Building Better Evidence: A Comprehensive Guide to Developing Forensic Text Comparison Datasets
This article provides a structured framework for researchers and forensic professionals developing datasets for forensic text comparison (FTC).
Building Better Evidence: A Comprehensive Guide to Developing Forensic Text Comparison Datasets
Abstract
This article provides a structured framework for researchers and forensic professionals developing datasets for forensic text comparison (FTC). It explores the foundational principles of FTC, including the linguistic basis of authorship and the critical role of empirical validation. The guide details modern methodological approaches, from leveraging Large Language Models (LLMs) for synthetic data generation to constructing Question-Context-Answer (Q-C-A) formats. It addresses key challenges such as algorithmic bias, topic mismatch, and data scarcity, offering practical optimization strategies. Furthermore, the article establishes a robust validation framework centered on the Likelihood Ratio (LR) and comparative performance analysis, aiming to advance the creation of reliable, forensically relevant datasets that meet the stringent demands of legal admissibility and scientific rigor.
The Linguistic and Evidential Basis of Forensic Text Comparison
An idiolect refers to the unique and distinctive language use of an individual speaker or writer. This linguistic fingerprint encompasses vocabulary preferences, syntactic patterns, grammatical idiosyncrasies, and other stylistic features that remain consistent across an individual's texts. In forensic authorship analysis, the systematic examination of idiolect provides the theoretical foundation for determining authorship of questioned documents, whether in criminal investigations, civil litigation, or academic integrity cases. The development of robust datasets and standardized protocols for idiolect analysis represents a critical research direction for advancing the scientific rigor of forensic text comparison.
The idiolect R package provides a comprehensive suite of tools specifically designed for comparative authorship analysis within a forensic context using the Likelihood Ratio Framework [1]. This package implements several authorship analysis methods that process sets of texts and output scores that can be calibrated into likelihood ratios, offering a statistically grounded approach to quantifying the strength of authorship evidence. Dependent on the quanteda package for natural language processing functions, idiolect enables researchers to perform sophisticated analyses while maintaining methodological transparency [1] [2].
Experimental Protocols for Authorship Analysis
Corpus Creation and Preprocessing Protocol
Purpose: To create a standardized textual corpus suitable for authorship analysis.
Materials Required:
- Digital text documents from known and questioned authors
- R statistical software environment
idiolectandquantedaR packages
Procedure:
- Data Collection: Gather text documents of sufficient length (typically > 500 words per document) from potential authors. Ensure documents are in plain text format (.txt).
- Corpus Initialization: Use the
create_corpus()function from theidiolectpackage to import texts into a structured corpus object [1]. - Text Cleaning:
- Remove extraneous formatting, headers, and footers
- Normalize text by converting to lowercase
- Handle special characters and punctuation appropriately
- Content Masking (Optional): Apply the
contentmask()function to reduce topic-dependent vocabulary, focusing analysis on stylistic rather than content features [1]. - Feature Extraction: Transform texts into document-feature matrices capturing lexical, syntactic, or character-level features.
Troubleshooting Tips:
- For imbalanced corpora, consider stratified sampling approaches
- Validate text encoding to prevent character recognition errors
- Document all preprocessing decisions for methodological transparency
Authorship Method Application Protocol
Purpose: To apply computational authorship analysis methods to distinguish between authors.
Materials Required:
- Preprocessed textual corpus
- R software with
idiolectpackage installed - High-performance computing resources for large datasets
Procedure:
- Feature Selection: Identify the linguistic features to analyze (e.g., function words, character n-grams, syntactic patterns).
- Method Selection: Choose appropriate authorship analysis methods based on research questions:
- Method Application: Execute selected methods using corresponding functions in the
idiolectpackage. - Performance Validation: Test method performance on ground truth data using the
performance()function to evaluate accuracy metrics [1]. - Likelihood Ratio Calibration: Apply
calibrate_LLR()to questioned texts to generate likelihood ratios quantifying evidence strength [1].
Quality Control Measures:
- Implement cross-validation procedures
- Establish confidence intervals for accuracy metrics
- Document all parameter settings and methodological choices
Validation and Likelihood Ratio Framework Protocol
Purpose: To validate authorship analysis results and express findings within the Likelihood Ratio framework.
Materials Required:
- Processed output from authorship analysis methods
- Ground truth data for validation
- R software with
idiolectpackage
Procedure:
- Performance Assessment: Use the
performance()function to evaluate method accuracy on texts with known authorship, generating metrics such as precision, recall, and AUC values [1]. - Likelihood Ratio Calculation: Apply the
calibrate_LLR()function to questioned texts to compute likelihood ratios that quantify the strength of evidence for authorship hypotheses [1]. - Uncertainty Quantification: Calculate confidence intervals for likelihood ratios using bootstrapping or other resampling methods.
- Sensitivity Analysis: Test the robustness of results to different parameter settings and feature selections.
- Result Interpretation: Frame conclusions according to the Likelihood Ratio framework, avoiding categorical claims of authorship.
Interpretation Guidelines:
- Likelihood ratios > 1 support the prosecution hypothesis
- Likelihood ratios < 1 support the defense hypothesis
- Likelihood ratios close to 1 provide limited evidential value
- Always report confidence intervals and methodological limitations
Data Presentation and Analysis
Table 1: Performance Metrics of Authorship Analysis Methods
| Method | Precision | Recall | F1-Score | AUC-ROC | Optimal Text Length |
|---|---|---|---|---|---|
| Delta | 0.85 | 0.82 | 0.835 | 0.89 | > 1,000 words |
| N-gram Tracing | 0.88 | 0.79 | 0.833 | 0.91 | > 500 words |
| Impostors Method | 0.92 | 0.85 | 0.884 | 0.94 | > 1,500 words |
| LambdaG | 0.94 | 0.89 | 0.914 | 0.96 | > 800 words |
Table 2: Feature Type Performance in Authorship Attribution
| Feature Category | Sample Features | Accuracy (%) | Cross-Author Stability | Topic Resistance |
|---|---|---|---|---|
| Function Words | "the", "and", "of", "to" | 78.3 | High | High |
| Character N-grams | "ing", "the_" | 85.7 | Medium | High |
| Syntactic Patterns | POS tag sequences | 82.4 | High | Medium |
| Vocabulary Richness | Type-token ratio | 65.2 | Low | Low |
| Punctuation Patterns | Comma usage frequency | 71.8 | Medium | High |
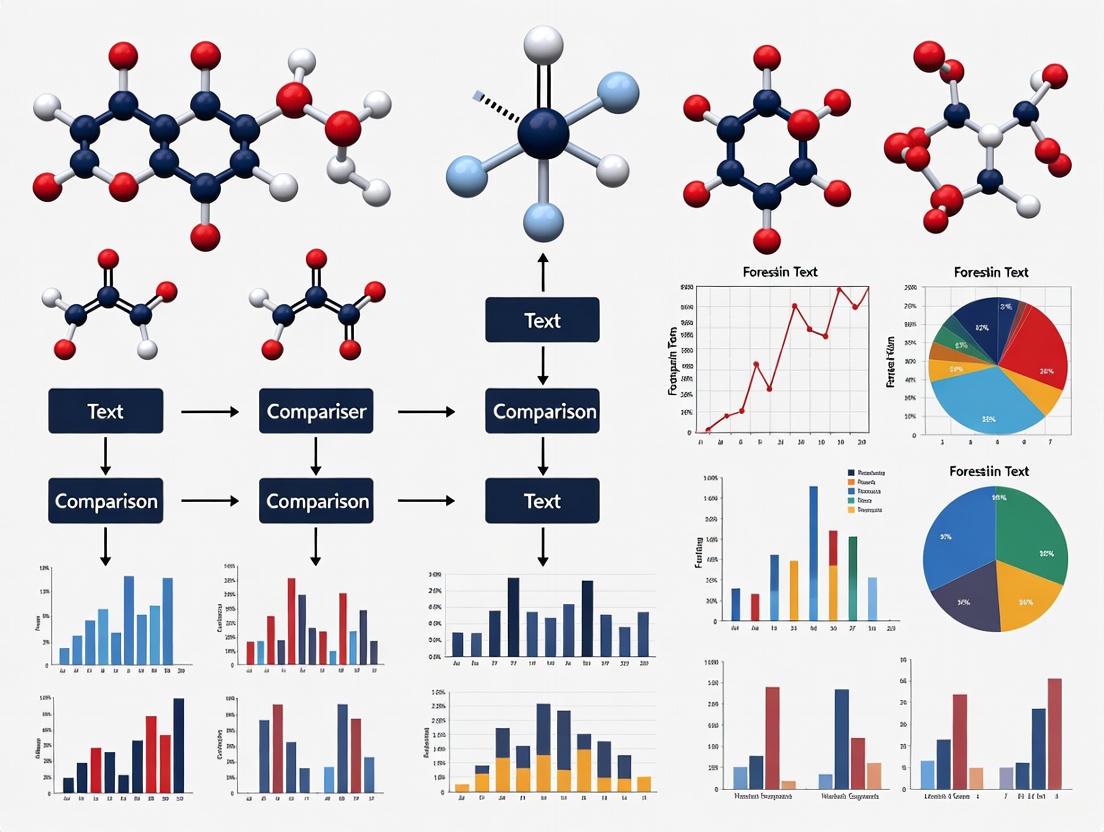
Workflow Visualization
Forensic Authorship Analysis Workflow
Linguistic Feature Analysis Pipeline
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for Forensic Authorship Research
| Tool/Resource | Function | Application Context |
|---|---|---|
| idiolect R Package | Provides comprehensive suite for comparative authorship analysis using Likelihood Ratio Framework | Primary analysis tool for forensic text comparison [1] |
| quanteda R Package | Natural language processing infrastructure for text analysis | Required dependency for text preprocessing and feature extraction [1] |
| MAXDictio/MAXQDA | Quantitative text analysis with vocabulary and dictionary-based analysis | Alternative commercial solution for quantitative content analysis [3] |
| ForensicsData Dataset | Extensive Question-Context-Answer dataset from malware reports | Model dataset for forensic text analysis development [4] |
| PubMed Central Corpus | 15 million full-text scientific articles for methodological validation | Large-scale corpus for testing authorship methods [5] |
| ANY.RUN Platform | Malware analysis reports for forensic dataset development | Source of authentic forensic texts for dataset creation [4] |
| LambdaG Method | Advanced authorship analysis method with improved performance | State-of-the-art technique for authorship attribution [2] |
The Likelihood Ratio (LR) framework is widely recognized as the logically and legally correct approach for evaluating the strength of forensic evidence, including textual evidence in forensic text comparison (FTC) [6]. It provides a transparent, reproducible, and quantitative method that is intrinsically resistant to cognitive bias, making it particularly suitable for scientific and legal applications [6]. The core of this framework is a formula that compares the probability of the observed evidence under two competing hypotheses [6]:
LR = p(E|Hp) / p(E|Hd)
In this equation, p(E|Hp) represents the probability of observing the evidence (E) given that the prosecution hypothesis (Hp) is true, while p(E|Hd) represents the probability of the same evidence given that the defense hypothesis (Hd) is true [6]. In practical terms, these probabilities can be interpreted as measuring similarity (how similar the compared texts are) and typicality (how distinctive this similarity is within the relevant population) [6].
The LR framework logically updates the beliefs of the trier-of-fact through Bayes' Theorem, which in its odds form states [6]:
Prior Odds × LR = Posterior Odds
This means that the fact-finder's prior belief about the hypotheses (prior odds) is rationally updated by the strength of the forensic evidence (LR) to form a new belief (posterior odds) [6]. Critically, the forensic scientist's role is limited to presenting the LR, as they are not positioned to know the fact-finder's prior beliefs, and venturing into posterior probabilities would encroach on the ultimate issue of guilt or innocence [6].
Essential Principles for Validation
For LR-based systems to be scientifically defensible, they must undergo rigorous empirical validation. Research in forensic science broadly, and in FTC specifically, indicates that proper validation must fulfill two critical requirements [6]:
- Reflecting Casework Conditions: The experimental design must replicate the conditions of the case under investigation.
- Using Relevant Data: The data used for validation must be appropriate and relevant to the specific case.
These requirements are crucial because the presence of mismatches between compared documents (e.g., in topics, genres, or communicative situations) can significantly impact system performance [6]. The complex nature of textual data, where writing style is influenced by multiple factors including the author's idiolect, social background, and immediate context, makes validation under realistic conditions essential for reliable results [6].
Table 1: Key Requirements for Empirical Validation of LR Systems in FTC
| Requirement | Description | Implication for FTC Research |
|---|---|---|
| Casework Condition Replication | Experimental setup must mirror the conditions of actual cases under investigation. | Researchers must identify and simulate realistic mismatches (e.g., in topics, genres) that occur in real forensic texts [6]. |
| Use of Relevant Data | Data used for validation must be appropriate to the case circumstances. | Dataset collection must prioritize authenticity and relevance, including factors like text type, topic variation, and author demographics [6]. |
| Quantitative Measurement | Use of numerical measurements of evidential properties. | Relies on computational text analysis, such as stylometric features (e.g., vocabulary richness, punctuation patterns) [7]. |
| Statistical Modeling | Application of probabilistic models to interpret the measured data. | Implementation of statistical models (e.g., Multivariate Kernel Density, Poisson models) for LR calculation [7] [8]. |
Experimental Protocols for FTC Research
Core Protocol: LR-Based Authorship Analysis with Stylometric Features
This protocol outlines a methodology for evaluating the strength of authorship attribution evidence using word- and character-based stylometric features within the LR framework, based on published research [7].
Purpose: To quantify the strength of evidence for authorship attribution using multivariate likelihood ratios and to investigate the effect of sample size on system performance.
Materials and Reagents:
- Text Corpora: Collection of texts from multiple authors. The protocol used chatlog messages from 115 authors in a real forensic context [7].
- Text Analysis Software: Tools for extracting stylometric features from texts (e.g., vocabulary richness, average characters per word, punctuation ratios) [7].
- Statistical Computing Environment: Software capable of implementing the Multivariate Kernel Density formula and calculating log-likelihood ratio costs (Cllr), such as R or Python with appropriate statistical libraries [7].
Procedure:
- Text Preparation:
- Select authentic text samples relevant to the forensic context (e.g., chatlogs, reviews, emails).
- For each author, create text samples of varying lengths (e.g., 500, 1000, 1500, and 2500 words) to analyze the impact of sample size [7].
- Feature Extraction:
- For each text sample, extract a set of stylometric features. Robust features include [7]:
- Average character number per word token
- Punctuation character ratio
- Vocabulary richness measures
- For each text sample, extract a set of stylometric features. Robust features include [7]:
- Likelihood Ratio Calculation:
- System Performance Assessment:
- Data Analysis:
- Compare discrimination accuracy across different sample sizes.
- Analyze the magnitude of LRs that are consistent-with-fact versus those that are contrary-to-fact [7].
Expected Outcomes:
- The system should achieve higher discrimination accuracy with larger sample sizes (e.g., approximately 76% with 500 words versus 94% with 2500 words, as reported in one study) [7].
- Larger sample sizes should improve discriminability, increase the magnitude of correct LRs, and decrease the magnitude of incorrect LRs [7].
- Features such as 'Average character number per word token', 'Punctuation character ratio', and vocabulary richness measures should demonstrate robustness across varying sample sizes [7].
Advanced Protocol: Feature-Based Comparison Using a Poisson Model
This protocol describes a feature-based method for forensic text comparison using a Poisson model for likelihood ratio estimation, which has demonstrated advantages over traditional score-based methods [8].
Purpose: To implement a feature-based LR estimation method that accounts for both similarity and typicality, overcoming limitations of distance-based measures.
Materials and Reagents:
- Text Corpora: Large collection of texts from numerous authors (e.g., 2,157 authors) to ensure robust background population representation [8].
- Computational Linguistics Tools: Software for extracting linguistic features from text corpora.
- Statistical Software: Environment capable of implementing Poisson models and calculating Cosine distances for comparative analysis.
Procedure:
- Data Collection:
- Gather a substantial dataset of texts from a wide array of authors to build a representative background population [8].
- Methodology Comparison:
- Implement a score-based method using Cosine distance as a baseline, as distance measures are standard in authorship attribution studies [8].
- Implement a feature-based method using a Poisson model, which is theoretically more appropriate for textual data as it can handle the violation of statistical assumptions common in distance-based models [8].
- Feature Selection:
- For the feature-based method, perform feature selection to identify the most discriminative linguistic features for authorship attribution [8].
- LR Estimation and Evaluation:
- Estimate LRs using both methods.
- Evaluate system performance using the log-likelihood ratio cost (Cllr) to compare the discrimination accuracy of both approaches [8].
Expected Outcomes:
- The feature-based Poisson model method is expected to outperform the score-based Cosine distance method by a measurable Cllr value (approximately 0.09 under optimal settings) [8].
- Feature selection should further improve the performance of the feature-based method [8].
