Building a Robust Risk Assessment Framework for Forensic Method Validation in Pharmaceutical Sciences
This article provides researchers, scientists, and drug development professionals with a comprehensive guide to implementing a risk assessment framework for forensic method validation.
Building a Robust Risk Assessment Framework for Forensic Method Validation in Pharmaceutical Sciences
Abstract
This article provides researchers, scientists, and drug development professionals with a comprehensive guide to implementing a risk assessment framework for forensic method validation. It covers foundational principles from international standards like ISO 21043, details methodological steps for application, addresses common troubleshooting scenarios, and establishes rigorous validation and comparative techniques. The content is designed to ensure that forensic methods in drug development are accurate, reliable, legally defensible, and suitable for regulatory submission, with a focus on managing uncertainties and leveraging emerging technologies such as Artificial Intelligence.
The Pillars of Forensic Validation: Principles, Standards, and Regulatory Requirements
Forensic validation is a systematic process essential for ensuring the reliability and accuracy of tools, methods, and analytical findings in forensic science. In the context of a risk assessment framework, validation provides the empirical foundation that allows researchers and practitioners to trust and defend their scientific conclusions, whether in a laboratory setting or a legal proceeding. At its core, validation refers to the process of ensuring that extracted data truly represents real-world events and that the methods used to obtain this data are robust, reproducible, and fit for purpose [1]. This process serves as a critical form of quality assurance, confirming that data is accurate, correctly interpreted, and meaningful within the specific context of a case [1].
The importance of validation extends beyond mere technical compliance. In digital forensics, for example, improperly validated evidence can be challenged for credibility in legal settings, potentially undermining case outcomes [1]. Similarly, in forensic chemistry and psychiatry, the validity of methods and tools directly impacts public safety, judicial decisions, and therapeutic interventions [2] [3] [4]. As forensic science continues to evolve with new technologies and methodologies, establishing a rigorous risk assessment framework for validation becomes paramount for ensuring that novel approaches meet the stringent requirements of scientific and legal scrutiny.
Core Dimensions of Forensic Validation
Forensic validation encompasses three interconnected dimensions, each addressing distinct aspects of the forensic workflow but collectively contributing to the overall reliability of forensic conclusions.
Tool Validation
Tool validation focuses on verifying that the software, instruments, and hardware used in forensic investigations produce accurate and consistent results. This dimension recognizes that forensic tools parse raw data into human-readable form, but no tool is infallible [1]. Parsing errors, software bugs, or unsupported data formats can lead to significant inaccuracies if undetected [1]. In digital forensics, for instance, the distinction between carved versus parsed data highlights this necessity. Parsed data is extracted from known database schemas and is generally more reliable, while carved data obtained by scanning raw data for patterns can produce false positives if not properly validated [1].
Tool validation extends to various forensic domains. In chemical analysis, Gas Chromatography-Mass Spectrometry (GC-MS) instruments require rigorous validation to ensure they detect and quantify substances accurately [3]. For forensic tools assessing risk in psychiatric populations, validation establishes whether these instruments reliably predict dangerousness or recidivism [2] [4]. The validation process for tools typically involves testing against known standards, verifying output consistency across multiple platforms, and assessing performance under different operating conditions.
Method Validation
Method validation establishes that the overall procedures and protocols used in forensic investigations are scientifically sound and consistently executable. This dimension addresses the complete analytical process rather than just the tools employed. A validated method demonstrates specificity, sensitivity, precision, and accuracy under defined operational parameters [3].
In forensic chemistry, method validation follows established guidelines such as those from the Scientific Working Group for the Analysis of Seized Drugs (SWGDRUG) and includes parameters like limit of detection (LOD), limit of quantification (LOQ), linearity, robustness, and reproducibility [3]. For example, a validated rapid GC-MS method for screening seized drugs demonstrated a 50% improvement in detection limits for key substances like cocaine and heroin, achieving detection thresholds as low as 1 μg/mL compared to 2.5 μg/mL with conventional methods [3]. The method also exhibited excellent repeatability and reproducibility with relative standard deviations (RSDs) less than 0.25% for stable compounds [3].
Analysis Validation
Analysis validation ensures that the interpretation of results is correct and contextually appropriate. This dimension addresses the human element of forensic science – how experts draw conclusions from data generated by validated tools and methods. Analysis validation involves cross-artifact corroboration, where multiple independent pieces of evidence are examined to determine if they tell a consistent story [1]. It also requires understanding the limitations of analytical techniques and recognizing when results may be misleading or inconclusive.
In digital forensics, analysis validation might involve verifying that a timestamp extracted from a device correctly accounts for timezone offsets and daylight saving time, rather than simply accepting the raw value at face value [1]. In forensic psychiatry, it entails ensuring that risk assessment scores are interpreted in the context of the individual's clinical history and current presentation, rather than being applied mechanistically [4]. Proper analysis validation acknowledges that even with validated tools and methods, interpretative errors can occur if the context and limitations of the data are not fully understood.
Table 1: Key Aspects of the Three Dimensions of Forensic Validation
| Dimension | Primary Focus | Validation Parameters | Common Challenges |
|---|---|---|---|
| Tool Validation | Instruments, software, hardware | Accuracy, consistency, output reliability, compatibility | Parser errors, software bugs, unsupported data formats, version compatibility |
| Method Validation | Procedures, protocols, workflows | Specificity, sensitivity, precision, accuracy, LOD, LOQ, robustness | Reproducibility across operators, environmental factors, matrix effects |
| Analysis Validation | Interpretation, contextualization, conclusion | Logical consistency, cross-artifact corroboration, contextual understanding | Cognitive biases, contextual misunderstandings, overinterpretation of limited data |
Experimental Protocols for Method Validation
The following section provides detailed protocols for validating forensic methods, with specific examples from forensic chemistry and risk assessment tool development.
Protocol for Validating a Rapid GC-MS Method for Seized Drug Analysis
This protocol outlines the systematic validation of a rapid Gas Chromatography-Mass Spectrometry (GC-MS) method for screening seized drugs, based on research conducted by the Dubai Police Forensic Laboratories [3].
Instrumentation and Materials
- GC-MS System: Agilent 7890B gas chromatograph connected to an Agilent 5977A single quadrupole mass spectrometer
- Column: Agilent J&W DB-5 ms column (30 m × 0.25 mm × 0.25 μm)
- Carrier Gas: Helium (99.999% purity) at a fixed flow rate of 2 mL/min
- Data Acquisition: Agilent MassHunter software (version 10.2.489) and Agilent Enhanced ChemStation software
- Reference Standards: Certified reference materials for target compounds (e.g., Tramadol, Cocaine, Codeine, Diazepam, THC, Heroin) from reputable suppliers like Cayman Chemical or Sigma-Aldrich
- Solvents: High-purity methanol (99.9%) for sample preparation
Method Optimization Procedure
Temperature Programming Optimization:
- Begin with an initial oven temperature of 80°C, held for 0.5 minutes
- Implement a ramp rate of 40°C/minute to 220°C
- Follow with a second ramp of 25°C/minute to 300°C, held for 1.5 minutes
- Maintain the transfer line temperature at 280°C
Flow Rate Optimization:
- Set helium carrier gas flow rate to 2 mL/min constant flow
- Use a 10:1 split ratio for injection
MS Parameter Configuration:
- Set ion source temperature to 280°C
- Configure quadrupole temperature at 180°C
- Utilize electron impact (EI) ionization mode at 70 eV
- Employ selected ion monitoring (SIM) mode for target compounds
Validation Parameters and Acceptance Criteria
Table 2: Validation Parameters for Rapid GC-MS Method for Seized Drug Analysis [3]
| Validation Parameter | Experimental Procedure | Acceptance Criteria | Reported Results |
|---|---|---|---|
| Limit of Detection (LOD) | Serial dilution of standards until S/N ratio ≥ 3 | Improvement over conventional methods | 50% improvement for key substances; cocaine LOD: 1 μg/mL vs. 2.5 μg/mL conventional |
| Precision (Repeatability) | Multiple injections (n=6) of same sample | RSD ≤ 2% for retention times | RSD < 0.25% for stable compounds |
| Reproducibility | Analysis by different analysts on different days | RSD ≤ 5% for retention times and peak areas | RSD < 0.25% under operational conditions |
| Specificity | Analysis of blank samples and potential interferents | No interference at retention times of target analytes | Baseline separation of all target compounds |
| Identification Accuracy | Comparison with reference standards and spectral libraries | Match quality score ≥ 90% | Match quality scores consistently > 90% across tested concentrations |
| Analysis Time | Comparison with conventional method | Significant reduction without sacrificing quality | Reduction from 30 minutes to 10 minutes total analysis time |
Application to Real Case Samples
Sample Preparation:
- For solid samples: Grind tablets/capsules to fine powder using mortar and pestle
- Extract approximately 0.1 g with 1 mL methanol via sonication for 5 minutes
- Centrifuge and transfer supernatant to GC-MS vial
- For trace samples: Swab surfaces with methanol-moistened swabs, extract swabs in 1 mL methanol via vortexing
Data Analysis:
- Compare retention times with certified standards
- Perform library searches using Wiley Spectral Library (2021 edition) and Cayman Spectral Library
- Verify identifications based on retention time and mass spectral match
Protocol for Validating a Risk Assessment Tool in Forensic Psychiatry
This protocol outlines the development and validation of a risk assessment tool for forensic psychiatry, based on the methodology used for the Dangerousness Index in Forensic Psychiatry (IPPML) [4].
Participant Recruitment and Sampling
Sample Composition:
- Recruit 261 participants (157 males, 104 females) aged 19-75 years
- Divide into experimental group (n=126) with history of forensic psychiatric examination and control group (n=135) diagnosed with schizophrenia but no forensic history
- Obtain written informed consent from all participants
- Secure ethical approval from institutional review board
Inclusion/Exclusion Criteria:
- Inclusion: Age ≥ 18 years, history of forensic psychiatric examination (for experimental group), ability to provide informed consent
- Exclusion: Uncontrolled mental illness, inability to provide informed consent, age < 18 years
Tool Development and Validation Procedure
Item Generation:
- Develop a broad set of initial items covering all potential aspects of dangerousness in forensic psychiatry
- Convene a panel of 10 experts (5 university professors, 5 medical specialists) to evaluate each statement for content validity and formal validity
- Experts rate each item on a 5-point scale from "Strongly Disagree (1)" to "Strongly Agree (5)"
- Retain items scoring above 3 or selected by at least one expert
- Further reduce item list by keeping only items assigned a priori by at least 60% of evaluators
Factor Analysis:
- Conduct exploratory factor analysis to identify underlying factor structure
- Determine number of factors based on eigenvalues > 1 and scree plot examination
- Interpret factors based on items with high loadings (> 0.4)
Reliability Assessment:
- Calculate internal consistency using Cronbach's alpha for the entire scale and for each identified factor
- Establish test-retest reliability through repeated administration to a subset of participants
Validity Testing:
- Assess discriminant validity by comparing scores between experimental and control groups
- Evaluate predictive validity through longitudinal follow-up of recidivism outcomes
- Examine convergent validity by correlating with established risk assessment tools
Validation Parameters and Outcomes
Table 3: Validation Parameters for Forensic Psychiatry Risk Assessment Tool [4]
| Validation Parameter | Methodology | Reported Outcomes for IPPML |
|---|---|---|
| Internal Consistency | Cronbach's alpha | α = 0.881 for entire sample; α = 0.896 for Factor 1; α = 0.628 for Factor 2 |
| Factor Structure | Exploratory factor analysis | Two factors identified: Performance and Social, explaining 45.55% of variance |
| Discriminant Validity | Comparison between experimental and control groups | Higher scores in forensic psychiatric evaluation group vs. schizophrenia-only group |
| Group Differences | Comparison of scores by gender | Higher dangerousness with forensic implications in males |
| Content Validity | Expert panel evaluation | 20 items retained from initial pool after expert review |
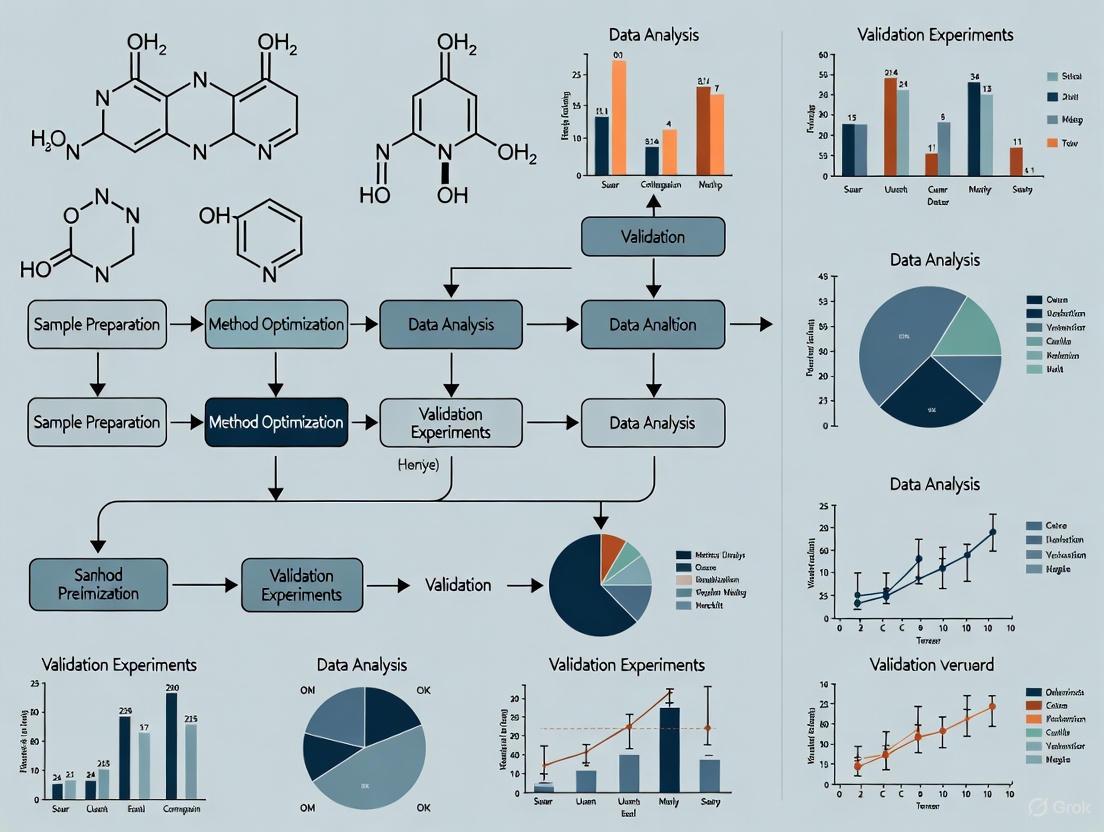
Visualization of Forensic Validation Workflows
Digital Forensic Validation Workflow
Forensic Chemistry Method Validation Workflow
Essential Research Reagent Solutions
Table 4: Essential Research Reagents and Materials for Forensic Validation Studies
| Category | Specific Items | Function in Validation | Example Applications |
|---|---|---|---|
| Reference Standards | Certified reference materials (CRMs) for drugs, explosives, toxicology | Provide known quantities for method calibration and accuracy determination | GC-MS method development for seized drugs [3] |
| Quality Control Materials | Blank matrices, spiked samples, proficiency test materials | Monitor analytical performance and detect contamination or interference | Validation of forensic toxicology methods |
| Software Tools | Volatility, Autopsy, Sleuth Kit, Wireshark, FTK Imager | Enable digital evidence acquisition, analysis, and verification | Memory forensics, disk imaging, network analysis [5] [6] |
| Instrumentation | GC-MS systems, HPLC, spectroscopic instruments, microscopy | Generate analytical data for qualitative and quantitative analysis | Drug identification, material analysis, trace evidence [3] |
| Statistical Packages | R, SPSS, Python with scikit-learn, specialized psychometric software | Perform statistical analysis of validation data and reliability assessments | Risk assessment tool validation, method comparison studies [2] [4] |
| Validation Guidelines | SWGDRUG guidelines, ISO standards, professional organization protocols | Provide standardized frameworks for validation parameters and acceptance criteria | Method validation in forensic laboratories [3] |
Forensic validation represents a multifaceted process that spans tools, methods, and analytical interpretations. Within a risk assessment framework, validation provides the evidentiary foundation that supports reliable and defensible forensic conclusions across diverse domains from digital forensics to forensic chemistry and psychiatry. The protocols and workflows presented in this document offer practical approaches for implementing comprehensive validation procedures that meet both scientific and legal standards.
As forensic science continues to advance with new technologies and methodologies, the principles of validation remain constant: systematic testing, empirical verification, and critical assessment of limitations. By adhering to rigorous validation practices, forensic researchers and practitioners can enhance the reliability of their findings, support the administration of justice, and contribute to the ongoing development of forensic science as a rigorous scientific discipline.
Forensic validation is a fundamental practice that ensures the tools and methods used to analyze evidence are accurate, reliable, and legally admissible [7]. Within a risk assessment framework for forensic research, validation functions as a critical safeguard against error, bias, and misinterpretation [7]. The core principles of Reproducibility, Transparency, and Error Rate Awareness form the foundational pillars of this process. These principles are essential for establishing scientific credibility and gaining legal acceptance under standards such as the Daubert Standard, which requires that scientific methods be demonstrably reliable [7]. This document outlines detailed application notes and experimental protocols to implement these principles effectively in forensic method validation research.
Core Principles and Application Notes
Principle 1: Reproducibility
Reproducibility ensures that results can be consistently repeated by different qualified professionals using the same method and data [7]. In practice, this means that any forensic method must produce equivalent outcomes when applied to the same evidence sample across different laboratories, instruments, and analysts.
Application Notes:
- Definition: Reproducibility is achieved when an independent party can follow the documented protocol and obtain results that fall within an acceptable margin of error of the original findings [7].
- Risk of Non-Compliance: Lack of reproducibility severely undermines the credibility of forensic findings and can lead to the exclusion of evidence in legal proceedings [7]. It introduces uncertainty and potential for miscarriages of justice.
- Implementation Strategy: Utilize controlled reference materials and standardized testing environments to establish a baseline for repeatable outcomes. Key practices include using hash values to confirm data integrity and comparing tool outputs against known datasets [7].
Principle 2: Transparency
Transparency requires that all procedures, software versions, logs, assumptions, and chain-of-custody records are thoroughly and clearly documented [7] [8]. A transparent methodology allows for the critical evaluation of the process and conclusions by the broader scientific and legal communities.
Application Notes:
- Definition: Full transparency involves disclosing all matters of scientific relevance, including fundamental principles, methodology, validity and error, assumptions and limitations, and areas of scientific controversy [8].
- Risk of Non-Compliance: Opaque methods create doubt regarding the reliability and impartiality of the analysis. This can lead to legal challenges, loss of credibility for the expert or laboratory, and increased questioning in court [7] [8].
- Implementation Strategy: Adopt a comprehensive reporting framework that documents every stage of the forensic process. As demonstrated by one multi-disciplinary laboratory, this includes information on competency testing, quality assurance, and cognitive factors, which ultimately improves the use of scientific evidence in courts [8].
Principle 3: Error Rate Awareness
Error Rate Awareness involves understanding, quantifying, and disclosing the known or potential error rates associated with a forensic method [7]. This principle is a key factor for courts in assessing the reliability of scientific evidence.
Application Notes:
- Definition: The error rate refers to the frequency with which a method produces false positives, false negatives, or other erroneous results under specified conditions. This must be established through rigorous empirical testing [7].
- Risk of Non-Compliance: Operating with an unknown or high error rate risks basing decisions on flawed evidence, potentially leading to wrongful convictions, acquittals of the guilty, and civil liability [7].
- Implementation Strategy: Conduct repeated testing (e.g., in triplicate) using control samples to calculate quantitative error rates [9]. Cross-validate results using multiple tools or methods to identify and account for inconsistencies [7].
Experimental Protocols for Validation
The following protocols provide a template for designing validation studies that adhere to the core principles.
Protocol: Tool Performance and Reproducibility Assessment
This protocol is designed to test the reliability and repeatability of a specific forensic tool or software.
1. Objective: To determine the reproducibility and error rate of [Tool Name] in performing [Specific Function, e.g., deleted file recovery]. 2. Materials: - See "Research Reagent Solutions" table for standard tools and reference materials. 3. Methodology: - Sample Preparation: Create a controlled testing environment with a standardized digital evidence sample (e.g., a forensic disk image) containing a known set of artifacts [9]. - Experimental Replication: Execute the core function (e.g., data carving) in triplicate to establish repeatability metrics [9]. - Data Integrity Checks: Use cryptographic hash values (e.g., SHA-256) to confirm the evidence integrity before and after analysis [7]. - Data Analysis: Calculate the tool's error rate by comparing the acquired artifacts against the known control reference. Metrics should include true positives, false positives, and false negatives [9]. 4. Documentation: Record all parameters, tool version, operating environment, and raw results. Any deviation from the protocol must be documented.
Protocol: Method Transparency and Cross-Validation
This protocol assesses the consistency of a forensic method across different tools or analysts.
1. Objective: To validate the transparency and robustness of the [Method Name] for [Analysis Type] by cross-validating results. 2. Materials: - See "Research Reagent Solutions" table. 3. Methodology: - Independent Analysis: Have multiple trained analysts or different software tools (e.g., commercial and open-source) analyze the same standardized evidence sample [7] [9]. - Result Comparison: Systematically compare the outputs from all sources to identify any inconsistencies in recovered data or interpreted results [7]. - Blind Testing: Where possible, incorporate blind testing to minimize cognitive bias. 4. Documentation: Maintain detailed logs from all tools and analysts. The final report must clearly present all findings, highlight any discrepancies, and discuss their potential impact on the conclusions.
Workflow and Signaling Pathways
The following diagram illustrates the logical workflow for integrating the core principles into a forensic method validation study, from planning through to court admission.
Forensic Validation Workflow
Research Reagent Solutions
The table below catalogues essential tools and materials for conducting rigorous forensic validation experiments, drawing on examples from digital forensics.
| Item Name | Type/Category | Function in Validation | Example Products/Tools |
|---|---|---|---|
| Commercial Forensic Suite | Software | Provides a benchmark for comparison; often court-accepted and commercially validated [9]. | FTK, EnCase, Forensic MagiCube [9] |
| Open-Source Forensic Tool | Software | A cost-effective alternative for cross-validation; allows peer review of methodologies [9]. | Autopsy, Sleuth Kit, ProDiscover Basic [9] |
| Standardized Reference Material | Data Set | A controlled evidence sample (disk image) with known content for testing tool accuracy and calculating error rates [7] [9]. | Custom-made disk images, NIST test datasets |
| Hash Algorithm Tool | Software/Utility | Generates cryptographic hashes (e.g., SHA-256) to verify data integrity and ensure evidence is unaltered during analysis [7]. | Built-in OS tools, forensic software modules |
| Validation Framework | Protocol | A structured methodology outlining steps for testing and confirming the reliability of tools and methods [9]. | Enhanced framework per Ismail et al., NIST Computer Forensics Tool Testing standards [9] |
Data Presentation and Analysis
Quantitative Metrics from Tool Validation Studies
The following table summarizes example outcomes from a comparative tool validation study, illustrating how key metrics like error rates are quantified.
| Tool Name | Tool Type | Test Scenario | Success Rate (%) | False Positive Rate (%) | False Negative Rate (%) |
|---|---|---|---|---|---|
| Tool A | Commercial | Data Carving | 99.5 | 0.5 | 0.1 |
| Tool B | Open-Source | Data Carving | 98.7 | 1.2 | 0.2 |
| Tool A | Commercial | Artifact Search | 98.9 | 0.8 | 0.4 |
| Tool B | Open-Source | Artifact Search | 97.5 | 2.1 | 0.5 |
| Tool C | Commercial | File Recovery | 99.8 | 0.1 | 0.1 |
Note: Data is illustrative, based on experimental methodologies described in the literature [9]. Success Rate is defined as the percentage of known artifacts correctly identified and recovered. Rates should be established through repeated testing in triplicate [9].
The ISO 21043 Forensic sciences standard series represents a comprehensive, internationally recognized framework designed to unify and advance forensic science as a discipline. Developed by ISO Technical Committee (TC) 272, this series provides a well-structured framework that addresses the entire forensic process, from crime scene to courtroom [10]. The standard aims to enhance the reliability of expert opinions and ultimately improve trust in the justice system by establishing common requirements, recommendations, and terminology across forensic practices [10].
The development of ISO 21043 was a worldwide effort, bringing together experts in forensic science, law, law enforcement, and quality management from 27 participating and 21 observing national standards organizations [10]. The complete publication of Parts 3, 4, and 5 in 2025 marks a significant milestone in establishing a unified approach to forensic science practice internationally [10].
Structural Framework of ISO 21043
The ISO 21043 standard is organized into five distinct parts, each addressing specific stages of the forensic process while working in tandem with established standards like ISO/IEC 17025 for testing and calibration laboratories [10].
Table 1: Components of the ISO 21043 Series
| Part Number | Title | Scope and Focus | Publication Status |
|---|---|---|---|
| ISO 21043-1 | Vocabulary [10] | Defines terminology and provides a common language for discussing forensic science [10] | Published [10] |
| ISO 21043-2 | Recognition, recording, collecting, transport and storage of items [11] | Addresses forensic science at the scene; early stages that can impact all subsequent processes [10] | Published 2018 [11] |
| ISO 21043-3 | Analysis [12] | Applies to all forensic analysis, emphasizing issues specific to forensic science [10] | Published 2025 [12] |
| ISO 21043-4 | Interpretation [10] | Centers on case questions and answers provided as opinions; links observations to case questions [10] | Published 2025 [10] |
| ISO 21043-5 | Reporting [10] | Addresses communication of forensic process outcomes, including reports and testimony [10] | Published 2025 [10] |
The relationship between these components follows the logical progression of the forensic process, with outputs from one stage serving as inputs for the next. This creates a seamless framework that maintains integrity and continuity throughout the entire forensic workflow [10].
