih.gov/articles/PMC12475113/]
- 101. AI and Plagiarism Detection Software: A Comparative Guide [https://academictech.uchicago.edu/detection-software/]
- 102. Charting Truth, Trust, and Transformers: A Critical Look at AI ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12503764/]