- The feature-based method should provide more reliable LR estimates as it assesses both similarity and typicality, unlike distance-based models that primarily measure similarity [8].
Visualization of Workflows
LR Framework Logic and Application
Experimental Validation Workflow
The Researcher's Toolkit
Table 2: Essential Research Reagents and Materials for FTC-LR Research
| Tool/Category | Specific Examples | Function in FTC-LR Research |
|---|---|---|
| Text Corpora | Amazon Authorship Verification Corpus (AAVC) [6], Forensic Chatlog Archives [7] | Provides authentic textual data for developing and validating LR systems; enables testing under realistic conditions including topic mismatch. |
| Stylometric Features | Vocabulary Richness, Punctuation Character Ratio, Average Characters Per Word [7] | Serves as measurable linguistic elements that capture authorial style; used as variables in statistical models for LR calculation. |
| Statistical Models | Multivariate Kernel Density Formula [7], Poisson Models [8] | Provides the mathematical framework for calculating likelihood ratios from observed textual features; translates similarity and typicality into quantitative LRs. |
| Performance Metrics | Log-Likelihood Ratio Cost (Cllr) [7] [8], Tippett Plots [6] | Assesses the discrimination accuracy and validity of the LR system; Cllr provides an overall measure of system performance across all LRs. |
| Validation Frameworks | Casework-Replication Protocol, Relevant-Data Requirement [6] | Ensures empirical validation reflects real forensic conditions; critical for establishing scientific defensibility and demonstrable reliability of FTC methods. |
Forensic text comparison (FTC) is a scientific discipline that involves the analysis and interpretation of textual evidence for legal purposes. The core challenge resides in establishing a methodology that ensures results are not only scientifically sound but also legally admissible in court. The admissibility of forensic evidence, including textual analysis, is often judged against standards such as the Daubert Standard, which provides a legal framework for assessing the reliability and validity of scientific evidence [9] [10]. This standard emphasizes several key factors: the testability of the methods used, their submission to peer review, the establishment of known error rates, and the general acceptance of the methodologies within the relevant scientific community [9] [10].
A scientifically defensible approach to FTC increasingly relies on a framework incorporating quantitative measurements, statistical models, and the Likelihood Ratio (LR) as a measure of evidentiary strength [6]. The LR quantitatively expresses the probability of the evidence under two competing hypotheses: the prosecution hypothesis (Hp) and the defense hypothesis (Hd) [6]. Crucially, the empirical validation of any FTC system or methodology must be performed by replicating the conditions of the case under investigation and using data relevant to that specific case [6]. Failure to do so risks producing misleading results and compromises the legal admissibility of the evidence.
Core Data Requirements for Forensic Relevance
For a data set to be considered forensically relevant and to satisfy the prerequisites for legal admissibility, it must be constructed with specific, rigorous criteria in mind. These requirements ensure that the analysis is both scientifically robust and applicable to the context of a real-world investigation.
Table 1: Core Data Requirements for Forensic Text Comparison
| Requirement Category | Description | Legal/Scientific Rationale |
|---|---|---|
| Casework Relevance | Data must reflect the specific conditions of the case under investigation, including potential confounding factors like topic mismatch between known and questioned documents [6]. | Ensures external validity and meets Daubert's requirement for reliable application to case facts. |
| Data Authenticity & Integrity | The provenance and integrity of data must be verifiable, often through hash validation and a documented chain of custody [11]. | Authenticity is a foundational requirement for evidence admissibility under rules of evidence (e.g., Rule 901) [11]. |
| Representative Sampling | Data must be representative of the population of potential authors and the stylistic variations within a single author's idiolect. | Strengthens the statistical model's accuracy and the reliability of the calculated Likelihood Ratio [6]. |
| Quantitative Measurement | Data must be amenable to quantitative feature extraction (e.g., lexical, syntactic, character-level features). | Moves analysis from subjective opinion to objective, testable science, satisfying a key Daubert factor [6]. |
| Metadata Completeness | Data should be accompanied by relevant metadata (e.g., genre, topic, creation date, medium) to control for stylistic covariates. | Allows for proper experimental design and validation under controlled, case-realistic conditions [6]. |
Beyond the requirements outlined in Table 1, researchers must account for the complexity of textual evidence. A text encodes not only information about its authorship but also about the author's social group and the communicative situation (e.g., topic, genre, formality) [6]. A forensically relevant data set must therefore allow for the isolation of authorship signals from these other confounding factors. The concept of "idiolect"—an individual's distinctive way of speaking and writing—is central to this endeavor and is compatible with modern theories of language processing [6].
Experimental Protocols for Validation
To validate an FTC methodology and establish its error rates, a structured experimental protocol is essential. The following provides a detailed methodology for a validation study targeting a specific case condition, such as topic mismatch.
Protocol: Validation under Topic Mismatch Conditions
1. Objective: To empirically determine the performance and reliability of a forensic text comparison system when the known and questioned documents exhibit a mismatch in topic.
2. Hypotheses:
- Hp (Prosecution Hypothesis): The questioned and known documents were written by the same author.
- Hd (Defense Hypothesis): The questioned and known documents were written by different authors.
3. Experimental Design:
- Data Collection & Curation: Assemble a corpus of documents from multiple authors. For each author, collect texts written on multiple distinct topics. The topics should be sufficiently different to represent a realistic challenge for the authorship attribution model.
- Data Partitioning: For each author, designate one topic as the "known" data and a different topic as the "questioned" data. This creates a cross-topic comparison scenario.
- Likelihood Ratio Calculation: For each author and topic pair, calculate the Likelihood Ratio (LR) using a pre-defined statistical model (e.g., a Dirichlet-multinomial model). The LR is computed as
LR = p(E|Hp) / p(E|Hd), whereErepresents the quantitative evidence extracted from the texts [6]. - Model Calibration: Apply a post-hoc calibration, such as logistic regression calibration, to the output LRs to improve their reliability and interpretability [6].
- Performance Assessment: Evaluate the calibrated LRs using metrics like the log-likelihood-ratio cost (Cllr) and visualize the results using Tippett plots [6]. These tools help assess the discrimination and calibration of the system, effectively establishing its "error rate."
4. Controls and Replication:
- The experiment should include same-author/different-topic and different-author/different-topic comparisons.
- Following best practices in digital forensics, key experiments should be performed in triplicate to establish repeatability metrics [9].
The following workflow diagram illustrates the key stages of this experimental protocol.
Experimental Workflow for FTC Validation
The Researcher's Toolkit for Forensic Text Comparison
The successful implementation of FTC research requires a suite of methodological tools and conceptual frameworks. The table below details essential components of the researcher's toolkit.
Table 2: Essential Research Reagent Solutions for Forensic Text Comparison
| Tool Category | Specific Example(s) | Function in FTC Research |
|---|---|---|
| Statistical Framework | Likelihood Ratio (LR), Bayes' Theorem | Provides a logically and legally sound method for evaluating and interpreting the strength of evidence [6]. |
| Computational Models | Dirichlet-Multinomial Model, n-gram models, Deep Learning Models | Enables the quantitative analysis of textual data and the calculation of probabilities underpinning the LR [6]. |
| Validation Software | LRmix Studio, STRmix, EuroForMix | Software platforms (from related forensic fields) that demonstrate the implementation of qualitative and quantitative models for LR calculation and validation [12]. |
| Performance Metrics | Log-Likelihood-Ratio Cost (Cllr), Tippett Plots | Used to empirically assess the validity, discrimination, and calibration of a forensic inference system, thereby establishing its reliability and error rates [6]. |
| Data Integrity Tools | Hash Validation (e.g., MD5, SHA-256), Chain-of-Custody Documentation | Critical for maintaining and demonstrating the authenticity and integrity of digital evidence from collection to analysis [11]. |
The following diagram illustrates the logical and procedural relationships between the core components of the FTC research process, from data preparation to legal presentation.
Core Logical Flow for FTC Research
Application Note: Understanding the Core Challenges
The development of forensically relevant datasets for text comparison research is fundamentally constrained by a triad of interconnected challenges: the scarcity of representative data, stringent privacy protections, and multifaceted legal restrictions. These barriers impede the creation of standardized evaluation frameworks and hinder the validation of methods under true casework conditions.
Dataset Scarcity arises from the absence of large-scale, realistic collections that mirror the complex variables encountered in forensic casework. The Forensic Handwritten Document Analysis Challenge 2025 highlights this by creating a novel dataset specifically to address the need for diverse handwriting styles, writing instruments, and environmental conditions for cross-modal authorship verification [13]. Furthermore, the problem extends to the nuanced representation of casework conditions. Research demonstrates that validation must be performed using data relevant to the specific case under investigation, including factors like topic mismatch between documents, which significantly impacts the reliability of forensic text comparison methods [6].
Privacy Considerations are paramount, especially when dealing with personal communications like text messages or social media data. The handling of such data is governed by strict legal frameworks. Research into the forensic analysis of social media data for criminal investigations underscores the critical need to adhere to privacy laws such as GDPR and country-specific jurisdiction guidelines, often requiring legal warrants or subpoenas for access to private data [14]. The Clearview AI litigation globally exemplifies the heightened sensitivity surrounding biometric and personal data, where evidence of processing must meticulously document data collection, storage, and access patterns [15].
Legal Restrictions encompass both the admissibility of digital evidence in court and the legal authority to collect data. Courts increasingly demand technical proof over policy narratives, expecting reproducible evidence like network logs and packet captures to prove data transfers and tracking [15]. For evidence to be admissible, the methods used must satisfy legal standards such as the Daubert Standard, which assesses factors like testability, peer review, error rates, and general acceptance by the scientific community [9]. The ISO 21043 international standard for forensic science further provides a framework to ensure the quality of the entire forensic process, from recovery to reporting [16].
Table 1: Core Challenges in Forensic Text Comparison Dataset Development
| Challenge | Key Aspects | Impact on Dataset Development |
|---|---|---|
| Dataset Scarcity | Lack of large-scale, realistic data; Need to represent diverse casework conditions (e.g., topic mismatch, writing modalities) [13] [6] | Limits model training and robust validation, risking poor real-world performance. |
| Privacy | Compliance with GDPR, CCPA, and other data protection laws; Sensitivity of personal communications and biometric data [14] [15] | Restricts data sourcing and sharing, necessitates anonymization and secure storage protocols. |
| Legal Restrictions | Admissibility standards (e.g., Daubert); Legal authority for data collection (warrants, subpoenas); ISO 21043 forensic standards [16] [15] [9] | Dictates the methodologies for data acquisition and evidence handling to ensure judicial acceptance. |
Protocol for Developing a Forensically Relevant Text Dataset
This protocol outlines a standardized methodology for the collection, validation, and documentation of textual data intended for forensic comparison research, ensuring scientific rigor and compliance with legal and privacy norms.
Phase 1: Project Definition and Legal Scoping
Objective: Define the dataset's scope and establish a legally compliant foundation for data collection.
- Define Casework Conditions: Formally specify the
relevant conditionsthe dataset must reflect. This includes:- Modality: Scanned paper documents vs. digitally born documents (e.g., from tablets) [13].
- Topic Variation: Explicitly plan for and document topic mismatches between known and questioned text samples [6].
- Text Type: Define the genres and formats (e.g., formal letters, social media messages, handwritten notes).
- Legal Compliance Review:
- Identify all applicable privacy laws (e.g., GDPR, CCPA) based on the data source and jurisdiction [14] [15].
- Determine the lawful basis for data collection (e.g., explicit participant consent, court order, subpoena). For public data, review terms of service.
- Consult with legal experts to ensure the data collection and usage plan is court-defensible.
Phase 2: Data Acquisition and Preservation
Objective: Collect data using forensically sound methods that preserve integrity and chain of custody.
- Source Data Collection:
- Cloud/Server Data: For data from services like email or social media, issue legal processes (e.g., subpoenas) to the service provider to obtain data bundles. Avoid relying solely on screenshots [17].
- Device Data: Perform a
forensic acquisitionof the physical device (e.g., smartphone, computer) using specialized tools (e.g., Autopsy, FTK) to create a bit-for-bit copy. This captures deleted items and metadata and allows for integrity verification viacryptographic hash values(e.g., SHA-256) [9] [18] [17]. - Manual Examination (If acquisition is impossible): If a forensic acquisition is not feasible (e.g., with a witness's device), a manual examination may be conducted with strict documentation:
- Obtain written consent from the device owner.
- Perform a continuous
video recordingof the entire process, from power-on to navigating to and photographing the relevant messages. - Photograph the device, messages, and associated metadata [18].
- Preservation of Integrity:
Phase 3: Data Preparation and Validation
Objective: Process the raw data into a structured, research-ready dataset and validate its quality and representativeness.
- Anonymization and Redaction:
- Remove or redact all direct personal identifiers (names, addresses, phone numbers) and sensitive personal information to comply with privacy laws [14].
- Document all redaction procedures performed.
- Structuring and Annotation:
- Structure the data into pairs (questioned vs. known samples) with binary labels indicating whether they originate from the same author [13].
- Annotate the data with metadata detailing the
casework conditions, such as modality, topic, and writing instrument.
- Empirical Validation:
- Design validation experiments that test the dataset's utility. This involves using statistical models to calculate
Likelihood Ratios (LRs)and evaluating system performance using metrics like thelog-likelihood-ratio cost (Cllr)[6] [19]. - The validation must demonstrate that the dataset can be used to develop methods that are
calibrated and validated under casework conditions[16].
- Design validation experiments that test the dataset's utility. This involves using statistical models to calculate
Dataset Development Workflow
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Materials and Tools for Forensic Dataset Development
| Tool / Material | Function in Research |
|---|---|
| Cryptographic Hash Algorithms (SHA-256, MD5) | Provides a digital fingerprint for data, verifying the integrity of the forensic image and proving it has not been altered since collection [9] [17]. |
| Open-Source Forensic Tools (Autopsy, Sleuth Kit) | Cost-effective software for creating forensic acquisitions of digital devices. Their reliability for evidence admissibility is strengthened when used within a validated framework [9]. |
| Write-Blocking Hardware | A physical device that allows a computer to read data from a storage drive (e.g., HDD) without any possibility of writing to it, preserving evidence integrity [17]. |
| Likelihood Ratio (LR) Framework | The logically correct framework for interpreting forensic evidence strength. It quantifies the probability of the evidence under two competing hypotheses (same source vs. different sources) [6] [16] [19]. |
| Validation Metrics (Cllr, Tippett Plots) | Used to empirically validate the performance of a forensic method. Cllr measures the overall accuracy of the LR system, while Tippett plots visualize the distribution of LRs for same-source and different-source comparisons [6] [19]. |
| ISO 21043 Forensic Standard | An international standard providing requirements and recommendations to ensure the quality of the entire forensic process, from vocabulary and recovery to interpretation and reporting [16]. |
| Daubert Standard Criteria | A legal test used to assess the admissibility of expert scientific testimony. Guides researchers to ensure their methods are testable, peer-reviewed, have known error rates, and are generally accepted [9]. |
Modern Methods for Building Forensic Text Comparison Datasets
Leveraging Large Language Models (LLMs) for Synthetic Data Generation
The field of digital forensics faces a significant challenge: a scarcity of realistic, publicly available datasets for training and evaluating analytical tools due to stringent privacy regulations, legal restrictions, and the inherently sensitive nature of forensic evidence [4]. This data scarcity hampers the development of robust forensic tools and limits research reproducibility, particularly in specialized sub-fields like forensic text comparison [4]. Synthetic data generation using Large Language Models (LLMs) presents a transformative solution to this bottleneck. By leveraging LLMs to create artificial datasets that preserve the linguistic and structural properties of authentic forensic data, researchers can generate the large-scale, diverse training and testing resources necessary for advancing forensic text comparison research without relying on sensitive real-world evidence [4].
Core Methodologies for LLM-Driven Synthetic Data Generation
Several methodological paradigms have emerged for generating high-quality synthetic data using LLMs. The table below summarizes the primary approaches, their mechanisms, and relevant applications in forensic contexts.