Core Principles and Requirements for Forensic Analysis
Foundational Principles of ISO 21043-3
ISO 21043-3: Analysis establishes critical requirements to safeguard the process for analyzing items of potential forensic value. The standard is designed to ensure the use of suitable methods, proper controls, qualified personnel, and appropriate analytical strategies throughout the forensic analysis of items [12]. It applies to activities conducted by forensic service providers at the scene and within a facility, covering all disciplines of forensic science with the exception of digital data recovery, which falls under ISO/IEC 27037 [12].
The requirements and recommendations in ISO 21043-3 are designed to facilitate comprehensive, accurate, and reliable analysis of items through standardized approaches [12]. The standard works in conjunction with ISO 17025, referencing it where issues are not specific to forensic science while emphasizing aspects particularly relevant to forensic analysis [10].
Method Validation Framework
A cornerstone of reliable forensic science is the demonstration that analytical methods are fit for purpose. Validation involves providing objective evidence that a method, process, or device is suitable for its specific intended purpose [13]. This process is critical for meeting accreditation requirements under ISO 17025 and ensuring that results presented in legal contexts can be relied upon [13].
The validation framework outlined in forensic guidance documents follows a structured process:
End-User Requirements Specification
A critical component of method validation involves determining end-user requirements. This process captures what different users of the method output require and focuses particularly on aspects that experts will rely on for their critical findings [13]. The end-user requirement directly influences the dataset needed to adequately assess the efficiency, effectiveness, and competence to perform the activity [13].
For novel methods developed in-house, user requirements may originate from method development documentation, while adopted or adapted methods require creating these requirements from scratch with focus on features affecting reliable results [13]. Defining these requirements specifically helps ensure that validation testing uses representative data that reflects real-life applications without being unnecessarily complex [13].
Experimental Protocols for Method Validation
Protocol for Developmental Validation of Novel Methods
Purpose: To establish objective evidence that a novel forensic method is fit for purpose when no prior validation data exists [13].
Scope: Applicable to newly developed analytical techniques, instruments, or methodologies with limited or no existing validation history.
Procedure:
Define Requirements Specification
- Document functional and non-functional requirements
- Identify critical findings the method must support
- Establish minimum performance thresholds
- Define operational constraints and limitations
Conduct Risk Assessment
- Identify potential failure modes
- Assess impact on result reliability
- Determine control measures for identified risks
- Document risk mitigation strategies
Set Acceptance Criteria
- Establish quantitative performance metrics
- Define qualitative assessment parameters
- Determine statistical confidence levels
- Specify tolerance ranges for control measures
Develop Validation Plan
- Design experiments to challenge method capabilities
- Select test materials representing casework scenarios
- Include stress testing with extreme conditions
- Plan replication studies to assess reproducibility
Execute Validation Study
- Generate test data under controlled conditions
- Implement quality assurance checks at critical points
- Document all deviations from protocol
- Collect data for statistical analysis
Assess Acceptance Criteria Compliance
- Analyze data against predefined metrics
- Evaluate method limitations and boundaries
- Document observed error rates or uncertainties
- Verify risk control effectiveness
Compile Validation Report
- Summarize objective evidence of fitness for purpose
- Document all method limitations
- Provide statement of validation completion
- Include implementation recommendations
Quality Control: Incorporate reality checks by independent experts, instrument calibration verification, and control samples throughout validation process [13].
Protocol for Adopted Method Verification
Purpose: To demonstrate laboratory competence for methods previously validated by another organization [13].
Scope: Applicable to standardized methods or techniques with existing validation data from reputable sources.
Procedure:
Review Existing Validation Records
- Evaluate original validation study design robustness
- Assess relevance to intended application
- Verify data comprehensiveness
- Identify potential gaps for specific applications
Define Laboratory-Specific Requirements
- Adapt end-user requirements to local context
- Consider population-specific factors
- Account for equipment differences
- Address jurisdictional legal standards
Design Verification Study
- Select representative test materials
- Focus on critical method aspects
- Include known reference materials
- Plan limited challenge testing
Execute Verification Testing
- Demonstrate analyst competency
- Verify equipment performance
- Confirm result reproducibility
- Validate reporting procedures
Document Verification Evidence
- Record performance metrics achieved
- Document any limitations identified
- Provide statement of verification
- Reference original validation data
Acceptance Criteria: Performance metrics must meet or exceed those documented in original validation studies and satisfy laboratory-specific requirements [13].
Quantitative Framework for Validation Assessment
Table 2: Validation Metrics for Forensic Method Evaluation
| Validation Parameter | Assessment Methodology | Acceptance Criteria Guidelines | Data Documentation Requirements |
|---|---|---|---|
| Accuracy | Comparison with reference materials or known values [13] | Agreement within established uncertainty margins [13] | Deviation from reference values, measurement uncertainty [13] |
| Precision | Repeated analysis of homogeneous samples [13] | Coefficient of variation ≤ laboratory-defined threshold [13] | Within-run and between-run variability estimates [13] |
| Specificity | Challenge with potentially interfering substances [13] | No significant interference at relevant concentrations [13] | List of substances tested and interference levels observed [13] |
| Robustness | Deliberate variation of operational parameters [13] | Method performance maintained within acceptable limits [13] | Parameter variations tested and their impact on results [13] |
| Sensitivity | Analysis of samples with decreasing analyte levels [13] | Reliable detection at or below relevant decision point [13] | Limit of detection, limit of quantification values [13] |
| Reproducibility | Inter-laboratory comparison or different analysts [13] | Consistent results across different implementations [13] | Between-operator, between-instrument, between-day variation [13] |
| Reliability | Extended analysis under routine conditions [13] | Consistent performance throughout method application [13] | Summary of performance over time and maintenance cycles [13] |
Table 3: Risk Assessment Matrix for Method Validation
| Risk Category | Potential Impact | Control Measures | Validation Approach |
|---|---|---|---|
| False Positive Results | Wrongful associations; miscarriage of justice [14] | Confirmatory techniques; independent verification [13] | Challenge with known exclusion samples; specificity testing [13] |
| False Negative Results | Missed associations; failure to solve crimes [14] | Sensitivity controls; minimum detection levels [13] | Analysis of low-level samples; dilution studies [13] |
| Contextual Bias | Influenced interpretation; skewed results [14] | Sequential unmasking; linear examination [13] | Blind testing; variation of irrelevant contextual information [13] |
| Method Limitations | Inappropriate application; overstatement of conclusions [13] | Clear documentation; staff training [13] | Boundary testing; application outside intended scope [13] |
| Data Integrity | Compromised results; challenged admissibility [13] | Audit trails; access controls; version management [13] | System security testing; audit trail verification [13] |
The Scientist's Toolkit: Essential Materials for Validation Research
Table 4: Research Reagent Solutions for Forensic Method Validation
| Reagent/Category | Function in Validation Studies | Application Examples | Quality Control Requirements |
|---|---|---|---|
| Reference Standards | Establish accuracy and calibration curves [13] | Quantification of analytes; method calibration [13] | Certified purity; documentation of traceability [13] |
| Control Materials | Monitor method performance and stability [13] | Positive and negative controls; process verification [13] | Documented stability; appropriate storage conditions [13] |
| Matrix Samples | Assess specificity and potential interferences [13] | Testing with different sample types; interference studies [13] | Representative of casework samples; documented composition [13] |
| Challenge Samples | Evaluate method limitations and robustness [13] | Stress testing; boundary condition assessment [13] | Known characteristics; appropriate heterogeneity [13] |
| Calibration Verification | Confirm instrument performance and response [13] | Regular performance checks; instrument qualification [13] | Traceable reference values; defined acceptance ranges [13] |
Integration with Risk Assessment Framework
The ISO 21043 standards provide an essential foundation for implementing a comprehensive risk assessment framework for forensic method validation research. By establishing standardized requirements across the entire forensic process, these standards enable systematic identification, evaluation, and mitigation of risks associated with forensic analysis [10].
The framework incorporates four key guidelines for evaluating forensic feature-comparison methods: plausibility, soundness of research design and methods, intersubjective testability, and availability of valid methodology to reason from group data to statements about individual cases [14]. These guidelines help bridge the gap between general scientific principles and the specific requirements of forensic applications, supporting the development of validated methods that meet both scientific and legal standards [14].
Implementation of ISO 21043 within a risk assessment framework emphasizes the importance of error rate quantification, method limitation documentation, and clear communication of uncertainties in forensic conclusions [14]. This approach aligns with legal admissibility standards such as Daubert, which require demonstration of methodological reliability and known error rates for scientific evidence presented in court proceedings [14] [15].
For researchers and scientists developing forensic methods, understanding the legal admissibility of expert testimony is crucial for ensuring that analytical techniques withstand judicial scrutiny. In the United States, admissibility is governed primarily by two competing standards: the Frye standard and the Daubert standard [16] [17]. The appropriate standard depends on the jurisdiction in which testimony is offered, with federal courts and a majority of states following Daubert, while a minority of states continue to adhere to Frye [16] [17].
This article provides application notes and experimental protocols to help forensic researchers design validation studies that satisfy these legal thresholds. A robust validation framework not only enhances scientific integrity but also ensures that expert testimony based on research findings will be admitted in legal proceedings.
Core Legal Standards: Comparative Analysis
The Frye Standard: General Acceptance
The Frye standard originates from the 1923 case Frye v. United States [16] [17]. This standard employs a "general acceptance" test, requiring that the scientific methodology underlying an expert's opinion be generally accepted as reliable within the relevant scientific community [16] [17].
Key Frye Characteristics:
- Primary Question: Has the methodology gained general acceptance in the relevant scientific field? [16] [17]
- Judicial Role: Courts evaluate whether the principle from which the deduction is made is sufficiently established in its field [16].
- Application Scope: Primarily applied to novel scientific techniques rather than all expert testimony [16].
- Hearing Focus: Frye hearings are narrow, addressing only general acceptance of the methodology, not the reliability or relevance of the conclusions [16].
The Daubert Standard: Relevance and Reliability
The Daubert standard emerged from the 1993 Supreme Court case Daubert v. Merrell Dow Pharmaceuticals, Inc., which held that the Federal Rules of Evidence superseded the Frye standard [17] [18]. Daubert assigns trial judges a "gatekeeping" role to ensure expert testimony rests on a reliable foundation and is relevant to the case [17] [18].
Daubert's five-factor test provides a framework for evaluating methodology reliability [18]:
- Testability: Whether the expert's technique or theory can be or has been tested
- Peer Review: Whether the technique or theory has been subjected to peer review and publication
- Error Rate: The known or potential rate of error of the technique
- Standards: The existence and maintenance of standards controlling the technique's operation
- General Acceptance: Whether the technique or theory has attained general acceptance in the relevant scientific community
The Daubert trilogy of cases further refined this standard:
- Daubert (1993): Established the factors and overruled Frye in federal courts [18]
- General Electric Co. v. Joiner (1997): Clarified that conclusions and methodology are not entirely distinct and established abuse of discretion as the standard for appellate review [18]
- Kumho Tire Co. v. Carmichael (1999): Extended Daubert to all expert testimony, not just scientific testimony [18]
Table 1: Comparison of Frye and Daubert Standards
| Feature | Frye Standard | Daubert Standard |
|---|---|---|
| Originating Case | Frye v. United States (1923) [16] [17] | Daubert v. Merrell Dow Pharmaceuticals (1993) [17] [18] |
| Primary Test | "General Acceptance" in the relevant scientific community [16] [17] | Relevance and Reliability, with a five-factor analysis [17] [18] |
| Judicial Role | Determines acceptance within scientific community [16] | "Gatekeeper" ensuring reliable foundation and relevance [17] [18] |
| Scope | Primarily novel scientific techniques [16] | All expert testimony (scientific, technical, specialized knowledge) [18] |
| Burden of Proof | Proponent must demonstrate general acceptance [16] | Proponent must demonstrate admissibility by preponderance of evidence [19] [18] |
| Key Considerations | - Widespread acceptance in field- Scientific publications- Judicial decisions [16] | - Testability- Peer review- Error rate- Standards & controls- General acceptance [18] |
Recent Legal Developments
Recent amendments to Federal Rule of Evidence 702 (effective December 2023) emphasize that the proponent of expert testimony must demonstrate by a preponderance of the evidence that the testimony meets all admissibility requirements [19]. The rule now explicitly states that the expert's opinion must "reflect[] a reliable application of the principles and methods to the facts of the case" [19]. This amendment clarifies that courts must perform their gatekeeping role with diligence, ensuring that expert testimony stays within the bounds of what can be concluded from a reliable application of the expert's basis and methodology [19].
Quantitative Data in Risk Assessment Validation
Forensic risk assessment tools require rigorous quantitative validation to meet legal admissibility standards. The following data points are critical for demonstrating reliability and accuracy under both Frye and Daubert.
Table 2: Key Quantitative Metrics for Risk Assessment Tool Validation
| Metric Category | Specific Measures | Daubert Consideration | Data Presentation Requirements |
|---|---|---|---|
| Predictive Accuracy | - Sensitivity & Specificity- Area Under Curve (AUC)- Positive/Negative Predictive Values [20] | Known or potential rate of error [18] | Report rates for relevant subpopulations; avoid highly selected samples [20] |
| Population Norms | - True/False Positive Rates- True/False Negative Rates [20] | General acceptance in relevant community [18] | Present raw numbers and percentages; disclose conflicts of interest [20] |
| Reliability | - Inter-rater Reliability- Test-retest Reliability- Internal Consistency | Maintenance of standards and controls [18] | Report statistical coefficients and confidence intervals |
| Validation Evidence | - Cross-validation Results- External Validation Findings [20] | Whether theory has been tested [18] | Specify validation sample characteristics and generalizability [20] |
Experimental Protocols for Method Validation
Protocol 1: Establishing Predictive Accuracy
Objective: To determine the predictive accuracy of a risk assessment tool for violent behavior using quantitative measures.
Materials:
- Validated risk assessment tool (e.g., HCR-20, VRAG, LS/CMI)
- Representative sample population (ensure inclusion of relevant subpopulations)
- Data collection instruments (standardized protocols)
- Statistical analysis software (R, SPSS, or SAS)
Procedure:
- Sample Recruitment: Recruit a prospective cohort of participants (N ≥ 300 recommended) from the target population. Document inclusion/exclusion criteria.
- Baseline Assessment: Administer the risk assessment tool to all participants at baseline. Record individual item scores and total scores.
- Rater Training: Train all assessors to established competency standards. Calculate inter-rater reliability coefficients (kappa ≥ 0.70 acceptable).
- Follow-up Period: Track participants for a predetermined follow-up period (typically 1-5 years for violence risk). Document all violent incidents using standardized definitions.
- Data Analysis:
- Calculate sensitivity, specificity, positive predictive value, and negative predictive value
- Generate receiver operating characteristic (ROC) curves and calculate area under the curve (AUC)
- Report true positive, false positive, true negative, and false negative rates
- Subgroup Analysis: Conduct stratified analyses for relevant demographic subgroups (e.g., by gender, ethnicity, age) to evaluate predictive fairness.
Validation Criteria: The tool demonstrates at least moderate predictive accuracy (AUC ≥ 0.70) with comparable performance across relevant demographic subgroups.
Protocol 2: Error Rate Determination
Objective: To establish the known error rate of a forensic methodology as required under Daubert.
Materials:
- Standardized protocol for the methodology
- Reference standards or ground truth data
- Blinded examiners with appropriate expertise
- Statistical analysis package
Procedure:
- Test Design: Create a set of test cases with known ground truth (e.g., known positive and negative samples). Ensure case complexity reflects real-world applications.
- Examiner Blinding: Assign examiners to analyze test cases under blinded conditions to prevent confirmation bias.
- Data Collection: Have each examiner analyze all test cases using the standardized methodology. Record all observations, interpretations, and conclusions.
- Error Calculation:
- Compare examiner results to ground truth
- Calculate false positive and false negative rates
- Determine overall accuracy rate
- Compute confidence intervals for error rates
- Sources of Error: Document and categorize sources of error (e.g., measurement error, interpretation error, contamination).
- Replication: Conduct multiple rounds of testing to establish stable error rate estimates.
Validation Criteria: The methodology demonstrates a known and acceptable error rate with confidence intervals that support reliability for forensic application.
Daubert Admissibility Assessment Workflow
The following diagram illustrates the logical relationship between research validation activities and judicial admissibility determinations under Daubert:
The Scientist's Toolkit: Research Reagent Solutions
Forensic validation research requires specific methodological "reagents" - standardized components that ensure reproducibility and reliability.
Table 3: Essential Research Reagents for Forensic Method Validation
| Research Reagent | Function | Application in Legal Standards |
|---|---|---|
| Standardized Protocols | Detailed, step-by-step procedures for method application | Ensures consistent application and maintenance of standards (Daubert factor) [18] |
| Reference Materials | Certified controls and standards with known properties | Provides basis for method calibration and accuracy determination |
| Validation Datasets | Curated collections of data with known ground truth | Enables empirical testing and error rate determination (Daubert factor) [18] |
| Statistical Analysis Plans | Pre-specified protocols for data analysis | Demonstrates methodological rigor and minimizes analytical flexibility |
| Blinded Assessment Tools | Instruments for unbiased evaluation of outcomes | Reduces bias in validation studies and error rate determination |
| Peer-Reviewed Publications | Scholarly articles vetted by experts in the field | Provides evidence of peer review and general acceptance (Daubert factors) [18] |
Navigating the Daubert and Frye standards requires forensic researchers to implement robust validation frameworks that address specific legal criteria. By employing the protocols, metrics, and reagents outlined in this article, researchers can generate evidence that demonstrates the reliability, validity, and general acceptance of their methodologies. This scientific rigor not only advances forensic science but also ensures that expert testimony based on research findings meets the evolving standards for legal admissibility.
The Critical Role of Risk Assessment in Proactive Method Development
The integrity of forensic and pharmaceutical data rests upon the reliability of analytical methods. A proactive, risk-based framework for method development, aligned with the forensic-data-science paradigm, ensures that methods are transparent, reproducible, and intrinsically resistant to cognitive bias [21]. This approach shifts the paradigm from a reactive "quality by testing" (QbT) model to a systematic Analytical Quality by Design (AQbD) framework, where quality and robustness are built into the method from its inception [22].
International guidelines, such as ICH Q9 on Quality Risk Management, define risk as the combination of the probability of occurrence of harm and the severity of that harm [22]. In the context of method development, this translates to a systematic process of identifying potential variables that may impact method performance and employing structured experiments to understand and control them. This is particularly critical in forensic science, where the method's output must withstand rigorous legal scrutiny. The adoption of a lifecycle management model, as reinforced by the modernized ICH Q2(R2) and ICH Q14 guidelines, moves validation from a one-time event to a continuous process that begins with predefined objectives [23].
The Analytical Method Lifecycle and Risk Management
The analytical method lifecycle encompasses all stages from initial conception through routine use and eventual retirement. A holistic risk management strategy must cover the entire lifecycle to guarantee the method remains fit-for-purpose [22].
The following diagram illustrates the continuous, risk-informed stages of the analytical method lifecycle:
Figure 1: The Analytical Method Lifecycle. This continuous process begins with method design and development (yellow), transitions to formal validation and operational control (green), and includes ongoing monitoring and improvement (red). Knowledge gained in later stages feeds back to inform future development cycles [22].
The initial Design and Development phase is where risk assessment plays its most crucial role. Here, the Analytical Target Profile (ATP) is defined, and risks to achieving its performance criteria are identified. The subsequent Validation phase confirms that the method meets the ATP. The Control Strategy and Continual Improvement phases rely on ongoing risk monitoring to manage post-approval changes and performance trends, ensuring the method's long-term robustness [22]. This lifecycle approach, supported by tools like the ATP, provides a structured framework that is consistent with the principles of ISO 21043 for forensic sciences, which emphasizes vocabulary, interpretation, and reporting [21].
Core Principles and Regulatory Framework
The transition from a unstructured approach to a systematic framework is guided by key principles and regulatory guidelines.
From Quality by Testing (QbT) to Analytical Quality by Design (AQbD)
The traditional Quality by Testing (QbT) approach involves varying one factor at a time (OFAT) and often leads to a "false optimum" with limited understanding of variable interactions, making the method fragile and difficult to modify [22]. In contrast, Analytical Quality by Design (AQbD) is a systematic, risk-based approach that begins with predefined objectives. It incorporates prior knowledge, risk assessment, and multivariate experiments via Design of Experiments (DoE) to build a deep understanding of the method [22]. The outcome is a well-understood Method Operability Design Region (MODR) where method performance is guaranteed with a defined probability.
Key Regulatory Guidelines: ICH Q2(R2), Q14, and Q9
Modern regulatory guidance firmly supports this proactive, scientific approach:
- ICH Q2(R2): Validation of Analytical Procedures: This revised guideline is the global standard for validation. It expands its scope to include modern technologies and formalizes a science- and risk-based approach, emphasizing that validation is part of a broader lifecycle [23].
- ICH Q14: Analytical Procedure Development: This new guideline complements Q2(R2) by providing a structured framework for development. It introduces the Analytical Target Profile (ATP) as a foundational element and differentiates between traditional and enhanced, more flexible development approaches [23] [24].
- ICH Q9: Quality Risk Management: This guideline provides the overarching principles for risk management, defining risk and outlining systematic processes for risk assessment, control, communication, and review [22].
The following table summarizes the core validation parameters as outlined in ICH Q2(R2), which form the basis of the ATP and method performance criteria [23].
Table 1: Core Analytical Method Validation Parameters as per ICH Q2(R2)
| Parameter | Definition | Typical Acceptance Criteria |
|---|---|---|
| Accuracy | The closeness of test results to the true value. | Measured by recovery of a known amount; typically ±10-15% of the theoretical value for assay. |
| Precision | The degree of agreement among individual test results. Includes repeatability, intermediate precision, and reproducibility. | Relative Standard Deviation (RSD) < 2% for assay, < 5-10% for impurities. |
| Specificity | The ability to assess the analyte unequivocally in the presence of other components. | No interference from blank, placebo, or known impurities. |
| Linearity | The ability to obtain test results proportional to the analyte concentration. | Correlation coefficient (r) > 0.998. |
| Range | The interval between upper and lower analyte concentrations for which linearity, accuracy, and precision are demonstrated. | Defined by the intended use of the method (e.g., 50-150% of test concentration). |
| LOD / LOQ | The Lowest Amount that can be Detected (LOD) or Quantitated (LOQ). | Signal-to-noise ratio of 3:1 for LOD, 10:1 for LOQ. |
| Robustness | A measure of the method's capacity to remain unaffected by small, deliberate variations in method parameters. | Method meets all validation criteria when parameters are deliberately altered. |
Practical Application: A Risk Assessment Workflow
Implementing a risk-based program requires a practical and standardized workflow. The following protocol and diagram outline a robust process for conducting an analytical risk assessment.
Experimental Protocol: Conducting an Analytical Risk Assessment (RA)
Objective: To systematically evaluate a developed analytical method to identify and mitigate risks, ensuring it is fit-for-purpose and ready for formal validation and technical transfer to a quality control (QC) environment [24].
Materials and Reagents:
- Method Documentation: Complete method development history, including the defined Analytical Target Profile (ATP) and proposed standard operating procedure (SOP).
- Risk Assessment Tool: A predefined spreadsheet template with lists of potential method concerns for the specific technique (e.g., LC, GC, LC/MS) [24].
- Data: All robustness study data and any method performance data from the development phase.
Procedure:
- Preparation: The method developer collates all method information, including the ATP, validation requirements, and robustness study data. The method risk assessment spreadsheet template is pre-populated with known parameters and potential concerns [24].
- Team Assembly: Convene a meeting with key stakeholders, including the method developer, analytical project lead, subject matter experts (SMEs), and quality and commercial analytical representatives [24].
- Risk Assessment Meeting (Round 1): a. Present the method development history, challenges, and data to "set the scene." b. Using the pre-populated spreadsheet tool, review the method line-by-line. The tool should assess variables related to sample preparation and sample analysis, organized by categories such as the "6 Ms" (Machine, Method, Material, humanpower, Measurement, Mother Nature) [24]. c. For each variable, the team discusses and agrees on one of three outcomes: the variable meets the ATP, it is a risk (graded as medium/yellow or high/red), or there is a knowledge gap. d. All identified risks and gaps are transcribed to a "Risk Heat Map" along with a proposed mitigation plan (e.g., perform further DoE, implement a control) [24].
- Mitigation Actions: Execute the experimental plan defined in the mitigation strategy (e.g., additional robustness testing or knowledge-gathering experiments).
- Re-assessment (Round 2): Re-convene the team to review the new data. The "Risk Heat Map" is updated to reflect the revised risk level (e.g., green after successful mitigation). The outcome is a formal confirmation of the method's readiness for validation or a directive for further work [24].
The Risk Assessment Workflow
The following diagram visualizes the iterative workflow of the risk assessment process:
Figure 2: The Iterative Risk Assessment Workflow. The process begins with a proposed method and its data. A formal risk assessment evaluates it against the ATP, leading to a decision point. Unacceptable risks trigger additional experiments, creating an iterative cycle until the method is deemed ready for validation [24].