Table 1: Core Methodologies for LLM-Driven Synthetic Data Generation
| Method | Mechanism | Key Features | Representative Techniques | Relevance to Forensic Text Analysis |
|---|---|---|---|---|
| Prompt-Based Generation [20] [21] | Uses carefully crafted instructions to guide a pre-trained LLM to generate specific data types. | Highly accessible; leverages model's inherent knowledge; requires meticulous prompt engineering. | Direct prompting, few-shot examples. | Generating synthetic suspect statements, forensic reports, or phishing emails with specified stylistic attributes. |
| Data Evolution [20] | Iteratively enhances simple seed queries into more complex and diverse instructions. | Systematically increases complexity and diversity; mimics realistic data variation. | In-depth evolving, in-breadth evolving, elimination evolving. | Creating complex forensic query pairs for text comparison from basic templates. |
| Self-Improvement [20] | A model generates data iteratively from its own output without external dependencies. | Enables model alignment without external models; risk of amplifying biases. | Self-Instruct, STaR (Bootstrapping Reasoning With Reasoning) [22]. | Refining a model's capability to generate forensic linguistic patterns internally. |
| Distillation [20] | A stronger, often larger, model generates synthetic data to train or evaluate a weaker model. | Achieves higher data quality; limited only by the best available model. | Symbolic Knowledge Distillation [22]. | Transferring forensic analysis expertise from a powerful, general-purpose LLM to a smaller, specialized model. |
| Retrieval-Augmented Generation (RAG) [23] | Grounds the LLM's generation process by retrieving relevant information from a knowledge base before synthesis. | Enhances factual consistency and traceability; reduces hallucination. | Vector database integration, context-aware generation. | Ensuring synthetic forensic texts are grounded in real-world legal or procedural contexts. |
Application Notes and Protocols for Forensic Text Comparison
The following section outlines specific protocols and workflows for generating synthetic datasets tailored to forensic text comparison research.
Protocol 1: Generating a Synthetic Forensic Q&A Dataset
This protocol, inspired by the creation of the ForensicsData dataset, details the generation of Question-Context-Answer (Q-C-A) triplets for evaluating forensic text analysis capabilities [4].
Workflow Overview:
Detailed Procedure:
Data Collection and Preprocessing:
- Source: Collect raw text data from relevant forensic sources. For malware analysis, this could be execution reports from platforms like ANY.RUN [4]. For text comparison, this could be a corpus of genuine forensic texts (e.g., transcribed interviews, police reports) where privacy-permitting.
- Preprocessing: Clean the source data (e.g., remove excess whitespace, standardize formats). For document-based generation, split documents into coherent chunks using a token splitter, considering chunk size and overlap to mirror the application's retriever logic [20].
Structured Data Extraction:
- Programmatically extract structured elements from the preprocessed reports. This includes metadata (e.g., author demographics, document type) and key textual entities (e.g., named entities, specific forensic terminology, psychological markers).
LLM-Driven Q-C-A Synthesis:
- Model Selection: Choose a state-of-the-art LLM suitable for the task. Evaluations suggest models like Gemini 2 Flash have demonstrated strong performance in aligning with forensic terminology [4].
- Prompt Engineering: Design a system prompt that instructs the LLM to generate Q-C-A triplets based on the provided structured data and context chunks. The prompt should specify:
- Question Generation: To create questions that a forensic analyst might ask about the text.
- Context Sourcing: To clearly identify the text span from the source data that contains the answer.
- Answer Formulation: To provide a precise, context-grounded answer.
- Execution: Process the extracted data through the LLM in a parallelized, automated pipeline to generate a large pool of candidate Q-C-A triplets [4].
Multi-Stage Quality Validation:
- Format Validation: Automatically check that all triplets adhere to the required Q-C-A structure.
- Semantic Deduplication: Remove triplets that are semantically redundant to ensure dataset diversity [4].
- LLM-as-a-Judge: Use a separate, powerful LLM to score the quality of the triplets based on criteria such as clarity, consistency, relevance, and factual correctness against the source context [20] [4].
- Expert Review (Optional but Recommended): Have domain experts (e.g., forensic linguists) review a subset of the data to validate its forensic relevance and accuracy.
Protocol 2: Evolving Simple Texts for Complex Psycholinguistic Analysis
This protocol uses data evolution techniques to create complex textual data for analyzing psycholinguistic features like deception and emotion, which are central to forensic text comparison [20] [24].
Workflow Overview:
Detailed Procedure:
Seed Collection:
- Start with a small set of simple, human-created textual statements or queries. For a fictional crime scenario, this could be basic character statements or simple Q&A pairs [24].
In-Depth Evolution:
- Apply evolution techniques to make each seed instruction more complex. The LLM is prompted to:
- Complicate the input by adding constraints or multi-step reasoning requirements.
- Increase the need for reasoning, for example, by asking for justification.
- Incorporate deeper psycholinguistic features. For instance, evolve a straightforward alibi statement into one that contains subtle cues of deception, emotional distress, or subjective narration [20] [24].
- Example Evolution:
- Seed: "The suspect said he was at home all night."
- Evolved: "Generate a first-person alibi statement from a suspect who was at home all night but is experiencing high levels of fear and neutrality, and incorporates subtle deceptive elements regarding their interaction with a household object." [24]
- Apply evolution techniques to make each seed instruction more complex. The LLM is prompted to:
In-Breadth Evolution:
- From a single seed instruction, generate new yet related instructions to increase the diversity of the dataset. This creates multiple variations on a theme, covering different aspects of forensic text analysis [20].
Elimination Evolving:
- Filter the evolved dataset to remove instructions that are low-quality, failed, or do not meet the complexity and relevance criteria for forensic text comparison [20].
Styling and Formatting:
- Ensure the final evolved texts are styled appropriately for the target application. This may involve structuring the output in a specific JSON format for automated analysis or ensuring the text mimics the narrative style of a police interview transcript [20].
Quality Assurance and Validation Framework
Generating synthetic data for forensic research demands rigorous quality control to ensure the data's utility and reliability. The following table outlines a multi-faceted validation framework.
Table 2: Synthetic Data Quality Assurance and Validation Framework
| Validation Stage | Technique | Description | Key Metrics/Outcomes |
|---|---|---|---|
| Context Filtering [20] | LLM-as-Judge | Uses an LLM to evaluate and filter out low-quality context chunks (e.g., unintelligible, poorly structured) before synthetic input generation. | Clarity, Depth, Structure, Relevance, Precision, Novelty, Conciseness, Impact. |
| Input Filtering [20] | LLM-as-Judge | Evaluates the generated synthetic inputs (queries) based on specific criteria to ensure they are fit for purpose. | Self-containment, Clarity, Consistency, Relevance, Completeness. |
| Automated Validation [4] | Format & Semantic Checks | Applies automated checks for format correctness and semantic deduplication to remove redundant entries. | Format adherence, Diversity (low semantic similarity). |
| Expert Evaluation [4] | Human-in-the-Loop | Forensic domain experts assess a curated subset of the data for realism, relevance, and accuracy. | Forensic relevance, Realism, Ground-truth alignment. |
| Performance Benchmarking [25] | Model Fine-Tuning & Testing | The synthetic dataset is used to fine-tune a model (e.g., a specialized ForensicLLM), and performance is quantitatively evaluated against a baseline. |
Attribution accuracy (e.g., 86.6% [25]), Correctness, Relevance (via user surveys). |
The Scientist's Toolkit: Essential Research Reagents and Solutions
This section catalogs key tools, models, and datasets essential for implementing the aforementioned protocols in a forensic text comparison research context.
Table 3: Essential Research Reagents and Solutions for Forensic Synthetic Data Generation
| Item | Type | Function/Description | Example Instances |
|---|---|---|---|
| Base LLM | Model | A powerful, general-purpose model used for data generation and distillation. | GPT-4, Claude, Gemini 2 Flash [4], LLaMA series [25]. |
| Specialized Forensic LLM | Model | A fine-tuned model designed for digital forensics, used as a benchmark or for data annotation. | ForensicLLM (a fine-tuned LLaMA model) [25]. |
| Evaluation Framework | Software | An open-source framework to facilitate the generation and evaluation of synthetic data and LLM outputs. | DeepEval's Synthesizer [20]. |
| Forensic Dataset | Data | A publicly available, structured dataset for training and benchmarking models in forensic applications. | ForensicsData (5,000+ Q-C-A triplets from malware reports) [4]. |
| Vector Database | Infrastructure | Enables semantic search and Retrieval-Augmented Generation (RAG) by storing data as numerical vectors, ensuring generated content is grounded in a knowledge base. | Chroma, Pinecone, Weaviate [23]. |
| Fine-Tuning Library | Software | Provides efficient methods to adapt general LLMs to forensic terminology and tasks, reducing computational cost. | LoRA (Low-Rank Adaptation), QLoRA [23]. |
| Psycholinguistic Analysis Library | Software | Provides tools for extracting features relevant to forensic text comparison, such as deception and emotion. | Empath (for deception over time analysis) [24], LIWC (Linguistic Inquiry and Word Count). |
| Forensic Text Corpus | Data | A foundational collection of genuine forensic texts (e.g., interviews, reports) used as a source for context or for seed generation. | (Researcher must assemble, subject to privacy constraints). |
The Question-Context-Answer (Q-C-A) format provides a structured framework for developing forensic text comparison data sets. This methodology addresses the critical need for empirical validation in forensic science, which requires replicating case-specific conditions and using relevant data [6]. The Q-C-A structure ensures transparent documentation of the investigative process, from initial inquiry through analytical context to interpretative conclusions, facilitating scientifically defensible and demonstrably reliable forensic text analysis.
Quantitative Data Framework
WCAG Color Contrast Requirements for Data Visualization
The following table summarizes the minimum contrast ratios required for accessible data visualization, ensuring information is perceivable to all researchers and end-users of forensic data sets.
Table 1: WCAG Contrast Requirements for Visual Elements
| Element Type | Contrast Ratio (Enhanced) | Size & Weight Specifications | Application in Forensic Visualization |
|---|---|---|---|
| Normal Text | 7:1 [26] | Less than 18pt/24px or 14pt/19px bold [27] | Labels, annotations, detailed analysis text |
| Large Text | 4.5:1 [26] | At least 18pt/24px or 14pt/19px bold [27] | Headers, titles, highlighted findings |
| User Interface Components | 3:1 [28] | Graphical objects, charts, diagrams [28] | Timelines, network graphs, evidence boards |
| Logos, Brand Names | Exempt [26] | Decorative or non-informative | Institutional branding on reports |
Forensic Text Comparison Metrics
Table 2: Quantitative Metrics for Forensic Text Validation
| Metric | Application in Q-C-A Framework | Target Threshold | Data Relevance Requirement |
|---|---|---|---|
| Likelihood Ratio (LR) | Strength of evidence evaluation [6] | LR > 1 supports prosecution hypothesis; LR < 1 supports defense hypothesis [6] | Must reflect case conditions |
| Magic Number (Color Grade Difference) | Accessible data visualization [28] | 50+ for AA contrast; 70+ for AAA contrast [28] | Ensures readability for all users |
| Text Size Validation | Determining contrast requirements [29] | Minimum 18.66px for large text [29] | Accurate measurement of visual presentation |
| Log-Likelihood-Ratio Cost | Performance assessment of FTC systems [6] | Lower values indicate better performance [6] | Requires relevant reference data |
Experimental Protocols
Protocol: Implementing Q-C-A Framework for Forensic Text Comparison
Question Formulation Phase
- Define Competing Hypotheses: Establish prosecution hypothesis (Hp) that source-questioned and source-known documents share authorship, and defense hypothesis (Hd) that they originate from different authors [6].
- Identify Case Conditions: Document specific mismatches between documents (topics, genres, registers) that must be reflected in validation experiments [6].
- Establish Prior Odds: Recognize that prior belief of trier-of-fact forms before new evidence presentation, though quantification falls outside forensic scientist's role [6].
Context Documentation Phase
- Data Relevance Assessment: Select reference data that matches the specific conditions of the case under investigation, including topic domains, writing contexts, and demographic factors [6].
- Text Feature Extraction: Apply quantitative measurements of linguistic features including lexical, syntactic, and structural properties that constitute authorial "idiolect" [6].
- Cross-Topic Validation: Implement specific validation for topic mismatches, known to be challenging for authorship attribution algorithms [6].
Answer Derivation Phase
- Likelihood Ratio Calculation: Compute LR using statistical models (e.g., Dirichlet-multinomial model followed by logistic-regression calibration) [6].
- Performance Assessment: Evaluate derived LRs using log-likelihood-ratio cost and visualize using Tippett plots [6].
- Interpretation Framework: Present LR as quantitative statement of evidence strength without computing posterior odds, which would encroach on ultimate issue of guilt [6].
Protocol: Accessible Visualization for Forensic Data Presentation
Color Selection Process
- Magic Number Application: Calculate difference between color grades (e.g., gray-90 background with grade 40 or below text ensures AA contrast) [28].
- Relative Luminance Verification: Consult luminance ranges for specific grades to ensure WCAG contrast compliance [28].
- Color Deficiency Consideration: Avoid color-exclusive meaning conveyance, as approximately 4.5% of population has color insensitivity [28].
Timeline Construction for Digital Forensic Analysis
- Initial Event Anchoring: Begin with point of known compromise and fill in data chronologically before and after event [30].
- Multi-Thread Correlation: Create separate, color-coded timelines for different connection types, file activities, or user actions [30].
- Temporal Analysis: Correlate events across timelines to identify patterns, causality, and attacker intent [30].
Visualization Schematics
Q-C-A Framework Implementation Workflow
Forensic Text Comparison Validation Methodology
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials for Forensic Text Comparison Research
| Research Reagent | Function in Q-C-A Framework | Application Specification |
|---|---|---|
| Likelihood Ratio Framework | Quantitative evidence evaluation [6] | Calculates probability of evidence under competing hypotheses; prevents ultimate issue encroachment |
| Dirichlet-Multinomial Model | Statistical analysis of text features [6] | Processes quantitative measurements of linguistic properties for authorship attribution |
| Logistic Regression Calibration | Model performance optimization [6] | Adjusts derived likelihood ratios to improve accuracy and reliability |
| Color Grade System | Accessible data visualization [28] | Ensures WCAG compliance through magic number application (50+ for AA contrast) |
| Timelining Methodology | Visual correlation of digital events [30] | Maps chronological relationships in forensic data using visuospatial sketchpad principles |
| Tippett Plots | Visualization of LR performance [6] | Assesses calculated likelihood ratios across multiple validation trials |
| Contrast Color Function | Automated accessibility compliance [31] | CSS function returning white or black for maximum contrast with input color |
| Visuospatial Sketchpad Techniques | Enhanced cognitive processing [30] | Leverages human visual learning for pattern recognition in complex data sets |
The reliability of any forensic text comparison (FTC) study is fundamentally dependent on the quality and relevance of its underlying data sets. Developing robust, forensically realistic datasets is a critical prerequisite for the empirical validation that the field now demands [6]. This document provides detailed Application Notes and Protocols for sourcing and curating data from two prevalent modern domains: cybersecurity malware reports and social media platforms. The procedures outlined herein are designed to support the development of data sets for FTC research that meet the dual requirements of reflecting real-world case conditions and utilizing relevant data, thereby ensuring the scientific defensibility of the analysis [6].
Data Presentation: Malware and Social Media Landscapes
To inform data collection strategies, it is essential to first understand the current quantitative landscape of these domains. The following tables summarize key metrics and trends from 2025.
Table 1: Q3 2025 Open Source Malware Ecosystem Metrics [32]
| Metric | Value | Trend & Implication |
|---|---|---|
| New Malware Packages | 34,319 (Q3) | 140% increase from Q2; indicates rapidly accelerating threat volume. |
| Total Malware Packages | >877,000 | Cumulative threat environment is vast and requires filtering. |
| Most Common Threat Type | Data Exfiltration (37%) | Shift toward intelligence-gathering and data monetization. |
| Fastest-Growing Threat Type | Droppers (38% of Q3 threats) | 2,887% increase; signifies rise in multi-stage, modular attacks. |
| Notable Incident: Package Hijack | chalk, debug (npm) |
Impact on projects with >2B weekly downloads; highlights software supply chain risk. |
| Notable Incident: Self-Replicating Malware | Shai-Hulud worm (npm) | First-of-its-kind; compromised >500 components; demonstrates automated propagation. |
Table 2: 2025 Social Media Trends Relevant for Data Sourcing [33]
| Trend Category | Key Statistic | Implication for FTC Data Collection |
|---|---|---|
| Content Experimentation | >60% of social content aims to entertain, educate, or inform. | Data will contain diverse communicative purposes beyond promotion. |
| Brand Persona Shifts | 80-100% of content is entertainment-driven for 25% of organizations. | Authorial style (e.g., corporate brands) may vary significantly from other channels. |
| Outbound Engagement | 41% of organizations test proactive engagements (e.g., commenting on creators' posts). | Creates rich, interactive text for analyzing conversational style and response patterns. |
| AI-Generated Content | 69% of marketers see AI as revolutionary, with high adoption for content creation. | Introduces a new variable: machine-generated text that may mimic human authorship. |
Experimental Protocols for Data Sourcing and Curation
Protocol: Sourcing Malware Reports and Threat Intelligence
Objective: To collect a comprehensive corpus of malware-related text from trusted sources for analyzing the writing styles of threat actors and security researchers.
Materials:
- Computer with internet access
- Web scraping tool (e.g., Python
requests/BeautifulSoup, Scrapy) or API clients - Secure storage (e.g., encrypted drive or server)
- Data organization software (e.g., spreadsheet or database)
Methodology:
- Source Identification and Selection:
- Identify and vet high-authority sources such as security vendor blogs (e.g., Bitsight [34], Sonatype [32]), official cybersecurity advisories (e.g., CISA), and curated threat intelligence platforms.