The Scientist's Toolkit: Essential Research Reagent Solutions
A robust risk assessment program is supported by both conceptual tools and practical materials. The following table details key reagents and materials critical for developing and validating analytical methods, particularly in a pharmaceutical QC or forensic context.
Table 2: Essential Research Reagent Solutions for Analytical Method Development
| Item | Function & Importance in Risk Mitigation |
|---|---|
| Certified Reference Standards | High-purity materials with certified identity and purity. Essential for accurately determining method Accuracy, Specificity, and for calibrating instruments. Using sub-standard materials is a major risk to data integrity. |
| System Suitability Test (SST) Mixtures | A prepared mixture of analytes and key impurities designed to verify that the chromatographic system (or other instrument) is operating correctly before analysis. A critical control to mitigate risks related to instrument performance [24]. |
| Stable Isotope-Labeled Internal Standards | Used in mass spectrometric methods (e.g., for mutagenic impurities). They correct for matrix effects and variability in sample preparation and ionization, directly improving Accuracy and Precision, thereby mitigating a key risk in quantitative bioanalysis [24]. |
| Forced Degradation Samples | Samples of the drug substance or product that have been intentionally stressed (e.g., with heat, light, acid, base, oxidant). Used to validate the Specificity of stability-indicating methods and demonstrate that the method can accurately measure the analyte in the presence of its degradation products. |
| Placebo/Blank Matrix | The formulation base without the active ingredient (for drugs) or a representative biological fluid/sample without the analyte (for forensics). Critical for assessing Specificity by confirming the absence of interfering signals from the sample matrix itself. |
The integration of a proactive risk assessment framework into analytical method development is no longer a best practice but a scientific and regulatory imperative. By adopting the principles of AQbD and leveraging tools like the ATP and structured risk assessments, researchers can build quality and robustness directly into their methods. This systematic approach yields methods that are not only compliant with global standards like ICH Q2(R2) and ISO 21043 but are also more resilient, understandable, and adaptable throughout their entire lifecycle. This ultimately ensures the generation of reliable, defensible data that is crucial for both patient safety and the integrity of the forensic justice system.
A Step-by-Step Framework: Implementing Risk Assessment in Validation Protocols
Within a comprehensive risk assessment framework for forensic method validation, the initial and most critical step is the systematic identification of risks. This process involves cataloging potential vulnerabilities inherent in analytical procedures before they can compromise data integrity, result reliability, or regulatory compliance. In forensic science, where findings must withstand legal scrutiny, and in drug development, where they impact patient safety, a structured approach to risk identification is an ethical and professional imperative [7]. This document provides detailed application notes and protocols for researchers and scientists to execute this foundational step effectively.
Methodology for Risk Identification
A multi-faceted approach ensures a holistic cataloging of vulnerabilities. The following methodologies should be employed concurrently.
Process Deconstruction and Mapping
The analytical procedure must be deconstructed into its discrete, sequential steps—from sample receipt and preparation to data analysis and reporting. Each step is then examined for potential failure modes. This mapping creates a logical workflow that is essential for visualizing and analyzing the entire process.
Expert-Led Brainstorming Sessions
Leverage the collective expertise of cross-functional teams, including analytical scientists, quality assurance personnel, and regulatory affairs specialists. Sessions should be structured using prompts derived from key validation parameters, such as "How could this method fail to be specific for the target analyte?" or "What conditions could affect the accuracy of this result?" [25].
Review of Historical Data and Deviations
Analyze data from past method validations, transfers, and routine use. Previous deviations, out-of-specification (OOS) results, and audit findings are invaluable resources for identifying recurrent or latent vulnerabilities.
Quantitative Risk Assessment Framework
Once potential vulnerabilities are identified, they must be assessed and prioritized based on their Likelihood (probability of occurrence) and Impact (severity of consequence). A risk matrix is the standard tool for this prioritization [26] [27].
Likelihood (Probability) Rating Scale
The following 5-point scale defines the probability of a risk event occurring. Definitions should be customized for the specific application, whether for a design flaw (DFMEA) or an operational failure [27].
Table 1: 5-Point Likelihood Rating Scale
| Likelihood Rating | Label | Description | Quantitative Guide (Probability) |
|---|---|---|---|
| 1 | Rare | Failure is highly improbable; method is proven and highly reliable. | < 0.01% |
| 2 | Unlikely | Failure is unlikely; low risk exposure with strong controls. | 0.1% - 1% |
| 3 | Occasional | Failure may occur under specific conditions; moderate controls. | 1% - 20% |
| 4 | Likely | Failure is likely; method shows weaknesses or insufficient controls. | 20% - 95% |
| 5 | Almost Certain | Failure is expected; method is new, untested, or has inherent flaws. | > 95% |
Impact (Severity) Rating Scale
The Impact scale measures the consequence of a single occurrence of the failure. The rating should consider multiple dimensions of effect [27].
Table 2: 5-Point Impact Rating Scale
| Impact Rating | Label | Operational & Scientific Impact | Regulatory & Legal Impact |
|---|---|---|---|
| 1 | Insignificant | Negligible delay or data noise; no impact on conclusion. | No regulatory impact. |
| 2 | Minor | Minor operational delay; requires data re-processing. | Minor documentation finding. |
| 3 | Moderate | Significant project delay; unreliable data for a parameter. | Regulatory observation; requires response. |
| 4 | Major | Widespread project disruption; invalidates a critical result. | Submission rejection; compliance warning. |
| 5 | Catastrophic | Project failure; scientifically incorrect conclusion. | Legal exclusion of evidence; wrongful conviction [7]. |
Risk Scoring and Prioritization Matrix
The Risk Score is calculated by multiplying the Likelihood and Impact ratings, emphasizing high-likelihood, high-impact risks. The resulting score places the risk into a priority category, which dictates the required response [26] [27].
Table 3: Risk Prioritization Matrix (Score = Likelihood x Impact)
| Likelihood Impact | 1 (Rare) | 2 (Unlikely) | 3 (Occasional) | 4 (Likely) | 5 (Almost Certain) |
|---|---|---|---|---|---|
| 1 (Insignificant) | 1 (Low) | 2 (Low) | 3 (Low) | 4 (Low) | 5 (Medium) |
| 2 (Minor) | 2 (Low) | 4 (Low) | 6 (Medium) | 8 (High) | 10 (High) |
| 3 (Moderate) | 3 (Low) | 6 (Medium) | 9 (High) | 12 (Extreme) | 15 (Extreme) |
| 4 (Major) | 4 (Low) | 8 (High) | 12 (Extreme) | 16 (Extreme) | 20 (Extreme) |
| 5 (Catastrophic) | 5 (Medium) | 10 (High) | 15 (Extreme) | 20 (Extreme) | 25 (Extreme) |
- Extreme (Red, GU): Unacceptable. Immediate mitigation and stringent controls are required. Action must be taken before method use.
- High (Orange, ALARP/GU): Undesirable. Requires specific mitigation plans and management attention.
- Medium (Yellow, ALARP): Acceptable with review. Mitigation measures should be considered.
- Low (Green, GA): Acceptable. Managed by routine procedures.
The relationship between the risk components and the resulting mitigation strategy can be visualized as a decision pathway.
Catalog of Common Vulnerabilities and Experimental Protocols
The following table catalogs common vulnerabilities associated with key analytical method validation parameters, providing a structured starting point for risk identification. It integrates the risk scoring framework and links vulnerabilities to experimental protocols for their detection.
Table 4: Catalog of Vulnerabilities in Analytical Method Validation
| Validation Parameter | Identified Vulnerability (Failure Mode) | Potential Root Cause | Risk Score (L x I) | Experimental Detection Protocol |
|---|---|---|---|---|
| Specificity/ Selectivity | Interference from sample matrix or impurities co-eluting with the analyte. | Inadequate chromatographic separation or detection wavelength. | 4-16 (M-E) | Protocol 1: Specificity Challenge. Inject blank matrix, placebo, and standard solutions. Compare chromatograms to confirm baseline resolution of the analyte from any interfering peaks. Calculate resolution factor (Rs > 1.5). [25] |
| Accuracy & Precision | Systematic bias (inaccuracy) or high variability (imprecision) in results. | Faulty reference standard, sample preparation error, or instrumental drift. | 6-20 (M-E) | Protocol 2: Spike/Recovery & Repeatability. Prepare samples at 3 concentration levels (low, mid, high) in triplicate. Calculate accuracy as mean % recovery (e.g., 98-102%). Calculate precision as %RSD of the measurements (e.g., RSD < 2%). [25] |
| Linearity & Range | Non-linear response across the intended working range. | Saturation of detector or non-optimal sample concentration. | 3-12 (L-E) | Protocol 3: Linearity Curve. Analyze a minimum of 5 concentration levels across the specified range. Plot response vs. concentration. Determine the correlation coefficient (R² > 0.998) and residual plots. [25] |
| Robustness & Ruggedness | Method performance is highly sensitive to small, deliberate variations in parameters. | Poorly optimized method conditions (e.g., pH, temperature, mobile phase). | 4-15 (M-E) | Protocol 4: Deliberate Variation. Intentionally vary one parameter at a time (e.g., flow rate ±0.1 mL/min, temperature ±2°C). Monitor the effect on critical performance attributes (e.g., retention time, resolution). [25] |
| LOD & LOQ | Inability to detect or quantify analytes at low concentrations. | Insufficient method sensitivity or high background noise. | 2-10 (L-H) | Protocol 5: Signal-to-Noise Determination. Analyze low concentration samples and measure the signal-to-noise ratio (S/N). LOD is typically S/N ≥ 3, and LOQ is S/N ≥ 10. [25] |
The Scientist's Toolkit: Essential Research Reagents and Materials
The following table details key materials and solutions required for conducting the experiments outlined in the risk identification and validation protocols.
Table 5: Essential Research Reagent Solutions and Materials
| Item Name | Function / Rationale for Use | Example / Specification |
|---|---|---|
| Certified Reference Standard | Provides the benchmark for accurate quantification and method calibration. Ensures traceability and validity of results. | Certified purity (e.g., > 99.5%), with valid Certificate of Analysis (CoA). Stored under specified conditions. |
| Blank Matrix | Used in specificity experiments to identify and account for interfering components from the sample itself. | The actual sample material (e.g., blood, tablet excipients) without the target analyte. |
| Internal Standard | Added to samples to correct for analyte loss during sample preparation and for instrumental variability. | A stable, non-interfering compound with similar chemical properties to the analyte, but distinguishable analytically. |
| Chromatographic Mobile Phase | The solvent system that carries the sample through the HPLC/UPLC column. Its composition is critical for retention and separation. | High-purity solvents (HPLC-grade) and buffers, prepared with precise pH and composition. Filtered and degassed. |
| System Suitability Test (SST) Solutions | A standardized solution used to verify that the total analytical system is performing adequately before and during sample analysis. | A mixture containing the analyte and any critical partners at a known concentration to test parameters like retention, resolution, and peak shape. |
Risk analysis is a fundamental step in establishing a robust risk assessment framework for forensic method validation research. It involves the systematic process of evaluating identified risks to determine their potential impact on the validation outcomes and the likelihood of their occurrence. In forensic science, where results carry significant weight in the criminal justice system, demonstrating that analytical methods are fit for purpose and produce reliable results is paramount [28]. This analysis occurs after risk identification and provides the critical data needed to prioritize risks and allocate resources effectively for risk treatment. The process enables researchers and scientists to make informed decisions about which risks require immediate mitigation and which can be accepted or monitored, ensuring that validation studies meet the rigorous standards expected by courts and regulatory bodies [28].
The Forensic Science Regulator's guidance emphasizes that validation involves "providing objective evidence that a method, process or device is fit for the specific purpose intended" [28]. Within the criminal justice system, there is a very reasonable expectation that forensic science results can be shown to be reliable. The risk assessment element helps ensure that "the validation study is scaled appropriately to the needs of the end-user," which for forensic science is primarily the criminal justice system rather than any particular analyst or laboratory [28]. This document provides detailed application notes and protocols for conducting both qualitative and quantitative risk assessments specifically within the context of forensic method validation research.
Foundational Concepts and Definitions
Key Risk Parameters
Understanding the core parameters of risk is essential for conducting a thorough analysis. The table below summarizes these fundamental concepts:
Table 1: Core Risk Parameters in Forensic Method Validation
| Parameter | Definition | Application in Forensic Validation |
|---|---|---|
| Impact | The effect a risk will have on the validation project if it occurs [29] | Also called consequence; measured in terms of effect on cost, schedule, functionality, and quality [29] |
| Likelihood | The extent to which the risk effects are likely to occur [29] | Comprises probability of occurrence and intervention difficulty; measured on defined scales [29] |
| Precision | The degree to which the risk is currently known and understood [29] | Indicates confidence in impact and likelihood estimates; rated as low, medium, or high [29] |
| Risk Severity | Combined measurement derived from impact and likelihood [29] | Determined using a risk matrix; used to prioritize risks [29] |
| Risk Appetite | The amount and type of risk an organization is willing to pursue or retain [30] | In forensic validation, typically very low for risks affecting result reliability [28] |
Qualitative vs. Quantitative Risk Analysis
Risk analysis approaches fall into two primary categories, each with distinct characteristics and applications:
Qualitative Risk Analysis involves identifying threats and opportunities, assessing how likely they are to happen, and evaluating the potential impacts if they do occur. The results are typically shown using a Probability/Impact ranking matrix [31]. This approach operates in a more generalized, "big-picture" space and is particularly valuable for prioritizing risks according to probability and impact, identifying the main areas of risk exposure, and improving understanding of project risks [31]. In forensic contexts, qualitative analysis helps researchers quickly identify which aspects of a method validation require the most attention.
Quantitative Risk Analysis (QRA) involves assessing and quantifying risks by assigning probabilistic values to potential outcomes. This technique helps organizations make more informed decisions by measuring the probability and impact of risks in financial or measurable terms [32]. According to Meyer, quantitative risk management in project management is "the process of converting the impact of risk on the project into numerical terms" [33]. This numerical information is frequently used to determine cost and time contingencies. In forensic validation, QRA might be applied to quantify the probability of false positives/negatives or to estimate the financial impact of validation delays.
Qualitative Risk Assessment Protocols
Core Qualitative Assessment Methodology
The qualitative risk assessment process for forensic method validation involves a structured approach to evaluating risks based on their potential impact and likelihood of occurrence. The protocol consists of the following key steps:
Step 1: Impact Assessment Define impact criteria specific to forensic validation success. Impact is typically rated on a discrete scale, such as 1=Very Low to 5=Very High [29]. For forensic method validation, consider four key impact dimensions:
- Technical Impact: Effect on method performance characteristics (accuracy, precision, specificity, sensitivity)
- Regulatory Impact: Effect on compliance with Forensic Science Regulator codes and international standards [28]
- Judicial Impact: Effect on admissibility of evidence and court acceptance [28]
- Resource Impact: Effect on project costs, timelines, and personnel requirements
The overall impact rating for a risk is determined by the highest of any individual impact dimension, not the average [29]. This conservative approach ensures that severe impacts in any single dimension receive appropriate attention.
Step 2: Likelihood Assessment Evaluate probability of occurrence using a defined scale (e.g., 1=Very Unlikely to 5=Near Certain) [29]. In forensic contexts, likelihood assessment should consider:
- Probability of Occurrence: The probability that risk events will occur if no action is taken
- Intervention Difficulty: The level of difficulty in preventing the risk event from occurring [29]
- Historical Data: Available data from similar validation studies or method applications
The likelihood rating is typically determined by the lower of the ratings for probability of occurrence and intervention difficulty, providing a conservative estimate [29].
Step 3: Precision Rating Assign a precision rating (Low, Medium, or High) that indicates the confidence in the impact and likelihood estimates [29]. This rating reflects the current knowledge and understanding of the risk. Low precision serves as a warning that a risk may be more serious than currently estimated and may require additional research or monitoring.
Step 4: Risk Matrix Application Plot impact and likelihood ratings on a risk matrix to determine overall risk severity levels. The matrix is typically divided into zones representing major (red), moderate (yellow), and minor (green) risks [29] [34].
Specialized Qualitative Techniques for Forensic Validation
Several qualitative techniques are particularly well-suited for forensic method validation research:
Delphi Technique: A form of risk brainstorming that uses expert opinion to identify, analyse, and evaluate risks on an individual and anonymous basis [35]. Each expert reviews every other expert's risks, and a risk register is produced through continuous review and consensus. This technique is valuable in forensic validation where specialized expertise is required and group dynamics might otherwise dominate discussions.
Structured What-If Technique (SWIFT): Applies a systematic, team-based approach in a workshop environment where the team investigates how changes from an approved design or plan may affect a project through a series of "What if" considerations [35]. This technique is particularly useful in evaluating the viability of opportunity risks and assessing the impact of deviations from validation protocols.
Bow-Tie Analysis: Starts by looking at a risk event and then projects it in two directions - to the left, all potential causes are listed, and to the right, all potential consequences are listed [35]. This enables researchers to identify and apply mitigations to each cause and consequence separately, effectively addressing both probability of occurrence and impact severity.
Table 2: Qualitative Risk Analysis Techniques for Forensic Validation
| Technique | Protocol | Application Context in Forensic Validation |
|---|---|---|
| Probability/Consequence Matrix | Standard method of establishing risk severity by ranking risks through multiplying likelihood against impact [35] | General application across all validation phases; provides quick visual prioritization |
| Bow-Tie Analysis | Identify causes (left) and consequences (right) of risk event; apply barriers to each [31] [35] | Complex validation steps where multiple failure points exist; instrument method validation |
| Delphi Technique | Anonymous expert input through multiple rounds until consensus reached [31] [35] | Novel techniques with limited historical data; resolving conflicting risk assessments |
| SWIFT Analysis | Structured "What-if" workshop investigating changes from approved plan [31] [35] | Protocol modifications; assessing impact of procedural deviations |
| Pareto Principle | Identify critical 20% of risks that will mitigate 80% of impact [31] | Resource-constrained validation projects; prioritizing risk treatment efforts |
Quantitative Risk Assessment Protocols
Quantitative Risk Assessment Methodology
Quantitative risk assessment (QRA) in forensic method validation provides numerical estimates of risk exposure, enabling more precise resource allocation and contingency planning. The QRA process consists of the following key steps:
Step 1: Risk Identification and Parameter Definition
- Identify risks amenable to quantitative analysis
- Define measurable parameters for probability and impact
- Establish probability distributions for key risk variables based on historical data or expert judgment
Step 2: Data Collection and Probability Assignment
- Gather historical data on similar validation activities
- Interview subject matter experts for probability estimates
- Document sources and rationale for all probability assignments
- For forensic validation, particular attention should be paid to data quality and reliability
Step 3: Model Construction and Analysis
- Select appropriate quantitative techniques (e.g., Monte Carlo simulation, sensitivity analysis)
- Build mathematical models representing the validation process and its risks
- Run simulations or calculations to generate probability distributions of outcomes
Step 4: Contingency Determination and Decision Support
- Analyze results to determine appropriate contingencies for time and resources
- Identify key risk drivers through sensitivity analysis
- Document findings and recommendations for risk treatment planning
Quantitative Techniques for Forensic Validation
Monte Carlo Simulation: A mathematical technique that runs multiple simulations (typically thousands) to predict the outcomes of risks by varying different factors [32]. It's used to evaluate the probability distribution of possible outcomes and is particularly valuable for assessing the combined effect of multiple risks on validation timelines and costs. In forensic validation, this technique can model the probability of achieving validation milestones within specific timeframes or budgets.
Sensitivity Analysis: Tests how sensitive the final outcome is to changes in input variables, allowing researchers to understand which risks have the most influence [32]. This solves a common challenge in quantitative risk analysis of identifying the most important variables for risk mitigation. For forensic method validation, sensitivity analysis helps prioritize which validation parameters require the most rigorous control.
Expected Value Methods: Multiply the probability of a risk by the maximum time/cost exposure of the risk to obtain a contingency value [33]. These methods include the Method of Moments and expected value of individual risks. These approaches are particularly useful for discrete, well-defined risks in validation protocols.
Decision Tree Analysis: Used to help determine the best course of action wherever there is uncertainty in the outcome of possible events or proposed plans [35]. This is done by starting with the initial proposed decision and mapping the different pathways and outcomes as a result of events occurring from the initial decision.
Table 3: Quantitative Risk Assessment Methods for Forensic Validation
| Method | Protocol Steps | Output Metrics | Forensic Validation Application |
|---|---|---|---|
| Monte Carlo Simulation | 1. Define probability distributions for input variables2. Run thousands of iterations3. Analyze output distributions [32] [33] | Probability distributions of completion dates, costs; confidence levels | Estimating validation timeline and budget contingencies; assessing probability of meeting acceptance criteria |
| Sensitivity Analysis | 1. Identify key input variables2. Systematically vary each input3. Measure impact on outputs [32] | Tornado diagrams; sensitivity indices; key risk drivers | Identifying most critical validation parameters; prioritizing method optimization efforts |
| Expected Value Method | 1. Estimate probability of each risk2. Determine maximum impact3. Calculate expected value [33] | Expected monetary value; expected time impact | Calculating contingency reserves for validation budget; assessing risk treatment cost-effectiveness |
| Decision Tree Analysis | 1. Map decision points and chance events2. Assign probabilities to branches3. Calculate expected values [35] | Optimal decision path; expected values of alternatives | Selecting between alternative validation approaches; choosing instrument configurations |
Integration and Application in Forensic Context
Risk Assessment Considerations for Forensic Validation
The application of risk assessment in forensic method validation requires special considerations due to the legal implications of forensic evidence. The Criminal Practice Directions in England and Wales provide factors which courts may consider in determining the reliability of evidence, including [28]:
- "The extent and quality of the data on which the expert's opinion is based, and the validity of the methods by which they were obtained"
- "If the expert's opinion relies on an inference from any findings, whether the opinion properly explains how safe or unsafe the inference is"
- "If the expert's opinion relies on the results of the use of any method, whether the opinion takes proper account of matters, such as the degree of precision or margin of uncertainty, affecting the accuracy or reliability of those results"
These judicial considerations directly inform the risk criteria used in both qualitative and quantitative assessments. Impact scales should reflect not only technical and operational consequences but also judicial consequences, including potential challenges to admissibility and weight given to evidence.
Structured Approach for Forensic Method Validation
A robust risk assessment protocol for forensic method validation should include:
Pre-Assessment Preparation
- Review regulatory requirements including the Forensic Science Regulator's Codes of Practice [28]
- Identify all stakeholders including forensic practitioners, legal professionals, and end-users
- Define risk appetite and tolerance levels specific to the forensic context
- Establish validation objectives and acceptance criteria
Assessment Execution
- Conduct iterative analysis starting with qualitative screening and progressing to quantitative analysis for high-priority risks
- Document all assumptions, data sources, and rationale for risk ratings
- Apply appropriate techniques based on data availability and risk complexity
- Review precision ratings and address knowledge gaps through additional research or experimentation
Post-Assessment Actions
- Develop risk treatment plans prioritized by risk severity
- Communicate findings to all stakeholders with appropriate context
- Establish monitoring protocols for high-priority risks
- Update risk assessments as new information becomes available throughout the validation process
Research Reagent Solutions for Risk Assessment Experiments
Table 4: Essential Research Materials for Risk Assessment in Forensic Validation
| Material/Resource | Function in Risk Assessment | Application Context |
|---|---|---|
| Risk Assessment Software (e.g., @RISK, Lumivero) | Enables quantitative analysis techniques including Monte Carlo simulation and sensitivity analysis [32] | All quantitative risk assessments; complex validation projects with multiple interdependent risks |
| Expert Panels | Provides qualitative input for probability and impact estimates; Delphi technique implementation [31] [35] | Novel method validation; addressing knowledge gaps; resolving conflicting risk assessments |
| Historical Validation Databases | Source data for probability estimates; benchmark for impact assessment [33] | All risk assessments; particularly valuable for quantitative analysis and establishing realistic probability distributions |
| Regulatory Guidance Documents (e.g., FSR Codes, ILAC-G19) | Defines impact criteria based on regulatory requirements; establishes validation expectations [28] | Setting risk criteria; determining impact severity for compliance risks |
| Statistical Analysis Tools | Supports quantitative analysis; enables sensitivity analysis and statistical modeling | Designing validation experiments; analyzing validation data; quantifying uncertainty |
The integration of both qualitative and quantitative risk assessment approaches provides a comprehensive framework for evaluating risks in forensic method validation research. Qualitative methods offer rapid prioritization and are accessible to all team members, while quantitative techniques provide numerical rigor and enable more precise contingency determination. In forensic science, where the consequences of validation failures can extend to miscarriages of justice, a structured approach to risk analysis is not merely beneficial but essential for demonstrating method reliability and fitness for purpose [28].
The protocols outlined in this document provide researchers with practical methodologies for implementing risk analysis within their validation frameworks. By applying these approaches consistently and documenting the process thoroughly, forensic researchers can not only improve their validation outcomes but also demonstrate due diligence in addressing uncertainties—a key consideration for admissibility in legal proceedings [28].
Risk Evaluation is the critical juncture in a risk assessment framework where identified and analyzed risks are judged against predefined criteria to determine their significance and decide on subsequent actions. For forensic method validation research, this step transforms qualitative concerns and quantitative data into a prioritized list of actionable risks, ensuring that scientific resources are allocated efficiently to mitigate the most impactful threats to method reliability, admissibility, and patient safety. A robust evaluation process is foundational to a risk-informed validation strategy, guiding researchers and drug development professionals in making consistent, defensible decisions.
Theoretical Foundation: Core Principles of Risk Evaluation
The evaluation process is built upon two core activities: setting risk thresholds and prioritizing actions. These activities are guided by the overarching principles of the risk management framework, which emphasize alignment with organizational objectives and structured decision-making [36].
- Setting Thresholds (Risk Criteria): This involves establishing the levels of risk that are deemed acceptable or tolerable for the specific validation project. These thresholds are derived from the project's risk appetite—the type and amount of risk the organization is willing to accept in pursuit of its objectives [36]. In a regulatory context like forensic method validation, this appetite is often constrained by strict guidelines for accuracy, precision, and reliability.
- Prioritizing Actions: Once risks are scored and compared against thresholds, they must be prioritized to direct resources and attention. Prioritization is typically based on the severity rating derived from a risk matrix, ensuring that risks with the highest potential impact and likelihood are addressed first [36].
Experimental Protocols for Risk Evaluation
Protocol: Establishing a Risk Assessment Matrix
A risk matrix is a fundamental tool for visualizing and scoring risks based on their likelihood and impact.
1. Objective: To create a consistent, standardized tool for scoring and categorizing risks identified during the forensic method validation process.
2. Materials and Reagents:
- Risk Register documenting identified potential failures [36].
- Data from initial risk analysis (e.g., preliminary experiments, historical data).
- Risk management software or a spreadsheet application.
3. Methodology: a. Define Impact Scales: Establish a 5-point scale for the severity of a risk's consequence, tailored to forensic validation. See Table 1 for detailed criteria. b. Define Likelihood Scales: Establish a 5-point scale for the probability of a risk occurring. See Table 1 for detailed criteria. c. Construct the Matrix: Create a 5x5 grid with impact on the Y-axis and likelihood on the X-axis. d. Define Risk Zones: Color-code the matrix to create risk zones (e.g., High, Medium, Low). The combination of likelihood and impact determines the final risk score and priority level.
4. Data Analysis: Each risk is plotted on the matrix based on its assigned likelihood and impact scores. The resulting position determines its priority for further action.
Protocol: Applying Thresholds for Risk Acceptance
1. Objective: To make consistent "accept" or "treat" decisions for each evaluated risk based on its priority level and the project's pre-defined risk thresholds.
2. Materials and Reagents:
- Populated Risk Assessment Matrix.
- Pre-approved Risk Appetite Statement for the validation project.
3. Methodology: a. Define Acceptance Criteria: Before evaluation, establish what constitutes an acceptable risk. For example: * Low (Green) Risks: Acceptable. No additional mitigation required beyond routine controls. * Medium (Yellow) Risks: Conditionally acceptable. May require management review and monitoring. * High (Red) Risks: Unacceptable. Must be mitigated to a lower level before method validation can be finalized. b. Compare and Decide: Systematically compare each risk's score from the matrix against the acceptance criteria. c. Document Justification: For all risks deemed "acceptable," especially medium-priority ones, document the rationale for the decision to provide a defensible audit trail.
Data Presentation and Analysis
Table 1: Risk Assessment Criteria for Forensic Method Validation
This table provides sample criteria for scoring the impact and likelihood of risks specific to analytical method validation.
| Category | Level | Score | Criteria Description |
|---|---|---|---|
| Impact (Severity) | Negligible | 1 | Minor deviation with no effect on final result or interpretability. |
| Minor | 2 | Deviation affects precision but not accuracy; result remains within acceptable regulatory limits. | |
| Moderate | 3 | Deviation poses a potential for inaccurate results, risking data quality and user safety. | |
| Major | 4 | Deviation leads to a false positive/negative, directly impacting patient diagnosis or legal outcome. | |
| Critical | 5 | Method failure that compromises patient safety, legal proceeding, or results in regulatory action. | |
| Likelihood (Probability) | Very Unlikely | 1 | <5% probability of occurrence in a standard validation study. |
| Unlikely | 2 | 5-20% probability of occurrence. | |
| Possible | 3 | 21-50% probability of occurrence. | |
| Likely | 4 | 51-80% probability of occurrence. | |
| Very Likely | 5 | >80% probability of occurrence. |
Table 2: Risk Treatment and Prioritization Matrix
This matrix guides the prioritization of actions based on the risk score, which is calculated as Impact x Likelihood.
| Impact Score | x1 (Very Unlikely) | x2 (Unlikely) | x3 (Possible) | x4 (Likely) | x5 (Very Likely) |
|---|---|---|---|---|---|
| 5 (Critical) | 5 (Medium) | 10 (High) | 15 (High) | 20 (High) | 25 (High) |
| 4 (Major) | 4 (Medium) | 8 (High) | 12 (High) | 16 (High) | 20 (High) |
| 3 (Moderate) | 3 (Low) | 6 (Medium) | 9 (High) | 12 (High) | 15 (High) |
| 2 (Minor) | 2 (Low) | 4 (Medium) | 6 (Medium) | 8 (High) | 10 (High) |
| 1 (Negligible) | 1 (Low) | 2 (Low) | 3 (Low) | 4 (Medium) | 5 (Medium) |
Priority and Action Guide:
- High (Red, Score 8-25): Unacceptable. Immediate mitigation required. Action must be taken to reduce the impact and/or likelihood.
- Medium (Yellow, Score 4-10): Conditionally acceptable. Monitoring and review required. Mitigation should be considered based on cost-benefit analysis.
- Low (Green, Score 1-3): Acceptable. Routine monitoring is sufficient. No additional mitigation is needed.
Visualization of the Risk Evaluation Workflow
The following diagram illustrates the logical workflow for the risk evaluation process, from an identified risk to a final treatment decision.
The Scientist's Toolkit: Essential Research Reagents and Materials
| Item | Function in Risk Assessment |
|---|---|
| Certified Reference Materials (CRMs) | Provides a ground truth for assessing the accuracy and trueness of an analytical method, a key parameter in evaluating the impact of quantitative risks. |
| Internal Standards (Stable-Labeled Isotopes) | Corrects for analytical variability and sample preparation losses, directly mitigating risks associated with poor precision and recovery. |
| Quality Control (QC) Samples | Monitors method performance over time, serving as a key control for detecting risks related to instrument drift or reagent degradation. |
| Robustness/Forced Degradation Samples | Systematically challenges the method with deliberate variations (e.g., pH, temperature) to identify and quantify risks related to method ruggedness. |
| Specificity/Interference Testing Panels | Assesses the risk of false positives or negatives by testing the method against structurally similar compounds and potential interferents found in the sample matrix. |
Within the framework of a risk assessment for forensic method validation research, risk treatment is the process of selecting and implementing measures to modify risk. This phase follows the identification, analysis, and evaluation of risks, and involves determining the most appropriate strategy to handle risks that are deemed unacceptable. For forensic science providers, the objective is to ensure that any method employed in the Criminal Justice System (CJS) is demonstrably fit for purpose, and that the results can be shown to be reliable for use in court [28]. This document outlines the four primary risk treatment strategies—Avoidance, Mitigation, Transfer, and Acceptance—providing detailed application notes and experimental protocols for researchers and scientists in forensic and drug development fields.
The Four Risk Treatment Strategies
The four primary strategies for treating risk are defined and distinguished in the table below, with specific examples relevant to forensic method validation.
Table 1: Core Risk Treatment Strategies and Their Applications
| Strategy | Definition | Objective | Example from Forensic Method Validation |
|---|---|---|---|
| Risk Avoidance [37] [38] | Taking action to eliminate the risk entirely by deciding not to proceed with the activity that introduces it. | To completely avoid any exposure to the risk and its potential consequences. | A research team abandons a novel, unproven analytical technique in favor of a well-established, standard method to avoid the risk of unreliable results [37]. |
| Risk Mitigation [37] [38] | Taking steps to reduce the likelihood of a negative event occurring and/or to lessen its potential impact. | To reduce the risk to an acceptable level, making it more manageable. | A lab conducts extensive internal replication studies and statistical analysis to lower the uncertainty of measurement for a new method, thereby reducing the risk of erroneous interpretation [28]. |
| Risk Transfer [37] [38] | Shifting the risk to a third party who is willing to accept it and manage the consequences. | To share or reallocate the responsibility and financial impact of the risk. | A forensic unit outsourcing the development and initial validation of a highly specialized DNA sequencing method to an accredited academic partner with specific expertise [38]. |
| Risk Acceptance [37] [38] [39] | Acknowledging the risk and consciously deciding to retain it, without taking specific action to change its likelihood or impact. | To formally accept risks that are low-impact, low-likelihood, or where the cost of treatment outweighs the benefit. | A lab, after thorough evaluation, accepts the minor risk associated with a known, well-characterized chemical interference in a test that occurs only at extreme concentrations not seen in casework [39]. |
Risk Treatment Decision-Making Protocol
The following workflow provides a logical sequence for selecting an appropriate risk treatment strategy. This process ensures that decisions are objective, evidence-based, and aligned with the goals of the forensic validation project.
Figure 1: A logical workflow for selecting a risk treatment strategy. This protocol guides the user through a series of key questions to arrive at the most appropriate strategy, culminating in the critical step of documentation and monitoring.
Experimental Protocol for Risk Treatment Selection
This protocol provides a detailed methodology for conducting a risk treatment evaluation session.
- Objective: To systematically select a risk treatment strategy for a specific risk identified during forensic method validation.
- Materials:
- Risk Register (from previous risk assessment steps)
- Pre-defined risk tolerance/appetite statement
- Cost-benefit analysis worksheet
- Procedure:
- Convene Review Panel: Assemble the lead researcher, a quality assurance representative, and a technical expert.
- Review Risk Evaluation: Present the risk, including its assessed likelihood, impact, and priority level.
- Apply Decision Workflow: Use the logic outlined in Figure 1 to guide the discussion.
- Compare the risk level against the pre-defined risk tolerance.
- For risks exceeding tolerance, brainstorm and evaluate all feasible treatment options (Avoid, Mitigate, Transfer).
- Perform Cost-Benefit Analysis: For the preferred option, document the estimated resources required for implementation versus the expected reduction in risk.
- Formalize Decision: Reach a consensus on the chosen strategy.
- Document Outcome: Record the decision, its justification, and any required actions in the risk register.
Detailed Application Notes for Forensic Validation
Risk Avoidance in Practice
Avoidance is often the most straightforward strategy but may not be feasible for core research objectives. In forensic validation, avoidance is typically applied when a proposed method is found to be fundamentally flawed, based on unsound scientific principles, or has a high potential for producing misleading results that cannot be engineered out. The decision to avoid a method must be documented with a clear scientific rationale, as this contributes to the overall body of knowledge and prevents future investment in unproductive avenues [28].
Risk Mitigation: The Primary Strategy
Risk mitigation is the most common and central strategy in forensic method validation. The entire validation process is, in essence, a form of risk mitigation—it is the action taken to provide objective evidence that a method is fit for purpose, thereby reducing the risk of unreliable evidence being presented in court [28].
Table 2: Risk Mitigation Measures in Validation Studies
| Risk Category | Potential Mitigation Measure | Validation Study Protocol |
|---|---|---|
| Poor Precision | Optimize instrumentation parameters and standardize sample preparation. | Protocol: Conduct a intermediate precision study where a homogeneous sample is analyzed repeatedly (n=10) by two different analysts on three different days. Calculate the relative standard deviation (RSD%) for results. Acceptance Criteria: RSD% is less than a pre-defined threshold based on the method's required performance. |
| Systematic Bias (Inaccuracy) | Use certified reference materials (CRMs) for calibration. | Protocol: Analyze a series of CRMs with known concentration/values covering the method's working range. Perform linear regression analysis. Acceptance Criteria: The calculated values from the regression model show a bias of less than ±5% from the certified values. |
| Cross-Reactivity/Interference | Test the method against a panel of structurally similar compounds and common interferents. | Protocol: Spike blank samples with potential interferents at physiologically relevant high concentrations and analyze. Acceptance Criteria: The response for the target analyte does not deviate by more than ±10% compared to a control, and no interferent is mistakenly identified as the target. |
| Data Interpretation Errors | Develop and validate clear, standardized criteria for positive/negative/inconclusive results. | Protocol: Provide a set of pre-characterized data (blinded) to multiple trained analysts for independent interpretation. Acceptance Criteria: A high degree of inter-analyst concordance (e.g., >95%) is achieved in the final conclusions. |
Risk Transfer through Collaboration
In a research context, risk transfer often involves partnering with other entities that possess specialized expertise or equipment. This is formalized through collaboration agreements and service contracts. The key is to ensure that the third party is competent, and their work is subject to the same rigorous quality standards. As noted in the UK Forensic Science Regulator's guidance, the forensic unit retains overall responsibility and must verify that the transferred work is performed to the required standard [28]. This is achieved by auditing the partner's validation data and conducting your own verification studies.
Formal Risk Acceptance
Risk acceptance is not negligence; it is a documented, conscious decision. For a risk to be accepted, it must fall below the organization's risk tolerance threshold, or the cost of mitigation must be demonstrably disproportionate to the benefit gained. The rationale for acceptance must be explicitly recorded in the validation documentation and signed off by appropriate management [38] [39]. This provides a defensible audit trail, which is critical for addressing potential challenges in court regarding the choices made during method development [28].
The Scientist's Toolkit: Essential Research Reagents & Materials
The following table details key materials and solutions used in the experimental protocols for risk mitigation during method validation.
Table 3: Key Reagents and Materials for Validation Experiments
| Item | Function / Rationale |
|---|---|
| Certified Reference Materials (CRMs) | Provides a traceable and definitive standard for establishing the accuracy (trueness) of a method. Essential for mitigating the risk of systematic bias [28]. |
| Homogeneous Control Sample | A stable, well-characterized sample used in precision studies (repeatability and reproducibility). Mitigates the risk of poor precision by providing a consistent matrix for analysis. |
| Panel of Interferents | A curated collection of chemical compounds known or suspected to cause interference. Used to challenge the method's specificity and mitigate the risk of false positives/negatives. |
| Blinded Sample Set | A set of samples with known properties but unidentified to the analyst. Used in robustness and data interpretation studies to mitigate the risk of subjective bias. |
| Quality Control (QC) Check Sample | A sample analyzed at regular intervals during a validation study to monitor the ongoing performance of the analytical system. Mitigates the risk of undetected instrument drift or failure. |
Method validation provides objective evidence that analytical procedures are reliable, reproducible, and fit for their intended purpose, forming the cornerstone of pharmaceutical quality control and forensic evidence reliability. In both fields, validation demonstrates that results produced are scientifically sound and legally defensible. The International Council for Harmonisation (ICH) provides a harmonized framework through guidelines like Q2(R2) that, once adopted by regulatory bodies like the U.S. Food and Drug Administration (FDA), becomes the global standard [23]. This framework ensures methods validated in one region are recognized worldwide, streamlining development to market pathways [23].
The simultaneous 2024 release of ICH Q2(R2) and ICH Q14 represents a significant modernization from prescriptive "check-the-box" approaches toward a scientific, lifecycle-based model [23]. This shift emphasizes that validation is not a one-time event but continuous throughout a method's entire lifespan [40]. Within forensic contexts, method validation demonstrates that results are reliable and fit for purpose, supporting admissibility in legal systems under Frye or Daubert standards [41]. All methods must be scientifically sound, add evidential value, and conserve sample for future analyses [41].
Case Study 1: Lifecycle Management of a Chromatographic Method for API Quantification
Background and Development
This case study details the application of a lifecycle approach to validating a reversed-phase ultra-high-performance liquid chromatography (RP-UHPLC) method for quantifying a new active pharmaceutical ingredient (API) and its degradation products. Traditional validation approaches often treated validation as a one-time event, but the lifecycle management approach required by modern guidelines integrates development, validation, and continuous verification [23] [40].
Method development began with defining an Analytical Target Profile (ATP) as introduced in ICH Q14 [23]. The ATP prospectively defined the method's purpose as "to quantify the API and identify any degradation products above 0.1% in finished drug products." The required performance characteristics included:
- Accuracy: ±2% of true value for API
- Precision: ≤2% RSD
- Specificity: Base resolution (R > 2.0) between API and all known degradation products
- Linearity: R² > 0.999 over 50-150% of target concentration
Experimental Protocol and Validation Data
The experimental methodology followed a risk-based approach aligned with ICH Q9 principles [23]. A Design of Experiments (DoE) approach identified critical method parameters, including mobile phase pH (±0.2 units), gradient slope (±2%), and column temperature (±5°C) [40]. The protocol evaluated these parameters through a structured matrix to establish a Method Operational Design Range (MODR) where the method remains robust [40].
Table 1: Summary of Validation Results for API Assay Method
| Validation Parameter | Protocol | Results | Acceptance Criteria |
|---|---|---|---|
| Accuracy | 9 determinations at 3 levels (50%, 100%, 150%) | 99.8-100.5% recovery | 98-102% |
| Precision (Repeatability) | 6 determinations at 100% | RSD = 0.8% | RSD ≤ 2.0% |
| Specificity | Forced degradation samples (acid, base, oxidation, thermal, photolytic) | Base resolution from all degradants | Resolution > 2.0 |
| Linearity | 5 concentrations (50-150%) | R² = 0.9998 | R² ≥ 0.999 |
| Range | 50-150% of target concentration | Demonstrated precise, linear, accurate | Established from linearity data |
| Robustness | Deliberate variations in pH, temperature, flow rate | All parameters within MODR | System suitability criteria met |
The validation followed a risk-based validation approach, concentrating resources on critical systems and processes that impact product quality [40]. Failure Modes and Effects Analysis (FMEA) was conducted to prioritize validation efforts, with high-risk scores assigned to specificity and accuracy parameters [40].
Lifecycle Monitoring and Control Strategy
Following initial validation, a control strategy was implemented for ongoing method performance verification [40]. This included system suitability tests before each analysis and periodic review of quality control data. The method was incorporated into a continuous process validation framework using Process Analytical Technology (PAT) for real-time monitoring where applicable [42].
The lifecycle approach enabled science-based, risk-based post-approval change management [23]. When a new degradation product was identified during stability studies, a risk assessment determined that only limited re-validation was required rather than full validation, demonstrating the efficiency of the lifecycle model [40].
Case Study 2: Collaborative Validation of a Forensic Toxicological Method
Background and Collaborative Framework
This case study examines a collaborative method validation for a liquid chromatography-tandem mass spectrometry (LC-MS/MS) method for novel synthetic opioid detection in biological samples, following the model proposed for Forensic Science Service Providers (FSSPs) [41]. The traditional approach of individual validations by each laboratory creates significant redundancy and misses opportunities to combine talents and share best practices [41].
The collaboration involved one originating laboratory conducting a full validation and publishing the work in a peer-reviewed journal, enabling subsequent laboratories to perform verification studies rather than full validations [41]. This approach required strict adherence to identical instrumentation, procedures, reagents, and parameters across all participating laboratories [41].
Table 2: Collaborative Validation Parameters for LC-MS/MS Opioid Panel
| Parameter | Originating Lab Results | Verifying Lab 1 Results | Verifying Lab 2 Results | Acceptance Criteria |
|---|---|---|---|---|
| LOD (pg/mg) | 5 | 5 | 5 | ≤10 |
| LOQ (pg/mg) | 10 | 10 | 10 | ≤20 |
| Accuracy (% bias) | ±8 | ±9 | ±7 | ≤±15 |
| Precision (% RSD) | 6 | 7 | 5 | ≤15 |
| Matrix Effects (%) | 85 | 88 | 83 | 80-120 |
| Process Efficiency (%) | 90 | 92 | 88 | ≥70 |
Experimental Protocol
The methodology employed hyphenated techniques (LC-MS/MS) to streamline analysis of multiple analytes in a single assay [40]. The originating laboratory developed and validated the method following SWGDAM standards and published the complete validation data [41]. Key protocol steps included:
- Sample Preparation: 10 mg hair samples underwent pulverization and extraction with methanol:acetonitrile:water (40:40:20)
- Chromatography: Kinetex C18 column (100 × 2.1 mm, 1.7 μm) with 0.1% formic acid in water and acetonitrile gradient
- Mass Spectrometry: Positive electrospray ionization with multiple reaction monitoring (MRM)
- Quantification: Isotope-dilution with deuterated internal standards for each analyte
Participating laboratories following the published method exactly could conduct an abbreviated method validation (verification) [41]. The verification process required each laboratory to:
- Demonstrate proficiency with the method using quality control materials
- Analyze a minimum of 20 authentic samples across the calibration range
- Compare results with the originating laboratory's data for statistical equivalence
- Establish that all performance parameters met the predefined acceptance criteria
Outcomes and Benefits
The collaborative model provided significant advantages. The originating laboratory invested 480 personnel hours in development and validation, while verifying laboratories required only 120-160 hours each - representing approximately 70% reduction in validation time [41]. Additional benefits included:
- Direct comparability of results across jurisdictions [41]
- Establishment of a working group to share results and optimize parameters [41]
- Cross-check of original validity through independent verification [41]
- More efficient sharing of best practices among forensic laboratories [41]
The collaboration extended to academic institutions, with graduate students generating validation data as part of thesis requirements, providing practical experience while contributing to the validation [41].
Instrumentation and Workflow Visualization
Pharmaceutical Method Validation Workflow
The following diagram illustrates the integrated lifecycle approach to pharmaceutical method validation, incorporating QbD principles and continuous verification as mandated by modern regulatory guidelines:
Collaborative Forensic Validation Model
The following workflow depicts the collaborative validation approach for forensic methods, demonstrating the reduced burden on verifying laboratories through resource and data sharing:
The Scientist's Toolkit: Essential Research Reagent Solutions
Table 3: Key Reagents and Materials for Pharmaceutical and Forensic Method Validation
| Item | Function | Application Examples |
|---|---|---|
| Certified Reference Standards | Provides known purity materials for accuracy, linearity, and calibration | API quantification, forensic analyte confirmation |
| Mass Spectrometry Grade Solvents | Minimize background interference and ion suppression in LC-MS/MS | High-sensitivity detection of trace-level analytes |
| Stable Isotope-Labeled Internal Standards | Correct for matrix effects and recovery variations | Quantitative bioanalysis in biological matrices |
| Characterized Impurities and Degradants | Establish specificity and forced degradation studies | Method validation for stability-indicating methods |
| Quality Control Materials | Monitor method performance over time | System suitability, ongoing quality assurance |
| Sample Preparation Materials | Efficient and reproducible extraction of analytes | Solid-phase extraction cartridges, supported liquid extraction |
The case studies presented demonstrate how modern validation approaches provide robust, efficient, and defensible analytical methods for both pharmaceutical and forensic applications. The lifecycle approach to pharmaceutical method validation, guided by ICH Q2(R2) and Q14, creates more robust and understandable methods while enabling more flexible post-approval change management [23]. The collaborative model for forensic validation significantly reduces redundant work while improving standardization and result comparability across laboratories [41].
Both approaches emphasize science- and risk-based principles rather than prescriptive check-box exercises, creating more efficient validation processes while maintaining or enhancing technical rigor. Implementation of these models requires strategic planning and investment but delivers substantial returns through reduced validation costs, faster implementation of new methods, and improved method reliability [40]. As analytical technologies continue to advance, these flexible, principles-based validation frameworks will accommodate new innovations while ensuring data quality and regulatory compliance.
Navigating Pitfalls and Enhancing Robustness in Forensic Methods
Common Failure Points in Digital and Analytical Forensic Methods
Within the framework of forensic science research, the validation of methods is paramount to ensuring the reliability and admissibility of evidence. This document outlines common failure points in digital and analytical forensic methods, serving as a foundational risk assessment tool for researchers and developers. The accelerating pace of technological change, including the proliferation of artificial intelligence (AI), complex cloud environments, and the Internet of Things (IoT), continuously introduces new vulnerabilities into forensic processes [43] [44]. A proactive identification of these failure points is essential for developing robust, validated methods that withstand legal and scientific scrutiny. This document provides structured application notes and detailed protocols to guide research and development efforts aimed at fortifying forensic methodologies against these inherent risks.
Common Failure Points: A Categorical Analysis
The failure points in modern forensic methods can be categorized into technical, procedural, and interpretative domains. The tables below summarize these key failure points, their impacts, and associated risks for researchers to target in their validation studies.