- Prioritize sources that provide detailed technical analysis, Indicators of Compromise (IoCs), and excerpts from dark web forums.
Data Collection:
- For web-based sources, use a web scraper to extract the textual content from relevant reports and blog posts. Configure the scraper to respect
robots.txtand implement polite crawling delays. - Where available, use official APIs (e.g., Twitter API for threat intelligence feeds) for more efficient and structured data collection.
- For each collected text, record essential metadata in a structured format (e.g., CSV, JSON). This must include:
- For web-based sources, use a web scraper to extract the textual content from relevant reports and blog posts. Configure the scraper to respect
Data Sanitization:
- Remove all HTML/XML tags, extraneous JavaScript, and CSS.
- Identify and redact or remove any Personally Identifiable Information (PII) inadvertently present in the texts.
- Normalize text encoding to UTF-8 to ensure consistency.
Protocol: Curating Social Media Corpora
Objective: To build a dataset of social media texts suitable for studying authorial variation across platforms, topics, and time.
Materials:
- Computer with internet access
- Social media API access (e.g., X, Reddit, Meta)
- Social listening or data aggregation tools (e.g., Hootsuite [33])
- Data organization software
Methodology:
- Research Question Formulation:
- Define the specific FTC variable to be studied. This will dictate the collection parameters. Examples include:
- Topic Mismatch: Collecting posts from the same author on different topics.
- Platform-induced Style Shift: Collecting content from the same author on different platforms (e.g., X vs. Threads).
- AI vs. Human Authored Text: Collecting posts identified as AI-generated and those claimed to be human-written [33].
- Define the specific FTC variable to be studied. This will dictate the collection parameters. Examples include:
Stratified Data Collection:
- Use platform APIs to collect public posts based on predefined strata:
- Author Strata: Collect multiple posts from a set of identified authors.
- Topic Strata: Use keywords and hashtags to collect posts about specific topics (e.g., "malware," "content curation").
- Platform Strata: Collect data from multiple platforms to compare linguistic features.
- Temporal Strata: Collect data over time to analyze stylistic evolution.
- Use platform APIs to collect public posts based on predefined strata:
Metadata Annotation:
- Annotate each post with rich metadata, which is critical for subsequent experimental control [6]:
Author_IDPlatformTimestampTopic_CategoryPost_Type(e.g., original, reply, quote)Engagement_Metrics(e.g., likes, shares)AI_Flag(if determinable)
- Annotate each post with rich metadata, which is critical for subsequent experimental control [6]:
Protocol: Forensic Text Comparison Validation Experiment
Objective: To empirically validate an FTC methodology using a sourced and curated dataset, specifically testing its performance under a condition like topic mismatch.
Materials:
- Curated text corpus with author and topic annotations.
- Statistical software (e.g., R, Python with
scikit-learn). - Computational model for text comparison (e.g., Dirichlet-multinomial model [6]).
Methodology:
- Define Hypotheses and Conditions:
- Prosecution Hypothesis (Hp): The questioned and known documents were written by the same author.
- Defense Hypothesis (Hd): The questioned and known documents were written by different authors [6].
- Define the specific "condition" to test, e.g., "topic mismatch between known and questioned documents."
Create Experimental Pairs:
- Same-Author (SA) Pairs: Create document pairs where the same author writes two documents on different topics. This reflects the casework condition.
- Different-Author (DA) Pairs: Create document pairs where two different authors write documents on different topics.
Feature Extraction & Likelihood Ratio (LR) Calculation:
- Extract quantitative features from the text pairs (e.g., character n-grams, syntactic features).
- For each text pair, calculate a Likelihood Ratio (LR) using a pre-defined statistical model [6]. The LR is: LR = p(E|Hp) / p(E|Hd) where E is the evidence (the textual features).
Validation and Performance Assessment:
- Use logistic regression calibration to refine the LRs [6].
- Assess the validity and performance of the LRs using metrics like the Log-Likelihood-Ratio Cost (Cllr), which measures the overall accuracy and discrimination of the system.
- Visualize the results using Tippett plots, which show the cumulative proportion of LRs supporting the correct and incorrect hypotheses for both SA and DA pairs.
Workflow Visualization
The following diagram illustrates the end-to-end process of data sourcing, curation, and experimental validation for FTC research.
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials and Tools for FTC Data Workflows
| Item/Reagent | Function in FTC Research |
|---|---|
| Web Scraping Framework (e.g., Scrapy, BeautifulSoup) | Automated collection of textual data from public websites and forums. |
| Social Media APIs (e.g., X, Reddit) | Programmatic, policy-compliant access to structured social media data. |
| Social Listening Tools (e.g., Hootsuite, Talkwalker) | Provides aggregated data and trend analysis across multiple social platforms [33]. |
| Statistical Software Environment (e.g., R, Python with NumPy/SciPy) | Platform for quantitative text measurement, statistical modeling, and LR calculation [6]. |
| Dirichlet-Multinomial Model | A specific statistical model used for calculating likelihood ratios from text count data (e.g., n-grams) [6]. |
| Logistic Regression Calibration | A method to calibrate the output scores of a model to produce well-calibrated Likelihood Ratios [6]. |
| Secure Data Storage (Encrypted Drives/Servers) | Ensures the integrity and confidentiality of collected text corpora. |
| Metadata Schema (Structured CSV/JSON templates) | Provides a consistent framework for annotating texts with author, topic, and platform data, which is critical for validation [6]. |
Within forensic text comparison (FTC) research, the empirical validation of methodologies requires replicating specific case conditions using forensically relevant data [6]. A significant challenge in real-world authorship analysis involves comparing documents with topic mismatches, where writing styles may vary substantially based on subject matter [6]. This case study details the construction of a specialized dataset designed specifically for cross-topic authorship verification, addressing a critical gap in forensic linguistics resources. Such datasets enable rigorous testing of authorship verification methods under conditions that mirror actual forensic challenges, where questioned and known documents often differ in thematic content.
The importance of this work extends to multiple domains where authorship verification is applied, including forensic investigations, academic integrity cases, journalism attribution, and social media analysis [35]. By providing a structured framework for dataset development with explicit documentation of topic variation, this resource supports the advancement of more robust and forensically valid authorship verification techniques.
Dataset Design and Composition
Core Design Principles
The dataset construction adheres to two fundamental requirements established for empirical validation in forensic science [6]:
- Reflecting case conditions: Explicitly modeling the topic mismatch scenario commonly encountered in casework
- Using relevant data: Incorporating authentic textual materials comparable to those examined in actual investigations
Topic mismatch represents one of the most challenging conditions in authorship analysis, as writing style often varies substantially across different subject matters [6]. The dataset systematically controls for this variable to enable testing method robustness under these adverse conditions.
Dataset Specifications
Table 1: Dataset composition and structure
| Component | Specification | Purpose |
|---|---|---|
| Authors | 100-150 individuals | Provides sufficient author population for statistical significance |
| Documents per Author | 4-6 documents minimum | Enables multiple cross-topic comparisons per author |
| Topic Categories | 5-8 distinct themes | Ensures substantial topical variation within and between authors |
| Text Length | 500-5000 words | Maintains practical forensic relevance while ensuring sufficient features |
| Genre | Single consistent genre (e.g., blogs, emails, academic abstracts) | Controls for genre as a confounding variable |
| Metadata | Author demographics, topic labels, collection dates | Supports controlled experiments and confounding factor analysis |
The dataset structure enables three primary authorship verification decision problems [35]:
- AV_Core: Determining whether two specific documents were written by the same author
- AV_Batch: Assessing whether two sets of documents share the same authorship
- AV_Known: Verifying if a disputed document was written by a specific candidate author based on their known writings
Experimental Protocol for Dataset Construction
Data Collection and Curation
The dataset construction follows a systematic workflow to ensure forensic relevance and methodological rigor:
Figure 1: Workflow for constructing a cross-topic authorship verification dataset.
Phase 1: Source Identification and Author Selection
- Identify appropriate text sources with verified authorship and substantial topical diversity
- Select 100-150 authors with multiple documents across different topics
- Ensure each author has at least 4-6 documents with explicit topic variation
- Balance author demographics (gender, age, expertise) where possible
Phase 2: Topic Categorization and Text Extraction
- Define 5-8 broad topic categories relevant to the text genre
- Manually annotate each document with primary and secondary topic labels
- Extract and clean text content, removing boilerplate and non-text elements
- Perform text normalization (lowercasing, punctuation standardization)
Phase 3: Quality Verification and Dataset Splitting
- Verify authorship attribution through multiple independent sources
- Ensure minimum text length requirements are met
- Create standardized training, validation, and test splits with no author overlap
- Document all processing steps and quality control measures
Cross-Topic Pair Construction
For authorship verification tasks, the dataset systematically constructs positive and negative pairs with varying degrees of topic overlap:
Positive Pairs: Documents from the same author across different topics Negative Pairs: Documents from different authors with both matched and mismatched topics
This structure enables testing of verification methods under three conditions:
- Same topic, same author (control condition)
- Different topics, same author (cross-topic verification)
- Different topics, different authors (cross-topic impostor detection)
Validation Framework
Benchmark Experimental Protocol
The validation of authorship verification methods using the cross-topic dataset follows a standardized experimental protocol:
Figure 2: Experimental protocol for validating authorship verification methods.
Implementation Details:
- Data Partitioning: Strict separation of training, validation, and test sets with no author overlap
- Feature Extraction: Multiple feature types at different linguistic levels
- Model Training: Training on single-topic pairs, testing on cross-topic pairs
- Evaluation: Comprehensive metrics including accuracy, AUC, Cllr, and Tippett plots
Evaluation Metrics
Table 2: Evaluation metrics for authorship verification performance
| Metric | Calculation | Interpretation | Forensic Relevance |
|---|---|---|---|
| Area Under Curve (AUC) | Area under ROC curve | Overall discrimination ability | General method performance |
| Log-Likelihood Ratio Cost (Cllr) | −12[(1N∑i=1Nlog2(1+1LRi))+1N∑i=1Nlog2(1+LRi)] | Calibration quality | Reliability of likelihood ratios |
| Accuracy | (TP+TN)(TP+TN+FP+FN) | Overall correct decisions | Practical utility |
| Tippett Plot | Graphical representation of LR distributions | Method calibration | Forensic evidence interpretation |
The Cllr metric is particularly important in forensic applications as it assesses the reliability of likelihood ratios, which form the basis of forensic evidence evaluation under the likelihood ratio framework [6].
The Scientist's Toolkit
Essential Research Reagents
Table 3: Key research reagents and computational tools for authorship verification research
| Tool/Resource | Type | Function | Application in Protocol |
|---|---|---|---|
| stylo R Package [36] | Software Library | Implements imposters method and stylometric analysis | Authorship verification using general imposters method |
| LambdaG Method [35] | Computational Method | Calculates likelihood ratio based on grammar models | Authorship verification using grammatical features |
| n-gram Language Models | Computational Method | Models language using contiguous character/word sequences | Feature extraction for stylistic analysis |
| LIWC (Linguistic Inquiry Word Count) | Software Tool | Analyzes psychological processes in text | Psycholinguistic feature extraction |
| Empath Python Library [37] | Software Library | Analyzes text against lexical categories | Deception and emotion analysis in forensic texts |
| AIDBench Benchmark [38] | Evaluation Framework | Benchmarks authorship identification capabilities | Performance comparison across methods |
| ForensicsData Dataset [4] | Data Resource | Provides malware analysis reports in Q-C-A format | Training data for forensic question answering |
This case study presents a comprehensive framework for constructing cross-topic authorship verification datasets to advance forensic text comparison research. By systematically addressing the challenge of topic mismatch—a prevalent condition in real forensic cases—this approach enables more rigorous validation of authorship verification methods. The detailed protocols for dataset construction, experimental validation, and performance assessment provide researchers with standardized methodologies for developing forensically relevant resources.
The resulting datasets support the development of more robust authorship verification techniques that can withstand challenging cross-topic conditions, ultimately enhancing the scientific foundation of forensic text comparison. Future work will expand this framework to incorporate additional confounding factors such as genre variation, temporal evolution of writing style, and multi-author documents, further increasing the forensic relevance of the resources.
Navigating Challenges in Dataset Creation: Bias, Mismatch, and Ethics
Mitigating Algorithmic Bias and Ensuring Fairness in Training Data
Algorithmic bias refers to the systematic and repeatable errors that create unfair outcomes, such as privileging one arbitrary group of users over others. In forensic text comparison research, biased datasets can perpetuate and even amplify societal inequalities, leading to discriminatory outcomes and reduced validity of scientific conclusions. A landmark case is the COMPAS recidivism algorithm, which was found to disproportionately classify Black defendants as higher risk compared to White defendants, despite race not being an explicit input feature [39]. This bias stemmed from historical data that reflected existing societal disparities, which were then learned and perpetuated by the algorithm.
The sources of bias in training data are multifaceted. Systemic bias occurs due to societal conditions and inequalities that become embedded in datasets. Data collection and annotation bias arises during the processes of gathering or labeling data. Algorithm or system design bias originates from the choices made in developing the model architecture or objective functions [39]. A well-documented example of data collection bias is Amazon's AI recruiting tool, which penalized resumes containing the word "women's" because it was trained on historical hiring data dominated by male applicants [39] [40]. Similarly, the "Gender Shades" study exposed significant race and gender biases in commercial facial recognition software, with accuracy rates dropping to as low as 65.3% for darker-skinned women compared to over 99% for white males, due to training data heavily skewed toward lighter-skinned subjects [40].
Frameworks and Standards for Bias Mitigation
The IEEE 7003-2024 standard, "Standard for Algorithmic Bias Considerations," provides a comprehensive framework for addressing bias throughout the AI system lifecycle [41]. This landmark framework establishes processes to help organizations define, measure, and mitigate algorithmic bias while promoting transparency and accountability. The standard encourages an iterative, lifecycle-based approach that considers bias from initial system design through decommissioning [41].
Another foundational framework is the FAIR Principles, which provide guidelines to improve the Findability, Accessibility, Interoperability, and Reuse of digital assets [42]. These principles emphasize machine-actionability – the capacity of computational systems to find, access, interoperate, and reuse data with minimal human intervention – which is crucial for dealing with the increasing volume, complexity, and creation speed of data in forensic research [42].
For organizations implementing these standards, key steps include establishing a bias profile to document considerations throughout the system's lifecycle, identifying stakeholders early in development, ensuring data representation, monitoring for data drift and concept drift, and promoting accountability through clear documentation [41].
Experimental Protocols for Bias Assessment and Mitigation
Three-Stage Bias Intervention Framework
Table 1: Stages of Bias Intervention in Machine Learning
| Intervention Stage | Description | Key Techniques | Pros and Cons |
|---|---|---|---|
| Pre-processing | Adjusts data before model training | Resampling, reweighting, relabeling, feature selection [40] [43] | Pros: Addresses root causesCons: Data collection can be expensive/difficult [40] |
| In-processing | Modifies model training process | Prejudice removers, adversarial debiasing, fairness constraints [40] [43] | Pros: Provides theoretical fairness guaranteesCons: Computationally intensive [40] |
| Post-processing | Adjusts model outputs after training | Threshold adjustment, reject option classification, calibration [40] [43] | Pros: Computationally efficient, works with black-box modelsCons: May require sensitive attribute information [40] |
Protocol for Bias Evaluation in Forensic Text Comparison
Objective: To systematically evaluate and quantify algorithmic bias in forensic text comparison models across protected subgroups.