Table 1: Technical and Data-Related Failure Points
| Failure Point | Description | Impact on Forensic Process | Risk Priority for Validation Research |
|---|---|---|---|
| Encryption & Secure Communication | Widespread use of encrypted messaging apps and storage makes data inaccessible without keys [43]. | Prevents acquisition and analysis of critical evidence; halts investigations. | High |
| Cloud Data Fragmentation | Evidence is distributed across servers in multiple jurisdictions with different legal frameworks [43] [44]. | Causes significant delays in evidence collection; creates legal hurdles for access. | High |
| AI-Generated Media (Deepfakes) | Use of AI to create convincing fake video and audio evidence that is difficult to detect [43] [45]. | Compromises evidence integrity; can mislead investigations and undermine trust in digital evidence. | High |
| IoT & Mobile Device Diversity | Proliferation of devices with varied operating systems, storage formats, and limited data retention [43] [45]. | Increases complexity of data acquisition; requires constant tool adaptation; critical data can be ephemeral. | High |
| Big Data Volume & Variety | The enormous amount of data from diverse sources (cloud, social media, blockchain) overwhelms traditional tools [43] [44]. | Slows down analysis; risks missing critical evidence due to information overload. | Medium |
Table 2: Procedural and Human-Related Failure Points
| Failure Point | Description | Impact on Forensic Process | Risk Priority for Validation Research |
|---|---|---|---|
| Inadequate Method Validation | Failure to demonstrate that a tool or method is fit for its intended purpose through rigorous testing [13] [7]. | Renders evidence inadmissible in court; foundational reliability of findings is questioned. | High |
| Break in Chain of Custody | Improper documentation of who handled evidence, when, and for what purpose [43] [46]. | Compromises evidence integrity and authenticity, leading to potential legal exclusion. | High |
| Outdated Guidelines & Standards | Reliance on legacy procedures (e.g., ACPO guidelines from 2012) that do not address modern technology [47]. | Creates a gap between established procedures and real-world challenges, leading to improper evidence handling. | Medium |
| Cross-Border Legal Inconsistencies | Conflicts in international data sovereignty laws (e.g., GDPR vs. U.S. CLOUD Act) complicate evidence gathering [43] [44]. | Delays or prevents access to evidence stored in other jurisdictions. | Medium |
| Black Box AI Analysis | Use of AI and machine learning tools whose decision-making processes are not transparent or explainable [44] [7]. | Undermines the credibility of expert testimony and makes cross-examination difficult. | High |
Table 3: Interpretative and Legal Failure Points
| Failure Point | Description | Impact on Forensic Process | Risk Priority for Validation Research |
|---|---|---|---|
| Interpretation Bias | The contextual information and subjective judgment of the analyst can lead to misinterpretation of digital traces [48] [7]. | Can lead to incorrect conclusions about the meaning of evidence, potentially resulting in miscarriages of justice. | High |
| Algorithmic Bias in Risk Tools | Violence risk assessment tools can demonstrate poor to moderate predictive accuracy, with higher false positive rates in minority ethnic groups [20]. | Can lead to unjustified prolonged detention or premature release, raising serious ethical and legal issues. | High |
| False Positive/Negative Tool Output | Forensic tools may incorrectly report data (e.g., overstating search history) or miss critical artifacts [7]. | Directly leads to incorrect investigative conclusions and undermines the entire forensic process. | High |
Experimental Protocols for Mitigating Key Failure Points
Protocol: Validation of a Novel Digital Forensic Tool
Objective: To rigorously test a new software tool for extracting and parsing data from a mobile device, ensuring it is fit for purpose and meets end-user requirements for a specific investigation type [13].
Workflow:
Methodology:
- Determine End-User Requirements: Define the specific needs of the investigation. Example: "The tool must reliably recover and display deleted WhatsApp messages from Android devices running OS version 14, with a recovery rate of ≥95% from a known test dataset." [13]
- Review Requirements and Specification: Formalize the requirements into a testable specification.
- Risk Assessment: Identify potential points of failure (e.g., tool cannot decrypt new encryption, misparses message timestamps).
- Set Acceptance Criteria: Define quantitative and qualitative benchmarks for success (e.g., 95% message recovery, zero alteration of source data, complete and accurate timeline generation).
- Validation Plan: Design experiments to stress-test the tool.
- Test Data: Use a representative, known dataset (e.g., a controlled Android device with a pre-populated and partially deleted WhatsApp message history) [13] [7].
- Comparative Analysis: Run the same dataset through multiple validated tools (e.g., Cellebrite, Magnet AXIOM) and compare outputs to identify discrepancies [7].
- Hash Verification: Before and after imaging, generate hash values (e.g., SHA-256) of the evidence to confirm data integrity [46] [7].
- Execute Validation Tests: Perform the tests as outlined in the plan, meticulously documenting all steps, tool versions, and outputs.
- Assess Against Acceptance Criteria: Evaluate the test results against the pre-defined criteria.
- Generate Validation Report: Compile a comprehensive report detailing the process, results, limitations, and a final statement on whether the tool is validated for the intended purpose [13].
Protocol: Deepfake Media Detection and Authentication
Objective: To establish a standardized methodology for detecting AI-generated video and audio content and verifying the authenticity of multimedia evidence [43] [47].
Workflow:
Methodology:
- Acquire Evidence Media File: Obtain the file through a forensically sound manner, preserving its integrity and chain of custody.
- Metadata Analysis: Scrutinize file metadata (EXIF, creation/modification times) for inconsistencies or signs of manipulation.
- Multi-Tool Detection Analysis: Process the media through multiple, validated deepfake detection algorithms. No single tool is infallible; consistent results across tools increases confidence [47].
- Frame-by-Frame Technical Analysis: Manually inspect the media for subtle artifacts indicative of deepfakes:
- Visual: Inconsistent lighting and shadows, unnatural blinking patterns, blurring at the subject-edge boundary, unnatural facial morphing [45].
- Audio: Lack of natural breath sounds, imprecise lip-syncing, synthetic voice artifacts.
- Contextual and Content Plausibility Check: Assess whether the content of the media aligns with known facts and is physically possible (e.g., does the weather in the video match the historical record for that date and location?).
- Synthesize Findings: Correlate findings from all analytical stages.
- Issue Authentication Report: Document the methodology, tools used, artifacts detected, and the final conclusion on the media's authenticity.
Protocol: Assessing Bias in AI-Driven Forensic Analysis
Objective: To evaluate and quantify potential biases in machine learning models used for analyzing digital evidence, such as mobile chat data or risk assessment scores [20] [47].
Methodology:
- Define Performance Metrics: Establish key metrics for evaluation: Precision, Recall, F1 Score, and Hallucination Rate (where the model generates incorrect or unsupported information) [47].
- Curate Diverse and Representative Datasets: Assemble test datasets that reflect real-world diversity, including variations in slang, dialects, linguistic styles, and demographic factors. The dataset must be representative of the population on which the tool will be used [20].
- Benchmarking: Test the AI model (e.g., GPT-4o, Gemini 1.5) on the curated dataset. Measure its performance against the defined metrics.
- Subgroup Analysis: Analyze the performance metrics across different subgroups within the dataset (e.g., defined by dialect or slang usage) to identify significant performance disparities [20].
- Error Analysis: Manually review false positives and false negatives to understand the contexts in which the model fails and identify potential sources of bias.
- Mitigation Strategy Development: Based on the findings, develop strategies to mitigate bias, which may include re-training the model on more balanced data, implementing post-processing filters, or establishing clear usage guidelines that acknowledge the model's limitations.
The Scientist's Toolkit: Essential Research Reagents & Materials
Table 4: Key Research Reagents and Solutions for Forensic Method Validation
| Item / Solution | Function in Validation Research | Example in Application |
|---|---|---|
| Certified Reference Materials (CRMs) | Provides a ground-truth dataset with known properties to verify tool accuracy. | A pre-configured mobile device image with a precisely mapped set of SMS, emails, and deleted files. |
| Hash Algorithm (SHA-256, MD5) | Generates a unique digital fingerprint for data; critical for proving integrity. | Used to verify that a forensic image is an exact, unaltered copy of the original evidence [46] [7]. |
| Write-Blocker | A hardware or software interface that prevents any data from being written to the source evidence device. | Essential during the data acquisition phase to preserve the integrity of the original evidence [46]. |
| Cross-Validation Tool Suite | A set of multiple forensic tools (commercial and open-source) used to verify results. | Running a disk image through both FTK and EnCase to cross-validate parsed artifacts and ensure consistency [7]. |
| Controlled Test Environment | A sandboxed, isolated computing environment (virtual or physical). | Prevents network contamination and allows for the safe execution of malware or analysis of suspicious files. |
| Standardized Operating Procedure (SOP) Template | A document framework ensuring all validation steps are documented consistently. | Provides the structure for the validation protocol, ensuring compliance with ISO17025 and other standards [13]. |
| Bias Assessment Dataset | A specially curated dataset designed to stress-test algorithms for fairness and accuracy across subgroups. | Used in Protocol 3.3 to evaluate if a chat analysis AI performs equally well across different demographic groups [20]. |
Forensic validation serves as the critical foundation for ensuring that forensic methods, tools, and interpreted results are accurate, reliable, and legally admissible [7]. It provides the scientific integrity necessary for justice systems to function properly. Within a risk assessment framework for forensic method validation research, understanding the consequences of inadequate validation is paramount for developing robust safeguards. When validation protocols fail or are incomplete, both legal proceedings and operational forensic processes face severe, measurable consequences that undermine their fundamental purpose.
The core principle of forensic validation is demonstrating that methods are "fit for purpose," meaning they consistently produce results that can be relied upon for specific applications [13]. Without this demonstrated reliability through proper validation, the entire forensic process becomes vulnerable to challenges at multiple levels.
Table 1: Categorization and Impact of Risks from Inadequate Forensic Validation
| Risk Category | Specific Consequence | Measured Impact / Examples |
|---|---|---|
| Legal & Judicial | Exclusion of Evidence | Evidence deemed inadmissible under legal standards (e.g., Daubert, Frye) due to reliability concerns [7]. |
| Miscarriages of Justice | Wrongful convictions or acquittals based on flawed or unvalidated forensic evidence [7]. | |
| Due Process Violations | Withholding underlying scientific data from the defense violates constitutional rights to a fair trial [49]. | |
| Operational & Analytical | Erroneous Data Interpretation | Case example: Software reported 84 searches for "chloroform"; validation proved only a single instance [7]. |
| Undetected Method Flaws | Unvalidated methods may have unknown error rates and unrecognized limitations [14]. | |
| Resource Inefficiency | Operational errors and rework required when decisions are based on flawed evidence [7]. | |
| Reputational & Financial | Loss of Credibility | Diminished trust in the forensic expert, laboratory, or entire discipline [7]. |
| Civil Liability | Exposure to financial damages in commercial disputes, insurance claims, or workplace investigations [7]. | |
| Increased Costs | Costs associated with re-investigation, legal defense, and reputational repair [7] [50]. |
Experimental Protocols for Validation
Core Validation Workflow for Forensic Methods
Adhering to established validation protocols is the primary mechanism for mitigating the risks detailed in Table 1. The following workflow, mandated by quality standards such as ISO/IEC 17025, provides a structured framework [13].
Figure 1: The standard methodology validation process for forensic sciences, illustrating the sequential stages required to establish that a method is fit for purpose [13].
Protocol: Digital Forensic Tool Validation
This protocol provides a detailed methodology for validating digital forensic tools (e.g., Cellebrite, Magnet AXIOM), a critical requirement given their rapid update cycles and the volatile nature of digital evidence [7].
- Objective: To verify that a digital forensic tool extracts, processes, and reports data accurately and completely without altering the original source.
- Primary Risk Mitigated: Legal exclusion of evidence and erroneous data interpretation.
Step-by-Step Procedure:
- Define Requirements & Acceptance Criteria: Specify the tool's intended purpose (e.g., "extract and parse chat messages from Android version X"). Define quantitative acceptance criteria, such as 98% accuracy in data parsing and zero alteration of source file hash values [13].
- Prepare Test Dataset: Create or obtain a reference dataset that is representative of real-case evidence. This dataset must include known data objects and ground truth to facilitate accuracy measurement [7] [13].
- Acquire and Hash Evidence: Using a write-blocker, create a forensic image (bit-by-bit copy) of the test dataset. Calculate and record the cryptographic hash (e.g., SHA-256) of the original source and the image to verify data integrity [7].
- Process Data with Tool: Run the tool according to the standard operating procedure to extract and analyze data from the forensic image.
- Verify Output Accuracy: Compare the tool's output against the known ground truth in the test dataset. Record any omissions, inaccuracies, or artifacts introduced by the tool.
- Cross-Validate with Alternative Tools: Process the same dataset using a different tool or method to identify any inconsistencies in output, which may indicate tool-specific errors [7].
- Document and Report: Record all steps, parameters, logs, and results. The final validation report must state whether the tool met the acceptance criteria and clearly outline any discovered limitations [13].
Protocol: Empirical Validation of Feature-Comparison Methods
This protocol addresses the validation of subjective, pattern-matching disciplines (e.g., firearms, fingerprints), which have faced significant scrutiny regarding their scientific validity [49] [14].
- Objective: To empirically establish the accuracy, reproducibility, and error rates of a forensic feature-comparison method.
- Primary Risk Mitigated: Miscarriages of justice due to unsupported individualization claims.
Step-by-Step Procedure:
- Guidelines-Based Study Design: Structure the validation study around four key scientific guidelines [14]:
- Plausibility: Is the method based on a sound, testable theory?
- Sound Research Design: Does the study design have construct and external validity?
- Intersubjective Testability: Can the results be replicated by other examiners?
- Group-to-Individual Inference: Is there a valid methodology to reason from population-level data to specific case conclusions?
- Create Blind Trial Sets: Develop a set of evidence samples (e.g., bullet casings, fingerprints) with a known ground truth. The set must include matching and non-matching pairs and should represent a range of difficulties.
- Execute Multi-Examiner Testing: Multiple trained examiners independently analyze the trial sets under blinded conditions to prevent confirmation bias.
- Quantify Performance Metrics: Calculate the method's false positive rate (incorrectly declaring a match), false negative rate (failing to declare a true match), and overall accuracy [14].
- Analyze for Bias: Introduce contextual, potentially biasing information to a subset of trials to measure its effect on examiner decision-making.
- Peer Review and Data Sharing: Submit the study design, results, and raw data for peer review. To satisfy due process requirements, the underlying data must be made available for independent audit and verification [49].
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Materials and Tools for Forensic Validation Research
| Tool / Material | Function in Validation |
|---|---|
| Reference Data Sets | Provides the known "ground truth" against which tool output and examiner conclusions are compared to measure accuracy [7] [13]. |
| Cryptographic Hashing Tools | Generates unique digital fingerprints (e.g., SHA-256) for data to unequivocally demonstrate integrity throughout the validation process [7]. |
| Forensic Write Blockers | Hardware or software that prevents any alteration of original evidence media during the imaging and analysis phases of tool validation [7]. |
| Open-Source Analysis Tools | Used as independent methods for cross-validating the results produced by proprietary commercial forensic tools [7]. |
| Stable Isotope & Trace Element Libraries | In product origin verification, these chemical profiles form the scientific baseline for validating claims about a product's geographic provenance [51]. |
| Blinded Trial Sets | Essential for empirically testing human-examiner-based methods, as they prevent confirmation bias and allow for true measurement of error rates [14]. |
| Data Sharing Repositories | Platforms for sharing analyzable datasets to enable independent verification of validation studies, fulfilling ethical and due process obligations [49]. |
Integrated Risk Assessment Diagram
A comprehensive risk assessment framework for forensic validation must account for the interconnectedness of scientific, legal, and operational factors. The following diagram maps these relationships and key control points.
Figure 2: A risk assessment framework for forensic method validation, illustrating primary consequences of inadequate validation and the key controls required to mitigate them.
The Role of Continuous Monitoring and Re-validation in a Dynamic Environment
In forensic method validation research, the traditional paradigm of one-time validation is insufficient for maintaining the integrity and reliability of analytical techniques over time. Dynamic environments, characterized by evolving sample types, emerging instrumental techniques, and changing regulatory requirements, demand a proactive framework centered on continuous monitoring and periodic re-validation. This approach ensures that forensic methods remain scientifically sound, legally defensible, and fit-for-purpose throughout their lifecycle, thereby directly supporting the accuracy and reliability of conclusions presented in legal contexts.
Integrating continuous monitoring into a forensic risk assessment framework transforms validation from a static event into a dynamic, data-driven process. It enables researchers and drug development professionals to detect subtle performance drifts, identify new risks, and make timely, evidence-based decisions about re-validation. This document outlines application notes and experimental protocols for implementing such a system, ensuring forensic methods withstand scrutiny in an ever-changing scientific and regulatory landscape.
Core Principles and Regulatory Context
Foundations in Forensic Science and Data Quality
The principles of continuous monitoring are deeply aligned with the forensic-data-science paradigm, which emphasizes transparent, reproducible, and empirically calibrated methods [21]. This paradigm requires that methods are intrinsically resistant to cognitive bias and use a logically correct framework for evidence interpretation.
A robust continuous monitoring system for forensic methods should operate along three key dimensions, as exemplified by advanced data feed monitoring systems [52]:
- Aggregation at multiple time intervals to detect performance changes at varying levels of sensitivity.
- Utilization of multiple data history lengths to balance model adaptability with stability.
- Incorporation of monitoring delays to account for lagged data arrival, ensuring comprehensive assessment.
Quality Standards and Lifecycle Approach
The ISO 21043 international standard for forensic science provides requirements and recommendations designed to ensure the quality of the entire forensic process, including analysis, interpretation, and reporting [21]. While not explicitly mentioned in the search results, standards such as ISO/IEC 17025 further reinforce the need for ongoing verification of method performance.
A lifecycle approach to validation, similar to that required in pharmaceutical cleaning validation [53], is equally applicable to forensic methods. This approach mandates:
- Initial validation to establish baseline performance characteristics.
- Continuous monitoring through scheduled reviews and real-time performance tracking.
- Trigger-based re-validation in response to predefined events or performance thresholds.
Quantitative Framework for Performance Assessment
A quantitative, data-driven approach forms the foundation for effective continuous monitoring. The table below summarizes key performance metrics and their application in forensic method monitoring.
Table 1: Key Quantitative Metrics for Continuous Monitoring of Forensic Methods
| Metric Category | Specific Metric | Application in Forensic Method Monitoring | Interpretation Guidelines |
|---|---|---|---|
| Discrimination | Area Under Curve (AUC) | Assesses method's ability to distinguish between true positives and false positives [54]. | AUC >0.7 indicates acceptable discrimination; >0.8 indicates excellent discrimination [54]. |
| Sensitivity/Recall | Measures proportion of true positives correctly identified. | High sensitivity critical for methods where false negatives have serious consequences. | |
| Specificity | Measures proportion of true negatives correctly identified. | High specificity needed when false positives could lead to incorrect legal conclusions. | |
| Calibration | Probability of Default (PD) Models | Statistical models estimating likelihood of method failure or significant deviation [55]. | Used in credit risk, adaptable for forensic method failure prediction. |
| Expected Shortfall (ES) | Measures average performance loss in worst-case scenarios beyond thresholds [55]. | Quantifies risk in extreme deviation events. | |
| Financial Impact | Single Loss Expectancy (SLE) | Monetary impact of a single method failure event [56]. | Helps justify investments in monitoring and re-validation. |
| Annual Loss Expectancy (ALE) | Expected monetary loss from method failures annually (ALE = SLE × ARO) [56]. | Guides resource allocation for method maintenance. |
Statistical Process Control for Forensic Methods
Statistical process control (SPC) techniques provide powerful tools for monitoring method stability over time. The following protocol outlines implementation:
Protocol 1: Establishing Control Charts for Quantitative Forensic Methods
Purpose: To detect deviations from established performance baselines through continuous statistical monitoring.
Materials:
- Quality control (QC) samples with known characterization
- Data management system for trend analysis
- Statistical software capable of control chart generation
Procedure:
- Baseline Establishment: Following initial method validation, analyze a minimum of 20 independent QC sample results over time to establish baseline performance metrics (mean, standard deviation) for key parameters (accuracy, precision, sensitivity).
- Control Limits Calculation: Calculate statistical control limits:
- Upper Control Limit (UCL) = Mean + 3σ
- Lower Control Limit (LCL) = Mean - 3σ
- Warning limits may be established at Mean ± 2σ
- Continuous Monitoring: With each subsequent analysis of QC materials, plot results on control charts and investigate any points exceeding control limits or showing non-random patterns (e.g., 7 consecutive points on one side of the mean).
- Response Protocol: Define and document specific actions for out-of-control conditions, including instrument maintenance, reagent replacement, or initiation of re-validation.
Continuous Monitoring System Implementation
System Architecture and Workflow
A continuous monitoring system for forensic methods requires a structured architecture that integrates data collection, analysis, and response mechanisms. The following diagram illustrates the core workflow:
Diagram 1: Continuous monitoring and re-validation workflow for forensic methods. The process integrates automated data collection with statistical analysis to trigger evidence-based re-validation decisions.
Monitoring Protocol for Dynamic Environments
Protocol 2: Implementing Multi-Scale Monitoring for Forensic Methods
Purpose: To continuously monitor method performance across multiple temporal scales and aggregation intervals, enabling detection of both gradual drifts and abrupt changes.
Materials:
- Feed inspection tool or laboratory information management system (LIMS) with monitoring capabilities
- Data visualization platform
- Automated alert system (email, SMS, or dashboard)
Procedure:
- Define Monitoring Parameters: Identify critical method performance indicators (e.g., retention time stability, peak area precision, calibration curve fit, reference material recovery).
- Establish Aggregation Intervals: Configure monitoring at multiple time scales:
- Short-term (e.g., within-batch, daily) for immediate issue detection
- Medium-term (e.g., weekly, monthly) for trend identification
- Long-term (e.g., quarterly, annually) for lifecycle assessment
- Configure Baseline Models: Develop statistical models using historical data with sliding windows of different lengths [52]:
- 30-day window for rapid adaptation to changes
- 90-day window for stable baseline establishment
- 365-day window for long-term performance assessment
- Set Alert Thresholds: Define data-driven thresholds for automated alerts:
- Standard deviation-based limits for quantitative parameters
- Trend analysis for directional changes
- Tolerance limits for categorical parameters
- Implement Monitoring Dashboard: Create visualization tools showing current performance against historical baselines with clear indication of alert status.
- Document Response Procedures: Establish standardized operating procedures for investigating and addressing alerts, including escalation pathways.
Re-validation Triggers and Protocols
Re-validation Decision Framework
Re-validation should be a risk-based decision informed by continuous monitoring data. The following table outlines common triggers and appropriate responses.
Table 2: Re-validation Triggers and Response Protocols for Forensic Methods
| Trigger Category | Specific Triggers | Risk Assessment | Recommended Response |
|---|---|---|---|
| Method Performance | Control chart violations (e.g., points outside 3σ limits) [53] | High - indicates potential loss of statistical control | Immediate investigation; limited re-validation of affected parameters |
| Trends in proficiency testing results | Medium-High - suggests systematic performance change | Root cause analysis; re-validation of accuracy and precision | |
| Environmental Changes | New instrumentation or major hardware upgrades | High - may affect all method parameters | Full re-validation including instrument detection limits |
| Changes in critical reagents or reference materials | Medium - potential for selective effect | Limited re-validation assessing specificity and accuracy | |
| Regulatory & Contextual | New scientific standards (e.g., ISO 21043 updates) [21] | Medium - necessary for compliance | Gap analysis; targeted re-validation to address new requirements |
| New sample matrices or expanded scope | High - unverified application | Extended re-validation for specificity, robustness, and recovery | |
| Statistical Indicators | Predictive model signals performance degradation | Medium - early warning of potential issues | Enhanced monitoring frequency; preemptive parameter verification |
Risk-Based Re-validation Protocol
Protocol 3: Conducting Trigger-Based Method Re-validation
Purpose: To execute a targeted, efficient re-validation process when triggered by continuous monitoring data or significant changes in method conditions.
Materials:
- Original validation protocol and report
- Quality control materials covering expected measurement range
- Documented evidence of triggering event
- Statistical analysis software
Procedure:
- Trigger Documentation: Document the specific trigger for re-validation with supporting data from continuous monitoring system.
- Risk Assessment: Conduct focused risk assessment to determine re-validation scope:
- Identify critical method parameters potentially affected by the change
- Prioritize parameters based on impact on method reliability and legal defensibility
- Define acceptance criteria for each parameter based on original validation and current requirements
- Experimental Design: Design efficient experiments to verify only affected parameters:
- For instrumental changes: focus on detection capabilities, precision, and calibration
- For reagent changes: emphasize specificity, selectivity, and accuracy
- For matrix changes: validate selectivity, recovery, and robustness
- Execution and Analysis:
- Conduct experiments according to approved protocol
- Compare results with original validation data and acceptance criteria
- Apply statistical tests to determine significance of any observed differences
- Decision Point:
- If all acceptance criteria are met: document re-validation and continue monitoring
- If criteria not met: implement corrective actions and repeat re-validation, or consider method replacement
- Reporting: Prepare comprehensive re-validation report including:
- Reason for re-validation
- Experimental data and statistical analysis
- Comparison with original validation
- Conclusion regarding method suitability for continued use
The Scientist's Toolkit: Essential Research Reagents and Materials
Table 3: Essential Research Reagent Solutions for Forensic Method Validation and Monitoring
| Reagent/Material | Function in Validation/Monitoring | Quality Requirements | Application Notes |
|---|---|---|---|
| Certified Reference Materials | Provide traceable accuracy assessment for quantitative methods | Certification with stated uncertainty and traceability to SI units | Use materials with matrix matching real samples when possible; verify stability throughout use period |
| Quality Control Materials | Monitor method precision and stability over time | Well-characterized, homogeneous, stable | Establish multiple concentration levels covering method range; monitor for stability degradation |
| Internal Standards | Correct for analytical variability in sample preparation and analysis | High purity, chemically similar to analytes, non-interfering | Verify selectivity and absence of cross-talk with target analytes during method changes |
| System Suitability Test Mixtures | Verify instrumental performance before sample analysis | Contains key analytes at critical concentrations | Establish failure thresholds based on validation data; trend results for early problem detection |
| Sample Matrices | Assess specificity, selectivity, and matrix effects | Representative of casework samples, properly characterized | Include in re-validation when encountering new matrix types; store appropriately to maintain integrity |
Data Integration and Reporting
Visualization for Performance Tracking
Effective continuous monitoring requires intuitive visualization of complex performance data. The following diagram illustrates a recommended dashboard architecture:
Diagram 2: Comprehensive dashboard architecture for forensic method monitoring, integrating data sources with performance tracking and alert systems to support re-validation decisions.
Reporting for Regulatory Compliance and Scientific Defense
Documentation of continuous monitoring and re-validation activities must support both regulatory compliance and potential legal defense of method reliability. Key reporting elements include:
- Continuous Monitoring Reports: Periodic summaries of performance metrics, alert investigations, and corrective actions.
- Re-validation Justification: Clear documentation of triggers, risk assessments, and experimental designs.
- Statistical Evidence: Comprehensive data analysis supporting continued method suitability.
- Decision Trail: Transparent record of all decisions regarding method maintenance and modification.
Implementation of this integrated continuous monitoring and re-validation framework ensures forensic methods maintain their scientific integrity and legal defensibility in dynamic operational environments, ultimately supporting the reliability of conclusions presented in legal proceedings.
The evolution of forensic science demands a shift from reactive to proactive risk control. Traditional validation approaches, which often identify issues only after implementation, are insufficient for modern forensic methodologies involving complex data analytics and automated systems. A proactive framework, integrated directly into the development and validation lifecycle, is essential for identifying and mitigating risks before they compromise scientific integrity or legal admissibility. This approach is particularly critical given the unique challenges in digital forensics, where the volatile nature of evidence and rapid technological evolution introduce significant risks that must be systematically managed [7]. The core of this proactive paradigm is the integration of continuous risk assessment with automated validation protocols, ensuring that forensic methods remain reliable, defensible, and effective against emerging threats.
Foundational Principles of a Risk Assessment Framework for Forensic Validation
A robust risk assessment framework for forensic validation is built upon principles adapted from both quality management and digital forensics. These principles ensure that the framework is both scientifically sound and legally defensible.
- Reproducibility and Transparency: Results must be repeatable by other qualified professionals using the same method, with all procedures, software versions, logs, and chain-of-custody records thoroughly documented [7].
- Error Rate Awareness and Continuous Validation: Forensic methods should have known error rates that can be disclosed in reports and during testimony. Because technology evolves rapidly, tools and methods must be frequently revalidated to maintain confidence in their outputs [7].
- Security-First Culture and Accountability: A leadership-driven, security-first approach to risk management ensures that activities like security risk assessments become a part of the regular operating landscape. This helps build a culture of accountability, which is critical for program success [57].
- Standardization and Feasibility: The success of a risk assessment and remediation program is dependent on giving your team a simplified and repeatable process that minimizes confusion and overhead. Standardization optimizes cybersecurity risk management and delivers greater insight into previously unseen vulnerabilities [57].
Implementing a Proactive Risk Control System: Protocols and Application Notes
This section provides detailed, actionable protocols for integrating data analytics and automation into a forensic validation workflow to achieve proactive risk control.
Protocol 1: Automated Validation of Forensic Software Tools
Objective: To ensure that forensic software tools and algorithms yield accurate, reliable, and repeatable results through an automated validation pipeline.
Background: Digital forensic tools are frequently updated, and without proper validation, they may introduce errors or omit critical data. For instance, two tools extracting data from the same mobile phone may yield different results based on their parsing capabilities [7].
Materials:
- Forensic software tool to be validated (e.g., Cellebrite Inseyets, Magnet AXIOM, MSAB XRY).
- Known test datasets with pre-verified data artifacts.
- Automated validation server or workflow orchestration platform (e.g., Camunda [58]).
- Hashing utility (e.g., for SHA-256/512).
Procedure:
- Baseline Establishment: Generate cryptographic hash values (e.g., SHA-256) for all known test datasets to confirm data integrity before and after imaging [7].
- Tool Execution: Process the known test datasets through the forensic tool(s) under validation. This should be integrated into an automated workflow, as exemplified by the Fast DNA IDentification Line (FIDL) which automates the process from raw data to report [58].
- Output Analysis: Automatically compare the tool's output against the expected results from the known dataset. Key comparison metrics should include:
- Data completeness (e.g., percentage of expected artifacts recovered).
- Data accuracy (e.g., fidelity of extracted metadata and content).
- Processing consistency across multiple runs.
- Cross-Validation: Where feasible, cross-validate results using multiple tools or methods to identify inconsistencies that may indicate a software error or bias [7].
- Reporting: Automatically generate a validation report detailing the tool's performance against each metric, any deviations from expected results, and a final validation status.
Application Note 1.1: This protocol should be executed not only for new tool acquisitions but also after every major software update. Automation is key to feasibility, allowing for frequent revalidation without imposing a significant manual burden on forensic personnel.
Protocol 2: Data Integrity and Anomaly Monitoring in Automated Forensic Workflows
Objective: To proactively monitor automated forensic analysis pipelines for data integrity breaches and anomalous results that may indicate underlying system or method failure.
Background: The "black box" nature of some advanced algorithms, including those used in AI-assisted forensics, can produce unexplained or inconsistent results. Continuous monitoring is essential for identifying these failures [7].
Materials:
- Live forensic analysis pipeline (e.g., automated DNA profile analysis, digital evidence processor).
- Log aggregation and analysis system (e.g., ELK Stack).
- Statistical process control (SPC) software.
Procedure:
- Data Lineage Tracking: Implement automated tracking of data lineage throughout the entire workflow, from evidence intake to final report. This should include logging all data transformations and analyses performed.
- Real-time Hash Verification: In workflows involving evidence imaging or data transfer, implement real-time hash verification to immediately flag integrity violations.
- Anomaly Detection: Apply statistical process control and machine learning models to the outputs of the forensic pipeline. For example, in a DNA profiling workflow, monitor the rate of allele drop-out/in or profile mixture ratios. A significant deviation from established baselines should trigger an alert for manual review [58].
- Bias Detection: Implement peer-validated methods, such as those formalized by Pagano et al., to formalize bias-mitigation frameworks for forensic AI. Techniques like SHAP analysis can be used to interpret model outputs and identify potential sources of bias [59].
Application Note 2.1: The thresholds for anomaly alerts must be calibrated based on historical data to avoid alert fatigue. This protocol turns the automated forensic system into a self-monitoring entity, capable of flagging its own potential errors.
Workflow Visualization: Proactive Risk Control in Forensic Validation
The following diagram illustrates the integrated, cyclical workflow for proactive risk control, combining automated forensic analysis with continuous risk assessment.
Figure 1. Integrated workflow for proactive risk control in forensic analysis.
Quantitative Framework: Key Risk Indicators (KRIs) for Forensic Validation
A proactive risk framework requires quantitative metrics for monitoring. The following table summarizes potential Key Risk Indicators (KRIs) derived from automated validation and monitoring protocols.
Table 1: Key Risk Indicators (KRIs) for Forensic Method Validation
| Risk Category | Key Risk Indicator (KRI) | Measurement Method | Threshold (Example) |
|---|---|---|---|
| Data Integrity | Evidence Hash Mismatch Rate | Percentage of cases with pre-/post-processing hash conflicts. | 0% [7] |
| Tool Accuracy | False Positive/Negative Rate in Test Datasets | Rate of missed/incorrectly identified artifacts vs. known baseline. | < 1% (lab-defined) |
| Process Stability | Analytical Output Drift (e.g., allele peak height, data parsing consistency) | Statistical Process Control (SPC) charts on quantitative outputs. | > 3σ from mean [58] |
| Method Bias | Disparate Impact on Different Data Types/Subsets | SHAP analysis or adversarial validation to measure fairness [59]. | < 10% variance |
| Operational Risk | Automated Pipeline Failure Rate | Percentage of analytical runs requiring manual intervention. | < 5% |
The Scientist's Toolkit: Essential Research Reagent Solutions
Successful implementation of a proactive risk control system relies on a suite of essential software and methodological "reagents."
Table 2: Essential Research Reagent Solutions for Automated Risk Control
| Item | Function in Proactive Risk Control | Example Tools / Methods |
|---|---|---|
| Workflow Orchestration Engine | Automates and sequences complex validation and analysis tasks, ensuring procedures are performed in a particular order and decisions are made based on outcomes. | Camunda, Apache Airflow [58] |
| Cryptographic Hashing Utility | Provides a digital fingerprint for data, used to verify evidence integrity before and after analysis, a fundamental practice in digital forensics. | SHA-256, SHA-512 utilities [7] |
| Statistical Process Control (SPC) Software | Monists the stability and consistency of analytical processes over time, enabling the detection of significant deviations or "drift" that indicates emerging risk. | Python (SciPy, NumPy), R Statistical Language |
| Bias Detection & Mitigation Framework | Formalizes the identification and mitigation of unfairness or bias in automated algorithms and AI models used in forensic analysis. | SHAP analysis, Adversarial Validation frameworks [59] |
| Known/Reference Datasets | Curated datasets with pre-verified attributes serve as the ground truth for validating tool accuracy, measuring error rates, and testing method changes. | Laboratory-generated mixtures, NIST standard reference data [58] |
The integration of data analytics and automation into a structured risk assessment framework transforms forensic method validation from a static, post-development checkpoint into a dynamic, proactive control system. By implementing automated validation protocols, continuous integrity monitoring, and a quantitative KRI framework, forensic laboratories can significantly enhance the reliability, defensibility, and scientific rigor of their methodologies. This proactive approach is not merely a technical improvement but an ethical and professional commitment to upholding the highest standards of justice in an increasingly complex digital world [7].
The reliability of forensic science is a cornerstone of a just legal system. Method validation provides the foundational data that demonstrates a technique is fit for its purpose, ensuring that results are accurate, reproducible, and scientifically defensible. This article analyzes the critical role of a proactive risk assessment framework in forensic method validation. By examining both a success story in rapid drug screening and a failure in cannabis DUI testing, we will extract key lessons on identifying, evaluating, and mitigating risks in forensic research and practice. Implementing structured risk assessments is not merely a regulatory checkbox; it is an essential safeguard for scientific integrity and public trust.
Case Study 1: Success Through Systematic Optimization
Optimized Rapid GC-MS Method for Seized Drugs
A study published in Frontiers in Chemistry (June 2025) exemplifies a rigorous approach to method development and validation. Researchers developed a rapid Gas Chromatography-Mass Spectrometry (GC-MS) method that significantly reduced analysis time for seized drugs from 30 minutes to just 10 minutes, while simultaneously improving key performance metrics [3]. This work provides a template for successful forensic method validation.
Experimental Protocol: Rapid GC-MS Analysis [3]
- Instrumentation: Agilent 7890B GC system coupled with an Agilent 5977A single quadrupole mass spectrometer.
- Column: Agilent J&W DB-5 ms (30 m × 0.25 mm × 0.25 μm).
- Carrier Gas: Helium, at a fixed flow rate of 2 mL/min.
- Injection: 1 μL, with a 10:1 split ratio.
- Temperature Program:
- Initial temperature: 80°C (hold 0.5 min)
- Ramp 1: 80°C to 280°C at a rate of 40°C/min
- Ramp 2: 280°C to 300°C at a rate of 60°C/min (hold 1.5 min)
- Total Run Time: 10 minutes.
- Mass Spectrometer: Transfer line temperature: 280°C, Ion source temperature: 230°C.
- Sample Preparation (Liquid-Liquid Extraction):
- Solid Samples: Approximately 0.1 g of powdered material was sonicated for 5 minutes in 1 mL of methanol, then centrifuged. The supernatant was analyzed.
- Trace Samples: Residues from items like digital scales or syringes were collected with methanol-moistened swabs. The swab tips were vortexed in 1 mL of methanol, and the extract was analyzed.
Quantitative Validation Data
The method's performance was systematically validated, yielding the following quantitative results, which showcase its significant improvements over conventional techniques [3].
Table 1: Validation Data for the Rapid GC-MS Method [3]
| Validation Parameter | Substance(s) | Performance Outcome | Significance vs. Conventional Method |
|---|---|---|---|
| Analysis Time | All analytes | 10 minutes | Reduced from 30 minutes (66% reduction) |
| Limit of Detection (LOD) | Cocaine | 1 μg/mL | Improved from 2.5 μg/mL (60% improvement) |
| Limit of Detection (LOD) | Heroin | Improved by ≥50% | Demonstrated enhanced sensitivity |
| Repeatability/Reproducibility | Stable compounds | Relative Standard Deviation (RSD) < 0.25% | Excellent precision and reliability |
| Identification Accuracy | Diverse drug classes | Match quality scores > 90% | High confidence in compound identification |
Experimental Workflow
The following workflow diagrams the optimized GC-MS protocol and its subsequent validation process.
Case Study 2: Failure Due to Systemic Risks
The UIC Forensic Lab Scandal
An investigation by Injustice Watch (2025) revealed a systemic failure at a forensic toxicology lab at the University of Illinois Chicago (UIC). Between 2016 and 2024, the lab conducted THC blood and urine tests for DUI-cannabis investigations using scientifically discredited methods and faulty machinery, leading to wrongful convictions [60].
Key Failures in Method Validation and Practice [60]:
- Use of Inappropriate Matrices: The lab routinely tested urine for DUI-cannabis investigations, despite the scientific consensus that THC metabolites in urine cannot determine recent use or current impairment.
- Failure to Differentiate Compounds: Internal records indicated the lab was unable to reliably differentiate between legal and illegal types of THC in bodily fluids.
- Known Instrument Problems: Lab management was aware that its machines were not producing reliable results for THC blood tests for years but failed to notify law enforcement or rectify the issues.
- Misleading Testimony: The senior forensic toxicologist provided testimony that conflated THC metabolites with active THC, misrepresenting the scientific evidence to courts.
- Lack of Transparency and Oversight: The lab was shut down only after an accreditor's audit uncovered operational problems, and there was no meaningful state-level forensic science oversight to intervene sooner.
Risk Pathway to Forensic Failure
The UIC case demonstrates a cascade of failures. The diagram below maps the pathway from underlying risks to the final consequences.
A Risk Assessment Framework for Forensic Validation
The contrasting cases highlight the necessity of a formalized risk assessment methodology. This framework should be integrated into every stage of method development, validation, and implementation.
Core Risk Assessment Methodologies
Several established methodologies can be adapted for forensic science contexts. The choice depends on the organization's maturity, data availability, and specific needs [61] [62].
Table 2: Risk Assessment Methodologies for Forensic Science [61] [62]
| Methodology | Description | Best For Forensic Context | Key Trade-offs |
|---|---|---|---|
| Qualitative | Uses scales (e.g., High/Medium/Low) for likelihood and impact based on expert judgment. | Early-stage method development, cross-functional reviews, labs without extensive historical data. | Fast and easy but subjective; can make prioritization difficult. |
| Semi-Quantitative | Blends qualitative judgment with numerical scoring (e.g., 1-5 scales for impact/likelihood). | Most forensic labs; provides more structure than qualitative alone without needing complex data. | Balances speed and structure, but scoring can create a false sense of precision. |
| Quantitative | Uses numerical data and models (e.g., Monte Carlo) to estimate risk in financial or statistical terms. | Justifying budget for new equipment, complex scenarios requiring precise cost-benefit analysis. | Highly objective and defensible, but data-intensive and complex to implement. |
| Threat-Based | Starts with identifying potential threats (e.g., analyst error, instrument drift, testimony misuse) and their pathways. | Mature labs focused on proactive defense, addressing specific failure modes like those in the UIC case. | Realistic and thorough, but requires good threat intelligence and is time-consuming. |
The Risk Assessment Process
A structured process ensures consistency and comprehensiveness. The following workflow, adapted from general risk management practice, is directly applicable to forensic method validation [62].
Applied Risk Mitigation Strategies
Using the framework above, specific risks can be identified and mitigated.
Table 3: Applied Forensic Risk Mitigation Strategies
| Identified Risk | Risk Category | Mitigation Strategy | Case Example Reference |
|---|---|---|---|
| Inappropriate sample matrix | Technical/Validation | Validate methods only for matrices with scientific consensus (e.g., blood for DUI, not urine). Adhere to SWGDRUG guidelines. | UIC Lab Failure [60] |
| Poor method sensitivity/LOD | Technical/Validation | Systematic optimization and validation, as demonstrated by the rapid GC-MS study. Use reference standards. | Rapid GC-MS Success [3] |
| Instrument failure/calibration drift | Operational/Technical | Rigorous calibration schedules, quality control samples, and preventive maintenance. | Implied in both cases |
| Misleading or inaccurate testimony | Human Factor/Operational | Robust training on ethics and testimony, peer review of reports, clear communication of limitations. | UIC Lab Failure [60] |
| Lack of oversight and accountability | Organizational/Governance | Independent audits, strong quality assurance programs, and a culture that prioritizes science over revenue. | UIC Lab Failure [60] |
The Scientist's Toolkit: Research Reagent Solutions
The following table details key materials and reagents essential for the development and validation of robust forensic methods, as exemplified by the rapid GC-MS case study [3].
Table 4: Essential Research Reagents for Forensic GC-MS Analysis [3]
| Reagent/Material | Function in Protocol | Specific Example |
|---|---|---|
| Certified Reference Standards | Serves as the benchmark for qualitative identification and quantitative calibration of target analytes. | Cocaine, Heroin, MDMA, THC (from Sigma-Aldrich/Cerilliant) [3]. |
| Internal Standards | Corrects for analytical variability during sample preparation and injection, improving accuracy and precision. | Deuterated analogs of target drugs (e.g., Cocaine-D3, THC-D3). |
| Chromatographic Solvents | Acts as the extraction medium and sample diluent; purity is critical to minimize background interference. | High-purity Methanol (99.9%) [3]. |
| GC-MS Capillary Column | The physical medium where chemical separation occurs; its properties dictate resolution and analysis time. | Agilent J&W DB-5 ms (30 m × 0.25 mm × 0.25 μm) [3]. |
| Carrier Gas | The mobile phase that transports vaporized samples through the GC column. | Ultra-high-purity (UHP) Helium (99.999%) [3]. |
| Quality Control (QC) Materials | Used to verify method performance and instrument stability during a sequence of analyses. | Calibration verifiers, positive and negative controls. |
Ensuring Scientific Rigor: From Benchmarking to Emerging Technologies
Within a risk assessment framework for forensic method validation research, establishing rigorous, method-specific benchmarks for accuracy, precision, and specificity is paramount. These parameters form the foundational triad for ensuring that analytical methods—whether for seized drug analysis, toxicology, or digital evidence—produce reliable, defensible, and reproducible data. The goal of validation is to provide documented evidence that a method is fit for its intended purpose, thereby mitigating the risk of erroneous conclusions that could impact legal outcomes, public safety, and scientific integrity [63] [7]. This document outlines detailed application notes and experimental protocols for quantifying these critical parameters, providing a standardized approach for researchers and forensic scientists.
Defining Core Validation Parameters
Accuracy
Accuracy is defined as the closeness of agreement between a measured value and an accepted reference or true value [63]. It is a measure of exactness and is typically expressed as the percentage of analyte recovered by the assay. In a risk-based context, accuracy directly influences the risk of false positive or false negative quantification, which is critical in determining compliance with legal thresholds.
Precision
Precision refers to the closeness of agreement between a series of measurements obtained from multiple sampling of the same homogeneous sample under prescribed conditions [63]. It is a measure of method reproducibility and is characterized at three levels:
- Repeatability (intra-assay precision): Results under the same operating conditions over a short interval.
- Intermediate Precision: Results within-laboratory variations (e.g., different days, analysts, equipment).
- Reproducibility: Results between different laboratories. Precision is usually expressed as the relative standard deviation (%RSD) of a set of measurements, with a common acceptance criterion being %RSD ≤ 10% for forensic applications [64].
Specificity
Specificity is the ability of the method to measure the analyte accurately and specifically in the presence of other components that may be expected to be present in the sample matrix, such as impurities, degradation products, or co-formulants [63]. A specific method ensures that a peak's response is due to a single component, thereby mitigating the risk of misidentification.
Quantitative Benchmark Tables
The following tables summarize typical acceptance criteria for accuracy, precision, and specificity across different forensic applications, derived from recent literature and international guidelines.
Table 1: Benchmark Acceptance Criteria for Quantitative Analysis
| Parameter | Recommended Benchmark | Forensic Application Example |
|---|---|---|
| Accuracy | Mean recovery of 90–110% for drug substances [65]; Documented via ≥9 determinations across 3 concentration levels [63]. | HS/GC-FID for ethanol in vitreous humor [66]. |
| Precision | Repeatability: %RSD ≤ 10% [64]; Intermediate Precision: %RSD ≤ 10% and statistical equivalence between analysts [63]. | Rapid GC-MS for seized drugs; RSD < 0.25% for retention times of stable compounds [3]. |
| Specificity | Resolution (Rs) > 1.5 between critical pairs; Peak purity confirmed via PDA or MS detection [63]. | Differentiation of drug isomers in seized samples using GC-MS [64]. |
Table 2: Method Performance Data from Recent Forensic Studies
| Analytical Method | Target Analyte | Accuracy (Mean Recovery) | Precision (%RSD) | Specificity Demonstration |
|---|---|---|---|---|
| HS/GC-FID [66] | Ethanol in Vitreous Humor | Established per EMA guidelines | Established per EMA guidelines | No interference from matrix |
| Rapid GC-MS [3] | Seized Drugs (e.g., Cocaine) | Not explicitly stated | RSD < 0.25% (retention time) | Match quality scores > 90% |
| GC-TCD with Na₂S₂O₄ [67] | Carbon Monoxide in Spleen | Improved vs. control | Good repeatability | Mitigation of MetHb interference |
Experimental Protocols
Protocol for Determining Accuracy
This protocol is designed for the accuracy assessment of an analyte in a drug substance.
1. Scope: Determination of accuracy for an Isomer I (specification: NMT 1.0%) in Drug Substance D.
2. Experimental Procedure:
- Prepare a stock solution of the analyte (Isomer I) and the drug substance.
- Prepare accuracy samples at 50%, 75%, 100%, 125%, and 150% of the specification level (e.g., for a 1.0 mg/mL sample, 50% = 5 mcg/mL, 100% = 10 mcg/mL, 150% = 15 mcg/mL) [65].
- Inject the 50%, 100%, and 150% solutions in triplicate, and the 75% and 125% solutions in singlicate.
- Generate the chromatogram and record the area response for each injection.
3. Data Analysis:
- Plot a linearity graph with concentration on the X-axis and the corresponding area response on the Y-axis.
- Using statistical software, calculate the slope (m), y-intercept (c), and coefficient of determination (R²) from the linear regression.
- For each measured area response (y), back-calculate the concentration (x) using the formula: ( x = \frac{(y - c)}{m} ) [65].
- Calculate the percent accuracy for each prepared concentration using the formula: ( \text{Accuracy} = \frac{\text{Calculated Concentration}}{\text{True Concentration}} \times 100 )
- Report the average accuracy at each level. The method is typically considered acceptable if the average deviation from 100% is within ±2% [65].
Protocol for Determining Precision (Repeatability)
1. Scope: Determination of repeatability for a seized drug method using rapid GC-MS.
2. Experimental Procedure:
- Prepare a homogeneous reference material or a fortified sample at the target concentration (e.g., 100% of the specification level).
- From this single preparation, aliquot a minimum of six separate sample preparations and analyze them according to the validated method [63].
- Ensure all analyses are performed under identical conditions (same analyst, same instrument, same day).
3. Data Analysis:
- For each of the six replicates, record the measured value of the analyte (e.g., concentration or peak area).
- Calculate the mean, standard deviation (SD), and relative standard deviation (%RSD) of the six results.
- The %RSD is calculated as: ( \%\text{RSD} = \frac{\text{SD}}{\text{Mean}} \times 100 )
- The method is considered to have acceptable repeatability if the %RSD is within a pre-defined limit, often ≤10% for forensic applications [64] [63].
Protocol for Determining Specificity
1. Scope: Demonstration of specificity for a GC-MS method screening seized drugs in the presence of potential isomers.
2. Experimental Procedure:
- Inject blank samples (solvent and matrix, if applicable) to demonstrate no interference at the retention times of the analytes of interest.
- Individually inject analytes and potential interfering substances (e.g., isomers like pentylone and 2,3-pentylone) at the target concentration.
- Inject a mixture containing all analytes and potential interferents to challenge the method.
3. Data Analysis:
- Chromatographic Separation: Report the retention time for each analyte. Calculate the resolution (Rs) between the two most closely eluting compounds; Rs > 1.5 is generally considered baseline resolution [63].
- Spectral Confirmation: For each peak, compare the mass spectrum against a certified reference standard using a library search. Report the match score. A score exceeding a laboratory's quality threshold (e.g., >90% match quality) confirms specificity [64] [3].
- Peak Purity: If using a photodiode array (PDA) detector, perform a peak purity assessment. The peak is considered pure if the purity angle is less than the purity threshold [63].
Workflow and Relationship Diagrams
Figure 1. A workflow diagram illustrating the parallel assessment of core validation parameters and the decision-making process within a risk assessment framework.
Figure 2. The logical relationship between potential risks in forensic analysis, the corresponding validation parameters that control them, and the specific experimental protocols used for risk mitigation.
The Scientist's Toolkit: Essential Research Reagents & Materials
Table 3: Key Reagents and Materials for Forensic Method Validation
| Item | Function / Application |
|---|---|
| Certified Reference Materials (CRMs) | Provide the accepted true value for accuracy and specificity assessments; essential for calibration [64] [3]. |
| Sodium Dithionite (Na₂S₂O₄) | A reducing agent used in postmortem CO analysis to convert methemoglobin (MetHb) back to functional heme hemoglobin, thereby restoring CO-binding ability and improving accuracy in putrefied samples [67]. |
| DB-5 ms Capillary Column | A common (5%-phenyl)-methylpolysiloxane GC column used for the separation of a wide range of analytes in seized drug and forensic toxicology analysis [3]. |
| Liberating Agent (e.g., K₃[Fe(CN)₆]) | A solution (e.g., potassium ferricyanide) added to release bound CO from hemoglobin into the gas phase for headspace analysis by GC [67]. |
| Headspace (HS) Vials | Used in conjunction with GC for the analysis of volatile organic compounds (e.g., ethanol) from complex matrices like vitreous humor or blood, minimizing sample preparation and instrument contamination [66]. |
Within a risk assessment framework for forensic method validation, establishing the reliability and error rates of analytical procedures is paramount. Cross-validation, the practice of comparing results from multiple tools or techniques, provides a powerful methodology for quantifying this uncertainty and strengthening scientific conclusions. This document outlines application notes and protocols for implementing cross-validation strategies, with a specific focus on their role in validating forensic methods, from digital evidence analysis to risk assessment tools used in criminal justice. The core principle is that a method or finding confirmed by multiple, independent means is inherently more trustworthy and defensible.