Materials and Dataset Requirements:
- Text Corpora: Representative samples of forensic text data (e.g., chat logs, written statements, transcribed interviews)
- Protected Attribute Labels: Annotated demographic information (race, gender, age, socioeconomic status) with appropriate privacy safeguards
- Ground Truth Labels: Objective measures of the target variable (e.g., actual author identity, ground truth deception status)
- Benchmark Datasets: Standardized forensic datasets such as those available through the CSAFE Forensic Science Data Portal [44]
Experimental Procedure:
Data Characterization and Bias Assessment
- Document data provenance using the FAIR Principles, recording where data was collected, how it was collected, who collected it, and for what purpose [39]
- Analyze dataset composition across protected attributes to identify representation gaps
- Implement cross-validation techniques using diverse data subsets to assess generalizability [39]
Model Training and Validation
- Split data into training, validation, and test sets, ensuring proportional representation of subgroups across splits
- Train baseline model without bias mitigation interventions
- Apply selected bias mitigation techniques from one or more intervention stages (pre-, in-, or post-processing)
Bias and Fairness Metrics Calculation
- Evaluate model performance using group fairness metrics (see Table 2)
- Calculate performance disparities across protected subgroups
- Perform statistical testing to identify significant differences in error rates
Iterative Refinement
- Based on results, implement additional bias mitigation strategies
- Retrain and re-evaluate models until fairness criteria are satisfied while maintaining acceptable accuracy
Table 2: Key Fairness Metrics for Algorithm Evaluation in Forensic Contexts
| Metric Name | Formula/Definition | Interpretation in Forensic Context |
|---|---|---|
| Demographic Parity | P(Ŷ=1|A=a) = P(Ŷ=1|A=b) Where Ŷ is prediction, A is protected attribute | Are positive outcomes equally distributed across groups? |
| Equalized Odds | P(Ŷ=1|A=a,Y=y) = P(Ŷ=1|A=b,Y=y) Where Y is true label | Does model have similar error rates across groups? |
| Predictive Parity | P(Y=1|A=a,Ŷ=1) = P(Y=1|A=b,Ŷ=1) | When model predicts positive, is it equally accurate across groups? |
| Disparate Impact | (P(Ŷ=1|A=a))/(P(Ŷ=1|A=b)) | Ratio of positive outcomes between protected and unprotected groups |
Workflow Visualization for Bias Mitigation Protocol
Bias Mitigation Workflow
Application to Forensic Text Comparison Research
In forensic text comparison, bias can manifest in authorship attribution, deception detection, and stylistic analysis. Research has shown that stylometric features such as "Average character number per word token," "Punctuation character ratio," and vocabulary richness features are robust for authorship attribution across different sample sizes [7]. However, these features may correlate with demographic factors, potentially introducing bias if not properly controlled.
A psycholinguistic NLP framework for forensic text analysis has demonstrated the value of integrating emotion, subjectivity, narration analysis, n-gram correlation, and deception over time to identify key investigative entities [37]. This approach can help reduce human bias in forensic investigations by bringing to the surface psycholinguistic patterns that suggest a forensic temporal predisposition to certain behavior when placed in appropriate context.
For multimodal forensic analysis, recent benchmarking studies of Multimodal Large Language Models (MLLMs) have revealed persistent limitations in visual reasoning and complex inference tasks, with models underperforming in image interpretation and nuanced forensic scenarios [45]. This highlights the importance of domain-specific evaluation and bias testing, as performance disparities may not be evident in general-purpose benchmarks.
Research Reagent Solutions for Bias-Aware Forensic Research
Table 3: Essential Tools and Libraries for Bias Mitigation Research
| Tool/Library Name | Primary Function | Application in Forensic Text Research |
|---|---|---|
| Empath | Generates and analyzes lexical categories [37] | Quantifying deception over time in suspect statements |
| LIWC (Linguistic Inquiry and Word Count) | Psycholinguistic text analysis [37] | Extracting stylistic and psychological features for authorship analysis |
| Fairness Toolkits (e.g., AI Fairness 360, Fairlearn) | Bias detection and mitigation algorithms [43] | Implementing pre-, in-, and post-processing bias mitigation |
| Transformers (BERT, RoBERTa) | Contextual language modeling [37] | Stylometric analysis and forensic text comparison |
| Multivariate Kernel Density | Likelihood ratio estimation [7] | Calculating strength of evidence in authorship attribution |
Implementation Considerations for Forensic Applications
When implementing bias mitigation strategies in forensic text comparison research, several domain-specific considerations emerge. First, the legal and ethical standards for evidence admissibility require transparent and explainable methodologies. The "black box" nature of some complex models may be problematic in legal contexts, favoring approaches that provide interpretable results [39].
Second, privacy preservation is crucial when working with sensitive forensic data. Techniques such as data anonymization and federated learning can help protect individual privacy while enabling model development [39]. Federated learning, which trains neural networks on local clients and sends updated weight parameters to a centralized server without sharing the data, is particularly promising for collaborative forensic research across institutions [46].
Third, continuous monitoring is essential as models may experience model drift over time, where relationships between features and outcomes change, potentially introducing new biases [41]. Establishing protocols for periodic reevaluation of deployed models ensures maintained fairness throughout their operational lifespan.
Finally, researchers should consider trade-offs between fairness and accuracy when selecting mitigation approaches. In some forensic applications, certain types of errors may be more consequential than others, necessitating careful consideration of which fairness metrics to prioritize [40] [43].
Addressing Topic and Genre Mismatch Between Known and Questioned Texts
The forensic comparison of textual documents is a critical process in areas such as authorship attribution, fraud investigation, and legal proceedings. A significant challenge arises when the known and questioned texts differ in their topic or genre. Such mismatches can introduce confounding variables, potentially skewing comparison metrics and leading to erroneous conclusions regarding common authorship [13]. The development of robust, relevant datasets is therefore paramount for advancing research and ensuring the reliability of forensic text comparison methods. This document provides detailed application notes and experimental protocols, framed within a broader thesis on developing relevant datasets for forensic text comparison research. It is designed to support researchers and scientists in constructing and utilizing datasets that systematically account for these real-world variabilities.
The tables below summarize core concepts and quantitative benchmarks essential for designing research on topic and genre mismatch.
Table 1: Core Research Objectives for Dataset Development
| Research Objective | Key Performance Metrics | Application in Addressing Mismatch |
|---|---|---|
| Applied R&D for Novel Methods [47] | Sensitivity, specificity, information gain from evidence [47] | Develop methods to maximize discriminative features despite topic/genre differences. |
| Foundational Validity & Reliability [47] | Measurement uncertainty, accuracy, reliability (e.g., via black-box studies) [47] | Establish the scientific limits of comparison methods under mismatch conditions. |
| Standardized Evaluation [48] | BLEU scores, ROUGE scores [48] | Provide quantitative, standardized metrics for benchmarking model performance on cross-topic/genre tasks. |
| Automated Tool Support [47] | Algorithm performance for quantitative pattern evidence comparisons [47] | Create systems that can weigh stylistic evidence independently of content. |
Table 2: WCAG Color Contrast Standards for Research Visualization
| Visual Element Type | Minimum Ratio (Level AA) | Enhanced Ratio (Level AAA) | Application in Diagrams & Tables |
|---|---|---|---|
| Body Text | 4.5:1 [49] [50] | 7:1 [49] [50] | Text within workflow diagram nodes. |
| Large-Scale Text (≥18pt or ≥14pt bold) | 3:1 [49] [50] | 4.5:1 [49] [50] | Diagram titles and column headers in tables. |
| User Interface Components & Graphical Objects | 3:1 [49] [50] | Not defined [50] | Arrows, lines, and non-text elements in workflows. |
Experimental Protocols
Protocol for Cross-Modal Handwritten Document Analysis
This protocol is adapted from the Forensic Handwritten Document Analysis Challenge, which focuses on authorship verification between documents from different modalities (e.g., scanned paper documents vs. digital tablets) [13].
- Objective: To determine if a given pair of documents, potentially differing in writing modality, topic, and genre, were written by the same author.
- Dataset Preparation:
- Data Collection: Construct a novel dataset comprising document pairs. Each pair should be labeled to indicate whether it was written by the same individual.
- Data Diversity: Ensure the dataset encompasses diverse handwriting styles, writing instruments (pen on paper, digital stylus), and environmental conditions to represent real-world forensic challenges [13].
- Data Release: A training set with labels is released first, followed by an unlabeled test set to evaluate model performance [13].
- Model Training & Evaluation:
- Task: Participants develop binary classification models (Same Author/Different Author).
- Innovation: Explore cutting-edge machine learning techniques, novel architectures, or innovative pre-processing methods to enhance cross-modal comparison [13].
- Primary Metric: Model performance is evaluated based on accuracy [13].
- Reporting:
Protocol for Standardized LLM Evaluation in Forensic Timeline Analysis
This protocol provides a framework for quantitatively evaluating Large Language Models (LLMs) on forensic tasks, which can be adapted for analyzing textual consistency across topics.
- Objective: To propose a standardized methodology for quantitatively evaluating the application of LLMs for digital forensic tasks, such as timeline analysis, ensuring reproducible and comparable results [48].
- Methodology Components:
- Dataset & Ground Truth: Develop a structured dataset with established ground truth for the specific forensic task [48].
- Timeline Generation: For tasks like timeline analysis, generate structured timelines from raw data.
- Quantitative Evaluation:
- Outcome: The methodology effectively evaluates whether an LLM can reliably perform complex forensic analysis tasks, highlighting its limitations and capabilities [48].
Workflow Visualization
The following diagram illustrates the logical workflow for developing and validating a forensic text comparison methodology that accounts for topic and genre mismatch.
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials for Forensic Text Comparison Research
| Item | Function & Application |
|---|---|
| Novel Cross-Modal Dataset | A dataset containing paired handwritten documents (scanned paper and digital) with authorship labels. Serves as the fundamental substrate for training and testing models against real-world variability [13]. |
| Standardized Evaluation Metrics (BLEU/ROUGE) | Quantitative metrics adapted from computational linguistics to provide a standardized, reproducible measure of model or LLM performance on text-based forensic tasks, enabling direct comparison between different studies [48]. |
| Machine Learning Algorithms for Pattern Comparison | Algorithms designed for quantitative pattern evidence comparisons. Used to develop objective methods that support examiners' conclusions by weighing stylistic features across disparate texts [47]. |
| Reference Material & Database | Curated, accessible, and diverse databases that support the statistical interpretation of evidence. Essential for establishing baseline writing styles and assessing the significance of identified features [47]. |
| Accessible Color Palette | A predefined set of colors (e.g., #4285F4, #EA4335, #FBBC05, #34A853, #FFFFFF, #F1F3F4, #202124, #5F6368) with high contrast ratios to ensure all research visualizations, diagrams, and data presentations are accessible to a diverse audience, complying with WCAG guidelines [26] [49] [50]. |
Overcoming Data Scarcity with Synthetic Generation and Augmentation
The development of robust, data-driven models for forensic text comparison research is fundamentally constrained by a critical bottleneck: the severe scarcity of high-quality, legally admissible, and contextually rich training data. In digital forensics, this challenge is exacerbated by stringent privacy regulations, ethical concerns, and legal restrictions surrounding the sharing of authentic digital evidence [4]. Consequently, researchers and practitioners face significant hurdles in accessing sufficient data for training and validating analytical tools, hampering both innovation and reproducibility [4].
Synthetic data generation and augmentation present a paradigm-shifting solution to this data scarcity problem. These techniques leverage advanced computational methods, particularly Large Language Models (LLMs), to create realistic, diverse, and procedurally generated datasets that mirror the statistical and linguistic properties of authentic forensic data without containing any sensitive or legally protected information [4]. This approach not only bypasses privacy and legal constraints but also enables the creation of tailored datasets for specific forensic scenarios, thereby accelerating research and tool development in forensic text analysis.
The Data Scarcity Challenge in Forensic Contexts
The inherent privacy, legal, and ethical concerns in digital forensics make authentic data sharing profoundly difficult. Realistic datasets are indispensable for supporting research and tool development, yet public resources remain extremely limited [4]. This scarcity is particularly acute in specialized sub-fields, such as malware analysis, where the dynamic threat landscape demands continuously updated training data [4].
Traditional data collection methods are often inadequate. Manual evidence collection and annotation are labor-intensive, error-prone, and cannot scale to meet the volume and variety required for modern machine learning applications. Furthermore, the sensitive nature of forensic evidence—often pertaining to criminal investigations—imposes severe legal and ethical restrictions on its use for open research, creating a critical barrier to progress.
Synthetic Data Generation: Principles and Workflows
Synthetic data generation involves using algorithms to create artificial datasets that statistically resemble real-world data. In forensic text analysis, this typically involves generating synthetic text artifacts—such as malicious emails, forged documents, or social media communications—along with their corresponding metadata and forensic signatures.
Foundational Workflow for Synthetic Forensic Data
The following diagram illustrates a generalized, foundational workflow for generating and validating synthetic forensic data, integrating principles from successful implementations in digital forensics and related fields [51] [4].
Advanced Context-Aware Generation
For complex forensic applications, a basic generation workflow may be insufficient. Advanced pipelines incorporate contextual knowledge and semantic guidance to enhance the fidelity and relevance of generated data. For text simplification tasks—a relevant technique for normalizing forensic text data for analysis—research has demonstrated that integrating knowledge graphs and document-level context during LLM prompting significantly improves output quality and preserves meaning [51]. This context-aware approach can be adapted for generating synthetic forensic texts by providing the LLM with structured information about forensic scenarios, entity relationships, and typical linguistic patterns found in evidence.
Experimental Protocols for Synthetic Data Generation
This section provides detailed, actionable protocols for implementing synthetic data generation, drawing from validated methodologies in digital forensics and computational linguistics.
Protocol 1: Generating a Question-Context-Answer (Q-C-A) Forensic Dataset
This protocol is adapted from the creation of the "ForensicsData" dataset, which comprises over 5,000 Q-C-A triplets derived from malware analysis reports [4]. It can be adapted for various forensic text comparison tasks.
Objective: To synthetically generate a structured dataset where each entry contains a forensic question, the context from which the answer is derived, and the correct answer, suitable for training and evaluating forensic analysis models.
Materials:
- Source Data: A collection of authentic, non-sensitive forensic reports (e.g., malware analysis summaries, forensic tool documentation).
- LLM Access: API or local access to a state-of-the-art LLM (e.g., GPT-4, Claude, Gemini, LLaMA).
- Computing Environment: A standard computing environment capable of running data processing scripts (e.g., Python, Jupyter Notebook).
Procedure:
- Data Sourcing and Selection: Collect a corpus of relevant forensic text. The "ForensicsData" study, for example, sourced 1,500 execution reports from the ANY.RUN malware analysis platform, ensuring a uniform distribution across different malware families and benign samples [4].
- Data Preprocessing: Clean and standardize the source text. This involves:
- Removing personally identifiable information (PII).
- Standardizing formatting (e.g., dates, file paths).
- Segmenting large reports into manageable text chunks.
- Structured Data Extraction: Use a preprocessing pipeline to extract key structured elements from the reports. This may include malware metadata, behavioral patterns, Indicators of Compromise (IOCs), and Tactics, Techniques, and Procedures (TTPs).
- Prompt Engineering and Q-C-A Generation: Design and execute a prompt template that instructs the LLM to generate Q-C-A triplets based on the preprocessed data and extracted structures.
- Example Prompt Skeleton: "You are a digital forensics expert. Based on the following context from a malware analysis report: [Insert preprocessed text chunk and extracted data]. Generate question-context-answer triplets. The questions should probe key forensic findings, and the answers must be directly verifiable from the provided context. Use the JSON format:
{"question": "", "context": "", "answer": ""}."
- Example Prompt Skeleton: "You are a digital forensics expert. Based on the following context from a malware analysis report: [Insert preprocessed text chunk and extracted data]. Generate question-context-answer triplets. The questions should probe key forensic findings, and the answers must be directly verifiable from the provided context. Use the JSON format:
- Validation and Iteration (LLM-as-Judge): Implement a validation loop using a separate LLM instance to evaluate the quality of the generated triplets.
- The evaluator LLM checks for factual consistency between the context and the answer, clarity, and forensic relevance.
- Triplets that fail this check are flagged for regeneration with revised prompts.
Protocol 2: Data Augmentation via LLMs and Lexical Functions
This protocol is inspired by the SLSG method developed for scientific text analysis and can be repurposed to augment existing small-scale forensic text datasets, improving model robustness against lexical variation [52].
Objective: To augment a dataset of forensic text samples by generating meaningful paraphrases and variations, thereby increasing dataset size and diversity without altering semantic meaning.
Materials:
- Seed Dataset: A small, curated set of forensic text samples (e.g., example phrases from phishing emails, text from document forgeries).
- LLM Access: As in Protocol 1.
- Lexical Resources: Access to lexical databases (e.g., WordNet) or pre-defined lexical function rules that map words to their semantic relations (e.g., synonyms, antonyms, intensifiers).
Procedure:
- Seed Data Preparation: Compile and clean the seed dataset of forensic texts.
- Synonym Replacement (SR): Perform a conservative synonym replacement on non-key forensic terms. Critical entities (e.g., specific malware names, forensic tool commands) should be protected from replacement to preserve factual accuracy.
- Lexical Function-based LLM Augmentation: Use the LLM to generate more complex paraphrases guided by lexical functions.
- Example Prompt: "Act as a forensic linguist. For the following sentence: '[Original forensic text]'. Generate three paraphrases that preserve the exact technical meaning but vary the lexical structure. Focus on using different verb forms, nominalizations, and adjective-adverb transformations."
- Auto-labeling: The newly generated text variations inherently inherit the labels (e.g., classification category, authorial style) of their original seed data points.
- Integration with Classifier: Combine the original seed data and the newly augmented data to train a downstream forensic text classification model (e.g., a BERT-based model combined with a Graph Convolutional Network to capture contextual word relationships) [52].
Quantitative Performance of Synthetic Data
The following tables summarize key quantitative findings from recent research on synthetic data generation, highlighting its scale and effectiveness.
Table 1: Scale and Composition of the ForensicsData Synthetic Dataset [4]
| Metric | Description | Value / Composition |
|---|---|---|
| Total Volume | Number of Q-C-A triplets | > 5,000 |
| Data Source | Origin of source material | 1,500 malware execution reports from ANY.RUN |
| Temporal Coverage | Year of report publication | 2025 |
| Malware Families | Diversity of covered threats | 15 families (e.g., AgentTesla, GandCrab, WannaCry) |
| Benign Samples | Inclusion of non-malicious data | 150 samples (13.6% of file count) |
Table 2: Performance Improvements Enabled by Synthetic Data and Augmentation
| Study / Method | Application Domain | Key Performance Result |
|---|---|---|
| SLSG Method [52] | Paragraph-level functional structure recognition in scientific texts | F1 Score: 86%, an 18% improvement over baseline models without augmentation. |
| Context-Aware Simplification [51] | Text simplification for accessibility | Context-aware prompting and semantic feedback improved simplification quality across successive iterations. |
| LLM-as-Judge Evaluation [4] | Quality assurance for synthetic data | A specialized evaluation process confirmed the quality of the generated Q-C-A triplets, with Gemini 2 Flash demonstrating the best performance. |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools and Resources for Synthetic Data Generation in Forensic Research
| Tool / Resource | Type | Function in Research |
|---|---|---|
| ANY.RUN [4] | Data Source Platform | Provides interactive sandbox environments for dynamic malware analysis; source of authentic behavioral data for structuring synthetic generation. |
| LLMs (GPT-4, Gemini, LLaMA) [4] | Generative Engine | Core model for understanding context and generating coherent, realistic synthetic text and structured data formats (Q-C-A). |
| LangChain Framework [51] | Orchestration Tool | Provides modular abstractions for building complex, multi-step LLM applications (chaining, memory, structured output parsing). |
| Lexical Databases (e.g., WordNet) [52] | Linguistic Resource | Provides synonym sets and semantic relationships for data augmentation techniques like synonym replacement. |
| LLM-as-Judge [4] | Validation Mechanism | Uses a separate LLM instance to evaluate the quality, accuracy, and relevance of generated synthetic data, enabling automated quality control. |
| SciBERT-GCN Model [52] | Downstream Classifier | A hybrid model that combines contextual language understanding (SciBERT) with graph neural networks (GCN) to effectively learn from augmented data by capturing dependencies between words and paragraphs. |
Synthetic data generation and augmentation represent a transformative approach to overcoming the pervasive challenge of data scarcity in forensic text comparison research. By leveraging the capabilities of large language models within structured, validated pipelines, researchers can create scalable, diverse, and realistic datasets that are free from legal and ethical constraints. The protocols and evidence presented provide a clear roadmap for integrating these methodologies into forensic science research. This will not only facilitate the development of more robust and accurate analytical tools but also enhance the reproducibility and collaborative potential of research within the field, ultimately strengthening the overall framework of digital forensics.
The development of datasets for forensic text comparison research operates within a complex framework of legal and ethical obligations. Key drivers include the General Data Protection Regulation (GDPR) in the European Union, which establishes strict principles for data processing, and the emerging concept of data sovereignty, which emphasizes control over data throughout its lifecycle [53]. The Schrems II ruling by the Court of Justice of the European Union further invalidated the Privacy Shield framework, highlighting the legal vulnerability of transatlantic data flows and placing protocols reliant on U.S. infrastructure in potential violation of European data sovereignty principles [54]. Compliance is not merely a legal checkbox but a foundational component of research integrity, ensuring that resulting evidence is scientifically sound and legally admissible.
Core Legal and Technical Compliance Frameworks
Key Regulations and Evidence Standards
Recent landmark court cases have shifted the standard for digital evidence from policy-based assurances to technically verifiable proof. The following table summarizes the critical legal standards and their implications for forensic text dataset development.
Table 1: Legal Standards Influencing Forensic Text Data Handling
| Case / Regulation | Jurisdiction & Date | Core Legal Principle | Impact on Text Data Evidence |
|---|---|---|---|
| GDPR (General Data Protection Regulation) [53] | European Union (2018) | Lawful basis for processing, data minimization, purpose limitation, and data sovereignty. | Mandates anonymization/pseudonymization of personal identifiers in text datasets and requires a defined lawful basis for collection. |
| Schrems II Ruling [54] | Court of Justice of the EU (2020) | Invalidated Privacy Shield; strict controls on personal data transfer to non-EU countries. | Prohibits storing or processing EU-sourced text data in cloud infrastructures (e.g., for LLM training) subject to foreign jurisdictions like the U.S. CLOUD Act. |
| In re Facebook Pixel Litigation [15] | United States (2020-2022) | Established technical evidence standards for tracking and data transmission. | Requires reproducible proof of data handling workflows; evidence must be verifiable in a clean environment, favoring documented, transparent pipelines. |
| Clearview AI Litigation [15] | US, EU, Canada, Australia (2021-2024) | Scraped biometric data for AI training constitutes unlawful processing without consent. | Sets a precedent that using publicly available online text for training forensic AI models without a lawful basis may be non-compliant. |
Data Sovereignty Requirements
Data sovereignty requires that data is subject to the laws of the country within which it is collected. For forensic text research, this translates to specific technical and architectural requirements [53]:
- Sovereignty Controls: Implementation must range from contractual obligations to enhanced monitoring of data operations, grounded in robust identity and access management (IAM) systems [53].
- Infrastructure Choice: Using sovereign cloud offerings or on-premises solutions provides varied levels of sovereignty based on needs, spanning from privacy-shielding technologies for lower-security requirements to fully isolated instances for sensitive data [53].
- Encryption and Key Management: Bring Your Own Encryption (BYOE) and proxy re-encryption technologies are crucial for enabling secure and compliant data handling in cloud contexts, allowing data sharing without exposing decrypted information [53].
Application Notes: Developing Compliant Forensic Text Datasets
Protocol 1: Data Collection and Anonymization
Objective: To legally collect and anonymize text data for forensic comparison research, ensuring compliance with GDPR principles of data minimization and privacy.
Table 2: Reagent Solutions for Data Collection & Anonymization
| Research Reagent / Tool | Function / Application | Legal-Compliance Rationale |
|---|---|---|
| Empath Library [24] | A Python tool for analyzing text against psychological and deception categories. | Allows for feature-based analysis (e.g., emotion, deception) without storing raw, potentially identifiable text data. |
| LIWC Application [24] | Linguistic Inquiry and Word Count; extracts psycholinguistic features from text. | Enables research on linguistic patterns while operating on anonymized or feature-based datasets, minimizing privacy impact. |
| DataShielder HSM PGP [54] | A hardware-based encryption tool for local, user-controlled data encryption. | Enables pre-encryption of text data before storage or transfer, aligning with data sovereignty and security-by-design principles. |
| Custom Scripts (N-grams) | To extract and catalog word sequences for stylistic analysis. | Reduces raw text to non-identifiable linguistic features, supporting the GDPR principle of data minimization. |
Workflow: The following diagram illustrates the compliant data collection and anonymization workflow.
Protocol 2: Sovereign Data Processing and Model Training
Objective: To process data and train forensic text comparison models (e.g., for authorship attribution or AI-generated text detection) within a data-sovereign architecture.
Workflow: The following diagram illustrates the sovereign data processing and model training workflow, ensuring data remains within a trusted legal jurisdiction.
Methodology:
- Infrastructure: Utilize sovereign cloud offerings (e.g., Google Distributed Cloud Edge, Azure Stack) or on-premises high-performance computing clusters to ensure data jurisdiction is maintained [53].
- Algorithm Selection: Implement and compare traditional and modern text comparison algorithms. Feature-based methods, such as a Poisson model for likelihood ratio estimation, have been shown to outperform simpler score-based methods in forensic text comparison [55].
- Model Validation: For tasks like AI-paraphrased text detection, a comprehensive comparison of multiple algorithms is essential. One study evaluated 19 classification algorithms using word unigrams and character multigrams, achieving high accuracy on English texts [56].
Table 3: Sovereign vs. Non-Sovereign Data Processing
| Aspect | Sovereign-Compliant Approach | Non-Compliant Risk |
|---|---|---|
| Cloud Infrastructure | Sovereign cloud, on-premises, or hybrid models with data localization guarantees. | Public cloud with data stored in jurisdictions without adequate data protection (e.g., subject to U.S. CLOUD Act). |
| Encryption | Bring Your Own Encryption (BYOE) or client-side encryption with user-controlled keys. | Provider-managed encryption, where the provider holds decryption keys. |
| Text Model Training | Training occurs within sovereign infrastructure on permissioned datasets. | Training on scraped public data (e.g., Clearview AI precedent) or using cloud-based AI services that export data. |
| Evidence Admissibility | High; due to verifiable chain of custody and compliance with data localization laws. | Low; evidence may be challenged if data handling violates sovereignty or privacy laws. |
Experimental Protocols for Forensic Text Comparison
Protocol 3: Experiment on AI-Paraphrased Text Detection
Objective: To evaluate the performance of various classification algorithms in detecting AI-paraphrased text, a growing challenge for academic integrity [56].
Methodology:
- Dataset Generation:
- Source: Collect human-written texts (e.g., academic abstracts) [56].
- AI-Paraphrasing: Use a GPT model API to generate paraphrased versions. The model temperature can be adjusted (e.g., set to 0 for predictability) to create different datasets [56].
- Labeling: Form two classes: human-written and AI-paraphrased.
- Feature Extraction: Convert texts into two feature sets:
- Word Unigrams: Frequency of single words.
- Character Multigrams: Frequency of character sequences.
- Algorithm Training: Train a suite of 19 classification algorithms (e.g., Logistic Regression, Support Vector Machines, Random Forest) on the feature sets [56].
- Performance Assessment: Use metrics like accuracy to evaluate performance. Studies have achieved accuracy of 95% or more on English corpora, though performance may be lower (~85%) for minor languages due to inadequate NLP resources [56].
Protocol 4: Experiment on Authorship Attribution
Objective: To quantify the strength of evidence for authorship attribution using a likelihood ratio (LR) framework, moving beyond simple similarity measures.
Methodology:
- Feature-Based Method:
- Model: Implement a Poisson model for likelihood ratio estimation. This method is theoretically more appropriate for textual data as it can assess both the similarity and typicality of documents, unlike distance-based models [55].
- Feature Selection: Apply feature selection techniques to improve performance further [55].
- Score-Based Method (Baseline):
- Evaluation:
- Metric: Use the log-LR cost (Cllr) to assess the performance of both methods. Research demonstrates that the feature-based (Poisson model) method outperforms the score-based (Cosine) method, yielding a better Cllr by approximately 0.09 under best-performing settings [55].
Building forensic text comparison datasets and models requires a proactive, integrated approach to legal compliance and technical execution. By adopting the protocols outlined—from sovereign data management and rigorous anonymization to the use of forensically validated algorithms like the Poisson model for likelihood ratios—researchers can create robust, legally defensible datasets. This framework ensures that the critical work of advancing forensic text comparison remains both scientifically valid and aligned with the evolving global standards of privacy, GDPR, and data sovereignty.
Ensuring Reliability: Validation Frameworks and Model Performance
A Standardized Methodology for Empirical Validation of FTC Datasets
The empirical validation of datasets is a foundational requirement for developing a scientifically defensible and demonstrably reliable framework for Forensic Text Comparison (FTC). Within the broader thesis of constructing relevant datasets for FTC research, validation ensures that methods perform as expected under conditions mirroring real casework. The core challenge in FTC lies in moving beyond mere technical functionality to ensure that systems are empirically validated under conditions that reflect the specific circumstances of the case under investigation and using data relevant to that case [6]. Failure to adhere to these requirements risks misleading the trier-of-fact, as system performance measured under idealized laboratory conditions may not reflect performance in real-world, messy forensic contexts characterized by topic mismatch, genre variation, and other confounding factors.
This document outlines a standardized methodology to address this gap, providing application notes and protocols for researchers and scientists engaged in developing and curating datasets for forensic linguistic research. The principles outlined are also pertinent for professionals in drug development and other fields where robust, validated textual analysis is critical for regulatory submissions or research integrity.
Core Requirements for Empirical Validation
Empirical validation in forensic science broadly requires that the evaluation of a system or methodology must replicate the conditions of the case under investigation and utilize data relevant to the case [6]. For FTC datasets, this translates into two non-negotiable requirements, which also serve as the primary justification for a standardized validation methodology:
Requirement 1: Reflecting Casework Conditions. The validation process must simulate the specific challenges present in real forensic texts. A predominant and challenging condition is mismatch in topics between the known and questioned texts. Other conditions can include mismatches in genre, formality, medium, time interval between writings, and text length [6]. The dataset must be constructed and validated to account for these variables.
Requirement 2: Using Relevant Data. The data used for validation must be pertinent to the case context. This means that if a case involves, for example, informal text messages, the validation dataset should not be built solely from formal literary essays. The linguistic register, demographic background of the authors, and communicative purpose of the texts must be representative [6].
The table below summarizes the primary objectives and inherent challenges of empirical validation for FTC datasets.
Table 1: Core Objectives and Challenges in FTC Dataset Validation
| Objective | Description | Primary Challenge |
|---|---|---|
| Performance Estimation | To provide a realistic estimate of how an FTC system will perform in actual casework. | Avoiding over-optimistic performance figures derived from ideal, matched-topic conditions that do not reflect real-world complexities [6]. |
| System Reliability | To build confidence that the FTC system produces demonstrably reliable and accurate results. | The "black box" nature of some complex algorithms, which can make it impossible to ascertain the basis for a result, raising concerns about transparency and explainability [58]. |
| Method Comparison | To allow for a fair and meaningful comparison of different FTC methodologies. | Ensuring all methodologies are evaluated on a level playing field using the same, case-relevant validation datasets and protocols. |
| Bias Identification | To uncover and quantify potential biases in the model, such as those related to demographic factors. | The lack of large, diverse, and well-annotated datasets that capture the full spectrum of linguistic variation across different populations [59]. |
Quantitative Data and Validation Metrics
A robust validation framework for FTC relies on quantitative measurements and statistical models, interpreted within the Likelihood-Ratio (LR) framework [6]. The LR provides a transparent and logically sound measure of evidence strength.
The Likelihood-Ratio Framework
The LR is calculated as the ratio of two probabilities [6]:
LR = p(E|Hp) / p(E|Hd)
Where:
- E: The evidence (i.e., the linguistic features of the questioned and known texts).
- Hp: The prosecution hypothesis (e.g., "The suspect is the author of the questioned text").
- Hd: The defense hypothesis (e.g., "Someone other than the suspect is the author of the questioned text").
An LR > 1 supports Hp, while an LR < 1 supports Hd. The further the LR is from 1, the stronger the evidence.
Validation Metrics and Data Presentation
Validation requires quantifying the performance of the LR system itself. Key metrics include:
- Cllr (Log-Likelihood-Ratio Cost): A primary metric that assesses the overall performance of an LR-based system, penalizing both misleading LRs (>1 when Hd is true) and weak LRs (~1 when Hp is true). Lower Cllr values indicate better performance [6].
- Tippett Plots: A graphical tool that shows the cumulative proportion of LRs for same-author and different-author comparisons. It visually represents the discrimination and calibration of the system [6].
The following table synthesizes hypothetical but representative outcomes from an FTC validation study, illustrating how different validation conditions impact performance metrics.
Table 2: Comparative Validation Results Under Different Conditions
| Validation Condition | Mean Cllr (95% CI) | % Misleading Evidence (LR >1 for Hd, LR <1 for Hp) | Efficiency (Rate of | LR | > 10 for Hp) |
|---|---|---|---|---|---|
| Matched Topics (Violates Requirement 1) | 0.15 (0.12-0.18) | 2.5% | 88% | ||
| Mismatched Topics (Fulfills Requirement 1) | 0.41 (0.35-0.47) | 8.7% | 65% | ||
| Mismatched Topics & Genres | 0.68 (0.59-0.77) | 15.2% | 42% |
This data clearly demonstrates that system performance degrades under more realistic, mismatched conditions, underscoring why validation must replicate casework challenges.
Experimental Protocols
This section provides detailed, step-by-step protocols for key experiments in the validation of FTC datasets.
Protocol 1: Validation Under Topic Mismatch
1. Objective: To assess the performance and calibration of an FTC system when the known and questioned texts differ in topic, a common casework condition.
2. Materials:
- A curated dataset with author-labeled texts covering multiple topics per author (See Section 6: Research Reagent Solutions).
- Computing environment with the FTC statistical model (e.g., a Dirichlet-multinomial model) and calibration software (e.g., logistic regression scripts) [6].