The following sections provide a detailed comparative analysis of key cross-validation techniques, present structured experimental protocols for their application, and visualize the integration of these practices into a robust forensic validation workflow.
Comparative Analysis of Cross-Validation Techniques
Selecting an appropriate cross-validation technique is critical for obtaining a realistic assessment of a model's performance. The table below summarizes the core characteristics, advantages, and limitations of several common methods.
Table 1: Comparison of Common Cross-Validation Techniques
| Technique | Core Principle | Key Advantages | Key Limitations | Ideal Forensic Application Context |
|---|---|---|---|---|
| Hold-Out Validation [68] | Simple random split of dataset into single training and testing set. | - Computationally efficient and straightforward to implement.- Useful for initial, quick model assessment. | - Performance estimate can have high variance due to dependence on a single, random data split.- Not suitable for small datasets. | Preliminary validation of a digital forensic tool function on a large, well-understood evidence dataset. |
| K-Fold Cross-Validation [69] [68] | Dataset is randomly partitioned into k equal-sized folds or subsets. The model is trained k times, each time using k-1 folds for training and the remaining fold for testing. | - More reliable performance estimate than Hold-Out by leveraging all data for both training and testing.- Reduces variance of the estimate. | - Higher computational cost than Hold-Out.- Requires multiple model trainings. | General-purpose model evaluation for forensic risk assessment tools or machine learning models used in evidence analysis. |
| Repeated K-Fold Cross-Validation [69] | The K-Fold process is repeated multiple times (n), with different random partitions of the data into k folds each time. | - Further reduces the variability of the performance estimate introduced by the random data splitting in K-Fold.- Provides a more robust and stable estimate. | - Computationally intensive (n x k model trainings). | Final, rigorous validation of a high-stakes model where the most stable performance estimate is required. |
| Leave-One-Out Cross-Validation (LOOCV) [69] | A special case of K-Fold where k equals the number of data samples (N). Each model is trained on all but one sample, which is used for testing. | - Virtually unbiased estimate as it uses N-1 samples for training.- Ideal for very small datasets. | - Extremely high computational cost for large datasets (N model trainings).- Performance estimate can have high variance. | Validating analytical methods for a rare type of digital evidence where only a few positive samples are available. |
The choice of technique directly impacts the reliability of the validation. For instance, a study comparing object detection models for a "smart and lean pick-and-place solution" found that K-Fold cross-validation provided a more robust evaluation, leading to a 6.26% improvement in mean Average Precision (mAP) compared to a baseline, while Hold-Out validation showed a higher but potentially less generalizable 44.73% mAP improvement [68]. Furthermore, computational costs vary significantly; the same study noted that while K-Fold is efficient, Repeated K-Fold can demand orders of magnitude more processing time, a critical factor in resource-constrained environments [69].
Experimental Protocols for Cross-Validation
Protocol for Tool-Function Cross-Validation in Digital Forensics
This protocol is designed to validate that a specific function (e.g., data recovery, string searching) in a forensic software tool produces accurate and consistent results, in line with standards such as those from the National Institute of Standards and Technology (NIST) [70].
- Define Requirements and Acceptance Criteria: Precisely define the function to be tested and the criteria for a successful outcome. For a data carving tool, this could be the percentage of known test files correctly recovered without alteration.
- Select or Create Test Data: Use a validated forensic image or create a custom dataset with known content (e.g., files with specific strings, hashes, and metadata). The data must be representative of real-case scenarios and include "challenge" data to stress-test the tool [13].
- Establish a Ground Truth Baseline: Process the test data using a previously validated tool or method to establish a known-good set of results (the ground truth).
- Execute Tool Function: Run the tool under test on the same test data, applying the defined function.
- Compare and Analyze Results: Automatically compare the output of the tool under test against the ground truth.
- Quantitative Analysis: Calculate metrics such as true positives, false positives, false negatives, precision, and recall.
- Qualitative Analysis: Check for any anomalies in the output, such as corrupted data or incorrect metadata.
- Verify Hash Integrity: Where applicable, use tools like ProDiscover's Auto Verify Image Checksum feature to ensure the integrity of the forensic image before and after analysis, confirming that the acquisition was not corrupted [70].
- Document and Report: Document the entire process, including the test environment, tool versions, test data, and all results. The report must be clear, unambiguous, and reproducible by another expert in a different laboratory [70].
Protocol for Risk Assessment Tool Cross-Validation
This protocol addresses the validation of violence risk assessment tools used in forensic psychiatry and criminal justice, where understanding the trade-off between false positives and false negatives is ethically critical [20].
- Contextual Definition: Define the specific application context (e.g., parole decisions, post-sentence detention). This determines the ethical balance between false positives (unnecessarily extended detention) and false negatives (premature release of a high-risk individual) [20].
- Dataset Curation and Stratification: Assemble a historical dataset of assessed individuals with known long-term outcomes. Stratify the dataset by relevant subpopulations (e.g., gender, ethnicity, offense type) to enable analysis of predictive accuracy across groups [20].
- Apply Multiple Risk Assessment Tools: Score the dataset using two or more validated risk assessment tools (e.g., VRAG, HCR-20, LS/CMI).
- Performance Metric Calculation: For each tool and subpopulation, calculate a comprehensive set of performance metrics, including:
- Sensitivity and Specificity: To understand the tool's ability to identify true positives and true negatives.
- Positive Predictive Value (PPV) and Negative Predictive Value (NPV): To understand the probability that a positive/negative score is correct in your specific context and population.
- False Positive and False Negative Rates: Directly quantify the potential for misclassification harm [20].
- Comparative Statistical Analysis: Perform statistical tests to compare the performance of the tools. Analyze whether differences in accuracy, particularly false positive rates, are consistent across different demographic subgroups to identify potential bias.
- Outcome Analysis and Reporting: Report the findings, highlighting the trade-offs between different tools. For example, state: "While Tool A had a higher overall accuracy, Tool B demonstrated a significantly lower false positive rate in the defined context, which may be preferable given the legal and ethical implications of unnecessary detention."
Visualizing the Cross-Validation Workflow in Forensic Validation
The following diagram illustrates the logical workflow for integrating cross-validation into a comprehensive forensic method validation framework, from planning to implementation.
Figure 1: A logical workflow for the integration of cross-validation strategies into a forensic method validation process, highlighting decision points and iterative refinement.
The Scientist's Toolkit: Essential Research Reagents and Materials
The following tools and platforms are essential for conducting rigorous cross-validation and MLOps in a modern research environment, including forensic method development.
Table 2: Essential Tools for Cross-Validation and Model Lifecycle Management
| Tool Name | Category / Function | Brief Description & Role in Cross-Validation |
|---|---|---|
| MLflow [71] [72] | Experiment Tracking & Model Management | An open-source platform to log parameters, code versions, metrics, and outputs from cross-validation runs, ensuring full reproducibility and comparison between different model iterations. |
| TensorFlow Extended (TFX) [73] | End-to-End ML Platform | Provides a complete framework for building production-ready, deployable ML pipelines, including components for data validation, model validation, and continuous evaluation that are essential for large-scale cross-validation. |
| DVC (Data Version Control) [72] | Data Versioning | Integrates with Git to version control datasets and models, ensuring that every cross-validation experiment is tied to the exact version of data on which it was run. |
| KNIME Analytics [73] | Visual Workflow for Data Science | A visual platform allowing researchers to build and execute complex data preprocessing, modeling, and cross-validation workflows without extensive coding, promoting transparency and reproducibility. |
| Google Cloud Vertex AI [73] [71] | End-to-End MLOps Platform | A unified environment that offers built-in support for automated model training (AutoML) and custom training with integrated tools for orchestrating cross-validation jobs at scale on cloud infrastructure. |
| H2O.ai [73] | Automated Machine Learning | Delivers open-source ML with a strong focus on automatic feature engineering and model explainability, which includes robust automated cross-validation to ensure model reliability and transparency. |
| ProDiscover [70] | Digital Forensics Software | A commercial forensics tool that includes features like Auto Verify Image Checksum, which is critical for validating the integrity of evidence data before it is used in any analytical or cross-validation procedure. |
| Weights & Biases (W&B) [71] | Experiment Tracking | A machine learning platform for tracking experiments, visualizing results, and comparing model performances across different cross-validation folds and hyperparameters. |
| Kubeflow [71] [72] | MLOps on Kubernetes | An open-source platform dedicated to deploying, orchestrating, and managing scalable and portable ML workflows, including complex cross-validation pipelines, on Kubernetes clusters. |
| Databricks [73] [71] | Unified Data Analytics | Provides a collaborative, cloud-based platform built on Apache Spark, ideal for running cross-validation on very large datasets that are common in forensic data analysis and risk modeling. |
Quantitative Benefit-Risk Assessment (qBRA) Frameworks for Medical Products
Quantitative Benefit-Risk Assessment (qBRA) represents a structured, transparent approach to evaluating medical products by formally integrating quantitative data on clinical outcomes with explicit preference weights from relevant stakeholders. Unlike qualitative assessments that rely on implicit judgment, qBRA provides a reproducible methodology for combining data on product performance with stakeholder values to inform critical decisions throughout the medical product lifecycle [74] [75]. The adoption of qBRA has gained significant momentum in recent years among regulatory agencies and pharmaceutical manufacturers seeking to enhance the rigor, transparency, and patient-centricity of their decision-making processes [74].
The fundamental premise of qBRA is that while the benefits of many medical products clearly outweigh their risks, some present complex trade-offs that challenge purely qualitative clinical judgment [74]. In these circumstances, qBRA provides additional insights that are invaluable for decision-making by making the weighting of benefits and risks explicit and evidence-based [74]. Regulatory interest in qBRA has heightened markedly over the past decade, with agencies including the FDA and EMA increasingly encouraging sponsors to apply quantitative approaches [75].
Core Methodological Frameworks and Applications
Primary qBRA Methodologies
Table 1: Core Methodological Approaches in Quantitative Benefit-Risk Assessment
| Method | Key Features | Typical Applications | Advantages |
|---|---|---|---|
| Multi-Criteria Decision Analysis (MCDA) | Uses value functions to convert multiple benefit-risk attributes to common units for evaluation [76] | Regulatory submissions, internal portfolio decision-making [75] [76] | Structured framework, handles multiple endpoints explicitly |
| Stochastic Multicriteria Acceptability Analysis (SMAA) | Extends MCDA to incorporate uncertainty in weights and measurements [76] | Complex decisions with significant uncertainty [76] | Accounts for parameter uncertainty, provides probabilistic results |
| Discrete Choice Experiment (DCE) | Elicits stakeholder preferences through series of choices between alternative profiles [75] | Patient preference studies, weighting endpoints [75] | Directly captures trade-offs respondents are willing to make |
| Bayesian Benefit-Risk Analysis | Incorporates prior information and integrates various sources of uncertainty [77] [76] | Early development decisions, leveraging historical data [77] | Formal use of prior evidence, links to optimal decision theory |
Industry Adoption and Implementation Contexts
Recent research indicates that while most major life sciences companies have applied qBRA methodologies, implementation is typically concentrated on a small fraction of assets where the benefit-risk profile is particularly complex [75]. These applications primarily support internal decision-making processes and regulatory submissions, with positive impacts reported in improved team decision-making and communication [75]. The most significant adoption drivers include championing by senior company leadership and demonstrated receptivity from regulators to such analyses [75].
qBRA finds application across the medical product lifecycle, from early development through post-marketing surveillance [75] [78]. In discovery and development phases, understanding benefit-risk tradeoffs important to patients and clinicians can inform pipeline prioritization based on expected benefit-risk profiles [75]. During regulatory review, qBRA provides a transparent framework for presenting complex trade-offs, while post-approval it can incorporate real-world evidence to refine benefit-risk understanding [78].
Standardized qBRA Protocol: A Five-Step Framework
A recent ISPOR Task Force established good practice guidelines for qBRA implementation, outlining five core steps for robust assessment [74]. The following protocol provides detailed methodologies for implementing this framework.
Step 1: Define the Research Question and Decision Context
Objective: Establish clear parameters for the assessment that address decision-maker needs and specify the role of external experts [74].
Protocol:
- Identify Decision Makers and Needs: Determine whether the assessment will inform internal development decisions, regulatory submissions, or post-marketing evaluations
- Characterize Preference Data Requirements: Specify whose values will inform the weighting (patients, clinicians, regulators) and the preference elicitation approach
- Establish Expert Involvement: Define the role and selection criteria for subject matter experts, including clinical, statistical, and patient representation
- Define Scope and Boundaries: Clearly articulate the decision being informed, alternatives being compared, and time horizon for evaluation
Step 2: Develop the Formal Analysis Model
Objective: Select benefit and safety endpoints while establishing a model structure that avoids double counting and accounts for attribute dependencies [74].
Protocol:
- Endpoint Selection: Identify critical efficacy and safety endpoints from available clinical data, considering:
- Clinical relevance to decision makers
- Statistical robustness of measurements
- Independence from other selected endpoints
- Model Structure Definition: Establish hierarchical value tree if using MCDA, ensuring:
- Logical grouping of related endpoints
- Clear separation between benefit and risk domains
- Appropriate level of aggregation for interpretability
- Dependency Assessment: Evaluate statistical and clinical dependencies between attributes and adjust model structure or weighting approach accordingly
Objective: Elicit quantitative weights that reflect the relative importance of benefits versus risks from relevant stakeholders [74].
Protocol:
- Method Selection: Choose appropriate preference elicitation method based on decision context:
- MCDA Swing Weighting: For technical experts and regulatory decisions
- Discrete Choice Experiments: For patient and clinician preferences
- Threshold Technique: For establishing minimum acceptable benefit
- Attribute Framing: Develop clear descriptions of each attribute for the elicitation instrument, including:
- Clinical meaning of the endpoint
- Range of possible outcomes (best to worst)
- Base case or reference level
- Data Quality Evaluation: Implement quality checks for preference data through:
- Consistency tests within elicitation instruments
- Test-retest reliability assessments
- Evaluation of cognitive burden on respondents
Step 4: Analysis and Uncertainty Assessment
Objective: Generate base-case benefit-risk results and comprehensively evaluate uncertainty and heterogeneity [74].
Protocol:
- Weight Normalization: Convert raw preference weights to ratio-scale values summing to 100% across all attributes
- Base-Case Analysis: Calculate overall benefit-risk balance using the formal model and base-case inputs
- Sensitivity Analysis: Conduct comprehensive uncertainty assessment through:
- Deterministic sensitivity analyses on individual parameters
- Probabilistic sensitivity analysis incorporating joint parameter uncertainty
- Scenario analyses for alternative clinical assumptions or preference weights
- Heterogeneity Assessment: Evaluate variation in benefit-risk balance across patient subgroups or stakeholder perspectives
Step 5: Communication of Results
Objective: Effectively communicate results to decision makers and other stakeholders through appropriate visualization and contextualization [74].
Protocol:
- Visualization Development: Create tailored visualizations for different audiences:
- Value contribution plots for technical audiences
- Summary trade-off graphics for executive decision makers
- Plain language summaries for patient communities
- Uncertainty Communication: Present sensitivity and heterogeneity results through:
- Tornado diagrams showing key drivers
- Scatter plots of probabilistic analyses
- Subgroup benefit-risk plots
- Contextualization: Frame results with appropriate comparators and clinical context to support interpretation
Figure 1: qBRA Implementation Workflow showing the five-step process for quantitative benefit-risk assessment
Advanced Methodological Approaches
Bayesian Methods for qBRA
Bayesian inference provides a natural framework for conducting quantitative assessments of benefit-risk trade-offs, offering several advantages over conventional approaches [77]. The Bayesian paradigm allows for formal incorporation of prior information and integration of various sources of evidence while explicitly accounting for uncertainty in the benefit-risk balance [77] [76]. This approach is particularly valuable in settings with limited data, where borrowing strength from related products or indications can strengthen inferences, and when linking to optimal decision theory for development planning [77].
Bayesian qBRA Protocol:
- Prior Elicitation: Define informative or non-informative prior distributions for key benefit and risk parameters based on historical data or expert opinion
- Evidence Synthesis: Integrate multiple sources of evidence (clinical trials, real-world evidence, mechanistic knowledge) within a coherent probabilistic framework
- Posterior Computation: Calculate posterior distributions for benefit-risk balance using Markov Chain Monte Carlo methods or analytical approximations
- Decision-Theoretic Application: Link posterior inferences to loss functions or value-based decision rules to identify optimal decisions
Addressing Methodological Challenges
Despite methodological advances, qBRA implementation faces several persistent challenges that require careful consideration in protocol design. Benefit-risk assessment is inherently dynamic, with clear imbalances in the sources, timing, and nature of information available throughout a medical product's development and lifecycle management [76]. Key challenges include handling multiple dimensions of favorable and unfavorable effects, appropriately characterizing and propagating uncertainty, and ensuring clinical relevance while maintaining methodological rigor [76].
Advanced qBRA frameworks address these challenges by allowing assessment in multiple dimensions of favorable and unfavorable aspects while accommodating clinical relevance through selection of clinically meaningful criteria and accounting for heterogeneity in patient preferences and characteristics [76]. These frameworks efficiently summarize quantitative evidence to support decision-making while maintaining transparency about limitations and assumptions.
Essential Research Reagents and Tools
Table 2: Essential Methodological Tools for Quantitative Benefit-Risk Assessment
| Tool Category | Specific Solutions | Function | Application Context |
|---|---|---|---|
| Statistical Software | R (prefLib, MCDA, bayesBR), SAS, Python | Data analysis, modeling, and visualization | End-to-end qBRA implementation [76] |
| Preference Elicitation Platforms | 1000minds, Adaptive Choice BASeS | Design and administration of preference surveys | Discrete choice experiments, swing weighting [75] |
| Decision Modeling | Logical Decisions, Hiview, MCDA Dashboard | Multi-criteria decision analysis with visualization | Structured decision conferences, portfolio prioritization [75] |
| Uncertainty Analysis | @Risk, Crystal Ball | Probabilistic sensitivity analysis | Characterizing uncertainty in benefit-risk balance [76] |
| Visualization Tools | Tableau, Spotfire, ggplot2 | Creation of benefit-risk graphics and interactive displays | Communication to diverse stakeholders [74] |
Figure 2: qBRA Ecosystem showing the relationship between data sources, analytical methods, implementation tools, and decision outputs
Connections to Forensic Method Validation
While developed for medical product evaluation, qBRA principles show significant conceptual parallels with validation frameworks in forensic sciences. Both domains require demonstrating that methodologies are "fit for purpose" through structured validation processes that provide objective evidence of reliability [13]. The determination of end-user requirements – a fundamental step in digital forensics method validation [13] – mirrors the critical importance of identifying decision-maker needs in qBRA [74].
In forensic method validation, the expectation is that methods to produce data for expert opinion are valid, with validation demonstrating fitness for specific intended purposes and understanding of limitations [13]. Similarly, qBRA requires transparent documentation of methodological choices and limitations to ensure appropriate interpretation by decision makers [74] [78]. Both fields face challenges with adoption of standardized methodologies, with forensic practice noting that many methods require treatment as "laboratory-developed methods" even when adapted from existing approaches [13] – a phenomenon similarly observed in qBRA implementation across pharmaceutical companies [75].
The structured process for method validation in digital forensics – comprising determination of end-user requirements, specification development, risk assessment, acceptance criteria setting, validation planning, and outcomes assessment [13] – provides a valuable template for standardizing qBRA application across organizations and decision contexts. This alignment suggests opportunities for cross-disciplinary methodological exchange between forensic science and medical product development in advancing rigorous, transparent assessment frameworks.
The integration of Artificial Intelligence (AI), particularly machine learning (ML) and deep learning, into forensic science represents a paradigm shift, introducing new dimensions of complexity to the traditional method validation framework [79] [80]. AI-driven tools can process vast volumes of data at speeds unattainable by human analysts, identifying complex patterns in everything from chromatographic data for source attribution to synthetic media in digital evidence [79] [81]. However, their "black box" nature, where the internal decision-making logic can be opaque, challenges established principles of forensic transparency and reliability. Validation in this context, therefore, must evolve beyond verifying consistent output to include scrutiny of the model's architecture, the data it was trained on, and its performance across diverse, real-world scenarios [13]. This document outlines application notes and protocols for validating AI-driven forensic tools within a robust risk assessment framework, ensuring they meet the stringent requirements for scientific and legal admissibility.
Validation Framework and Risk Assessment for AI Tools
Validating an AI-driven forensic tool is a systematic process designed to provide objective evidence that the method is fit for its intended purpose [13]. This process must be risk-based, identifying and mitigating potential points of failure unique to AI systems, such as data bias, model overfitting, and vulnerability to adversarial attacks. The framework, adapted from guidelines for digital forensics, is a cycle of defined stages that ensure thoroughness and accountability [13].
Core Validation Lifecycle Stages:
- Determination of End-User Requirements: This foundational step defines what the tool must reliably accomplish. Requirements must be specific, measurable, and traceable. For an AI tool, this includes defining the specific types of evidence it will analyze (e.g., GC-MS chromatograms, video files), the questions it will answer (e.g., "Do these two diesel samples share a common origin?"), and the required form of its output (e.g., a Likelihood Ratio) [79] [13].
- Risk Assessment of the Method: This involves a proactive analysis of what could cause the AI method to fail or produce misleading results. Key risks include:
- Training Data Bias: The model is trained on non-representative data, leading to poor performance on specific demographics or sample types [20].
- Data Drift: The model's performance degrades over time as the nature of the evidence it encounters evolves.
- Over-reliance on Automation: The risk that human analysts will cede their judgment to the AI output without critical review [81] [82].
- Adversarial Attacks: Malicious manipulation of input data to deceive the AI model.
- Setting Acceptance Criteria: These are the quantitative and qualitative benchmarks the tool must meet to be deemed valid. They are derived directly from the user requirements and the risk assessment. Examples include a minimum threshold for accuracy, precision, and a maximum allowable rate of false positives/negatives [13].
- The Validation Plan & Exercise: This is the detailed protocol for testing the tool against the acceptance criteria. For AI, this requires a diverse and challenging test dataset that is completely separate from the training data. The plan should include "stress tests" with complex, ambiguous, or deliberately corrupted data to evaluate the model's robustness and limitations [13].
- Assessment and Reporting: The results of the validation exercise are compiled into a report that objectively states whether the acceptance criteria were met. The report must also clearly document the tool's limitations and the specific contexts in which it can be reliably used [13].
Quantitative Performance Data
Validation requires empirical evidence of performance. The following tables summarize key metrics from validation studies, providing a benchmark for evaluating AI-driven forensic tools.
Table 1: Comparative Performance of AI vs. Traditional Forensic Methods
| Application Area | Traditional Method Accuracy/Time | AI-Driven Method Accuracy/Time | Key Performance Insight |
|---|---|---|---|
| Source Attribution (Diesel) | Benchmark Statistical Models (LR: 180-3200) [79] | CNN-based Model (LR: ~1800) [79] | Convolutional Neural Network (CNN) model showed robust performance, effectively processing complex chromatographic patterns [79]. |
| Phishing Detection | 68% Accuracy [80] | 89% Accuracy [80] | AI methods significantly improved detection rates over traditional manual analysis [80]. |
| General Cyber Incident | 75% Detection Rate [80] | 92% Detection Rate [80] | AI-enhanced forensic methods demonstrated a 17% improvement in accuracy [80]. |
| Evidence Processing | Weeks to months (Manual review) [80] | Hours to days (Automated analysis) [80] | AI automation provides a significant reduction in investigation timelines [80]. |
Table 2: AI Model Performance Metrics for Forensic Source Attribution
| Performance Metric | Score-Based CNN Model (A) | Score-Based Statistical Model (B) | Feature-Based Statistical Model (C) |
|---|---|---|---|
| Median LR (H1: Same Source) | ~1800 [79] | ~180 [79] | ~3200 [79] |
| Discriminative Power | Good to Excellent (AUC 0.70-0.80 range typical for validated tools) [15] | Good to Excellent (AUC 0.70-0.80 range typical for validated tools) [15] | Good to Excellent (AUC 0.70-0.80 range typical for validated tools) [15] |
| Key Advantage | Learns features directly from raw data; no need for manual feature selection [79] | Based on pre-defined, expert-selected peak ratios [79] | Constructs probability densities from key feature ratios [79] |
| Primary Limitation | Requires large datasets for training; "black box" interpretation [79] | Limited by human expert's feature selection [79] | Limited by human expert's feature selection [79] |
Experimental Protocols for AI Tool Validation
Protocol 1: Validation of a Machine Learning Model for Chemical Source Attribution
This protocol outlines the validation of an AI model, such as a Convolutional Neural Network (CNN), for attributing a questioned sample (e.g., diesel oil) to a specific source based on Gas Chromatography – Mass Spectrometry (GC/MS) data [79].
1. Objective: To validate a CNN-based model for determining whether two diesel oil samples originate from the same source, and to quantify the strength of this evidence using a Likelihood Ratio (LR) framework [79].
2. Hypotheses:
- H1: The questioned (Q) and known (K) samples originate from the same source.
- H2: The questioned (Q) and known (K) samples originate from different sources [79].
3. Materials and Reagents:
- Gas Chromatograph – Mass Spectrometer (GC/MS): For example, an Agilent 7890A GC coupled with an Agilent 5975C MS detector [79].