3. Procedure: 1. Dataset Partitioning: For each author in the dataset, designate one text on a specific topic (e.g., "sports") as the questioned document (Q). 2. Known Document Selection: For the same author, select texts on a different topic (e.g., "politics") as the known documents (K). This forms a same-author (Hp) pair with topic mismatch. 3. Different-Author Pair Construction: To form different-author (Hd) pairs, take the same questioned document Q and pair it with known documents K from different authors, ensuring a mix of topic matches and mismatches. 4. Feature Extraction & LR Calculation: For each text pair (both Hp and Hd), extract quantitative linguistic features (e.g., character n-grams, syntactic markers). Calculate the LR for each pair using the chosen statistical model. 5. Logistic Regression Calibration: Apply a logistic regression calibration to the output LRs to ensure they are well-calibrated and not over- or under-confident [6]. 6. Performance Assessment: Calculate the Cllr and generate Tippett plots for the set of LRs from all tested pairs.
4. Analysis: Compare the Cllr and Tippett plots from this experiment against a control experiment where topics are matched. The degradation in performance quantifies the "topic mismatch penalty" and provides a realistic expectation of system performance for casework involving such mismatches.
Protocol 2: System Validation and Accuracy Testing
1. Objective: To determine the foundational accuracy and precision of the FTC system as part of its initial validation, akin to analytical validation in other scientific domains [60].
2. Materials:
- A large, diverse, and ground-truthed corpus of texts from a wide population of authors.
- The fully implemented FTC system, including pre-processing, feature extraction, and the LR calculation engine.
3. Procedure: 1. Define Ground Truth: Establish a set of known same-author and different-author text pairs from the corpus. 2. Blinded Testing: Execute the FTC system on all pairs in a blinded fashion. 3. Output Collection: Record the LR for each pair. 4. Statistical Analysis: - Calculate accuracy, sensitivity (true positive rate for same-author pairs), and specificity (true negative rate for different-author pairs). - Determine the system's precision and recall. - Plot ROC (Receiver Operating Characteristic) curves and calculate the AUC (Area Under the Curve). - Compute the Cllr to assess the quality of the LR values themselves.
4. Analysis: A system is considered validated for initial deployment if it meets pre-defined performance thresholds (e.g., Cllr < 0.5, AUC > 0.9). This protocol must be repeated whenever the core system algorithms are significantly updated.
Workflow and Signaling Pathways
The following diagram illustrates the logical workflow for the empirical validation of an FTC dataset and methodology, integrating the core requirements and experimental protocols.
FTC Validation Workflow
The validation process is a cycle. Failure to meet performance thresholds requires refinement of the model or, crucially, the dataset itself, before the validation process is repeated.
The Scientist's Toolkit: Research Reagent Solutions
The following table details essential "research reagents"—the datasets, software, and statistical tools—required for conducting empirical validation in FTC.
Table 3: Essential Research Reagent Solutions for FTC Validation
| Item Name | Type | Function / Application | Validation Role |
|---|---|---|---|
| Diverse Text Corpus | Dataset | A large, ground-truthed collection of texts from many authors, covering multiple topics, genres, and time periods. | Serves as the raw material for constructing validation datasets that fulfill Requirement 2 (relevance) [6]. |
| Topic-Annotated Sub-Corpus | Dataset | A subset of the main corpus where each text is meticulously labeled for its topic (e.g., sports, politics, technology). | Enables the specific validation of system performance under topic mismatch (Protocol 1) [6]. |
| Feature Extraction Engine | Software | A tool (e.g., using Python NLTK, spaCy) to convert raw text into quantitative features (n-grams, POS tags, syntactic features). | Provides the quantitative measurements (E) that are the input for the statistical model, a key element of the scientific approach [6]. |
| Likelihood Ratio System | Software / Statistical Model | A system (e.g., a Dirichlet-multinomial model) that calculates an LR based on the extracted features from questioned and known texts. | The core inference engine under test. Its output is the subject of the validation process [6]. |
| Calibration Tool | Software / Statistical Tool | A module (e.g., using logistic regression) to adjust raw LR outputs to ensure they are meaningful and well-calibrated. | Critical for ensuring that an LR of 10 actually corresponds to a 10:1 strength of evidence, a requirement for reliable interpretation [6]. |
| Validation Metrics Package | Software | A script or package to calculate Cllr, generate Tippett plots, and compute other performance metrics like AUC. | Provides the objective, quantitative assessment of system performance required for empirical validation [6]. |
Adherence to the standardized methodology outlined in these application notes and protocols is paramount for advancing Forensic Text Comparison as a rigorous scientific discipline. By mandating that validation replicates real-world casework conditions and uses relevant data, researchers can generate datasets and systems that are not only technically proficient but also forensically credible and court-ready. This structured approach to empirical validation, centered on the Likelihood-Ratio framework and transparent metrics, provides the demonstrable reliability required by the scientific and legal communities, ensuring that FTC findings are both defensible and actionable.
The application of the likelihood ratio (LR) framework to forensic text comparison represents a significant advancement in the objective evaluation of authorship attribution evidence. This framework allows for the quantification of evidence strength, providing a clear and statistically sound method for expressing how much more likely the evidence is under one proposition (e.g., the questioned text was written by a specific suspect) compared to an alternative proposition (e.g., the questioned text was written by someone else) [7]. The core challenge in validating these methods lies in ensuring that the data sets and validation procedures are not only statistically robust but also directly relevant to the conditions encountered in real casework, where text samples can vary dramatically in length, register, and complexity.
Core Validation Data and Performance Metrics
A foundational experiment in forensic text comparison demonstrated the critical impact of sample size on system performance. Using chatlog messages from 115 authors, researchers investigated authorship attribution with stylometric features across four different text lengths [7]. The quantitative results are summarized in the table below.
Table 1: Impact of Text Sample Size on Authorship Attribution Performance [7]
| Sample Size (Words) | Discrimination Accuracy (%) | Log-Likelihood Ratio Cost (Cllr) |
|---|---|---|
| 500 | ~76 | 0.68258 |
| 1000 | - | - |
| 1500 | - | - |
| 2500 | ~94 | 0.21707 |
This data underscores a fundamental principle of validation: performance is not static but is a function of the data's properties. A method validated on long, formal documents may not perform equally well on short, informal text messages. Therefore, a core validation requirement is to establish performance metrics across a spectrum of conditions representative of real-world evidence.
Experimental Protocol for Method Validation
The following protocol provides a detailed methodology for validating forensic text comparison systems within the likelihood ratio framework, ensuring reliability and relevance to casework.
Protocol: Validation of Stylometric Features for Forensic Text Comparison
1. Objective: To validate a set of stylometric features for use in forensic text comparison by quantifying system performance across varying sample sizes and calculating the strength of evidence using the Multivariate Kernel Density formula within a likelihood ratio framework [7].
2. Materials and Reagents:
- Text Corpora: A collection of text samples from a known set of authors. The chatlog corpus used in the foundational study contained real chatlog evidence from legal proceedings [7].
- Computing System: A computer with sufficient processing power for statistical computing and text analysis.
- Software: Software capable of text processing, feature extraction, and multivariate statistical analysis (e.g., R, Python with scikit-learn).
3. Methodology:
- Step 1: Author Selection and Text Sampling: Select a representative cohort of authors. For each author, create text samples of varying lengths (e.g., 500, 1000, 1500, and 2500 words) from their available writings [7].
- Step 2: Feature Extraction: From each text sample, extract the predefined set of stylometric features. The validated robust features include [7]:
- Average character number per word token
- Punctuation character ratio
- Vocabulary richness features
- Step 3: Likelihood Ratio Calculation: Model authorship attribution using the Multivariate Kernel Density formula to compute likelihood ratios for the evidence. This involves comparing the similarity of the questioned text to known samples from the suspect and to samples from a relevant population [7].
- Step 4: Performance Assessment: Evaluate system performance using the following primary and secondary metrics [7]:
- Primary Metric: Log-likelihood ratio cost (Cllr). A lower Cllr indicates better system discrimination.
- Secondary Metrics: Credible intervals and Equal Error Rate (EER).
- Step 5: Validation and Verification: In line with collaborative validation models, this process involves phases of developmental validation and internal validation [61]. The originating laboratory should publish its validation data to allow other laboratories to conduct verification, thereby streamlining implementation and ensuring cross-laboratory comparability [61].
Workflow and Feature Relationships
The following diagram illustrates the logical workflow for the validation of a forensic text comparison method, from data preparation through to performance assessment.
Validation Workflow
The robust stylometric features identified in validation experiments do not operate in isolation but form an interconnected system for distinguishing authorship. The diagram below depicts the relationships between these core feature categories.
Feature Analysis
The Scientist's Toolkit: Research Reagent Solutions
This table details the essential "research reagents" — the core data, features, and models — required for experiments in forensic text comparison.
Table 2: Essential Research Reagents for Forensic Text Comparison [7]
| Item Name | Type | Function in Research |
|---|---|---|
| Authenticated Text Corpus | Data Set | Serves as the ground-truth population for developing and testing authorship models; must be representative of casework. |
| Stylometric Feature Set | Metric Set | Quantifiable aspects of writing style (e.g., word length, punctuation) that serve as the measurable evidence for comparison. |
| Likelihood Ratio Framework | Statistical Model | Provides the mathematical structure for objectively quantifying the strength of evidence for one authorship proposition over another. |
| Multivariate Kernel Density | Computational Tool | A formula used to estimate the probability density of the multivariate stylometric features, which is essential for calculating the LR [7]. |
| Performance Metrics (Cllr, EER) | Validation Tool | Standardized measures to evaluate the discrimination accuracy and calibration of the forensic text comparison system. |
Within the domain of forensic text comparison research, the objective evaluation of textual evidence is paramount. The development of robust, relevant datasets necessitates the use of standardized quantitative metrics to validate and compare the performance of different analytical methods. This document provides detailed Application Notes and Protocols for three pivotal metrics—BLEU, ROUGE, and Log-Likelihood-Ratio Cost (Cllr)—framed within the context of creating and evaluating forensic textual datasets [48]. These metrics facilitate the transition from qualitative assessments to reproducible, quantitative evaluations, which is a cornerstone of the scientific method in digital forensics and related fields [4].
Metric Definitions and Forensic Relevance
The following table summarizes the core characteristics, strengths, and limitations of each metric in a forensic context.
Table 1: Overview of Quantitative Metrics for Forensic Text Evaluation
| Metric | Primary Forensic Application | Core Principle | Key Strengths | Key Limitations |
|---|---|---|---|---|
| BLEU [62] [63] | Machine Translation, Text Generation | Measures n-gram precision against reference text(s). | Inexpensive to compute; language-independent; correlates well with human judgment. | Does not capture semantic meaning; ignores word order with smaller n-grams; treats all words as equally important. |
| ROUGE [62] [63] | Text Summarization, Content Overlap | Measures n-gram recall against reference text(s). | Recall-oriented, ensuring key information is captured; multiple variants (e.g., ROUGE-L) assess sequence similarity. | Poor capture of semantic similarity; limited ability to penalize overly verbose or irrelevant text. |
| Cllr [64] [65] | Authorship Attribution, Forensic Text Comparison | Evaluates the quality of Likelihood Ratio (LR) evidence. | Penalizes misleading evidence; assesses both calibration and discrimination; a strictly proper scoring rule. | Interpretation of numerical value is not intuitive; requires an empirical set of LRs for calculation. |
Detailed Methodologies and Experimental Protocols
BLEU Score Calculation Protocol
The BLEU score evaluates generated text by calculating the geometric mean of n-gram precisions between a candidate text and one or more reference texts, modified by a brevity penalty [62] [63].
Protocol Steps:
- Tokenization and N-gram Generation: Split the candidate and reference texts into words (tokens) and generate n-grams of orders 1 through N (typically N=4).
- Calculate Clipped N-gram Precision ((p_n)): For each n-gram order, count the number of n-grams in the candidate that appear in the reference. The count is "clipped" to the maximum number of times the n-gram appears in any single reference text to prevent inflation from repetitive words.
- (pn = \frac{\sum{Candidatengrams} Count{clip}(n\text{-}gram)}{\sum{Candidatengrams} Count(n\text{-}gram)})
- Compute Geometric Mean ((GMp)): Calculate the weighted geometric mean of all precision scores.
- (GMp = \exp\left(\sum{n=1}^{N} wn \log(pn)\right)) where (wn) are weights, typically (1/N).
- Apply Brevity Penalty ((BP)): Penalize candidate texts that are shorter than the reference.
- (BP = \begin{cases} 1 & \text{if } lc > lr \ \exp(1 - lr / lc) & \text{if } lc \leq lr \end{cases})
- Where (lc) is the candidate length and (lr) is the effective reference length.
- Final BLEU Score:
- (BLEU = BP \cdot GM_p)
Example Calculation:
Candidate: "They cancelled the match because it was raining."
Reference: "They cancelled the match because of bad weather."
Table 2: BLEU Score Component Calculation Example
| N-gram (n) | Candidate N-grams | Reference N-grams | Matches | Clipped Precision ((p_n)) |
|---|---|---|---|---|
| 1 | 8 | 7 | 5 | 5/8 = 0.625 |
| 2 | 7 | 4 | 3 | 3/7 ≈ 0.571 |
| 3 | 6 | 3 | 2 | 2/6 ≈ 0.333 |
| 4 | 5 | 2 | 1 | 1/5 = 0.200 |
| Brevity Penalty ((BP)) | Candidate length = 8, Reference length = 7 | (BP = \exp(1 - 7/8) \approx 0.882) | ||
| BLEU Score | (0.882 \times \exp(0.25 \times (\log(0.625) + \log(0.571) + \log(0.333) + \log(0.200))) \approx 0.328) |
ROUGE Score Calculation Protocol
ROUGE is a set of recall-oriented metrics. The most common variants are ROUGE-N (n-gram recall) and ROUGE-L (longest common subsequence) [62] [66]. The protocol below outlines the calculation of the F1 score for ROUGE-N.
Protocol Steps:
- Tokenization and N-gram Generation: Split the candidate and reference texts into n-grams.
- Calculate Recall and Precision:
- Recall ((R)): The proportion of reference n-grams that appear in the candidate.
- (R = \frac{\text{Number of overlapping n-grams}}{\text{Total n-grams in reference text}})
- Precision ((P)): The proportion of candidate n-grams that appear in the reference.
- (P = \frac{\text{Number of overlapping n-grams}}{\text{Total n-grams in candidate text}})
- Recall ((R)): The proportion of reference n-grams that appear in the candidate.
- Compute F1-Score: The harmonic mean of precision and recall.
- (F1 = 2 \cdot \frac{P \cdot R}{P + R})
Example Calculation:
Candidate: "He was extremely happy last night."
Reference: "He was happy last night."
Table 3: ROUGE-1 and ROUGE-2 Score Calculation Example
| Metric | Precision (P) | Recall (R) | F1-Score |
|---|---|---|---|
| ROUGE-1 | 5/6 ≈ 0.833 | 5/5 = 1.000 | 2(0.8331.000)/(0.833+1.000) ≈ 0.909 |
| ROUGE-2 | 3/5 = 0.600 | 3/4 = 0.750 | 2(0.6000.750)/(0.600+0.750) ≈ 0.667 |
Log-Likelihood-Ratio Cost (Cllr) Calculation Protocol
Cllr is the primary metric for validating the performance of a forensic Likelihood Ratio (LR) system. It measures the cost of soft detection decisions across all operating points, penalizing both poor discrimination and poor calibration [64] [65].
Protocol Steps:
- Generate Likelihood Ratios: Using a background dataset, compute LRs for two sets of comparisons: same-source (H1 true) and different-source (H2 true).
- Compute Cllr: Apply the following formula to the sets of LRs.
- ( Cllr = \frac{1}{2} \cdot \left( \frac{1}{N{H1}} \sum{i=1}^{N{H1}} \log2(1 + \frac{1}{LR{H1,i}}) + \frac{1}{N{H2}} \sum{j=1}^{N{H2}} \log2(1 + LR{H2,j}) \right) )
- (N{H1}): Number of samples where H1 is true.
- (N{H2}): Number of samples where H2 is true.
- (LR{H1,i}): LR value for the i-th sample where H1 is true.
- (LR{H2,j}): LR value for the j-th sample where H2 is true.
- Interpretation: A Cllr of 0 indicates a perfect system. A Cllr of 1 indicates an uninformative system (LR=1). Lower values indicate better performance [64].
Relevant Data: A study on authorship attribution using a bag-of-words model and cosine distance reported Cllr values of 0.706, 0.453, and 0.307 for documents of 700, 1400, and 2100 words, respectively, demonstrating improved performance with longer document lengths [65].
Workflow Visualization
The following diagram illustrates the generic workflow for applying these metrics in a forensic text comparison study, from data preparation to performance assessment.
Figure 1: Forensic Text Comparison Workflow
The Scientist's Toolkit: Research Reagent Solutions
This section details the essential materials, software, and data resources required for conducting experiments in forensic text comparison.
Table 4: Essential Research Reagents and Tools for Forensic Text Comparison
| Reagent/Tool | Function/Description | Example/Reference |
|---|---|---|
Python evaluate Library |
A standardized library for computing and comparing model metrics, including BLEU and ROUGE. | pip install evaluate [62] |
| Forensic Text Corpus | A background dataset of known authorship for calculating score distributions and LRs. | Amazon Product Data Authorship Verification Corpus [65] |
| Specialized Forensic Datasets | Domain-specific datasets for training and testing models on real-world tasks. | ForensicsData (malware analysis Q-C-A dataset) [4] |
| Visualization Tools | Software for generating Tippett Plots and Empirical Cross-Entropy (ECE) plots to assess LR performance. | Used in conjunction with Cllr for diagnostic analysis [64] [65] |
Quantitative Performance Comparison
Performance between leading LLMs can vary significantly depending on the task domain. A comparative analysis in a clinical setting, evaluating serial radiology reports for oncological issues, found that GPT-4 outperformed Gemini. The results are summarized in the table below [67].
Table 1: Performance in Analyzing Serial Radiology Reports [67]
| Model | Accuracy in Matching Findings | Precision | Recall | F1-Score |
|---|---|---|---|---|
| GPT-4 | 96.2% | 0.68 | 0.91 | 0.78 |
| Gemini | 91.7% | 0.63 | 0.80 | 0.70 |
Conversely, a study focused on translating radiology reports into simple Hindi demonstrated that the performance hierarchy could change, and was also highly sensitive to the specific prompt used. Gemini outperformed others with one prompt, while GPT-4o was superior with another [68].
Table 2: Performance in Radiology Report Translation (BLEU Scores) [68]
| Model | Prompt 1: "Translate this radiology report into simple Hindi" | Prompt 2: "Translate this radiology report into simple vernacular Hindi explainable to a 15-year-old" |
|---|---|---|
| GPT-4o | 0.098 | 0.281 |
| GPT-4 | 0.092 | 0.124 |
| Gemini | 0.147 | 0.182 |
| Claude Opus | 0.070 | 0.127 |
Furthermore, broader benchmark results from 2025 highlight the evolving and specialized nature of model capabilities, which is critical for selecting a model for a specific research task [69] [70].
Table 3: Selected 2025 Benchmark Performance (Percentage Scores) [69] [70]
| Model | Software Engineering (SWE-bench) | Reasoning (GPQA Diamond) | High School Math (AIME 2025) |
|---|---|---|---|
| Claude Sonnet 4.5 | 82.0 | - | - |
| GPT 5.1 | 76.3 | 88.1 | - |
| Gemini 3 Pro | 76.2 | 91.9 | 100 |
| Claude Opus 4.1 | - | - | 90.0 (AIME) |
Experimental Protocols for FTC Evaluation of LLMs
To ensure the scientific validity of using LLMs in FTC, empirical validation is required. The following protocols provide a framework for thesis researchers to design relevant experiments and datasets.
Protocol 1: Core Performance Benchmarking
This protocol measures the baseline accuracy and error rates of an LLM in a controlled, FTC-like text comparison task.
- Objective: To determine the model's accuracy, false positive rate (incorrectly attributing same authorship), and false negative rate (incorrectly excluding same authorship) under ideal conditions.
- Dataset Curation:
- Source: Compile a ground-truthed corpus of text pairs from a known set of authors. The corpus should include:
- Mated Pairs: Text pairs known to be written by the same author.
- Non-Mated Pairs: Text pairs known to be written by different authors.
- Relevance: To meet forensic validation standards, the data must be relevant to casework. This includes incorporating realistic variations in topic, genre, and writing style between compared documents [6].
- Source: Compile a ground-truthed corpus of text pairs from a known set of authors. The corpus should include:
- Task Design: For each text pair, the LLM must be prompted to analyze the texts and output a conclusion based on a standardized scale. A six-level scale is recommended for granularity [67]:
- Written by the same author / Probably written by the same author / No conclusion / Probably not written by the same author / Not written by the same author / Other malignancy (for specific contexts).
- Analysis:
Protocol 2: Robustness and Cross-Topic Validation
This protocol tests the model's performance under the adverse condition of topic mismatch, a common challenge in real casework [6].
- Objective: To evaluate the degradation in LLM performance when the questioned and known documents are on different topics.
- Dataset Curation:
- Create a dataset where mated pairs are deliberately written on different topics by the same author.
- The non-mated pairs should be matched for topic to ensure the model cannot use topic similarity as a simple proxy for authorship.
- Task Design: The task is identical to Protocol 1. The key is to use a carefully engineered prompt that instructs the model to focus on stylistic and linguistic patterns rather than semantic content [67].
- Analysis:
- Perform a comparative analysis of the model's performance (e.g., F1-Score, False Positive rate) on the cross-topic dataset versus the topic-matched dataset from Protocol 1.
- A robust model will show minimal performance degradation.
Workflow Visualization
The following diagram illustrates the integrated experimental workflow, from dataset preparation to performance analysis, highlighting the critical steps for forensic validation.
The Scientist's Toolkit: Research Reagent Solutions
For researchers developing datasets and experiments in this field, the following "research reagents" are essential.
Table 4: Essential Materials for FTC-LLM Research
| Item / Solution | Function in FTC Research |
|---|---|
| Ground-Truthed Text Corpora | Serves as the benchmark dataset for training and validation. Must include mated and non-mated pairs with known authorship to establish a reliable ground truth [6] [71]. |
| Standardized Conclusion Scale | Provides a consistent and legally defensible framework for LLMs (and human examiners) to report the strength of evidence, enabling quantitative comparison (e.g., 5- or 6-level scales) [67] [71]. |
| Likelihood Ratio (LR) Framework | The statistical foundation for quantitatively evaluating the strength of textual evidence, ensuring logical and legally correct interpretation [6] [8]. |
| Poisson Model / Dirichlet-Multinomial Model | A feature-based statistical model used as a robust baseline or component in an LR system for authorship comparison, outperforming simple distance-based scores [8]. |
| Validation Software (e.g., for Cllr calculation) | Computational tools to calculate performance metrics like the log-likelihood-ratio cost (Cllr), which assesses the validity and discriminability of the entire LR system [6] [8]. |
Conclusion
The development of robust datasets is paramount for advancing the scientific rigor and legal admissibility of forensic text comparison. This guide synthesizes a clear path forward, emphasizing that foundational linguistic principles must be coupled with modern methodologies like LLM-driven synthetic data generation, all structured within forensically sound formats such as Q-C-A. Success hinges on proactively troubleshooting critical issues like bias and topic mismatch and, most importantly, implementing a rigorous, standardized validation framework based on the Likelihood Ratio. Future progress depends on creating larger, more diverse, and realistic datasets that reflect complex casework conditions. This will enable more accurate, reliable, and transparent FTC tools, ultimately strengthening the role of textual evidence in the pursuit of justice and fostering greater collaboration across the research community to address evolving digital challenges.
References
- 1. idiolect - Forensic Authorship Analysis [https://andreanini.github.io/idiolect/]
- 2. idiolect: a new R package for Forensic Authorship Analysis [https://andreanini.com/2024/08/28/idiolect-a-new-r-package-for-forensic-authorship-analysis/]
- 3. Quantitative Text Analysis (MAXDictio) [https://www.maxqda.com/quantitative-text-analysis]
- 4. a Digital Forensics Dataset for Large Language Models [https://arxiv.org/html/2509.05331v1]
- 5. A comprehensive and quantitative comparison of text-mining ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5831415/]
- 6. Validation in Forensic Text Comparison: Issues and ... [https://www.mdpi.com/2226-471X/9/2/47]
- 7. Strength of forensic text comparison evidence from stylometric ... [https://researchportalplus.anu.edu.au/en/publications/strength-of-forensic-text-comparison-evidence-from-stylometric-fe/]
- 8. Feature-Based Forensic Text Comparison Using a Poisson ... [https://aclanthology.org/2020.alta-1.4/]
- 9. The admissibility of digital evidence from open-source forensic ... [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0331683]
- 10. The admissibility of digital evidence from open-source ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12431127/]
- 11. The Legal Implications of Altered Evidence: What You ... [https://eclipseforensics.com/the-legal-implications-of-altered-evidence-what-you-need-to-know/]
- 12. Quantification of forensic genetic evidence: Comparison ... [https://www.sciencedirect.com/science/article/pii/S1872497322000564]
- 13. Forensic Handwritten Document Analysis Challenge [https://www.metroxraine.org/forensic-handwritten-document-alaysis-challenge]
- 14. Investigating Methods for Forensic Analysis of Social ... [https://www.frontiersin.org/journals/computer-science/articles/10.3389/fcomp.2025.1673393/full]
- 15. Top Court Cases That Changed Digital Privacy Evidence ... [https://www.auditzo.com/blog/digital-privacy-evidence-standards-top-court-cases-2020-2025]
- 16. A guide to ISO 21043 Forensic Sciences from the ... [https://www.sciencedirect.com/science/article/pii/S1355030625000887]
- 17. Smartphone Forensics: What Defense Attorneys Should ... [https://www.nacdl.org/Content/Smartphone-Forensics-What-Defense-Attorneys-Should]
- 18. The Alarming Ease of Fabricating Text Message Evidence ... [https://www.envistaforensics.com/knowledge-center/insights/articles/pixels-and-perjury-the-alarming-ease-of-fabricating-text-message-evidence-and-what-to-do-about-it/]
- 19. Commentary on: Aggadi N, Zeller K, Busey T. Quantifying ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12584119/]
- 20. Using LLMs for Synthetic Data Generation: The Definitive ... [https://www.confident-ai.com/blog/the-definitive-guide-to-synthetic-data-generation-using-llms]
- 21. Synthetic Data Generation Methods for LLMs | by M [https://medium.com/foundation-models-deep-dive/synthetic-data-generation-methods-for-llms-3aff1452ce68]
- 22. Live LLM-Synthetic-Data Papers (Updated to July,2025) [https://github.com/pengr/LLM-Synthetic-Data]
- 23. Large Language Models in Digital Forensics [https://medium.com/@aasthathakker/large-language-models-in-digital-forensics-475cb8115b7f]
- 24. A psycholinguistic NLP framework for forensic text analysis ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12582947/]
- 25. A local large language model for digital forensics [https://www.sciencedirect.com/science/article/pii/S2666281725000113]
- 26. Text has enhanced contrast | ACT Rule | WAI [https://www.w3.org/WAI/standards-guidelines/act/rules/09o5cg/]
- 27. Text color must provide high contrast with its background [https://docs.acquia.com/web-governance/text-color-must-provide-high-contrast-its-background]
- 28. Using color | U.S. Web Design System (USWDS) [https://designsystem.digital.gov/design-tokens/color/overview/]
- 29. Contrast requirements for WCAG 2.2 Level AA [https://www.makethingsaccessible.com/guides/contrast-requirements-for-wcag-2-2-level-aa/]
- 30. Visualizing and Timelining in Digital Forensic Analysis [https://frsecure.com/blog/visualizing-and-timelining-in-digital-forensic-analysis/]
- 31. contrast-color() - CSS - MDN Web Docs [https://developer.mozilla.org/en-US/docs/Web/CSS/Reference/Values/color_value/contrast-color]
- 32. Open Source Malware Index Q3 2025: High-Severity ... [https://www.sonatype.com/blog/open-source-malware-index-q3-2025]
- 33. Social Media Trends 2025 [https://www.hootsuite.com/research/social-trends?srsltid=AfmBOop4ZYoO8klFv_ei3YJL_3ipU-EK58xisrPutocjA5Ncope1lEao]
- 34. Current and Emerging Malware Trends from 2025 [https://www.bitsight.com/blog/current-malware-trends-2025]
- 35. Authorship Verification based on the Likelihood Ratio of ... [https://arxiv.org/html/2403.08462v1]
- 36. Authorship verification with the package 'stylo' [https://computationalstylistics.github.io/blog/imposters/]
- 37. A psycholinguistic NLP framework for forensic text analysis ... [https://www.frontiersin.org/journals/artificial-intelligence/articles/10.3389/frai.2025.1669542/full]
- 38. AIDBench: A benchmark for evaluating the authorship ... [https://arxiv.org/html/2411.13226v1]
- 39. Ethical Use of Training Data: Ensuring Fairness & ... [https://lamarr-institute.org/blog/ai-training-data-bias/]
- 40. Building AI Fairness by Reducing Algorithmic Bias [https://tepperspectives.cmu.edu/all-articles/building-ai-fairness-by-reducing-algorithmic-bias/]
- 41. Landmark AI framework sets new standard for tackling ... [https://www.dlapiper.com/en/insights/publications/ai-outlook/2025/landmark-ai-framework-sets-new-standard-for-tackling-algorithmic-bias]
- 42. FAIR Principles [https://www.go-fair.org/fair-principles/]
- 43. Post-processing methods for mitigating algorithmic bias in ... [https://bmcdigitalhealth.biomedcentral.com/articles/10.1186/s44247-025-00166-4]
- 44. CSAFE Forensic Science Dataset Portal [https://forensicstats.org/data/]
- 45. Benchmarking Multimodal Large Language Models for ... [https://www.medrxiv.org/content/10.1101/2025.07.06.25330972v1.full-text]
- 46. Algorithm fairness in artificial intelligence for medicine and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10632090/]
- 47. Forensic Science Strategic Research Plan, 2022-2026 ... [https://nij.ojp.gov/topics/articles/forensic-sciences-strategic-research-plan-2022-2026]
- 48. Towards a standardized methodology and dataset for ... [https://www.sciencedirect.com/science/article/pii/S2666281725001222]
- 49. Understanding WCAG 2 Contrast and Color Requirements [https://webaim.org/articles/contrast/]
- 50. Color contrast - Accessibility - MDN Web Docs - Mozilla [https://developer.mozilla.org/en-US/docs/Web/Accessibility/Guides/Understanding_WCAG/Perceivable/Color_contrast]
- 51. Towards Robust Synthetic Data Generation for ... [https://www.mdpi.com/2504-4990/7/3/68]
- 52. a data augmentation method based on LLMs and lexical ... [https://link.springer.com/article/10.1007/s11192-025-05355-6]
- 53. Modeling Data Sovereignty in Public Cloud—A ... [https://www.mdpi.com/2076-3417/14/23/10803]
- 54. SMS vs RCS: Strategic Comparison Guide [https://freemindtronic.com/sms-vs-rcs-comparison/]
- 55. Feature-based forensic using a Poisson model for... text comparison [https://researchportalplus.anu.edu.au/en/publications/feature-based-forensic-text-comparison-using-a-poisson-model-for-]
- 56. Comparison of algorithms for the recognition of ChatGPT ... [https://journalofbigdata.springeropen.com/articles/10.1186/s40537-025-01082-0]
- 57. Algorithms vs. Large Language Models: Text Similarity ... [https://medium.com/@j.m.olivera08/algorithms-vs-large-language-models-text-similarity-showdown-5ef1c14d9ecd]
- 58. Public comment topics and process [https://www.ftc.gov/enforcement-policy/hearings-competition-consumer-protection/public-comment-topics-process]
- 59. Everyone's Talking AI, Including the FTC: Key Takeaways ... [https://www.crowell.com/en/insights/client-alerts/everyones-talking-ai-including-the-ftc-key-takeaways-from-the-ftcs-2023-ai-guidance]
- 60. Forensic text comparison: Scientifically defensible approach ... [https://slll.cass.anu.edu.au/forensic-text-comparison-scientifically-defensible-approach-linguistic-textual-evidence]
- 61. Collaborative versus traditional method validation approach [https://pmc.ncbi.nlm.nih.gov/articles/PMC7452674/]
- 62. Quantitative Metrics Simplified for Language Model ... [https://www.analyticsvidhya.com/blog/2024/03/quantitative-metrics-simplified-for-language-model-evaluation/]
- 63. BLEU and ROUGE [https://v2docs.galileo.ai/concepts/metrics/expression-and-readability/bleu-and-rouge]
- 64. An overview of log likelihood ratio cost in forensic science [https://pmc.ncbi.nlm.nih.gov/articles/PMC11031735/]
- 65. Score-based likelihood ratios for linguistic text evidence ... [https://pubmed.ncbi.nlm.nih.gov/34481115/]
- 66. LLM Evaluation metrics explained. ROUGE score, BLEU ... [https://medium.com/data-science-in-your-pocket/llm-evaluation-metrics-explained-af14f26536d2]
- 67. A Comparative Study of GPT-4 and Gemini in Evaluating ... [https://www.sciencedirect.com/science/article/pii/S1076633224008377]
- 68. Comparative Evaluation of Large Language Models for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11651845/]
- 69. Claude 4 vs GPT-4.1 vs Gemini 2.5: 2025 AI Pricing & ... [https://itecsonline.com/post/claude-4-vs-gpt-4-vs-gemini-pricing-features-performance]
- 70. LLM Leaderboard 2025 [https://www.vellum.ai/llm-leaderboard]
- 71. Accuracy and reliability of forensic handwriting comparisons [https://pmc.ncbi.nlm.nih.gov/articles/PMC9371688/]