- Reference Diesel Samples: A validated set of 136 or more samples from known sources (e.g., gas stations, refineries) to be split into training, validation, and test sets [79].
- Solvent: Dichloromethane (CH₂Cl₂), analytical grade [79].
- Computing Environment: Workstation with sufficient GPU and RAM for deep learning model training and evaluation (e.g., Python with TensorFlow/PyTorch, scikit-learn).
4. Procedure: 1. Sample Preparation: Dilute each diesel oil sample in approximately 7 mL of dichloromethane and transfer to a GC vial [79]. 2. Data Acquisition: Analyze all samples using a consistent GC/MS method as defined in the developmental validation [79]. 3. Data Preprocessing: Export the raw chromatographic signal. Apply necessary pre-processing (e.g., alignment, normalization, LambertW transformation for certain statistical models) [79]. 4. Dataset Partitioning: Randomly split the data into three independent sets: - Training Set (e.g., 60%): Used to train the CNN model. - Validation Set (e.g., 20%): Used for hyperparameter tuning during training. - Test Set (e.g., 20%): Used only for the final, unbiased evaluation of model performance. 5. Model Training: Train the CNN model on the training set. The model should learn to extract relevant features directly from the raw chromatographic data [79]. 6. LR System Calibration: Develop a score-based LR system using the features extracted by the CNN. This converts a similarity score between Q and K into a quantitative Likelihood Ratio [79]. 7. Performance Evaluation: Apply the fully trained model and LR system to the held-out test set. Calculate performance metrics including: - Distributions of LRs for same-source and different-source comparisons. - Discriminative Power using metrics like Area Under the Curve (AUC) of the ROC plot. - Calibration to assess the validity and reliability of the LR values (e.g., using ECE plots, PAV-OLR) [79].
5. Data Analysis: Compare the performance of the CNN model against benchmark statistical models (e.g., models based on expert-selected peak height ratios) to demonstrate its relative validity and fitness for purpose [79].
Protocol 2: Performance Validation of an AI-Based Digital Evidence Triage Tool
1. Objective: To validate an AI tool (e.g., using Natural Language Processing or predictive analytics) that automates the initial triage of digital evidence from large datasets, such as emails, logs, or communications [82].
2. Materials:
- AI Triage Tool: The software platform to be validated.
- Ground-Truthed Dataset: A large, diverse dataset of digital artifacts (e.g., emails, chat logs, documents) where a ground truth classification (e.g., "relevant" vs. "non-relevant," "malicious" vs. "benign") has been established by human experts.
- Computing Infrastructure: Appropriate server or cloud environment to handle the data volume.
3. Procedure: 1. Define Triage Categories: Clearly define what the AI tool is classifying (e.g., "priority for human review," "potential phishing email," "evidence of intellectual property theft"). 2. Baseline Establishment: Have a panel of qualified forensic analysts manually triage a representative subset of the data to establish the "ground truth." 3. Blinded Testing: Run the AI tool on the ground-truthed dataset. 4. Metric Calculation: Compare the AI's output to the ground truth and calculate: - Accuracy, Precision, and Recall - False Positive and False Negative Rates: Critical for understanding the risk of missing evidence or wasting resources [20]. - Time-to-Triage: Measure the time saved compared to a fully manual process [80]. 5. Robustness Testing: Test the tool with noisy, incomplete, or novel data types to understand its failure modes.
Research Reagent Solutions and Essential Materials
Table 3: Essential Research Toolkit for AI Forensic Tool Validation
| Tool / Material | Function in Validation | Application Context |
|---|---|---|
| Validated Reference Sample Sets | Serves as ground-truthed data for training and testing AI models; must be representative of casework [79]. | Chemical source attribution, digital file authentication, synthetic media detection. |
| GC-MS Instrumentation | Generates the high-quality, complex chemical data used to build and validate AI models for material analysis [79]. | Fire debris analysis, drug profiling, oil spill fingerprinting. |
| Convolutional Neural Network (CNN) | A deep learning architecture ideal for finding patterns in complex, multi-dimensional data like images, spectra, and chromatograms [79] [80]. | Analysis of chromatographic data, video and image authentication, facial recognition. |
| Likelihood Ratio (LR) Framework | A quantitative framework for evaluating the strength of evidence, providing a transparent and logically correct method for reporting AI findings [79]. | Source attribution, comparison of any digital or physical evidence. |
| Structured Professional Judgment (SPJ) Tools | Established, validated risk assessment frameworks that provide a benchmark and structural model for developing new AI tools [15]. | Violence risk assessment (e.g., HCR-20v3), sexual offense risk assessment. |
| Natural Language Processing (NLP) Engine | Allows AI tools to parse, understand, and categorize unstructured text data from emails, documents, and chat logs [82] [80]. | Automated evidence triage, eDiscovery, investigation of encrypted communications. |
Workflow and Signaling Pathway Diagrams
The following diagram illustrates the core logical workflow for the validation of an AI-driven forensic tool, integrating both technical and governance steps.
Diagram 1: AI forensic tool validation workflow.
This workflow demonstrates the iterative, evidence-based process for validating an AI-driven forensic tool, from initial scoping to operational deployment and continuous monitoring.
The adoption of the open-source programming language R for clinical trial analysis and reporting represents a significant shift in the pharmaceutical regulatory landscape. Unlike proprietary software, open-source packages vary widely in their quality, maintenance, and testing rigor, making robust validation processes essential for regulatory compliance [83]. Regulatory bodies like the FDA require software validation to ensure consistent, reliable outputs, defined as "establishing documented evidence which produces a high degree of assurance that a specific process will consistently produce a product meeting its predetermined specifications and quality characteristics" [83]. This application note details the frameworks and case studies emerging from industry leaders to address these challenges through a hybrid validation approach combining programmatic tools with expert human judgment.
Industry-Wide Initiative: R Consortium FDA Pilots
The R Consortium's Working Group has pioneered a series of pilot submissions to test and validate the use of R in regulatory contexts, with participation from major pharmaceutical companies including Merck, Novartis, Roche, Eli Lilly, and GlaxoSmithKline [84] [85] [86]. These pilots methodically increased in complexity to explore different aspects of R-based submissions, with all code, documentation, and feedback made publicly available to serve as blueprints for the industry [85].
Table 1: Evolution of R Consortium FDA Pilot Submissions
| Pilot Phase & Timeline | Primary Focus & Objectives | Key Outcomes & Regulatory Feedback |
|---|---|---|
| Pilot 1 (2021-2022) [85] | Deliver four static Tables, Listings, and Figures (TLFs) using R with simulated data. | FDA provided positive feedback in 2022, confirming R could generate regulatory-grade static outputs [85]. |
| Pilot 2 (2022-2023) [85] | Package TLFs into an interactive Shiny app delivered via the eCTD portal. | Successfully reviewed in 2023; FDA advised removing p-values from filtered tables to prevent misinterpretation [85]. |
| Pilot 3 (2023-2024) [85] | Use R to generate Analysis Data Models (ADaMs) feeding into TLFs. | Received FDA approval in April 2024, validating R for critical data preparation steps [85]. |
| Pilot 4 (In Progress) [85] | Compare WebAssembly and container technology for delivering Shiny apps. | Initial FDA feedback found WebAssembly easier as it runs in a browser without a container runtime [85]. |
| Pilot 5 (Just Starting) [85] | Explore dataset-JSON format to potentially replace legacy XPT files. | Aims to streamline data formatting and enhance compatibility with modern data science workflows [85]. |
Corporate Case Studies: Validation Frameworks in Practice
Merck: External R Package Qualification
Merck has developed a systematic algorithm to qualify CRAN packages for use in its GxP environment. Following the R Validation Hub's framework, the company classifies base R packages as Level 1, acknowledging the R Foundation's efforts to ensure their validity. For other packages, Merck implements a risk-based qualification process [84].
Roche: Automated Validation with Human Oversight
Roche employs an automated R package validation process that incorporates a "human-in-the-middle" component to reconcile gaps in automated metadata checks. This approach balances automation with risk mitigation, encourages in-house package development, and introduces transparency to the validation process while ensuring high package quality for regulatory use [84].
Novartis: Risk Assessment for R Packages
Novartis addresses the unique challenge of validating imported R packages within drug submission projects. The company recognizes that while data validation and in-house source code validation follow standard practices, the open-source nature of R requires specialized risk assessment methodologies for package validation [84].
Experimental Protocol: Hybrid Risk Assessment Methodology
The following protocol outlines a comprehensive, hybrid approach to R package risk assessment, integrating both automated tools and expert human judgment as implemented by industry leaders.
Protocol: Hybrid Risk Assessment for R Packages
Purpose: To establish a standardized methodology for evaluating the suitability and reliability of R packages for use in regulatory submissions.
Scope: Applicable to all R packages considered for use in clinical trial analysis and reporting intended for FDA or other health authority submissions.
Principles: This hybrid approach combines programmatic risk assessment using tools like {riskmetric} with essential expert human review to evaluate aspects that automated tools cannot capture [83].
Procedure:
Package Identification and Categorization
- Action: Identify the R package and its intended use in the analysis workflow.
- Risk Classification: Categorize the package type (e.g., data formatting, visualization, statistical modeling). Statistical modeling packages require more rigorous verification than visualization packages [83].
Automated Metrics Collection
- Tool: Utilize the
{riskmetric}package or similar automated framework to collect quantitative metrics [83]. - Metrics:
- Maintenance Frequency: How often the package is updated.
- Community Usage: Download statistics and prevalence of use.
- Code Coverage: The percentage of functions covered by unit tests (e.g., using
{covr}) [83]. - Documentation Availability: Presence of vignettes and manuals.
- Tool: Utilize the
Expert Human Review
- Maintenance Quality: Assess how issues are addressed, not just frequency. Evaluate if the maintainers are Posit, R Core contributors, or other reputable entities [83].
- Documentation Quality: Evaluate the clarity, thoroughness, and usability of documentation, not just its presence [83].
- Test Quality: Determine if the most crucial functions for the package's intended use are adequately validated, as code coverage percentage alone can be misleading [83].
- Functionality Cross-Check: For packages like
{corrplot}that perform statistical calculations (e.g., significance testing) despite a primary visualization purpose, ensure they are classified and validated with appropriate rigor [83].
Final Risk Assessment and Reporting
- Action: Synthesize automated scores and human review findings into a final risk classification.
- Output: Generate a validation report documenting the evidence that provides assurance the package is fit for its intended use in a regulatory submission.
Workflow Visualization
The following diagram illustrates the sequential and iterative workflow for the hybrid risk assessment protocol:
The Scientist's Toolkit: Essential Research Reagents & Solutions
The following table details key tools and frameworks used in the validation processes described in the industry case studies.
Table 2: Essential Tools and Frameworks for R Package Validation
| Tool / Framework Name | Type / Category | Primary Function in Validation |
|---|---|---|
{riskmetric} [83] |
R Package / Automated Scoring | Provides automated, quantitative risk metrics for R packages (e.g., maintenance frequency, code coverage, community usage). |
renv [85] |
R Package / Dependency Management | Creates reproducible R environments by managing specific package versions, ensuring the same analysis can be run later. |
| OpenVal [83] | Validated Framework / Integrated Solution | Atorus's framework implementing the hybrid philosophy, combining automated checks with structured human review processes. |
| R Validation Hub Framework [84] | Conceptual Framework / Guidelines | Provides the foundational risk-based approach used by companies like Merck to qualify R packages for GxP environments. |
| WebAssembly [85] | Technology / Application Delivery | Allows Shiny applications to run directly in a web browser, simplifying deployment and review for regulatory agencies. |
| Container Technology (e.g., Docker) [85] | Technology / Application Delivery | Packages the entire application environment to ensure consistent execution across different computing systems. |
The pharmaceutical industry's collective experience demonstrates that a hybrid risk assessment strategy—integrating automated metrics with expert human judgment—provides the most robust framework for validating R packages in regulatory submissions. The successful FDA pilot programs and corporate case studies from Merck, Roche, and Novartis establish a clear precedent for using open-source tools in even the most highly regulated environments. This approach ensures scientific integrity and reliability while embracing the transparency, efficiency, and collaborative potential of the open-source ecosystem, ultimately contributing to more rigorous and reproducible clinical research.
Conclusion
A systematic risk assessment framework is indispensable for ensuring the reliability and admissibility of forensic methods in pharmaceutical research and development. By integrating foundational standards, a structured methodological approach, proactive troubleshooting, and rigorous validation techniques, organizations can significantly mitigate risks. The future of forensic method validation will be shaped by the increasing integration of Artificial Intelligence, demanding even more sophisticated validation protocols to manage the 'black box' complexity. Ultimately, a mature risk assessment strategy not only safeguards product quality and patient safety but also fortifies the scientific and legal integrity of the entire drug development lifecycle.
References
- 1. Digital Forensic : Principles, Validation , and Examples Methods [https://www.linkedin.com/pulse/digital-forensic-validation-principles-methods-examples-james-henning-xbjye]
- 2. Validation of the ORAC-PCQ, an actuarial risk assessment ... [https://www.sciencedirect.com/science/article/abs/pii/S0047235225001667]
- 3. Frontiers | Rapid GC-MS method for screening seized drugs in... [https://www.frontiersin.org/journals/chemistry/articles/10.3389/fchem.2025.1559279/full]
- 4. Dangerousness Index in Forensic Psychiatric Examination [https://pmc.ncbi.nlm.nih.gov/articles/PMC12026387/]
- 5. Essential Cyber Forensics Tools in 2025 : The Top 24... - Craw Security [https://www.craw.sg/cyber-forensics-tools/]
- 6. 9 BEST Digital Forensic ( Tools ) 2025 [https://www.guru99.com/computer-forensics-tools.html]
- 7. What is forensic validation and how is it used? [https://www.envistaforensics.com/knowledge-center/insights/articles/forensic-validation-pay-attention-to-the-man-behind-the-curtain/]
- 8. A transparent approach: Openness in forensic science ... [https://www.sciencedirect.com/science/article/pii/S2589871X24000214]
- 9. The admissibility of digital evidence from open-source ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12431127/]
- 10. Finally a really forensic worldwide standard: ISO 21043 ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12166772/]
- 11. ISO 21043-2:2018 - Forensic sciences — Part 2 [https://www.iso.org/standard/72041.html]
- 12. -3:2025 - Forensic sciences — Part 3: Analysis ISO 21043 [https://www.iso.org/standard/72040.html]
- 13. Method validation in digital forensics (accessible) [https://www.gov.uk/government/publications/method-validation-in-digital-forensics/method-validation-in-digital-forensics-accessible]
- 14. Scientific guidelines for evaluating the validity of forensic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10576079/]
- 15. Forensic Psychiatry Risk Assessment Tools & Standards Guide [https://thebh.us/blog/forensic-psychiatry-risk-assessment-tools-standards-guide/]
- 16. The Frye Standard | Expert Testimony, Admissibility, History [https://www.expertinstitute.com/resources/insights/admitting-expert-testimony-under-the-frye-standard-the-ultimate-guide/]
- 17. The Differences Between the Frye & the Daubert Standards [https://burnswhite.com/differences-between-frye-daubert/]
- 18. The Daubert Standard | Expert Testimony, Admissibility ... [https://www.expertinstitute.com/resources/insights/the-daubert-standard-a-guide-to-motions-hearings-and-rulings/]
- 19. Unpacking Rule Changes on Expert Testimony [https://dicellolevitt.com/unpacking-rule-changes-on-expert-testimony/]
- 20. Risk assessment tools in criminal justice and forensic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5408162/]
- 21. A guide to ISO 21043 Forensic Sciences from the ... [https://www.sciencedirect.com/science/article/pii/S1355030625000887]
- 22. Review Risk-based approach for method development in ... [https://www.sciencedirect.com/science/article/abs/pii/S0731708518312147]
- 23. ICH and FDA Guidelines for Analytical Method Validation [https://www.labmanager.com/ich-and-fda-guidelines-for-analytical-method-validation-34252]
- 24. Analytical Method Development with a Practical Risk ... [https://www.americanpharmaceuticalreview.com/Featured-Articles/619865-Analytical-Method-Development-with-a-Practical-Risk-Assessment-Program-that-Enhances-Commercial-QC-Robustness/]
- 25. The Hidden Risks in Analytical Method Validation - [https://pharmuni.com/2025/05/16/the-hidden-risks-in-analytical-method-validation/]
- 26. Download Free, Customizable Risk Matrix Templates [https://www.smartsheet.com/all-risk-assessment-matrix-templates-you-need?srsltid=AfmBOooBH__W1SzwvXfZ4aIdk5lwcQfcd5U-X4wUCK5-xRINI9y8MQQM]
- 27. Risk Assessment Matrix Template [https://www.vertex42.com/ExcelTemplates/risk-assessment-matrix.html]
- 28. Forensic science providers: validation (accessible) [https://www.gov.uk/government/publications/forensic-science-providers-validation/forensic-science-providers-validation-accessible]
- 29. Qualitative risk assessment [https://www.pmi.org/learning/library/qualitative-risk-assessment-cheaper-faster-3188]
- 30. Guide to Comparing Risk Assessment Methodologies [https://www.zengrc.com/blog/guide-to-comparing-risk-assessment-methodologies/]
- 31. An Introduction to Qualitative Risk Analysis [https://www.safran.com/content/introduction-qualitative-risk-analysis]
- 32. Quantitative risk analysis: Definition, techniques and benefits [https://lumivero.com/resources/blog/quantitative-risk-analysis-101/]
- 33. Quantifying risk [https://www.pmi.org/learning/library/quantitative-risk-assessment-methods-9929]
- 34. Risk Assessment Matrix: Overview and Guide [https://auditboard.com/blog/what-is-a-risk-assessment-matrix]
- 35. 5 Useful Qualitative Risk Analysis Techniques [https://www.project-risk-manager.com/blog/qualitative-risk-techniques/]
- 36. Risk Management Framework 2025 | NIST, COSO, ISO, AI ... [https://www.neotas.com/risk-management-framework/]
- 37. Risk response strategies: mitigation, transfer, avoidance ... [https://twproject.com/blog/risk-response-strategies-mitigation-transfer-avoidance-acceptance/]
- 38. What is Risk Mitigation? The Four Types and How to Apply ... [https://mha-it.com/blog/four-types-of-risk-mitigation]
- 39. Risk Tolerance: Avoid, Transfer, Mitigate, or Accept? [https://www.pivotpointsecurity.com/risk-tolerance-in-business/]
- 40. 2025 Trends In Pharmaceutical Analytical Methods ... [https://agnopharma.com/blog/trends-in-pharmaceutical-analytical-methods-development-validation/]
- 41. Collaborative versus traditional method validation approach [https://pmc.ncbi.nlm.nih.gov/articles/PMC7452674/]
- 42. How to be prepared for Pharmaceutical Validation in 2025 [https://www.gillsprocess.com/blog-1/2024/12/11/how-to-be-prepared-for-pharmaceutical-validation-in-2025]
- 43. 7 Challenges Facing Digital Forensics Teams in 2025 [https://agt-technology.com/7-challenges-facing-digital-forensics-teams-in-2025/]
- 44. Key Trends in Digital Forensics 2025: Chanllenges and ... [https://www.salvationdata.com/knowledge/key-trends-in-digital-forensics-for-2025/]
- 45. CEO Lee Reiber: The Digital Forensics Landscape in 2025 [https://www.oxygenforensics.com/en/resources/digital-forensics-trends-2025/]
- 46. Cybersecurity Forensics: Types and Best Practices [https://www.sentinelone.com/cybersecurity-101/cybersecurity/cybersecurity-forensics/]
- 47. Digital Forensics Round-Up, September 17 2025 [https://www.forensicfocus.com/news/digital-forensics-round-up-september-17-2025/]
- 48. From digital trace to evidence: Challenges and insights ... [https://www.sciencedirect.com/science/article/pii/S1355030625000905]
- 49. A call for open science in forensics - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC11181113/]
- 50. Fraud Risk Management: Strategies & Future Insights in 2025 [https://www.getfocal.ai/blog/fraud-risk-management]
- 51. Proof, Not Promises: The Forensic Path to Compliance [https://oritain.com/resources/blog/proof-not-promises-the-forensic-path-to-compliance]
- 52. US10977147B2 - System for continuous ... - Google Patents monitoring [https://patents.google.com/patent/US10977147B2/en]
- 53. Cleaning Validation Guidelines 2025 [https://www.leucine.io/cleaning-validation-blogs/cleaning-validation-guidelines]
- 54. Violence risk assessment instruments in forensic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10914679/]
- 55. A Comprehensive Guide to Quantitative Risk Frameworks [https://www.metricstream.com/learn/quantitative-risk-frameworks.html]
- 56. 2021 Volume 2 Risk Assessment and Analysis Methods [https://www.isaca.org/resources/isaca-journal/issues/2021/volume-2/risk-assessment-and-analysis-methods]
- 57. 5 Best Practices for Successful Application Risk Assessments [https://www.legitsecurity.com/blog/5-best-practices-for-successful-application-risk-assessments]
- 58. Development and validation of a fast and automated DNA ... [https://www.sciencedirect.com/science/article/abs/pii/S1872497322000795]
- 59. Investigating Methods for Forensic Analysis of Social ... [https://www.frontiersin.org/journals/computer-science/articles/10.3389/fcomp.2025.1673393/full]
- 60. Rogue UIC lab misled courts in cannabis DUI cases [https://www.injusticewatch.org/project/forensic-failures/2025/uic-forensics-lab-cannabis-dui-scandal/]
- 61. 6 Types of Risk Assessment Methodologies + How to Choose [https://drata.com/grc-central/risk/risk-assessment-methodologies]
- 62. Keys to Developing an Effective Risk Assessment ... [https://auditboard.com/blog/risk-assessment-methodology]
- 63. Analytical Method Validation: Back to Basics, Part II [https://www.chromatographyonline.com/view/analytical-method-validation-back-basics-part-ii]
- 64. Validation of a rapid GC–MS method for forensic seized ... [https://www.sciencedirect.com/science/article/abs/pii/S2468170924000614]
- 65. How To Perform Accuracy In Analytical Method Validation [https://pharmaguru.co/accuracy-in-analytical-method-validation/]
- 66. Development and validation of headspace gas ... [https://pubmed.ncbi.nlm.nih.gov/39822986/]
- 67. Advancing forensic accuracy - scientific reports [https://www.nature.com/articles/s41598-025-12183-4]
- 68. A Comparative Analysis of Cross-Validation Techniques for ... [https://www.mdpi.com/2079-9292/12/11/2371]
- 69. LOOCV, K-folds Cross-Validation, and Repeated ... [https://papers.ssrn.com/sol3/papers.cfm?abstract_id=5266507]
- 70. Validating and Testing Forensics Software [https://www.geeksforgeeks.org/techtips/validating-and-testing-forensics-software/]
- 71. MLOps Landscape in 2025: Top Tools and Platforms [https://neptune.ai/blog/mlops-tools-platforms-landscape]
- 72. Top 10 MLOps Tools for 2025 [https://controlplane.com/community-blog/post/top-10-mlops-tools-for-2025]
- 73. Top 9 Machine Learning Platforms for Developers in 2025 [https://amyrasheldon.medium.com/top-9-machine-learning-platforms-for-developers-in-2025-the-ultimate-guide-748ec494ab02]
- 74. Expert Panel Publishes New Guidance on Quantitative ... [https://www.ispor.org/heor-resources/news-top/news/view/2023/04/11/global-expert-panel-publishes-new-guidance-on-designing-conducting-and-analyzing-quantitative-benefit-risk-assessment]
- 75. Quantitative Benefit–Risk Assessment: State of the Practice ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7864811/]
- 76. A new framework to address challenges in quantitative ... [https://www.sciencedirect.com/science/article/abs/pii/S1551714420301518]
- 77. Bayesian Benefit-Risk Analysis: A Framework for ... [https://www.diaglobal.org/zh-cn/conference-listing/meetings/2025/06/dia-2025-global-annual-meeting/agenda/17/bayesian-benefit-risk-analysis-a-framework-for-quantitative-evidence-based-decision-making-in-medical-product-development?ref=BayesianBenefitRiskAnalysisAFrameworkforQuantitativeEvidenceBasedDecisionMakinginMedicalProductDevelopment]
- 78. An Approach to a Benefit-Risk Framework [https://acrpnet.org/2024/04/12/an-approach-to-a-benefit-risk-framework]
- 79. Comparing a machine learning approach with traditional ... [https://www.sciencedirect.com/science/article/abs/pii/S246817092500061X]
- 80. AI-Driven Forensics 101: What It Is and Why It Matters [https://angle.ankura.com/post/102lq8w/ai-driven-forensics-101-what-it-is-and-why-it-matters]
- 81. Beyond The Screen, Part 7: Forensic Readiness For The AI ... [https://lcgdiscovery.com/beyond-the-screen-part-7-forensic-readiness-for-the-ai-era/]
- 82. Deep Dive: AI Forensic Tools and Techniques Driving ... [https://www.linkedin.com/pulse/deep-dive-ai-forensic-tools-techniques-driving-modern-bise--romke]
- 83. Blog: Risk Assessment for R Package Validation [https://www.atorusresearch.com/r-package-risk-assessment-why-a-hybrid-approach-is-the-future-of-package-validation/]
- 84. Case Studies [https://pharmar.org/categories/case-studies/]
- 85. R in FDA Submissions: Lessons Learned from 5 FDA Pilots [https://www.appsilon.com/post/r-in-fda-submissions]
- 86. R packages and Shiny for FDA clinical trial submissions [https://posit.co/blog/fda-shiny-r-package-submissions/]